
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 | ||
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Since 2002
  "This is a historic find, the earliest known recording of sound." – Samuel Brylawski "What are the rights of the discoverer versus the improver? Come, Parisians, don’t let them take our prize." – Édouard-Léon Scott de Martinville, inventor of recorded sound "We don't want to be subject to laws of the Patriot Act." – Tom Puk "Listen, I just think it’s bizarre and funny. My main consideration is that my daughter doesn’t get embarrassed about it." – Rick Astley "We do in fact sell more CDs than we did ten years ago, and I suspect there’ll be a lot of albums sold on CD [in future] as well." – Matt Philips, British Phonographic Industry "This deal is the direct result of public pressure, and the threat of FCC action, against Comcast. But with Comcast's history of broken promises and record of deception, we can't just take their word that the Internet is now in safe hands." – Marvin Ammori "We have decided on our own, not due to any court order or agreement, to bring the TorrentSpy.com search engine to an end and thus we permanently closed down worldwide on March 24, 2008. We now feel compelled to provide the ultimate method of privacy protection for our users - permanent shutdown." – Justin Bunnell "Today all big torrent sites are pressured somehow. TPB has its share of pressure, however we expected it and have a legal system that is more just in cases like this. The way that the copyright lobby is going at this is totally wrong and we can’t let them win. And we won’t let them win." – Brokep "It's a great clusterfuck for the American mind's idea of Mexico. This teaches the rest of the world that Mexico is not just a bunch of cactuses and sombreros." – Gustavo Arellano "I don't fall over and convulse, but it hurts. I was on the phone when it happened, and I couldn't move and couldn't speak." – RyAnne Fultz "I think we're right on the verge of 'ultra budget' filmmaking." – Kirk Mastin "I have lived in the shadow of this my whole life. I am so happy now, I just can’t explain it." – Laura Siegel Larson March 29th, 2008  Creator’s Family Reclaims the Rights to Superman Michael Cieply Time Warner is no longer the sole proprietor of Superman. A federal judge here on Wednesday ruled that the heirs of Jerome Siegel — who 70 years ago sold the rights to the action hero he created with Joseph Shuster to Detective Comics for $130 — were entitled to claim a share of the United States copyright to the character. The ruling left intact Time Warner’s international rights to the character, which it has long owned through its DC Comics unit. And it reserved for trial questions over how much the company may owe the Siegel heirs for use of the character since 1999, when their ownership is deemed to have been restored. Also to be resolved is whether the heirs are entitled to payments directly from Time Warner’s film unit, Warner Brothers, which took in $200 million at the domestic box office with “Superman Returns” in 2006, or only from the DC unit’s Superman profits. Still, the ruling threatened to complicate Warner’s plans to make more films featuring Superman, including another sequel and a planned movie based on the DC Comics’ “Justice League of America,” in which he joins Batman, Wonder Woman and other superheroes to battle evildoers. If the ruling survives a Time Warner legal challenge, it may also open the door to a similar reversion of rights to the estate of Mr. Shuster in 2013. That would give heirs of the two creators control over use of their lucrative character until at least 2033 — and perhaps longer, if Congress once again extends copyright terms — according to Marc Toberoff, a lawyer who represents the Siegels and the Shuster estate. “It would be very powerful,” said Mr. Toberoff, speaking by telephone on Friday. “After 2013, Time Warner couldn’t exploit any new Superman-derived works without a license from the Siegels and Shusters.” Time Warner lawyers declined to discuss the decision, a spokesman said. A similar ruling in 2006 allowed the Siegels to recapture their rights in the Superboy character, without determining whether Superboy was, in fact, the basis for Warner Brothers’s “Smallville” television series. The decision was later challenged in a case that has yet to be resolved, said Mr. Toberoff, who represented the family in that action. This week’s decision by Stephen G. Larson, a judge in the Federal District Court for the Central District of California, provided long-sought vindication to the wife and daughter of Mr. Siegel, who had bemoaned until his death in 1996 having parted so cheaply with rights to the lucrative hero. “We were just stubborn,” Joanne Siegel, Mr. Siegel’s widow, said in a joint interview with her daughter, Laura Siegel Larson. “It was a dream of Jerry’s, and we just took up the task.” The ruling specifically upheld the Seigels’ copyright in the Superman material published in Detective Comics’ Action Comics Vol. 1. The extent to which later iterations of the character are derived from that original was not determined by the judge. In an unusually detailed narrative, the judge’s 72-page order described how Mr. Siegel and Mr. Shuster, as teenagers at Glenville High School in Cleveland, became friends and collaborators on their school newspaper in 1932. They worked together on a short story, “The Reign of the Superman,” in which their famous character first appeared not as hero, but villain. By 1937, the pair were offering publishers comic strips in which the classic Superman elements — cape, logo and Clark Kent alter-ego — were already set. When Detective Comics bought 13 pages of work for its new Action Comics series the next year, the company sent Mr. Siegel a check for $130, and received in return a release from both creators granting the company rights to Superman “to have and hold forever,” the order noted. In the late 1940s, a referee in a New York court upheld Detective Comics’ copyright, prompting Mr. Siegel and Mr. Shuster to drop their claim in exchange for $94,000. More than 30 years later, DC Comics (the successor to Detective Comics) gave the creators each a $20,000-per-year annuity that was later increased to $30,000. In 1997, however, Mrs. Siegel and her daughter served copyright termination notices under provisions of a 1976 law that permits heirs, under certain circumstances, to recover rights to creations. Mr. Toberoff, their lawyer, has been something of a gadfly to Warner in the past. In the late 1990s, for example, he represented Gilbert Ralston, a television writer, in a legal battle over his rights in the CBS television series “The Wild Wild West,” which was the basis for a 1999 Warner Brothers film that starred Will Smith. The case, said Mr. Toberoff, was settled. Compensation to the Siegels would be limited to any work created after their 1999 termination date. Income from the 1978 “Superman” film, or the three sequels that followed in the 1980s, are not at issue. But a “Superman Returns” sequel being planned with the filmmaker Bryan Singer (who has also directed “The Usual Suspects” and “X-Men”) might require payments to the Siegels, should they prevail in a demand that the studio’s income, not just that of the comics unit, be subject to a court-ordered accounting. Mrs. Siegel and Ms. Larson said it was too soon to make future plans for the Superman character. But they were inclined to relish this moment. “I have lived in the shadow of this my whole life,” Ms. Larson said. “I am so happy now, I just can’t explain it.” http://www.nytimes.com/2008/03/29/bu.../29comics.html  The Google Of Peer To Peer? John Foley Tiversa, a five-year-old company based in Pittsburgh, specializes in knowing what kind of content is being shared over peer-to-peer networks. Until now, it's concentrated on helping businesses find and fix data leaks caused by file-sharing users. But Tiversa's got other plans for its technology, including working with advertisers to understand and respond to user activity on P2P networks. P2P networks have long suffered a bad rap, going back to the troubles of Napster seven or eight years ago. They can be a hornet's nest of copyright violation, ill-intended searches, and leaked data. As InformationWeek reported earlier this week, P2P networks are rife with sensitive business documents and personal information, often the result of users inadvertently storing those documents in their music folders or otherwise misconfiguring the file-sharing application during installation. (See "Your Data And The P2P Peril" and "Our P2P Investigation Turns Up Business Data Galore." Tiversa helps businesses get the data leak problem under control, and it turns out that its technology can be used in other ways, too. The company has begun working with unnamed advertisers to see if the information it culls from P2P activity -- primarily search terms and search matches -- might be used for market intelligence or even targeted ad campaigns. How might that work? Say someone is looking for a copy of the 2007 movie Beowulf. Tiversa's real-time monitoring system might respond to the search with an offer of a licensed copy of the movie or a related game. These are somewhat murky waters given that P2P networks have served as a distribution channel for unlicensed music and movies, but it could be another step toward commercializing and legitimizing file sharing. Just last week, the Distributed Computing Industry Association, a trade group for the P2P industry, held a conference devoted to P2P advertising and new business models. Tivera's technology could ultimately turn up in browsers. Tiversa COO Chris Gormley says incorporating P2P search into a browser tool bar would be a "no brainer." The company has been in discussions with a major Web portal, though it won't disclose names. "They could use our technology to create a whole different search engine," he says. "They could be become the Google of peer to peer." Don't scoff. Tiversa says 1.5 billion searches a day take place on P2P networks, several times the volume handled by Google. If accurate, it's only a matter of time before mainstream advertisers get serious about the file-sharing crowd. http://www.informationweek.com/blog/...ogle_of_p.html  BitTorrent Sites Show Explosive Growth Ernesto BitTorrent’s popularity is growing every day. Despite efforts from anti-piracy outfits such as the MPAA and IFPI, torrent sites continue to grow traffic wise, and there is no sign that this trend will be brought to a halt anytime soon. We decided to compile a list of the 25 most popular BitTorrent sites, and see how their (relative) popularity has grown over the past three months. Out of the 25 sites in the list, 21 improved their ranking in Alexa’s list of most popular sites on the Internet. There are a few changes in the top 10 compared to the list of 2007’s top torrent sites. Mininova is still leading the bunch, but The Pirate Bay is now in second place, in front of isoHunt. Torrentportal and TorrentReactor traded places as well, the sites are now 7th and 9th respectively. YouTorrent is the only newcomer, and it’s really impressive that the site made it into the top 25 only 2 months after its launch. Top 25 torrent sites March 2007 Rank # Torrent Site Alexa Rank (Dec 07) Alexa Rank (Mar 08) Change (%) 1. mininova.org 63 53 + 19 % 2. ThePirateBay.org 182 130 + 40 % 3. isohunt.com 170 147 + 16 % 4. Torrentz.com 231 192 + 20 % 5. BtJunkie.org 689 469 + 47 % 6. torrentspy.com 376 585 - 36 % 7. TorrentReactor.net 909 616 + 48 % 8. GamesTorrents.com 942 641 + 47 % 9. TorrentPortal.com 699 697 no change 10. btmon.com 924 743 + 24 % 11. sumotorrent.com 1,894 1,101 + 72 % 12. myBittorrent.com 1,861 1,454 + 28 % 13. animesuki.com 1,738 1,473 + 18 % 14. Fulldls.com 1,448 1,646 - 12 % 15. bitdig.com 5,805 1,945 + 300 % 16. torrentz.ws 7,990 1,991 + 400 % 17. newtorrents.info 3,348 2,272 + 47 % 18. Torrent-Finder.com 3,404 2,635 + 29 % 19. TorrentBox.com 2,812 2,686 + 5 % 20. Fenopy.com 3,102 2,901 + 7 % 21. torrentvalley.com 5,276 3,014 + 75 % 22. youtorrent.com … 3,107 New! 23. TorrentReactor.to 3,016 3,313 - 9 % 24. www.zoozle.org 4,669 3,369 + 39 % 25. www.seedpeer.com 3,992 3,449 + 16 % Note: Alexa’s data gathering is not perfect. The exact figures may be not be completely accurate, but it is a great tool (especially the traffic rank) to compare sites within the same niche and to get a global impression of traffic shifts over time. http://torrentfreak.com/bittorrent-s...growth-080322/  When Capacity Is Never Enough The Cautionary Tale of Video Downloads Tom Steinert-Threlkeld A bit is a bit is a bit. An electronic packet of data is a packet is a packet. Unless you look inside to see what it contains. Yet Internet-access providers such as Comcast and Time Warner Cable, the nation’s two largest cable operators, are loath to open the envelopes. Even if those packets are generated by a relatively small number of users carrying illegally obtained goods — and hogging bandwidth in the process. “How do you distinguish, without invading the privacy of the people communicating?” asked Federal Communications Commissioner Jonathan Adelstein at last week’s Internet Video Policy Symposium in Washington, D.C. “It’s very hard to distinguish, just looking at packets, whether they’re legal or illegal.” What Adelstein was talking about was Internet video — and more specifically, the distribution of movies, TV shows and other content by a technique called peer-to-peer sharing. Broadband Internet-access subscribers use their own computers — and those of anyone who wants to share shows — to manage the distribution of whatever they want to watch. Unchecked, peer-to-peer users have become the bane of network operators, who see no way to limit the ability of these Net-video hogs to usurp the bandwidth they have spent billions to install. Sharing a single high-definition movie can employ 25 Megabits per second of capacity, until completed. A standard-definition show can take up 6 Mpbs. This isn’t a case for your garden-variety 256,000-bit “broadband” connection anymore. The solution? If you’re a policymaker, such as Adelstein, the answer looks like … more bandwidth. But the answer is not that simple, according to cable-system operators. With peer-to-peer file-sharing, there’s never enough capacity. And broadband network owners would spend huge sums — more billions — to serve the voracious appetites of as little as 5% of their subscribership. The Video Hog “Video can be a real bandwidth hog sometimes,” Adelstein said Tuesday night. “Of course, one great solution for that problem is adding more capacity.” If that were accomplished, there would be no debate about the P2P file-sharing problem. You don’t see this kind of problem in Japan, where Internet users are already connected at 100 Megabits per second, Adelstein contends. But wait. It’s not that cut and dried, according to Comcast. In the face of this form of hogging, there’s never enough capacity. Invest in more bandwidth and, by definition, it will almost immediately be overtaken by file-sharing. “Because these P2P protocols are designed to devour any and all available bandwidth on the network, it is not possible to build one’s way out of the need for reasonable network management,” Comcast public policy counsel Joseph Waz and a phalanx of other Comcast lawyers argued to the Federal Communications Commission in a Feb. 12 filing of comments on broadband industry practices. How can that be? It’s relatively straightforward, according to Sena Fitzmaurice, senior director of corporate communications and government affairs for Comcast in the nation’s capital. The primary program used for efficient distribution of files, BitTorrent, splits tasks between available personal computers. A few central servers “seed” participating PCs with content and those machines, in turn, seed others. In the end, each computer becomes part of a one-for-all, all-for-one union, using a cable network’s last-mile bandwidth to distribute heavy duty content. To move video or other large files, the seeded computers ask for as much capacity as they can get, to deliver the final result as quickly as possible. And since much of that work takes place in neighborhoods and not network backbones, available capacity is maxed out more rapidly. When it comes to downloading video for later viewing, as opposed to streaming it for on-demand playback (“I Want My Web TV,” March 17, 2008, page 14), network operators and economic analysts define BitTorrent — and its adherents — as bandwidth hogs. “It’s a question that answers itself, doesn’t it?” former FCC chief economist Gerry Faulhaber, now a professor at the University of Pennsylvania’s Wharton School of Business, said at the symposium. “It’s not called BitTrickle, after all.” By one count in the middle of last year, video and audio streaming overtook peer-to-peer applications as the top consumer of Internet bandwidth, accounting for 46% of all traffic. That came after four years of P2P overwhelmingly consuming the most bandwidth, according to Ellacoya Networks. But even though that report indicated P2P was “losing its status as the biggest bandwidth hog on the Net, that’s not what we’re seeing,” said Yankee Group analyst David Vorhaus. Cable operators continue to report that 60% to 75% of their Internet traffic is being generated by P2P file-sharing, Vorhaus said. And, as with streaming video, it all boils down to a very small number of outsized users. Vorhaus estimates that 5% to 10% of Internet users are generating 80% to 90% of this P2P traffic. In 2006, research conducted by CableLabs staffer Terry Shaw and Clemson University computer science professor Jim Martin found, in fact, that it only takes about 10 BitTorrent users bartering files on a 500-home network node to double the delays experienced by all other users. That’s especially true if the BitTorrent users are taking in video and everybody else is using “normal priority” services, like e-mail or Web surfing, which are characterized as “best-effort” traffic. Online, BitTorrent has tried to refashion itself as a legitimate purveyor of video content. Its BitTorrent Entertainment Network, akin to Apple’s iTunes Store, allows legitimate downloads of more than 10,000 movies, TV shows, games and music videos. BitTorrent is marketing its technology to businesses that want to distribute video. Its first client was Brightcove, an online distributor that serves publishers such as Reuters, National Geographic and TMZ. But Vorhaus, Faulhaber and many other experts believe the vast majority of BitTorrent’s Web traffic consists of content that is being distributed in violation of copyright law. Indeed, 90% of P2P downloads are still of illegally copied content, according to David Hahn, vice president of product management at SafeNet, which tracks the networks. That means if the capacity of a cable or telephone broadband network were doubled to accommodate more traffic — and such file-sharing continued — it would, in effect, only support further theft. Pamela’s Parts Not managing this traffic flow could be life-threatening, Faulhaber said. Under a network-neutrality regime, an episode of Baywatch would have the same priority as the transfer of your personal medical history to a hospital the minute you collapse at a restaurant. “Pamela Anderson’s parts are not as important as your heart,” said Faulhaber. But increasing capacity to support P2P traffic may be inevitable — because legitimate uses of the technology could skyrocket. Using local computers, not just central servers, to distribute video content can be extremely efficient. And if a large, for-profit enterprise such as Amazon or Netflix or Blockbuster or The Walt Disney Co., or all of the above, become heavy users of the technology for video downloads, bandwidth would be under heavy pressure. “That’s the real concern,” said Vorhaus. To that point, Comcast has tried to curb the current herd of download hogs by focusing on the uploads that fuel the sharing of files over swarms of personal computers. To try and limit its network load, Comcast, according to its FCC comments, only manages the uploading of files — at a time when a customer or customers are not downloading files at the same time. Such “unidirectional sessions” indicate an automated file-sharing process is underway and can be held up until “usage drops below an established threshold” of simultaneous sessions. This is akin to smoothing out the flow of cars onto a highway through the use of temporary stop lights at on-ramps, Comcast contends. In effect, Comcast has tried to curb the effects of the use of a P2P application without condemning the application itself. But why? “Why not target the thing that is causing the problem?” Georgetown Center for Business and Public Policy senior fellow Scott Wallsten said of BitTorrent. “What we have is a problem in waiting.” Normal network-management technique or not, the Comcast practice of delaying BitTorrent traffic at peak times has prompted scrutiny from the Federal Communications Commission. After the Associated Press called the practice data “blocking,” a coalition of consumer groups and law professors filed a complaint with the FCC. They claimed Comcast had violated the agency’s two-year-old net neutrality policy statement, and should be ordered to stop, as well as fined up to $195,000 per affected customer. Comcast has about 13 million high-speed data subscribers. “Comcast does not block any Web site, application, or Web protocol, including peer-to-peer services, period,” its executive vice president, David Cohen, responded. “What we are doing is a limited form of network management objectively based upon an excessive bandwidth-consumptive protocol during limited periods of network congestion.” The commission subsequently opened a formal investigation of the practice; and held a hearing a few weeks ago at the Harvard Law School into the fairness of the practice. The commission’s chairman, Kevin Martin, says that two troubling aspects of the case are that, in his view, Comcast at first denied the allegations. Also troubling, he said, were allegations that Comcast altered certain user information in packets to effect a delay in peer-to-peer transmissions. He said a ruling will come by July 1. For its part, Comcast told the commission in its February comments that many of the complaints about the effects of the “blocking” had nothing to do with blocks or delays. Among the complaints: that users couldn’t check e-mail when sending files from home to work and that chat services weren’t working properly, allegedly because of bad network management. “These commenters’ calls for Commission intervention are misplaced,” Waz and the Comcast attorneys said. “Surely, the Commission has neither the resources nor the ability to turn itself into the help desk for 60 million broadband households.” The Capacity Panacea The solution again, at first blush, looks like this: Add capacity. Then you could handle all bits equally, without delay. That “would also deal with the network-neutrality issues. The more capacity, the less of an issue it becomes,” Adelstein said. But capacity can be a chimera, said Faulhaber. Just look at Japan, a country that Adelstein cites as an exemplar of serving net video hogs and average users at the same time. Japanese consumers are already used to Internet-access speeds of 100 Mbps — the rate touted by Comcast CEO Brian Roberts at the 2007 Cable Show as the imminent signal speed of “wideband Internet access” from cable operators. Faulhaber notes that even in Japan, 100 Mbps is not fast enough to avoid the suddenly cardinal sin of managing its network that Comcast has committed. Even in Japan, delaying the arrival of some content — so-called traffic-shaping — is common. This is a normal practice that allows more efficient traffic processing for all users, not just hogs. “To say, 'We have a neutral network,’ you never do,” said Faulhaber. You have to be proactive, to give more users more services on a consistent basis, he said. Telcos like Verizon also face bandwidth scarcity problems from peer-to-peer applications. The problem, however, is more acute for cable, since the upstream bandwidth of a DOCSIS cable modem is just a fraction of the downstream speeds. Meanwhile, Verizon’s public-relations handling of broadband network management-related issues stands in contrast to Comcast’s. Earlier this month, the telco announced it has tested a system called P4P, developed by researchers at Yale and the University of Washington, designed to keep peer-to-peer traffic off the Internet’s backbone networks. This technology more intelligently directs P2P traffic to local peers, instead of letting software like BitTorrent try to suck data willy-nilly from all over the world. Verizon claimed that using P4P, 58% of peer-to-peer traffic came from nearby P2P users on its network, compared with 6% before. Verizon attempted to position the move as an embrace of P2P, pointing out there are legitimate uses of peer-to-peer. In a press release, the telco noted that NBC Universal is using P2P as part of its NBC Direct episode-download service. NBCU has been a critic of P2P networks used to swap copyrighted material, urging the FCC last year to require broadband providers to prevent video piracy. “No longer the dark-alley distribution system for unauthorized file sharing, advanced P2P delivery networks link content-seekers with licensed files they want,” Verizon’s announcement said. The cable industry also says it’s working on such engineering solutions to handle P2P traffic with technology suppliers. And that’s how the issues ought be resolved, National Cable & Telecommunications Association CEO Kyle McSlarrow said during a conference call with reporters last Thursday. “Let the marketplace and the Internet community examine the results of what is, and is not, working,” McSlarrow said. The management of traffic — and the curbing of bandwidth hogs — is going to get more critical as more types of video unique to the Internet — like feeds from security cameras, or video-rich faux-3D imagery found in such games as the Second Life/Google Earth Web environment Second Earth — emerge. It’s presumed that Internet video will amount to either narcissistic homemade, personally-focused video or high-end, high-quality professional fare. The real result, though, is likely to be a host of new types of video applications that could only exist with such a low-cost mechanism of worldwide distribution. The trick, said Faulhaber, is for video content producers to collaborate with distributors to provide a protected channel of high-quality video to legitimate viewers. Otherwise, charging for content will be impossible. Timing is the problem, said Georgetown’s Wallsten. In essence: Knowing what to do about Net video hogs, and when to do it. “The Internet changes really fast,” he said. “Policies can’t.” Todd Spangler contributed to this report. http://www.multichannel.com/article/CA6544099.html  Comcast to Stop Hampering File-Sharing Deborah Yao Comcast Corp., an Internet service provider under investigation for hampering online file-sharing by its subscribers, announced Thursday an about-face in its stance and said it will treat all types of Internet traffic equally. Comcast said it will collaborate with BitTorrent Inc., the company founded by the creator of the peer-to-peer file-sharing protocol, to come up with better ways to transport large files over the Internet instead of delaying file transfers. Since user reports of interference with file-sharing traffic were confirmed by an Associated Press investigation in October, Comcast has been vigorously defending its practices, most recently at a hearing of the Federal Communications Commission in February. Consumer and ''Net Neutrality'' advocates have been equally vigorous in their attacks on the company, saying that by secretly blocking some connections between file-sharing computers, Comcast made itself a judge and gatekeeper for the Internet. They also accused Comcast of stifling delivery of Internet video, an emerging competitor to the core business of the nation's largest cable operator. It was not immediately clear what effect, if any, the move will have on the FCC's ongoing probe, but Net Neutrality groups remained skeptical. ''This deal is the direct result of public pressure, and the threat of FCC action, against Comcast,'' said Marvin Ammori, general counsel of Free Press, a media reform group. ''But with Comcast's history of broken promises and record of deception, we can't just take their word that the Internet is now in safe hands.'' Shares in Comcast rose 29 cents, or 1.5 percent, to $20 in midday trading Thursday. Comcast has said that its practices were necessary to keep file-sharing traffic from overwhelming local cable lines, where neighbors share capacity with one another. On Thursday, Comcast said that by year's end, it will no longer target files based on the type of protocol used, such as BitTorrent's, and will instead explore alternatives. ''The outcome will be a traffic management technique that is more appropriate for today's emerging Internet trends,'' Tony Werner, Comcast's chief technology officer, said in a statement. One option is to delay file transfers for the heaviest downloaders, regardless of protocol, the Philadelphia-based company said. Comcast said it also was monitoring Time Warner Cable Inc.'s experiment in placing explicit caps on the monthly downloads for new customers in Beaumont, Texas. Subscribers who go over their allotment will pay extra, much like a cell-phone subscriber who uses too many minutes in a month. But Comcast may be wary about charging certain users more because of competitive pressure, especially after rival Verizon Communications Inc. said recently that such traffic is legitimate and that its FiOS network can handle the flow, said Harold Feld of Media Access Project, a nonprofit advocacy group in Washington, D.C. Comcast has been hampering the BitTorrent file-sharing protocol, which together with the eDonkey protocol, accounts for about a third of all Internet traffic, according to figures from Arbor Networks. The vast majority of that is illegal sharing of copyright-protected files, but file-sharing is also emerging as a low-cost way of distributing legal content -- in particular, video. On Thursday, Werner all but embraced peer-to-peer file transfers, saying the techniques have ''matured as an enabler for legal content distribution.'' The company initially veiled its traffic-management system in secrecy, saying openness would allow users to circumvent it. Werner said the company now would ''publish'' the new technique and take into account feedback from the Internet community. Comcast and BitTorrent said they want to work out network management issues privately, without the need for government intervention. FCC Commissioner Robert McDowell agreed as much, saying in a statement that ''the private sector is the best forum to resolve such disputes.'' For its part, BitTorrent acknowledged that service providers have to manage their networks somehow, especially during peak times. ''While we think there were other management techniques that could have been deployed, we understand why Comcast and other ISPs adopted the approach that they did initially,'' Eric Klinker, BitTorrent's chief technology officer, said in a statement. Comcast also said that the issue is larger than BitTorrent. It said it was in talks with other parties to find solution, although the cable company might not have much of a choice. Verizon recently announced that by sharing information with Pando Networks, another file-sharing company, Verizon was able to speed up file-sharing downloads for its subscribers while reducing the strain on its own network. AT&T Inc. has been looking at similar collaboration. However, phone companies are in a better position than cable companies to deal with file-sharing traffic, since neighbors don't share capacity on phone lines. ------ Associated Press Business Writer Barbara Ortutay and Technology Writer Peter Svensson in New York contributed to this story. http://www.physorg.com/news125835899.html  BitTorrent Inc. + Comcast = Love, Peace, Harmony…Not! enigmax When Robb Topolski made the initial discovery that Comcast was interfering with BitTorrent traffic, he couldn’t have imagined that it would lead to an FCC hearing or, more importantly, to apparent reconciliation this week between Comcast and the rest of the world. Thing is, Robb doesn’t believe a word of it. Ever since the news broke that Comcast had been using ‘hacker-like’ techniques to hamper BitTorrent traffic, Comcast’s name has been dragged through the mud, with claim after claim of dirty tricks, lies, half-truths and strategic omission. It seems that nothing could go right for the company. Until this week, that is. Apparently, everything in the Comcast garden is rosy these days, with previous arch-rival BitTorrent now working things out together over afternoon tea. However, not everyone is celebrating. In 2007, Robb Topolski discovered and documented the Comcast interference, informed TorrentFreak and we published an article which ignited the whole debate. It’s safe to say, he’s been following this one closely. Here are his thoughts on the Comcast / BitTorrent reconciliation: —– I’m probably a key figure as to why we’re all talking about Network Neutrality again. I was having a problem uploading on Gnutella in early 2007. I tracked it down to Comcast using Sandvine-injected RST packets. Blog stories led to press stories which led to independent confirmation. And here we are today. Peace and harmony? Probably not. Today Comcast and BitTorrent seems to have solved world hunger — and I’d love nothing more than to be optimistic about it. But I cannot be. As they say on Slashdot — show video, or it didn’t happen. This deal is treachery, relies on how much we can trust the word of Comcast, and leaves the public interests out in the cold. I think it’s strange that anyone believes a word that Comcast says. This is the Comcast that: 1. Told the FCC in 2005 that they would not degrade traffic in order to convince the FCC that network neutrality regulations were not needed. 2. Started degrading P2P traffic the very next year, and failed to tell anyone what they were doing. 3. Used a system that utilized forgery, and successfully placed blame on the other peer instead of Comcast. 4. Denied it when caught. 5. Then changed their story when the denials were not believed, but still never came out and said what they were doing. 6. Then they justified their actions by throwing their other Cable-Internet brothers and sisters under the bus with their “they do it too!” defense 7. Then stealthily changed the AUP days before an FCC filing where they referred to the new provisions. 8. When the changed AUP started getting press attention, they stated that a prominent story on Comcast.net alerted millions of visitors of the change and accused Marvin Ammori of crying wolf. (Google cache proved that nothing alerted users to the changed AUP until the day after the press started asking questions.) 9. Then they packed the Harvard FCC hearing. This company has not demonstrated that you can trust its promises, nor can you believe its assertions. Comcast just used BitTorrent Inc. as a tool to try and defang the FCC. BitTorrent Inc. is a content provider. Vuze, who actually DID make a complaint and petition to the FCC, is a competitor. Neither BitTorrent, Vuze, nor Comcast represents the interests of 12 million Comcast users nor the The Internet Society nor the public. And this middle-of-the-night deal was made without their input. Nothing has changed. The RST interference continues. It was a wrongful act. BitTorrent Inc. has no right making a deal with Comcast allowing it to continue to commit wrongful acts until it finally decides it is ready to stop. The correct relief is to stop the interference immediately and to FULLY DISCLOSE what it did and to accept responsibility for those actions. (Even today, Comcast’s Policy VP refused to answer questions about the interference.) Their word is worthless. Until the interference stops, I have no reason to believe it will. Until either meaningful competition returns to broadband, or until sufficient government regulation enforces Network Neutrality, we have no reason to think that this agreement will last through the night. Robb Topolski —– TorrentFreak confronted Ashwin Navin of BitTorrent Inc. with Robb’s comments, and he told us: “We decided to collaborate with Comcast because they agreed to stop using RSTs, increase upload capacity, and evaluate network hardware that accelerates media delivery and file transfers. We’re at the beginning of the formal collaboration, but Robb’s work was instrumental to identify the offending practice. We need him and the community to keep an eye on ISPs across the world.” “Our work with Comcast will benefit all P2P development because Comcast has agreed to manage traffic at Layer 3 (the network layer) rather than Layers 4-7 (the protocol/application layers). This is a core component of the neutrality debate,” he added. As always, time will tell… http://torrentfreak.com/bittorrent-c...ve-not-080329/  New Project Sniffs Out Bandwidth Shaping ISPs Thomas Mennecke The file-sharing world has been consumed by a continuous barrage of coverage on the Comcast vs BitTorrent battle. While Comcast may be able to escape their policy of delaying traffic relatively unscathed, their image has taken a beating in the public relations department. In response to the growing distrust of ISPs, members of the p2pforum.it community developed a tool, dubbed Project Gemini, which allows users to test whether their ISPs block traffic. According to a forum post, a spokesperson for the project states that, "our aim is to produce evidence with the technique below: we've developed two "Live" operating systems designed to connect with one another over the Internet, to start a BitTorrent transfer, and to record the transmission - after which it will generate a report containing the analysis of the traffic." Testing for a shaped BitTorrent transmission isn't terribly difficult, but may be foreboding for the less computer savvy. The project requires the end user to download and mount an ISO to CD, change the boot sequence to initialize from an optical drive, and run the program which can only function with Ubuntu. The end user isn't required to have Ubuntu previously installed, rather the CD is a self contained with all the required data. So if you can burn and mount an ISO - a familiar task in the file-sharing world - and are suspicious of your ISP, this program may be worth a try. http://www.slyck.com/story1680_New_P...h_Shaping_ISPs  ISPs Limit Access to CBC Download, Users Say Thousands of viewers have embraced CBC-TV's experiment with BitTorrent, but many Canadians have found their attempts to access a CBC show online restricted by their internet service providers. On Sunday, CBC offered a final episode of reality TV program Canada's Next Great Prime Minister for download via BitTorrent, a file-sharing service. The release was an experiment for the public broadcaster in new ways of offering its programming. Downloads were in the thousands, said Tessa Sproule, executive in charge of digital programming for factual entertainment at CBC Television. It is impossible to tell how many people actually saw the program because the files are passed from one computer user to another through BitTorrent, she added. "It was very promising," Sproule told CBC News. "People around the world are seeing the file, probably because it's the first time.… We're very happy about it." ISP bottlenecks However, downloaders who blogged about the experience on the Canada's Next Great Prime Minister site complained about very long periods required to download the show. One user received a notice that it could take 2½ hours to download, while another was quoted 11 hours. The bottleneck is occurring because ISPs such as Rogers and Bell limit the amount of bandwidth allocated for file-swapping on BitTorrent. The controversial practice, called traffic shaping, is meant to stop illegal downloading through BitTorrent. But it also slows the times on legal downloads such as Canada's Next Great Prime Minister. Michael Geist, an Ottawa-based advocate of open sharing over the internet, called the CBC experiment an "enlightened approach to content distribution." But he warned that ISP practices could get in the way. "It would be ironic if ISP network management practices ensured that viewers outside the country enjoyed better access to the program than the Canadian taxpayers who helped fund its creation," he wrote in his blog. Some people posting on the show blog said they'd left their computers running to help speed up downloading through BitTorrent for others. Most users posting on the blog welcomed the CBC's experiment with BitTorrent. "With the state of affairs of Canada's fading telecommunications industry, it's fantastic to see that CBC is pressing new boundaries. Kudos on finding new ways to provide Canadian content," said a user called Bob. Others asked for more content to be delivered this way, including favourite shows such as Jpod, Rick Mercer Report, Fifth Estate and the news. "I'd like to see more content delivered in this way, without restriction and I can tell you that the majority do not mind ad placement within the content," said a user called Steven G. There were complaints about the quality of the download, with some saying the images were distorted. Sproule said CBC is working on refining the quality of broadcast via BitTorrent. http://www.cbc.ca/arts/tv/story/2008...rrent-cbc.html  Norwegian ISPs Refuse MPAA’s Request to Disconnect Pirates Ernesto After being blown off by the Norwegian police, MPAA lawyer Espen Tøndel is now demanding that ISPs disconnect Norwegian file-sharers from the Internet. According to IKT Norway, an interest group for ISPs, the lawyer has sent a letter to Norwegian ISPs on behalf of The Norwegian branch of the MPAA. In the letter, Tøndel asks the ISPs to notify customers who share copyrighted content, and threaten to disconnect them from the internet. Tøndel also attached a document that supposedly links the IP-addresses of seeders to copyrighted works. It seems that Norway is not alone in this, Jim Williams, the MPAA’s senior vice president opted for a similar disconnection policy in the US yesterday. IKT Norway is not too happy about the letter though. “In a constitutional state, the police and the prosecuting authority have the job of investigating and indicting, not lawyers and communication engineers”, says Hallstein Bjercke from IKT Norway, in a press release. “Most of the big ISPs in Norway are members of IKT Norway and we will support the various ISPs as best we can against what we see as a preposterous demand from Simonsen”, Bjercke adds. He asks the ISPs to contact IKT Norway instead of answering the law firm’s letter. “In our opinion, Tøndel asks the ISPs to assist them in their private investigation on filesharers. Tøndel’s law firm asks the ISPs to use personal information about their customers in a way that would be a breach on the Norwegian laws on personal information and personal privacy, in addition to breaching the contract between individual customers and their respective ISP.” “What Simonsen is actually asking for is confessions from the alleged filesharers, which can be used against them if Simonsen decides to sue”, Bjercke said. IKT Norway makes it clear that the Norwegian ISPs will not take the role of investigator and judge against their own customers. “To give that kind of responsibility to the ISPs is like asking the mailman to control the contents of every letter and package he delivers,” Bjercke says. IKT Norway is now checking into the legality of the law firms private investigation and the legality of connecting personal information to the customers of Norwegian ISPs. http://torrentfreak.com/isps-refuse-...equest-080328/  Swedish ISP Refuses To Block The Pirate Bay enigmax After forcing a single ISP in Denmark to block The Pirate Bay, it now appears that the IFPI has a plan to sue all of the major Swedish ISPs to force them to do the same. Telia Sonera, a large Swedish ISP is refusing to be bullied, stating that such blocking and filtering actions are illegal under EU law. Now that the IFPI has realized that it can’t sue every file-sharer in the world, it tries to force ISPs to block their customers from accessing filesharing sites such as The Pirate Bay. The IFPI recently forced an Israeli ISP to block access to HTTPShare.com - which boosted its visitors significantly - but it’s the block it achieved against The Pirate Bay in Denmark that is currently being used as leverage against other ISPs, this time in Sweden. When IFPI pressure forced Danish ISP ‘Tele2′ to block access to The Pirate Bay, the trade organization chose to view this as some sort of landmark decision which could be used to make other ISPs take the same action, regardless of the likelihood that the block ordered by Denmark broke EU law. According to reports, the IFPI is using this ’successful’ block as a legal hammer to start hitting Swedish ISPs over the head with, as it formulates its plan to sue all of Sweden’s major ISPs into blocking The Pirate Bay. One such ISP is Telia Sonera, the dominant internet provider in Sweden with a total of 106 million subscribers across Europe. According to a report, they have received a letter from the IFPI which states that legal measures will be taken against them unless they block The Pirate Bay initially, and also some other (as yet unnamed) sites connected to it. However, Telia is highly experienced in its field and has a very clear understanding of its obligations under the law, law which does not require them to block sites or filter content. Patrik Hiselius of Telia Sonera explains: “The rules say that we as Internet carriers are not allowed to listen in on what our customers are sending to each other or are talking with each other about. That’s something police and prosecutors are allowed to do after a decision has been made about it in court.” Unfortunately for the IFPI, the law is very stringent when it comes to wiretapping communications. Eavesdropping is allowed, but only in cases of very severe crime. Anna Hörnlund, a lawyer with the The Swedish Post and Telecom Agency believes that it’s impossible to identify illegal file-sharing without breaking the law on wiretapping: “To get access to this information, there needs to be a crime that is punishable by imprisonment and where a prosecutor believes charges can be made that leads to prison. In those cases, the ISP can hand over the information to the police. I don’t know how they think they will get through this by suing the ISP.” Patrik Hiselius of Telia Sonera agrees that the record companies have a problem to solve he says they are approaching the issue in the wrong manner: “The best way to meet the demand for music and film on the Internet would be to make good, simple legal services available with good pricing. The legal sites still have lots of shortcomings when it comes to availability.” The IFPI has recently sued Irish ISP Eircom, claiming that it’s responsible for the actions of its users. TJ McIntyre, chairman of Digital Rights Ireland (DRI) said: “ISPs are intermediaries. They are not, in law, responsible for what Internet users do, any more than [the post office] is responsible for what individuals send in the mail. In fact, European law specifically states that they may not be put under a general obligation to monitor the information they transmit.” Clearly the IFPI believes that European law doesn’t count when applied to their interests. If their lawyers weren’t getting so financially fat from these frivolous lawsuits, maybe they would take the time to explain it to them. http://torrentfreak.com/swedish-isp-...te-bay-080327/  Winny Copyright Infringers 'Should be Identified' The Yomiuri Shimbun An advisory panel to the National Police Agency that is looking into ways to prevent cybercrime released Thursday a report on copyright violation issues concerning the person-to-person file sharing software Winny, proposing that Internet service providers should be required to disclose the identity of customers who have used the software to illegally exchange copyrighted movies and music. The panel, headed by Prof. Masahide Maeda of Tokyo Metropolitan University, also suggests in the report the establishment of a system to make it easier for copyright associations to demand compensation from violators. In response to the report, Internet industry groups plan to start discussions with copyright associations regarding guidelines on disclosure of violators' identities. The service providers are required to protect the confidentiality of communications in line with the Constitution. However, the law stipulating the responsibilities of the providers allows them to disclose a person's identity in cases where that person has clearly violated other people's rights. However, no specific rule concerning the disclosure of identities has been implemented, so the identities of those who infringed copyrights using Winny and other so-called P2P file-sharing software have rarely been disclosed. Many people use Winny to download copyrighted movies and music over the Internet free of charge. Losses resulting from these illegal transactions are estimated at 10 billion yen. Members of the Telecom Services Association, the Japanese Society for Rights of Authors, Composers and Publishers and other related organizations have been discussing how to tackle the problem. Ahead of the release of the panel's latest report, the providers and copyright groups agreed to withdraw Internet services from copyright violators. http://www.yomiuri.co.jp/dy/national...28TDY02308.htm  TorrentSpy Shuts Down Ernesto A little over a year ago, TorrentSpy.com was still the most visited BitTorrent site, but times have changed. After an expensive two year battle with the MPAA, TorrentSpy decided to throw in the towel and the site has now shut down permanently. TorrentSpy is no more, Justin Bunnell, the founder of the site writes: “We have decided on our own, not due to any court order or agreement, to bring the TorrentSpy.com search engine to an end and thus we permanently closed down worldwide on March 24, 2008.” The main reason for the shutdown is the ongoing legal battle with the MPAA, which started February 2006. “We now feel compelled to provide the ultimate method of privacy protection for our users - permanent shutdown,” Justin writes. By the end of 2006 TorrentSpy was more popular than any other BitTorrent site, but this changed quickly in August 2007, when a federal judge ordered TorrentSpy to log all user data. The judge ruled that TorrentSpy had to monitor its users in order to create detailed logs of their activities, and hand these over to the MPAA. In a response to this decision - and to ensure the privacy of their users - TorrentSpy decided that it was best to block access to all users from the US. This led to a huge decrease in traffic and revenue. This was not enough for the MPAA, who argued that TorrentSpy had ignored the court decision. The legal battle continued, and this eventually led to a preventative closure of the site by Justin, to protect the privacy of its users. Brokep from The Pirate Bay had this to say about the closure: “Today all big torrent sites are pressured somehow. TPB has its share of pressure, however we expected it and have a legal system that is more just in cases like this. The way that the copyright lobby is going at this is totally wrong and we can’t let them win. And we won’t let them win. Today we reached a loss of a site, but it was more a person having to give up for economical reasons than anything else. The copyright lobby has their big cards - money and influence. In the long run they will have to give up as well. And when they do, I’ll go to the US and buy Justin a well-deserved beer.” At this point it is not clear what will happen to the TorrentSpy.com domain. The domain was offered to other BitTorrent site owners, but has not yet been sold. http://torrentfreak.com/torrentspy-shuts-down-080327/  10 Tips and Tricks for Private BitTorrent Sites sharky The first thing to notice when you join a private BitTorrent site is the eye-popping quality of the torrents. Each one is carefully culled, hand-picked through a strict moderation process. However, before you start hammering away on that download link - here are a few things you need to know. On private torrent sites, everything revolves around ratios. A 1:1 ratio (or 1.0) means that you’ve downloaded exactly the same amount of data as you’ve uploaded. Thus a 0.80 ratio indicates that you’ve uploaded less than you’ve downloaded, which is hurtful to the health of the torrent. Inversely, a 3.0 ratio means you’ve uploaded 3 times more data than you’ve downloaded. Strive to achieve at least a 1.0 ratio - each site will have specific consequences for members who maintain a ratio of less than this. Attain a ratio over 1.0 and the rewards shall follow you into the P2P afterlife. If you’re brand-new to a private site, it will be difficult in the beginning to acquire a 1.0 ratio. Luckily, users are given a ‘grace’ period to achieve this. Since there are so many more seeds than leechers (a total flip-flop from public BT sites), it becomes harder to upload to others - due to the fact that there are fewer people to share with. So why go through all the trouble to keep an honest ratio? Because deep down, you’re an upstanding denizen of file-sharing society! Aside from that shameless pat-on-the-back, good ratios offer many perks, including an upgraded account on the tracker (i.e. VIP status), higher download speeds, free “invites” for your friends, and no waiting periods associated with accounts in arrears. Here are Ten Tips to get your ratio in top-shape as fast as possible: 1. Start out with Smaller Files Initially, opt for smaller (i.e. under 1 GB) files for downloading. This gives you a greater chance of someone coming along after you and downloading the same torrent (and you’ll be able to upload to them). Obviously a 700MB movie file will be more appealing to other site members than a 30GB ‘Blu-Ray’ rip. 2. Jump on the ‘Newly Released’ torrents This is a great tip for increasing your ratio in a hurry. Camp out in your favorite private BT site, and refresh the torrent listings frequently. Newly added entries will have many more leechers than seeds, so you’ll be able to share (upload) more data. To maximize this tip, select smaller files - the “TV Episode” category works great for this. 3. Select Files that have a High ‘L’ or upload number This is important. When selecting torrents, base your initial selections on a high number of leechers (the more, the better). This will ensure you have many avenues to upload to during (and after) the transfer. When starting out on a new private BT site, we would even go so far as to say that you should download torrents that you don’t want - just start grabbing torrents that have lots of leechers. Once your ratio get over the 1:1 (1.0) mark, delete them. TIP: If one of your seeding torrents remains popular, leave it running in µtorrent permanently. This will always help to boost your upload ratio. 4. Avoid ‘Zero-Leech’ torrents When you’re new to a private site, steer clear of the ‘zero-leech’ torrents - it is impossible to increase your share ratio when there are no other downloaders. When viewing a list of torrents, look for the “Leecher” column (or just “L”) and avoid anything that has a zero ( “0″ ) in it. After your account ratio has become relatively stable, now is the time to snag whatever you want. 5. Leave some tasks running in uTorrent After the completed download of a torrent, leave the task running (as a seed) in µtorrent to increase your upload statistics. Don’t delete (or move) the files of a running task! You can, however, extract (unRAR) the files, or copy the files from one place to the next. In the event of a movie/video file - you’ll be able to “burn” or “extract” the *.avi file (or even play it on the PC) without affecting the seeding torrent. TIP: Always keep a few things running as ’seeds’ in your BT client. If you notice that they aren’t uploading, replace them with newer ones. 6. Go for the ‘Freebie’ downloads Many private sites will offer “free” torrents that won’t count against your download statistics (thus, your ratio will remain unchanged). Grab these freebies - especially when searching for torrents on a new account. 7. Use ‘Credits’ to purchase… A popular feature among superior private BitTorrent sites is the addition of a ‘credits’ feature for account holders. Credits can be used to ‘purchase’ VIP status, increased sharing ratios and other perks. Not all sites are the same, but some credits can be acquired just from staying active in their IRC channel, or from just having the torrents available for download in your BT client. 8. Do NOT try to ‘cheat’ the Private Trackers There are a variety of ratio cheating tips available out there, but don’t be tempted. Trackers are fairly sophisticated and ever-evolving. If you get caught cheating, you won’t even be warned - it’s a permanent ban for you and bye-bye for good. 9. Set a proper Upload Limit Setting a proper upload limit in the BT client makes all the difference! You’ll want to supply a high enough limit to maximize uploading, but not have it eat into your download bandwidth. The general rule is to set it at 80 - 85% of your upload limit. To figure this out, visit www.speedtest.net and conduct the simple test. Results are shown in kilobits, so divide the result by 1/8 and then multiply that by 0.85. This will give you the proper number in KB/s (KiloBytes). In µtorrent, go to OPTIONS > Preferences… > Connection and enter your upload rate. Click “Apply” and then “OK” to save the changes. While your in that same ’settings’ page, make sure to use a port number from the good list (e.g. 49152 - 65535). 10. And if all else fails…donate Most sites allow for monetary contributions to keep up with the server costs. If you enjoy a particular site immensely but cannot seem to be able to approach a decent sharing ratio (due to turning off your computer at night, going to work, or sharing your computer with your kids, wife, husband or siblings), think about donating. In most cases even a not-so-generous gratuity will robustly affect your account status - plus you’ll feel good about helping out the BitTorrent community. Other Tips - Follow ‘The Rules’ Yeah, we know: you hate rules! That’s why you probably moved out of your parents’ basement. Rules are probably why some turned to P2P. Nevertheless, rules are an important aspect to private BT sites - they ensure healthy torrents and blazing-fast download speeds for all. Each site will have their “rules” posted - the link is usually not hard to find. Below are some general rules / tips that pertain to any private BitTorrent site: Use an ‘Accepted’ BitTorrent client Not all private trackers are the same - and each one has different rules in regards to which BitTorrent client is on the “allowable” list. Most sites recommend µtorrent, but only specific versions (or builds) of it. If you stick with v1.6.1 or the latest version v1.7.7 (recommended), you can’t go wrong with ANY private site (avoid any versions in between these numbers). And do not use BitComet on private trackers. Proper BitTorrent client configuration: Many trackers recommend that you disable DHT and Peer Exchange (PEX) in your BT client’s settings. To do this in µtorrent, go to OPTIONS > Preferences… > and select the BitTorrent tab. Remove the three checkmarks that pertain to DHT and PEX (see image below): Do not ‘Hit & Run’ a Private BT site: A ‘Hit & Run’ (or H&R) is when someone joins a private tracker, and downloads as much as they can before making off without uploading to a proper ratio. While this practice is frowned upon even on public sites such as mininova.org, it is deplorable to private sites. This can (and sometimes will) lead to your IP address being banned from the site - forever. Stick within these guidelines for HAPPY Torrenting! http://torrentfreak.com/10-tips-tric...-sites-080323/  White House Tech Policy Called `Magical Thinking` Bush policy draws criticism for failing to promote effective competition. Roy Mark No conference on technology policy would be complete without a debate on where America stands in the global competition race. Is the pipe half full or half empty? Not surprisingly, the talk at the second annual Tech Policy Summit was decidedly mixed. "The U.S. is still the most dynamic broadband economy in the world," said Ambassador Richard Russell, the associate director of the White House's Office on Science and Technology Policy. "As opposed to being miles ahead, though, we're only a little ahead." But Yale Law School's Susan Crawford called Russell's position "magical thinking. We're not doing well at all." She proceeded to call the White House's effort "completely inadequate on broadband competition." Crawford added that what America needs is "access to a general communication structure that is open with universal access," a notion characterized by Russell as a "tragic mistake" and invoked an image of a single, regulated monopoly. "More pipes into the home is the key," Russell said. Crawford, though, said the administration has failed to promote competition through its free-market approach, noting that even the recent 700MHz spectrum auction is not likely to change the competitive landscape much, since Verizon Wireless won the best slice for wireless broadband. "The big actors [telecoms and cable companies] are running regional duopolies," she said. Russell said there is no need for any new legislation to create a more competitive atmosphere. "People don't understand how hard it is to write legislation," he said, citing the 1996 Telecommunications Act as a prime example. As originally passed by Congress, lawmakers envisioned the act creating competition by forcing telecoms and cable companies to share their lines at discounted prices with competitors. "Look how that turned out. [Congress] decided to have everyone share the same line and the wire was copper," Russell said. "The administration has opposed any new legislation because you never know how it might turn out." Joe Waz, Comcast's vice president of external affairs and public policy, blamed the failure of the 1996 legislation on "endless gaming of the system by the incumbents." M2Z Networks Chairman and CEO Milo Medin laid the 1996 act's failure at the feet of politicians. "Congress was trying to cut the baby in half. Politicians love this sort of thing," he said. Crawford said Congress' primary mistake was imposing a "thy shall cooperate" regime on the Baby Bells and cable companies. However, they did not and proceeded to launch a blizzard of protracted litigation. By the end of the debate, Crawford was the only member of the panel still insisting on an activist Congress to address issues such as network neutrality and network management. The other members were putting their faith in the free market. "This is really about the rights of unborn technology," she said. http://www.eweek.com/c/a/Infrastruct...WK_032808_SDT2  Low-Income Residents Get High-Speed Access Katie Hafner Last summer, when Earthlink pulled the plug on plans to build a city-wide Wi-Fi network in San Francisco, it looked like only those with the money to pay for high-speed Internet access (or with a decent laptop and a good map of free hotspots) would be able to get it. Such bad things should happen more often. To bridge the gap, earlier this week, the Internet Archive, a San Francisco-based non-profit organization, began offering free Internet service to a number of public housing projects where the Internet will be piped in at speeds far greater than most high-speed systems provide. The first project to be connected is Valencia Gardens in the city’s Mission District, with 260 units. It is now up and running in a pilot project. The project expects to wire more than 2,500 units in the city over the next eight to ten months, said Brewster Kahle, the founder of the Internet Archive, which is best known for its digital archiving work. The apartments are connected to the Internet at 100 megabits per second, a speed that contrasts sharply with the normal high-speed Internet service offered by telephone and cable companies, which is usually less than 6 megabits/second. Mr. Kahle said the Internet Archive has achieved such high speed by working with the city of San Francisco to connect the city’s municipal fiber optic network, which runs through the public housing developments, to an Internet Archive switching center, which in turn, connects to the Internet. “We are pleased to be the first non-profit organization to bring public housing online,” Mr. Kahle said. “We are excited to see much faster access to the Internet as a way to experiment with advanced applications, and are pleased that the underserved get first access to advanced technology.” http://bits.blogs.nytimes.com/2008/0.../index.html?hp  Why Old Technologies Are Still Kicking Steve Lohr IN 1991, Stewart Alsop, the editor of InfoWorld and a thoughtful observer of industry trends, predicted that the last mainframe computer would be unplugged by 1996. Last month, I.B.M. introduced the latest version of its mainframe, the aged yet remarkably resilient warhorse of computing. Today, mainframe sales are a tiny fraction of the personal computer market. But with the mainframe facing extinction, I.B.M. retooled the technology, cut prices and revamped its strategy. A result is that mainframe technology — hardware, software and services — remains a large and lucrative business for I.B.M., and mainframes are still the back-office engines behind the world’s financial markets and much of global commerce. The mainframe stands as a telling case in the larger story of survivor technologies and markets. The demise of the old technology is confidently predicted, and indeed it may lose ground to the insurgent, as mainframes did to the personal computer. But the old technology or business often finds a sustainable, profitable life. Television, for example, was supposed to kill radio, and movies, for that matter. Cars, trucks and planes spelled the death of railways. A current death-knell forecast is that the Web will kill print media. What are the common traits of survivor technologies? First, it seems, there is a core technology requirement: there must be some enduring advantage in the old technology that is not entirely supplanted by the new. But beyond that, it is the business decisions that matter most: investing to retool the traditional technology, adopting a new business model and nurturing a support network of loyal customers, industry partners and skilled workers. The unfulfilled predictions of demise, experts say, tend to overestimate the importance of pure technical innovation and underestimate the role of business judgment. “The rise and fall of technologies is mainly about business and not technological determinism,” said Richard S. Tedlow, a business historian at the Harvard Business School. To survive, technologies must evolve, much as animal species do in nature. Indeed, John Steele Gordon, a business historian and author, observes that there are striking similarities in the evolutionary process of markets and biological ecosystems. Dinosaurs, he notes, may be long gone, victims of a change in climate that better suited mammals. But smaller reptiles evolved and survived, and today there are more than 8,000 species of reptiles, mainly lizards and snakes, compared with about 5,400 species of mammals. As a media technology, radio is an evolutionary survivor. Its time as the entertainment hub of American households in the 1930s and ’40s, captured in the Woody Allen film “Radio Days,” gave way to the rise of television. TV replaced radio as the box families gathered around in their living rooms. Instead, radio adopted shorter programming formats and became the background music and chat while people ride in cars or do other things at home — “audio wallpaper,” as Paul Saffo, a technology forecaster in Silicon Valley, puts it. While television did pose a threat to movies, it also served as a prod to innovation, including failures like Smell-O-Vision but also wide-screen, rich-color technologies like Cinerama and CinemaScope. The idea — and a good one — was to give viewers a more vivid, immersive experience than they could possibly have with television. Today movies, like other traditional media, face the digital challenge of the Internet. And Mr. Saffo is betting that after a period of adjustment and experimentation, they will make another life-prolonging adaptation. “Technologies want to survive, and they reinvent themselves to go on,” he said. The survivors also build on their own technical foundations as well as the human legacy of people skilled in the use of a technology and the business culture and habits that surround it. And a change in the economic environment can sometimes lead to the renaissance of an older technology. Railroads, for example, have enjoyed a revival of investment recently as rising fuel costs and road congestion have prompted shippers to move from trucks to trains; some travelers, too, have opted for railways, along routes like the Boston-New York-Washington corridor. The weight of legacy is underestimated, according to John Staudenmaier, editor of the journal Technology and Culture, because innovation is so often portrayed as a bold break with the past. A few stories of technological achievement fit that mold, like the Manhattan Project, but they are rare indeed. The mainframe is the classic survivor technology, and it owes its longevity to sound business decisions. I.B.M. overhauled the insides of the mainframe, using low-cost microprocessors as the computing engine. The company invested and updated the mainframe software, so that banks, corporations and government agencies could still rely on the mainframe as the rock-solid reliable and secure computer for vital transactions and data, while allowing it to take on new chores like running Web-based programs. “The mainframe survived its near-death experience and continues to thrive because customers didn’t care about the underlying technology,” said Irving Wladawsky-Berger, who led the technical transformation of the mainframe in the early 1990s and is now a visiting professor at the Massachusetts Institute of Technology. “Customers just wanted the mainframe to do its job at a lower cost, and I.B.M. made the investments to make that happen.” I.B.M.’s most recent model, the z10, represents an investment of $1.5 billion and the work of 5,000 technical professionals. To nurture its ecosystem, the company partners with 400 universities worldwide in programs to teach mainframe skills. The mainframe doomsayer, Mr. Alsop, is now a venture capitalist. In retrospect, he says, his 1991 prediction was wrong only in the timing. I.B.M. has so drastically reinvented the mainframe technology and its business model that the mainframes he wrote about are long gone. “It is a different world,” he said. http://www.nytimes.com/2008/03/23/te...gy/23digi.html  How Did Your Computer Crash? Check the Instant Replay Michael Fitzgerald ANYONE who uses a computer knows what it’s like to have the system crash. Crashes are the digital world’s addition to that short list of inevitables, death and taxes. But what if you could record the crash and play it back, like TiVo for software? That idea inspired two software engineers, Jonathan Lindo and Jeffrey Daudel, to figure out such a product. They have succeeded, and are now moving from the niche market where they proved the idea and onto a bigger stage. System crashes and other software flaws are more than an annoyance. A 2002 study by the National Institute of Standards and Technology estimated that software flaws cost the United States economy as much as $59.5 billion a year. For software developers, the flaws that cause crashes rank among their biggest problems, especially the ones that can’t be reproduced, like the proverbial noise in the car engine that disappears when you visit the mechanic. Mr. Lindo says he and Mr. Daudel found themselves overwhelmed by bugs they couldn’t find while working together at an Internet start-up in 2002. “We were spending almost all of our time not fixing the issues, but trying to get to the point where we could just see the issue, and we said, ‘Wouldn’t it be great if we could just TiVo this and replay it?”’ Mr. Lindo recalls. Innovation by analogy is a powerful concept, says Giovanni Gavetti, an associate professor at the Harvard Business School who, with his colleague Jan W. Rivkin, has published research on how businesses can use analogic reasoning as a strategic tool. Human beings are analogy machines, he notes, dealing with new information by comparing it to things they already know something about. It would take time for Mr. Lindo and Mr. Daudel to prove that their analogy worked. They were tackling a daunting problem — in fact, friends told them that they had a great idea, but one that was probably impossible to carry out. For one thing, they had to account for everything that can affect a program, from keystrokes, mouse movements and other software applications to network traffic and programming instructions that are designed to occur randomly. (For instance, in a computer game, the villain shouldn’t always do the same thing.) Ideally, their tool would not slow down the system as it recorded what was happening. They were also developing it for game platforms, among the most complex of software environments. There were already programs on the market that could do things like log all the various inputs a program received. But none of them worked as the program was running, which is what developers really want, say analysts like Theresa Lanowitz of Voke, a technology research firm. In effect, that meant these products took snapshots, not the “video” that Mr. Lindo and Mr. Daudel thought was necessary. Eventually, they got their technology working, and in late December 2003 quit their jobs and started Replay Solutions — so named because it would replay software crashes. Their product, ReplayDirector, works on the Xbox gaming platform and several versions of the Microsoft Windows operating system. One customer is Electronic Arts, which began using the product in the fall of 2006, according to Steven Giles, its director of online operations. Mr. Giles says he was referred to Replay by a venture capitalist he knows. The venture capitalist was worried that the company’s software might be “smoke and mirrors,” and Mr. Giles initially felt the same way. But when he realized that it worked, he convinced a number of developer teams at Electronic Arts to license the tool. (The venture capitalist ended up investing in Replay.) Mr. Giles says that he liked a number of things about the tool, but that one stood out: its ability to capture bugs that cannot be reproduced. “That’s something that nobody inside or outside our industry has really been able to solve,” he says. “We refer to it almost as magic.” He declined to say how much Electronic Arts saves by using Replay, but says that “where it’s obvious that there are savings is when you see your most senior and expensive developers working on the game rather than chasing these ghost bugs.” Replay’s gaming software sells for $50,000 a project, with negotiated pricing for multiple projects. There are still pieces missing from the TiVo analogy. For instance, software developers can’t yet fast-forward to see their crashes. Still, having tackled games, Replay is now expanding into new markets. Last week, it released a beta version of its next product, for developers who write code in the Java language. Versions for other markets will also start appearing later this year, and the technology should transfer to almost any kind of software environment, says Vishwanath Venugopalan, an enterprise software analyst at the 451 Group, a research firm in New York. THE best news for business is that Replay is one of a number of innovators, big and small, aiming to improve how software is developed, says Dana Gardner, president of Interarbor Solutions, a consulting firm in Gilford, N.H. This burst of innovation, he says, reflects the increasing importance of software across the business world. Even a clever tool like Replay, however, cannot completely eliminate system crashes. With new software applications, “you’re always trying to solve a problem nobody’s ever solved before,” notes Michael D. Ernst, an associate professor of computer science at M.I.T. who studies programmer productivity and has independently been researching the idea of “replaying” software. New software, then, guarantees new bugs. But having a way to replay problems should make it much faster to find — and swat — those bugs. http://www.nytimes.com/2008/03/23/te...y/23proto.html  Buyer Beware: Pointless Text File Wins 16 Software Awards D. Scott Pinzon An amusing story over on Successful Software.Net highlights the risky side of relying on freeware and shareware for any mission-critical purpose. Andy Brice, a UK-based software developer, had grown suspicious about "awards" ascribed to freeware and shareware programs that he knew lacked functions and features of rival offerings. So he invented a program named AwardMeStars. It didn't run; in fact, it wasn't actually a program. It was a text file comprised solely of the words, "This program does nothing at all," and renamed as an executable (.EXE). He had a third party submit his file to just about every software aggregation site; then he sat back to watch the results. His non-operating, do-nothing program won 16 awards. Various cites labeled it "Certified 5-Star," "Editor's Pick," and "Cool Discovery." All of them, obviously, from sites that didn't even bother to note the blatant name of the program, nor try to run it even once. What's going on? Brice surmises that the software sites award their top rating to everything submitted, in hopes that the software authors will boast of the awards on their own sites and link back to the aggregator sites -- thus, raising the aggregator site's rankings in search engines. Small businesses in particular love to rely upon low-cost solutions, and since shareware typically comes from an author with no marketing budget, network administrators who use free tools often find themselves downloading a piece of code they've never heard of. Well, if you're relying on "reviews" and "awards" to help you judge the reputation of that freeware, move carefully. Here is one more reason you should dedicate a computer to being your test machine, keep it off your primary network -- and try before you buy. Or, in the case of freeware, enjoy before you deploy. Kudos to Brice for sharing his story, and further kudos to Slashdot affiliate freshmeat.com for being one of the few sites to reject Brice's "program." To see the list of sub-standard sites that issue the awards, check out Brice's full story. http://www.watchguard.com/RSS/showar...k=RSS.16Awards  A One-Stop Site Offers All the Photo Functions, From Posting Online to Red-Eye Removal J .D. Biersdorfer Flickr and Facebook allow you to share photos online, and desktop programs like Picasa, iPhoto and Photoshop Elements let you make the pictures look good before you upload. But starting today with its new Photoshop Express site, Adobe is putting the two together. After signing up for the free site at www.photoshop.com/express, members can upload their images and then edit them with Adobe’s simplified set of point-and-click controls for red-eye removal, cropping, exposure, saturation and other functions. Users can group images into Web albums and post them to popular social networking sites, all from within Photoshop Express. Each basic account at the site, which is still in a beta test version, gets two gigabytes of online storage, although Adobe soon plans to offer more services for a fee. If you think you went too far with your photo manipulation, Photoshop Express lets you remove changes one by one — or go all the way back to the original picture. http://www.nytimes.com/2008/03/27/te...h/27adobe.html  Dinner and a video event At Cineplexes, Sports, Opera, Maybe a Movie Kelly Shimoda Brooks Barnes Movie theaters are not just for movies anymore. Coming soon will be broadcasts of live baseball games, rock concerts, classic TV shows and an array of other offerings not associated with the silver screen. From nickelodeons to drive-ins to multiplexes, American movie theaters have always evolved with the times. But the latest evolution, set off by stagnating attendance and advances in digital technology, marks the first time that movie theaters have reinvented themselves without motion pictures as the centerpiece. “Exhibitors are heading toward showing more than just movies faster than anyone expected,” said Ted Mundorff, chief executive of Landmark Theaters, which operates multiplexes in California, Texas and New York, among other states. “Live simulcasts of sporting events or whatever won’t displace the first week of ‘Harry Potter,’ but they might displace the fifth week.” Chains in Tennessee and New Jersey sell $25 tickets to performances of La Scala operas. AMC and Regal, two of North America’s biggest chains, have promoted concerts (Celine Dion), marathons of classic TV shows (“Star Trek”) and seasonal events (the St. Olaf Christmas Festival). On April 24, hundreds of theaters are scheduled to show highlights from the Drum Corps International World Championships. Few think nonmovie content will supplant movies as the primary reason people trek to the multiplex. Rather, the hope is that all the niche offerings will add up to steady supplemental income. “I love film, but the simple fact is that we can’t count on movie attendance to grow,” said Thomas W. Stephenson Jr., president of Rave Motion Pictures, which operates theaters in 11 states. Movie attendance inched up less than 1 percent in 2007, year-over-year, after a narrow increase in 2006 and three previous years of sharp declines — even as studios pumped out a record number of blockbuster-style pictures. Movie fans bought about 1.42 billion tickets in 2007, according to Media by Numbers, delivering $9.6 billion in revenues. As televisions get bigger and the gap between a film’s theatrical release and DVD release shrinks, exhibitors worry that attendance could slump further. Video on demand poses another threat. Piracy, meanwhile, eats away more than $600 million annually in movie ticket sales, according to the National Association of Theater Owners. Exhibitors have long sought to come up with new ways to fill seats. Renting out auditoriums for meetings gained popularity a decade ago. And some theaters have experimented with nonmovie content for years. Screenvision, a New York company that sells on-screen advertising for more than 1,900 theaters, simulcast the 2003 MTV Movie Awards to a handful of theaters. What is different now? The economic need is greater, and the technology needed to show live broadcasts and high-definition films is now accessible enough, and reliable enough, to make this a real market, operators say. About 5,000 movie screens in the United States are equipped with digital projectors, up from 200 just three years ago. Within the next two years, that number is expected to be 10,000. Digital projection systems, while expensive, give theaters the ability to pull off live, high-definition simulcasts — and also open the door for 3-D presentation, something that is expected to lift their core movie business. “We can now replicate Carnegie Hall across the country,” said Matthew Kearney, the chief executive of Screenvision. Perhaps not exactly. But a $40 ticket to hear the New York Philharmonic play at Carnegie Hall gets patrons a balcony seat. At a multiplex, for half that price, customers would get digital surround-sound and a close-up view. Simulcasts of the Metropolitan Opera over the last year helped turn the tide. National CineMedia, a competitor of Screenvision, said nearly 300,000 people attended screenings in 2007, which was the inaugural season; in 2008, simulcasts of Met performances in movie theaters are expected to draw upwards of a million people. The New York Mets could not have been happier with a simulcast last August at Ziegfeld Theater in New York, where a live organist and the team mascot led viewers in singalongs as though they were in the ballpark. “Tickets to watch the game in the theater sold out so quickly that we’re in talks to do a bunch more of them this summer,” said Dave Howard, executive vice president for business operations for the Mets. Doug and Margarita Gibson, on the other hand, were annoyed two weeks ago during a Landmark simulcast of a Tennis Channel exhibition match between Pete Sampras and Roger Federer. The couple paid $20 for tickets only to discover that the event was not shown in high-definition as advertised. Also, a technical problem interrupted the match for 10 minutes after the first set. “Next time, we will just stay home and watch it,” said Mr. Gibson, who asked for, and received, a refund. Marketing is the biggest puzzle that operators need to figure out, said Jeffrey B. Logsdon, an entertainment analyst at BMO Capital Markets. Trying to contain costs, most have relied on advertising on their Web sites and in movie listings. Still, most people do not think to seek this kind of content at the movies, he said. Consumer psychology, Mr. Logsdon says, plays as big a role in the shift as economics. Operators want people to think of theaters as vibrant, busy places. But when weekends account for 70 percent of movie ticket sales, multiplex parking lots spend a lot of time sitting empty. “We want people to get used to coming into our building,” said Shari Redstone, president of National Amusements, the operator of 1,500 screens and the parent company of both Viacom and CBS. “It’s less ‘let’s be a movie theater’ and more ‘let’s be a community entertainment destination.’ ” http://www.nytimes.com/2008/03/23/bu...3multi.html?hp  Regal, Like AMC, to Add Imax Screens Brooks Barnes The Regal Entertainment Group, which owns the nation’s largest movie theater chain, will work with the Imax Corporation to open 31 new, large-format outlets. The two companies said they would share the cost of installation and the revenue, but declined to reveal more detailed financial information. One of Regal’s primary competitors, AMC Entertainment, announced a similar deal with Imax in December. The movie theater business, buffeted by a decade-long boom in home entertainment that has hurt attendance, is betting that Imax’s eye-popping imagery will help lure patrons to the multiplex. Currently Imax has 150 theaters in the United States, with plans for more than 300 by 2010. The increased emphasis on Imax comes as Hollywood makes more movies available in the format, which is still struggling to expand beyond its roots in science and history museums. Several summer blockbusters will have an Imax option, including “Kung Fu Panda,” a DreamWorks Animation picture featuring the voice of Jack Black. Regal said it will install Imax digital projection systems in 20 of its largest markets. It noted that the equipment will help improve profitability for itself and movie studios by cutting the expenses of shipping and handling film prints. The first converted theaters will open in November. http://www.nytimes.com/2008/03/24/bu...ia/24imax.html  Video Camera Shoot-Off Jack $3200.00 Canon High Definition XH-A1 VS. the $169.00 Flip. "I think we're right on the verge of 'ultra budget' filmmaking." - Kirk Mastin http://kirkmastin.blogspot.com/2008/...ormats_21.html Things are getting very interesting for independent content creators.  Amazon Kindle and Sony Reader Locked Up: Why Your Books Are No Longer Yours If you buy a regular old book, CD or DVD, you can turn around and loan it to a friend, or sell it again. The right to pass it along is called the "first sale" doctrine. Digital books, music and movies are a different story though. Four students at Columbia Law School's Science and Technology Law Review looked at the particular issue of reselling and copying e-books downloaded to Amazon's Kindle or the Sony Reader, and came up with answers to a fundamental question: Are you buying a crippled license to intellectual property when you download, or are you buying an honest-to-God book? In the fine print that you "agree" to, Amazon and Sony say you just get a license to the e-books—you're not paying to own 'em, in spite of the use of the term "buy." Digital retailers say that the first sale doctrine—which would let you hawk your old Harry Potter hardcovers on eBay—no longer applies. Your license to read the book is unlimited, though—so even if Amazon or Sony changed technologies, dropped the biz or just got mad at you, they legally couldn't take away your purchases. Still, it's a license you can't sell. But is this claim legal? Our Columbia friends suggest that just because Sony or Amazon call it a license, that doesn't make it so. "That's a factual question determined by courts," say our legal brainiacs. "Even if a publisher calls it a license, if the transaction actually looks more like a sale, users will retain their right to resell the copy." Score one for the home team. There's a kicker, though: If a court ruled with you on that front, you still can't sell reproductions of your copy, an illegal act tantamount to Xeroxing your Harry Potters. You'd have to sell the physical media where the "original" download is stored—a hard drive or the actual Kindle or Sony Reader. Our guess is that it only gets more complicated from here. What happens when the file itself resides only on some $20-per-month Google storage locker? For more details, have a look at the original, surprisingly readable legal summary: Quote:
 Feds Tout New Domestic Intelligence Centers Ryan Singel Federal, state and local cops are huddling together in domestic intelligence dens around the nation to fuse anti-terror information and tips in ways they never have before, and they want the American people to know about it -- sort of. Some of the nation's top law enforcement and anti-terror officials got together to hold press briefings Tuesday and Wednesday mornings at the second annual National Fusion Center conference held in San Francisco. Homeland Security Under Secretary Charlie Allen, formerly of the CIA, described how sharing threat assessments, and even the occasional raw intel, with the new fusion centers marks a cultural shift from the Cold War era. Back then, spies treated everyone, other departments and agencies included, as suspicious. "Things have changed remarkably in Washington. We are talking to each other," Allen said Tuesday. "I am from the shadows of the CIA where in the Cold War, we followed a different model. That model does not apply for the kinds of threats we have today that are borderless. The threats are so different and so remarkably dangerous for our citizens." The fifty or so U.S. fusion centers are where the federal, state and local cops share intelligence, sift data for clues, run down reports of suspicious packages and connect dots in an effort to detect and thwart terrorism attacks, drug smuggling and gang fighting. Privacy and civil liberties groups are increasingly suspicious of the fusion centers, but state and local officials have complained for years that the feds don't share any useful information. The 9/11 Commission agreed, blaming the CIA and FBI's lack of information-sharing for wasted chances to stop the airline hijackings. The commission strongly urged they change their ways and put holes in so-called "stove pipes." And in 2007, the Democrats boosted fusion centers' stature and funding in the first bill they passed after taking control of Congress. More than $130 million federal dollars have fed the development of the fusion centers in locations as diverse as Kansas and Northern California. On Tuesday, San Francisco police chief Heather Fong said the information flow was getting better, especially around big events being held in the city. "When we get information, it's not how much can we amass and keep to ourselves," Fong said. "It's how much information can we obtain but appropriately share so that it positively assists others in doing their jobs around the country and the world." The dominant catchphrase from the officials was that the centers need to focus on "all threats, all hazards." That means that the fusion centers would be working on immigration, radicalization, demographic changes, hurricanes, biological and chemical threats, as well as common criminal activity. Officials say the centers must look at even the most mundane crimes, since they can be used to fund terrorism. By way of example, Los Angeles police chief Bratton cites the investigation of a string of gas station stick-ups in L.A. in 2005. The robbery investigation led to the prosecution of militant Muslim convicts who were planning attacks on synagogues. That, Bratton said, illustrates why these intelligence centers need to be analyzing run-of-the-mill crimes. "Information that might seem innocuous may have some connection to terrorism," Bratton said. But critics say that "all hazards, all threats" approach sounds suspiciously like the government is building a distributed domestic intelligence service that could easily begin keeping tabs on Americans exercising their First Amendment rights. The scope also seems at odds with the federal government's Information Sharing Environment guidelines, which say these centers are supposed to focus on terrorism. California's Anti-Terrorism Information Center admitted to spying on anti-war groups in 2003. And Denver's police department built their own secret spy files on Quakers and 200 other organizations. Earlier this year, the ACLU issued a warning report about Fusion Centers, complete with an interactive fusion center map, earlier this year. The report, entitled What's Wrong With Fusion Centers, cited concerns about military units operating in the centers, as well as the potential for scope creep and data mining. How, the group asked, can citizens contest information about themselves, given the patchwork of state, local and federal sunshine laws that may or may not apply. But in a conference keynote Tuesday, Congresswoman Jane Harman (D-California), a powerful force in intelligence matters and funding, pooh-poohed the ACLU's concerns, and said she supported both fusion centers, and civil liberties. "I was frustrated when I met with the [ACLU] report authors and they could not point to a single instance of a fusion center violating someone's civil rights or liberties," Harman said. "In fact, state and local laws and protections in place at many fusion centers are more rigorous than their federal counterparts." Tim Sparapani, the ACLU's top legislative lawyer in D.C., bristled at Harman's remakrs. "Our prognosticating track record in identifying programs ripe for abuse of privacy and civil liberties is pretty solid," Sparapani wrote in an e-mail that listed several other programs that the ACLU correctly raised warning flags on. "That's not luck," he wrote. "It's a trend based on seeing the surveillance industrial complex being built bit-by-bit and terabyte by terabyte. As sure as the sun rises in the east and sets in the west, if Fusion Centers aren't built with rigid controls they will be privacy-invading monsters. The ACLU points to Virginia, where legislators are moving to exempt their fusion center from government sunshine laws and give legal immunity to companies that report information -- such as the name of a person accosted by a private security guard for taking pictures of a skyscraper. On Wednesday, a trio of federal privacy and civil liberties officers, including the Department of Homeland Security's chief privacy officer Hugo Teufel, promised they were working to make sure the centers respect citizens' civil liberties and privacy. David Gersten, the director of the civil rights and civil liberties programs at DHS, said he was working to expand their training course for Fusion Center employees to "include an examination of the history of privacy and civil liberties as they relate to intelligence and criminal investigations." That history includes the famous 1976 Church Committee report on the FBI's notorious COINTELPRO spying program. The report warned in the introduction "Unless new and tighter controls are established by legislation, domestic intelligence activities threaten to undermine our democratic society and fundamentally alter its nature. THREAT LEVEL asked conference attendees about the concerns over expanding the dissemination of intelligence given the continuing trouble innocent Americans have trying to get off the nation's unified terrorist watch list. Just this week, the Justice Department's inspector general issued a watch list audit (.pdf), finding that FBI agents were watch-listing people who they weren't even investigating. Moreover, since those names were added through a back channel, there was no scheduled review or follow-up to take them off the watch list. Leonard Boyle, who runs the Terrorist Screening Center that curates and runs the watch list, said those problems are being fixed. "We have streamlined our processes so [...] we avoid delays in amending nominations or removing people who ought to be removed because they are no longer suspected of having a nexus to terrorism," Boyle said. Also present at the conference was Ambassador Thomas McNamara who now works at the Director of National Intelligence Office. McNamara's group is working on custom-built XML schemes, such as a standard for Suspicious Activity Reports. The idea is have all fusion centers and intelligence agencies using the same data format, to more easily share, search, sort and store intelligence data. Surprisingly, a total of only three reporters showed up over two days of the conference to hear from the officials. THREAT LEVEL was the only media outlet to show up both days. Despite journalists taking up only two of the fifty or so chairs, officials stuck with the formality of a press conference. Each day six to eight officials stood in a semicircle flanking the lectern and took turns issuing short remarks. After each set of speeches, the director of the Iowa fusion center and designated emcee Russell Porter allowed for a handful of questions from the two-reporter audience. And as for information sharing, the conference's openness extended only so far, and the press was not allowed into sensitive sessions such as "How to Generate Suspicious Activity Reporting" and "Commanders and Analysts: Sharing Perspectives." Government employees manning an informational booth for the Director of National Intelligence's OpenSource.gov website refused to even describe the program, saying they would need to call in a press minder. The website seems to indicate that the program is a way for the government to share intel reports composed by analysts who read international newspapers and watch TV stations from around the world. THREAT LEVEL guessed we would not be able to sign up for the email blasts, due to our propensity to share information with the public. The taciturn DNI employees confirmed that fact, adding that they also couldn't share the information from OpenSource.gov due to copyright issues. http://blog.wired.com/27bstroke6/200...out-new-d.html  Overstock.com CEO: Wikipedia Has Become An Instrument Of Mass Mind-Control Reader Adam forwarded us this bizarre email from Patrick Byrne, CEO of Overstock.com. After announcing deals on watches and exercise equipment, the email invites readers "Take 5 with Patrick, " which involves the CEO likening Wikipedia to mind-control and Wall Street corruption. Apparently the feud between Wikipedia and Overstock goes way back. Back in late 2006, someone from Overstock edited the company's Wikipedia page to read like an advertisement. This was reverted by one of the site's editors. Over the next few months, Overstock's "director of social media," Judd Bagley, used dozens of Wikipedia identities to revert Overstock's entry and harass editors. Overstock also began a site called antisocialmedia.net, run by Bagley. Fed up, Wikipedia banned all Overstock. IP addresses from editing Wikipedia pages. Since then, Byrne has used his "Take 5 with Patrick" postings to disseminate articles such as "Social Media - Hijacking the Discourse," "How to Handle a Corrupt Reporter," "A Small Thing Called, the First Amendment," and "Our Corrupt Federal Regulator the SEC." http://consumerist.com/371015/overst...s-mind+control  Will Homeland Security the Militarized Police State Shock You Into Submission? Karen De Coster This is perhaps one of the most kooky and creepy Security State tactics that I have come across: the EMD safety bracelet, which is being billed as the "last line of defence." A company called Lamperd Firearm Training Systems (scroll down) is trying to commercialize this item as an "airline security product." The company’s video that hawks this device talks about the current facial recognition system called biometrics, where cameras capture photos of people and compare those images to the images of "terrorists" in its "terrorist" database. No matter how sophisticated this technology, it can all too often allow a terrorist on board a plane, and, this technology can also have the effect of creating airport bottlenecks. Ahem. The solution? The "viable, workable answer" is an electronic ID bracelet. This bracelet will replace the need for a ticket and contain all necessary information about the person, and as a bonus, it can allow the passenger to be tracked through the terminal. Crew members would be empowered with radio frequency transmitters to subdue "hijackers." The technology will override a person’s central nervous system and zap them down quicker than you can say "Homeland Security." The company assures us that being dragged through the bracelet process is a "small inconvenience in order to assure your safe arrival." In fact, its studies show that most people would "happily opt" for wearing the bracelet to "insure their own security." Here’s the Lamperd video on YouTube - you must watch it. Here’s the patent for this device. The patent actually reads this: Upon activation of the electric shock device, through receipt of an activating signal from the selectively operable remote control means, the passenger wearing that particular bracelet receives the disabling electrical shock from the electric shock device. Accordingly, the passenger becomes incapacitated for a few seconds or perhaps a few minutes, during which time the passenger can be fully subdued and handcuffed, if necessary. Depending on the type of transmission medium used to send the activating signal, other passengers may also become temporarily incapacitated, which is undesirable and unfortunate, but may be unavoidable. Lamperd even posts a series of letters on its website showing interest in the product for use "outside of airport security," which, of course, is the real reason for the product. Why it can be used for border control to subdue illegal aliens or by local law enforcement agencies to control the "criminal element!" http://www.infowars.com/?p=995  Spy-In-The-Sky Drone Sets Sights on Miami Tom Brown Miami police could soon be the first in the United States to use cutting-edge, spy-in-the-sky technology to beef up their fight against crime. A small pilotless drone manufactured by Honeywell International, capable of hovering and "staring" using electro-optic or infrared sensors, is expected to make its debut soon in the skies over the Florida Everglades. If use of the drone wins Federal Aviation Administration approval after tests, the Miami-Dade Police Department will start flying the 14-pound (6.3 kg) drone over urban areas with an eye toward full-fledged employment in crime fighting. "Our intentions are to use it only in tactical situations as an extra set of eyes," said police department spokesman Juan Villalba. "We intend to use this to benefit us in carrying out our mission," he added, saying the wingless Honeywell aircraft, which fits into a backpack and is capable of vertical takeoff and landing, seems ideally suited for use by SWAT teams in hostage situations or dealing with "barricaded subjects." Miami-Dade police are not alone, however. Taking their lead from the U.S. military, which has used drones in Iraq and Afghanistan for years, law enforcement agencies across the country have voiced a growing interest in using drones for domestic crime-fighting missions. Known in the aerospace industry as UAVs, for unmanned aerial vehicles, drones have been under development for decades in the United States. The CIA acknowledges that it developed a dragonfly-sized UAV known as the "Insectohopter" for laser-guided spy operations as long ago as the 1970s. And other advanced work on robotic flyers has clearly been under way for quite some time. "The FBI is experimenting with a variety of unmanned aerial vehicles," said Marcus Thomas, an assistant director of the bureau's Operational Technology Division. "At this point they have been used mainly for search and rescue missions," he added. "It certainly is an up-and-coming technology and the FBI is researching additional uses for UAVs." Safety, Privacy Concerns U.S. Customs and Border Protection has been flying drones over the Arizona desert and southwest border with Mexico since 2006 and will soon deploy one in North Dakota to patrol the Canadian border as well. This month, Customs and Border Protection spokesman Juan Munoz Torres said the agency would also begin test flights of a modified version of its large Predator B drones, built by General Atomics Aeronautical Systems, over the Gulf of Mexico. Citing numerous safety concerns, the FAA -- the government agency responsible for regulating civil aviation -- has been slow in developing procedures for the use of UAVs by police departments. "You don't want one of these coming down on grandma's windshield when she's on her way to the grocery store," said Doug Davis, the FAA's program manager for unmanned aerial systems. He acknowledged strong interest from law enforcement agencies in getting UAVs up and running, however, and said the smaller aircraft particularly were likely to have a "huge economic impact" over the next 10 years. Getting clearance for police and other civilian agencies to fly can't come soon enough for Billy Robinson, chief executive of Cyber Defense Systems Inc, a small start-up company in St. Petersburg, Florida. His company makes an 8-pound (3.6 kg) kite-sized UAV that was flown for a time by police in Palm Bay, Florida, and in other towns, before the FAA stepped in. "We've had interest from dozens of law enforcement agencies," said Robinson. "They (the FAA) are preventing a bunch of small companies such as ours from becoming profitable," he said. Some privacy advocates, however, say rules and ordinances need to be drafted to protect civil liberties during surveillance operations. "There's been controversies all around about putting up surveillance cameras in public areas," said Howard Simon, Florida director of the American Civil Liberties Union. "Technological developments can be used by law enforcement in a way that enhances public safety," he said. "But every enhanced technology also contains a threat of further erosion of privacy." (Reporting by Tom Brown; Editing by Michael Christie and Eddie Evans) http://www.reuters.com/article/newsO...29797920080326  California Backs Off Real ID – Update Ryan Singel For a short moment Thursday, millions of Californians were in danger of facing pat-downs at the airport and being blocked from federal buildings come May 11. In a Tuesday letter to Homeland Security chief Michael Chertoff, the head of California's DMV said that while California had already applied for and gotten an extension on the Real ID deadline, it wasn't actually committing to complying with Real ID rules by 2010. That's when states who ask for extension have to begin issuing driver's licenses and state IDs that comply with the federal rules. "California's request for an extension is not a commitment to implement Real ID, rather it will allow us to fully evaluate the impact of the final regulations and precede with necessary policy deliberations prior to a final decision on compliance," DMV director George Valverde wrote. States have until March 31 to request a two-year extension, and DHS had said before Thursday it won't grant Real ID extensions to states who don't commit to implementing the rules in the future. That meant Tuesday's letter looked like enough to join California to the small rebellion against the Real ID rules. For Californians that would mean enduring the same fate facing citizens of South Carolina, Maine, Montana and New Hampshire. They would have needed to dig out their passport, if they had one, every time they boarded a plane, or go through an extra level of TSA screening at airport metal detectors. Los Angeles and San Francisco airports could have had security lines stretching to the Sierras. Californians would also have been barred from buying certain medicine, entering federal court buildings or getting help at the Social Security Administration, unless they have a passport. But after Threat Level provided Homeland Security spokesman Laura Keehner with the letter, Keehner said California's commitment to thinking about commitment is good enough. "For right now, there is nothing that says they will not comply with Real ID," Keehner said. Even though California just said it might not comply with Real ID, Keehner said that's fine since there was an ongoing process that might lead to compliance. "It is different than saying we are not complying with Real ID," Keehner said. "If they were saying that, they would not get an extension." At issue are long-delayed rules that require states to collect, verify and store birth and marriage certificates for nearly all citizens who have state-issued licenses or identification cards. That means almost every driver's license holder will have to get certified documents and go into the DMV to get a new license -- and many will likely have to go in more than once. The rules also require the nation's DMVs to interconnect their systems to prevent duplicate licenses and conform to federal standards for the physical cards themselves. DHS estimates the changes will cost from $4 to $20 billion, but is only offering some $80 million in direct funds. In early January when DHS unveiled the final rules, Secretary Michael Chertoff said Real ID would make the country safer. "For about $8 per license, Real ID will give law enforcement and security officials a powerful advantage against falsified documents, and it will bring some peace of mind to citizens wanting to protect their identity from theft by a criminal or illegal alien," Chertoff said. Maine, Montana, South Carolina and New Hampshire are fighting the mandate, saying the rules violate state rights, will cost them billions and intrude on citizens' privacy rights. The states aren't alone. Interest groups ranging from the AARP, the right wing Eagle Forum and the ACLU oppose the rules, and Homeland Security's own outside privacy advisers explicitly refused to endorse Real ID as "workable or appropriate" in 2007. In February, New Hampshire asked for the extension, but also said that the request is "not an indication of our state's intent to comply with the Real ID final rule." In 2007, New Hampshire lawmakers passed, and Democratic governor John Lynch signed, a law banning New Hampshire from complying with Real ID. So far, DHS has not accepted New Hampshire's request for an extension. DHS says that it is committed to rejecting the rebel states' driver's licenses as acceptable proof of identification come May 11. DHS spokesman Russ Knocke told Threat Level two weeks ago that citizens need to lay the blame for any inconveniences on their state officials and suggested the residents apply for passports now. Keehner reiterated that that there "will be real consequences for states whose leadership chooses not to comply." For instance, showing up with a driver's license at the airport "will be the same as showing up with no license currently," Keehner said. She added that Secretary Chertoff held a conference call today with a number of governors to talk about Real ID, and that included Governor Mark Sanford of the rogue state of South Carolina. The group is "working together on going forward," Keehner said. Bill Scannell, a spokesman for the Identity Project which is fighting Real ID, questioned whether DHS can keep its hard line if California joins the mix. "California has stated quite clearly they do not intend to comply with Real ID," Scannell said. "It begs the the question: Will DHS be playing hardball with the big 40-ton gorilla California in the same way it has been slapping around little tiny New Hampshire? Their issues are the same." The letter from California comes a little more than a week after Assembly member Pedro Nava, the head of the Transportation committee in the California legislature, introduced a resolution calling on California's congressional crew to rewrite the rules because they were too expensive and privacy invasive. Update: This story was changed substantially after DHS spokeswoman Laura Keehner said that the letter would not lose California's extension. The original version relied on the presumption that it could. http://blog.wired.com/27bstroke6/200...rnia-back.html  Outsourced Passport Work Risky Bill Gertz The United States has outsourced the manufacturing of its electronic passports to overseas companies — including one in Thailand that was victimized by Chinese espionage — raising concerns that cost savings are being put ahead of national security, an investigation by The Washington Times has found. The Government Printing Office's decision to export the work has proved lucrative, allowing the agency to book more than $100 million in recent profits by charging the State Department more money for blank passports than it actually costs to make them, according to interviews with federal officials and documents obtained by The Times. The profits have raised questions both inside the agency and in Congress because the law that created GPO as the federal government's official printer explicitly requires the agency to break even by charging only enough to recover its costs. Lawmakers said they were alarmed by The Times' findings and plan to investigate why U.S. companies weren't used to produce the state-of-the-art passports, one of the crown jewels of American border security. "I am not only troubled that there may be serious security concerns with the new passport production system, but also that GPO officials may have been profiting from producing them," said Rep. John D. Dingell, the Michigan Democrat who chairs the House Energy and Commerce Committee. Officials at GPO, the Homeland Security Department and the State Department played down such concerns, saying they are confident that regular audits and other protections already in place will keep terrorists and foreign spies from stealing or copying the sensitive components to make fake passports. "Aside from the fact that we have fully vetted and qualified vendors, we also note that the materials are moved via a secure transportation means, including armored vehicles," GPO spokesman Gary Somerset said. But GPO Inspector General J. Anthony Ogden, the agency's internal watchdog, doesn't share that confidence. He warned in an internal Oct. 12 report that there are "significant deficiencies with the manufacturing of blank passports, security of components, and the internal controls for the process." The inspector general's report said GPO claimed it could not improve its security because of "monetary constraints." But the inspector general recently told congressional investigators he was unaware that the agency had booked tens of millions of dollars in profits through passport sales that could have been used to improve security, congressional aides told The Times. Decision to outsource GPO is an agency little-known to most Americans, created by Congress almost two centuries ago as a virtual monopoly to print nearly all of the government's documents, from federal agency reports to the president's massive budget books that outline every penny of annual federal spending. Since 1926, it also has been charged with the job of printing the passports used by Americans to enter and leave the country. When the government moved a few years ago to a new electronic passport designed to foil counterfeiting, GPO led the work of contracting with vendors to install the technology. Each new e-passport contains a small computer chip inside the back cover that contains the passport number along with the photo and other personal data of the holder. The data is secured and is transmitted through a tiny wire antenna when it is scanned electronically at border entry points and compared to the actual traveler carrying it. According to interviews and documents, GPO managers rejected limiting the contracts to U.S.-made computer chip makers and instead sought suppliers from several countries, including Israel, Germany and the Netherlands. Mr. Somerset, the GPO spokesman, said foreign suppliers were picked because "no domestic company produced those parts" when the e-passport production began a few years ago. After the computer chips are inserted into the back cover of the passports in Europe, the blank covers are shipped to a factory in Ayutthaya, Thailand, north of Bangkok, to be fitted with a wire Radio Frequency Identification, or RFID, antenna. The blank passports eventually are transported to Washington for final binding, according to the documents and interviews. The stop in Thailand raises its own security concerns. The Southeast Asian country has battled social instability and terror threats. Anti-government groups backed by Islamists, including al Qaeda, have carried out attacks in southern Thailand and the Thai military took over in a coup in September 2006. The Netherlands-based company that assembles the U.S. e-passport covers in Thailand, Smartrac Technology Ltd., warned in its latest annual report that, in a worst-case scenario, social unrest in Thailand could lead to a halt in production. Smartrac divulged in an October 2007 court filing in The Hague that China had stolen its patented technology for e-passport chips, raising additional questions about the security of America's e-passports. Transport concerns A 2005 document obtained by The Times states that GPO was using unsecure FedEx courier services to send blank passports to State Department offices until security concerns were raised and forced GPO to use an armored car company. Even then, the agency proposed using a foreign armored car vendor before State Department diplomatic security officials objected. Concerns that GPO has been lax in addressing security threats contrast with the very real danger that the new e-passports could be compromised and sold on the black market for use by terrorists or other foreign enemies, experts said. "The most dangerous passports, and the ones we have to be most concerned about, are stolen blank passports," said Ronald K. Noble, secretary general of Interpol, the Lyon, France-based international police organization. "They are the most dangerous because they are the most difficult to detect." Mr. Noble said no counterfeit e-passports have been found yet, but the potential is "a great weakness and an area that world governments are not paying enough attention to." Lukas Grunwald, a computer security expert, said U.S. e-passports, like their European counterparts, are vulnerable to copying and that their shipment overseas during production increases the risks. "You need a blank passport and a chip and once you do that, you can do anything, you can make a fake passport, you can change the data," he said. Separately, Rep. Robert A. Brady, chairman of the Joint Committee on Printing, has expressed "serious reservations" about GPO's plan to use contract security guards to protect GPO facilities. In a Dec. 12 letter, Mr. Brady, a Pennsylvania Democrat, stated that GPO's plan for conducting a security review of the printing office was ignored and he ordered GPO to undertake an outside review. Questionable profits GPO's accounting adds another layer of concern. The State Department is now charging Americans $100 or more for new e-passports produced by the GPO, depending on how quickly they are needed. That's up from a cost of around just $60 in 1998. Internal agency documents obtained by The Times show each blank passport costs GPO an average of just $7.97 to manufacture and that GPO then charges the State Department about $14.80 for each, a margin of more than 85 percent, the documents show. The accounting allowed GPO to make gross profits of more than $90 million from Oct. 1, 2006, through Sept. 30, 2007, on the production of e-passports. The four subsequent months produced an additional $54 million in gross profits. The agency set aside more than $40 million of those profits to help build a secure backup passport production facility in the South, still leaving a net profit of about $100 million in the last 16 months. GPO was initially authorized by Congress to make extra profits in order to fund a $41 million backup production facility at a rate of $1.84 per passport. The large surplus, however, went far beyond the targeted funding. The large profits raised concerns within GPO because the law traditionally has mandated that the agency only charge enough to recoup its actual costs. According to internal documents and interviews, GPO's financial officers and even its outside accounting firm began to inquire about the legality of the e-passport profits. To cut off the debate, GPO's outgoing legal counsel signed a one-paragraph memo last fall declaring the agency was in compliance with the law prohibiting profits, but offering no legal authority to back up the conclusion. The large profits accelerated, according to the officials, after the opinion issued Oct. 12, 2007, by then-GPO General Counsel Gregory A. Brower. Mr. Brower, currently U.S. Attorney in Nevada, could not be reached and his spokeswoman had no immediate comment. Fred Antoun, a lawyer who specializes in GPO funding issues, said the agency was set up by Congress to operate basically on a break-even financial basis. "The whole concept of GPO is eat what you kill," Mr. Antoun said. "For the average taxpayer, for them to make large profits is kind of reprehensible." Likewise, a 1990 report by Congress' General Accounting Office stated that "by law, GPO must charge actual costs to customers," meaning it can't mark up products for a profit. Like the security concerns, GPO officials brush aside questions about the profits. Agency officials declined a request from The Times to provide an exact accounting of its e-passport costs and revenues, saying only it would not be accurate to claim it has earned the large profits indicated by the documents showing the difference between the manufacturing costs and the State Department fees. Questioned about its own annual report showing a $90 million-plus profit on e-passports in fiscal year 2007 alone, the GPO spokesman Mr. Somerset would only say that he thinks the agency is in legal compliance and that "GPO is not overcharging the State Department." Mr. Somerset said 66 different budget line items are used to price new passports and "we periodically review our pricing structure with the State Department." Public Printer Robert Tapella, the GPO's top executive, faced similar questions during a House subcommittee hearing on March 6. Mr. Tapella told lawmakers that increased demand for passports — especially from Americans who now need them to cross into Mexico and Canada — produced "accelerated revenue recognition," and "not necessarily excess profits." GPO plans to produce 28 million blank passports this year up from about 9 million five years ago. A State Department consular affairs spokesman, Steve Royster referred questions to GPO on e-passports costs. Congress to weigh in GPO's explanations have not satisfied lawmakers, who are poised to dig deeper. Mr. Dingell, the House Commerce chairman, said The Times' findings are "extremely serious to both the integrity of the e-passport program and to U.S. national security" and he has asked an investigative subcommittee chaired by Rep. Bart Stupak, Michigan Democrat, to begin an investigation. "Our initial inquiry suggests that more needs to be done to understand whether the supply chain is secure and fully capable of protecting the manufacturing of this critical document," Mr. Dingell told The Times. Mr. Stupak said that considering the personal information contained on e-passports, "it is essential that the entire production chain be secure and free from potential tampering." He added: "The GPO needs to make every effort to ensure that future passport components are made in America under the tightest security possible." Michelle Van Cleave, a former National Counterintelligence Executive, said outsourcing passport work and components creates new security vulnerabilities, not just for passports. "Protecting the acquisition stream is a serious concern in many sensitive areas of government activity, but the process for assessing the risk to national security is at best loose and in some cases missing altogether," she told The Times. "A U.S. passport has the full faith and credit of the U.S. government behind the citizenship and identity of the bearer," she said. "What foreign intelligence service or international terrorist group wouldn't like to be able to masquerade as U.S. citizens? It would be a profound liability for U.S. intelligence and law enforcement if we lost confidence in the integrity of our passports." http://washingtontimes.com/apps/pbcs...86493/0/SPORTS  Australian WiMAX Pioneer Trashes Technology as "Miserable Failure" Australia’s first WiMAX operator, Hervey Bay’s Buzz Broadband, has closed its network, with the CEO labeling the technology as a “disaster” that “failed miserably.” In an astonishing tirade to an international WiMAX conference audience in Bangkok yesterday afternoon, CEO Garth Freeman slammed the technology, saying its non-line of sight performance was “non-existent” beyond just 2 kilometres from the base station, indoor performance decayed at just 400m and that latency rates reached as high as 1000 milliseconds. Poor latency and jitter made it unacceptable for many Internet applications and specifically VoIP, which Buzz has employed as the main selling point to induce people to shed their use of incumbent services. Freeman highlighted his presentation with a warning to delegates, saying “WiMAX may not work.” He said that the technology was still “mired in opportunistic hype,” pointing to the fact most deployments were still in trials, that it was largely used by start-up carriers and was supported by “second-tier vendors”, which he contrasted with HSPA with 154 commercial networks already in operation and support from top tier vendors. What made Freeman’s presentation most extraordinary was that just 12 months ago he fronted the same event with a generally positive appraisal of the platform which at that stage he had deployed just a few months before. At the time, Freeman said that his company had signed 10% of its 55,000 user target market in just two months, a market share that rose to 25%, on the back of an advertising campaign that highlighted value VoIP prices. He did acknowledge at the time that the technology had indoor coverage issues, which he yesterday said had earned him a quick and negative reaction at the time from his supplier, Airspan. Other early WiMAX adopters have also reported issues with indoor coverage: VSNL in India reported indoor loss at just 200m from the base station at an IEEE conference last year. HORSES FOR COURSES: Freeman says Buzz has now abandoned WiMAX in favour of a “horses for courses” policy. This includes use of the TD-CDMA standard at 1.9GHz—used by operators such as New Zealand’s Woosh Wireless—and a platform he described as wireless DOCSIS– a relatively little known technology that takes HFC plant and extends its capabilities via wireless mesh. He said wireless DOCSIS operates at up to 38Mbps in the 3.5GHz spectrum and its customer premises equipment supported two voice ports for under $A70 while it boasted “huge cell coverage.” He also was employing more conventional wireless mesh platforms at 2.4GHz that support up to 10Mbps with CPE voice ports costing less than A$80. Despite his problems with WiMAX, Freeman is a believer that competitors should operate their own infrastructure and not depend on Telstra unbundled or wholesale offerings. Prior to Buzz he was involved in the rollout of regional Victorian HFC networks as an executive with Neighborhood Cable. He says the use of wireless is essential in Hervey Bay, because ADSL is blocked to 80% of the population because of Telstra’s use of pairgain and RIMs, while what ADSL ports are available are now largely exhausted. But years of successive government policies had weakened the case for standalone infrastructure, beginning with restrictive policies in the pay television market which he said undermined independent HFC deployments. “I’m against government micromanagement of the market. Government should start to provide a conducive investment environment.” Not all WiMAX operators are unhappy. Internode says an Airspan-supplied network is providing consistent average speeds of 6Mbps at distances up to 30km, with CEO Simon Hackett describing the platform as “proven.” Freeman’s frank words left many at the WiMAX event looking uncomfortable but none more so than his co-panelist Adrian de Brenni representing Opel Networks. De Brenni, standing in for an absent Jason Horley, said little new about Opel that hasn’t already been discussed, except to state that QoS would be a product feature of the future Opel wholesale offering “including voice.” http://www.commsday.com/node/228  Sprint, Clearwire Team Up on WiMax Cable Joint Venture Cable companies discuss funding wireless venture Comcast Corp and Time Warner Cable Inc, the two largest U.S. cable operators, are discussing a plan to fund a new wireless company that would be run by Sprint Nextel Corp and Clearwire Corp, people familiar with the discussions said on Tuesday. Comcast is expected to contribute as much as $1 billion for the wireless venture, which would use emerging WiMax technology for the nationwide venture, said the sources, who were familiar with the deal but not authorized to speak to the media about it. WiMax is a largely unproven technology that promises to support Internet access at speeds up to five times faster than traditional wireless networks, and can support a range of mobile and video applications. WiMax is a potential substitute for fixed-wire high-speed Internet that, for instance, could be offered across an entire metropolitan region. Time Warner Cable is expected to put in about $500 million, the sources said. These parties are trying to raise $3 billion for the joint venture. Intel Corp may contribute $1 billion, one of the sources said. Google Inc may be potential funding partner, the person said. Bright House Networks, the sixth-largest U.S. cable provider, is also involved in the discussions and would provide between $100 million and $200 million for the venture, the person said. But the talks are still in "very early stages," the sources said and a deal could fail to come to a conclusion. Intel, Sprint, Google and Clearwire officials declined to comment. Officials from Comcast and Time Warner Cable were not immediately available. Sprint, the No. 3 U.S. mobile service, has said it aims to use WiMax technology to provide wireless connections to consumer electronic devices such as music players and cameras as well as cell phones and laptops. Sprint, which has been bleeding subscribers amid customer service problems, said recently that it was reviewing its WiMax plans after it was widely criticized by shareholders for a commitment to spend $5 billion to build the high-speed wireless network based on WiMax. Both Sprint and Clearwire have said they were looking for outside funding for their WiMax networks. Sprint and Clearwire also said last month they were continuing to talk even after they announced late last year that they ditched an agreement to let customers roam between both companies' WiMax networks. Meanwhile, cable companies like Comcast are making a push to enter the wireless business to fend off competition from telecom giants such as Verizon Communications These companies have been snatching traditional cable customers by offering bundled services including high-speed Internet, cell-phone, land-line and video. (Reporting by Anupreeta Das and Duncan Martell in San Francisco and Yinka Adegoke and Sinead Carew in New York; Editing by Gary Hill and Lincoln Feast) http://www.reuters.com/article/techn...28498320080326  Google Offers New Plan for the Airwaves Google Inc on Monday unveiled plans for a new generation of wireless devices to operate on soon-to-be-vacant television airwaves, and sought to alleviate fears that this might interfere with TV broadcasts or wireless microphones. In comments filed with the Federal Communications Commission, the Internet leader outlined plans for low-power devices that use local wireless airwaves to access the "white space" between television channels. A Google executive called the plan "Wi-Fi 2.0 or Wi-Fi on steroids." "The airwaves can provide huge economic and social gains if used more efficiently ...," Google said in the comments. Rick Whitt, Google's Washington telecom and media counsel, said this class of Wi-Fi devices could eventually offer data transmission speeds of billions of bits per second -- far faster than the millions of bits per second available on most current broadband networks. Consumers could watch movies on wireless devices and do other things that are currently difficult on slower networks. The white-space airwaves could become available in February 2009, when TV broadcasters switch from analog to digital signals. Whitt said he expects devices using white-space spectrum could be available by the end of 2009. Shares of Google surged $27.36, or 6.3 percent, to $460.91 amid a sharp rise in U.S. stock markets. The Nasdaq composite index was up 3.3 percent. Google sees the white-space spectrum as a natural place to operate a new class of phones and wireless devices based on Android, Google's software that a variety of major equipment makers plan to use to build Internet-ready phones. The Silicon Valley company also said that, in general, it stands to benefit whenever consumers have easier access to the Internet. Google's primary business is selling online ads as people perform Web searches. The FCC filing comes less than two weeks after Bill Gates, co-founder of Google rival Microsoft Corp, urged the agency to free up the white-space spectrum so it could be used to expand access of wireless broadband. Google and Microsoft are part of a coalition of technology companies that has been lobbying the FCC to allow unlicensed use of white-space spectrum. The group also includes Dell Inc, Intel Corp, Hewlett-Packard Co and the north American unit of Philips Electronics. The idea is opposed by U.S. broadcasters and makers of wireless microphones, who fear the devices would cause interference. The FCC currently is testing equipment to see if the white-space spectrum can be used without interfering with television broadcasts. In a compromise designed to mollify some interest groups opposed to expanding use of white-space spectrum, Google proposed a "safe harbor" on channels 36-38 of the freed-up analog TV spectrum for exclusive use by wireless microphones, along with medical telemetry and radio astronomy devices. In effect, no white-space devices could use these channels. Google said "spectrum-sensing technologies" could be used that would automatically check to see whether a channel was open before using it, thereby avoiding interference with other devices. It said such technology is already being used by the U.S. military. Google said the enhancements "will eliminate any remaining legitimate concerns about the merits of using the white space for unlicensed personal/portable devices." Google also said it would provide free technical assistance to other companies seeking to take advantage of white-space airwaves. This would include having Google help to maintain "open geo databases" of local channels for use by any device certified to use the spectrum. A proposal being studied by the FCC would create two categories of users for the airwaves: one for low-power, personal, portable devices, and a second group for fixed commercial operations. (Editing by Tim Dobbyn and John Wallace) http://www.reuters.com/article/ousiv...00918220080324  FCC to Investigate D-Block Auction 9/11 Commission joins the chorus of observers calling the auction results out of key. Carol Pinchefsky The Federal Communications Commission will investigate complaints that a contractor tried to extort potential bidders for a block of the spectrum set aside for emergency responders, and doomed the auction to failure. The auction of the agency's D block of the 700MHz spectrum, reserved at a lower price for emergency responders and private ventures who agree to share it with emergency responders, netted a single $472 million offer from Qualcomm, which was well below the FCC's $1.3 billion reserve price. Several public interest groups, including the 9/11 Commission and members of Congress, have asked the agency to investigate accusations that Cyren Call, a consultant hired to manage the handover of the D-block spectrum, demanded payment from auction participants and discouraged bids. Kevin J. Martin, chairman of the FCC, referred the matter March 21 to FCC Inspector General Kent R. Nilsson. Although anti-collusion laws prevent people, businesses, and other interests involved from discussing the specifics of the auction, organizations like The Public Interest Spectrum Coalition—comprised of several public interest groups including Public Knowledge, U.S. PIRG, Free Press, and the Media Access Project—believe that a failure to meet the reserve price was not merely a problem of logistics. The 9/11 Commission also raised objections to the auction result. In a press release, PISC referred to a letter they sent to the FCC on March 19, 2008. "[W]hile not accusing any party of wrongdoing, the letter asks the FCC to investigate whether discussions between Morgan O'Brien of Cyren Call and possible D Block bidder Frontline Wireless caused Frontline to lose financial backing and scared off other bidders." Cyren Call, the advisor to The Public Safety Spectrum Trust Corporation, manages the public use of the spectrum in the FCC's public-private partnership. In the last few days, allegations that Cyren Call tried to tack on $50 million worth of fees annually in order for the winning bidder to lease the spectrum—on top of the $1.3 billion minimum licensing fee—are either a whispering campaign against the company, fact, or something in between. Representative Edward J. Markey, D-Mass, chairman of the House Subcommittee on Telecommunications and the Internet, also called for an investigation into why the auction failed to meet its reserve price. When asked if the hearing would address alleged interference by Cyren Call in the auction, Jessica Schafer, communications director for Representative Markey, said, "We're looking at several issues all related to this auction. If there are issues about tampering, I assume they would come up." Schafer said, "The point of the hearing is we don't know what the problem was, why we didn't manage to meet the reserve price…. the point of this hearing is we need to figure out what were the concerns of all players. We want to find out what happened here and how we can make it a successful auction." http://www.eweek.com/c/a/Government/...Block-Auction/  Bill Criminalizing WiFi Leeching Shot Down, and Rightly So Eric Bangeman If you use someone else's WiFi signal without permission, you're a thief. That's the conclusion of a bill introduced into the Maryland General Assembly last week. Sponsored by Delegate LeRoy E. Myers, Jr., the legislation would criminalize the unauthorized use of a wireless access point in the state; it has since received an "unfavorable report" by the House Judiciary Committee, which all but dooms its prospects of passage. The bill's purpose is to prohibit anyone from accessing a wireless access point "intentionally, willfully, and without authorization." It appears to ban both everyday WiFi leeching and using an open access point for more nefarious activities. And if you live in a Maryland neighborhood with broadband usage caps, it would be illegal to deliberately cause someone to overuse their bandwidth allotment. Violators would be subject to fines of up to $1,000 and three years in jail, unless they tried to hack into a password-protected system or used their unauthorized access for mischief. Then the penalties could climb to $10,000 and 10 years in prison. With 802.11b/g/n technology becoming widespread over the past several years, there has been a corresponding rise in cases of people being arrested for using open access points without permission. One of the first cases came in 2005 when a Florida man was convicted of accessing a computer network without authorization. He was arrested and charged with the third-degree felony after the WAP's owner discovered him surfing in an SUV outside of their home. There have been other cases, including an Illinois man who pleaded guilty to remotely accessing a computer system without permission in 2006 and a Michigan man who parked his car in front of a café and used its free WiFi service—without even ordering so much as a latte. When combined, it's a troubling trend of law enforcement and politicians overreacting to what is generally a harmless activity. In the case of Delegate Myers, the legislation was prompted by his neighbor's use of Myer's WiFi connection without permission, according to Maryland newspaper The Herald-Mail. Apparently, Myers hadn't bothered to password-protect his WAP or use rudimentary security precautions. The proposal of the bill suggests that Myers would rather see this legislated than learn how to set up wireless security. Sanity appears to reign in Maryland, however. The Maryland public defender's office is opposing the bill, noting the widespread availability of WiFi networks. "A technically unsophisticated user, such as a visiting parent, or simply a houseguest unfamiliar with the home's Internet could and probably would choose the first available network," the office noted in a filing. The public defender makes the obvious point (one that seems to have escaped Myers) that those wanting to prevent unauthorized access should enable routers' built-in security functions. It's so easy that there's no excuse for not doing it. Of course, some people don't mind sharing their WiFi connections. In a piece I did earlier this year on the ethics of using unprotected wireless access points, I mentioned a friend who left his WAP unsecured as a public service. If people don't bother to protect their networks, there's no way of telling whether or not they want others to use it. Using an open WAP to cause harm should be punished in the same way as other nefarious hacking activities, using one to check e-mail, surf the 'Net, or read RSS should not be punished at all. Thankfully, the Maryland House Judiciary Committee appears to have more common sense than Del. Leroy Myers. That said, we probably haven't see the last of such bills. http://arstechnica.com/news.ars/post...ightly-so.html  Hazards of Wifi Dale Dougherty Our town, Sebastopol, had passed a resolution in November to permit a local Internet provider to provide public wireless access. This week, fourteen people showed up at a City Council meeting to make the claim that wireless caused health problems in general and to them specifically. These emotional pleas made the Council rescind its previous resolution. So, a few people in this town strongly believe a wide variety of problems are caused by low frequency electromagnetic radiation (EMF). Some label the problem as "electromagnetic hypersensitivity" or EHS. Here's the Wikipedia entry on " Electrical Sensitivity." It reports that the World Health Organization found that "there is no scientific basis for the belief that EHS is caused by exposure to electromagnetic fields." An online petition collected 235 "signatures" opposed to public Wifi in Sebastopol. The resolution reads: "The convenience of this technology does not warrant the increase in radiation and the potential risks to the health of our community." Here's a typical comment from someone signing the petition: I have had health challenges, and my body cannot handle wifi...it gives me headaches and makes me very sick. I would be unable to go to the store, shop. I have enough problems being limited in my travels, it is outrageous that a place so environmentally conscious would create this in our/my hometown. In Europe they are much more advanced than us, and there wifi is not allowed in cities in the European commonwealth. The person organizing the petition believes that people don't understand the harm that electromagnetic radiation and basic electricity is doing to them. On a local bulletin board, the opponents cite bioinitiative.org. One person writes: We are urged us to switch from regular incandescent light bulbs to compact fluorescent (CFL) light bulbs, to save energy. However, there is a very good reason NOT to use CFL bulbs. They create electromagnetic frequencies proven to be extremely detrimental to human health. Others write about living without electricity, except for the brief period they are using their computer to write messages in support of the petition. One can see the fear spreading. Science should be a way to dispel such fears but it is clear with this group of people that science cannot be trusted. They put forth the idea that science should be able to prove that there is no harm and therefore eliminate any risk, and without such proof, we should not move forward. They use this logic to recommend a "precautionary" approach, which is their keyword for a "know-nothing, do-nothing" approach. Yet another person writes: Research is increasingly showing a correlation between adverse health symptoms and emf radiation exposure. Local and national governmental bodies in other western countries are paying attention and are beginning to legislate limits to exposure to wi-fi radiation by prohibiting it in certain locations. The trend towards increasing international concern is clear. Why are we so sanguine in this country? Of course, the research is not specified. I can't find much about governments banning wifi except a college in Ontario and a European directive on radiation that threatens to eliminate MRI scans. The article "Wifi Woo" in Junkscience.blogspot.com is interesting. The effect of the resolution would have been to add a few wireless access points downtown. There are already several hundred in private homes and businesses in town. The same people who oppose public wifi still walk along streets and into buildings where they are invisibly bathing in wifi. Will this small group of people now demand that we outlaw wireless in public areas, just to accommodate their fears? Now, I don't know that wireless (or electricity) is without harm. I can read the research that does exist and learn more -- if I have the time and reason to do so. However, I do not like the smell of fear, and when people justify actions based on their own fears, I become suspicious that the concern is unwarranted. If it wasn't wifi, it would be flouride. Something is needed to affix to their anxiety. I can only be glad that they weren't alive when the city decided on electrification a century ago. I plan to write an editorial for our local paper. I'd appreciate hearing from you on this issue if it has come up in your community. http://radar.oreilly.com/archives/20...s-of-wifi.html  Analysis: Patent Reform Bill Unable to Clean up Patent Mess Timothy B. Lee Fixing serious flaws Last September, the House of Representatives approved the Patent Reform Act of 2007, legislation that would make important changes to America's patent system. With the legislation being fiercely debated behind closed doors in the Senate, Ars takes a closer look at the legislation's provisions, the major players in the debate, and the legislation's prospects for curing what ails the American patent system. There are formidable forces arrayed on both sides of the patent debate. On one side are major technology firms who are concerned that the explosion of dubious patent litigation threatens their bottom line. Their interest has been piqued by recent eye-popping awards to patent trolls. These companies want to make it more difficult for patent holders to extract large payouts from deep-pocketed firms. But at the same time, most hold large patent portfolios of their own, and are wary of changes that could cut too deeply into their licensing revenues. On the other side are a variety of interest groups who benefit from the current patent system and are wary of changes that might reduce the profits of patent holders. These include the pharmaceutical industry, which feels well-served by existing patent rules. It also includes the patent bar, patent examiners, and other groups that are invested in the current process. Despite the heated rhetoric on both sides, it is unclear if the legislation will do much to fix the most serious flaws in the patent system. A series of appeals court rulings in the 1990s greatly expanded patentable subject matter, making patents on software, business methods, and other abstract concepts unambiguously legal for the first time. The result has been a flood of patents of broad scope and dubious quality. With one very minor exception, none of the proposals being debated on the Hill would address these changes. As a result, it may be hard for advocates for fundamental reform of the patent system to get too excited about this year's debates on the Hill. Although the legislation includes provisions that are likely to moderately reduce the toll that patents take on high-tech innovation, none of the proposals address the fundamental problems that have cropped up in recent years. Opponents of software patents, in particular, will find the provisions of the Patent Reform Act underwhelming. Their best hope is that the Supreme Court tackles the issue in the coming years. If that doesn't happen, then they will likely need to wait for the situation to deteriorate further before there will be sufficient political will for serious reforms. Damage control Probably the most important changes under consideration are reforms that would reduce the size of damages that could be awarded to successful plaintiffs in patent lawsuits. Two features of present patent laws have contributed to the astonishing size of recent damage awards. One is that when a patent covers one component of a complex product, courts have sometimes awarded damages based on the value of the entire product, even if the patent covers only a small aspect of that product. The other is the ability to win treble damages if patent infringement is found to be "willful." Both of these provisions increase the potential payoff to patent holders, encouraging more patenting and more patent litigation. On the issue of apportionment of damages, both last fall's House legislation and the pending Senate bill dictate that when a patent covers only a portion of an invention and an appropriate royalty cannot be computed from existing licensing agreements, that damages should be calculated based on "the economic value of the infringement attributable to the claimed invention's specific contribution over the prior art." Advocates hope that this provision will prevent the holder of a patent on one part of a complex system from holding the entire system ransom. Under patent law, infringement damages can be trebled if the court finds that infringement was done willfully. But critics charge that this rule causes many firms—especially in the software industry—to avoid looking at patents at all out of fear of heightened liability. Recent court decisions have reduced this problem somewhat, but both bills would go further by limiting findings of willful infringement to cases where the infringer had received specific written notice from the patentee, the infringer intentionally copied from the patent, or the infringer continued to infringe after losing in court. This would go a long way toward ensuring that software firms could conduct patent searches without fear of heightened liability. Procedural reforms The legislation would make a variety of changes to patent procedures that would be a big deal for patent lawyers, but may not have significant effects outside the patent bar. Possibly the most important change would be the creation of a new system for challenging patents after they've been granted. The patent office has had a limited reexamination process since 1981, but it has enjoyed broad discretion regarding the patents it chose to review. The Patent Reform Act would create a new "post-grant review" process that can be initiated by third parties. This process could provide a new avenue for striking down bad patents without the need for full-blown patent litigation. Probably the most discussed procedural change is the switch from a first-to-invent to a first-to-file rule for granting patents. In most countries, the first person to file a patent application generally receives the patent, unless it can be shown that he copied the idea from another applicant. In contrast, the United States grants the patent to the first person to have developed the invention claimed in the patent, even if she wasn't the first person to file for the patent. This can cause administrative headaches for the patent office because it must sometimes conduct elaborate investigations to ascertain who was the true first inventor (although such "interference" proceedings occur for only a small fraction of patent applications). The Patent Reform Act would, for the first time, institute a first-to-file rule for granting patents, bringing the US into line with the rest of the world. Another major procedural reform relates to disclosure. Traditionally, the patent application process has been secret, with only the applicant and Patent Office officials having access to pending applications. In 1999, Congress for the first time required disclosure of pending patent application 18 months after they were filed. But this requirement had an important limitation: it applied only to patents that were simultaneously being sought overseas, where such disclosures are common. The House and Senate bills drop the rule about foreign filing and require that, in most cases, applications should be disclosed within 18 months. Trolls love purple A final key procedural reform relates to venue shopping. Certain jurisdictions—especially the Eastern District of Texas—have become notorious for being sympathetic to plaintiffs in patent cases. As a result, a inordinate number of patent cases have found their way to East Texas courtrooms. The Patent Reform Act would rein in this abuse of jurisdictional rules by restricting plaintiffs' options when filing a patent lawsuit. While the House and Senate versions differ slightly, both would require that patent litigation occur in a location where either the plaintiff or the defendant have a significant presence. The legislation does almost nothing to rein in the Federal Circuit's increasingly permissive attitude toward patents on abstract concepts like software, business methods, and mental processes. Only one provision of the Patent Reform Act addresses this issue: the House bill includes a prohibition on patents for tax planning methods. Evaluating the Patent Reform Act To help us understand the implications of the Patent Reform Act, Ars talked to James Bessen, co-author of a recent book on the patent system. Bessen told Ars that the most important changes currently under consideration on the Hill are the post-grant review process, the apportionment of damages, and willful infringement. But he argued that none of these changes will address the serious flaws that plague the patent system. Rather, their most important effect will be the signal it sends that the IT industry is finally taking patent issues seriously and organizing to tackle the problem in Congress. He predicted that Congress will need to revisit the issue in the coming years as patent problems continue to mount. Bessen had three major suggestions to offer to Congress once it gets serious about fundamental reform. First, there needs to be much stronger limits on patenting of abstract ideas, including software and business methods. Bessen argued that narrowly construing patent scopes will significantly improve the situation by preventing patent holders from using a single, broad patent to harass entire sectors of the technology industry. Second, Bessen said that dramatically increasing maintenance fees would give patent holders a strong incentive to let unimportant patents lapse. That would reduce the total number of patents in effect and make it easier for potential innovators to review the remaining patents for possible infringement. Finally, Bessen told Ars that the law needs to have protections for inadvertent infringers. Under current law, in most cases there are no legal protections available to a firm that independently develops a technology that is covered by an existing patent. An independent invention defense to patent infringement would be the strongest possible reform in this direction. A less ambitious approach would be to reduce damages in cases where independent invention can be demonstrated. Bessen was pessimistic that any of these reforms would prove politically feasible in the short term. The interest groups that now profit from the expansion of patent scope and the resulting litigation won't accept such changes without a fight. On the other hand, as the problems with the patent system become more and more obvious, the momentum for reform may grow to the point where serious reforms become possible. Prospects for passage Indeed, it remains to be seen if even the modest reforms of the Patent Reform Act will survive the Congressional sausage factory. The legislation has the backing of the IT industry, but it is opposed by the pharmaceutical industry, the patent bar, and some labor unions. Negotiations have dragged on for months, as these competing interest groups have spent millions on lobbying and public relations campaigns. Earlier this month, supporters of the legislation were predicting an imminent compromise on the bill's key provisions, but no announcement has been forthcoming and insiders are now predicting that the legislation's backers will be lucky to see a vote in April. The uphill climb faced by even this modest patent reform legislation suggests that momentum for serious reform is unlikely to originate on Capitol Hill. Two major developments could bring about serious reform. One would be continued interest in the subject from the Supreme Court, which has already heard several patent cases and will rule on another case this term. In the oral arguments in last year's AT&T v. Microsoft case, Justices Breyer and Stevens both raised questions about the patentability of software. The End Software Patents Project is focusing much of its efforts on laying the groundwork for a challenge to the patentability of software should an appropriate case come before the Supreme Court. The other development that could add momentum to patent reform efforts is if abusive patent litigation continues to spiral out of control. Thus far, the coalition for patent reform has been somewhat disorganized, as many technology firms have been split between their desire for protection against patent trolls and their desire to collect royalties on their own patents. But a few more nine-figure jackpots for patent trolls could help focus their minds. As the costs of the patent system continue to soar, Silicon Valley's heavyweights may become more sympathetic to more sweeping reforms, and more willing to put more effort into making them happen. http://arstechnica.com/articles/cult...atent-mess.ars  IP Hypocrisy: US Likes WTO Rulings Only When it Wins Nate Anderson The US likes to call out other countries for not being tough enough with intellectual property rules, and it tosses countries like Russia, China, and even Israel onto "watch lists" and "priority watch lists" in an attempt to force changes. But the US comes in for its share of IP-related criticism from other countries both small and large, too. When it happens, though, we're not nearly so quick to change our ways. US hauls China before WTO again: less counterfeiting, piracy please Two ongoing cases illustrate the point. First, the European Union is pushing for the US to change a pair of rules that it calls "long-standing trade irritants." Despite World Trade Organization rulings against it, the US has not yet corrected either case for a period of several years. Ambassador John Bruton, who represents the EU in the US, said in a statement late last week that he wants to see the matters resolved. "As the stakes continue to grow in the intellectual property arena, the US should not weaken its voice in the debate by ignoring treaty obligations and WTO decisions," Bruton said. "American delay on fixing the 'Irish Music' and 'Havana Club' cases diminish the arguments that both the US and EU countries have against China and other countries that continue to tolerate widespread intellectual property rights infringement." The so-called "Irish Music" dispute concerns the portion of US copyright law that lets restaurants and shops play broadcast music without compensating the copyright holders. As previous coverage of this issue shows, Europe takes a fairly hard-line stance on these payments; a UK car repair chain was even targeted by collecting societies because its mechanics played their radios loud enough that customers could hear them. The WTO ruled against the US in 2000, and the US responded not by changing its laws, but by making payments directly to European collecting societies. Now, those payments have lapsed but the US law remains. The Havana Club issues stems from the long-standing US effort to impose sanctions on Cuba. The US reduced the rights of US companies who owned trademarks "which previously belonged to a Cuban national or company expropriated in the course of the Cuban revolution." Such marks, including "Havana Club Rum," were no longer protected in the US, could not be renewed, and could not be enforced. This makes EU companies that have invested in Cuban business less than pleased, especially when they believe that US drink makers were behind the rule change. The US also lost a WTO ruling on the matter and was to have complied by 2005. To date, it has not. The second case concerns Antigua and Barbuda, a small Caribbean country home to all sorts of online vices, including gambling and DRM circumvention. Antigua took the US to the WTO years ago over charges that the US was unfairly criminalizing access to Antiguan gambling websites while still allowing US-based horse racing sites to function. The WTO ruled against the US on several occasions, including a 2007 ruling that found the US had not yet bothered to comply with previous rulings. In retaliation, Antigua has announced a radical plan in an attempt to force its larger neighbor to play ball. The Antiguan government has recently stated that it will allow piracy of US intellectual property such as movies and movies unless the US changes its gambling policy (though this move has yet to be authorized by the WTO). Apparently, it's easy to get hot and bothered when it's industries from your country that claim to be badly affected by rules elsewhere. When it comes to the claims of other countries, though, even claims that have been validated by the WTO, it's much easier to see the complexity of the situation, to spend years arguing those complexities before judges, and to do nothing even when compelled by rulings. This sort of behavior makes it that much harder to assert some kind of moral high ground when China, Russia, and others pick and choose which of their WTO obligations they are going to comply with. http://arstechnica.com/news.ars/post...n-it-wins.html  Wikileaks Releases Over 120 Censored Videos and Photos of the Tibet Uprising Today Wikileaks released over 120 censored photos and videos of the Tibet uprising and has called on bloggers around the world to help drive the footage through the Chinese internet censorship regime -- the so called "Great Firewall of China". The transparency group's move comes as a response to the the Chinese Public Security Bureau's carte-blanche censorship of youtube, the BBC, CNN, the Guardian and other sites carrying video footage of the Tibetan people's recent heroic stand against the inhumane Chinese occupation of Tibet. Wikileaks has also placed the collection in two easy to use archives together with a HTML index page so they may be easily copied, placed on websites, emailed across the internet as attachments and uploaded to peer to peer networks. Censorship, like communism, seems like a reasonable enough idea to begin with. While 'from each according to his ability and to each according to his need' sounds unarguable, the world has learned that these words call forth a power elite to administer them with coercive force. Such elites are quick to define the needs of their own members as paramount. Similarly 'from each mouth according to its ability and to each ear according to its need' seems harmless enough, but history shows that censorship also requires an anointed class to define this "need" and to make violence against those who continue talking. Such power is quickly corrupted. The first ingredient of civil society is the people's right to know, because without such understanding no human being can meaningfully choose to support anything, let alone a political party. Knowledge is the driver of every political process, every constitution, every law and every regulation. The communication of knowledge is without salient analogue. It is living, unique and demands its rightful place at the summit of society. Since knowledge is the creator and regulator of all law, its position beyond law commands due respect. James Madison, Thomas Jefferson and other Enlightenment framers of the US Bill of Rights understood this well when they began the First Amendment's constitutional protections of speech and of the press with 'Congress shall make no law....'. As knowledge flows across the world it is time to sum great freedoms of every nation and not subtract or divide them. Let us then unite in common purpose for the surest way to protect the freedoms of any nation is to protect the freedoms of every nation. http://wikileaks.org/wiki/Wikileaks_...Tibet_uprising  BBC Website 'Unblocked in China' People in China are able to access English language stories on the BBC News website in full, after years of strict control by Beijing. The Communist authorities often block news sites such as the BBC in a policy dubbed the "great firewall of China". But BBC staff working in China now say they are able to access news stories that would have been blocked before. However, the firewall remains in place for Chinese language services on the website and for any links in Chinese. 'Without hindrance' Beijing has never admitted to blocking access to BBC news stories - and there has been no official confirmation that the website has been unblocked. But Chinese users trying to access pages on the site have almost always been redirected to an error message telling them: "The connection was reset." It now appears that this is no longer the case, and access to the site is much easier. Steve Herrmann, editor of the BBC News website, says this is a welcome development. "We want BBC News to be as accessible in China as anywhere else in the world," he said. "We will endeavour to continue working with the Chinese authorities to improve our access in other areas." Technology experts say such a development would not be possible without the approval of internet service providers - which are under strict supervision by Beijing. Surprised readers Statistics show that traffic to the website from China has been much higher than usual. Typically fewer than 100 people read stories from Chinese computers - but on Tuesday that figure jumped to more than 16,000. And comments have been flooding in to BBC forums from all over China. Ross Brown in Qingdao, Shandong province, wrote: "We were just discussing with some of our Chinese colleagues about the fact BBC website was blocked, went on to show them and we see this latest news. Excellent news." Many of the comments came from readers of the website who have spent years accessing the stories by linking their computers to others based outside of China. Tibet difficulties The Chinese authorities had promised to give foreign journalists more freedom in the run-up to this summer's Olympic Games. But analysts say that recent outbreaks of unrest in Tibet have made this promise more difficult for Beijing to uphold. The BBC and other media organisations still find reporting from Tibet very difficult - foreign journalists were refused permission to enter the region during the recent protests. The websites of UK newspapers the Times and Guardian - as well as video-sharing site YouTube - were blocked or partially blocked during the unrest. This week the Chinese government has arranged a trip for foreign media organisations to Tibet - but the BBC's request to be included was rejected. Although no official ban has ever been announced, the BBC News website has been blocked for almost a decade. The Chinese language website has been blocked since its launch in 1999. Are you in China? What is your reaction to this story? Is this your first time reading the BBC News website? Name: Email address: Town and Country: Phone number (optional): Comments: http://news.bbc.co.uk/go/pr/fr/-/2/h...ic/7312240.stm  Germany's Top Court Curtails Disputed Data Storage Law Critics feel the law would make huge amounts of data vulnerable to misuse In a blow to Berlin's efforts to boost anti-terrorism measures, Germany's highest court on Wednesday, March 19 blocked parts of a sweeping data-collection law that had prompted large protests by civil liberties Germany's constitutional court on Wednesday severely curbed parts of a wide-reaching and highly controversial data collection law that requires telecom companies to store telephone and Internet data for up to six months, dealing a setback to government efforts to fight terrorism. The law which went into effect in January gave the federal government broad access to data including e-mail addresses, length of call and numbers dialed and in the case of mobile phones, the location calls are made from. Fears of data misuse The court in Karlsruhe on Wednesday declared that parts of the law were unconstitutional pending review. It ruled that the data may continue to be stored by telecom companies but that details may only be transferred to investigators in the event of inquires into serious crime and only with a warrant. In cases of less serious crime, investigating authorities may only access the data subject to a final decision by the top court, judges said. The legislation is part of an EU directive formulated in response to bomb attacks in Madrid and London in past years. Demonstrators in Hamburg staged a mock funeral marking the "Death of Privacy" It has sparked large protests by German civil liberties campaigners, privacy advocates and opposition politicians in recent months who argue it would make huge amounts of personal data vulnerable to misuse and place everybody under general suspicion of being a terrorist. Critics are also concerned that the data may be handed over to foreign intelligence agencies and could be used by entertainment companies to pursue and prosecute people who illegally download music and videos. On Dec 31, over 30,000 opponents of the law filed a class-action suit, the biggest of its kind in Germany, against the bill. "A serious blow to the government" Wednesday's decision was the latest in a series of rulings against tighter security measures by Chancellor Angela Merkel's government. Last month, the constitutional court established a new "fundamental right" for German citizens to surveillance-free computer systems. In recent years, the court has set limits on bugging homes, trawling electronic databases and monitoring computers of suspected criminals. The decision was hailed by opposition politicians and privacy advocates. "The grand coalition should finally draw the lesson of these verdicts and stop crossing the limits of constitutionality on citizen rights," said Claudia Roth of the opposition Greens party. "This is a serious blow to the federal justice ministry which until recently has been trying to play down the violation of basic rights of citizens by the data collection bill," said Joerg van Essen from the opposition free-market liberal Free Democratic Party (FDP). http://www.dw-world.de/dw/article/0,...203058,00.html  China's Battle to Police the Web Web users in China are able to view the BBC News website for the first time in years. So how does the so-called great firewall of China work? Darren Waters It is not clear why China's net population, the world's largest, is suddenly able to view the BBC News website after years of being blocked. Nor is it clear how long the access will continue. But what is certain is that China's authorities have dynamic control of what their citizens can and cannot access. Most countries that block or filter the internet do so on a site-by-site basis. For example, Pakistan blocked YouTube recently by telling Internet Service Providers (ISPs) in the country to redirect traffic whenever someone typed in the address for the popular video sharing site. By deliberately rewriting the net address books inside Pakistan, authorities were able to redirect traffic. But this is a blunt method of filtering and relies on authorities to actively track websites it wants to ban. China does not block content or web pages in this way. Instead the technology deployed by the Chinese government, called Golden Shield, scans data flowing across its section of the net for banned words or web addresses. There are five gateways which connect China to the internet and the filtering happens as data is passed through those ports. When the filtering system spots a banned term it sends instructions to the source server and destination PC to stop the flow of data. Amnesty International has accused net giant Cisco and Sun Microsystems of actively assisting with the development of censorship and surveillance systems in the country. Both firms have rejected the accusation and have said the equipment they sell to China is no different from products sold in other countries. The dynamic nature of filtering in China gives the government more control over content and means the authorities can react to news events. Oppressive regimes It has been called "just-in-time filtering" and is being employed more widely around the world in oppressive regimes. It allows authorities to block access to information around key events like elections, demonstrations etc. Security researchers believe this form of filtering was employed on YouTube in China during the recent unrest in Tibet. In January last year, President Hu Jintao reportedly ordered officials to regulate the internet better and "purify the online environment" ensuring that online information is "healthy" and "ethically inspiring". This was followed by a new wave of censoring certain websites, blogs and online articles. But there have been well-documented ways to by-pass China's firewall. One method involves connecting to a friendly computer outside China and using it as a proxy, to access websites that are banned. China cannot block every computer outside its borders so this method has proved popular with citizens wanting unfettered access to the net. The problem has been in informing users in China of the IP address, the unique number of every device online, of the machines willing to act as proxy servers. E-mail has been one method to alert people; however China is believed to have 30,000 people who routinely scan e-mails for this kind of information. Organisations in the US and elsewhere have been working on technology to make this process of finding friendly computers more easily. The University of Toronto's Citizen Lab has developed software called psiphon which acts as a tunnel through the firewall. Psiphon works through social networks. A net user in an uncensored country can download the program to their computer, which transforms it into an access point. They can then give contacts in censored countries a unique web address, login and password, which enables the restricted users to browse the web freely through an encrypted connection to the proxy server. Its creators say the system provides strong protection against "electronic eavesdropping" because censors or ISPs can see only that end users are connected to another computer and not view the sites that are being visited. China Wide Web? But even without specialised software, some China net users are able to crack the firewall. A report released last year by US researchers showed that the firewall was more porous than previously thought. It found that the firewall often failed to block what the Chinese government finds objectionable, and was least effective when lots of Chinese web users were online. But even when no technology is used to filter or ban, China's net citizens are not getting unfettered access to the web. Western companies like Google and Microsoft have been criticised for launching services which effectively self-censor. A search request on Google in China will not bring back the same results as it would in the US, with many websites removed from the list of returned items. Microsoft's blog service in China does not allow people to use words such as democracy, freedom and human rights. Many observers now feel that China is not really connected to the web at all. Instead, net users in the country experience a China Wide Web and not the World Wide Web. http://news.bbc.co.uk/go/pr/fr/-/1/h...gy/7312746.stm  CNet Networks to Cut 120 Jobs AP CNet Networks Inc. says it is laying off 120 employees as part of an effort to streamline the online media company while generating more content for its news and entertainment sites. All the layoffs -- about 4.4 percent of CNet's work force -- will involve employees in the U.S., according to a document CNet filed Wednesday with the Securities and Exchange Commission. CNet's suite of popular Web sites commands a huge worldwide audience, but its investors have long complained the company's profits haven't kept pace with the growth of Internet advertising. The company indicated in the filing that the layoffs would be effective immediately and cost at least $3.8 million in severance pay, outplacement and other expenses. Along with the technology news site CNet.com, the San Francisco-based company operates News.com, TV.com, GameSpot.com, Chow.com and BNet.com. It said in a February filing that, as of Dec. 31, it employed about 2,700 people worldwide. CNet shares rose 6 cents Wednesday to close at $7.25. http://ap.google.com/article/ALeqM5j...8JZIQD8VLFAS00  Motorola, Under Pressure, to Split in Two Cellphone unit separating after push for shake-up Ashley Heher Motorola Inc., after months of agitation from frustrated investors, announced plans yesterday to separate its struggling handset business from other operations and form two separate publicly traded companies. The cellphone maker has been under pressure from billionaire investor Carl Icahn for changes meant to revitalize its cellphone business, which has seen its sales and stock price plummet after the company failed to find a second act to the once-popular Razr phone. Motorola said the handset business will operate separately from a company that includes its home and networks business and sells TV set-top boxes and modems, and from the enterprise that sells computing and communications equipment to businesses. "Our priorities have not changed," chief executive Greg Brown said in a statement. "We remain committed to improving the performance of our Mobile Devices business by delivering compelling products that meet the needs of customers and consumers around the world." Motorola said it hopes the transaction will be tax-free, allowing shareholders to own stock in both new companies. If the deal is approved, the two units would be separated in 2009. Brown said Motorola will search for a new chief executive of the Mobile Device business as it works to regain favour with customers and its No. 2 position in the cellphone market. Motorola lost that spot last year to rival Samsung Electronics Co. Finland's Nokia Corp. is the industry leader. Yesterday's announcement was just the latest shake-up at Motorola, which rode the success of the iconic Razr phone from 2005 to 2006, but has stumbled since amid stiff competition. Last year, the company pulled back from developing markets, cut 7,500 jobs and CEO Ed Zander resigned. A flock of executives has left the company this year, and more cuts and changes are likely as the new management team scrambles to retain control in the face of a revived threat from Icahn. Icahn, who has been steadily increasing his Motorola position, disclosed in a filing this month that he now owns 142.4 million shares, or 6.3 per cent – up from five per cent a month ago. Yesterday's announcement came two days after Icahn sued Motorola, seeking documents about its executives and its cellphone business. Icahn plans to use the material in his battle to win four seats on the company's board, his second proxy fight in two years with Motorola. He rejected a concessionary offer of two seats from the company. http://www.thestar.com/Business/article/356911  Windows XP: Going, Going ... Gone? David DeJean The approaching death of Windows XP may upset you, but it shouldn't come as a surprise. Microsoft Corp.'s product life-cycle guidelines have foretold the fate of XP since 2001. In fact, Microsoft has been killing off one version of a product as it is replaced with another for years now. But this time around, the approaching demise of XP is getting more attention than, say, the final passing of Windows 2000. Why? For a couple of reasons: XP is the most widely used operating system on the planet, and its long-delayed successor, Windows Vista, is not proving to be universally popular. The companies that make up the enterprise market for Windows are dragging their feet about upgrading, and on the consumer side there are signs of a rebellion against Vista. Microsoft has already made changes in its timetables. Last year, the company extended the sales life cycle -- the time during which PC manufacturers and system builders could sell computers with XP installed -- to June 30, 2008. It will stop selling XP altogether on Jan. 31, 2009. And it extended the mainstream support period for XP to April 14, 2009, in an effort to reassure customers made nervous by the long delays in shipping Vista. The result of all this tweaking is that Microsoft will stop selling XP long before it stops supporting it. You may be able to run XP for as long as you want, but before too long you may not be able to buy a legitimate copy of XP to run. So will there be any way to get a copy of XP after June 30? If you want to continue using XP, what problems will you face? If you buy a PC with Vista installed and decide you want XP instead, what are your options? The product life-cycle guidelines Microsoft's product life-cycle guidelines grew out of two sets of needs: Microsoft's need to make a profit, and its customers' (particularly enterprise customers) needs for some certainty about the products they were committing to. The policy was an attempt at transparency, a promise that new products would be supported for a definite period and that as they aged Microsoft wouldn't just abandon them. Instead, the company would withdraw support in a series of scheduled steps that corresponded to the pace of technological change, allowing customers time to transition to newer products. (The guidelines apply to all Microsoft products, not just operating systems.) The problem is that what sounds like a promise to some (particularly enterprise customers) can sound like a threat to others -- particularly consumers. And they're not taking it well. XP timeline June 30, 2008 PC manufacturers stop selling computers with XP installed. Jan. 31, 2009 Microsoft stops selling XP altogether. April 14, 2009 Mainstream support (free live support and warranty support) ends. Free maintenance is limited to security fixes. April 8, 2014 All support for XP ends. This incipient consumer rebellion is a relatively new phenomenon, even in the short history of PCs. For most of the '90s, Microsoft couldn't bring out new products fast enough to satisfy customers. Computing technology was exploding, and Windows exploded along with it, from Windows 3.1 to Windows 95 to Windows 98 to Windows 98 Second Edition to Windows Millennium Edition. PC sales boomed and Windows users raced to upgrade to the latest version. But that binge left Microsoft with a huge hangover. As the new decade started, it was supporting a tangle of versions and upgrades. Then the Internet bubble burst and PC sales slowed. New products like Windows ME weren't as well received as the older ones. Microsoft needed to reduce its support liabilities and create a profit plan. The product life-cycle guidelines were the solution. The three phases of support First laid out in 2001 and revised in 2002 and 2004, the guidelines defined a three-phase life span and created a division between business desktop software and consumer desktop software. (In the beginning, it was easier to distinguish between business products based on the NT kernel -- like Windows NT and Windows 2000 -- and consumer products that ran on top of DOS, like Windows 98 and ME.) • Mainstream phase: In the prime of a product's life, Microsoft provides both free and paid live support, support for warranty claims and online self-help support information. Software support and maintenance is extensive and free, with downloadable fixes and updates, service packs and freely available support for problem incidents, as well as requests for design changes and new features. Business customers may pay for additional support. • Extended phase: Free live support and warranty support end, and free maintenance of consumer products is limited to security fixes. Self-help support information remains available online. Pay-per-incident live support remains available. Software patches and updates continue for business desktop software. • End of life: Online support information is removed. Patches and updates cease. The product is history. These phases were set in a schedule with definite dates and durations. Business products would be supported for 10 years -- mainstream support for five years, extended support for another five. Consumer products would get five years of mainstream support, but no extended support. But there are two other factors in a product's life cycle -- service packs and the availability of a new version of the product: • Service packs have a life cycle of their own. Support for each service pack ends 24 months after the next service pack release (support for Windows XP Home SP1 support, for example, ended in 2006, two years after the release of SP2 in 2004) or at the end of the product's support life cycle, whichever comes first. • When it looked like mainstream support for Windows XP might run out before the next version of Windows made it to market, Microsoft amended the support life cycle policy to promise that mainstream support would last for either five years or for two years after a successor version is released, whichever period is longer. While the product life-cycle guidelines set very definite limits on product life spans, Microsoft has shown a willingness to move the goal posts when it gets enough pressure. When Windows XP shipped in December 2001, it was slated to be in mainstream support until December 2006. Microsoft's internal problems with getting Vista out the door finally forced the company to extend the mainstream period for XP out to April 2009, and to make some other accommodations, like eliminating the distinction between business and consumer versions, so that XP Home will have an extended support phase just like XP Pro. The result is that next year, on April 14, 2009, Microsoft will end mainstream support for XP, and five years later, on April 8, 2014, it will stop supporting XP at all. The other life cycle But even before that, XP faces a major event in an entirely different life cycle, one that Microsoft has said very little about -- the sales life cycle. The key dates for sales come much sooner than 2009 or 2014. In fact, in only a few weeks, on June 30, 2008, Microsoft will stop selling XP through its retail and reseller channels (the resellers are big manufacturers like Dell Inc. and Hewlett-Packard Co. that sell PCs with Windows preinstalled). System builders, the "white box" retailers who build PCs to order, will be given another seven months, but on Jan. 31, 2009, a couple of months before XP exits mainstream support, Microsoft will stop selling XP altogether (except for a version sold in some less-developed countries and a special arrangement for XP Home in China). At least that's the current information. It could change. It has before. What sounds like a promise to some can sound like a threat to others -- particularly consumers. And they're not taking it well. In the past, the company has generally kept the previous version of Windows on the market for two years or so, past the introduction of a new version. That was apparently the plan for XP. When Vista finally shipped to enterprise customers in late 2006, the on-sale dates for XP were reset to January 2009. But the new operating system didn't capture the popular imagination quite the way Microsoft had planned. Vista's heavy demands for hardware, its rocky support for applications and peripherals, and its draconian security features have left consumers less than enthusiastic. (InfoWorld.com, for example, has collected more than 100,000 signatures on a Save Windows XP petition.) Enterprise customers have also been slower to move to Vista than to previous versions of Windows. A Microsoft reseller, CDW Corp., reported this January the results of a poll that found that a year after its release, fewer than half of businesses were using or evaluating Vista. Big resellers, the PC manufacturers who preinstall Windows on their products, initially switched from XP to Vista when the consumer versions of the operating systems shipped in January 2007. But by April, Dell, Lenovo, and HP were once again selling machines with XP installed. An April 4 post on Dell's Web site announced the company's intention to sell XP on certain systems "until later this summer." Nearly a year later, the company is still selling XP systems. In September 2007, Microsoft agreed to a six-month extension of XP's on-sale dates, along with license provisions for Vista's business editions that grant buyers the right to downgrade to XP. All this leaves Microsoft in an unfamiliar position. Its major customers -- the resellers, system builders and enterprise licensees -- and a vocal part of the Windows user base all appear to be reluctant users of Vista. None of this means that Microsoft is likely to grant XP another stay of execution. But it does mean we're going to be in for an interesting few weeks leading up to June 30. What happens after June 30? XP won't suddenly disappear, though. It will take some time for PCs loaded with XP to move from factories to warehouses to sellers to buyers. Shrink-wrapped FPP versions of the various editions of XP will also remain on sale until supplies are exhausted. And even after June 30, there will still be two ways to obtain XP until Jan. 31, 2009. The easiest way will be to buy a new PC with XP installed from a white box system builder. It will, of course, be a reseller's version of the operating system (white box builders tend to use the same reseller versions as the larger vendors), which is tied to the PC it's installed on and can't be transferred to another computer. Or you can buy a new PC with a reseller version of Vista Business or Vista Ultimate installed and downgrade to XP Pro (download PDF). There are enough pain points in this process that you won't want to undertake it lightly. Although you may have the right to downgrade, the maker of your PC isn't obliged to supply an XP install disk. If it's important to you, check before you buy. And although you can reinstall Vista later on, you have to do it from the installation files or media you got with the machine, so don't wipe those out by accident. You won't be able to activate your new XP install with its previously used product key across the Internet, either. A query to Microsoft on this last point produced the following clarification: "A customer who wishes to downgrade to XP should be able to do so using their original XP disc and original XP product key. That customer may have to call [Microsoft customer service] to get an override in case their hardware changed and their hardware ID went out of tolerance. Activation is governed by the RIT/ROT count. 'RIT' equals the number of activations on the single machine. 'ROT' equals the number of activations [of that product key] on different machines. So if the customer activated the key more than the RIT limit or if he changed the hardware, only then would they have to call a Product Activation call center." Does that make everything clearer? Support goes on Although the sales life cycle starts to wind down on June 30, you can keep on using XP for as long as you want to. You might want to run XP until the next version of Windows (currently called Windows 7) comes out; it's expected in 2010. Or you might want to give some other operating system a little more time to mature. Perhaps you think that Ubuntu Linux is just a couple of versions away from real usability. In both these cases, time is on your side. There won't be any changes in XP support until April 14, 2009, when Windows XP Service Pack 2 moves from mainstream support to extended support. Extended support's security fixes should certainly keep you going safely until April 8, 2014, or until Windows 7 actually does ship, whichever comes first. Can You Save XP? InfoWorld is conducting a campaign to rally XP users to demand that XP be kept available. If you want to join that campaign, you'll find these links useful: Save XP.com The "Save XP" petition count update The problem is, there's support and then there's support. The last time Microsoft ended mainstream support for a version of Windows was in June 2005, when it stopped supporting Windows 2000. By the end of 2006, major software vendors had also ended their support for the operating system. New products didn't support Windows 2000, and upgrades of existing Win2K products to new versions weren't available. This lack of upgrades to run on defunct operating systems is a natural result of market forces. Application software makers, just like Microsoft, want to minimize their support costs by supporting their products on as few operating system versions as economically possible, so when an operating system version's percentage of the installed base falls below its potential to contribute to the bottom line, the vendor will cut its support -- and deflect complaints by pointing at Microsoft. XP is certainly much more widely used than Win2K, and it will probably be supported by application vendors for a lot longer as a result. But if you really want to stay with XP, you should be prepared to stay with your current applications as well. There may not be any upgrades. Whether you merely tolerate XP or won't give it up until it's pried from your cold, dead fingers, it will be gone. Finally, there is one more factor that might stretch out the life of XP a bit. Benjamin Gray, an analyst at Forrester Research Inc., predicted last fall that Service Pack 3 for XP, which will ship later this year, may play a part. Big corporate customers are still looking forward to XP SP3, and Gray said he wouldn't be surprised to see Microsoft extend mainstream support for this updated version of the operating system past April 2009 in response to pressure from the enterprise market. If you're clinging to XP because you're waiting for that stability and compatibility, whether in Vista or in the next version of Windows, or just because you're entirely happy with XP and see no reason to change, then the product life-cycle guidelines are your friend. The combination of mainstream and extended support will give you several years of protection. And even if you find in a couple of years that you can't get an XP version of some upgraded application, extended support means that your XP machine still has some life expectancy; you won't have to junk it just because it's become a malware magnet. But if you're holding onto XP because you're just purely mad at Microsoft, or your PC won't run Vista anyway, then you're only buying time. Sooner or later, it's inevitable. Whether you love Vista or hate it, merely tolerate XP or won't give it up until it's pried from your cold, dead fingers, it will be gone. The product life-cycle guidelines say so. http://www.computerworld.com/action/...icleId=9070119  Gone in 2 Minutes: Mac Gets Hacked First in Contest Robert McMillan It may be the quickest $10,000 Charlie Miller ever earned. He took the first of three laptop computers -- and a $10,000 cash prize -- Thursday after breaking into a MacBook Air at the CanSecWest security conference's PWN 2 OWN hacking contest. Show organizers offered a Sony Vaio, Fujitsu U810 and the MacBook as prizes, saying that they could be won by anybody at the show who could find a way to hack into each of them and read the contents of a file on the system, using a previously undisclosed "0day" attack. Nobody was able to hack into the systems on the first day of the contest when contestants were only allowed to attack the computers over the network, but on Thursday the rules were relaxed so that attackers could direct contest organizers using the computers to do things like visit Web sites or open e-mail messages. The MacBook was the only system to be hacked by Thursday, however, the word on the show floor is that the Linux and Vista systems will meet with some serious challenges on Friday. Miller, best known as one of the researchers who first hacked Apple's iPhone last year, didn't take much time. Within 2 minutes, he directed the contest's organizers to visit a Web site that contained his exploit code, which then allowed him to seize control of the computer, as about 20 onlookers cheered him on. He was the first contestant to attempt an attack on any of the systems. Miller was quickly given a nondisclosure agreement to sign and he's not allowed to discuss particulars of his bug until the contest's sponsor, TippingPoint, can notify the vendor. Contest rules state that Miller could only take advantage of software that was preinstalled on the Mac, so the flaw he exploited must have been accessible, or possibly inside, Apple's Safari browser. Last year's contest winner, Dino Dai Zovi, exploited a vulnerability in QuickTime to take home the prize. Dai Zovi, who congratulated Miller after his hack, didn't participate in this year's contest, saying it was time for someone else to win. By late Thursday, Apple engineers were already working on patching the issue, said Aaron Portnoy, a TippingPoint researcher who is one of the contest's judges. Miller's $10,000 payday may sound sweet, but it's not the most Miller has been paid for his work. In 2005, he earned $50,000 for a Linux bug he delivered to an unnamed government agency. Last year's contest winner, Dino Dai Zovi, exploited a vulnerability in QuickTime to take home the prize. Dai Zovi, who congratulated Miller after his hack, didn't participate in this year's contest, saying it was time for someone else to win. Shane Macaulay, who was Dai Zovi's co-winner last year, spent much of Thursday trying to hack into the Fujitsu Vista laptop, at one point rushing back to his Vancouver area home to retrieve a file that he thought might help him hack into the system. But it was all in vain. "It's one thing to find a vulnerability, it's another thing to make working exploit code," said Terri Forslof, TippingPoint's Manager of Security Response. Forslof said that a number of "high quality" researchers have said that they will attempt to hack the machines on Friday, the last day of the conference. She expects both systems to be hacked on Friday, when contest rules will be further eased, and hackers will be able to attack popular third-party software that can be installed on the systems. "I don't think we'll have to take any home," she said. http://security.itworld.com/5013/mac...27/page_1.html  Amazon Takes on Apple with Copy-Protection-Free Music Jefferson Graham The music industry is finally comfortable selling digital music without copy protection, but the huge shift hasn't resulted in dramatically higher sales. Instead, it produced something that major music labels have long sought: a strong No. 2 competitor to Apple. Amazon's (AMZN) MP3 store - which sells only songs without copy protection - has quietly become No. 2 in digital sales since opening nearly six months ago. That's even though Apple (AAPL) dominates digital music with its iTunes Store (the second-largest music retailer in the world, after Wal-Mart) (WMT) and its hugely popular iPod. The push for copy-protection-free music began nearly a year ago, when Apple and major label EMI shocked the industry by announcing a landmark arrangement to sell 150,000 songs without digital rights management (DRM) software. It was the first time a major label had agreed to such terms. Consumers had long complained about DRM, saying it hindered what they could do with their purchases. For instance, a song sold at iTunes with DRM couldn't be played on a Microsoft (MSFT) Zune digital music player. Apple, which claims an 80% share of digital music sales, said consumers would be ecstatic about the EMI deal and that digital sales would greatly increase. CEO Steve Jobs predicted his iTunes catalog would be 50% DRM-free by the end of 2007. But that never happened. Warner (TWX), Sony/BMG (SNE) and Universal all opted to sell their DRM-free music on Amazon instead. "The labels think Apple has too much influence," says Phil Leigh, an analyst at Inside Digital Media. Apple now has 2 million songs from EMI and independent labels available without DRM, out of its 6 million-song catalog. Amazon offers 4.5 million DRM-free songs. Amazon's arrival "removed some of the stranglehold iTunes had on the market," says Ted Cohen, a former EMI Music executive and managing partner of the Tag Strategic consulting firm. Apple originally sold each DRM-free song for a premium, $1.29, compared with 99 cents for a song with copy protection. But Apple was forced to lower the price to 99 cents when Amazon launched its MP3 download store at that price. Pete Baltaxe, Amazon's director of digital music, won't say how many songs Amazon has sold but will say that consumers love the experience. "What we hear a lot is, 'Thank you.' They appreciate that everything is DRM-free and so comprehensive," he says. Apple declined to comment for this story. 'Music is mature' The labels are also offering DRM-free songs at other digital media outlets. Universal is working with Wal-Mart, Rhapsody, Best Buy (BBY) and a handful of smaller retailers. Sony/BMG has a deal with Target (TGT). That hasn't significantly boosted sales. It hasn't hurt them either, although music label executives had argued against selling songs without copy protection, saying such a move would increase piracy. About 239 million digital tracks have been sold this year, according to Nielsen SoundScan. That compares with 189 million at the same time last year, which is not a dramatic jump. (CD sales continue their decline: 74.3 million this year, compared with 89.2 million at the same time in 2007.) That's because "music is mature," says Eric Garland, CEO of BigChampagne, which monitors online piracy. "The growth is in TV shows, movies and gaming." Garland says there is no evidence that download sales will be affected by DRM-free songs. "The music consumer holds all the cards, and they have a list of complaints. They want iTunes to be 100% DRM-free. They want unlimited selection and to have more of a social component to their songs. Having one label without DRM (at iTunes) isn't enough to make an impact," Garland says. Amazon's Baltaxe says the best defense against piracy is a good offense. "Songs sold without DRM, at high quality, with album art, that's the best way to get people to buy music instead of stealing it. DRM is a way to punish people who are buying," he says. "Offering a great product at a great price is a way to combat piracy." http://news.yahoo.com/s/usatoday/200...ctionfreemusic  Diddy's Girl Group Danity Kane Tops U.S. Pop Chart Danity Kane, a prefabricated MTV girl group, scored its second consecutive No. 1 on the U.S. album chart Wednesday, while pop-soul duo Gnarls Barkley's latest release entered at a disappointing No. 18 after being rushed out three weeks ahead of schedule. Danity Kane's "Welcome to the Dollhouse" sold 236,192 copies in the week ended March 23, according to Nielsen SoundScan. It ranks as the second-biggest opening of the year, behind the 375,000-unit start for Jack Johnson's "Sleep Through the Static" in February. Perhaps more incredibly, at a time when most artists are routinely suffering big sales drops amid a decadelong slump in the music industry, "Welcome to the Dollhouse" managed to sell about 2,000 copies more than Danity Kane's 2006 self-titled debut. The debut has sold 926,000 copies to date. The MTV "Making the Band 3" troupe is signed to Sean "Diddy" Combs' Bad Boy imprint. It's a good day for Combs. The Los Angeles Times said it is reviewing a recent story linking the hip-hop mogul to the 1994 shooting of rapper Tupac Shakur, amid an online report that the paper may have relied on forged FBI documents. Combs strongly denied any involvement in the shooting. The Grammy-winning Gnarls Barkley's second album, "The Odd Couple," sold 31,000 copies for its No. 18 start. Its 2006 debut, "St. Elsewhere," opened at No. 20 and peaked at No. 4 as the single "Crazy" turned into a monster hit. "St. Elsewhere" has sold 1.4 million copies to date. "The Odd Couple" was rushed out last Tuesday, three weeks earlier than planned, likely because of an early leak on the Internet; online buyers accounted for 85% of the sales. A spokeswoman from the group's Atlantic Records label did not respond to an email seeking comment. Elsewhere, the multi-artist "NOW 27" compilation held steady at No. 2 with 170,000 copies in its second week. Last week's champ, Rick Ross' "Trilla," fell to No. 3 with 90,000. Rookie rapper Flo Rida may have recently topped Billboard's Hot 100 singles chart for a massive 10 weeks with "Low," but his debut album "Mail on Sunday" bowed at No. 4 with a relatively modest 86,000 copies. By contrast, "Low" has sold 3.3 million downloads since its November release, the biggest selling digital download of all time. Johnson's "Static" slipped one to No. 5 with 67,000 in its seventh week. Sales to date stand at 939,000 copies. Miley Cyrus' Disney double-disc "Hannah Montana 2 (Soundtrack)/Meet Miley Cyrus" soared 10 to No. 6 with 61,000. Additionally, her "The Best of Both Worlds Concert" set held at No. 10 with 51,000. Snoop Dogg's "Ego Trippin"' slid four to No. 7 with 57,000. Blender magazine cover girl Taylor Swift's self-titled album jumped four to No. 8, also with 57,000. Three weeks after it debuted at No. 1, Janet Jackson's "Discipline" now resides at No. 17. Its sales to date stand at about 310,000 copies; at the same point in its cycle, her previous release "20 Y.O." had sold 443,000 copies. The 2006 disc was considered a big disappointment. Album sales, boosted by the Easter holiday, rose 11.3% over the prior week to 8.83 million units, but were down 1.1% compared to the same week in 2007. http://www.billboard.com/bbcom/news/..._id=1003741823  BPI Admits CD Sales Booming! P2PNet Despite harassing their customers with bogus threats and lawsuits and saying they’re, “stealing music”, and false claims that file sharing is killing the music industry, the BPI (British Phonographic Industry) publicly states the labels do in fact sell more CDs today than they did 10 years ago. BPI ‘members’ include Warner Music Group, EMI, Sony BMG, and Universal Music Group. During an interview with BPI rep Matt Philips and music critic Neil McCormick, BBC News reported CD sales are in a “downward spiral”. But, Philips responded, “We do in fact sell more CDs than we did ten years ago, and I suspect there’ll be a lot of albums sold on CD [in future] as well.” And this is confirmed on the BPI website which states >>> Quote:
“Furthermore, 2007 saw the overall market increase by 9%.” A recent BPI press release also states, ” … (CD) sales remain 26% higher than those recorded a decade ago.” While the BPI claims, “The industry continues to innovate in developing new online and mobile business models,” the truth is actually explained in the interview succinctly by McCormick: “If you’re putting something on the internet, it doesn’t cost anything. Anybody can put anything anywhere. The music business is convulsed by fear and excitement about what that means. (They are) a rabbit in the headlights of the internet.” Wabbit hunting season is open. ‘Nuf said. http://www.p2pnet.net/story/15386  RIAA, MPAA, Pressure US Schools American educators continue to fight entertainment industry attempts to force US colleges and universities into not only becoming corporate copyright cops, but also installing, and paying for, software designed to filter all but corporate ‘product’ from online school networks. “In a letter to members of Congress dated Tuesday, the Motion Picture Association of America and the Recording Industry Association of America took exception to claims by higher-education groups that online music services and technology tools to block file-sharing are costly and ineffective,” says the Chronicle of Higher Education’s Wired Campus. “The entertainment-industry groups were responding to a letter that 13 higher-education groups sent to some members of Congress last week urging them to reject language in a House-approved bill that would require colleges to use such tools. “The entertainment industry groups want the House language to become law. A similar Senate bill omits the language on peer-to-peer file sharing.” A “filtering product is now deployed at approximately 70 colleges and universities across the country, and it has demonstrated the ability to impede illegal P2P activity on a number of campus networks,” the story quotes the RIAA and MPAA as saying. It’s probably referring to Audible Magic’s CopySense which, four years ago, was brazenly touted around congress by then newly appointed RIAA boss Mitch Bainwol. It was later analysed by the EFF (Electronic Frontier Foundation). Network administrators, “will want to ask Audible Magic tough questions before investing in the company’s technology, lest the investment be rendered worthless by the next P2P ‘upgrade’,” said the EFF’s Chris Palmer. Ohio University is boasting it spent more than $75,000 for a device —- CopySense —- that, “scans data crisscrossing its network for copyrighted media,” said p2pnet. ‘Disproportionately responsible’ The MPAA/RIAA letter, “says one university ’saved $1.2-million a year in terms of bandwidth and $70,000 in personnel costs’ after installing a technology filter on a campus network,” continues Wired Campus. “The letter did not name the university.” The letter also said US college students are, “disproportionately responsible for digital theft of copyrighted materials and that this dynamic is one that needs to be proactively addressed by the university community without further delay”. It’s now Standard Operating Procedure for people working for, and with, the RIAA and brother organisation, Hollywood’s MPAA, “to make false statements or issue grossly inaccurate statistics they know will be picked up by the ever-faithful lamescream corporate media and repeated as though they came from reliable sources,” said p2pnet in February, going on: “The statements and/or statistics can later be discarded as ‘mistakes’.” An example is the now-infamous MPAA ’study’ which concluded American students were responsible for 44% of Hollywood’s domestic losses. It was picked up by the international press corps and reported as fact. It was also one of the principal contributing factors to Section 494 of the College Opportunity and Affordability Act of 2007. However, the study, by LEK and dismissed by Britain’s Industry Trust for Intellectual Property Awareness (ITfIPA) as “inaccurate and out of date,” turned out to be based on specious statistics. The figure should have been 15%, the MPAA reluctantly admitted after the damage had been done. However, even 15% was well over the top, said Mark Luker, vice president of campus IT group Educause. It didn’t account for the fact more than 80% of college students live off campus and aren’t necessarily using college networks, he said, going on to state 3% was a more reasonable estimate for the percentage of revenue that might be at stake on campus networks. “The 44 percent figure was used to show that if college campuses could somehow solve this problem on this campus, then it would make a tremendous difference in the business of the motion picture industry,” Luker said. The new figures proved, “any solution on campus will have only a small impact on the industry itself”. ‘Ill conceived’ Educause has increased the level of its opposition to Section 494 of the College Opportunity and Affordability Act of 2007 as it stands, said another p2pnet post, going on: “ ‘Educause continues to feel that the mandates contained in the House bill are expensive, ineffective, and inappropriate,’ Steve Worona, director of policy and networking programs and founding director of the Educause/Cornell Institute for computer policy and law, said.” In a letter to CIOs in universities across the the US, the bill, “requires every college and university to develop a plan for offering alternatives to illegal downloading or peer-to-peer distribution of intellectual property as well as a plan to explore technology-based deterrents to prevent such illegal activity,” said Educause, declaring: “These requirements are ill conceived and would be harmful to higher education if passed into law. The legal online services they imagine are immature and have been rejected by student communities on many campuses, even when offered at no charge.” It would, “impose new costs and regulatory burdens on both the Department of Education and campuses while doing very little to address the problem,” says ACE president David Ward. “Therefore, we ask that the House recede to the Senate with respect to the proposed new Section 494.” However, the major Hollywood studios, Time Warner, Viacom, Fox, Sony, NBC Universal and Disney, and Warner Music, EMI, Vivendi Universal and Sony BMG, the members of the Big 4 organised music cartel, aren’t giving in. Higher-education groups are “trying to divert attention from the real and immediate problems at hand,” says the industry letter, according to Wired Campus, which adds: “The letter was signed by Dan Glickman, president of the motion picture group, and Mitch Bainwol, chairman and CEO of the recording-industry group. The letter was addressed to the chairmen and ranking minority members of the Senate Committee on Health, Education, Labor, and Pensions, and the House Committee on Education and Labor.” http://p2pnet.net/story/15366  Milestones Richard Widmark, Actor, Dies at 93 Aljean Harmetz Richard Widmark, who created a villain in his first movie role who was so repellent and frightening that the actor became a star overnight, died Monday at his home in Roxbury, Conn. He was 93. His death was announced Wednesday morning by his wife, Susan Blanchard. She said that Mr. Widmark had fractured a vertebra in recent months and that his conditioned had worsened. As Tommy Udo, a giggling, psychopathic killer in the 1947 gangster film “Kiss of Death,” Mr. Widmark tied up an old woman in a wheelchair (played by Mildred Dunnock) with a cord ripped from a lamp and shoved her down a flight of stairs to her death. “The sadism of that character, the fearful laugh, the skull showing through drawn skin, and the surely conscious evocation of a concentration-camp degenerate established Widmark as the most frightening person on the screen,” the critic David Thomson wrote in “The Biographical Dictionary of Film.” The performance won Mr. Widmark his sole Academy Award nomination, for best supporting actor. Tommy Udo made the 32-year-old Mr. Widmark, who had been an established radio actor, an instant movie star, and he spent the next seven years playing a variety of flawed heroes and relentlessly anti-social mobsters in 20th Century Fox’s juiciest melodramas. His mobsters were drenched in evil. Even his heroes, including the doctor who fights bubonic plague in Elia Kazan’s “Panic in the Streets” (1950), the daredevil pilot flying into the eye of a storm in “Slattery’s Hurricane” (1949) and the pickpocket who refuses to be a traitor in Samuel Fuller’s “Pickup on South Street” (1953) were nerve-strained and feral. “Movie audiences fasten on to one aspect of the actor, and then they decide what they want you to be,” Mr. Widmark once said. “They think you’re playing yourself. The truth is that the only person who can ever really play himself is a baby.” In reality, the screen’s most vicious psychopath was a mild-mannered former teacher who had married his college sweetheart, the actress Jean Hazelwood, and who told a reporter 48 years later that he had never been unfaithful and had never even flirted with women because, he said, “I happen to like my wife a lot.” He was originally turned down for the role of Tommy Udo by the movie’s director, Henry Hathaway, who told Mr. Widmark that he was too clean-cut and intellectual. It was Darryl Zanuck, the Fox studio head, who, after watching Mr. Widmark’s screen test, insisted that he be given the part. Among the 65 movies he made over the next five decades were “The Cobweb” (1955), in which he played the head of a psychiatric clinic where the staff seemed more emotionally troubled than the patients; “Saint Joan” (1957) , as the Dauphin to Joan Seberg’s Joan of Arc; John Wayne’s “The Alamo” (1960), as Jim Bowie, the inventor of the Bowie knife; “Judgment at Nuremberg” (1961), as an American army colonel prosecuting German war criminals; and John Ford’s revisionist western “Cheyenne Autumn” (1963), as an army captain who risks his career to help the Indians. The genesis of “Cheyenne Autumn” was research Mr. Widmark had done at Yale into the suffering of the Cheyenne. He showed his work to John Ford and, two years later, Ford sent Mr. Widmark a finished screenplay. Mr. Widmark created the role of Detective Sergeant Daniel Madigan in Don Siegel’s 1968 film “Madigan.” It proved so popular that he later played the loner Madigan on an NBC television series during the 1972-73 season. As his blonde hair turned grey, Mr. Widmark moved up in rank, playing generals in the nuclear thriller “Twilight’s Last Gleaming” (1977) and “The Swarm” (1978), in which he waged war on bees. He was the evil head of a hospital in “Coma” (1978) and a United States Senator in “True Colors” (1991). He was forever fighting producers’ efforts to stereotype him. Indeed, he became so adept at all types of roles that he consistently lent credibility to inferior movies and became an audience favorite over a career that spanned more than half a century. “I suppose I wanted to act in order to have a place in the sun,” he once told a reporter. “I’d always lived in small towns, and acting meant having some kind of identity.” Richard Widmark (he had no middle name) was born on Dec. 26, 1914, in Sunrise, Minn., and grew up throughout the Midwest. His father, Carl Widmark, was a traveling salesman who took his wife, Mae Ethel, and two sons from Minnesota to Sioux Falls, S.D.; Henry, Ill.; Chillicothe, Mo.; and Princeton, Ill., where Mr. Widmark graduated from high school as senior class president. Movie crazy, he was afraid to admit his interest in the “sissy” job of acting. On a full scholarship at Lake Forest College in Illinois, he played end on the football team, took third place in a state oratory contest, starred in plays and was, once again, senior class president. Graduating in 1936, he spent two years as an instructor in the Lake Forest drama department, directing and acting in two dozen plays. Then he headed to New York City in 1938, where one of his classmates was producing 15-minute radio soap operas and cast Mr. Widmark in a variety of roles. “Getting launched was easy for me — too easy, perhaps,” he said of his success playing “young, neurotic guys” on “Big Sister,” “Life Can Be Beautiful,” “Joyce Jordan, M.D.,” “Stella Dallas,” “Front Page Farrell,” “Aunt Jenny’s Real Life Stories” and “Inner Sanctum.” At the beginning of World War II, Mr. Widmark tried to enlist in the army but was turned down three times because of a perforated eardrum. So he turned, in 1943, to Broadway. In his first stage role, he played an Army lieutenant in F. Hugh Herbert’s “Kiss and Tell,” directed by George Abbott. Appearing in the controversial play “Trio,” which was closed by the License Commissioner after 67 performances because it touched on lesbianism, he received glowing reviews as a college student who fights to free the girl he loves from the domination of an older woman. After a successful, 10-year career as a radio actor, he tried the movies with “Kiss of Death,” which was being filmed in New York. Older than most new recruits, he was, to his surprise, summoned to Hollywood after the movie was released. “I’m probably the only actor who gave up a swimming pool to go out to Hollywood,” Mr. Widmark told The New Yorker in 1961. He had never expected 20th Century Fox to pick up the option on the contract he was forced to sign to get the role of Tommy Udo. During the seven years of his Fox contract, he starred in 20 movies, including “Yellow Sky” (1948), as the blackguard who menaces Gregory Peck; “Down to the Sea in Ships” (1949), as a valiant whaler; Jules Dassin’s “Night and the City” (1950), as a small- time hustler who dreams of becoming a wrestling promoter; and “Don’t Bother to Knock” (1952), in which the tables were turned and he was the prey of a psychopathic Marilyn Monroe. A passionate liberal Democrat, Mr. Widmark played a bigot who baits a black doctor in Joseph Mankiewicz’s “No Way Out” (1950). He was so embarrassed by the character that after every scene he apologized to the young actor he was required to torment, Sidney Poitier. In 1990, when Mr. Widmark was given the D.W. Griffith Career Achievement Award by the National Board of Review, it was Mr. Poitier who presented it to him. Within two years after his Fox contract ended, Mr. Widmark had formed a production company and produced “Time Limit” (1957), a serious dissection of possible treason by an American prisoner of war that The New York Times called “sobering, important and exciting.” Directed by the actor Karl Malden, “Time Limit” starred Mr. Widmark as an army colonel who is investigating a major (Richard Basehart) who is suspected of having broken under pressure during the Korean War and aided the enemy. Mr. Widmark produced two more films: “The Secret Ways” (1961) in which he went behind the Iron Curtain to bring out an anti-Communist leader; and “The Bedford Incident” (1964), another Cold War drama, in which he played an ultraconservative naval captain trailing a Russian submarine and putting the world in danger of a nuclear catastrophe. Mr. Widmark told The Guardian in 1995 that he had not become a producer to make money but to have greater artistic control. “I could choose the director and my fellow actors,” he said. “I could carry out projects which I liked but the studios didn’t want.” He added: “The businessmen who run Hollywood today have no self-respect. What interests them is not movies but the bottom line. Look at ‘Dumb and Dumber,’ which turns idiocy into something positive, or ‘Forrest Gump,’ a hymn to stupidity. ‘Intellectual’ has become a dirty word.” He also vowed he would never appear on a talk show on television, saying, “When I see people destroying their privacy — what they think, what they feel — by beaming it out to millions of viewers, I think it cheapens them as individuals.” In 1970, he won an Emmy nomination for his first television role, as the president of the United States in a mini-series based on Fletcher Knebel’s novel “Vanished.” By the 1980s, television movies had transformed the jittery psychopath of his early days into a wise and stalwart lawman. He played a Texas Ranger opposite Willie Nelson’s train robber in “Once Upon a Texas Train,” a small-town police chief in “Blackout” and, most memorably, a bayou country sheriff faced with a group of aged black men who have confessed to a murder in “A Gathering of Old Men.” “The older you get, the less you know about acting,” he told one reporter, “but the more you know about what makes the really great actors.” The actor he most admired was Spencer Tracy, because, he said, Tracy’s acting had a reality and honesty that seemed effortless. Mr. Widmark, who hated the limelight, spent his Hollywood years living quietly on a large farm in Connecticut and an 80-acre horse ranch in Hidden Valley, north of Los Angeles. Asked once if he had been “astute” with his money, he answered, “No, just tight.” He sold the ranch in 1997 after the death of Ms. Hazelwood, his wife of 55 years. “I don’t care how well known an actor is,” Mr. Widmark insisted. “He can lead a normal life if he wants to.” Besides his wife, Ms. Blanchard, Mr. Widmark is survived by his daughter, Anne Heath Widmark, of Santa Fe, N.M., who had once been married to the Hall of Fame pitcher Sandy Koufax. Well into his later years, the nonviolent, gun-hating Mr. Widmark, who described himself as “gentle,” was accosted by strangers who expected him to be a tough guy. There is even a story that Joey Gallo, the New York mobster, was so taken by Mr. Widmark’s performance in “Kiss of Death” that he copied the actor’s natty posture, sadistic smirk and tittering laugh. “It’s a bit rough,” Mr. Widmark once said, “priding oneself that one isn’t too bad an actor and then finding one’s only remembered for a giggle.” http://www.nytimes.com/2008/03/26/ar...idmark.html?hp  Neil Aspinall, Beatles Aide, Dies at 66 Allan Kozinn Neil Aspinall, who left an accounting job to become the Beatles’ road manager when the group was still a local dance band and who went on to manage the band’s production and management company, Apple, died Sunday night in Manhattan. He was 66 and lived in Twickenham, England. Geoff Baker, a spokesman for the family, said the cause was lung cancer. Mr. Aspinall had been undergoing treatment at Memorial Sloan-Kettering Cancer Center. He retired from Apple last year. Of all the people in the Beatles’ orbit, Mr. Aspinall had the most durable relationship with the group; in fact, he had already been a crucial member of the Beatles' entourage for about 18 months when Ringo Starr became the Beatles' drummer. When the Beatles were inducted into the Rock and Roll Hall of Fame in 1988, George Harrison made a point of saying that Mr. Aspinall should be considered the fifth Beatle. In November 1967, when the Beatles formed Apple to oversee their creative and business interests, they asked Mr. Aspinall, by then a trusted assistant of longstanding, to manage it. He never took a formal title, but he ran a company that, in its first years, included a record label, a film production company and electronics, publishing and retailing divisions. He also quickly put the Beatles’ own complicated contractual commitments in order. Nevertheless, expenses at Apple spun out of control as the open kitchen and bar at the company’s Savile Row office began feeding and watering a parade of journalists, would-be Apple artists and hangers-on. When the American manager Allen Klein was brought in to sort out the Beatles’ finances, Mr. Klein fired much of the staff but was told by John Lennon, “Don’t touch Neil and Mal, they’re ours,” referring to Mr. Aspinall and his assistant, Mal Evans, who had also been with the group since its Liverpool days. During the first 25 years at the head of Apple, Mr. Aspinall oversaw a succession of lawsuits. In one, not settled until 1974, Paul McCartney sued the other Beatles to dissolve their partnership. At the same time, the Beatles as a group sued EMI Records in a royalties dispute that took 20 years to settle. Apple also sued the Broadway show “Beatlemania” for unauthorized use of the Beatles’ name and logo, and it fought several court battles against Apple Computer for trademark infringement. The last was settled in 2006, in favor of the computer company. Mr. Aspinall was often blamed for the slow pace at which Beatles archival projects were released as several projects have languished on Apple's shelves for years, including a home-video production of the Beatles' 1965 concert at Shea Stadium, remastered versions of the film "Let It Be" and digital download versions of all the Beatles' studio recordings. What the complaints did not take into account is that Mr. Aspinall could release only what Apple’s principals — Mr. McCartney, Mr. Starr, Olivia Harrison and Yoko Ono (the widows of George Harrison and John Lennon) — unanimously agree should be released. And the interpersonal politics at Apple are such that unanimity is hard to come by. Even so, Mr. Aspinall did oversee several important releases since 1993. These include “Live at the BBC,” a two-disc compilation of the group’s radio performances; “Yellow Submarine Songtrack,” a remixed version of the music from the “Yellow Submarine” animated film, which Apple also restored and reissued; “1,” a single-disc hits compilation; “Let It Be ... Naked,” a remixed and reconfigured version of “Let It Be,” without the string and choral overdubs that fans have long complained about; two installments of “The Capitol Albums,” which brought together mono and stereo versions of eight Beatles albums in their American (rather than British) configurations; and “Love,” a multi-media collaboration with Cirque du Soleil (and a matching recording). His biggest achievement was “The Beatles Anthology.” The idea was to use performance film and interview clips to let the Beatles tell their own story. Originally meant to be a theatrical film, the project was begun in 1970 but shelved until the final EMI lawsuits were settled in 1989. By then, Mr. Aspinall had proposed that instead of making a film, the Beatles should contribute new interviews (with archival interviews with John Lennon, who was murdered in 1980) to a six-hour television series and a nearly 13-hour home video edition. When the Beatles agreed, he assembled an extraordinary archive of television and concert film, photograph collections and other materials, for use both in “The Beatles Anthology” and other potential Apple projects. He was one of the few non-Beatles interviewed in “The Beatles Anthology” and credited as executive producer. He retired from Apple in 2007. Mr. Aspinall’s history with the Beatles reached back to their earliest days as a band, when he hung flyers around Liverpool advertising their performances. In February 1961, with the group’s popularity in Liverpool soaring, Mr. Aspinall gave up his job as an apprentice accountant and began driving the group from job to job, often three performances a day. On international tours, Mr. Aspinall left the business of equipment setup to Mr. Evans and became the Beatles’ principal aide. One of Mr. Aspinall’s later jobs was to round up the pictures of the celebrities and other influential crowd members for the cover of the 1967 album “Sgt. Pepper’s Lonely Hearts Club Band.” He also accompanied Lennon and Mr. McCartney to New York in May 1968 for a series of interviews announcing Apple. On occasion, he was drafted as a performer. He was among the singers in the celebratory chorus of “Yellow Submarine,” and he played tambura (an Indian drone instrument) on “Within You Without You,” harmonica on “Being for the Benefit of Mr. Kite” and percussion on “Magical Mystery Tour.” Mr. Aspinall was born in Prestatyn, Wales, on Oct. 13, 1941, and grew up in Liverpool, where he attended the Liverpool Institute with Mr. McCartney and Mr. Harrison. He became friendly with the Beatles through Pete Best, their drummer from 1960 to 1962. Mr. Aspinall, originally a boarder in Mr. Best’s house, had started a romantic relationship with Mona Best, Mr. Best’s mother. Their son, Roag Best, was born in 1962. Mr. Aspinall accompanied Pete Best to the meeting with the Beatles manager Brian Epstein at which the drummer was fired. Mr. Aspinall decided to continue working for the group and also maintained his relationship with Mrs. Best for several years. He eventually had an opportunity to help Mr. Best make up for his missed fortune as a member of the Beatles: because several of the group’s previously unissued recordings with Mr. Best were used on “The Beatles Anthology,” Mr. Aspinall negotiated a generous royalty arrangement for the drummer. In 1968, Mr. Aspinall married Suzy Ornstein, whose father, George “Bud” Ornstein, was head of European production for United Artists, the company for which the Beatles made the films “A Hard Day’s Night,” “Help!” and “Let It Be.” She survives him, as do their daughters Gayla, Dhara and Mandy; their son Julian, and Mr. Aspinall’s first son, Roag Best. Mr. Aspinall made several films for the Beatles individually and collectively during his years as their principal aide. One accompanied the group’s 1969 single “Something” for which Mr. Aspinall filmed the Beatles and their wives walking placidly through an English garden (or, in Mr. McCartney’s case, the grounds of his farm in Scotland). What Mr. Aspinall’s idyllic film avoided showing was that the Beatles were at that point barely on speaking terms. In the film, no two Beatles are seen together. During they group’s heyday, Mr. Aspinall wrote articles about their recording sessions for “The Beatles Monthly Book,” an officially sanctioned fan magazine. Virtually alone among Beatles insiders, he resisted the temptation to publish his memoirs, but joked that if he did write them, he would arrange to have them published only after his death. He is not known to have undertaken the project. http://www.nytimes.com/2008/03/24/ar...pinall.html?hp |
||
|
|

|
|
|
#2 | ||
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Futurist Ray Kurzweil Pulls Out All the Stops (and Pills) to Live to Witness the Singularity
Never Mind the Singularity, Here's the Science Gary Wolf Ray Kurzweil, the famous inventor, is trim, balding, and not very tall. With his perfect posture and narrow black glasses, he would look at home in an old documentary about Cape Canaveral, but his mission is bolder than any mere voyage into space. He is attempting to travel across a frontier in time, to pass through the border between our era and a future so different as to be unrecognizable. He calls this border the singularity. Kurzweil is 60, but he intends to be no more than 40 when the singularity arrives. Kurzweil's notion of a singularity is taken from cosmology, in which it signifies a border in spacetime beyond which normal rules of measurement do not apply (the edge of a black hole, for example). The word was first used to describe a crucial moment in the evolution of humanity by the great mathematician John von Neumann. One day in the 1950s, while talking with his colleague Stanislaw Ulam, von Neumann began discussing the ever-accelerating pace of technological change, which, he said, "gives the appearance of approaching some essential singularity in the history of the race beyond which human affairs as we know them could not continue." Many years later, this idea was picked up by another mathematician, the professor and science fiction writer Vernor Vinge, who added an additional twist. Vinge linked the singularity directly with improvements in computer hardware. This put the future on a schedule. He could look at how quickly computers were improving and make an educated guess about when the singularity would arrive. "Within 30 years, we will have the technological means to create superhuman intelligence," Vinge wrote at the beginning of his 1993 essay The Coming Technological Singularity: How to Survive in the Post-Human Era. "Shortly after, the human era will be ended." According to Vinge, superintelligent machines will take charge of their own evolution, creating ever smarter successors. Humans will become bystanders in history, too dull in comparison with their devices to make any decisions that matter. Kurzweil transformed the singularity from an interesting speculation into a social movement. His best-selling books The Age of Spiritual Machines and The Singularity Is Near cover everything from unsolved problems in neuroscience to the question of whether intelligent machines should have legal rights. But the crucial thing that Kurzweil did was to make the end of the human era seem actionable: He argues that while artificial intelligence will render biological humans obsolete, it will not make human consciousness irrelevant. The first AIs will be created, he says, as add-ons to human intelligence, modeled on our actual brains and used to extend our human reach. AIs will help us see and hear better. They will give us better memories and help us fight disease. Eventually, AIs will allow us to conquer death itself. The singularity won't destroy us, Kurzweil says. Instead, it will immortalize us. There are singularity conferences now, and singularity journals. There has been a congressional report about confronting the challenges of the singularity, and late last year there was a meeting at the NASA Ames Research Center to explore the establishment of a singularity university. The meeting was called by Peter Diamandis, who established the X Prize. Attendees included senior government researchers from NASA, a noted Silicon Valley venture capitalist, a pioneer of private space exploration, and two computer scientists from Google. At this meeting, there was some discussion about whether this university should avoid the provocative term singularity, with its cosmic connotations, and use a more ordinary phrase, like accelerating change. Kurzweil argued strongly against backing off. He is confident that the word will take hold as more and more of his astounding predictions come true. Kurzweil does not believe in half measures. He takes 180 to 210 vitamin and mineral supplements a day, so many that he doesn't have time to organize them all himself. So he's hired a pill wrangler, who takes them out of their bottles and sorts them into daily doses, which he carries everywhere in plastic bags. Kurzweil also spends one day a week at a medical clinic, receiving intravenous longevity treatments. The reason for his focus on optimal health should be obvious: If the singularity is going to render humans immortal by the middle of this century, it would be a shame to die in the interim. To perish of a heart attack just before the singularity occurred would not only be sad for all the ordinary reasons, it would also be tragically bad luck, like being the last soldier shot down on the Western Front moments before the armistice was proclaimed. In his childhood, Kurzweil was a technical prodigy. Before he turned 13, he'd fashioned telephone relays into a calculating device that could find square roots. At 14, he wrote software that analyzed statistical deviance; the program was distributed as standard equipment with the new IBM 1620. As a teenager, he cofounded a business that matched high school students with colleges based on computer evaluation of a mail-in questionnaire. He sold the company to Harcourt, Brace & World in 1968 for $100,000 plus royalties and had his first small fortune while still an undergraduate at MIT. Though Kurzweil was young, it would have been a poor bet to issue him life insurance using standard actuarial tables. He has unlucky genes: His father died of heart disease at 58, his grandfather in his early forties. He himself was diagnosed with high cholesterol and incipient type 2 diabetes — both considered to be significant risk factors for early death — when only 35. He felt his bad luck as a cloud hanging over his life. Still, the inventor squeezed a lot of achievement out of these early years. In his twenties, he tackled a science fiction type of problem: teaching computers to decipher words on a page and then read them back aloud. At the time, common wisdom held that computers were too slow and too expensive to master printed text in all its forms, at least in a way that was commercially viable. But Kurzweil had a special confidence that grew from a habit of mind he'd been cultivating for years: He thought exponentially. To illustrate what this means, consider the following quiz: 2, 4, ?, ?. What are the missing numbers? Many people will say 6 and 8. This suggests a linear function. But some will say the missing numbers are 8 and 16. This suggests an exponential function. (Of course, both answers are correct. This is a test of thinking style, not math skills.) Human minds have a lot of practice with linear patterns. If we set out on a walk, the time it takes will vary linearly with the distance we're going. If we bill by the hour, our income increases linearly with the number of hours we work. Exponential change is also common, but it's harder to see. Financial advisers like to tantalize us by explaining how a tiny investment can grow into a startling sum through the exponential magic of compound interest. But it's psychologically difficult to heed their advice. For years, an interest-bearing account increases by depressingly tiny amounts. Then, in the last moment, it seems to jump. Exponential growth is unintuitive, because it can be imperceptible for a long time and then move shockingly fast. It takes training and experience, and perhaps a certain analytical coolness, to trust in exponential curves whose effects cannot be easily perceived. Moore's law — the observation by Intel cofounder Gordon Moore that the number of transistors on an integrated circuit doubles roughly every 18 months — is another example of exponential change. For people like Kurzweil, it is the key example, because Moore's law and its many derivatives suggest that just about any limit on computing power today will be overcome in short order. While Kurzweil was working on his reading machine, computers were improving, and they were indeed improving exponentially. The payoff came on January 13, 1976, when Walter Cronkite's famous sign-off — "and that's the way it is" — was read not by the anchorman but by the synthetic voice of a Kurzweil Reading Machine. Stevie Wonder was the first customer. The original reader was the size of a washing machine. It read slowly and cost $50,000. One day late last year, as a winter storm broke across New England, I stood in Kurzweil's small office suite in suburban Boston, playing with the latest version. I hefted it in my hand, stuck it in my pocket, pulled it out again, then raised it above a book flopped open on the table. A bright light flashed, and a voice began reading aloud. The angle of the book, the curve of its pages, the uneven shadows — none of that was a problem. The mechanical voice picked up from the numerals on the upper left corner — ... four hundred ten. The singularity is near. The continued opportunity to alleviate human distress is one key motivation for continuing technological advancement — and continued down the page in an artificial monotone. Even after three decades of improvement, Kurzweil's reader is a dull companion. It expresses no emotion. However, it is functionally brilliant to the point of magic. It can handle hundreds of fonts and any size book. It doesn't mind being held at an angle by an unsteady hand. Not only that, it also makes calls: Computers have become so fast and small they've nearly disappeared, and the Kurzweil reader is now just software running on a Nokia phone. In the late '70s, Kurzweil's character-recognition algorithms were used to scan legal documents and articles from newspapers and magazines. The result was the Lexis and Nexis databases. And a few years later, Kurzweil released speech recognition software that is the direct ancestor of today's robot customer service agents. Their irritating mistakes taking orders and answering questions would seem to offer convincing evidence that real AI is still many years away. But Kurzweil draws the opposite conclusion. He admits that not everything he has invented works exactly as we might wish. But if you will grant him exponential progress, the fact that we already have virtual robots standing in for retail clerks, and cell phones that read books out loud, is evidence that the world is about to change in even more fantastical ways. Look at it this way: If the series of numbers in the quiz mentioned earlier is linear and progresses for 100 steps, the final entry is 200. But if progress is exponential, then the final entry is 1,267,650,600,228,229,400,000,000,000,000. Computers will soon be smarter than humans. Nobody has to die. In a small medical office on the outskirts of Denver, with windows overlooking the dirty snow and the golden arches of a fast-food mini-mall, one of the world's leading longevity physicians, Terry Grossman, works on keeping Ray Kurzweil alive. Kurzweil is not Grossman's only client. The doctor charges $6,000 per appointment, and wealthy singularitarians from all over the world visit him to plan their leap into the future. Grossman's patient today is Matt Philips, 32, who became independently wealthy when Yahoo bought the Internet advertising company where he worked for four years. A young medical technician is snipping locks of his hair, and another is extracting small vials of blood. Philips is in good shape at the moment, but he is aware that time marches on. "I'm dying slowly. I can't feel it, but I know its happening, little by little, cell by cell," he wrote on his intake questionnaire. Philips has read Kurzweil's books. He is a smart, skeptical person and accepts that the future is not entirely predictable, but he also knows the meaning of upside. At worst, his money buys him new information about his health. At best, it makes him immortal. "The normal human lifespan is about 125 years," Grossman tells him. But Philips wasn't born until 1975, so he starts with an advantage. "I think somebody your age, and in your condition, has a reasonable chance of making it across the first bridge," Grossman says. According to Grossman and other singularitarians, immortality will arrive in stages. First, lifestyle and aggressive antiaging therapies will allow more people to approach the 125-year limit of the natural human lifespan. This is bridge one. Meanwhile, advanced medical technology will begin to fix some of the underlying biological causes of aging, allowing this natural limit to be surpassed. This is bridge two. Finally, computers become so powerful that they can model human consciousness. This will permit us to download our personalities into nonbiological substrates. When we cross this third bridge, we become information. And then, as long as we maintain multiple copies of ourselves to protect against a system crash, we won't die. Kurzweil himself started across the first bridge in 1988. That year, he confronted the risk that had been haunting him and began to treat his body as a machine. He read up on the latest nutritional research, adopted the Pritikin diet, cut his fat intake to 10 percent of his calories, lost 40 pounds, and cured both his high cholesterol and his incipient diabetes. Kurzweil wrote a book about his experience, The 10% Solution for a Healthy Life. But this was only the beginning. Kurzweil met Grossman at a Foresight Nanotech Institute meeting in 1999, and they became research partners. Their object of investigation was Kurzweil's body. Having cured himself of his most pressing health problems, Kurzweil was interested in adopting the most advanced medical and nutritional technologies, but it wasn't easy to find a doctor willing to tolerate his persistent questions. Grossman was building a new type of practice, focused not on illness but on the pursuit of optimal health and extreme longevity. The two men exchanged thousands of emails, sharing speculations about which cutting-edge discoveries could be safely tried. Though both Grossman and Kurzweil respect science, their approach is necessarily improvisational. If a therapy has some scientific promise and little risk, they'll try it. Kurzweil gets phosphatidylcholine intravenously, on the theory that this will rejuvenate all his body's tissues. He takes DHEA and testosterone. Both men use special filters to produce alkaline water, which they drink between meals in the hope that negatively charged ions in the water will scavenge free radicals and produce a variety of health benefits. This kind of thing may seem like quackery, especially when promoted by various New Age outfits touting the "pH miracle of living." Kurzweil and Grossman justify it not so much with scientific citations — though they have a few — but with a tinkerer's shrug. "Life is not a randomized, double-blind, placebo-controlled study," Grossman explains. "We don't have that luxury. We are operating with incomplete information. The best we can do is experiment with ourselves." Obviously, Kurzweil has no plan for retirement. He intends to sustain himself indefinitely through his intelligence, which he hopes will only grow. A few years ago he deployed an automated system for making money on the stock market, called FatKat, which he uses to direct his own hedge fund. He also earns about $1 million a year in speaking fees. Meanwhile, he tries to safeguard his well-being. As a driver he is cautious. He frequently bicycles through the Boston suburbs, which is good for physical conditioning but also puts his immortality on the line. For most people, such risks blend into the background of life, concealed by a cheerful fatalism that under ordinary conditions we take as a sign of mental health. But of course Kurzweil objects to this fatalism. He wants us to try harder to survive. His plea is often ignored. Kurzweil has written about the loneliness of being a singularitarian. This may seem an odd complaint, given his large following, but there is something to it. A dozen of his fans may show up in Denver every month to initiate longevity treatments, but many of them, like Matt Philips, are simply hedging their bets. Most health fanatics remain agnostic, at best, on the question of immortality. Kurzweil predicts that by the early 2030s, most of our fallible internal organs will have been replaced by tiny robots. We'll have "eliminated the heart, lungs, red and white blood cells, platelets, pancreas, thyroid and all the hormone-producing organs, kidneys, bladder, liver, lower esophagus, stomach, small intestines, large intestines, and bowel. What we have left at this point is the skeleton, skin, sex organs, sensory organs, mouth and upper esophagus, and brain." In outlining these developments, Kurzweil's tone is so calm and confident that he seems to be describing the world as it is today, rather than some distant, barely imaginable future. This is because his prediction falls out cleanly from the equations he's proposed. Knowledge doubles every year, Kurzweil says. He has estimated the number of computations necessary to simulate a human brain. The rest is simple math. But wait. There may be something wrong. Kurzweil's theory of accelerating change is meant to be a universal law, applicable wherever intelligence is found. It's fine to say that knowledge doubles every year. But then again, what is a year? A year is an astronomical artifact. It is the length of time required by Earth to make one orbit around our unexceptional star. A year is important to our nature, to our biology, to our fantasies and dreams. But it is a strange unit to discover in a general law. "Doubling every year," I say to Kurzweil, "makes your theory sound like a wish." He's not thrown off. A year, he replies, is just shorthand. The real equation for accelerating world knowledge is much more complicated than that. (In his book, he gives it as: .) He has examined the evidence, and welcomes debate on the minor details. If you accept his basic premise of accelerating growth, he'll yield a little on the date he predicts the singularity will occur. After all, concede accelerating growth and the exponential fuse is lit. At the end you get that big bang: an explosion in intelligence that yields immortal life. Despite all this, people continue to disbelieve. There is a lively discussion among experts about the validity of Moore's law. Kurzweil pushes Moore's law back to the dawn of time, and forward to the end of the universe. But many computer scientists and historians of technology wonder if it will last another decade. Some suspect that the acceleration of computing power has already slowed. There are also philosophical objections. Kurzweil's theory is that super-intelligent computers will necessarily be human, because they will be modeled on the human brain. But there are other types of intelligence in the world — for instance, the intelligence of ant colonies — that are alien to humanity. Grant that a computer, or a network of computers, might awaken. The consciousness of the this fabulous AI might remain as incomprehensible to us as we are to the protozoa. Other pessimists point out that the brain is more than raw processing power. It also has a certain architecture, a certain design. It is attached to specific type of nervous system, it accepts only particular kinds of inputs. Even with better computational speed driving our thoughts, we might still be stuck in a kind of evolutionary dead end, incapable of radical self-improvement. And these are the merely intellectual protests Kurzweil receives. The fundamental cause for loneliness, if you are a prophet of the singularity, is probably more profound. It stems from the simple fact that the idea is so strange. "Death has been a ubiquitous, ever-present facet of human society," says Kurzweil's friend Martine Rothblatt, founder of Sirius radio and chair of United Therapeutics, a biotech firm on whose board Kurzweil sits. "To tell people you are going to defeat death is like telling people you are going to travel back in time. It has never been done. I would be surprised if people had a positive reaction." To press his case, Kurzweil is writing and producing an autobiographical movie, with walk-ons by Alan Dershowitz and Tony Robbins. Kurzweil appears in two guises, as himself and as an intelligent computer named Ramona, played by an actress. Ramona has long been the inventor's virtual alter ego and the expression of his most personal goals. "Women are more interesting than men," he says, "and if it's more interesting to be with a woman, it is probably more interesting to be a woman." He hopes one day to bring Ramona to life, and to have genuine human experiences, both with her and as her. Kurzweil has been married for 32 years to his wife, Sonya Kurzweil. They have two children — one at Stanford University, one at Harvard Business School. "I don't necessarily only want to be Ramona," he says. "It's not necessarily about gender confusion, it's just about freedom to express yourself." Kurzweil's movie offers a taste of the drama such a future will bring. Ramona is on a quest to attain full legal rights as a person. She agrees to take a Turing test, the classic proof of artificial intelligence, but although Ramona does her best to masquerade as human, she falls victim to one of the test's subtle flaws: Humans have limited intelligence. A computer that appears too smart will fail just as definitively as one that seems too dumb. "She loses because she is too clever!" Kurzweil says. The inventor's sympathy with his robot heroine is heartfelt. "If you're just very good at doing mathematical theorems and making stock market investments, you're not going to pass the Turing test," Kurzweil acknowledged in 2006 during a public debate with noted computer scientist David Gelernter. Kurzweil himself is brilliant at math, and pretty good at stock market investments. The great benefits of the singularity, for him, do not lie here. "Human emotion is really the cutting edge of human intelligence," he says. "Being funny, expressing a loving sentiment — these are very complex behaviors." One day, sitting in his office overlooking the suburban parking lot, I ask Kurzweil if being a singularitarian makes him happy. "If you took a poll of primitive man, happiness would be getting a fire to light more easily," he says. "But we've expanded our horizon, and that kind of happiness is now the wrong thing to focus on. Extending our knowledge and casting a wider net of consciousness is the purpose of life." Kurzweil expects that the world will soon be entirely saturated by thought. Even the stones may compute, he says, within 200 years. Every day he stays alive brings him closer to this climax in intelligence, and to the time when Ramona will be real. Kurzweil is a technical person, but his goal is not technical in this respect. Yes, he wants to become a robot. But the robots of his dreams are complex, funny, loving machines. They are as human as he hopes to be. http://www.wired.com/medtech/drugs/m...04/ff_kurzweil  Patriot Act Haunts Google Service Simon Avery Google Inc. is a year into its ground-shifting strategy to change the way people communicate and work. But the initiative to reinvent the way that people use software is running headlong into another new phenomenon of the information technology age: the unprecedented powers of security officials in the United States to conduct surveillance on communications. Eighteen months ago, Lakehead University in Thunder Bay, Ont., had an outdated computer system that was crashing daily and in desperate need of an overhaul. A new installation would have cost more than $1-million and taken months to implement. Google's service, however, took just 30 days to set up, didn't cost the university a penny and gave nearly 8,000 students and faculty leading-edge software, said Michael Pawlowski, Lakehead's vice-president of administration and finance. U.S.-based Google spotlighted the university as one of the first to adopt its software model of the future, and today Mr. Pawlowski boasts the move was the right thing for Lakehead, saving it hundreds of thousands of dollars in annual operating costs. But he notes one trade-off: The faculty was told not to transmit any private data over the system, including student marks. The U.S. Patriot Act, passed in the weeks after the September, 2001, terrorist attacks in the United States, gives authorities the means to secretly view personal data held by U.S. organizations. It is at odds with Canada's privacy laws, which require organizations to protect private information and inform individuals when their data has been shared. At Lakehead, the deal with Google sparked a backlash. "The [university] did this on the cheap. By getting this free from Google, they gave away our rights," said Tom Puk, past president of Lakehead's faculty association, which filed a grievance against Lakehead administration that's still in arbitration. Professors say the Google deal broke terms of their collective agreement that guarantees members the right to private communications. Mr. Puk says teachers want an in-house system that doesn't let third parties see their e-mails. Some other organizations are banning Google's innovative tools outright to avoid the prospect of U.S. spooks combing through their data. Security experts say many firms are only just starting to realize the risks they assume by embracing Web-based collaborative tools hosted by a U.S. company, a problem even more acute in Canada where federal privacy rules are at odds with U.S. security measures. "You have to decide which law you are going to break," said Darren Meister, associate professor of information systems at the Richard Ivey School of Business, who specializes in how technology enhances organizational effectiveness. "If I were a business manager, I would want to be very careful about what kind of data I made accessible to U.S. law enforcement." Using their new powers under the Patriot Act, U.S. intelligence officials can scan documents, pick out certain words and create profiles of the authors - a frightening challenge to academic freedom, Mr. Puk said. For instance, a Lakehead researcher with a Middle Eastern name, researching anthrax or nuclear energy, might find himself denied entry to the United States without ever knowing why. "You would have no idea what they are up to with your information until, perhaps, it is too late," Mr. Puk said. "We don't want to be subject to laws of the Patriot Act." Google's free Web tools are advertising-based and they automatically extract information from personal content to build a profile for advertisers. Lakehead professors also object to this feature, although Mr. Puk says Google has refrained from attaching ads until the grievance is settled. The privacy issue goes far beyond academia. In Toronto, at SickKids Foundation, which has the largest endowment of any Canadian hospital, employees have been keen to use Google tools. But the foundation's IT department blocked access for two reasons. "Wherever possible, we keep our donor and patient records in Canada, as trying to enforce privacy laws in other jurisdictions is complex and expensive," said Chris Woodill, director of IT and new media at SickKids Foundation. Second, free hosted software offers limited support and no formal legal contract, limiting an organization's ability to demand additional privacy or security measures, he said. Google says it has a strong track record in regard to protecting customers' data. The firm cites a court case it fought in 2006 against attempts by the U.S. Justice Department to subpoena customer search records. "We will continue to be strong advocates on behalf of protecting our users' data," said Peter Fleischer, Google's global privacy counsel. But the Mountain View, Calif.-based company will not discuss how often government agencies demand access to its customers' information or whether content on its new Web-based collaborative tools has been the subject of any reviews under the Patriot Act. Montreal security strategist Jeffrey Posluns says Google's software suite may suit some small businesses because cost savings are significant. But he warns that the deciding factor should be the sensitivity of the organization's information. http://www.theglobeandmail.com/servl...echnology/home  Google to Push Privacy Initiatives in U.S. Grant Gross Google is working with other companies to push consumer privacy legislation in the U.S. Congress and will work with the U.S. Federal Trade Commission to fine-tune online advertising principles the agency proposed in December, the company's top privacy executives said Wednesday. In addition, Google is reaching out to privacy advocates in an effort to allay concerns about its acquisition of online advertising vendor DoubleClick, company officials said. Privacy is of such concern for Google that it embeds privacy lawyers with product teams, Nicole Wong, Google's deputy general counsel, told reporters in Washington, D.C. Google, in its own products and in policy discussions, has focused on three privacy principles: transparency of privacy policies, security of data and user choice, and control over how data is used, she said. "People don't like binary choices about how to use data," Wong said. "They want to be [online] on their own terms." This week, Google hosted a meeting of the Consumer Privacy Legislative Forum, a group of companies focused on getting a consumer privacy bill passed in the U.S. Congress. The group, formed in 2006, doesn't expect legislation to pass this year, but is working toward consensus on privacy issues, said Jane Horvath, Google's senior privacy counsel. The group plans to run its ideas past privacy groups and the FTC before pushing for legislation, she said. In addition, Google plans to file formal comments about the FTC's proposed privacy principles for online behavior advertising, added Peter Fleischer, Google's global privacy counsel. Among the FTC proposals: Web sites should provide clear and prominent statements that data is being collected to provide targeted ads, and companies should obtain consumer consent before using data in a different way from what the companies promised when they collected the data. Google supports the FTC's work on the privacy principles, Fleischer said, but it will raise some questions when it files its comments. For example, the FTC has asked for comments on what constitutes "sensitive data" and whether it should prohibit the use of sensitive data. For example, an anonymous search on Google for health care providers that treat AIDS may be sensitive, but it's not personally identifiable, he said. In most cases, IP (Internet Protocol) addresses are not personally identifiable -- Web sites cannot connect IP addresses to individuals in most cases, he said. The debate over what constitutes personally identifiable information is the "hardest question" in privacy, Fleischer said. "There's a grey area in between [the obvious cases], and that's what we're struggling with right now," he said. Asked about the controversy over whether Google's DoubleClick acquisition threatens people's privacy, Fleischer said one issue was lost in the debate: DoubleClick doesn't collect personally identifiable information when it serves ads. Instead, DoubleClick does collect IP addresses that give general location of the computer users and other information such as the language of the users, he said. "DoubleClick does its ad targeting anonymously," Fleischer said. Privacy groups, including the Electronic Information Privacy Center and the Center for Digital Democracy (CDD), unsuccessfully pushed the FTC to reject the Google purchase of DoubleClick, saying the combined company would hold massive amounts of personal data. Jeff Chester, CDD's executive director, was among the privacy advocates who met with Google executives this week. He praised Google for having "thoughtful" employees willing to discuss the issues, but said Google still doesn't seem to understand the privacy concerns that are part of the DoubleClick deal. "It's clear that several of the Google privacy staff don't fully comprehend the privacy implications of DoubleClick," he said. http://www.thestandard.com/news/2008...nitiatives-u-s  PrivacyFinder.org: Search, But with Privacy Peter Eckersley The level of privacy offered by search engines is generally woeful. Last year, the three big players (Google, Yahoo! and MSN) made some improvements by limiting the duration for full retention of logs about who has searched and what they've searched for. That means that after a year or two, it would be harder — though probably not impossible — for the major search engines and their advertising partners to reconstruct a complete history of your searches. Ask.com went further with their AskEraser feature, which allows users to have their logs deleted and to opt-out of being tracked (Ask.com could have done better by finding a way for opt-out to be available without a cookie). Despite these improvements, the average Internet user still has very little privacy for their search history. We have documented the measures you can take to protect yourself, but they aren't all that simple. So it's exciting to report that one small search engine is experimenting with ways to be an aide, rather than a threat, to privacy. PrivacyFinder is a research project at the CMU Usable Privacy and Security Laboratory (full disclosure: Lorrie Cranor, who heads the lab, is also on the EFF Board). It offers an interface to Yahoo! and Google, but with two notable improvements: an excellent logging/data retention policy, and a feature that shows the user information about sites' privacy policies along with the search results. That way, if two sites offer the same service but one of them is better from a privacy point of view, the user will see that quickly. The PrivacyFinder researchers tell us they've observed that people will, for instance, pay more for an item from an online store if they can see that it has an excellent privacy policy. PrivacyFinder seems to be making productive use of P3P, an old privacy standard that has, in many other respects, fallen short of expectations. If you run a search on the site, you can quickly see when one result matches your standards and others don't. Privacyfinder's logging policy is amongst the best in the industry (Ixquick is also first-rate). Privacyfinder only keeps search records for a week, unless the user explicitly opts in to being tracked. Because the CMU Laboratory wants to do research on the use of search engines, it's offering prizes for people who are willing to be tracked for research purposes. That's the way we like to see it done. Meanwhile, several other developments are in the works. New York State legislators have been talking about taking parts of the search privacy problem into their own hands. There are rumors of new startups planning to enter the "privacy search" market. And EFF is working on a scorecard for systematically evaluating the effectiveness of various privacy measures at search engines. Stay tuned to Deeplinks for future developments! http://www.eff.org/deeplinks/2008/03/search-privacy  Antigua Threatens to Allow Piracy Gov't hopes to settle trade dispute with US William Triplett The government of Antigua is likely to abrogate intellectual property treaties with the U.S. by the end of March and authorize wholesale copying of American movies, music and other "soft targets" if the Bush administration fails to respond to proposals for settling a trade dispute between the two counties, according to the lawyer representing the Caribbean island nation. The Motion Picture Assn. of America has been closely following the case with tremendous concern, an org official said, fearing that the copying could be extensively damaging and that -- worse -- a dangerous precedent could be set for other small countries angry at U.S. trade policy. "It is not our preferred option to punish the MPAA or others for the U.S. government's intransigence, but the U.S. has refused to negotiate fairly," said Mark E. Mendel, who represents Antigua. Goods and materials that would be copied include "virtually everything from pharmaceuticals to music, anything with IP protection that can be duplicated, though we'll go for softer targets first," Mendel said. Antigua has previously suggested it might retaliate as such -- with approval from the World Trade Organization -- but has never stipulated when. So far, the U.S. Trade Representative has dismissed that threat simply as a negotiating ploy. "Antigua would be breaking the law if it did that," said USTR spokesman Sean Spicer. The WTO ruled last year that Antigua was entitled to $21 million in damages because of a dispute with the U.S. over Internet gambling. But Antigua has not received WTO approval to procure its damages via reproducing and selling domestically U.S.-copyrighted goods and materials, Spicer added. "They continually engage in disinformation," Mendel responded. "The reality is, yes, we have to go before WTO and request their authorization for IP sanctions against the U.S., but we can do that at any time and the WTO will agree. That is 100% guaranteed." Mendel acknowledged his client would like such entities as the MPAA, the recording industry and Microsoft -- orgs that depend on IP protection -- to pressure the Bush administration into negotiating a "preferred" settlement, which would allow Internet gambling between Antigua and the U.S. But he insisted the threat was neither idle nor empty. "Perhaps the U.S. doesn't think we're serious," Mendel said. "We are." The case dates back to 2003, when Antigua claimed that the U.S. unlawfully prevented Antigua's online gambling operators from accessing American markets although the U.S. allowed domestic online bets for horse racing. Antigua claimed $3.4 billion in losses and took its grievance to the WTO, which agreed, but awarded only $21 million in damages. Mendel said his client has been trying ever since to work out an agreement that would allow online gambling between the two countries, but instead the U.S. has responded by "using every possible appeal, counterattack and side attack it could think of. We've been through five separate full-blown WTO proceedings on this and have won every step of the way." The most recent victory was in December, when the WTO ruled that Antigua could exact damages by ignoring IP agreements with the U.S. should a negotiated settlement fail. Mendel said the U.S. promised then to respond to proposals for settling the dispute. "We have been waiting for three months already and there's been nothing," he said. "If the U.S. doesn't come in with something by the end of March, my suggestion to the Antiguan government will be to forge ahead and impose IP sanctions." In a letter to the USTR about the potential effects of Antigua's retaliation, sent prior to December's ruling granting $21 million in damages, the MPAA wrote: "The proposed retaliation would be impossible to manage. The real and resulting economic harm would vastly exceed any amount the (WTO) might approve, even the grossly exaggerated amount ($3.4 billion) for which Antigua seeks approval, plus the economic harm would extend to other WTO members. "MPAA believes it would be very difficult to insulate other WTO members from the effects of Antigua's proposed retaliation," the letter continued. "The unfortunate reality is that the failure to offer or enforce adequate protection of intellectual property rights in Antigua could foster abuses in other countries." http://www.variety.com/article/VR111...ryid=1338&cs=1  Mukasey: Piracy Funding Terror Jordan Robertson Attorney General Michael Mukasey warned Friday that the huge profits generated from piracy and counterfeiting are increasingly flowing into the coffers of terrorist groups. In remarks to Silicon Valley executives at the Tech Museum of Innovation, Mukasey said the economy and national security of the United States are increasingly threatened by violations involving copyrighted software code, patented inventions and trademarked properties. Terror groups are taking their cues from organized crime and increasingly funding their operations from counterfeiting and piracy, he said. Mukasey said his department is devoting more resources to prosecuting intellectual property crimes, which led to a 7 percent increase in the number of IP cases filed in 2007 over the year before and a 33 percent increase over 2005. "Criminal syndicates, and in some cases even terrorist groups, view IP crime as a lucrative business and see it as a low-risk way to fund other activities," Mukasey said. "A primary goal of our IP enforcement mission is to show these criminals that they're wrong." Before Friday's speech, he met privately with representatives from companies including Apple Inc. and Adobe Systems Inc. Mukasey did not elaborate on the topics discussed in that meeting. The attorney general also met with entertainment industry executives in Los Angeles a day earlier during this three-day California trip, and did not discuss those talks. http://news.yahoo.com/s/ap/20080328/...ctual_property  How YOUR Tech Blog Posts are RIPPED OFF While You Sleep! Mike Duncan You work hard on your posts… So you get an idea for a blog post. You mull it over, finally commit to it, and start to get down to work. Now that you’re in it for the long haul there’s probably a good time sink involved. Depending on your writing style your work involved might be something like: • Researching the topic so you understand it really as well as you think you do. • Thinking about the points you are going to make, what order makes some sort of sense. • Collecting and wiring up good outbound links to more authoritative, encylopedic reference for your readers to continue on with. • (HOLY CRAP, DON’T READ THIS!!!) Thinking up a good magnetic headline to grab some interest. • Thinking about how to break up your content into manageable, scannable bits. • Searching for / creating / farming-out some for some pithy images to break the monotony of endless text. If you are into copywriting, a slow worker, disturbed by animals, etc, this process may be long and soul crushing. And the payoff is…. You birth your creation into the wild. You lord it over your friends, shamelessly promote it on a few social networks, get your mom to check it out, etc. As people add comments and you watch the visitors count in your analytics, you get that satisfying ego-boost you had hoped for. You can feel your social capital on the rise. Rad. And then, YOU ARE RIPPED OFF! Ok, so here’s my story. As avid readers of www.mikeduncan.com you’ve undoubtedly read my scintillating post SQLite on .NET - Get up and running in 3 minutes. Catchy, isn’t it? It was birthed into the world as the timestamp clearly reminds us on January 15th, 2008. People seemed to dig it, a good time was had by all. Maybe *too good* of a time. TWO DAYS after my post was out in the wild, I started seeing some interesting inbound links coming in from InfoQ, a tech news - paid story aggregator type site. While not somewhere I go often, their site is indeed large, thriving, and as it turns out, morally bankrupt. It seems that one Robert Bazinet has a story on the front page of the 250,000 unique visitors per month, page rank 7, mega-site that is InfoQ.com cleverly titled: Up and Running with SQLite on .Net in 3 Minutes Come on,…… really? That’s really what its called? You bet. So what do we find in this lovely post? You got it, exactly my post, just stripped of its sexy mikeduncan.com voice and replaced with a few business buzzwords. • The steps of what to do are the same. • And in the same order. • And the arbitrary number of minutes is the same. • And the links to the further sources are the same. • And the footer says "InfoQ.com and all content copyright © 2006-2007" !!! You’re damn right Jackie! Ok, to set the record straight, they do give a shout-out to me briefly mentioning I have a post similar to this on my site, and if you bothered to go to my site, you’d see that they are maybe-admittedly re-hashing my post? Or maybe you wouldn’t. The Pros and Cons of this intellectual larceny… So let’s see what to make of this situation in inverse pro/con order (to build suspense) Cons: • My personal work and time invested in this post is being leveraged for InfoQ / Robert Bazinet’s big-uppance. • Organic search traffic relating to SQLite on .net will ultimately be split between mikeduncan.com and InfoQ. As a corporate, constantly updated entity, they have a lot of page rank that will flow down into their version of my story, probably trumping mine in the SERPs in the long run. Pros: • InfoQ will send me some traffic I might not otherwise get from regular infoq readers who don’t already know about my post from DotNetKicks, Google, my blog feed, etc. • I gain greater *perceived authority* (if thats even possible) by being linked to from a supposedly authoritative, news publishing source. • My ego still gets boosted in some small way in that someone thought my post was worth paraphrasing and submitting. Perhaps they got $20 out of it. The *real* pro though, is I have now have this very topic to write about on mikeduncan.com, which I’m sure will be identifiable to a lot of other folks. Looking through InfoQ, there are indeed many stories just like this one that are just paraphrased versions of other bloggers hard work. Many other people are knowingly or not, in the same boat. (Maybe it’s time to do a search on InfoQ ey?) You WILL be next!!! Clearly any blog is up for thievery a source of inspiration. If indeed you as a writer get a kickback for stories are accepted on InfoQ, why not scan DotNetKicks, maybe DZone, looking for catchy stories you can paraphrase into cold, hard Jacksons? A quick look through Infoq shows a number of posts that are similarly just paraphrased summaries of bloggers work. Just picking the first one on the front page that that I recognized by the title, Implementing NOLOCK with LINQ to SQL and LINQ to Entities for instance is just a Scott Hansleman post rehashed. Again, Scott is quickly credited, but then pretty much his whole post is just copied over into the Infoq system. Scott, on one hand, being in a tech evangelist role and all around Dude, is probably fine with getting the word out however he can. On the other hand, Scott does have advertisers and runs diabetes research fundraising campaigns through his site. A part of his fundraising ability relies upon the popularity of and traffic to his authoritative site based on his original content. Maybe Scott is OK with this, maybe not. Either way I doubt InfoQ told him they were rehashing his posts. My direct boss and good friend is a lawyer, but does not play one on tv. He advised me that I could certainly send them a letter asking for the post to be removed, but would probably not really be worth his time as he had compelling video games scheduled to be played. Thinking about the above mentioned pros and cons I think I’m ok with the net gain on this one. What do YOU think? Ok, the internet is all about learning, communicating, extending what has come before, standing on the shoulders of giants, blah blah blah. I’m not really trying to push for some sort of copyright policing, I like the wild west days we are in. At the same time, when it happens to you, it’s kind of phony / corny in a Catcher In the Rye way. Particularly the InfoQ.com and all content copyright © 2006-2007 footer. What do you, esteemed readers, think? Should I just quit complaining and consider it flattery? Or is this something that as tech writers / bloggers we should be more in tune with. With Gawker Media type bloggers making 9K a month, perhaps this isn’t just bitching. Original content is certainly some kind of currency these days be it devalued US dollars, career credibility, or promoting charities. Tell me your tales! If you don’t post comments, I’ll just cut and paste some from your blogs into here anyway, copyright 2008 mikeduncan.com. Man, you’ve read this far, if you feel like it, hook a humble blogger up with some diggs or whatever. Your awesomeness will be embiggened, I promise. http://www.mikeduncan.com/tech-post-ripoff/  ‘Good’ Pirates Help Companies Sell More Products enigmax If you are downloading stuff you wouldn’t have bought in the first place, according to economist Karen Croxson, you are probably doing the company that created the product a big favor. You, Mr ‘Good’ Pirate, are telling your friends, adding to the media ‘buzz’ and driving up sales. Imagine a situation in the future where Internet pirates are accepted - maybe even recruited - to replace expensive marketing and consumer awareness teams when bringing a product to market. Imagine the reward for the pirate was a free copy of the software/media he agrees to promote. According to an economist, it could be happening right now. In her talk at the Annual Conference of the Royal Economic Society, Oxford economist Karen Croxson says that when people copy software, music and movies, it may actually help the producer. “Digital piracy has been claimed to endanger whole industries” said Ms Croxson. “A natural question to ask is: Why do some companies develop water-tight technology to safeguard their intellectual property when others appear more relaxed about copying?” Many pirates say that they would never have bought much of the stuff they downloaded or copied. If you fall into this category, you might be a ‘good’ or ‘promotional’ pirate. Croxson says that piracy is only a threat to sales when people who originally intended to buy, didn’t, and pirated instead. The others - of which there a many, many millions - never intended to buy and these, says Croxson, cannot possibly harm the seller. Far from the “all pirates are evil” cry, these pirates tell their friends, and they tell their friends and so the priceless product ‘buzz’ is generated. This consumer ‘buzz’ is difficult to put a price on, but needless to say it’s very valuable indeed. Even if companies ‘paid’ a pirate with a free copy of their product in exchange for him spreading the word about the product, it’s still a fantastic deal - especially if these ‘promotional’ pirates weren’t going to buy the product in the first instance. Also considered by Croxson are the reasons why people are tempted to copy something, which include value put on time, concerns about being caught and moral issues. Using these and other factors enables Croxson to discover piracy’s true threat to sales of a product and suggest the best responses. Due to computer games being most popular in the youth market, they are heavily protected. Although young people place a lot of value on games, they have fewer fears when it comes to copying and have more time than most to do so. It’s suggested that this could be ‘bad’ piracy, in that these activities negatively affect sales, without the ‘promotional’ benefits. On the other hand, business software companies put a lot less effort into anti-piracy measures. It’s suggested that people who use software in the course of their business place higher value on it, have less time to pirate and worry more about the legal aspects, so are less likely to pirate. Croxson said: ‘With valuable users shying away from copying, the sellers in the business software market find themselves more naturally insulated against lost sales. Those more inclined to pirate, perhaps students, probably wouldn’t have bought the product anyway, so represent virtually free promotion. This helps explain why business software companies do not put as many resources into protection as computer games manufacturers.” “Building a theoretical model of `promotional piracy’,” says Croxson, “it is possible to distinguish markets that are best advised to put considerable resource into safeguarding their products from others which may live quite comfortably with a higher incidence of digital piracy.” http://torrentfreak.com/good-pirates...roduct-080324/  60% of Photoshop Users are PIRATES! Brian Auer Yo ho, yo ho, a pirate’s life for me. We pillage, we plunder, we rifle, and loot, Drink up, me ‘earties, yo ho. We kidnap and ravage and don’t give a hoot, Drink up me ‘earties, yo ho. So here it is… the one week results from our previous poll on software piracy. In that short time, we’ve had nearly 500 photographers cast their votes and the outcome is quite interesting. It looks like Adobe’s high-end photo editing software packages (like Photoshop and Lightroom) are hot items in the pirated software market. I’m not here to make judgments or anything — I’m just presenting the results from our little study. I’d also like to mention that my computer is 100% free of pirated or “borrowed” software and that the poll results are no indication of my own habits. Each of the results below have two graphs. The first is a measure of how many of us use a particular piece of software: users versus non-users. The second graph takes the users and splits them into pirates and non-pirates. Also, I’m going to leave the polls running for a while to see how things progress over time. Wow… I expected the number of Photoshop pirates to be high, but not quite that high! 58%?!? So for every legal copy of Photoshop, there’s a pirated counterpart… and then some! An equally interesting observation from the poll is that 87% of the people who read this blog are Photoshop users of some sort. I’m sure we represent a higher density population of Photoshoppers, but my guess is that well over 50% of digital photographers have access to Photoshop. Although Lightroom isn’t quite as popular as Photoshop with the general public (with only 58% of the voters), the users of Lightroom are just as willing to pirate the software. I assumed that Lightroom would be less pirated because it’s newer software and because the price is slightly lower than that of Photoshop. I assumed wrong. Then again, if you’re going to pirate a copy of Photoshop, why not Lightroom too? We have quite a few “other software” users in the mix too. I didn’t break down the polls into every piece of software on the market, so I clumped everything other than Photoshop and Lightroom into this category. Interestingly, the rate of piracy (at 38%) is much lower than with the high-end Adobe products. I can’t imagine that other software would be more difficult to steal, so this lower number is probably a factor of popularity, price, and availability. And out of the four groups in the poll, this was the only one with absolutely no piracy. Go figure. I’m actually impressed at how many people use free and open source software for photo editing — 64%! And only 19% of those are using the software that came with their cameras. The rest is all open source and freeware/shareware. Good for you guys! Although, there’s probably some percentage of free software users who have pirated copies of commercial software. What do you guys think? Are the results surprising? Should Adobe care about this? I’m sure they’re aware of Photoshop and Lightroom being pirated, but I wonder what their position is on the topic. http://blog.epicedits.com/2008/03/28...s-are-pirates/  GT-R Waiting Game About to End Paul Duchene HARDLY a model year goes by without the debut of at least one new car that sets off a frenzied run on dealers’ showrooms. In the last decade, introductions for vehicles as disparate as the Volkswagen New Beetle, Chrysler PT Cruiser, Mini Cooper and Ford GT each resulted in months-long waiting lists, accompanied by gigabytes of Internet speculation. So far in 2008 that must-have car seems to be the Nissan GT-R, a 480-horsepower sports coupe with all-wheel drive and a full-time cheering section. It will be available in the United States in June, starting around $70,000. Nissan plans to import 2,500 GT-Rs this year and about 1,500 annually in the future. Typically, the cars that set off these stampedes carry names steeped in history or, at the least, a design that gestures to a beloved icon of the past. Why, then, is a car whose predecessors Nissan has never sold in the United States proving such a phenomenon? The 2009 GT-R may be the first car whose reputation was forged primarily in the virtual world, at least in the minds of young American enthusiasts. The GT-R is a mainstay of leading video games, notably the Gran Turismo series that Sony PlayStation fans devote hours to, and was a featured star of a promotion that linked the introduction of the actual GT-R at the 2007 Tokyo auto show with the release of a special prologue edition of Gran Turismo 5. To a much smaller group of fans in the United States — those who follow international sports car racing series — the GT-R is a high-performance hero of long standing, a car closer to meeting the definition of a supercar than any earlier effort by a Japanese automaker. While sports cars like the Toyota 2000GT and Acura NSX were memorable, they did not attain the same level of performance — or incite the same degree of lust — as European exotics. The GT-R could be different. The GT-R comes by its reputation honestly, having matured from Skyline models that trace their roots back to the late 1960s. The first GT-R version of the Skyline made its debut in 1969, lasting only a few years before oil shocks put the whole idea on hiatus. Though it was nearly two decades before the model name reappeared, the GT-R’s reputation went on to worldwide recognition, mainly on the strength of its racing successes in Japan and Australia. (Until now, the GT-R was sold only with right-hand drive.) Driving a GT-R a few years ago (the fourth-generation R34 model produced in 1999-2002 that had a role in “The Fast and The Furious” films) I came to appreciate this special machine as the automotive equivalent of a samurai sword. It seemed to be something created with such intense focus and precision that it generated its own presence. Nissan uses the sword metaphor to describe the latest GT-R, too, pointing to the “aero blade canopy” of the passenger cabin’s roofline and describing the curved form of the rear roof pillar as a sword edge. William Scott Wilson, a Florida-based writer and teacher who lived in Japan and has translated classics like “The Book of Five Rings” by the 17th-century swordsman Miyamoto Musashi, helped put the Japanese design discipline into perspective for me. Mr. Wilson recalled living in a village of craftsmen in Japan and visiting an 80-year-old sword maker, where he learned the history of the curved samurai sword, or katana, developed in the 10th century by folding and tempering steel many times to create a razor-sharp edge on a flexible blade. “When a man makes a sword, there’s kinetic energy in the steel — a spirit of deep respect for what the swordsman is doing that infuses his product,” Mr. Wilson said. “By the time it has been tempered and washed, the sword gets the spirit of the man.” Part of what makes the new GT-R so special may be the spirit of the research and development team inside Nissan that developed the car’s technology. The designers are a tight-knit group. Peter Bedrosian, Nissan’s North American product manager for the GT-R, said. “They all wear special badges and sign secondary nondisclosure forms. “Everything has to be perfect on these cars,” he said. “They took great pains to keep this new car a secret. We’ve had V.P.’s go to Japan, request to see the model and be told they can’t.” The association of the GT-R with the video game world turns out to be a two-way relationship. Not only did Nissan give GT-R data to the Sony PlayStation designers and the software developers at Xanavi Information to make sure the cars in the Gran Turismo games would be accurate, the game producers returned the favor, helping to create the car’s 11 instrument panel display screens. Mr. Bedrosian said this relationship provides a link between generations. “If you’re over 30, you have to be a real car nut to know about the GT-R,” he explained. “If you’re under 25, Gran Turismo has exposed you to it already.” http://www.nytimes.com/2008/02/24/au...issan-gtr.html  Indonesia Passes Bill to Block Porn Sites Indonesia plans to restrict access to pornographic and violent sites on the Internet after the country's parliament passed a new information bill, officials said on Tuesday. The Southeast Asian country has had a vigorous debate over pornography in recent years, exposing deep divisions in the Muslim-majority nation. "I think we all agree there's no way we can save this nation by spreading pornography, violence and ethnic hostility," Information Minister Mohammad Nuh told reporters. Nuh said that members of the public had asked the government to block sites with violent and pornographic content, concerned about their negative impact as more Indonesians gain access to the Internet. The new legislation, the Electronic Information and Transactions Law, will allow courts to accept electronic material as evidence in cases involving Internet abuse, officials said. Under the law, anyone found guilty of transmitting pornographic material, false news or racial and religious hate messages on the Internet could face up to six years in prison or a fine of 1 billion rupiah ($109,000). Edmon Makarim, an adviser for the information ministry, said the government hoped to start implementing restrictions on sites containing banned material next month using special software. Software for blocking sites would be made available for downloading on the ministry's Web site (www.depkominfo.go.id), he said, adding that it was also looking at the possibility of direct blocking. Indonesia's parliament has yet to pass a controversial pornography bill, which aims to shield the young from pornographic material and lewd acts. Earlier draft versions contained provisions that could jail people for kissing in public and criminalize many forms of art or traditional culture that hinge on sensuality, sparking criticism it could curb freedoms and hurt Indonesia's tolerant tradition. The bill has since been watered down. A court cleared the editor of Playboy Indonesia last year for distributing indecent pictures to the public and making money from them. The editor had argued the magazine was good for developing a pluralistic society, while the prosecution and Islamic hardliners said he had "harmed the nation's morals". About 85 percent of Indonesia's more than 220 million population follow Islam. (Reporting by Telly Nathalia; Editing by Ed Davies) http://uk.reuters.com/article/techno...K8242120080325  Syria Tightens Internet Monitoring, Jails Bloggers Zeina Karam Syria is cracking down more on Internet use, imposing tighter monitoring of citizens who link to the Web, as well as jailing bloggers who criticize the government and blocking YouTube and other Web sites deemed harmful to state security. The tighter hand is coming even as Syrian officials show off a press center with fast Internet access and wireless technology for journalists covering this weekend's Arab League summit. The clampdown doesn't appear to be tied to the summit. In recent days, authorities extended restrictions on Web use by requiring owners of Internet cafes to keep detailed logs of their customers, apparently to make it easier to track down anyone deemed to be a threat. The rules, conveyed orally by security agents, require Internet cafes to record a client's full name, ID or passport number, the computer used and the amount of time spent on the device. The logs must be available to show to security agents upon demand. "It's a new form of psychological pressure and part of the state's systematic intimidation of Internet users," said Mazen Darwish, a journalist who heads the independent Syrian Media Center. "It works to a certain extent in the sense that it creates a kind of self-censorship among users," he told The Associated Press. Darwish has been targeted in a crackdown on journalists. He was arrested in January as he reported on unrest over a murder in Adra, near Damascus, and is on trial before a military court for allegedly defaming state institutions. He faces up to a year in jail if convicted, he says. President Bashar Assad, who succeeded his late father, Hafez Assad, in 2000, relaxed his father's iron grip a bit by introducing the Internet and cell phones. But he has also cracked down on dissent by jailing writers and democracy activists. Almost all print and broadcast media remain state-controlled. In 2006, the group Reporters Without Borders ranked Syria among 13 "enemies of the Internet," calling it the Middle East's "biggest prison for cyber-dissidents." According to the Syrian Media Center and other rights group, there are at least 153 Web sites blocked by Syrian authorities. They include sites run by the Syrian opposition, newspapers critical of the regime and networking and video-sharing sites. Among the most popular are Facebook, which was blocked in late December, YouTube, Skype and Google's blogging engine. Users who try to access online versions of the Lebanese anti-Syria newspapers An-Nahar and Al-Mustaqbal and the Saudi-owned daily Asharq al-Awsat get blank pages. Lebanon's official Web site for slain former Lebanese Prime Minister Rafik Hariri also is blocked. Lebanese political factions opposed to Syria's influence accuse Syria of being behind Hariri's assassination, a charge the Damascus denies. The Syrian government does not comment on its Internet restrictions, but reports in Syrian media at the time Facebook was blocked said the ban was put in place to prevent Israeli users from infiltrating Syrian social networks. Ahed al-Hindi, a 23-year-old who was hauled from an Internet cafe in handcuffs and a blindfold in late 2006 for criticizing the regime on an online forum, said security services often ask cafe owners to spy on clients, providing them with software for the task. He was let go after spending a month in jail without trial, but left Syria three months later because of "nonstop harassment and intimidation" by security agents, he said. "They made life impossible and I decided to leave the country," said al-Hindi, an economics student now living in Lebanon. Rami al-Saadi, who manages an Internet cafe in Damascus, said it bothers him when security agents stop in to check on his business. "This is wrong. Of course I don't like it," he said. Still, he said Syria has come a long way in just a few years, and believes it is progress that the Internet is now available in Syria. "I remember only few years ago when we didn't even know what the Internet was," he said. The New York-based activist group Human Rights Watch said in a recent report that around 1 million of Syria's 18 million people have online access, compared to just 30,000 in 2000. "There is progress in the sense that it's become easier to be online," said Rasha Ibrahim, 24, a psychology graduate. She also argued that government controls tend to backfire. "Everything forbidden becomes more tempting," she said. http://www.azstarnet.com/allheadlines/231330  Dutch Anti-Islamic Film's Internet Site Suspended AFP An American network provider Sunday said it had suspended a website that Dutch MP Geert Wilders had reserved to post his anti-Islamic film, which has sparked wide condemnation and fears of a backlash. "Network Solutions has received a number of complaints regarding this site that are under investigation," the provider said a message posted on the Internet. Although his website is offline, Wilders on Sunday insisted he still wants to put the movie "on the internet quickly" but did not specify how. He also told the Dutch ANP news agency that he would not allow anyone to see the film before it was broadcast. Until Sunday, his site (www.fitnathemovie.com) had shown the cover of a Koran on a black background with the text: "Coming soon: Finta". Network Solutions said it investigating whether the website conforms to its guidelines, saying it cannot allow "any material in violation of any applicable law." This includes material deemed harassing, hate propaganda, threatening, harmful or "otherwise objectionable." The service provider also cites technical reasons for possibly taking the site offline including "excessive use of services which shall impair the fair use of other Network Solutions customers". Far-right lawmaker Geert Wilders plans to release a movie attacking Islam and the Koran, despite complaints from religious groups and warnings that it could provoke violent protests around the world. Wilders said in November that the 15-minute film would show the Koran was a "fascist book", a claim which has already drawn complaints from several Muslim countries, including Pakistan, Indonesia, Egypt, Iran and Afghanistan. No one has seen the film in its entirity yet but a Dutch paper which has seen some of the opening images from the film, said it shows the cover of the Koran and then images of "a decapitation in Iraq, a stoning in Iran and an execution in Saudi Arabia, where sharia (Islamic law) is applied". Dutch officials have unsuccessfully urged him to drop the project, fearing a repeat of the violent protests that erupted in many countries when European newspapers printed cartoons mocking the Prophet Mohammed. Wilders has said that he will release the film "before April 1", posting it on the Internet because he cannot find a broadcaster willing to carry it. Computer experts have warned that controversy surrounding the movie could cause network mayhem once it is put online, if too many people try to view it at the same time. Wilders has repeatedly stated that the content of his film will not violate Dutch law. On Friday a Dutch Muslim association filed a legal claim asking a court to appoint a panel of censors to view the film before it is aired in order to see if there is a reason to ban it. The court is set to deliver its ruling next Friday but Wilders has said that he would try to release the film before than to avoid having to show it to censors. Dutch film-maker and polemicist Theo Van Gogh was murdered by an Islamic extremist in Amsterdam in 2004 after he made a short film attacking Islam's treatment of women. http://afp.google.com/article/ALeqM5...XyoHS5KGajzC9Q  Dutch Critic of Islam Launches Anti-Koran Film Emma Thomasson and Alexandra Hudson Dutch lawmaker Geert Wilders launched a film on Thursday that accuses the Koran of inciting violence and warns that Muslim immigrants threaten the West, prompting the government to appeal for calm. The film "Fitna" was posted on his Freedom Party's Web site (www.pvv.nl), which crashed soon afterwards. But it could still be viewed on a file-sharing Web site in English and Dutch. Dutch broadcasters had refused to show the film and a U.S.-based web service which Wilders had planned to use deactivated the site at the weekend after receiving complaints. The Dutch government is anxious to avert the kind of Muslim backlash Denmark suffered in 2006 over cartoons of the Prophet Mohammad. Prime Minister Jan Peter Balkenende said on Thursday he rejected the film's attempt to link Islam with violence. Wilders has been under heavy guard because of Islamist death threats since the 2004 murder of Dutch director Theo van Gogh, who made a film critical of Islam's treatment of women. "Fitna," a Koranic term sometimes translated as "strife," intersperses shots of the September 11, 2001 attacks and other bombings with quotations from the Koran. "Prepare for them whatever force and cavalry ye are able of gathering to strike terror, to strike terror in the hearts of the enemies of Allah and your enemies," the first quote reads. The film warns that the rising number of Muslims in the Netherlands and the rest of Europe threatens democratic values. After the caption "The Netherlands in the future?" the film shows images of gay men being executed, children with bloody faces, a woman being stoned and another of genital mutilation. It shows an image of the Koran followed by the sound of ripping paper: "The sound just heard was a page being torn from a phone book, as it is not for me but for Muslims themselves to tear out the hate-filled verses from the Koran," a caption says. After the words "Stop Islamisation. Defend our freedom," the film concludes with a cartoon of the Prophet Mohammad with a bomb under his turban that was originally published in Danish newspapers, accompanied by the sound of ticking. "We believe it serves no purpose other than to cause offence," Balkenende told a news conference. "But feeling offended should never be used as an excuse for aggression and threats." He added he was heartened by the initial restraint of Dutch Muslims. Propaganda? Brahim Bourzik, a spokesman for a Dutch Moroccan group, said mosques would open their doors on Friday to help defuse tension. "It is not a film -- it is propaganda. All the elements have been seen before, there is nothing new in it," he said, adding he hoped there would not be an angry reaction at home or abroad. Demonstrators have already taken to the streets from Afghanistan to Indonesia to burn Dutch and Danish flags, while the governments of Pakistan and Iran have sharply criticized the film. About a thousand people protested against Wilders in Amsterdam on Saturday. NATO had expressed concern the film could worsen security for foreign forces in Afghanistan, including 1,650 Dutch troops. Earlier this month, Dutch security officials raised the national risk level to "substantial" because of the Wilders film and perceptions of an increased al Qaeda threat. Van Gogh's killing by an Islamist militant triggered a wave of unrest in the Netherlands, home to almost 1 million Muslims out of a total population of 16 million. Wilders, a right-winger, said he hoped the film would not put Dutch people at risk: "If something should happen, which I hope won't be the case, then the people who use threats or violence, they are responsible." Dutch exporters have expressed fears of a possible boycott in the Muslim world, though trade with such countries makes up only a small amount of total exports. There is also concern for 25,000 Dutch citizens living in Muslim countries. (Additional reporting by Niclas Mika, Foo Yun Chee and Gilbert Kreijger; editing by Andrew Roche) http://www.washingtonpost.com/wp-dyn...032702082.html  Czech Far-Right Party Offers to Post Dutch Anti-Quran Film A Czech far-right party has offered to help a Dutch lawmaker distribute an anti-Quran film on the Internet if it is banned from being released in the Netherlands. The offer was made after a U.S. company that provides Web hosting services suspended the site promoting Geert Wilders' 15-minute film, which has sparked demonstrations in the Netherlands even before it has been shown. Hosting provider Network Solutions said it had suspended the promotional Web site until its sponsor could show that the plans for the site did not violate the service's standards. "Over the last month, Network Solutions received a number of complaints," prompting it to seek reassurance about the content, it said in a statement. "We are still waiting to hear from our customer. In the interim, we have temporarily suspended the site." The move has been criticized in tech circles, but the company denied it was "taking any action to limit freedom of speech or to preemptively censor content," saying that it was responding to complaints in this case. The statement did not elaborate on the nature of the complaints. Dutch officials fear the movie could prompt violent protests in Muslim countries, similar to those two years ago after the publication of cartoons of the Prophet Muhammad in a Danish newspaper. The Czech Republic's small National Party offered to release the film on the Internet using one of its servers, the party said in a message posted on its Web site. The exact contents of the movie, due to be released by March 31, are unknown, but Wilders has said it will underscore his view that Islam's holy book is "fascist." He has said he will release his movie on the Internet after television stations refused to air it. Thousands demonstrated in central Amsterdam against Wilders' film Saturday in a protest intended to show that he does not represent the whole country. Wilders heads a reactionary party with nine seats in the 150-member Dutch parliament, elected on an anti-immigration platform. http://www.siliconvalley.com/news/ci_8691339  China Orders Shutdown of 25 Video Entertainment Web Sites AP China has ordered more than two dozen video entertainment Web sites to shut down under new rules governing such sites, a broadcast regulator said on its Web site Friday. The new rules, which took effect Jan. 31, bans providers from broadcasting video that involves national secrets, hurts the reputation of China, disrupts social stability or promotes pornography. Providers are required to delete and report such content under the rules. The State Administration of Radio, Film and Television, or SARFT, said in a statement on its Web site Friday that officials have completed a two-month audit on video entertainment and video sharing Web sites based on the new rules and decided to shut down 25. Another 32 have been slated to be "punished" - although it wasn't immediately clear what that entailed. Popular video sharing Web site Tudou.com was one of those listed for punishment. The list included few major players. SARFT said in its statement dated Thursday that most of the punished sites broadcast video containing pornography or violence, or showed movies or documentaries that "endangered national security and national interest." http://www.siliconvalley.com/news/ci...nclick_check=1  Cyber Attacks Target Pro-Tibet Groups Brian Krebs Human rights and pro-democracy groups sympathetic to anti-China demonstrators in Tibet are being targeted by sophisticated cyber attacks designed to disrupt their work and steal information on their members and activities. Alison Reynolds, director of the Tibet Support Network, said organizations affiliated with her group are receiving on average 20 e-mail virus attacks daily. Increasingly, she said, the contents of the messages suggest that someone on one or more of the member groups' mailing lists has an e-mail account or computer that has already been compromised. On March 18, as protests in Tibet intensified, a technology specialist working with Reynolds's group sent a message to members warning them to expect a sharp increase in e-mail and other cyber attacks against groups rallying the international community against China's crackdown. Less than 24 hours later, Reynolds said, someone sent the exact same message out to the list, urging recipients to review an attached Microsoft Word document for online safety instructions (file-named "cyberattack.doc"). The attachment included a Trojan horse program that opened a "backdoor" on any computer used to open the file, giving the senders remote access over the system. "If successful, these attacks can impact the safety of the people we work with, but the other part of this is it seems they're trying to make it more difficult for us to function effectively, to disrupt our activities," Reynolds said. Sharon Hom, executive director of the New York-based Human Rights in China, said the group's 25 member organizations worldwide have reported a marked upswing in the number and sophistication of e-mail virus attacks. In 2006, the group intercepted just two targeted e-mail attacks, and by the end of last year that number had grown to 40. In the first three months of 2008, the group's members have received more than 100 such targeted attacks. Experts say attributing such attacks to any one group or government is extremely difficult, as computer systems that appear to be the source of malicious activity online often are controlled by persons or groups using computers in completely different locations. But Reynolds said these types of sustained, targeted attacks suggest a level of organization, tenacity and degree of commitment not typically seen in attacks by individual hackers. "They're really trying to disrupt the Tibetan movement, and whoever is perpetrating this is doing it on full-time basis," she said. A handful of recent targeted attacks shared the same Internet resources and tactics in common with those used in a spate of digital assaults against number of major U.S. defense contractors, said Maarten Van Horenbeeck, an incident handler with the SANS Internet Storm Center, Bethesda, Md.-based organization that tracks online security trends. According to a January article in Air Force Online, a series of e-mail attacks originating in China targeted 28 defense contractor locations in the United States late last year. The story named specific Beijing-based Internet addresses that the FBI later determined were the origin of the attacks. Van Horenbeeck, who provides security and technical advice to several Tibetan groups, said he has uncovered evidence that those same numeric Internet addresses were used in targeted attacks against Students For a Free Tibet, another New York-based human rights group. The attacks on pro-Tibet organizations are not the first to be tied to computers in China. The Washington Post reported March 21 that the FBI is investigating whether hackers in China targeted a group working for human rights in Darfur, the war-torn province of Sudan. China has economic and strategic interests in the African nation's oil fields. Van Horenbeeck said the danger with the e-mail viruses involved in the attacks is that they are so hand-crafted and new that they usually go undetected by dozens of commercial anti-virus scanners on the market today. "Last week, I had two of these samples that were detected by two out of 32 different anti-virus scanners, and another that was completely undetected," he said. The specificity of information sought in the targeted attacks also suggests the attackers are searching for intelligence that might be useful or valuable to a group that wants to keep tabs on human rights groups, said Nathan Dorjee, a graduate student who provides technology support to Students for a Free Tibet. Dorjee said one recent e-mail attack targeted at the group's members included a virus designed to search victim's computers for encryption keys used to mask online communications. The attackers in this case were searching for PGP keys, a specific technology that group members routinely use to prevent outsiders or eavesdroppers from reading any intercepted messages. Dorjee said the attacks have been unsettling but ineffective, as the Students for a Free Tibet network mostly operates on more secure platforms, such as Apple computers and machines powered by open source operating systems. "The fact that we're being attacked with the same resources thrown at multi-billion defense contractors is flattering," said Lhadon Tethong, executive director of Students for a Free Tibet. "It shows that we really are an effective thorn in the side of a repressive regime." http://www.washingtonpost.com/wp-dyn...032102605.html  FBI Opens Probe of China-Based Hackers Ellen Nakashima and Colum Lynch The FBI has opened a preliminary investigation of a report that China-based hackers have penetrated the e-mail accounts of leaders and members of the Save Darfur Coalition, a national advocacy group pushing to end the six-year-old conflict in Sudan. The accounts of 10 members were hacked into between early February and last week, and the intruders also gained access to the group's Web server and viewed pages from the inside, the group said yesterday. The intruders, said coalition spokesman M. Allyn Brooks-LaSure, "seemed intent on subversively monitoring, probing and disrupting coalition activities." He said Web site logs and e-mails showed Internet protocol addresses that were traced to China. The allegation fits a near decade-old pattern of cyber-espionage and cyber-intimidation by the Chinese government against critics of its human rights practices, experts said. It comes as calls for a boycott of the 2008 Beijing Olympics have been mounting since China's crackdown on Tibetan protesters last week. The coalition, headquartered in Washington, has been a vocal critic of China's support for the Sudanese government and its refusal to allow anyone to pressure Khartoum to end the conflict. The group has urged China -- Sudan's chief diplomatic sponsor, major weapons provider and largest foreign investor and trade partner -- to use its position as a member of the U.N. Security Council to bring peace to the region. "Someone in Beijing is clearly trying to send us a message," coalition President Jerry Fowler said. "But they're mistaken if they think these attacks will end efforts to bring peace to Darfur." A senior Chinese official, who spoke on the condition of anonymity, said the allegation is false. http://www.washingtonpost.com/wp-dyn...032003193.html  Bell Canada Throttles Wholesalers, Doesn't Bother To Tell Them Karl Users of the Canadian family-run ISP Teksavvy (which we profiled last year) have started noticing that Bell Canada is throttling traffic before it reaches wholesale partners. According to Teksavvy CEO Rocky Gaudrault, Bell has implemented "load balancing" to "manage bandwidth demand" during peak congestion times -- but apparently didn't feel the need to inform partner ISPs or customers. The result is a bevy of annoyed customers and carriers across the great white north. Says Gaudrault in our forums: Quote:
Quote:
http://www.dslreports.com/shownews/B...ell-Them-92915  Can We Police Canadian Content on the Internet? That's a thorny question the CRTC is mulling over as pressure mounts from producers and unions to protect their material Chris Sorensen and Rita Trichur Nearly a decade after adopting a strict hands-off approach to the Internet, Canada's broadcast watchdog is once again mulling the thorny issue of regulating Canadian content online as people across the country turn to their computers for news and entertainment. The Canadian Radio-television and Telecommunications Commission has drawn up a draft report on "new media," obtained by the Toronto Star, calling for further "discussion and validation" of the issue amid pressure from Cana- dian-content creators who are concerned about traditional programming that's increasingly finding its way to the unregulated Web. Such developments, observers say, were not clearly envisioned in 1999 when the CRTC essentially ruled that the Internet was to be a regulatory-free zone. "I think that they (CRTC) feel that being stuck back in 1999 makes them look kind of foolish," said Tim Richardson, an electronic-commerce and technology expert at the University of Toronto. But the mere notion of regulating online content in 2008, regardless of the motive, is certain to draw howls of protest from those who believe the heavy hand of government has no place on the Internet, where a "Wild West" ethos is often credited for encouraging innovation, personal choice and the free exchange of ideas. Richardson said Canadians are "incredibly" fixated on the regulation of Canadian content and questioned enforceability of such so-called Can-con rules given that the Internet is effectively borderless. "You know, Canadians want to have rules and regulations about things. The Americans will say: `Well, basically, if nobody is being killed, let's let it be.'" While the CRTC has not yet committed to taking action, the regulator nevertheless acknowledges in its report that "there is minimal investment in producing ancillary or new online broadcasting content," although it says broadcasters are repurposing their content for online consumption. The report cites research that shows that 19 of the top 20 websites visited by Canadians originate outside the country's borders. "Canadians have an increased ability and opportunity to effectively participate in the new media broadcasting environment and to see themselves reflected in this global environment," said the document, which was distributed to stakeholders and will be followed by a final report in May. Public hearings will also be scheduled. The CRTC goes on to ask how Canadian programming has "flourished in the new media environment" and whether there is a need to "measure new media broadcasting performance indicators." Should its exemption be reversed, the CRTC's mandate would likely be limited to potentially overseeing online content offered by TV networks or radio stations. So-called "user-generated content" – personal videos uploaded to YouTube, for example – would be unaffected by any policy change. A CRTC spokesperson declined to comment on the document, which hasn't been released publicly. CRTC chair Konrad von Finckenstein told the International Institute of Communications last October that when the CRTC first looked at new media in 1999, "it offered little competition to traditional broadcasters and there seemed no need to stimulate its carriage of Canadian content." He also conceded "a lot has changed" since then. "For us at the CRTC, the guiding principle in our approach to new media will be exactly the same one that we have followed in our approach to the traditional media: to regulate as effectively as we can to further the two primary goals of the Broadcasting Act – Canadian content and full access to the system for all Canadians," he said. Vast improvements in both computer technology and high-speed broadband availability means Canadians are today more likely to use the Internet as a source of broadcast media by downloading music, podcasts and even full TV episodes, according to the draft report. It says more than half of Canadians with an Internet connection now download videos, with younger Canadians now spending roughly the same amount of time online as they do watching TV – about 15 to 17 hours a week. Broadcasters, meanwhile, have been compelled to push more of their content online as they try to adapt to the changing viewing habits of their audiences, with advertisers following closely behind. That has left Canadian content creators concerned about an industry shift from a regulated environment to one where few rules exist. "We're not looking for regulation, per se, but rather incentives to promote Canadian production on the Internet," said Stephen Waddell, national executive director of the Alliance of Canadian Cinema, Television and Radio Artists, or ACTRA. "If there's no opportunity for Canadian programming or content on the Net, where will Canadian performers, writers and directors be able to work?" ACTRA is one of several stakeholders proposing a levy on Internet service providers, or ISPs, to help fund the creation of digital content in the same way that satellite and cable TV providers are required to use a portion of their revenues to help fund Canadian television programs. But critics say placing a "regressive tax" on ISPs is the wrong approach, since it could limit access to the Internet among lower-income Canadians. "I'm a huge fan of Canadian content and I think we do need to subsidize it," said Philippa Lawson, the director of the Canadian Internet Policy and Public Interest Clinic. "But that subsidy should come through the general tax system rather than a surcharge on what has really become a basic service." Officials at Rogers Communications Inc. and Bell Canada Inc., two of the country's largest Internet providers, declined to comment before a final report is published. Even if the CRTC were to decide to regulate Canadian content online, some say, the issue would be a non-starter with the current federal Conservative government and its free-market ideology. As well, the CRTC is expected to issue a final decision this year on reforming the Canadian Television Fund, which could include, among other proposals, establishing new funding up to $25 million from current revenues to support Canadian new media programming. http://www.thestar.com/article/349575  Fingerprint Scheme at Heathrow's Terminal 5 Challenged BAA's plan to require fingerprints from both international and domestic passengers who use the terminal may violate the U.K. Data Protection Act; Thursday's opening of the £4.3 billion terminal may be delayed Plans to fingerprint millions of passengers at Heathrow's new Terminal 5 could be illegal and have been challenged by the U.K. data protection watchdog. The Information Commissioner's Office warned airport operator BAA that the security measure, designed to stop terrorists getting into the country, may breach the Data Protection Act. The Telegraph's Nick Allen writes that the move led to fears the planned operational opening of the £4.3 billion terminal on Thursday could be delayed causing flight chaos. Terminal 5 was officially opened by the Queen on 16 March. BAA said it was in negotiations with the Commissioner over fingerprinting but insisted there was no prospect of the row delaying the opening. Under the plan all four million domestic passengers using Terminal 5 annually will have their fingerprints taken when they first go through security. They will then be checked again at the gate. BAA said the measure was required because Terminal 5 will host domestic and international passengers who will be sharing lounges and public areas after checking in. Without fingerprinting, terrorists, criminals, and illegal immigrants could arrive at Heathrow on a transit flight then exchange boarding passes with a colleague in the departure lounge and join a domestic flight to enter the U.K. without being checked by immigration authorities. Deputy Information Commissioner David Smith questioned why BAA needed to use fingerprinting at Heathrow when other airports like Gatwick and Manchester rely on photographs to ensure security at their common departure lounges. He said photographs were "less intrusive" and BAA's case for fingerprinting at Heathrow had not been made. Smith said: "If we find there is a breach of data protection legislation we would hope to persuade them to put things right. If that is not successful we can issue an enforcement notice. If they don't comply, it is a criminal offence and they can be prosecuted." A leading barrister has already informed BAA that he will refuse to give his fingerprints, describing the process as an "Orwellian" abuse of civil liberties. Nigel Rumfitt QC, a specialist in serious crime including terrorism, said it was a move toward a "database state" and Britain would become a nation that "restricts the internal movement of its citizens". BAA said it would destroy information from fingerprinting within 24 hours, in accordance with the Data Protection Act, and it would not be passed on to police. A spokesman said: "It does not include personal details nor is it cross-referenced with any other database." The airport operator said that once common departure lounges had been decided on, fingerprinting was the "most robust" way of ensuring security. The Home Office said BAA was required to ensure that arrangements at Terminal 5 did not breach border security but there was no requirement for that to involve fingerprinting. A spokesman said: "Our primary concern is that the UK border is secure and we won't allow BAA to have a common departure lounge unless they ensure the border is secure. They presented us with this plan, which we are happy secures the border. The design of the plan is a matter for BAA." http://hsdailywire.com/single.php?id=5809  CCC Publishes the Fingerprints of German Interior Minister A guide shows how to collect fingerprints. With a spectacular protest action of the Chaos Computer Club (CCC) against the progressive recovery of biometric data. In the current edition of the club magazine The Datenschleuder publish the hacker's fingerprint by German Interior Minister Wolfgang Schauble. The hackers want to be against the increasing collection of biometric data to defend themselves. Especially the storage of fingerprints in the E-Pass bad encounters the CCC. "We want to work with the publication of a warning signal," explains CCC spokesman Dirk Engling towards heise online. Fingerprints were not so sure how the policy claims Engling said: "They do not belong in safety application - and certainly not in the E-Pass." The hacker did not at the footprint of Schäuble's fingerprint respectively - the issue is also a completed fingerprint dummy. The thin foil is glued to the tip of the finger, for example, fingerprint scanners to deceive. "We recommend that the imprints on erkennungsdienstlichen treatments, a visa to enter the United States, for the intermediate landing at Heathrow, but also in the local supermarket, and - prophylactically - at the touch of many possible glass surfaces using" says Engling. The CCC assured that the published fingerprint was genuine. A sympathizer of the club have a glass of the hackers transferred from the interior minister, during a panel discussion drunk. The hacker secured the fingerprint and produced in small nächtelanger work dummies for the booklet. A total of 4000 copies of the booklet have been printed - more than 2000 of them are currently on the road to the members of the CCC. Schäuble is not the only politician on whose fingerprint is the hacker apart. In a "biometric scrapbook" published a wish list of politicians whose fingerprints they still want to publish. Besides Schäuble will include German Chancellor Angela Merkel and Bavarian Prime Minister Guenther Beckstein on the list. Open sight light of the CCC says it seriously: In addition to the biometric scrapbook, the hackers published a guide on how to fingerprints and ideally secure the club through the post. The publication of the fingerprint involves not only political but also legal explosives. That the Chaos Computer Club with the publication may violate the federal Privacy Act and other laws, provides Engling left. So just the Federal Interior Ministry before the introduction of the e-passport stressed that it was very little difference between a passport photograph and fingerprint electronically stored there. Prior to the publication of the club had also brought legal advice, "Our lawyer does not handle against the publication of the fingerprint in the Datenschleuder." The view is not shared by all lawyers. "I can well imagine that the affected politicians and prosecutors will attempt to publish with the usual presserechtlichen tools to prevent and to bring a charge," explained Ulrich Wehner of the Berlin law firm Buchheim and partners. "With the collection of fingerprints and their use to produce a Fingerabdruckattrappe there is a risk an administrative or even a criminal offence." At the same time, the attorney attested to the Chaos Computer Club an impressive examination of the internal security issue: "If journalists and citizens to do what the government millions and increasingly through collection and use of biometric data happens under circumstances is the prosecutor at the door." Update: In a first opinion on Saturday afternoon indicated the Federal Interior Ministry unimpressed: "That one fingerprints of a glass can decrease, it has been known for years," said a spokeswoman of the Ministry towards heise online. The concept of e-passport will not be questioned. Whether the actual fingerprint to the Wolfgang Schauble, the Ministry could not yet confirm. Also possible legal action against the CCC would not exclude the spokeswoman. (Torsten Kleinz) / (db / c't) This page was automatically translated from German. View original web page.  Intelligent Wireless Networks Promoted by European Consortium The proliferation of wireless communication-enabled embedded systems will have significant effects in areas from emergency management to critical infrastructure protection to healthcare and traffic control; European consortium to promote idea From traffic lights to mobile phones, small computers are all around us. Enabling these embedded systems to create wireless communications networks automatically will have significant effects in areas from emergency management to critical infrastructure protection to healthcare and traffic control. Networks of mobile sensors and other small electronic devices have huge potential, ICT Results reports. Applications include emergency management, security, helping vulnerable people to live independently, traffic control, warehouse management, and environmental monitoring. One scenario investigated by European researchers was a road-tunnel fire. With fixed communications destroyed and the tunnel full of smoke, emergency crews would normally struggle to locate the seat of the blaze and people trapped in the tunnel. Wireless sensors could cut through the chaos by providing the incident control room with information on visibility, temperatures, and the locations of vehicles and people. Firefighters inside the tunnel could then receive maps and instructions through handheld terminals or helmet-mounted displays. For this vision to become reality, mobile devices have to be capable of forming self-organizing wireless networks spanning a wide variety of communications technologies. Developing software tools to make this possible was the task of the RUNES project (for Reconfigurable Ubiquitous Networked Embedded Systems). Ad-hoc mobile networks are very different from the wireless computer networks in homes and offices, explains Dr. Lesley Hanna, a consultant and dissemination manager for RUNES. Without a human administrator, an ad-hoc network must assemble itself from any devices that happen to be nearby, and adapt as devices move in and out of wireless range. While office networks use powerful computers with separate routers, the building blocks of ad-hoc mobile networks are low-power devices which must do their own wireless routing, forwarding signals from other devices that would otherwise be out of radio range. The Week in Review is edited and published by Jack Spratts. A typical network could contain tens or even hundreds of these embedded systems, ranging from handheld computers down to "motes": tiny units each equipped with a sensor, a microcontroller, and a radio that can be scattered around an area to be monitored. Other devices could be mounted at fixed points, carried by robots, or worn as "smart clothing" or "body area networks." Wireless standards are not the issue: Most mobile devices use common protocols, such as GSM, Wi-Fi, Bluetooth, and ZigBee. The real challenge, suggests Hanna, is to build self-managing networks that work reliably on a large scale, with a variety of operating systems and low-power consumption. The EU-funded RUNES covered twenty-one partners in nine countries. RUNES was led by Ericsson, but it had an academic bias, with twice as many universities as industrial partners, and most of the resulting software is publicly available. RUNES set out to create middleware: Software which bridges the gap between the operating systems used by the mobile sensor nodes, and high-level applications that make use of data from the sensors. RUNES middleware is modular and flexible, allowing programmers to create applications without having to know much about the detailed working of the network devices supplying the data. This also makes it easy to incorporate new kinds of mobile device, and to re-use applications. Interoperability was a challenge, partly because embedded systems themselves are so varied. At one end of the spectrum are powerful environments, such as Java, while at the other are simple systems designed for wireless sensors. For devices with small memories, RUNES developed middleware modules that can be uploaded, used to carry out specific tasks, and then overwritten. Project partners also worked on an operating system and a simulator. Contiki is an open-source operating system designed for networked, embedded systems with small amounts of memory. Simics, a simulator allowing large networks to be tested in ways that are impractical with real hardware, is commercially available from project partner Virtutech. Back to the tunnel fire scenario: It was valuable in demonstrating what networks of this kind can achieve. Using real sensor nodes, routers, gateways, and robots developed during the project, a demonstration setup showed how, for instance, a robot router can manoeuvre itself to cover a gap in the network’s wireless coverage. “A lot of people have been looking at embedded systems networking, but so far there has been a reluctance to take the plunge commercially,” says Hanna. “RUNES’ open-source model is an excellent way to stimulate progress, and it should generate plenty of consultancy work for the academic partners.” http://hsdailywire.com/single.php?id=5798  Satellite Radio Merger Gets Antitrust OK Peter Kaplan and Randall Mikkelsen Sirius Satellite Radio's (SIRI.O: Quote, Profile, Research) $4.59 billion purchase of rival XM Satellite Radio (XMSR.O: Quote, Profile, Research) was given antitrust clearance on Monday as the Justice Department concluded consumers have many alternatives, including mobile phones and personal audio players. Investors sent shares of both companies sharply higher even though the Federal Communications Commission must still approve the combination of the only two U.S. providers of satellite radio, a deal first announced in February 2007. In a victory for Sirius Chief Executive Mel Karmazin, who lobbied hard for the deal, the Justice Department agreed the satellite radio companies face stiff competition from traditional AM/FM radio, high-definition radio, MP3 players and programming delivered by mobile phones. "Competition in the marketplace generally protects consumers and I have no reason to believe that this won't happen here," Justice Department antitrust chief, Thomas Barnett, told a conference call with reporters. The traditional radio industry, consumer groups and some U.S. lawmakers had criticized the deal, which would bring entertainers such as talk show host Oprah Winfrey and shock-jock Howard Stern under one roof. The National Association of Broadcasters, which fought against the deal, said the Justice Department had granted XM and Sirius a "monopoly" and called the decision "breathtaking." Sirius and XM, which are losing money, each currently charge subscribers about $13 a month for more than 100 channels of news, music, talk and sports. New York-based Sirius' programming includes lifestyle guru Martha Stewart and NFL Football while Washington, D.C.-based XM is home to Bob Dylan's radio show and Major League Baseball. The Justice Department said the combination would lead to "substantial" cost saving steps such as consolidating the line of radios they offer. It said those savings would "most likely to be passed on to consumers in the form of lower prices." XM stock ended Monday up 15.5 percent to $13.79, while Sirius closed up 8.6 percent to $3.15, both on Nasdaq. At that price for Sirius' stock, the deal, in which 4.6 shares of Sirius are to be exchanged for each XM share outstanding, is worth $4.59 billion. AWAITING FCC DECISION The antitrust decision shifts the spotlight to the FCC, which must determine whether the XM-Sirius is in the public interest, and whether to enforce its 1997 order barring either satellite radio company from acquiring the other. A source at the FCC said Chairman Kevin Martin has yet to make a proposal either approving or opposing the XM-Sirius combination, but has asked the agency's staff to draft documents for different possible outcomes. This source said the FCC could be strongly influenced by the Justice Department decision. "I think it would be hard to go in the complete opposite direction," said the source. Analysts at Stifel Nicolaus said the FCC could impose conditions, such as requiring the companies to adhere to promises Karmazin made to Congress last year. Karmazin promised lawmakers that a combined company would offer packages of channels that customers could pick on an "a la carte" basis, and that customers would be able to block adult channels and get a refund for those channels. In addition, Stifel Nicolaus said, the FCC also may require Sirius and XM to promise that all existing satellite radios will continue to work after the companies are combined. David Bank, an analyst with RBC Capital Markets, was optimistic about FCC approval. "Now it's past DOJ, and we feel pretty optimistic it will get through the FCC," he said. The Justice Department's decision provoked immediate criticism from a key lawmaker in Congress, Senate antitrust subcommittee chairman Sen. Herb Kohl, a Wisconsin Democrat. Kohl took the department to task for "failing to oppose numerous mergers which reduced competition in key industries, resulting in the Justice Department not bringing a single contested merger case in nearly four years." "We urge that the FCC find the merger contrary to the public interest and exercise its authority to block it," Kohl said in a statement. Sirius and XM said in a brief statement that they had received antitrust clearance and that their deal was still subject to FCC approval. (Additional reporting by Diane Bartz; editing by Tim Dobbyn) http://www.reuters.com/article/techn...00918420080325  Banks Balk at Paying for Clear Channel Deal Michael J. de la Merced and Andrew Ross Sorkin The $19.5 billion sale of the radio broadcaster Clear Channel Communications to two private equity firms is in jeopardy. This time, however, instead of the buyers balking, the banks that had agreed to finance the deal have become apprehensive. Clear Channel and the private equity buyers may go to court to try to force the banks to complete the buyout, according to people briefed on the negotiations, who were given anonymity because they were not authorized to discuss the deal. The legal threat is the latest indication that the banks have become reluctant to put up the money for the sale, these people said. Earlier, the banks proposed that the buyers — Bain Capital and Thomas H. Lee Partners — put down more cash and agree to stricter repayment terms. The buyout firms have refused. Among the lenders are Citigroup, Deutsche Bank, Morgan Stanley, Credit Suisse, the Royal Bank of Scotland and Wachovia. Negotiations continued on Tuesday night, these people said, but if a deal is not reached, Clear Channel and the two private equity firms are expected to file their lawsuit, possibly as soon as Wednesday. Clear Channel’s problems are the most recent instance of a private equity deal tumbling into court, as the squeeze in the credit markets has disrupted the buyout world. The cheap debt that powered the recent two-year buyout boom has disappeared, forcing the banks to sell those loans and bonds at steep discounts. At the same time, the acquisition business has cooled with private equity firms largely sidelined because they are unable to get financing from the banks. The backlog of unsold debt from already completed deals — estimated at $130 billion for the loans alone — has forced banks to take billions of dollars in write-downs. While those write-downs have been only a small part of the losses that the banks have reported so far, many analysts expect problems with leveraged loans to grow. Already, several other buyouts have ended in court, including those for Sallie Mae, the student-loan lender, and United Rentals, the equipment rental company. Sallie Mae settled with its buyers while a Delaware judge ruled that United Rentals could not force its buyer, Cerberus Capital Management, to finish the deal. Many investors have long regarded the sale of Clear Channel, first announced in late 2006, as one of the private equity deals most likely to fall apart. That has been reflected in its stock price, which has seesawed despite the buyers’ insistence that the deal would go through. A cornerstone of the buyers’ argument is that the financing was rock solid, with few outs for the lenders. It is possible that the banks are willing to take their chances in court, given the estimated $20 billion in debt needed to complete the deal. The breakup fee is $660 million. By financing the deal, the banks would likely record an immediate loss of $3 billion based on the 15 percent discount that buyout-related debt is trading at in the markets, these people said. Clear Channel, the nation’s No. 1 owner of radio stations and based in San Antonio, sued another buyout firm, Providence Equity Partners, earlier this year to complete the purchase of its television unit. That was quickly settled, but was replaced by another lawsuit — this time by Wachovia, which was financing the television station sale, against its client, Providence. That second lawsuit was settled little more than a week ago. http://www.nytimes.com/2008/03/26/bu...6radio.html?hp  FCC Allows DIRECTV and Dish to Downconvert Broadcast HD FCC chairman Kevin Martin originally wanted satellite operators to offer full HD carriage by February 2009. However, DIRECTV and the Dish Network complained his proposed rule would damage their ability to compete with cable. DIRECTV and Dish Network won a major victory last week when the FCC allowed them to downconvert the high-definition signals of broadcast stations, in an effort to save bandwidth.. The satellite operators, with a combined 30 million subscribers, persuaded FCC officials that they lacked the channel capacity to provide every eligible station in high-definition immediately. They insisted that they needed several years to prepare for a full HD carriage requirement. Under the new ruling, the “carry one, carry all in HD” principle kicks in when a satellite company starts carrying local signals in high-definition. The satellite operators have until 2013 to carry all stations in HD within any market where they have elected to carry any station’s signal in the high-definition format. The satellite deal is far better than the one offered to cable operators by the FCC. The commission did not announce the vote or release the text of the rules, though an FCC official said it was a unanimous vote. FCC chairman Kevin Martin started off negotiations by requiring the satellite operators to offer full HD carriage next February, coupled with a market-by-market waiver process. However, he scrapped his original plan after DIRECTV and the Dish Network complained his proposed rule would damage their ability to compete with cable. As part of the new deal, the FCC demanded that DIRECTV and Dish comply with its benchmarks. For example, by Feb. 17, 2010, the operators need to provide full HD carriage in 15 percent of their HD markets. Dish Network has 35 HD markets today. If a 15 percent quota were in place today, EchoStar would have a “carry one, carry all in HD” obligation in five markets. The benchmark jumps to 30 percent in the second year, 60 percent in the third and 100 percent in the fourth. Because the FCC didn’t specify the markets that had to be served, DIRECTV and Dish Network are free to pursue a large-market strategy, which could keep rural consumers waiting a long time for their local TV signals in HD via satellite. Cable, for now, gets a much poorer deal. The commission requires cable carriage of TV signals in digital and analog formats for three years for any station that demands cable carriage after Feb. 17, 2009. In some cases, this leads to triple carriage. In February, C-SPAN, Discovery Communications and The Weather Channel sued the FCC in a federal appeals court over the digital TV station carriage mandates. http://broadcastengineering.com/hdtv...ctv_dish_0324/  Proposal Would Curb Web Tracking for Advertisements Louise Story After reading about how Internet companies like Google, Microsoft and Yahoo collect information about people online and use it for targeted advertising, one New York assemblyman said there ought to be a law. So he drafted a bill, now gathering support in Albany, N.Y., that would make it a crime - punishable by a fine to be determined - for certain Web companies to use personal information about consumers for advertising without their consent. And because it would be extraordinarily difficult for the companies that collect such data to adhere to stricter rules for people in New York alone, these companies would probably have to adjust their rules everywhere, which could effectively turn the New York legislation into national law. "Should these companies be able to sell or use what's essentially private data without permission? The easy answer is absolutely not," said the assemblyman who sponsored the bill, Richard L. Brodsky, a Democrat. Brodsky is not the only lawmaker with this idea. In Connecticut, the General Law Committee of the state assembly has introduced a bill that focuses on data collection rules for ad networks, the companies that serve ads on sites they do not own. The New York bill, still a work in progress, is shaping up as much broader. Although it is likely to see some tinkering before it comes to a vote - which Brodsky hopes will happen this spring - it aims to force Web sites to give consumers obvious ways to opt out of advertising based on their browsing history and Web actions. If it passed, computer users could request that companies like Google, Yahoo, AOL and Microsoft, which routinely keep track of searches and surfing conducted on their own properties, not follow them around. Users would also have to give explicit permission before these companies could link the anonymous searching and surfing data from around the Web to information like their name, address or phone number. http://www.siliconvalley.com/news/ci_8676030  The Buzz on the Bus: Pinched, Press Steps Off Jacques Steinberg As Senators Hillary Rodham Clinton and Barack Obama debated in Cleveland on a snowy evening in late February, 650 journalists descended on the city to follow every jab and parry, albeit on enormous televisions in two makeshift filing centers. But early the next morning, as the two candidates set off for engagements across Ohio and Texas, representatives of only two dozen or so news organizations tagged along. For most of the others, the price of admission — more than $2,000 for just one person to travel on Mr. Obama’s charter flights that day — was too steep, in an era in which newspapers in particular are slashing costs and paring staff, and with no end in sight to a primary campaign that began more than a year ago. Among the newspapers that have chosen not to dispatch reporters to cover the two leading Democratic candidates on a regular basis are USA Today, the nation’s largest paper, as well as The Boston Globe, The Dallas Morning News, The Houston Chronicle, The Atlanta Journal-Constitution, The Baltimore Sun, The Miami Herald and The Philadelphia Inquirer (at least until the Pennsylvania primary, on April 22, began to loom large). Traveling campaign reporters say they try to do more than just regurgitate raw information or spoon-fed news of the day, which anyone who watches speeches on YouTube can do. The best of them track the evolution and growth (or lack thereof) of candidates; spot pandering and inconsistencies or dishonesty; and get a measure of the candidate that could be useful should he or she become president. Deep and thoughtful reporting is also being produced by journalists off the trail. And some news organizations that can afford it are doing both. But the absence of some newspapers on the trail suggests not only that readers are being exposed to fewer perspectives drawn from shoe-leather reporting, but also that fewer reporters will arrive at the White House in January with the experience that editors have typically required to cover a president on Day 1. For anyone familiar with “The Boys on the Bus,” Timothy Crouse’s rollicking account of the reporters from papers large and small who provided blanket coverage of the 1972 presidential campaign — or with later accounts that noted the prominence of girls on the bus, and the swapping of typewriters for laptops by nerds on the bus — the presence of relatively few print reporters on the candidates’ buses and planes this year is striking. In the weeks leading up to the 22 Democratic nominating contests on Feb. 5, and in the weeks since, few newspapers beyond The Washington Post, The Los Angeles Times, The Chicago Tribune, The Wall Street Journal and The New York Times have sought to shadow the candidates on a near-daily basis. For firsthand, daily dispatches from the campaign trail, most of the others have relied heavily on reports from the wire services, including The Associated Press, Bloomberg and Reuters; a handful of Web sites; and video captured by camera-toting producers from the television networks and cable news channels. “We’d all like to be able to be out there,” said Lee Horwich, a senior editor at USA Today who oversees political coverage. “Given the reality of the costs and various priorities, not just political priorities but across the rest of the newspaper, it just isn’t realistic for us.” The vacuum left by the news organizations that have stayed home this year has often been filled by bloggers, who may travel part time, if at all. Their kitchen is often their bus, where they can watch a candidate speak on YouTube and then pick up supplemental information from the conference calls staged daily by the candidates’ press aides, before ruminating online. To some, the pullback by mainstream news organizations was overdue. S. Robert Lichter, director of the Center for Media and Public Affairs at George Mason University, said the confluence of a long, expensive campaign with the tightening of editors’ wallets had forced a welcome development: the receding of the one-story-suits-all pack journalism depicted in “The Boys on the Bus” and criticized in other quarters ever since “I’m not sure too much is lost,” Mr. Lichter said. “There used to be a self-defined cadre of campaign reporters. Now the news comes from everywhere — from bloggers, maybe some guy with a video camera. Anyone can generate news and everyone can generate news. What’s the advantage of being the 50th guy on the bus?” In the past, one advantage for those reporters who committed to spend as many as two years on the campaign trail was that they were often vaulted into the White House press room; many of those assigned to cover the next president will not have had the benefit of such seasoning, or exposure to the new president’s advisers. Not so at Newsweek. Jon Meacham, the editor, long ago assigned at least one writer (doing double duty for print and the Web) to ride full-time on the Obama and Clinton planes — at a cost that can exceed $30,000 a month per person. “We have a commitment to getting as firm an understanding as we possibly can, as nuanced an understanding as we possibly can, of these candidates and their staffers,” Mr. Meacham said. “The only way to do that is to be there with them.” Like Newsweek, CNN has felt it could not afford not to travel with the candidates, who may touch down in several states in one day. Mrs. Clinton is trailed virtually every moment by Peter Hamby, a CNN producer with a digital camera. Among his responsibilities is to be there when Mrs. Clinton wanders back to the press section of the plane. “You are the eyes and ears of every other producer and reporter at the network,” Mr. Hamby said by phone from the Clinton bus last Wednesday, between bites of a cheese steak. Those news organizations that have chosen to observe the campaign mostly from outside the bubble have hardly shied from original reporting. The Morning News, which had a reporter at George W. Bush’s side in 2000 and 2004, has this year focused on issues of particular resonance to Texans. Mark Edgar, a deputy managing editor, said his reporters had strayed off the trail in California to write about the Hispanic vote, “and how that was different than the Texas Hispanic vote.” “Not being in the bubble is sometimes better,” he said. Still, in the days leading up to the vote in Texas on March 4, reporters for The Morning News paid to climb on the planes ferrying Senators Clinton and Obama, as well as Senator John McCain. Similarly, The Inquirer — which for years had bureau chiefs in Houston, Chicago and Los Angeles travel with the candidates in their regions but has since shuttered those bureaus — has two full-time reporters covering the race, and sometimes riding the candidates’ planes. William K. Marimow, the paper’s editor, said he considered a newspaper’s “pulling out all the stops on a presidential race” to be in service of “a core purpose of the First Amendment.” “But ‘all the stops,’ ” he added, “is defined in part by the resources available.” Mr. Crouse, the Rolling Stone writer who introduced the nation to “The Boys on the Bus,” has long since retired from the campaign trail to North Carolina, where he writes short stories. When asked in an interview to size up the changes on the bus this year, he declined, saying, “I am following the campaign more or less, but not in any deep way.” Had he boarded the Obama campaign bus before 7 a.m. the day after the Cleveland debate, Mr. Crouse would have encountered a scene much like those he chronicled more than 35 years ago. Among the bleary-eyed souls rousing in the fabric-lined seats was Mark Z. Barabak of The Los Angeles Times, who has been riding the bus more or less since Gary Hart and Walter F. Mondale ran for president in 1984. Dressed in a tan patterned suit and Façonnable shirt, Mr. Barabak, 48, poured hot water from a thermos onto a tea bag. “What you have lost,” he said, panning the other seats and seeing few faces from previous campaigns, “is the benefit of getting 6, 12, 15 different perspectives.” “Now you may get three or four,” he said, before adding, “they may be very good.” Among those leading the new generation is Mr. Hamby, 26, who was born a decade after Mr. Crouse’s book came out. Asked if there was any remnant of the carousing that was so prominent in Mr. Crouse’s rendering of the campaign, Mr. Hamby said it depended on when the candidate knocked off for the night. “The younger producers and reporters are more likely to stay up and have a couple of drinks,” he said. “Sometimes you don’t finish working till 1 in the morning. Then it’s impossible to stay awake.” http://www.nytimes.com/2008/03/26/us.../26bus.html?hp  Finding Political News Online, the Young Pass It On Brian Stelter Senator Barack Obama’s videotaped response to President Bush’s final State of the Union address — almost five minutes of Mr. Obama talking directly to the camera — elicited little attention from newspaper and television reporters in January. But on the medium it was made for, the Internet, the video caught fire. Quickly after it was posted on YouTube, it appeared on the video-sharing site’s most popular list and Google’s most blogged list. It has been viewed more than 1.3 million times, been linked by more than 500 blogs and distributed widely on social networking sites like Facebook. It is not news that young politically minded viewers are turning to alternative sources like YouTube, Facebook and late-night comedy shows like “The Daily Show.” But that is only the beginning of how they process information. According to interviews and recent surveys, younger voters tend to be not just consumers of news and current events but conduits as well — sending out e-mailed links and videos to friends and their social networks. And in turn, they rely on friends and online connections for news to come to them. In essence, they are replacing the professional filter — reading The Washington Post, clicking on CNN.com — with a social one. “There are lots of times where I’ll read an interesting story online and send the U.R.L. to 10 friends,” said Lauren Wolfe, 25, the president of College Democrats of America. “I’d rather read an e-mail from a friend with an attached story than search through a newspaper to find the story.” In one sense, this social filter is simply a technological version of the oldest tool in politics: word of mouth. Jane Buckingham, the founder of the Intelligence Group, a market research company, said the “social media generation” was comfortable being in constant communication with others, so recommendations from friends or text messages from a campaign — information that is shared, but not sought — were perceived as natural. Ms. Buckingham recalled conducting a focus group where one of her subjects, a college student, said, “If the news is that important, it will find me.” A December survey by the Pew Research Center for the People and the Press looked broadly at how media were being consumed this campaign. In the most striking finding, half of respondents over the age of 50 and 39 percent of 30- to 49-year-olds reported watching local television news regularly for campaign news, while only 25 percent of people under 30 said they did. Fully two-thirds of Web users under 30 say they use social networking sites, while fewer than 20 percent of older users do. MySpace and Facebook create a sense of connection to the candidates. Between the two sites, Mr. Obama has about one million “friends,” Senator Hillary Rodham Clinton, his rival for the Democratic nomination, has roughly 330,000, and Senator John McCain, the presumed Republican nominee, has more than 140,000. Four out of 10 young people have watched candidate speeches, interviews, commercials or debates online, according to Pew, substantially more than people 30 and older. Young people also identify online discussions with friends and videos as important sources of election information. The habits suggest that younger readers find themselves going straight to the source, bypassing the context and analysis that seasoned journalists provide. In the days after Mr. Obama’s speech on race last week, for example, links to the transcript and the video were the most popular items posted on Facebook. On The New York Times’s Web site, the transcript of the speech ranked consistently higher on the most e-mailed list than the articles written about the speech. The way consumers filter their news is being highlighted now that a generation of Americans is coming of age in the midst of a campaign that has generated intense interest and voter involvement. Exit polls in 22 states estimate that more than three million voters under the age of 30 participated in Democratic primaries this year, up from about one million four years ago. In three of the most populous states — California, Texas and Ohio — the share of voters under 30 who turned out for Democratic primaries increased to 16 percent, up from less than 10 percent in 2004, according to exit polls by Edison/Mitofsky. In the Republican primaries, the increases in most states have been less striking but still visible. “Young people are particularly galvanized in this campaign, and they have a new set of tools that make it look different from the enthusiasm that greeted other politicians 30 years ago,” said Lee Rainie, director for the Pew Internet and American Life Project. “They read a news story and then blog about it, or they see a YouTube video and then link to it, or they go to a campaign Web site, download some phone numbers, and make calls on behalf of a candidate.” Media companies are benefiting from the heightened interest. CNN, which drew about 60,000 viewers ages 18 to 34 a night in February 2007, drew 218,000 on an average night this February, numbers that were increased by coverage of several presidential debates. Fox News and MSNBC also posted gains among young viewers last month, with both networks averaging more than 100,000 young viewers in prime time, according to Nielsen Media Research. Although some college seniors may say they learned about Mr. Obama’s speech about race on CNN, more are likely to have seen it on YouTube, where it has been viewed almost 3.4 million times, or on Facebook, where it remains among the most shared links. Candidates are capitalizing on this social development, and so are their supporters. A youth-minded music video called “Yes We Can” has been perhaps the biggest beneficiary. A musical version of Mr. Obama’s campaign speech made by the singer will.i.am of the Black Eyed Peas and a bevy of celebrities, it was released on YouTube three days before the series of coast-to-coast nominating contests on Feb. 5. Counting hits on YouTube and other sites, the video has been viewed more than 17 million times. To a lesser extent, videos of Mrs. Clinton and Mr. McCain have also been traveling through the online networks. A video of Mr. McCain asking citizens what issues matter most in the election has been viewed 300,000 times. Rather than treating video-sharing Web sites as traditional news sources, young people use them as tools and act as editors themselves. “We’re talking about a generation that doesn’t just like seeing the video in addition to the story — they expect it,” said Danny Shea, 23, the associate media editor for The Huffington Post (huffingtonpost.com). “And they’ll find it elsewhere if you don’t give it to them, and then that’s the link that’s going to be passed around over e-mail and instant message.” Marjorie Connelly contributed research. http://www.nytimes.com/2008/03/27/us.../27voters.html  Houston Mayor Plans 10 'Bubbles' of Free WiFi Mayor targets low-income areas and eyes citywide coverage in future Brad Hem Houston is aiming to turn EarthLink's lemons into the city's lemonade. The company had to pay the city $5 million after defaulting on a contract to build a citywide wireless Internet network last year. On Monday, Mayor Bill White announced the city will use about $3.5 million of that money to build 10 free wireless network "bubbles" in low-income parts of Houston to give residents access they otherwise might do without. The long-term possibility, White said, is that the bubbles could be connected and the areas between them added to the network, providing WiFi access across the city. "It's a matter of connecting those bubbles," White said. Monday's announcement launched the first bubble in the densely populated Gulfton area of southwest Houston. The city is establishing a committee to determine where future networks will be located. Build-out is expected to happen over the next two years. Upload and download speeds on the network are about 3 megabits per second, said Nicole Robinson, director of the city's Digital Inclusion Project. Comparable DSL service can cost $29 a month. Several cities, including Philadelphia, San Francisco and Chicago, have struggled in the past few months to create municipal WiFi networks after EarthLink abandoned that part of its corporate strategy and paid millions in default fees, said Craig Settles, an independent municipal wireless consultant and author of two books on city WiFi. Various financial and operational models are emerging. Settles said the new Houston model could be successful because it limits some cost by locating network transmitters on government-owned property. And by focusing on low-income areas, the plan is more politically acceptable and possibly open to future funding — either from government sources or private companies interested in boosting philanthropy, he said. "I think where the city is going makes a lot of sense," he said. To expand the network beyond the first 10 bubbles will require partnerships with other private businesses, said Settles. He suggested deals with area hospitals, which tend to be spread throughout the city and might have interest in establishing a network to communicate with ambulances, clinics, doctors and patients citywide. Last week, the city finished the formal process of requesting information from potential service providers about how it might build out the network, said Richard Lewis, director of the city's information technology department. The city likely will ask for bids to build the remaining nine networks, maintain them, provide technical support for users and create a system for businesses to advertise on the network, potentially building revenue for operational costs, he said. Hewlett-Packard, Microsoft, Verizon Wireless and Tropos Networks — which donated equipment for the Gulfton network — are pilot sponsors. HP will help develop an "affordable computer purchase plan," according to a news release. In addition to installing Internet service, the city is working with social service groups to provide computer access and training for users. Each bubble will include about 15 public access points at schools, city facilities and community organizations within the area. The pilot network in the Gulfton area includes access points at Family Road Literacy Center, Sylvan Rodriguez Elementary School and Burnett Bayland Community Center. Most city libraries already provide free wireless hot spots, and the new library branch location at Discovery Green downtown will provide wireless service throughout the new park when it opens in April. With most new jobs requiring at least a familiarity with computers, White said it is critical the city helps people learn basic computer skills. "Allowing somebody to have access to computers and to feel confident with them ... you will open a whole horizon for that individual from which they can pull themselves up," he said. http://www.chron.com/disp/story.mpl/front/5645574.html  Wireless Disruption Sebastopol officials reject offer of free Wi-Fi downtown due to health concerns; proponents say that's ridiculous Robert Digitale Concerned about possible health effects from wireless Internet networks, Sebastopol officials have reversed course and turned down a free Wi-Fi area network. The City Council voted 4-0 last week to rescind an agreement with Sonic.net that would have allowed the Santa Rosa-based Internet provider to install the network in the city center as it has done in the downtowns of Santa Rosa and Petaluma. Sebastopol Mayor Craig Litwin thanked Sonic for a "very nice gesture" but said citizens had voiced concerns that "create enough suspicion that there may be a health hazard." Sonic CEO Dane Jasper said his company is sympathetic to those who blame radiofrequency signals for their health problems. But he maintained that the exposure from a Wi-Fi network would be "a drop in the bucket" compared to the amount that people receive daily from TV, radio and cellular phone signals. Moreover, he said, downtown Sebastopol already has plenty of businesses emitting Wi-Fi signals. In a one-block radius around the town's central intersection of Bodega Avenue and Main Street, Jasper detected 25 such signals. His company had proposed to add one more signal at that intersection. "Wi-Fi is pretty much everywhere," he said. Jasper and Wi-Fi critics strongly disagree on what is known about the possible health risks from radiofrequency, or RF, signals. Jasper cited the World Health Organization. Its Internet site concludes: "Considering the very low exposure levels and research results collected to date, there is no convincing scientific evidence that the weak RF signals from base stations and wireless networks cause adverse health effects." But critics said good studies exist that show ill effects to both adults and children from such signals. And they disputed Jasper's contention that one more wireless network will have a negligible effect on Sebastopol residents. "A little bit more is going to cause a little more problems," said Jeffrey Fawcett, president of the Sustainable Health Institute, an educational nonprofit based in Camp Meeker. Last fall the council reached agreement with Sonic to install the network, which would allow wireless Internet connections for people with Wi-Fi-enabled devices, such as laptop computers and cell phones. Sebastopol resident Sandi Maurer gathered support to persuade the council to reconsider the matter. Maurer, who said she is sensitive to electricity much as some people are sensitive to chemicals, worked with others to gather roughly 500 signatures from people concerned about the effects of Wi-Fi signals. Sebastopol Councilwoman Linda Kelley requested that the issue come back to the council last week, giving Maurer and other critics a chance to successfully plead their case. "I feel very grateful to the City Council, to Linda Kelley," Maurer said. http://www1.pressdemocrat.com/articl...0314/1033/NEWS  Turn Your PC into a DVD Ripping Monster Commercial DVDs are far too expensive to let scratches turn your video into a glorified coaster, but most people still don't back up their DVD collection. Once upon a time, the four to eight gigabyte footprint of a DVD on your hard drive was prohibitively large. But since the price of a gigabyte has plummeted, ripping your entire DVD collection to your computer is not just possible, it's prudent—and it's easy. Let's take a look at the best ways to back up and play any DVD rip on your home computer, along with how to burn a DVD rip back to a playable DVD. What You'll Need All you need is a PC with a DVD drive and a hard drive with some extra space. If you're working on a computer with limited space, that doesn't rule you out. You can find huge internal hard drives for cheap (like this 500GB drive for $99), and installing that hard drive is a breeze. You only need a DVD drive capable of burning DVDs if you want to burn your backups back to a disc you can play in a DVD player. DVD burners are crazy cheap at under $30, and they install just as easily as hard drives. I'm focusing on Windows solutions for this article. That doesn't mean there aren't methods available for other operating systems—it just means that the scope of this feature is limited to Windows users. Set Up Painless DVD Ripping to Your Hard Drive There are several methods for ripping your DVDs on your Windows computer, but lets run down a couple of the best below. Rip DVDs in One-Click with DVD Rip and DVD Shrink Our first and favorite option for ripping DVDs to your hard drive is DVD Rip, a free, open source application built in the Lifehacker workshop designed to make backing up DVDs to your hard drive as simple as possible. DVD Rip works in conjunction with another tool called DVD Shrink, a freeware application that rips and compresses the DVD image. DVD Shrink does all the heavy lifting—DVD Rip just makes it super-simple to use. Pros: DVD Shrink compresses your rips so they take about half the space on your hard drive, so despite the fact that storage is cheap, you can still get more bang from your buck. Also, using DVD Rip in conjunction with DVD Shrink is designed to be simple enough that anyone in your family could use it. DVD Rip is also designed to work well with DVD Play, another helper app (mentioned below), for playing back your DVDs. Cons: If you want your backups to be exact copies of your DVDs, the shrinking aspect of DVD Shrink probably isn't for you. It saves space, but it skimps on some video fidelity to do it. The space versus quality trade-off is one I'm comfortable making with most DVDs, but you may want to try it out yourself to be sure. NOTE: DVD Shrink can break the copy protection on most DVDs without issue, but if you're having a problem, try running previously mentioned DVD43, which promises to remove copy protection from virtually any DVD, before you start DVD Shrink. DVDFab HD Decrypter Like DVD Shrink, DVDFab HD Decrypter breaks copy protection and rips the DVD contents to your hard drive. Unlike DVD Shrink, DVDFab does not compress the rip, so it's going to be the same quality as the original. DVDFab is actually a shareware app, but the trial version does full DVD rips and will even rip only the main movie. Pros: DVDFab has a great reputation for cutting through copy protection, and it results in full quality rips. Cons: Full quality rips mean lots of hard drive space per movie—around 8GB. If that's not a problem, more power to the full rip. If it is, DVD Shrink (with or without DVD Rip) will half that to about 4 or 5GB and might be more your taste. You might also consider ripping just the main movie with DVDFab if you don't want or need the extra features to save space. Play Back Your Rips Now that you've set up your computer to inhale any and every DVD you throw its way, you want to play these ripped DVDs. You could go one step further and encode them to popular compressed formats like DivX, but the rips you've already set up have their own charm for a couple of reasons. First, ripping DVDs to the VIDEO_TS and AUDIO_TS folders (the default output for these methods) means you retain the entire DVD structure, so watching the rip works just like if you were watching the DVD, complete with menus and special features. Second, these folders can easily be burned back to DVDs so that—in the event that one of your physical discs is damaged—you can just burn the backup and never miss a beat. Here are a few methods and apps you can use to play back these DVDs on your computer and burn new DVDs from the rips. Play Back Ripped DVDs with DVD Play and VLC Similar to DVD Rip, DVD Play is a helper application that works in conjunction with the popular open source media player, VLC, to help you navigate and play back your ripped DVDs. To get a look at how DVD Play works in action, check out the video below. In this video DVD Play is playing back a DVD ripped using DVD Rip and DVD Shrink. All you have to do is point DVD Play at the folder where you're ripping all of your DVDs, and it provides a nice interface for browsing and playing back those ripped DVDs. Play Back Ripped DVDs in Windows Media Center If you're a Windows Media Center user, you can play back these ripped DVDs from directly within Media Center. In pre-Vista versions of Media Center, you can just add your rips folder to your My Videos library and they'll automatically show up as playable. The DVD library feature is turned off by default in Vista's Media Center, but all it takes is one small tweak to enable it. Burn Your Backups to a New DVD with ImgBurn Finally, if your physical disc gets damaged, you can always burn a new DVD from your backup (again, with DVD menus and all the extra features). This time, we're using a freeware application called ImgBurn. To burn one of your backups to a new DVD, just fire up ImgBurn and enter Build mode by selecting Mode -> Build from the ImgBurn menu. Now just click browse folder icon beneath the source dropdown and point ImgBurn to the folder of the ripped DVD you want to burn. After you've selected the folder, insert a blank DVD and then click on ImgBurn's Calculate button to determine if your DVD has enough space to burn the backup. If you want to back up DVDs you ripped using DVDFab (all 8GBs), you'll need a dual-layer DVD burner capable of burning to 8GB dual-layer DVDs. If you've just got a regular old DVD burner that can only burn to 4GB single-layer discs (which I suspect is most of us), the DVD Shrink method above is your best choice. Now, assuming you've got a DVD big enough to handle your DVD rip, just click the Build button (pictured) and let 'er burn. Note: If your Build button does not look like the button pictured, you need to switch to Device Output mode by clicking the small button to the left of the Build button to switch to Device Output mode—otherwise ImgBurn will want to create an ISO file on your hard drive rather than burn the disc. http://lifehacker.com/371636/turn-yo...ipping-monster  Social Site’s New Friends Are Athletes Tim Arango Late last year, Pamela Firestone, the mother of Tony Parker, the San Antonio Spurs point guard, went rooting through her home in Paris and dug up a VHS tape of a 9-year-old Tony on a Parisian basketball court with his two brothers. “O.K., let’s start,” the future N.B.A. star says in French. “It’s going to be the Chicago Bulls versus the San Antonio Spurs.” In most families such artifacts are merely heirlooms, their value measured in memories. For the Hollywood talent agency Creative Artists Agency and the hedge fund Pequot Capital, these are assets to be exploited. Photos and videos showing blue-chip athletes like Mr. Parker, LeBron James, Derek Jeter and Peyton Manning will be part of a new venture that C.A.A. and Pequot along with the Internet arm of Major League Baseball are expected to announce today. The venture, WePlay.com, a social networking site for youth sports — something like Facebook for young athletes — is expected to start in mid-April. The site caters to youth athletes, parents and coaches — a vast audience. About 52 million children a year participate in organized sports leagues, according to the National Council of Youth Sports. Young athletes will be able to set up a profile, post pictures, communicate with friends and share videos of games. Parents will be able to get practice schedules, coordinate car pools and find out which equipment to purchase. Coaches will be able to communicate with their players and parents, as well as learn about strategy and other skills. “Two hundred forty million people in America are one degree of separation from youth sports,” said Steve Hansen, the chief executive of WePlay. “Youth sports is held together by e-mails, phone calls and clip boards. We want to change that.” The videos of the athletes as children, as well as footage from recent shoots — a camera crew will join LeBron James at his high school gym in the coming weeks, for example — will surround the more traditional features of social media. The site will be mostly advertiser supported, initially in the form of sponsorships integrated in to the site, and later, banner ads. Madison Avenue has long seen the value of aligning with sports teams, and over the years has been reaching further down the athletic food chain: first professional, then college, and more recently high school. Takkle, a social-networking site for high school athletes, is partially owned by Sports Illustrated. With WePlay, advertisers will have the chance to go even younger. At the same time, WePlay can also be seen as an attempt on the part of the professional athletes to gain more control over how their images are used commercially — in other words, why let ESPN run video of their Little League games free, when they can do so and sell advertising alongside it? The idea originated at C.A.A., which about 20 months ago began a sports division and whose agents have been trying to find ways beyond the traditional endorsement deal to increase an athlete’s earning potential, by starting companies in which the players can be owners. “One of the reasons they chose to come here was so their clients could have these opportunities,” said David Rone, co-head of C.A.A. Sports, the division of the talent agency that represents athletes. “They can be the best agents they can be by exposing themselves to the rest of the disciplines we have at C.A.A..” Other athletes involved in WePlay.com have been looking for their own relics of early stardom. In a spare bedroom at her home in New Orleans, Olivia Manning collected relics from her son Peyton’s days as a child quarterback to be copied and digitized by an employee from Major League Baseball Advanced Media. Mr. James’s mother rustled up old photos and videos of her son from a storage area in her garage. And in New Jersey, Mr. Jeter’s mother found a video of her son playing Little League — a treasure whose value was diminished 10 minutes into the film because someone in the Jeter family taped over it with the movie “RoboCop.” “This is really the quintessential execution of what we’d like to do on behalf of our clients,” Mr. Rone said. “All of them want to move beyond holding soda cans or holding a Big Mac in their hands.” So for players like Mr. Jeter, who will make about $20 million this year playing shortstop for the Yankees, being a hired promotional gun is not enough. Mr. Jeter, who in addition to receiving equity in WePlay in exchange for his involvement also invested some of his own money (he will not say how much), began filming clips for the site in mid-December. Having equity, Mr. Jeter said in a telephone interview, is “very important, because you can really feel good about something if you help build it.” The focus of the business also fits with Mr. Jeter’s own philanthropy. “What it boils down to is, it’s a really outstanding idea,” he said. “I have my own foundation, and we are trying to get kids to be active and play sports. Kids today spend too much time playing video games, and there’s a huge obesity problem in this country.” Inside C.A.A., agents liken the venture to the sports version of the Web site FunnyOrDie.com, a partnership between C.A.A., the actor Will Ferrell and a Silicon Valley venture firm. “These are assets — content — that our athletes control,” Mr. Rone said. “The content that all our athletes control is somewhat limited. We want to build businesses around that content. We hope we can help them properly monetize that content. Otherwise it’s just sitting on a shelf.” The last time a group of famous athletes linked up on the Web, the result was a bust. In 1999, a group led by the Silicon Valley venture firm, Benchmark Capital, sunk $65 million in to MVP.com, an Internet venture involving John Elway, Michael Jordan and Wayne Gretzky. “It was a big flameout,” said Mr. Hansen, an Internet veteran who was formerly chief operating officer of GeoCities, a Web-hosting firm. He said MVP.com did not work because an athlete’s name alone isn’t enough for success. “It can’t just be P.R.,” he said. “It can’t just be, give me Peyton’s name and likeness and that will be enough for my site.” One advertiser that has already signed on is the trading card company Upper Deck, which will offer online trading games for youngsters and access to a digital trading card library. “We believe very strongly in the deep integration of a small number of advertisers in a contextual way,” said Mr. Hansen. The investment in WePlay so far is $4.5 million — much more modest than the investment in MVP.com — and the financial backers are already thinking about other niche-oriented social networking sites. “There’s no reason to believe that the organizing principles that are applied here to sports can’t be applied elsewhere, such as to religious organizations,” said Rick Heitzmann, managing director at Pequot Ventures, the venture arm of Pequot Capital Management. “So you could go from WePlay to WePray.” http://www.nytimes.com/2008/03/26/technology/26caa.html  Sony BMG, Warner Near Deal with Myspace Brian Garrity MySpace's plan to launch a digital-music joint venture with the major record companies is picking up steam, as the social networking giant nears deals with Sony BMG and Warner Music Group, multiple sources familiar with the situation told The Post. The agreements could be signed as soon as this week. The service is expected to launch later this year. "Everybody's operating with a sense of urgency to try to close it out," said one industry insider close to the talks. MySpace, News Corp. (which also owns The Post), Sony BMG, and Warner all declined to comment. Unlike most music licensing agreements, which require upfront advances, no money is expected to change hands. Instead, the labels are trading content rights in exchange for minority equity stakes in MySpace Music and the chance to participate in the advertising revenues that News Corp. hopes to generate from the service. MySpace attracts more than 15 million unique monthly visitors to its existing music portal, a sub-site within MySpace that specializes in new music promotion and tour date information, rather than commerce. In addition, MySpace claims more than 5 million individual artist pages attracting Web traffic not counted as part of its total music traffic tracked by comScore. The new MySpace Music is expected to be a mix of pay-per-download and ad-supported video and audio. "The concept of the joint venture is to bring in all forms of [making money from digital music] and much more tightly integrate them," said one person familiar with the negotiations. Users could expect to buy digital downloads in the MP3 format, see and hear ad-supported streaming video, and buy such products as downloadable videos and ringtones. Jamba - a mobile entertainment service that News Corp. owns jointly with VeriSign - is expected to play a role in MySpace Music's cellphone commerce strategy, a source said. Record companies are looking to maximize available revenue opportunities, and expand the number of alternatives to Apple's iTunes music store. iTunes is the second-largest music retailer in the US behind Wal-Mart, with 4 billion songs sold since its April 2003 launch. Collectively, the record companies are expected to hold less than a 50 percent stake in the MySpace venture. Just how large a piece each label gets in MySpace Music will be determined by market share, sources said. Sony BMG and Warner currently rank as the world's second- and third-largest music companies, respectively. Further behind in the negotiating process are Universal Music Group, the industry's largest record company, and EMI. Universal is currently suing MySpace for copyright infringement associated with its viral video offering - one of the biggest hubs of user-generated video on the Web behind Google's YouTube. The two sides first need to settle that fight before a deal can be struck for the MySpace Music joint venture. http://www.nypost.com/seven/03242008...iny_103302.htm  Sony BMG Eyeing All-Inclusive MP3 Service FMQB Sony BMG is taking steps to launch its own digital music service that would give users unlimited access to its digital catalog for a monthly fee. In an interview with the German newspaper Frankfurter Allgemeine Zeitung, chief executive Rolf Schmidt-Holtz said, "We are working on an online music subscription service. The simplest option would be a flat rate under which a monthly payment would provide access to our entire music catalog for all digital players, including Apple's iPod." He suggested that the cost would be around 6 to 8 euros ($9 to $12 per month) for unlimited access to Sony BMG's entire music catalog. "It is even possible that clients could conserve some songs indefinitely, that they would own them even after the subscription expired," he added. Schmidt-Holtz didn't give an exact timetable for the project, but it could get off the ground sometime this year. He said that the company is in talks with other music distributors on the subject, and that cooperation agreements with mobile phone manufacturers is also possible. http://fmqb.com/Article.asp?id=630946  Innocent Man Pinched by RIAA Asks SCOTUS for Attorney's Fees Eric Bangeman Cliff Thompson, a San Antonio resident sued by the RIAA for copyright infringement, has asked the Supreme Court to decide whether the record labels should be forced to pay attorneys' fees in cases where they voluntarily dismiss copyright infringement cases. Thompson was sued by the RIAA in 2006 for allegedly using KaZaA to distribute music, but the labels dismissed their case against him once it became apparent that his adult daughter was the KaZaA user in question. Thompson sought an award of attorneys' fees, arguing that since he was the prevailing party in the copyright infringement lawsuit, he was entitled to have his legal bills paid for by the RIAA. The problem is that different courts do not handle attorneys' fees in copyright infringement cases uniformly. The judge in Virgin v. Thompson denied his request, citing a "purported lack of responsiveness," and Thompson was thwarted once again at the Fifth Circuit Court of Appeals. Citing a 1997 Supreme Court ruling, the appeals court decided that attorneys' fees awards are "not automatic." Instead, courts must take a number of factors into consideration, including "frivolousness, motivation, objective unreasonableness... and the need in particular circumstances to advance considerations of compensation and deterrence," noted the opinion. In contrast, the Seventh Circuit Court of Appeals has held that a simple "material alteration of the legal relationship of the parties" is sufficient for an attorneys' fees award. That decision, which involved a copyright infringement lawsuit between video poker game manufacturers, was based on a 2001 Supreme Court ruling. Midwest Electronic Specialties was entitled to legal fees once the case against it was dismissed, said the appeals court. "Midwest obtained a favorable judgment," wrote the judges. "That this came about when Riviera threw in the towel does not make Midwest less the victor than it would have been had the judge granted summary judgment or a jury returned a verdict in its favor. Riviera sued; Midwest won; no more is required." Attorney: the Supreme Court should end the recording industry's gambling In the petition for certiorari filed with the Supreme Court, Thompson's attorney Ted Lee lays out the RIAA's legal strategy and notes what he describes as the "inherent unfairness" of the lawsuits. "Clearly, the industry has gambled that defendants will make the financially-rational decision of settling the lawsuits—regardless of culpability—rather than risk financial ruin in a knock-down, drag-out legal fight," reads Lee's petition. "More often than not this strategy works, as the vast majority of these defendants never see the inside of a courtroom in these lawsuits, simply because even if the innocent defendant were to win his case on the merits, he more than likely would lose in his pocket book." Lee focuses on a 1994 Supreme Court decision in Fogerty v. Fantasy Inc., which appeals courts throughout the US have interpreted differently. He argues that federal courts have "latched on to one footnote" from the case and only look at "frivolousness, motivation, objective unreasonableness, and the need to advance considerations of compensation and deterrence" when making a decision on attorneys' fees. The Fogerty factors are inherently unfair to prevailing defendants, says Lee. "Simply put, it is impossible for a court to apply the factors mentioned in Fogerty to prevailing plaintiffs and prevailing defendants in an evenhanded manner," reads the petition. "For example, the trial court's opinion gave no consideration to the merits of Thompson’s defense, but essentially concluded, contrary to the tenor of Fogerty, that because the plaintiffs' cause was not "frivolous," no attorney's fees should be awarded to Thompson." That logic flies in the face of the Supreme Court's finding that innocent defendants should be encouraged to fight back in court, says Lee. "There is a clear and present need for this Court's intervention and guidance on this important issue of copyright law," Lee concludes. "Moreover, an absence of uniformity between the circuits, concurrent with an onslaught of litigation by the music companies against internet account holders, only serves to provide innocent defendants with even little, if any, incentive to fully litigate any meritorious defenses they may have, contrary to the policies this Court has recognized." Obviously, no one outside of the nine justices can say whether or not the Supreme Court will hear this case. But there are some significant reasons why the Court may be interested in taking up this case. First, there is a conflict at the Appeals Court level, as at least two circuits are interpreting the same ruling and law very differently. Second, and more significantly, there's a lot at stake here. The fight between the RIAA and alleged copyright infringers is inherently unbalanced due to the vast financial resources available to the record labels. The risk-reward ratio for defendants is seriously out of kilter, and mandating that a successful defense—even if it comes from the RIAA's decision to voluntarily dismiss a case—results in the record labels picking up the tab would even things out. http://arstechnica.com/news.ars/post...neys-fees.html  Fee for All Jim Griffin will lead Warner Music's fight to tame the Web's lawless music frontier. Sam Gustin Edgar Bronfman Jr.'s Warner Music Group has tapped industry veteran Jim Griffin to spearhead a controversial plan to bundle a monthly fee into consumers' internet-service bills for unlimited access to music. The plan—the boldest move yet to keep the wounded entertainment industry giants afloat—is simple: Consumers will pay a monthly fee, bundled into an internet-service bill in exchange for unfettered access to a database of all known music. Bronfman's decision to hire Griffin, a respected industry critic, demonstrates the desperation of the recording industry. It has shrunk to a $10 billion business from $15 billion in almost a decade. Compact disc sales are plummeting as online music downloads skyrocket. "Today, it has become purely voluntary to pay for music," Griffin told Portfolio.com in an exclusive sit-down this week. "If I tell you to go listen to this band, you could pay, or you might not. It's pretty much up to you. So the music business has become a big tip jar." Nothing provokes sheer terror in the recording industry more than the rise of peer-to-peer file-sharing networks. For years, digital-music seers have argued the rise of such networks has made copyright law obsolete and free music distribution universal. Bronfman has asked Griffin, formerly Geffen Music's digital chief, to develop a model that would create a pool of money from user fees to be distributed to artists and copyright holders. Warner has given Griffin a three-year contract to form a new organization to spearhead the plan. Griffin says he hopes to move beyond the years of acrimonious record-industry litigation against illegal file-swappers, college students in particular. "We're still clinging to the vine of music as a product," Griffin says, calling the industry’s plight "Tarzan" economics. "But we're swinging toward the vine of music as a service. We need to get ready to let go and grab the next vine, which is a pool of money and a fair way to split it up, rather than controlling the quantity and destiny of sound recordings."Warner Music Share Price In the last year, the Recording Association of America, the industry group that represents the major labels, has sent 5,400 threatening letters to students at more than 150 schools, and reached settlements with more than 2,300 them. It has filed formal lawsuits against 2,465 others, who did not respond. "I don't think we should be suing students and I don't think we should be suing people in their homes," says Griffin. "We want to monetize the anarchy of the internet." Griffin says Warner Music is "totally committed to this." The fundamental issue, he says, is whether music consumers will buy songs and albums individually, or whether they will subscribe monthly to access a "universal" database of songs. Will Tanous, Warner Music's communications chief, said Griffin's initiative is part of Warner's "ongoing effort to explore new business models in the music industry." In recent weeks, major music industry players have signaled their interest in the "music as a service" model. Sony BMG Music Entertainment is said to be developing an online music subscription service that would give users unlimited access to its catalog. Apple is reportedly negotiating with the major record labels to offer consumers free access to the entire iTunes library in exchange for paying a premium for Apple hardware. Warner's plan would have consumers pay an additional fee—maybe $5 a month—bundled into their monthly internet-access bill in exchange for the right to freely download, upload, copy, and share music without restrictions. Griffin says those fees could create a pool as large as $20 billion annually to pay artists and copyright holders. Eventually, advertising could subsidize the entire system, so that users who don't want to receive ads could pay the fee, and those who don't mind advertising wouldn't pay a dime. "Ideally, music will feel free," says Griffin. "Even if you pay a flat fee for it, at the moment you use it there are no financial considerations. It's already been paid for." While few of the plan's details have emerged, critics have begun their attacks. David Barrett, engineering manager for peer-to-peer networks at Web content-delivery giant Akamai, says he's opposed to it on principle. Griffin's plan, he says, is tantamount to extortion, because it forces everyone to join. "It's too late to charge people for what they're already getting for free," says Barrett. "This is just taxation of a basic, universal service that already exists, for the benefit a distant power that actively harasses the people being taxed without offering them any meaningful representation." Griffin, who in 1994 was part of the team that made Aerosmith's "Head First" the first song available on the internet, goes to great pains to emphasize that the collective licensing plan is not "his" plan. "This isn't my idea," says Griffin. "While I would gladly take the credit, blanket licensing has over 150 years of history behind it." "Collective licensing is what people do when they lose control, or when control is no longer practical or efficient," Griffin says. "A pool of money and a fair way to split it up replaces control." Griffin was quick to point out that the $5 figure is arbitrary. "We negotiate in every place," Griffin says. "Clearly $5 per month would be an insane number in China or India. If you could get a nickel a month you could grow the business tenfold in those countries. In another country that had a high G.D.P., a nickel per month would be ridiculously cheap. So you negotiate. Fair is whatever you agree upon." Griffin says Bronfman and Michael Nash, the company's digital-strategy chief, brought him into Warner to create an organization to negotiate collective licensing deals. But Griffin's ambitions extend far beyond just Warner Music. "We're building a [as yet unnamed] company inside Warner that is not intended to be solely owned by Warner," Griffin says. "We hope all of the rights holders will come in and take ownership with us, and Warner will not control it. Our goal is to create a collective society for the digital age." Meanwhile, critics have already attacked the plan as a kind of mandatory "culture tax." "Jim will vehemently deny the 'tax' label," says Akamai's Barrett. "But it's a tax nonetheless. It'll be a government-approved cartel that collects money from virtually everyone—often without their knowledge—and failure to pay their tax will ultimately result in people with guns coming to your door. "Jim's proposal does nothing but direct money to the very people that tried to prevent this future from coming to be," Barrett adds, "while further legitimizing the terror being waged in the courtrooms against their members." Griffin dismisses such criticism. "I understand what David is thinking, but I assure you, we have no such interest in government running this or having any part of it," he says. Griffin says that in just the few weeks since Warner began working on this plan, the company has been approached by internet service providers "who want to discharge their risk." "But more important than the risk for an I.S.P. is the marketing," Griffin says, drawing a comparison to Starbucks' marketing of "fair trade" coffee. "I.S.P.'s want to distinguish themselves with marketing," Griffin says. "You can only imagine that an I.S.P. that marketed a 'fair trade' network connection would see a marketing advantage." Gerd Leonhard, a respected music-industry consultant who has advised Sony/BMG, which recently announced plans for a flat-rate-subscription model for digital music, rejects Barrett's argument that the monthly fee amounts to a tax. "This is not a tax," says Leonhard. "It's bundled into another charge." "People should not be too harsh on Jim for trying to get the ball rolling," says Leonhard. "At this point, 96 percent of the population is guilty of some sort of infringement, whether they're streaming or downloading or sharing. "What we have here is the widespread use of technology that declares all of the population to be illegal." http://www.portfolio.com/news-market...s-New-Web-Guru  Smashing Pumpkins Sue Virgin Records FMQB Smashing Pumpkins have sued Virgin Records, the band's home for the majority of their career, claiming the label damaged their credibility by using their name and music in a recent promotion. According to TMZ, the Pumpkins (who are essentially frontman Billy Corgan and drummer Jimmy Chamberlin) sued Virgin over their use in the recent "Pepsi Stuff" promotion between Pepsi and Amazon. The band have filed a breach of contract lawsuit in Los Angeles, stating they have "worked hard" to build their credibility with their fanbase and Virgin has hurt their "artistic integrity." The Pumpkins are asking for profits from the Pepsi promotion as well as an injunction against Virgin using their name and music in the future. It should be noted, however, that the Pumpkins' song "That's The Way (My Love Is)" was just featured prominently in a Ford commercial. Though that song appeared on the band's comeback album, 2007's Zeitgeist, which was released by Reprise Records. http://fmqb.com/Article.asp?id=631079  Web Scout Exclusive! Rick Astley, King of the 'Rickroll,' Talks About His Song's Second Coming Astley talks about discovering the "Rickroll" On a frosty Canadian morning, a masked crusader tromps across a parking lot, over a snow bank and onto the sidewalk. He has a loudspeaker strapped ominously to his chest. He halts, aiming the speaker toward the building across the street. “This is a song by some dead guy,” he says. And then, music booms forth: “Never gonna give you up, never gonna let you down, never gonna run around and desert you.” It’s an anti-Scientology protest, and across the street, a dozen or so warmly dressed young people begin to dance and sing along, waving their picket signs in rhythm to the familiar tune. “It’s a bit spooky, innit?” said Rick Astley, the singer who made the song famous in 1987 and who is not dead. With considerable help, including assists from RCA Records, the webmaster of Astley’s U.K. fan site, and his manager at Sony BMG, I tracked down Astley at his home in London last weekend. He spoke for the first time about the phenomenon called Rickrolling, best described by example: You are reading your favorite Hollywood gossip blog and arrive at a link urging you to “Click here for exclusive video of Britney’s latest freakout!!” Click you do, but instead of Britney, it’s a dashing 21-year-old Briton that pops onto the screen. You, sir, have been Rickroll’d. Over the last year or so, Astley has watched with puzzled amazement as “Never Gonna Give You Up” has been mocked, celebrated, remixed and reprised, its original music video viewed millions of times on YouTube, all by a generation that could barely swallow its Gerber carrots when the song first topped the pop charts. “I think it’s just one of those odd things where something gets picked up and people run with it,” Astley said. “But that’s what brilliant about the Internet.” Saying he thought "Anonymous" Rickrolling Scientology was "hilarious" Search for Astley’s name on YouTube and you’ll find dozens of instances of the campy, infectious video, which features a heavily coiffed Astley bobbing and swaying behind oversized sunglasses. He’s flanked by two blond backup dancers (one of whom apparently didn’t have the footwork down), and a male bartender in short shorts who excels at spontaneous back flips. Rickrolling is an example of an Internet “meme” (defined by Wikipedia as “any unit of cultural information ... that gets transmitted verbally or by repeated action from one mind to another"). Its less sophisticated memetic forebear is the “duckroll,” where the roll-ee is misdirected to an image of a duck on wheels. And the Rickroll has sired many memelets, including the Fresh Prince roll, the rainroll (plopping you in front of a video of Tay Zonday’s "Chocolate Rain") and even the Reichroll, where Astley’s song is spliced with footage of Adolf Hitler for an unsettling sort of lip sync. With all the online momentum it’s gathered, the Rickroll has now trundled its way into the real world, too. The spectacle of trench-coated pranksters blaring the song into unsuspecting crowds has become a symbol of harmless, geeky rebellion. As the blog LAist.com noted last week, and the New York Times reported Tuesday, a recent basketball game at Eastern Washington University was interrupted by a dancing Astley imitator, and there’s now a small YouTube library of the anti-Scientology group “Anonymous” Rickrolling different church locations. Why have people picked up on the song so much? For his part, Astley was nothing if not modest about his new cultural role. “If this had happened around some kind of rock song, with a lyric that really meant something -- a Bruce Springsteen, "God bless America" ... or an anti-something kind of song, I could kind of understand that,” Astley said. “But for something as, and I don’t mean to belittle it, because I still think it’s a great pop song, but it’s a pop song; do you know what I mean? It doesn’t have any kind of weight behind it, as such. But maybe that’s the irony of it.” Astley would never put the song down, mind you. It’s just that, as he says, “If I was a young kid now looking at that song, I’d have to say I’d think it was pretty naff, really.” (Wikipedia on “naff”: British slang for “something which is seen to be particularly ‘cheesy’ or ‘tacky’ or in otherwise poor aesthetic taste.”) “For me it’s a good example of what some of the ’80s were about in that pop sort of music way. A bit like you could say Debbie Gibson was absolutely massive, but if you look back at it now ... do you know what I mean?” Yes, I think we do. But even still, with all the renewed attention to his work and his — albeit 20-year-old — image, does Astley have any plans to cash in on Rickrolling, maybe with his own YouTube remix? “I don’t really know whether I want to be doing that,” he said. “ I’m not being an ageist, but it’s almost a young person’s thing, that.” “I think the artist themselves trying to remix it is almost a bit sad,” he said. “No, I’m too old for that.” Astley, who will be touring the U.K. in May with a group of other ’80’s acts, including Bananarama, and Nick Heyward, Heaven 17, Paul Young and ABC, sums up his thoughts on his unexpected virtual fame with characteristic good humor: “Listen, I just think it’s bizarre and funny. My main consideration is that my daughter doesn’t get embarrassed about it.” http://latimesblogs.latimes.com/webs...stley-kin.html  Anti-Emo Riots Break Out Across Mexico Alexis Madrigal Riot police have taken to the streets of several cities in Mexico to ... defend emo kids? A series of attacks on dyed-hair, eye-makeup-wearing emo kids began in early March when several hundred people went on an emo-beating rampage in Querétaro, a town of 1.5 million about 160 miles north of Mexico City. The next week, shaggy-haired emo teenagers were harassed again by punks and rockabillys in the capital, prompting police protection and a segment on the TV news. Most recently, a Mexican newspaper reported that metal heads and gangsters have warned Tijuana's emo kids to stay away from the town's fair next month. But the so-called emos are organizing, too. Last week, they demonstrated against the violence, pictured above, and Wednesday some met with police in Mexico City. "They're organizing to defend their right to be emo," wrote Daniel Hernandez of LA Weekly on his personal blog, which has provided stellar coverage of the whole affair. Music-based subcultures have permeated Mexico's major cities for decades, fueled by constant migration from rural cities. But only in the past year have emos begun to make their presence felt in the streets. In response, many of the established so-called tribus urbanas like punks and metalheads are responding with violence. The emo-punk battles are reminiscent of earlier subculture fights among various factions, like the Hell's Angels fighting hippies at the Altamont Music Festival or the Mods taking on the Rockers. But while videos of Mexican teenagers with pompadours advancing on equally baby-faced emo rockers seem like scenes from a south-of-the-border version of John Waters' Crybaby, there are ugly undercurrents to the story. First, by some accounts, the emo subculture is identified with homosexuality in Mexico. As Mexico City youth worker Victor Mendoza told Time.com: "At the core of this is the homophobic issue. The other arguments are just window dressing for that." Gustavo Arellano, the author of Ask a Mexican and an editor at OC Weekly, said that the sexual ambiguities cultivated by emo fashion helped set the group up for targeting by more macho groups. "What do you do when you are confronted with a question mark about sexuality in Mexico?" Arellano said. "You beat it up." Forum posts show similar sentiments. One person wrote on a government youth-website forum, "detesto a los emosexuales," which translates as "I hate emosexuals." Emosexual is an obvious play on homosexual, especially in Spanish, where the H is silent. Many of the attacks have been planned, or at least fomented, on violently anti-emo websites like Movimiento Anti Emosexual, which features videos of physical violence sprinkled liberally with anti-gay sentiment. Last.fm's Anti Emo Death Squad group has almost 4,000 members. But Arellano said he thought the riots could have a positive impact here in the US. "It's a great clusterfuck for the American mind's idea of Mexico," Arellano said. "This teaches the rest of the world that Mexico is not just a bunch of cactuses and sombreros." http://blog.wired.com/underwire/2008...emo-riots.html  Researchers Play Tune Recorded Before Edison Jody Rosen 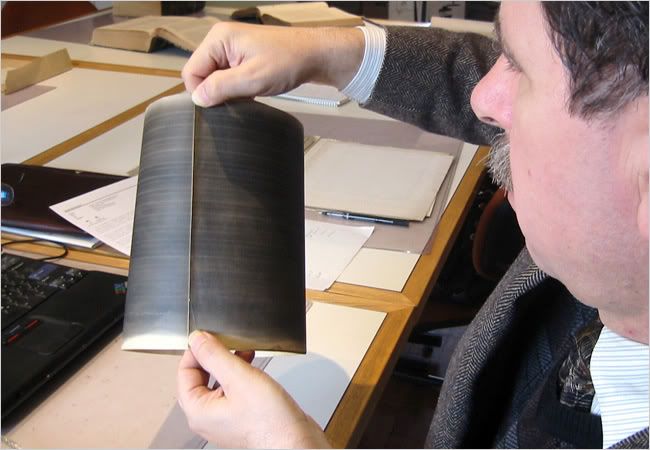 For more than a century, since he captured the spoken words “Mary had a little lamb” on a sheet of tinfoil, Thomas Edison has been considered the father of recorded sound. But researchers say they have unearthed a recording of the human voice, made by a little-known Frenchman, that predates Edison’s invention of the phonograph by nearly two decades. The 10-second recording of a singer crooning the folk song “Au Clair de la Lune” was discovered earlier this month in an archive in Paris by a group of American audio historians. It was made, the researchers say, on April 9, 1860, on a phonautograph, a machine designed to record sounds visually, not to play them back. But the phonautograph recording, or phonautogram, was made playable — converted from squiggles on paper to sound — by scientists at the Lawrence Berkeley National Laboratory in Berkeley, Calif. “This is a historic find, the earliest known recording of sound,” said Samuel Brylawski, the former head of the recorded-sound division of the Library of Congress, who is not affiliated with the research group but who was familiar with its findings. The audio excavation could give a new primacy to the phonautograph, once considered a curio, and its inventor, Édouard-Léon Scott de Martinville, a Parisian typesetter and tinkerer who went to his grave convinced that credit for his breakthroughs had been improperly bestowed on Edison. Scott’s device had a barrel-shaped horn attached to a stylus, which etched sound waves onto sheets of paper blackened by smoke from an oil lamp. The recordings were not intended for listening; the idea of audio playback had not been conceived. Rather, Scott sought to create a paper record of human speech that could later be deciphered. But the Lawrence Berkeley scientists used optical imaging and a “virtual stylus” on high-resolution scans of the phonautogram, deploying modern technology to extract sound from patterns inscribed on the soot-blackened paper almost a century and a half ago. The scientists belong to an informal collaborative called First Sounds that also includes audio historians and sound engineers. David Giovannoni, an American audio historian who led the research effort, will present the findings and play the recording in public on Friday at the annual conference of the Association for Recorded Sound Collections at Stanford University in Palo Alto, Calif. Scott’s 1860 phonautogram was made 17 years before Edison received a patent for the phonograph and 28 years before an Edison associate captured a snippet of a Handel oratorio on a wax cylinder, a recording that until now was widely regarded by experts as the oldest that could be played back. Mr. Giovannoni’s presentation on Friday will showcase additional Scott phonautograms discovered in Paris, including recordings made in 1853 and 1854. Those first experiments included attempts to capture the sounds of a human voice and a guitar, but Scott’s machine was at that time imperfectly calibrated. “We got the early phonautograms to squawk, that’s about it,” Mr. Giovannoni said. But the April 1860 phonautogram is more than a squawk. On a digital copy of the recording provided to The New York Times, the anonymous vocalist, probably female, can be heard against a hissing, crackling background din. The voice, muffled but audible, sings, “Au clair de la lune, Pierrot répondit” in a lilting 11-note melody — a ghostly tune, drifting out of the sonic murk. The hunt for this audio holy grail was begun in the fall by Mr. Giovannoni and three associates: Patrick Feaster, an expert in the history of the phonograph who teaches at Indiana University, and Richard Martin and Meagan Hennessey, owners of Archeophone Records, a label specializing in early sound recordings. They had collaborated on the Archeophone album “Actionable Offenses,” a collection of obscene 19th-century records that received two Grammy nominations. When Mr. Giovannoni raised the possibility of compiling an anthology of the world’s oldest recorded sounds, Mr. Feaster suggested they go digging for Scott’s phonautograms. Historians have long been aware of Scott’s work. But the American researchers believe they are the first to make a concerted search for Scott’s phonautograms or attempt to play them back. In December Mr. Giovannoni and a research assistant traveled to a patent office in Paris, the Institut National de la Propriété Industrielle. There he found recordings from 1857 and 1859 that were included by Scott in his phonautograph patent application. Mr. Giovannoni said that he worked with the archive staff there to make high-resolution, preservation-grade digital scans of these recordings. A trail of clues, including a cryptic reference in Scott’s writings to phonautogram deposits made at “the Academy,” led the researchers to another Paris institution, the French Academy of Sciences, where several more of Scott’s recordings were stored. Mr. Giovannoni said that his eureka moment came when he laid eyes on the April 1860 phonautogram, an immaculately preserved sheet of rag paper 9 inches by 25 inches. “It was pristine,” Mr. Giovannoni said. “The sound waves were remarkably clear and clean.” His scans were sent to the Lawrence Berkeley lab, where they were converted into sound by the scientists Carl Haber and Earl Cornell. They used a technology developed several years ago in collaboration with the Library of Congress, in which high-resolution “maps” of grooved records are played on a computer using a digital stylus. The 1860 phonautogram was separated into 16 tracks, which Mr. Giovannoni, Mr. Feaster and Mr. Martin meticulously stitched back together, making adjustments for variations in the speed of Scott’s hand-cranked recording. Listeners are now left to ponder the oddity of hearing a recording made before the idea of audio playback was even imagined. “There is a yawning epistemic gap between us and Léon Scott, because he thought that the way one gets to the truth of sound is by looking at it,” said Jonathan Sterne, a professor at McGill University in Montreal and the author of “The Audible Past: Cultural Origins of Sound Reproduction.” Scott is in many ways an unlikely hero of recorded sound. Born in Paris in 1817, he was a man of letters, not a scientist, who worked in the printing trade and as a librarian. He published a book on the history of shorthand, and evidently viewed sound recording as an extension of stenography. In a self-published memoir in 1878, he railed against Edison for “appropriating” his methods and misconstruing the purpose of recording technology. The goal, Scott argued, was not sound reproduction, but “writing speech, which is what the word phonograph means.” In fact, Edison arrived at his advances on his own. There is no evidence that Edison drew on knowledge of Scott’s work to create his phonograph, and he retains the distinction of being the first to reproduce sound. “Edison is not diminished whatsoever by this discovery,” Mr. Giovannoni said. Paul Israel, director of the Thomas A. Edison Papers at Rutgers University in Piscataway, N.J., praised the discovery as a “tremendous achievement,” but called Edison’s phonograph a more significant technological feat. “What made Edison different from Scott was that he was trying to reproduce sound and he succeeded,” Mr. Israel said. But history is finally catching up with Scott. Mr. Sterne, the McGill professor, said: “We are in a period that is more similar to the 1860s than the 1880s. With computers, there is an unprecedented visualization of sound.” The acclaim Scott sought may turn out to have been assured by the very sonic reproduction he disdained. And it took a group of American researchers to rescue Scott’s work from the musty vaults of his home city. In his memoir, Scott scorned his American rival Edison and made brazen appeals to French nationalism. “What are the rights of the discoverer versus the improver?” he wrote less than a year before his death in 1879. “Come, Parisians, don’t let them take our prize.” http://www.nytimes.com/2008/03/27/arts/27soun.html  Hackers Assault Epilepsy Patients via Computer Kevin Poulsen Internet griefers descended on an epilepsy support message board last weekend and used JavaScript code and flashing computer animation to trigger migraine headaches and seizures in some users. The nonprofit Epilepsy Foundation, which runs the forum, briefly closed the site Sunday to purge the offending messages and to boost security. "We are seeing people affected," says Ken Lowenberg, senior director of web and print publishing at the Epilepsy Foundation. "It's fortunately only a handful. It's possible that people are just not reporting yet -- people affected by it may not be coming back to the forum so fast." The incident, possibly the first computer attack to inflict physical harm on the victims, began Saturday, March 22, when attackers used a script to post hundreds of messages embedded with flashing animated gifs. The attackers turned to a more effective tactic on Sunday, injecting JavaScript into some posts that redirected users' browsers to a page with a more complex image designed to trigger seizures in both photosensitive and pattern-sensitive epileptics. RyAnne Fultz, a 33-year-old woman who suffers from pattern-sensitive epilepsy, says she clicked on a forum post with a legitimate-sounding title on Sunday. Her browser window resized to fill her screen, which was then taken over by a pattern of squares rapidly flashing in different colors. Fultz says she "locked up." "I don't fall over and convulse, but it hurts," says Fultz, an IT worker in Coeur d'Alene, Ohio. "I was on the phone when it happened, and I couldn't move and couldn't speak." After about 10 seconds, Fultz's 11-year-old son came over and drew her gaze away from the computer, then killed the browser process, she says. "Everyone who logged on, it affected to some extent, whether by causing headaches or seizures," says Browen Mead, a 24-year-old epilepsy patient in Maine who says she suffered a daylong migraine after examining several of the offending posts. She'd lingered too long on the pages trying to determine who was responsible. Circumstantial evidence suggests the attack was the work of members of Anonymous, an informal collective of griefers best known for their recent war on the Church of Scientology. The first flurry of posts on the epilepsy forum referenced the site EBaumsWorld, which is much hated by Anonymous. And forum members claim they found a message board thread -- since deleted -- planning the attack at 7chan.org, a group stronghold. Fultz says the attack spawned an uncommonly bad seizure. "It was a spike of pain in my head," she says. "And the lockup, that only happens with really bad ones. I don't think I've had a seizure like that in about a year." But she's satisfied with the Epilepsy Foundation's relatively fast response to the attack, about 12 hours after it began on Easter weekend. "We all really appreciate them for giving us this forum and giving us this place to find each other," she says. Epilepsy affects an estimated 50 million people worldwide, about 3 percent of whom are photosensitive, meaning flashing lights and colors can trigger seizures. http://www.wired.com/politics/securi...08/03/epilepsy  Whatever you say pops Turn Off the Lights! John C. Dvorak The April 2008 issue of the magazine is all worked up about things green. I admire the efforts, especially in a tech industry that is based on all forms of waste—from planned obsolescence and hazardous materials to impossible-to-recycle miniaturized components and landfill issues. To make us feel better about the whole thing, let's buy Energy Star products exclusively. Yay! Hey, I have an idea: Grow up and learn to turn off the darn lights in the house! Talk about leaving lights on; I have a view of San Francisco from my home. The place is lit up 24/7 like a Roman candle. Turn off some lights! Why am I the one hassled by all this politically correct green blather while these lights are on? I can only imagine what a nightmarish, overlit world we will inhabit once low- energy LED lights dominate. The worst part is that most of the light isn't used for public safety—or anything else—since it is going into space in what astronomers call "light pollution." From an airplane at 35,000 feet you can see lights everywhere. And what about turning off the computer at night? This would reduce energy use and spam too, since over half the machines left on all night are doing nothing but turning into zombies to send spam all over the place. Of course, this would be easier if computers had an instant-on boot mechanism. Exactly how much energy do you think is wasted when a computer spends 5 minutes booting up? What bothers me most about the green movement is the arrogance—the greener-than-thou attitude—of many participants. Combine these people with the dummies who just go along with the flock regarding what is best for mankind—er, personkind—and you have a dunce brigade telling everyone what to do. One of my favorites is the movement toward cheap, Chinese-made compact fluorescent lightbulbs (CFLs). These things do save energy, but at what cost to the environment? They are loaded with mercury, which I can assure you will end up in landfills leaching mercury into the water and fish that the greeners so dearly love. Seldom will these lightbulbs be "disposed of properly." Exactly what does that mean, anyway? Who do you call? The mercury-removal company? To most people, "dispose of properly" means throw it in the recycle bin, where it will get busted up and contaminate everything in the bin. One specious argument says that using CFLs will reduce the need for electricity, thus reducing the mercury from coal-powered electric plants for a net mercury loss. In fact, people will just keep these lights on all over the place. When has anything taming the overall demand for electricity resulted in burning less coal? We wouldn't need CFLs if we just turned off the blasted lights! Personally, I do not like CFLs because they do not generate any heat. I like my bulbs hot so they can kill the stray mosquito that accidentally gets into the house and wanders toward the light. There are always a few odd dead bugs around a good 100-watt incandescent bulb. This is disease prevention as far as I'm concerned. And the heat from the bulbs helps warm the house in the winter, saving on fuel costs. Heat does warm the air, right? It's not a complete waste, as the CFL lobby wants you to believe.—Next: Back to Computers > But let's get back to computers, since I will never win the lightbulb argument. And don't get me started about using food—corn, that is—to make fuel for cars. How about this for an energy-saving idea: Turn off the computer when you are not using it. Hook all your gear to a good UPS and turn everything off when you go to bed or leave the office, and boot the machine and peripherals only when you are working on something. Leaving desktop computers, laser printers, and other gear on is like leaving a 1,500-watt hair dryer going all day. Part of the problem is that in the late 1980s and early 1990s people were advised to leave their machines on. Being responsible doesn't mean you have to buy a Prius or wear a green badge or ride a bike. It's the little things you get no credit for that make a difference, like buying perfectly good used products, insulating the water heater, turning off the computer, and cooking with pressure cookers. Most of today's greenies are in it for the accolades from fellow travelers who also like to brag about their green accomplishments. The green scene is as good a hobby as a Barnes & Noble book club, but little of it is well directed or realistic. There seems to be a lot of posturing, clichés, pontification, hot air, and out-and-out BS. Welcome to 2008, the Year of the Green. Meanwhile, turn off your lights and computers! http://www.pcmag.com/article2/0,2817,2276127,00.asp Until next week, - js.  Current Week In Review  Recent WiRs - March 22nd, March 15th, March 8th, March 1st Jack Spratts' Week In Review is published every Friday. Submit letters, articles, press releases, comments, questions etc. in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
||
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - September 22nd, '07 | JackSpratts | Peer to Peer | 3 | 22-09-07 06:41 PM |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |