
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 | |||||
|
Join Date: May 2001
Location: New England
Posts: 10,016
|
Since 2002
  "Don’t visit Digg for programming advice. What you’ll hear is questionable at best." – Bryant Zadegan "When Vudu popped up and had more high-definition movies than Blu-ray, it was a warning sign. I think Blu-ray can sustain itself as a transition technology, but, at the end of the day, I don’t think it will ever replace the DVD." – Rob Enderle "I was really scared when I saw the [first] computer. I didn't go near it. I was worried it might explode and kill me. It was only when the teacher called me saying it was harmless that I went into the room, but I still hesitated." – Kamal Prasad Sharma, aged 12 "Welcome to the internets, newcomer... where the men are men, the women are men and the kids are FBI agents.." - jaywalker32 "I am in a (undisclosed) third-world country with no legislation whatsoever about this, so don't worry so much and just enjoy it." – The Coda.fm Guy "We’ve got some unfinished business." – Bob Weir January 10th, 2009  When Labels Fought the Digital, and the Digital Won Dwight Garner APPETITE FOR SELF-DESTRUCTION The Spectacular Crash of the Record Industry in the Digital Age By Steve Knopper 301 pages. Free Press. $26. “You can’t roll a joint on an iPod,” the singer-songwriter Shelby Lynne told The New York Times Magazine early last year. And, O.K., I suppose that’s among the iPod’s drawbacks. But it’s hard to think of an electronic device released in recent decades that’s brought more pleasure to more people. Should anyone care that in the process, the iPod has all but killed the music industry as we’ve known it? Maybe not, Steve Knopper writes in “Appetite for Self-Destruction,” his stark accounting of the mistakes major record labels have made since the end of the LP era and the arrival of digital music. These dinosaurs, he suggests, are largely responsible for their own demise. Mr. Knopper, a contributing editor at Rolling Stone, provides a wide-angled, morally complicated view of the current state of the music business. He doesn’t let those rippers and burners among us — that is, those who download digital songs without paying for them, and you know who you are — entirely off the hook. But he suggests that with even a little foresight, record companies could have adapted to the Internet’s brutish and quizzical new realities and thrived. This is a story that begins in earnest in the early 1980s, when digital music first arrived in the form of the compact disc. At first, Mr. Knopper suggests, almost everyone was frightened of these small, shiny new toys. The labels worried about digital piracy and about refitting the factories that made vinyl LPs. Record stores didn’t want to buy new sales racks. Producers worried about the effects on recording sessions, now that every footstep and door click would be audible. A group called MAD (Musicians Against Digital) quickly formed, and artists like Neil Young declared that CDs were soulless. “The mind has been tricked,” Mr. Young said at the time, sounding a bit like Yoda, “but the heart is sad.” The labels came around because they could jack up prices. (LPs at the time sold for about $9; most CDs went for almost twice that. ) Labels could also renegotiate contracts with artists and force customers to buy entire new album collections. According to Mr. Knopper, executives also thought it was cool watching “that little drawer open and close” on CD players. Producers and artists came around, Mr. Knopper says, because the CD “just sounded better than the LP, no matter how much its detractors complain to this day about losing the rich, warm analog sound.” But record stores remained resistant, and thus the existence of the much loathed cardboard or plastic “longboxes” — remember those? — until the early 1990s. (The author reminds us that in the movie “Defending Your Life” Albert Brooks’s character dies as he tries to tear one open while driving.) “The CD boom lasted from 1984 to 2000,” Mr. Knopper writes. Then the residue of old mistakes and a wave of new realities began hammering the music industry from all sides. One of the first things the labels got wrong, Mr. Knopper says, was the elimination of the single. It got young people out of the habit of regularly visiting record stores and forced them to buy an entire CD to get the one song they craved. In the short term this was good business practice. In the long term it built up animosity. It was suicidal. When Napster and other music-sharing Web sites showed up, the single came back with a vengeance. Before long MP3 — the commonly used term for digitally compressed and easily traded audio files — had replaced sex as the most searched-for term on sites like Yahoo! and AltaVista. The record industry bungled the coming of Napster. Instead of striking a deal with a service that had more than 26 million users, labels sued, forcing it to close. A result, Mr. Knopper writes, was that users simply splintered, fleeing to many other file-sharing sites. “That was the last chance,” he declares, “for the record industry as we know it to stave off certain ruin.” Some of the seeds for this debacle were planted much earlier, during an industry fight in the mid-1980s over Digital Audio Tape (DAT). The labels, once again worried about illegal copying, installed a widget on DATs that permitted songs to be copied only once. But they made a short-sighted allowance for CD-rewrite drives on computers. Users could copy music almost endlessly there. Oops. “They blew it,” a Sony marketer says. “Completely.” The final sections of “Appetite for Self-Destruction” describe the arrival of Steve Jobs and Apple on the scene. The release of the iPod was a kind of coup de grâce for the struggling industry. Before long, Apple became America’s biggest music retailer. Music executives watched, apoplectic and helpless. “Apple had basically taken over the entire music business,” Mr. Knopper writes. He paints a devastating picture of the industry’s fumbling, corruption, greed and bad faith over the decades. (“The business ain’t full of Martin Luther Kings,” one former music executive admits.) It’s too bad his interesting arguments and observations are wedged into such an uningratiating book. The prose in “Appetite for Self-Destruction” is undercooked, packed with clichés (the stakes are always high, people constantly take the fall, one-two punches are thrown) and awkward descriptions. Michael Jackson “danced like a backwards angel, screeched and squealed”; the Sony executive Tommy Mottola “wore gold chains and purple leather jackets and looked cool.” What’s more, Mr. Knopper apparently did not get access to many of the major players in this tale, including Mr. Jobs. His account rehashes material covered in earlier, better books, including “Hit Men” by Fredric Dannen and “The Perfect Thing” by Steven Levy. The record labels have, in the last few years, found some new reasons to believe. Ring tones have become serious business. Computer games like Guitar Hero and Rock Band have taken off, and need to be fed with new songs. And there’s always the hope that Apple’s near monopoly on music sales will be broken by other devices and services, allowing the labels to bargain for a better cut on song sales. That could be a long wait. Apple will always be hard to beat. Mr. Jobs is probably at work right now on an iPod that will roll Shelby Lynne’s joint for her. http://www.nytimes.com/2009/01/07/books/07garn.html  Norwegian Broadcaster's Attempt To "Digitalize" Beatles Goes Sour Brock Thiessen Just when Beatles fans thought the band were finally going digital, the Norwegian national broadcaster has been forced to call off the deal. Broadcasting company NRK has had to remove a series of 212 podcasts, each of which featured a different Beatles song and would have effectively allowed fans to legally download the entire Fab Four catalogue for free. Earlier this week, NRK announced that its 2007 documentary series Vår Daglige Beatles (Our Daily Beatles), would be made available as free podcasts, with each featuring Norwegian journalists telling the story behind a Beatles song and the actual recorded song itself. However, the broadcaster has since hit some legal roadblocks, mostly due to a stipulation that the broadcaster can only post podcasts from shows broadcasted in the previous four weeks. "The Beatles comes under our agreement with IFPI [the organization that owns the rights to the Beatles’ songs], which says that we only can put up shows for download that were aired the latest four weeks, and where the music is less than 70 percent of the show's length," said a statement from NRK. "Our Daily Beatles aired in 2007, so we have to pull the podcast. If it was aired today, we could have podcasted the next four weeks within the agreement We could have done it, but choose not to." And even if NRK did choose to rebroadcast the series, it appears the broadcaster would have to deal with Beatles’ Apple Corps, who don’t seem too happy about the whole thing. “It has recently been reported that a Norwegian broadcasting company, NRK, will make Beatles music available for download via a series of podcasts. These podcasts are not authorized by Apple Corps Ltd.,” the company said in a statement. As previously reported, the Beatles remain one of the last big acts not to offer their catalogue digitally, and they apparently will continue to be. Recently, Paul McCartney said negotiations to get the Fab Four onto iTunes had “stalled,” leaving some fans more than a little ticked that they still have to listen to the band the old-fashioned way. http://www.exclaim.ca/articles/gener...4&fid1=35 621  Overall Total U.S. Music Sales Up In 2008 FMQB Nielsen SoundScan has released its year-end report for 2008 on music sales in the U.S., and while overall music purchased was up, album sales fell for another year. Overall music sales, including albums, singles, all digital tracks and more, grew by 10.5 percent last year, with over 1.5 billion total units sold. However, total album sales declined for the seventh time in eight years, with a 14 percent drop to 428.4 million sold in '08. Digital tracks flew past one billion sold in 2008, with a record 1.07 billion songs sold digitally, a 27 percent jump from '07. Digital album sales grew 32 percent to 65.8 million. Though sales of physical albums sold over the Web fell by 8.6 percent to 27.5 million. All genres saw a decline in album sales in 2008, with Classical music seeing the biggest drop, a 26 percent fall. Country music slipped by 24 percent, with Latin music sales declining 21.1 percent. Metal, Rock, New Age and Alternative saw the smallest declines. The major labels saw their shares of the pie essentially remain the same in 2008. Universal Music Group was on top with 31.52 percent, compared to 31.9 percent the year before. Sony BMG increased its share from 13.86 percent to 15.24 percent in '08. Warner Music Group grew from 20.28 percent to 21.38 percent and EMI slipped from 9.37 percent to 8.97 percent. All other labels made up 12.83 percent of total music sales. Lil Wayne's Tha Carter III was the best-selling album of the year, with 2,874,000 copies sold. Coldplay's Viva La Vida... was the second-biggest seller, followed by Fearless from Taylor Swift, Kid Rock's Rock N Roll Jesus and Black Ice from AC/DC. Swift was also the best-selling overall artist for the year, combining all her album sales. "Bleeding Love" by Leona Lewis was the best-selling individual digital song of '08. The comeback of vinyl continued in 2008, as 1.88 million records were sold last year, more than any other year in the history of SoundScan. Also, over two out of every three vinyl records were sold at independent record stores. http://fmqb.com/Article.asp?id=1084373  Digital Boom Helps British Music Sales Hit Record British music sales are booming as young fans increasingly buy songs online rather than illegally downloading them, the country's industry body said Wednesday. The BPI, formerly known as the British Phonographic Industry, said big-selling releases by artists including Leona Lewis, Coldplay, the Killers and Take That also helped drive sales to record levels last year. The industry has struggled in recent years to adapt to rapidly changing technologies, and has been hit hard by illegal downloading of music via peer-to-peer (P2P) file-sharing websites. But download sales grew by 33 percent last year, while 2008 was the biggest sales year on record in terms of singles sales in all formats, with 115 million single tracks sold. The deepening recession has hit some retailers -- notably Woolworths and high street music retailer Zavvi, formerly Virgin Megastore -- but in other ways it could even be helping the industry, said BPI boss Geoff Taylor. "Every business and consumer in the UK is having a tough time, and these difficult trading conditions make the resilience of the UK's music market all the more notable," he said. "During a recession, people look for purchases that are excellent value for money and bring a lot of enjoyment, and music does just this," he added. While downloads of single tracks have soared, the market for albums has also been helped by growing online sales: some 10 million albums were sold, a 65 percent increase on 2007. Kim Bayley, head of the Entertainment Retailers Association, said traditional high street music sales were also holding up. "Music performed better in UK stores in 2008 than anyone had expected. "The big lesson of 2008 is that if the music is strong enough and retailers work well with suppliers to get that product in-store, music fans will respond and buy in their droves." The upbeat British music news came a day after US technology giant Apple said that every song in its iTunes library will be available without anti-piracy software by April. http://news.theage.com.au/technology...0107-7c2t.html  Want to Copy iTunes Music? Go Ahead, Apple Says Brad Stone In moves that will help shape the online future of the music business, Apple said Tuesday that it would remove anticopying restrictions on all of the songs in its popular iTunes Store and allow record companies to set a range of prices for them. Beginning this week, three of the four major music labels — Sony Music Entertainment, Universal Music Group and Warner Music Group — will begin selling music through iTunes without digital rights management software, or D.R.M., which controls the copying and use of digital files. The fourth, EMI, was already doing so. In return, Apple, whose dominance in online music sales gives it powerful leverage, agreed to a longstanding demand of the music labels and said it would move away from its insistence on pricing all individual song downloads on iTunes at 99 cents. Instead, the majority of songs will drop to 69 cents beginning in April, while the biggest hits and newest songs will go for $1.29. Others that are moderately popular will remain at 99 cents. The music companies are hoping that their eagerly awaited compromise with Apple will give a lift to digital downloads. They will be able to make more money on their best-selling songs and increase the appeal of older ones. And with the copying restrictions removed, people will be able to freely shift the songs they buy on iTunes among computers, phones and other digital devices. Technologically sophisticated fans of digital music complain that D.R.M. imposes unfair restrictions on what they can do with the tracks they have bought. For example, the protected files from iTunes do not work on portable players made by companies other than Apple. “I think the writing was on the wall, both for Apple and the labels, that basically consumers were not going to put up with D.R.M. anymore,” said Tim Bajarin, an analyst with Creative Strategies, a market research company. Music industry watchers widely applauded the move and said it could help digital music sales, which have shown signs of slowing down just five years after Apple introduced iTunes. In particular, lower prices for some songs could spur consumers “to buy deeper into the catalog, and expand their relationship with digital music,” said Russ Crupnick, an analyst with the NPD Group. The music industry could use a lift. Sales of CDs fell 20 percent last year from 2007. About 2.4 billion songs were bought on iTunes in the last year, aided by Apple’s expansion into international markets. But that was not nearly enough to make up for losses in traditional retail stores. Industry pundits have long pointed to D.R.M. as one culprit for the music companies’ woes, saying it alienated some customers while doing little to slow piracy on file-sharing networks. Apple has been campaigning against D.R.M. at least since February 2007, when the chief executive, Steven P. Jobs, wrote an open letter criticizing the software. Apple reached a deal with EMI that year to offer music without the copying restrictions. But it could never reach the same agreement with EMI’s larger rivals. Sony, Warner and Universal allowed other online music services, like Amazon’s MP3 Store, to sell unprotected music, but they withheld it from Apple. Their goal, industry analysts say, was to try to strengthen online rivals to iTunes, which they viewed as having a dangerous level of control over their business. “Apple definitely wanted to remove D.R.M. from music, but the record labels would not allow them to renegotiate their licensing agreements, because they wanted to help competitors succeed against Apple in the market,” said Bill Rosenblatt, president of GiantSteps Media Technology Strategies, a consulting firm. Apple, for its part, appeared to resist variable pricing, fearing it would amount to a price increase for the most popular tracks on iTunes, which constitute the bulk of sales on the service. It has also said the consistent 99-cent price made things simpler for buyers. It is not clear what broke the impasse, but the deteriorating economy may have put pressure on music companies. “For the major labels, it was clearly time for them to accelerate becoming digital music companies in a macroeconomic environment that is downright frightening,” said Greg Scholl, chief executive of The Orchard, a digital distributor of music from independent labels. The compromise gives the recording industry new leverage over their online music sales, Mr. Scholl added. They can start to sell new tracks at the higher price, then gradually drop prices to keep sales moving. Labels could also experiment with bundled packages of songs and even special editions at higher prices. Harry Wang, director of mobile product research at the consulting company Parks Associates, said, “They aren’t going to get a huge amount of money from this new arrangement, but in an ailing music industry, anything that can provide more money will be better than the status quo.” Apple said customers would be able to pay a one-time fee to strip copying restrictions from music they have already bought on iTunes, at 30 cents a song or 30 percent of the album price. ITunes customers can achieve the same effect by burning all of their music to a CD and then reimporting the music into the iTunes software, although this reduces sound quality somewhat. The company also said that its popular iPhone would be able to download songs from iTunes over wireless data networks like AT&T’s. Previously, iPhone owners had to either attach the phone to a computer or connect to a local Wi-Fi network. Apple reported the changes in iTunes at its keynote presentation at the annual Macworld conference in San Francisco, given by Philip W. Schiller, Apple’s senior vice president for worldwide marketing. Mr. Jobs was not at the event, after disclosing this week that he had a treatable hormone problem that had resulted in significant weight loss over the last year. Ben Sisario and Jenna Wortham in New York contributed reporting. http://www.nytimes.com/2009/01/07/te...s/07apple.html  Free Nine Inch Nails Albums Top 2008 Amazon MP3 Sales Charts Nate Anderson Creative Commons provides easy and effective ways to offer up your content without abandoning all rights to its use—free distribution might be allowed, for instance, but only as long as the author is attributed and the distribution is noncommercial. Sounds great for hippies and Web 2.0 types, but what big-name artist would actually commit this sort of career suicide? Nine Inch Nails, for one, and Trent Reznor & Co. produced the bestselling MP3 album of 2008 at Amazon.com, even though the music could be had for free. Ghosts I-IV offered four albums of instrumental music, but Reznor bypassed the normal distribution channels and released the music himself. Ghosts I was offered as a free download and was even thrown up (legally) on The Pirate Bay for anyone to grab, but the entire set of albums was offered under a Creative Commons license. That license allowed free sharing and remixing of the entire work. Though fans could grab the music free of charge, Reznor racked up huge amounts of cash by offering limited edition sets with extras like Blu-ray discs and deluxe packaging; this was widely praised as a way to profit from scarcity while simply giving away the stuff that's easily copied (i.e., the digital bits that make up the music). But Reznor actually made a ton of cash from even those basic digital bits. Forget about the deluxe artwork and the high-priced, limited-edition extras; Reznor actually sold more copies of the basic Ghosts I-IV albums through Amazon's MP3 store than did any other act in 2008. He beat out Coldplay, Death Cab for Cutie, Vampire Weekend, Beck, and hundreds of others, and he did it without a label and by giving the music away. This is exactly the sort of success story that Creative Commons likes to highlight ("See, it's not just for hippies and anarchists— it's for actual business use, too!"), and the group did so Monday with a blog entry that attempts to answer the question of how Reznor succeeded. "So why would fans bother buying files that were identical to the ones on the file sharing networks?" asks Fred Benenson of Creative Commons, and he has an answer. "One explanation is the convenience and ease-of-use of NIN and Amazon's MP3 stores. But another is that fans understood that purchasing MP3s would directly support the music and career of a musician they liked. The next time someone tries to convince you that releasing music under CC will cannibalize digital sales, remember that Ghosts I-IV broke that rule, and point them here." Assuming the answer is correct—fans will directly support work that matters to them—a few additional questions arise. Certainly, a Creative Commons license doesn't mean penury for all musicians, but Reznor had the incredible advantage of a large fan base before taking over music production and distribution. Is the model of "do it all yourself, control all rights, release the music freely" really a feasible one without getting some name recognition first? Second, would CC licensing work for labels? That is, could an indie label release all its music for free sharing and still see good financial results? The feeling of directly supporting an artist would be lost, though there's always the convenience and ease-of-use argument for downloading from a site like Amazon for those who have more money than time. Question and answer I put both questions to Benenson. Regarding the first one, he notes, "Sometimes people say that Reznor has an advantage over independent musicians because he's previously benefited from marketing and traditional record label support. What isn't taken into consideration is that Reznor, through splitting his royalties and earnings over the years, has actually paid for that marketing and then some." Given the ease of digital distribution today, artists are in a better position to be "mini-labels" of their own, hiring marketers and tour managers themselves, as needed, rather than signing away control and huge chunks of revenue. As to the second question about traditional labels adopting CC licenses, Berenson says it's not just possible but already happening. "There are many labels that use Creative Commons licenses. Magnatune is an example of one that uses CC licenses exclusively—you can download everything the label has released for free. They make a significant amount of their income by licensing that music commercially and splitting the revenues with artists. I have about a dozen other labels if you'd like a list." But what about that feeling of direct connection to the artist that buyers get when the artist gets to keep all the cash you pay for their work? "While a lot of NIN's success with Ghosts can be attributed to fans interested in supporting Reznor digitally," Benenson says, "I think this dynamic can work for labels too. That is, if labels can properly message what they do as something that helps artists and new talent (rather than exploiting them), then I think fans will act supportively. "There's an opportunity to add value to the once-cut-and-dry music transaction where it has never existed before—consumers love feeling that they are contributing to something good, and if a label can transparently represent itself (and perhaps more importantly, distance itself from the behavior of the majors) as well as offer new value to its community, then I think the same affect as Reznor's Ghosts offer can be achieved." Licensing music for free and noncommercial distribution might not take over the world in 2009—no other act in Amazon's list did so, though Radiohead (#11) did. Still, it's encouraging to see examples of artists making a living without having to adopt a confrontational approach to fans. Under Reznor's model, everyone wins... well, except for the major labels, which a decade ago would have raked in much of the profit from his work. http://arstechnica.com/news.ars/post...es-charts.html  Obama Picks RIAA's Favorite Lawyer for a Top Justice Post Declan McCullagh As a presidential candidate, Barack Obama won applause from legal adversaries of the recording industry. Stanford law professor Larry Lessig, the doyen of the "free culture" movement, endorsed the Illinois senator, as did Google CEO Eric Schmidt and even the Pirate Party. That was then. As president-elect, one of Obama's first tech-related decisions has been to select the Recording Industry Association of America's favorite lawyer to be the third in command at the Justice Department. And Obama's pick as deputy attorney general, the second most senior position, is the lawyer who oversaw the defense of the Copyright Term Extension Act--the same law that Lessig and his allies unsuccessfully sued to overturn. Obama made both announcements on Monday, saying that his picks "bring the integrity, depth of experience and tenacity that the Department of Justice demands in these uncertain times." The soon-to-be-appointees: Tom Perrelli for associate attorney general and David Ogden for deputy attorney general. Campaign rhetoric aside, this should be no surprise. Obama's selection of Joe Biden as vice president showed that the presidential hopeful was comfortable with someone with firmly pro-RIAA views. Biden urged the criminal prosecutions of copyright-infringing peer-to-peer users and tried to create a new federal felony involving playing unauthorized music. Perrelli is currently a partner in the Washington offices of Jenner and Block, where he represented the RIAA in a a slew of cases, including a high-profile bid to unmask file sharers without the requirement of a judge reviewing the evidence first. Verizon initially lost to the RIAA, but eventually prevailed in 2003 when a federal appeals court ruled the record labels' strategy under the Digital Millennium Copyright Act was unlawful. Perrelli has represented the RIAA in other lawsuits against individual file sharers. One filed in Michigan accuses a university student of distributing "hundreds of sound recordings over his system without the authorization of the copyright owners." A lawsuit against a Princeton University student makes similar arguments; Perrelli and his colleagues also tried to force Charter Communications to give up the names of 93 file-trading subscribers. A 2004 summary of a Boston lawsuit written by Harvard's Berkman Center--which opposed the RIAA in this and a current case--quotes Perrelli as telling a federal judge that it would be easy to determine who was using a wireless network to share music. "It is correct that the actual downloader may be someone else in the household," he said, but any errors can be determined easily after a "modest amount of discovery." An article on his law firm's Web site says that Perrelli represented SoundExchange before the Copyright Royalty Board--and obtained a 250 percent increase in the royalty rate for music played over the Internet by companies like AOL and Yahoo. Perrelli previously worked in the Clinton Justice Department. An article in Legal Times titled "Building an Entertainment Beast in D.C." says that in 2002, Perrelli used Jenner's reputation as an appellate law firm to "get a meeting with officials at the RIAA, at a time when Internet file-sharing entities like Napster were threatening the music business." A year later, in 2003, the law firm recruited Steven Fabrizio, previously the RIAA's senior vice president for business and legal affairs, and business began booming (the RIAA also used the Jenner law firm to write a friend-of-the-court brief in the copyright extension lawsuit). If confirmed by the Senate, which is unlikely to pose much of a hurdle, Perrelli would oversee the department's civil division, the antitrust division, and the civil rights division. Obama's choice for deputy attorney general--the second-in-command at Justice--is David Ogden, who's currently a partner at the WilmerHale law firm. As assistant attorney general for the civil division, Ogden was responsible for organizing the defense of the Child Online Protection Act, or COPA, an antiporn law that has been challenged by the ACLU in court for more than a decade with no resolution. His department also successfully defended the Sonny Bono Copyright Term Extension Act before the U.S. Supreme Court. Ogden's biography at Wilmer Hale says only that he represents the "media and Internet industries, as well as major trade and professional associations," without listing details. The Justice Department, barring exceptional cases, has a duty to defend laws enacted by Congress. Perrelli, on the other hand, went out of his way to recruit the RIAA as a very lucrative client: his law firm bills some partners' time at a princely $1,000 an hour. During his confirmation hearing, it will be instructive to see if senators ask whether his zealous anti-file sharing advocacy can make him an objective civil servant--especially when these same politicians want the Justice Department to sue peer-to-peer pirates at taxpayer's expense. (Then again, if that proposal becomes law, Perrelli's surely the right man for the job.) It will also be instructive to see if this week's news prompts some of the RIAA's longtime adversaries to moderate their enthusiasm for Obama's technology policies. http://news.cnet.com/8301-13578_3-10133425-38.html  RI Judge Hears Arguments in Music Downloading Case AP A Rhode Island couple whose son is accused of illegally sharing songs online should not be forced to surrender their home computer for inspection because it would violate their privacy, their lawyer argued at a federal court hearing Tuesday. Joel Tenenbaum, a 25-year-old Boston University graduate student, is accused by the Recording Industry Association of America of downloading at least seven songs and making 816 music files available for distribution on the Kazaa file-sharing network through 2004. The industry’s lawsuit against him is part of an aggressive campaign targeting people who share music online. The industry says it’s lost billions of dollars because of peer-to-peer networks that make it easy for Internet users to share songs online. Record company lawyers believe Tenenbaum downloaded the songs on his parents’ personal computer in Providence and urged a federal magistrate on Tuesday for permission to copy the machine’s hard drive for proof of copyright infringement. "The information on the computer is directly relevant and material to the underlying claims in this case," said industry lawyer Daniel Cloherty. But Charles Nesson, a Harvard Law professor representing Arthur and Judie Tenenbaum, said the computer contains information protected by attorney-client privilege and holds other sensitive and personal material that has nothing to do with the case. "You can hardly imagine anything more intrusive than asking anyone to disgorge a computer," said Nesson, who is also challenging in U.S. District Court in Boston the constitutionality of a federal copyright law that the music industry has used to target song-swappers. Nesson also argued that the computer was not the one on which the alleged downloading took place. Judie Tenenbaum has stated in an affidavit that the couple bought the computer after their son had left home, and that he had only used it only occasionally to check his e-mail. Magistrate Judge Lincoln Almond did not immediately rule. Joel Tenenbaum had offered to settle the case for $500 after the industry confronted him in September 2005 with allegations of illegal file-sharing. But music companies rejected that, demanding $12,000. They sued in 2007. Judie Tenenbaum said outside court Tuesday that the lawsuit has been a "horrible" and time-consuming experience. RIAA spokeswoman Cara Duckworth said the industry group wanted to settle the case quickly but blamed Nesson for dragging it out. "During the past several years, thousands of regular working class folks in the music community have lost their jobs precisely because of the illegal activity involved in this case," she said in a written statement. "While this might be an interesting academic exercise for the professor and his class, there’s been real world consequences for those who create music." http://news.bostonherald.com/enterta...osition=recent  Local news RIAA Gives Up In Atlantic Recording v. Brennan NewYorkCountryLawyer In Atlantic Recording v. Brennan, the landmark Connecticut case in which the first decision rejecting the RIAA's "making available" theory was handed down, the RIAA has finally thrown in the towel and dismissed its own case (PDF). Mr. Brennan never appeared in the case at all. In February, 2008, the RIAA's motion for a default judgment was rejected for a number of reasons, including the Court's ruling (PDF) that there is no claim for "making available for distribution" under the US Copyright Act. The RIAA moved for reconsideration; that motion was denied. Then, in December, the RIAA's second motion for default judgment was rejected. Finally the RIAA filed a "notice of dismissal" ending the case." http://news.slashdot.org/article.pl?sid=09/01/09/022236  Changing Tack, RIAA Ditches MediaSentry Sarah McBride In another sign of the music industry's recently announced retreat from a five-year-old antipiracy strategy, the Recording Industry Association of America has dumped the company it used to help it gather evidence for mass lawsuits it filed against people it claimed were illegally uploading copyrighted music. The RIAA long used a company called MediaSentry to troll the Internet in search of people who uploaded large amounts of music. The information that MediaSentry collected became an integral part of the RIAA's aggressive litigation campaign. Since 2003, the RIAA -- a trade organization representing Vivendi SA's Universal Music Group, Sony Corp.'s Sony BMG Music Entertainment, EMI Group Ltd. and Warner Music Group Corp. -- has sued around 35,000 people for what it says are illegal music uploads. Now the RIAA will be rid of a company that became a frequent target of civil-rights advocates and others who complained that the RIAA's legal tactics were excessive. MediaSentry is a unit of closely held, Belcamp, Md.-based SafeNet Inc. Ray Beckerman, a New York lawyer who maintains the Recording Industry vs. the People blog and who has represented more than a dozen clients fighting the RIAA, said he considered the decision to drop MediaSentry a "victory" for his clients. MediaSentry representatives "have been invading the privacy of people. They've been doing very sloppy work," he said. Mr. Beckerman cites MediaSentry's practice of looking for available songs in people's file-sharing folders, downloading them, and using those downloads in court as evidence of copyright violations. He says MediaSentry couldn't prove defendants had shared their files with anyone other than MediaSentry investigators. MediaSentry says its work is high quality. The RIAA also stands by MediaSentry's techniques, citing University of Washington research released last year that concluded the company's methodology incorporates "best practices." The RIAA decided quietly to drop MediaSentry several months ago. It didn't disclose why. John Desmond, vice president at MediaSentry, said that the company had already begun to wind down its evidence-collecting business. Instead, it is focusing on other areas, such as measuring the popularity of various online entertainment sites. The RIAA announced last month that it planned to curtail its practice of filing mass lawsuits for copyright infringement. However, it still plans to closely monitor people it believes are illegally uploading copyrighted music, and continue with the legal action it already has in progress. It says it will still file lawsuits for exceptional cases. In place of MediaSentry, the RIAA says it will use Copenhagen-based DtecNet Software ApS. The music industry had worked with DtecNet previously both in the U.S. and overseas, and liked its technology, said RIAA spokesman Jonathan Lamy. http://online.wsj.com/article/SB123109364085551895.html  Online Video-Sharing Sites Score Copyright Victory David Kravets Online video-sharing sites are scoring another major legal victory, as a federal judge is ruling that the Digital Millennium Copyright Act protects such sites from copyright violations if they abide by takedown notices as the DMCA prescribes. The case was brought by Universal Music Group, which claimed that San Diego-based Veoh -- financially backed by Time Warner and Michael Eisner – engaged in wanton copyright infringement because it allowed users to upload and store the music concern's copyrighted videos. U.S. District Judge Howard Matz agreed with Veoh that its business model complied with the 1998 Digital Millennium Copyright Act's so-called safe harbor provisions. The case is similar to other suits targeting YouTube, MySpace, MP3Tunes and others. And it marks just the second time that a federal judge has ruled the DMCA protects video-sharing sites – even user-generated sites like Veoh that transform user-uploaded content into flash-formatted videos that can later be accessed by users. U.S. District Judge Howard Matz, citing the DMCA's language, ruled (.pdf) that copyright law precludes monetary liability on a service provider "for infringement of copyright by reason of the storage at the discretion of a user of material that resides on a system or network controlled or operated by or for the service provider." Matz noted that in order to win immunity under the DMCA, the service provider, in this case Veoh, must not have "actual knowledge" of the infringing material and, among other things, "must expeditiously remove or disable access to material if it is notified that the material is infringing or is the subject of infringing activity." Veoh scored its first victory in August, when a San Jose magistrate dismissed a lawsuit with similar allegations brought by porn company IO Group. Both rulings are not binding on other judges, however. And neither the U.S. appellate courts nor the U.S. Supreme Court has directly addressed the issue. Check out the Electronic Frontier Foundation's take by Fred von Lohmann on the topic. http://blog.wired.com/27bstroke6/200...-video-sh.html  Feds Note Gaming DRM Woes: FTC to Hold Town Hall Meeting Ben Kuchera 2008 may become known as the year of digital rights management, thanks in no small part to EA's bringing the issue front and center with Spore and the ensuing backlash. These days gamers want to know what kind of DRM a game employs before they make a purchase, and for many people the inclusion of SecuROM means a lost sale. All of the sound and fury surrounding the issue has gotten the attention of the Federal Trade Commission, and the government agency is planning on holding a town hall meeting devoted to the subject of DRM on March 25. The official page describes the meeting and its aim. "Digital rights management (DRM) refers to technologies typically used by hardware manufacturers, publishers, and copyright holders to attempt to control how consumers access and use media and entertainment content," the FTC explains. "Among other issues, the workshop will address the need to improve disclosures to consumers about DRM limitations." The agenda includes demonstrations of DRM-related technology, panel discussions about how these technologies affect consumers, legal issues surrounding DRM, and discussions on the potential need for government involvement to protect consumers. You can get involved, as well. "The Commission invites interested parties to submit requests to be panelists and to recommend other topics for discussion. The requests should be submitted electronically to drmtownhall@ftc.gov by January 30, 2009....The Commission will select panelists based on their expertise and on the need to represent a range of views." If you would simply like to have your voice heard you can submit comments or original research as well. This is an excellent opportunity to make your voice heard on this matter, and to explain your feelings on the state of DRM in the gaming industry. Is this a matter that deserves government attention? Absolutely. Having standards for disclosure of what exactly you're installing with your software, along with easily available tools to remove those programs, would go a long way toward keeping publishers honest about what is shipping with our games. A recent class-action lawsuit filed against EA is indicative of the problem: "Consumers are given no notices whatsoever that the FREE trial version of [Spore] includes Digital Rights Management technology... Consumers are given no control, rights, or options over SecuROM," the suit alleges. "The program cannot be completely uninstalled." The suit lists some of the potential side-effects of having the program installed on a system, including disruption of fire walls and "complete operating system failure." Too often, customers have no clear picture of what else they may be installing onto their computer when they buy a game, or how those programs could affect the day-to-day use of that computer. There is no disclosure, no accountability, and very little education going on around the issue of DRM and its related technologies. It's likely the discussion will be lively, with both publishers and consumer rights associations weighing in. The core issue is a simple one, however: consumers deserve to know what they're installing, and exactly what it does. It's looking increasingly likely that consumers may need the FTC's help to make sure what happens during software installations becomes as transparent and open as possible. The town hall meeting will take place at the University of Washington School of Law, and will be free and open to the public, no registration required. http://arstechnica.com/news.ars/post...l-meeting.html  Hustler Hires Media Protector to Chase Online Porn Pirates enigmax Hustler Europe, part of the world’s largest adult entertainment company, has hired anti-piracy company Media Protector to start chasing down file-sharers. The partnership will have a familiar aim - to find alleged infringers on P2P networks and send them threats to pay up - or else. Hustler Europe is getting on the “turn piracy into profit” bandwagon. It has recently hired anti-piracy tracking company Media Protector to start tracking down those who share Hustler videos online. Media Protector operates in a similar way to tracking company Digiprotect, who currently work with lawyers Davenport Lyons in the UK. It connects to BitTorrent swarms, eD2k and other filesharing networks, and harvests IP addresses of those sharing copyright works without permission. Media Protector then works with lawyers to force ISPs to disclose the personal details of those allegedly sharing files, sending them letters ordering them to pay a ‘fine’ (out-of-court settlement) or face legal action. “We are working today with a lot of international rights-holders and leading production companies — including Hustler, the world’s largest adult entertainment company — and have detected well over 200,000 copyright infringements in Germany alone,” Media Protector founder and Managing Director Rainer Strassmeir told Xbiz. Strassmeir believes that aggressive anti-piracy enforcement is the key to embedding a type of fear in the illegal downloader. He claims it soon becomes known which content producers chase pirates, with those that do witnessing a corresponding decrease in illicit downloads. He also believes that the decrease in piracy leads to an increase in retail sales. Anti-piracy company Digiprotect has been open about its aims - it says it helps clients “turn piracy into profit”, although the lawyers it works with in the UK deny that there is any profit motive, rather their actions are purely for anti-piracy purposes. Strassmeir isn’t embarrassed to say that he tries to generate profit from piracy either, as he states that his customers “enjoyed a new revenue stream by effectively monetizing copyright infringements.” Last year, the evidence collected by Media Protector was called into doubt. A recipient of a 700 Euro compensation demand for unauthorized uploading was actually operating a client which was modified never to upload, thus making infringement impossible. http://torrentfreak.com/hustler-hire...irates-090103/  Trojan Blocks The Pirate Bay and Mininova Ernesto A new trojan popped up at several torrent sites a few weeks ago, one that blocks access to The Pirate Bay and Mininova, while informing its victims that “downloading is wrong.” The trojan edits the hosts file on Windows machines, and redirects the BitTorrent sites to localhost, making them impossible to load. The trojan in question (Troj/Qhost-AC) identified by anti-virus company Sophos, is a rather unusual one. It doesn’t seem to install spyware or traditional malware, but instead blocks access to the two most popular BitTorrent sites. One of its victims, who got the trojan from downloading a torrent from The Pirate Bay, contacted TorrentFreak. He told us: “I didn’t follow the well established rules of downloading. It was a file with a low number of seeds, many leechers and no comments. I’ve downloaded the file and didn’t visit the torrent page again to view if there were any negative comments.” It turned out that the trojan originated from a keygen supplied with a copy of pirated software. Instead of generating a key, it modified the hosts file of the computer so that it redirects The Pirate Bay, Suprbay (The Pirate Bay forums) and Mininova to 127.0.0.1, which means that the sites never load. Aside from blocking the three sites in question, the trojan caused popups and even played a sound file saying that “downloading is wrong”. The bad torrent was removed from The Pirate Bay soon after users commented that the key generator didn’t work, but it is safe to assume that this is not the first and only attempt to spread a trojan like this one. The question remains, who is behind this? While some might argue that the MPAA, RIAA or other anti-piracy advocates might be the source, we think it more likely that the attack originates from a relatively innocent prankster targeting pirates. The good news is that it is fairly easy to fix, manually removing the entries from the hosts file solves the problem. “Overall a bad experience, but the computer is fine now,” the affected user told us. Advice and tips about the Windows Hosts file can be found here. http://torrentfreak.com/trojan-block...ninova-090104/  Contemplating the Consumerist Sale and the Adpocalypse Jon Stokes Plans to ride out a possible advertising nuclear winter continue apace at Gawker Media, Nick Denton's New York blog publishing mini-empire, with the recent announcement that Consumerist.com is being sold to the Consumers Union, publisher of Consumer Reports. YouTube's future (or lack thereof) Consumerist is the latest of Denton's blogs to be sold off, in a move that he described in an e-mail to AllthingsD's Peter Kafka as part of the process of "pruning" his network down to only his highest-growth, most profitable sites. Hollywood gossip site Defamer.com is also on the block. Consumers Union claims that it won't be making any editorial changes to its new property, with the group insisting that the site's snarky editorial voice represents a return to the somewhat staid organization's early roots as a scrappy consumer advocate. Much more interesting, though, than the actual sale of Consumerist—either what was paid for it (Kafka says "mid six figures") or what will be done with it (see Portfolio's Felix Salmon for a good, insidery post on this)—is Denton's reason for thinning the herd. In short, he's planning for an economy in which online ad spending tanks by a whopping 40 percent before it turns back up again (whenever that is). Cliff diving: Internet edition (h/t CR) Back in November, when doom-and-gloom presentations at public conferences and in private boardrooms were all the rage, Denton published his own take on the economic meltdown. Called "Doom-Mongering: a 2009 Internet Media Plan," this read is as gloomy as they come. Denton takes Mary Meeker's (in)famous Web 2.0 presentation as a starting point; in it, the Morgan Stanley analyst suggested that for each percentage point decline of GDP growth, advertising market growth drops roughly three times as fast. But Denton thinks that Meeker is too optimistic, and he refines her results with some other GDP and ad market data from downturns in Indonesia, Sweden, and Japan to arrive at an ad market spending collapse of between 9 and 43 percent over the course of the entire downturn. Denton then advises publishers to prepare for the worst-case scenario of an eventual 40 percent decline, with a possible 27 percent drop coming in 2009. I can't speak in detail to the numbers behind Denton's projection, so I leave the projection itself as just a data point, maybe an outlier, but not necessarily worth discounting. (Indeed, if the past few months have taught us anything, it's that even outliers to the downside can be too optimistic.) Before moving on to a summary of my own thoughts on this issue, developed over the course of some recent, off-the-record conversations with analysts and media types, I want to offer two more data points for your consideration. The first datapoint is a widely cited MasterCard report (linked at Ars but most widely known from the WSJ report on it), which shows an unprecedented, double-digit year-over-year decline in the advertiser-heavy luxury goods and electronics categories (35 percent and 27 percent, respectively). And this is in the face of super-steep discounts at retail outlets. The second datapoint is a research note from Morgan Stanley's Mark Lipacis, who created some ripples in the (admittedly very small) semiconductor econ blogging pool with his forecast that chip company revenues could decline as much as 30 percent next year, leading to earnings-per-share drops of as high as 78 percent. For my own reporting on the severe, margin-killing supply glut facing the chip sector next year, see this post. In short, a 30 percent decline in net revenues for semis next year would not surprise me, and it would have painful ripple effects in the ad market via reduced spends for companies like Sony, Toshiba, Intel, AMD, and many others. So things look bad in 2009, but there's a light at the end of the tunnel, right? Wait; maybe that's an oncoming train. Ad infinitum Most of the discussion of ad spending and GDP (non)growth skips lightly over the question of value, but it's a question that's worth asking. Specifically, what if the end result of all of this pain and trauma will be not a return to the "normalcy" of the past decade but a reappraisal and repricing of the basic units of online display advertising? Denton himself touches on these issues twice in his memo. The first time is a mention in passing of a point that I've heard made at two different conferences, i.e., that nothing can move the sales needle in a dramatic and measurable way like good TV exposure; if you get on Oprah or buy a Superbowl spot, then the very next day you can expect to sell a whole lot of whatever you were hawking. The second place where Denton touches on this point is when he raises the issue of the restrictive nature of online display ad formats. I actually think about this a lot, myself, especially in the light of my academic interest in the history of media. In short, both a TV program and a magazine represent a finite unit of (more or less) undivided attention. Each of these media objects is carefully designed to grab your attention and to hold it within a bounded space—with boundaries being the start and end times of the program for TV, or the two covers of a magazine. What advertisers buy when they purchase a magazine or TV ad is slice of the attention of some subset of that media object's audience. And the ads that they create for those purchased slices are attention-worthy objects in and of themselves, e.g., Angelina Jolie posing with a diamond watch, or a hilarious vignette centered around a brand of beer. A web page, in contrast, is typically festooned with hyperlinked visual objects that fall all over themselves in competing to take you elsewhere immediately once you're done consuming whatever it is that you came to that page for. So the page itself is just one very small slice of an unbounded media experience in which a nearly infinite number of media objects are scrambling for a vanishingly small sliver of your attention. Advertisers already seem to have a sense that this sliver of attention that they're getting is extremely miniscule, and they also know that it grows ever smaller as web users become more proficient at navigating the cacaphony of links in order to focus their attention on precisely what they came to a page for (content). This being the case, it's entirely possible that cash-strapped advertisers will have exactly the same kind of "moment of clarity" that shopaholic consumers are reportedly having now that they've seen entire store inventories marked down 50 percent or more in pre-Christmas sales—that is, they may say to themselves, "We knew all along that this stuff was made in China for a tiny fraction of what it sells for here; we were nuts to pay so much in markup for it." Note that no one should interpret the above as some sort of prediction on my part that display ads will be permanently and drastically repriced downwards because advertisers are deciding that the standard IAB units really aren't worth anything close to what they've been paying for them. But I do throw this out there as being somewhere on the spectrum of possible outcomes, and I'm not alone in entertaining this possibility at least as a hypothetical. In conclusion, the online advertising experiment in which so many of us have engaged is really only ten years or so old. Those who say that it's "mature" are not only mistaken, but they drastically underestimate what a true break the web is from the offline media that came before. We've had a few hundred years to learn to monetize print, over 75 years to monetize TV, and, most importantly, millennia to build business models based on scarcity. In contrast, our collective effort to monetize post-scarcity digital media have only just begun. http://arstechnica.com/news.ars/post...pocalypse.html  Police Set to Step Up Hacking of Home PCs David Leppard THE Home Office has quietly adopted a new plan to allow police across Britain routinely to hack into people’s personal computers without a warrant. The move, which follows a decision by the European Union’s council of ministers in Brussels, has angered civil liberties groups and opposition MPs. They described it as a sinister extension of the surveillance state which drives “a coach and horses” through privacy laws. The hacking is known as “remote searching”. It allows police or MI5 officers who may be hundreds of miles away to examine covertly the hard drive of someone’s PC at his home, office or hotel room. Material gathered in this way includes the content of all e-mails, web-browsing habits and instant messaging. Nowhere to hide Under the Brussels edict, police across the EU have been given the green light to expand the implementation of a rarely used power involving warrantless intrusive surveillance of private property. The strategy will allow French, German and other EU forces to ask British officers to hack into someone’s UK computer and pass over any material gleaned. A remote search can be granted if a senior officer says he “believes” that it is “proportionate” and necessary to prevent or detect serious crime — defined as any offence attracting a jail sentence of more than three years. However, opposition MPs and civil liberties groups say that the broadening of such intrusive surveillance powers should be regulated by a new act of parliament and court warrants. They point out that in contrast to the legal safeguards for searching a suspect’s home, police undertaking a remote search do not need to apply to a magistrates’ court for a warrant. Shami Chakrabarti, director of Liberty, the human rights group, said she would challenge the legal basis of the move. “These are very intrusive powers – as intrusive as someone busting down your door and coming into your home,” she said. “The public will want this to be controlled by new legislation and judicial authorisation. Without those safeguards it’s a devastating blow to any notion of personal privacy.” She said the move had parallels with the warrantless police search of the House of Commons office of Damian Green, the Tory MP: “It’s like giving police the power to do a Damian Green every day but to do it without anyone even knowing you were doing it.” Richard Clayton, a researcher at Cambridge University’s computer laboratory, said that remote searches had been possible since 1994, although they were very rare. An amendment to the Computer Misuse Act 1990 made hacking legal if it was authorised and carried out by the state. He said the authorities could break into a suspect’s home or office and insert a “key-logging” device into an individual’s computer. This would collect and, if necessary, transmit details of all the suspect’s keystrokes. “It’s just like putting a secret camera in someone’s living room,” he said. Police might also send an e-mail to a suspect’s computer. The message would include an attachment that contained a virus or “malware”. If the attachment was opened, the remote search facility would be covertly activated. Alternatively, police could park outside a suspect’s home and hack into his or her hard drive using the wireless network. Police say that such methods are necessary to investigate suspects who use cyberspace to carry out crimes. These include paedophiles, internet fraudsters, identity thieves and terrorists. The Association of Chief Police Officers (Acpo) said such intrusive surveillance was closely regulated under the Regulation of Investigatory Powers Act. A spokesman said police were already carrying out a small number of these operations which were among 194 clandestine searches last year of people’s homes, offices and hotel bedrooms. “To be a valid authorisation, the officer giving it must believe that when it is given it is necessary to prevent or detect serious crime and [the] action is proportionate to what it seeks to achieve,” Acpo said. Dominic Grieve, the shadow home secretary, agreed that the development may benefit law enforcement. But he added: “The exercise of such intrusive powers raises serious privacy issues. The government must explain how they would work in practice and what safeguards will be in place to prevent abuse.” The Home Office said it was working with other EU states to develop details of the proposals. http://www.timesonline.co.uk/tol/new...cle5439604.ece  NYPD Wants to Jam Cell Phones During Terror Attack Noah Shachtman The New York Police Department wants to be able to shut down cell phones, in case of a terrorist attack. During last month's massacre in Mumbai, terrorist handlers over micromanaged via mobile phone the assaults on the hotels, train stations, and Jewish center that killed more than 170 people. In testimony today before the Senate Committee on Homeland Security and Governmental Affairs, New York Police Commissioner Ray Kelly (pictured) said he wanted to take out that "formidable capacity to adjust tactics while attacks are underway." Quote:
But Charles Allen, the Department of Homeland Security's top intelligence official, confessed to the Senate panel that "response to a similar terrorist attack in a major U.S. urban city would be complicated and difficult." Quote:
 British Government Wants Private Firm To Monitor Super Database Of Every Person In Britain Bill Lindner The British Government is contemplating the third-party construction of a super database containing the identities and location of every person in Britain. The 'super database,' which comes at the hefty cost of 12 billion British pounds, would be run by one or a number of private companies and would track every citizen's Internet usage, every phone call, every text message, as well as many other transactions. The government claims the database is necessary to fight terrorism and serious crime. Of course, the government also claims it would come with stringent safeguards to protect a user's personal private information, but if history is any indication, those safeguards would prove mostly ineffectual and that information will inevitably end up being leaked into the public domain. (Source: telegraph.co.uk) The British government -- as well as the U.S. and many other governments -- has had major problems keeping the private information of its citizens safe. Last year, the UK's HM Revenue & Customs Department lost 25 million child benefit records. (Source: techworld.com) Needless to say, the personal and privacy rights violations could be quite staggering and no matter what alleged safeguards are put in place, the resulting violations could be disastrous. As history has repeatedly proven, no government can be trusted to protect so much personal information. (Source: guardian.co.uk) As noted by Sir Ken MacDonald, former Director of Public Prosecutions, "the tendency of the state to seek ever more powers of surveillance over its citizens may be driven by protective zeal, but the notion of total security is a paranoid fantasy which would destroy everything that makes living worthwhile. It would be a complete readout of every citizen's life in the most intimate and demeaning detail." (Source: theregister.co.uk) The new plan, to be outlined early this year in a consultation paper on the interception modernization program, would allow one or a number or organizations to proactively collect all communications data, including broadband phone calls and chat rooms instead of being provided by the ISP's and telecoms at the request of the police or other governmental agencies. Internet Service Providers and Telecom companies are already able to provide the police necessary information about the whereabouts and identities of suspects when necessary. http://www.infopackets.com/news/cens...in_britain.htm    Hard Drive Destruction 'Crucial' BBC The only way to stop fraudsters stealing information from old computer hard drives is by destroying them completely, a study has found. Which? Computing magazine recovered 22,000 "deleted" files from eight computers purchased on eBay. Freely available software can be used to recover files that users think they have permanently deleted. While Which? recommends smashing hard drives with a hammer, experts say for most consumers that's a step too far. Criminals source old computers from internet auction sites or in rubbish tips, to find users' valuable details, and a number of recent cases have shown the dangers in disposing of second-hand equipment. A number of software solutions exist to more definitively erase files and information. The most straightforward solution, according to Which?, is complete destruction - and it recommends using a hammer. It must be done with caution because those smithereens contain environmentally harmful materials so they should be recycled - for instance at the vendor from whom a new hard drive is purchased. Worth it? However experts advise that even a treatment with a hammer may not be the end of your data. Expensive and sophisticated techniques could be used to recover deleted data, even from a hard drive platter that has been physically damaged. But for most people, the freely available deleting software or a simple hard drive formatting procedure should make the data sufficiently difficult to retrieve as to not be worth a criminal's time. "You can get a credit card number on the internet for about ten pounds from credit card thieves," says Rupert Goodwins, editor of technology news website ZDNet. "So nobody's going to spend more than ten pounds trying to nick your credit card number off your hard disk." Mr Goodwins argues that the free software is as effective as the hammer - indeed, he argues it is as effective as the software that can be quite costly. "Unless you're a spook or the kingpin of a criminal consortium, there's no need to go out and buy deleting software and no need to put a hammer through the damned thing," Mr Goodwins told the BBC. "If you're that worried, get rid of it properly: burn it or put it in acid." http://news.bbc.co.uk/2/hi/technology/7816446.stm  UK e-Mail Law 'Attack on Rights' Angus Crawford Rules forcing internet companies to keep details of every e-mail sent in the UK are a waste of money and an attack on civil liberties, say critics. From March all internet service providers (ISPs) will by law have to keep information about every e-mail sent or received in the UK for a year. Human rights group Liberty says it is worried what will happen next. The Home Office insists the data, which does not include e-mails' content, is vital for crime and terror inquiries. Some three billion e-mails are thought to be sent each day in the UK. Safe keeping Shami Chakrabarti, director of Liberty, said ISPs already kept the information on a voluntary basis. "The thing we have to worry about is what happens next because the government is already mooting plans not just to leave this stuff with the providers but to create a central government database where they hold all the information. "I'm afraid we just don't trust any government or any organisation to keep that much very sensitive information about us all and to keep it safe." Critics of the new rules also include an association of internet service providers and computer experts. Dr Richard Clayton, a security researcher at the University of Cambridge's computer lab, said the money could have been better spent. He said:"There's going to be a record of every single e-mail which arrived addressed to you and all the e-mails you sent out via your ISP. "That, of course, includes all the spam. "I'd have liked to see more bobbies on an electronic beat investigating internet crimes. "There are much better things to do to spend our billions on than snooping on everybody in the country just on the off-chance that they're a criminal." The new rules are due to come into force on 15 March, as part of a European Commission directive which could affect every ISP in the country. The firms will have to store the information and make it available to any public body which makes a lawful request, which could include police, local councils and health authorities. To help set up the system the government may end up paying ISPs between £25m and £70m. The rules already apply to telephone companies, which routinely hold much of the data for billing. The Earl of Northesk, a Conservative peer on the House of Lords science and technology committee, said it meant anyone's movements could be traced 24 hours a day. "This degree of storage is equivalent to having access to every second, every minute, every hour of your life," he said. "People have to worry about the scale, the virtuality of your life being exposed to about 500 public authorities. "Under Article 8 of the European Convention on Human Rights, privacy is a fundamental right... it is important to protect the principle of privacy because once you've lost it, it's very difficult to recover." The Home Office said the data was a vital tool for investigation and intelligence gathering. "It will allow investigators to identify suspects, examine their contacts, establish relationships between conspirators and place them in a specific location at a certain time. "Implementing the EC directive will enable UK law enforcement to benefit fully from historical communications data in increasingly complex investigations and will enhance our national security." 'Better things' But the industry itself has concerns about how the new rules will work. Malcolm Hutty, from LINX (London Internet Exchange), a membership association for ISPs, said: "The position as to what the ISPs are to do is not clear." He said on paper the law applied to all companies, but the Home Office has been saying informally that small ISPs would be exempt. He said they were now left "in limbo", fearful of legal action if at some time in the future as the company became bigger, they were then expected to collect the data. Reports have suggested the government has even bigger plans for data retention called the Interception Modernisation Programme. It could involve one central database, gathering details on every text sent, e-mail sent, phone call made and website visited. Consultation on the plans is due to begin later this year. http://news.bbc.co.uk/go/pr/fr/-/1/hi/uk/7819230.stm  Deep Throat Meets Data Mining In the nick of time, the digital revolution comes to democracy's rescue. And, perhaps, journalism's. John Mecklin If you pay passing attention to the media landscape, you know that most mainstream news outlets have had their business models undermined by the digital revolution. As their general-interest monopolies have been pillaged by niche online competitors, traditional news organizations have lost revenue and cachet, laying off journalists in waves that have grown into tsunamis. This process has created dire prospects for the future of investigative reporting, often seen as the most costly of journalistic forms. In the middle of November, Sam Zell, the occasionally foul-mouthed chief executive officer of Tribune Company, concisely summarized a common 21st-century media-titan view of public interest journalism in an interview by Joanne Lipman, editor in chief of Condé Nast's business magazine, Portfolio: "I haven't figured out how to cash in a Pulitzer Prize." Now, though, the digital revolution that has been undermining in-depth reportage may be ready to give something back, through a new academic and professional discipline known in some quarters as "computational journalism." James Hamilton is director of the DeWitt Wallace Center for Media and Democracy at Duke University and one of the leaders in the emergent field; just now, he's in the process of filling an endowed chair with a professor who will develop sophisticated computing tools that enhance the capabilities — and, perhaps more important in this economic climate, the efficiency — of journalists and other citizens who are trying to hold public officials and institutions accountable. In fact, Hamilton says, his interest in computational journalism grew out of his studies of media economics, which suggested that accountability journalism — the watchdog function that really can involve sorting through tens of thousands of documents, looking for the one smoking invoice — does not have the kind of everyday utility or broad interest value that will ever make it a revenue center in the disaggregated media world of the Internet. For every Watergate exposé that brings renown and readers to a Washington Post, there are dozens of other investigative reports — often equally time-consuming and expensive — that pass largely unnoticed, as the public mind focuses on the return of Britney or the current vogue in sexy vampires. (And if you don't think Britney and vampires are important, go find yourself a Dec. 11 copy of Rolling Stone, which was, once upon a distant time, the politico-cultural bible of the Watergate age.) On a disaggregated Web, it seems, people and advertisers simply will not pay anything like the whole freight for investigative reporting. But Hamilton thinks advances in computing can alter the economic equation, supplementing and, in some cases, even substituting for the slow, expensive and eccentric humans required to produce in-depth journalism as we've known it. Already, complex algorithms — programming often placed under the over-colorful umbrella of "artificial intelligence" — are used to gather content for Web sites like Google News, which serves up a wide selection of journalism online, without much intervention from actual journalists. Hamilton sees a not-too-distant future in which that process would be extended, with algorithms mining information from multiple sources and using it to write parts of articles or even entire personalized news stories. Hamilton offers a theoretical example, taking off from EveryBlock, the set of Web sites masterminded by Adrian Holovaty, one of the true pioneers of database journalism and a former innovation editor at washingtonpost.com. If you live in one of the 11 American cities EveryBlock covers, you now can enter your address, and the site gives you civic information (think building permits, police reports and so on), news reports, blog items and other Web-based information, such as consumer reviews and photos, all connected to your immediate geographic neighborhood. In the not-too-distant future, Hamilton suggests, an algorithm could take information from EveryBlock and other database inputs and actually write articles personalized to your neighborhood and your interests, giving you, for example, a story about crime in your neighborhood this week and whether it has increased or decreased in relation to a month or a year ago. I understand the potential utility of such a program, which could provide "hyperlocal" news without the cost of journalists (or, at least, with a lot fewer journalists than daily newspapers have employed). It's just not something that excites me, professionally or as a reader. But Hamilton also talks of an emerging trend that quickens the heart of even a grumpy old investigative reporter like me. Let's call it data mining in the public interest. When The New York Times reported late in 2002 that the Defense Advanced Research Projects Agency was developing a terrorist tracking system known as Total Information Awareness and led by Iran-Contra affair alumnus John Poindexter, privacy advocates were horrified . The horror: Government terror trackers planned to vacuum the huge trove of digital information now available on the Internet and other electronic systems into an enormous database and then use computer algorithms — so-called data-mining strategies — and human analysts to identify previously unnoticed patterns and associations that signaled terrorist planning. The obvious potential for political abuse (not to mention Poindexter's ethically troubled history) led Congress to cut off funding for the program and shut down the Pentagon's Information Awareness Office in September 2003. And to this day, the term data mining maintains its authoritarian/Big Brother/Dr. Strangelove connotations in many left and libertarian quarters. But the cross-referencing of information contained in multiple databases to find patterns of possible wrongdoing is not an inherently dastardly activity. It can, in fact, enhance government accountability. If you don't believe me, take a look at the Web site for the Sunlight Foundation, which has founded or funded a dizzying array of projects aimed at revealing "the interplay of money, lobbying, influence and government in Washington in ways never before possible." Because it supports so many fascinating ways of tracking the performance of politicians and government agencies, I can only hint at how inventive Sunlight's agenda actually is. But here's one entertaining hint: The foundation's Party Time site tells you where Washington's politicos are partying (and, very often, raking in campaign contributions). I clicked in a few weeks ago to see that the Build America PAC, a committee that seems to give primarily to Democratic causes and candidates, was cordially inviting people to join Congressman Gregory Meeks, D-N.Y., at the fourth annual Las Vegas weekend retreat at Bellagio early in December. For a suggested contribution of $5,000 for a co-host and $2,500 for a sponsor, a retreat-goer could get a private reception with Congressman Meeks and a "Special Guest," not to mention a discounted room rate at Bellagio. I know these particulars because Party Time includes PDFs of the invitations to political partying. Now, click over to Fortune 535, a Sunlight Foundation attempt to chart the wealth of members of Congress using the vague, flawed financial disclosure system they have set up for themselves. There are all sorts of reasons that the estimated average net worth of U.S. Sen. Orrin Hatch, R-Utah, may have nearly tripled (from $1.2 million to $3.4 million) between 1995 and 2006. All of those reasons may be perfectly legitimate. Still, it's nice to be able to track the general financial fortunes of congresspeople through the years, via Fortune 535, at a click of the mouse. It used to take a trip to Washington and hours of work (at least) to gather the financial disclosures of just one congressman. Party Time and Fortune 535 are actually some of the simpler offerings that the Sunlight Foundation funds. For a more complex glimpse of the future of government accountability, go to Sunlight-supported watchdog.net ("The Good Government Site With Teeth") and enter the name "Pelosi," just as an example. With a click of the mouse, you'll get the House speaker's campaign contribution totals, earmark activity and legislative record, as well as a listing of how her votes align with the stances of different interest groups. It's a wonderful and important cross-layering of databased information from the Federal Election Commission, Project Vote Smart, GovTrack, Taxpayers for Common Sense, MAPLight.org and other groups aiming to make government information more easily available to the public. And it is, truly, easy. Bill Allison, a senior fellow at the Sunlight Foundation and a veteran investigative reporter and editor, summarizes the nonprofit's aim as "one-click" government transparency, to be achieved by funding online technology that does some of what investigative reporters always have done: gather records and cross-check them against one another, in hopes of finding signs or patterns of problems. Allison has had a distinguished career, from his work as an investigative reporter at The Philadelphia Inquirer to his investigative duties at the Center for Public Integrity, where he co-authored The Cheating of America with legendary center founder Charles Lewis. Before he came to the Sunlight Foundation, Allison says, the notion that computer algorithms could do a significant part of what investigative reporters have always done seemed "far-fetched." But there's nothing far-fetched about the use of data-mining techniques in the pursuit of patterns. Law firms already use data "chewers" to parse the thousands of pages of information they get in the discovery phase of legal actions, Allison notes, looking for key phrases and terms and sorting the probative wheat from the chaff and, in the process, "learning" to be smarter in their further searches. Now, in the post-Google Age, Allison sees the possibility that computer algorithms can sort through the huge amounts of databased information available on the Internet, providing public interest reporters with sets of potential story leads they otherwise might never have found. The programs could only enhance, not replace, the reporter, who would still have to cultivate the human sources and provide the context and verification needed for quality journalism. But the data-mining programs could make the reporters more efficient — and, perhaps, a less appealing target for media company bean counters looking for someone to lay off. "I think that this is much more a tool to inform reporters," Allison says, "so they can do their jobs better." Investigative reporters have long used computers to sort and search databases in pursuit of their stories. Investigative Reporters and Editors and its National Institute for Computer-Assisted Reporting, for example, hold regular computer-assisted reporting training sessions around the country. And the country's major journalism schools all deal in some way with computer-enhanced journalism. The emerging academic/professional field of computational journalism, however, might be thought of as a step beyond computer-assisted reporting, an attempt to combine the fields of information technology and journalism and thereby respond to the enormous changes in information availability and quality wrought by the digital revolution. I would be remiss to write about computational journalism and not mention Irfan Essa, a professor in the School of Interactive Computing of the College of Computing at the Georgia Institute of Technology, who teaches a class in computational journalism and is often credited with coining the term. He says both journalism and information technology are concerned, as disciplines, with information quality and reliability, and he views the new field as a way to bring technologists and journalists together so they can create new computing tools that further the traditional aims of journalism. In the end, such collaboration may even wind up spawning a new participant in the public conversation. "We're talking about a new breed of people," Essa says, "who are midway between technologists and journalists." Essa was an organizer of the first "Symposium on Computation and Journalism," a conference held at Georgia Tech early last year that was sponsored by entities ranging from the National Science Foundation to Google and Yahoo to CNN and Wired. The conference included representatives from the relevant fields — traditional media (including particularly The Washington Post and The New York Times), digital media, social media, academics and the programming community — all trying to understand how the world of information has changed and what the change means for journalism. So far, the attempt to bring together technologists and journalists has been going "amazingly well," Essa says. But the field is so new that those involved are still drawing a road map for the discipline and deciding what questions it will attempt to answer through research. At Duke, Hamilton's forays into computational journalism have included programs to plumb the U.S. Environmental Protection Agency's Toxics Release Inventory database, which contains information on chemical emissions by industry and the government. He says he used statistical and mathematical methods to tease out possible inaccuracies or outright lies in companies' reports of toxic releases. For instance, his programs searched for violations of Benford's law, the mathematical rule holding (accurately but counterintuitively) that in many lists of numbers from the real world, the first digit will be "1" about 30 percent of the time and "9" less than 5 percent of the time. Another of the programs looked for toxic release reports that were the same from year to year, on the theory that it is extremely unlikely for any industrial plant to emit precisely the same amount of toxins many years running. "That's sort of the supplement (for investigative reporting), where you see the pattern," Hamilton says. "It's like a virtual tip." After he fills the endowed chair for the Knight Professor of the Practice of Journalism and Public Policy Studies, Hamilton hopes the new professor can help him grow an academic field that provides generations of new tools for the investigative journalist and public interest-minded citizen. The investigative algorithms could be based in part on a sort of reverse engineering, taking advantage of experience with previous investigative stories and corruption cases and looking for combinations of data that have, in the past, been connected to politicians or institutions that were incompetent or venal. "The whole idea is that we would be doing research and development in a scalable, open-source way," he says. "We would try to promote tools that journalists and others could use." It is dangerous to generalize about a class of people who enjoy revealing ugly truths under large headlines. I can, however, say that in my experience, investigative reporters are the type of people who think looking through 10,000 or 20,000 pieces of paper could be — if not exactly fun — challenging and even exciting. Investigative reporters also can have finely honed senses of outrage. Unlike Capt. Renault, they are not ironically shocked to discover that gambling is going on at Rick's Café Américain; they actually are shocked — shocked! — and determined to tell the world all the shocking facts, whether the world cares or not. I've also found many investigative reporters to have substantial egos hidden away beneath their outrage. They believe themselves to be engaged in heroic quests that will end in fame, fortune and acknowledgment of their selfless pursuit of the public interest. As a result, older investigative journalists can be a grouchy lot. (Just ask my wife.) So, to summarize: Investigative journalists are often strident, self-righteous, boring as a phone book, absurdly egotistical and grouchy. The good ones are also national treasures. During my lifetime alone, they have helped save American democracy from two presidents who seemed determined to destroy the checks and balances that support it. Without investigative reporters and the news organizations that pay their freight, we would not know about the National Security Agency's illegal electronic surveillance program (thank you, Eric Lichtblau, James Risen and The New York Times), the administration's plans to attack Iran (bravo, Seymour Hersh and The New Yorker), the Walter Reed Army Medical Center's shameful treatment of wounded Iraq war veterans (cheers, Dana Priest, Anne Hull and The Washington Post), and the extent of systematic mistreatment of detainees during the so-called War on Terror (salute, Washington bureau of Knight Ridder and, subsequently, the McClatchy newspapers). Just as important, without investigative reportage, an astonishing array of major local and regional problems and corruptions would go unrevealed and unaddressed every year. There is no person more important to the general civic health — and yet more consistently under-rewarded in financial and social status terms — than the quality investigative reporter at a local news organization. I like my Facebook feed and all those funny YouTube clips; I'm glad my RSS reader tells me whenever new fake news pops up on theonion.com. But The Onion won't save the Republic from the next president who thinks that whatever he does is, by definition, legal. Perhaps a new breed of investigative reporter — practiced in the seduction of Deep Throat sources and armed with algorithms that parse 20,000 documents quicker than you can say, "Follow the money" — will. At the least, a new and more efficient class of investigative reporters might still be on the payroll, the next time we need one to tell us the story we really ought to know, even if it isn't sexy enough to make the cover of the Rolling Stone. http://www.miller-mccune.com/article...ts-data-mining  When Hackers Attack: Practicing Cybersecurity at Home Brian Krebs While Barack Obama has selected key members of his national security team—Defense Secretary, National Security Adviser and Secretary of State—there are calls for the president-elect to make another security appointment. The bipartisan Commission on Cybersecurity for the 44th Presidency suggests that there is a dire need to create a National Office for Cyberspace to protect our nation’s most sensitive computer networks. The need for national cyberspace security is a no-brainer, but who is going to protect us from the digital devices that organize our lives and leaves personal information vulnerable to theft? Here, a behind-the-scenes look at how hackers are unearthing the private details of our lives by attacking our web browsers, cell phones, and personal electronics. Marisel Garcia first suspected something was amiss with her laptop when she noticed that the tiny activity light above the built-in camera flickered whenever she was in front of it. The Hialeah, Fla., resident also thought the PC’s battery was draining faster than normal. When she brought her laptop to a friend who worked in technology, he found that someone had installed software that allowed the computer to be controlled remotely. What’s worse, that person had been taking photos through her webcam. Investigators say the spyware was created and installed by Craig Matthew Feigin, a 23-year-old student at the University of Florida who had previously offered to fix a problem with Garcia’s computer. Police arrested Feigin, who now faces a federal charge for computer tampering, to which he has pleaded not guilty. In his statement to police, Feigin described how he had configured the software to take snapshots of anyone who moved in front of the webcam. He eventually amassed more than 20,000 images of Garcia, her boyfriend and other friends, and sent snapshots of their most private moments over the Internet to contacts in Eastern Europe. Considered tech-savvy around campus, Feigin was often approached by students who needed help with their computers, and Garcia was in town visiting friends when she asked for his help to make her PC run faster. He admitted to investigators that he had installed the same software on PCs belonging to more than half a dozen other women. According to court records, Garcia used her laptop the way many people do today—as a communications link that’s always online and carried from room to room for e-mailing, instant messaging and shopping. This type of open digital pipeline connecting private space and the public Internet is swiftly becoming the norm in America. According to the Pew Internet and American Life Project, more than half of the adult population in America now use broadband Internet. Plus, almost 30 percent of Americans have 3G-capable phones. These are the twin pillars of our digitally connected modern society: High-speed DSL and cable broadband connections have transformed the way people use the Internet at home, while 3G cellular networks have allowed us to take that digital connection on the road. As these powerful networks have evolved, so have the devices we use to access them. Personal computers, once self-contained processing machines, have become permanently connected devices. Most software also requires an Internet link to work properly; in fact, the latest trend in “cloud computing” moves software off the computer altogether. The evolution in cellphones has been even more dramatic. These were once analog devices designed exclusively for making phone calls; now they are data-centric mini-computers with integrated satellite-tracking capability. With each new gadget we buy and use, we make a choice to further integrate our lives into the public Internet. That decision has enormous implications for our conventional understanding of privacy and personal space. Our digital tools provide an open window to our lives, and a long list of curious characters—hacker peeping Toms, corporate marketers, jealous jilted lovers, snooping government agencies—are eager to look inside. And the digital portrait they see is more detailed than ever. According to market research firm IDC, the average person has an online digital presence of 45 GB—about half of which is created by outside sources. This digital shadow of our lives is colored in with e-mails, photo posts, password hints, Facebook friend requests and location-based queries flowing fluidly in and out of the electronic devices we bring with us everywhere. Mobile Positioning System Cellular phones are the most ubiquitous location-aware devices on the planet: Their very operation depends on knowing where the user is. Any phone can determine its own location (and thus the location of the user) by triangulating from multiple cell towers, then send that information back to the wireless service provider. This capability makes it possible to route calls efficiently to subscribers, and it can often save lives. In 1996, the Federal Communications Commission mandated that cellular providers phase in location-aware Enhanced 911 (E911) capabilities on most cellphones by 2012 to determine the position of a caller in an emergency to within 300 ft. Just last June, two hikers who wandered off course in Alaska’s Denali National Park were found a few days later when rescue workers tracked them through their cellphones. Many newer phones are shipping with embedded GPS antennas, giving them location and mapping capabilities that rival embedded navigation systems in cars. But since phones are two-way communications systems, they are open to a variety of uses beyond E911 and simple navigation. Many companies are taking advantage of these capabilities to help manage time cards, monitor gas mileage and ensure that workers aren’t slacking off. Gearworks, based in Eagan, Minn., provides location-tracking services to the transportation, infrastructure and healthcare industries. Phones outfitted by Gearworks operate like digital foremen for employees in the field. They can navigate an employee to a job site, record the amount of time it took to get there and perform the job, then allow him to remotely punch out when the job is done. According to company co-founder and chief technology officer Rob Juncker, devices using Gearworks location-tracking technology explicitly inform users that they are being tracked, and employees have the option of temporarily disabling the tracking feature for “privacy breaks.” Many emerging businesses are using the native tracking ability of modern cellphones to sell location-based information as a lifestyle service to consumers. Startup companies such as Loopt and Whrrl offer everything from real-time directions to information on local restaurants, movie showings and friends in the area. The trend toward location tracking is expected to become the future model for mobile advertising and marketing, serving up ads and special deals not only targeted at you personally, but relevant to where you are geographically. Yet legal standards of privacy for use of your location data are inconsistent at best. “The law says that information can’t be disclosed without prior opt-in from the consumer, but that law only applies to telecommunications carriers,” says Jim Dempsey, vice president for public policy at the Center for Democracy & Technology. “But many entities handling location information, or with access to it, are not telecom carriers.” A survey of the privacy policies of many location-based service providers shows how fluid the traffic in personal location data has become. Because many of these services are opt-in, once the user has agreed to the terms, his phone can be tracked even when the application is turned off. And the data collected, along with other personal information, can and will be shared with advertising and marketing partners—that is, in fact, the business strategy of these services. A personalized marketing campaign offering discounts at the burger shop around the corner may seem relatively innocuous, but as more cellphone users embrace location-aware phones, their devices automatically create a worldwide web of evidence that can easily show up in court. Albert Gidari, a partner with the Seattle offices of Perkins Coie, represents a number of wireless carriers. He has seen at least two civil suits so far in which companies have sought location data from providers. One of these cases, brought by a large insurance company, sought location data on a subscriber who was suspected of stealing and setting fire to his own car in order to recover the insurance payout. Both cases were ultimately abandoned by the plaintiffs because of costs. But Gidari suspects the reason more cases don’t involve requests for location data is that litigants simply aren’t aware it’s available. “What I think is on the horizon is that in every insurance case involving a distracted driver, someone’s going to ask, ‘Was the driver on the phone?’ and ‘Was the driver texting at the time of the crash?’” The tracking technology in cellphones is exploited not just by businesses and the courts. An established market exists for consumer spyware programs that can be installed on cellphones. Dozens of Web sites advertise GPS tracking devices and stealth software, encouraging users to “catch a cheating spouse” or “keep a watchful eye on your children.” A few hundred dollars can outfit suspicious or obsessed amateur detectives with an arsenal of spy gear. Some of these services let users log into a Web page and get daily reports of their subjects’ movements and even chart their activity using Google Earth, the search giant’s free satellite imagery software. Too often, these tools end up in the hands of stalkers and obsessed former lovers. According to Cindy Southworth, director of the Safety Net Project—a nonprofit that trains law-enforcement officers to understand the role of technology in domestic abuse—computer spyware and GPS tracking services are showing up in a huge number of stalking and domestic violence cases. “We get at least one call a week on a new case where spyware is being misused in stalking and ex-lover cases,” Southworth says. In 2006, Washington state resident Sherri Peak suspected that her estranged husband Robert was tracking her movements. An investigator confirmed her fears: Robert Peak had hidden a cellphone and a GPS tracking device in the dashboard of her car. Peak rigged the phone so he could dial in silently and listen in on his wife, while tracking her movements on his laptop computer. Peak pleaded guilty to felony stalking and was sentenced to eight months in prison. Data Trafficking The wealth of free content and services that Web surfers find so valuable is largely supported by a hidden economy. Companies give away software and services in exchange for the ability to collect and share data about where users go online, as well as what they’re searching for or buying. With advertisers under pressure to collect ever more detailed information on consumers, the stakes are enormous. According to a report commissioned last year by the Interactive Advertising Bureau, online advertising in the U.S. grossed $21.2 billion in 2007, trumping cable ($20.9 billion), radio ($19.8 billion) and broadcast television ($19.2 billion). The tool most commonly used to track user behavior is the HTTP “cookie.” Cookies are not programs, but chunks of code stored on your computer to identify you as you move from page to page on a Web site. Without cookies, most retail sites wouldn’t be able to offer virtual shopping carts or remember the preferences of their users. But the use of cookies has become far more sophisticated than mere account management. And that troubles privacy advocates. “Free Web services aren’t free,” says Gregory Conti, a computer science professor at the United States Military Academy at West Point. “We pay for them with micropayments of personal information. Users aren’t entirely oblivious to the fact that information is being collected, and they’re doing a cost–benefit analysis, but they’re not thinking long-term.” Even those who take the time to read a Web site’s privacy policy may not realize how many companies have access to their data. That’s because most Web sites pull advertisements, snippets of code and other content from a number of third-party sources, any one of which may track the visitor and use the data in a manner that differs from the host site’s data-collection policies. “When you visit msnbc.com, you’re actually visiting 16 third-party sites, 10 of which are from different companies,” Conti says, referring to the secondary content of providers and advertisers whose data make up the page. “You’re really dealing with the lowest common denominator privacy policy when many sites are involved.” Just how much data are advertisers collecting and sharing? In a study commissioned by The New York Times, Internet research firm ComScore found that on average Yahoo and its advertising-partner networks collect more than 2500 bits of data from each user per month. Every time Yahoo users enter a search query, their profiles become more detailed. Advertisers piece together digital dossiers on consumers by collecting these tiny fragments of information. But the mother lode of personal data is in the hands of the Internet service providers (ISPs), who know exactly who their subscribers are, where they live, where they go online and with whom they communicate. Because a service provider is the point of first contact between a consumer and the Internet, all data traffic going in and out of his or her household goes through the ISP’s routers. Logs of that information can be stored on an ISP’s servers for an indefinite period of time. With such a wealth of valuable information, some ISPs are starting to share this data with marketers. In May 2008, St. Louis–based Charter Communications, the third largest publicly traded cable operator in the United States, announced plans to serve customers with ads based on the content of the Web sites they visited. The company that powers this so-called “deep-packet inspection” service, NebuAd, based in Redwood City, Calif., had similar deals with more than a dozen other U.S.-based ISPs. After a public outcry, the House Energy and Commerce Committee last summer opened an inquiry into NebuAd’s controversial tactics, forcing the company to put a temporary hold on its technology for tracking ISP customers. ISPs are prohibited by law from sharing the content of their customers’ digital correspondence, but the peripheral details of your browsing, e-mailing and online shopping habits are fair game. “The only thing that would prevent an ISP from giving away or selling this data to marketers is its own privacy policies,” says Kevin Bankston, a senior staff attorney with the Electronic Frontier Foundation. “So there’s a big question right now of which ISPs are selling what data to whom, and the answer is we really don’t know.” “Free Web services aren’t free,” says Gregory Conti, computer scientist at the U.S. Military Academy. “We pay for them with micropayments of personal information.” The Privacy Cloud The one foolproof countermeasure to prevent prying marketers and hacker snoops from digging into your data has always been to yank the cord. Data can’t be siphoned off an unconnected computer. But consumers are increasingly leaving everything from e-mail to photos to documents on off-site data-storage services—a trend known as cloud computing. Tech heavyweights such as Amazon, Google, IBM, Intel, Microsoft and Yahoo market the services as everything from disaster backup and recovery solutions to Web-based software that allows consumers to access and work on their files from any digital device on the planet. The advantage of this approach is obvious: If your data isn’t located on any one machine, it can never be lost or corrupted. But when your personal data isn’t on your personal computer, it’s out of your control. Experts warn that data left in the cloud does not enjoy the level of legal and privacy protections as the same data residing on the user’s home PC. “The police can only get into your home if they have a search warrant, but the laws for police access to remote servers are much looser,” says Peter Swire, a former privacy advisor to the Clinton administration who now teaches cyberspace law at Ohio State University’s College of Law. “That means in civil or criminal litigation or a divorce case, you may not know if someone is looking at your files. You have to hope the provider objects.” Because cloud computing is still such a new phenomenon, many of its threats to personal privacy remain unexplored. Seventy percent of consumers use Web-based e-mail services such as Yahoo Mail, Gmail, Microsoft’s Hotmail or Apple’s MobileMe. The contents of and attachments to these e-mails could be processed or stored on servers around the world. All of these companies state in their terms of use that they must comply with legitimate requests for information from law enforcement, and this is by no means limited to law enforcement in the U.S. That could potentially make the correspondence of a U.S. citizen subject to foreign laws. Cloud-based social-networking sites such as Facebook and MySpace push the privacy envelope even further, encouraging users to post and share massive amounts of personal data that can be scooped up and stored indefinitely. And in an increasing number of cases, information that people willingly post about themselves online is coming back to haunt them. “The problem is that teenagers, college students and even some adults who ought to know better are not thinking through the long-term consequences of putting up so much personal information,” says Daniel Solove, author of The Future of Reputation: Gossip, Rumor, and Privacy on the Internet. “Today’s reality is that once something is out in the public, it usually stays there.” A Pennsylvania woman is currently embroiled in a lawsuit against Millersville University alleging that the school denied her a teaching degree after viewing a photo on her MySpace page titled “drunken pirate,” which shows her sipping from a plastic cup while wearing a pirate hat. Stacy Snyder was of legal drinking age when she posted the photo, but she claims university officials called the snapshot “unprofessional,” and said that it could have offended students at a local high school where she was a student teacher. The university has declined to comment on the case, pending a decision by the judge. High school seniors and recent college grads have good reason to be nervous if they’ve posted overly personal data on their social networking pages. According to a survey released in September by education prep provider Kaplan, 10 percent of admissions officers surveyed admitted viewing applicants’ MySpace and Facebook pages. Another survey conducted by CareerBuilder found 22 percent of hiring managers used social networking sites to evaluate job applicants, and more than one-third reported finding content that disqualified candidates. As more personal information is pumped into the cloud, the ability to search through it becomes more sophisticated. That makes digging up intimate details on others even easier. Millions of amateur photographers upload photos to the Web with little regard for the staying power of the medium. In September, Google launched a new version of its Picasa photo-organizing software that uses facial recognition technology to help users identify people in their pictures. Anyone can tag a photo with your name and Google will store that facial fingerprint indefinitely. Picasa’s facial recognition will then try to tag any subsequent photos of you it can find. Another Picasa feature, “geo-tagging” (adding geographical data to shots), allows you to overlay images onto Google maps. While Google has implemented privacy safeguards—users can only tag photos in their own accounts’ Web albums—some experts worry that Picasa and other cloud services need to provide consumers with additional protection. “What’s to stop a zealous prosecutor from searching the state’s digital database of driver’s license photos for people under 21 whose online Flickr photos show them engaged in underage drinking?” writes Raeanne Young, a program associate at the Center for Democracy & Technology. “What’s to stop an employer from doing the same with a photo taken by a video camera in the lobby of the building where you went for your job interview?” Legally, not much. Those photos could show up in court as well. Law enforcement can search even password-protected online accounts without your knowledge, so long as they can obtain a court order. Richard Stallman, founder and president of the Free Software Foundation, condemns cloud computing and free Web-based services as a trap for consumers. “To use these things is to close your eyes to the question of who these machines are really serving,” he says. None of these technologies ever truly feels like a trap until it’s too late—when your embarrassing photos are posted online by your angry ex, when your cellphone data becomes damning evidence against you in court, or when the ads delivered to your e-mail in box become disturbingly personal. And it may turn out that the technological trade-off is unavoidable—to be a part of our digitally connected society requires a redefinition of privacy. The only other option is to unplug completely. http://www.popularmechanics.com/tech...y/4295100.html  Could Your Social Networks Spill Your Secrets? In an article at the end of last year we looked at some of the ways data-mining techniques are being used by marketeers and security services to extract sometimes private information by assembling huge amounts of data from web visits, emails, purchases, and more. Now researchers at Google caution in a paper that by becoming entangled in ever more social networks online, people are building up their own piles of revealing data. And as more websites gain social features, even the things users strive to keep private won't necessarily stay that way, they suggest. As a hypothetical example, combining public information on, say, the business social network LinkedIn with that on another like MySpace could reveal that one of your key business contacts spends their free time in full Kiss makeup, even their two profiles are kept relatively anonymous and are not linked directly in any way. That approach is dubbed "merging social graphs" by the researchers. In fact, it has already been used to identify some users of the DVD rental site Netflix, from a supposedly anonymised dataset released by the company. The identities were revealed by combining the Netflix data with user activity on movie database site IMDb. The Google team's proposed solution is a kind of privacy warning system. When you sign up for a new online service, it would take a look on the internet and let you know if there's a risk that the new information you are uploading could be used to make connections about you. In 2007 computer scientists at Palo Alto Research Center, California, and the University of Waterloo, Ontario, built a similar warning system. It calculates whether data about to be released - for example medical records sent to insurers - could be combined with publically available information - for example wikipedia articles on health conditions - to reveal diagnoses purposefully removed from the original data. It occurs to me that such warning systems can easily be turned on their heads, and become a kind of automated data detective. How long before such programs are circulated online to help people learn the secrets of others? The Google team's paper (Under)mining privacy in social networks (pdf) will be presented at the Web 2.0 Security and Privacy 2009 meeting in May. http://www.newscientist.com/blogs/sh...ork-can-r.html  Google Hopes to Open a Trove of Little-Seen Books Motoko Rich Ben Zimmer, executive producer of a Web site and software package called the Visual Thesaurus, was seeking the earliest use of the phrase “you’re not the boss of me.” Using a newspaper database, he had found a reference from 1953. But while using Google’s book search recently, he found the phrase in a short story contained in “The Church,” a periodical published in 1883 and scanned from the Bodleian Library at Oxford. Ever since Google began scanning printed books four years ago, scholars and others with specialized interests have been able to tap a trove of information that had been locked away on the dusty shelves of libraries and in antiquarian bookstores. According to Dan Clancy, the engineering director for Google book search, every month users view at least 10 pages of more than half of the one million out-of-copyright books that Google has scanned into its servers. Google’s book search “allows you to look for things that would be very difficult to search for otherwise,” said Mr. Zimmer, whose site is visualthesaurus.com. A settlement in October with authors and publishers who had brought two copyright lawsuits against Google will make it possible for users to read a far greater collection of books, including many still under copyright protection. The agreement, pending approval by a judge this year, also paved the way for both sides to make profits from digital versions of books. Just what kind of commercial opportunity the settlement represents is unknown, but few expect it to generate significant profits for any individual author. Even Google does not necessarily expect the book program to contribute significantly to its bottom line. “We did not think necessarily we could make money,” said Sergey Brin, a Google founder and its president of technology, in a brief interview at the company’s headquarters. “We just feel this is part of our core mission. There is fantastic information in books. Often when I do a search, what is in a book is miles ahead of what I find on a Web site.” Revenue will be generated through advertising sales on pages where previews of scanned books appear, through subscriptions by libraries and others to a database of all the scanned books in Google’s collection, and through sales to consumers of digital access to copyrighted books. Google will take 37 percent of this revenue, leaving 63 percent for publishers and authors. The settlement may give new life to copyrighted out-of-print books in a digital form and allow writers to make money from titles that had been out of commercial circulation for years. Of the seven million books Google has scanned so far, about five million are in this category. Even if Google had gone to trial and won the suits, said Alexander Macgillivray, associate general counsel for products and intellectual property at the company, it would have won the right to show only previews of these books’ contents. “What people want to do is read the book,” Mr. Macgillivray said. Users are already taking advantage of out-of-print books that have been scanned and are available for free download. Mr. Clancy was monitoring search queries recently when one for “concrete fountain molds” caught his attention. The search turned up a digital version of an obscure 1910 book, and the user had spent four hours perusing 350 pages of it. For scholars and others researching topics not satisfied by a Wikipedia entry, the settlement will provide access to millions of books at the click of a mouse. “More students in small towns around America are going to have a lot more stuff at their fingertips,” said Michael A. Keller, the university librarian at Stanford. “That is really important.” When the agreement was announced in October, all sides hailed it as a landmark settlement that permitted Google to proceed with its scanning project while protecting the rights and financial interests of authors and publishers. Both sides agreed to disagree on whether the book scanning itself violated authors’ and publishers’ copyrights. In the months since, all parties to the lawsuits — as well as those, like librarians, who will be affected by it — have had the opportunity to examine the 303-page settlement document and try to digest its likely effects. Some librarians privately expressed fears that Google might charge high prices for subscriptions to the book database as it grows. Although nonprofit groups like the Open Content Alliance are building their own digital collections, no other significant private-sector competitors are in the business. In May, Microsoft ended its book scanning project, effectively leaving Google as a monopoly corporate player. David Drummond, Google’s chief legal officer, said the company wanted to push the book database to as many libraries as possible. “If the price gets too high,” he said, “we are simply not going to have libraries that can afford to purchase it.” For readers who might want to buy digital access to an individual scanned book, Mr. Clancy said, Google was likely to sell at least half of the books for $5.99 or less. Students and faculty at universities who subscribe to the database will be able to get the full contents of all the books free. For the average author, “this is not a game changer” in an economic sense, said Richard Sarnoff, chairman of the Association of American Publishers and president of the digital media investments group at Bertelsmann, the parent company of Random House, the world’s largest publisher of consumer books. “They will get paid for the use of their book, but whether they will get paid so much that they can start living large — I think that’s just a fantasy,” Mr. Sarnoff said. “I think there will be a few authors who do see significant dollars out of this, but there will be a vast number of authors who see insignificant dollars out of this.” But, he added, “a few hundred dollars for an individual author can equate to a considerable sum for a publisher with rights to 10,000 books.” So far, publishers that have permitted Google to offer searchable digital versions of their new in-print books have seen a small payoff. Macmillan, the company that owns publishing houses including Farrar, Straus & Giroux and St. Martin’s Press and represents authors including Jonathan Franzen and Janet Evanovich, offers 11,000 titles for search on Google. In 2007, Macmillan estimated that Google helped sell about 16,400 copies. Authors view the possibility of readers finding their out-of-print books as a cultural victory more than a financial one. “Our culture is not just Stephen King’s latest novel or the new Harry Potter book,” said James Gleick, a member of the board of the Authors Guild. “It is also 1,000 completely obscure books that appeal not to the one million people who bought the Harry Potter book but to 100 people at a time.” Some scholars worry that Google users are more likely to search for narrow information than to read at length. “I have to say that I think pedagogically and in terms of the advancement of scholarship, I have a concern that people will be encouraged to use books in this very fragmentary way,” said Alice Prochaska, university librarian at Yale. Others said they thought readers would continue to appreciate long texts and that Google’s book search would simply help readers find them. “There is no short way to appreciate Jane Austen, and I hope I’m right about that,” said Paul Courant, university librarian at the University of Michigan. “But a lot of reading is going to happen on screens. One of the important things about this settlement is that it brings the literature of the 20th century back into a form that the students of the 21st century will be able to find it.” Google’s book search has already entered the popular culture, in the film version of “Twilight,” based on the novel by Stephenie Meyer about a teenage girl who falls in love with a vampire. Bella, one of the main characters, uses Google to find information about a local American Indian tribe. When the search leads her to a book, what does she do? She goes to a bookstore and buys it. http://www.nytimes.com/2009/01/05/te.../05google.html  Edd Cartier, 94, Pulp Illustrator, Dies William Grimes Edd Cartier, whose noirish illustrations for the pulp magazine The Shadow and action-packed, often whimsical illustrations for stories by L. Ron Hubbard, Isaac Asimov and other writers made him one of the leading science-fiction and horror artists of his time, died on Dec. 25 at his home in Ramsey, N.J. He was 94. The death was confirmed by his son, Dean. Mr. Cartier began illustrating The Shadow while a student at Pratt Institute in Brooklyn. He went on to create more than 800 drawings for The Shadow and hundreds more for pulp magazines like Unknown and Astounding Science Fiction. “He was a legend, one of the greatest illustrators in the history of science fiction,” said Anthony Tollin, who writes the blog The Shadow’s Sanctum (shadowsanctum.com) and is reissuing pulp magazines. “It was very difficult to draw for the crude pulp paper, but he was a master at getting the most out of the format.” By dramatically placing thick swaths of black and turning blank spaces into shafts of brilliant light, Mr. Cartier evoked the murky world of the Shadow, a mysterious, lurking crime fighter in a black cloak and broad-brimmed black hat who, on the radio, entered American living rooms with the famous introduction: “Who knows what evil lurks in the hearts of men? The Shadow knows.” In his science fiction work, Mr. Cartier adopted a more precise, propellant style, with crowded panels and lots of action, often leavened with humor. “He brought humanity to science fiction, and an appreciation of foibles,” Mr. Tollin said. “What Norman Rockwell brought to his Saturday Evening Post covers, Cartier brought to science fiction and horror.” Edward Daniel Cartier was born in North Bergen, N.J., where his father ran Cartier’s Saloon and allowed his son to paint Christmas scenes on the bar’s windows. At Pratt, where he studied illustration, one of his teachers was an art director for Street & Smith, a leading publisher of pulps. Mr. Cartier began doing illustrations at $8 apiece for Wild West Weekly, Movie Action and Detective Story Magazine. He signed his work Edd Cartier, using a compressed form of his first two names. After graduating from Pratt in 1936, Mr. Cartier contributed regularly to The Shadow, beginning with “The Sledgehammer Crimes,” a novel-length story in the issue for Aug. 1, 1936. The Shadow began on radio in 1930 as a voice narrating adventures adapted from Detective Stories Magazine. Public interest in the voice led Smith & Street to create the pulp magazine The Shadow in 1931. A radio show of his own followed in 1937. “The gritty atmosphere of The Shadow’s relentless fight against crime gave me the opportunity to illustrate a weird and fantastic world,” Mr. Cartier wrote in an introduction to “City of Crime/Shadow Over Alcatraz” (2008), a reprint of two Shadow stories by Sanctum Books. It was a world, he wrote, of “dark hallways, one-room flats, spooky mansions, dingy subways, dead-end alleys and fog-shrouded wharves.” His work caught the eye of Norman Rockwell, who offered him a job as an assistant. Mr. Cartier turned it down, a move he later said he regretted. Besides the stories involving the title character of The Shadow, he illustrated backup pieces that filled out the magazine. These included the adventures of Hook McGuire, bowling detective, and Danny Garrett, a shoeshine boy who does detective work on the side. He also drew for Smith & Street’s other mystery titles, including The Whisperer, The Wizard and Detective Story. In 1939 John W. Campbell Jr., the editor of Street & Smith’s Astounding Science Fiction, asked him to illustrate a new, groundbreaking science fiction and fantasy magazine, Unknown. “That’s where he really shined,” said Robert Weinberg, the author of The Biographical Dictionary of Science Fiction and Fantasy Artists. “He had a deft caricature style, and he was able to draw not just very expressive people but expressive creatures like fairies, gnomes and gods.” Mr. Cartier’s work was also prominent in Astounding Science Fiction, for which he illustrated stories by writers like Hubbard, Asimov, Theodore Sturgeon and Robert A. Heinlein. In 1941 Mr. Cartier enlisted in the Army and, after drawing maps in Britain, fought in France and Germany in World War II as a machine gunner with a tank battalion. He was severely wounded at Bastogne, Belgium, during the Battle of the Bulge, and wounded again when his hospital train was blown up. He was awarded a Purple Heart and a Bronze Star. After the war, Mr. Cartier resumed work on The Shadow, Astounding Science Fiction and Doc Savage, but the pulp market went into decline as its audience was stolen by comic books and television. The Shadow, for example, ceased publication in 1948. Mr. Cartier found work as a draftsman for an engineering company and, in the late 1950s, as the art director for Mosstype, a company that printed corporate logos, packaging, wrapping papers and lottery tickets. In addition to his son Dean, of Ramsey, he is survived by another son, Kenn, of Redmond, Wash.; and two grandchildren. His wife, Georgina, whom he married in 1943, died in 2007. “He really excelled at monsters,” Mr. Weinberg said. “There was one, a puddle of slime that could assume different forms, and he showed it as an icky, drippy humanoid rising from the ooze. It was fantastic.” http://www.nytimes.com/2009/01/08/arts/08cartier.html  Hollywood’s Superheroes Save the Day Brooks Barnes As companies big and small — if they still exist at all — trudge into January after a dismal 2008, the movie business is quietly celebrating solid if not spectacular results at the multiplex. Ticket sales at North American movie theaters totaled $9.6 billion, a decrease of less than 1 percent over the previous year, according to Media by Numbers, a box office tracking company. Although attendance declined 5 percent, to about 1.3 billion, the industry was able to buttress revenue with higher ticket prices and premium 3-D offerings. “Considering the economic climate, I think that’s a pretty terrific result,” said Michael L. Campbell, the chief executive of the Regal Entertainment Group, which owns the nation’s largest chain of movie theaters. “This industry is as recession-resistant as any I can think of,” he added. The results were largely attributable to superheroes, either reinvented ones like “The Dark Knight” (the top moneymaker) or newcomers like “Iron Man” (the runner-up). Four computer-animated movies delivered giant returns, with “Wall-E,” “Kung Fu Panda,” “Madagascar: Escape 2 Africa” and “Horton Hears a Who” all in the top 10. A new franchise about a well-behaved teenage vampire was born to tiny Summit Entertainment in “Twilight.” And never underestimate a well-executed marketing campaign and a dollop of nostalgia: “Indiana Jones and the Kingdom of the Crystal Skull” overcame dreary reviews to sell $317 million in tickets and place third in the top 10, according to Box Office Mojo, an online tracking site. Beneath the numbers, however, are some gnawing concerns. Executives must confront drooping DVD sales — where most profits are made — and a messy, unresolved labor dispute with the powerful Screen Actors Guild. Parent companies like General Electric, Sony and the Walt Disney Company are demanding leaner studio operations and some are looking to sell noncore units like specialty film divisions as they wrestle with television, publishing and consumer product troubles. But studio chiefs want to forget all of that for now. “We’re more than holding our own as a business,” said Marc Shmuger, the chairman of Universal Pictures. The studio, part of NBC Universal, which is owned by G.E., recorded its biggest box office year ever in 2008, with global grosses totaling $2.83 billion. It is foolhardy to read too much into what worked and what did not at the box office in any given year. Successes and failures usually involve the mechanics of individual titles and do not signal any clear trends. And in Hollywood, the wind changes perhaps faster than anywhere else. In 2008, the musical “Mamma Mia” became a smash for Universal, selling $572 million in tickets around the world, and “Sex and the City” was a surprise hit for Warner Brothers, selling $415 million in tickets. It might have seemed that movies attracting women were back, but then came Warner’s remake of “The Women” with $46 million, Box Office Mojo figures show. Still, movie executives say a few clear signals can be gleaned from the last 12 months. People love watching a dog on the big screen, including dancing ones. “Beverly Hills Chihuahua” sold $93 million in tickets for Walt Disney Studios in the United States, while the company’s animated “Bolt” overcame a soft opening to sell nearly $110 million through Sunday, according to Box Office Mojo estimates. Fox’s “Marley & Me,” about a naughty yellow lab, has generated estimated sales of $106 million as of Sunday, Box Office Mojo said, and is still going strong. The ability of stars to open a movie may be fading in North America, but it remains powerful overseas. “Body of Lies,” a Warner release starring Leonardo DiCaprio and Russell Crowe, did not do well in the United States, selling just $39 million in tickets. But it went on to do respectable business overseas, with its global total now over $100 million. The definition of what counts as a success in the modern movie business might have changed. “The Chronicles of Narnia: Prince Caspian” sold $420 million in tickets around the world for Disney and Walden Media. But because that was almost half of what the first “Narnia” film had generated, and because Disney had to share the profits and lacked a big consumer products offshoot, the company dumped the franchise. Finally, it appears that premium pricing — a longtime challenge for the business — is here to stay. In 2008, the studios discovered that audiences would pay ticket prices of up to $25 to see a movie in 3-D (“Hannah Montana/Miley Cyrus: Best of Both Worlds Concert Tour”). Screenings of “The Dark Knight” and “Kung Fu Panda” at Imax theaters, also carrying premium prices, did blockbuster business. “We had our best year ever by some measures, which suggests to me that people are rewarding themselves with little pleasures,” said Richard L. Gelfond, the chief executive for Imax. The results for last year varied studio by studio, and sometimes within the same studio. Warner, for instance, was easily the industry leader, with an 18 percent market share, according to Box Office Mojo. “The Dark Knight,” now the No. 2 most popular film in modern movie history without adjusting for inflation, behind “Titanic,” was largely the reason. But the studio also released the biggest flop of 2008, the disastrous “Speed Racer.” The road ahead for Warner could be difficult. The studio is the largest seller of DVDs, and it is locked in a legal battle with Fox — so far, Warner is losing — over “Watchmen,” a potential blockbuster based on the graphic novel. While the studio considers its next entry in the superhero genre (it could be a movie based on the Green Lantern comic book character), it has at least one surefire hit on the way, “Harry Potter and the Half-Blood Prince.” Paramount, more than any studio, exhibited marketing prowess in 2008, analysts said, helping to turn movies made by other production companies like Marvel (“Iron Man”) and DreamWorks (“Tropic Thunder”) into hits. With “The Curious Case of Benjamin Button,” Paramount would like to quiet industry sniping about its thin track record with homegrown hits. In many ways, the 2009 spotlight will be on Paramount, analysts say, as the studio tries to resuscitate a franchise (“Star Trek,” due in May) and introduce another (“G.I. Joe,” set for August). The studio, in partnership with DreamWorks, is also preparing a sequel for June release that is sure to get heavy scrutiny: “Transformers: Revenge of the Fallen.” Sony had success by sticking to its knitting. A Will Smith blockbuster in summer (“Hancock”), a blockbuster James Bond entry in the fall (“Quantum of Solace”) and a smattering of sophomoric comedies (“Step Brothers,” “You Don’t Mess With the Zohan” and “Pineapple Express”) delivered another solid year. Coming up: a strike-delayed “Angels & Demons,” based on the book by the author of “The Da Vinci Code.” On the surface, Disney’s year was just fine. “High School Musical 3: Senior Year” sold $237 million in tickets around the world (against an $11 million production budget), according to Box Office Mojo, and “Wall-E” outperformed its immediate Pixar predecessor, “Ratatouille.” A few big hits, however, are not enough any more for this studio. Because Disney decided a couple of years ago to drastically reduce the number of pictures it released each year, every release must deliver huge profits. As “Prince Caspian” demonstrated, big ticket sales do not translate to a fatter bottom line. One crucial test ahead for Disney involves Ms. Cyrus. “Hannah Montana: The Movie,” set for April release, will give investors a read on how much potential remains in the important franchise. Fox started the year with a blockbuster DVD (“Alvin and the Chipmunks”) and solid returns for “Horton” and the inexpensive comedies “27 Dresses” and “What Happens in Vegas.” But the studio stumbled badly over the summer, failing to release a single blockbuster movie and recorded a $111 million decline in operating income for the third quarter over the previous year. For Fox, the pain of the much-maligned “Australia” was eased by the Australian government, which covered 40 percent of the production costs, and Fox has several films in its pipeline that could soon make 2008 a distant memory. Among them are “X-Men Origins: Wolverine” and sequels to “Ice Age” and “Night at the Museum.” http://www.nytimes.com/2009/01/05/bu...boxoffice.html  What if Sundance Isn't About the Sales Anymore? Steven Zeitchik One of the most promising indie films this winter features several stars and already has buyers circling. It sounds like a top Sundance Film Festival hopeful, except for one thing -- it isn't going to Sundance. "My One and Only," a period romantic dramedy starring Renee Zellweger and Kevin Bacon, has been screening for buyers the past few weeks in the hope of sealing a deal before the first parkas are zipped up in Utah on January 15. The film, about a 1950s single mother in search of a wealthy suitor, is classic Sundance bait, but filmmakers and reps decided against taking the mid-range-budgeted film to Park City. Instead, they believe a more deliberate rollout to buyers will serve the film's interests better than a high-profile fest screening. While they might be sacrificing the chance for a bidding war, they also avoid the possibility that the movie's value will plummet if that first screening doesn't start a fire -- in other words, if it plays like most festival movies have this past year. "You take a movie to Sundance, there's an expectation," says a sales agent at another firm. "You're running uphill. Show a movie in L.A. and you're running downhill." There are, to be sure, movies with the requisite big names and big promise coming to Park City this year. A Jim Carrey comedy drama ("I Love You Phillip Morris") and an Antoine Fuqua cop thriller ("Brooklyn's Finest") could easily have been studio movies, but because of plot particulars (gay themes and grittiness, respectively) became Sundance acquisition targets. Ashton Kutcher's off-kilter raunch comedy "Spread" and Kevin Spacey's drama "Shrink" also have strong prefestival hype. If things break right, movies like these could provoke pricey bids from studios looking to avoid the creative risks -- and production costs -- of making the films themselves. But if these titles don't ignite bidding wars -- which, given the recent state of the indie marketplace, wouldn't be surprising -- the disappointment could accelerate a shift toward the "One and Only" model. "We're starting to screen stuff more and more outside of festivals," said attorney John Sloss, who brokers deals through his Cinetic Media firm. This in part, he says, because "I'm more unsure about the market than I've ever been." Sloss this year opted to take James Ivory's new film to execs directly instead of taking it to Park City. Sony Pictures Classics began negotiating to acquire "Rudo y Cursi," a Spanish-language film directed by Carlos Cuaron and starring Diego Luna and Gael Garcia Bernal, more than a week before its planned Sundance premiere. The new attitudes are enough to cause sellers and distributors to start asking what was an unthinkable question even a few years ago: What if Sundance isn't about the sales anymore? "There's nothing that says that Sundance has to be the Andover or Exeter for the specialty film business's Harvards and Yales," says longtime producer and sales rep Jonathan Dana. Recent history suggests that the Ivy League of distributors is indeed looking elsewhere. There wasn't a Sundance box office hit to be found last year, and the two major sales -- "Hamlet 2," which went to Focus Features, and "Choke," which Fox Searchlight bought -- both underperformed. In fact, there hasn't been a robust festival market by conventional definitions since Cannes in 2007 (though Toronto pickups like "The Visitor" last year and "The Wrestler" this year have provided glimmers of hope). In the meantime, many specialty divisions have either closed or cut back. Add it all up, and many are drastically downsizing their expectations before they arrive in Park City. "There may be three or four big sales -- or there may barely be one," says one acquisitions exec. "Neither would surprise me." The reason to expect a chillier sales climate has as much to do with production trends as it does the market itself. The indie world is already beginning to see filmmaking contract as financiers cut back amid the economic and credit crises. The prospect of lower sales returns at festival markets might shrink ambitions even further. "If there are people paying $200,000 for the rights to a movie, then some of those movies can no longer be made, or they have to be made for $200,000," says Sundance veteran Mark Urman, president of distribution at Senator. "Which means a lot of Sundance staples may no longer get made." Those that do could soon have a tougher time not just finding a sale, but finding a sales agent. One sales rep says he turned down a dark film even though the director has a stellar reputation. "In earlier years, I would have been all over it like a cheap suit," the agent says. "Now I'm hoping it goes to another rep. It was not an easy sell whatsoever in good times. It certainly won't be now." The rhythms of the calendar and fest organizers' sharp eye for quality assures that there will always be sales at Sundance. But it might be that the business is entering a phase in which debuts are measured not in terms of their dollar value, but in the value of their discovery. Two of the most prominent movies to emerge from the festival last year were "Frozen River" and "Roman Polanski: Wanted and Desired." The former announced the arrival of talent like director Courtney Hunt and star Melissa Leo; the latter has had an enduring cultural life, bolstering the reputation of director Marina Zenovich and having an impact on Polanski's long-running court case. Sony Pictures Classics and the team of HBO/ThinkFilm, which acquired the respective pictures for modest price tags, will both earn decent ancillary revenue from their purchases, if not overwhelming box office. But what these breakouts show is that the fest's main value might now lie in the classic indie model, in which little money is spent and little is earned. The payoff comes in the form of critical cachet and awards, not in a "Little Miss Sunshine"-style plug-and-play blockbuster. It's a switch that takes the fest back to its emergence two decades ago, when movies like "sex, lies & videotape" were championed not as possible crossover hits but as giving rise to directorial talent and even a new style of filmmaking. Such a shift would dovetail, in a sense, with the festival's own ambitions. While organizers haven't voiced outright opposition to the sales market as they have with swag and ambush marketing, they have had an ambivalent relationship with it: Organizers like the heat and industry attendance it brings but privately worry that it puts the emphasis on the big sale instead of the great film. If Sundance were to return to its roots, documentaries could be the canary in this coal mine. Gone is the market of even two years ago, when compelling nonfiction stories like "My Kid Could Paint That" or "In the Shadow of the Moon" drew bidders who readily paid $1.5 million or $2 million for the right to release them. (Last year's lone big documentary sale, the $700,000-priced "American Teen," sank at the box office for Paramount Vantage, which could further cool this year's market.) Still, Sundance offers plenty of movies that could get small distributors and cinephiles excited, from Tom DiCillo's documentary on the Doors ("When You're Strange") to the Fisher Stevens-produced environmental mystery "The Cove." They probably won't sell for a lot, but they might be the titles that this year's fest is remembered for. Changes are afoot all over Park City. Just ask Jeffrey Best, who for years operated swag suites at the centrally located Town Lift but who this year will run a toned-down site in official conjunction with the festival there instead. "It's necessary to change the model to stand out in a cluttered environment," says Best, a man who once helped cultivate the corporate and celebrity sides of Sundance. This year, Best is offering less flash and more substance. Outside the Lift, expect the same. http://www.reuters.com/article/enter...5061NK20090108  All a-Twitter About Stars Who Tweet Noam Cohen THE golfing star Natalie Gulbis recently joined the microblogging site Twitter, where she gives the public frequent updates of her life in short text messages, or tweets. First, though, there had to be a meeting between her media consultant, Kathleen Hessert, and other advisers. “I had to talk her management team into it,” recalls Ms. Hessert, whose company, Sports Media Challenge, represents athletes and professional teams. Deciding to join a service devoted to spontaneous, often spectacularly mundane updates throughout the day apparently was something to be thought out carefully. Ms. Gulbis and her team were concerned about who would be reading what she writes on Twitter and what they would do with the information. “There is a risk,” Ms. Hessert conceded. “Whenever you open yourself to the public there is risk. The way I convinced her to do it, is to say that people see you one way and there is so much more.” Ms. Gulbis agreed to use Twitter, but she said she wasn’t simply following Ms. Hessert’s lead. “When I decided to do Twitter, I had a plan — there is information I wanted to get out,” she said in a telephone interview last week from a yacht in the Caribbean. And she established clear parameters. “I don’t think I would ever Twitter about my personal life, who I was dating, who I was going out with. That is something I would be very protective of,” she said. Instead, Ms. Gulbis’s tweets thus far tend to be circumscribed and have a clear point to make, whether it relates to her work on behalf of the Boys and Girls Clubs, or a sponsor, TaylorMade, or even the broad outlines of her oceangoing vacation. By comparison, the attitude of another of Ms. Hessert’s clients, the basketball star Shaquille O’Neal, couldn’t be more different. There seemingly is no plan to his frequent, all-over-the-place musings. Some are intensely personal, including news that a dear great-grandmother died; some reflect false bravado (“Schwwww, tim duncan was lucky i was tired”); some are whimsical (“Shaq a Claus makes an appearance”); and some could be mistaken for fortune-cookie wisdom (“Laugh as much as u breathe, its a true stress reliever, trust me.”). But through it all there is a marriage between a man frequently on the road and his medium, the cellphone — and a wit that plays with the peculiar art form known as text-messaging. An example: “Its co sold in porltand icatn even tpye straight.” • As celebrities take advantage of the Internet’s ability to break down the barrier between stardom and the public, they are being forced to pick a spot on the Gulbis-O’Neal scale of openness. Yet, even this scale demands an asterisk. No one with a brand that represents tens of millions of dollars a year cavalierly decides to share details of his life and communicate with the public unfiltered, not even Shaquille O’Neal. For example, Mr. O’Neal’s decision to use Twitter also came after a meeting of his management team, Ms. Hessert said. Someone on Twitter had been doing a sharp Shaquille O’Neal impression (he used Mr. O’Neal’s name, since Twitter doesn’t require proof to take a user name) and it came to Ms. Hessert’s attention. A meeting was called. “Somebody associated with Shaq said, ‘Let me call our lawyers,’ ” Ms. Hessert said. “I said don’t do that. I happened to be going to Phoenix that day and met with Shaq. I had been telling him he had to get on Twitter and he hadn’t done it.” • She said Mr. O’Neal agreed that the best way to drive out a fake Shaquille O’Neal was to become The Real Shaq (his handle on Twitter). He is a technology fan, she said, and quickly taught himself how to Twitter and more recently to post photos on TwitPic, a service that uses the Twitter technology. She said Mr. O’Neal was motivated by wanting to reach out to his fans: “He told me, ‘I just want to have fun and make people who hurt feel better.’ ” “It is a perfect match between someone who is larger than life and has a great personality that people are drawn to,” Ms. Hessert said. “When that happens, their brand becomes bigger — brand investment from the word go. There are people in China who have contacted me who want to spread Shaq’s tweets world round.” Ms. Gulbis is upfront about promoting her appearances, both professional and commercial. She said that golf, particularly women’s golf, sorely lacks media coverage and that her fans genuinely need to be informed about when the women’s golf tour is coming to town. “Twitter is a way to get accurate information to the fans, and get feedback,” she said, adding that she is going to design an Adidas golf shoe next year and plans to use Twitter to ask fans about what sort of colors and designs. For Mr. O’Neal, the transition to outright promotion is more complicated, Ms. Hessert said. “It’s a delicate issue — you don’t want the authenticity to be smeared by the commercialism,” she said. “People who know that you really care, this is really you, will accept a certain degree of commercialism down the line.” And perhaps Ms. Hessert’s commercial hand can be seen in the recent Twittering between Mr. O’Neal and Ms. Gulbis. Apparently from reading tweets from the Caribbean yacht, he Twittered: “natalie_gulbis, can i come plsplspls iwanna come 2 da party.” However, Ms. Hessert said she was not optimistic that another of her clients, the perfectionist quarterback Peyton Manning who had just won his third N.F.L. Most Valuable Player award, would take up Twitter. “It’s not the right fit for Peyton, he’s not that spontaneous,” she said. “If Peyton did it he would plan it all out and make sure he did the best — he wouldn’t have any typos.” http://www.nytimes.com/2009/01/05/te...et/05link.html  Twitter Reveals Mundane Lifestyles of Celebrities Stars using Twitter to post minute-to-minute updates for fans have given an inadvertent insight into their surprisingly mundane lives. Sarah Knapton The micro-blogging website offers users the chance to post regular short updates from their computers or mobile phones. But the resulting streams of consciousness from people like Will Carling, Jonathan Ross and John Cleese have proved less than inspiring. To welcome in the New Year Carling twittered that he was 'just about to make a cup of tea.' The following day he rambled: "Listening to Coldplay whilst helping to get lunch ready for some mates who are around. Amazing no hangover from the Earl Grey last night." On December 30 Cleese made the astounding admission he was a fan of Marmite but then declared a preference for mustard. During a holiday in Florida, Ross told the online community: "Cold weather can be nice to go out in providing you have warm clothes on." Users are given their own page on Twitter where updates appear and other users can sign up to receive their updates. A total of 3,109 people are currently following Ross' messages. Britney Spears is also a prolific twitterer and currently has 13,610 followers. During a recent trip to Japan she commented: "I love Japan! I think all the tiny cars are so cute!" One Labour politician, Bristol East MP Kerry McCarthy even posted a message from inside the House of Commons. On December 21 she wrote: "In Chamber thinking I'm not going to get called and won't have long enough to say anything meaningful even if I am." The social networking site was founded by Jack Dorsey, Biz Stone and Evan Willimas in July 2006 and began life as an internal research and development project for podcasting company Odeo, But aside from micro-blogging stars the service also has a serious side. On December 30 Israel became the first government to hold a worldwide press conference to take questions from members of the public about violence in Gaza. The Los Angeles Fire Department put the technology to use during the October 2007 California wildfires to keep members of public up to date. NASA used Twitter to break the news of the discovery of what appeared to be water ice on Mars by the Phoenix Mars Lander. And 10 Downing Street now has its own micro-blog detailing the movements of Gordon Brown as well as keeping the country updated on the situation in Iraq. "A golden sun sets behind the Union Jack at Basra airbase," was the picturesque entry on December 17. http://www.telegraph.co.uk/sciencean...lebrities.html  Twitter Gets Hacked, Badly Michael Arrington Phishing attacks, which hit Twitter over the weekend, are a sign a service has arrived (Facebook has the same problem). But someone hacking into Twitter’s internal admin tools and compromising 33 high profile accounts, including President Elect Barack Obama, has Twitter users freaking out about what to do. Here is Twitter’s official explanation: Quote:
http://www.techcrunch.com/2009/01/05...-hacked-badly/  Weak Password Brings 'Happiness' to Twitter Hacker Kim Zetter An 18-year-old hacker with a history of celebrity pranks has admitted to Monday's hijacking of multiple high-profile Twitter accounts, including President-Elect Barack Obama's, and the official feed for Fox News. The hacker, who goes by the handle GMZ, told Threat Level on Tuesday he gained entry to Twitter's administrative control panel by pointing an automated password-guesser at a popular user's account. The user turned out to be a member of Twitter's support staff, who'd chosen the weak password "happiness." Cracking the site was easy, because Twitter allowed an unlimited number of rapid-fire log-in attempts. "I feel it's another case of administrators not putting forth effort toward one of the most obvious and overused security flaws," he wrote in an IM interview. "I'm sure they find it difficult to admit it." The hacker identified himself only as an 18-year-old student on the East Coast. He agreed to an interview with Threat Level on Tuesday after other hackers implicated him in the attack. The intrusion began unfolding Sunday night, when GMZ randomly targeted the Twitter account belonging to a woman identified as "Crystal." He found Crystal only because her name had popped up repeatedly as a follower on a number of Twitter feeds. "I thought she was just a really popular member," he said. Using a tool he authored himself, he launched a dictionary attack against the account, automatically trying English words. He let the program run overnight, and when he checked the results Monday morning at around 11:00 a.m. Eastern Time, he found he was in Crystal's account. That's when he realized that Crystal was a Twitter staffer, and he now had the ability to access any other Twitter account by simply resetting an account holder's password through the administrative panel. He also realized he hadn't used a proxy to hide his IP address, potentially making him traceable. He said he hadn't used a proxy because he didn't think the intrusion was important enough to draw law-enforcement attention, and "didn't think it would make headlines." He said he decided not to use other hacked accounts personally. Instead he posted a message to Digital Gangster, a forum for hackers and former hackers, offering access to any Twitter account by request. "I ... threw the hack away by providing DG free accounts," he said. He also posted a video he made of his hack to prove he had administrative access to Twitter. President-Elect Barack Obama was among the most popular requests from Digital Gangster denizens, with around 20 members asking for access to the election campaign account. After resetting the password for the account, he gave the credentials to five people. He also filled requests for access to Britney Spears' account, as well as the official feeds for Facebook, CBS News, Fox News and the accounts of CNN correspondent Rick Sanchez and Digg founder Kevin Rose. Other targets included additional news outlets and other celebrities. Fox won the hacker popularity contest, beating out even Obama and Spears. According to Twitter, 33 high-profile accounts were compromised in all. GMZ doesn't know what the reset passwords were, because Twitter resets them randomly with a 12-character string of numbers and letters. On Monday morning, the Twitter accounts belonging to Obama, Britney Spears, FoxNews and others, began sending out bogus messages. Someone used the Obama account to send out a message urging supporters to click on a link to take a survey about the president-elect, and be eligible to win $500 in gasoline. A fake message sent to followers of the Fox News Twitter feed announced that Fox host Bill O'Reilly "is gay," while a message from Britney Spears' feed made lewd comments about the singer. It was initially believed that the Twitter account hijackings were related to two phishing scams that surfaced over the weekend. But GMZ's hack was unrelated. Shortly after GMZ posted his original message to Digital Gangster, the site's administrator deleted it, along with the responses from members asking for access to other accounts. But a subsequent thread on the site supports GMZ's account of the hack. GMZ said he didn't access any of the high-profile accounts himself, and didn't send out any of the bogus tweets. He thinks he was in Twitter a couple of hours before the company became aware of his access and locked him out. Twitter co-founder Biz Stone confirmed for Threat Level that the intruder had used a dictionary attack to gain access to the administrative account, but wouldn't confirm the name of the employee who was hacked, or the password. He also wouldn't comment on how long the intruder was in the Twitter account resetting passwords before he was discovered. "Regarding your other questions, I'd feel more comfortable addressing them once we've spoken to counsel because this is still ongoing," he wrote Threat Level in an e-mail. Stone said that Twitter has already been contacted by the Barack Obama campaign about the hack and has been in touch with everyone whose account was accessed by the intruders. He said Twitter had not had contact with the FBI or any other law enforcement agency. "We're waiting to hear back from our lawyer about what our responsibilities are about this and how to approach it," Stone said in a separate phone interview. As for addressing the security issues that allowed the breach, he wrote in a follow-up e-mail that the company is doing "a full security review on all access points to Twitter. More immediately, we're strengthening the security surrounding sign-in. We're also further restricting access to the support tools for added security." GMZ, who said he's been hacking for about three years and is currently studying game development, said he conducted the dictionary attack using a script he wrote and used last November to break into the YouTube account of teen queen Miley Cyrus. That hack gained widespread attention when someone posted a video memorial to Cyrus on the account, claiming Cyrus had died in a car accident. GMZ said a friend of his was responsible for the hoax. GMZ said he's used the same dictionary attack to breach the SayNow accounts of Disney star Selena Gomez and other celebrities. After YouTube blocked his IP and patched some vulnerabilities he was exploiting, he decided "for the fun of it (curiosity and self-entertainment) I'll pen-test Twitter." He was "shocked to realize that there was no rate limit" to lock someone out after a specific number of failed password attempts. He said he'd never even heard of Twitter until he saw someone mention it on YouTube. http://blog.wired.com/27bstroke6/200...sed-twitt.html  Model Sues Google Over Mean, Nasty Blog Remarks Caroline McCarthy You just can't make this stuff up. Liskula Cohen, a Canadian model, has sued Google because of offensive remarks made about her on a blog hosted by its Blogger publishing service, according to the New York Daily News. The 36-year-old Cohen, who appeared on the covers of W and Australian Vogue magazines in the early '90s, wants to know the identity of an anonymous blogger who called her "our #1 skanky superstar," among other lovely epithets. The blog is called Skanks in NYC, and it is devoted more or less to ridiculing photographs of Cohen, all of which were posted on a single day: August 21, 2008. But Cohen has taken enough offense to pursue legal action against Google in a Manhattan court, demanding that the Internet giant expose the "Skanks" blogger's details. "I'm tall, I'm blond, I've been modeling for many years, and people get jealous," she told the Daily News. "If I had to deal with everyone who is jealous, I wouldn't have time to do anything else." Her lawyer called the site "libelous" and "defamatory." Meanwhile, the search terms "Liskula Cohen" and "Skanks in NYC" skyrocketed to the top of (ironically) Google Trends, earning "on fire" ratings. Hey, considering that I'd never heard of Liskula Cohen before, and I'm sure that I'm not the only one, this might've been the best thing that ever happened to her. But is her claim against Google viable? Um, probably not. http://news.cnet.com/8301-13577_3-10133085-36.html  Jenny McCarthy - Worst of 2008 Steven Novella Here’s a few safety tips: don’t give a loaded gun to child or homicidal maniac; don’t give a box of deluxe gourmet chocolates to a brittle diabetic; don’t give a lit blow torch to a pyromaniac… And don’t give dangerous anti-vaccination crank Jenny McCarthy 50 million dollars. But, that is exactly what Jim Carrey has just done - provided a 50 million dollar trust for his girlfriend Jenny McCarthy. For those who have already listened to the SGU 2008 year end wrap-up episode, you know that McCarthy earned my vote as the worst skeptical “douchebag” of 2008 for her anti-vaccination efforts. McCarthy decided that her son Evan’s autism was caused by vaccines - because she had heard the rumors and her “mommy instinct” told her it was right. She then confirmed her beliefs by attending Google University’s confirmation bias program. McCarthy is too arrogantly ignorant to appreciate the depths of her own ignorance. She feels that her mommy instincts and her dabblings on the internet were enough to trump the consensus of expert opinion built on numerous high quality studies that shows that there is no link between vaccines and autism. Well, no problem. Her instincts can’t be wrong, so all those doctors, scientists, and public health servants must be corrupt and evil. So confident that she was right and the scientific community was wrong, stupid, and evil, she decided to go on a campaign to tell the world that the sky was falling. She wrote a couple of books, took the reigns of the anti-vaccine movement, organzied a green-our-vaccines rally, and went on as many talk shows as she could to spread her hard-won wisdom. She does have a lot of energy, I have to give her that. Of course, the combination of dangerous stupidity, overconfidence, zeal, and millions of dollars is a pernicious one. I predict we are no where close to seeing the end of Jenny McCarthy’s mischief. Let’s also look back and see what else McCarthy’ instincts told her. Mddawson on the message boards provided this gem of a link: Quote:
But her best work is on the Indigo child thing. She has tried to scrub her indigo past from the web, but that is a fool’s errand. Too much is archived. Here’s a taste: Quote:
Promoting The Secret and Indigo nonsense is pathetic and carries all the negatives that promoting gullible nonsense to the public has - but at least they are not directly physically harmful. As an Indigo McCarthy was just another celebrity whacko, another Tom Cruise. But now she has decided that her mommy instinct is sufficient for her to decide public health policy. After the MMR scare in the UK sparked by the now-discredited research of Andrew Wakefield, vaccinations rates dipped and as a result there was a resurgence of measles. Now in the US McCarthy is trying hard to replicate that effect. There are now pockets of low vaccination rates in communities where McCarthy’s scare tactics have had an effect. As a result there has been a resurgence of measles outbreaks. Jenny McCarthy is a dangerous deluded crank who does not have the sliver of common sense or humility it would take to consider the possibility that perhaps she does not understand the science as well as trained scientists. At the very least she should recognize that this is a controversy - one that should be decided by the scientific evidence. I am willing to let the scientific chips fall where they may. Right now they show no link between vaccines and autism. If new evidence changes the balance of the evidence, my opinion will change with it. But McCarthy does not want the evidence to decide the outcome of the controversy - she is so certain of her mommy instinct that she wants to use her celebrity and money to put her thumb on the scale. She is therefore like any ideologue who wishes to distort science for their own ends - similar to using the power of government or religious faith to dictate science, rather than having objective science inform our policy. In 2009 the fight will have to continue. In the review episode I gave props to Amanda Peet and Paul Offit for doing their part in opposing the anti-vaccinationists. I also give credit to the entire skeptical community - this is a battle we are well equipped to fight. http://www.theskepticsguide.org/sgublog/?p=408  West Coast Fashionista Takes on Manhattan, Manolos in Tow Ginia Bellafante  It is has been hard to watch “The Hills” without developing at least a tepid affection for the person-character of Whitney Port. Her fixed expression of feigned surprise suggests she is willing to risk everything — even wrinkles by the time she is 26 — all for the art of pseudo-improvised reality television. “The Hills,” which recently concluded its fourth season, is MTV’s ethnography of young people with enviable dentistry living in Hollywood and aspiring to careers that sociologists 50 years ago would have ascribed to the world of science fiction. Whitney had been courtier to Lauren Conrad’s queen of the canyons until she decided to leave Los Angeles and a job at a company called People’s Revolution, where she wore headsets and helped produce fashion shows. She was moving to New York to take up an offer to work as a publicity assistant at Diane von Furstenberg, a job Whitney describes early on in “The City,” a new series about her acclimatizing to Manhattan, as “an opportunity of a lifetime.” (“The City” is broadcast Mondays on MTV following “Bromance,” a comparatively conventional but completely unwatchable reality show also spun from “The Hills.”) On “The Hills” Whitney’s private life was largely conducted off camera, allowing her to pass as the show’s pre-eminent careerist. It wasn’t all that long into her internship at Teen Vogue that she knew she wanted more out of life: she wanted to become a stylist. During her interview at People’s Revolution she didn’t cower when her new boss explained that she would essentially be giving up every waking moment of her life: “Like you’re basically making a deal with the devil,” her boss warns her. Whitney’s work ethic was rivaled only briefly by Heidi Montag’s, during a period when Heidi was refusing to submit to her boyfriend’s oppressive authority and aiming to become the Carly Fiorina of event planning. Paradoxically Whitney now finds herself in the great city of ambition doing little more than dating a jerky Australian rock singer named Jay. He thinks she should believe him when he tells her he isn’t sleeping with his ex-girlfriend because of the “energy” he displays when he’s trying to convince her. Whitney’s job seems to require only that she show up in good shoes, so she’s got lots of time to deal with Jay’s arrogance, and Jay’s got lots of time to deal with a head of hair so voluminous it could house a groundhog. In the show’s phony anthropological characterization he is meant to be emblematic of “downtown,” because he doesn’t care what people think, and he doesn’t comb. Sharing the burden of symbolism is Whitney’s roommate, Erin, who is meant to suggest a below-14th Street vibe by dint of her odd-color nail polish and wacky hats. Uptown is represented by a fantastically detestable office rival of Whitney’s, Olivia Palermo, who has provided the show’s single greatest contribution to the nomenclature of reality TV by referring to herself not as a socialite but as a “social.” This has the benefit of confirming for whoever might actually be wondering that she is in no position to unseat Anne Bass. If you ask me, Olivia is the only reason the cameras ever ought to be in the DVF headquarters, given how little appears to go on there beyond pointless staff meetings underscoring the urgency of fashion week. Olivia is the uptown not of Brearley and Yale but of ostentatious dressing and dumb luck. She transmits her ding-dong thoughts in imperious glares, and reeks of the insecurities of entitlement. She wants to make sure Whitney understands who she is, though we are given no idea of where in the world the Palermo name is supposed to resonate. At a press event for Manolo Blahnik, she tells Whitney she got her first pair of the designer’s heels for her coming-out party, then says it again after she has claimed that Manolo himself is a family friend even as he barely appears to recognize her. “The City” is not the advertisement for New York that “The Hills,” with its dreamily shot opening-credit sequence, is for Los Angeles. There seems to be West Coast bias at play because Manhattan is made to look boxy and claustrophobic and, so far at least, is evoked primarily by images of the meatpacking district at night. In only one shot, of Whitney and Jay together, does New York seem like a place of possibility and does “The City” look as it should, like a Woody Allen movie for people who might stumble on a copy of The New York Review of Books and wonder why there are no ads for Chanel. Still, the pleasures of “The City” are greater than any attempted in “Bromance,” in which Brody Jenner — of “The Princes of Malibu,” “Keeping Up With the Kardashians,” and “The Hills” — sets out to find a best friend among a bunch of chumps competing for the position. Why would you want to be Bruce Jenner’s son’s best friend? So you can go to parties and meet lots of women. What do you have to do to become his consigliere, his sidekick, his mandate? You have to find as many good-looking women as you can and show up at a party with them. The whole enterprise is really just an act of mental jujitsu because in this environment you are also expected to have good manners. One contestant was eliminated for poor etiquette. Luckily for whoever wins there is more than a lifetime of carousing with Mr. Jenner. There is also a bachelor pad in Los Angeles, “including the furniture in it,” he tells the contestants, “from West Elm.” THE CITY MTV, Monday nights at 10, Eastern and Pacific times; 9, Central time. Created by Adam DiVello; Mr. DiVello, Liz Gateley and Sean Travis, executive producers; Colin Nash, co-executive producer; Sophia Rossi and Spike Van Briesen, senior producers; Catherine K. Whyte, executive in charge of production for MTV. BROMANCE MTV, Monday nights at 9, Eastern and Pacific times; 8, Central time. Created by Jason Henry and Kathy Sutula; Ryan Seacrest, Brody Jenner and Eric Podwall, executive producers; Eliot Goldberg, Mr. Henry and Ms. Sutula, co-executive producers; Frankie Delgado, producer; Maira Suro and Lauren Dolgen, executives in charge of production for MTV. Produced by Ryan Seacrest Productions. http://www.nytimes.com/2009/01/05/ar...on/05city.html  Conservative Christian Investment Firm Flags Gay Content in Games Ruibo If the Gay-dar rings, don’t buy it. This is what the conservative Christian investment firm, The Timothy Plan, warns for parents planning to get games for their kids. Apart from the usual gaming no-no’s, such as sex, violence, and substance abuse, the investment firm also flags games with homosexual content as inappropriate and unsafe for minors. For this, The Timothy Plan hands out a list of the 30 “most offensive” games on the market. They maintain a “Do Not Buy List” for morally responsible consumers, against publishers that trade in abortion, porno, anti-family entertainment, and vices. They evaluate games on these eight categories: Sex, Nudity, Gay & Lesbian, Violence, Language, Drugs, Alcohol, and Game Addiction. They also specified if games have “demonic” content. The usual suspects are all here: Grand Theft Auto IV (Xbox 360, PlayStation 3) and Saint’s Row 2 (Xbox 360 and PlayStation 3) (both of which have a check mark on seven of eight categories - even gay content), Fallout 3 (PS3, Xbox 360, PC), and Age of Conan and World of Warcraft to name a few. If they’re such phobes about gay content, I’m surprised they didn’t tag Manhunt 2 with a gay title. They made a lot of comments that made me laugh, here are a few of my favorites: • God of War II: “This game has a sex mini-game. During the “game,” you press one of the four main PS2 buttons when indicated, which causes the women to moan louder, helping them reach climax.” Now that’s a detailed review! • Saints Row 2: “Homosexual Encounters: …Characters like Randy the Tranny were used in marketing the game.” • BioShock: “Strong Language: Strong profanity including the “f-word”, as well as numerous others we prefer to not include in this report.” Wow, that’s some hardcore swearing! Note to self: Get BioShock. • Manhunt 2: “Strong Language: Strong Language: The game’s first two words are “Holy F**k.” • Blitz: The League II: “Suggestive Themes: Females appear in miniskirts with thong underwear only to be spanked by players during touchdown celebrations.” • Bully: Scholarship Edition: “Homosexual Encounters: Gay achievements such as “over the rainbow” can be reached on the Xbox 360 when you kiss 20 boys.” • Army of Two: Homosexual Encounters: (not mentioned): Somewhat homo-erotic undertones between the two main characters are present. Well, I guess they’re not looking forward to joining FLAG, but hey, this was worth a few laughs. More info can be found at http://www.timothyplan.com/ProActive...-videogame.htm http://www.tumeroks.com/conservative...tent-in-games/  The Atheist Bus Journey Ariane Sherine Today, thanks to many Cif readers, the overall total raised for the Atheist Bus Campaign stands at a truly overwhelming £135,000, breaking our original target of £5,500 by over 2400%. Given this unexpected amount, I'm very excited to tell you that 800 buses – instead of the 30 we were initially aiming for – are now rolling out across the UK with the slogan, "There's probably no God. Now stop worrying and enjoy your life", in locations all over England, Scotland and Wales, including Manchester, Edinburgh, Glasgow, York, Cardiff, Devon, Leeds, Bristol and Aberdeen. From today's launch, two hundred of the buses will run in London, because the campaign was originally started as a positive counter-response to the Jesus Said ads running on London buses in June 2008. These ads displayed the URL of a website which stated that non-Christians "will be condemned to everlasting separation from God and then you spend all eternity in torment in hell … Jesus spoke about this as a lake of fire prepared for the devil". Our rational slogan will hopefully reassure anyone who has been scared by this kind of evangelism. In addition, we're running adverts on two further types of media. In my last Cif blog on the campaign, I asked Cif readers for ideas on alternative ways to spend the funds, and also for thoughts on different slogans. Commenters WoollyMindedLiberal, PaoloV and Catch22 suggested that we use quotes from famous freethinkers, and we've done just that: from Monday January 12, 1,000 tube cards will run on London Underground featuring atheist quotations from Douglas Adams, Albert Einstein, Emily Dickinson and Katharine Hepburn (see above), alongside the original campaign slogan. An animated version of the slogan will also appear on two large LCD screens on Oxford Street (opposite Bond Street tube station), so that you can see the advert live without having to wait for an atheist bus. And, to thank all donors and show the strength of atheism in the UK, every ABC advertisement will contain the line "This advert was funded by public donations". Amazingly, the campaign has now gone international. Spain's Union of Atheists and Freethinkers are launching buses across Barcelona today with a translation of our slogan, Italy's Union of Atheist, Agnostics and Rationalists are also planning to roll out atheist buses, while the American Humanist Association have been inspired to launch a campaign, and buses carrying their slogan "Why believe in a God? Just be good for goodness' sake" have now been running for over a month in Washington DC. Sadly, not every country has been so open to the idea: the Atheist Foundation of Australia tried to place the slogan "Atheism – celebrate reason" on buses, but were rejected by Australia's biggest outdoor advertising company. The campaign's success is thanks to Cif and Cif readers. If Matt Seaton hadn't allowed me to run with the idea here, and so many of you hadn't been so enthusiastic about it and donated generously to it, it would never have happened. There may be further campaign developments, and the campaign website and Facebook group will be regularly updated with the latest news; but for now, I hope you enjoy seeing the adverts on the streets, and that they brighten these bleak January days just a little bit. As Charlie Brooker – one of the first people to donate to the Atheist Bus Campaign – says: "Public transport in Britain suggests there isn't a God anyway, but in case anyone hasn't noticed, or feels isolated for thinking such a thing, this campaign should help." I hope it does. http://www.guardian.co.uk/commentisf...ligion-atheism  Atheist Bus Adverts Could Lead to Watchdog Ruling on God's Existence The advertising watchdog is being called upon to rule on the likelihood of God's existence after complaints were made about the atheist bus advert campaign. Martin Beckford Officials at the Advertising Standards Authority are now considering whether to tackle the question that has taxed the minds of the world's greatest thinkers for centuries. It has recorded 48 complaints since Tuesday when buses first hit the streets emblazoned with the message: "There's probably no God. Now stop worrying and enjoy your life." At least 40 more people were understood to have made objections by last night. Most of those who have contacted the ASA consider the adverts offensive and say they break guidelines on taste and decency. However Stephen Green, the Christian campaigner who led the protests against the BBC's broadcast of Jerry Springer – The Opera, is claiming they should be taken down because the statement in the adverts cannot be substantiated. He said: "If you're going to put out what appears to be a factual statement then you have to be able to back it up. They've got to substantiate this proposition that in all probability, God doesn't exist." The ASA is now considering whether to investigate his complaint, which could lead to it reaching a deep ontological conclusion about a supreme being. If it ruled that the wording in the posters was unsubstantiated, it would be interpreted as effectively saying that in all probability God does exist. Ruling that the words were justified could be taken as an agreement that God probably does not exist. Members of the public donated £140,000 to the Atheist Bus Campaign after its founder, the writer Ariane Sherine, suggested there should be an antidote to religious posters on public transport that "threaten eternal damnation" to non-believers. Some supporters of the movement, which has now paid for 800 bendy-buses across Britain to carry the posters for a month as well as placing 1,000 adverts on Tube trains, had wanted a stronger slogan that denied God's existence categorically. But the word "probably" was included in order to meet ASA rules. The British Humanist Association, which is co-ordinating the campaign, said it was confident the chosen wording will not be banned by the watchdog. Hanne Stinson, the group's chief executive, said: "I've sought advice from some of our key people here, but I'm afraid all I've got out of them so far is peals of laughter. I am sure that Stephen Green really does think there is a great deal of evidence for a God – though presumably only the one that he believes in – but I pity the ASA if they are going to be expected to rule on the probability of God's existence. However, if they do investigate we will be very happy to respond." The ASA said: "We are assessing these complaints to see whether there are grounds for an investigation." http://www.telegraph.co.uk/news/news...existence.html  Atheist Bus: 'Sleep in on Sunday Morning' Adverts Banned Atheist bus adverts celebrating the fact that non-believers get to "sleep in on Sunday morning" have been banned. Martin Beckford Secular groups in Australia wanted to put the posters on local public transport after being inspired by the campaign in Britain, which took to the streets this week after raising £140,000 in donations. They hoped to put adverts on the back of buses with slogans stating "atheism – celebrate reason" or "atheism - sleep in on Sunday mornings". But the proposed campaign was rejected by APN Outdoor, the country's biggest outdoor advertising company. David Nicholls, president of the Atheist Foundation of Australia, said: "I am flabbergasted. This is extremely disappointing and a severe blow to freedom of expression in Australia. "Australia is going to look provincial and narrow in outlook to the rest of the world because of this decision. The planet is moving to a more enlightened era but apparently, public transport advertising agents in Australia have missed the bus." A similar plan for atheist bus adverts in Tasmania was thrown out by the state-owned bus company, Metro, which is set to lead to legal action on the grounds that it is discriminatory. Metro has previously allowed adverts from religious groups including anti-abortion campaigners, but says it has now changed its policy to ban all material deemed controversial. A spokesman said: "We try to apply it equitably to all people that wish to advertise on our buses." Atheist adverts – stating "There's probably no God. Now stop worrying and enjoy your life" – have now been placed on 200 buses in London and 600 others around Britain, while different slogans will be put on 1,000 Tube trains from next week. Secularist slogans were placed on buses in Washington DC last November, triggering hundreds of complaints and counter-campaigns by religious groups, while atheist buses will be launched in Barcelona on Monday. http://www.telegraph.co.uk/news/worl...ts-banned.html  Facebook Sues Social-Network Aggregator Power.com Jennifer Guevin Facebook is suing Power.com, a Brazilian start-up that lets users access a number of social networks through one portal. Facebook filed a lawsuit on Tuesday in U.S. District Court in San Jose, Calif., for copyright and trademark infringement; unlawful competition; and violation of the Digital Millennium Copyright Act, CAN-SPAM Act, and the Computer Fraud and Abuse Act, among other charges. Power.com signs users into their various social networks and messaging clients and delivers the data from those sites and services to one page. For example, you can see all of your friends, their status updates, visit their profile pages, and even send a message to multiple friends on multiple social networks--all in one place. Last month, Webware editor Rafe Needleman described it as Meebo for social networks, and it's obviously a big convenience for people who have profiles and friends spread across Facebook, MySpace, Orkut, Hi5, and the AOL, Yahoo, and MSN instant messaging clients. But Facebook would rather users go through them. It has requested that Power.com use Facebook Connect instead of asking users for their log-in information and has been in discussions with the start-up for a month, according to The New York Times. But the Times reports the two failed to come to any resolution, and so Facebook decided to file suit. Power removed access to Facebook after the claim was filed. It's true that Power.com does its thing without consent from the sites and services it taps into. But a month ago, when the company was making its first big push into the U.S., CEO Steve Vachani told the Times that Power.com was in fine legal standing because it only accesses other sites' content when a user voluntarily logs in. He likened Power.com's actions to the way social networks import contact lists from e-mail services or the way Meebo accesses users' instant message accounts. Facebook seems to be feeling the pressure from FriendFeed, Twitter, and other social sites du jour--doing its own compiling of third-party sites. In May, it added feeds from Google Reader, Hulu, Last.fm, Pandora, StumbleUpon, and YouTube into its Mini Feed service, which had already included Delicious, Digg, Flickr, Picasa, and Yelp. And in August it launched Live Feed, a real-time stream of everything your Facebook friends are doing on the site, giving users a more centralized way to track their contacts' activity. http://news.cnet.com/8301-17939_109-10130543-2.html  LA Judge Hears Bid to Dismiss MySpace Conviction Greg Risling An attorney for a woman convicted in a MySpace hoax directed at a teen who ended up committing suicide asked a judge to dismiss her convictions Thursday, saying a computer-fraud law was improperly used to prosecute her. U.S. District Court Judge George Wu did not immediately rule after oral arguments and will likely issue a written decision, although he didn't indicate when. He did set an April 30 sentencing date for Lori Drew, who was not present. Drew was found guilty in November of three misdemeanor counts of accessing computers without authorization. Prosecutors said the Missouri woman violated MySpace service rules by helping create a fictitious teen boy on the social networking site and sent flirtatious messages from him to 13-year-old neighbor Megan Meier, a former friend of Drew's daughter. The fake boy then dumped Megan in a message saying the world would be better without her. She soon hanged herself. The case hinged on an unprecedented application of computer-fraud law. Drew was not directly charged with causing Megan's death, but she was indicted under the federal Computer Fraud and Abuse Act, which in the past has been used in hacking and trademark theft cases. Defense attorney Orin Kerr argued that it's not a crime to violate a Web site's service terms under current law. "The question here is: What is the proper reading of the statute?" asked Kerr. "Reading the law, there is insufficient evidence to find someone guilty of a misdemeanor." If Wu grants the defense motion, he would set aside the jury's verdict and enter a judgment of acquittal. Reached by phone Thursday in Missouri, Megan's mother, Tina Meier, said it would "absolutely be horrendous for all parties involved and a huge disservice to the jurors" to dismiss the conviction. "It's been a long road, and the judge has had plenty of time to make decisions before now," Meier said. Jurors found Drew was not guilty of the more serious felonies of intentionally causing emotional harm while accessing computers without authorization and couldn't reach a unanimous verdict on a felony conspiracy charge. Prosecutors want Wu to dismiss the conspiracy charge "in the interests of justice," according to court documents, but didn't elaborate. The judge did not make a decision. Drew faces up to three years in prison and a $300,000 fine. The trial was held in Los Angeles because the servers of social networking site are in the area. http://www.washingtonpost.com/wp-dyn...010800877.html  Chatterbox "Welcome to the internets, newcomer... where the men are men, the women are men and the kids are FBI agents.." - jaywalker32  A Lesson on Infinite Loops Bryant Zadegan Yesterday, I took a look at the varying perspectives taken with regards to the Zune 30 debacle. Today, I’ll take a look at what exactly led the Zune 30s to freeze. If you’d like to see the code for the entire driver, click here. Below the fold lies a sufficiently sized code sample with everything you’ll need to understand what happened with the Zune 30 bug. Relevant code is non-gray code: #define ORIGINYEAR 1980 BOOL ConvertDays(UINT32 days, SYSTEMTIME* lpTime) { int dayofweek, month, year; UINT8 *month_tab; //Calculate current day of the week dayofweek = GetDayOfWeek(days); year = ORIGINYEAR; while (days > 365) { if (IsLeapYear(year)) { if (days > 366) { days -= 366; year += 1; } } else { days -= 365; year += 1; } } // Determine whether it is a leap year month_tab = (UINT8 *)((IsLeapYear(year))? monthtable_leap : monthtable); for (month=0; month<12; month++) { if (days <= month_tab[month]) break; days -= month_tab[month]; } month += 1; lpTime->wDay = days; lpTime->wDayOfWeek = dayofweek; lpTime->wMonth = month; lpTime->wYear = year; return TRUE; } So what’s the purpose of the while loop? To put it simply, it’s designed to get the number of years from the number of days since 1980 as well as a remainder of days out of the current year. Well, let’s look at how the code plays out in my confusingly simple While Loop in Plain English™. Keep in mind that you’re never supposed to retry the loop without committing some sort of action which will ultimately exit the loop: 1. year is set to ORIGINYEAR. Since ORIGINYEAR is 1980, any addition to year is added on top of 1980. This is fine because the hardware is passing the number of days since January 1, 1980. 2. Is the number of days greater than 365? If so, proceed. Otherwise, skip to number 6. 3. Is the current year a leap year? If so, proceed. Otherwise, subtract 365 from the number of days, add 1 to the number of years, and skip to number 5. 4. Is the number of days greater than 366? If so, subtract 366 from the number of days, add 1 to the number of years, and proceed. 5. retry number 2. 6. … 7. Profit? The problem lies in the fact that there is one case which can never escape the loop. If it’s a leap year, the number 366 will stay within the loop forever because 366 will never be greater than 366, but 366 will also always be greater than 365. 366 days will pass through, in our Plain English While Loop, without having any action committed upon it. There’s a very quick solution to this: Since 366 is a valid remainder of days in a leap year (December 31 is the 366th day in a leap year), 366 can technically exit the loop without any problems. All we need to do is add a way to exit the loop when the number of days is 366. Let’s see how things go with this new breakpoint: 1. year is set to ORIGINYEAR. Since ORIGINYEAR is 1980, any addition to year is added on top of 1980. This is fine because the hardware is passing the number of days since January 1, 1980. 2. Is the number of days greater than 365? If so, proceed. Otherwise, skip to number 6. 3. Is the current year a leap year? If so, proceed. Otherwise, subtract 365 from the number of days, add 1 to the number of years, and skip to number 5. 4. Is the number of days greater than 366? If so, subtract 366 from the number of days, add 1 to the number of years, and proceed. Otherwise, skip to number 6. 5. retry number 2. 6. … 7. Profit! Thanks to the break (represented by “Otherwise, skip to number 6”), 366 days can escape the loop properly. This would lead to the end result for December 31, 2008 being years == 2008 and days == 366. This is what the break would look in the while loop: while (days > 365) { if (IsLeapYear(year)) { if (days > 366) { days -= 366; year += 1; } else { break; } } else { days -= 365; year += 1; } } Clarifying one quick thing: A number of people on outlets such as Digg suggested that changing “if (days > 366)” to “if (days >= 366)”: The problem with doing this is that the end result, upon hitting “if (days >= 366)” with the value 366, one would end up with the year going up by one and the operation “366 –= 366” playing out. End result: December 31 of the leap year is suddenly January 0 of the following year. Extra credit: This loop can be fixed such that the loop’s condition is based on the year’s status as a leap year. The change needed is simple: while (days > (IsLeapYear(year) ? 366 : 365)) //The above line basically says “Is it a leap year? Check days against 366. //Otherwise, check it against 365” { if (IsLeapYear(year)) { days -= 366; year += 1; /*You’ll notice we no longer need a break. The loop condition now *checks the days properly. Because the loop properly checks *whether days is greater than 365 or 366, the second days > 366 *check is no longer needed. */ } else { days -= 365; year += 1; } } However, if this change is made, IsLeapYear() is now being called twice. This is inefficient, especially on small devices (like the devices which would be using this driver). In order to reduce the number of times IsLeapYear() is being called, it would be best to store the value of IsLeapYear() in a variable. int leap = IsLeapYear(year); //leap is determined before the loop begins. //In this case, it would be true (1980 is a leap year) while (days > (leap ? 366 : 365)) { if (leap) { days -= 366; year += 1; } else { days -= 365; year += 1; } leap = IsLeapYear(year); //leap is determined again now that the year has changed. } This can actually be reduced even further. If you look at how the if/else statement is operating, you can see that it’s basically saying “If it’s a leap year, subtract 366. Otherwise, subtract 365,” which is similar to the while loop’s condition! int leap = IsLeapYear(year); while (days > (leap ? 366 : 365)) { days -= (leap ? 366 : 365); //days is equal to days - 366 if it's a leap year, // days - 365 if it isn't. year += 1; leap = IsLeapYear(year); } If you wanted to reduce the number of times (leap ? 366 : 365) is checked, you could do this instead: int daysThisYear = (IsLeapYear(year) ? 366 : 365); //The number of days in the current year is now calculated instead. while (days > daysThisYear) { days -= daysThisYear; year += 1; daysThisYear = (IsLeapYear(year) ? 366 : 365); } It’s questionable whether or not this code is any better than the original solution with the break, but this would be the “proper” way to do it (instead of using an arbitrary break in your code). It’s also easier to understand if you know C. The irony in all of this is that this specific driver is used in multiple Windows CE devices, not just the Zune. This is why quality assurance is so necessary. There are three morals here: Test every condition which could happen in every single loop in your code (though, as Matt Boehm points out in the comments, this might be a tad bit hard). Don’t visit Digg for programming advice. What you’ll hear is questionable at best Make your code easy to read for other developers. http://www.aeroxp.org/2009/01/lesson-on-infinite-loops/  Windows 7 Beta 1 Performance - How Does the OS Compare to Vista and XP? Adrian Kingsley-Hughes How does Windows 7 beta 1 compare to Vista and XP in terms of performance? That’s a question that’s been hitting my inbox regularly over the past few weeks. Let’s see if we can’t answer it! [p]Important note: Before I go any further I feel I need to make a point, and make it clear. The build I’m testing of Windows 7 (build 6.1.7000.0.081212-1400) is a beta build, and as a rule beta builds are usually more geared towards stability than performance. That said, the performance of this build should give us a clue as to how the OS is coming along.[/p] Rather than publish a series of benchmark results for the three operating systems (something which Microsoft frowns upon for beta builds, not to mention the fact that the final numbers only really matter for the release candidate and RTM builds), I’ve decided to put Windows 7, Vista and XP head-to-head in a series of real-world tests to find out which OS comes out top. The tests There are 23 tests in all, most of which are self explanatory: 1. Install OS - Time it takes to install the OS 2. Boot up - Average boot time to usable desktop 3. Shut down - Average shut down time 4. Move 100MB files - Move 100MB of JPEG files from one hard drive to another 5. Move 2.5GB files - Move 2.5GB of mixed size files (ranging from 1MB to 100MB) from one hard drive to another 6. Network transfer 100MB files - Move 100MB of JPEG files from test machine to NAS device 7. Network transfer 2.5GB files - Move 2.5GB of mixed size files (ranging from 1MB to 100MB) from test machine to NAS device 8. Move 100MB files under load - Move 100MB of JPEG files from one hard drive to another while ripping DVD to .ISO file 9. Move 2.5GB files under load - Move 2.5GB of mixed size files (ranging from 1MB to 100MB) from one hard drive to another while ripping DVD to .ISO file 10. Network transfer 100MB files under load - Move 100MB of JPEG files from test machine to NAS device while ripping DVD to .ISO file 11. Network transfer 2.5GB files under load - Move 2.5GB of mixed size files (ranging from 1MB to 100MB) from test machine to NAS device while ripping DVD to .ISO file 12. Compress 100MB files - Using built-in ZIP compression 13. Compress 1GB files - Using built-in ZIP compression 14. Extract 100MB files - Using built-in ZIP compression 15. Extract 1GB files - Using built-in ZIP compression 16. Install Office 2007 - Ultimate version, from DVD 17. Open 10 page Word doc - Text only 18. Open 100 page Word doc - Text and images only 19. Open simple Excel doc - Basic formatting 20. Open complex Excel doc - Including formula and charts 21. Burn DVD - Win 7 beta 1 .ISO to disc using CDBurnerXP 22. Open 10 page PDF - Text only, using latest Adobe Reader 8 23. Open 100 page PDF - Text and images, using latest Adobe Reader 8 These series of tests will pitch Windows 7 build 7000 32-bit against Windows Vista SP1 32-bit and Windows XP SP3 32-bit. The scoring for each of the tests is simple. The winning OS scores 1, the runner up 2 and the loser scores a 3. The scores are added up and the OS with the lowest score at the end wins. The test systems I’ve used two desktop systems as the test machines: An AMD Phenom 9700 2.4GHz system fitted with an ATI Radeon 3850 and 4GB of RAM An Intel Pentium Dual Core E2200 2.2GHz fitted with an NVIDIA GeForce 8400 GS and 1GB of RAM Conclusion The bottom line is that the more I use Windows 7 the more I like it. Sure, we’re looking at a beta build here and not the final code, so things could change between now and release (although realistically final code ends up being faster than beta code). Also I still have some nagging issues relating to the interface, and some concerns that the UAC changes will break applications and other code, especially installers, but overall Windows 7 beta 1 is a robust, solid bit of code. Sure, Windows 7 is not XP, and never will be (thankfully). And if you’re put off by things such as activation and DRM, then Windows isn’t the OS for you (good news is there are others to choose from). But if you’re looking for a solid OS then Windows 7 seems ready to deliver just that - a fast, reliable, relatively easy to use platform for your hardware and software. http://blogs.zdnet.com/hardware/?p=3236  Steve Jobs Has Hormone Imbalance, Will Remain CEO AP Apple Inc. founder and Chief Executive Steve Jobs, looking to quell rumors about his health, said Monday his doctors have discovered a hormonal imbalance that has been causing his weight loss. Jobs, 54, said he will undergo a ''relatively simple'' treatment and will remain as head of Apple. ''A hormone imbalance ... has been 'robbing' me of the proteins my body needs to be healthy,'' Jobs said in a public letter, adding, ''Sophisticated blood tests have confirmed this diagnosis.'' Speculation about his health have intensified since Cupertino, Calif.-based Apple said in December that Jobs would not be making his annual keynote address tomorrow in San Francisco at the Macworld conference. Apple said this year's conference will be its last, with Phil Schiller, an Apple marketing executive, giving the company's presentation. Macworld is run by the company IDG, and Apple has said it no longer wanted to be committed to releasing new products at another company's trade show -- and that it didn't see reason to have its CEO speak at a conference it wouldn't be attending in the future. Adding to the speculation, Jobs, who survived pancreatic cancer, has appeared increasingly gaunt at public appearances. In his statement Monday, Jobs said, ''The remedy for this nutritional problem is relatively simple and straightforward, and I've already begun treatment.'' He added, ''Just like I didn't lose this much weight and body mass in a week or a month, my doctors expect it will take me until late this Spring to regain it.'' The company's board released a statement separately, saying, ''Apple is very lucky to have Steve as its leader and CEO, and he deserves our complete and unwavering support during his recuperation. He most certainly has that from Apple and its Board.'' http://www.nytimes.com/aponline/2009...bs-Health.html  Ron Asheton, Influential Guitarist for The Stooges Randy Lewis Ron Asheton, whose scorching and energetic guitar work behind singer Iggy Pop in the band The Stooges established a model of raw emotion for a succeeding generation of punk, grunge, and alternative rockers, has died. He was 60. His body was discovered yesterday at his home in Ann Arbor, Mich., after his personal assistant had been unable to reach him. Police said it appeared he had been dead for several days and died of natural causes. "That first Stooges album and the second one had a big influence on me," Sex Pistols guitarist Steve Jones said yesterday. "The Stooges' and the New York Dolls' albums were my blueprint for how to play guitar." Iggy Pop called Mr. Asheton "my best friend" in a statement yesterday, and the band expressed shock at his death. "For all that knew him behind the façade of Mr. Cool & Quirky, he was a kind-hearted, genuine, warm person who always believed that people meant well even if they did not," the band said in a written statement. "As a musician Ron was The Guitar God, idol to follow." "In many ways Ron was the heart of The Stooges, and The Stooges were the creators of punk rock," Paul Trynka, author of the 2007 biography "Iggy Pop: Open Up and Bleed," said yesterday. "If you don't understand Ron, you don't understand The Stooges, and if you don't understand The Stooges, you don't understand punk rock." The Stooges charted a short but influential career from its formation in 1967 until it disbanded seven years later. Like New York's Velvet Underground, The Stooges had minimal commercial success, but their recordings and explosive live performances, during which Pop was known to cut himself and vomit on stage, put primal emotion front and center. "We really did open up the gate," Pop said last year, "and through that gate came rats, scorpions, and all sorts of things." Ron Asheton was born in Washington, D.C., and grew up in Ann Arbor. He and his younger brother, Scott, a drummer, befriended Jim Osterberg, who adopted the stage name Iggy Pop. Bassist Dave Alexander rounded out the original lineup. The Stooges shocked late-'60s audiences with the intensity of performances that were a decade ahead of the explosion of punk rock that broke open the floodgates on music as a weapon of confrontation. Despite often being reviled by club-goers and music critics, they landed a record contract with Elektra Records, also home of The Doors. Velvet Underground keyboardist and songwriter John Cale signed on to produce their debut, "The Stooges," which spent 11 weeks on the Billboard album chart in 1969. Songs from that album, however, notably the one that became The Stooges' signature number, "I Wanna Be Your Dog," inspired countless aspiring musicians. "It's a song that gave birth not to 1,000 bands, but probably 50,000 bands," Trynka said. Mr. Asheton's distinctive guitar style was evident from the beginning, employing massive distortion in blistering riffs. The group disbanded after the commercial failure of "Raw Power" in 1973. http://www.boston.com/ae/music/artic...r_the_stooges/  The Dead Coming Back To Life In 2009 FMQB After reuniting to play a few gigs in support of Barack Obama last year, The Dead has decided to embark on their first full tour in almost five years. The band will feature four founding members — bassist Phil Lesh, guitarist Bob Weir and drummers Mickey Hart and Bill Kreutzmann — along with Ratdog keyboardist Jeff Chimenti and Allman Brothers Band/Gov’t Mule guitarist Warren Haynes. The 19-date tour will kick off April 12 in Greensboro, NC and wrap on May 10 in Mountain View, CA. Pre-sale tickets go on sale January 13, and the regular on sale date is January 23. "We’ve got some unfinished business," Weir said of the tour. "Everybody has a whole new bag of tricks; we have the body of material we worked up over the years and we have a mind meld going on here and it would be a sin to let that just wither and die." Lesh added, "For me, it's the question mark that's really pulling me in... what's gonna happen? When you walk out on the stage the possibilities are infinite every time. It’s infinite and therefore you can still explore it till the day that you die." The Dead tour dates are as follows: April 12: Greensboro, NC April 14: Washington, DC April 15: Charlottesville, VA April 17: Albany, NY April 18-19: Worcester, MA April 21: Buffalo, NY April 22: Wilkes-Barre, PA April 24: Uniondale, NY April 25: New York April 26: Hartford, CT April 28-29: East Rutherford, NJ May 1-2: Philadelphia May 5: Chicago May 7: Denver May 9: Los Angeles May 10: Mountain View, CA http://fmqb.com/Article.asp?id=1088315  The Day the Music Died QRS has ended production of player-piano rolls Mark Sommer The remark scribbled at the end of the production sheet said simply, “End of era.” It was written shortly after the last piano roll came off the assembly line at QRS Music Technologies, 1026 Niagara St., at noon Wednesday. The halt in production comes 108 years after the company was founded in Chicago, and 42 years since it moved to Buffalo. Rolls used in player pianos reached their peak in popularity in the early 20th century, when a roll of paper was able to reproduce music through perforations signifying notes played on the piano. The company is now a leading manufacturer of digitized and computerized player-piano technology that runs on CDs. “The roll market has continued to decline, which is no surprise,” said Bob Berkman, the company’s music director and manager of the Buffalo office. “It no longer is, nor has it been for some time, the central part of our business. “We’re still doing what we always did, which is to provide software for pianos that play themselves. It’s just the technology that has changed. But I would be lying to say [the halting of production] doesn’t sadden me.” Bill Chapman, membership secretary of the Automatic Musical Instrument Collectors’ Association, expressed disappointment at hearing that production of piano rolls had stopped. “QRS has greatly facilitated getting new rolls and new music, and it’s going to be very sad and a great loss that they are not able to sustain their operation,” Chapman said. Until Thursday, QRS was the only continuously operating mass producer of piano rolls in the world. The only other company, in Australia, stopped earlier this decade. Sales dropped about 80 percent from 15 years ago to around 50,000 annually, Berkman estimated. Five of the 10 employees in Buffalo have been laid off because of the piano roll shutdown. The remaining employees will produce all the music for its high-tech Pianomation system for now. But that operation ultimately will be absorbed into QRS’s Seneca, Pa., plant. The piano-roll manufacturing equipment also is being sent there. Berkman said the company eventually hopes to resume production in Seneca, Pa. The piano rolls were at full production in 2008, building up a stockpile of one to two years, he said. “Production shouldn’t be interrupted in any huge way. No one wants to see an end to it, and I think the numbers are favorable for resuming production,” Berkman said. However, QRS stopped making player pianos earlier this decade. The company had bought the sole manufacturer of player pianos, Classic Player Piano, in 1993 with the express purpose of providing a continuing source of pianos to play its rolls. Berkman said reassembling the piano roll factory elsewhere will be difficult. One machine dates back to the 1880s when it was used to make shoes, and for the past 100 years has made the tabs with brass eyelets used to hook the roll into a piano. There are also aging machines to perforate and punch the holes, to cut the stencils to print the lyrics, to spool the rolls and to glue the roll boxes together. “There are so many facets of it. The perforating machines are old and cantankerous, and they’re one star in a constellation of machines that all have to be functioning,” Berkman said. The company’s fortunes in recent years have been tied to Pianomation, the digitized player-piano system that can be retrofitted on most acoustic pianos. QRS also pre-installs the system on some of its own Story and Clark grand pianos. The Pianomation systems sell for between $6,000 and $8,000, not including the piano. “After a home and car, pianos might be the next big purchase a family would contemplate,” Berkman said. “But grand pianos are still regarded as an elegant piece of furniture, and if you’re part of contemporary culture, you want it to have all the bells and whistles it can possibly have.” The company also makes the “Virtuoso Violin,” which plays by itself and in tandem with the piano. QRS dates back to 1900. Melville Clark, a Chicago piano designer and inventor, created a subsidiary of the Melville Clark Piano Co. based on the 88-note standard piano roll he developed. The company changed names and hands several times — even locating for a time in New York City — before Ramsi Tick, manager of the Buffalo Philharmonic Orchestra, bought it in 1966. Richard A. Dolan, the current chairman of the board, bought QRS in 1987. The QRS Marking Piano, a boxlike device Clark invented in 1912 that enabled a master roll to be recorded of a live performance, was designated a National Historical Engineering Landmark by the American Society of Mechanical Engineers in 1992. The original machine is under consideration for acquisition by the Smithsonian Institution, Berkman said. The last new-issue piano roll that went off the assembly line Dec. 31 was the company’s 11,060th. The song was “Spring is Here,” by Rodgers and Hart, recorded by Buffalo-based pianist Michael T. Jones. “The last roll goes against the grain,” Berkman said, since the company had been mostly making pop songs. “We looked through our list [of songs] and said, ‘There’s a great American song we had never issued.’ ” http://www.buffalonews.com/cityregion/story/538967.html  World Wrestling to Cut 10 Percent of Staff AP Sports entertainment company World Wrestling Entertainment Inc. said Friday it will cut more than 60 jobs, or about 10 percent of its staff, as part of a broader cost-reduction plan. The company behind such television shows as "Friday Night SmackDown" said the cuts will occur across all areas of the more roughly 600-employee company, yielding expected annual savings of $8 million in compensation and benefit costs. Performers in World Wrestling Entertainment's live and televised wrestling matches are hired through outside contracts, and are not directly affected by the job cuts, World Wrestling spokesman Robert Zimmerman said. The cuts are part of a broader campaign to reduce costs by $20 million this year through stronger cost controls and other steps. World Wrestling Entertainment expects to record a $3 million restructuring charge against its first-quarter earnings as a result of the move. Most of the reductions are expected to be accomplished through layoffs in the first quarter, with some cuts coming through attrition, Zimmerman said. "With these actions, we believe we can execute our key strategic initiatives, including our digital strategy and international expansion, in a more profitable manner," Chief Executive Linda McMahon said. Shares of World Wrestling Entertainment fell 46 cents, or about 4 percent, to $10.60 in morning trading. http://www.newstimes.com/ci_11414438  Blu-ray’s Fuzzy Future Matt Richtel and Brad Stone The biggest news at the Consumer Electronics Show in Las Vegas last January was not the birth of a new product but the death of one. A decision by Warner Brothers to withdraw support for the HD DVD video disc format sent shock waves through the electronics industry and appeared to hand the future of home entertainment to Blu-ray, a rival format. The move set the stage for this year’s Consumer Electronics Show, which starts Wednesday under the dark cloud of a recession and a sharp downturn in consumer spending. Nearly two million square feet of convention hall will be stocked with the latest mobile phones, portable music players, digital cameras and expensive flat-screen televisions. But many eyes will be on Blu-ray, which for the first time has the floor largely to itself as the heir apparent to the DVD. Over the last decade, DVD players and discs have generated tens of billions of dollars for Hollywood and the consumer electronics industry, so the pressure for a blockbuster sequel is high. This year will be crucial for the new format. Heavy holiday discounting and the natural decline in electronics prices over time have pushed prices for some Blu-ray players under $200, a drop of well more than half in the last few years — and into the realm of affordability for many. At the same time, Blu-ray’s backers, including Sony and the Walt Disney Company, face a growing chorus of skeptics that says the window for a high-definition disc format may be closing fast. One reason is that discs of all kinds may become obsolete as a new wave of digital media services starts to flow into the living room. On Monday, for example, the Korean television maker LG Electronics plans to announce a new line of high-definition televisions that connect directly to the Internet with no set-top box required. The televisions will be able to play movies and television shows from online video-on-demand services, including Netflix. “The Blu-ray format is in jeopardy simply because the advent of downloadable HD movies is so close,” said Roger L. Kay, president of Endpoint Technologies Associates. a research and consulting company. “Streaming video from the Internet and other means of direct digital delivery are going to put optical formats out of business entirely over the next few years.” Blu-ray’s supporters have another view. They say the technology had a breakout year, crowned by the holiday success of “The Dark Knight,” which sold 600,000 Blu-ray copies in one day. They also say that Blu-ray players are selling faster than DVD players did at a comparable time in their emergence. “What we saw in 2008 was increasing adoption of Blu-ray along with decreasing hardware prices,” said Reed Hastings, the chief executive of Netflix, which has persuaded more than half a million members to pay an extra dollar a month to rent Blu-ray discs. “The window of opportunity for DVD and Blu-ray discs is longer than most people think. But it’s not going to last forever.” The Consumer Electronics Association predicts that North American consumers will spend $1.3 billion on Blu-ray players in 2009, outpacing the projected $1.2 billion that will be spent on regular DVD players, although Blu-ray players are two to three times more expensive. Last year “was a launching pad, and 2009 is going to be our growth year,” said Andy Parsons, the chairman of the Blu-ray Disc Association, a consortium of the format’s backers. “We think this year we’ll start to see the format really take off into the mass market.” But evidence exists that many people either do not know enough about Blu-ray to buy or do not think the more expensive players and discs are worth the extra investment. Going from the whirring VCRs of yore to a DVD player was a big leap in picture quality and convenience, while the jump from DVD to Blu-ray is subtler, at least for those who do not have the latest and largest high-definition televisions. Americans are still expected to buy more standard DVD players next year than Blu-ray players, according to the Consumer Electronics Association. People like Erik Swenson, a 37-year-old interior designer in San Francisco, represent one reason. “I’ve heard of Blu-ray, but I don’t know much about it,” he said, shopping last week at a Best Buy for a DVD player. “I’m a little behind with this tech stuff.” Blu-ray’s backers acknowledge that they have a tougher sell with Blu-ray than they did with DVD, particularly in light of the sour economy. “Satisfaction with DVD is very high, and sales figures for the DVD, though the market is contracting, are very strong,” said Chris Fawcett, vice president for the home audio and video division of Sony Electronics, which has lowered growth projections for Blu-ray to account for the downturn in consumer spending. But Mr. Fawcett also said that technology companies, electronics makers, movie studios and retailers have made a significant investment in developing and promoting the format and are largely united in their determination to see it succeed. That commitment has been on display recently. In November, a group of studios and electronics manufacturers began a $25 million barrage of television commercials, using the theme “Tru Blu” and promoting Blu-ray as “the best way to watch movies at home. Ever.” On Black Friday, the crucial shopping day after Thanksgiving, electronics manufacturers coordinated with retailers to heavily discount Blu-ray players. As a result, sales surged. The continued push for Blu-ray will be a central theme at the Consumer Electronics Show, as manufacturers introduce new players and continue to cut prices on older models. Analysts say they expect companies to announce more support for a feature called BD Live (as in Blu-ray disc live), which lets people download additional material from the Internet and interact with friends in text chats that appear on the television while playing a movie. Consumers must buy adapters to bring most Blu-ray players online, though devices to be unveiled at the show may have Internet access built in. Integrating the Internet may be a matter of survival for Blu-ray, because the Internet is shaping up to be its biggest rival. More services are popping up that let people download high-definition movies and shows directly to their televisions and home computers. There are 1,092 discs available in Blu-ray format, mostly new movies like “The Dark Knight” and “Wall-E.” Apple’s iTunes Store introduced high-definition movies a year ago and already has 600 titles available to rent or download. A similar Internet-connected box, Vudu, can access about 1,400 high-definition films. “When Vudu popped up and had more high-definition movies than Blu-ray, it was a warning sign,” said Rob Enderle, president of the Enderle Group, which advises technology companies like Microsoft and Toshiba. “I think Blu-ray can sustain itself as a transition technology, but, at the end of the day, I don’t think it will ever replace the DVD.” Still, for some consumers, nothing beats the crisp, clear picture of a Blu-ray disc. “It’s a huge difference,” said Gary Tsang, 31, a computer network engineer in San Francisco who bought a $299 Blu-ray player in October and was among the shoppers who rushed out to buy “The Dark Knight” last month. Mr. Tsang added that Blu-ray made a real difference only when viewed on a good high-definition television, like the one his family bought in February for $2,700. “We’re not bleeding edge, but we’re cutting edge.” http://www.nytimes.com/2009/01/05/te.../05bluray.html  Netflix Streaming To Be Built Into TVs Dan Frommer More options on the way for watching Netflix (NFLX) streaming movies in your living room: Beginning this spring, Korean electronics giant LG will build Netflix streaming directly into some of its plasma and LCD HDTVs, the companies will announce today. This means that Netflix subscribers will be able to stream more than 12,000 movies and TV shows on their TVs without a separate set-top box or a PC. The move puts Netflix -- for convenience, at least -- ahead of its Internet streaming rivals like Amazon (AMZN) and Apple (AAPL), which require set-top boxes or computers for their movie streaming/rental services. (It's especially helpful if you don't have any more hi-def inputs available on your TV.) It's possible Amazon or Apple could announce similar partnerships. Or perhaps Apple will make its own TVs at some point. But so far, Netflix leads here, especially if it can get other companies like Samsung and Panasonic to build similar TVs. More deals like this could also eventually put some pressure on cable companies like Comcast (CMCSA) to increase their on-demand libraries -- especially the stuff that's available for free. What we don't know yet: How much LG will charge for the TVs. If they're standard fare, we could see this boosting Netflix's subscriber count. If they're overpriced, it probably won't help. Likewise, while Netflix's streaming service is solid and keeps getting better, it would be most useful if the TVs were capable of streaming other Internet video, such as video from Hulu, Google's (GOOG) YouTube, etc. Today, Netflix and its partners offer several set-top box options for streaming Netflix movies, including LG and Samsung Blu-ray disc players, TiVo (TIVO) DVRs, Roku set-top boxes, and Microsoft (MSFT) Xbox 360 game consoles. http://www.alleyinsider.com/2009/1/n...-streaming-tvs  Online Video Viewing Jumps 34 Percent Steven Musil Americans appear to be getting more comfortable watching videos online--and Google is the clear winner. Internet users in the U.S. watched 12.7 billion online videos in November, an increase of 34 percent versus a year ago, according to numbers released Monday by market researcher ComScore. Thanks to YouTube, Google Sites retained the crown as the top U.S. video property with nearly 5.1 billion videos viewed--or about 40 percent of all videos viewed online--with the video-sharing site accounting for more than 98 percent of Google's traffic. Fox Interactive Media was a distant second with 439 million videos watched (or 3.5 percent), followed by Viacom Digital with 325 million videos watched (2.6 percent). The data also showed that 77 percent of all U.S. Internet users had viewed online videos in 2008, and that the average online video viewer watched 273 minutes of video. That's all good news for sites like YouTube and Hulu that are trying to build an online ad market around video. One analyst firm expects the market for video ads to grow 45 percent to $850 million this year. An eMarketer study released in December forecast more growth in years to come: $1.25 billion in 2010; $1.85 billion in 2011; $3 billion in 2012; and $4.6 billion in 2013. http://news.cnet.com/8301-1023_3-101....html?part=rss  Comcast Confirms New Network Management Practices Grant Gross Comcast, the second largest broadband provider in the U.S., has stopped network-management practices that focus on slowing the BitTorrent peer-to-peer application, the company said. Comcast confirmed Tuesday that it has ended its old network management practices, as required by the U.S. Federal Communications Commission. The FCC in August ruled that Comcast's throttling of P-to-P (peer-to-peer) traffic violated the agency's network neutrality rules prohibiting broadband providers from blocking or slowing Internet traffic or applications. Comcast has appealed the FCC decision, saying the agency didn't have authority to enforce a net-neutrality policy statement, but last March, Comcast announced it would move away from application-specific network management. News reports in late 2007 unveiled Comcast's practice of slowing some BitTorrent traffic, and Comcast's practices caused an uproar among net-neutrality advocates. Comcast later said it was slowing traffic only at times of peak congestion, but the FCC and other groups disputed that the traffic management was limited. The new techniques shouldn't come as a surprise, said Sena Fitzmaurice, a Comcast spokeswoman. "This just confirms what we said we would do back in ... March, that we would transition to a protocol agnostic technique by year end," she said. Since the FCC's August decision, Comcast has instituted a 250GB monthly bandwidth cap on customers. The separate, new network management policy also allow the broadband providers to slow traffic to high-bandwidth users during time of peak network congestion, Comcast said. Comcast "will identify which customer accounts are using the greatest amounts of bandwidth and their Internet traffic will be temporarily managed until the period of congestion passes," the company said on its network management Web page. "Customers will still be able to do anything they want to online, and many activities will be unaffected, but they could experience things like: longer times to download or upload files, surfing the Web may seem somewhat slower, or playing games online may seem somewhat sluggish." The new technique will not manage congestion based on what applications high-bandwidth subscribers are using, Comcast said. "Rather it only focuses on the heaviest users in real time, so the periods of congestion could be very fleeting and sporadic," the company said. Public Knowledge, a consumer rights group that protested Comcast's earlier network management efforts, applauded the company's decision to change techniques. "We're pleased with the development and hope Comcast will respect the concept of the open Internet," said Art Brodsky, Public Knowledge's communications director. http://www.itworld.com/networking/60...ment-practices  Petition to Fight Copyright Law Change A newly launched organisation is trying to persuade the government to scrap the delayed change to copyright legislation that will require ISPs to disconnect Internet users found to be breaching copyright by downloading music, movies and other material from illicit sources. The Creative Freedom Foundation says Section 92 of the Copyright Amendment Act “assumes 'Guilt Upon Accusation' – cutting off Internet connections and Web sites based on accusations of Copyright infringement, without evidence or even a trial”. Foundation Co-Founder and Director, Bronwyn Holloway-Smith says: “The result of this law could be that one rogue employee or even one virus-infected computer could bring down a whole organisation's Internet and it's highly likely that schools, businesses, hospitals, and phone services will be harmed by this.” The previous government delayed implementation of Section 92 – which has been widely opposed by the telecoms industry – to allow ISPs time to formulate a policy for administering this part of the Act. Section 92 is due to take effect on February 28. The Creative Freedom Foundation was founded by artists and technologists Bronwyn Holloway-Smith and Matthew Holloway in response to the new law and “its effect on creativity, the economy, and public rights”. “The Creative Freedom Foundation views the Internet as an opportunity for artists in New Zealand, not a threat,” CFF said in a statement. The foundation is asking New Zealand artists to sign a petition to the government calling for the law changes to be scrapped, and to spread the word among other artists in support of its long-term goal of ending digital rights management (DRM) – access control technologies which allow copyright holders to limit the use of digital technology and devices. The petition can be signed at www.CreativeFreedom.org.nz The position of the new National government on the copyright law is still unclear. http://www.netguide.co.nz/index.php?...=849&Itemid=16  Campaign to Stop File-Sharers Being “Guilty Upon Accusation” enigmax Next month, New Zealand is scheduled to implement Section 92 of the Copyright Amendment Act. The controversial act provides ‘Guilt Upon Accusation’, which means that if a file-sharer is simply accused of copyright infringement, they are immediately guilty. The punishment - summary Internet disconnection. The term “3 Strikes” is a familiar one to those monitoring attempts to crack down on illicit file-sharing. Many countries are looking at proposals which if implemented, would mean that a ‘graduated response’ is taken against those accused of online copyright infringement. ‘Strike One’ would earn the infringer a warning, ‘Strike Two’ would result in a slowing of the user’s Internet connection, with Internet disconnection proposed on a third accusation. However draconian these proposals might appear, they are nothing compared to the proposed ‘Section 92′ of the Copyright Amendment Act in New Zealand. Scheduled for introduction at the end of February 2009, the act assumes that any individual simply accused of sharing copyright works on the Internet, is guilty. The punishment for ‘guilty’ is summary disconnection from the Internet. Understandably, this proposal hasn’t been well received by many outside of the entertainment industries. Indeed, RIANZ, New Zealand’s answer to the RIAA, has been a vocal supporter. One group voicing dissent is The Creative Freedom Foundation. On December 18th the group launched with the aim to “unite artists who are against the removal of New Zealander’s rights through proposed changes in Copyright law, done in the name of protecting creativity.” Foundation Co-Founder and Director, Bronwyn Holloway-Smith is strongly opposed to Section 92, which she says threatens Internet disconnections “without evidence or even a trial.” “The result of this law could be that one rogue employee or even one virus infected computer could bring down a whole organization’s internet and it’s highly likely that schools, businesses, hospitals, and phone services will be harmed by this,” she said. Hollyway-Smith warns that as the government has shown support for the bill, unless there is a major public protest against it the proposals will “roll over into law” - just 54 days from now. To this end, the foundation has started a petition and campaign against the “Guilt Upon Accusation” laws, called “Not in my Name”. The petition can be signed on the Creative Freedom Foundation website. http://torrentfreak.com/campaign-to-...sation-090105/  LimeWire Mixing Social Networking, P2P Daniel Terdiman Get ready for the collision of social networking and peer-to-peer file sharing. With the beta release of LimeWire 5.0, which was announced at the Consumer Electronics Show here, the popular P2P service is incorporating a social element that will enable people using Jabber-compatible services like Gmail to share files with friends on their buddy lists. Lime Wire calls this a "personal sharing network." The idea, said Lime Wire CEO George Searle, is to add trusted context to user searches for content, given that people are more likely to want--and feel comfortable with--content from people they know. Additionally, Searle explained that the new social features of LimeWire--which has 70 million monthly unique users and more than 5 billion queries a month--will enable people to choose whether to make files available to the public at large, or just to their friends and family. In many ways, this is much like many other content-sharing systems. But to Searle, adding a social component to LimeWire means making what is already an extremely popular service more personal to many users. Essentially, the way the new feature works is that users will be able to decide whether to make files--photographs, for example--available to anyone on LimeWire, or just to people on their buddy lists. Similarly, users will be able to search for files from their friends. And this will take advantage of a sharing system that tens of millions of people already use, something that Lime Wire hopes will encourage many on the service to adopt the social elements. Searle said he hopes that the social feature will allow users to trust the sources of the content they share across the system in a way that's not really possible when sharing with strangers. http://news.cnet.com/8301-13772_3-10137030-52.html  Coda.fm, First Public Music-Only Torrent Indexer New open music torrents directory The Coda.fm guy Hi, i am the developer and administrator of a new music torrents directory, http://coda.fm, maybe the world's first public music-only torrent indexer. We (well, i) worked hard to offer a refreshing approach to how music torrents should be displayed, offering browsing by music genre and artist, showing album art, metadata, track listings, album reviews and even artist information and pictures. We offer RSS feeds too, and we are totally ad-free. No registration is required, even for uploading torrents (only req. for comments). The server is in the USA, but the hosting company is in New Zealand. The server is a virtual machine and i have daily backups, so in case of trouble i can move it really fast. And i am in a (undisclosed) third-world country with no legislation whatsoever about this, so don't worry so much and just enjoy it. About the ads, it will have in the future, when (and if) it gets enough traffic to be really profitable. The reception so far has been very positive, lots of visits and excellent reviews in a couple of weblogs. I will keep adding features and polishing things in the following days, so expect to see some changes. Anyway, take a look, i'm sure it would we worth of your time and interest, and i wold like to get some feedback, so tell me what you guys think about it. Thanks for your consideration, and have a happy new year! http://www.p2pconsortium.com/index.p...0&#entry146735  Netlabel Shares Music on BitTorrent Sites, for Free Ernesto An increasing number of musicians are experimenting with giving away their music for free on BitTorrent. This trend has led to the formation of a new Netlabel, CXCR6, which specifically targets the BitTorrent community with new album releases. We got in touch with its founder about his motivation to promote free music. Unlike traditional record labels, CXCR6 doesn’t work with contracts, nor does it claim copyright to the music of the artists that join. It’s a non-profit operation whose goal is to get the music out in the open by distributing it to as many people as possible. That’s where BitTorrent comes in. The label distributes its artist’s albums on well know BitTorrent sites such as The Pirate Bay, Demonoid, What.cd, Waffles.fm and Indietorrents - and doesn’t mind when they leak to even more sites. TorrentFreak spoke with Lloyd Cox, one of the founders of CXCR6, who is a musician himself. We asked him how the label operates, and why he feels BitTorrent is such a great way to share music. Lloyd told us that CXCR6 is more like a collective, although it functions as a label. “The label works because it’s basically pooling resources. Under a ‘label’ we essentially share any promotion we get, because everything comes back to CXCR6. So if one of the artists blows-up, the other artists get more promotion and downloads through it,” he explained. The main purpose of the label is to promote the artists in any way possible, free of charge. “As well as just promoting the music, we also send copies for review to various sites and publications, general ‘label’ things like that. We don’t sell anything at CXCR6 but you can donate directly to the PayPal of the artists themselves,” Lloyd said. CXCR6 is just starting as a Netlabel, but they already have 5 artists on board. Three of them - Xihilisk, Slicepad and Severn - have posted their albums already. The other two musicians are expected to follow soon. Lloyd already has some experience with BitTorrent as a promotional tool. Last year he released one of his albums exclusively on Demonoid. This experience was one of the things that encouraged him to motivate others to join in the concept. “Some artists I’ve found make incredible music, but aren’t getting heard by anywhere near the amount of people they deserve. With CXCR6, I can potentially get that music to a ton of people,” Lloyd said. “I’ve been sharing my own music on BT for a few years now, but the precursor to CXCR6 was organizing a couple of unsigned music compilations on What.cd. They’ve had nearly 30,000 downloads in a few months, and that made me realize that using BT is the right way to promote new music. I don’t know many other ways you could get 30k downloads of some compilations by a load of artists no-one has heard of.” “BitTorrent provides the ultimate convenience,” Lloyd explained. “You can try something new, for free, and if you don’t like it, you can just delete it. If you really like something, you can donate to the artist, buy one of their CDs or go see them live to show your support. And who doesn’t like getting something for nothing?” We have to agree with him there, don’t you? http://torrentfreak.com/netlabel-sha...r-free-090108/  MediaSentry May be Gone, But RIAA Tactics Will Live On Nate Anderson The Wall Street Journal reported Monday that the Recording Industry Association of America has dropped long-time P2P investigator MediaSentry in favor of European firm DtecNet. The move comes as the RIAA switches tactics in its war on copyright infringement; MediaSentry was a controversial symbol of the RIAA lawsuit campaign, and the company has come under scrutiny in several states over whether its investigative practices demand a license. In addition, with record labels around the world tightening their belts in recent years and the global economy in a downturn, funding the full legal campaign is increasingly difficult; we would be shocked if price didn't enter into the decision to switch to DtecNet. Watching the watchers What's often missed in discussions of MediaSentry's work is just how boring and generally low-tech it all is. Mark Weaver, the director of MediaSentry operations at parent company SafeNet, explained the process during the Jammie Thomas trial last year. We would use the Kazaa program to search for users that are distributing our clients' songs. We would find users using the Kazaa program. We would then use the Kazaa program to look at everything that that user is distributing using the view of user's collection feature. We would then take screen shots, which are basically sort of photographs of the screens, the thing that your print screen on your keyboard does. We will take screen shots of that share folder. And then we use the Kazaa application to actually download a sample of the songs that the user is distributing. And while we're doing that, we'll also—we have a program which monitors the traffic going back and forth. And so when that process is finished, we just combine all of those things up into a bundle of data that we then pass onto the record companies. And that's basically a capture or a capture report. Essentially, the MediaSentry approach was simply to sit around all day running KaZaA and similar P2P tools, searching for (or using scripts to search for) a long list of copyrighted songs controlled by RIAA members. They would then choose some user's account to visit, take a screenshot of all the files in that person's "shared" folder, and attempt to download all of the tracks in question. The thought of doing this for more than 20 minutes a day is horrible enough, but it gets worse. Investigators stop all the partial downloads in progress and examine the files to see which appear to be copyrighted music files. KaZaA is restarted, and a small sample of the music files (11 tracks, in Jammie Thomas' case) are actually downloaded in toto. (Should the RIAA prosecute a retrial in the Thomas case, where the judge has already thrown out the "making available" theory of copyright infringement, these actual downloads would form the center of the case.) Once this process has wrapped up, MediaSentry runs a traceroute to verify the connection to the remote computer in question. It's all quite rote, tedious-sounding work, most of which involves using the KaZaA client rather than any unbelievably awesome custom software. At the end of the process, just to spice things up, MediaSentry then has a bit of fun—it sends instant messages to the user who has just been busted, informing them that they appear to be infringing copyright. The "terreastar" account that was allegedly linked to Jammie Thomas received two such instant messages. Meet the new boss, same as the old boss So, while detection operations like those run by MediaSentry might sound like something out of CSI, the reality is more prosaic. The upside is that the such an approach should produce accurate IP addresses, though mapping those to individual users can prove tricky or even impossible. The big drawback is that the method doesn't give groups like MediaSentry clarity into the sharing going on over P2P networks. All the company knows is that 1) a certain username and IP address are making certain files available and 2) that MediaSentry itself is able to download said files. But without being able to show that a particular IP address was actually sharing files with other users (as opposed to music industry investigators), lawyers will no doubt attempt to argue the legal theory that uploading to an authorized agent of a rightsholder can't infringe on the rightsholder's copyright. While it sounds like an arcane point, there is actually a surprising amount of case law on this issue, much of it involving private investigators deputized by photographers, movie studios, etc, to enter particular stores and purchase bootleg videos or infringing photographs. Given the recent RIAA decision to pursue "graduated response" agreements with ISPs rather than file mass lawsuits against end users, the technology in question might seem unimportant. But the music industry will actually need the capability to identify songs on P2P networks now more than ever; in this case, though, they will be used to generate notices for ISPs, not to file lawsuits. When we spoke with RIAA boss Cary Sherman a few weeks back, he indicated that "the technology for identifying infringement is essentially the same" as it had been in the litigation era. However the details might vary, the basic approach will apparently remain the same. DtecNet does offer something extra, though, "a unique ISP filtering solution specifically targeting copyrighted content" that only targets "content positively identified as illegal." Should notifying ISPs not prove enough to substantially curtail file-swapping, will content owners continue to push filtering at the ISP level? If so, the music industry will already have a close working relationship with a company that offers such a solution. http://arstechnica.com/news.ars/post...l-live-on.html  US Rep Boucher Headed For Telecom Subcommittee Chair U.S. Rep. Rich Boucher, D-Va., will take the helm of the panel overseeing the heavily regulated telecommunications industry after Rep. Edward Markey, D-Mass., opted Thursday to vacate the post and seek the helm of a newly minted Energy and Environment Subcommittee on the powerful House Energy and Commerce Committee. Boucher's leadership of the Telecommunications and Internet Subcommittee will be stylistically different than that of Markey, who is known for friendly yet cutting interrogations of witnesses during hearings. Like Markey, Boucher is serious about technology and brings an earnestness to difficult regulatory questions. The Virginia Democrat has long been involved in the telecommunications field. Like President-elect Barack Obama, he is a strong advocate of government funding for building high-speed Internet connections in rural areas. Boucher also has sponsored legislation to overhaul the government fund that subsidizes phone and cable companies for offering service in hard-to-reach areas. That effort stalled in the committee in the last Congress largely over disagreements with other members. Boucher is a proponent of open Internet legislation supported by Obama and Silicon Valley-based companies like Google Inc. (GOOG). More traditional Internet service providers like AT&T Inc. (T) and Verizon Communications Inc. ( VZ) are wary of legislation dictating "net neutrality" policies, preferring that the industry set standards. The recording and movie industries may suffer some heartache with Boucher leading the telecom subcommittee. For several years running, Boucher has sponsored bills dictating "fair use" of copyrighted material, for example, allowing individuals to copy music or movies for their own use without violating copyright laws. http://money.cnn.com/news/newsfeeds/...2_FORTUNE5.htm  The Cost of Bulk Cold Storage James Hamilton I wrote this blog entry a few weeks ago before my recent job change. It’s a look at the cost of high-scale storage and how it has fallen over the last two years based upon the annual fully burdened cost of power in a data center and industry disk costs trends. The observations made in this post are based upon understanding these driving costs and should model any efficient, high-scale bulk storage farm. But, and I need to be clear on this, it was written prior to my joining AWS and there is no information below relating to any discussions I’ve had with AWS or how the AWS team specifically designs, deploys, or manages their storage farm. When Amazon released Amazon S3, I argued that it was priced below cost at $1.80/GB/year. At that time, my estimate of their cost was $2.50/GB/year. The Amazon charge of $1.80/GB/year for data to be stored twice in each of two data centers is impressive. It was amazing when it was released and it remains an impressive value today. Even though the storage price was originally below cost by my measure, Amazon could still make money if they were running a super-efficient operation (likely the case). How could they make money charging less than cost for storage? Customers are charged for ingress/egress on all data entering or leaving the AWS cloud. The network ingress/egress charged by AWS are reasonable, but telecom pricing strongly rewards volume purchases, so what Amazon pays is likely much less than the AWS ingress/egress charges. This potentially allows the storage business to be profitable even when operating at a storage cost loss. One concern I’ve often heard is the need to model the networking costs between the data centers since there are actually two redundant copies stored in two independent data centers. Networking, like power, is usually billed at the 95 percentile over a given period. The period is usually a month but more complex billing systems exist. The constant across most of these high-scale billing systems is that the charge is based upon peaks. What that means is adding ingress or egress at an off peak time is essentially free. Assuming peaks are short-lived, the sync to the other data center can be delayed until the peak has passed. If the SLA doesn’t have a hard deadline on when the sync will complete (it doesn’t), then the inter-DC bandwidth is effectively without cost. I call this technique Resource Consumption Shaping and it’s one of my favorite high-scale service cost savers. What is the cost of storage today in an efficient, commodity bulk-storage service? Building upon the models in the cost of power in large-scale data centers and the annual fully burdened cost of power, here’s the model I use for cold storage with current data points: 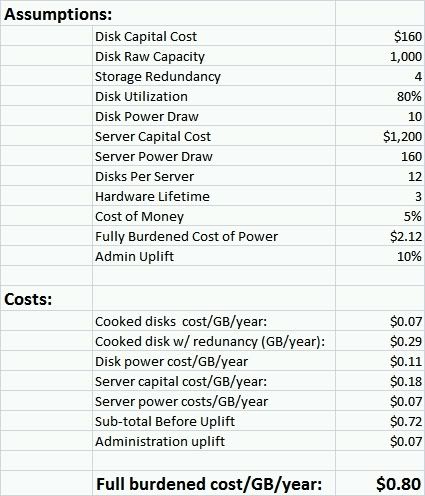 Note that this is for cold storage and I ignore the cost of getting the data to or from the storage farm. You need to pay for the networking you use. Again, since it’s cold storage the model assume you can use 80% of the disk which wouldn’t be possible for data with high I/O rates per GB. And we’re using commodity SATA disks at 1TB that only consume 10W of power. This is a cold storage model. If you are running higher I/O rates, figure out what percentage of the disk you can successfully use and update the model in the spreadsheet (ColdStorageCost.xlsx (13.86 KB)). If you are using higher-power, enterprise disk, you can update the model to use roughly 15W for each. Update: Bryan Apple found two problems with the spreadsheet that have been updated in the linked spreadsheet above. Ironically the resulting fully brudened cost/GB/year is the unchanged. Thanks Bryan. For administration costs, I’ve used a fixed, fairly conservative factor of a 10% uplift on all other operations and administration costs. Most large-scale services are better than this and some are more than twice as good but I included the conservative 10% number Cold storage with 4x copies at high-scale can now be delivered at: 0.80/GB/year. It’s amazing what falling server prices and rapidly increasing disks sizes have done. But, it’s actually pretty hard to do and I’ve led storage related services that didn’t get close to this efficient -- I still think that Amazon S3 is a bargain. Looking at the same model but plugging in numbers from about two years ago shows how fast we’re seeing storage costs plunge. Using $2,000 servers rather than $1,200, server power consumption at 250W rather than 160W, disk size at ½ TB and disk cost at $250 rather than 160, yield an amazingly different $2.40/GB/year. Cold storage with redundancy at: $0.80 GB/year and still falling. Amazing. http://perspectives.mvdirona.com/200...ldStorage.aspx  One Hacker's Audacious Plan to Rule the Black Market in Stolen Credit Cards Max Butler had an audacious plan to rule the black market in stolen credit cards. But angry hackers and pesky Feds had other ideas. Kevin Poulsen The heat in Max Butler's safe house was nearly unbearable. It was the equipment's fault. Butler had crammed several servers and laptops into the studio apartment high above San Francisco's Tenderloin neighborhood, and the mass of processors and displays produced a swelter that pulsed through the room. Butler brought in some fans, but they didn't provide much relief. The electric bill was so high that the apartment manager suspected Butler of operating a hydroponic dope farm. But if Butler was going to control the online underworld, he was going to have to take the heat. For nearly two decades, he had honed his skills as a hacker. He had swiped free calls from local telephone companies and sneaked onto the machines of the US Air Force. Now, in August 2006, he was about to pull off his most audacious gambit yet, taking over the online black markets where cybercriminals bought and sold everything from stolen identities to counterfeiting equipment. Together, these sites accounted for millions of dollars in commerce every year, and Butler had a plan to take control of it all. Settling into his chair and resting his fingers on his keyboard like a concert pianist, Butler began his attack. Most illegal online loot was fenced through four so-called carder sites—marketplaces for online criminals to buy and sell credit card numbers, Social Security numbers, and other purloined data. One by one, Butler took them down. (This story, like the rest of this article, has been reconstructed using court documents and conversations with friends and associates; Butler declined to be interviewed.) First, he breached their defenses, tricking their SQL database servers into running his own commands or simply slipping in with a hacked password. Once inside, he sucked out their content, including the logins, passwords, and email addresses of everyone who bought and sold through the sites. And then he decimated them, wiping out the databases with the ease of an arsonist flicking a match. He worked for two straight days; when he tired, he crashed out on the apartment's foldaway bed for an hour or two, then got up and went back at it. Butler sent an email under the handle Iceman to all the thieves whose accounts he had usurped. Whether they liked it or not, he wrote, they were now members of his own site, CardersMarket.com. In one bold stroke, Butler had erected one of the largest criminal marketplaces the Internet had ever seen, 6,000 users strong. The takeover was all business. The stolen-data market had become fractured across too many sites, and they were pocked with snitches and security holes. By taking control of the entire underworld, Butler had created a marketplace he could trust. Even more important, it satisfied his competitive urge. Offline, Butler was a gentle giant with a generous nature and hippie sensibilities. But in the privacy of his hidden redoubt, Iceman pursued his online enterprise with ruthless zeal. He wasn't after money, not really. He just wanted to prove that he was smarter, bolder, and tougher than everyone else. The hostile takeover was Butler's crowning achievement, but it also marked the beginning of his downfall. His actions made him a target of law enforcement, to whom he represented the epitome of a new kind of computer criminal: mercenary cybercrooks who were emerging as a far greater Internet scourge than recreational hackers. The growth of carder forums allowed thieves around the world to purchase data, equipment, and services. Since 2005, hackers and corrupt insiders have stolen more than 140 million records from US banks and other companies, accounting for some $67 billion in losses each year, according to the FBI. In 2002, FBI director Robert Mueller listed cybercrime as one of the bureau's top priorities, below only terrorism and foreign espionage. Butler's power grab planted him directly in the Feds' kill zone. In the days to come, his vanquished competitors raged against the forced merger, fought to regain their users, and staged limp counterattacks. If Butler was at all intimidated by the forces mobilized against him, he didn't show it. "Basically," he wrote later, the consolidation "was long overdue." He was fearless and doomed, just as he had always been. From the start, Max Butler, now 36, struggled to find his place in the world. The older of two children, he grew up in Meridian, Idaho, a computer geek in a rural town where rodeo champions got all the girls. When he was 14, his parents divorced. Butler found a community in the local BBS scene. Computers provided an alternate reality, a place where every problem could be solved by will, guile, or reason. Hacking was even more exciting, adding an adventuresome, competitive dimension. By high school, friends say, Butler was dabbling in computer and phone hacking, carting printouts of the hacker zine Phrack to class and phreaking free phone calls. He was also developing an aggressive streak. A fit 6'5", he was one of the few geeks who could stand up to the cowboy-hatted bullies who taunted his friends at every corner. But he wasn't just pugnacious; he was troubled. In his junior year, he broke into his high school, scrawled messages on the chalkboards, and sprayed a fire extinguisher in the halls before plundering the supply closet in the chemistry lab; psychiatrists later diagnosed him with bipolar disorder. In 1990, his freshman year of college, his girlfriend of eight months told him she wanted to see other people. Butler took the breakup badly, phoning her repeatedly and hinting at suicide. When she visited him at his mother's house to talk him down, he put his hands around her throat and said he would kill her. Butler was charged with assault with a deadly weapon—his hands. In 1991, a jury found him guilty, and he received a harsh five-year sentence. Butler emerged from prison in 1995 and tried to start over. He eventually took a new name—Max Vision—and moved to the Bay Area, where a few fellow Idaho geeks had coalesced after college. The group rented a mansion overlooking Half Moon Bay, a sleepy town on the Pacific 20 miles from Silicon Valley, where the dotcom economy was swelling to ripeness. They transformed the house into a geek paradise, pimping it out with high-performance game machines and strewing Cat 5 cable through the halls. When the sun went down, Butler celebrated his freedom at all-night raves in San Francisco. At one, he met a cute college student named Kimi Winters and invited her to a party at the house the next night. Six months later, they were married. Now in his mid-twenties and thinking about settling down, Butler started a consulting business, renting himself out as a hacker for hire. He earned more than $100 an hour performing penetration tests for corporate clients while also volunteering his whitehat skills for the FBI's San Francisco office. But it wasn't enough. For a real hacker, sniffing out a system's defenses with the owner's consent is like watching porn when you could be having sex. And so, friends say, he spent his off-hours traipsing through private networks—the very kind of trespasses he spent his days defending clients against. In spring 1998, his double life collapsed. Internet experts had found a security hole in the ubiquitous BIND name server daemon. If left unpatched, the hole would allow attackers to seize control of hundreds of thousands of machines. Butler took it upon himself to break into federal sites and fix the error. While he was at it, though, he installed a small backdoor, leaving himself an entryway into government and military networks around the country. Pop-ups informed Butler every time his backdoor finished installing, and soon his computer screen exploded with alerts: military bases, nuclear laboratories, the US Departments of Commerce, Transportation, and the Interior, even the National Institutes of Health. Then, a few weeks later, there was a knock at the door. It was the same FBI agents he'd been helping as a volunteer, accompanied by a young Air Force investigator who had traced Butler through his pop-up notifications. Three years after he had emerged from jail with an opportunity to reboot his life, Butler was headed back inside. In May 2001, he was sentenced to 18 months in Taft federal prison. Two months later, Winters told him over the phone that she wanted a divorce. She'd met someone else. "I don't know if you even think about the future anymore," she said. Butler shouted and pleaded. In search of closure, his wife traveled to Taft, 300 miles southeast of San Francisco. When Butler was brought in, he fruitlessly appealed to her to change her mind. He did think of the future, he told her, and he'd been making plans. "I've been talking to some people," he said, lowering his voice. "People I think I could work with." Jeff Norminton was finishing an 11-month stint at Taft for wire fraud when he met Butler. He was struck by the affable geek's obvious talent. The duo took daily walks in the yard, an associate says, fantasizing about working together when they got out. Butler could crack brokerage houses, where they'd tap into trading accounts and drain them into off-shore banks. One big haul and they'd have enough cash for the rest of their lives. (Norminton declined to comment for this article.) It's the kind of talk hackers routinely indulge in when they hit the joint and mix with career criminals for the first time. After they get out, the schemes are usually forgotten. So it was for Butler, initially. In 2002, he was released from Taft to a halfway house in Oakland. Ordered to get a job or go back to prison, Butler offered his services at discount prices. "The last half-dozen employers I have had paid me at least $100/hr for my time," he wrote on a computer security job board. "Now I am only asking for $6.75." A Berkeley company answered his plea, and Butler moved in with his new girlfriend, Charity Majors—a sysadmin at a porn site who painted her fingernails the color of Skittles and wore contact lenses that tinted her eyes an impossible emerald. The combination of low salary and expensive new apartment left him gasping for cash. When Norminton called to continue their prison-yard planning, Butler listened. Norminton wanted to hook Butler up with one of his associates. Christopher Aragon had recently run an Orange County leasing company, had access to cash and, just as important, had a good reputation in the criminal underworld; when he was 18, he had driven the getaway car in a trio of Colorado bank robberies. He served eight and a half years and never snitched. Norminton invited Aragon to San Francisco, where they met with Butler at a North Beach coffee shop. "This is the guy who's going to help fund our expedition," Norminton told Butler with a grin. The three talked for hours—Aragon and Butler were both vegetarians and shared Age of Aquarius philosophies—then headed to a nearby Holiday Inn, where Butler performed a demo, staging some rudimentary hacks. Aragon was impressed. Butler gave him a shopping list of equipment he'd need to get started, including a new laptop, military-grade crypto, and an antenna. Butler had gotten out of jail just in time for the cybercrime gold rush. In 2002, the first generation of carder forums was infusing the underground with an entrepreneurial esprit de corps never before seen. For the first time, an identity thief in Denver could buy stolen credit card numbers from a hacker in Moscow, send them to Shanghai to be turned into counterfeit cards, then pick up a fake driver's license from a forger in Ukraine before hitting the mall. But hacking from home was for idiots and teenagers; it was too easy for law enforcement to trace an IP address and subpoena the ISP for the location. So, according to Aragon, once a month he and Butler headed to downtown San Francisco, where the pair would check into a hotel—the Hilton, Westin, W, Hyatt—for up to a week at a time. They would sneak Butler's antenna into the room and mount it on a tripod duct-taped to the floor near the window. Butler would putter for a while to locate a high-speed wireless connection with a strong signal that he could hop onto and use anonymously. If he came up dry, Aragon ran down to the front desk to ask for a different room, explaining that he couldn't get a cell phone signal or was too afraid of heights to remain on the 20th floor. Aragon remembers that Butler, rusty from his time in prison, started by attacking easy targets: other hackers, a breed that had evolved as all teeth and no shell. He lurked in online chat rooms, sniffing out the most vulnerable cybercrooks and tapping into their systems. He vacuumed up everything—stolen identity information, passwords, PINs. The most valuable goods were "dumps," the magnetic-stripe data on the backs of credit cards, filched primarily by corrupt restaurant wait staff and gas station attendants wielding pocket-size skimmers. Stealing credit card numbers was a way to dupe lenders without directly harming innocent consumers, who aren't held liable for fraud—an added benefit for the humanist Butler. When Butler scored dumps, Aragon went to work, hurriedly stamping out bogus plastics using an embosser, a card printer, a heat foil press, and an MSR206 magstripe writer. The cards entered Aragon's assembly line as white plastic and emerged as near-perfect full-color forgeries, complete with holograms. As soon as the ink was dry, Aragon and his friends went shopping for luxury items that could be easily fenced. Timing was key; they had to grab the freshest dumps, press them in plastic, and buy as much as they could before the crooks who had purchased or stolen the numbers maxed them out first. After months of ripping off crooks, Butler started knocking over primary sources. According to court documents, he picked his targets from the FDIC's Web site, choosing small regional banks and credit unions that couldn't afford top-notch security and pulling down virgin card numbers. He sold the goods to Aragon—for $5,000 to $10,000 a month—who, back in Orange County, hired a shadow staff: an assistant to help with card-printing and programming and pretty young women to shop at high-end department stores with his plastic. Their job was to snap up designer handbags, jeans, shoes, and watches for resale on eBay in exchange for a percentage of the profits. The work was easy to love; the first time a new hire swiped one of Aragon's cards and saw approved flicker on the PIN pad, she was hooked. By late 2003, Aragon's enterprise was paying his rent and sending his oldest son to private school. But as the money poured in, the onetime bank robber found less-wholesome uses for it. Some members of the Orange County crew liked to party, Aragon says, and cocaine, ecstasy, and pot beckoned. Aragon began vanishing with his comely employees for weekend bacchanals in Vegas. (Butler preferred an ascetic lifestyle; a big-screen TV was his only indulgence.) Success introduced fractures into Butler and Aragon's friendship. Butler worried that his partner's drug use would make him reckless, and he began pestering Aragon for a larger share of the profits. In April 2004, Aragon tried to pass a few suspicious cards at the front desk of the San Francisco W Hotel. That slipup earned him an arrest, three years' probation, and a lifetime ban from the W. It was the kind of bullshit bust that happened to Aragon's staff all the time—a local police matter with no serious follow-up investigation—but to Butler, it was unforgivably sloppy. He started looking for other buyers for his wares. For most cybercrooks, that would mean creating an account on Shadowcrew, a 4,000-member carder site. Butler logged in—as Iceman—but soon grew suspicious. One of the site's admins, who went by Cumbajohny, was encouraging members to use an invitation-only virtual private network to evade surveillance. This gave Cumbajohny an exclusive peephole into members' activities. The offer apparently spooked Butler, who kept his distance. Sure enough, four months later Cumbajohny was exposed as a snitch when the Secret Service rounded up 28 Shadowcrew members and shuttered the site. Operation Firewall, as it was dubbed, was the largest-ever law enforcement operation against the computer underground. US attorney general John Ashcroft declared the sting the first major victory in a war against carders. Butler's prudence had kept him safe. Even though new online forums popped up, he decided to build his own, CardersMarket. He incorporated the standard features: Vendors submitted their product to an approved reviewer, who ran test transactions. Fake IDs or bogus plastics were scrutinized for fuzzy logos, missing microprint, and signature panels that couldn't take ballpoint. Buyers were rated on each transaction. And vendors who didn't deliver what they promised saw the epithet "ripper" branded across their profile—the equivalent of a single-star review on eBay. Butler assembled a team of handpicked admins—trusted forum capos with the power to delete posts, ban users, and appoint reviewers. One of them, Gollumfun, had survived Operation Firewall and enjoyed a sterling reputation in the underworld. Another, Zebra, was a teenager from New York who Butler thought could become a partner some day. Butler also gave Aragon admin status—presumably a salve for the sting of Butler's mercantile infidelity. His dependence on admins may have been necessary, but it was increasingly risky. In May 2000, the US Sentencing Commission had changed the penalties for possession of stolen credit cards. Previously, sentencing guidelines had punished thieves in proportion to how much money they stole. That worked great with low-level credit card cashers but not at the top of the distribution chain, where kingpins sit on thousands of untapped accounts. Letting them off the hook was like granting probation to a drug lord because his bricks of heroin hadn't yet found their way into a junkie's veins. Under the new rule, every stolen card number, used or not, was valued at sentencing at an arbitrary minimum of $500. Get caught with 1,000 numbers—an afternoon's work for a decent vendor—and you might as well have transferred $500,000 in cash, a crime worth about 10 years in the joint. Byte for byte, stolen cards now carried more prison time than child porn. CardersMarket was an instant success. Butler ran the site under his Iceman identity and created two more usernames—Digits and Darkest—behind which he sold goods, Feds say. Butler expanded from banks to credit card transaction processing centers, as well as small restaurants and retailers, where he became an expert at smuggling sniffers onto point-of-sale terminals. He distributed price lists to potential buyers: $12 for Visa Classic, $19.50 for Visa Gold, $16.50 for MasterCard, $36 for American Express. Inquire for volume discounts. Within a year, CardersMarket had signed up 1,500 buyers, sellers, and scenesters, as many as any of its rival sites. Butler wanted more. A fluent Russian speaker—a young Mongolian immigrant named Tsengeltsetseg Tsetsendelger—was brought in to help snag users from Russian and Ukrainian forums. As the operation grew, Aragon worried that Butler was losing focus on the ultimate goal, the big score that could catapult them both out of the crime business for good. But while Aragon craved a return to life as a legitimate entrepreneur, he saw Butler indulging his aggressive tendencies. Butler wasn't looking to escape the criminal underworld—he had new plans to rule it. Butler spent months plotting to infiltrate and overtake his four competitors, culminating in the two-day hackfest in his overheated safe house high above the Tenderloin. The sites blinked out of existence, their thousands of forum posts later rematerializing on CardersMarket. Iceman now had upwards of 6,000 users on his site, making it by far the biggest carder site on the Internet. To cope with the inevitable backlash and the increased workload, Butler relied on a new admin, Th3C0rrupted0ne—a well- regarded hacker who had helped run some of the sites Butler absorbed. But not all ruffled feathers were so easily smoothed. CardersMarket banned David "El Mariachi" Thomas, a former FBI operative, from the site. The blackballing sent Thomas into a rage. On public forums, he accused Iceman of working with law enforcement, calling him "Officer Ice" and "a fucking piece of shit on my shoes" and threatened to put a contract out on Iceman's life. The scuffle exposed a side of Butler that nobody had seen since Idaho. "You better pray to your god that I am never outed," he responded. "Because not only will you look like even more of a jackass than you already do, but then I will have no inhibition about coming over and wringing your snitch punk neck." Thomas wasn't the only one gunning for Iceman. In October 2006, a USA Today reporter contacted Butler for a story about the CardersMarket takeover and the fear that the consolidation could spark a new wave of cybercrime. Butler, as Iceman, told him that CardersMarket was just a service he offered to the public, like craigslist. "You don't see me ... engaging in any commerce." Butler's comments didn't make it into the piece, but Aragon was apoplectic when he heard about them. He had watched as Butler burned hours squabbling with critics in the underground and pulling unprofitable, altruistic hacks like razing a kid-porn site. Now he was giving press interviews? "You've lost your fucking mind," Aragon told him. On September 29, 2006, some 500 employees of Capital One received an email from a reporter for Lending News named Gordon Reily, seeking an interview about "the recent leak of customer records from Capital One." In the email, Reily said he got their name from a report that ran in Financial Edge and included a link to the original article. When the recipients clicked on the link—as about 125 of them did—they were sent to a blank page. While they puzzled over the empty site, a hidden payload rocketed through Capital One's firewall and onto their machines. In reality, there'd been no data leak at the fifth-largest US credit card issuer; but Reily—or someone using that name—was working on making one happen. When Capital One security officials learned about the scam, they called the FBI, which referred it to the National Cyber-Forensics and Training Alliance. Founded in 2002, the nonprofit NCFTA acts as a Justice League for hacking, pulling FBI specialists and security personnel from banks and technology companies to share best practices and intelligence. The FBI agents weren't surprised to find that financialedgenews.com had been registered under an alias. But when they investigated the account records, they discovered it had been registered from the same account as another site they'd been watching: CardersMarket.com. The Feds had some history with Iceman, the mysterious founder of CardersMarket. In 2006, one of their agents, after months of work, had won a coveted admin spot on DarkMarket under the alias Master Splynter. The government was preparing a massive sting—its biggest since Operation Firewall—through the site when, out of nowhere, Iceman shut it down and absorbed its members into CardersMarket. Not only that, he had traced Splynter's IP address to NCFTA offices and was telling everyone in the underground about the embryonic sting. Now the Capital One attack implied that Iceman wasn't just hosting a scurrilous Web site for cyberthieves. He seemed to be a thief himself, and a sneaky one at that. Butler acted as if he knew the Feds were after him. In November 2006, he declared Iceman's retirement and let it be known that he had handed control of CardersMarket to Th3C0rrupted0ne, then secluded himself. Soon he took back the site under another handle, Aphex. He boosted his physical security, switching safe houses to become a moving target. But the Feds were working on a secret asset: Jonathan "Zebra" Giannone, the promising young hacker who had served as one of CardersMarket's first admins. Zebra had made a fatal mistake in June 2005, when he sold 21 Bank of America platinum card numbers to Gollumfun for $600. Unbeknownst to Zebra, Gollumfun—whose real name was Brett Shannon Johnson—had recently been popped passing counterfeit checks in Charleston and agreed to serve as an undercover informant; he'd been working out of the Secret Service's Columbia office. Butler had sniffed out the rat quickly and banned him, but not in time to save Zebra. On March 8, 2007, the kid was found guilty of wire fraud and identity theft. Zebra was summoned from his cell in the Lexington County jail in South Carolina a week after his trial. He instantly recognized the Secret Service agents: Bobby Kirby and Brad Smith had been Gollumfun's handlers. "We want to know who this guy Iceman is," one of them demanded. The agents called Zebra's lawyer, who consented to an interview in the hope of winning leniency for his client. In a series of meetings over the next three weeks, authorities say, Zebra told them everything he knew: Iceman lived in San Francisco, did a brisk business in dumps, sometimes used the alias Digits to sell his goods, and, most crucially, had a partner named Christopher Aragon. The Secret Service didn't know much about Aragon, but the FBI had a file on him. Back in 2005, Jeff Norminton had been nabbed on a new fraud charge in Orange County. While locked up, he willingly told the FBI all about Aragon and his partner Max Butler. Investigators never acted on the information. Now all the Feds had to do was get enough solid evidence on Aragon for a search warrant. A month later, someone else beat them to it. On Saturday, May 12, Aragon was busted by the local police at a Bloomingdale's 20 miles from his house in Capistrano Beach, California, along with an associate who was buying handbags with his fake cards. The detectives got a search warrant for his home and a nearby warehouse and collected hundreds of cards, a computer, counterfeiting gear, and tasting portions of cocaine, pot, and ecstasy. Using Aragon's meticulous business records as a road map, they swept up his cashers and other confederates, making seven more arrests, including Aragon's wife, Clara, who had been fencing handbags on eBay. His mother took custody of the two boys, now 6 and 9. Aragon's arrest appeared to frighten Butler. He deleted Aragon's CardersMarket account, ditched his cell phone, and found yet another safe house—the Oakwood Geary Courtyard, a corporate apartment building back in San Francisco's Tenderloin district. On June 7, Butler checked out a red Mustang from his neighborhood Zipcar, loaded it with a computer and bag, and drove to the Oakwood. He didn't notice the Secret Service agents watching from the street as he moved in. A month later,Butler jolted awake, shot upright in bed, and blinked fretfully into the darkness of his apartment. It was his girlfriend, Charity Majors; she had crawled into bed next to him, trying in vain not to wake him. Butler was growing more tense every day; he had stopped exercising, and his health was suffering. "Sweetie, you can't keep doing this," Majors murmured. " You're losing focus on who you are and what you're doing." "You're right," he said. "I'm done." It was time to get out. Butler's supervised release was over, and getting a job would be easier now without his probation officer looking over his shoulder. But he couldn't bring himself to just abandon CardersMarket, and he didn't trust any of his remaining admins to take the reins. Even Th3C0rrupted0ne, who was devoting 14 hours a day to the site, sometimes behaved suspiciously. Butler didn't know it, but he was running out of time. In July and August, the Secret Service interviewed Tsetsendelger, his former Russian interpreter, who was on probation after getting caught with Aragon-produced gift cards at an Apple store in Emeryville, California. Meanwhile the FBI won a secret court order that allowed agents to monitor the IP addresses of visitors to CardersMarket's server. It was the modern equivalent of taking down license plate numbers outside a mob hangout, and the Feds knew it was no coincidence that several traced back to broadband subscribers living within a block of the Oakwood. Butler was accessing his neighbors' Wi-Fi, they figured. On Wednesday, September 5, Butler dropped Majors off at the post office and directed his cabdriver to the Oakwood. He rode to the fourth floor, unlocked the door, and crashed out on the bed for an uneasy slumber. At about 2 pm, the front door flew open and a half-dozen Secret Service agents rushed the room, guns drawn. They handcuffed Butler and transported him to the nearby federal building for questioning. Two of the agents were dispatched to Majors' apartment. They told her what happened and took her to say good-bye to Butler. "I'm sorry," he told her when she walked in. "You were right." Months later, Aragon's lawyer gave him some bad news. The Secret Service had cracked Butler's crypto and knew more about the hacker than Aragon did—which meant Aragon would probably never be offered a deal, even if he wanted one. Even more troubling, the lawyer said Butler had about 1 million credit card numbers on his hard drive. Aragon was shocked. All those years they'd spent searching for one big score, and Butler was sitting on enough dumps to set them up for life. Butler never said a word to Aragon. Aragon's anger faded as he realized the implications for Butler. A million dumps; the sentencing equivalent of a $500 million heist. Butler was potentially looking at the first life sentence in US hacking history. "I couldn't figure it out; what is this guy doing? Why doesn't he just go get a job? Then it dawned on me, many years later: Max just likes to hack." Christopher Aragon is in a jail-issue V-neck at the Orange County Central Men's Jail, a grim lockup in the flat, sun-baked center of Santa Ana, California. He's been studying the Bhagavad Gita and reflecting on his life, his friendship with Butler, and the choices that have brought him to the precipice of a final plunge into the justice system. Seven members of Aragon's old crew have pleaded guilty and received sentences ranging from a few months to seven years. His wife is about to finish her time. Aragon is alone: His bank robbery arrest as a young man and a related conviction for stealing a getaway car count against him under California's Three Strikes law. He's awaiting trial and, if convicted, could face 25 years to life. Across the country in a holding facility near Pittsburgh, Max Butler has it even worse. He has spent a year in prison awaiting trial. The only deal prosecutors have offered is 30 years instead of life. His lawyer tried to get Butler released on bail, but the judge refused after the Feds speculated that Butler was sitting on vast stores of hidden cash and could easily use his contacts to disappear with a new name. To prove he was a flight risk, they played their trump card: messages between Butler and a Secret Service informant who had infiltrated CardersMarket. In them, Butler revealed the steps he took to cover his tracks after Aragon's arrest—showing his ability to assume fake identities and evade law enforcement. The name was blacked out, but the messages left little doubt as to the snitch's identity. Th3C0rrupted0ne's handle, it turns out, may have had dual meaning. To his friends, Butler seems at peace with his confinement, as if he feels he deserves to be in jail for a while. He speaks daily with Majors, in long conversations more intimate than any they had while he was immersed in his double life. And he has made some like-minded acquaintances in the joint. They've started a Dungeons & Dragons campaign together. But this time, he isn't thinking about what he's going to do when he gets out of prison. Finally, it seems like Max Butler has nothing left to prove. http://www.wired.com/techbiz/people/.../ff_max_butler  Many Teens Display Risky Behavior on MySpace: Study Julie Steenhuysen More than half of teenagers mention risky behaviors such as sex and drugs on their MySpace accounts, U.S. researchers said on Monday. They said many young people who use social networking sites such as News Corp's MySpace do not realize how public they are and may be opening themselves to risks, but the sites may also offer a new way to identify and help troubled teens. "We found the majority of teenagers who have a MySpace account are displaying risky behaviors in a public way that is accessible to a general audience," said Dr. Dimitri Christakis of Seattle Children's Research Institute, whose studies appear in the journal Archives of Pediatric & Adolescent Medicine. In one of two studies, Christakis and Dr. Megan Moreno of the University of Wisconsin analyzed 500 randomly chosen MySpace profiles of 18-year-olds in 2007. Overall, 54 percent of the publicly available accounts they checked contained information about high-risk behaviors: 41 percent mentioned substance abuse, 24 percent sexual behavior and 14 percent violence. Christakis said many teens are unaware of how public and permanent Internet information can be, while parents often do not know what their kids are up to. "No one says, "Whoa! Why are you putting that up there?'" Christakis said. In a second study, the researchers identified 190 individuals aged 18 to 20 whose MySpace accounts displayed multiple risky behaviors. Half were sent a message from "Dr. Meg" from Dr. Moreno's MySpace profile. The message warned about the risks of disclosing personal details online and offered a link to a site with information about testing for sexually transmitted diseases. Three months after this single message, many of the young people had withdrawn references to sex and substance abuse and tightened security controls. "It really provides the opportunity to reach millions of potential at-risk teens and try to modify their behaviors or at least prevent them from disclosing them to the entire world," Christakis said in a telephone interview. The e-mail was most effective at curtailing references to sex, with 13.7 percent of profiles in the group that received the warning deleting all references, compared with 5.3 percent of those who were not sent the message. Christakis said displaying sexual information online can expose a teen to advances from sexual predators. Employers and universities may also check those sites. (Editing by Alan Elsner and Maggie Fox) http://www.reuters.com/article/lifes...50451820090106  Doctors Will Make Web Calls in Hawaii Claire Cain Miller American Well, a Web service that puts patients face-to-face with doctors online, will be introduced in Hawaii on Jan 15. Its first customer, Hawaii Medical Service Association, the state’s Blue Cross-Blue Shield licensee, will make the Internet version of the house call available to everyone in the state, the company said. The service is for people who seek easier access to physicians because they are uninsured or do not want to wait for an appointment or spend time driving to a clinic, said Roy Schoenberg, co-founder and chief executive of American Well Systems, which is based in Boston. Dr. Schoenberg, a physician, said that American Well had piqued the interest of policy makers in Washington who want to expand access to health care. Insurers in other states will soon offer the service, he said. Patients use the service by logging on to participating health plans’ Web sites. Doctors hold 10-minute appointments, which can be extended for a fee, and can file prescriptions and view patients’ medical histories through the system. American Well is working with HealthVault, Microsoft’s electronic medical records service, and ActiveHealth Management, a subsidiary of Aetna, which scans patients’ medical history for gaps in their previous care and alerts doctors during their American Well appointment. The Hawaiian health plan’s 700,000 members pay $10 to use the service. The insurer also offers the service to uninsured patients for $45. Health plans pay American Well a license fee per member and a transaction fee of about $2 each time a patient sees a doctor. Hawaii is particularly well suited for online medicine because the islands are remote, it takes time to travel among them and it is difficult for the state to recruit doctors to rural areas, said Mike Stollar, vice president of marketing for the Hawaii Medical Service Association. However, some critics of doctor visits via webcam worry that doctors will miss important symptoms if they do not see patients in person. Others doubt that the poor and uninsured will have the broadband connection and webcams to use the service. . “It’s a tool to help doctors do better, the way a stethoscope is a tool,” said Robert Sussman, a family practice doctor on Oahu. “You still have to use your common sense, your medical knowledge.” Certain diagnoses, such as whether a sore throat is a virus or a strep infection, are difficult using a webcam, says Dr. Sussman, who has been testing the service for several weeks. He predicts the service will be useful for patients who need medication refills or follow-up consultations after surgery or who are elderly and homebound. It can save valuable time in the case of a serious condition, he said, because an online doctor can recommend that a patient visit an emergency room or specialist immediately rather than waiting a week to see a general practitioner. A doctor can see, for example, whether a baby with a fever is lethargic and needs to visit a physician or is active and just needs rest. “It’s a better iteration on, ‘Take two aspirin and call me in the morning,’ ” Dr. Sussman said. “We can’t lay on the hands, but we can lay on the eyes and get a better feel.” Patients and doctors can use American Well with one camera or with text chat. A study last November by Forrester Consulting for the California HealthCare Foundation found that about two-thirds of uninsured patients used broadband at home and that almost all medical professionals did. http://www.nytimes.com/2009/01/06/te.../06health.html  Directors and Studios Sharing Economic Pressure Tom Roston Catherine Hardwicke had every reason to celebrate as her latest film, "Twilight," opened to nearly $70 million in November. The haul exceeded even the most optimistic expectations, and reviewers credited Hardwicke for breathing cinematic life into novelist Stephenie Meyer's vampire romance. But when Summit Entertainment immediately began fast-tracking a sequel, "New Moon," Hardwicke was conspicuously absent. The director had concerns about the direction of the new franchise and the amount of prep time available. Summit, by some accounts, had reservations about working with the indie-minded Hardwicke again. The studio soon announced it would hire another director, Chris Weitz, to ensure its follow-up film would be ready by November. An isolated instance of financial dictates undercutting a director's power? Perhaps. But there is evidence this awards season that the challenging economy is forcing studios to take tougher stands when it comes to keeping directors happy. "It's the climate that's different," says one producer, who declined to be identified. "It's not so much the conversations. Conversations about budgets have always been difficult. But in the last year, (they've) been markedly different. There's even more of a pressure on budgets." When Danny Boyle turned in "Slumdog Millionaire" to Warner Bros., which was in the process of shuttering specialty divisions Warner Independent Pictures and Picturehouse, the studio was no longer interested in distributing the film -- even though it had invested in it. Instead, Warners allowed Fox Searchlight to take over distribution, and the film has since become an Oscar front-runner. Director Stephen Daldry begged producer Harvey Weinstein for eight more filming days on "The Reader," so Weinstein made him agree to a Faustian bargain: In exchange for the shooting upgrade, Daldry had to consent to test an early cut of the movie. If it passed muster with the audience, the director would then be obligated to finish the film in time for a 2008 release. Never mind that both films were specialty fare, where the director's vision is more highly valued. Business interests took precedence. Of course, the days when directors were given blank checks and full creative freedom are long gone. No way would Dennis Hopper be allowed to disappear into Peru for a hallucinogenic project like 1971's "The Last Movie." Francis Ford Coppola likely could not set up base camp for months on end in the Philippines, as he did to capture 1979's "Apocalypse Now" -- the excesses of Michael Cimino's "Heaven's Gate," which crippled United Artists in 1980, saw to that. But even in the current era of corporate Hollywood, the downtrodden economy is putting added pressure on filmmakers. That's partly because studio execs don't control their own destiny. Rather, it's their bosses at conglomerates like Time Warner, News Corp., Disney, Viacom and Sony who call the shots. A studio regime that enjoys a good year at the box office can't automatically roll over some of those returns into its upcoming production slate. Instead, with parent companies decreeing cost cuts, and companies like Disney and Paramount cutting back on the number of films they release, it's become even more challenging to mount a risky movie. Oliver Stone, forced to turn to independent financing for "W.," adopted a near-gonzo style, knocking off the biopic in just 46 filming days and shooting in Louisiana to take advantage of tax incentives. Even Clint Eastwood, known for his economical shooting style, picked up the pace. Back in 2004, his "Million Dollar Baby" was budgeted for 39 shooting days and he completed it in just 37. But he raced through his latest film, "Gran Torino," in a mere 32 days, while also agreeing that Nick Schenk's script, originally set in the writer's home state of Minnesota, be reworked so that it could be shot in tax-friendly Detroit. In fact, tax incentives played as large a role as anything in shaping this season's awards hopefuls, making the Australia-shot "Australia" feasible and also leading David Fincher's "The Curious Case of Benjamin Button" to be set in New Orleans rather than the Baltimore of the original F. Scott Fitzgerald short story. These concessions suggest a slight shift in the balance of power away from top directors and toward the studios that control their purse strings. "To the extent that it's a buyer's market, (studios) may feel empowered to exert more authority," says Robert Newman, an agent at the Endeavor talent firm. "But at the same time, nobody hires someone to make their life miserable. There's enough competition for each (directing) job that you want to find someone who shares your vision, with whom you can establish a lasting relationship." The most expensive tentpoles -- where, presumably, studios watch over directors' shoulders most closely -- often turn into the most collaborative enterprises, since both usually are focused on turning out a commercial crowd-pleaser. "I welcome the collaboration. The studio often has greater objectivity than the director," says Rob Cohen, who masterminded the summer sequel "The Mummy: Tomb of the Dragon Emperor," which has grossed nearly $400 million worldwide. "Working with (Universal execs) Marc Shmuger and Donna Langley, I took them entirely into my process and benefited from their insight. The net result was a better movie." In the middle of postproduction, Cohen screened a second assembly of the movie for the Universal executives. Shmuger didn't believe the Mummy character was scary enough. At first, Cohen says, he was taken aback, but then decided he had become too involved in the technical challenges of bringing the emperor and his terra cotta army to life. Mulling it over that night, Cohen returned to an earlier idea that the terra cotta should break open to reveal a burned and shriveled version of the emperor. At 5 a.m. he called character designer Aaron Sims to work up some sketches, and by noon he was back at Universal. "This will be scary, but it will cost $4 million," Cohen says he told Shmuger, who immediately OK'd the new effects. "He was the one who put his finger on the problem. I came up with the solution and he paid for it. If I had been stubborn about his first response, maybe I wouldn't have seen it myself." Ironically, it's on those big movies where directors have to worry the least about being nickel-and-dimed. "If you're already into a movie for $100 million, you'll do what's necessary to protect that investment," says one insider. "If a director wants a couple of extra days, as a percentage of the budget, it's not that great. A few extra days has a much greater impact on a smaller film." The studios often put greater pressures on the directors of midrange pictures -- thrillers, action pictures, comedies -- that fill out the bulk of their schedules. With only a few exceptions -- like prolific filmmaker Judd Apatow, whose genially raunchy comedies have been successful enough to afford him rare freedom -- genre directors don't call the shots. And where filmmakers once resisted or downplayed test screenings, those results now often dictate the final shape of a movie. "Everybody's trying to score an 80 or 90 in the top two boxes ("excellent" and "very good") at the research screenings," says one veteran. If signs are ominous, drastic measures are sometimes taken: Unhappy with "The Invasion" (German director Oliver Hirschbiegel's 2007 remake of "Invasion of the Body Snatchers"), producer Joel Silver recruited James McTeigue to helm reshoots. Yet even in these economically depressed times, directors can still take some comfort in the fact that though some studios want to view them as hired hands, they remain essential to the process. "Studio executives are always thinking about the next movie, and the right director can get a movie made," says Tom Pollock, a former studio head-turned-producer. "So the studio doesn't want to be fighting with a director because they may want to woo him for his next movie." http://www.reuters.com/article/enter...5050VQ20090106  Patrick Wants Net Sales Tax Created Mass. coffers would gain $15m per year Casey Ross Governor Deval Patrick is pushing lawmakers to expand the state's ability to collect sales tax on products sold over the Internet, which could add millions of dollars in revenue each year and alleviate a severe budget crisis. Patrick's revenue commissioner, Navjeet K. Bal, has submitted a report to the Legislature asking it to approve an Internet sales tax by the end of this year. Currently, only Internet retailers that have in-state locations, such as stores and warehouses, collect and remit sales taxes on purchases by Massachusetts residents. The proposed law would expand that to collect taxes from Internet retailers that have agreed to participate in a multistate compact, called the streamlined sales tax initiative. Because participation is voluntarily, Massachusetts officials estimate the state would collect only an additional $15 million in taxes a year. Still, state officials said passage of the law would help spur Congress to approve a broader version of an Internet sales tax that could produce hundreds of millions of dollars in additional revenue. So far, 22 states have adopted Internet, phone, and mail-order sales taxes based on the streamlined sales tax sys tem. Legislation by Congress would require all 45 states that have sales taxes to collect on those transactions. Because it would be a federal mandate, the law would dramatically increase the number of retailers required to participate, generating as much as $545 million for Massachusetts alone, according to an analysis by the University of Tennessee. The US House version of the bill is sponsored by Representative William Delahunt, Democrat from Quincy, who has argued that implementing the tax agreement is more about creating a fair tax policy than raising revenue. "This will protect Massachusetts businesses that are disadvantaged by the current system," Delahunt said. "Small- and medium-sized businesses need this in order to compete with large sellers from out of state" that aren't required to collect and remit sales taxes. But opponents argue such a tax would unfairly burden Internet retailers with the cost and complication of setting up systems to collect the tax and expose them to audits if tax collectors argue they did not collect enough. "Why in the world would you think increasing taxes on people buying stuff would help the economy?" said Grover Norquist, president of Americans for Tax Reform. "It won't do anything other than throw sand in the gears of commerce." In Massachusetts, the tax proposal appears to enjoy broad support in the Legislature, where members are grappling with anticipated budget cuts that could reduce local aid to communities, hurting schools and cutting public safety services. A special corporate tax committee that studied the issue voted 14 to 1 in 2007 to support its implementation here. Even the one lawmaker on the committee who voted against it, Brad Jones, a North Reading Republican, now sounds more supportive. Jones said an Internet sales tax would be a far better option for the state than an across-the-board tax increase. He noted that taxing Internet sales is technically not a tax increase, because consumers are currently required under a seldom-enforced law to pay tax directly to the state on those items they've purchased from out-of-state vendors. "There are some questions that need to be vetted and explored, but this is something that is deserving of consideration," Jones said. Some of those questions include whether the state can reconcile conflicts in its tax code with the system being developed by the streamlined project. For example, the current system does not allow states to use price thresholds when taxing certain categories of products, but Massachusetts only taxes clothes that cost more than $175. Last month the members of the multistate organization gave preliminary approval to allowing the Massachusetts clothing threshold. A final vote is expected within months. http://www.boston.com/business/taxes...s_tax_created/  Thailand Blocks 2,300 Websites for Insulting Monarchy AFP Thai authorities have blocked 2,300 websites for allegedly insulting the country's revered monarchy and are waiting for court approval to restrict another 400, the government said Tuesday. The blocking of the websites under harsh lese majeste laws which protect King Bhumibol Adulyadej has been criticised by rights groups and media organisations in recent months. "The blocking of websites that disseminate content and pictures which insult the monarchy is one of the government's crucial policies," Information and Communication (ICT) minister Ranongruk Suwanchawee said in a statement. "We have blocked more than 2,300 websites. We are preparing to ask for court approval to shut down an additional 400 sites and will amend the... law to increase powers of ICT officials as soon as parliament reopens," she said. The ministry had spent 45 million baht (1.28 million dollars) to buy equipment for a round-the-clock "war room" targeting inappropriate web sites, Ranongruk said. The ministry would ask the ministries of justice, interior and defence to "decisively" prosecute violators, who face imprisonment and a fine for breaking the law, the minister said. Defaming the royals in Thailand carries a a maximum jail sentence of 15 years but media groups say the law is often used as a political tool. Thailand made headlines around the world in 2007 when it blocked the popular video-sharing website YouTube after clips started appearing mocking the 81-year-old King Bhumibol. Global media watchdog Reporters Without Borders recently accused the Thai government of using the laws that protect the monarchy to suppress dissenting voices on the Internet. New Prime Minister Abhisit Vejjajiva however defended the crackdown in a recent interview with AFP, saying that there were "historical and cultural differences" with other countries. "We will respect the rights, but those rights are exercised within the same limits that even the most liberal of countries apply," Abhisit said in the interview on December 26. The royal family's role in politics became a sensitive subject last year amid protests by a group claiming loyalty to the monarchy which opposed the previous government for being too close to ousted premier Thaksin Shinawatra. A court verdict on December 2 effectively dissolved that government, paving the way for Abhisit to become premier mid-way through last month. Parliament is due to reconvene on January 21. http://www.google.com/hostednews/afp...QeuqiHgskLqTaw  China Targets Google in Pornography Crackdown Henry Sanderson China warned Google and other popular Web portals Monday that they must do more to block pornographic material from reaching Chinese users, the latest in a series of government crackdowns targeting Internet content. The crackdown focused on pornography but is part of a larger Chinese effort to control freedom of expression and root out material it considers destabilizing, such as sites that criticize the Communist Party, promote democratic reform or advocate Taiwan independence. Pornography is banned in China but remains widely available on and off the Internet. Popular Chinese Web portals frequently show sexually explicit pictures and provide links to pornographic Web sites. The announcement said Google and Baidu, China's two most heavily used search engines, had failed to take "efficient" measures after receiving notices from the country's Internet watchdog that they were providing links to pornographic material. Google asserted that it abides by Chinese law and does not generate pornographic content. The statement also criticized popular Web portals Sina and Sohu, as well as a number of video sharing sites and popular online bulletin boards such as Tianya, that it said contain problematic photos, blogs and postings. Jeremy Goldkorn, founder of Danwei.org, a Web site that covers Chinese media issues, said such campaigns happen regularly in China to keep Internet sites in line with the government and the mention of Google and Baidu is meant to send a strong message to the whole industry. "The fact that they rapped every major Web site on the knuckles ... it is sending a message out to be on their best behavior and that's a system that everyone understands," he said. Charles Freeman, a China specialist at the Washington-based Center for Strategic and International Studies, said the pornography issue was a "stalking horse" for the Chinese government. "They're looking extensively at political speech, the sort of things traditionally cast under the First Amendment in this country," Freeman said. He said 2009 is a "very sensitive year politically in China," noting it was 50 years since the Dalai Lama fled Tibet after a failed uprising, 30 years after the democracy wall movement, and 20 years after the crackdown on pro-democracy protesters in Tiananmen Square. Beijing loosened some media and Internet controls during the 2008 Summer Olympics _ gestures that were meant to show the international community that the games had brought greater freedom to the Chinese people, but blocked The New York Times' Web site on Dec. 19. It was unblocked a couple days later and remained open Monday. The Chinese government remains wary of losing its control over the Internet, which could be used for organized opposition to the rule of the Communist Party. Last month over 300 lawyers, writers, scholars and artists signed a petition online called "Charter 08", calling for a new constitution guaranteeing human rights. In the past, the Foreign Ministry has defended China's right to censor Web sites that have material deemed illegal by the government, saying that other countries also regulate Internet usage. It was unclear what the government classifies as pornographic but it said seven government agencies will work together on the campaign to "purify the Internet's cultural environment and protect the healthy development of minors," the notice said. The statement, which was posted to a news and information Web site managed by the State Council, said violators will be severely punished, but did not give details. The official Xinhua News Agency said the national campaign would last for one month. It is unlikely anything other than a fine will be meted out to offenders, Goldkorn said, and the move more likely signifies a need for a quick clean-up ahead of the Chinese Spring Festival, or new year, at the end of this month. Private Chinese Web sites often hire their own censors to delete sensitive content and images can be erased quickly at the behest of the authorities, he said. This happened early last year when explicit photos of Hong Kong actor Edison Chen and several female partners performing sex acts circulated online. Chinese authorities arrested or detained nearly a dozen people for circulating the photos. Sexually explicit photos still appeared on online portals Monday, including pictures of actress Zhang Ziyi sunbathing on a beach topless. A Google spokeswoman in China, Cui Jin, defended the site's operations, saying it is a search engine and does not generate any pornographic content. The company obeys Chinese law, she said. "If we find any violation, we will take action. So far, I haven't seen any examples of violations," Cui said. As a search engine, Google doesn't control the content of the billions of pages in its index, added California-based company spokesman Scott Rubin. Baidu did not immediately return an e-mail seeking comment, and phones at Sina and Sohu rang unanswered. China has the world's largest population of Internet users with more than 250 million, and China's attitude to love and sex has changed markedly since it was denounced as a bourgeois decadence under Mao Zedong, a byproduct of rising prosperity and looser government restrictions on private life. http://www.washingtonpost.com/wp-dyn...010500383.html  Facebook Won’t Budge on Breastfeeding Photos Jenna Wortham Facebook is standing firm on a policy that has led to the removal of some photos posted by women that show breastfeeding. The deletions have spurred Facebook members to stage protests both online and offline. Dozens of supporters gathered last Saturday at Facebook headquarters in Palo Alto, Calif., while online, and more than 11,000 members participated in a virtual “nurse-in,” or changed their profile photos to images depicting women breastfeeding. The controversy began after several women began noticing that photographs of themselves nursing their children had been flagged for removal. They formed a group called “Hey Facebook, Breastfeeding Is Not Obscene!” to protest a policy that prohibits members from uploading any content deemed to be “obscene, pornographic or sexually explicit,” which can include images showing exposed breasts. Stephanie Knapp Muir, 40, one of the organizers of the Facebook group, said the company’s policy was unfair and discriminatory towards women. “If they were removing all photos of any exposed chest — male or female — in any context, at least that would be fair,” Ms. Muir said. “But they’re targeting women with these rules. They’ve deemed women’s breasts obscene and dangerous for children and it’s preposterous.” Facebook has said that it has no problem with breastfeeding, but that photos showing nipples are deemed to be a violation and can be removed. It has said that the photos flagged for removal were brought to the company’s attention almost exclusively by user complaints. As Facebook swells beyond 140 million members, regulating content on the site becomes more difficult. Barry Schnitt, a spokesman for the company, said banning nudity was a clear line to draw. “We think it’s a consistent policy,” said Mr. Schnitt. “Certainly we can agree that there is context where nudity is not obscene, but we are reviewing thousands of complaints a day. Whether it’s obscene, art or a natural act — we’d rather just leave it at nudity and draw the line there.” The pro-breastfeeding group has attracted more than 116,000 members. Mr. Schnitt noted that other protests around Facebook policies, such as when the company rolled out its News Feed feature, drew more support. Ms. Muir estimated that hundreds of photos showing women breastfeeding their children had been removed from the site. “The vast majority of the removed images were in people’s private profiles — you’d have to look for them to find them,” she said. “You can opt not to do that –- just as I choose to not check out the ‘Girls Gone Wild’ group. It’s not anyone’s responsibility but my own to make that decision.” Ms. Muir said she understood how hard it is for Facebook to deal with millions of photos and other user contributions. “But they need to be more discerning as to what they’re classifying as obscene,” she said. “It’s highly offensive to mothers and babies to be lumped in as true obscenity.” Mr. Schnitt said the company had no plans to change the policy. http://bits.blogs.nytimes.com/2009/0...cebook-photos/  “Crush” Porn and Free Speech Jill Let it be said that there are officially sexual fetishes that, should you engage in them, make you a really really bad person: crushing. (h/t). I’ve never heard of this before, but the New York Times describes it as follows: A decade ago, Congress decided it was time to address what a House report called “a very specific sexual fetish.” There are people, it turns out, who take pleasure from watching videos of small animals being crushed. “Much of the material featured women inflicting the torture with their bare feet or while wearing high-heeled shoes,” the report said. “In some video depictions, the woman’s voice can be heard talking to the animals in a kind of dominatrix patter. The cries and squeals of the animals, obviously in great pain, can also be heard in the videos.” Yes, folks, there are people out there who get off on women stomping puppies and kittens to death. I’m generally a live and let live kind of gal, and I don’t really care all that much what you do in your bedroom, but I’m willing to draw the line at stomping on small animals. More interesting, though — or at least more interesting to nerds like me, who find Constitutional law more compelling than stories about naked chicks crushing kitties — are the First Amendment issues caught up in Congress’s outlawing of “crushing” videos. See, “crushing” itself was already illegal in all 50 states, but it was nearly impossible to prosecute anyone for it, because the videos rarely showed the woman’s face and were difficult to trace. So Congress went a step further and in 1999 outlawed the depiction of crushing, and most depictions of cruelty to animals, making crush-porn illegal. Last month, the United States solicitor general asked the Supreme Court to hear the case. “Depictions of the intentional infliction of suffering on vulnerable creatures,” the brief said, “play no essential role in the expression of ideas.” The First Amendment, the brief went on, is therefore irrelevant to the case. Interestingly, most of the cases that have been brought under this law have depicted dog-fighting, not crush-porn. But crush porn essentially disappeared from the market after 1999; since a Third Circuit court ruled that the law banning animal cruelty videos is unconstitutional, the videos have sprung up again. To complicate things further, it doesn’t matter if the act was legal where it was filmed; the standard is that if the act of cruelty is illegal where the video is bought or sold, the law is being violated. So a video of bullfighting in Spain (or dog-fighting somewhere dog-fighting is legal) is illegal to sell in the United States. Basically, the “crush” law places depictions of animal cruelty in the same category that we place depictions of child pornography, where we say that depictions of the crime have absolutely no free speech value; or alternately, where the potential for harm is so great that it justifies this kind of reach. Amy Adler, who I had as a professor at NYU, has written about the exceptionalism of child pornography laws extensively, and I’d recommend checking out her stuff for a deeper understanding of the constitutional issues involved here. The other legal scholars who the reporter speaks to also seem to think that the law will be struck down. It will be interesting to see what this would mean for U.S. pornography law in general. Child pornography laws may be troubling to First Amendment absolutists (of which I usually consider myself one, or at least close), but most people seem pretty content to leave them be. Animal cruelty, though, is another issue. The question is where we draw the line when it comes to banning the sale of videos depicting certain crimes, and where First Amendment rights begin and end. Child pornography laws make sense to me for a lot of reasons, though I think the line gets much blurrier when we’re dealing with child porn that doesn’t involve “real” children. Free speech isn’t absolute, and banning child porn seems like a very basic limitation to set. Yes, there is always the “slippery slope” arguments, but as a society we can and do set limits — child porn is, in my opinion, limited fairly (though defining what is “pornographic” and “obscene” is always a challenge, even with child pornography). Those limits are being pushed in this animal cruelty case. The Court could say that the level of pure harm and lack of consent inherent to animal abuse videos are enough to warrant them utterly meritless. But the First Amendment doesn’t just protect speech that we like, and I suspect that this law will be found unconstitutional. That doesn’t mean that abusing animals will be legal, but it will mean that I could buy a video of that abuse if I wanted. Which is fucked, but fucked-up outcomes are unfortunately what you get when you have a free society populated by a lot of people — some percentage of them are going to be cruel people who enjoy watching horrible things. As a society, we can of course criminalize the horrible acts themselves; but criminalizing the depiction of those acts is another story. Of course, then again, we do outlaw depictions of child pornography. I’m actually mostly ignorant when it comes to the details of our laws on porn that depicts illegal and actually harmful acts — videos of actual sexual assaults, for example — but I’m guessing that most of it is illegal, since you can’t consent to being in that kind of pornography. Animals obviously can’t consent either, but “consent” isn’t a standard for the treatment of animals under the law. Animals can’t consent to being killed for food or kept as pets, but we legally do both things to them anyway. So I don’t think a consent model would fit here. Animal cruelty is illegal for good reason. Videos of animal cruelty are disgusting. And I desperately want to think of a reason why outlawing these videos should pass constitutional muster. But I can’t. I just hope that, regardless of the Supreme Court’s decision here, law enforcement starts cracking down on cruelty to animals — especially cruelty for profit, like dog-fighting. Of course, if Congress is really concerned with animal cruelty, they could also take a look at their local factory farming practices, which I’m pretty sure aren’t tidy and painless. But I won’t hold my breath. http://www.feministe.us/blog/archive...d-free-speech/  For BlackBerry, Obama’s Devotion Is Priceless Stephanie Clifford This week, Michael Phelps signed a deal worth more than $1 million to advertise Mazda in China. Jerry Seinfeld earned a reported $10 million to appear in Microsoft’s recent television campaign. But the person who may be the biggest celebrity pitchman in the world is not earning a penny for his work. President-elect Barack Obama has repeatedly said how much his BlackBerry means to him and how he is dreading the prospect of being forced to give it up, because of legal and security concerns, once he takes office. “I’m still clinging to my BlackBerry,” Mr. Obama said Wednesday in an interview with CNBC and The New York Times. “They’re going to pry it out of my hands.” What could the “BlackBerry president” charge for his plugs of the device if he were not a public servant? More than $25 million, marketing experts say, and maybe as much as $50 million. “This would be almost the biggest endorsement deal in the history of endorsements,” said Doug Shabelman, the president of Burns Entertainment, which arranges deals between celebrities and companies. “He’s consistently seen using it and consistently in the news arguing — and arguing with issues of national security and global welfare — how he absolutely needs this to function on a daily basis.” Mr. Obama is an ideal marketing representative, other agents say — popular, constantly in the news and explicit about his attachment to the product. “You always want the celebrity to be a good fit with your brand, and is anybody considered a better communicator right now than Barack Obama, or a better networker?” said Fran Kelly, the chief executive of the advertising agency Arnold Worldwide, who estimated that an endorsement by Mr. Obama would be worth $25 million. “It couldn’t have a better spokesperson.” Mr. Shabelman put the value even higher, at $50 million or more, because the endorsement is worldwide. “The worth to a company to have the president always talking about a BlackBerry and how it absolutely is a necessity to keep in touch with reality?” he said. “Think about how far the company has come if they’re able to say, ‘The president has to have this to keep in touch.’ ” The maker of the BlackBerry, Research in Motion, recently introduced advertising campaigns and products like the touch-screen Storm that are meant to position BlackBerry as not just a business device but a consumer product like the iPhone. The company, which declined to comment on Mr. Obama’s enthusiasm for its product, also struck a sponsorship deal with John Mayer, a popular guitarist but hardly the leader of the free world. “The most powerful man in the country is saying, at this moment, basically, I can’t live without mine,” Lori Sale, the head of artist marketing at the agency Paradigm, which pairs actors like Adrien Brody and Katherine Heigl with advertisers. “It represents their now complete and final crossover to a device that people adore.” Ms. Sale said that Mr. Obama had essentially participated in what is called a satellite media tour for BlackBerry by discussing the product with reporters. Just a single day of a media tour, “with the most A-list of A-list of A-list, would probably be 10 to 15 million dollars,” she said. That he is not paid to promote BlackBerry is even better for R.I.M. “What makes it even more valuable than that is how authentic it is,” she said. Mr. Kelly said the endorsement went both ways: while Mr. Obama was doing a lot for BlackBerry, BlackBerry had helped Mr. Obama’s image by making his message seem more relevant. “The BlackBerry anecdotes are a huge part of Obama’s brand reputation,” he said. “It positions him as one of us: he’s got friends and family and people to communicate with us, just like all of us. And it positions him as a next-generation politician.” Inevitably, perhaps, marketing executives dream about creating an ad featuring the president-elect, something Gene Liebel, a partner in the Brooklyn agency Huge, said would be a “fantasy assignment.” Asked what tagline he might use for the campaign, Mr. Liebel repeated one his employees had thought up: “If Blagojevich can pick my replacement, I can pick my device.” R. Vann Graves, the chief creative officer of the UniWorld Group, suggested a campaign showing Mr. Obama in the Oval Office. “In the foreground, you have the desk, but instead of having the proverbial red phone, you have a red BlackBerry,” Mr. Graves said, with the tagline “Shot Caller.” Matt Reinhard, the executive creative director of DDB Los Angeles, suggested Apple try to steal Mr. Obama away from BlackBerry as a spokesman for the iPhone. The message could be, “It’s time for change,” Mr. Reinhard said. http://www.nytimes.com/2009/01/09/bu...lackberry.html  Palm Unveils iPhone Competitor, the Pre Matt Richtel Seeking to revive its sharply fallen fortunes and produce a successor to its aging Treo device, Palm unveiled a sleek new smartphone, the Pre, on Thursday and an exclusive partnership with Sprint to distribute it. Palm executives say the touch-screen device and the new operating system inside it, WebOS, break new ground in the fiercely competitive smartphone market. The phone’s selling points include an emphasis on fast Web browsing and efficient multitasking. Jonathan J. Rubinstein, executive chairman of Palm, resisted comparisons of the Pre with the iPhone from Apple. “Our intention was never to build an iPhone killer but to build a killer Palm product,” Mr. Rubinstein said in an interview. He said he felt Palm had been fighting an uphill battle with outdated devices and software, and was doing so no longer. “The Pre allows us to get back in the game,” he said. Edward T. Colligan, president and chief executive of Palm, said at a press conference at the Consumer Electronics Show here that the Pre would be available in the first half of the year “as soon as possible.” The company did not disclose its price. Mr. Colligan showed off the phone’s sophisticated interface and the way it charges on a special platform without the need to attach a cable. The Pre comes with eight gigabytes of storage, GPS navigational capabilities, Wi-Fi networking and a slide-out keyboard. For Palm, the announcement is part of an effort to reboot a company whose Treo was once synonymous with smartphones, before competitors like the iPhone and BlackBerry surpassed it. It not only wants to catch up in the phone market, it wants to set a new bar. But it faces intense competition from companies that are vying for the same customers. Investors welcomed the Pre’s unveiling, sending Palm’s stock up $1.15, or 35 percent, to $4.45. The stock was near $14 two years ago. Roger Entner, a telecommunications industry analyst at Nielsen, said that while Palm had serious hurdles, his early impressions of the phone were positive. He said that if the Pre catches on, it could improve the outlook for Palm and also Sprint, which like Palm has been struggling to regain its former stature. “If this device does really well, it gives people a reason to go to Sprint,” Mr. Entner said. “It’s one of those potentially iconic devices. The Razr, the iPhone, devices like that made people switch carriers. That’s what Sprint is hoping for.” Daniel R. Hesse, the chief executive of Sprint, said at the press conference that Sprint had the most dependable high-speed data network, an apparent swipe at the problems iPhone users have had with AT&T’s network. Industry analysts have been skeptical of Palm’s ability to revive its reputation and market share. In the United States, phones that use the current Palm operating system make up about 14 percent of smartphones in use, putting Palm fourth behind the BlackBerry maker Research in Motion, Windows-based phones and the iPhone, according to the marketing research firm comScore. The company’s financial fortunes have soured too. In its second fiscal quarter, which ended Nov. 28, its sales of smartphones were $171 million, down 39 percent from a year ago. Excluding one-time charges, its quarterly losses soared to $80.2 million, up from $7.8 million the year earlier. Palm has not had much luck with its recent efforts to innovate. In 2007 it announced that it would build the Foleo, a kind of smartphone accessory in the form of a laptop, but it canceled the project within a few months. Analysts say Palm could have trouble getting outside software developers to create programs that will work on its WebOS phones. Developers are now heavily focused on BlackBerry devices and the iPhone because the number of people using them is large and growing. The developers have become more crucial to the success of mobile phones because they can enrich the devices by adding all kinds of functions like games and navigation services. “The essence of what is going to make or break a Palm platform is whether or not you can get developers committed to it,” said Ken Dulaney, a mobile computing analyst with Gartner, the information technology research company. Another challenge is economics. People are less likely to spend money to upgrade to a fancy new gadget if they are keeping an eye on their bank balance. Roger McNamee, a Palm board member and a major investor in the company, acknowledged that economic conditions were not ideal, but he added that he thought the size of the mobile phone market left plenty of room. “Given the economy, a perfect outcome would be a critically acclaimed start followed by something like the early days of the iPod, where every buyer loved the product, but unit volumes started small and grew with time,” Mr. McNamee said. “In the 1.2-billion-unit cellphone market, you don’t need much market share to generate billions in revenues.” Mr. McNamee is a founder of Elevation Partners, an investment firm that last year invested $325 million in Palm. This month it agreed to invest $50 million to $100 million more, which could bring its stake in Palm to as much as 40 percent. Mr. McNamee said he believed that the new Palm platform represented a fundamental improvement over that of the iPhone and BlackBerry. Because it emphasizes on-the-go browsing and multitasking, he said, it is better suited for a mobile device. “Apple’s Mac OS X is about eight years old, and the BlackBerry platform is more than a decade old,” he said. “Palm’s platform is brand new. A new platform gives us the opportunity to innovate the way Google does. This product is just the starting point.” http://www.nytimes.com/2009/01/09/te...ch/09palm.html  Data Analysts Captivated by Power of R Ashlee Vance To some people R is just the 18th letter of the alphabet. To others, it’s the rating on racy movies, a measure of an attic’s insulation or what pirates in movies say. R is also the name of a popular programming language used by a growing number of data analysts inside corporations and academia. It is becoming their lingua franca partly because data mining has entered a golden age, whether being used to set ad prices, find new drugs more quickly or fine-tune financial models. Companies as diverse as Google, Pfizer, Merck, Bank of America, the InterContinental Hotels Group and Shell use it. But R has also quickly found a following because statisticians, engineers and scientists without computer programming skills find it easy to use. “R is really important to the point that it’s hard to overvalue it,” said Daryl Pregibon, a research scientist at Google, which uses the software widely. “It allows statisticians to do very intricate and complicated analyses without knowing the blood and guts of computing systems.” It is also free. R is an open-source program, and its popularity reflects a shift in the type of software used inside corporations. Open-source software is free for anyone to use and modify. I.B.M., Hewlett-Packard and Dell make billions of dollars a year selling servers that run the open-source Linux operating system, which competes with Windows from Microsoft. Most Web sites are displayed using an open-source application called Apache, and companies increasingly rely on the open-source MySQL database to store their critical information. Many people view the end results of all this technology via the Firefox Web browser, also open-source software. R is similar to other programming languages, like C, Java and Perl, in that it helps people perform a wide variety of computing tasks by giving them access to various commands. For statisticians, however, R is particularly useful because it contains a number of built-in mechanisms for organizing data, running calculations on the information and creating graphical representations of data sets. Some people familiar with R describe it as a supercharged version of Microsoft’s Excel spreadsheet software that can help illuminate data trends more clearly than is possible by entering information into rows and columns. What makes R so useful — and helps explain its quick acceptance — is that statisticians, engineers and scientists can improve the software’s code or write variations for specific tasks. Packages written for R add advanced algorithms, colored and textured graphs and mining techniques to dig deeper into databases. Close to 1,600 different packages reside on just one of the many Web sites devoted to R, and the number of packages has grown exponentially. One package, called BiodiversityR, offers a graphical interface aimed at making calculations of environmental trends easier. Another package, called Emu, analyzes speech patterns, while GenABEL is used to study the human genome. The financial services community has demonstrated a particular affinity for R; dozens of packages exist for derivatives analysis alone. “The great beauty of R is that you can modify it to do all sorts of things,” said Hal Varian, chief economist at Google. “And you have a lot of prepackaged stuff that’s already available, so you’re standing on the shoulders of giants.” R first appeared in 1996, when the statistics professors Ross Ihaka and Robert Gentleman of the University of Auckland in New Zealand released the code as a free software package. According to them, the notion of devising something like R sprang up during a hallway conversation. They both wanted technology better suited for their statistics students, who needed to analyze data and produce graphical models of the information. Most comparable software had been designed by computer scientists and proved hard to use. Lacking deep computer science training, the professors considered their coding efforts more of an academic game than anything else. Nonetheless, starting in about 1991, they worked on R full time. “We were pretty much inseparable for five or six years,” Mr. Gentleman said. “One person would do the typing and one person would do the thinking.” Some statisticians who took an early look at the software considered it rough around the edges. But despite its shortcomings, R immediately gained a following with people who saw the possibilities in customizing the free software. John M. Chambers, a former Bell Labs researcher who is now a consulting professor of statistics at Stanford University, was an early champion. At Bell Labs, Mr. Chambers had helped develop S, another statistics software project, which was meant to give researchers of all stripes an accessible data analysis tool. It was, however, not an open-source project. The software failed to generate broad interest and ultimately the rights to S ended up in the hands of Tibco Software. Now R is surpassing what Mr. Chambers had imagined possible with S. “The diversity and excitement around what all of these people are doing is great,” Mr. Chambers said. While it is difficult to calculate exactly how many people use R, those most familiar with the software estimate that close to 250,000 people work with it regularly. The popularity of R at universities could threaten SAS Institute, the privately held business software company that specializes in data analysis software. SAS, with more than $2 billion in annual revenue, has been the preferred tool of scholars and corporate managers. “R has really become the second language for people coming out of grad school now, and there’s an amazing amount of code being written for it,” said Max Kuhn, associate director of nonclinical statistics at Pfizer. “You can look on the SAS message boards and see there is a proportional downturn in traffic.” SAS says it has noticed R’s rising popularity at universities, despite educational discounts on its own software, but it dismisses the technology as being of interest to a limited set of people working on very hard tasks. “I think it addresses a niche market for high-end data analysts that want free, readily available code," said Anne H. Milley, director of technology product marketing at SAS. She adds, “We have customers who build engines for aircraft. I am happy they are not using freeware when I get on a jet.” But while SAS plays down R’s corporate appeal, companies like Google and Pfizer say they use the software for just about anything they can. Google, for example, taps R for help understanding trends in ad pricing and for illuminating patterns in the search data it collects. Pfizer has created customized packages for R to let its scientists manipulate their own data during nonclinical drug studies rather than send the information off to a statistician. The co-creators of R express satisfaction that such companies profit from the fruits of their labor and that of hundreds of volunteers. Mr. Ihaka continues to teach statistics at the University of Auckland and wants to create more advanced software. Mr. Gentleman is applying R-based software, called Bioconductor, in work he is doing on computational biology at the Fred Hutchinson Cancer Research Center in Seattle. “R is a real demonstration of the power of collaboration, and I don’t think you could construct something like this any other way,” Mr. Ihaka said. “We could have chosen to be commercial, and we would have sold five copies of the software.” http://www.nytimes.com/2009/01/07/te...07program.html  Pupils Conquer Fear of Computers Ishwar Rauniyar The children were scared of computers at first Kamal Prasad Sharma, aged 12, a student at Saraswati Secondary School in a small village not far from Kathmandu, was afraid when he saw a computer for the first time. He didn't dare enter the room, thinking the computer would harm him. "I was really scared when I saw the computer," he says. "I didn't go near it. I was worried it might explode and kill me. "It was only when the teacher called me saying it was harmless that I went into the room, but I still hesitated." Things have changed now, he adds. Games and fun "I'm feeling much better. The E-library has helped with my studies. "We can see the periodic table of science, and also maps and other geography things in a pictorial way that is easy to understand. It's not only that - we can also play games and have fun." Kamal says his parents were very excited when he told them about the computer and came to watch the very next day. It was not only Kamal. His computer teacher, Shankar Prajapati, says all the pupils were afraid. "They all worried they would catch some virus and fall ill or even die. But now they are familiar with computers," he says. "Even we teachers are gaining knowledge from the E-library. It's really helpful for us, too. "The students can see science experiments carried out on screen and search for whatever they want in the encyclopaedia." E-libraries use audio, video and text technology. Their digital "books" cover various topics of the school syllabus, ranging from social science to literature and from mathematics to science. Computer awareness The E-library concept was initiated by Help Nepal Network (HeNN), a non-governmental organisation. Its goals are to provide literacy and awareness about the use of computer and information technology, and to set up one E-library in each of Nepal's 75 districts, which range from the high Himalayas to the hot plains. The Help Nepal Network hopes to reach all 75 districts in time Much of the country is remote and accessible only on foot, and many of its people have never glimpsed a computer, let alone touched one. Working with other organisations, including Save the Children-Norway, HeNN is setting up the libraries with the use of what is called the Linux Terminal Server Project (LTSP). This is a free and open-source (accessible to everyone) package which connects one powerful central server in the school, using the Linux operating system, to a number of diskless low-end computers. When linked to the server, each computer receives a full Linux desktop. LTSP is seen as a cost-effective, power-saving and durable technology, not only in schools but also in other sectors. What's more, it is also virtually free of tampering and computer viruses - and the Linux software developed by Madan Puraskar Pustakalaya, a charitable educational library based in Kathmandu, is being provided free of cost. And its appeal is growing. In front of the little shops on the rough village streets, men gather to play cards and drink tea. But even they have developed a fascination for the computer. So the school has arranged some computer classes for them, too. "It's really useful for us to get to know about this technology which we didn't see when we were younger," says Sahakul Puri, a 35-year-old farmer. "Getting to learn and know about it is a great opportunity for our children. I can't afford to send my child to computer classes an hour's drive from here. So we're grateful for this project." Of the books scanned in the E-library, one of the most popular among the villagers is called "where there is no doctor". It is like a first-aid manual, giving the information necessary for the treatment of wounds or illnesses – including traditional remedies such as chewing burnt ginger or brewing ginger soup with honey for a cough. The school has even attracted lots of villagers to its campaign known as "Leave Your Playing Cards - Learn Computers". Reaching remote areas I also visited a much more remote school where the E-library project has just been set up. Villagers and students carried the computers up and down the steep hills and valleys to the Shree Koldung Devi secondary school, nearly two hours' walk from the main road. Before this, anyone wanting access to computers or sizeable shops would have to walk two hours and drive two more, so the system has proved highly significant for local pupils. Most of the places where E-libraries have been set up so far are in the hills. Sudarshan Shrestha, information and marketing director for Save the Children-Norway, says the system has been very helpful but notes that there are challenges. He says students tend to get only about two hours' access per week "because there are not more than 10 computers for several hundred students". For the library, Save The Children-Norway has developed awareness materials on subjects such as children's rights and child abuses. Roshendra Dhoj Khadka of Help Nepal Network is very optimistic about the E-library project. "I believe this information and communication technology project is essential. It may not be a basic requirement, but it's a tool to uplift the health and education sectors. And we're taking it forward. I hope we'll be able to cover all 75 districts some day." So far it has reached six. http://news.bbc.co.uk/2/hi/uk_news/e...on/7684616.stm  How Newspapers Tried to Invent the Web But Failed. Jack Shafer A moment of sympathy, please, for newspapers, whose readers and advertisers have been fleeing at a frightening rate. It would be easy to accuse editors and publishers of being clueless about the coming Internet disruption and to insist that the industry's proper reward for decades of haughty attitude, bad planning, and incompetence is bankruptcy. But newspapers have really, really tried to wrap their hands around the future and preserve their franchise, an insight I owe to Pablo J. Boczkowski's 2004 book, Digitizing the News: Innovation in Online Newspapers. The industry has understood from the advent of AM radio in the 1920s that technology would eventually be its undoing and has always behaved accordingly. For instance, publishers aggressively pursued radio licenses in the early days of broadcasting and, later, sought and acquired TV licenses when they were dispensed. As early as 1947, Walter Annenberg's Philadelphia Inquirer and John S. Knight's Miami Herald experimented with fax editions of their papers. Seems visionary enough to me. Newspapers and other media entities started experimenting with videotex technology in the 1970s, according to David Carlson's Online Timeline. Newspapers considered themselves vulnerable to new entrants and worried aloud to anybody who would listen about falling readership. In 1979, the Knight Ridder newspaper chain established a videotex subsidiary to develop its Viewtron service, Boczkowski writes. Clunky and toylike by today's standards (see the silly, pre-Donkey Kong-quality graphics), the early system required an expensive, dedicated terminal. Yet after conducting trials in 1980, the system held sufficient promise that Knight Ridder succeeded in selling Viewtron franchises to other newspapers. More than a dozen other dailies played with videotex during the decade, including newspapers in the Times-Mirror chain, Cowles Media, and McClatchy Newspapers, as well as at the Chicago Sun-Times and the Washington Post. Howard Finberg of the Poynter Institute remembers that Viewtron could fetch from the "Miami Herald or the New York Times the night before the paper hit your doorstep," access the Associated Press, look up airline schedules, access bank account info, and order a meal online. Not bad for the dark ages, eh? Broadcasters joined the text fray, too. In Los Angeles during the early 1980s, CBS was testing the Extravision teletext service, and NBC was experimenting with its own offering, Tempo L.A., according to the New York Times. So intense was the industry's devotion to videotex and so rampant its paranoia that some other medium would usurp its place in the media constellation that the American Newspaper Publishers Association lobbied Congress in 1980 to prevent AT&T from launching its own "electronic yellow pages." Washington Post Co. CEO Katharine Graham, then chair of the ANPA, and other publishers met with Sen. Robert Packwood, R-Ore., to discuss the legislation that would free AT&T to start its service. As the Wall Street Journal would later report, Packwood said to the publishers, "What you're really worried about is an electronic Yellow Pages that will destroy your advertising base, isn't it?" Graham's response: "You're damn right it is." Videotext failed to catch on commercially, with Knight Ridder burning through $50 million before closing Viewtron in 1986. The industry's next favorite newsprint alternative was audiotext, and while Boczkowski writes that the format generated modest profits, it never enjoyed the wild enthusiasm that videotex did. As the decade progressed, the Chicago Tribune, Minneapolis Star Tribune, Hartford Courant, and the New York Times revisited the idea of fax newspapers. Some of the fax editions found a niche but not much more. According to Boczkowski, newspapers didn't rush into videotex because they were visionaries in a hurry to invent the future but because they were "reactive, defensive, and pragmatic" about their mature, lucrative business. Having observed the videotex experiments in England and elsewhere, they feared that if they didn't adopt the technology or at least test it, somebody else would and displace them. Once they determined that nobody could make money from videotex and the technology posed no threat to the newsprint model, they were happy to shutter their ventures. By the mid-1980s, the industry's biggest worry was that the PC, which had eased its way into homes and the workplace like an algae bloom, would somehow supplant them. Boczkowski acknowledges that newspapers' early online strategies were as much about blocking new competitors as beating a path to the future. That said, by the early to mid-1990s, the New York Times, the San Jose Mercury News, the Chicago Tribune, the Washington Post, the Los Angeles Times, and many others were producing electronic-edition business, striking deals with the burgeoning proprietary online systems, such as CompuServe, America Online, Prodigy, and Interchange, or throwing content up on bulletin board systems. Publishers adored the proprietary online services because they locked down the user experience to the newspaper's benefit. A Washington Post spokesman quoted in Boczkowski's book applauds the way Interchange "preserves the company's direct business relationship with Post readers." The publishers were pretty sure that proprietary online services were the next wave, but if you remember having used one, you know how badly they sucked. Let's say you subscribed to AOL to read the New York Times but wanted to read a story in the Washington Post. You couldn't get to the Post from AOL because the Post was published exclusively on Interchange. What you had to do was disconnect your screeching modem from AOL, purchase an Interchange subscription, log onto Interchange, and then navigate to the Post. A return visit to the Times required the reverse of that drill. The extreme suckage of proprietary online services stemmed from the fact that they were "non-generative" technologies, to borrow a phrase from Jonathan Zittrain's excellent The Future of the Internet—And How To Stop It. Nongenerative technologies can't be tinkered with or otherwise improved by outsiders. The iPhone is a good example of a nongenerative device: Its software updates "actively seek out and erase" unauthorized modifications, to paraphrase Zittrain. Generative technologies such as the PC, on the other hand, invite improvement by outsiders, making them more and more useful to users as time passes—and often more useful in ways that the original designers never would have imagined. When you connect a generative technology to a nongenerative one, you usually end up crippling the generative one. Indeed, the proprietary online services—the AOLs and CompuServes—hobbled the PC, turning the versatile and powerful machine into a dumb terminal. It's a tribute to newspapers and their keen sense of the future that they quickly determined that the online services would never attract the masses they desired. No sooner had newspapers taken up residence on the proprietary online services than they were packing up their pixels and starting their en masse migration to the World Wide Web, which was as generative as the online services were nongenerative. Newspapers were anything but late arrivers to the Web party, according to Carlson's Online Timeline and other sources. Among the earliest pure Web newspapers in the United States were the two dueling dailies started in San Francisco during the autumn 1994 press strike—one by union members and one by management. (As a point of reference, the high-tech sharpies at Wired spun off the Hotwired.com site in October 1994.) The San Jose Mercury News broke from AOL and started on the Web in February 1995. USA Today launched a Web edition in August 1995. Later that year, the Boston Globe started its Boston.com, and the Los Angeles Times announced plans to leave Prodigy. The New York Times and Washington Post got webby in 1996. After that, few newspapers held back. Boczkowski writes that more than 750 North American dailies were publishing on the Web in April 1998, and by July 1999 only two of the 100 largest dailies were not. Newspapers deserve bragging rights for having homesteaded the Web long before most government agencies and major corporations knew what a URL was. Given the industry's early tenancy, deep pockets, and history of paranoid experimentation with new communication forms, one would expect to find plenty in the way of innovations and spinoffs. But that's not the case, and I think I know why: From the beginning, newspapers sought to invent the Web in their own image by repurposing the copy, values, and temperament found in their ink-and-paper editions. Despite being early arrivals, despite having spent millions on manpower and hardware, despite all the animations, links, videos, databases, and other software tricks found on their sites, every newspaper Web site is instantly identifiable as a newspaper Web site. By succeeding, they failed to invent the Web. http://www.slate.com/id/2207912 Until next week, - js.  Current Week In Review  Recent WiRs - January 3rd, December 27th, December 20th, December 13th Jack Spratts' Week In Review is published every Friday. Submit letters, articles, press releases, comments, questions etc. in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|||||
|
|

|
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - September 22nd, '07 | JackSpratts | Peer to Peer | 3 | 22-09-07 06:41 PM |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |