
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 | |
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Since 2002
  "I have two kids in private school, man, Fox is hitting me where it hurts. I’m always going to have a creative outlet here, but jeez, don’t take my money away." – Danny Smith "It's puzzling that the [Rock and Roll] Hall [of Fame] has sided with RIAA in the performance tax fight, given the record labels' historic abuse of artists and the fact that the labels would pocket 50 percent of the proceeds from a devastating new fee on radio stations. The reality is that free radio airplay helped turn rock and roll into the cultural phenomenon that it is today." – Dennis Wharton "Some of those photos are 10 years old. People hide behind trees. They put up photos of their dog, and they don’t have a dog." – Rachel DeAlto "Frankly, I think we’re having tremendous success at a number of levels. We file new complaints every day." – Steve Gibson When You Absolutely, Positively Have to Read It Fast I often find myself in situations where I have to plow through online content quickly. I can do it but the mind wanders, and speed suffers. I discovered this helpful app and thought I'd pass it along. It’s called Spreeder and it enhances my focus by breaking down entire articles into single words, enlarging and then flashing them individually at speeds ranging from 300 to 600 WPM. I can easily double my comprehension speed, at least for a while. If you’d like to try it simply copy the text from the site you’re reading, paste it into the Spreeder box and hit play. Spreeder does the rest. Just remember to fasten your seatbelt. Shakespeare might’ve protested back in the day, but it's perfect for the times. Indeed, Amazon reports this week its e-books are outselling hardcovers nearly 2-1. Maybe they’re just that much faster to read. Enjoy, Jack July 24th, 2010  World’s First Pirate ISP Launches In Sweden enigmax The Swedish Pirate Party, who are at the forefront of anti-copyright lobbying in Sweden, are planning to shake up the country’s ISP market. After taking over the supply of bandwidth to The Pirate Bay, Piratpartiet will now partner in the launch of Pirate ISP, a new broadband service that will offer anonymity to customers and provide financial support to the Party. To defend the rights of BitTorrent users worldwide, the Swedish Pirate Party volunteered to provide bandwidth to The Pirate Bay after previous hosts got into legal trouble in May. At the beginning of July, the Pirate Party surprised again. Not only would they be The Pirate Bay’s new host, but they would use Parliamentary immunity to run the site from inside the Swedish Parliament. Now the Party have made another interesting announcement. Together with technology partners, they will enter the broadband market with Pirate ISP, a new service designed to deliver consumer Internet in line with the Pirate Party’s ideals. Gustav Nipe, student of economics, long-standing Pirate Party member and CEO of Pirate ISP told TorrentFreak that Pirate ISP is based on the hacker ontology. “If you see something and you think it’s broken you build a patch and fix it. With that as a reference point we are launching an ISP. This is one way to tackle the big brother society.” “The Pirate ISP is needed in different ways. One is to compete with other ISPs, let them fight more for our internet. If they don’t behave there will always be someone else taking their share,” Nipe added. Aside from the competition angle, Gustav Nipe told TorrentFreak that the Pirate ISP will maximize privacy for all its customers. Operated by ViaEuropa – the company behind the iPredator anonymity service – Pirate ISP users will remain anonymous. The service began beta testing in the city of Lund yesterday with around 100 residents of LKF, a housing organization whose aim is to provide quality accommodations at a reasonable cost. After the first two weeks of testing, the initial expansion aim is to take 5% of the market in Lund and then set up in further locations around Sweden. This is a reasonable aim according to Nipe, who told TorrentFreak that they start small so they can assure quality service to all their customers. At the Hacknight conference in Malmö yesterday, Nipe further said that they will not allow the Swedish Government to monitor Pirate ISP users and will refuse to retain logs. He warned that any attempt to force it to do otherwise will result in a constitutional issue. Nipe was also clear on how Pirate ISP would respond to outside interference, in particular that from the United States. “They can bring on whatever they have, we will refuse to follow there. We don’t agree with what they are saying and we don’t agree with the laws they are making so if they have an issue with us, then we will have an issue – but that’s it.” For most potential Pirate ISP customers who intend to use the service to file-share, the immediate threats will come from closer to home, primarily from Henrik Pontén at Svenska Antipiratbyrån, the Swedish Anti-Piracy Bureau. Nipe said they are prepared to deal with this challenge. “It would be a pity to reveal all the tricks that we have, so we will save those for later. But we have ways to ensure that no customer should have to get a sad letter home from Henrik Pontén.” For his part, yesterday Pontén seemed unimpressed. “Our investigations have focused on people with much higher safety. The question has been asked a thousand times before,” he said. “When the police come calling, they must disclose the information.” It seems that the wider Swedish public won’t have long to wait to discover if Pirate ISP can live up to its promises. According to Nipe they will roll out big in Sweden at the end of this summer. http://torrentfreak.com/worlds-first...sweden-100720/  Attention Movie Pirates: New Round of Lawsuits Coming Eriq Gardner Get ready for the second phase of a litigation campaign against thousands of individuals accused of pirating "The Hurt Locker" and other films. The U.S. Copyright Group, which is representing a handful of independent film production companies, has signed up 15 law firms across the continental U.S. to act as local counsel and begin filing individual lawsuits against those alleged file-sharers who refused to settle. Beginning the first week of August, expect an explosion of lawsuits around the nation. Meanwhile, there's other news in this litigation campaign. Two weeks ago, a federal judge ordered the U.S. Copyright Group to cooperate with the EFF, ACLU, Public Citizen and others in drafting a notice that would be sent out to those flagged for alleged copyright infringement in these cases, explaining their legal rights. Hardly surprising that the parties aren't seeing eye-to-eye so far. The amici groups have gone back to the judge now, hoping to compel the plaintiffs into adopting their suggestions about what the alleged pirates should see in the notices. The amici groups have submitted a memorandum to the court expressing concerns that the proposed notice contains legal terms and phrases such as "motion to quash" that will go over the head of those without legal training. Additionally, they want the notice to explicitly mention grounds for opposition, including joinder issues and the First Amendment. The amici groups want the plaintiffs to maintain a website that will contain copies of principal case documents, such as a motion for early discovery and motions to quash. They point to precedents such as the site set up in the Google Books case that informed class members about their rights and options in the aftermath of a settlement. Of course, this isn't a class action per se, and we're not aware of any plaintiff that has had to maintain a website before trial and without a settlement. But a case where thousands of "John Does" are being sued for copyright infringement has been treading new ground from the get-go. Regardless of the judge's decision on the proposed notice, new lawsuits will be filed soon. By subpoenaing the records of ISPs, a fair number of the targeted "John Does" have already been identified, especially in some of the early cases involving such films as "Far Cry," "Steam Experiment," "Uncross the Stars" and "Call of the Wild 3D." We'll have more big news on this litigation campaign soon. http://thresq.hollywoodreporter.com/...cy-update.html  France’s Three-Strikes Law for Internet Piracy Hasn’t Brought Any Penalties Eric Pfanner In the World Cup final between Spain and the Netherlands, the referee, Howard Webb, handed out a record 14 yellow cards. Nonetheless, the game turned nasty, as the players apparently concluded that Mr. Webb was all bark and no bite. Is something similar happening in the French government’s high-profile battle against digital piracy of music, movies and other media content? Nearly three years ago President Nicolas Sarkozy proposed what was to have been the world’s toughest crackdown on illegal file-sharing. After two years of political, judicial and regulatory setbacks, the legislation was approved last September, authorizing the suspension of Internet access to pirates who ignored two warnings to quit. Early this year, the government set up an agency to implement the law. Since then, not a single warning has been sent out; not a single broadband connection has been cut. At a news conference in June, the president of the agency, Marie-Françoise Marais, said it was “technically and legally ready” to take action. The first warnings would be sent out “before long,” she added. But she did not give a date, and news reports have shown growing unease about the legislation. Even some lawmakers in Mr. Sarkozy’s party have expressed doubts. Jean-Claude Larue, the head of a trade group representing video game publishers, questioned the cost of tracking pirated works, after officials of the new agency said they planned to pursue only the most prolific pirates, rather than all violators. He told the magazine L’Express that monitoring 100 games would cost more than €400,000, or $517,000, a year. “That’s a lot, and we want to be sure that Hadopi will deal with all the cases,” he said, referring to the French acronym for the new agency. Meanwhile, Jean-François Copé, leader in the National Assembly of Mr. Sarkozy’s party, the Union for a Popular Movement, or U.M.P., recently said he saw “weaknesses” in the three-strikes law, adding that his position on the issue of piracy had “evolved” since the vote, according to the newspaper Le Figaro. Mr. Copé was speaking during a meeting to introduce a U.M.P. digital policy paper that appeared to challenge the rationale for the three-strikes approach. It states, “Illegal downloading will be marginalized not by restrictive legislation but by technological progress and changing patterns of usage.” Digital music is indeed changing, both on the legal and illegal sides, as Internet users wake up to the convenience of cloud-based services offering on-demand listening, rather than the bother of downloading and storing music in their own computers or MP3 players. As consumer preferences and technology change, some people in the music industry are proposing new ways to deal with piracy. For example, PRS for Music, a royalty collection agency in Britain, proposed a levy on Internet service providers, based on the amount of pirated music that passes through their networks. The British government also recently approved legislation for a three-strikes approach. But, as in France, the measure has yet to be implemented. The French government seems unlikely to scrap the system, given the amount of political energy that has been expended. Some rights holders , are keeping the faith. “This is a complex law and it needs time to clear every step of the implementation process,” said Marc Guez, general manager of an agency that collects licensing fees on behalf of record labels. “Obviously, we would have been pleased if some steps were reached sooner than they were, but the major steps now have been reached.” Meanwhile, piracy persists. According to at least one study, by the University of Rennes, unauthorized sharing of content on the Internet has actually increased in France since the legislation was passed. That could change if and when the written warnings actually go out. Unless those warnings are actually followed up with action, however, they might be about as effective as Mr. Webb’s yellow cards. http://www.nytimes.com/2010/07/19/te...iht-CACHE.html  File-Sharers: Expect a Mountain of Mail Rory Cellan-Jones Thought the Digital Economy Act, with its controversial measures aimed at deterring illegal file-sharing, had gone away? Well it hasn't, and the big Internet Service Providers (ISP) who see themselves as the main victims of the act are determined to make sure we know about its potential impact. They are engaged in discussions with Ofcom about how the law will be implemented, and two of the biggest ISPs tell me that the assumptions being made by the regulator will startle consumers. They say Ofcom is expecting that the volume of letters that the big providers will have to send out to customers on behalf of media businesses who think their rights have been infringed will be enormous - hundreds of thousands a month, perhaps three or four million over the space of a couple of years. "It's a monster thing to do, to write to hundreds of thousands of people," said a senior executive at one ISP. "Some will move to another network, there might be thousands of appeals." He says the customers will be told they have to take "reasonable steps" to avoid infringing copyright in the future but it's not clear what is reasonable. "Will they have to secure their wireless networks, or sit over their children's shoulders making sure they're not being naughty, or perhaps stop using perfectly legal peer-to-peer services like Spotify? It's a dog's breakfast." Now Ofcom is playing down its rough estimate of the number of warning letters that will be despatched. A spokeswoman suggested it was a back of the envelope calculation, and the point of talking to the ISPs was to get a more accurate idea. But when I turned to the record industry which lobbied so hard to get this act through there was little surprise about the figures. Apparently last year alone the industry trade body the British Phonographic Institute (BPI) sent evidence it had gathered of more than a million cases of music copyright infringement to ISPs - with no result, it adds. It believes there are six to seven million illegal file-sharers in the UK - a figure which the ISPs seem to accept so it's not surprising that a large amount of paperwork will be involved. And, as the music industry points out, long before the act was even thought of, consumers were receiving letters accusing them of illegal file-sharing - letters that have often been far more threatening than those that could be sent next year. In the last week, a firm of solicitors called Gallant Macmillan has sent out thousands of letters on behalf of the Ministry of Sound record label. I've seen one which accuses the recipient of illegally making available an album and inviting them to pay £350 or face court proceedings for infringing the rights of the label. It's a tactic from which the BPI has dissociated itself in the past, and the trade body now says it believes the Digital Economy Act, with its three warning letters giving householders the opportunity to stop any illegal file-sharing, is a better way for content owners to protect their rights. If the ISPs have their way, it will be a long time before the Act begins to bite. BT and TalkTalk say their lawyers tell them they have a good chance of getting it blocked if the judicial review they are seeking goes ahead. The battle over this controversial law is far from over. http://www.bbc.co.uk/blogs/thereport..._mountain.html  Court Bans The Pirate Bay From The Netherlands Ernesto In a full trial the Amsterdam Court has confirmed an earlier judgment and ordered The Pirate Bay to stop all their activities in The Netherlands. The Court ruled that the site’s operators were assisting copyright infringement. If the three ‘operators’ fail to ban Dutch users, they will have to pay penalties of 50,000 euros per day. In an attempt to ensure that Dutch citizens can’t access The Pirate Bay, Dutch anti-piracy outfit BREIN took three of the tracker’s founders to court last summer. The anti-piracy group won the case and Fredrik Neij, Gottfrid Svartholm and Peter Sunde were ordered to block Dutch users, a decision they decided to appeal. In the verdict of the initial appeal, the Court ruled that The Pirate Bay had to remove a list of torrents linking to copyrighted works and make their website inaccessible to Dutch visitors. This ruling was confirmed yesterday in a full trial by the Amsterdam Court. The judge ruled that The Pirate Bay itself is not necessarily guilty of copyright infringement. However, according to the Court, the site’s operators assist in copyright infringement by allowing and encouraging its users to share torrents. Previously, the defendants had argued that they were not the owners of the site, but a Seychelles-based company named Reservella. The Court rejected this defense as the defendants could not name the current owners or provide any documents proving that the site was sold. It concluded that the three defendants are responsible for the site. In an appeal of one of the earlier cases against BREIN the defendants hired a lawyer to represent them, but in the full trial the defendants did not show up or defend themselves. The Amsterdam Court ruled that Fredrik, Gottfrid and Peter will now have to pay penalties of 50,000 euros per day if they don’t comply. However, based on their previous inaction and the claims that they are no longer responsible for The Pirate Bay, it is unlikely that Dutch users will be cut off. The worrying thing for other BitTorrent site owners is that BREIN might use this case as a precedent in an attempt to get other big torrent sites offline. If that’s the case, the effects of the current judgement might be more severe that they appear at the moment. In the meantime, BREIN has been anticipating and making the best of The Pirate Bay’s lack of response by starting a lawsuit against Dutch ISP Ziggo, demanding it blocks user access to The Pirate Bay website. http://torrentfreak.com/court-bans-t...rlands-100717/  Man Arrested for BitTorrent File Sharing in Japan Joshua Williams A 31-year old unemployed man was arrested by police in Japan on July 20th for illegal transmission of TV programs over the controversial file sharing software BitTorrent. According to Japanese news reports, under the support of the Metropolitan Police Department’s cyber crime division, investigators arrested Shuichiro Tanaka in Saitama Prefecture, north of Tokyo, on suspicion of uploading and sharing TV shows. Police indicated that from June 4th to June 9th, Tanaka is believed to have recorded three programs on his computer, and then to have shared them via BitTorrent to an unspecified number of users. In addition, between mid-February and July of this year, the suspect is believed to have shared approximately 165 shows, largely Japanese variety programs such as “Waratte Iitomo” and “Genius! Shimura Zoo.” Tanaka told investigators, “I did it for people who missed the programs. Because there is a potential for viruses on Winny [another popular Japanese peer-to-peer file sharing program] and others, I used BitTorrent, which I heard police weren’t investigating,” according to a report from the Mainichi. Police added that the arrest was a first for Japan relating to BitTorrent use. http://www.examiner.com/x-16352-Japa...aring-in-Japan  U.S. Targeting China in New Anti-Piracy Drive The United States will make China "a significant focus" of its beefed-up efforts to fight global piracy and counterfeiting of U.S. goods ranging from CDs to manufactured products, a U.S. official said on Wednesday. A customs officer displays a counterfeit branded mobile phone at a rubbish dump site in Kunming A customs officer displays a counterfeit branded mobile phone at a rubbish dump site in Kunming, Yunnan province April 26, 2010. "It's fair to say China raises a particularly troubling set of issues," Victoria Espinel, the U.S. intellectual property enforcement coordinator, said in prepared testimony to the House of Representatives Foreign Affairs Committee. "Therefore, China will be a significant focus of our enforcement efforts as we address intellectual property infringement abroad," Espinel said testifying on the Obama administration's new intellectual property enforcement strategy, which was mandated by Congress. The International Intellectual Property Alliance, which represents U.S. copyright industry groups, has estimated lost sales in China at more than $3.5 billion in 2009 due to piracy of U.S. music, movies and software. U.S. manufacturers also complain that China's counterfeiters rip off their goods and sell them in markets around the world, including the United States. "Whether it's coordinating our law enforcement personnel overseas, developing a strategy to go after foreign-based websites or using policy tools to address the competitive disadvantages that we face, China will be a priority," Espinel said. (Reporting by Doug Palmer; Editing by Doina Chiacu) http://www.ibtimes.com/articles/3722...racy-drive.htm  Lawsuit Saying Scribd's Copyright-Protection Filters Infringe On Copyrights Has Been Dumped from the good-work dept Last year, we wrote about the somewhat bizarre class action lawsuit filed against Scribd for copyright infringement. It was bizarre on multiple levels. First, the lawyers filing the lawsuit against Scribd were the same lawyers, Joe Sibley and Kiwi Camara, who had famously defended Jammie Thomas against copyright infringement claims. It seemed odd for them to flip to the other side. But, their actual case was even more ridiculous. It made blatantly false claims, such as that Scribd (and other "West Coast technology" firms") believed that "commercial copyright infringement is not illegal." Uh, yeah. But then it got even more bizarre. Despite claiming that Scribd didn't care about copyright infringement, the crux of the case was that its copyright filters infringed. Yes, part of the claim was that because Scribd uses a copy of the text within its filters, it's that copy that's illegal. Got that straight? The company is damned if they do and damned if they don't. If they don't filter, they're blamed for ignoring infringement. If they do filter, they're accused of infringing copyrights with the filter. Either way, that case has now been dropped, officially due to a "settlement." However, the details provided suggest this was no real settlement. Scribd, in a statement, notes that Camara and Sibley not only failed to meet the basic deadlines related to the lawsuit, but they effectively walked away from this case: Quote:
http://techdirt.com/articles/20100719/12105310280.shtml  Newspaper Chain’s New Business Plan: Copyright Suits David Kravets Steve Gibson has a plan to save the media world’s financial crisis — and it’s not the iPad. Borrowing a page from patent trolls, the CEO of fledgling Las Vegas-based Righthaven has begun buying out the copyrights to newspaper content for the sole purpose of suing blogs and websites that re-post those articles without permission. And he says he’s making money. “We believe it’s the best solution out there,” Gibson says. “Media companies’ assets are very much their copyrights. These companies need to understand and appreciate that those assets have value more than merely the present advertising revenues.” Righthaven CEO Steve Gibson is embarking on a copyright trolling litigation campaign Gibson’s vision is to monetize news content on the backend, by scouring the internet for infringing copies of his client’s articles, then suing and relying on the harsh penalties in the Copyright Act — up to $150,000 for a single infringement — to compel quick settlements. Since Righthaven’s formation in March, the company has filed at least 80 federal lawsuits against website operators and individual bloggers who’ve re-posted articles from the Las Vegas Review-Journal, his first client. Now he’s talking expansion. The Review-Journal’s publisher, Stephens Media in Las Vegas, runs over 70 other newspapers in nine states, and Gibson says he already has an agreement to expand his practice to cover those properties. (Stephens Media declined comment, and referred inquiries to Gibson.) Hundreds of lawsuits, he says, are already in the works by year’s end. “We perceive there to be millions, if not billions, of infringements out there,” he says. Righthaven’s lawsuits come on the heels of similar campaigns targeting music and movie infringers. The Recording Industry Association of America sued about 20,000 thousand file sharers over five years, before recently winding down its campaign. And a coalition of independent film producers called the U.S. Copyright Group was formed this year, already unleashing as many as 20,000 federal lawsuits against BitTorrent users accused of unlawfully sharing movies. The RIAA’s lawsuits weren’t a money maker, though — the record labels spent $64 million in legal costs, and recovered only $1.3 million in damages and settlements. The independent film producers say they nonetheless expect to turn a profit from their lawsuits. “People are settling with us,” says Thomas Dunlap, the head lawyer of the Copyright Group’s litigation. The out-of-court settlements, the number of which he declined to divulge, are ranging in value from $1,500 to $3,500 — about the price it would cost defendants to retain a lawyer. The RIAA’s settlements, which it collected in nearly every case, were for roughly the same amounts. But experts say that settling the Righthaven cases, many of which target bloggers or aggregation sites, might not be as easy. The RIAA lawsuits often accused peer-to-peer users of sharing dozens of music files, meaning the risk of going to trial was financially huge for the defendants. The same is true of the BitTorrent lawsuits. The movie file sharers are accused of leeching and seeding bits of movie files, contributing to the widespread and unauthorized distribution of independent movies such as Hurt Locker, Cry of the Wolf and others. But each of the Righthaven suits charge one, or a handful, of infringements. Defendants might be less willing to settle a lawsuit stemming from their posting of a single news article, despite the Copyright Act’s whopping damages. “You’d have to go after a lot of people for a relatively small amount of money,” says Jonathan Band, a Washington, D.C. copyright lawyer. “That is a riskier proposition.” Gibson claims Righthaven has already settled several lawsuits, the bulk of which are being chronicled by the Las Vegas Sun, for undisclosed sums. One defendant who is ready to settle is Fred Bouzek, a Virginia man who runs bikernews.net, a user-generated site about hardcore biker news. He was sued last week on allegations the site ran a Las Vegas Review-Journal story about police going under cover with the Hell’s Angels. Even if he had grounds to fight the case, he says it would be cheaper to settle. “The only choice I have is to try to raise money and offer a settlement,” he says. Bill Irvine of Phoenix says he is fighting infringement allegations targeting AboveTopSecret.com, the site he controls under The Above Network. The site is accused of infringing a Review-Journal article on the Gulf of Mexico oil spill. The site is a user-generated discussion on “conspiracies, UFO’s, paranormal, secret societies, political scandals, new world order, terrorism, and dozens of related topics” and gets about 5 million hits monthly, Irvine says. Righthaven, he says, should have sent him a takedown notice under the Digital Millennium Copyright Act, because the article was posted by a user, not the site itself. “In this case, we feel this suit does not have merit,” he says. “We are confident we will have success challenging it.” Gibson says he’s just getting started. Righthaven has other media clients that he won’t name until the lawsuits start rolling out, he says. “Frankly, I think we’re having tremendous success at a number of levels,” Gibson says. “We file new complaints every day.” http://www.wired.com/threatlevel/201...g-for-dollars/  A World Without Intellectual Property There are many good reasons to completely repeal patents and copyright laws: they are too complex to be understood or obeyed by anybody except a highly trained Intellectual Property (IP) attorney, they are often used for predatory purposes, they impede innovation since a patented invention cannot be improved by a third party. Additionally, because one firm holds a monopoly on the patented product, competition diminishes bringing with it the high prices and low quality of all monopoly services. Intellectual property is also very expensive to enforce since it requires surveillance and enforcement on millions of consumers. Nevertheless, some continue to support IP rights under the following mantras: * Authors of IP should be paid for their work * IP supports investment and innovation in R&D departments * An industry with no IP would lose productivity This article attempts to answer those and other objections. The Fashion Industry If we removed IP law from the fashion industry, what would be the effect on this industry, which thrives on creativity and new design. Would innovation and creativity cease? Would companies like WalMart copy fashions the second they were created and undercut the brilliant producers behind the scenes? Would the market stagnate? The answer is "No" for a very simple reason. The fashion industry is not covered under the blanket protection that IP law provides so many other industries. The creativity and variety that are the hallmark of this industry are the results of natural market evolution, without any IP protection. WalMart already does copy the designs straight from the runway. Advertising Revenue The elimination of IP law would have a dramatic effect on advertising revenue. While it could be argued that many companies would continue to receive such funding, some will not. In the event that every television show, every song and every book were made public domain, then there would be two options for funding the distribution. First, there are the traditional channels. This would use your viewing time to pay for the service of hosting and delivering the content. The authors of such content would not necessarily be paid from these funds, but it may be sufficient to run a bunch of servers producing on demand content. Second, fee for use hosting and peer based sharing could serve as the distribution mechanism. It would be hard to deliver a service that interrupted the show every fifteen minutes to advertise when the same content could be gotten elsewhere without the annoyance. This may cripple or even destroy many firms which fund their operations from advertising revenue. The Electronic Accreditation Technique Under this paradigm, all media would be stamped with a unique signiture that maps back to the authoring group or individual author. Tools could be cheaply created that allow you to donate directly to any producers you like. Like DRM, this stamp would be unique and tamper proof. Unlike DRM, it would not encrypt the media in any way. This would require very simple integration with media playing software and can be set up to donate 5/10/25 cents to anything you rate highly enough... at your choosing. Accreditation can be used alongside copyright or as a replacement. This type of producer compensation is made possible by current technology and may provide a suitable producer targetted replacement for the business friendly copyright laws. Books & Newspapers Imagine you run a major book publisher. You publish a book, but then --whoops-- somebody clear across the country (or across the world) starts printing the same work. Because you don't have exclusive control over your content, you cannot pay your authors. Major newspapers, on the other hand, produce new content on a daily (or weekly) basis, print millions of copies, and have them on their customers' doorsteps before anybody else has a chance to copy their work. Because of this, they don't need a government-enforced monopoly on their content. In centuries past, authors used to have their books published one chapter at a time in major periodicals. Readers had to purchase multiple issues to read the entire book. In a world without copyright laws, authors would probably follow a similar protocol. Then, after the last chapter has been published, other printers could copy the author's work and distribute it far and wide. Authors have two main interests: to be paid for their writing services work, and to have their work widely read and enjoyed so as to make a name for themselves. Those two interests sometimes run contrary to each other. However, the system discribed above, works for everybody. Authors can get paid by the newspapers. The newspapers make a profit by selling multiple, successive issues. Printing companies can "free ride" by printing the book without paying royalties. Authors are promoted by having their works published by multiple firms. Consumers get the best deal of all: they can read a few chapters in the newspaper, then purchase the entire book at a competitive price. Movies Movie makers receive most of their revenues from motion-picture theatres, not DVD sales. Motion-picture theatres, unlike DVDs, are at low risk of piracy. Therefore, movie piracy is not nearly as harmful to the movie industry as they would have you to believe. Broadcasting Broadcasters are funded by advertising revenues, not by selling content. Hence, broadcasting would continue as usual without IP laws. Music Musicians could still get paid, even without copyright. They would still be able to sell concert tickets, even if they did not make a thin dime from CDs and MP3 downloads. In fact, file-sharing might actually make them more famous! They could then cash in on their new-found fame in other ways (increased ticket sales, T-shirts and promotional items, product endorsements, movie deals...) Of course, people would still buy CDs, even with unrestricted file sharing networks in place. If you hear a CD being played in a store, and you like it, what are you going to do: * Spend a few dollars, get a dozen good songs in your possession, or * Spend the next four hours on the Web trying to find those songs performed by some obscure local artists. The answer is obvious. Inventions When Thomas Edison (or, more accurately, Edison's company) invented the light bulb, he was three steps ahead of anybody who would try to manufacture light bulbs of their own. He had the technical know-how, he had the necessary equipment to manufacture light bulbs, and his name was known in every household. Because of these three major advantages, he did not need a legal monopoly on light bulbs to get a return on his investment. He must, however, remain three steps ahead of the competition. Let's invent a a parallel universe, however, where Edison invents the light bulb, and then does not bother in any way to improve it or reduce the cost of manufacturing it. After several years, a rival inventor reverse-engineers the light bulb and build his own on his garage. He then discovers a way to manufacture the light bulb for cheaper than Edison's. He would quickly capture Edison's market share. In the absence of patents, Edison's laziness is punished and his rival's ingenuity is rewarded. This happened with the invention of the steam engine. James Watt made important improvements and secured a patent for them, but then blocked many further improvements, which could be applied only when his patent expired. "During the period of Watt's patents the United Kingdom added about 750 horsepower of steam engines per year. In the thirty years following Watt's patents, additional horsepower was added at a rate of more than 4,000 per year. Moreover, the fuel efficiency of steam engines changed little during the period of Watt's patent; while between 1810 and 1835 it is estimated to have increased by a factor of five." (*) Software Even without copyright laws, programmers would continue to produce software. They might engineer the software to work only with permission from the software firm, requiring the consumer to pay for it. A second profitable business model is to allow consumers to use to the software for free, courtesy of advertisers. Google follows this model. A third option, and probably most preferable from the consumer's perspective, is the open-source freeware/shareware model, or software written by volunteers/hobbyists and made freely available without difficult licensing restrictions. Users may copy, edit, modify, sell, or pretty much do anything with the software. (For-profit entrepreneurs are able to take a piece of shareware, add useful features, and sell copies with tech support.) Brands & Trademarks Let's take it a step further. Why do we need to have registered trademarks? The conventional answer is that it helps consumers recognize a familiar product and distinguish it from other manufacturers' products. Without corporations having legal monopolies on their respective trademarks, though, consumers would still be able to distinguish one producer's products from another's. Imagine that you are an entrepreneur who makes O-shaped cereal similar to General Mills' Cheerios. Without legal trademarks, it would be perfectly legitimate to call your product Cheerios. Even though you would have the right to call your product Cheerios, grocery stores may refuse to carry your product. They might object to the name and request you to call it something else. In the absence of intellectual property laws, general consensus would determine which words refer to a specific firm and which words refer to a generic product. NOTE: Most authors address registered trademarks independently of copyrights and patents. While a patent has the potential to stifle innovation, no such danger exists with trademarks. Many authors treat trademarks as a unique identifier to establish a level of trust with the consumer. It would be fraudulent to impersonate a company to try to trick customers into trusting them. Immitation is okay... impersonation is not. The cereal above would be fine if it was labeled "SomeCompany Toasty-O's", but would be lying to imply that they are indeed General Mills. There you have it. Without patents and copyright, we would still have books, music, software, and world-changing inventions. We could still watch movies, and authors would still get paid for their work. There would by less mind-numbing regulation, and more competition in the market. Plus, you wouldn't need to feel guilty for downloading audio files from your next-door neighbor. Further Reading http://www.micheleboldrin.com/research/aim/anew02.pdf http://mises.org/Community/wikis/eco...-property.aspx  Have You Partnered with Thieves and Robbers? Alok Kejriwal In early 2008, at games2win.com, we had created a huge hit game called ‘Bombay Taxi’. It was a really funny flash game that challenged you to park a Black and Yellow taxi in the crowded streets of Mumbai while overcoming obstacles like beggars, kite fliers, local trains and elephants. And in a typical Internet style, we began receiving massive traffic to our portal via viral traffic – especially from USA and EU since Bombay Taxi was a classic parking game blended in a new exotic theme. Just after the huge spurt of traffic, I was shocked to notice that visitors suddenly disappeared – almost like they had fallen off a cliff. This was not typical – traffic always tapers down and then plateaus out, so I decided to investigate. When I typed ‘Bombay Taxi Online Game’ on Google, I was shocked to find that overnight almost 400 websites had stolen our game and embedded it on their portals. These thieves had sniffed out a good game and now were enjoying traffic on their own sites thanks to our hard work! My partner Mahesh Khambadkone and I huddled in our corner office conference room and brooded. This was a disaster. Each time we would make a hit game, thieves would steal it and we would never reap the benefits of tsunami like viral traffic. Flash files could not be protected and this was a big blow to our business model since we relied on advertising on our site to make us $$$. Also DRM (digital rights management) for flash games was really not a successful technology. This led us to apply a thought process model at 2win group that we call “mental demolition”. Essentially it converts ‘how things are’ to ‘how things can become’. Just demolish each fact and event and build it into something that works for you. So, we realized: * Why do things get stolen? o Because they have value… no one steals the dirt of the streets and takes it home. So one big positive was that we had created some great content that the world loved to take home. * The sheer number of websites that had stolen our game in 3 days overwhelmed us. This proved that there was a massive distribution opportunity for our games amongst sites we had never heard of before. * What was really hurting us? The fact that we were missing on the ad revenues that these stolen games were generating on the pirate site. * Was protection ever going to work? Everyone we knew had pirated music and videos and films from all over the Internet. Protecting IP was futile on the Internet. In a brain wracking session, there was a flash of inspiration and a ‘Eureka’ moment: We plotted to create a technology that would allow us to place INVISIBLE ads in our games (for the pirates not to notice them) that would then travel along with the game to the pirate sites and become automatically VISIBLE when the game played there! We actually cracked this technology (MK and I are the inventors in our patent filing), and the games2win.com business changed dramatically after that day. To give you a perspective, we now touch 15-20 million users via Inviziads each month (comScore May data – extended web). These ads are fully controlled by us and we change and sell the ads as per our control in each of the 160 countries the games have been stolen in. Over 8900 websites have stolen our games and new websites get added each day. Games2win from zero has become a top 50 global games business (comScore online games ranking May 2010) thanks to the traffic we pull into our sites via inviziads! Internally, we now benchmark a game’s success by how many websites have stolen it! Look at the love triangle – Pirates love our content and steal our games. We love ads and place ‘invisible to visible’ ads in our games. Consumers love games and they play them on all kinds of websites all over the world!! Players such as Viacom, Ubisoft and Warner Brothers now license Inviziads and you can study the business model on www.inviziads.com. What are the lessons for entrepreneurs and start ups in this story? * Try and create gold from dust. If you have a problem that is destroying you, look at it using a prism that could turn it to an advantage. I always feel that if Virgin Music and EMI etc., would have bought Napster (instead of suing it and closing it down) and then converted the site into their official mp3 website, iTunes would have been a me-too and not the gorilla it is today * Understand and accept the eco-system. If the internet is about piracy and lifting, flow with it – don’t fight it * Foes can be Friends just by a flick of a switch. Think of everyone as a Dr. Jekyll and Mr. Hide. Make your enemies work for you Remember that winning the nuclear war in planet start up requires not just creativity and innovation but the ability to mentally demolish and rebuild yourself from scratch. http://rodinhood.com/have-you-partnered-thieves-robbers  Only 0.3% of Files on BitTorrent Confirmed to be Legal Jacqui Cheng The large majority of content found on BitTorrent is illegal, a new study out of the University of Ballarat in Australia has confirmed. Researchers from the university's Internet Commerce Security Laboratory scraped torrents from 23 trackers and looked up the content to determine whether the file was confirmed to be copyrighted. They found that 89 percent of the files they sampled were confirmed to be illegally shared, and most of the remaining ambiguous 11 percent was likely to be infringing. The total sample consisted of 1,000 torrent files—a random selection from the most active seeded files on the trackers they used. Each file was manually checked to see whether it was being legally distributed. Only three cases—0.3 percent of the files—were determined to be definitely not infringing, while 890 files were confirmed to be illegal. Additionally, 16 files were of ambiguous origin and 91 files were pornographic, which were unclear due to their oft-mislabeled nature. "[M]any files were tagged as amateur (suggesting no copyright infringement) but further inspection revealed that they were in fact infringing," wrote the researchers. Basically, the 89 percent is a baseline number when it came to infringing files, and the three most shared categories were movies, music, and TV shows—among those categories, there were zero legal files being shared. Assuming all 16 files of ambiguous legality were in fact legal, the researchers said that there was an overall figure of 97.9 percent infringing content being distributed on BitTorrent. This report echoes similar results out of Princeton that were published earlier this year. Though the top categories were slightly different—Princeton found that movies and TV were the most popular, while music fell behind games/software, pornography, and unclassifiable files—that study found that all of the movie, TV, and music content being shared was indeed infringing. Overall, Princeton said that 99 percent of the content on BitTorrent was illegal. The University of Ballarat said that just four percent of torrents were responsible for 80 percent of the seed population. And, according to the list of the top 10 most seeded files, they were all Hollywood films (save for Lady Gaga's album, The Fame Monster, at number 7)—it's clear that Linux distros weren't exactly dominating the charts here. Copyright holders have one consolation, however: P2P users seem to buy more content than the average person, so there's still some chance of earning those users' money after all. http://arstechnica.com/tech-policy/n...o-be-legal.ars  Times’ Paid Model: The Unofficial Numbers Come In The Times’ paid model is just two weeks old but, still, a number of stats came through this weekend - none of them from the horse’s mouth… First, the meat - some potentially significant first numbers on how successful the paper’s paid websites have been in their first two weeks. There’s no attribution for these, but the fact they’re reported by former Times media correspondent Dan Sabbagh might be some cause for validity… —Readers registered during free trial period: 150,000. —Paying subscribers: 15,000 (Sabbagh: “This figure, apparently, is considered disappointing”). —iPad customers so far: 12,500. If true, this suggests that 12 percent of Times Online’s pre-wall daily audience created an account during the first-month-free period, then a tenth of them have paid. The Times spokespeople did not respond to a request for comment over the weekend gave no comment, but we wouldn’t expect them to comment on such speculation. The next data set, from Hitwise, got some confusing write-ups in weekend papers (FT.com, Observer), but the bottom line is… The registration wall, despite being free for a month, resulted in site visits declining by 58 percent. By the time actual payments had been required for a week, visits were down by 67 percent, compared with the old days. This won’t worry many at the paper, since the whole strategy is about courting fewer, more loyal users. And it’s a darn sight better than the 90 percent drop-off that many, including The Times’ editor, have braced for. Ultimately, we have nothing from Times Newspapers to back any of this up - it likely won’t comment on the reported customer up-take and it stopped reporting its web traffic back in April. The days are still so early; the new model is just two weeks old - traffic may fall further, but paying customers may get steadily added. We would expect the paper to shout success, if it happens, from the rooftops in the next month or two. http://paidcontent.org/article/419-t...mbers-come-in/  Amazon Says E-Books Now Top Hardcover Sales Claire Cain Miller The heft and musty smell of a hardcover book are one step closer to becoming relics in a museum. Amazon.com, one of the nation’s largest bookstores, said Monday that for the last three months, sales of electronic books for the Kindle, Amazon’s e-reader, outnumbered sales of hardcover books for the first time. The fact that e-books now outsell hardcover books is “astonishing when you consider that we’ve been selling hardcover books for 15 years, and Kindle books for 33 months,” Amazon’s chief executive, Jeffrey P. Bezos, said in a statement. In the quarter, Amazon said it sold 143 Kindle books for every 100 hardcover books, including hardcovers for which there is no Kindle edition. That number includes the last four weeks, when sales increased to 180 electronic books for every 100 hardcover copies. There are 630,000 Kindle books in Amazon’s library, a fraction of the millions of books sold on the site. The Kindle sales figure does not include free Kindle books, of which there are 1.8 million originally published before 1923 available for downloading. Amazon does not disclose how paperback sales compare with e-book sales, but paperback sales still probably outnumber e-books. Book buyers who do not own a Kindle can read their Kindle books on a variety of devices, including laptops, iPhones, iPads, BlackBerries and Android phones. But even with the popularity of the iPad, which Apple has marketed as a leisure device for reading and which has its own e-book store, sales of the Kindle are growing, Amazon said. Kindle sales increased each month in the second quarter, the same period that Apple began selling the iPad, and the growth rate tripled after Amazon lowered the price of the Kindle from $259 to $189 in late June, Amazon said. That came after Barnes & Noble dropped the price of its Nook e-reader to $199 from $259. During about the same period, Apple said it sold three million iPads. Amazon’s stock price is down about 16 percent in the last three months, in part because of investor concerns that the iPad threatened Kindle sales. http://www.nytimes.com/2010/07/20/te.../20kindle.html  Vampire Weekend's Cover Art 'Contra'-versy: Model Sues Band for $2 Million Lyndsey Parker While debate regarding unauthorized use of Facebook pics rages on, a photograph from the pre-digital age has gotten one indie group in some serious trouble. Former fashion model Ann Kirsten Kennis is suing buzz band Vampire Weekend for a cool $2 million, claiming a 1983 photo of her was used in their Contra album cover art without her consent. 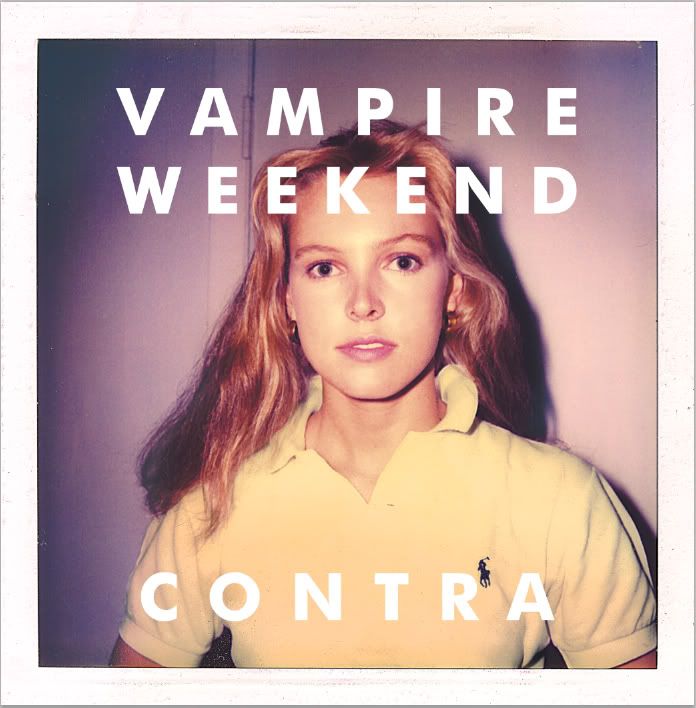 Kennis, who currently resides in Fairfield, Connecticut, with her family, was reportedly very surprised to see her doe-in-headlights likeness in a preppy Polo shirt on the Contra cover, when her daughter showed her the disc earlier this year. "Her daughter came home one day and said, "Hi, Mom, see your picture?'" Kennis's lawyer, Alan Neigher, told Entertainment Weekly. Neigher also told EW that the photo was never intended for professional use. "It was taken by her family. It was a Polaroid, not a modeling picture," he insisted. "Her mother was a chronic Polaroid snapshot-taker, and used to sell whole archives of photographs to these shops, five bucks a hundred or whatever. Her mother may have given away to a charity bazaar a whole ream of photographs. We just really don't know...[Kennis] has no idea how that photograph got into the photographer's hands." The photographer in question is Tod Brody, who along with Vampire Weekend's record label, XL Recordings, is also named in Kennis's $2 million misappropriation-of-identity lawsuit. See, Kennis claims Brody duped Vampire Weekend into believing he was the photographer who had shot the Polo pic, and that he forged her signature (as "Kirsten Johnson" in one spot and "Kirsten Johnsen" in another, Neigher says) on the photo's release form. Brody of course has denied this, telling EW: "Ms. Kennis's claim that I didn't take the photo is blatantly false. I took the photo in 1983. The photo was in my possession the entire time, for 26 years, until it was delivered to Vampire Weekend." (Incidentally, the photograph seems to have been removed from Brody's website, www.todbrodyphoto.com, although it was once included in the Portraits section under the file name "Kirsten.") The band, who reportedly paid $5,000 to use the picture, have also issued their own formal statement: "As is standard practice, Vampire Weekend and XL Recordings licensed the rights to use the photo on the cover of Contra pursuant to a license agreement that contains representations and warranties authorizing this use of the photo. Now that a lawsuit has been filed, we look forward to having the matter resolved in court." So there are several questions here. First, who took the photo--Kennis's mother or Tod Brody? And if it was the mom, then did Brody really forge Kennis's signature and claim he was the real photographer? And if so, how did he think he'd get away with such a scam, since it was inevitable that Kennis would eventually see the cover? (After all, the album did debut at number one on the Billboard album chart in January 2010, so it was hardly obscure.) Conversely, if it was Brody who took the pic, is it possible that Kennis failed to read the fine print and didn't realize she was signing away rights to the picture 27 years ago? And finally, did Vampire Weekend have any responsibility--as Kennis alleges--to make sure the photo release form's signature was legit? It's unclear just how much the band knew about their cover model before this lawsuit; when asked about the girl in interviews at the time of Contra's release, they gave deliberately vague answers. Lead singer Ezra Koenig told MTV News: "We know where the image came from, but we're not being very specific about her. We don't know her or anything....there's just something infinitely fascinating about a nice portrait of somebody, especially when she's got this ambiguous look, and people can read a lot into it....It makes you realize how much you can imagine about somebody when you know nothing about them, based on only a few signifiers." The mystery surrounding the enigmatic golden girl on the Contra cover continues, although not in the way Koenig may have imagined. Kennis retired from modeling years ago; additional photos of her, from either the past or present, professional or candid, are seemingly non-existent on the Web (even the profile pic on what appears to be her private Facebook page is a photo of a dog); and she's refused to speak to the press thus far (she did come to the phone when the Village Voice rang her recently, and was reportedly polite, but declined to be interviewed). Perhaps when the reclusive ex-model finally appears in court, we'll all find out the real story behind this now-infamous photograph. http://new.music.yahoo.com/blogs/sto...for-2-million/  Rock Hall Joins Fight Over Performers' Rights for Radio Play Stephen Koff The Rock and Roll Hall of Fame has joined the battle of Bruce Springsteen, Paul McCartney, Sam Moore and other musical performers who want artists to get paid when their songs are on the radio. But that doesn't mean the Rock Hall is entirely at odds with the nation's broadcasters, who say performers are compensated plenty in the form of free publicity every time their songs go over the air -- the primary platform for exposing new music to the public. Rock Hall officials are avoiding the thorny details that pit the MusicFIRST Coalition, the Grammies and influential record labels against the National Association of Broadcasters and powerful voices in radio such as Clear Channel and Radio One. The Rock Hall's position steers clear of endorsing the pending Performance Rights Act, with its proposed formulas for royalties, or of supporting any specific method of compensating artists. Instead, it hopes the parties can find some middle ground. Still, the Rock Hall's position puzzled the National Association of Broadcasters, which used news of the Rock Hall's position to take a fresh shot at the record industry and its umbrella group, the Recording Industry Association of America, or RIAA. Depending on who owns the recordings, in many cases the artists and their record labels would share equally in the new royalties proposed in the Performance Rights Act. "It's puzzling that the Hall has sided with RIAA in the performance tax fight, given the record labels' historic abuse of artists and the fact that the labels would pocket 50 percent of the proceeds from a devastating new fee on radio stations," said Dennis Wharton, executive vice president of the broadcasters' group. "The reality is that free radio airplay helped turn rock and roll into the cultural phenomenon that it is today." Joel Peresman, president and CEO of the Rock and Roll Hall of Fame Foundation, issued a statement saying, "We're encouraging Congress, musicians and the recording and broadcasting industries to come together to bring the U.S. copyright laws to the same standards of equity that exist in most countries." And Terry Stewart, president and CEO of the Rock and Roll Hall of Fame and Museum in Cleveland, said, "The Rock and Roll Hall of Fame is advocating a simple proposition: that everyone should be paid for their work. Our hope is that this issue can be resolved in such a manner that is fair and equitable to artists and broadcasters alike." Composers and music publishers are paid when their songs get airplay. Performers get paid when their songs are on Internet radio, a recent development. But as long as there has been free radio, Congress has given it a pass, agreeing with broadcasters that the symbiotic relationship between radio stations and performers serves both well. The newest attempt to force radio to pay comes from lawmakers such as Democratic Reps. John Conyers of Michigan and Marcia Fudge of Cleveland, as well as California Republican (and Cleveland Heights native) Darrell Issa. An array of performing artists have lobbied Congress on the bill or voiced their support, from Mary Wilson of the Supremes and Mickey Dolenz of the Monkees to well-known stars like Springsteen, McCartney, Bono, Gladys Knight and Rod Stewart. But broadcasters, meantime, are pushing a resolution signed by a majority of U.S. House members that asks, without force of law, to keep radio "free." Broadcasters say a new royalty system would be the equivalent of a tax that could put some stations out of business, although the proposed new royalties would factor in station revenues to soften any economic harm. Positions have been extreme. Parties in the radio and record businesses are talking, at the urging of lawmakers like Conyers, but no breakthroughs or compromises exist just yet. The recording industry has been predicting a vote in the House to pass the Performance Rights Act by the end of the year. Asked what made the Rock Hall add its voice, spokesman Todd Mesek said, "We're supportive of performers getting paid for their work. No specific action prompted this." http://www.cleveland.com/open/index...._over_per.html  Clear Channel Calls For Dropping Radio Ownership Restrictions FMQB Clear Channel has chimed in on the FCC's review of the media ownership rules. In a new filing, the broadcasting giant calls for the loosening of restrictions on station ownership. CC says that with terrestrial radio facing more competition than ever, from the Internet, satellite and more, it makes current restrictions outdated. In the filing, CC states, "Today, terrestrial radio stations compete not only with their local peers but also with the growing panoply of regulated and unregulated competitors at the local, regional, and global levels. These competitors use new technologies and services to deliver music, entertainment, and news in formats and on platforms that today’s audiences demand. Many of these outlets did not exist in 1996, and several were in nascent stages in 2006; today, satellite radio and internet-based services are robust competitors to terrestrial radio stations." The broadcaster argues that "Unlike terrestrial radio broadcasters, none of these powerful competitors are limited in the number of outlets or program streams they can provide. Coupled with sharply increasing competition from other terrestrial broadcasters and new audio platforms, the radio industry has experienced significant financial setbacks since 2006. Beginning with the financial meltdown of 2007, the number of bankruptcy filings and lender workouts among terrestrial radio companies, along with other broadcast and print media, has ballooned." http://www.fmqb.com/article.asp?id=1878481  North American Concert Sales Plunge in First Half Combined ticket sales for the biggest concert tours in North America during the first half of the year fell to their lowest point since 2005 as the weak economy and "piggish" ticket prices kept fans at home, a trade publication reported on Thursday. The top 100 tours grossed $965.5 million during the first six months, a 17 percent slide from the year-ago period, and the lowest for the time frame since the $731 million haul in the first half of 2005, according to Pollstar magazine. High-profile outings by the Eagles, the Jonas Brothers and the latest crop of American Idol finalists suffered poor sales. Christina Aguilera, Limp Bizkit and the Go-Gos' canceled their tours, and organizers of the all-female Lilith Fair organizers said last week that they had scrapped about a third of the shows. Pollstar said fans "may be turned off by piggish top-tier prices, resentful of ticket add-on fees, and downright angry when they hear about discounted tickets after they have paid full price." But it noted that tours by Lady Gaga, Justin Bieber, Taylor Swift and rock band Muse did well, as did singer/songwriter James Taylor's trek with Carole King. On a worldwide basis, Australian rockers AC/DC came out on top, selling $177.5 million worth of tickets, followed by Bon Jovi with $75.7 million and Metallica with $60.8 million, Pollstar said. Taylor and King took in $53.9 million, ahead of the Black Eyed Peas with $48.4 million. In the United States and Canada, Bon Jovi ($52.8 million), Taylor/King ($41 million), Swift ($34.2 million) and Paul McCartney ($31.5 million) led the field. "Fans still crave live music and will come out to shows when they can afford it, despite the industry's misguided efforts to squeeze the fun out of the experience," Pollstar said. (Reporting by Dean Goodman; Editing by Jill Serjeant) http://news.yahoo.com/s/nm/20100708/...nm/us_concerts  ‘Inception’ Exceeds Box-Office Dreams Brooks Barnes Guess what? Movies don’t have to be sequels or animated to do enormous box-office business in the summer. “Inception,” a complex dramatic thriller about dream invasion, was No. 1 at North American theaters over the weekend with $60.4 million in ticket sales, according to Hollywood.com, which compiles box-office data. That total gave the star of “Inception,” Leonardo DiCaprio, the biggest opening of his career. (While “Titanic,” which starred Mr. DiCaprio, went on to become one of the highest-grossing films ever made, it took in $28 million on its first weekend.) “Being original and fresh and different matters in this marketplace, and this movie had all of those things,” said Dan Fellman, president for domestic distribution at Warner Brothers, which produced the $160 million film in partnership with Legendary Pictures. “Inception,” which won mostly positive reviews, was written and directed by Christopher Nolan, the cinematic powerhouse behind films like “The Dark Knight” and “Memento.” It was not as pretty a picture for Walt Disney Studios and the producer Jerry Bruckheimer. Their action fantasy “The Sorcerer’s Apprentice,” starring Nicolas Cage, had a disastrous weekend, selling just $17.4 million for the weekend for a five-day total of $24.5 million. “The Sorcerer’s Apprentice,” which cost about $150 million to make, is Mr. Bruckheimer’s fourth box-office disappointment in a row. This PG-rated movie, marketed with the clunky tag line “It’s the coolest job ever,” will now need to outperform overseas to avoid becoming a financial debacle for Disney. The hope is that “The Sorcerer’s Apprentice” will mimic the pattern of “Prince of Persia: The Sands of Time,” Mr. Bruckheimer’s previous outing with Disney. “Prince,” made for about $200 million, was a dud in North America, selling only about $89 million. But overseas sales of $237 million eased the pain a bit. Chuck Viane, Walt Disney Studio’s president for distribution, did not respond to phone and e-mail messages on Sunday. In limited release overseas, “The Sorcerer’s Apprentice” sold an additional $8.3 million. For the weekend in North America it was third behind the holdover hit “Despicable Me,” which sold $32.7 million for a new total of $118.4 million. This animated title, from Universal Pictures and Illumination Entertainment, is another example of an original idea succeeding. Amid a sea of sequels — “Shrek Forever After,” “Toy Story 3” — “Despicable Me” broke through the old-fashioned way: a well-executed story backed by smart marketing. In fourth place “The Twilight Saga: Eclipse” (Summit Entertainment) continued its powerful run with $13.5 million for a new total of $264.9 million. Disney-Pixar’s “Toy Story 3” was fifth with $11.7 million for a new domestic total of $362.7 million. The unexpectedly strong performance of “Inception” — surveys that track audience interest had indicated an opening of about $40 million — helped keep the summer box office buoyant. Between May 7 and Sunday, moviegoers spent $2.7 billion on tickets, a 2 percent increase over the same period last year, according to Hollywood.com. http://www.nytimes.com/2010/07/19/movies/19box.html  Hollywood Braced for Teamsters Walkout Carl DiOrio and Jonathan Handel Television would be hit hardest if Hollywood transportation workers go on strike for the first time in 22 years next month when their current labor agreement expires, according to industry observers. Upward of 20 shows are in production ahead of the fall television season, and production executives are puzzling over ways of getting actors and others on and off their lots without crossing picket lines. "If (a strike) were to happen, it would be hugely unfortunate," said Ed Bernero, executive producer on the CBS series "Criminal Minds." It's possible the Teamsters would agree to work under a contract extension even if their pact expires August 1 without a new agreement in place, but the union's Hollywood Local 399 is expected to take a strike-authorization vote during a general membership meeting on Sunday morning. That would arm Local leaders with the ability to walk at any point after the midnight expiration of the Local's current "Black Book" agreement a week from Saturday. The transportation union's talks with Hollywood studios involve proposals for a new two- or three-year contract but have hit an impasse over money terms. The Teamsters want annual raises of 3%; management is offering 2% yearly boosts. The studios would prefer a three-year deal but are offering two years at the union's request, which would allow the Teamsters to synch up their contract expiration with the International Association of Theatrical Stage Employees. That, in turn, would give the Teamsters more input into contract matters affecting the pension and health plan that covers members of both unions. Negotiators for the union and employers remain in touch this week ahead of the next formal bargaining session, set for Friday morning, and another session could be scheduled for next week. An additional session would seem only natural, as a successful strike-authorization vote would enhance the union's hand at the bargaining table, and management appears inclined to agree to continued talks. The contract negotiations started June 14, and the parties' failure to agree on terms has prompted handicapping around town of the chances of a Teamsters strike. "I would be surprised if there were a strike, but there are some other people here who disagree with me," an exec on one lot said. "The water-cooler talk is that if there is a strike, it won't be pretty -- not necessarily in terms of length or financial impact, but in terms of tone, this could be worse than the writers' strike." The 100-day Writers Guild of America (WGA) strike of 2007-08 had TV networks scrambling to fill programing grids with extra reality fare after the scripted well ran dry. There was no immediate evidence of those sorts of contingencies, but some disruptions of film and TV productions are inevitable if the Teamsters go out. "Like all writers, I'm grateful for the solidarity the Teamsters showed us during the WGA strike," said Matthew Weiner, creator and executive producer of AMC's "Mad Men." "I think they know they can count on me to support them in any way I can." On-location shoots are particularly vulnerable to disruption, but projects are being pushed forward. At least a dozen movies are listed for shooting in August, and some -- such as the New Line comedy "Horrible Bosses" -- already are shooting in the L.A. area. Even executives with productions housed in soundstages have to figure out how to get actors on and off lots. Studio executives are reviewing infrastructure maps to identify discreet entrances less likely to draw pickets. Some lot disruptions would fall into the category of annoying inconvenience. For instance, studio commissaries' daily shipments of food and beverages could be halted if delivery drivers honor the union's pickets, and creative means of obtaining office supplies might become necessary. Other Hollywood guilds are prohibited from staging sympathy strikes. But the Screen Actors Guild or others could make statements suggesting members follow their consciences in deciding whether to report to work. "We'll honor our contracts and support our union brothers and sisters as much as possible," one actor observed this week. Hollywood Teamsters worked more than two months after the expiration of its contract with studios in 1988 before mounting a 25-day work stoppage, the Local's last full-fledged strike. If a new strike breaks out, studios also can be expected to boost lot security and may hire some new staff where necessary to replace workers refusing to cross picket lines. http://www.reuters.com/article/idUSTRE66K0K720100721  Banned TV Episode Has Its Day on DVD Dave Itzkoff In many ways, the “Family Guy” episode “Partial Terms of Endearment” is typical of that audacious Fox animated comedy, teeming with rapid-fire jokes and willfully offensive non sequiturs about disabled animals, God, Nazis, bodily functions and the sexual habits of “Sesame Street” characters. It is also an episode in which a central character finds herself with an unwanted pregnancy and contemplates an abortion, a subject that is frankly discussed — and flagrantly satirized — by the cartoon’s cast. The Fox network has said it will not broadcast “Partial Terms of Endearment,” which was produced for the 2009-10 season. However, the home video arm of 20th Century Fox plans to release the episode as a stand-alone DVD in September, in packaging that plays up its polarizing qualities. When it does, many “Family Guy” fans will get their first look at an unlikely reminder of the television networks’ aversion to the issue of abortion, and a rare boundary encountered by an often rebellious series. “Times really have changed,” said Seth MacFarlane, the creator of “Family Guy.” “The network is making a decision that is, unfortunately, probably based on people’s current ability to handle and dissect controversial narratives.” As a longtime admirer of the comedies of Norman Lear — to the point that the “Family Guy” opening credits pay homage to “All in the Family” — Mr. MacFarlane said he tried to include two to three episodes each season that are issue-oriented. When the topic of abortion came up in the “Family Guy” writers’ room, he said, “There’s nothing about that issue that should be any different than doing an episode about gay marriage or an episode about the oil spill.” Mr. MacFarlane enlisted Danny Smith, a veteran “Family Guy” writer and producer, to draft the episode’s script, assigning him to read a part of Carl Sagan’s book “Billions and Billions” that tries to find common ground between the “absolutist positions” of abortion rights advocates and anti-abortion groups. In the script that Mr. Smith delivered, Lois Griffin, the wife of the titular “Family Guy” lummox, Peter Griffin, agrees to be a surrogate mother for a college friend who cannot conceive. When the friend and her husband are killed in a car accident, Lois debates whether she should keep the child, frequently finding herself in opposition to Peter’s wishes. Mr. Smith, who describes himself as “a recovering Catholic,” said the script was not especially contentious when it was revised by the show’s mostly male writing staff. “We’ve had more spirited debates about whether or not we should state whether Santa Claus is real,” Mr. Smith said. When Mr. MacFarlane presented the concept to Fox, it warned him that the subject matter raised a red flag, but allowed him to produce the episode anyway. He said he believed that the network would eventually run it, as it had an earlier episode called “When You Wish Upon a Weinstein” that it rejected in 2000. That installment, in which Peter yearns for his son Chris to become smarter by converting to Judaism, was first shown on Adult Swim on Cartoon Network in 2003, and then on Fox in 2004. (“Nobody got too offended,” Mr. MacFarlane said. “Most of the time these things turn out to be nothing.”) But the Fox network decided not to show “Partial Terms of Endearment.” The network said in a statement that it fully supported “the producers’ right to make the episode and distribute it in whatever way they want,” and declined to elaborate on its decision. A spokeswoman for Adult Swim also said in an e-mail message that there were “no plans to air that episode of ‘Family Guy.’ ” Last August Kevin Reilly, Fox’s entertainment president, told reporters at the Television Critics Association tour that the rejection of the episode “was a business decision” because it represented “fragile subject matter at a sensitive time.” But the “Family Guy” staff remains unclear on Fox’s rationale. It’s not that abortion is a totally forbidden subject on network television: a recent episode of the NBC drama “Friday Night Lights” dealt with it, and the best-known treatment of the issue, a two-episode arc of “Maude,” was produced by Mr. Lear in 1972. On one level the “Family Guy” producers understand that some of their jokes — a scene in which Lois is impregnated by Peruvian natives wielding blow-dart guns; a lengthy Warner Brothers parody in which Peter stalks Lois with an Acme Miscarriage Kit — may not have treated the abortion debate with proper gravity. But they say there is no way to predict what material will offend audiences. Mr. Smith pointed to an episode in which the family dog, Brian, becomes an advocate for marijuana legalization. “I have two sons,” Mr. Smith said, “and I don’t know if I feel comfortable with this cartoon dog telling people that life is better with a bag of weed.” Mr. Smith said more viewers complained about a scene in which Peter accidentally kills a neighbor’s cat. There was also support from Twentieth Century Fox Home Entertainment, which felt that issues of taste would not discourage “Family Guy” fans from seeking the episode on DVD, and determined that DVD sales could cover the production costs of “Partial Terms of Endearment” if the network did not broadcast it. “Seth and I have had arguments where I’m the nervous Nellie, and he’s pushing the envelope,” said Mike Dunn, the president of Fox’s home entertainment unit. “Finally it’s like, O.K., you win. This franchise does better when it’s pushed.” Mr. MacFarlane said that the word abortion may simply be a “comedy red zone that you just shouldn’t enter,” noting that Fox had also made him change a joke because it contained the phrase World Trade Center. But he did not criticize Fox for its decisions, which he said revealed more about mass audiences than about the networks. “People in America, they’re getting dumber,” Mr. MacFarlane said. “They’re getting less and less able to analyze something and think critically, and pick apart the underlying elements. And more and more ready to make a snap judgment regarding something at face value, which is too bad.” Whatever Fox’s reasons for refusing to broadcast “Partial Terms of Endearment,” Mr. MacFarlane said it was unlikely that the decision came from the corporation’s politically conservative chairman, Rupert Murdoch. “My assessment of him has always been that he is a shrewd businessman first and a conservative second,” Mr. MacFarlane said, adding: “If he felt that something like this would be profitable to the corporation, he would have no issue airing it.” Meanwhile, Mr. Smith joked that he was more worried about what the loss of network residuals for the episode would mean for his own bottom line. “I have two kids in private school, man,” he said. “Fox is hitting me where it hurts. I’m always going to have a creative outlet here, but jeez, don’t take my money away.” http://www.nytimes.com/2010/07/20/ar.../20family.html  UK Independent Films Facing Tough Times Tim Masters Low budget independent films are facing a tough time financially amid the economic slowdown, the UK Film Council has said. The number of feature films funded solely in the UK fell slightly from 77 in 2008 to 71 in 2009. Overall, budgets for independent films in 2009 also showed a slight drop. However, it was a record year at the UK box office overall last year, with takings of £944m and the highest admissions since 2002 (173.5 million). One of the main reasons for this growth, the report said, was the emergence of 3D cinema. Avatar, Harry Potter and the Half-Blood Prince, and Ice Age III were the three most popular films in UK cinemas in 2009. The figures came as the Film Council launched its first fully-searchable website with comprehensive statistics. 'Tough transition' "Overall it's clear that British cinema has been weathering the global recession well," said UK Film Council chief executive John Woodward. He said the sectors of production, distribution and exhibition were "firing on all cylinders". Avatar James Cameron's Avatar was one of the most popular films of 2009 But he said the marketplace for financing smaller, independently-produced British films was becoming more difficult. This was partly as a result of the overall economic slowdown and partly down to "the increasingly tough transition from the analogue to the digital age". "Low budget independent production is a tough business - it always has been," he said, noting that figures for the first half of 2010 showed a continuing pressure on smaller film production. "I'm not saying this is a catastrophe, what I am saying there is something quite serious going on here," Mr Woodward said. "Around the world broadcasters are paying less for feature films, and there's a slow erosion of the DVD market. "The film industry has not managed yet to properly monetise the online space. Revenues are drifting away from DVD and TV, but they are not being replaced by online sales at the moment." The UK Film Council report showed that independent UK films were at their most popular in 2009 - both in the UK and global markets - since records began. Helped by the success of Slumdog Millionaire, indie films took 8.2% of the UK and 2.3% of the global market share. Other top performers included Nativity and The Young Victoria. The report also showed that British film talent - including actors, writers, directors and crew - continued to shine on the international stage. Some 14% of all major awards won around the world between 2001-2009 were won by British films and talent. 2009 saw a substantial increase in film production in the UK, driven by a record level of "inward investment" - films largely financed and controlled from outside the UK. Examples in 2009 included Harry Potter, Robin Hood and Fantastic Mr Fox. The number of films made in the UK but funded by inward investment rose slightly from 27 in 2008, to 32 in 2009. Total UK production activity rose from £613m in 2008 to £957m in 2009, £753 million of which came from inward investment (up 111% on the 2008 figure of £357 million). "Film really matters to people, it's an integral part of people's leisure time," said Mr Woodward. http://www.bbc.co.uk/news/entertainment-arts-10710877  Industrywide Digital Locker Beta to Launch in Fall A consortium of 55 entertainment and technology giants hoping to standardize digital formats for video playback said on Monday it will start beta testing in the fall as it added two more companies to its ranks and unveiled its brand name, Ultraviolet. The Digital Entertainment Content Ecosystem (DECE) said LG Electronic and Marvell Technology Group Ltd joined the group aiming to standardize and streamline the digital supply chain by using cloud-based technology. For instance a consumer with an Ultraviolet account can buy a copy of a film, store it in a "digital locker" and then view it in various ways from a cable company's video-on-demand service to a game console. Driven largely by Hollywood seeking to offset a sharp decline in DVD sales, the DECE has recruited industry behemoths from technology firms Adobe Systems Inc and Cisco to cable giant Comcast, but has two big holdouts -- Walt Disney Co and Apple Inc. Disney is developing a competing system called KeyChest, while Apple sells songs and videos in proprietary formats through its iTunes Store. "We have enough critical mass to launch," said Mitch Singer, president of the DECE and chief technology officer for Sony Pictures, noting the group is talking with more potential partners and chose the brand name Ultraviolet in part because it is a natural extension of Hollywood's Blu-ray high-definition format. (Reporting by Susan Zeidler; Editing by Tim Dobbyn) http://www.reuters.com/article/idUSTRE66J0C920100720  ‘Yes Men’ Use BitTorrent To Avoid Censorship Ernesto The Yes Men are a culture jamming activist duo who expose the lies and social problems caused by governments and corporations. In their much awarded films they impersonate people in power to bring out the truth. Because the US Chamber of Commerce is suing their asses, they have now turned to BitTorrent to get their message out. With millions of daily users BitTorrent is a great outlet for filmmakers to promote their work, but there are more advantages to this 21st century distribution platform. After their first film turned into a huge success, The Yes Men don’t have to worry too much about promotion. However, it is still much-needed to avoid censorship from governments and corporations and to raise funds for future endeavors. In 2009 The Yes Men hijacked a United States Chamber of Commerce press conference, declaring a U-turn on their climate change policy. In a response to this “identity correction” the Chamber filed a lawsuit against the duo, claiming that they misled the public. Due to this legal battle no TV-station wants to take the risk to run some of the most controversial material, so The Yes Men took matters into their own hands by releasing an updated P2P-edition of their latest film today. In addition to avoiding censorship, The Yes Men are looking for donations to fund their upcoming projects. This is where the BitTorrent-powered distribution platform VODO comes in. With free promotion from uTorrent, Limewire and a variety of prominent torrent sites including The Pirate Bay and EZTV, this release will instantly have an audience of millions of downloaders. To find out more about their motivation to get the film out on BitTorrent and to find out whether they were also this excited about BitTorrent when their first film was pirated by more than a million people, we caught up with Mike Bonanno, one half of The Yes Men. “There are a few reasons why we chose BitTorrent. First off, it’s a way to avoid censorship,” Mike Bonanno told TorrentFreak. “This version includes video of an action against the US Chamber of Commerce that we are being sued for. No commercial outlets will touch it. We had a TV show scheduled on Planet Green and their lawyers nearly wet themselves when they heard we wanted to use footage of us making political mince-meant out of the largest lobbying organization in the world.” “It’s unlikely that anyone would distribute this material before we get out of court,” Bonanno continued. “But we don’t want them to win a de-facto censorship case, so P2P is a great workaround. Another reason we are doing this is because this is the way people see movies these days, and we made this movie for people to see it. We would love it if people bought our DVD, but we also want people who don’t do that to see it. And last of all: we do hope to generate some donations: we are broke and there are not so many funders for our new project, especially given that they are all spooked by lawsuits, no matter how stupid!” Although the benefits of BitTorrent are clear in this case, The Yes Men’s previous film was also pirated by more than a million people. When we asked Mike Bonanno how he felt about this we found out that he’s more upset about the stranglehold that the ‘copyright mafia’ puts on indie productions than the people who grab a copy of their movie on BitTorrent. “It’s great that people are watching our films! We are very happy that they are getting seen. But that having been said, we do wish that a few more people were paying for it. We borrowed a shit-load of money from friends to make our latest movie and we still can’t pay them back. Also, the way the industry is set up, if you want your stuff on TV or delivered through any official channels you have to spend a massive amount of money clearing rights and paying for legal stuff and that is just silly.” “For us to get our ‘errors and omissions insurance’ required for any distributor to take it, we had to clear the rights on all sorts of stuff we should not really have had to… including music written in the 17th century, which apparently because of some kind of law in Austria was not public domain according to the interpretation of insurance industry lawyers! Anyway, that’s just one example… so what happens as a film maker – especially a documentary maker – is that in today’s market we are fucked.” “Because to get it on TV we still need to act like we have deep pockets and can pay for rights for all sorts of shit, but then with the collapse of the indy film market distributors won’t pay for it. And of course most people file-share it rather than pay for it. So yeah, we are happy that people are watching it but not so happy that we are financially screwed! But we also see that it’s the system that is screwing us: we are not blaming the pirates, we are blaming casino capitalism!” This comment from Bonanno led us to ask the question whether The Yes Men would ever consider exposing the ‘copyright mafia’ and anti-piracy groups. These outfits have turned copyright into a cash cow while pretending to protect the rights of artists, something we address here on TorrentFreak every week. As it turns out, The Yes Men are siding with us in this regard. “I think in some ways most of our work is about targeting ideas about the rule of private property… so this is related,” Bonanno said. “Our first four years as The Yes Men was dedicated to attacking the World Trade Organization, which has historically supported the idea of proprietary media. Overall, I think that in some ways everything today, every major issue facing us can be seen through the lens of what role it plays in the commons… or lack thereof, as many a government and corporation would have it.” “If copyright was actually working the way it was supposed to, and protecting the authors that would be great. But that’s not how it works anymore – it just protects money; whoever has the most of it. And usually that means that the authors are fucked anyway!” The Peer-to-Peer edition of The Yes Men Fix The World is now available for free on VODO. To spread their knowledge The Yes Men have started The Yes Lab, which is also worth checking out. Lastly, don’t forget to donate a few bucks if you like what you see. http://torrentfreak.com/yes-men-use-...orship-100723/  WSJ's Mossberg Wants a Broadband Plan with Teeth Gautham Nagesh Wall Street Journal technology columnist Walt Mossberg is glad the federal government is finally creating a national broadband plan but wishes it were more aggressive about broadband speed and less vague about the details. "I think it's interesting that we as a country are only now stumbling around trying to create a broadband policy," Mossberg said. During a conversation with Hillicon Valley Mossberg said the FCC's National Broadband Plan is short on details and lacks teeth. "For the first time the FCC has come up with a broadband policy so yes, that's progress," Mossberg said. "I don't think it's very strong, and I think a lot of it is just suggestions and kind of pretty vague. So I wish it were tougher. But I also understand there are a lot of other important issues that the president and congress have to worry about right now." Mossberg also said the plan is too focused on expanding access into rural areas. "That's like motherhood, everyone wants to vote for that and I certainly support that," Mossberg said. But there are two other issues that he said don't receive enough attention: speed and cost. "There are plans and services that are sold in this country as broadband which wouldn't even be allowed to be labeled broadband in a lot of other countries they're so slow," Mossberg said. "And yet, at the very same time we pay more per unit of broadband speed than anyone else. So there's something wrong in my opinion." Mossberg said improving the country's broadband access would be crucial to its economic competitiveness. "We need a strong broadband policy on the part of the government not to run or take over broadband, but to set the private sector and the society on a course where we can make sure that we always have the kind of speed, availability and affordability of broadband that will allow the innovation around it that will keep us competitive or hopefully ahead of other countries and I do worry about that," he said. http://thehill.com/blogs/hillicon-va...lan-with-teeth  Broadband Picture May Not be so Bleak A new study disputes the claim that Internet data rates in the U.S. are only half as high as advertised; study’s authors call for better data. Larry Hardesty In March, the Federal Communications Commission released its National Broadband Plan, in which it reported that “the actual download speed experienced on broadband connections in American households is approximately 40-50% of the advertised ‘up to’ speed to which they subscribe.” That finding, which the FCC had previously cited, caused some consternation among bloggers and op-ed writers, to say nothing of broadband subscribers. But a new study by MIT researchers calls it into question. Most of the common methods for measuring Internet data rates, the researchers conclude, underestimate the speed of the so-called access network — the part of the Internet that Internet service providers control. The number of devices accessing a home wireless network, the internal settings of a home computer, and the location of the test servers sending the computer data can all affect measurements of broadband speed. The researchers don’t cast their findings as supporting any particular policy positions. But they do argue that everyone with an interest in the quality of broadband access — governments, service providers, subscribers, and market analysts — should be more precise about what they’re measuring and how. “If you are doing measurements, and you want to look at data to support whatever your policy position is, these are the things that you need to be careful of,” says Steve Bauer, the technical lead on the MIT Internet Traffic Analysis Study (MITAS). “For me, the point of the paper is to improve the understanding of the data that’s informing those processes.” In addition to Bauer, the MITAS team includes William Lehr, an economist, and David Clark, a senior research scientist at the Computer Science and Artificial Intelligence Laboratory who from 1981 to 1989 was the Internet’s chief protocol architect. The researchers analyzed a half-dozen different systems for measuring the speed of Internet connections, from free applications on popular websites to commercial software licensed by most major Internet service providers (ISPs). Both MITAS and MIT’s Communications Futures Program, which also supported the study, receive funding from several major telecommunications companies. In each case that the study examined, the underestimation of the access networks’ speed had a different cause. The study that the FCC relied upon, for instance, analyzed data for broadband subscribers with different “tiers of service”: Subscribers paid differing fees for differing data rates. But the analysts didn’t know which data corresponded to which tier of service, so they assumed that the subscription tier could be inferred from the maximum measured rate. The MITAS researchers show that, in fact, the subscribers in lower tiers sometimes ended up getting higher data rates than they had paid for. In the study cited by the FCC, exceptionally good service for a low tier may have been misclassified as exceptionally bad service for a higher tier. In other tests, inaccurately low measurements were the result of an idiosyncrasy of the Transmission Control Protocol (TCP), the software that determines how Internet-connected computers exchange data. With TCP, the receiving computer indicates how much data it is willing to accept at any point in time; the sending computer won’t exceed that threshold. For some common computer operating systems, however, the default setting for that threshold is simply too low. In practice, many applications get around this constraint by opening multiple TCP connections at once. But if an Internet speed test is designed to open only one TCP connection between two computers, the computers can’t exchange nearly as much data as they would if they opened multiple connections. Their data rates end up looking artificially low. In yet another case, Bauer was running a popular speed test on his own computer. Much of the time, he was getting rates close to those advertised by his ISP; but one afternoon, the rate fell precipitously. For days, the test had been pairing Bauer’s computer in Cambridge with a test server in New York. But on the afternoon in question, the New York server was overburdened with other requests, so it redirected Bauer to the nearest free server it could find — in Amsterdam. The long sequence of links, including a transatlantic link, between his computer and the test server probably explains the difference in data rates, Bauer says. His ISP’s access network may not have been any more congested than it had been during the previous tests. This points to the difficulty of using a single data rate to characterize a broadband network’s performance, another topic the MITAS researchers address in their paper. “What is it that people care about if they want to compare a metric of merit?” Lehr asks. “If you’re watching lots of movies, you’re concerned about how much data you can transfer in a month and that your connection goes fast enough to keep up with the movie for a couple hours. If you’re playing a game, you care about transferring small amounts of traffic very quickly. Those two kinds of users need different ways of measuring a network.” The researchers have submitted their report to both the FCC and the Federal Trade Commission and will present a version of it at the Telecommunications, Policy, and Research Conference in Arlington, Va., in October. “This report from Dave, Steve Bauer, and Bill Lehr is the first comparative study that I’ve seen,” says FCC spokesman Walter Johnson. As Johnson points out — and the MITAS researchers acknowledge in their paper — the FCC is currently in the early stages of a new study that will measure broadband speeds in 10,000 homes, using dedicated hardware that bypasses problems like TCP settings or the limited capacity of home wireless networks. “What we’re doing right now," Johnson says, “is a follow-up to the broadband plan, recognizing that we need better data.” http://web.mit.edu/newsoffice/2010/broadband-0716.html  U.S. Said to Toughen up Broadband Deployment Report John Poirier High-speed Internet providers are expected to get a subtle rebuke from U.S. regulators this week when a report omits language that has previously said they are rolling out broadband to all areas in a "reasonable and timely fashion." According to a source familiar with the contents of the Federal Communications Commission report, it will be the first time the phrase has been omitted since the report was first issued in 1999. In March the FCC issued a broadband blueprint seeking to boost Internet speeds and deploy broadband services to all Americans including the 14 million to 24 million Americans currently without high-speed access. "The conclusion is going to be for the first time the FCC will find that broadband deployment is not timely and reasonable," the source said. The 2010 report "is saying we are no longer on the right track," the source said. The source, who declined to be identified because the report has not been made public, said the deployment report could be issued as early as Tuesday and does not make specific policy recommendations. Telecoms industry officials disagree with the report's conclusion, but a senior FCC official said the report is not meant to be critical of the carriers. "Congress requires the FCC to assess whether broadband has been reasonably and timely deployed to every American -- no matter where they live," said the official who declined to be identified. The broadband report, mandated by Congress, is similar to a tougher line taken in a May report on the wireless industry, in which the FCC for the first time since 2002 failed to describe the wireless industry as having "effective competition." It is likely to fuel criticism from public interest groups that competition is lacking in the broadband industry. "Until now, the Federal Communications Commission (FCC) has issued reports finding the state of broadband was acceptable," said Gigi Sohn, who heads Public Knowledge, a public interest group. The report on the state of broadband deployment could advance the agenda of the broadband plan, that includes a recommendation to refocus the U.S. telephone subsidy program, called the universal service fund, to subsidize broadband. Carriers have resisted deploying broadband technology to some rural areas due to the cost of investing. USTelecom, a trade group for broadband providers, disagreed with the pending report, saying the United States is in the middle of a broadband explosion. USTelecom President Walter McCormick said it was appropriate for the commission to be concerned about the remaining small percentage of Americans who may not yet have access to wired broadband. "However, it is inconsistent with the commission's own data to conclude that deployment is not progressing in a timely and reasonable manner," McCormick said in a statement. Qwest Communications International Inc said there were some remote areas where broadband was not available because of the high cost of deployment but it had applied for federal stimulus funds to bring broadband to many of these primarily rural communities. (Reporting by John Poirier; Editing by Tim Dobbyn) http://www.reuters.com/article/idUSTRE66I61J20100719  GOP Senators Move to Block FCC on Net Neutrality Declan McCullagh Seven Republican senators have announced a plan to curb the Obama administration's push to impose controversial Net neutrality regulations on the Internet. On Wednesday, Sen. Jim DeMint of South Carolina and six other GOP senators introduced legislation (PDF) that would dramatically limit the Federal Communications Commission's ability to regulate broadband providers. "The FCC's rush to takeover the Internet is just the latest example of the need for fundamental reform to protect consumers," DeMint said in a statement. Without this legislation, DeMint said, the FCC will "impose unnecessary, antiquated regulations on the Internet." The new bill--called the Freedom for Consumer Choice Act, or FCC Act--doesn't eliminate the FCC's power over broadband providers. But that power would be narrowed in scope, and come to resemble the antitrust enforcement power of the Department of Justice. One section, for instance, lets the FCC define "unfair methods of competition" and levy "requirements" on the industry, but only if marketplace competition is inadequate. DeMint's bill is a response to a federal appeals court that unanimously ruled earlier this year that the FCC's attempt to slap Net neutrality regulations on Internet providers--in a case that grew out of Comcast throttling BitTorrent transfers--was not authorized by Congress. The opinion called the FCC's claims "flatly inconsistent" with the law. Soon after the appeals court's ruling, the FCC announced plans to reclassify broadband service as a telecommunications service, effectively importing a subset of the regulations designed for the analog phone system to the Internet. Supporters of Net neutrality say new Internet regulations or laws are necessary to prevent broadband providers from restricting content or prioritizing one type of traffic over another. Broadband providers and many conservative and free-market groups, on the other hand, say some of the proposed regulations would choke off new innovations and could even require awarding e-mail spam and telemedicine identical priorities. A broadband industry representative, who did not want to be identified by name, said DeMint's measure turns the current debate upside-down. Currently, that person said, Net neutrality advocates can invent a "parade of horribles that could happen if the Internet was left unregulated." But under the DeMint bill, the FCC and Net neutrality advocates "would need to prove a tangible consumer benefit in order to impose new regulation." New regulation would only be permitted if the FCC can demonstrate that "marketplace competition is not sufficient to adequately protect consumer welfare" and the lack of competition "causes or is likely to cause substantial injury to consumers." (If the FCC decides to impose regulations without sufficient proof, look for broadband providers to file a lawsuit.) Art Brodsky of Public Knowledge, one of the more prominent supporters of Net neutrality regulations, told CNET that: "No one wants to regulate the Internet. They start from that premise, which is mistaken." The bill takes a wrong turn, Brodsky said, by "duplicating the jurisdiction and purpose" of the Department of Justice and the Federal Trade Commission, which share antitrust authority. A Republican Senate source who's familiar with the thinking of the bill's supporters said the intent is to go further than merely curbing Net neutrality regulations. The DeMint bill is in response to the FCC's announcement of reclassification--it's "meant to impose a whole new framework on the FCC so that they can't impose any new rules unless they find that a market failure led to ongoing consumer harm, and not just in the Net neutrality context, but in any rule making," the source said. Kyle McSlarrow, president of the cable lobby group NCTA, said in e-mail to CNET that his group commends DeMint. "This legislation represents a valuable addition to the debate over how best to modernize the regulatory framework governing broadband services and how best to continue policies that promote growth of broadband and the development of innovative Internet services," McSlarrow said. In theory, many Democrats favor Net neutrality. President Obama recently reiterated through a spokesman that he remains "committed" to the idea, as have some Democratic committee chairmen. But theory doesn't always mesh with political practice. More than 70 House Democrats sent a letter to FCC Chairman Julius Genachowski instructing him to abandon his Net neutrality plans. A majority of Congress now opposes Genachowski's proposals. Other sponsors of the FCC Act, all Republicans, are Orrin Hatch of Utah; John Ensign of Nevada; John Thune of South Dakota; Tom Coburn of Oklahoma); John Cornyn of Texas; and Jeff Sessions of Alabama. http://news.cnet.com/8301-13578_3-20011269-38.html  In a World of Online News, Burnout Starts Younger Jeremy W. Peters In most newsrooms, the joke would have been obvious. It was April Fools’ Day last year, and Politico’s top two editors sent an e-mail message to their staff advising of a new 5 a.m. start time for all reporters. “These pre-sunrise hours are often the best time to reach top officials or their aides,” the editors wrote, adding that reporters should try to carve out personal time “if you need it,” in the midafternoon when Internet traffic slows down. But rather than laugh, more than a few reporters stared at the e-mail message in a panicked state of disbelief. “There were several people who didn’t think it was a joke. One girl actually cried,” said Anne Schroeder Mullins, who wrote for Politico until May, when she left to start her own public relations firm. “I definitely had people coming up to me asking me if it was true.” Such is the state of the media business these days: frantic and fatigued. Young journalists who once dreamed of trotting the globe in pursuit of a story are instead shackled to their computers, where they try to eke out a fresh thought or be first to report even the smallest nugget of news — anything that will impress Google algorithms and draw readers their way. Tracking how many people view articles, and then rewarding — or shaming — writers based on those results has become increasingly common in old and new media newsrooms. The Christian Science Monitor now sends a daily e-mail message to its staff that lists the number of page views for each article on the paper’s Web site that day. The New York Times, The Washington Post and The Los Angeles Times all display a “most viewed” list on their home pages. Some media outlets, including Bloomberg News and Gawker Media, now pay writers based in part on how many readers click on their articles. Once only wire-service journalists had their output measured this way. And in a media environment crowded with virtual content farms where no detail is too small to report as long as it was reported there first, Politico stands out for its frenetic pace or, in the euphemism preferred by its editors, “high metabolism.” The top editors, who rise as early as 4:30 a.m., expect such volume and speed from their reporters because they believe Politico’s very existence depends, in large part, on how quickly it can tell readers something, anything they did not know. “At a paper, your only real stress point is in the evening when you’re actually sitting there on deadline, trying to file,” said Jim VandeHei, Politico’s executive editor, in an interview from the publication’s offices just across the Potomac River from downtown Washington. “Now at any point in the day starting at 5 in the morning, there can be that same level of intensity and pressure to get something out.” (Not all reporters are expected to be on their game by dawn, Mr. VandeHei added, noting that many work a traditional 10 a.m. to 7 p.m. newspaper day.) At Gawker Media’s offices in Manhattan, a flat-screen television mounted on the wall displays the 10 most-viewed articles across all Gawker’s Web sites. The author’s last name, along with the number of page views that hour and over all are prominently shown in real time on the screen, which Gawker has named the “big board.” “Sometimes one sees writers just standing before it, like early hominids in front of a monolith,” said Nick Denton, Gawker Media’s founder. Mr. Denton said not all writers have warmed to the concept. “But the best exclusives do get rewarded,” he added, noting that bonuses for writers are calculated in part based on page views. The pace has led to substantial turnover in staff at digital news organizations. Departures at Politico lately have been particularly high, with roughly a dozen reporters leaving in the first half of the year — a big number for a newsroom that has only about 70 reporters and editors. At Gawker, it is not uncommon for editors to stay on the job for just a year. Physically exhausting assembly-line jobs these are not. But the workloads for many young journalists are heavy enough that signs of strain are evident. “When my students come back to visit, they carry the exhaustion of a person who’s been working for a decade, not a couple of years,” said Duy Linh Tu, coordinator of the digital media program at the Columbia University Graduate School of Journalism. “I worry about burnout.” In Washington, the news cycle promises to become even more frenzied as outlets like The Huffington Post expand their operations there. The Atlantic Media Company, which publishes the National Journal and The Atlantic, plans to hire 30 new journalists for a new venture set to open this fall that will publish breaking news and analysis online. At Politico, Mr. VandeHei, who has been known to pace between rows of reporters’ desks asking who has broken news lately, said editors experimented with monitoring how many articles reporters were writing, but decided that raw numbers did not give a full picture of a reporter’s performance. But output matters. An unofficial credo around the office is “W.W.M.D.,” short for “What Would Mikey Do?” It refers to Politico’s famously indefatigable front man, Mike Allen, who is known to wake up at 2 or 3 a.m. to start work on his daily newsletter, Playbook. Politico editors talk about losing their audience as if it could happen at any moment. “Everybody in the audience is his or her own editor based on where they want to move their mouse or their finger on the iPad,” said the editor in chief, John F. Harris. “And if you’re not delivering to that reader, you’re going to lose them.” It is not uncommon for reporters to awaken to find e-mail messages from either Mr. VandeHei or Mr. Harris — sent before dawn — asking why the competition had a story Politico did not. Both men, former Washington Post reporters, harbor deep aversions to the inefficiencies that can burden large news organizations. “That’s one of the reasons we were very attracted to starting our own thing,” Mr. Harris said. “We just felt like you could start from scratch and build a culture that doesn’t have those bad habits already cooked into it.” But some former reporters described feeling overtaxed at times. “Sometimes you felt like it was just too much, whether it’s the workload, the pressure,” said Helena Andrews, a former Politico reporter who left to write a memoir. “I think that some people felt like they were sinking. It was like boot camp, the Politico. But I know a lot of people were proud they survived.” Many of Politico’s reporters are in their 20s, enticed by jobs where starting pay can be around $40,000 for the promise of working at a news organization that influences the conversation among Washington’s elite. Mr. VandeHei and Mr. Harris say they know that reporters can feel pressured at times. But they said the notion of Politico as a journalistic sweatshop is pure myth. Still, Politico management seems to be trying to soften some of its rough edges. Employees recently received an e-mail message informing them that they had been entered in a drawing to win an iPad. The catch: they would all be required to wear a name tag for a day in the spirit of fostering friendly workplace conversation. http://www.nytimes.com/2010/07/19/bu...a/19press.html  The Art of Trolling: Inside a 4chan Smear Campaign Adrian Chen Last night, the users of 4Chan.org's notorious /b/ message board declared war on the lead singer of an obscure electro-pop band. More than 12 hours later, they're still waging it. This is how the Internet's worst trolls work. This week, 4Chan's /b/ board launched an Internet gang-up on an 11-year-old girl, Jessi Slaughter, who had been the target of dubious Internet rumors about an underage sex scandal. They posted her real name, phone number, address and social networking information and spearheaded a campaign of Internet and real-life harassment. They made her cry. /b/'s denizens have turned their ire now on 25 year-old Dahvie Vanity, the other half of that very likely made-up scandal. Vanity is the lead singer of the terrible electro-pop MySpace band Blood on the Dance Floor (Sample lyric:"I'll fuck you in the face/and leave a nice taste.") Now, /b/ has sworn to destroy him. 4chan's /b/ message board is ground zero for Internet mischief. Some of their most famous pranks include sending Justin Bieber to North Korea, flooding YouTube with porn and getting 4cha.org's founder, Christopher Poole, voted Time's most influential person. /b/'s campaign against Dahvie Vanity—dubbed "Operation: The Consequences"—is a good case study in how these often impressive, sometimes awful feats are pulled off. I've been following the trolling operation since it began last night on /b/, watching as it moved from /b/ to chatrooms to the inbox of the Orlando Police Department. Here's how it's unfolded so far: Sometime last night after 10pm, a /b/ user posted a proposition that the board's users troll the "pedophile" Dahvie Vanity. 4chan was still basking in its earlier harassment of Jessi Slaughter, so users quickly got on board—the thread exploded with suggestions and encouragement accompanied by unrelated pictures of boobs. One user compiled a dossier of Dahvie's personal information—name, date of birth, links to his social networking profiles and articles about him. Someone posted a link to a chatroom. When I entered it, about 44 users were chattering in all caps about how to take Vanity down. (If you typed in lowercase a flurry of users scolded: "CAPS OR GET BANNED.") This is where most of the detailed planning would occur, with users frequently posting to the main /b/ board for reinforcements. The early plans thrown around were the most technically ambitious, involving hacking into Vanity's MySpace or email accounts. Since users had found Dahvie Vanity's real name, date of birth and home state, the only thing they needed to reset the password on one of his email accounts (which one was unclear) was the answer to his security question: Name of first pet. One person posted the question to Yahoo! Answers, hoping some deeply obsessed fangirl would know the name of Vanity's first cat. Another one impersonated a fan and emailed Dahvie himself: "i just got a new cat and i wanted to name it after a pet you've had because i love you." Then they posted the email: None of these deception tactics worked. "What happened to the old 4chan where everyone was a hax0r," griped one user. "They're all Tumblr fags now," replied another. So they decided to launch a more pedestrian attack on Vanity's Internet reputation by Googlebombing him. Googlebombing consists of artificially boosting the number of searches for a term so it shows up in Google Hot Trends. (The origin of the virulent Justin Bieber syphilis rumor.) The phrase in this case was "Dahvie Vanity raped Jessica [redacted]"—Jessica being Jessi Slaughter, 4chan's earlier victim. The bomb was primed with a post on /b/ telling users to type the phrase into Refreshthing, a website which can automatically Google a phrase once every five seconds. Users also created scores of pages on the crowdsourcing service Yahoo! Answers, asking questions like "Did Dahvie Vanity actually rape a girl?" Hey, just asking! This afternoon, talk in the chatroom turned to trolling Dahvie In Real Life. IRL trolling is reserved for only /b/'s most hated enemies, but throughout the night, users had decided unequivocally that Dahvie was a serial rapist and a pedophile. They wanted to get him arrested. A couple of users emailed the Orlando police department, pretending to be worried parents who had heard rumors of Vanity molesting underage children. They posted the email: One user emailed Gurl, an online community for teen girls, telling them that they had been molested by Vanity. Another had the inspired the idea to email Westboro Baptist Church, I guess in the hopes that they'll protest outside his house or something. And that's basically where things stand as of this posting. 4chan has been having site problems for the last few hours, so Operation: The Consequences is in a holding pattern, unable to summon the full force of 4chan's user base. But the chat room still has 22 users. And this is what they're talking about: [14:38] anonymousey: damn internet, you scary :/ [14:38] anonymousey: i would never want to be on the reciving end of us [14:38] anonymousey: i'll just say that much [14:38] cyahnidde: lol same [14:38] cyahnidde: we are like...some kind of internet hate machine This is the chat room. Dare you to troll it. Update: Chat room: Trolled. Shots: Fired. http://gawker.com/5589721/  11-Year-Old Viral Video Star Placed Under Police Protection After Death Threats Adrian Chen Earlier this week, a funny video went viral of 11-year-old Jessi Slaughter (AKA Kerligirl13) crying while her dad yelled at the people trolling her on the Internet. It's not so funny now that she's been placed under police protection. More than 1.7 million people have seen the foul-mouthed Floridan's breakdown and laughed at her dad's luddite rage. But the video, "You Dun Goofed Up," wasn't the only thing to go viral: Jessi Slaughter's real name, address and phone number was distributed widely via Internet pranksters 4chan.org, Tumblr and other online backchannels. (Read the full back-story here.) We spoke with Jessi's mother, Dianne Leonhardt, on the phone today. She tells us the family has received a slew harassing phone calls since the video went viral Thursday. According to Leonhardt, some of those phone calls have been death threats, and the local sheriff's department has launched a criminal investigation into the video. Jessi was placed under police protection and brought to a safe house soon after it went viral. She came home today, but she's not online: A court order has barred her from using the Internet for at least three days. So far, things haven't escalated past phone calls and online vandalism of Jessi's social-networking accounts. But Leonhardt says the family's life has been completely upended by a stream of prank calls." I've had people calling, impersonating themselves as cops, as child protection services," she says. Though Leonhardt says Child Protection Services is in fact involved in the case. "Something we never wanted!" Leonhardt's husband shouted from somewhere in the room when she told us this over the phone. Leonhardt says the family is under "24/7 police surveillance" but still doesn't feel safe knowing that anyone on the Internet could have their home address. "We've had may, many death threats," she says. "We're afraid to leave the house. We're afraid to go to bed. We're sleeping in shifts, my husband and I am." Above all, Leonhardt says, "I wan't my life back. I want my daughter's life back." Pre-teen or not, Jessi isn't an entirely passive player in this. The freakout in "You Dun Goofed" was over harassment sparked by one of Jessi's earlier videos that had also gone viral, to a lesser extent: An astonishingly profane rant in which Jessi tells Internet haters to "suck my non-existent penis" and "Get AIDS and die" and hurls epithets no 11-year-old should know. What does her mother think of it? "I haven't seen it," she says. "I don't even go on the computer." (The Leonhardt's local sheriff's department couldn't be reached for comment.) http://gawker.com/5590166/11+year+ol...-death-threats  Policing the Web’s Lurid Precincts Brad Stone Ricky Bess spends eight hours a day in front of a computer near Orlando, Fla., viewing some of the worst depravities harbored on the Internet. He has seen photographs of graphic gang killings, animal abuse and twisted forms of pornography. One recent sighting was a photo of two teenage boys gleefully pointing guns at another boy, who is crying. An Internet content reviewer, Mr. Bess sifts through photographs that people upload to a big social networking site and keeps the illicit material — and there is plenty of it — from being posted. His is an obscure job that is repeated thousands of times over, from office parks in suburban Florida to outsourcing hubs like the Philippines. With the rise of Web sites built around material submitted by users, screeners have never been in greater demand. Some Internet firms have tried to get by with software that scans photos for, say, a large area of flesh tones, but nothing is a substitute for a discerning human eye. The surge in Internet screening services has brought a growing awareness that the jobs can have mental health consequences for the reviewers, some of whom are drawn to the low-paying work by the simple prospect of making money while looking at pornography. “You have 20-year-old kids who get hired to do content review, and who get excited because they think they are going to see adult porn,” said Hemanshu Nigam, the former chief security officer at MySpace. “They have no idea that some of the despicable and illegal images they will see can haunt them for the rest of their lives.” David Graham, president of Telecommunications On Demand, the company near Orlando where Mr. Bess works, compared the reviewers to “combat veterans, completely desensitized to all kinds of imagery.” The company’s roughly 50 workers view a combined average of 20 million photos a week. Mr. Bess insists he is still bothered by the offensive material, and acknowledges the need to turn to the cubicle workers around him for support. “We help each other through any rough spots we have,” said Mr. Bess, 52, who previously worked in the stockrooms at Wal-Mart and Target. Last month, an industry group established by Congress recommended that the federal government provide financial incentives for companies to “address the psychological impact on employees of exposure to these disturbing images.” Mr. Nigam, co-chairman of the group, the Online Safety and Technology Working Group, said global outsourcing firms that moderate content for many large Internet companies do not offer therapeutic care to their workers. The group’s recommendations have been submitted to the National Telecommunications and Information Administration, which advises the White House on digital policy. Workers at Telecommunications On Demand, who make $8 to $12 an hour, view photos that have been stripped of information about the users who posted them. Rapidly cycling through pages of 300 images each, they are asked to flag material that is obviously pornographic or violent, illegal in a certain country or deemed inappropriate by a specific Web site. Caleris, an outsourcing company based in West Des Moines, Iowa, says it reviews about 4.5 million images a day. Stacey Springer, its vice president for support operations, says the job is not for everybody and that “people find they can do it, but it is usually a lot harder than they thought.” The company offers counseling as part of its standard benefits package for workers. Ms. Springer says she believes that content moderators tend to become desensitized to the imagery, making it easier to cope. But she is called on to review the worst material, like sexual images involving children, and says that she finds some of it “hard to walk away from.” “I do sometimes take it really personally,” she said of the pictures she reviews. “I remind myself, somebody has to do it.” A common strategy at Web sites is to have users flag questionable content, then hand off material that needs further human review to outsourcing companies that can do so at low cost. Global outsourcing firms like Infosys Technologies, based in Bangalore, India, and Sykes Enterprises, based in Tampa, Fla., have leapt to offer such services. Internet companies are reluctant to discuss the particulars of content moderation, since they would rather not draw attention to the unpleasantness that their sites can attract. But people in the outsourcing industry say tech giants like Microsoft, Yahoo and MySpace, a division of the News Corporation, all outsource some amount of content review. YouTube, a division of Google, is an exception. If a user indicates a video is inappropriate, software scans the image looking for warning signs of clips that are breaking the site’s rules or the law. Flagged videos are then sent for manual review by YouTube-employed content moderators who, because of the nature of the work, are given only yearlong contracts and access to counseling services, according to Victoria Grand, a YouTube spokeswoman. For its part, Facebook, the dominant social network with more than 500 million members around the world, has relied on its users to flag things like pornography or harassing messages. That material is reviewed by Facebook employees in Palo Alto, Calif., and in Dublin. Simon Axten, a Facebook spokesman, said the company had tried outsourcing the manual review of photos but had not done so widely. Outsourcing companies are also reluctant to discuss the business on the record, since their clients demand confidentiality. One executive at a global outsourcing firm, who did not want to be named, said that large Internet firms “are paying millions a year to do this kind of thing and essentially provide some type of control over the beast that is the Internet, which for the most part is uncontrollable.” “If they don’t do it, their commercial interests will completely die,” he added. One major outsourcing firm with staff in the Philippines was aware of the risks of this type of work and hired a local psychologist to assess how it was affecting its 500 content moderators. The psychologist, Patricia M. Laperal of Behavioral Dynamics, said she had developed a screening test so the company could evaluate potential employees, and helped its supervisors identify signals that the work was taking a toll on employees. Ms. Laperal also reached some unsettling conclusions in her interviews with content moderators. She said they were likely to become depressed or angry, have trouble forming relationships and suffer from decreased sexual appetites. Small percentages said they had reacted to unpleasant images by vomiting or crying. “The images interfere with their thinking processes. It messes up the way you react to your partner,” Ms. Laperal said. “If you work with garbage, you will get dirty.” Carlos Conde contributed reporting. http://www.nytimes.com/2010/07/19/te.../19screen.html  China Satisfied with Google Search Engine Tweak China is satisfied that U.S. Internet giant Google Inc is complying with Chinese laws after it tweaked the way it directs users to an unfiltered search page, a senior official said on Tuesday. The comments from a Ministry of Industry and Information official largely echoed previous Chinese statements, but are still likely to be seen as good news for the company as Beijing has been coy about its long-term future in China. Google is also in the process of ending its partnership with Chinese community site Tianya, in which it owns a stake, the firm said in a blog post on Tuesday. "As it was announced earlier this year, this week we will be ending technical cooperation with Tianya on Tianya Come and Tianya Questions," Google said in its official Chinese language blog. (here) Google bought the stake in Tianya.cn in August 2007. Google is trying to achieve the delicate balance of ending self-censorship of searches while holding onto its business foothold in a country where control of information has been key to ensuring the Communist Party's decades in power. Google's market share in China continued to slip in the second quarter, falling to 27.3 percent from 29.5 percent in the first, according to data from research firm iResearch. Before its high-profile spat with Beijing, Google was slowly gaining ground on China's top search engine Baidu. At the end of last year, Google's market share was 32.8 percent. Guxiang, a company that operates Google's websites in China, had committed to "abide by Chinese law," and ensure the company did not provide illegal content, said Zhang Feng, head of the ministry's communication development division. "After examination, we have concluded that it has basically met the requirements according to the relevant laws and regulations," Zhang told a news conference. Google unexpectedly warned in January it might quit China over censorship concerns and after suffering a hacker attack it said came from within the country, but eventually terminated its Google.cn search service and started rerouting users to its unfiltered Hong Kong site. In early July the company ended automatic redirection, saying Beijing was unhappy about the system and would not renew Google's operating license if it continued. Visitors are now invited to click through to the Hong Kong page instead of being sent straight there. China's firewall remains in place however, meaning most sensitive sites turned up on searches are inaccessible from within the country's borders. Google's move was seen as a sign that the firm would fight to hold onto as much of its China business as possible, and Beijing said earlier this month it had renewed its Chinese operating license after the company "made improvements." Guxiang accepted that government regulators will have the right to supervise content provided by the firm, Zhang said, declining to comment directly on Google's provision of the link to its uncensored Hong Kong page. "As for the question of Hong Kong, this is an operational act made by the company itself," he added, without elaborating. China's decision to allow Google to continue operating in China apparently resolved a months-long censorship dispute that had threatened the U.S. company's future in the world's top Internet market by users. The move also removed another thorn in U.S.-China relations and reflects Beijing's desire to be seen as friendly to major foreign firms in spite of ideological differences, analysts said. (Reporting by Ben Blanchard and Melanie Lee; Editing by Ken Wills and Alex Richardson) http://www.reuters.com/article/idUSTRE66J0MS20100720  Attackers Moving to Social Networks For Command and Control Dennis Fisher Bot herders and the crimeware gangs behind banker Trojans have had a lot of success in the last few years with using bulletproof hosting providers as their main base of operations. But more and more, they're finding that social networks such as Twitter and Facebook are offering even more fertile and convenient grounds for controlling their malicious creations. New research from RSA shows that the gangs behind some of the targeted banker Trojans that are such a huge problem in some countries, especially Brazil and other South American nations, are moving quietly and quickly to using social networks as the command-and-control mechanisms for their malware. The company's anti-fraud researchers recently stumbled upon one such attack in progress and watched as it unfolded. The attack is as simple as it is effective. It begins with the crimeware gang setting up one or more fake profiles on a given social network (RSA isn't naming the network on which it saw this specific attack). The attacker then posts a specific set of encrypted commands to the profile. When a new machine is infected with the banker Trojan, the malware then goes out and checks the profile for new commands. The specific command in this case begins with a string of random characters that serves as an authentication mechanism of sorts, letting the Trojan know it's found the right commands. The rest of the encrypted string are hard-coded instructions telling the Trojan what to do next, whether it's to look for other machines on the network, search for saved data or log keystrokes when the user visits a specific online banking site. This certainly is not the first example of this kind of activity on social networks. There have been botnets controlled via Twitter for at least a year now, and researchers have found a number of example of Facebook profiles set up specifically for malicious activity. But this is one of the results of the success that researchers and law enforcement have had in recent years in shutting down the bulletproof hosting providers who have been harboring botnet C&C servers and Trojan drop zones for a long time. "The most interesting thing is that it's part of a growing trend. These groups have had four main options for hosting if they want to put it in a resilient infrastructure," said Uri Rivner, head of new technologies--consumer identity protection at RSA, the security division of EMC. "You can build your own, and there are some that are very sophisticate with great disaster recovery, but that's expensive. You can go with bulletproof hosting, but that's getting harder. You can use cloud services, which we've seen some of lately. Or you can now use social networks. That's getting more popular because resilience is they key for some of these Trojans that can run for months or years. It's so important to them to find a good hosting environment." The other thing that makes networks such as Twitter and Facebook attractive for bot herders and Trojan gangs is the ease with which they can set up new profiles. The profiles themselves essentially become disposable, because the attackers can code a list of dozens or hundreds of such profiles into the Trojan and if one is discovered and taken offline, the malware move on to the next one. It's also quite difficult for the operators of these sites to identify and block these profiles quickly enough, making them soft targets for the attackers. "The only downside for the attackers is if the companies start fighting back against it, but that's hard," Rivner said. "This is the easiest, the cheapest and most reliable infrastructure that I see." http://threatpost.com/en_us/blogs/at...control-071910  Dell Accidentally Sent out Malware-Riddled Motherboards Nick Mokey A hiccup at Dell’s service parts department saw a number of motherboards with malware-infected firmware go out the door to customers. Like patients who enter the hospital for a simple tonsillectomy and end up leaving with pneumonia, it seems like customers seeking help from Dell’s service parts department may have made things worse for themselves, while trying to make things better. The company admits it may have sent out a number of motherboards with malware lurking within their firmware. According to Dell itself, the infection affects only a “small number” of motherboards, which were sent out through service dispatches. The malware in question has shown up on the embedded server management firmware on the PowerEdge motherboards. “To date we have received no customer reports related to data security,” a Dell representative said on the company’s own support forums. “Systems running non-Windows operating systems are not vulnerable to this malware and this issue is not present on motherboards shipped new with PowerEdge systems.” Since all the boards were sent out through service dispatches, Dell apparently has a list of customer e-mails and will be contacting owners of potentially infected boards directly. Since the issue has been limited to the company’s enterprise-level PowerEdge servers, consumers have nothing to worry about. http://www.digitaltrends.com/computi...-motherboards/  WPA2 Vulnerability Found 'Hole 196' means malicious insiders could spoof WI-Fi packets, compromise WLAN Joanie Wexler Perhaps it was only a matter of time. But wireless security researchers say they have uncovered a vulnerability in the WPA2 security protocol, which is the strongest form of Wi-Fi encryption and authentication currently standardized and available. Malicious insiders can exploit the vulnerability, named "Hole 196" by the researcher who discovered it at wireless security company AirTight Networks. The moniker refers to the page of the IEEE 802.11 Standard (Revision, 2007) on which the vulnerability is buried. Hole 196 lends itself to man-in-the-middle-style exploits, whereby an internal, authorized Wi-Fi user can decrypt, over the air, the private data of others, inject malicious traffic into the network and compromise other authorized devices using open source software, according to AirTight. The researcher who discovered Hole 196, Md Sohail Ahmad, AirTight technology manager, intends to demonstrate it at two conferences taking place in Las Vegas next week: Black Hat Arsenal and DEF CON 18. The Advanced Encryption Standard (AES) derivative on which WPA2 is based has not been cracked and no brute force is required to exploit the vulnerability, Ahmad says. Rather, a stipulation in the standard that allows all clients to receive broadcast traffic from an access point (AP) using a common shared key creates the vulnerability when an authorized user uses the common key in reverse and sends spoofed packets encrypted using the shared group key. Ahmad explains it this way: WPA2 uses two types of keys: 1) Pairwise Transient Key (PTK), which is unique to each client, for protecting unicast traffic; and 2) Group Temporal Key (GTK) to protect broadcast data sent to multiple clients in a network. PTKs can detect address spoofing and data forgery. "GTKs do not have this property," according to page 196 of the IEEE 802.11 standard. These six words comprise the loophole, Ahmad says. Because a client has the GTK protocol for receiving broadcast traffic, the user of that client device could exploit GTK to create its own broadcast packet. From there, clients will respond to the sending MAC address with their own private key information. Ahmad says it took about 10 lines of code in open source MadWiFi driver software, freely available on the Internet, and an off-the-shelf client card for him to spoof the MAC address of the AP, pretending to be the gateway for sending out traffic. Clients who receive the message see the client as the gateway and "respond with PTKs", which are private and which the insider can decrypt, Ahmad explains. From there, "the malicious insider could drop traffic, drop a [denial-of-service] attack, or snoop," Ahmad says. The ability to exploit the vulnerability is limited to authorized users, AirTight says. Still, year-after-year security studies show that insider security breaches continue to be the biggest source of loss to businesses, whether from disgruntled employees or spies who steal and sell confidential data. What can we do about Hole 196? "There's nothing in the standard to upgrade to in order to patch or fix the hole," says Kaustubh Phanse, AirTight's wireless architect who describes Hole 196 as a "zero-day vulnerability that creates a window of opportunity" for exploitation. http://www.networkworld.com/newslett...wireless1.html  I Know Who Your Name, Where You Work, and Live (Safari v4 & v5) Jeremiah Grossman Right at the moment a Safari user visits a website, even if they’ve never been there before or entered any personal information, a malicious website can uncover their first name, last name, work place, city, state, and email address. Safari v4 & v5, with a combined market browser share of 4% (~83 million users), has a feature (Preferences > AutoFill > AutoFill web forms) enabled by default. Essentially we are hacking auto-complete functionality. This feature AutoFill’s HTML form text fields that have specific attribute names such as name, company, city, state, country, email, etc. <* form> <* input type="text" name="name"> <* input type="text" name="company"> <* input type="text" name="city"> <* input type="text" name="state"> <* input type="text" name="country"> <* input type="text" name="email"> <* /form> These fields are AutoFill’ed using data from the users personal record in the local operating system address book. Again it is important to emphasize this feature works even though a user never entered this data on any website. Also this behavior should not be confused with normal auto-complete data a Web browser may remember after its typed into a form. All a malicious website would have to do to surreptitiously extract Address Book card data from Safari is dynamically create form text fields with the aforementioned names, probably invisibly, and then simulate A-Z keystroke events using JavaScript. When data is populated, that is AutoFill’ed, it can be accessed and sent to the attacker. As shown in the proof-of-concept code (graciously hosted by Robert "RSnake" Hansen), the entire process takes mere seconds and represents a major breach in online privacy. This attack could be further leveraged in multistage attacks including email spam, (spear) phishing, stalking, and even blackmail if a user is de-anonymized while visiting objectionable online material. Fortunately any AutoFill data starting with a number, such as phone numbers or street addresses, could not be obtained because for some reason the data would not populate in the text field. Still, such attacks could be easily and cheaply distributed on a mass scale using an advertising network where likely no one would ever notice because it’s not exploit code designed to deliver rootkit payload. In fact, there is no guarantee this has not already taken place. What is safe to say is that this vulnerability is so brain dead simple that I assumed someone else must have publicly reported it already, but exhaustive searches and asking several colleagues turned up nothing. I figured Apple might appreciate a vulnerability disclosure prior to public discussion, which I did on June 17, 2010 complete with technical detail. A gleeful auto-response came shortly after, to which I replied asking if Apple was already aware of the issue. I received no response after that, human or robot. I have no idea when or if Apple plans to fix the issue, or even if they are aware, but thankfully Safari users only need to disable AutoFill web forms to protect themselves. http://jeremiahgrossman.blogspot.com...-work-and.html  Wal-Mart Radio Tags to Track Clothing Miguel Bustillo Wal-Mart Stores Inc. (WMT - News) plans to roll out sophisticated electronic ID tags to track individual pairs of jeans and underwear, the first step in a system that advocates say better controls inventory but some critics say raises privacy concerns. Starting next month, the retailer will place removable "smart tags" on individual garments that can be read by a hand-held scanner. Wal-Mart workers will be able to quickly learn, for instance, which size of Wrangler jeans is missing, with the aim of ensuring shelves are optimally stocked and inventory tightly watched. If successful, the radio-frequency ID tags will be rolled out on other products at Wal-Mart's more than 3,750 U.S. stores. "This ability to wave the wand and have a sense of all the products that are on the floor or in the back room in seconds is something that we feel can really transform our business," said Raul Vazquez, the executive in charge of Wal-Mart stores in the western U.S. Before now, retailers including Wal-Mart have primarily used RFID tags, which store unique numerical identification codes that can be scanned from a distance, to track pallets of merchandise traveling through their supply chains. Wal-Mart's broad adoption would be the largest in the world, and proponents predict it would lead other retailers to start using the electronic product codes, which remain costly. Wal-Mart has climbed to the top of the retailing world by continuously squeezing costs out of its operations and then passing on the savings to shoppers at the checkout counter. Its methods are widely adopted by its suppliers and in turn become standard practice at other retail chains. But the company's latest attempt to use its influence—executives call it the start of a "next-generation Wal-Mart"—has privacy advocates raising questions. While the tags can be removed from clothing and packages, they can't be turned off, and they are trackable. Some privacy advocates hypothesize that unscrupulous marketers or criminals will be able to drive by consumers' homes and scan their garbage to discover what they have recently bought. They also worry that retailers will be able to scan customers who carry new types of personal ID cards as they walk through a store, without their knowledge. Several states, including Washington and New York, have begun issuing enhanced driver's licenses that contain radio- frequency tags with unique ID numbers, to make border crossings easier for frequent travelers. Some privacy advocates contend that retailers could theoretically scan people with such licenses as they make purchases, combine the info with their credit card data, and then know the person's identity the next time they stepped into the store. "There are two things you really don't want to tag, clothing and identity documents, and ironically that's where we are seeing adoption," said Katherine Albrecht, founder of a group called Consumers Against Supermarket Privacy Invasion and Numbering and author of a book called "Spychips" that argues against RFID technology. "The inventory guys may be in the dark about this, but there are a lot of corporate marketers who are interested in tracking people as they walk sales floors." Smart-tag experts dismiss Big Brother concerns as breathless conjecture, but activists have pressured companies. Ms. Albrecht and others launched a boycott of Benetton Group SpA last decade after an RFID maker announced it was planning to supply the company with 15 million RFID chips. Benetton later clarified that it was just evaluating the technology and never embedded a single sensor in clothing. Wal-Mart is demanding that suppliers add the tags to removable labels or packaging instead of embedding them in clothes, to minimize fears that they could be used to track people's movements. It also is posting signs informing customers about the tags. "Concerns about privacy are valid, but in this instance, the benefits far outweigh any concerns," says Sanjay Sarma, a professor at the Massachusetts Institute of Technology. "The tags don't have any personal information. They are essentially barcodes with serial numbers attached. And you can easily remove them." In Europe some retailers put the smart labels on hang tags, which are then removed at checkout. That still provides the inventory-control benefit of RFID, but it takes away other important potential uses that retailers and suppliers like, such as being able to track the item all the way back to the point of manufacture in case of a recall, or making sure it isn't counterfeit. Wal-Mart won't say how much it expects to benefit from the endeavor. But a similar pilot program at American Apparel Inc. in 2007 found that stores with the technology saw sales rise 14.3% compared to stores without the technology, according to Avery Dennison Corp., a maker of RFID equipment. And while the tags wouldn't replace bulkier shoplifting sensors, Wal-Mart expects they'll cut down on employee theft because it will be easier to see if something's gone missing from the back room. Several other U.S. retailers, including J.C. Penney and Bloomingdale's, have begun experimenting with smart ID tags on clothing to better ensure shelves remain stocked with sizes and colors customers want, and numerous European retailers, notably Germany's Metro AG, have already embraced the technology. Robert Carpenter, chief executive of GS1 U.S., a nonprofit group that helped develop universal product-code standards four decades ago and is now doing the same for electronic product codes, said the sensors have dropped to as little as seven to 10 cents from 50 cents just a few years ago. He predicts that Wal-Mart's "tipping point" will drive prices lower. "There are definitely costs. Some labels had to be modified," said Mark Gatehouse, director of replenishment for Wrangler jeans maker VF Corp., adding that while Wal-Mart is subsidizing the costs of the actual sensors, suppliers have had to invest in new equipment. "But we view this as an investment in where things are going. Everyone is watching closely because no one wants to be at a competitive disadvantage, and this could really lift sales." Wal-Mart won't disclose what it's spending on the effort, but it confirms that it is subsidizing some of the costs for suppliers. Proponents, meanwhile, have high hopes for expanded use in the future. Beyond more-efficient recalls and loss prevention, RFID tags could get rid of checkout lines. "We are going to see contactless checkouts with mobile phones or kiosks, and we will see new ways to interact, such as being able to find out whether other sizes and colors are available while trying something on in a dressing room," said Bill Hardgrave, head of the RFID Research Center at the University of Arkansas, which is funded in part by Wal-Mart. "That is where the magic is going to happen. But that's all years away." http://finance.yahoo.com/family-home...track-clothing  EU Authorities: Implementation of Net Surveillance Directive Is Unlawful Katitza Rodriguez In a landmark announcement issued today, the data protection officials across the European Union found that the way that EU Member States have implemented the data retention obligations in the 2006 EU Data Retention Directive is unlawful. The highly controversial 2006 EU Data Retention Directive compels all ISPs and telecommunications service providers operating in Europe to retain telecom and internet traffic data about all of their customers' communications for a period of at least 6 months and up to 2 years. European privacy officials from the Article 29 Data Protection Working Party have been reviewing how the EU Member States have implemented these obligations in their national laws. Among the most important findings of the Article 29 Working Party’s report are: * "Service providers were found to retain and hand over data in ways contrary to the provisions of the [data retention] directive." * "There are significant discrepancies regarding the retention periods, which vary from six months to up to ten years, which largely exceeds the allowed maximum of 24 months." * "More data are being retained than is allowed. The data retention directive provides a limited list of data to be retained, all relating to traffic data. The retention of data relating to the content of communication is explicitly prohibited. However, it appears from the inquiry that some of these data are nevertheless retained." * Regarding Internet traffic data: "Several service providers were found to retain URLs of websites, headers of e-mail messages as well as recipients of e-mail messages in "CC"- mode at the destination mail server. * Regarding phone traffic data: "it was established that not only the location of the caller is retained at the start of the call, but that his location is being monitored continuously." * "Member states have scarcely provided statistics on the use of data retained under the Directive, which limits the possibilities to verify the usefulness of data retention." * "The provisions of the data retention directive are not respected and the lack of available sensible statistics hinders the assessment of whether the directive has achieved its objectives." The timing of the Article 29 Working Party’s opinion is particularly sensitive because the European Commission is currently conducting an evaluation of the impact of the Data Retention Directive on economic operators and citizens in Europe. One of the possible outcomes of this evaluation is a recommendation that the Data Retention Directive should be amended or repealed in its entirety. The Article 29 Working Party has submitted its report to the European Commission to provide the Commission with vital empirical evidence for its evaluation of whether to recommend the amendment or repeal the Directive. Once completed, the Commission’s evaluation will be sent to the European Parliament and the Council of Ministers. Reflecting the far-reaching impact and sensitive policy issues involved in the Data Retention Directive, three Commissioners are likely to be engaged in its review. The EU Commissioner for Home Affairs, Commissioner Malmström leads the evaluation process, but it is expected that Vice President of the Commission and EU Commissioner for Justice, Fundamental Rights and Citizenship, Commissoner Reding and the Commissioner for the Digital Agenda, Commissioner Kroes will also participate actively in the review process. EFF, AK Vorrat and a coalition of over 100 organizations across Europe recently called for an end to mandatory data retention of telecom and Internet traffic data. In a joint letter sent last month to European Commissioners Malmström, Reding, and Kroes, the coalition urged the Commissioners to "propose the repeal of the EU requirements regarding data retention in favor of a system of expedited preservation and targeted collection of traffic data as agreed in the Council of Europe's Convention on Cybercrime." In her July 7 reply to the coalition letter, Commissioner Reding stated that, "the review of the EU Data Retention directive provides the European Commission, but also the 27 EU Member States and the European Parliament, with an opportunity to assess the effectiveness and proportionality of the measures included in the Directive. I will in this context ask for a particular focus on the considerable impact data retention may have on fundamental rights of all European citizens, especially with regard to their privacy." With the recent adoption of the Lisbon Treaty and the entry into force of the Charter of Fundamental Rights, privacy and data protection has been strengthened in the European Union, including in the sensitive areas of law enforcement and crime prevention. We must now see whether the European Commission will be faithful to the Charter of Fundamental Rights, and recommend the repeal of the overbroad 2006 Data Retention Directive. http://www.eff.org/deeplinks/2010/07/eu-authorities  Search Top Secret America’s Database of Private Spooks Figuring out exactly who’s cashing in on the post-9/11 boom in secret programs just got a whole lot easier. Spencer Ackerman and Noah Shachtman U.S. spy agencies, the State Department and the White House had a collective panic attack Friday over a new Washington Post exposé on the intelligence-industrial complex. Reporters Dana Priest and William Arkin let it drop Monday morning. It includes a searchable database cataloging what an estimated 854,000 employees and legions of contractors are apparently up to. Users can now to see just how much money these government agencies are spending and where those top secret contractors are located. Check out the Post’s nine-page list of agencies and contractors involved in air and satellite observations, for instance. No wonder it scares the crap out of official Washington: It’s bound to provoke all sorts of questions — both from taxpayers wondering where their money goes and from U.S. adversaries looking to penetrate America’s spy complex. But this piece is about much more than dollars. It’s about what used to be called the Garrison State — the impact on society of a praetorian class of war-focused elites. Priest and Arkin call it “Top Secret America,” and it’s so big and grown so fast, that it’s replicated the problem of disconnection within the intelligence agencies that facilitated America’s vulnerability to a terrorist attack. With too many analysts and too many capabilities documenting too much, with too few filters in place to sort out the useful stuff or discover hidden connections, the information overload has become its own information blackout. “We consequently can’t effectively assess whether it is making us more safe,” a retired Army three-star general who recently assessed the system tells the reporters. The Post — whose editorial page has been notably receptive to the growth of the security state over the years — explains in an editorial comment that it ran its constellation of websites by security officials to ensure that it wasn’t jeopardizing national security. In one instance, the editors deleted certain unspecified specific “data points” the project initially disclosed. The editors further explain that most of what the project documents, like the locations of contractor and agency facilities, is already public information, distributed on company and agency websites. So it’s not as if the paper has put anyone in harm’s way. (Some of those overlapping contracts issued by the “263 organizations [that] have been created or reorganized as a response to 9/11″ might now be in danger, however.) Still, in compiling all this information, there’s a risk that the Post provides a hostile foreign agent looking to infiltrate the U.S. security apparatus with an online yellow pages for sending out his resume. Ironically, the very nature of the phenomenon Priest and Arkin document might be enough to foil an infiltrator. Security agencies and their companies produce more information than anyone can consume, adding uncertain value to the amount of information already public. And the spigot — contained in congressional budgets that are either politically sacrosanct or entirely secret — doesn’t seem to be able to close. One impressed observer told the paper about a useless intel program scheduled for closure: ”Like a zombie, it keeps on living.” That rise in what might be called the counterterrorism-industrial complex is a story we’ve covered since this blog set up shop in 2007, as have many of our friends, because privatized intelligence is one of the major security developments of the last decade-plus. It’s also been enshrouded by near-baroque secrecy. The intelligence community would not even disclose just how many contractors it employs, for instance, until the Post did so. That secrecy has concealed — barely — how inextricable the contractors are from the intelligence community. Take Bill Black, who ended his nearly 40-year career with the National Security Agency in 1997, when he became a vice president of intel contractor SAIC. That lasted for barely two years before Black returned as the agency’s deputy director — with some ideas about which company could revamp NSA’s software. Long story short: Several years and a billion dollars later, the only thing the program yielded was an indictment of a whistleblower accused of leaking info to reporter Siobhan Gorman. That’s been par for the course in the post-9/11 cash-in. Similarly to their military counterparts, intelligence companies (sometimes they’re the same companies) often “bid back” the nation’s spies, enticing veteran intel professionals to the contracting sector with greater salaries — raising the overall price of the U.S. security infrastructure when the spy agencies basically contract out for their old workforce. Want data-mining, or a logic layer for your surveillance architecture? Contractors are often able to take a piece of the job with less red tape getting in the way. Except that the information produced in “Top Secret America” has questionable ability to thwart, capture or kill terrorists. Umar Farouk Abdulmutallab made his way onto Northwest Airlines Flight 253, and only alert passengers prevented him from detonating a bomb in his underwear. In fairness, the law enforcement and intelligence communities have racked up notable successes in recent years, like arresting Najibullah Zazi before, an indictment alleges, he could place suicide bombers in the New York City subway. And the fact remains that the closest thing the nation has experienced to a second 9/11 came from a deranged Army major who shot up Fort Hood in November, a horrific act that killed over a dozen people, but not thousands. Still, this is a critique that resonates: When Maj. Gen. John M. Custer was the director of intelligence at U.S. Central Command, he grew angry at how little helpful information came out of the NCTC. In 2007, he visited its director at the time, retired Vice Adm. John Scott Redd, to tell him so. “I told him that after 4½ years, this organization had never produced one shred of information that helped me prosecute three wars!” he said loudly, leaning over the table during an interview. Um, three wars? Only in Top Secret America … UPDATE: Acting Director of National Intelligence David Gompert just released a wet-noodle response to “Top Secret America.” “The reporting does not reflect the intelligence community we know,” Gompert says in a statement. “We accept that we operate in an environment that limits the amount of information we can share. However, the fact is, the men and women of the intelligence community have improved our operations, thwarted attacks, and are achieving untold successes every day.” Gompert goes on: In recent years, we have reformed the IC in ways that have improved the quality, quantity, regularity, and speed of our support to policymakers, warfighters, and homeland defenders, and we will continue our reform efforts…. We will continue to scrutinize our own operations, seek ways to improve and adapt, and work with Congress on its crucial oversight and reform efforts. We can always do better, and we will. And the importance of our mission and our commitment to keeping America safe will remain steadfast, whether they are reflected in the day’s news or not. In other words: we’re doing just great, and pinching pennies, too. Now stop looking at that database. http://www.wired.com/dangerroom/2010...rivate-spooks/  Why Web Host Shut Down 73,000 Blogs a Mystery Greg Sandoval Blogetery.com, a little-known WordPress platform used by more than 70,000 blogs, was shut down by its Web hosting company more than a week ago and nobody seems willing to say why or who is responsible. BurstNet, the Web-hosting company, informed Blogetery's operator that service was terminated at the request of some law enforcement agency but wouldn't say which one. As for the reason, BurstNet hasn't made that clear either. In an e-mail to Blogetery's operator, BurstNet managers did say that they had little choice but to terminate service. "Please note that this was not a typical case in which suspension and notification would be the norm," BurstNet wrote to Blogetery's operator. "This was a critical matter brought to our attention by law enforcement officials. We had to immediately remove the server." BurstNet executives were not immediately available for comment. Though BurstNet never indicated Blogetery's problems were caused by copyright violations, TorrentFreak, a blog that covers Web file-sharing issues and broke the story, wrote that the U.S. government may be involved as part of stepped-up antipiracy operations. Nearly three weeks ago, a group of federal law enforcement agencies, including the U.S. District Court for the Southern District of New York and the U.S. Immigration and Customs Enforcement (ICE), a unit of the Department of Homeland Security--seized assets and Web sites belonging to people authorities say operated illegal file-sharing sites. President Obama has said his administration is going to get tough on piracy and counterfeiting. But on Sunday, a spokeswoman for ICE said "while ICE's Internet piracy enforcement efforts are still very much ongoing, we were not involved with the action." A spokesman for the Recording Industry Association of America said Sunday that the trade group for the four top record labels had nothing to do with Blogetery's shut down. A spokesman for the Motion Picture Association of America said he had never heard of Blogetery. That the MPAA and RIAA may not be involved makes sense. Typically, they give warnings before they move like this. They also try to make big news out of any enforcement efforts; they want them to act as deterrents. And these trade groups have historically had to file lawsuits, spend millions of dollars, and wait years before convincing courts to shut down such sites as TorrentSpy, Isohuntand Napster. If this was a copyright issue, BurstNet would likely have to deal with the Digital Millennium Copyright Act's safe harbor. This a provision designed to protect Web service providers from being held responsible for copyright violations committed by users. Blogetery's operator said he played by the rules. In the e-mail exchange with BurstNet, the blog platform's operator, said that he always obeyed copyright law. Whenever anyone on his platform was accused of posting links to unauthorized movie or music files, he said he removed the material "within 24 hours." Sure, there's still lots unanswered questions. We don't know which law enforcement agency is involved. We don't know whether BurstNet disconnected Blogetery with proper cause. We don't know for sure whether the reason for the shut down was due to copyright violations. But at this point, it sure doesn't appear to be a generic file-sharing issue. Update 3:20 p.m. PT: In an interview, a BurstNet spokesman declined to identify the law enforcement agency that ordered Blogetery shut down or provide the reason but did say that it had nothing to do with copyright violations. http://news.cnet.com/8301-31001_3-20010872-261.html  Feds Charge Couple in $40M Theft of GM Hybrid Car Tech for Chinese Company Layer 8 An FBI investigation has lead a Michigan couple to be charged with stealing hybrid car information from GM to use in a Chinese auto outfit. A federal indictment charged Yu Qin, aka Yu Chin, 49, and his wife, Shanshan Du, aka Shannon Du, 51, of Troy, Michigan with conspiracy to possess trade secrets without authorization, unauthorized possession of trade secrets, and wire fraud. One of the individuals was also charged with obstruction of justice, said Barbara McQuade, United States Attorney for the Eastern District of Michigan in a statement. GM estimates that the value of the stolen documents is over $40 million. According to the indictment, from December 2003 to May 2006, the defendants conspired to possess trade secret information of General Motors relating to hybrid vehicles, knowing that the information had been stolen, converted, or obtained without authorization. The indictment alleges that Du, while employed with GM, provided GM trade secret information relating to hybrid vehicles to her husband, Qin, for his benefit and for the benefit of a company, Millennium Technology International Inc., that the defendants owned and operated. Approximately five days after Du was offered a severance agreement by GM in January 2005, she copied thousands of GM documents, including trade secret documents, to an external computer hard drive used for MTI business. A few months later, Qin moved forward on a new business venture to provide hybrid vehicle technology to Chery Automobile, a Chinese automotive manufacturer based in China and a competitor of GM. The indictment further alleges that in May 2006, the defendants possessed GM trade secret information without authorization on several computer and electronic devices located in their residence, according to the statement. The indictment also charges the defendants dumped plastic bags containing shredded documents in a dumpster after they were subpoenaed by a federal grand jury looking for information relating to MTI and hybrid vehicles. The conspiracy to possess trade secrets without authorization count and each of the counts charging unauthorized possession of trade secrets carry a maximum penalty of 10 years' imprisonment and a $250,000 fine. The wire fraud counts each carry a maximum penalty of 20 years' imprisonment and a $250,000 fine. The obstruction of justice count carries a maximum penalty of 20 years' imprisonment and a $250,000 fine, according to the release from McQuade's office. http://www.networkworld.com/community/node/64031  US Senate Passes 'Libel Tourism' Bill The US Senate on Monday passed a bill to shield US journalists, authors, and publishers from "libel tourists" who file suit in countries where they expect to get the most favorable ruling. The popular legislation headed to the House of Representatives, which was expected to approve it and send the measure to US President Barack Obama to sign into law despite misgivings from key US allies. Backers of the bill have cited England, Brazil, Australia, Indonesia and Singapore as places where weak libel safeguards attract lawsuits that unfairly harm US journalists, writers and publishers. The Senate approved the measure in a "unanimous consent" voice vote. The bill's supporters have said that "libel tourism" undermines free speech rights under the US Constitution's cherished first amendment, and so erode accountability of powerful figures in a healthy democracy. The measure would prevent US federal courts from recognizing or enforcing a foreign judgment for defamation that is inconsistent with the first amendment of the US Constitution, which guarantees freedom of speech. It would bar foreign parties in such cases from targeting the US assets of an American author, journalist, or publisher as part of any damages. Senate Judiciary Committee chairman Patrick Leahy, a Democrat, charged that libel judgments in foreign courts were "undermining" freedom of speech and of the press and "chilling" open debate in the United States. "While we cannot legislate changes to foreign law that are chilling protected speech in our country, we can ensure that our courts do not become a tool to uphold foreign libel judgments that undermine American First Amendment or due process rights," he said in a statement. The US Constitution's first amendment, backed by a series of US Supreme Court decisions, makes it harder to win a libel suit in the United States relative to many other countries. "This bill is a needed first step to ensure that weak free-speech protections and abusive legal practices in foreign countries do not prevent Americans from fully exercising their constitutional right to speak and debate freely," said Senator Jeff Sessions, the top Republican on Leahy's committee. http://www.google.com/hostednews/afp...TH2QM2UGZ-xNtg  No Minister: 90% of Web Snoop Document Censored to Stop 'Premature Unnecessary Debate' Ben Grubb The federal government has censored approximately 90 per cent of a secret document outlining its controversial plans to snoop on Australians' web surfing, obtained under freedom of information (FoI) laws, out of fear the document could cause "premature unnecessary debate". The government has been consulting with the internet industry over the proposal, which would require ISPs to store certain internet activities of all Australians - regardless of whether they have been suspected of wrongdoing - for law-enforcement agencies to access. All parties to the consultations have been sworn to secrecy. Industry sources have claimed that the controversial regime could go as far as collecting the individual web browsing history of every Australian internet user, a claim denied by the spokesman for Attorney-General Robert McClelland. The exact details of the web browsing data the government wants ISPs to collect are contained in the document released to this website under FoI. The document was handed out to the industry during a secret briefing it held with ISPs in March. But from the censored document released, it is impossible to know how far the government is planning to take the policy. The government is hiding the plans from the public and it appears to want to move quickly on industry consultation, asking for participants to respond within only one month after it had held the briefings. The Attorney-General's Department legal officer, FoI and Privacy Section, Claudia Hernandez, wrote in her decision in releasing the highly-censored document that the release of some sections of it "may lead to premature unnecessary debate and could potentially prejudice and impede government decision making". Hernandez said that the material in question related to information the department was "currently weighing up and evaluating in relation to competing considerations that may have a bearing on a particular course of action or decision". "More specifically, it is information concerning the development of government policy which has not been finalised, and there is a strong possibility that the policy will be amended prior to public consultation," she wrote. Further, she said that although she had acknowledged the public's right to "participate in and influence the processes of government decision making and policy formulation ... the premature release of the proposal could, more than likely, create a confusing and misleading impression". "In addition, as the matters are not settled and proposed recommendations may not necessarily be adopted, release of such documents would not make a valuable contribution to public debate." Hernandez went further to say that she considered disclosure of the document uncensored "could be misleading to the public and cause confusion and premature and unnecessary debate". "In my opinion, the public interest factors in favour of release are outweighed by those against," Hernandez said. The "data retention regime" the government is proposing to implement is similar to that adopted by the European Union after terrorist attacks several years ago. Greens Communications spokesman Scott Ludlam said the excuse not to release the proposal in full was "extraordinary". Since finding out about the scheme, he has launched a Senate inquiry into it and other issues. "The idea that its release could cause 'premature' or 'unnecessary' debate is not going to go down well with the thousands of people who have been alarmed by the direction that government is taking," he said in a telephone interview. "I would really like to know what the government is hiding in this proposal," he said, adding that he hoped that the Attorney-General's Department would be "more forthcoming" about the proposal in the senate inquiry into privacy he pushed for in June. Deputy Leader of the Opposition in the Senate, George Brandis, said the government’s decision to censor the documents showed ‘‘how truly Orwellian this government has become". "To refuse disclosure of material that had already been circulated among stakeholders, on an issue of intense current political debate on the ground that it might provide unnecessary discussion, shows that the Gillard government has become beyond satire," Brandis said. Online users' lobby group Electronic Frontiers Australia spokesman Colin Jacobs said what was released was "a joke". "We have to assume the worst," he said. "And that is that the government has been badgering the telcos with very aggressive demands that should worry everybody." Jacobs said that the onus was now on government to "explain what data they need, what problem it solves and, just as importantly, why it can't be done in an open process". "The more sensitive the process and the data they want, the more transparent the government needs to be about why it wants that data," he said. "Nobody could argue that public consultation ... would somehow help criminals," he added. "We have to turn the age-old question back on the government: if you don’t have anything to hide, then you shouldn't be worried about people having insight into the consultation. "This is a very sensitive and important issue. It raises huge questions about privacy, data security and the burden of increased costs to smaller internet service providers. What really needs to be debated is what particular information they want, because that's where the privacy issue rears its ugly head," he said. According to one internet industry source, the release of the highly censored document was "illustrative of government's approach to things where they don't want people to know what they're thinking in advance of them getting it ready to package for public consumption". "And that’s worrying." The Attorney-General's spokesman declined to comment, referring comment to the department. The department said it had "nothing to add" to the FOI letter it provided. http://www.smh.com.au/technology/tec...722-10mxo.html  The New Dating Tools: A Card and a Wink Stephanie Rosenbloom LORI CHEEK was walking through the meatpacking district of Manhattan when she spotted a handsome man sitting with friends amid the dinner crowd outside Pastis. As she neared his table, she flashed a diminutive black card. “I nestled it in his French fries,” she said, “and kept going.” As Ms. Cheek, 37, disappeared into the July night, the man plucked the card from his fries. It read: “Look up. You might miss something.” Below, in smaller letters, were the words “find me,” a code and the address of a new Web site for singles. Move over, Match.com. This is the next generation of online dating. Unlike traditional dating sites where members spend hours on computers writing autobiographies and scrutinizing photographs, a raft of newfangled dating tools are striving to better bridge the gap between online and real-world romance. Some companies offer a combination of flirty calling cards and Web pages. Others operate dating applications that use the global positioning systems in cellphones to help local singles find one another. All of them contend they are superior to big online dating sites like Match.com and eHarmony.com because meeting people is faster, more organic and less formal. And participants are not limited to a database of members: the world is their dating pool. “It’s almost like you’re shopping online,” said Ms. Cheek, “but you’re shopping in real life.” At the same time, these hybrid dating tools still enable users to keep their names and personal information private for as long as they like. Ms. Cheek, an architect who works part-time in sales for a high-end Manhattan furniture company, founded one such venture, Cheek’d, which had its debut in May. Users receive calling cards to dole out to alluring strangers they encounter in their everyday lives, be it in a club or in a subway on their morning commute. Recipients of the cards can use the identification code printed on them to log onto Cheekd.com and send a message to their admirer. A pack of 50 cards and a month’s subscription to Cheek’d, where users can receive messages and post information about themselves, is $25. There is no fee for those who receive cards to communicate with an admirer through the site. Each Cheek’d card has a sassy phrase like “I am totally cooler than your date,” or, for those with no regard for subtlety: “I’m hitting on you.” Ms. Cheek is dreaming up specialized card sets, too. One for New York City singles will have lines like “I live below 14th Street” and “I hope my five-story walkup won’t be a problem.” Willa Bernstein, 43, who uses Cheek’d, was recently making eyes with a man at the Soho Grand Hotel but was feeling shy, so she dispatched a friend to slip him a card on her behalf. Ms. Bernstein was not bold that night, but the words on her card were: “I’m looking forward to our first date.” “I felt a little bit high school,” confessed Ms. Bernstein, a former government lawyer who now heads the philanthropy company Manthropy. “It was just a little intimidating to cross the room.” No matter. The next morning she awoke to find a message in her Cheekd.com mailbox. “My only regret from last night,” wrote the man from the Soho Grand, “was that you didn’t come over and introduce yourself in person.” The two have since exchanged messages, and Ms. Bernstein hopes to arrange a date soon. Cheek’d is not the only new company integrating calling cards and the Internet. Inspired by their own love story, Rachel and John DeAlto, 30 and 33, founded FlipMe!, which was introduced a few weeks ago and works similarly to Cheek’d. Ms. DeAlto first spied the man who would eventually become her husband while having dinner at a restaurant in Red Bank, N.J. He had been dining with colleagues, and on his way out, he handed a waitress $5 and asked her to pass a note scribbled on a scrap of place mat to Rachel. She waited three days, then called the number and said “I’m the girl from Juanitos.” Six weeks later, they were engaged. On each red FlipMe! card is an explanation for the recipient: “I’ve said ‘what if’ too many times ... not this time.” A pack of 30 cards and a three-month membership to flipmedating.com is $24.99. The cards, which all say the same thing, are sold online and in some salons and spas in the Northeast. A cellphone application is in the works. “It’s getting me out more,” said Christine Langfeld, 36, a food stylist who has tried online dating and has just begun experimenting with the cards. “Instead of running home to my computer, I’m going out for drinks and coffee and just being more social.” Card users said companies like FlipMe! and Cheek’d are emboldening them to approach people who might otherwise have been missed connections. They also appreciate how the companies reverse the online dating process — observe someone in person first, then send an electronic message. There’s no need to contend with false advertising on dating Web sites. “Some of those photos are 10 years old,” Ms. DeAlto said. “People hide behind trees. They put up photos of their dog, and they don’t have a dog.” Other companies are helping singles connect through location-based technology on their mobile phones. In the last few years the number of Web sites and applications like Grindr, Are You Interested? and Urban Signals, has swelled. One of the biggest is the free iPhone dating application Skout, which recently surpassed its millionth member. Skout uses a cellphone’s global positioning system to help users to find like-minded people within a walkable radius of one another. (For safety reasons, Skout does not identify a user’s precise location.) Those who sign up for the application create basic profiles with photographs and then use an instant message feature to communicate when they are within range of each other. Then, they can arrange a mutual meeting spot. “It’s really combining the best of online dating and real-world people discovery,” said Christian Wiklund, Skout’s founder. He likened using the application to entering a bar. “You walk into the bar, you can see who’s around, you can engage and flirt and wink.” Hunter Carren, 26, who works in industrial design, began using Skout a few months ago after a relationship with a girlfriend ended. “It breaks the ice,” he said of the application. Most of the singles who use Skout are in their 20s, according to the site’s statistics. Users are typically looking for dates rather than spouses, and are seeking activities in their hometowns or while traveling. “I used it about two weeks ago as soon as I got off the plane in Las Vegas,” Mr. Carren said. While in the Sheep Meadow in Central Park recently, Jessica Hirsch, 25, and a friend tried Skout and met some men who were also relaxing in the grass. They all ended up spending the afternoon sipping drinks on a picnic blanket. “This was very easy and free and straightforward,” Ms. Hirsch said, unlike her experience with JDate.com, which she said was “very formal.” On such sites there are back-and-forth introductory messages, Ms. Hirsch said, then still more messages about the selection of a time and location for the date — all of which usually happens over the course of a few days, not a few minutes. As for Ms. Cheek, the handsome man eating fries at Pastis sent her a message on Cheekd.com. But like an order of those Pastis fries, he was gone all too soon. “It turned out he was from Argentina,” Ms. Cheek said. http://www.nytimes.com/2010/07/22/fashion/22date.html  The Web Means the End of Forgetting Jeffrey Rosen Four years ago, Stacy Snyder, then a 25-year-old teacher in training at Conestoga Valley High School in Lancaster, Pa., posted a photo on her MySpace page that showed her at a party wearing a pirate hat and drinking from a plastic cup, with the caption “Drunken Pirate.” After discovering the page, her supervisor at the high school told her the photo was “unprofessional,” and the dean of Millersville University School of Education, where Snyder was enrolled, said she was promoting drinking in virtual view of her under-age students. As a result, days before Snyder’s scheduled graduation, the university denied her a teaching degree. Snyder sued, arguing that the university had violated her First Amendment rights by penalizing her for her (perfectly legal) after-hours behavior. But in 2008, a federal district judge rejected the claim, saying that because Snyder was a public employee whose photo didn’t relate to matters of public concern, her “Drunken Pirate” post was not protected speech. When historians of the future look back on the perils of the early digital age, Stacy Snyder may well be an icon. The problem she faced is only one example of a challenge that, in big and small ways, is confronting millions of people around the globe: how best to live our lives in a world where the Internet records everything and forgets nothing — where every online photo, status update, Twitter post and blog entry by and about us can be stored forever. With Web sites like LOL Facebook Moments, which collects and shares embarrassing personal revelations from Facebook users, ill-advised photos and online chatter are coming back to haunt people months or years after the fact. Examples are proliferating daily: there was the 16-year-old British girl who was fired from her office job for complaining on Facebook, “I’m so totally bored!!”; there was the 66-year-old Canadian psychotherapist who tried to enter the United States but was turned away at the border — and barred permanently from visiting the country — after a border guard’s Internet search found that the therapist had written an article in a philosophy journal describing his experiments 30 years ago with L.S.D. According to a recent survey by Microsoft, 75 percent of U.S. recruiters and human-resource professionals report that their companies require them to do online research about candidates, and many use a range of sites when scrutinizing applicants — including search engines, social-networking sites, photo- and video-sharing sites, personal Web sites and blogs, Twitter and online-gaming sites. Seventy percent of U.S. recruiters report that they have rejected candidates because of information found online, like photos and discussion-board conversations and membership in controversial groups. Technological advances, of course, have often presented new threats to privacy. In 1890, in perhaps the most famous article on privacy ever written, Samuel Warren and Louis Brandeis complained that because of new technology — like the Kodak camera and the tabloid press — “gossip is no longer the resource of the idle and of the vicious but has become a trade.” But the mild society gossip of the Gilded Age pales before the volume of revelations contained in the photos, video and chatter on social-media sites and elsewhere across the Internet. Facebook, which surpassed MySpace in 2008 as the largest social-networking site, now has nearly 500 million members, or 22 percent of all Internet users, who spend more than 500 billion minutes a month on the site. Facebook users share more than 25 billion pieces of content each month (including news stories, blog posts and photos), and the average user creates 70 pieces of content a month. There are more than 100 million registered Twitter users, and the Library of Congress recently announced that it will be acquiring — and permanently storing — the entire archive of public Twitter posts since 2006. In Brandeis’s day — and until recently, in ours — you had to be a celebrity to be gossiped about in public: today all of us are learning to expect the scrutiny that used to be reserved for the famous and the infamous. A 26-year-old Manhattan woman told The New York Times that she was afraid of being tagged in online photos because it might reveal that she wears only two outfits when out on the town — a Lynyrd Skynyrd T-shirt or a basic black dress. “You have movie-star issues,” she said, “and you’re just a person.” We’ve known for years that the Web allows for unprecedented voyeurism, exhibitionism and inadvertent indiscretion, but we are only beginning to understand the costs of an age in which so much of what we say, and of what others say about us, goes into our permanent — and public — digital files. The fact that the Internet never seems to forget is threatening, at an almost existential level, our ability to control our identities; to preserve the option of reinventing ourselves and starting anew; to overcome our checkered pasts. In a recent book, “Delete: The Virtue of Forgetting in the Digital Age,” the cyberscholar Viktor Mayer-Schönberger cites Stacy Snyder’s case as a reminder of the importance of “societal forgetting.” By “erasing external memories,” he says in the book, “our society accepts that human beings evolve over time, that we have the capacity to learn from past experiences and adjust our behavior.” In traditional societies, where missteps are observed but not necessarily recorded, the limits of human memory ensure that people’s sins are eventually forgotten. By contrast, Mayer-Schönberger notes, a society in which everything is recorded “will forever tether us to all our past actions, making it impossible, in practice, to escape them.” He concludes that “without some form of forgetting, forgiving becomes a difficult undertaking.” It’s often said that we live in a permissive era, one with infinite second chances. But the truth is that for a great many people, the permanent memory bank of the Web increasingly means there are no second chances — no opportunities to escape a scarlet letter in your digital past. Now the worst thing you’ve done is often the first thing everyone knows about you. THE CRISIS — AND THE SOLUTION? All this has created something of a collective identity crisis. For most of human history, the idea of reinventing yourself or freely shaping your identity — of presenting different selves in different contexts (at home, at work, at play) — was hard to fathom, because people’s identities were fixed by their roles in a rigid social hierarchy. With little geographic or social mobility, you were defined not as an individual but by your village, your class, your job or your guild. But that started to change in the late Middle Ages and the Renaissance, with a growing individualism that came to redefine human identity. As people perceived themselves increasingly as individuals, their status became a function not of inherited categories but of their own efforts and achievements. This new conception of malleable and fluid identity found its fullest and purest expression in the American ideal of the self-made man, a term popularized by Henry Clay in 1832. From the late 18th to the early 20th century, millions of Europeans moved from the Old World to the New World and then continued to move westward across America, a development that led to what the historian Frederick Jackson Turner called “the significance of the frontier,” in which the possibility of constant migration from civilization to the wilderness made Americans distrustful of hierarchy and committed to inventing and reinventing themselves. In the 20th century, however, the ideal of the self-made man came under siege. The end of the Western frontier led to worries that Americans could no longer seek a fresh start and leave their past behind, a kind of reinvention associated with the phrase “G.T.T.,” or “Gone to Texas.” But the dawning of the Internet age promised to resurrect the ideal of what the psychiatrist Robert Jay Lifton has called the “protean self.” If you couldn’t flee to Texas, you could always seek out a new chat room and create a new screen name. For some technology enthusiasts, the Web was supposed to be the second flowering of the open frontier, and the ability to segment our identities with an endless supply of pseudonyms, avatars and categories of friendship was supposed to let people present different sides of their personalities in different contexts. What seemed within our grasp was a power that only Proteus possessed: namely, perfect control over our shifting identities. But the hope that we could carefully control how others view us in different contexts has proved to be another myth. As social-networking sites expanded, it was no longer quite so easy to have segmented identities: now that so many people use a single platform to post constant status updates and photos about their private and public activities, the idea of a home self, a work self, a family self and a high-school-friends self has become increasingly untenable. In fact, the attempt to maintain different selves often arouses suspicion. Moreover, far from giving us a new sense of control over the face we present to the world, the Internet is shackling us to everything that we have ever said, or that anyone has said about us, making the possibility of digital self-reinvention seem like an ideal from a distant era. Concern about these developments has intensified this year, as Facebook took steps to make the digital profiles of its users generally more public than private. Last December, the company announced that parts of user profiles that had previously been private — including every user’s friends, relationship status and family relations — would become public and accessible to other users. Then in April, Facebook introduced an interactive system called Open Graph that can share your profile information and friends with the Facebook partner sites you visit. What followed was an avalanche of criticism from users, privacy regulators and advocates around the world. Four Democratic senators — Charles Schumer of New York, Michael Bennet of Colorado, Mark Begich of Alaska and Al Franken of Minnesota — wrote to the chief executive of Facebook, Mark Zuckerberg, expressing concern about the “instant personalization” feature and the new privacy settings. The reaction to Facebook’s changes was such that when four N.Y.U. students announced plans in April to build a free social-networking site called Diaspora, which wouldn’t compel users to compromise their privacy, they raised more than $20,000 from more than 700 backers in a matter of weeks. In May, Facebook responded to all the criticism by introducing a new set of privacy controls that the company said would make it easier for users to understand what kind of information they were sharing in various contexts. Facebook’s partial retreat has not quieted the desire to do something about an urgent problem. All around the world, political leaders, scholars and citizens are searching for responses to the challenge of preserving control of our identities in a digital world that never forgets. Are the most promising solutions going to be technological? Legislative? Judicial? Ethical? A result of shifting social norms and cultural expectations? Or some mix of the above? Alex Türk, the French data-protection commissioner, has called for a “constitutional right to oblivion” that would allow citizens to maintain a greater degree of anonymity online and in public places. In Argentina, the writers Alejandro Tortolini and Enrique Quagliano have started a campaign to “reinvent forgetting on the Internet,” exploring a range of political and technological ways of making data disappear. In February, the European Union helped finance a campaign called “Think B4 U post!” that urges young people to consider the “potential consequences” of publishing photos of themselves or their friends without “thinking carefully” and asking permission. And in the United States, a group of technologists, legal scholars and cyberthinkers are exploring ways of recreating the possibility of digital forgetting. These approaches share the common goal of reconstructing a form of control over our identities: the ability to reinvent ourselves, to escape our pasts and to improve the selves that we present to the world. REPUTATION BANKRUPTCY AND TWITTERGATION A few years ago, at the giddy dawn of the Web 2.0 era — so called to mark the rise of user-generated online content — many technological theorists assumed that self-governing communities could ensure, through the self-correcting wisdom of the crowd, that all participants enjoyed the online identities they deserved. Wikipedia is one embodiment of the faith that the wisdom of the crowd can correct most mistakes — that a Wikipedia entry for a small-town mayor, for example, will reflect the reputation he deserves. And if the crowd fails — perhaps by turning into a digital mob — Wikipedia offers other forms of redress. Those who think their Wikipedia entries lack context, because they overemphasize a single personal or professional mistake, can petition a group of select editors that decides whether a particular event in someone’s past has been given “undue weight.” For example, if the small-town mayor had an exemplary career but then was arrested for drunken driving, which came to dominate his Wikipedia entry, he can petition to have the event put in context or made less prominent. In practice, however, self-governing communities like Wikipedia — or algorithmically self-correcting systems like Google — often leave people feeling misrepresented and burned. Those who think that their online reputations have been unfairly tarnished by an isolated incident or two now have a practical option: consulting a firm like ReputationDefender, which promises to clean up your online image. ReputationDefender was founded by Michael Fertik, a Harvard Law School graduate who was troubled by the idea of young people being forever tainted online by their youthful indiscretions. “I was seeing articles about the ‘Lord of the Flies’ behavior that all of us engage in at that age,” he told me, “and it felt un-American that when the conduct was online, it could have permanent effects on the speaker and the victim. The right to new beginnings and the right to self-definition have always been among the most beautiful American ideals.” ReputationDefender, which has customers in more than 100 countries, is the most successful of the handful of reputation-related start-ups that have been growing rapidly after the privacy concerns raised by Facebook and Google. (ReputationDefender recently raised $15 million in new venture capital.) For a fee, the company will monitor your online reputation, contacting Web sites individually and asking them to take down offending items. In addition, with the help of the kind of search-optimization technology that businesses use to raise their Google profiles, ReputationDefender can bombard the Web with positive or neutral information about its customers, either creating new Web pages or by multiplying links to existing ones to ensure they show up at the top of any Google search. (Services begin from $10 a month to $1,000 a year; for challenging cases, the price can rise into the tens of thousands.) By automatically raising the Google ranks of the positive links, ReputationDefender pushes the negative links to the back pages of a Google search, where they’re harder to find. “We’re hearing stories of employers increasingly asking candidates to open up Facebook pages in front of them during job interviews,” Fertik told me. “Our customers include parents whose kids have talked about them on the Internet — ‘Mom didn’t get the raise’; ‘Dad got fired’; ‘Mom and Dad are fighting a lot, and I’m worried they’ll get a divorce.’ ” Companies like ReputationDefender offer a promising short-term solution for those who can afford it; but tweaking your Google profile may not be enough for reputation management in the near future, as Web 2.0 swiftly gives way to Web. 3.0 — a world in which user-generated content is combined with a new layer of data aggregation and analysis and live video. For example, the Facebook application Photo Finder, by Face.com, uses facial-recognition and social-connections software to allow you to locate any photo of yourself or a friend on Facebook, regardless of whether the photo was “tagged” — that is, the individual in the photo was identified by name. At the moment, Photo Finder allows you to identify only people on your contact list, but as facial-recognition technology becomes more widespread and sophisticated, it will almost certainly challenge our expectation of anonymity in public. People will be able to snap a cellphone picture (or video) of a stranger, plug the images into Google and pull up all tagged and untagged photos of that person that exist on the Web. In the nearer future, Internet searches for images are likely to be combined with social-network aggregator search engines, like today’s Spokeo and Pipl, which combine data from online sources — including political contributions, blog posts, YouTube videos, Web comments, real estate listings and photo albums. Increasingly these aggregator sites will rank people’s public and private reputations, like the new Web site Unvarnished, a reputation marketplace where people can write anonymous reviews about anyone. In the Web 3.0 world, Fertik predicts, people will be rated, assessed and scored based not on their creditworthiness but on their trustworthiness as good parents, good dates, good employees, good baby sitters or good insurance risks. Anticipating these challenges, some legal scholars have begun imagining new laws that could allow people to correct, or escape from, the reputation scores that may govern our personal and professional interactions in the future. Jonathan Zittrain, who teaches cyberlaw at Harvard Law School, supports an idea he calls “reputation bankruptcy,” which would give people a chance to wipe their reputation slates clean and start over. To illustrate the problem, Zittrain showed me an iPhone app called Date Check, by Intelius, that offers a “sleaze detector” to let you investigate people you’re thinking about dating — it reports their criminal histories, address histories and summaries of their social-networking profiles. Services like Date Check, Zittrain said, could soon become even more sophisticated, rating a person’s social desirability based on minute social measurements — like how often he or she was approached or avoided by others at parties (a ranking that would be easy to calibrate under existing technology using cellphones and Bluetooth). Zittrain also speculated that, over time, more and more reputation queries will be processed by a handful of de facto reputation brokers — like the existing consumer-reporting agencies Experian and Equifax, for example — which will provide ratings for people based on their sociability, trustworthiness and employability. To allow people to escape from negative scores generated by these services, Zittrain says that people should be allowed to declare “reputation bankruptcy” every 10 years or so, wiping out certain categories of ratings or sensitive information. His model is the Fair Credit Reporting Act, which requires consumer-reporting agencies to provide you with one free credit report a year — so you can dispute negative or inaccurate information — and prohibits the agencies from retaining negative information about bankruptcies, late payments or tax liens for more than 10 years. “Like personal financial bankruptcy, or the way in which a state often seals a juvenile criminal record and gives a child a ‘fresh start’ as an adult,” Zittrain writes in his book “The Future of the Internet and How to Stop It,” “we ought to consider how to implement the idea of a second or third chance into our digital spaces.” Another proposal, offered by Paul Ohm, a law professor at the University of Colorado, would make it illegal for employers to fire or refuse to hire anyone on the basis of legal off-duty conduct revealed in Facebook postings or Google profiles. “Is it really fair for employers to know what you’ve put in your Facebook status updates?” Ohm asks. “We could say that Facebook status updates have taken the place of water-cooler chat, which employers were never supposed to overhear, and we could pass a prohibition on the sorts of information employers can and can’t consider when they hire someone.” Ohm became interested in this problem in the course of researching the ease with which we can learn the identities of people from supposedly anonymous personal data like movie preferences and health information. When Netflix, for example, released 100 million purportedly anonymous records revealing how almost 500,000 users had rated movies from 1999 to 2005, researchers were able to identify people in the database by name with a high degree of accuracy if they knew even only a little bit about their movie-watching preferences, obtained from public data posted on other ratings sites. Ohm says he worries that employers would be able to use social-network-aggregator services to identify people’s book and movie preferences and even Internet-search terms, and then fire or refuse to hire them on that basis. A handful of states — including New York, California, Colorado and North Dakota — broadly prohibit employers from discriminating against employees for legal off-duty conduct like smoking. Ohm suggests that these laws could be extended to prevent certain categories of employers from refusing to hire people based on Facebook pictures, status updates and other legal but embarrassing personal information. (In practice, these laws might be hard to enforce, since employers might not disclose the real reason for their hiring decisions, so employers, like credit-reporting agents, might also be required by law to disclose to job candidates the negative information in their digital files.) Another legal option for responding to online setbacks to your reputation is to sue under current law. There’s already a sharp rise in lawsuits known as Twittergation — that is, suits to force Web sites to remove slanderous or false posts. Last year, Courtney Love was sued for libel by the fashion designer Boudoir Queen for supposedly slanderous comments posted on Twitter, on Love’s MySpace page and on the designer’s online marketplace-feedback page. But even if you win a U.S. libel lawsuit, the Web site doesn’t have to take the offending material down any more than a newspaper that has lost a libel suit has to remove the offending content from its archive. Some scholars, therefore, have proposed creating new legal rights to force Web sites to remove false or slanderous statements. Cass Sunstein, the Obama administration’s regulatory czar, suggests in his new book, “On Rumors,” that there might be “a general right to demand retraction after a clear demonstration that a statement is both false and damaging.” (If a newspaper or blogger refuses to post a retraction, they might be liable for damages.) Sunstein adds that Web sites might be required to take down false postings after receiving notice that they are false — an approach modeled on the Digital Millennium Copyright Act, which requires Web sites to remove content that supposedly infringes intellectual property rights after receiving a complaint. As Stacy Snyder’s “Drunken Pirate” photo suggests, however, many people aren’t worried about false information posted by others — they’re worried about true information they’ve posted about themselves when it is taken out of context or given undue weight. And defamation law doesn’t apply to true information or statements of opinion. Some legal scholars want to expand the ability to sue over true but embarrassing violations of privacy — although it appears to be a quixotic goal. Daniel Solove, a George Washington University law professor and author of the book “The Future of Reputation,” says that laws forbidding people to breach confidences could be expanded to allow you to sue your Facebook friends if they share your embarrassing photos or posts in violation of your privacy settings. Expanding legal rights in this way, however, would run up against the First Amendment rights of others. Invoking the right to free speech, the U.S. Supreme Court has already held that the media can’t be prohibited from publishing the name of a rape victim that they obtained from public records. Generally, American judges hold that if you disclose something to a few people, you can’t stop them from sharing the information with the rest of the world. That’s one reason that the most promising solutions to the problem of embarrassing but true information online may be not legal but technological ones. Instead of suing after the damage is done (or hiring a firm to clean up our messes), we need to explore ways of pre-emptively making the offending words or pictures disappear. EXPIRATION DATES Jorge Luis Borges, in his short story “Funes, the Memorious,” describes a young man who, as a result of a riding accident, has lost his ability to forget. Funes has a tremendous memory, but he is so lost in the details of everything he knows that he is unable to convert the information into knowledge and unable, as a result, to grow in wisdom. Viktor Mayer-Schönberger, in “Delete,” uses the Borges story as an emblem for the personal and social costs of being so shackled by our digital past that we are unable to evolve and learn from our mistakes. After reviewing the various possible legal solutions to this problem, Mayer-Schönberger says he is more convinced by a technological fix: namely, mimicking human forgetting with built-in expiration dates for data. He imagines a world in which digital-storage devices could be programmed to delete photos or blog posts or other data that have reached their expiration dates, and he suggests that users could be prompted to select an expiration date before saving any data. This is not an entirely fanciful vision. Google not long ago decided to render all search queries anonymous after nine months (by deleting part of each Internet protocol address), and the upstart search engine Cuil has announced that it won’t keep any personally identifiable information at all, a privacy feature that distinguishes it from Google. And there are already small-scale privacy apps that offer disappearing data. An app called TigerText allows text-message senders to set a time limit from one minute to 30 days after which the text disappears from the company’s servers on which it is stored and therefore from the senders’ and recipients’ phones. (The founder of TigerText, Jeffrey Evans, has said he chose the name before the scandal involving Tiger Woods’s supposed texts to a mistress.) Expiration dates could be implemented more broadly in various ways. Researchers at the University of Washington, for example, are developing a technology called Vanish that makes electronic data “self-destruct” after a specified period of time. Instead of relying on Google, Facebook or Hotmail to delete the data that is stored “in the cloud” — in other words, on their distributed servers — Vanish encrypts the data and then “shatters” the encryption key. To read the data, your computer has to put the pieces of the key back together, but they “erode” or “rust” as time passes, and after a certain point the document can no longer be read. Tadayoshi Kohno, a designer of Vanish, told me that the system could provide expiration dates not only for e-mail but also for any data stored in the cloud, including photos or text or anything posted on Facebook, Google or blogs. The technology doesn’t promise perfect control — you can’t stop someone from copying your photos or Facebook chats during the period in which they are not encrypted. But as Vanish improves, it could bring us much closer to a world where our data didn’t linger forever. Kohno told me that Facebook, if it wanted to, could implement expiration dates on its own platform, making our data disappear after, say, three days or three months unless a user specified that he wanted it to linger forever. It might be a more welcome option for Facebook to encourage the development of Vanish-style apps that would allow individual users who are concerned about privacy to make their own data disappear without imposing the default on all Facebook users. So far, however, Zuckerberg, Facebook’s C.E.O., has been moving in the opposite direction — toward transparency rather than privacy. In defending Facebook’s recent decision to make the default for profile information about friends and relationship status public rather than private, Zuckerberg said in January to the founder of the publication TechCrunch that Facebook had an obligation to reflect “current social norms” that favored exposure over privacy. “People have really gotten comfortable not only sharing more information and different kinds but more openly and with more people, and that social norm is just something that has evolved over time,” he said. PRIVACY’S NEW NORMAL But not all Facebook users agree with Zuckerberg. Plenty of anecdotal evidence suggests that young people, having been burned by Facebook (and frustrated by its privacy policy, which at more than 5,000 words is longer than the U.S. Constitution), are savvier than older users about cleaning up their tagged photos and being careful about what they post. And two recent studies challenge the conventional wisdom that young people have no qualms about having their entire lives shared and preserved online forever. A University of California, Berkeley, study released in April found that large majorities of people between 18 and 22 said there should be laws that require Web sites to delete all stored information about individuals (88 percent) and that give people the right to know all the information Web sites know about them (62 percent) — percentages that mirrored the privacy views of older adults. A recent Pew study found that 18-to-29-year-olds are actually more concerned about their online profiles than older people are, vigilantly deleting unwanted posts, removing their names from tagged photos and censoring themselves as they share personal information, because they are coming to understand the dangers of oversharing. Still, Zuckerberg is on to something when he recognizes that the future of our online identities and reputations will ultimately be shaped not just by laws and technologies but also by changing social norms. And norms are already developing to recreate off-the-record spaces in public, with no photos, Twitter posts or blogging allowed. Milk and Honey, an exclusive bar on Manhattan’s Lower East Side, requires potential members to sign an agreement promising not to blog about the bar’s goings on or to post photos on social-networking sites, and other bars and nightclubs are adopting similar policies. I’ve been at dinners recently where someone has requested, in all seriousness, “Please don’t tweet this” — a custom that is likely to spread. But what happens when people transgress those norms, using Twitter or tagging photos in ways that cause us serious embarrassment? Can we imagine a world in which new norms develop that make it easier for people to forgive and forget one another’s digital sins? That kind of social norm may be harder to develop. Alessandro Acquisti, a scholar at Carnegie Mellon University, studies the behavioral economics of privacy — that is, the conscious and unconscious mental trade-offs we make in deciding whether to reveal or conceal information, balancing the benefits of sharing with the dangers of disclosure. He is conducting experiments about the “decay time” and the relative weight of good and bad information — in other words, whether people discount positive information about you more quickly and heavily than they discount negative information about you. His research group’s preliminary results suggest that if rumors spread about something good you did 10 years ago, like winning a prize, they will be discounted; but if rumors spread about something bad that you did 10 years ago, like driving drunk, that information has staying power. Research in behavioral psychology confirms that people pay more attention to bad rather than good information, and Acquisti says he fears that “20 years from now, if all of us have a skeleton on Facebook, people may not discount it because it was an error in our youth.” On the assumption that strangers may not make it easy for us to escape our pasts, Acquisti is also studying technologies and strategies of “privacy nudges” that might prompt people to think twice before sharing sensitive photos or information in the first place. Gmail, for example, has introduced a feature that forces you to think twice before sending drunken e-mail messages. When you enable the feature, called Mail Goggles, it prompts you to solve simple math problems before sending e-mail messages at times you’re likely to regret. (By default, Mail Goggles is active only late on weekend nights.) Acquisti is investigating similar strategies of “soft paternalism” that might nudge people to hesitate before posting, say, drunken photos from Cancún. “We could easily think about a system, when you are uploading certain photos, that immediately detects how sensitive the photo will be.” A silly but surprisingly effective alternative might be to have an anthropomorphic icon — a stern version of Microsoft’s Clippy — that could give you a reproachful look before you hit the send button. According to M. Ryan Calo, who runs the consumer-privacy project at Stanford Law School, experimenters studying strategies of “visceral notice” have found that when people navigate a Web site in the presence of a human-looking online character who seems to be actively following the cursor, they disclose less personal information than people who browse with no character or one who appears not to be paying attention. As people continue to experience the drawbacks of living in a world that never forgets, they may well learn to hesitate before posting information, with or without humanoid Clippys. FORGIVENESS In addition to exposing less for the Web to forget, it might be helpful for us to explore new ways of living in a world that is slow to forgive. It’s sobering, now that we live in a world misleadingly called a “global village,” to think about privacy in actual, small villages long ago. In the villages described in the Babylonian Talmud, for example, any kind of gossip or tale-bearing about other people — oral or written, true or false, friendly or mean — was considered a terrible sin because small communities have long memories and every word spoken about other people was thought to ascend to the heavenly cloud. (The digital cloud has made this metaphor literal.) But the Talmudic villages were, in fact, far more humane and forgiving than our brutal global village, where much of the content on the Internet would meet the Talmudic definition of gossip: although the Talmudic sages believed that God reads our thoughts and records them in the book of life, they also believed that God erases the book for those who atone for their sins by asking forgiveness of those they have wronged. In the Talmud, people have an obligation not to remind others of their past misdeeds, on the assumption they may have atoned and grown spiritually from their mistakes. “If a man was a repentant [sinner],” the Talmud says, “one must not say to him, ‘Remember your former deeds.’ ” Unlike God, however, the digital cloud rarely wipes our slates clean, and the keepers of the cloud today are sometimes less forgiving than their all-powerful divine predecessor. In an interview with Charlie Rose on PBS, Eric Schmidt, the C.E.O. of Google, said that “the next generation is infinitely more social online” — and less private — “as evidenced by their Facebook pictures,” which “will be around when they’re running for president years from now.” Schmidt added: “As long as the answer is that I chose to make a mess of myself with this picture, then it’s fine. The issue is when somebody else does it.” If people chose to expose themselves for 15 minutes of fame, Schmidt says, “that’s their choice, and they have to live with it.” Schmidt added that the “notion of control is fundamental to the evolution of these privacy-based solutions,” pointing to Google Latitude, which allows people to broadcast their locations in real time. This idea of privacy as a form of control is echoed by many privacy scholars, but it seems too harsh to say that if people like Stacy Snyder don’t use their privacy settings responsibly, they have to live forever with the consequences. Privacy protects us from being unfairly judged out of context on the basis of snippets of private information that have been exposed against our will; but we can be just as unfairly judged out of context on the basis of snippets of public information that we have unwisely chosen to reveal to the wrong audience. Moreover, the narrow focus on privacy as a form of control misses what really worries people on the Internet today. What people seem to want is not simply control over their privacy settings; they want control over their online reputations. But the idea that any of us can control our reputations is, of course, an unrealistic fantasy. The truth is we can’t possibly control what others say or know or think about us in a world of Facebook and Google, nor can we realistically demand that others give us the deference and respect to which we think we’re entitled. On the Internet, it turns out, we’re not entitled to demand any particular respect at all, and if others don’t have the empathy necessary to forgive our missteps, or the attention spans necessary to judge us in context, there’s nothing we can do about it. But if we can’t control what others think or say or view about us, we can control our own reaction to photos, videos, blogs and Twitter posts that we feel unfairly represent us. A recent study suggests that people on Facebook and other social-networking sites express their real personalities, despite the widely held assumption that people try online to express an enhanced or idealized impression of themselves. Samuel Gosling, the University of Texas, Austin, psychology professor who conducted the study, told the Facebook blog, “We found that judgments of people based on nothing but their Facebook profiles correlate pretty strongly with our measure of what that person is really like, and that measure consists of both how the profile owner sees him or herself and how that profile owner’s friends see the profile owner.” By comparing the online profiles of college-aged people in the United States and Germany with their actual personalities and their idealized personalities, or how they wanted to see themselves, Gosling found that the online profiles conveyed “rather accurate images of the profile owners, either because people aren’t trying to look good or because they are trying and failing to pull it off.” (Personality impressions based on the online profiles were most accurate for extroverted people and least accurate for neurotic people, who cling tenaciously to an idealized self-image.) Gosling is optimistic about the implications of his study for the possibility of digital forgiveness. He acknowledged that social technologies are forcing us to merge identities that used to be separate — we can no longer have segmented selves like “a home or family self, a friend self, a leisure self, a work self.” But although he told Facebook, “I have to find a way to reconcile my professor self with my having-a-few-drinks self,” he also suggested that as all of us have to merge our public and private identities, photos showing us having a few drinks on Facebook will no longer seem so scandalous. “You see your accountant going out on weekends and attending clown conventions, that no longer makes you think that he’s not a good accountant. We’re coming to terms and reconciling with that merging of identities.” Perhaps society will become more forgiving of drunken Facebook pictures in the way Gosling says he expects it might. And some may welcome the end of the segmented self, on the grounds that it will discourage bad behavior and hypocrisy: it’s harder to have clandestine affairs when you’re broadcasting your every move on Facebook, Twitter and Foursquare. But a humane society values privacy, because it allows people to cultivate different aspects of their personalities in different contexts; and at the moment, the enforced merging of identities that used to be separate is leaving many casualties in its wake. Stacy Snyder couldn’t reconcile her “aspiring-teacher self” with her “having-a-few-drinks self”: even the impression, correct or not, that she had a drink in a pirate hat at an off-campus party was enough to derail her teaching career. That doesn’t mean, however, that it had to derail her life. After taking down her MySpace profile, Snyder is understandably trying to maintain her privacy: her lawyer told me in a recent interview that she is now working in human resources; she did not respond to a request for comment. But her success as a human being who can change and evolve, learning from her mistakes and growing in wisdom, has nothing to do with the digital file she can never entirely escape. Our character, ultimately, can’t be judged by strangers on the basis of our Facebook or Google profiles; it can be judged by only those who know us and have time to evaluate our strengths and weaknesses, face to face and in context, with insight and understanding. In the meantime, as all of us stumble over the challenges of living in a world without forgetting, we need to learn new forms of empathy, new ways of defining ourselves without reference to what others say about us and new ways of forgiving one another for the digital trails that will follow us forever. http://www.nytimes.com/2010/07/25/ma...rivacy-t2.html  India Develops World's Cheapest "Laptop" at $35 India has come up with the world's cheapest "laptop," a touch-screen computing device that costs $35. India's Human Resource Development Minister Kapil Sibal this week unveiled the low-cost computing device that is designed for students, saying his department had started talks with global manufacturers to start mass production. "We have reached a (developmental) stage that today, the motherboard, its chip, the processing, connectivity, all of them cumulatively cost around $35, including memory, display, everything," he told a news conference. He said the touchscreen gadget was packed with Internet browsers, PDF reader and video conferencing facilities but its hardware was created with sufficient flexibility to incorporate new components according to user requirement. Sibal said the Linux based computing device was expected to be introduced to higher education institutions from 2011 but the aim was to drop the price further to $20 and ultimately to $10. The device was developed by research teams at India's premier technological institutes, the Indian Institute of Technology and the Indian Institute of Science. India spends about three percent of its annual budget on school education and has improved its literacy rates to over 64 percent of its 1.2 billion population but studies have shown many students can barely read or write and most state-run schools have inadequate facilities. (Reporting by Reuters Television, Editing by Belinda Goldsmith) http://www.reuters.com/article/idUSTRE66M0R720100723  Vibration-Powered Generators Replace AA, AAA Batteries Hideyoshi Kume Brother Industries Ltd developed small vibration-powered generators that can replace AA and AAA batteries. For example, when the generator, which the company calls "Vibration-powered Generating Battery," is set inside a remote control, it is possible to use the remote by shaking it to generate power. "The new generator will semipermanently eliminate the need to replace batteries and contribute to reducing the amount of wastes," Brother Industries said. Brother Industries ensured the versatility of the generator by employing the shapes of commonly-used batteries. When used with a low power consumption device such as a remote, the generator can replace a battery, the company said. Specifically, the generator can be used for a device that does not always consume electricity and has a power consumption of about 100mW, the company said. For example, the power consumption of a normal remote is 40 to 100mW. This time, Brother Industries prototyped the generator in AA and AAA sizes. Inside a battery-shaped case, there are an electromagnetic induction generator and an electric double layer capacitor with a capacitance of about 500mF. The average output of the AA-size generator is 10 to 180mW (frequency: 4-8Hz). Brother Industries will exhibit the Vibration-powered Generating Battery for the first time at Techno-frontier 2010, an exhibition that will run from July 21 to 23, 2010, in Tokyo. The company plans to demonstrate a TV remote control, a remote for lighting equipment and an LED flashlight using the battery. http://techon.nikkeibp.co.jp/english...100716/184262/  Google Discontinues the Nexus One Android Phone Google has pulled the plug on the Nexus One, its once highly anticipated smartphone, following disappointing sales. The last shipment has arrived at Google HQ, and once those are gone there will be no more Nexus One devices for U.S. consumers. The handset will still be sold through Vodafone in Europe and some Asian carriers, and developers will still be able to get their hands on one. However, it looks like the Droid phones on Verizon will carry the mantle for Google’sGoogleGoogle AndroidAndroidAndroid mobile operating system. This is the end of the company’s grand experiment with an unlocked consumer handset in the U.S. Google closed the Nexus One web store two months ago; this final nail in the coffin was well overdue. Google announced the end of the line on its blogblogblog on Friday, but there was so little fanfare or interest in the story that the story slipped through the cracks. Although the Nexus One was popular with geeks, most American consumers probably just didn’t understand the concept of an unlocked handset, and Google didn’t put much marketing muscle behind the device. Thus, it’s no surprise that the phone has been discontinued and hardly anyone noticed. It’s too bad, actually. It was a fine device, improved further by the Android 2.2 update a couple of weeks ago. http://mashable.com/2010/07/18/nexus-one-discontinued/  Here's Your Free Case, Jerk Apple's Condescending iPhone 4 Press Conference. Farhad Manjoo On Thursday, I hoped that Apple CEO Steve Jobs would admit there's a problem with the new iPhone's antenna and apologize for pretending there wasn't. I didn't get that apology. Not even close. Instead, in a defensive press conference at Apple's headquarters on Friday, Jobs argued that the new iPhone offers terrific, out-of-this-world reception. He blamed the media for whipping up a frenzy out of a "fact of life" that affects every phone on the market. As Jobs sees it, the only problems with the iPhone 4 are the pesky "laws of physics," which pretty much ensure that anyone who holds a mobile phone in her hands is asking for trouble. The only reason people have been focusing on the iPhone is that blogs keep singling Apple out, perhaps because "when you're doing well, people want to tear you down." Still, if you want to be a total jerk about it and keep insisting there's a problem with your magical iPhone, Jobs has an offer for you. "OK, great, let's give everybody a case," he said. Happy now, whiners? I wasn't invited to Apple's event; I followed along on various live blogs. (All quotes here are as transcribed by Engadget and GDGT.) I cringed as I watched. Reports leading up to the event—including a New York Times article that quoted an unnamed Apple rep—suggested that Apple would own up to a problem in the phone's hardware or software. But Jobs kicked off the conference by playing "The iPhone Antenna Song," a YouTube video in which a guy croons, "The media loves a failure in a string of successes." Things got worse when Jobs took the stage and offered a blizzard of statistics to suggest the problems people are reporting aren't unique in the phone market. Apple, he said, has sold more than 3 million iPhones in the last three weeks, yet only 0.55 percent of purchasers have called the company with reception problems. Very few people are returning the phone, he continued, fewer than returned the iPhone 3GS. He showed off demonstrations of the BlackBerry Bold, the HTC Droid Eris, and the Samsung Omnia II that exhibited the same problem that's been reported on the iPhone—when you hold them a certain way, their signal bars begin to drop. "Phones aren't perfect," he said, and the problem reported with the iPhone is a "challenge for the entire industry." But Jobs' numbers are misleading. From the very first reports of trouble, Apple has publicly insisted that there's no reception problem with the iPhone; it even sent its AppleCare technical support staff "positioning statements" telling them to inform customers that "iPhone 4's wireless performance is the best we have ever shipped." It's no wonder, then, that not very many people called Apple to complain about problems. It's been clear to everyone who bought the iPhone 4 that Apple would not acknowledge its reception problems. Why would you waste time on the phone with technical support when you knew it would be no help? What about the fact that so few people are returning the phone? Jobs is right—it is an indicator that the iPhone 4 is a great device that people want to keep. That doesn't mean, however, that the phone isn't afflicted with an annoying flaw. The fact that people aren't returning the new iPhone doesn't mean the problem doesn't exist. More probably, it means that customers were waiting to see how Apple, a company known for good customer service, might respond to the problem. Jobs' claim that the same call-dropping problem can be observed on other phones also misses the point. Even if that's true, Jobs elided the clear evidence that the issue is much more obvious and repeatable with the iPhone 4. (When a reporter asked, "I can't get my [BlackBerry] Bold to drop right now, maybe you can show me how to do it?" Jobs responded, "You may not see it in certain areas.") If it were the case that people were simply out to attack Apple, why didn't we see people posting dozens of videos showing last year's iPhone, the 3GS, dropping calls when you held it wrong? Jobs' data offered a clue why—as the CEO admitted, it turns out that the iPhone 4 drops more calls than the iPhone 3GS. While Jobs did admit this fact in his press conference, he mangled the stats to make the iPhone 4's dropped call increase look minor. "The iPhone 4 drops less than one additional call per 100 than the 3GS," he said. As Jobs sees it, that's not a big rise in dropped calls. Yet that's not an obvious conclusion. Last year, an AT&T spokesman told me that AT&T's average iPhone dropped-call rate is 1 percent—in other words, the old iPhone dropped one call out of 100. If the iPhone 4 drops nearly one additional call out of 100, that could be close to a 2 percent dropped-call rate—or double the dropped-call rate of the old iPhone. That sounds a lot more serious, doesn't it? Jobs also ignored the possibility that people are adjusting their behavior to avoid dropped calls on the iPhone 4. After all, Jobs himself allegedly counseled a customer who's getting poor reception to "avoid holding it in that way." As my own dropped call rate rose after switching to the iPhone 4 (from the 3GS), I found myself constantly on edge about how I held the phone, and have lately taken to keeping it in my pocket while I use hands-free earbuds. Sure, that's helped my dropped-call problem, but it's far from an ideal solution. So, why is the iPhone 4 having this dropped-call problem? Jobs said he had his own "pet theory": It's not a design problem, but an accessory problem. When the 3GS came out, there were lots of third-party cases available for it. But there aren't enough cases for the new iPhone. "Only 20 percent leave the store with a case," Jobs said. So there are more dropped calls on the new iPhone because fewer of them are in cases. That's the closest Jobs came all day to admitting that there is a design flaw in the iPhone; if you need a case to reduce dropped calls, then the product, by itself, must be flawed. Don't get me wrong. I'm happy Apple is giving iPhone users a free case. I'm hoping the freebie will reduce my dropped calls, and if that's the case, I won't be returning my iPhone. I just wish Jobs could have handled this mini-crisis in a classier way. His data clearly show that the new iPhone is dropping more calls than the old one. He could have admitted a problem, offered a fix, and said, "We're sorry for any trouble we caused you." Instead, he sounded wounded and paranoid, as if we were all being ungrateful for not recognizing Apple's contributions to the world. "We love our users so much we've built 300 Apple retail stores for them," he claimed at one point. Wow, thanks, Steve—all this time, I thought you built those stores just to sell stuff! He said that a Bloomberg Business Week report that he'd been warned about potential antenna problems was "total bullshit." At another point, he asked a questioner, bizarrely, "What would you prefer, that we're a Korean company? Do you not like the fact that we're an American company leading the world right here?" What I'd prefer, since Jobs is asking, is a company that doesn't pee on my leg and tell me it's the "most revolutionary rain storm ever!" A free case is all well and good. Just lose the attitude, Steve. You screwed up. We know it. You know it. Just admit it. http://www.slate.com/id/2260619 Until next week, - js.  Current Week In Review  Recent WiRs - July 17th, July 10th, July 3rd, June 26th Jack Spratts' Week In Review is published every Friday. Submit letters, articles, press releases, comments, questions etc. in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|
|
|

|
|
|
#2 |
|
Thanks for being with arse
Join Date: Jan 2002
Location: The other side of the world
Posts: 10,343
|
still drop in for a read of your WiR
Jack keep up the good work |
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - February 13th, '10 | JackSpratts | Peer to Peer | 0 | 10-02-10 07:55 AM |
| Peer-To-Peer News - The Week In Review - January 30th, '10 | JackSpratts | Peer to Peer | 0 | 27-01-10 07:49 AM |
| Peer-To-Peer News - The Week In Review - January 23rd, '10 | JackSpratts | Peer to Peer | 0 | 20-01-10 09:04 AM |
| Peer-To-Peer News - The Week In Review - January 16th, '10 | JackSpratts | Peer to Peer | 0 | 13-01-10 09:02 AM |
| Peer-To-Peer News - The Week In Review - December 5th, '09 | JackSpratts | Peer to Peer | 0 | 02-12-09 08:32 AM |