
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 |
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Since 2002
  "No company should be allowed to censor the message we want to send to people who have asked us to send it to them. Regardless of people's political views, Verizon customers should decide what action to take on their phones. Why does Verizon get to make that choice for them?" – Nancy Keenan "I'm concerned about symbolism. This is not the type of message America needs to be sending to the world." – Dave vonKleist "Sometimes we ask the driver to stop and get a sandwich, but mostly we eat whatever is backstage, a yogurt, a cookie. You know, whatever — a grape." – Janeta Samp "I’m like, 'Sure, but what is he selling, the Magna Carta?'" – James Zemaitis September 29th, 2007  Demonoid Down Demonoid is a BitTorrent tracker website. It was apparently set up by an anonymous Yugoslav known only as Deimos. The website indexes torrents uploaded by its members. These torrents can then be searched and the content shared using the peer to peer BitTorrent protocol. Demonoid is one of the largest BitTorrent trackers and its torrents are found on other BitTorrent search engines. Demonoid has been down and the constant rumor is that Demonoid is out of business. http://bu.bulicio.us/gadgets/demonoid-taken-down/  IsoHunt Takes Down BitTorrent Trackers in the US Ernesto Starting today, the Isohunt team will deny access to all US visitors on their TorrentBox and Podtropolis tracker. They are forced to take this action because of their involvement in a lawsuit initiated by the MPAA. The IsoHunt crew released this statement today: As of earlier today, we have disabled access from users in the US to our trackers. This goes for ALL trackers (torrentbox, podtropolis) we run. This is due to the US’s hostility towards P2P technologies, and we feel with our current lawsuit brought by the MPAA, we can no longer ensure your security and privacy in the US. So, if you’re outside the US, you may notice less peers. We encourage you to add other public, unhampered trackers to torrents you post, in addition to Torrentbox and Podtropolis’s trackers. IsoHunt is not alone in their battle with the MPAA. Last month TorrentSpy, another site named in the MPAA lawsuit blocked access to US users on their site. However, the takedown of IsoHunt’s trackers will have an even bigger effect on the BitTorrent community worldwide, especially because TorrentBox runs one of the biggest public BitTorrent trackers. As mentioned by the Isohunt team, this means that users outside the US will see less peers connected to their torrents which may result in slower download speeds. The MPAA announced the lawsuit against Torrentspy, Torrentbox and Isohunt in February 2006. Isohunt owner Gary later told TorrentFreak that they will not bow down to the MPAA. Isohunt hired a top-notch lawyer, specialized in Internet copyrights. It now seems that this wasn’t enough to keep the trackers in the air. For now, the websites are still available to US visitors. The MPAA argues that the sole purpose of these BitTorrent trackers and sites is to share copyrighted content. But they are wrong according to Gary, who said, “We process copyright takedown requests daily, and have done so for hundreds of requests in the past, if not thousands. We work with all copyright owners, and even the RIAA email us routinely. The MPAA is the only organization unwilling to cooperate with us.” Luckily, quite a lot of torrents are tracked by more that one tracker these days. And if that doesn’t work there’s always DHT. You can read more about how to protect yourself from failing BitTorrent trackers in this article. Long live the hydra! http://torrentfreak.com/mpaa-takes-d...entbox-070925/  Game over? RIAA Changes Gears Just Before Hitting Brick Wall Anders Bylund Maybe you saw my diatribe against the Recording Industry Association of America earlier this week and shook your head at the assertion that the coalition has to change gears now. Well, the change is happening in Internet time, which is somewhere between "instantly" and "yesterday." Today, Ray Beckerman's RIAA litigation blog noted that the attack lawyers' lawsuit boilerplate has changed dramatically, and no longer tries to pin a "making available" claim on the hapless defendant. In a nutshell, that claim used to be a central pillar in the RIAA strategy, because it's fairly easy to show that some files were made available for download from a given IP address. Easy money if the lawsuit were to go anywhere. But few of them ever did, and many suits have been thrown out because it isn't actually illegal to have a pile of files ready for others to download. Someone actually has to download them, which is a much harder point to prove. Sony BMG, Warner Music, Vivendi's Universal Music, and EMI can't lean on that crutch anymore. It's real. It's happening. There's no way the RIAA could afford to start many more lawsuits when the chances of winning dwindle to nothing. Good riddance. http://www.fool.com/investing/genera...-hitting-.aspx  MediaDefender’s Decoy Effectiveness on BitTorrent Sites Ernesto MediaDefender’s email and anti piracy tool leaks gave the world an unique insight into the workings and the effectiveness of their BitTorrent decoy operations. So how effective were they? And which sites were best protected against these fake torrents? Let’s find out. MediaDefender determines the effectiveness of their spoofs and decoys by analyzing the top search results for the file in question, mostly movies and music albums. If 2 out of 10 top search results are fake files spread by them, their effectiveness is 20% on that particular BitTorrent site. Their goals is of course to get as many fake files in there, hoping people will end up downloading useless data. There is a lot of variance in the reported effectiveness between BitTorrent sites and the different decoy projects. We scanned through most of the reports and it seems that The Pirate Bay and Mininova were best protected against fake files whereas MediaDefender was more effective on sites like BiteNova and TorrentPortal. Niek from Mininova, the toughest site to get onto according to MediaDefender, wrote a blog post in response to the leaked MediaDefender emails. He sums up some of the quotes that show how well protected Mininova is. Niek adds, “We can only be grateful for the many nice words from our friends at MediaDefender. All thanks go to our great moderating team, who did (and do) great work.” The Pirate Bay always has been one of MediaDefender’s main targets because this site is often mentioned in the press. Unfortunately for MediaDefender The Pirate Bay is also one of the sites that is well protected against fake files. In July, Brokep from The Pirate Bay already told us that they were doing all they can to block Media Defender from accessing their trackers. “We block them and some other torrent sites do as well.” he said. This apparently annoyed MediaDefender, as we can see from one of their emails regarding the effectiveness of their decoys for Micheal Moore’s Sicko: “we still have no presence on Pirate bay which is a site they [Weinstein?] are likely watching as it was mentioned in the AdAge article they referenced.” Here is an example of an effectiveness report for “Fantastic 4: Rise of the Silver Surfer” based on the top search results. Note that an effectiveness of 100% means that all the torrents that showed up in the search results (top 6/10/15) were fake. BiteNova: 100% Bittorrent.am 27% Btjunkie 20% Btmon 15% BushTorrent 100% ExtraTorrent 47% Fenopy 100% FlixFlux 23% FullDLS 32% IsoHunt 100% Meganova 100% Mininova 0% Monova 35% MyBittorrent 91% NewTorrents 0% Novatina 98% PirateBay 0% Snarf-it 74% TorrentBox 32% TorrentLocomotive 47% TorrentPortal 100% TorrentReactor 0% TorrentSpy 4% TorrentValley 77% TorrentView 27% Torrentz 22% Underground 0% WorldNova 97% Yotoshi 92% http://torrentfreak.com/mediadefende...-sites-070922/  BitTorrent Opens Subsidiary in Japan BitTorrent Japan to be headquartered in Tokyo Clement James BitTorrent has established a wholly owned subsidiary headquartered in Tokyo. The company said that BitTorrent Japan will address a growing demand for peer-assisted content delivery technology among Japanese content publishers and consumer electronics manufacturers. Japan has some of the world's most advanced broadband and mobile networks, electronics devices and game consoles, as well as web services. BitTorrent believes that there is high demand among content publishers and electronic software providers for BitTorrent Delivery Network Accelerator (DNA), a secure, managed peer-assisted networking platform that reduces bandwidth and content delivery costs. BitTorrent DNA enables websites to provide a better end-user experience by adding speed, reliability and efficiency to their current content delivery infrastructure. The company said that there is also high demand among Japanese hardware manufacturers to integrate BitTorrent's software development kit into next-generation consumer electronics devices. BitTorrent is already working with Japanese device manufacturers such as Buffalo Technology and Planex Communications to integrate its technology into the latest network-attached storage devices, wireless routers and set-top boxes. "We are intrigued by Japan's advanced broadband environment that exists as a result of innovation and competition among ISPs," said Ashwin Navin, president and co-founder of BitTorrent. "BitTorrent has the ability to leverage the capacity that exists within the Japanese internet to create great user experiences for online applications while dramatically reducing infrastructure costs for publishers." The company believes that, although P2P technologies are still misunderstood as a result of being abused, BitTorrent's security, performance, efficiency and technical merits will become the leading peer-assisted delivery platform in Japan for on-demand video, software, and video games. "Having a physical presence in Japan promises an unparalleled level of support to our Japanese partners and commitment to customer success," added Navin. http://www.vnunet.com/vnunet/news/21...onichiwa-japan  "txtor" Tool Circumvents Basic Torrent Blockers Jacqui Cheng To the frustration of many students and other avid torrent downloaders, some universities and ISPs have been known to block the download of .torrent files in an effort to curb illegal file sharing. This quick and dirty method of filtering Internet content is usually done through the use of a proxy server that will look for a torrent mime-type in the file or, even simpler, the file extension itself. Although this method seems almost too simple to take seriously, enough admins have found it effective enough to justify its use. That's why a group of developers launched txtor today, a site that makes it possible to download .torrent files as if they were text files. As the site explains, from the user perspective, the service functions very simply. Plug in the URL of a torrent file, and it's translated to a text file for you to download. For a moderately more technical explanation, the site merely takes the file and changes the mimetype and extension, then spits it back out at you as a text file in order to bypass proxy-level torrent file blocks. Then, all you need to do is change the file extension back from .txt to .torrent and open it up in your favorite torrent client. Based on our testing of txtor, we can say that the tool works exactly as advertised. txtor does not, however, help to bypass more sophisticated methods of blocking torrents, such as deep packet inspection (DPI). Since DPI involves scanning the contents of a data stream (and not just file names or mime-types), an obvious sidestep such as txtor won't be able to elude it. Luckily for regular torrenters, most ISP haven't full deployed DPI gear just yet, save that required to fully comply with the Communications Assistance for Law Enforcement Act (CALEA). Because this "hack" is so basic, we wouldn't be surprised to see some equally basic torrent-blocking tools to catch up eventually. Simply blocking text files, however, certainly won't work (at least without irritating a large portion of an admin's user base), so it might prove to be a slightly bigger challenge than just blocking files with certain extensions. When it comes to P2P services though, it's safe to say that the cat-and-mouse game between clever developers and network admins won't be over anytime soon. If you're one of the unfortunate group behind a proxy server that blocks torrent files from being downloaded, txtor will probably do the job... for now, anyway. http://arstechnica.com/news.ars/post...-blockers.html  Copyright Lawyer Tells Universities to Resist "Copyright Bullies" Nate Anderson Wendy Seltzer, the founder of the Chilling Effects Clearinghouse and a former EFF staff attorney, gave a talk yesterday at Cornell (RealPlayer required) on "Protecting the University from Copyright Bullies." The bullies in question are the RIAA, and the issue is the recording industry's current campaign of both litigation and political pressure. Should universities assist the music industry in identifying the "pirates," or should they do everything in their power to resist? The title of Seltzer's talk gives the game away. She believes that the mission of the university is to promote academic freedom, research, the testing of boundaries, and the learning of personal responsibility by students and researchers. An open network facilitates such things; one that is filtered and used to watch the activities of its users does not, in her view, produced the sorts of effects that universities want. The campus has become the latest battleground in the war on file-sharing. The RIAA has taken its fight to the halls of Congress, where it recently failed to secure some legislation that would have required colleges and universities to implement content filtering solutions on their networks and would direct the government to produce a list of the top 25 infringing schools. "Why Congress should be getting into the business of naming names and pointing fingers is beyond me," Seltzer said. The idea was shot down, but the RIAA has also embarked on an aggressive plan to sue thousands of college students into submission this year, and that plan continues to move forward. Universities, including Cornell, now routinely receive "pre-litigation" letters from the RIAA that contain only an IP address. The group wants universities to pass these letters on to students. The letters offer students the possibility of a several thousand dollars settlement or the more expensive alternative of going to court. If the letters don't produce a response, the RIAA then files a "John Doe" lawsuit and obtains a subpoena to force the university to turn over the student information (some of these subpoenas were recently quashed on technical grounds). Once that happens, a specific lawsuit is filed against the student. Seltzer hopes to encourage universities to start challenging these tactics, especially challenging the subpoenas on the ground that they pose an "undue burden" to the university. While cost is certainly one factor here, the "burden" that Seltzer is primarily talking about is the effect that complying with the subpoenas has on the university's mission. In her view, it makes universities take a stand as an adversary of students, since they are forced to turn over personal information shared with them only for reasons of education. It also curtails the openness of the university's network. One questioner asked whether the issue wasn't complicated by the fact that students also live at the university; that is, the users of the network aren't simply doing academic research, and massive copyright infringement is no doubt going on at most universities. Seltzer responded by pointing out that universities already deal with legal and law enforcement issues on a regular basis, and they generally do so without tracking or monitoring their students. For instance, underage drinking can be a problem on most campuses, but few or no schools install cameras or other devices to detect underage drinkers. Part of letting students grow up, she said, was taking a step back. Normally, that would also mean letting students pay the penalty for their mistakes, but Selzer doesn't believe that it is fair for a few students to be singled out for such draconian penalties while nothing happens to the vast majority of their peers. In addition to the severity of the statutory penalties for copyright infringement, there are the well-known evidentiary problems of linking an IP address to an individual. It's an interesting talk for those on both sides of the debate, but especially for those in university administration across the country who have to confront these issues on a daily basis. http://arstechnica.com/news.ars/post...t-bullies.html  P2P Services Slashed During the 2007 China Internet Conference, a senior official from the Ministry of Information Industry (MII) accused peer-to-peer (P2P) downloading of occupying too much of the Internet bandwidth, making it impossible to launch other new Internet services. Han Xia, Deputy Director of Telecommunications Administration Bureau under MII, pointed out that many problems have appeared during the growth of Chinese internet industry. In Han's opinion, P2P downloading is one of the most serious problems. Although the number of Chinese broad brand users is below the world's average level, the P2P fluxes in China are 3 to 4 times of those in the US. According to statistics from Chinese Internet service providers, P2P downloading accounts for 35 to 60 percent of the whole fluxes in the day and 50 to 90 percent during the night. For Chinese users, the Internet is used mainly for downloading movies and music. http://www.china.org.cn/english/business/225782.htm  Did Music, Movie Labels Attack Pirate Site? Swedish police are weighing charges for alleged efforts to disrupt Pirate Bay file-sharing site. Jeremy Kirk Swedish police are expected to decide later this week whether a criminal case is warranted against 10 major music and movie companies over their alleged efforts to disrupt the Pirate Bay, one of the largest file-sharing search engines. If Swedish police decide to pursue a criminal complaint, the Pirate Bay will be spared the time and expense of pursuing its own civil suit against the companies, Peter Sunde, one of a small circle of volunteers in Sweden that runs the Web site, said on Tuesday. The Pirate Bay, with an estimated two million daily users, is a search engine for torrents, or small files used to trade content between computers via a peer-to-peer (P-to-P) network. Media companies say the site is used mainly to enable the illegal trading of copyright files and have sought its closure. But the Pirate Bay struck back last Friday, filing a criminal complaint in Sweden against content companies that hired MediaDefender Inc., a company that specializes in disrupting P-to-P networks. The Pirate Bay alleges that MediaDefender attacked its operations by distributing fake torrent files and other methods. It is charging the media companies, which include the Swedish subsidiaries of Twentieth Century Fox, Universal Pictures and Sony BMG Music Entertainment, with infrastructural sabotage, denial of service attacks and other hacking and spamming offenses, according to its blog. The complaint followed the damaging release of thousands of internal MediaDefender e-mails, which described in part how the company tries to foil file-sharing services. MediaDefender uses a software program that sets up fake user accounts and then distributes fake torrent files, which are designed to reduce the volume of copyright files being traded, Sunde said. The source code for that software, as well as the internal e-mails, are now being widely circulating on file-sharing networks. The software can read "captchas," the strings of distorted numbers and letters designed to ensure that real people are using a Web site rather than an automated program. The Pirate Bay says it matched IP (Internet protocol) addresses for some of the fake torrents to some of the internal e-mails, providing compelling evidence that MediaDefender was sending out fake torrents, according to Sunde. The Pirate Bay blacklists IP addresses associated with fake torrents and also shares those lists with other torrent search engines, Sunde said. "We are very proactive when it comes to spam handling, but it's still a problem when they [MediaDefender] do it," he said. Despite complaints from media and content companies, the Pirate Bay has continued to operate in Sweden. In May 2006, Swedish police seized at least 25 servers after a raid on five locations, but have yet to file charges. Swedish prosecutors have until Oct. 1 to file a criminal case, but Sunde said he expects the government attorneys to file for an extension. Sunde maintains that the Pirate Bay is just a search engine and doesn't actually store any files, merely directing users to where files are located. "We are quite sure the Pirate Bay is legal in Sweden," said Sunde, who is based in Malmo, in the south of Sweden, and also runs a Web site consulting business. As a precaution against future police action, Sunde said he knows the location of only one of the 40 or so servers currently powering the Pirate Bay. Some of those servers are now in countries outside of Sweden, he said. http://www.pcworld.com/article/id,13...t/article.html  Majority of Films Watched Online are Not Through Video Sharing Site 9 billion films were watched online in July 2007 in the US alone, according to the latest figures from comScore Networks. The figure is up from around 7 billion in March, with 134 million people each watching an average of 181 minutes of video during the month. Interestingly, just 27% of clips watched were through Google/YouTube, which nevertheless far outstripped its rivals - Yahoo nabbed a distant second place, serving up 4.3 percent of the clips, while Fox Interactive Media (MySpace), came in third with 3.3 percent. Viacom (3.1 percent) and Disney (2 percent) rounded out the top five. Google also ranked first in July in unique video viewers with almost 68 million, followed by Fox Interactive (35.8 million), Yahoo (35.3 million), Time Warner Inc. (26.6 million) and Viacom (22.6 million), comScore said. That means over 50% of films watched online on either very small video sharing/hosting sites or on people's own sites. http://www.netribution.co.uk/2/content/view/1278/182/  Ohio Federal Judge Strikes Down Net-Censorship Law Declan McCullagh It's no surprise that politicians are rarely conversant with the limits on their legislating found in the U.S. Constitution. But it is worth noting when federal judges have actually read the First Amendment and strike down a law accordingly. That brings us to Ohio's constitutionally impaired legislature, which enacted two laws that were touted as ways to protect children on the Internet but in reality would become a new censorship regime. An Ohio federal judge on Monday struck down (see PDF) the state's combined "harmful to minors" law on the grounds that it ran afoul of the First Amendment's guarantee of freedom of speech. 2709.31(A) of the law generally says "no person" shall "disseminate" or offer to disseminate to a "juvenile" any material that is "harmful to juveniles." Ohio's House Bill 490 amended it by defining electronic dissemination as having "reason to believe that the person receiving the information is a juvenile." You can see where this is going. Let's say that one-sixth of the Internet's users are minors. That means that for almost any Web site, assuming the audience is representative, the operator has reason to believe that something like one-sixth of them are under 18 years old. (There's another section that tries to limit that requirement's sweep, but in practice it wouldn't amount to much.) Fortunately, U.S. District Judge Walker Herbert Rice realized this. Rice said the definition of "harmful to juveniles" does not by itself violate the First Amendment and that it does not violate the Commerce Clause. But he ruled that, in practice, applying that definition to the Internet is overly broad. In particular, he said, sexually explicit conversations in adults-only chat rooms (where a minor sneaks in) could be prosecuted. It would "act as a ban to that segment of speech between adults which is protected by the First Amendment." This is consistent with other judges' rulings on "harmful to minors" or "harmful to juveniles" Internet statutes. The 2nd Circuit overturned Vermont's; the 10th Circuit overturned New Mexico's. In this case, Judge Rice granted a permanent injunction. He had, by the way, already granted an injunction in the case based on the earlier version of the law, but the proceedings essentially restarted after the law was changed around four years ago. The plaintiffs include the National Association of Recording Merchandisers, the American Booksellers Foundation for Free Expression, and the Association of American Publishers, and it was brought by their trade association called the Media Coalition. If the appeals court upholds this ruling, the Media Coalition may be able to get attorneys' fees--which amounted to a requested $488,601 in a similar Internet censorship suit in Virginia. And that's not even counting proceedings before an appeals court, which has already happened (briefly) in the Ohio case but didn't in Virginia. The problem is that when Ohio politicians enact unconstitutional laws, and subsequently lose in court, taxpayers end up footing the bill. It would be a far more just system if politicians were held personally responsible for paying their fair share of a half-million dollar fine for their constitutional ignorance. I'm sure Ohio politicos would have no objection--right? http://www.news.com/8301-13578_3-978...tml?tag=repblg  Company Will Monitor Phone Calls to Tailor Ads Louise Story Companies like Google scan their e-mail users’ in-boxes to deliver ads related to those messages. Will people be as willing to let a company listen in on their phone conversations to do the same? Pudding Media, a start-up based in San Jose, Calif., is introducing an Internet phone service today that will be supported by advertising related to what people are talking about in their calls. The Web-based phone service is similar to Skype’s online service — consumers plug a headset and a microphone into their computers, dial any phone number and chat away. But unlike Internet phone services that charge by the length of the calls, Pudding Media offers calling without any toll charges. The trade-off is that Pudding Media is eavesdropping on phone calls in order to display ads on the screen that are related to the conversation. Voice recognition software monitors the calls, selects ads based on what it hears and pushes the ads to the subscriber’s computer screen while he or she is still talking. A conversation about movies, for example, will elicit movie reviews and ads for new films that the caller will see during the conversation. Pudding Media is working on a way to e-mail the ads and other content to the person on the other end of the call, or to show it on that person’s cellphone screen. “We saw that when people are speaking on the phone, typically they were doing something else,” said Ariel Maislos, chief executive of Pudding Media. “They had a lot of other action, either doodling or surfing or something else like that. So we said, ‘Let’s use that’ and actually present them with things that are relevant to the conversation while it’s happening.” The company’s model, of course, raises questions about the line between target advertising and violation of privacy. Consumer-brand companies are increasingly trying to use data about people to deliver different ads to them based on their demographics and behavior online. Pudding Media executives said that scanning the words used in phone calls was not substantially different from what Google does with e-mail. Still, even some advertising executives were wary of the concept. “We can never obtain too much information from the targets, and I would love to get my hands on that information,” said Jonathan Sackett, chief digital officer for Arnold Worldwide, a unit of the advertising company Havas. “Still, it makes me caution myself and caution all of us as marketers. We really have to look at the situation, because we’re getting more intrusive with each passing technology.” Mr. Maislos said that Pudding Media had considered the privacy question carefully. The company is not keeping recordings or logs of the content of any phone calls, he said, so advertisements only relate to current calls, not past ones, and will only arrive during the call itself. Besides, Mr. Maislos said, he thought that young people, the group his company is focusing on with the call service, are less concerned with maintaining privacy than older people are. “The trade-off of getting personalized content versus privacy is a concept that is accepted in the world,” he said. Mr. Maislos founded Pudding Media with his brother, Ruben. Each had spent several years doing intelligence work for the Israeli military. Before Pudding Media, Ariel Maislos ran a broadband company called Passave, which he sold in May 2006 to PMC-Sierra, a maker of computer chips for telecommunications equipment, for $300 million. Richard Purcell, a former chief privacy officer at Microsoft, is an adviser to Pudding Media, Ariel Maislos said. To give the ads greater accuracy, Pudding Media asks users for their sex, age range, native language and ZIP code when they sign up. For now, the company is running ads that are sold by a third-party network, but Pudding Media plans to also sell its own ads in a few months. Advertisers pay based on how often a user click on their ads, and a spokeswoman said the rates were similar to the cost-per-click prices in Google’s AdSense network. Pudding Media plans to add other payment models, like charging for each ad impression or by the number of calls an ad generates to the advertiser. As the company’s software listens in on conversations, it filters out explicit words in determining which ads to select, so that content and ads will not be shown with those inappropriate words. Pudding Media would not elaborate, beyond saying that these were “keywords with profanity and things you wouldn’t want a 13-year-old to hear.” While the calling service only works through computers for now, Mr. Maislos said he saw the potential to use it with cellphones. The company is offering the technology to cellphone carriers to allow their customers to enjoy free calls in exchange for simultaneously watching contextually relevant ads on their screens. Callers can try Pudding Media at www.thepudding.com, dialing any number in North America. Because the service has so far been in a quiet beta test, the company would not say how many people have tried it so far. Pudding Media is also trying to sell the technology to Web publishers and media companies that would like to offer readers free calls and content related to those calls. A news site, for example, could show only its own articles and ads to people as they talked to friends. Mr. Maislos said that during tests he noticed that the content had a tendency to determine conversations. “The conversation was actually changing based on what was on the screen,” he said. “Our ability to influence the conversation was remarkable.” http://www.nytimes.com/2007/09/24/bu...hp&oref=slogin  Tech Wonders on Homeland Security Horizon  The "Nano Air Vehicle," or NAV (R) is powered by a two-stage rocket thruster and carries interchangeable payload modules. Jim Wolf Americans are facing a brave new world of post-September 11 technology marvels that could soon find their way into billions of dollars of projected homeland security spending. Gee-whiz know-how -- from swarms of tiny airborne sensors to ever-sharper satellite imagery -- is being developed by companies chasing potentially lucrative federal, state and local deals to address 21st-century security threats. Already in use are such things as infrared cameras with built-in brains that capture license plate images and match them in milliseconds to police records of vehicles of interest to the authorities. Such license plate recognition systems, fixed and mobile, already are stopping criminals in cars in New York City, Washington D.C. and 23 states, according to Mark Windover, president of Remington ELSAG Law Enforcement Systems, which is marketing its product to 250 U.S. police agencies. "Seventy percent of all criminal activity can be tied to a vehicle," he said. "Had to get there, had to go home." Remington ELSAG says its algorithms -- which turn images into data in the blink of an eye -- could guard airports, military bases and other federal facilities as well as crack down on the drug trade, robberies and other crime hinging on stolen cars. In other surveillance developments, the Department of Homeland Security, or DHS, is defending a plan to make broader use of eyes in the sky that, until now, have mostly fed military and scientific needs. "The use of geospatial information from military intelligence satellites may turn out to be a valuable tool in protecting the homeland," Democrats on the House of Representatives Homeland Security Committee wrote to Homeland Security Secretary Michael Chertoff this month. But they voiced privacy and civil liberties concerns about the scheduled October 1 launch of the National Applications Office, a clearing house for expanded output of imagery to police, border security and other law-enforcement outfits. "We are so concerned that, as the department's authorizing committee, we are calling for a moratorium on the program until the many constitutional, legal and organizational questions it raises are answered," Chairman Bennie Thompson of Mississippi and colleagues wrote on September 6. Satellites, Tiny Aerial Vehicles DigitalGlobe, a potential beneficiary of stepped-up demand for such products, launched a satellite this week that can daily collect up to 750,000 square kilometers of imagery able to pick out suitcase-sized objects. The WorldView-1 satellite is part of a U.S. program, dubbed NextView, designed to give government customers priority access. Many of the gizmos under development will be pitched first and foremost to the Pentagon, which is increasingly trying to keep tabs on foes in urban and other hard-to-monitor settings. Lockheed Martin Corp, the Pentagon's No. 1 supplier by contract value, is working on a keychain-sized, remote-controlled aerial vehicle designed to collect and transmit data with military and homeland security uses. Resembling the seed of a silver maple tree, the single-winged device would pack a tiny two-stage rocket thruster along with telemetry, communications, navigation, imaging sensors and a power source. The nano air vehicle, or NAV, is designed to carry interchangeable payload modules -- the size of an aspirin tablet. It could be used for chemical and biological detection or finding a "needle in a haystack," according to Ned Allen, chief scientist at Lockheed's fabled Skunk Works research arm. Released in organized swarms to fly low over a disaster area, the NAV sensors could detect human body heat and signs of breathing, Allen said. "The NAV swarm can pinpoint the location of survivors, send the data back to the first responders and help concentrate rescue operations where they are most likely to be successful," he said in an e-mail interview. Meanwhile, Boeing Co (BA.N: Quote, Profile, Research) is leading the technology segment of a multiyear plan to secure U.S. borders that includes database and intelligence analysis systems. Projected by U.S. Customs and Border Protection officials to cost as much as $8.8 billion over the next six years, the system also features ground-based and tower-mounted sensors, cameras and radar plus high-speed communications, command and control equipment and devices that detect tunnels. Airport screening is another area that could be transformed within 10 years, using scanning wizardry to pinpoint a suspected security threat through biometrics -- based on one or more physical or behavioral traits. "We can read fingerprints from about five meters .... all 10 prints," said Bruce Walker, vice president of homeland security for Northrop Grumman Corp (NOC.N: Quote, Profile, Research). "We can also do an iris scan at the same distance." (Additional reporting by Andrea Shalal-Esa) http://www.reuters.com/article/techn...43732820070923  Agent Accused of Using Homeland Data to Stalk Girlfriend A special agent with the Department of Commerce has been charged with unlawfully accessing a database within the Department of Homeland Security to stalk his former girlfriend and her family. Benjamin Robinson, 40, of Oakland, Calif., was indicted by a federal grand jury in San Jose Wednesday in connection with allegations that he accessed a government database known as the Treasury Enforcement Communications System (TECS) at least 163 times to track a woman's travel patterns. He is being charged with making a false statement to a government agency, and unlawfully obtaining information from a protected computer. Robinson faces a maximum of 10 years in prison and a fine of US$500,000. http://www.freemarketnews.com/WorldNews.asp?nid=49330  Sex in the Park, and Its Sneaky Spectators Philip Gefter WHY are the Japanese couples in Kohei Yoshiyuki’s photographs having sex outdoors? Was 1970s Tokyo so crowded, its apartments so small, that they were forced to seek privacy in public parks at night? And what about those peeping toms? Are the couples as oblivious as they seem to the gawkers trespassing on their nocturnal intimacy? If the social phenomena captured in these photographs seem distinctly linked to Japanese culture, Mr. Yoshiyuki’s images of voyeurs reverberate well beyond it. Viewing his pictures means that you too are looking at activities not meant to be seen. We line up right behind the photographer, surreptitiously watching the peeping toms who are secretly watching the couples. Voyeurism is us. The series, titled “The Park,” is on view at Yossi Milo Gallery in Chelsea, the first time the photographs have been exhibited since 1979, when they were introduced at Komai Gallery in Tokyo. For that show the pictures were blown up to life size, the gallery lights were turned off, and each visitor was given a flashlight. Mr. Yoshiyuki wanted to reconstruct the darkness of the park. “I wanted people to look at the bodies an inch at a time,” he has said. The oversize prints were destroyed after the show, and the series was published in 1980 as a book, one now difficult to find. Last year Mr. Yoshiyuki made new editions of the prints in several sizes, which have brought renewed interest in his work. Since April images from the series have been acquired by the Museum of Modern Art in New York, the Museum of Contemporary Photography in Chicago, the Museum of Fine Arts in Houston and the San Francisco Museum of Modern Art. Mr. Yoshiyuki was a young commercial photographer in Tokyo in the early 1970s when he and a colleague walked through Chuo Park in Shinjuku one night. He noticed a couple on the ground, and then one man creeping toward them, followed by another. “I had my camera, but it was dark,” he told the photographer Nobuyoshi Araki in a 1979 interview for a Japanese publication. Researching the technology in the era before infrared flash units, he found that Kodak made infrared flashbulbs. Mr. Yoshiyuki returned to the park, and to two others in Tokyo, through the ’70s. He photographed heterosexual and homosexual couples engaged in sexual activity and the peeping toms who stalked them. “Before taking those pictures, I visited the parks for about six months without shooting them,” Mr. Yoshiyuki wrote recently by e-mail, through an interpreter. “I just went there to become a friend of the voyeurs. To photograph the voyeurs, I needed to be considered one of them. I behaved like I had the same interest as the voyeurs, but I was equipped with a small camera. My intention was to capture what happened in the parks, so I was not a real ‘voyeur’ like them. But I think, in a way, the act of taking photographs itself is voyeuristic somehow. So I may be a voyeur, because I am a photographer.” Mr. Yoshiyuki’s photographic activity was undetected because of the darkness; the flash of the infrared bulbs has been likened to the lights of a passing car. “The couples were not aware of the voyeurs in most cases,” he wrote. “The voyeurs try to look at the couple from a distance in the beginning, then slowly approach toward the couple behind the bushes, and from the blind spots of the couple they try to come as close as possible, and finally peep from a very close distance. But sometimes there are the voyeurs who try to touch the woman, and gradually escalating — then trouble would happen.” Mr. Yoshiyuki’s pictures do not incite desire so much as document the act of lusting. The peeping toms are caught in the process of gawking, focused on their visual prey. Alexandra Munroe, senior curator of Asian art at the Guggenheim Museum, suggested in a telephone interview that this phenomenon was not uncommon in Japan. She cited the voyeurism depicted in Ukiyo-e woodblock erotic prints from 18th- and 19th-century Japan, in which a viewer watches a couple engage in sexual activity. “It’s a consistent erotic motif in Japanese sexual imagery and in Japanese films like ‘In the Realm of the Senses,’ ” she said. Karen Irvine, curator of the Museum of Contemporary Photography in Chicago, said Mr. Yoshiyuki’s work is important because “it addresses photography’s unique capacity for observation and implication.” She locates his work in the tradition of artists who modified their cameras with decoy lenses and right-angle viewfinders to gain access to private moments. Weegee, for example, rigged his camera to capture couples kissing in darkened New York movie theaters. Walker Evans covertly photographed fellow passengers on New York subways. “Like the work of these artists,” Ms. Irvine said, “Yoshiyuki’s photographs explore the boundaries of privacy, an increasingly rare commodity. Ironically, we may reluctantly accommodate ourselves to being watched at the A.T.M., the airport, in stores, but our appetite for observing people in extremely personal circumstances doesn’t seem to wane.” Mr. Milo also noted a connection between Mr. Yoshiyuki’s work and surveillance photography. “The photographs are specifically of their time and place and reflect the social and economic spirit of the 1970s in Japan,” he wrote in an e-mail message. “Yet the work is also very contemporary. With new technologies providing the means to spy on each other, a political atmosphere that raises issues about the right to privacy and a cultural climate obsessed with the personal lives of everyday people, themes of voyeurism and surveillance are extremely topical and important in the U.S. right now.” Yet earlier artists also went to great lengths to capture transgressive behavior. In the 1920s Brassai photographed the prostitutes of Paris at night; his camera was conspicuously large, but his subjects were willing participants. More recently, in the early 1990s, Merry Alpern set up a camera in the window of one New York apartment and photographed the assignations of prostitutes through the window of another. Susan Kismaric, curator of photography at the Museum of Modern Art, agrees that Mr. Yoshiyuki’s work falls into a photographic tradition. “The impulse is the same,” she said. “To bring forth activity, especially of a sexual nature, that ‘we’ don’t normally see. It’s one of the primary impulses in making photographs — to make visible what is normally invisible.” “The predatory, animalistic aspect of the people in Yoshiyuki’s work is particularly striking,” she continued. “The pictures are bizarre and shocking, not only because of the subject itself but also because of the way that they challenge our clichéd view of Japanese society as permeated by authority, propriety and discipline.” Sandra S. Phillips is organizing an exhibition on surveillance imagery for the San Francisco Museum of Modern Art next year. “A huge element of voyeuristic looking has informed photography and hasn’t been studied as it should be,” she said. “Voyeurism and surveillance are strangely and often uncomfortably allied. I think Yoshiyuki’s work is amazing, vital and very distinctive. “It is also, I feel, strangely unerotic, which I find very interesting since that is the subject of the pictures. I would compare him to Weegee, one of the great photographers who was also interested in looking at socially unacceptable subjects, mainly the bloody and violent deaths of criminals.” The raw graininess in Mr. Yoshiyuki’s pictures is similar to the look of surveillance images, but there is an immediacy suggesting something more personal: that here is a person making choices, not a stationary camera recording what passes before it. As Vince Aletti writes in the publication accompanying the current show, Mr. Yoshiyuki’s pictures “recall cinéma vérité, vintage porn, frontline photojournalism and the hectic spontaneity of paparazzi shots stripped of all their glamour.” Surveillance images, so far, do not have that signature. http://www.nytimes.com/2007/09/23/ar...gn/23geft.html  China Bans "Sexual Sounds" on Airwaves China has banned "sexually provocative sounds" on television and pulled the plug on a show reconstructing infamous crimes by women ahead of a major Communist Party meeting next month. The order, issued by the State Administration of Radio, Film and Television, is the latest in a raft of measures which have included axing reality shows featuring sex changes and plastic surgery and banning talent contests during prime-time. "Sexually suggestive advertisements and scenes showing how women are influenced into a life of crime are detrimental to society," it said in a statement posted on its Web site on Wednesday, referring to its decision to axe "Red Question Mark," a crime documentary. "Commercials containing sexually provocative sounds or tantalizing language as well as vulgar advertisements for breast enhancement and female underwear are banned, effective immediately," said the SARFT notice. The watchdog also ordered an end to programs with titles including the names of "sex-related drugs, products or medical institutions." A total of 1,466 advertisements worth 2 billion yuan ($246 million) in revenues had been stripped from China's airways since August, SARFT said, citing department statistics. Since launching a campaign to purify China's state-controlled airways earlier in the year, the media watchdog's edicts have gained fever pitch in recent weeks, ahead of a meeting of the 17th Party congress, a sensitive five-yearly meeting at which key government leaders are appointed and national policy set for the next few years. It earlier urged the country's increasingly freewheeling broadcasters to forgo vulgarity and bad taste in the pursuit of ratings in favor of providing "inspiring" content for the masses imbued with "socialist" values. http://www.reuters.com/article/oddly...T7470320070926  Nan Goldin Photo Yanked from Exhibit UPI Police have removed a photograph taken by a U.S. artist and owned by Elton John from a British gallery on the grounds it may violate child pornography laws. The Nan Goldin picture, which depicts two young girls -- one of whom is sitting down with her legs apart -- was seized the day before it was to go on display at the BALTIC Centre for Contemporary Art in Gateshead, The Daily Telegraph said Tuesday. The picture was slated to appear along with some of Goldin’s other work, but police removed it for fear it violated the 1978 Protection of Children Act, the British newspaper said. The photo was being examined by lawyers at the Crown Prosecution Service. Officials at the gallery confirmed the police were involved, but declined to say who had decided the picture should be removed. Well-known for her pictures of young, semi-clothed girls, Goldin has had her work taken off display before because critics thought it was obscene. Elton John, a close friend of Goldin's, was not available for comment and a spokesman for the rock star referred The Telegraph's inquiries to the gallery. http://www.upi.com/NewsTrack/Enterta..._exhibit/5950/  Town Is Shaken After Prosecutor’s Arrest in a Child-Sex Sting Abby Goodnough To neighbors here, J. D. Roy Atchison was a deft federal prosecutor, an involved father and a devoted volunteer, coaching girls’ softball and basketball teams year in and year out. His wife is a popular science teacher; his youngest daughter, an honors student who was on her high school homecoming court last year. Their house, with rocking chairs on the porch, oaks in the yard and a wrought-iron fence, is among the prettiest in town. But in an instant last week, the community pillar became an object of community loathing. Mr. Atchison, 53, was arrested getting off a plane in Detroit on Sept. 16 and charged with the unthinkable. The authorities there said he was carrying a doll and petroleum jelly, and that he had arranged with an undercover agent to have sex with a 5-year-old girl. Now Mr. Atchison is awaiting trial in a federal prison in Michigan, and the people of Gulf Breeze, an affluent bayside suburb in the Florida Panhandle, are outraged, baffled and repulsed. “He had an excellent reputation,” said Barry Beroset, a criminal defense lawyer in Pensacola who has known Mr. Atchison for 15 years. “He was very businesslike and appeared to be a very good man, no question about it.” Ronald Johnson, a defense lawyer in Pensacola who has worked with Mr. Atchison, described him as “fairly intellectual,” adding, “Sometimes he was a little eccentric, but nothing perverted or weird. Just a little different.” Pressed, Mr. Johnson could not elaborate. In fact, no one could describe Mr. Atchison in a way that transcended generalities. In interviews around this town of 6,450, the phrase “nice guy” came up a lot. Edwin A. Eddy, the city manager, said he was “no more charismatic than anybody else” and “not any quieter or more gregarious than anyone else.” Mr. Eddy said he had scoured his memory for any clue that Mr. Atchison, who he said seemed “as straight as they come,” was not. “I constantly think about all the interactions I had with Mr. Atchison over the years,” said Mr. Eddy, who coached softball with him, “and I think, ‘Should I have been able to see something?’ ” What the authorities saw in the Internet sting operation that led to Mr. Atchison’s arrest was a man who led a second life as “fldaddy04,” the moniker on a Yahoo profile traced to him. “I adore everything about young girls,” the profile says, “how they talk, think, act, walk, look.” The police in Michigan said Mr. Atchison had been chatting online for two weeks with an undercover detective for the Macomb County Sheriff’s Department, who posed as a mother offering to let men have sex with her young daughter. When she expressed concern that sex could injure the girl, according to court documents, Mr. Atchison responded, “I’m always gentle and loving; not to worry; no damage ever; no rough stuff ever ever.” He added, “I’ve done it plenty.” People here found that statement especially chilling, though the Gulf Breeze Police Department said that so far, no one here has come forward with accusations of abuse. “There’s so many unanswered questions,” said Deputy Police Chief Robert Randle. “So many people had children involved with him. But unless somebody steps forward and lodges a complaint, we have nothing to go on.” Mr. Atchison has worked at the small United States Attorney’s Office in Pensacola since the 1980s, most recently handling asset forfeitures in criminal cases as an assistant United States attorney. In one high-profile case, Mr. Atchison oversaw the government seizure of a popular beach bar at the center of a cocaine-trafficking ring. His is considered one of the most conservative United States attorney’s offices in the country, known for refusing plea agreements and seeking the stiffest sentences. Mr. Johnson said Mr. Atchison was close with the other prosecutors in his office, going with some on an annual lobster-diving trip in the Florida Keys. A big white fishing boat sat in his otherwise-empty driveway this week. His interests, according to the Yahoo profile that the police said was his, include “surfing, skiing, diving, boating, young girls, petite girls, skinny girls.” The F.B.I., which is working with Macomb County in the investigation, said that in one of his last e-mail exchanges with the undercover agent, Mr. Atchison told her to tell her daughter that “you found her a sweet boyfriend who will bring her presents.” Mr. Atchison has pleaded not guilty to charges of traveling across state lines to have sex with a child under 12, using the Internet to entice a minor and traveling to another state to engage in illicit sex. He could face life in prison if convicted. He tried to hang himself with a bed sheet in his jail cell last week after assuring his lawyer and a judge that he would not harm himself. The lawyer, James C. Thomas of Detroit, did not return a call seeking comment. The F.B.I. is continuing its investigation, and Mr. Atchison’s trial is scheduled to start Nov. 27. One night this week, as evening fell on the broad playing fields at Shoreline Park, down the road from Mr. Atchison’s house, several parents expressed shock at Mr. Atchison’s arrest as their children kicked soccer balls, threw passes and learned cheerleading stunts. Richard McLeod, a father of two, said he had asked his 6-year-old daughter if she recognized Mr. Atchison’s photo to quell fears about her safety. She did not. “They ought to torch this guy,” Mr. McLeod said. Holly Cook, a homemaker who was watching her two sons, 3 and 1, at the park earlier in the day, wondered aloud whether the local sports association should psychologically screen coaching candidates from now on, but concluded it would be impractical. “Coaches put in tons of time,” Ms. Cook said. “How can you ask them to take a psychological evaluation on top of that?” Mr. Eddy said that while parents sometimes asked that their children not be assigned to certain coaches in the sports program, none had ever complained about Mr. Atchison, who was also president of the Gulf Breeze Athletic Association. “Nobody ever had any negative comments,” Mr. Eddy said. “Nobody ever said, ‘Anybody but this guy.’ ” Around town, praise flowed for Mr. Atchison’s wife, Barbara, who teaches anatomy at Gulf Breeze High School but took a leave of absence after his arrest. She won the town’s teacher-of-the-year award in 2004. Several people said she was as stunned as anyone by the news. “She’s shell shocked,” said Deputy Chief Randle, who went with F.B.I. agents to execute a search warrant on the Atchison home, where they seized at least one computer. “She’s just floored.” Randy Sansom, an accountant whose youngest child, like Mr. Atchison’s, is a senior at the high school, said townspeople were determined to support Mrs. Atchison and her three children, two of whom are away at college. “We are here to be their friends and pray for them and know they had nothing to do with this,” Mr. Sansom said. “They are victims as well.” Terry Aguayo contributed reporting from Miami, and Mari Krueger, from Gulf Breeze, Fla. http://www.nytimes.com/2007/09/29/us/29florida.html  Facebook Subpoenaed for Not Responding to Sex Predator Complaints Michael Gormley The New York Attorney General has subpoenaed Facebook after the company did not respond to "many" complaints by investigators who were solicited for sex while posing as teenagers on the social-networking site. State investigators, who set up profiles as 12- to 14-year olds, said they were quickly contacted by other Facebook users with comments such as "u look too hot....... can i c u online," "do you like sex?" and "call me if u want to do sex with me." Investigators said that when they wrote to Palo Alto, Calif.-based Facebook about their experiences, the concerns were ignored "many" times. "My office is concerned that Facebook's promise of a safe Web site is not consistent with its performance in policing its site and responding to complaints," said Attorney General Andrew Cuomo. "Parents have a right to know what their children will encounter on a Web site that is aggressively marketed as safe." On Monday, he publicly released a letter to Facebook about its safety claims. Those concerns are based on several "undercover tests" in recent weeks, he said. The subpoenas seek complaints made to the company and copies of its policies. Cuomo said the investigation is still in its early stages. Privately held Facebook did not immediately return a phone call seeking comment. http://www.siliconvalley.com/news/ci_6985894  Microsoft Is Said to Consider a Stake in Facebook Brad Stone and Andrew Ross Sorkin Some people laughed at Mark E. Zuckerberg when he reportedly turned down a $900 million offer last year for Facebook, the social networking Web site he founded three and a half years ago. But Microsoft, Google and several funds are considering investments in the fast-growing site, according to people with knowledge of the talks, that could give the start-up a value of more than $10 billion. While discussions were still in the early stage, these people said that Microsoft was considering an investment of $300 million to $500 million for a 5 percent stake of the company. Google is also said to be interested in an investment. Facebook’s valuation could go even higher as the two rivals create the kind of competitive bidding situation that has recently driven the acquisition prices of other start-ups into the stratosphere. Representatives from Facebook, Microsoft and Google all declined to comment on the talks. The investment discussions by Facebook are part of its effort to raise an additional round of capital to further the company’s growth and build on its current momentum. The company has solicited interest not only from Internet companies but also from a handful of financial players including venture capitalists, hedge funds and private equity firms, according to people with knowledge of its plans. Facebook is seeking a minimum valuation of $10 billion but interested bidders have expressed a willingness to value it as high as $13 billion, on the assumption that, in the future, Facebook will become a powerful player in the online world. These numbers might have little basis in actual revenue or profit. Facebook is a private company and does not reveal its income. But earlier this year, a Pali Research analyst, Richard Greenfield, estimated that the company brought in $60 million to $96 million in annual revenue, with no real profit. Much of that revenue comes from a year-old advertising relationship with Microsoft, which places display advertisements on the site. Mr. Greenfield said the investment price that Microsoft was considering might have more to do with keeping the prize out of the hands of its powerful rivals. “There may be competitive reasons to be connected to this asset beyond what the specific valuation is today,” he said. “You may be paying a premium to keep others out.” The lack of a track record for Facebook might actually be driving the price up. “Trying to delineate a value today of what was a new industry five years ago is challenging right now,” Mr. Greenfield said. Last September, Yahoo was in acquisition talks with Facebook. It reportedly offered $900 million to buy the site outright and was rebuffed by Mr. Zuckerberg, the 23-year-old chief executive, who has said that he was determined to keep the company independent and take it public through an initial public offering. Google and Microsoft are jockeying for a stake in a social networking site that is said to be creating a new way for Internet users to meet people and interact with friends on the Web. In May, Facebook redefined itself as a platform, allowing other companies to create features like games, photo-sharing tools and music players that run in Facebook. That strategy, just four months old, has unleashed a flood of interest in the company, with thousands of independent software developers creating a range of programs for the service. “We have this situation where every developer worth his salt here in Silicon Valley seems to be working on a Facebook application,” said Charlene Li, an analyst at Forrester Research. Facebook is full of activities, from the goofy, like “biting” friends with a virtual vampire, to the more utilitarian, like seeing what parties and events Facebook friends are attending. There are more than 4,000 third-party applications on Facebook, the company said. The strategy has drawn plenty of attention and new users to the site. Facebook has more than 40 million members, up from 9 million last year. There may be personal reasons that Facebook would align itself with Microsoft, according to a person with knowledge of the companies’ executives. Mr. Zuckerberg has a personal friendship with Ray Ozzie, Microsoft’s chief software architect and one of the people stepping in for Bill Gates, the co-founder who is giving up his day-to-day responsibilities at the company. Also, Jim Breyer, a managing partner at the venture capital firm of Accel Partners and one of three Facebook board members, was an investor in Groove Networks, Mr. Ozzie’s company, which Microsoft purchased in 2005. The discussions between Microsoft and Facebook were first reported Monday on the Web site of The Wall Street Journal. http://www.nytimes.com/2007/09/25/te...25soft.html?hp  100Mbps Symmetrical: $48.50 Did we mention you need to live in Hong Kong? Karl Hong Kong telco City Telecom’s broadband unit Hong Kong Broadband Network (HKBN) just launched a new suite of fiber-to-the-home services in Hong Kong. Back in 2004, the company became the first to offer residential apartment customers 1Gbps symmetrical connectivity for $215 (bb1000). They've since expanded their suite of offerings if you're in the market for more modest broadband service: HKBN has turned traditionally cost prohibitive FTTH technology into affordable mass-deployed residential service, at US$48.5 service fee for its 100Mbps access service. . . . Effective immediately, HKBN will offer residential FTTH broadband services ranging from 100Mbps to 1Gbps, namely, FiberHome100, FiberHome200 and FiberHome1000, at US$48.5, US$88.2 and US$215.4 respectively. The company says they're phasing out their symmetrical 10Mbps service -- the slowest tier they offer now clocks in at a symmetrical 25Mbps. HKBN chairman Ricky Wong calls FTTH "a foreseeable inevitability." http://www.dslreports.com/shownews/1...cal-4850-87851  Where's My Free Wi-Fi? Why municipal wireless networks have been such a flop. Tim Wu It's hard to dislike the idea of free municipal wireless Internet access. Imagine your town as an oversized Internet cafe, with invisible packets floating everywhere as free as the air we breathe. That fanciful vision inspired many cities to announce the creation of free wireless networks in recent years. This summer, reality hit—one city after another has either canceled deployments or offered a product that's hardly up to the hype. In Houston, Chicago, St. Louis, and even San Francisco, once-promising projects are in trouble. What happened—was the idea all wrong? Not quite. The basic idea of offering Internet access as a public service is sound. The problem is that cities haven't thought of the Internet as a form of public infrastructure that—like subway lines, sewers, or roads—must be paid for. Instead, cities have labored under the illusion that, somehow, everything could be built easily and for free by private parties. That illusion has run straight into the ancient economics of infrastructure and natural monopoly. The bottom line: City dwellers won't be able to get high-quality wireless Internet access for free. If they want it, collectively, they'll have to pay for it. For the last 20 years or so, the thorniest economic issue in the telecommunications world has been the "last mile." Physically, the last mile consists of the wires that run from your home or business to the local phone or cable company. It's pricey and uses old technology, but almost everything depends on it and a few giant companies—like AT&T and Comcast—control it. The last mile is a bottleneck: The price and speed of the whole Internet depends on it. When people talk about the United States lagging behind the world in broadband speed and access, they're talking about the last-mile problem. In the late 1990s and early 2000s, dozens of companies were launched that had new ideas for busting through the last mile and getting the Internet into homes. I remember going to industry trade shows where grown men demonstrated robots designed to crawl through city sewers and deliver a fiber-optic cable to your toilet. (That firm, CityNet, received $375 million in funding and actually wired the sewers of Albuquerque, N.M.) Others proposed to fire laser beams at homes to bring Internet access through the proverbial bathroom window. And in 2004, the New York Times wrote that "Internet service over power lines is probably a year or more away from becoming widely available." Oh, really? While both the FCC and paid industry analysts have continually predicted an "explosion" in broadband over power lines, its current market share is approximately 0.008 percent. Each of these ventures proved a dismal failure—with the exception of satellite service in rural areas, no competitor to DSL and cable has gotten far in the United States. The startups have run into the oldest problem in the regulated industries book: the barriers to entry created by sunk costs. The phone and cable companies have already recovered the initial billions they've spent over decades, making it possible to set prices at levels that cannot be matched. The competitors brought weak products that were not substantially different. Against that kind of competition, the newcomers never stood a chance. So much for the market solution—how about government? The failures of other ventures made municipal Wi-Fi seem an ideal alternative. After all, cities provide their citizens with water and garbage pickup—why not the Internet, too? A few important points seemed to distinguish muni Wi-Fi from the toilet robots. First, wireless skipped the whole issue of feeding wires into people's homes, the stumbling block for so many ventures. And Wi-Fi routers, if not perfect, are a proven and cheap technology. They work great on college campuses. Even my mother has a Wi-Fi router. In 2004, when Philadelphia announced it was considering deploying the first major citywide Wi-Fi system, many assumed it would be free, or near-free, just like when you get Internet access from a generous neighbor. But that kind of system, of course, would cost real public money. The city would have to pay for the deployment with no hope of return. By 2005, it became clear that major cities didn't really want to build out Wi-Fi networks as public works projects. Instead, places like Philadelphia and San Francisco announced "private/public" partnerships. That meant giving a private company the right to build a wireless network and try to make money off of it. Often, this simply meant giving a company like Earthlink the rights to install Wi-Fi devices on street lamps and charge citizens for access. The cities then washed their hands of the issue of success or failure. The result, as this summer has made clear, has been telecom's Bay of Pigs—a project the government wanted to happen but left to underqualified private parties to deliver. Firms like Earthlink promised too much, and the cities have stood by and watched as the firms trying to build Wi-Fi systems have twisted and died on the beachhead. This summer, Earthlink fired half of its staff, including the head of the municipal Wi-Fi division. Major projects in Chicago and San Francisco have been stopped cold, and Houston has fined Earthlink for falling behind deadlines. Some observers blame these failures on Wi-Fi's technical limits. Wi-Fi does have serious limitations, but wireless Internet technology has worked well even on large college campuses. The deeper problem is economics. When municipal Wi-Fi became a private service, it fell into the same economic trap as the toilet robots. Private municipal wireless networks have to compete against competitors with better infrastructure who paid off their capital investments years ago. Setting up a large wireless network isn't as expensive as installing wires into people's homes, but it still costs a lot of money. Not billions, but still millions. To recover costs, the private "partner" has to charge for service. But if the customer already has a cable or telephone connection to his home, why switch to wireless unless it is dramatically cheaper or better? In typical configurations, municipal wireless connections are slower, not dramatically cheaper, and by their nature less reliable than existing Internet services. Those facts have put muni Wi-Fi in the same deathtrap that drowned every other company that peddled a new Net access scheme. Today, the limited success stories come from towns that have actually treated Wi-Fi as a public calling. St. Cloud, Fla., a town of 28,000, has an entirely free wireless network. The network has its problems, such as dead spots, but also claims a 77 percent use rate among its citizens. Cities like St. Cloud understand the concept of a public service: something that's free, or near-free, like the local swimming pool. Most cities have been too busy dreaming of free pipes to notice that their approach is hopelessly flawed. The lesson here is an old one about the function of government. When it comes to communications, the United States relies on a privateer system: We depend on private companies to perform public callings. That works up to a point, but private industry will build only so much. Real public infrastructure costs real public money. We already know that, in the real world, if you're not willing to invest in infrastructure, you get what we have: crumbling airports, collapsing bridges, and broken levees. Why did we think that the wireless Internet would be any different? http://www.slate.com/id/2174858/  Juicy I've estimated the electricity consumption for the internet as follows: US: 350 billion kWh per year World: 868 billion kWh per year These numbers represent 9.4% of total US electricity consumption, and 5.3% of global electricity consumption. =========================================================== The breakout of the data is as follows: Annual Electricity Use for the Internet--US and World Category..........................US Consumption.......World Consumption .....................................Billion kWh........Billion kWh (1) Data Centers (includes cooling)......45.................112.5 (2) PCs&Monitors........................235.................588 (3) Modems/routers/etc...................67.................167 (4) Phone network.......................0.4...................1.0 TOTAL ELECTRICITY DEMAND ~350 billion kWh ~868 billion OF THE INTERNET ............................U.S.................World http://uclue.com/index.php?xq=724  Photocopier Translates Japanese to English at Touch of Button Specialist translators could soon be heading for job centers across the world if Fuji Xerox makes good on the technology it has developed for its latest prototype photocopy machine. The device, currently on show only in Japan, can scan a printed sheet of Japanese text from a newspaper or magazine and churn out a translation of it in Chinese, English or Korean while retaining the original layout. Flip a switch and the linguistic parsing works in the opposite direction too. Fuji Xerox’s secret lies in networking the unnamed copier to a dedicated translation server and combining this with algorithms that can distinguish between text, drawings and lines for maintaining page layouts. While the concept of a one-touch translation machine is a wonderful idea for anyone who regularly works in multiple languages (guilty…), let’s hope the technology moves on from the current generation of machine-translation (MT) software that can be seen mangling sentences on sites like Babel Fish and Google Translate. http://www.digitalworldtokyo.com/ind...h_of_butto n/  What to Watch? How About a ‘Simpsons’ Episode From 1999? Claire Atkinson To get caught up with the ABC show “Grey’s Anatomy,” Joanna Palmer, who had never watched the two-year-old series, bought a DVD set of the entire first season and indulged in a marathon viewing session. “I had the day off and watched it all day, from 10 a.m. until my husband got home at 5:30,” said Ms. Palmer, 34, a merchandising assistant at Victoria’s Secret who lives in Brooklyn. “It was awesome.” Now, she plans to watch all of the new season, which starts this week. Ms. Palmer is in good company. Although DVD sales are down this year, television series on disc have fared better than other categories. Sales of complete seasons are a rare bright spot, registering actual growth. Some shows, like “Friends,” “Sex and the City” and “The Sopranos,” have each sold more than $300 million in DVDs. Those numbers are not staggering, and expectations for the format are limited by the growing number of alternatives, like Internet downloads to streaming video. Even so, the enduring appeal of the DVD and its ability to get time-pressed consumers hooked on shows are giving network executives renewed faith in the format and prompting some experimentation. “The great thing about having a TV series is that new viewers discover the franchise every day, and they come through season one,” said Sofia Chang, vice president of marketing at HBO Video. “Even though ‘The Sopranos’ is eight years old, you still have new people coming to the franchise.” HBO is not the only network looking to DVD sales to refresh its shows’ popularity. “Jericho,” a dark serial on CBS about a town cut off from the rest of the world, was canceled last year in its first season and then revived, in part because of fan pressure. To build momentum for “Jericho,” CBS Television Distribution is pointedly releasing the first season on DVD in October. John Miller, chief marketing officer of NBC Universal Television Group, said that DVDs are not necessarily expected to generate profit for the network, but are considered valuable because of their power to turn casual viewers into loyal ones. [NBC said last week that it would start offering free ad-supported downloads of its popular shows on its Web site.] To get discs into people’s hands, NBC Universal made a deal with Starbucks in July to sell a DVD with highlights from “Saturday Night Live” as well as an episode of “30 Rock.” Tina Fey, the star of “30 Rock,” is a former “Saturday Night Live” cast member, and the idea was that longtime “SNL” fans might be tempted to sample the newer show for the first time. The discs went on sale in late August, timed to whet demand for the fall season. In a separate deal, NBC Universal worked with Wal-Mart to create a half-season pack of “Friday Night Lights” for $9.99, with promotions for a new show, “Bionic Woman,” thrown in. “They’re doing it as a break-even,” Mr. Miller said. In the case of “Friday Night Lights,” NBC is even offering a money-back guarantee. DVDs have also given life to many series beyond their small-screen run. Take, for example, “Babylon 5,” a science-fiction cult hit that ran from 1994 to 1998. In July, Warner Home Video began distributing “Babylon 5: The Lost Tales” on DVD, with fresh episodes of the defunct show. J. Michael Straczynski, who created the series, said that going straight to DVD appealed to him more than reviving the show through a network. “The idea that such a venue could lead to considerable creative freedom was tremendously appealing,” he said in an e-mail interview. Similarly, with “Battlestar Galactica” soon to end its run on the Sci-Fi Channel, Universal Media Studios is filming a separate spinoff alongside the final season. “Battlestar Galactica: Razor (Unrated Extended Edition)” will be out on DVD in December. But even strong demand will not bring some shows to DVD, because of the high cost of securing music rights. Many shows were made before the DVD format was developed, and transferring the content to the newer format can require making fresh deals with the actors or musicians. The music rights on the “Happy Days” DVD, for instance, were reported to cost as much as $1 million. For this reason, fans of the series “The Wonder Years,” which ran from 1988 to 1993, will most likely never be able to see the shows on DVD, and why fans of “WKRP in Cincinnati” sometimes express disappointment with the DVD version, which by necessity swapped out many of the original songs (substitutions that sometimes make the dialogue seem illogical). Nostalgia clearly drives a lot of DVD sales. Among the 300,000 registered users of the Web site www.tvshowsondvd.com, “The Wonder Years” is the most in-demand unreleased show, followed by “Batman,” “Daria” and “Third Watch.” At Amazon.com, “The Muppet Show” is a regular top seller. “As people enter adulthood, they want to go back and buy shows from their childhood,” said Dan Vancini, a movie editor at Amazon. TVshowsondvd, which is backed by TV Guide magazine, tracks the release dates for various shows, a schedule that looks like an amalgam of different eras. For example, tomorrow is the scheduled release date for volume two of the first season of “The Streets of San Francisco” (from the early 1970s), lost episodes from “Davey and Goliath” (a religious animated show that ran from 1960 to 1977) and the best of “The Cosby Show” (1984-92), among others. “At some companies, they have great synergy between the TV division and the DVD division,” said Gord Lacey, the founder of TVshowsondvd. “Sometimes they don’t talk. If you’re the guy doing the budget for a TV show and licensing the DVD rights to the music you want is going to add to your budget, why would you do that if you don’t get any benefit?” But network executives have grown wise to the problem. “More and more, we are out obtaining DVD rights at the beginning of the licensing process in one all-encompassing rights package,” said Alexandra Patsavas, music supervisor on “Grey’s Anatomy.” “This ensures that the producer’s first choices for bands and songs are included on the DVDs and the audience sees the episodes intact with the original soundtrack.” Ms. Patsavas, who has also worked on Fox’s “The O.C.” — another show known for its catchy tunes — says that in the late 1990s, bands were not that interested in working with television executives, fearing that they would be perceived as less than cool. But “the music business has changed, and TV licensing is now seen as both an artistic and marketing opportunity for both new and established artists,” she said. October marks the start of the fourth quarter, the heaviest promotion period on the DVD sales calendar. So far this year, sales of complete seasons of TV shows on DVD are up 6 percent from the comparable period last year, according to Nielsen VideoScan (although growth has slowed from a 17 percent rise in 2006 over 2005). The figures are noteworthy given that total DVD sales are down 7 percent this year, with the overall television segment down only 1 percent. Not all popular shows perform well on DVD. Highly rated procedural dramas like “C.S.I.” and “Law and Order” are not strong sellers, and reality shows do even worse. “American Idol, Seasons 1-4” ranked No. 14,672 on the Amazon charts on Sept. 10, and costs just $7. Evan Shapiro, executive vice president and general manager at the Independent Film Channel, said that the poor performance of reality shows on DVD and other markets has helped spur demand for more scripted programming. Unlike at other networks, he said, at IFC, the television broadcast is viewed as a marketing platform for DVDs. For instance, IFC decided to reintroduce the former Fox sitcom “Greg the Bunny” on the basis of its strong DVD sales. Despite the wide range of television viewing options provided by the likes of iTunes from Apple, executives say they are confident that the DVD format will endure; DVDs are portable and can be played on a variety of devices. “As soon as I found out that ‘West Wing’ had been canceled, I went out and bought the whole collection,” said Lee Westerfield, a media analyst at BMO Capital Markets. Steve Feldstein, a senior vice president at 20th Century Fox Home Entertainment, says he thinks that sales of complete series on DVD have remained buoyant simply because there are a lot of good shows around. Pilot episodes that cost upward of $5 million are common, putting TV production values on par with movies. Mr. Feldstein suggests that viewers were more likely to catch up on a single episode via iTunes or an Internet download, while still buying a collector’s boxed set. “Anyone who is a fan is going to want nice packaging with all the extras,” he said. http://www.nytimes.com/2007/09/24/bu...dia/24dvd.html  New Series: Women Test Mettle, and Metal Alessandra Stanley When future anthropologists study prime-time television at the dawn of the 21st century, they will inevitably have to grapple with one gnawing question: What was so bad about Lindsay Wagner? NBC has remade “The Bionic Woman” (and lost the article in the title) almost as a rebuke to the original 1970s show that starred Ms. Wagner as Jaime Sommers, a professional tennis player who, after a sky-diving accident, receives artificial body parts that give her superhuman abilities. The new $6 million woman — though the bionic program, like any other military project today, would be measured as a percentage of the total economy, and, adjusted for inflation and changes in the gross domestic product, come in at about $50 million — is played by Michelle Ryan as a sullen bartender turned cyborg. Jaime 2.0 wakes up from a car crash with new legs, a new arm, a new ear and a new eye and nary a scratch on her face, and is not the least bit grateful. NBC’s show, which is more about fembot martial arts and slick “Matrix”-ish special effects than about character development, is oriented toward young male viewers. There is no such excuse for ABC’s “Private Practice,” a spinoff of “Grey’s Anatomy,” which is also on tonight and supposedly offers a postfeminist sensibility that is more playful and palatable than the overearnest women’s lib of the Lindsay Wagner generation. Dr. Addison Forbes Montgomery (Kate Walsh), a top-notch surgeon, has left Seattle to heal her broken heart in Los Angeles, where her best friend has founded a private wellness clinic. She is no longer surrounded by the kind of strong, tough, ambitious surgeons played by Sandra Oh and Chandra Wilson. Instead her new colleagues collectively offer one of the most depressing portrayals of the female condition since “The Bell Jar.” Or worse: The premiere showcases seven different women, doctors and their patients, in various states of anger, insecurity and neediness. It’s like a Hogarth engraving of the seven stages of womanly despair, “A Surgeon’s Progress.” Both shows suggest that the easiest way to make a female protagonist likable is to dumb her down with self-doubt. The heroine of “Bionic Woman” starts out as a single, pregnant bartender who doesn’t understand what her scientist boyfriend sees in her. On “Private Practice” Addison is a leading neonatal specialist who freaks out, in front of her patient’s father, when she has to perform an emergency Caesarean in a clinic, not a fully equipped hospital. “Bionic Woman” is dark, not polyester bright, but it isn’t much better than the original at depicting running at superspeed. The new series is filmed in the sleek, washed-out palette that is currently so fashionable on shows like “Heroes” and “Prison Break.” “Bionic Woman” also follows the current fad for serialized confusion: There is a mysterious conspiracy surrounding the bio-military experiments at a research center that keeps the plot murky and drives characters to speak in terse, enigmatic undertones. Jaime’s boyfriend, Will Anthros (Chris Bowers), is a bionics expert and surgeon who performs a top-secret experimental operation to save her life — without permission from his superiors, who include a stern taskmaster, Jonas Bledsoe (Miguel Ferrer). Jaime discovers that she is not the first female cyborg or even the most unpleasant. Sarah Corvus (Katee Sackhoff), a pasty platinum blonde who looks a little like Courtney Love on steroids, was the earliest prototype, and designed to serve as a soldier. Sarah appears to have morphed into a rogue agent and lurks in the shadows, stalking and attacking people, including Jaime. Sarah should be dead but isn’t. When she isn’t trying to kill former associates, even she has a needy side: “Tell me you love me,” she repeatedly implores men. All the women on “Private Practice” are looking for love, and they are all making a mess of it. Addison’s old friend Naomi Bennett (Audra McDonald) is a fertility specialist whose husband, a partner in the clinic, has moved out. Naomi can barely keep her rage under wraps at the office; at home she locks herself in the bathroom with an entire cake and tearfully scarfs it down. Their other female colleague is a psychiatrist, Dr. Violet Turner (Amy Brenneman), who between patients stalks her former boyfriend, who is married to someone else. And so on. The fact that the men in the practice are heels isn’t much consolation. Viewers don’t need to be feminists to yearn to turn the clock back 30 years to when Ms. magazine had half a million readers, the Equal Rights Amendment seemed on the brink of ratification, and Ms. Wagner played an accomplished professional who was courteous, well balanced and actually seemed to like herself. PRIVATE PRACTICE ABC, tonight at 9, Eastern and Pacific times; 8, Central time. Shonda Rhimes, creator and executive producer; Betsy Beers, Marti Noxon, Mark Gordon and Mark Tinker, executive producers. An ABC Studios production. WITH: Kate Walsh (Dr. Addison Forbes Montgomery), Tim Daly (Dr. Pete Wilder), Audra McDonald (Dr. Naomi Bennett), Paul Adelstein (Dr. Cooper Freedman), KaDee Strickland (Dr. Charlotte King), Chris Lowell (William Dell Parker), Taye Diggs (Dr. Sam Bennett) and Amy Brenneman (Dr. Violet Turner). BIONIC WOMAN NBC, tonight at 9, Eastern and Pacific times; 8, Central time. David Eick and Jason Smilovic, executive producers. Produced by Universal Media Studios. WITH: Lucy Hale (Becca Sommers), Michelle Ryan (Jaime Sommers), Chris Bowers (Will Anthros), Miguel Ferrer (Jonas Bledsoe), Will Yun Lee (Jae), Molly Price (Ruth), Mark Sheppard (Dr. Anthony Anthros). http://nytimes.com/2007/09/26/arts/t...priv.html?8dpc  As the Fall Season Arrives, TV Screens Get More Cluttered Wendy A. Lee Kyra Sedgwick, star of “The Closer” on TNT, walks under a police tape and scans the screen with her flashlight. And every time she does, she makes Gretchen Corbin, a technical writer in Berkeley, Calif., irate. The promotional ads for “The Closer” run in the bottom right of the screen during other TNT programs — a graphic called a snipe. But for Ms. Corbin, who sometimes watches movies that have subtitles, the tiny images block the dialogue. “Some ad just took over the entire bottom of the screen so I missed what the characters said to each other,” said Ms. Corbin, describing a recent experience. “And it’s TV, so you can’t rewind.” Snipes are just the latest effort by network executives to cram promotions onto television screens in the age of channel surfing, ad skipping and screen-based multitasking. At first, viewers may feel a slight jolt of pleasure at the sight of a new visual effect, they say, but over time the intrusions contribute to the sense that the screen is far more cluttered — not just with ads, but with news crawls and other streams of information. For better or worse, viewers say, the additions are making the experience of watching television more closely mirror the feeling of using a computer. That may be so, network executives say, but the extra content is here to stay. The snipes — not to be confused with bugs, those network logos that pop up in screen corners during shows — are important enough to the beleaguered television industry that the networks plan to tolerate the backlash. This fall ABC is introducing the “ABC Start Here” campaign, which consists of a series of icons in the lower right of the screen that direct viewers to related content in other media, like books, DVDs and Web sites. At the end of “Ugly Betty,” for instance, a shopping icon could direct viewers to places where they could buy Betty’s shoes, or an iTunes icon could invite them to that site to buy episodes of the show. The point, said Marla Provencio, an ABC executive vice president of marketing, is “to accommodate viewers’ multimedia, multichannel habits and still lead them back to ABC.” ABC tested the icons in July and will introduce them gradually this fall to get viewers familiar with the shorthand. To minimize complaints, ABC will keep the icons and all similar visuals silent. “We do not want to invade in the viewers’ space so much that we intrude on their experience,” said Ms. Provencio. Promotional content on what the industry calls the “lower third” of the television screen is “the way of the world these days,” Ms. Provencio said. ABC, she said, tries to make sure that the embedded ads do not interrupt, say, “a dramatic moment on ‘Grey’s Anatomy’ ” but the network does want to remind people they are watching ABC. Viewers say that snipes and bugs are degrading their experience of watching television. Even some performers seem to resent the assaults on their work’s integrity. At last week’s Emmy Awards, the comedian Lewis Black delivered a blow against screen clutter, yelling, “We don’t care about the next show. We’re watching this show.” Network executives say that the trend toward busy screens is an attempt to cater to the tastes and habits of younger viewers, who reflexively toggle among screens, online and on cellphones. David Grazian, a sociologist at the University of Pennsylvania, said that television is simply borrowing a successful feature from the video game industry. “Screen clutter can be extremely eye catching, especially for the viewer who surfs between several channels,” he said. Viewers of MTV, VH1 and sports channels have come to expect frenetic programming. At ESPN, there has been a conscious effort to pump up the visual excitement of the viewing experience, said Norby Williamson, executive vice president of programming. “The key word in television these days is engagement,” he said. The network first introduced a crawling banner of sports scores to the bottom of the screen in 1985, has recently introduced more aggressive visuals, such as a Monday Night Football score box in the center of the screen that changes into other bugs and banners. Today’s viewers today are conditioned to have a lot going on at once, Mr. Williamson said, adding, “Everything is shifting. Television has to shift, too.” Sports commentators have always promoted their networks during broadcasts, but now they have extra reminders. Last month during CBS’s broadcast of the United States Open semifinals between Svetlana Kuznetsova and Anna Chakvetadze, a mini-trailer for “Survivor: China” ran on the bottom of the screen. Mary Carillo, who was providing commentary, promptly observed that Ms. Kuznetsova would likely “survive” the match (and she did). The trend toward visual clutter has also reshaped television news broadcasts, where the familiar sight of a lone anchor talking to a camera has grown increasingly rare. On CNN, the hyperactive pace of Wolf Blitzer’s nightly news show “The Situation Room” is so extreme that it was parodied on “Saturday Night Live.” With one glance at the screen, is it really possible to absorb the United States military strategy in Iraq, or that a thunderstorm is moving over the Midwest, the Standard & Poor’s index is up 16.95 points, and Sean Combs has separated from his girlfriend? “Our pixel footprint can get way out of control,” acknowledged Jonathan Klein, the president of CNN U.S., referring to the television industry in general. Research suggests that packed screens can impede comprehension. Tom Grimes, a journalism professor at Texas State University in San Marcos, Tex., said that people who are looking for quick information like stock quotes or a weather update can handle a certain amount of clutter. But “if they’re trying to listen to a reporter describe a complicated series of events, it’s very difficult to absorb that information” with too great a visual barrage, he said. With the Internet offering an increasingly sophisticated yet chaotic visual experience, television must decide how much it wants to mimic the computer, said Aslam Khader, vice president for marketing and strategy of Ensequence Inc., an interactive media company in Portland, Ore. “TV is having to reinvent itself,” he said. The question remains how many self-promotions the networks can dish up without degrading the quality of their shows. Sherry Sklar, a writer in Phoenix, Ariz., said visual clutter on television “has gotten worse — more movement and more intrusive” in recent months. During a drama, if a character from a different show suddenly walks across the bottom of the screen, “it’s a total disconnect and ruins your suspension of disbelief,” Ms. Sklar said, adding, “I mainly watch PBS and HBO, probably because they don’t do as much of this stuff.” http://www.nytimes.com/2007/09/24/bu...=1&oref=slogin  Preliminary 'total viewer figure' is 7.3 million 'The War' Has Strong Ratings Start David Bauder A handful of new series got the jump on the fall TV season, none as successfully as Ken Burns' epic miniseries about World War II. The first of the seven parts of "The War" attracted 15.5 million viewers to PBS on Sunday, according to Nielsen Media Research. Add in a rerun that was telecast immediately after it was done, and an estimated 18.7 million people saw it on Sunday. (The noncommercial Public Broadcasting Service is not included in the weekly ratings.) That outpaced everything on the commercial broadcast networks all week, except for Sunday night's telecast of the Dallas-Chicago National Football League game on NBC. CBS' first telecast of the controversial reality show "Kid Nation" was seen by 9.4 million viewers. The Fox debut of the drama "K-Ville" landed just outside Nielsen's top 20 programs for last week with 8.9 million viewers. They didn't quite match the viewership for the returns of old favorites like "Cold Case," "Family Guy" and "The Simpsons," however. The return "Survivor" — this one in China — did best of all, placing No. 2 right behind football. A new TV season technically began Monday, with most of the new programming to follow. CBS won the last week of the "old" season by averaging 8.9 million prime-time viewers (5.8 rating, 10 share). NBC had 7.6 million (5.0, 8), Fox 7.4 million (4.7, 8), ABC 5.7 million (3.8, 7), the CW 2.8 million (1.8, 3), My Network TV 900,000 (0.6, 1) and ION Television 540,000 (0.4, 1). Among the Spanish-language networks, Univision averaged 3.5 million viewers last week (1.9 rating, 3 share). Telemundo had 980,000 (0.5, 1), TeleFutura 590,000 (0.3, 1) and Azteca 120,000 (0.1, 0). The evening news ratings race was essentially a dead heat, with ABC's "World News" averaging 7.69 million viewers (5.3 rating, 11 share) and NBC's "Nightly News" 7.66 million (5.3, 12). The "CBS Evening News" averaged 6.1 million (4.2, 9). A ratings point represents 1,130,000 households, or 1 percent of the nation's estimated 112.8 million TV homes. The share is the percentage of in-use televisions tuned to a given show. For the week of Sept. 17-23, the top 10 shows, their networks and viewerships: NFL Football: Dallas at Chicago, NBC, 19.05 million; "Survivor: China," CBS, 15.35 million; "CSI: Crime Scene Investigation," CBS, 14.07 million; "Sunday Night Pre-Kick Show," NBC, 13.86 million; "Cold Case," CBS, 12.75 million; "Deal or No Deal" (Monday), NBC, 11.72 million; "Shark," CBS, 11.42 million; "60 Minutes," CBS, 11.37 million; "Without a Trace," CBS, 11.28 million; "Two and a Half Men," CBS, 10.84 million. http://ap.google.com/article/ALeqM5i...6c4AAbsfWDlvgA  New DVDs Dave Kehr THE 3 PENNY OPERA Traditionally, G. W. Pabst’s 1931 film of “The 3 Penny Opera” was considered a disappointment, interesting mainly because it was the closest in time to the original stage production. The Kurt Weill and Bertolt Brecht musical opened in Berlin in 1928 and quickly became an international hit. Pabst, known for social-psychological dramas like “The Joyless Street” (1925) and “Pandora’s Box” (1929), was an understandable choice by the producers, but not, as it turned out, a particularly happy one. Apparently uncomfortable with characters bursting into song, the sober-minded Pabst threw out several numbers and curtailed others, while forcing Brecht’s anti-realist, anti-theater into a conventional realist mode. Or so it seemed, until the German-language version of the film was restored by the German film archive in 2005. Drawn from the original camera negative, this version is being released today by the Criterion Collection, and it’s a revelation. With the images restored to a digital approximation of their original clarity and depth, it seems quite a different movie. The film takes place not in a real world but in an almost cubist approximation of one. A labyrinth of shop fronts, storehouses, narrow streets and crooked alleys, where the billboards are in English but the protest placards are in German, was built inside a mammoth studio. It represents the London waterfront where Weill and Brecht’s politically charged revision of John Gay’s 18th-century satire takes place. Huge interior sets were a specialty of the Weimar cinema, exemplified by the grand hotel of F. W. Murnau’s “Last Laugh” (1924) and the Berlin boulevard of Joe May’s “Asphalt” (1929). But Pabst, working with the art director Andrej Andrejew and the cinematographer Fritz Arno Wagner, might have created the most detailed and expressive. The mobile camera seems determined to explore every nook and cranny of this tall and curiously built environment, from the pier where the street singer (Ernst Busch) relates the tale of Mack the Knife, to the warehouse where Mackie marries Polly Peachum (Carola Neher) to the bordello that is home to Mackie’s spurned lover, Jenny (Lotte Lenya). Mackie Messer is played by Rudolf Forster as a cold, solid block of a man, a pillar of malevolence who draws the innocent-seeming Polly to him with one magnetic look. Polly, of course, is no shrinking virgin but the daughter of London’s beggar king, Peachum, played by Weimar’s most creative interpreter of evil, Fritz Rasp. As Tiger Brown, Mackie’s old buddy from the British Army and the current chief of the London police, Pabst cast Reinhold Schünzel, a writer-director whose 1933 “Viktor und Viktoria” was remade several times, most famously by Blake Edwards as “Victor Victoria” in 1982. And yet it is Lenya, Weill’s wife and a member of the original stage cast, who most memorably embodies the piece’s bitterly cynical yet profoundly humanitarian spirit. Here she performs “Pirate Jenny,” that heart-wrenching ballad of lyrical revenge, standing motionless before a window as Pabst cuts in on her in three progressive close-ups, leaving her isolated and astonished by her own repressed cruelty. The Criterion edition also includes the French-language version, “L’Opéra de Quat’Sous,” which Pabst filmed on the same sets, using largely the same shots but a French cast. The French version is not nearly as gripping, and not only because the music drifts toward operetta when sung in trained French voices. The casting of two conventionally attractive movie stars — Albert Préjean as Mackie, and Florelle as Polly Peachum — also strips away the hard, tawdry sexuality of the German version. What’s missing, too, in this less well preserved, much softer and flatter print, is precisely the presence of Pabst’s imagined London. Detached from the more faintly registered backgrounds, unimplicated in the receding perspectives of Pabst’s compositions, these are simply actors standing in front of a set. Here again is proof of what a fragile medium the movies are, and of how foolish it is for us to condescend to the perceived primitivism of a past that is largely a creation of our own neglect. (Criterion Collection, $39.95, not rated) THE INTRUDER The celebrated exploitation filmmaker Roger Corman used to boast that “The Intruder” was the only one of the 55 films he directed to lose money. But in an interview on the new DVD that Buena Vista is releasing today, he laughingly, if reluctantly, admits that thanks to a 2001 home video release, the picture has finally tipped into profit. As well it deserves to. For a director best known for horror films (“The Masque of the Red Death”) and motorcycle movies (“The Wild Angels”), this black-and-white social drama from 1962 is a fascinating departure. It’s a “problem picture” close in spirit to the early wave of American indies (“One Potato, Two Potato”; “Nothing but a Man”) that were starting to appear around the same time. A young William Shatner plays the title character, Adam Cramer, a man without a past who appears in a small Southern town where the white citizens are still reeling under the recent imposition of school integration. Adam appears at first like one of the “outside agitators” accused at the time of stirring up racial hatred, and so he is, though he is working the opposite side of the street. He moves through the little town, befriending its powerful and seducing its daughters, stirring up resentment against the handful of black teenagers who will soon be attending the formerly all-white high school. His motives, in the fine script by Charles Beaumont (based on his novel), are pure: ideology doesn’t concern him. His only interest is power. Somewhere between making “Teenage Cave Man” (1958) and “Creature From the Haunted Sea” (1961), Mr. Corman had become a skilled filmmaker. “The Intruder” is full of magnificently staged scenes: a midnight rally where Adam whips a crowd into a murderous frenzy, a confrontation in a hotel room between Adam and a traveling pitchman (Leo Gordon) whose wife Adam has seduced, all shot with a scientifically precise concern with framing and camera movement. You wonder, then, why this new transfer is presented “open frame,” without the matting that would have been used at the time to narrow the image to the more rectangular screen proportions we still use today. Purists will need to adjust the zoom feature on their televisions to find the proper aspect ratio, but “The Intruder” remains a powerful film and a tantalizing turning point. If this little movie had made money, the world would have known a very different Roger Corman, with a wider collection of Oscars on his mantelpiece. As for me, I’m very happy with the one we have. (Buena Vista Home Entertainment, $19.99, PG-13) http://www.nytimes.com/2007/09/25/mo...5dvd.html?8dpc  Scientists Feel Miscast in Film on Life’s Origin Cornelia Dean A few months ago, the evolutionary biologist Richard Dawkins received an e-mail message from a producer at Rampant Films inviting him to be interviewed for a documentary called “Crossroads.” The film, with Ben Stein, the actor, economist and freelance columnist, as its host, is described on Rampant’s Web site as an examination of the intersection of science and religion. Dr. Dawkins was an obvious choice. An eminent scientist who teaches at Oxford University in England, he is also an outspoken atheist who has repeatedly likened religious faith to a mental defect. But now, Dr. Dawkins and other scientists who agreed to be interviewed say they are surprised — and in some cases, angered — to find themselves not in “Crossroads” but in a film with a new name and one that makes the case for intelligent design, an ideological cousin of creationism. The film, “Expelled: No Intelligence Allowed,” also has a different producer, Premise Media. The film is described in its online trailer as “a startling revelation that freedom of thought and freedom of inquiry have been expelled from publicly-funded high schools, universities and research institutions.” According to its Web site, the film asserts that people in academia who see evidence of a supernatural intelligence in biological processes have unfairly lost their jobs, been denied tenure or suffered other penalties as part of a scientific conspiracy to keep God out of the nation’s laboratories and classrooms. Mr. Stein appears in the film’s trailer, backed by the rock anthem “Bad to the Bone,” declaring that he wants to unmask “people out there who want to keep science in a little box where it can’t possibly touch God.” If he had known the film’s premise, Dr. Dawkins said in an e-mail message, he would never have appeared in it. “At no time was I given the slightest clue that these people were a creationist front,” he said. Eugenie C. Scott, a physical anthropologist who heads the National Center for Science Education, said she agreed to be filmed after receiving what she described as a deceptive invitation. “I have certainly been taped by people and appeared in productions where people’s views are different than mine, and that’s fine,” Dr. Scott said, adding that she would have appeared in the film anyway. “I just expect people to be honest with me, and they weren’t.” The growing furor over the movie, visible in blogs, on Web sites and in conversations among scientists, is the latest episode in the long-running conflict between science and advocates of intelligent design, who assert that the theory of evolution has obvious scientific flaws and that students should learn that intelligent design, a creationist idea, is an alternative approach. There is no credible scientific challenge to the theory of evolution as an explanation for the complexity and diversity of life on earth. And while individual scientists may embrace religious faith, the scientific enterprise looks to nature to answer questions about nature. As scientists at Iowa State University put it last year, supernatural explanations are “not within the scope or abilities of science.” Mr. Stein, a freelance columnist who writes Everybody’s Business for The New York Times, conducts the film’s on-camera interviews. The interviews were lined up for him by others, and he denied misleading anyone. “I don’t remember a single person asking me what the movie was about,” he said in a telephone interview. Walt Ruloff, a producer and partner in Premise Media, also denied that there was any deception. Mr. Ruloff said in a telephone interview that Rampant Films was a Premise subsidiary, and that the movie’s title was changed on the advice of marketing experts, something he said was routine in filmmaking. He said the film would open in February and would not be available for previews until January. Judging from material posted online and interviews with people who appear in the film, it cites several people as victims of persecution, including Richard Sternberg, a biologist and an unpaid research associate at the National Museum of Natural History, and Guillermo Gonzalez, an astrophysicist denied tenure at Iowa State University this year. Dr. Sternberg was at the center of a controversy over a paper published in 2004 in Proceedings of the Biological Society of Washington, a peer-reviewed publication he edited at the time. The paper contended that an intelligent agent was a better explanation than evolution for the so-called Cambrian explosion, a great diversification of life forms that occurred hundreds of millions of years ago. The paper’s appearance in a peer-reviewed journal was a coup for intelligent design advocates, but the Council of the Biological Society of Washington, which publishes the journal, almost immediately repudiated it, saying it had appeared without adequate review. Dr. Gonzalez is an astrophysicist and co-author of “The Privileged Planet: How Our Place in the Cosmos Is Designed for Discovery” (Regnery, 2004). The book asserts that earth’s ability to support complex life is a result of supernatural intervention. Dr. Gonzalez’s supporters say his views cost him tenure at Iowa State. University officials said their decision was based, among other things, on his record of scientific publications while he was at the university. Mr. Stein, a prolific author who has acted in movies like “Ferris Bueller’s Day Off” and appeared on television programs including “Win Ben Stein’s Money” on Comedy Central, said in a telephone interview that he accepted the producers’ invitation to participate in the film not because he disavows the theory of evolution — he said there was a “very high likelihood” that Darwin was on to something — but because he does not accept that evolution alone can explain life on earth. He said he also believed the theory of evolution leads to racism and ultimately genocide, an idea common among creationist thinkers. If it were up to him, he said, the film would be called “From Darwin to Hitler.” On a blog on the “Expelled” Web site, one writer praised Mr. Stein as “a public-intellectual-freedom-fighter” who was taking on “a tough topic with a bit of humor.” Others rejected the film’s arguments as “stupid,” “fallacious” or “moronic,” or described intelligent design as the equivalent of suggesting that the markets moved “at the whim of a monetary fairy.” Mr. Ruloff, a Canadian who lives in British Columbia, said he turned to filmmaking after selling his software company in the 1990s. He said he decided to make “Expelled,” his first project, after he became interested in genomics and biotechnology but discovered “there are certain questions you are just not allowed to ask and certain approaches you are just not allowed to take.” He said he knew researchers, whom he would not name, who had studied cellular mechanisms and made findings “riddled with metaphysical implications” and suggestive of an intelligent designer. But they are afraid to report them, he said. Mr. Ruloff also cited Dr. Francis S. Collins, a geneticist who directs the National Human Genome Research Institute and whose book, “The Language of God: A Scientist Presents Evidence for Belief” (Simon & Schuster, 2006), explains how he came to embrace his Christian faith. Dr. Collins separates his religious beliefs from his scientific work only because “he is toeing the party line,” Mr. Ruloff said. That’s “just ludicrous,” Dr. Collins said in a telephone interview. While many of his scientific colleagues are not religious and some are “a bit puzzled” by his faith, he said, “they are generally very respectful.” He said that if the problem Mr. Ruloff describes existed, he is certain he would know about it. Dr. Collins was not asked to participate in the film. Another scientist who was, P. Z. Myers, a biologist at the University of Minnesota, Morris, said the film’s producers had misrepresented its purpose, but said he would have agreed to an interview anyway. But, he said in a posting on The Panda’s Thumb Web site, he would have made a “more aggressive” attack on the claims of the movie. Dr. Scott, whose organization advocates for the teaching of evolution and against what it calls the intrusion of creationism and other religious doctrines in science classes, said the filmmakers were exploiting Americans’ sense of fairness as a way to sell their religious views. She said she feared the film would depict “the scientific community as intolerant, as close-minded, and as persecuting those who disagree with them. And this is simply wrong.” http://www.nytimes.com/2007/09/27/sc...7expelled.html  Vitter Earmarked Federal Money for Creationist Group Bill Walsh Sen. David Vitter, R-La., earmarked $100,000 in a spending bill for a Louisiana Christian group that has challenged the teaching of Darwinian evolution in the public school system and to which he has political ties. The money is included in the labor, health and education financing bill for fiscal 2008 and specifies payment to the Louisiana Family Forum "to develop a plan to promote better science education." The earmark appears to be the latest salvo in a decades-long battle over science education in Louisiana, in which some Christian groups have opposed the teaching of evolution and, more recently, have pushed to have it prominently labeled as a theory with other alternatives presented. Educators and others have decried the movement as a backdoor effort to inject religious teachings into the classroom. The nonprofit Louisiana Family Forum, launched in Baton Rouge in 1999 by former state Rep. Tony Perkins, has in recent years taken the lead in promoting "origins science," which includes the possibility of divine intervention in the creation of the universe. The group's stated mission is to "persuasively present biblical principles in the centers of influence on issues affecting the family through research, communication and networking." Until recently, its Web site contained a "battle plan to combat evolution," which called the theory a "dangerous" concept that "has no place in the classroom." The document was removed after a reporter's inquiry. Vitter, Forum have ties The group's tax-exempt status prohibits the Louisiana Family Forum from political activity, but Vitter has close ties to the group. Dan Richey, the group's grass-roots coordinator, was paid $17,250 as a consultant in Vitter's 2004 Senate race. Records also show that Vitter's campaign employed Beryl Amedee, the education resource council chairwoman for the Louisiana Family Forum. The group has been an advocate for the senator, who was elected as a strong supporter of conservative social issues. When Vitter's use of a Washington, D.C., call-girl service drew comparisons last month to the arrest of Sen. Larry Craig, R-Idaho, in what an undercover officer said was a solicitation for sex in an airport men's room, Family Forum Executive Director Gene Mills came to Vitter's defense. In a video clip the group posted on the Internet site YouTube, Mills said the two senators' situations are far different. "Craig is denying the allegations," he said. "Vitter has repented of the allegations. He sought forgiveness, reconciliation and counseling." Vitter's office said it is not surprising that people he employed would also do work for Louisiana Family Forum, which shares his philosophical outlook. He said the education earmark was meant to offer a broad array of views in the public schools. "This program helps supplement and support educators and school systems that would like to offer all of the explanations in the study of controversial science topics such as global warming and the life sciences," Vitter said in a written statement. The money in the earmark will pay for a report suggesting "improvements" in science education in Louisiana, the development and distribution of educational materials and an evaluation of the effectiveness of the Ouachita Parish School Board's 2006 policy that opened the door to biblically inspired teachings in science classes. "I believe it is an important program," Vitter said. Critics said taxpayer money should not go to support a religion-based program. "This is a misappropriation of public funds," said Charles Kincade, a civil rights lawyer in Monroe who has been involved in church-state cases. "It's a backdoor attempt to push a religious agenda in the public school system." Group has history Former Sen. Rick Santorum, R-Pa., a Christian conservative defeated for re-election in 2004, attempted to open the door for such money when he inserted language into a report accompanying the 2001 No Child Left Behind Act enabling teachers to offer "the full range of scientific views" when "topics that may generate controversy (such as biological evolution)" are taught. In 1987, the U.S. Supreme Court threw out a Louisiana law that would have required schools to teach creationist theories, which hold that God created the universe, whenever evolution was taught. In 2002, the Louisiana Family Forum unsuccessfully sought to persuade the state Board of Elementary and Secondary Education to insert a five-paragraph disclaimer in all of its science texts challenging the natural science view that life came about by accident and has evolved through the process of natural selection. The group notched a victory last year when the Ouachita School Board adopted a policy that, without mentioning the Bible or creationism, gave teachers leeway to introduce other views besides those contained in traditional science texts. "Many of our educators feel inadequate to address the controversies," said Mills, executive director of the Louisiana Family Forum. Mills said that his group didn't request the money in the 2008 appropriations bill, and that Vitter's proposal "was a bit of a surprise." Mills said his group is not attempting to push the teaching of evolution out of the schools, but wants to supplement it. Yet, some of the material posted on the Louisiana Family Forum's Web site suggests a more radical view. Among other things, a "Louisiana Family Forum Fact Sheet" at one point included "A Battle Plan -- Practical Steps to Combat Evolution" by Kent Hovind, a controversial evangelist who is serving a 10-year prison sentence for tax offenses and obstruction of justice. Hovind's paper stated, "Evolution is not a harmless theory but a dangerous religious belief" that underpinned the atrocities committed by Adolf Hitler, Joseph Stalin and Pol Pot of the Khmer Rouge in Cambodia. Looking deeper urged "I've got so much stuff on the Web site I don't know what's there," Mills said. "We think that in order to teach controversial topics successfully, you have to teach both sides." The group's "Evolution Addendum for Public Schools," also posted on the Web site, offers a flavor of its concerns. The document rejects the evolutionary connection between apes and humans, questions the standard explanation of fossil formation and seeks to undercut the prevailing scientific view that life emerged from a series of chemical reactions. "Under ideal conditions, the odds of that many amino acids coming together in the right order are approximately the same as winning the Power Ball Lotto every week for the next 640 years," it states. "How could this have happened accidentally?" Kincade, the Monroe lawyer, said Vitter's and Louisiana Family Forum's motives are not benign. "What you have to do is look below the surface," said Kincade, who holds an undergraduate degree in physics and has been active in legal cases in which religious groups challenge science instruction. "It frames the issue in a way that appeals to America's sense of fair play. The problem is, except for fringe people, evolution is an accepted fact of science. It is not a hotly contested issue. The general concept of natural selection and evolution is settled and beyond dispute. To suggest otherwise is misleading. They are trying to backdoor creationism." Vitter's appropriation was contained in a database compiled by Taxpayers for Common Sense, a nonprofit group seeking to reduce the number of earmarks in federal legislation. Earlier this year, Congress agreed for the first time to begin linking specially requested earmarks to the names of their sponsors. Taxpayers for Common Sense has compiled thousands of them into searchable databases. Vitter said the financing request was submitted earlier this year and "was evaluated on its merit." But Steve Ellis, of the taxpayers' group, said most earmarks are not vetted by anyone except the member requesting it. "Using an earmark to dictate that the Louisiana Family Forum receive the funding to develop a science education program ironically ignores a hallmark of scientific research, making decisions on the basis of competitive, empirical research," Ellis said. The appropriations bill is awaiting Senate action. http://blog.nola.com/times-picayune/...ral_money.html  Teacher: I was Fired, said Bible Isn't Literal The community college instructor says the school sided with students offended by his explanation of Adam and Eve. Megan Hawkins A community college instructor in Red Oak claims he was fired after he told his students that the biblical story of Adam and Eve should not be literally interpreted. Steve Bitterman, 60, said officials at Southwestern Community College sided with a handful of students who threatened legal action over his remarks in a western civilization class Tuesday. He said he was fired Thursday. "I'm just a little bit shocked myself that a college in good standing would back up students who insist that people who have been through college and have a master's degree, a couple actually, have to teach that there were such things as talking snakes or lose their job," Bitterman said. Sarah Smith, director of the school's Red Oak campus, declined to comment Friday on Bitterman's employment status. The school's president, Barbara Crittenden, said Bitterman taught one course at Southwest. She would not comment, however, on his claim that he was fired over the Bible reference, saying it was a personnel issue. "I can assure you that the college understands our employees' free-speech rights," she said. "There was no action taken that violated the First Amendment." Bitterman, who taught part time at Southwestern and Omaha's Metropolitan Community College, said he uses the Old Testament in his western civilization course and always teaches it from an academic standpoint. Bitterman's Tuesday course was telecast to students in Osceola over the Iowa Communications Network. A few students in the Osceola classroom, he said, thought the lesson was "denigrating their religion." "I put the Hebrew religion on the same plane as any other religion. Their god wasn't given any more credibility than any other god," Bitterman said. "I told them it was an extremely meaningful story, but you had to see it in a poetic, metaphoric or symbolic sense, that if you took it literally, that you were going to miss a whole lot of meaning there." Bitterman said he called the story of Adam and Eve a "fairy tale" in a conversation with a student after the class and was told the students had threatened to see an attorney. He declined to identify any of the students in the class. "I just thought there was such a thing as academic freedom here," he said. "From my point of view, what they're doing is essentially teaching their students very well to function in the eighth century." Hector Avalos, an atheist religion professor at Iowa State University, said Bitterman's free-speech rights were violated if he was fired simply because he took an academic approach to a Bible story. "I don't know the circumstances, but if he's teaching something about the Bible and says it is a myth, he shouldn't be fired for that because most academic scholars do believe this is a myth, the story of Adam and Eve," Avalos said. "So it'd be no different than saying the world was not created in six days in science class. "You don't fire professors for giving you a scientific answer." Bitterman said Linda Wild, vice president of academic affairs at Southwest, fired him over the telephone. Wild did not return telephone or e-mail messages Friday. Bitterman said that he can think of no other reason college officials would fire him and that Smith, the director of the campus, has previously sat in on his classes and complimented his work. "As a taxpayer, I'd like to know if a tax-supported public institution of higher learning has given veto power over what can and cannot be said in its classrooms to a fundamentalist religious group," he said. "If it has ... then the taxpaying public of Iowa has a right to know. What's next? Whales talk French at the bottom of the sea?" http://www.desmoinesregister.com/app...=2007709220333  'Net Neutrality' War Comes to Fore Adam Liptak Saying it had the right to block "controversial or unsavory" text messages, Verizon Wireless last week rejected a request from Naral Pro-Choice America, the abortion rights group, to make Verizon's cellular network available for a text-message program. The other leading wireless carriers accepted the program, which allows people to ask to receive text messages from Naral by sending a message to a five-digit number known as a short code. Text messaging is a growing political force in the United States and a dominant one abroad, and such programs are used by many political candidates and advocacy groups to send updates to supporters. But legal experts said private companies like Verizon probably have the legal right to decide what messages to carry. The laws that forbid common carriers from interfering with voice transmissions on ordinary phone lines do not apply to text messages. The dispute over the Naral messages is a skirmish in the larger battle over the question of "net neutrality." "This is right at the heart of the problem," said Susan Crawford, a visiting professor at the University of Michigan law school, referring to the treatment of text messages. "The fact that wireless companies can choose to discriminate is very troubling." In turning down the program last week, Verizon told Naral that said it "does not accept issue-oriented (abortion, war, etc.) programs - only basic, general politician-related campaigns (Mitt Romney, Hillary Clinton, etc.)." Naral provided a copies of its communications with Verizon to The New York Times. Nancy Keenan, Naral's president, said Verizon's decision interferes with political speech and activism. "No company should be allowed to censor the message we want to send to people who have asked us to send it to them," Keenan said. "Regardless of people's political views, Verizon customers should decide what action to take on their phones. Why does Verizon get to make that choice for them?" A spokesman for Verizon defended the decision. "It is accurate to say that the organization and the content that they would like to distribute broadly does not fit our current content standards," said the spokesman, Jeffrey Nelson. "We continue to review our content standards with an eye toward making more information available across ideological and political views." Text messaging programs based on five and six-digit short codes are a popular way to receive updates on news, sports, weather and entertainment. Several of the leading Democratic candidates have used them, as have the Republican National Committee, Save Darfur and Amnesty International. Texting has proven to be an extraordinarily effective political tool. According to a study released this month from researchers at Princeton and the University of Michigan, young people were 4.2 percent more likely to vote in the November 2006 elections after receiving a text-message reminder. The cost per vote generated, the study said, was much smaller than other sorts of get-out-the-vote efforts. Around the world, the phenomenon is even bigger. "Even as dramatic as the adoption of text messaging for political communication has been in the United States, we've been quite slow compared to the rest of the world," said James Katz, the director of the Center for Mobile Communication Studies at Rutgers University. "It's important in political campaigns and political protests, and it has affected the outcomes of elections." Timothy Wu, a law professor at Columbia, said it is possible to find analogies to Verizon's decision abroad. "Another entity that controls mass text messages is the Chinese government," Wu said. Jed Alpert, the chief executive officer of Mobile Commons, which says it is the largest provider of mobile services to political and advocacy groups, including Naral, said he had never seen a decision like Verizon's. "This is something we haven't encountered before, that is very surprising and that we're concerned about," Alpert said. Naral provided an example of a recent text message from another program: "End Bush's global gag rule against birth control for world's poorest women! Call Congress. (202) 224-3121. Thnx! Naral Text4Choice." Messages urging political action are generally thought to be at the heart of what the First Amendment protects, legal scholars said. But the First Amendment limits government power, not that of private companies like Verizon. Some scholars said competition rather than government regulation is the appropriate response to concerns about limitations like the one imposed by Verizon. "Instead of getting in the game of regulating who can carry what," said Christopher Yoo, a law professor at the University of Pennsylvania, "I would get in the game of promoting as many options as possible. You might find text-messaging companies competing on their openness policies." In rejecting the Naral program, Verizon appeared to be acting against its economic interests. It would have received a small fee to set up the program and additional fees for messages sent and received. Naral said it may have to cancel the program given that Verizon controls about a quarter of the market. "We had hoped to spend $135,000 investing in this new form of technology," Keenan said. http://www.iht.com/articles/2007/09/...ss/verizon.php  Verizon Wireless Ends Ban On Abortion-Rights Group Kevin Kingsbury Verizon Wireless has dropped its ban on text messages from a prominent abortion-rights group one day after getting a letter from the group about the ban. Naral Pro-Choice America requested that Verizon Wireless and other carriers distribute its text messages that users sign up for by sending a message to a five- or six-digit number called a "short code." The program is used by many companies and other groups to distribute short text messages for marketing and other purposes. Verizon Wireless - owned by Verizon Communications Inc. and the United Kingdom's Vodafone Group PLC - had rejected Naral's request, citing the carrier's "code of content," which prohibits "highly controversial" content. In a statement Thursday, Verizon Wireless spokesman Jeffrey Nelson said, "The decision to not allow text messaging on an important, though sensitive, public policy issue was incorrect, and we have fixed the process that led to this isolated incident." He added, "Upon learning about this situation, senior Verizon Wireless executives immediately reviewed the decision and determined it was an incorrect interpretation of a dusty internal policy." Verizon Wireless said Thursday its policy had been developed before text messaging protections such as spam filters "adequately protected customers from unwanted messages." It was designed, the company said, to ward against communications such as anonymous hate messaging and adult materials sent to children. Verizon Wireless's had ban sparked outrage from Naral and the company hinted on Wednesday it was near loosening its restrictions. Major U.S. wireless carriers have strict decency standards for content. Many of the rules for content of partners such as providers of ring tones or mobile video go far beyond limits set by federal regulators for television and radio. A 2006 Verizon Wireless content-guideline document for its media partners, for example, lists restrictions for expletives and how much bare skin models can show and a ban on any derogatory references to Verizon Wireless. http://online.wsj.com/article/SB1190...googlenews_wsj  Prisons to Restore Purged Religious Books Neela Banerjee Facing pressure from religious groups, civil libertarians and members of Congress, the federal Bureau of Prisons has decided to return religious materials that had been purged from prison chapel libraries because they were not on the bureau’s lists of approved resources. The bureau had said it was prompted to remove the materials after a 2004 Department of Justice report mentioned that religious books that incite violence could infiltrate chapel libraries. After the details of the removal became widely known this month, Republican lawmakers, liberal Christians and evangelical talk shows all criticized the government for creating a list of acceptable religious books. The bureau has not abandoned the idea of creating such lists, Judi Simon Garrett, a spokeswoman, said in an e-mail message. But rather than packing away everything while those lists were compiled, the religious materials will remain on the shelves, Ms. Garrett explained. In an e-mail message Wednesday, the bureau said: “In response to concerns expressed by members of several religious communities, the Bureau of Prisons has decided to alter its planned course of action with respect to the Chapel Library Project. “The bureau will begin immediately to return to chapel libraries materials that were removed in June 2007, with the exception of any publications that have been found to be inappropriate, such as material that could be radicalizing or incite violence. The review of all materials in chapel libraries will be completed by the end of January 2008.” Only a week ago the bureau said it was not reconsidering the library policy. But critics of the bureau’s program said it appeared that the bureau had bowed to widespread outrage. “Certainly putting the books back on the shelves is a major victory, and it shows the outcry from all over the country was heard,” said Moses Silverman, a lawyer for three prisoners who are suing the bureau over the program. “But regarding what they do after they put them back, I’m concerned.” The bureau originally set out to take an inventory of all materials in its chapel libraries to weed out books that might incite violence. But the list grew to the tens of thousands, and the bureau decided instead to compile lists of acceptable materials in a plan called the Standardized Chapel Library Project. The plan identifies about 150 items for each of 20 religions or religious categories. In the spring, prison chaplains were told to remove all materials not on the lists. The bureau said it planned to issue additions to the lists once a year. Chaplains packed up libraries with thousands of books collected over decades. Unidentified religious experts helped the bureau shape the lists of acceptable materials, which independent scholars said omitted many important religious texts. Bob Moore, director of prison policy oversight at Aleph, an advocacy group for Jews in prison, said the lack of detail and transparency about how the lists were determined troubled him. “This is a positive step: it means they are not throwing the baby out with the bath water,” Mr. Moore said of keeping books on the shelves for now. “But our position is there should not be a list of what should be on the shelves, but what shouldn’t be.” Mr. Silverman said the return of the books would “go a long way” to resolving the lawsuit. But he added, “I remain concerned that the criteria for returning the books will be constitutional and lawful.” http://www.nytimes.com/2007/09/27/wa.../27prison.html  Canadian Heritage Copyright Policy Rocked By Conflict of Interest Concerns Michael Geist The Hill Times is reporting that Patricia Neri, the Director General of Copyright Policy at Canadian Heritage has been removed from her position to become a special advisor to Assistant Deputy Minister Jean-Pierre Blais with "duties still to be determined." While people move all the time in government, this development is noteworthy - not just because it comes mere weeks before a copyright bill may be unveiled, but because there are mounting rumours that the move comes as a direct result of a conflict of interest concerns. Personnel at the Copyright Policy branch were advised by email late last week that the move was for "personal reasons," though Neri apparently stopped coming into work soon after Labour Day. According to multiple sources, the personal reason involves a personal relationship with one of Canada’s leading copyright lobbyists. While Neri’s personal life is no one’s business but her own, this does raise troubling questions about the quick passage of Bill C-59, the anti-camcording legislation, since Neri appeared as a witness before a Senate hearing on the bill with the lobbyist in the room. The Privy Council Office places particular responsibility on public servants that appear before a Parliamentary committee since they do so on behalf of the Minister. Further, when was this known to senior officials at Canadian Heritage? If weeks ago, why does it appear that no one took action, particularly since this came at a time when Neri was briefing Josée Verner, the new Minister of Canadian Heritage, and the Prime Minister’s Office on copyright matters? This is not an easy issue to raise, but if these reports are true, it surely creates at least a perceived conflict of interest contrary to Government Ethics Guidelines on a file that is very controversial and likely to grab the spotlight this fall. The Hill Times notes that Canadian Heritage has been slow to comment on the situation other than to confirm the move. Although it is important to protect the privacy of those affected, public confidence in the copyright process will be undermined if there is not a frank and full disclosure about who knew what and when. http://www.michaelgeist.ca/content/view/2251/125/  Video Professor Sues Anonymous Griping Posters, Demands Their Identities Greg Beck Video Professor, a company that uses infomercials to sell computer-training lessons, sued 100 anonymous "John Doe" posters who expressed their opinions about the company on various online forums, including infomercialratings.com. The company's lawsuit claims that the griping posters violated federal trademark laws by saying negative things about the company, and committed defamation and several violations of state law. After filing suit, the company sent subpoenas to the operator of the websites, demanding the release of the posters' identifying information and the IP addresses from which they made the posts. Here's the complaint and the company's motion to subpoena the anonymous posters' identity. The challenged posts are here and here. The Internet has become the preeminent forum for consumers to share information about products and services online. Courts have recognized that the First Amendment protects the right to post criticism anonymously, noting the risk that critical opinions would be chilled if the identity of anonymous critics could too easily be revealed. Indeed, Video Professor's own website advises consumers to search for customer reviews online: [i]f you decide to use a lesser-known merchant, there are a few things you can do to check out the seller and make sure he’s legit. For one, you can visit the Federal Trade Commission’s Web site for links to consumer protection resources, including lists of complaints lodged against businesses. You also have the option of searching the business section of a major search engine, where you can view company profiles and customer reviews of that company’s products and services. Last but not least, you can request that a seller send you a catalog or other information about his or her company. My colleague Paul Levy sent a letter to Video Professor today objecting to the subpoena (PDF). http://pubcit.typepad.com/clpblog/20...professor.html  Movie Director Sentenced for Lying About Detective David M. Halbfinger and Allison Hope Weiner A federal judge on Monday sentenced John McTiernan, the director of action movies including “Die Hard” and “Predator,” to four months in prison for lying to an F.B.I. agent about hiring the private investigator Anthony Pellicano to wiretap the producer of one of his films. Mr. McTiernan, 56, became the first Hollywood figure to receive prison time because of dealings with Mr. Pellicano, who is awaiting trial on charges of masterminding a long-running wiretapping conspiracy on behalf of stars, studio executives and others in the entertainment industry. According to prosecutors, Mr. McTiernan paid Mr. Pellicano $50,000 to wiretap Charles Roven, a producer of his box-office flop “Rollerball,” in August 2000. But he denied having done so when an F.B.I. agent called to ask him about it in February 2006. Two months later, Mr. McTiernan pleaded guilty to a false-statement charge and offered his cooperation to federal prosecutors digging into Mr. Pellicano’s electronic-eavesdropping operation. But after prosecutors made clear that they thought he was not being truthful and would seek a prison sentence, he hired new lawyers and sought to withdraw his guilty plea and take his chances at trial. A federal district judge, Dale S. Fischer, quickly rejected that attempt on Monday. In a withering rebuke from the bench, Judge Fischer appeared to treat Mr. McTiernan more harshly because of his Hollywood career, calling him a “world-famous director” who arrogantly considered himself “above the law” and had shown no remorse. “If anything, Mr. McTiernan’s privileged background is an aggravating factor,” she said, imposing a $100,000 fine in addition to the prison sentence. Mr. McTiernan has until Jan. 15 to surrender. His new lead lawyer, Milton Grimes, said Mr. McTiernan would appeal the ruling. Mr. McTiernan was also ordered to surrender his passport. It was unclear what his sentence would mean for a movie he was preparing to film in Argentina, “Run,” about an Interpol agent who uncovers a conspiracy while pursuing a murder suspect. The sentence was considered light compared with the many years Mr. Pellicano could face if convicted at his trial in February on racketeering and other charges. But it was severe given that federal prosecutors’ guidelines advise against charging people who merely deny their crimes without embellishing their denials with further lies. In court on Monday, an assistant United States attorney, Daniel A. Saunders, asserted that Mr. McTiernan lied in insisting to prosecutors that Mr. Roven was the only person he had hired Mr. Pellicano to wiretap. Mr. Saunders expressed a belief that Mr. McTiernan had previously hired Mr. Pellicano to wiretap someone else, most likely his former wife, Donna Dubrow, during their 1997 divorce. Mr. McTiernan, wearing brown cowboy boots and a blue blazer, did not speak when given the chance by the judge. His new lawyers argued that on the night he received the call from the F.B.I. agent, he was jet-lagged from a location-scouting trip to Thailand, had contracted typhoid and had stopped taking his antidepressant medication. Asking for no prison time, the lawyers said that his Wyoming ranch, where he raises beefalo, a cross of cattle and bison, would suffer, and that his ranch hands could lose their jobs if he were absent for an extended time. But Judge Fischer said she found their arguments “completely lacking in credibility.” Mr. McTiernan, she added, had taken two years to make the 1987 movie “Predator” and left Wyoming to work on other projects more recently, and yet the ranch had somehow managed to survive. She also scolded Mr. McTiernan for saying in an e-mail message to his previous lawyer that he was “offended” at the idea he could be prosecuted because he had “refused to make movies in which F.B.I. agents are the bad guys,” and for complaining that his legal woes could get in the way of his making a “patriotic movie.” The judge also noted that Mr. McTiernan had arranged to pay Mr. Pellicano by overpaying his own assistant by $50,000, thus involving another person in the wiretapping scheme “so it would not be traceable to him.” Mr. Grimes, the new lawyer, said he was “gravely disappointed” by the sentence and took exception to the judge’s characterization of his client as someone who “lived a privileged life and simply wants to continue that.” “He’s probably one of the most down-to-earth people I’ve met from Hollywood in my 30 years working here,” Mr. Grimes said. http://www.nytimes.com/2007/09/25/bu...hollywood.html  Thieves Raid Argentine Home Of Francis Ford Coppola Thieves broke into the Buenos Aires home of film director Francis Ford Coppola and made off with a laptop containing work on his new movie, an employee said on Thursday. The Oscar-winning director of "The Godfather" movies was out when five thieves raided the house late on Wednesday, injuring a member of the production crew working on Coppola's next film, "Tetro," due to start shooting in February. "Coppola is very sad and the only thing he's asked for is to get back his computer, which is essential for him and for his work," the employee, who was not identified, told a local television station. She said the thieves took computers and other digital equipment including a camera. Coppola, 68, is living in the Argentine capital during the making of "Tetro," which is expected to launch 2009. It is a story about an artistic Italian immigrant family in Buenos Aires and is said to be reminiscent of his life. http://www.reuters.com/article/enter...32279120070927  Court to Consider Technology Patent Case Christopher S. Rugaber The Supreme Court said Tuesday it will consider a technology patent case that could have far-reaching ramifications for computer makers and other industries with global supply chains. The case was brought by a group of Taiwanese computer makers, who have accused a South Korean rival of using its patents in an effort to "shake down the entire computer industry for several billion dollars in duplicative licensing fees." At issue is whether a patent holder can seek royalties from multiple companies as a patented product works its way through the manufacturing process. The Taiwanese firms, led by Quanta Computer Inc., are asking the justices to overturn a 2006 federal appeals court ruling that they say would open the door for patent holders to do just that. Quanta and the other companies manufacture computers under contract for U.S. companies such as Hewlett-Packard Co., Gateway Inc. and Dell Inc. The three U.S. corporations filed court papers in support of Quanta. They said the ruling, by the Court of Appeals for the Federal Circuit, "threatens to impose a huge financial and practical burden on manufacturers of technology products." The companies outsource much of the assembly of their computers to companies like Quanta, the world's largest contract manufacturer of laptop computers. The case began in 2000 when the Taiwanese companies were sued by South Korea-based LG Electronics Inc. for allegedly infringing several patents LG holds on computer chip technology. The case is Quanta Computer Inc. v. LG Electronics Inc., 06-937. Oral arguments haven't yet been scheduled. http://www.washingtonpost.com/wp-dyn...092500609.html  EchoStar Mulls Asset Spinoff, Buys Sling Media Satellite television operator EchoStar Communications Corp (DISH.O: Quote, Profile, Research) said it may spin off its technology assets and announced plans to buy Sling Media, the maker of a device that relays TV programs to laptops and cell phones. EchoStar shares rose as much as 9 percent in early trading, raising the possibility that the move could position either the technology unit or its pay-TV business Dish Network for an eventual sale. "It is likely that the potential spin-off/restructuring will trigger renewed speculation about possible M&A transactions," Sanford C. Bernstein analyst Craig Moffett said in a note to clients, though he questioned whether a spinoff was necessary to selling either of EchoStar's businesses. EchoStar said on Tuesday it asked the U.S. Internal Revenue Service whether it can split its technology and infrastructure properties into a new publicly-traded entity on a tax free basis to the company and shareholders. Under the plan, EchoStar's consumer pay-TV business would continue to operate on its own as the Dish Network. Shareholders would have separate pro rata ownership interests in each company. "Each company would be able to separately pursue the strategies that best suit its respective long-term interests," said EchoStar Chairman and Chief Executive Charlie Ergen in a statement. He added that a spin-off would allow the two companies to build more precise performance-based incentives for employees, as well as financing and expansion plans. The Dish Network operations accounted for 98 percent of the company's overall revenue in the second quarter. EchoStar, which competes with rival satellite provider DirecTV and U.S. cable operators, said late on Monday it would buy Sling Media in a deal that values the privately-held company at $380 million. Sling Media is known for its Slingbox device that connects cable and satellite TV set-top boxes to the Internet, allowing a viewer to call up programs out of the home on mobile devices that have Web access. EchoStar had previously made an investment in the company, but Sling officials would not disclose financial details. Bernstein's Moffett said the Sling Media acquisition could help EchoStar differentiate its service from rival DirecTV and cable operators by offering subscribers television on the go. But that strategy carries its own risks since Sling relies on high-speed Internet connections for its service to work properly, Moffett noted. "Increasingly, those broadband connections are likely to belong to cable operators, or, in parts of the country, to (phone companies) offering their own video services," he wrote in a research note to clients. Sling Media would be incorporated into EchoStar's technology and infrastructure segment, but remain a wholly owned subsidiary using its brand name. EchoStar's asset spinoff would include its set-top box design and manufacturing business, its international operations and assets used to provide fixed satellite services to third parties. Ergen would continue to serve as Chairman and CEO of both Dish Network and the spun-off company. It will sell hardware and services to the Dish Network, as well as market to other cable and satellite companies and directly to consumers, a Sling spokesman said. The purchase is expected to close in the fourth quarter. Shares in EchoStar were up 7 percent, or $2.80, to $44.12 in early Nasdaq trading, after touching an intraday high of $45, its highest level since July. http://www.reuters.com/article/merge...35404820070925  Buy a Laptop for a Child, Get Another Laptop Free Steve Lohr One Laptop Per Child, an ambitious project to bring computing to the developing world’s children, has considerable momentum. Years of work by engineers and scientists have paid off in a pioneering low-cost machine that is light, rugged and surprisingly versatile. The early reviews have been glowing, and mass production is set to start next month. Orders, however, are slow. “I have to some degree underestimated the difference between shaking the hand of a head of state and having a check written,” said Nicholas Negroponte, chairman of the nonprofit project. “And yes, it has been a disappointment.” But Mr. Negroponte, the founding director of the M.I.T. Media Laboratory, views the problem as a temporary one in the long-term pursuit of using technology as a new channel of learning and self-expression for children worldwide. And he is reaching out to the public to try to give the laptop campaign a boost. The marketing program, to be announced today, is called “Give 1 Get 1,” in which Americans and Canadians can buy two laptops for $399. One of the machines will be given to a child in a developing nation, and the other one will be shipped to the purchaser by Christmas. The donated computer is a tax-deductible charitable contribution. The program will run for two weeks, with orders accepted from Nov. 12 to Nov. 26. Just what Americans will do with the slender green-and-white laptops is uncertain. Some people may donate them to local schools or youth organizations, said Walter Bender, president of the laptop project, while others will keep them for their own family or their own use. The machines have high-resolution screens, cameras and peer-to-peer technology so the laptops can communicate wirelessly with one another. The machine runs on free, open source software. “Everything in the machine is open to the hacker, so people can poke at it, change it and make it their own,” said Mr. Bender, a computer researcher. “Part of what we’re doing here is broadening the community of users, broadening the base of ideas and contributions, and that will be tremendously valuable.” The machine, called the XO Laptop, was not engineered with affluent children in mind. It was intended to be inexpensive, with costs eventually approaching $100 a machine, and sturdy enough to withstand harsh conditions in rural villages. It is also extremely energy efficient, with power consumption that is 10 percent or less of a conventional laptop computer. Staff members of the laptop project were concerned that American children might try the pared-down machines and find them lacking compared to their Apple, Hewlett-Packard or Dell laptops. Then, in this era of immediate global communications, they might post their criticisms on Web sites and blogs read around the world, damaging the reputation of the XO Laptop, the project staff worried. So the laptop project sponsored focus-group research with American children, ages 7 to 11, at the end of August. The results were reassuringly positive. The focus-group subjects liked the fact that the machine was intended specifically for children, and appreciated features like the machine-to-machine wireless communication. “Completely beastly” was the verdict of one boy. Another environmentally conscious youngster noted that the laptop “prevents global warming.” Still, the “Give 1 Get 1” initiative is mainly about the giving. “The real reason is to get this thing started,” Mr. Negroponte said. He said that if, for example, donations reached $40 million, that would mean 100,000 laptops could be distributed free in the developing world. The idea, he said, would be to give perhaps 5,000 machines to 20 countries to try out and get started. “It could trigger a lot of things,” Mr. Negroponte said. Late last year, Mr. Negroponte said he had hoped for orders for three million laptops, but those pledges have fallen short. Orders of a million each from populous Nigeria and Brazil did not materialize. Still, the project has had successes. Peru, for example, will buy and distribute 250,000 of the laptops over the next year — many of them allocated for remote rural areas. Mexico and Uruguay, Mr. Negroponte noted, have made firm commitments. In a sponsorship program, the government of Italy has agreed to purchase 50,000 laptops for distribution in Ethiopia. Each country will have different ideas about how to use the machines. Alan Kay, a computer researcher and adviser to the laptop project, said he expects one popular use will be to load textbooks at 25 cents or so each on the laptops, which has a high-resolution screen for easy reading. “It’s probably going to be mundane in the early stages,” said Mr. Kay, who heads a nonprofit education group, whose learning software will be on the XO Laptop. “I’m an optimist that this will eventually work out,” Mr. Kay said. http://www.nytimes.com/2007/09/24/bu.../24laptop.html  Why OLPC Mesh Wireless Networking Won’t Work George Ou One of the touted features of the $200 OLPC laptop is the peer-to-peer mesh topology networking feature that can theoretically bring an Internet infrastructure where there is no network infrastructure. The problem is that peer-to-peer wireless LAN mesh topology sounds better than it actually works and there’s a good reason it isn’t used commercially. [UPDATE 3:00PM - I should clarify that OLPC mesh technology applies to the XO laptop shown on the left or to the Intel Classmate. Intel is also on the board of OLPC so it’s not OLPC versus Intel. Intel is also providing some help on technology based on the centralized Access Point and Bridge model. OLPCs can also work with centralized wireless LAN infrastructures and that is the point of this blog; that the two technologies work best together and that they’re not mutually exclusive. A $60 Linksys router running modified Linux and a $20 antenna can provide fast and reliable infrastructure for the entire school.] The word “mesh” is traditionally highly regarded in the networking world because every IT student is taught in Computer Networking 101 that “mesh topology” is the most advanced form of networking. Mesh topology traditionally conjures up the image of multiple redundant links with high-performance distributed loads but that only applies to the wired networking world when multiple physical links are used to build the network. High-performance and load-distribution does not apply to wireless mesh topology especially when we’re talking about typical implementations that use a single radio and a single radio frequency. In fact, every wireless relay adds another hop and the relay action doubles the radio contention because the same data has to be retransmitted on the same radio frequency. Even if we ignore the delay and contention problems of mesh topology wireless LANs, there’s an even more fundamental problem facing the peer-to-peer mesh technology being implemented in projects like the OLPC. The radios and antennas are so small that it would take hundreds of OLPC devices with perfect spacing to replace a single high-powered Access Point with high-gain antennas. Consider the illustration below where I compare OLPC laptops that are capable of transmitting up to 50 meters with their small 30mW radios and small antennas versus a centralized AP that’s capable of 400 meters range. Note that I’m being very conservative with the 400 meter range with a 300mW Access Point because those things can easily go twice as far. But even with a mere 8:1 advantage in range, it would take more than a hundred OLPC laptops to cover the same area. If we’re talking about a more realistic 16:1 advantage in range, then it would take more than 400 OLPC laptops to cover the same area and they would all have to be spaced out perfectly. We also have the possibility of using 500mW radios and 16 dBi antennas for even longer range in rural areas. When we consider the fact that a single failure in one of the mesh nodes due to battery drainage, moving out of range, software hang will cause the entire mesh scheme to break, there simply is no way to get around the centralized architecture. Last week at Intel’s IDF convention in San Francisco, Intel’s “World Ahead Program” was showing off some cheap commodity technology and blueprints that would empower schools with wireless networking and Internet access. These blueprints and part lists allow the schools to build their own wireless infrastructure with cheap off-the-shelf components. The all-in-one Wireless Access Point and Wireless Bridge box (dual radio) allows remote locations that lack wired Internet uplinks to bridge wirelessly to the central uplink. I came up a slightly modified version shown in the illustration below to show the flexibility of this architecture. With a few of these “towers” with sufficient transmit power and high-gain omni-directional antennas for client access and directional antennas for the backhaul; we can reliably cover a very large campus. http://blogs.zdnet.com/Ou/?p=777  Fight Cyberbullies, Schools Told Schools are being given guidance urging them to take firm action against pupils who use mobile phones and the internet to bully other children and teachers. More than a third of 12 to 15-year-olds have faced some kind of cyberbullying, according to a government study. Ministers are also launching an awareness campaign on the social networking sites used by many pupils. Schools have been told they can confiscate mobile phones and how to get hurtful material pulled from websites. 'Happy slapping' Schools Secretary Ed Balls said cyber bullying was "insidious" and had grown with technology and changes in society. Schools needed to get to grips with newer forms of bullying, he said. Examples cited include threats, intimidation, harassment or "cyber-stalking", unauthorised publication of private information or images, impersonation and so-called "happy slapping". Mr Balls also called for action against anti-gay bullying -calling for schools to promote a "culture of respect" and saying that "homophobic insults should be viewed as seriously as racism". Ed Balls said: "The vast majority of schools are safe environments to learn in. However, we know that behaviour, particularly bullying, is a key concern for parents and bullying of any kind is unacceptable. "Cyberbullying is a particularly insidious type of bullying as it can follow young people wherever they go and the anonymity that it seemingly affords to the perpetrator can make it even more stressful for the victim. "One message that I want to get across to young people is that bystanders can inadvertently become perpetrators - simply by passing on videos or images, they are playing a part in bullying. TIPS TO AVOID CYBER BULLYING Don't respond to malicious texts or e-mails Save evidence Report cyber bullying Keep passwords safe Don't give out personal details online "We now have an advanced approach to cyber bullying, thanks in no small part to the co-operation with the industry, teaching unions and charities." The guide being sent out to schools in England says cyberbullying can be an extension of face-to-face bullying, "with technology providing the bully with another route to harass their target". But it says it differs in that it invades home and personal space and the perpetrator can use the cloak of anonymity. Among the new guidance are tips for drawing up anti-bullying policies to cover cyber bullying, how to have offensive or malicious material removed from websites, and advice on confiscating equipment used in bullying, such as mobile phones. Offensive weapons call The new measures were developed in consultation with anti-bullying experts, mobile phone companies and websites including Bebo, MySpace and YouTube. Teaching unions say children are not the only victims of cyberbullying and that school staff are increasingly falling victim to it. Chris Keates, general secretary of the NASUWT teachers' union, said teachers would be pleased that ministers had recognised the problem. "Mobile phones capture videos and pictures of teachers at work," she said. "The often distorted images are transferred to the phones of other pupils within the class, across the school or uploaded on to the internet. E-mails are used to abuse, harass and insult. "Misuse of internet sites can destroy teachers' confidence and professional reputation and provide yet another vehicle for false allegations against staff." The union is calling for pupils' mobile phones to be classed as potentially offensive weapons and for them to be banned during school sessions. Mick Brookes, general secretary of the National Association of Head Teachers (NAHT), said: "Sadly, bullying is a negative feature of any society and will only be countered by strong action against bullies and a bullying culture. "We would encourage all partners in the world of education to play a part in stamping out wanton actions that negatively affect the lives of others. "Many schools harness the student voice, through student councils and other means, to counter bullying in the most effective way, because students are closer to the lives of their peers." The ATL teachers' union also backed the need for action against homophobic bullying - saying that it remained a "pervasive" problem in schools. A survey for the union found that 70% of teachers had heard children in their schools using homophobic language. http://news.bbc.co.uk/go/pr/fr/-/2/h...on/7005389.stm  Artists Erect Giant Pink Bunny on Mountain  Wahge wabbit An enormous pink bunny has been erected on an Italian mountainside where it will stay for the next 20 years. The 200-foot-long toy rabbit lies on the side of the 5,000 foot high Colletto Fava mountain in northern Italy's Piedmont region. Viennese art group Gelatin designed the giant soft toy and say it was "knitted by dozens of grannies out of pink wool". Group member Wolfgang Gantner said: "It's supposed to make you feel small, like Gulliver. You walk around it and you can't help but smile." And Gelatin members say the bunny is not just for walking around - they are expecting hikers to climb its 20 foot sides and relax on its belly. The giant rabbit is expected to remain on the mountain side until 2025. http://www.ananova.com/news/story/sm_1541732.html  My Business Failure – AnywhereCD Michael Robertson My newest business, AnywhereCD, is unfortunately on its last flicker of light before it officially flames out in a few days (my contract expires at midnight on September 30th so check out the close-out sale here where you can get a CD and instant delivery of 192k MP3s for only $7). It's a real shame because I think it was a solid business idea and in an effort to get some value from it, I want to tell you about it so you can learn from my mistakes. I believe that if you give people real value (music or anything else) they are happy to pay. The AnywhereCD concept was quite simple: create an online store where customers could get the immediacy of digital files along with the permanence and familiarity of a physical CD. For one purchase price they would get the best of both worlds, with no need to take any extra steps just to get a MP3 file to play on their player. Sounds great in theory, but I wasn't able to pull it off. With CD sales slumping sharply, I thought it would be a good time to approach the record labels with a new idea to spur sales. Obviously $1 song sales on iTunes are ongoing, but losing a $15 CD sale means a $14 net loss for the music business. I thought the labels would be receptive to the proposition of reinventing the CD by making it Internet friendly. In our web-savvy world, people expect everything immediately -- we want to bank, shop and communicate in real time. While we can buy a CD on the web immediately, we can't listen to it immediately -- instead we have to wait for the postman to show up with the plastic. It's no wonder that fewer and fewer people are buying CDs. But what if anyone could buy a CD and immediately get the corresponding MP3 tracks to play anywhere? I assumed the labels wouldn't be too excited about users getting MP3 tracks, but CDs are perfect digital copies anyway so customers wouldn't be getting anything they couldn't already have. To entice the labels my strategy was to pay the wholesale price for CDs plus give them $2 for the digital tracks. I met with all of the major labels (Universal, EMI, Sony, and Warner Music) and they seemed open minded to new ideas. One had a cautious 'wait and see' type of attitude. Another wanted millions of dollars up front. One insanely asked me if I would embed the purchaser's credit card number in the song files they bought. (I pointed out as politely as I could that no one would shop at Barnes and Noble if they printed your credit card number on every page of every book you bought. And, um, oh yeah, I'd be breaking a variety of federal and state laws!) AnywhereCD eventually launched with the inventory from only one major label -- Warner Music. Of course, I wanted to launch with all the labels since most people don't have a clue what label any particular artist is on -- but we decided to open AnywhereCD with just Warner Music titles in the hopes that other labels would see the light. After signing the contract we invested months of labor and resources into building the technology to amass the digital inventory, creating the web site, constructing the e-commerce system and testing the process. While we were working on this, Apple announced that they had entered into a deal to sell EMI tracks in MP3 format. That definitely stole some of AnywhereCD's thunder even though Apple's was just a pre-announce and wouldn't have music available for weeks. Days later we launched AnywhereCD. Sadly, few press outlets covered our grand opening. Looking back I suspect there were probably many contributing factors. Maybe the price for the CD+MP3 bundle was too high? Thanks to iTunes the world thinks albums are worth $9.99 and many of the CDs on AnywhereCD were more expensive. Maybe nobody cares about CDs anymore? Clearly they are becoming less relevant as people adapt to a digital-only world. Maybe having just a fraction of the major label music made for a disappointing consumer experience? Warner Music represents roughly 20% of the major label titles -- so we were missing 80%. Maybe I didn't give the leading off-line publications enough notice to compete with the bloggers? Maybe the press is Apple-fixated? Maybe I didn't do a good job explaining the system to Warner Music who could have helped to educate a confused press? The answer is probably a combination of all these factors. AnywhereCD will close-up shop shortly and surely be forgotten in digital music history. In spite of its ultimate demise I do think AnywhereCD helped push the world towards MP3. I was able to make a case -- that record labels will make more money if they utilize MP3 as part of their offerings. This is something I did once before when I started MP3.com in 1998, but they nearly threw me out of their offices. This time they listened intently to my proposal and responded promptly. I think record labels are becoming more comfortable with the fact that selling MP3 files can have a positive impact on their business. Since my campaigning, EMI is selling their entire catalog in MP3. Universal just recently kicked off a significant test with several major retailers vending MP3 tracks. This week, Warner Music is selling the new James Blunt CD with digital tracks that you can load into an iPod for $9.99. Although AnywhereCD was an expensive experience for me and not my proudest business accomplishment, I hope you get some value from my experience. And even if you don't give a rip about the business experience, but you like music, you can benefit right now! In its final week of existence, AnywhereCD will be selling most of its CD inventory for a mere $7. For that 7 bucks you will get a new CD plus high quality 192k MP3 tracks that you can immediately download, stream and sync with your iPod. And hey, I'd rather take a loss, see music fans get great music at great prices and empower their music freedom. http://www.michaelrobertson.com/arch...?minute_id=245  Starbucks to Give Away Music as New Service Starts Starbucks on Monday said it will give away millions of songs via downloads starting next month, as it launches a wireless music service with Apple. From October 2 to November 7 at more than 10,000 U.S. Starbucks locations, customers can receive "Song of the Day" cards redeemable on Apple's iTunes store for a complimentary song hand-selected by Starbucks Entertainment, the company said. Starbucks said it will give away 1.5 million downloads per day for a total of more than 50 million free songs. Customers will have until the end of the year to redeem the song on iTunes. Earlier this month, Apple and Starbucks said they had reached a deal to allow people to buy songs wirelessly from Apple's iTunes music store in Starbucks coffee shops without paying Wi-Fi connection fees. The service is to debut at more than 600 Starbucks stores in New York and Seattle on October 2, and will be expanded to other major U.S. cities later this year and next. http://www.news.com/Starbucks-to-giv...3-6209620.html  Virgin Digital Can't Reach Escape Velocity, to be Grounded Permanently Jacqui Cheng Virgin Digital, the online presence of the UK-based Virgin Group that owns Virgin Megastores, has announced that it has begun closing its doors in stages, beginning last week. According to a message on the site, the online music store has already shut its doors to new customers as of last Friday, and as of this coming Friday, it will cease selling individual tracks to current customers. Only subscribing members will have access to the site until their next payment is due or October 19, whichever comes first. After that, the site will cease to operate for both US and UK customers. "I don't really know what else to say, it's not our decision to go," writes MikeCK on the Virgin Digital Big Mouth Blog. "It's the powers that be who have decided they don't want us anymore." Virgin launched Virgin Digital in 2004 with both subscription and per-track pricing available to its users. As with most subscription services, Virgin's allowed users to listen to an unlimited number of tracks per month that they could access as long as they continued to pay their $7.99 monthly subscription fee. Individual tracks could also be purchased for 99¢ apiece, which allowed users to burn them to CD and access the songs for as long as they wanted. All tracks used Windows Media DRM, and therefore were only playable under Windows and on WMA-compatible devices. The site now advises its customers who have purchased tracks to back them up, as they will not be able to download them again once Virgin Digital has closed. It's unclear whether the purchasers of individual tracks will be able to access their songs without burning them to CD and reimporting them as MP3s, but it's better to be safe than sorry if you're one of those customers. And naturally, subscribing members will lose access altogether once their subscriptions lapse. Song credits on the site must be used up before the service shuts down, too, or else they'll be lost. Fortunately, US users of the service will be able to transfer any remaining song credits to Napster's music service, although UK users will be out of luck if they don't use their song credits now. Outside of the iTunes Store, online music stores like Virgin Digital haven't exactly been making home runs in terms of popularity or sales. The subscription model for music hasn't been received well by the general population, and heavy DRM restrictions have left many potential customers giving these services the cold shoulder. The shuttering of Virgin's digital doors is only the most recent example of this—MTV recently ditched Microsoft in its partnership over URGE, likely signaling the service's imminent demise. Also, Virgin Digital users might want to use up their credits quickly even if they can transfer them to Napster—everyone's favorite P2P-turned-legit service has had monetary problems of its own for several years now. And let's not forget that Sony Connect closed its doors less than a month ago, too. When it comes to digital music sales, DRM-free is the new hotness and almost everything else is old and busted. Several online music stores have begun to sell DRM-free tracks, with labels like EMI, Nettwerk Music Group, and even music giant Universal testing the waters. EMI even claims that its early numbers indicate that DRM-free tracks are selling pretty darn well. We can only hope that this trend continues and that the labels take notice, because until they decide to loosen DRM restrictions or (better yet) ditch DRM altogether, we're likely to continue hearing stories like this. http://arstechnica.com/news.ars/post...rmanently.html  Amazon Launches DRM-Free "Amazon MP3" Music Downloads Joshua Topolsky If you're into DRM-free music, you have a reason to get pretty excited today. As speculated, Amazon has launched the public beta of its new digital music portal called Amazon MP3, which will feature two million songs from 180,000 artists and 20,000 labels, all without the painful and annoying restrictions of DRM. The press release claims that the site, which will include EMI and Universal tracks (take that, Jobs), will make separate songs available for $.89 or $.99, and boasts that all of the "top 100" tracks will be priced at the former, lower amount. Albums will range in cost from $5.99 to $9.99, with the best selling albums coming in at $8.99. Of course, since there's no DRM, users are free to throw the 256Kbps MP3s on any player they like, as well as burn CDs, copy to MiniDisc, and dump to 8-track. http://www.engadget.com/2007/09/25/a...sic-downloads/  DRM Advocates Getting Nervous About Consumer Backlash Ken Fisher You all know the slogan: "Guns don't kill people, people kill people." At the Digital Rights Strategies conference in New York City, a similar message could be heard: "DRM doesn't anger consumers, content owners abusing DRM anger consumers." Few, of course, would argue that the mere existence of DRM is a bad thing. Locked away in a vault somewhere or trapped in one of those nifty mirrors featured in Superman, DRM can do little harm. Such assertions are merely academic, of course. Tools are designed to be used, and DRM is being used to do what it was designed to do: control how consumers interact with content. But the growing backlash against DRM is causing dissension in the pro-DRM ranks. Paul Sweeting's excellent report on the DRS conference records the frustrations of the DRM community at the tactics of the content industry. They apparently feel that an overzealous content industry is abusing DRM; this is a bit like Smith & Wesson complaining that bullets can kill. When DRM proponents start pointing fingers and attempting to separate the theory (really, the ideology) from the practice, we have to stop and ask: what's going on here? It appears that players in the DRM ecosystem know the tide is turning against them because DRM is punishing the wrong people, namely the folks who are buying DRM-laden content. This is bad for their business, because a DRM backlash could harm DRM peddlers. Then, of course, there's the hypocrisy. At a conference convened by the overlords of DRM, Sony vice president Scott Smyers admits that he circumvents the copy protection on DVDs (CSS) in order to make backups for personal use. Apparently Mr. Smyers doesn't agree with Hollywood or the Register of Copyrights, both of which argue that "backups" can readily be had in the form of new copies you can buy at the store. The corporate hypocrisy is obvious: what the corporate parent demands (DRM that prevents DVD copying), even its own employee disregards. We can't blame him. Among DRM peddlers, there's also a bit of jealously because some DRM systems are "successful." Take the comments made by Talal Shamoon, CEO of InterTrust (a company working on interoperable DRM schemes, among other things): "Apple is using encryption to try to do what Ma Bell used to do with the phone network: wall people in," he said. "It frustrates consumers and ultimately feeds piracy." Such views are nonsense, of course, when you're trying to pin them on just one proponent of DRM. Re-read that quote, and replace "Apple" with "DRM." It's every bit as true. While proponents of universal or interoperable DRM schemes might say that they don't want to wall people in around any given manufacturer's products, the "Cask of Amontillado" aspects remain: interested consumers can only utilize DRM'd products on devices that support that DRM system (interoperable or not). Take the widest, most universal DRM implementation to date: CSS for DVDs. A properly equipped computer still cannot legally play DVDs in countries like the US if it runs an operating system or carries components not blessed by the "powers that be" (in this case, the DVD-CCA and friends). Then look at the next-gen version of CSS, known as AACS. The implementation requirements for AACS are even more stringent, even more exclusive. If you don't have a team of engineers available to make your new product work with AACS, then you're out of luck. The consumer electronics world is well aware of the devastating effects of DRM on innovation. Take the comments of Jim Helman, CTO of Hollywood-backed MovieLabs. Helman says that if he were in the hardware business, he'd be focusing his attention on building a DVD-ripping movie jukebox. Yet this is something that is currently illegal and scares the DVD-CCA to death. The same activity that gave birth to the MP3 player and revolutionized the music industry is anathema to the content owners in Hollywood. MPAA VP Fritz Attaway even suggested that without DRM in place, Hollywood wouldn't have any other option than to simply not release its movies. DRM-free is apparently unthinkable at the MPAA, despite an acknowledgment from Attaway that current implementations cause problems for fair use! The message is, essentially: yes, we know this CSS stuff stomps on fair use, but better that than we release products without encryption. The DRM backlash is indeed coming, and kudos to these industry players for realizing it. Heck, the backlash is already here and has been for years. Now that major players like Apple and even labels like EMI and Universal are starting to realize it, it's only a matter of time before it turns into a full-scale revolt. Whether or not there will be a revival of interoperable DRM cure-all theories remains to be seen, but backers have at least figured one thing out: when DRM does what it is designed to do—namely inconvenience and control end user behavior—users bite back. http://arstechnica.com/news.ars/post...-backlash.html  Vivendi Calls Apple iTunes Contract Terms "Indecent" Astrid Wendlandt Vivendi condemned as "indecent" the contract terms between its Universal Music Group (UMG) unit and Apple Inc, the computer maker whose iTunes online store dominates the digital music market. Vivendi is one of many large media companies that are trying to challenge Apple's grip on the digital entertainment market and obtain more control over pricing. It said it was in talks with rival distributors. "The split between Apple and (music) producers is indecent ... Our contracts give too good a share to Apple," Vivendi Chief Executive Jean-Bernard Levy told reporters at a gathering on Monday organized by the association of media journalists in France. At present, UMG, the world's largest record company, gets 0.70 euro ($0.99) out of the 0.99 euro retail price charged by iTunes, Vivendi said. Among other things, Levy called for the remuneration of a new release to be higher than for a 30-year-old classic. "We should have a differentiated price system," he said. UMG renews its music distribution contracts with Apple every month after having failed to agree a longer-term arrangement earlier this year. The music publisher can end its contract with Apple at one month's notice, but Levy declined to say whether UMG was ready to bypass Apple altogether. "We are in a phase during which many different actors are talking to each other ... We are trying to put in place several projects to ensure that music is better remunerated ... We are not just talking to Apple," he said. In August, NBC Universal, a unit of General Electric, decided against renewing its contract to sell television shows on iTunes and this month reached a deal to sell TV downloads to online retailer Amazon. Artist's Image Commenting on the outlook for revenues at UMG, Levy said: "At constant exchange rates, we should probably be stable again in 2007." Fleshing out UMG's strategy, Levy said it planned to focus on better exploiting the "monetization of an artist's image" which included branded clothes and TV shows. "This is what we hope will revive our business," Levy said. "People indulge in piracy but spend a lot of money on many other things that are linked to an artist." Levy forecast that "in the not so distant future", traditional music products such as DVDs and CDs would make up less than 50 percent of music publishing revenues. At the half-year stage, digital music sales made up 15 percent of UMG's total music revenue. Separately, Levy said Vivendi expects the profitability of its pay-TV group Canal Plus to improve in 2007, excluding restructuring costs. "We hope to generate, excluding restructuring costs, an EBIT margin of above 7 percent this year" at Canal Plus, Levy said. In 2006, Canal Plus's earnings before interest and taxation (EBIT) reached between 4 and 5 percent of revenue, on a comparable basis excluding restructuring costs. Levy said Canal Plus aimed to reach an operating margin of 20 percent by 2010, matching the level of British rivals and narrowing the gap with U.S. peers with margins near 30 percent. "To get there, we need savings and particularly in (TV) content," Levy said, adding that Canal Plus planned to cut 200 to 250 million euros in TV content costs, which now hovered around 2 billion euros annually. But Levy acknowledged that competition for good TV content such as film or sports rights remained high, particularly against new entrants such as France Telecom which he described as a "semi-public company" with deep pockets. Vivendi shares closed down 1.2 percent at 29.74 euros. http://www.reuters.com/article/music...88079220070924  Apple Sends Takedown Notice to iPod Hacker's ISP Mike Schramm Yesterday, Erica posted in her state of the iPod touch jailbreak that a hacker named "Martyn" had obtained a broken iPod touch, and was planning to dive in and download every bit of code on it in the increasingly complicated effort to put 3rd party applications on the iPod touch. He didn't plan to release the code to the public, but he did plan to upload the code to a secured area of his site in order to let the other touch hackers have a crack at it. But even before his upload finished, we're told, his ISP showed up, with a takedown notice in hand. Apple had somehow found his site, had contacted his ISP, and let them know that it would be against copyright law for him to upload that code to the Internet. Martyn isn't interested in breaking the law (and it would be illegal to share that code), so he pulled the page off. But what's amazing here is how fast Apple moved on this-- either they've got someone listening in on the development wiki, or they're taking cues from us on how things are going over there (hi, Apple!). Despite what we've heard before, clearly they are very, very interested in making sure the iPod touch doesn't get hacked. Martyn tells me, as has Erica, that Apple has clearly gone out of their way to keep hackers out of their latest iPod. We're also told that progress continues despite all that, but Apple is apparently bending over backwards to do everything they can to keep the iPod touch closed. http://www.tuaw.com/2007/09/25/apple...d-hackers-isp/ |
|
|

|
|
|
#2 |
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Apple: Firmware Update Likely to Make Unlocked iPhones "Permanently Inoperable"
Jacqui Cheng Apple said today that a firmware update to the iPhone due to be released later this week "will likely result" in SIM-unlocked iPhones turning into very expensive bricks. "Apple has discovered that many of the unauthorized iPhone unlocking programs available on the Internet cause irreparable damage to the iPhone's software, which will likely result in the modified iPhone becoming permanently inoperable when a future Apple-supplied iPhone software update is installed," said Apple in a statement issued this afternoon. Apple CEO Steve Jobs last week reiterated the company's stance on unlocked iPhones: Apple will work against them. "It's a constant cat and mouse game," Jobs said. At that time, we also said that we had reason to believe that the next update to the iPhone would brick iPhones that had been unlocked to use SIM cards from other GSM carriers, which Apple's press release has confirmed. Sources familiar with the matter have told Ars that the company did not decide to cause such irreparable damage to the iPhone intentionally, however, and Apple's statement appears to confirm this as well. Apple says that it "strongly discourages" users from installing these unlocking programs, and that doing so violates users' iPhone software license agreements as well as voids their warranties. This is corroborated by individual user accounts of being turned away at Apple Stores after having various hacks installed on their iPhones. "The permanent inability to use an iPhone due to installing unlocking software is not covered under the iPhone's warranty," warns Apple. So what are users of SIM-unlocked iPhones to do? Not run the latest software update, that's for sure. Users can instead pray to the hacking deities—the famed iPhone Dev Team that released the free software unlock, and iPhoneSIMfree, which released a commercial software unlock—to write applications that will undo the unlocks, as it were, if those users want to run the latest iPhone software. And then the teams get to start anew with their hacking efforts on the new firmware. What was that about a cat-and-mouse game again? http://arstechnica.com/news.ars/post...noperable.html  Did Apple Violate Magnuson-Moss over iPhone Unlocks? Christopher Price Apple has today stated that unlocking the iPhone is an official warranty violation. Further, they have stated that future iPhone firmware updates may damage unlocked iPhones. However, Apple may have violated an important federal warranty law in doing so. Click read more for full analysis. The newcomer to the wireless industry has consistently taken a closed policy to iPhone. AT&T, which generally provides SIM unlock codes to customers that have completed a certain portion of the contract, is saying that they are unable to with iPhone. They cite Apple as being unwilling to provide them with such codes. Apple also refuses to release a Software Development Kit (SDK) to enable developers to write software for the embedded version of Mac OS X inside of iPhone. However, today's decision may put Apple in legal trouble. The Magnuson-Moss Warranty Act states that Apple cannot void a warranty for a product with third-party enhancements or modifications to their product. The only exception to this rule is if Apple can determine that the modification or enhancement is responsible damaging the product in question. While Apple has the opportunity to make further exemptions, we will explain how the exemptions Apple has made do not fully apply to this case. The legal question is three-fold here: Is the SIM Unlock process that has become mainstream (anySIM/iUnlock, available from our iPhone encyclopedia entry) doing damage to iPhone? And, also, is Apple designing future software updates to do damage to iPhone when said SIM Unlock code is present? Finally, is Apple's limited warranty setup to prohibit such unlocks, as defined by federal law and the specific terms of the limited warranty itself? Unfortunately, the answers lie in complex legal and technical terms. First, the status of SIM unlocks in and of themselves. Generally, phone manufacturers consider a phone successfully unlocked to maintain its warranty. A phone that has been unsuccessfully unlocked may lose its warranty if the phone cannot be repaired by re-flashing its firmware. The SIM unlock process for iPhone relies on making a modification to Apple's baseband firmware. The baseband firmware is essentially the software that exists on the radio itself. It is independent of the embedded Mac OS X installation. While this is an unorthodox way of unlocking a phone, it appears to be the only viable software unlock solution; there is no evidence that Apple has implemented a way of entering a SIM Unlock code, similar to entering a PUK code. Apple left implementers with the only option of patching the firmware. Does this do damage to iPhone? There is no evidence that it does. The part of the baseband that is modified only controls SIM unlocks. For Apple to void the warranty, they would have to provide clear technical evidence and documentation... something Apple has not yet provided. Until they do, this appears to be an initial violation of Magnuson-Moss. It's no different from putting a third-party part in a car that does not damage or inhibit any other part of the car. Furthermore, it is valid and has been ruled as not a DMCA violation by the U.S. Copyright Office, so there is no tainted hand argument either. Apple does, however, have one card in their hand... they can require users that have SIM unlocked their iPhone, to re-lock them. The baseband firmware can be re-flashed and re-locked to AT&T's network. However, Apple is currently holding that any iPhone that has ever been attempted to unlocked has a voided warranty. In short, if Apple changes that position to simply requiring that the iPhone be re-locked to AT&T, they are back in compliance with the law. The second question of updates from Apple damaging unlocked iPhones, is much more complicated. If an update can, unintentionally, do damage, is again a question Apple must answer before rendering iPhone's warranty void. And, Apple is legally required to prove it... at least on the civil grounds of more-likely-than-not. If Apple will release an update that intentionally detects the baseband modification, and then does damage iPhones that have it is more simple to answer; they could, but it's illegal for them to do so. Magnuson-Moss prevents Apple from intentionally voiding the warranty based on the presence of a modification. Extrapolating from that, it also prevents them from damaging other components of iPhone (such as Boot ROM or baseband components) simply because the modification has been detected (which an updater can detect by checksumming the baseband). It is questionable if Apple can simply word in their warranty agreement that SIM unlocks are a voiding condition. This would be necessary for Apple to legally void warranties based on a SIM unlock, and under Magnuson-Moss, any term of iPhone's warranty that does so must be explicit and easy for the consumer to understand. Magnuson-Moss is vague on the implications of such a situation. It would be similar to stating that using a third-party ink jet cartridge voids the warranty of a printer. While Apple makes the statement of "a product or part that has been modified to alter functionality or capability without the written permission of Apple" voids the warranty, SIM unlock processes that are free and openly sourced, are not salient products, nor are they traditionally defined as a part. Furthermore, the SIM unlock can be reversed, and thus is not a permanent modification... in other words, Apple can remove it easily. Furthermore, any iPhones unlocked before said wording would still be entitled to warranty care... and Apple has no way of detecting exactly when an iPhone was unlocked. The conclusion here is simple: Apple has, at least in a minor and reversible way, violated the Magnuson-Moss Warranty Act. Apple should take action to correct their policy, and require that iPhone customers seeking warranty service, return their iPhone's to locked condition. Apple could also release a software tool that aides in this process, though legally they are not required to... it would make the job of the Genius Bar easier to have such a tool in-house. http://www.phonenews.com/content/view/2386/9/  Steve Jobs Girds for the Long iPhone War Saul Hansell There is something futile about the way Apple appears to be fighting some of its most ardent fans, those who want to use the full capabilities of the iPhone. Thursday afternoon, Apple released the scheduled update to the iPhone software. And the gadget blogs confirm that it does, as Apple threatened, wreak havoc on modified iPhones. Some phones have indeed been “bricked.” In others, unofficial applications have been disabled. And there are worries that hacking the updated phone will be harder. The result: Serious hackers will keep finding new ways to break in. Less technically inclined may well find themselves chastened into technological submission, assuming they can get their pricey toys to work at all. Will Apple really refuse to help people with iBricks? Speaking in London last week, Steve Jobs, Apple’s chief executive, said the company is in a “cat and mouse” game with hackers. “People will try to break in, and it’s our job to stop them breaking in,” he said. David Pogue, our technology reviewer, received a cautionary message Wednesday night from a person familiar with Apple’s plans after he posted a video showing some unofficial, but entertaining, applications that can be installed on the iPhone. Take those applications off your phones now, David was warned, or a software update scheduled for Thursday afternoon could turn your phone into a brick. [David takes a closer look at the iPhone update here.] On Monday, Apple had issued a press release warning of “irreparable damage” to iPhones that have been modified or unlocked from the AT&T network. It also threatened users that “the permanent inability to use an iPhone due to installing unlocking software is not covered under the iPhone’s warranty.” This caused a scurry by hackers to develop software that will relock iPhones before software updates. It’s like kids at the slumber party turning out the lights and jumping under the covers each time mom thumps up the stairs. Apple may well be justified using tough tactics against people who modify their phones so they no longer use the AT&T network. Apple stands to receive several hundred dollars for each phone over the course of two years from AT&T’s service fees. Some people—actually a lot of people—don’t much like AT&T. Or they don’t want to pay AT&T’s roaming fees overseas and would rather use a local cellular company. And these people will always be looking for ways to defeat Apple’s locking system. The simple way to defuse this fight, of course, would simply be for Apple to sell an unlocked iPhone for, say, $300 more than the locked version. But this gets at Apple’s propensity for control. The phone is, in some ways, a better experience on AT&T because of its links to voice mail and so on. But does that mean if Apple’s way is better it should always prevent people from using its products in some less optimal way? Since the iPhone is a very sleek, capable handheld computer, people are going to want to run programs on it. They are going to want to hack and see what they can build. It’s a law of nature. And Apple might as well be fighting gravity. Many other cell phones are locked down, of course. But few other phones capture the imagination of programmers the way the iPhone does. Apple did allow for some application development inside its Safari browser. But it is not supporting Java or Flash, the two environments that allow the most flexible applications. And there is no official way to write applications that run on the phone’s operating system. Apple has said that it is worried that some applications could cause trouble for the AT&T network. But it’s hard to imagine that there isn’t a way to wall off and limit network usage without preventing people from developing well-mannered programs. Apple essentially has two choices. Either it exposes most of the iPhone’s capabilities to developers. Or it will have to gird for an ever escalating war in which it will have to send ever more electronic brick-bombs to its best customers who don’t follow its strict rules. http://bits.blogs.nytimes.com/2007/0.../index.html?hp  Interview With A Convicted Hacker: Robert Moore Tells How He Broke Into Routers And Stole VoIP Services Sharon Gaudin On his way to federal prison, the 23-year-old hacker says breaking into computers at telecom companies and major corporations was "so easy a caveman could do it." Convicted hacker Robert Moore, who is set to go to federal prison this week, says breaking into 15 telecommunications companies and hundreds of businesses worldwide was incredibly easy because simple IT mistakes left gaping technical holes. Moore, 23, of Spokane, Wash., pleaded guilty to conspiracy to commit computer fraud and is slated to begin his two-year sentence on Thursday for his part in a scheme to steal voice over IP services and sell them through a separate company. While prosecutors call co-conspirator Edwin Pena the mastermind of the operation, Moore acted as the hacker, admittedly scanning and breaking into telecom companies and other corporations around the world. "It's so easy. It's so easy a caveman can do it," Moore told InformationWeek, laughing. "When you've got that many computers at your fingertips, you'd be surprised how many are insecure." Pena, who is charged with acting as a legitimate wholesaler of Internet-based phone services as part of what the government called a "sophisticated fraud," fled the country a year ago and is wanted as a fugitive. Assistant U.S. Attorney Erez Liebermann said Pena allegedly stole and then sold more than 10 million minutes of service at deeply discounted rates, netting more than $1 million from the scheme. Acting as the operation's technical muscle only netted Moore $20,000 of the haul, according to Moore. The government identified more than 15 VoIP service providers that were hacked into, adding that Moore scanned more than 6 million computers just between June and October of 2005. AT&T reported to the court that Moore ran 6 million scans on its network alone. However, the names of the companies Moore and Pena hacked into don't appear in the court documents--aliases are used instead--and Moore said he wasn't at liberty to identify them publicly. Liebermann noted that one small telecom went out of business because of expenses the company incurred during the break-in. The company legitimately routed its own VoIP traffic through a larger telecom and was forced to pay the other company for the calls that Pena and Moore fraudulently sent through their network. "They had to eat the bill and were unable to remain in business," added Liebermann. Default Passwords: A Hacker's Dream Moore said what made the hacking job so easy was that 70% of all the companies he scanned were insecure, and 45% to 50% of VoIP providers were insecure. The biggest insecurity? Default passwords. "I'd say 85% of them were misconfigured routers. They had the default passwords on them," said Moore. "You would not believe the number of routers that had 'admin' or 'Cisco0' as passwords on them. We could get full access to a Cisco box with enabled access so you can do whatever you want to the box. ... We also targeted Mera, a Web-based switch. It turns any computer basically into a switch so you could do the calls through it. We found the default password for it. We would take that and I'd write a scanner for Mera boxes and we'd run the password against it to try to log in, and basically we could get in almost every time. Then we'd have all sorts of information, basically the whole database, right at our fingertips." Keith Rhodes, chief technologist at the U.S. Government Accountability Office, said he's not surprised at all by what Moore says he found. "Default passwords are a silly problem," said Rhodes, who is widely considered to be the federal government's top hacker. "But they were able to take a silly flaw and turn it into a business. ... It disappoints me, but I'm not surprised." Kenneth van Wyk, principal consultant with KRvW Associates, said leaving default passwords up is a widespread and dangerous problem. "It's a huge problem, but it's a problem the IT industry has known about for at least two decades and we haven't made much progress in fixing it," said van Wyk. "People focus on functionality when they're setting up a system. Does the thing work? Yes. Fine, move on. They don't spend the time doing the housework and cleaning things up." It's also a problem for which the companies themselves are liable, Moore said. "I think it's all their fault," he added. "They're using default passwords and their administrators don't even care. ... Anybody who has bad security, it's their fault. There are so many people out there who are malicious hackers who look for these vulnerable boxes. All this information is right on the Web and it's easy to find. They need to get more education and security in the VoIP industry. There were thousands of routers that were compromised in this, just from my scans alone." Alan Paller, director of research at the SANS Institute, says it's not the companies' fault. He even says it's not IT's fault. The problem, he says, lies with the vendors. "Products should be sold so the default password has to be changed first time they use it," said Paller. "It's all on the vendors. It's not about the user being careless. It's a silly thing for them to have to know to do." Rhodes, however, says until vendors make it necessary to change the default password before a system or product will work, IT departments need to be given the time and resources to get it done. "I have nothing but empathy for all the security personnel I've ever worked with," he said. "I've never met one yet who had enough people, enough time, enough support. ... It would take nothing to change a default password, but you need to actually have people who have the job to do that." The Break In Moore, who describes himself as a "mega geek" more upset about being banned from using a computer than actually going to prison, said his job in the operation largely was to write software that ran scans and brute-force attacks against Cisco XM routers and Quintum Tenor VoIP gateways. To do it, he said he used 2 gigs of information on corporate IP ranges that they bought for $800. He explained that he would first scan the network looking mainly for the Cisco and Quintum boxes. If he found them, he would then scan to see what models they were and then he would scan again, this time for vulnerabilities, like default passwords or unpatched bugs in old Cisco IOS boxes. If he didn't find default passwords or easily exploitable bugs, he'd run brute-force or dictionary attacks to try to break the passwords. "We would go to telecom forums and other telecom sites that list company names and where they're from," he explained. "We'd look at foreign countries first. We'd take the name and IP range and then dump it into the scanner. ... Some of the Cisco versions, like IOS, were old and easier to get into." Liebermann, the prosecutor, also noted that while Moore broke into telecoms so they could steal the VoIP service, he also hacked into countless other businesses so they could use the hijacked company connections to disguise the calls they were sending to the telecoms. With the VoIP connections in place, they simply needed corporate connections to mask their trail. "He wanted me to look for [a network] with lots of traffic," said Moore. "Even if it was not a telecom, they might be connected to a telecom and then you could move through that connection to the telecom. ... [Pena] was taking legit calls that he had customers for and then rerouting the calls through rogue boxes." And Moore didn't just focus on telecoms. He said he scanned "anybody" -- businesses, agencies and individual users. "I know I scanned a lot of people," he said. "Schools. People. Companies. Anybody. I probably hit millions of normal [users], too." Tips From The Hacker Moore said it would have been easy for IT and security managers to detect him in their companies' systems ... if they'd been looking. The problem was that, generally, no one was paying attention. "If they were just monitoring their boxes and keeping logs, they could easily have seen us logged in there," he said, adding that IT could have run its own scans, checking to see logged-in users. "If they had an intrusion detection system set up, they could have easily seen that these weren't their calls." The hacker said IT technicians also could have set up access lists, telling the network to only allow their own IP addresses to get in. "We came across only two or three boxes that actually had access lists in place," he added. "The telecoms we couldn't get into had access lists or boxes we couldn't get into because of strong passwords." The GAO's Rhodes said if companies don't fix the small problems, they can open up gaping holes that hackers are ready to jump through. "All it takes is one bad access point and they're in," he noted. "The weak link -- you find that one point and all the security unravels. ... I'm not surprised that someone going to prison said 70% are at risk. You only have to have one default password and all your security is at risk." http://www.informationweek.com/news/...leID=202101781  Sources: Staged Cyber Attack Reveals Vulnerability in Power Grid Jeanne Meserve Researchers who launched an experimental cyber attack caused a generator to self-destruct, alarming the federal government and electrical industry about what might happen if such an attack were carried out on a larger scale, CNN has learned. Sources familiar with the experiment said the same attack scenario could be used against huge generators that produce the country's electric power. Some experts fear bigger, coordinated attacks could cause widespread damage to electric infrastructure that could take months to fix. CNN has honored a request from the Department of Homeland Security not to divulge certain details about the experiment, dubbed "Aurora," and conducted in March at the Department of Energy's Idaho lab In a previously classified video of the test CNN obtained, the generator shakes and smokes, and then stops. DHS acknowledged the experiment involved controlled hacking into a replica of a power plant's control system. Sources familiar with the test said researchers changed the operating cycle of the generator, sending it out of control. Watch the generator shake and start to smoke » The White House was briefed on the experiment, and DHS officials said they have since been working with the electric industry to devise a way to thwart such an attack. "I can't say it [the vulnerability] has been eliminated. But I can say a lot of risk has been taken off the table," said Robert Jamison, acting undersecretary of DHS's National Protection and Programs Directorate. Government sources said changes are being made to both computer software and physical hardware to protect power generating equipment. And the Nuclear Regulatory Commission said it is conducting inspections to ensure all nuclear plants have made the fix. Industry experts also said the experiment shows large electric systems are vulnerable in ways not previously demonstrated. "What people had assumed in the past is the worst thing you can do is shut things down. And that's not necessarily the case. A lot of times the worst thing you can do, for example, is open a valve -- have bad things spew out of a valve," said Joe Weiss of Applied Control Solutions. "The point is, it allows you to take control of these very large, very critical pieces of equipment and you can have them do what you want them to do," he said. Adding to the vulnerability of control systems, many of them are manufactured and used overseas. Persons at manufacturing plants overseas have access to control system schematics and even software program passwords, industry experts say. Weiss and others hypothesize that multiple, simultaneous cyber-attacks on key electric facilities could knock out power to a large geographic area for months, harming the nation's economy. "For about $5 million and between three to five years of preparation, an organization, whether it be transnational terrorist groups or nation states, could mount a strategic attack against the United States," said O. Sami Saydjari of the nonprofit Professionals for Cyber Defense. Economist Scott Borg, who produces security-related data for the federal government, projects that if a third of the country lost power for three months, the economic price tag would be $700 billion. "It's equivalent to 40 to 50 large hurricanes striking all at once," Borg said. "It's greater economic damage than any modern economy ever suffered. ... It's greater then the Great Depression. It's greater than the damage we did with strategic bombing on Germany in World War II." Computer experts have long warned of the vulnerability of cyber attacks, and many say the government is not devoting enough money or attention to the matter. "We need to get on it, and get on it quickly," said former CIA Director James Woolsey on Tuesday. Woolsey, along with other prominent computer and security experts, signed a 2002 letter to President Bush urging a massive cyber-defense program. "Fast and resolute mitigating action is needed to avoid a national disaster," the letter said. But five years later, there is no such program. Federal spending on electronic security is projected to increase slightly in the coming fiscal year, but spending in the Department of Homeland Security is projected to decrease to less than $100 million, with only $12 million spent to secure power control systems. Despite all the warnings and worry, there has not been any publicly known successful cyber-attack against a power plant's control system. And electric utilities have paid more attention to electronic risks than many other industries, adopting voluntary cyber-standards. "Of all our industries, there are only a couple -- perhaps banking and finance and telecommunications -- that have better cyber-security or better security in general then electric power," Borg said. And DHS notes that it uncovered the vulnerability discovered in March, and is taking steps with industry to address it. While acknowledging some vulnerability, DHS's Jamison said "several conditions have to be in place. ... You first have to gain access to that individual control system. [It] has to be a control system that is vulnerable to this type of attack." "You have to have overcome or have not enacted basic security protocols that are inherent on many of those systems. And you have to have some basic understanding of what you're doing. How the control system works and what, how the equipment works in order to do damage. But it is, it is a concern we take seriously." "It is a serious concern. But I want to point out that there is no threat, there is no indication that anybody is trying to take advantage of this individual vulnerability," Jamison said. Borg notes that industry will have to remain forever vigilant at protecting control systems. "It will always be an ongoing problem. It's something we will have to be dealing with [for] lots of years to come," he said. http://www.cnn.com/2007/US/09/26/pow...isk/index.html  ABN Amro Suffers P2P Data Breach Frank Washkuch Jr. A former employee of Citi's ABN Amro Mortgage group leaked the personal information, including Social Security numbers, of more than 5,000 customers via a peer-to-peer (p2p) file-sharing network. The former employee reportedly compromised three spreadsheets containing more than 5,000 Social Security numbers. Data-leak prevention vendor Tiversa traced the breach back to a Florida computer with BearShare software installed, according to an Associated Press report. The data was leaked from the former employee's home computer. Tiversa Chief Operating Officer Christopher Gormley told SCMagazineUS.com today that his company investigated the incident after being called by a Wall Street Journal reporter, and found data — including names, Social Security numbers, amounts of loans and types of banks where loans had originated — had been leaked. Citi spokesman Mark Rodgers referred questions today to a company statement saying that the financial services giant has taken actions to rectify the breach. “Protecting customer information remains a priority at Citi, and we remain fully committed to physical, electronic and procedural safeguards to protect personal information,” the company said in a statement. “The customer information involved has been retrieved from the source computer. We are taking appropriate steps to identify, notify and protect the customers involved, including offering complimentary credit monitoring services.” A Seattle man was arrested earlier this month in what is believed to be the first case against someone using p2p programs for identity theft. Gregory Thomas Kopiloff, 35, stands accused of using Lime Wire, Soulseek and other file-sharing applications to steal personal and financial information from victims' PCs. He allegedly used stolen credit card information to go on an online shopping spree, according to a federal indictment filed in U.S. District Court in Seattle. TD Ameritrade revealed this month that the names and contact information of 6.3 million customers were exposed after a company database was infiltrated. The Omaha, Neb.-based brokerage said it discovered the breach after customers told the company they received spam offering unsolicited investment advice. Saying that p2p networks can enable access to “basically a treasure chest of personal information,” Avivah Litan, Gartner vice president and distinguished analyst, told SCMagazineUS.com today that financial institutions should use data-monitoring solutions to prevent breaches. “There are definitely some technology solutions out there that enable banks to monitor all of the data that moves through the network. So Citi just didn't have the sense of urgency that they should have had in putting those systems in,” she said. “In this day and age, there aren't a lot of excuses for this sort of breach.” Gordon Rapkin, president and CEO of Protegrity, told SCMagazineUS.com today that he is surprised the data wasn't encrypted. “For one, what was the data doing on a computer and why wasn't it protected? And once you get past all those types of questions, the process question here is, what did Citi do to educate their users to the dangers?” he said. “This looks like [a case of] an uneducated employee who didn't realize the risks of associating a peer-to-peer network with sensitive corporate data.” Steve Fossen, manager of threat research at Fortinet, told SCMagazineUS.com today that unmonitored use of file-sharing applications can open up networks to similar threats. “Installing any sharing application opens up a large hole in your network, even stuff like messaging clients,” he said. “It's a policy issue. In many cases, [administrators] can install firewalls and stop networks traffic when it's about to go out.” http://www.scmagazineus.com/ABN-Amro...article/35828/  Unisys Under Investigation for Cyber Attacks on Homeland Security Computers AP A top homeland security lawmaker has called for an investigation into possible cyber attacks on computer systems at the Homeland Security Department. Rep. Bennie Thompson, D-Miss., said he believes Unisys Corp - the company that holds the $1.7 billion contract to build parts of the Homeland Security Department's computer network - is at fault for these network break-ins. Thompson chairs the House Homeland Security committee and asked the department's inspector general to investigate. Thompson's investigation found that dozens of computers may have been compromised by hackers, but the incidents were not noticed until months after the attacks. Information taken from the department's systems was sent to a Web service that connects to Chinese Internet sites, and contractors gave misleading information to the department about the attacks, according to Thompson's findings. "The department is the victim not only of cyber attacks initiated by foreign entities, but of incompetent and possibly illegal activity by the contractor charged with maintaining security on its networks," Thompson wrote in a Sept. 21 letter to the department's inspector general. Homeland Security spokesman Russ Knocke would not comment on Thompson's allegations. But he said the Unisys contract is being subjected to a new round of competition that includes other contractors. While Unisys is not prohibited from competing, past performance will be considered in the contract award, he said. Unisys was awarded a one-year contract in 2006 with two one-year options. "We are aware of, and have responded to, malicious cyber activity directed at the U.S. government over the past few years," Knocke said. "We take cyber security very seriously." The FBI would not say whether it is investigating Unisys. Unisys disputed the committee's findings, but company spokeswoman Lisa Meyer would not go into detail because of security concerns. The department's inspector general will decide in the next few days whether to pursue the investigation, a spokeswoman said Monday. http://www.siliconvalley.com/news/ci_6984962  Terrorist Threat Risk Leaked on P2P Net How did a confidential terrorist threat assessment of Chicago end up on Limewire? Jaikumar Vijayan Officials at consulting firm Booz Allen Hamilton Inc. are looking into how a Fox News reporter acquired a confidential terrorist threat assessment on Chicago over a public file-sharing network. Larry Yellen, an investigative reporter with WFLD Fox News in Chicago, on Tuesday reported that he recently used a peer-to-peer (P2P) program called LimeWire to obtain the Booz Allen document. The firm authored the document in 2002. George Farrar, a spokesman for Booz Allen, Thursday confirmed the incident and said the document was commissioned by the Federal Transit Administration (FTA) five years ago. It was one of 35 threat assessments of the nation's bus and rail systems that Booz Allen was commissioned to do by the agency. "Essentially, yes, those were Booz Allen documents that were available on the Internet via a peer-to-peer file-sharing system," Farrar said. "What we don't know is from what system those documents made their way to the Internet." Farrar said that after Booz Allen completed the threat assessment, it made the document available to numerous federal, state and private-sector entities and first responders as required under its contract with the FTA. It was then the responsibility of those entities to protect the documents, Farrar said. "We investigated internally and didn't find the document on our computers," Farrar said. He also noted that employees at Booz Allen cannot connect to file-sharing networks at work. "We are continuing to investigate. We can't say definitely one way or the other," who the source of the leaked document was. But he said it is possible that the document was leaked from a computer belonging to one of the entities that got the report. "We don't know what controls were put in place after the document left our hands. So far, we haven't been able to find evidence that it was from our computers," he said. The Booz Allen incident again highlights what some analysts say is a growing problem: the easy availability of all sorts of government, personal and confidential information on P2P networks. The situation is the result of information being leaked onto these networks by individuals who fail to take precautions for securing their computers during P2P sessions. Popular P2P clients such as Kazaa, LimeWire, BearShare, Morpheus and FastTrack are designed to let users quickly download and share music and video files. Normally, such clients allow users to download files to -- and share items from -- a particular folder on their system with other users on the network. But if the access these P2P clients have on a system is not controlled, it is easy to expose and share personal data with all other users on a file-sharing network. U.S. authorities recently arrested a Seattle man on charges that he deliberately mined and harvested P2P networks for such data which he then used to commit ID theft -- the first time that anyone in the U.S. has been arrested on charges of committing ID theft over P2P networks. In July, the House Committee on Oversight and Government Reform heard testimony from several witnesses about how everything from classified military documents to corporate data can be found on P2P networks. The leaked documents on P2P networks cited as examples at the hearing included the Pentagon's entire secret backbone network infrastructure diagram; contractor data on radio frequency manipulation to defeat improvised explosive devices in Iraq; and physical terrorism threat assessments for three major U.S cities. http://www.pcworld.com/article/id,13...s/article.html  Anti-Piracy Technology For Sale On eBay For $1m enigmax In 2005, anti-piracy company Viralg burst onto the file-sharing scene promising to end 99% of all online piracy. Today, if you need a top secret piracy solution, have an eBay account, can collect in person and have $1,000,000 burning a hole in your pocket, you’re in luck. Imagine the scenario - you’re the head of a multi-million dollar label, someone has convinced you that your business is losing money due to file-sharing. What do you do? Call in the Ghostbusters? Or do what lots of companies do and call in the likes of MediaDefender to help them. As no anti-piracy system can do anything other than make a very small impact on file-sharing, it’s a far from satisfactory solution. Early in 2005, established anti-piracy company Viralg of Finland burst onto the P2P scene with a staggering claim: With their technology it was possible to end 99% of all file-sharing. In 2004, Viralg listed Electronic Arts, Vivendi, Microsoft Game Studios, Sony Computer Entertainment, Atari, Nintendo, Codemasters and THQ as just some of their customers. They were among the nominees for the ICT Prize 2005 and the winner of the Venture Cup business plan competition. The portfolio certainly made them appear impressive at the time, so when an eBay auction caught the eye today offering to sell Viralg’s technology for a cool $1,000,000, TorrentFreak became a little curious. So what’s on offer? Looks like Viralg’s ‘intellectual property’ in the form of some patent applications: Viralg supplies technology aimed at preventing sharing of illegal content such as music, movies, GPS maps, games and software from being shared over P2P networks such as Gnutella. Viralg technology is in widespread use by record companies in Finland (90% of customers) and in the other Scandinavian countries. Technology has generated turnover of over 500.000 US dollars. The patent applications for sale cover the necessary key technology for the only possible effective protection against illegal P2P sharing. Depending on the source illegal P2P causes damages of 4 to 12 billion US dollars to media companies per year. So should likely buyers (unhappy MediaDefender customers perhaps?) invest in this technology? Viralg claimed to be able to create a corrupted file but with a working hash, giving it the appearance of a genuine file. As people downloaded they got a selection of genuine and corrupt parts sent to them rendering the final file useless. Although partially effective on the FastTrack network (KaZaA [R.I.P] )years ago, Viralg’s offer of 40 hours of training to use the system still doesn’t cut it in today’s BitTorrent dominated file-sharing world. Before Prince gets any fancy ideas about buying this for the Web Sheriff to use against The Pirate Bay, this outdated system is pretty useless against BitTorrent, which renders its ‘Patented Virtual Algorithm’, well - useless. TorrentFreak spoke to Dr. Ir. Johan Pouwelse, researcher on P2P technology at Delft University of Technology, who explained why: “Bittorrent uses a separate hash for every 1-4 MByte. This means you can still exploit the weakness in the protocol by sending bad data. However, clients are now generally so smart that they only accept maximum 1 fake 1-4MB block from an IP address.” Of course to corrupt lots of files, you need lots of presence on file-sharing networks (servers, accounts, the whole MediaDefender-style setup) so the $1m tag is just the tip of an enormous iceberg. Maybe some of the sales statistics will tempt prospective buyers? The system has been running since 2003, and in that time it generated a turnover of $500,000. Potential buyers are likely to be more interested in the bottom line, especially now that the bottom has fallen out of the FastTrack network. Anyone with a bulging bank balance needing a guarantee of being able to corrupt files on the FastTrack network (and is unaware that MediaDefender’s tools are available for free) should hurry over to the eBay auction right now, there’s not long left to go - for the auction or Viralg http://torrentfreak.com/anti-piracy-...for-1m-070925/  Gmail Cookie Vulnerability Exposes User's Privacy Liam Tung Petko Petkov of "ethical hacking" group GNUCitizen has developed a proof-of-concept program to steal contacts and incoming e-mails from Google Gmail users. "This can be used to forward all your incoming e-mail," Pure Hacking security researcher Chris Gatford said. "It's just a proof of concept at the moment, but what they're demonstrating is the potential to use this vulnerability for malicious purposes." According to Gatford, attackers could compromise a Gmail account--using a cross-site scripting vulnerability--if the victim is logged in and clicks on a malicious link. From that moment, the attacker can take over the session cookies for Gmail and subsequently forward all the account's messages to a POP account. "If someone picks up on this before Google fixes it--or if someone knew of the vulnerability before this guy published it--this could be very damaging to Gmail users," he added. The problem is potentially compounded by Google's policy of retaining cookies for two years. "Once you've managed to snarf a cookie, you can access (a user's) Gmail account without the password for the next two years," he said. While the obvious risk is to the home user, many organizations could be exposed, since they do not filter employee e-mails sent from work to personal accounts, he added. "People do use private accounts to store work information," IBRS security analyst James Turner said. "I've worked at one organization where this was implicitly expected, because the mail server at the time was so unreliable. But that scenario is certainly less than optimal. "In an ideal world, an organization would be able to draw a line in the sand and say that corporate data does not pass this point. The current reality is that there are Gen-Y workers who are sharing information with each other on multiple alternative communication channels--Gmail and Facebook included." One work-around is to use Gmail through Firefox and disable JavaScript. While this limits user access to many components of popular Web sites, it will protect against the potential threat. Developers at many large enterprises are not aware of the power of cross-site scripting, said Pure Hacking's Gatford. "In the last year or so, (XSS vulnerabilities) have been used by attackers to grab cookie values and therefore gain access to normally password-protected sites." "When you have organizations like Google spending countless man-hours reducing security vulnerabilities...you can imagine how bad the actual situation is for other organizations," Gatford said. Gatford advised organizations to use resources such as the Open Web Application Security Project, or OWASP, which offers free tools to help write secure code and allow testing for XSS vulnerabilities. Google was unavailable to comment. http://www.news.com/Gmail-cookie-vul...3-6210353.html  Despite AOL’s Claim, AIM Worm Hole Still Wide Open Ryan Naraine There’s a nasty worm hole in America Online’s standalone AIM (instant messaging) software that won’t be patched until the middle of October. AOL claims that the vulnerability, which allows a remote attacker to launch executable code without any user action, has been patched in the latest beta client but, as I’ve confirmed in a test with security researcher Aviv Raff (see screenshot below), fully patched versions of the beta is still wide open to a nasty worm attack. Production copies of the software, which sits on tens of millions of desktops around the world, are also unpatched. [SEE: Zero-day flaws surface in AOL, Yahoo IM products ] In the demonstration, Raff simply sent me an IM to trigger the launch of the calculator application. The attack scenario works without the target clicking on a link and only requires that the AIM user is logged on and accepting incoming messages. This vulnerability, first reported to AOL by researchers at Core Security more than a month ago, is caused by the way AIM supports the rendering of HTML content via an embedded Internet Explorer server control. In an advisory issued after a lengthy back-and-forth with AOL security engineers, Core warned: [AIM does] not properly sanitize the potentially malicious input content to be rendered and, as a result, an attacker might provide malicious HTML content as part of an IM message to directly exploit Internet Explorer bugs or to target IE’s security configuration weaknesses. The attack scenarios outlined by Core includes: Direct remote execution of arbitrary commands without user interaction. Direct exploitation of IE bugs without user interaction. For example, exploitation bugs that normally require the user to click on a URL provided by the attacker can be exploited directly using this attack vector. Direct injection of scripting code in Internet Explorer. For example, remotely injecting JavaScript code into the embedded IE control of the AIM client. Remote instantiation of Active X controls in the corresponding security zone. Cross-site request forgery and token/cookie manipulation using embedded HTML. AOL coordinated with Core on the release of the advisory on the understanding that the flaw was patched in the latest beta version but, as Raff discovered, the underlying vulnerability was never fixed. “The problem with AOL’s patch is that they filter specific tags and attributes, instead of fixing the main cause of the vulnerability, which is locking down the local zone of their client’s web-browser control,” Raff said. The scary thing in all this is that Core Security and Raff are not the only researchers finding trivial variations of this flaw. Earlier this month, a security researchers “Shell” and “Lone” issued a public warning for what appears to be a similar input sanitization bug. Even worst, AOL has not seen it fit to fix the issue for its millions of users. Outside of proof that the flaw has not been fixed in beta updates, there really is no excuse for AOL to opt only to fix beta versions — which are generally frowned upon in many businesses that rely on AIM for inter-office communication. AOL is on record as saying a comprehensive patch won’t be available until the middle of October. In the meantime, if you’re using standalone AIM on desktops with valuable data, my best advice is to log off immediately and uninstall the product. Cross-platform IM clients like Trillian (Windows) and Adium (Mac) can fill in as replacements. [ UPDATE: September 27, 2007 @ 3:17 PM] A statement from AOL’s Erin Gifford: I spotted your post and wanted to let you know that as of today no AIM users are at risk. We were able to implement server side fixes that fully address all of the client vulnerabilities cited by Aviv Raff in his blog. Regardless of the AIM client our users are currently on, they are completely protected. Aviv Raff responds: They’ve added my adjusted proof-of-concept to their filters, but it took me 5 seconds to bypass it. Took them over 3 hours to add one filter, which I bypassed in 5 seconds. This is an endless cat and mouse game. And the cat can never win. http://blogs.zdnet.com/security/?p=542  Ebay Hacked, User Info Posted This morning a hacker posted the personal contact information and credit card data of 1,200 ebay users on the eBay.com Trust & Saftey forums. eBay pulled the Trust & Saftey forums off line, but not before one user made a video of the hacked forums and posted it on youtube.com. eBay response is on the eBay chatter page, and seems to try and down play this 'fraudster's' activity. http://it.slashdot.org/article.pl?sid=07/09/26/144210  Is Cyber Crime Really the FBI's No. 3 Priority? Brian Krebs The Federal Bureau of Investigation says that its No. 3 priority is protecting the United States "against cyber-based attacks and high-technology crimes." Given the increasing pervasiveness and costs associated with such crime, FBI Director Robert Mueller should be commended for giving anti-cyber crime investigations such high status, second only to terrorism and espionage/counter intelligence investigations. But according to an analysis by Security Fix, cyber crime remains a distant third priority for the federal law enforcement agency, at least in terms of resources applied to the problem. That assessment is based on information from the Justice Department itself, based on a reading of a 203-page document justifying its fiscal year 2008 budget request to Congress. The cyber portion of the 2008 request includes a request for $258.5 million in funding for some 659 field agents, a 1.5 percent increase over 2007 levels. That's 659 out of a total of 11,868 FBI agents nationwide, which would mean the FBI is on track to dedicate roughly 5.5 percent of its agents to cyber crime investigations. But as we'll see later, the true number may actually be lower. To be clear, the FBI's cyber program encompasses everything from battling traditional cyber crime -- the kind of illegal activity you might associate with someone hacking into your PC or stealing your identity -- to illicit online activities that could potentially support terrorist activity. Here's how the Bureau describes its cyber efforts (the text is from the DOJ '08 budget justification): "The FBI's Cyber Program consolidates Headquarters and field resources dedicated to combating cyber-crime under a single entity. This allows the Cyber Program to coordinate, supervise, and facilitate the FBI's investigation of those federal violations in which the Internet, computer systems, or networks are exploited as the principal instruments or targets of terrorist organizations, foreign government-sponsored intelligence operations, or criminal activity. Included under the purview of the Cyber Program are counterterrorism, counterintelligence and criminal computer intrusion investigations; intellectual property rights-related investigations involving theft of trade secrets and signals; copyright infringement investigations involving computer software; credit/debit card fraud where there is substantial Internet and online involvement; online fraud and related identity theft Investigations; and the Innocent Images National Initiative." While the "Innocent Images National Initiative" is listed last in the excerpt above, it's by no means least among the FBI's cyber priorities. The initiative -- designed to catch sickos who enjoy looking at and facilitating child pornography -- claims the attention of roughly a third of the agency's cyber agents, according to the document. I'm certainly not trying to take anything away from that important program, or suggest that fewer agents be dedicated to it. The drive to lock up child predators is one of few law enforcement imperatives that transcends national boundaries or politics. Experts say it is rare to find a form of crime which elicits such visceral and rapid reaction and cooperation from law enforcement officials around the world. The main reason I single it out is that it clouds the agency's record on addressing the kinds of crimes that most people probably think about when they hear the words "cyber crime." According to the FBI, the Innocent Images program accounted for a major share of the FBI cyber crime convictions and "pre-trial diversions" in fiscal year 2006. For example, Innocent Images netted 1,018 convictions and plea agreements in 2006, whereas the Justice Department won 118 convictions or pleas for computer intrusion cases last year. If we look at the number of agents the FBI has tasked to investigating illegal online activities of the sort that involve computer intrusions or the trade and/or sale of stolen business and consumer data (crimes increasingly committed by organized crime syndicates based overseas), then it appears that the FBI has requested a total of 427 agents to fight the cyber crime problem next year. So, assuming Congress grants its budget request, the FBI is on track to have about 3.6 percent of all of its active agents dedicated to its stated No. 3 priority. Of course, the FBI is not the only agency fighting cyber crime. The U.S. Secret Service and the U.S. Postal Inspection Service both play critical roles. Also, none of this analysis should take anything away from the work being done by several industry-government partnerships, such as the National Cyber-Forensics & Training Alliance (NCFTA) in Pittsburgh and the Internet Crime Complaint Center (IC3) in West Virginia. Nor should it diminish the work the FBI does in tandem with various task forces that rely heavily upon state and local law enforcement officers to investigate identity theft cases that often have roots in cyber crime. But this data does seem to raise the following question: If the FBI's third most-important priority claims just over 3.5 percent of its active agents, how many agents and FBI resources are dedicated to the remaining Top Ten priorities? The FBI says those priorities are, in the following order: 4. Combat public corruption at all levels. 5. Protect civil rights. 6. Combat transnational and national criminal organizations and enterprises. 7. Combat major white-collar crime. 8. Combat significant violent crime. 9. Support federal, state, county, municipal, and international partners. 10. Upgrade technology to successfully perform the FBI's mission. Again, a major reason I want to call attention to these figures it to spark a debate over whether the FBI is dedicating enough resources to fighting cyber crime. For his part, Paul Kurtz, a former White House cyber security adviser for the Bush administration, said absolutely not. "I think that we need to dramatically increase the number of agents and analysts supporting the government's overall cyber investigative efforts," Kurtz said. "The FBI -- for what resources it has -- is not doing a bad job. But when we have as many problems going on as we have today, with China and Russia and organized crime and white-collar criminals getting involved in computer crimes, we don't have nearly enough agent workforce to take on this problem. And until we see a major increase, we're going to remain behind on fighting this problem." But Jim Lewis, a senior fellow at the Center for Strategic & International Studies and director of its Technology and Public Policy Program, said you can throw all the FBI agents in the world at the cyber program without much improvement in the current situation if the U.S. cannot build stronger ties with foreign law enforcement agencies. "When there are political or legal situations in other countries that keep you from using your resources efficiently, then adding more resources doesn't help you very much," Lewis said. "The FBI shouldn't be trying to do everything, but should focus mainly on the largest cyber criminal operations. The problem is that the level of cooperation we get from many countries is kind of dubious, and criminals will gravitate to places where they have the best chance of not getting caught." http://blog.washingtonpost.com/secur...rd_p.html#more  Stealth Windows Update Prevents XP Repair Scott Dunn A silent update that Microsoft deployed widely in July and August is preventing the "repair" feature of Windows XP from completing successfully. Ever since the Redmond company's recent download of new support files for Windows Update, users of XP's repair function have been unable to install the latest 80 patches from Microsoft. Repaired installations of XP can't be updated Accounts of conflicts with XP's repair option came to our attention after Microsoft's "silent install" of Windows Update (WU) executable files, known as version 7.0.600.381, was reported in the Sept. 13 and 20 issues of the Windows Secrets Newsletter. The trouble occurs when users reinstall XP's system files using the repair capability found on genuine XP CD-ROMs. (The feature is not present on "Restore CDs.") The repair option, which is typically employed when XP for some reason becomes unbootable, rolls many aspects of XP back to a pristine state. It wipes out many updates and patches and sets Internet Explorer back to the version that originally shipped with the operating system. Normally, users who repair XP can easily download and install the latest patches, using the Automatic Updates control panel or navigating directly to Microsoft's Windows Update site. However, after using the repair option from an XP CD-ROM, Windows Update now downloads and installs the new 7.0.600.381 executable files. Some WU executables aren't registered with the operating system, preventing Windows Update from working as intended. This, in turn, prevents Microsoft's 80 latest patches from installing — even if the patches successfully downloaded to the PC. I was able to reproduce and confirm the problem on a test machine. When WU tries to download the most recent patches to a "repaired" XP machine, Microsoft's Web site simply states: "A problem on your computer is preventing the updates from being downloaded or installed." __________ Most ordinary Windows users might never attempt a repair install, but the problem will affect many administrators who must repair Windows frequently. Anyone who runs XP's repair function will find that isolating the cause of the failed updates is not a simple matter. Beginning in July, it is not possible for Windows users to install updates without first receiving the 7.0.6000.381 version of nine Windows Update support files. (See my Sept. 13 story for details.) If Automatic Updates is turned on, the .381 update will be installed automatically. If AU is not turned on, you'll be prompted to let Windows Update upgrade itself before you can installing any other updates. Consequently, users are forced to get the silent update before they can attempt to install Microsoft's latest security patches. The problem apparently arises because seven of the DLLs (dynamic link library files) used by WU fail to be registered with Windows. If files of the same name had previously been registered — as happened when Windows Update upgraded itself in the past — the new DLL files are registered, too, and no problem occurs. On a "repaired" copy of XP, however, no such registration has occurred, and failing to register the new DLLs costs Windows Update the ability to install any patches. Registering DLL files is normally the role of an installer program. Unlike previous upgrades to WU, however, Microsoft has published no link to an installer or a downloadable version of 7.0.6000.381. Strangely, there's no Knowledge Base article at all explaining the new version. The lack of a KB article (and the links that usually appear therein) makes it impossible for admins to run an installer to see if it would correct the registration problem. One possible fix is to install an older version of the Windows Update files (downloadable from Step 2 of Microsoft Knowledge Base article 927891) over the newer version. This involves launching the installer from a command line using a switch known as /wuforce. That corrects the registration problem, although even in this case you must still accept the .381 stealth update (again) before you can get any updates. The fact that the /wuforce procedure solves the problem suggests that the installer for .381 is the source of the bug. Manually registering files solves the problem If you find that Windows Update refuses to install most patches, you can register its missing DLLs yourself. This can be accomplished by manually entering seven commands (shown in Step 2, below) at a command prompt. If you need to run the fix on multiple machines, it's easiest to use a batch file, as Steps 1 through 5 explain: Step 1. Open Notepad (or any text editor). Step 2. Copy and paste the following command lines into the Notepad window (the /s switch runs the commands silently, freeing you from having to press Enter after each line): regsvr32 /s wuapi.dll regsvr32 /s wuaueng1.dll regsvr32 /s wuaueng.dll regsvr32 /s wucltui.dll regsvr32 /s wups2.dll regsvr32 /s wups.dll regsvr32 /s wuweb.dll Step 3. Save the file to your desktop, using a .bat or .cmd extension. Step 4. Double-click the icon of the .bat or .cmd file. Step 5. A command window will open, run the commands, and then close. The next time you visit the Windows Update site, you should not have any problem installing the latest patches. In my articles in the last two weeks on the silent installation of the Windows Update support files, I stated that the stealthy upgrade seemed harmless. Now that we know that version .381 prevents a repaired instance of XP from getting critical patches, "harmless" no longer describes the situation. The crippling of Windows Update illustrates why many computer professionals demand to review updates for software conflicts before widely installing upgrades. "I understand the need to update the infrastructure for Windows Update," says Gordon Pegue, systems administrator for Chavez Grieves Engineers, a structural engineering firm in Albuquerque, N.M. "But I think Microsoft dropped the ball a little bit communicating how the system works. Administrators should know these sorts of things, in case problems arise." A Microsoft spokeswoman offered to provide an official response about the situation, but I received no reply by press time. If you ever need to run the repair option on XP, first see the detailed description provided by the Michael Stevens Tech Web site. I'd like to thank Windows Secrets contributing editor Susan Bradley for her help in bringing reports of this problem to light. http://www.windowssecrets.com/2007/0...ents-XP-repair  PC Users Still Prefer XP to Vista Josephine Moulds It took took five years and $6bn (£3bn) to develop, but Microsoft's Vista operating system, which was launched early this year, has been shunned by consumers – with computer manufacturers taking the bizarre step of offering downgrades to the old XP version of Windows. A note on the electronics retailer website Dabs.com reads: "If you're not ready for Vista, you can downgrade to Windows XP without affecting your Sony VAIO warranty and switch back to Vista at any time." Dell took a similar line earlier this year when it brought back XP on a range of computers for its US customers in response to a deluge of online complaints. The software giant launched the Vista operating system to great fanfare in January, at least a year late. Because of Windows' market dominance the system was to be pre-loaded on the majority of new PCs and it was hoped that the release would drive sales of new computers. Microsoft says it has sold more than 60m Vista licences to date, but hardware sales have disappointed. DSG International, which owns PC World and Currys, said it was forced to discount laptops after a lacklustre response to Vista. Users complain that computers running Vista crash frequently and many of their favourite programmes such as Windows Mobile do not work with the new operating system. Microsoft said: "We understand that our [original equipment manufacturer] partners are responding appropriately to a small minority of customers that have this specific request. But, as they have said before, the vast majority of consumers want the latest and greatest technology and that includes Windows Vista." http://www.telegraph.co.uk/money/mai...24/cnpc124.xml  Why Microsoft Must Abandon Vista to Save Itself Don Reisinger While Vista was originally touted by Microsoft as the operating system savior we've all been waiting for, it has turned out to be one of the biggest blunders in technology. With a host of issues that are inexcusable and features that are taken from the Mac OS X and Linux playbook, Microsoft has once again lost sight of what we really want. As we're more than aware, Vista Ultimate comes at a premium. For an additional $160 over the Premium SKU price, Ultimate gives you a complete backup and restore option, BitLocker Drive encryption, the ever so popular Windows Fax & Scan, and the "Ultimate Extras." But what started with a promise of "Extras" by summer, quickly turned into an apology from Microsoft and the eventual release of DreamScene and Windows Hold 'Em (among others) today. And while each of the "Extras" runs just fine, Microsoft's "Extras" blunder is just another reason why the company must abandon Vista before it's too late. The first indication that Microsoft should abandon Vista is its poor sales figures. According to a recent report titled "Windows Vista Still Underperforming in U.S. Retail" from NPD, Vista sales are significantly behind XP sales during its early days. Even worse for Redmond, some are reverting to XP, citing issues with compatibility and overall design. And if that wasn't enough, Macs continue to surge and with the impending release of Leopard, Microsoft may be in for a rough holiday season. With each passing day, it's becoming blatantly clear that Microsoft released Vista too early and the company's continual mistakes and promises that can't be kept are further annoying the Windows faithful. Much talk has been given to Service Pack 1 and how this update should address many of the issues users have with Vista, but I simply don't agree. Will SP1 eliminate the ridiculous Microsoft licensing schemes? Will SP1 drop the price on the higher-end versions? Will SP1 eliminate the need for users to buy a new computer just to use the faulty OS? SP1 will do nothing but fix the holes and issues we currently know about and create even more. As we all know from the days of Windows ME and even XP, Microsoft is not the best company at finding and addressing security issues, and chances are, Vista will be no different. One significant problem that I have with Vista is its inclusion of new DRM, specifically the company's decision to install Protected Video Path. To prevent a person from copying (or in most cases, backing up) a movie, the operating system provides process isolation and if an unverified component is in use, the operating system shuts down DRM content. For the first time on any operating system, we're not even allowed to backup our favorite movies? Come on. I also find it interesting that Microsoft decided to take the user access control concept from Mac OS X and make it much worse. Can someone please explain to me why I need to be asked if I wanted to do something entirely innocuous like open a third-party app from a well-known software company? Never before have I seen such an abysmal start to an operating system release. For almost a year, people have been adopting Vista and becoming incensed by how poorly it operates. Not only does it cost too much, it requires more to run than XP, there is still poor driver support, and that draconian licensing scheme is a by-product of Microsoft picking on the wrong people. The road ahead looks dangerous for Vista and Microsoft must realize that. With Mac OS X hot on its tail, Vista is simply not capable of competing at an OS level with some of the best software around. If Microsoft continues down this path, it will be Vista that will bring the software giant to its knees--not Bill Gates' departure. Of course, categorically dumping an operating system is quite difficult and with millions already using the OS, chances are Microsoft won't find a good enough reason to do it. And while I can understand that argument, there's no reason the company can't continue to support Vista and go back to the drawing board for its next OS. Even better, go back to XP--it's not nearly as bad as Vista. As a daily user of Mac OS X, Ubuntu and Vista, I'm keenly aware of what works and what doesn't. Mac and Linux work. The time is up. Microsoft must abandon Vista and move on. It's the company's only chance at redemption. http://www.news.com/8301-10784_3-978...?tag=nefd.only  Defense Lawyers Cringe at MediaDefender's Child-Porn Patrol Plans Kim Zetter New York state Attorney General Andrew Cuomo is raising the eyebrows of defense attorneys over his recently exposed plans to pay the controversial anti-piracy firm MediaDefender to gather evidence for child-porn prosecutions. A law enforcement partnership with the peer-to-peer policing company raises questions about possible conflicts of interest and the integrity and security of evidence collected for criminal prosecutions, say attorneys. "Generally it is not looked upon favorably when a prosecutor engages a private company to collect evidence in a case or to ... partner with in a criminal case," says San Francisco public defender Jeff Adachi. "This raises grave ethical concerns regarding the propriety of that relationship between the prosecuting authority and the private company, and it also could potentially show favoritism toward that company in the future," if the company broke a different law in New York and faced prosecution by the attorney general's office. MediaDefender, a peer-to-peer policing firm that works with the entertainment industry to thwart the illegal trading of copyright works, became the target of hackers who stole and recently posted more than 6,000 of the company's internal e-mails online, along with a database, source code for its file-sharing tools and a recorded phone call between a MediaDefender employee and investigators with the New York attorney general's office. The e-mails and the recorded phone call revealed that the attorney general's office planned to outsource certain steps in its evidence-collection process against New York child-porn violators to MediaDefender, a company based in Santa Monica, California. Few specifics are known about the project, and MediaDefender did not return several phone calls seeking comment. The New York attorney general's office will not speak on the record about it. But according to the e-mails, MediaDefender planned to unleash a peer-to-peer crawler to search unspecified file-sharing networks for child-porn videos and images based on keywords -- such as "young," "kids" and "taboo" -- provided by the AG's office. Once suspected image files were found, the software would collect the IP address of the machines trading those files and filter for any addresses based in New York. The data MediaDefender collected would then be sent automatically to the AG's office, where investigators would analyze and investigate it, using a MediaDefender application to visit the IP addresses and download the suspect files. It's unclear whether MediaDefender planned to download the suspected-child porn itself, or leave that to the AG's investigators. Jeffrey Lerner, spokesman for the New York AG's office, refused to comment on the record about whether MediaDefender was downloading child porn, due to "an ongoing investigation." If the company knowingly downloaded child porn, it could run afoul of federal law, notwithstanding any arrangement it made with state authorities, legal experts say. Either way, several defense attorneys expressed surprise that a law enforcement agency would outsource any evidence collection to a private company. "It is bizarre," says Martin Pinales, former president of the National Association of Criminal Defense Lawyers. "What they're doing is saying, 'We're going to make you a bounty hunter. We're going to pay you to go collect evidence so that in the future we can prosecute somebody.' But (MediaDefender doesn't) have the training of law enforcement." Jeffrey Douglas, a criminal defense attorney in Santa Monica, California, finds other aspects of the MediaDefender law enforcement partnership disturbing. A private company that's under contract to collect information for law enforcement investigators has a financial incentive to produce results, he says. "At the end of the contract, if they haven't made 'x' number of cases, are they going to lose their contract?" he asks. "The company knows there are certain expectations that they're going to accomplish, or they're not going to get another contract." He also expressed concern about what could be described as a fishing expedition to net as many suspects as possible using less-than-accurate tools. The e-mails between MediaDefender and the AG's office, for example, discuss sending the AG 1 gigabyte of "media data" daily, along with "a couple thousand New York IPs that our geo IP database identified using our software." An initial test MediaDefender conducted for the AG's office produced "a lot of false positives," according to one of the exposed e-mails. "No software can determine whether a person (in a picture) is 17 or 18," Douglas says, so there are bound to be a lot of innocent IP addresses collected by MediaDefender and sent to the AG, before further investigation weeds out innocent suspects from actual lawbreakers. San Francisco public defender Adachi says the relationship also conceivably gives MediaDefender the power to decide whom to collect evidence against and whom to let go. "Say I ... find a web site that's run by my sister-in-law and decide that, 'Geez, I'm not going to turn that over,'" Adachi says. "There's no sworn duty by the private company (collecting evidence for law enforcement) to prosecute people in a fair, evenhanded manner." On top of all these concerns is the issue of data security and the integrity of evidence against manipulation by intruders -- either inside or outside the company -- particularly in light of the hack of MediaDefender's internal e-mail. Of course, evidence on a law enforcement computer is at the same risk of being accessed and altered, but the e-mail breach at MediaDefender makes the danger all the more glaring. "It is extremely difficult to protect the material under the best of circumstances," Douglas says. "The more computers it passes through and separate control centers that it passes through, the less likely it is that the integrity of the material will be maintained." In the phone call between MediaDefender and the AG's office, an AG investigator tells MediaDefender that the "intelligence information" MediaDefender is sending them needs to be able to stand up in court, and that the AG needs to know that there's no chance that the data coming from MediaDefender was compromised, edited or modified. Then there's the question of MediaDefender's own trustworthiness. Legal experts says the biggest risk for prosecutors in using a private company like MediaDefender to aid in catching child pornographers is that the company's stock-in-trade is deception: It specializes in introducing decoy "pirated" content onto file-sharing networks. A blogger even discovered in July that the company was secretly operating a video-download site called MiiVi -- apparently as another way of injecting decoy files and tracking downloaders. The hacked e-mails show the company tried unsuccessfully to hide its connection with the site, and even relaunched it under another name after it was exposed. Mark Rasch, a former Justice Department cybercrime lawyer and current managing director of technology for FTI Consulting, says if he were defending a child-porn suspect against evidence produced by a law enforcement agency that worked with MediaDefender, he would raise an obvious question. "How do we know that MediaDefender didn't put these files on the computer first?" he says. http://www.wired.com/politics/online...efender_police  Leaked E-Mails of Anti-Piracy Firm Raise Ethical Questions All Around It is a nightmare scenario for any company. Your firm's dirty tricks are aired for world to see when months of your company’s private e-mails are posted to the Internet. That's exactly what happened to MediaDefender who suffered a very public humiliation earlier this month when a hacker(s) broke into a MediaDefender employee's GMail account and posted nine months of company e-mails outlining the firm's nasty and deceitful anti-piracy practices. A group calling itself MediaDefender-Defenders claimed responsibility for swiping the e-mails and making them publicly available. "By releasing these e-mails we hope to secure the privacy and personal integrity of all peer-to-peer users," MediaDefender-Defenders said. The group first made the e-mails available as a digital download on peer-to-peer networks. Now the e-mails are available on multiple Web sites in an easy-to-read HTML format. Who's the Bad Guy? I'm having a hard time choosing who to side with. Hacking someone's e-mail account is bad enough. But MediaDefender-Defenders took it one step further releasing 6000 messages of a private company's e-mail to the Internet. However, the more I learn of MediaDefender and its business practices the less sympathy I have for it. MediaDefender business is to protect unauthorized downloads of content owned by record companies and Hollywood film studios. It protects copyrighted content from being illegally swapped online by intentionally seeding peer-to-peer networks with bogus decoy files designed to frustrate illegal file swappers. According to e-mails leaked to the Internet MediaDefender even went so far as to create the Web site WiiVii.com that would pose as a pirate site that offered downloads of copyrighted movies and music but would actually track users who accessed it, then report their IP addresses back to MediaDefender. Either way you slice it, both MediaDefender and its nemesis MediaDefender-Defenders are up to no good. What Comes Around Goes Around Despite its righteous rhetoric, MediaDefender-Defenders aren't the most righteous guys around. Sure, it fought the good fight to "secure the privacy and personal integrity of all peer-to-peer users" as it states. But I'm hesitant to put MediaDefender-Defenders on a vigilante pedestal. Right now MediaDefender-Defenders seems like a creepy version of Charles Bronson's thuggish vigilante character in Hollywood movie Death Wish. The difference is MediaDefender hadn't broken any laws that I'm aware of. If MediaDefender-Defenders is supposed to be celebrated than what for? Is it really that it secured the “privacy and personal integrity” of people who use peer-to-peer networks to rip off Hollywood and the music industry? I'm even more disappointed with MediaDefender. MediaDefender's tactics are very shady. The company's Website has no qualms in referring to its "practical, proven methods to thwart Internet piracy." Practical and proven perhaps, but they are hardly ethical. The MediaDefender e-mails even discussed the possibility of infecting the computers of P2P users with crap-ware that would turn unsuspecting users PCs into zombies to upload decoy files to file-sharing networks. Cold War Gets Frigid Does neither side have concern for online integrity? So who wins in the end? P2P users are elated with MediaDefender-Defenders' actions. I can only imagine MediaDefender is only committed now to dreaming up new more dastardly ways to hurt file swappers. Neither side has much concern for its means to an end. http://blogs.pcworld.com/staffblog/archives/005486.html  Feist Commercial Airs, Sales Soar NeutralMilk If you've watched any show at any time during the past couple of weeks, then you've definitely seen Apple's iPod Nano commercial featuring Feist's "1 2 3 4." Talk about "ad" nauseum! Anyhow, ever since every person I know has asked me, "Hey, who is that?" and "What is that song?," the song (and her album, The Reminder) have been firing up the iTunes charts. Currently, "1 2 3 4" is #4 on the singles chart and The Reminder is #7 on the album ranks. If you live in a hole, here's the spot. Here's the entire video for the song. http://www.shoutmouth.com/index.php/...%2C_Sales_Soar Worked for me. I saw it and acquired it, too – Jack.  Shareholders Approve Clear Channel Buyout AP Clear Channel Communications Inc. shareholders approved on Tuesday a $19.5 billion buyout of the nation's biggest radio station operator, more than 10 months after the deal was proposed. The offer from a private equity group led by Thomas H. Lee Partners LP and Bain Capital Partners LLC was first announced in November but was sweetened several times after some large shareholders signaled they would oppose earlier offers. The latest offer was $39.20 per share in cash or stock. Current shareholders could end up with as much as 30% of the new, privately held company. "We are pleased with the outcome of today's vote," CEO Mark Mays said in a statement. "We look forward to completing this transaction with T.H. Lee and Bain as quickly as possible." Of the shares voted, about 98% were in favor of the buyout of the San Antonio-based company in a preliminary tabulation, Clear Channel said. The company said more than 73% of the total shares outstanding and entitled to vote at the meeting were in favor the deal. Two-thirds of shareholders were needed to approve the buyout, and previous offers of $37.60 and $39 per share were deemed too low by some and weren't expected to pass. "It appears that all the stars have aligned," Stanford Group analyst Frederick Moran said before the vote. "We also think that the credit crunch and the shaky stock market environment over the summer causes more comfort on behalf of shareholders to approve the deal." Clear Channel, which also has an interest in the outdoor billboard business, has been divesting some of its broadcasting operation. Its 56 television stations were sold in April, and sales deals have been reached on 402 of its radio stations. It plans to keep about 675 stations, mostly in larger metro areas. The offer to allow shareholders to keep part of the newly private company is an unusual concession because private equity buyers pay a premium to get total control and fewer regulatory requirements than those required of public companies. The company said Tuesday preliminary results showed shareholders of about 67.3 million shares of Clear Channel stock chose to receive shares in the new company. That is more than twice the 30.6 million shares -- or 30% of the outstanding capital stock of the new company -- that were allowed in the buyout agreement. Because of that, shareholders will get shares in the new company on a prorated basis, the company said. The deal is expected to close before the end of the year. The buyers will also assume $8 billion in debt. Clear Channel shares rose 22 cents to $36.98 in afternoon trading Tuesday. http://www.hollywoodreporter.com/hr/...fa5694bd22814b  In Love With Pop, Uneasy With the World A. O. Scott IT was the last day of summer, but on the boardwalk here it seemed more like a perfect morning in early July: the Atlantic Ocean sparkled under a cloudless sky; the humid air was soothed by a soft, salty breeze. I looked down the empty beach, past the souvenir shops and snack bars with their fresh paint and new green awnings, toward the proud Victorian hulk of the old Casino, and felt that I had walked into a Bruce Springsteen song. (Oh, I don’t know. Maybe “Fourth of July, Asbury Park.” Or is that too obvious?) The feeling, no less potent for being self-induced, had been with me all morning. Bright and early, me and my girl — my wife of nearly two decades, that is — had let the screen door slam, dropped off the kids at school and set out on the open road, blowing through the E-ZPass lanes on the Garden State Parkway in our Volvo station wagon. We had an advance copy of Mr. Springsteen’s new album, “Magic,” in the CD slot, and most of his back catalog in reserve on the iPod. And now we were driving down Kingsley, figuring we’d get a latte. One more chance to make it real. Tramps like us, baby! Our purpose was not to fantasize but rather to observe the E Street Band in rehearsal, and then to hear what the man himself had to say about the new record, the coming tour and whatever else was on his mind. “Magic” is, musically, one of the most upbeat, accessible records he has made, even as its themes and stories make it one of his most political. Once again he is hitting the road as a presidential election heats up. “I like coming out on those years,” he would tell me later, when we sat down to talk in a backstage dressing room after the rehearsal. “Whatever small little bit we can do, that’s a good time to do it.” At an age when most rock ’n’ rollers, if they’re still alive, have become either tributes to or parodies of their earlier selves, Mr. Springsteen seems to have settled into an enviable groove, with new musical forms to explore and an existing body of work that never seems to get old, with plenty to say and an audience that hangs on his every word. In which — as if it weren’t already obvious — I include myself. I’ve been listening to Bruce Springsteen for a long time, but I can’t pretend that he provided the soundtrack for my youth. I spent my teenage years in the thrall of punk rock and its various aftermaths and came to Springsteen late, past the stage of life when his great anthems of romance, rebellion and escape might have had their most direct impact. As a result, I associate his work with the sorrows and satisfactions of adulthood; it’s music to grow up to, not out of. Mr. Springsteen’s best songs, it seems to me, are about compromise and stoicism; disappointment and faith; work, patience and resignation. They are also, frequently — even the ones he wrote when he was still in his 20s — about nostalgia, about the desire to recapture those fleeting moments of intensity and possibility we associate with being young. Moments that tend, not coincidentally, to crystallize within a certain kind of popular song. A song, let’s say, like “Girls in Their Summer Clothes,” which arrives smack in the middle of “Magic” and which the E Street Band was in the middle of playing when my wife and I tiptoed through the doors of the Asbury Park Convention Hall. It was a little after 10; the band was about an hour into its morning rehearsal, preparing for a tour of North America and Europe that kicks off on Tuesday in Hartford. The Convention Hall is a battered, pocket-size arena where, as a teenager, Mr. Springsteen saw bands like the Who and the Doors. This morning it was filled with a shimmery, summery sound, as if we had traveled back 40 years into the mid-’60s sonic landscape of Phil Spector, Brian Wilson and the Byrds. Steve van Zandt was strumming a 12-string guitar, and the vocal harmonies, the chiming keyboards, Clarence Clemons’s saxophone and Soozie Tyrell’s violin combined to produce a lush orchestral cushion for Mr. Springsteen’s voice, which swooned through a lyric as unabashedly romantic as the song’s title. “I wanted one thing on the record that was the perfect pop universe,” Mr. Springsteen said, once the band had wandered off and he had finished an early lunch of granola with fresh fruit and soy milk. It was two days before his 58th birthday, and he looked trimmer and tanner than he had the last time I’d seen him, which was on the JumboTron video screen at Giants Stadium a few years back. “You know, that day when it’s all right there; it’s the world that only exists in pop songs, and once in a while you stumble on it.” Not that “Girls in Their Summer Clothes” is untouched by melancholy. Its narrator, after all, stands and watches as the girls of the title “pass me by.” “It’s the longing, the unrequited longing for that perfect world,” Mr. Springsteen continued. “Pop is funny. It’s a tease. It’s an important one, but it’s a tease, and therein resides its beauty and its joke.” And much of “Magic,” on first hearing, seems to unfold in a similar spirit. There is a brightness of sound and a lightness of touch that are not quite like anything else Mr. Springsteen has done recently. In the past five years he has released four albums of original material, a zigzag through new and familiar styles and idioms. “The Rising” (2002) brought the E Street Band back into the studio after a long hiatus (their sound updated by the producer Brendan O’Brien) and answered the trauma of 9/11 with the defiant, redemptive roar of solid, down-the-middle rock. With “Devils and Dust” (2005) Mr. Springsteen picked up the thread of Western stories and acoustic ballads that stretched back through other non-E Street projects like “The Ghost of Tom Joad” and “Nebraska” (as well as some parts of “The River”). “The Seeger Sessions,” released last year, was an old-time old-lefty hootenanny, with a big, unruly jug band rollicking through spirituals, union songs and Dust Bowl ballads. All of those discs were infused with Mr. Springsteen’s bedrock populism, but none was quite what you would call a pop record. Pop, though, is the term he and his band mates use, again and again, to describe “Magic.” Mr. Van Zandt, who has been playing and arguing about music with Mr. Springsteen for 40 years (scholars cite Nov. 3, 1967, as the date of their first meeting), noted that in the past Mr. Springsteen’s more tuneful, playful compositions tended not to make it onto albums. “It was nice on this one to start to be a little bit more inclusive,” he said in a telephone interview a few days after my visit to Asbury Park, “with a little bit more of the poppier side of things, without losing any of the integrity, or any of the high standards. That was a nice surprise, a nice change of pace to include those things and integrate them into the album, rather than having them be fun to record and then cast them aside.” For his part, Mr. Sprinsteen said that in writing the songs for “Magic,” he had experienced “a reinfatuation with pop music.” “I went back to some forms that I either hadn’t used previously or hadn’t used a lot, which was actual pop productions,” he said. “I wrote a lot of hooks. That was just the way that the songs started to write themselves, I think because I felt free enough that I wasn’t afraid of the pop music. In the past I wanted to make sure that my music was tough enough for the stories I was going to tell.” The paradox of “Magic” may be that some of its stories are among the toughest he has told. The album is sometimes a tease but rarely a joke. The title track, for instance, comes across as a seductive bit of carnival patter, something you might have heard on the Asbury Park boardwalk in the old days. A magician, his voice whispery and insinuating in a minor key, lures you in with descriptions of his tricks that grow more sinister with each verse. (“I’ve got a shiny saw blade/All I need’s a volunteer.”) “Trust none of what you hear/And less of what you see,” he warns. And the song’s refrain — “This is what will be” — grows more chilling as you absorb the rest of the album’s nuances and shadows. You can always trust what you hear on a Bruce Springsteen record (irony, he notes, is not something he’s known for), but in this case it pays to listen closely, to make note of the darkness, so to speak, that hovers at the edge of the shiny hooks and harmonies. “I took these forms and this classic pop language and I threaded it through with uneasiness,” Mr. Springsteen said. And while the songs on “Magic” characteristically avoid explicit topical references, there is no mistaking that the source of the unease is, to a great extent, political. The title track, Mr. Springsteen explained, is about the manufacture of illusion, about the Bush administration’s stated commitment to creating its own reality. “This is a record about self-subversion,” he told me, about the way the country has sabotaged and corrupted its ideals and traditions. And in its own way the album itself is deliberately self-subverting, troubling its smooth, pleasing surfaces with the blunt acknowledgment of some rough, unpleasant facts. “Magic” picks up where “The Rising” left off and takes stock of what has happened in this country since Sept. 11. Then, the collective experiences of grief and terror were up front. Now those same emotions lurk just below the surface, which means that the catharsis of rock ’n’ roll uplift is harder to come by. The key words of “The Rising” were hope, love, strength, faith, and they were grounded in a collective experience of mourning. There is more loneliness in “Magic,” and, notwithstanding the relaxed pop mood, a lot less optimism. The stories told in songs like “Gypsy Biker” and “The Devil’s Arcade” are vignettes of private loss suffered by the lovers and friends of soldiers whose lives were shattered or ended in Iraq. “The record is a tallying of cost and of loss,” Mr. Springsteen said. “That’s the burden of adulthood, period. But that’s the burden of adulthood in these times, squared.” In conversation, Mr. Springsteen has a lot to say about what has happened in America over the last six years: “Disheartening and heartbreaking. Not to mention enraging” is how he sums it up. But his most direct and powerful statement comes, as you might expect, onstage. It is not anything he says or sings, but rather a piece of musical dramaturgy, the apparently simple, technical matter of shifting from one song to the next. On the Convention Hall stage, the band handled the new material as deftly as the chestnuts — after 35 years together, communication is pretty much effortless — pausing to work out an occasional kink or adjust the sound mix. But they must have gone over the segue from “The Rising” to their next number at least a half-dozen times. “You’ve got to let that chord sustain. Everybody!” Mr. Springsteen urged. “It can’t die down.” The guitarists had the extra challenge of keeping the sound going while changing instruments, a series of baton-relay sprints for the crew whose job was to assist with the switch, until a dissonant organ ring came in to signal a change of key and the thunderous opening of “Last to Die.” It’s not much of an exaggeration to say that Mr. Springsteen’s take on the post-9/11 history of the United States can be measured in the space between the choruses of those two songs. The audience is hurled from a rousing exhortation (“Come on up to the rising”) to a grim, familiar question: “Who’ll be the last to die for a mistake?” “That’s why we had to get that very right today,” he said later. “You saw us working on it. That thing has to come down like the world’s falling on you, that first chord. It’s got to screech at the end of ‘The Rising,’ and then it’s got to crack, rumble. The whole night is going to turn on that segue. That’s what we’re up there for right now, that 30 seconds.” But the night does not end there. Onstage, “Last to Die” is followed, as it is on the album, by a song called “Long Walk Home.” In the first verse, the speaker travels to some familiar hometown spots and experiences an alienation made especially haunting by the language in which he describes it: “I looked into their faces/They were all rank strangers to me.” That curious, archaic turn of phrase — rank strangers — evokes an eerie old mountain lament of the same title, recorded by the Stanley Brothers. “In that particular song a guy comes back to his town and recognizes nothing and is recognized by nothing,” Mr. Springsteen said. “The singer in ‘Long Walk Home,’ that’s his experience. His world has changed. The things that he thought he knew, the people who he thought he knew, whose ideals he had something in common with, are like strangers. The world that he knew feels totally alien. I think that’s what’s happened in this country in the past six years.” And so the song’s images of a vanished small town life (“The diner was shuttered and boarded/With a sign that just said ‘gone’ “) turn into metaphors, the last of which is delivered with the clarity and force that has distinguished Mr. Springsteen’s best writing: My father said “Son, we’re lucky in this town It’s a beautiful place to be born. It just wraps its arms around you Nobody crowds you, nobody goes it alone. You know that flag flying over the courthouse Means certain things are set in stone Who we are, and what we’ll do And what we won’t” It’s gonna be a long walk home. “That’s the end of the story we’re telling on a nightly basis,” Mr. Springsteen said. “Because that’s the way it’s supposed to be. And that’s not the way it is right now.” http://www.nytimes.com/2007/09/30/ar...30scot.html?hp  Mistrial Declared in Spector Murder Case Randal C. Archibold The murder trial of the music producer Phil Spector ended on Wednesday in a mistrial after the jury, leaning heavily to convict him, could not reach a unanimous verdict. The Los Angeles County district attorney’s office said it planned to retry the case. Mr. Spector, 67, charged with second-degree murder in the killing of Lana Clarkson in his home in 2003, stared blankly forward as Judge Larry Paul Fidler of Superior Court ended the proceedings after the jury foreman had reported a 10-2 deadlock. The impasse occurred after an earlier deadlock of 7-5 that jurors later said also tilted toward conviction. That impasse led the judge to take the unusual step of sending the jurors back to deliberate with new instructions, angering the defense. Three jurors, speaking to reporters afterward, said the two holdouts gave credence to a defense assertion that the death of Ms. Clarkson, 40, a struggling actress, might have been a suicide rather than a murder. The three jurors said the jury had also been troubled by the lack of large amounts of blood on Mr. Spector and the poor English of a witness, Mr. Spector’s driver, who said he had heard Mr. Spector say, “I think I killed somebody.” Judge Fidler retained orders for silence, preventing lawyers and others in the case from speaking publicly. He set a hearing for Oct. 3. Mr. Spector, the mastermind behind hits like “Da Doo Ron Ron” and “Be My Baby,” escorted by his wife, lawyers and bodyguards, left through an adjacent courtroom without saying a word, free on bail. He joins Michael Jackson, O. J. Simpson and Robert Blake among celebrities whom Southern California prosecutors have failed to convict in high-profile criminal cases. Alan Jackson, a lead prosecutor in the case, sat glumly in a courthouse hallway as a spokeswoman for the district attorney’s office reiterated the judge’s order barring him from speaking. “We’re disappointed the jury was unable to reach a verdict in this case, and we will immediately begin preparations for a retrial,” the spokeswoman, Sandi Gibbons, said later at a news conference. She declined to comment further. Mr. Spector was accused of killing Ms. Clarkson, whom he had met at a nightclub hours before she was found dead from a gunshot wound to her mouth in the foyer of Mr. Spector’s house in a Los Angeles suburb. Prosecutors said Mr. Spector shot Ms. Clarkson in an alcohol-fueled rage after she had resisted his advances. They presented testimony from five other women who described similar threats by Mr. Spector. The prosectors failed to present forensic evidence that placed the gun in Mr. Spector’s hand and relied instead on a spray of blood on his clothes. The defense, portraying Ms. Clarkson as despondent over her career and finances, presented experts and scientific evidence to buttress their assertion that she had shot herself, intentionally or not. They said the pattern of blood indicated that Mr. Spector was too far away to have pulled the trigger. One juror who declined to give his name said he voted to convict, because given “the totality of the evidence, what was the most plausible reason she could have died.” Another juror suggested that a psychological profile of Ms. Clarkson by prosecutors might have indicated whether she had been suicidal. The jury foreman said some jurors were troubled with the statement from Mr. Spector’s driver, Adriano De Souza, a Brazilian immigrant, who admitted having problems with English. The case was remarkable for the virtual second chance the judge gave prosecutors after the jury reported a deadlock on Sept. 10, having deliberated for seven days. Judge Fidler removed an instruction that they considered confusing, ruling that it misstated the law on second-degree murder, and read them new instructions that, to the fury of the defense, included a few situations in which Mr. Spector could have killed Ms. Clarkson. Jean Rosenbluth, a former federal prosecutor and University of Southern California law professor who monitored the case, said there was little more prosecutors could have done. Professor Rosenbluth said she doubted that jurors were impressed by Mr. Spector’s celebrity, as he was a behind-the-scenes figure and his fame had faded from the 1960s and early ’70s. She suggested that the defense had succeeded in creating doubt about the prosecution case with expert witnesses and said prosecutors had erred in not pushing hard for the jury to consider a lesser charge of involuntary manslaughter. “A lot people may say this is just like the other cases, but he was not acquitted,” Professor Rosenbluth said. “He was almost convicted. I think this says much more about money than celebrity and the resources money can buy when you are on trial.” It was the first televised Los Angeles celebrity trial since the Simpson case in 1995, but it did not attract the following or frenzied coverage of that or other cases. Mr. Spector has not been behind a hit in decades. He is best known in music circles for his Wall of Sound technique, marrying lush orchestral arrangements to guitars and other staples of pop music. A member of the Rock and Roll Hall of Fame, he collaborated with top rock stars, including the Beatles. http://www.nytimes.com/2007/09/27/us/27spector.html  Kids Advocate: Show Not a 'Nation' of Laws Ray Richmond Well, "Kid Nation" premiered on schedule Wednesday night despite the vehement protestations of TV critics and child advocates, and the republic still stands. CBS no doubt got an audience bump from the summerlong controversy that shrouded the reality hour that finds kids age 8-15 recruited to create their own pioneer society from a barren ghost town in New Mexico. But starting now, it's on its own. The ratings for the opener were solid, if unspectacular, with "Nation" winning the 8 p.m. hour with adults 18-49 and kids 2-11 with a 3.0 rating and 9 share, according to Nielsen Media Research overnight numbers. Yet despite the seeming tameness of the debut, some who watched it are hardly appeased. And it should surprise no one that those ranks include Paul Petersen, the former child actor who played Jeff Stone on "The Donna Reed Show" in the early 1960s and who has spent most of his adult life crusading to assist onetime child stars who have fallen on tough times. The crown jewel of his efforts is A Minor Consideration, a nonprofit that Petersen formed in 1991 to provide emotional and financial assistance for "young performers past, present and future." Petersen has not been shy in sharing his feelings about "Kid Nation." And watching it on Wednesday merely served to fuel his rage over a show that he calls "despicable," "shameful" and "a celebration of exploitation and abuse." It is Petersen's contention that no matter the claims of CBS and creator-executive producer Tom Forman, "Kid Nation" is hardly representative of "reality," taking advantage of the less stringent child labor laws in New Mexico to hire child "performers" who were then "worked 17 hours a day for 40 straight days and paid the mighty fee of $5,000." "Watching the show on Wednesday only reinforced my disgust and disdain," he says. "It could have been a worthwhile project if the production company had treated these children like the performers they were and allowed them to really do what we were told they were doing -- which is practice nation-building in a controlled setting." What perhaps rankles Petersen most is how the production was mounted in New Mexico to avoid the more rigorous California child labor restrictions, a fact the producers don't deny. "You have kids who were taken out of school for six weeks and weren't even provided with a tutor on-set," he charges. "Is that legal? Of course not. Yet somehow, they were able to get it waived. It's also standard industry practice that a parent has to be within sight and hearing of their child at all times during a shoot. It's the law in California. But they didn't bother with that. "And then I saw on the first show how they're giving away a $20,000 award every week, which in essence turns children who aren't professional into rampant mercenaries. The level these people have stooped to was staggering," he says. In his and CBS' defense, Forman has contended that the furor is entirely media-created and without merit and that all applicable laws that apply in New Mexico to working kids were adhered to. The network has stood behind the creator. Petersen promises to keep sounding this particular alarm on behalf of kids "whose parents sold them out." And he's further perturbed by preparations being made for "Kid Nation 2" that's set to go before the cameras by year's end. "We've got to stop this," he warns, "before more kids are victimized." http://www.hollywoodreporter.com/hr/...50343dfab906ac  US Online Video Popularity Keeps Climbing Juan Carlos Perez People in the U.S. have steadily increased the amount of time they spend watching videos online, as Google’s YouTube remains by far their preferred video site, according to a study. In July, almost 75 percent of U.S. Internet users watched videos online, up from 71.4 percent in March, according to comScore Networks. The monthly time spent watching videos went up to an average of 181 minutes per viewer in July from 145 minutes per viewer in March, according to comScore. People in the U.S. are also watching more video clips. In July, the average user watched 68 clips, up from 55 clips in March. Overall, almost 134 million U.S. Internet users watched a little over 9 billion video clips in July, up from 126.6 million people and a little over 7 billion clips in March. In July, Google ranked as the top provider of video clips, serving up 27 percent of the total — almost 2.5 billion clips — most of them via YouTube, comScore said. Yahoo nabbed a distant second place, serving up 4.3 percent of the clips. Fox Interactive Media, the News Corp. Internet division that includes MySpace.com, came in third with 3.3 percent. Viacom (3.1 percent) and Disney (2 percent) rounded out the top five. Google also ranked first in July in unique video viewers with almost 68 million, followed by Fox Interactive (35.8 million), Yahoo (35.3 million), Time Warner Inc. (26.6 million) and Viacom (22.6 million), comScore said. After years of unfulfilled promises, online video has taken off in a big way in the past year and a half, rapidly accelerating its momentum across a wide variety of sites. The revolution is widely credited to YouTube and its video-sharing format, but now companies are prominently featuring videos in portals, news sites, blogs, social networks, online stores and film and television industry sites. YouTube’s popularity can be attributed to several factors, including its ease of use — both for viewers and uploaders —, a strong community of millions of people who submit, view and share personal videos and an abundance of commercial clips from movies and television. It is this last component of its popularity — the commercial clips — that have put YouTube at the center of the Internet industry’s struggle with video copyright protection, because many of those videos are copied and uploaded without their owners’ permission. A landmark legal action is currently under way, as Viacom pursues a copyright-infringement lawsuit against Google over the unauthorized appearance of its clips on YouTube. In addition to copyright, other technical and operational issues are in flux, such as the options for generating revenue from video content, the best ways to use video for online advertising and the different alternatives of delivering the clips to viewers. Another area of interest are video search engines, as well as alternate devices for online video beyond the PC, from small ones like cell phones to large ones like living-room home entertainment centers. For example, currently the Web seems a vehicle primarily for short video clips, as evidenced by comScore’s finding that the average video clip duration in July was 2.7 minutes. http://www.macworld.com/news/2007/09/13/video/  Google Video Blasted Over Piracy Claims Clement James Copyright watchdog files report alleging violations on Google Video. A US-based copyright watchdog has sunk its teeth into Google by sending a report alleging copyright violations on Google Video to members of Congress. The National Legal and Policy Center (NLPC) researched the extent of copyrighted material being hosted on Google Video earlier this summer and released a Top 50 list of apparently copyrighted movies. But, in the latest spot-check of Google Video conducted from 10 to 18 September, the NLPC claims to have discovered 300 additional instances of apparently copyrighted films, including over 60 movies released this year. Several popular summer releases including Shrek the Third, Oceans Thirteen, The Bourne Ultimatum and Knocked Up were easily found on the video sharing site. The 300 apparently pirated films, along with many other copyrighted works, received more than 22 million views in the past year on Google Video, according to the NLPC. This is despite Google's claim that it respects the rights of copyright holders, and provides tools to help identify and remove copyrighted intellectual property from the site. "While Google faces numerous legal challenges related to the posting of copyrighted content on its video sharing websites, there is a growing chorus who believe that evidence of Google's seemingly indifferent attitude towards internet video piracy has resulted in a legitimisation or 'mainstreaming' of video piracy which will have broad and damaging implications for all intellectual property owners," said the letter to Congress signed by NLPC chairman Ken Boehm. "Since [we originally identified evidence of copyright infringement] the number of apparently copyrighted movies being hosted by Google Video appears to have grown substantially. "During the past two weeks, the NLPC again conducted random spot-checks of Google Video in an attempt to identify clearly copyrighted works that continue to be hosted on the site. "What we found raises serious questions about Google's oft-stated commitment to prevent apparently copyrighted content from being hosted on its video sharing site." The NLPC added that Google has been promising video filtering technology to screen for copyrighted content since at least the Autumn of 2006. However, it appears that Google still had not implemented the promised technology either for its YouTube or Google Video sites. The NLPC said that internet piracy theft cost nearly $2.3bn in lost revenue to the US film industry. http://www.itnews.com.au/News/62054,...cy-claims.aspx  Reconstructing Iraq's Film Industry: Antonia Bird and Human Film in Jordan Nicol Wistreich When the United Nations imposed sanctions on Iraq in August 1990, the cinema industry went into steep decline. New equipment, film stock, and chemicals for film laboratories were forbidden under import rules and no new feature films were made until Mohamed Al Daradji's Oscar nominee Ahlaam in 2004. As producers Human Film prepare to make their second feature in the region, the British production company has traveled to Jordon to run a series of workshops to help train up the next generation of filmmakers in the region. Supported by the Royal Film Commission of Jordan, the workshops will teach 23 filmmakers from both Iraq and Jordan the basics of directing, screenwriting, camera/technical, production and post-production. Next week the students will produce a film on 16mm or 35mm. The eight tutors include Antonia Bird (Priest, Face), and experts from the UK, Portugal, The Netherlands, Iraq and Canada. One of the key stipulations is that each country provides at least two female trainees. Richard Lawson of Kodak Dubai has supplied all the filmstock while The Gate in Lebanon is helping with processing. "Each group consists of 5 students and the Jordanian student acts as the translator for the teacher - this has really made groups reliant on each other and already strong bonds and friendships have been created." Human Film's Isabelle Stead told Netribution. "It's amazing how much they are taking in". Human Film is a remarkable company focused human resilience at the heart of tragedy, and is made up of Iraqi-born Mohamed, producer/writer Isabelle and Daniel Evans. The Leeds-based outfit is testament to film and art's ability to cross boundaries, right down to the make-up of the company. Mohammed told me in an interview, soon to be published here: "To be honest we don't put religion in there. But I am Muslim. Danny, he is Christian. Isabelle is half-Jewish. And we never think about religion, at the end of the day, what is religion but about human beings learning to live in peace? What Islam , Christian and Jewish religions say is the same. The ten commandments: don't kill, don't kill, don't steal, don't lie, don't talk about people - religion is about human beings. All the religions are the same. So when my friend Danny goes on Sunday to the church and prays to God and when I go on Friday to the Mosque, and on Saturday she goes to the synagogue it's the same thing... Religion is something private, it's about you and your God." The two weeks workshop came about after Mohamed did a Sundance workshop in 2006 with the Royal Film Commission of Jordan and spoke with them exploring the possibility of a workshop. Isabelle then went to shoot a short film in Jordan and the company decided this would be a good way for Iraqis and Jordanians to work together. Human Film's work Iraq, alongside it's sister company Al Rafidain is perhaps the most notable since Oliver Reed's appearance in The Great Question, which documented the 1920 revolt against British rule. Reed played the part of an arrogant British officer murdered by the mob in a nationwide revolt now regarded as one of the most important steps towards eventual Iraqi independence. More information on the history of Iraqi cinemacan be found in an interesting Guardian article. http://www.netribution.co.uk/2/content/view/1284/182/  Festival Shows Movies on Web at Same Time Owen Gibson The UK's largest independent film festival will this week become the first to simultaneously show its movies via the web, claiming the initiative could help establish a new revenue model for independent filmmakers. The Raindance Film Festival in London has done a deal with broadband provider Tiscali to make six of its films available to all via the web at the same time as they premiere in London cinemas. They include the feature-length documentary Flames in the Looking Glass, tracking the lives of three Indian transgenders living with Aids, the Scottish road trip The Inheritance, and a film about hip hop in Brighton called South Coast. All the films will be made available from 9pm on the day they are first shown. On five nights, a selection of short films from aspiring film makers will also be aired. The festival's website will also host content from the previous night's screenings. Alongside the screenings, Raindance also hosts a series of events. At one, aspiring film makers will pitch ideas to a panel of film grandees, including Nik Powell, Sally Caplan and Ewan McGregor. Online video consumption has exploded as high speed broadband connections have proliferated. Elliot Grove, who founded Raindance, said online distribution offered film makers new ways to fund their films. Online distribution would give aspiring film makers an opportunity to find an audience without having to go through the traditional Hollywood system. The festival runs from September 26 to October 7. http://www.guardian.co.uk/uk_news/st...175555,00.html  'Look' Spy-Cam Footage Looks Real, But Isn't Martin A. Grove Spy-cam stars: We may not realize it, but we're all movie stars thanks to the roughly 30 million surveillance cameras throughout the U.S. that capture each of us on film about 200 times daily. That's the premise of writer-director Adam Rifkin's "Look," a fascinating feature that appears to be actual spy-cam footage strung together, but is really a fiction film spring-boarding off the idea that our comings and goings these days are anything but private. Produced by Brad Wyman and Barry Schuler, "Look" won the Grand Jury Prize this summer at the CineVegas Film Festival and was recently acquired by the new distribution company Liberated Artists, which is releasing it Dec. 14 in New York and L.A. It was executive produced by Donald Kushner and Richard Bishop. None of "Look's" ensemble cast members are recognizable actors because that would have instantly shattered the illusion that what we're looking at are real people who are being surreptitiously filmed. Rifkin is best known as a screenwriter with such credits as "Underdog," "Mousehunt" and "Small Soldiers." On the directing front, his credits include co-directing and starring in the mock documentary "Welcome to Hollywood," which featured cameos by John Travolta, Sandra Bullock and Will Smith. After an early look at "Look," which I've been telling friends not to miss, I was happy to be able to focus on the making of the film with Rifkin. "We all, I think, are aware of it, but I don't think we think about it enough," Rifkin said about the cameras that record so much of what we do in public today. "I don't think most people are aware of it to the extent that it really permeates the culture. When I started thinking about the idea to make the movie, I started looking around everywhere I went and there were just cameras everywhere. Most of the time (when) you're sitting in a restaurant, you're shopping at a grocery store, you're changing in a changing room, you're in a public bathroom, you're just not thinking about it -- but they're everywhere. And interestingly the number of cameras is growing exponentially." An indication of just how quickly the camera population is increasing is seen, according to Rifkin, in that "From the time we finished the movie to now those numbers have jumped even higher. We had to change the opening cards of our film before the film gets released because the original numbers were roughly 26 million surveillance cameras in the United States generating about four billion hours of footage a week and the average American was being captured 170 times a day. We just finished (the movie) this summer and we showed it for the first time to an audience at the CineVegas Film Festival, where we won the Grand Jury Prize, which was so exciting. The new numbers are every day the average American is captured by over 200 cameras and the numbers are just growing and growing (and the total camera population) is nearing 30 million, which is pretty scary -- or good, depending on how you look at it. "I did not want to make a political statement with this movie. I did not want to take a stand and say, 'I think (having) surveillance cameras in every store and on every street corner is a good idea unilaterally or is a bad idea unilaterally.' I just kind of wanted the film to spark the debate because some people are very passionate about one side of that fence and other people are really passionate about the other side of that fence. And, if nothing else, I just think it's interesting for people to be aware of because since we started making the film and people have seen the film everybody says that they're more aware of cameras now than they've ever been and they start looking for them everywhere they go. If you allow it to make you feel so, it can make you feel a little paranoid." When I asked how he'd obtained the surveillance footage used in the movie, Rifkin surprised me by replying, "Well, we created it. The movie is a narrative feature. The concept is that we followed several storylines that are all intersecting, but the movie is shot exclusively from surveillance cameras. But we created all the footage that was shot. It's very much a narrative film where the actors are portraying characters and they're saying lines from a script. We shot all the footage and then we degraded it in post to look as authentic as possible to surveillance footage. "It was very important to us that we hold very, very true to the conceit that this movie is shot from angles that only would actually be surveillance camera angles. So there's no camera in the movie ever that is anywhere where an actual surveillance camera wasn't placed or would be placed. In most instances, where we shot the film we just put our cameras right next to whatever real surveillance camera happened to be there. And if were in a location that didn't happen to have surveillance cameras, we were very careful to only put the cameras where a surveillance camera would actually be." Asked how he came up with the idea of making the film, Rifkin explained, "The original spark of the idea hit me when unbeknownst to me I had been photographed going through a yellow light. I thought it was a yellow light (but the police said it was red). The photograph came back and it was me and it was my car, it was my license plate number and I was in that intersection and I was making a very embarrassing expression because I was singing to the radio at that moment. And then I started thinking about there's a true-life case where a man was photographed at a red light cam and sitting next to him was a woman who was not his wife. And when that letter from the police department came to his home with the photograph of him in the car with another woman, his wife opened the letter. It ruined his marriage and he sued the city and it changed the law so now, I believe, the person in the passenger seat has to be blurred. But all those things started hitting me at the same time. "I started thinking about that story. I started walking through a Target and I was looking around at the cameras on the ceilings and everywhere I went I realized I was being photographed from a different angle. As a filmmaker I started to think, if I were to obtain all these angles and start cutting them together that's coverage. That's like shooting a movie. I mean, granted the scene would be a particularly boring scene of me looking for a super-soaker for my nephew's birthday party, but I thought to myself, 'You know, (it's staggering) if you think about where all these cameras are on any given day and all the different cameras we pass in front of (in places like) grocery stores, banks, hospitals, elevators.'" At that point Rifkin said he, "Started to look into where cameras were and weren't illegal and I learned that in (only) very, very few states is it illegal to put cameras in public bathrooms and public dressing rooms. In most states it's perfectly legal. So that raised my eyebrows, as well. And then I just started to think, 'If in a random city for a random week somebody were able to compile the millions and millions of feet of footage of all the surveillance cameras and if you were to be able to somehow manage to wade through all that footage to the three, four or five most interesting stories that happened that week and could follow them all, I wonder how much they would intersect, I wonder how dramatic they'd be, I wonder how funny they'd be. The cameras are just capturing life as it plays out, but the advantage the camera has that none of us has is that the camera sees all. The camera sees both sides of everybody's persona. "I mean, everybody to a certain degree has a secret life and whether the extent of that secret life is you'll only pick your nose if you're alone in an elevator or that secret life is that you're having an affair on your spouse or that secret life is you are living a completely dual personality from the reality that people know as you, you may think you have this information hidden from all the people that you know, but the camera sees all. And that's kind of what the movie's about for me. At its core, to me it's a movie about the things people do when they think no one is watching." About a year or so ago, he continued, "I said to Brad Wyman, who produced the movie, 'I've got this idea for a movie.' I told him about all the different cameras that exist and what I'd learned looking up some information about it. I said, 'What if we shot an entire movie entirely from the point of view of surveillance cameras?' And he said, 'I love it. Write it immediately. We'll get it made immediately.' So I wrote it really fast. He gave the script to a friend of his, who he's in business with on some other projects, named Barry Schuler. Now Barry Schuler is one of the creators of AOL. They had been looking for things to work on together. Barry read the script and loved it and said, 'I'm in. I want to finance this movie. I get it.' "He comes from the tech world and he's got so many great philosophies on upsetting the apple cart in terms of how to disseminate information and media. He really was one of the architects of creating the Internet as we know it. He just saw this as an opportunity to have a lot of fun with the kind of stuff that just hits him right in his soft spot. So we all rolled up our sleeves and made the movie together. I think it turned out really good. The first audience that ever saw it was (at) CineVegas and it won. That was just in July. We were so thrilled and so excited." As for the challenges of making the movie, he pointed out, "When I first thought about the idea, I thought this was going to be the easiest movie I've ever made. I thought, 'OK, we'll put a couple cameras in a couple corners in some rooms up by the ceiling and we'll have the actors come in and say their lines and we're done. We can go home by lunch every day, is what I thought.' I was so wrong. This was the hardest movie I've ever made. The reason being is that it had to feel 100% real. All my other movies relied so much on movie trickery to be able to fudge -- okay, if a line gets fudged here or if that didn't feel real I know I can compress the timing and I know I can do this and can do that. I couldn't do any of that (in this film). I had to believe that when I'm watching this film that it could be real footage and these could be real people that were actually captured. "So it brought up a whole new form of challenges because where the cameras were set up was kind of out of our control. OK. We're in a 7-Eleven. There has to be one camera there, one camera there, one camera there. We can't mess with that. But how can we tell all these different scenes and tell the story in an interesting and compelling way when we know we can't move the camera and we can't cut in for close-ups. I mean, this is a character drama with no close-ups. That was very scary for me. I had to figure out ways that we could recognize the characters in other ways than seeing a close-up of their face and through working with the actors and with the performances and with the staging within the framework of the static camera angles, how to most interestingly get to know who they were, get to care enough about who they were and do it in some sort of way that's still visually interesting so you don't just tune out." Everyone is familiar, he continued, "with the two minutes of surveillance footage on the news every other day, but to tell an entire narrative from the point of view of surveillance cameras and expect to be able to feel for the characters was a very scary challenge. I was shocked though by something that emerged that I did not expect. You know, movies are all about voyeurism. I mean, you're looking in on other people's lives. But with this movie, you're forced to continually be reminded that you are not living vicariously through the characters, as is the case with most films. "You are a spectator into these people's lives so what it basically forces you to feel like is an accomplice sometimes in a good way and sometimes in a bad way. You're forced to be observing things that you sort of feel like you shouldn't be observing. You're looking at things that people don't know are being captured (on film) and, as a result, it's titillating. But it's also at times shameful because you're seeing things that you know you shouldn't be seeing. And that was kind of a neat thing that emerged that I didn't really expect was going to happen." Real surveillance footage, he explained, "at times is so murky that to see it for two minutes is fine, but to see it for 90 minutes it can give you a headache. So we were very meticulous in creating different looks for different locations to make sure that the film could be watched and digested without giving everybody a headache. The look of every different surveillance camera is authentic to real footage we have researched. But certain locations (look different because) let's say we decided the police station has a higher caliber surveillance system or the mall has a higher caliber surveillance system so the quality of the image might be better whereas the 7-Eleven or the garage or the ATM machine cameras haven't been maintained as well so those cameras are maybe of a lesser quality. And that kind of helped give the film all different locations and all different looks." Casting "Look" required a different process than is typically used in making a movie: "Usually, making any film we're always trying to get the biggest name actors to attach themselves to our material because obviously it ups the value of the film and enables the film to get seen by a wider audience. In this film because the intention was for it to feel real, it had to feel like these could be real surroundings and these could be real people. We made the decision early on that we did not want any actors of note. We did not want to recognize any faces. And wouldn't you know it, when we sent the script out to all the agents and said, 'Give us all your best actors that may be working but aren't known' more known actors that are big actors that we would have in any other instance be thrilled to have in our film, we had to pass on. "And the more we passed, the more (those kind of) actors wanted to do it. It was a tough test of character for us all, I'll tell you that, because those things obviously guarantee a film getting more of an opportunity to be seen on the road. But I had to stick to my guns. I had to say no to so-and-so (because) we have to go with unfamiliar faces. And I think that paid off." On the marketing front, he added, "The film doesn't come out until December so we're not showing it to reviewers yet, but we've started a series of screenings for political shows, political journalists and people that are not necessarily from the entertainment side of journalism (but) from the politics and social side of journalism. We feel that the film, though not a political film, has an inherently political issue in this privacy vs. security issue. And we're finding that, so far, all the different outlets we've been showing it to and the editors and reporters and journalists we've been showing it to have really sparked to that debate, which is really, really exciting. "We just happened to luck out timing-wise. The movie happens to be about a topic that is on the front page of papers every day. We happened to finish the film at time when all the big cities are wanting more and more surveillance cameras on every street corner to stop crime. The whole situation in London with those doctors who were planning those bombs -- those things were all solved by the complex matrix of surveillance cameras they have there. We were all familiar with the iconography on the news every week of a child being abducted and the surveillance footage is so grainy and we can't see who the guy was who took her or the (footage of) the nanny hitting the baby. There's so many iconic images that are so (much) a part of the collective consciousness to do with this subject matter, I just feel that the timing is right, luckily for us, for this movie right now." Filmmaker flashbacks: From Dec. 22, 1989's column: "Behind every successful movie there seems to be a story about how many years it took to be put together. The latest such story comes from Freddie Fields, whose production 'Glory,' directed by Ed Zwick and starring Matthew Broderick and Denzel Washington, got off to a fine start for Tri-Star last weekend. "'A lot of projects suffer that difficulty of getting made,' Fields told me. 'This one certainly did. I suffered the problems of being turned down and rejected for reasons which at times I understood and at other times I became so frustrated about that -- that's what really kept me going.' "What did they tell Fields? 'I would sit and tell the story and they'd be fascinated and maybe take a full meeting or even a second meeting,' he replies. 'But by the next day or within a short period of time when they got their feedback from their audience researchers they'd say, 'Listen, Freddie, here's the way it looks. Our researchers say, bottom line, who wants to see this movie? It's a period piece. Worse that just being a period piece, it's Civil War. And not only is it Civil War, but it's a Civil War piece about the first black regiment in history. Everything is working against this thin. There's nothing that says anybody wants to see this movie.' "'So it was really basically that. It wasn't a disagreement that the story was fascinating. It was fascinating and fine, but who wants to see it? Then, of course, when those who did take the time to read the first draft, and many of them wouldn't, they also saw in their minds a very, very expensive picture costing $35 million or $40 million. It was impossible for them to believe, as I said at the time, that this picture could be done for anywhere from $15 million to $20 million, depending on the result that we wanted to get....' "How did he get Tri-Star to make it? 'I kept hitting Jeff Sagansky three or four times,' says Fields. 'He started to feel what I felt. He then really was the one who sold it to David Matalon (then president of Tri-Star). David Matalon, then, became the champion of the film and still remains its champion. He got Victor Kaufman (then chairman) excited. They put me in touch with Ed Zwick, whom I'd never met before. They were very excited about Ed because they'd had a great experience with him on 'About Last Night.' We hit it off great. After we had our meetings I gave him the Kevin Jarre script and he said he wanted to do it.'" Update: "Glory" went wide Feb. 16, 1990 with $2.7 million at 801 theaters ($3,350 per theater). It wound up grossing $26.8 million domestically, making it the year's 45th biggest movie. "Glory" did better on the awards front, winning Oscars for best supporting actor (Washington), cinematography and sound and also receiving nominations for best art direction-set decoration and film editing. Washington won the Golden Globe for best supporting actor and the film was honored with Globe noms for best motion picture -drama, director, original score and screenplay. http://www.hollywoodreporter.com/hr/...153da8c2c8dd89  Art or Bioterrorism: Who Cares? RU Sirius The Emergency Response Team might have thought they'd stumbled upon an underground bioterrrorist's laboratory. On May 11, 2004, 911 received a call from SUNY Buffalo University professor and artist Steve Kurtz reporting the death of Kurtz's wife Hope from heart failure. The responders entered the home where Kurtz worked on his projects for Critical Arts Ensemble (CAE) — projects which explore and critique bio-issues like our contemporary use of biotechnology for weapons programs, reproduction, and food. The responders noted a table with scientific equipment and peculiar substances that are an essential part of Kurtz' work. The FBI detained and questioned Kurtz for 22 hours. His house — and his wife's body — were confiscated. Kurtz' entire street was quarantined while agents from numerous agencies, including Homeland Security and the Department of Defense, descended on his home in hazmat suits. Everything was confiscated – computers, books on bioweaponry, garbage, posters with "suspicious" Arabic lettering on them… everything. After about two days, the authorities had tested the biological materials and declared that no toxic material had been found. On May 17, Kurtz was allowed to return to his home. Whoops! So did the authorities apologize to the grieving professor before busying themselves with pursuing real crimes and threats? Not on your life! Despite the Public Health Commissioner's conclusions about the safety of Kurtz's materials, and despite the FBI's own field and laboratory tests showing they weren't harmful to people or the environment, the Justice Department still sought charges under the U.S. Biological Weapons Anti-Terrorism Act of 1989, as expanded by the USA PATRIOT Act — Prohibitions With Respect to Biological Weapons. A federal grand jury rejected the charges, but instead handed down indictments with two counts each for "mail fraud" and "wire fraud." According to the CAE, the charges "concern technicalities" about how Kurtz obtained "$256 worth of harmless bacteria for one of CAE's art projects." (Robert Ferrell, former head of the Department of Genetics at the University of Pittsburgh's School of Public Health, and a collaborator on several of CAE’s projects, now facing charges along with Kurtz) In this interview, Kurtz characterizes the charges even more bluntly. "The Department of Justice can drop a major felony on someone for filling out a warranty card incorrectly and mailing it." To bring more attention to the case, film director Lynn Hershman Leeson (Teknolust, Conceiving Ada) has released a unique new film, Strange Culture. Starring Tilda Swinton, Peter Coyote, Thomas Jay Ryan, and Josh Kornbluth — plus Kurtz himself — the film effectively communicates the story while also reinventing the documentary genre in Leeson's unique style. Strange Culture was screened in the virtual world of Second Life as part of the 2007 Sundance Festival, a first for the festival. The film has also been screened in Los Angeles, Albequerque, Chicago, Buffalo, Seattle and Minneapolis and is just finishing up showings in San Francisco and San Rafael on September 27. The film has not gone into conventional release, but future showings are planned for New York City. RU SIRIUS: Describe the project you were working on that caused you to have the materials that caused law enforcement officials to go nuts. STEVE KURTZ: Three projects seemed to really bother law enforcement. Critical Art Ensemble was working on a biochemical defense kit against Monsanto’s Roundup Ready products for use by organic and traditional farmers. That was all confiscated. We had a portable molecular biology lab that we were using to test food products labeled “organic” to see if they really were free of GMO contaminant. Or, when in Europe, to see if products not labeled as containing GMOs really had none. We'd finished the initiative in Europe and were about to launch here in the U.S. when the FBI confiscated all our equipment. Finally, we were a preparing project on germ warfare and the theater of the absurd. We were planning to recreate some of the germ warfare experiments that were done in the '50s (which were so insane that they could only have been paid for with tax dollars). We had two strains of completely harmless bacteria that simulated the behavior of actual infectious diseases — plague and anthrax. To accompany these performances, we were in the middle of a manuscript on the militarization of civilian health agencies in the U.S. by the Bush administration. Everything described was confiscated. We had to start from scratch on the project and the book. Happily, we did eventually do the experiments, and published the book — Marching Plague: Germ Warfare and Global Public Health. RU: Would you say that originally, they authentically suspected they had found some sort of bioterror weapon, and once they realized they hadn't, they found other reasons to remain hostile? SK: What I think they thought was that they had a situation, along with a vulnerable patsy, out of which they could manufacture a terrorism case. After all, the rewards that were heaped on the agents, prosecutors, and institutions that brought home the so-called “Lackawana Six sleeper cell” case — another railroad job — were witnessed by others in these agencies and noted. This made it too lucrative to pass up turning anything they could into “terrorism”. They also had plenty of other reasons to be — and remain — hostile. RU: Could you describe the scene of the raid? Did they use a lot of weaponized overkill? SK: I really don’t know any more than anybody else about that. At the time of the real action, I was at the Yes Men’s compound in Troy, NY. (Due to the initial media circus, I was told by my lawyers to leave town for a few days.) From what I can tell from the news footage and the reports of neighbors, the entire alphabet soup of the federal investigative agencies was launched. Each took a turn entering my home wearing hazmat suits with guns drawn, and proceeded to do their “bioterrorism” exercises. RU: Oh, I had the impression that the entire situation involving your wife's death, the discovery of the materials, and the raid all happened fairly instantly. Did this scene stretch out over days? SK: It did stretch out a ways. Even though I was illegally “detained” for 22 hours the day after my wife’s death and they had confiscated my house, the raid didn’t begin. It took a few days for them to assemble all the troops and to obtain a search warrant. RU: And did they think you were trying to avoid arrest since you were hiding? SK: No. I was out of town on advice of my attorneys. I had already been in custody and released. They knew they only had to contact my lawyer and I would self-surrender. RU: This must have all been a tremendous strain, coming as it did coupled with the death of your wife. Can you describe some of the thoughts and emotions you had around all this? SK: I think all adults know the feelings of intense grief and depression that are brought about by the loss of a loved one. My feelings were in no way unique. But when you spice it with the adrenalin and the hyperanxiety of being attacked by the full weight of federal forces, which in turn causes all your survival instincts to really kick in, you have a bad trip from which you are not going to come down for a long time. In my case, it was six months or so before I started feeling anything approaching normal. This close proximity to mortality stemming from two different extremes (loss and attack) creates a feedback loop that turns your brain into static. Patterns of thought, emotion, and behavior deconstruct and seem to lose any identifiable point of origin. I was a zombie— an animated organic mass with modest brain function. RU: Have you run into particularly Kafkaesque scenarios given this cases' attachment to The Patriot Act and Homeland Security? SK: The case has been a hyperreal, bureaucratic grind, but I have yet to wait endlessly in any hallways not knowing why I was there or what I was charged with. RU: Explain a little bit more about the project you were planning around these materials related to biological warfare and theater of the absurd. SK: We did the projects. You can see them at our website at critical-art.net. We just recreated a couple of the experiments that different militaries did to see if germs were viable candidates for weaponization. For the British Plague experiments, Critical Art Ensemble went to the Isle of Lewis in Scotland where they had originally been done. The British tests started south of this location and were land-based, but the results were so appallingly bad from a military perspective that they began to believe that the only way infectious disease could possibly be of use militarily was as a tactical ship-to-ship weapon. To test this idea they moved to an even less populated area (the Isle of Lewis). They put a bunch of monkeys and guinea pigs on a pontoon and started shooting germs at them in both powder and wet forms from about a mile away — a very difficult shot in the blustery weather of Northern Scotland. The infection rates were again poor, and included a fishing vessel that unsuspectingly sailed through the experiment. The British Navy had to follow the vessel to make sure it didn’t land or make physical contact with other ships until they were sure no one on the boat was infected. No one was. The only conclusion reached from this experience was to move the test to the colonies — in this case, the Bahamas. Critical Art Ensemble did the same thing, only we recreated the harmless simulant tests (not the actual plague tests), and only used guinea pigs overseen by the SSPCA — no monkeys. Our results were just as bad, so it seems as if we reliably replicated the test. CAE went to the end of the world to shoot bacteria at guinea pigs. Can there be a more absurdist gesture than that? Well yes — one: Bush reinitiating a failed germ warfare program at public expense and at the cost of civilian interests in world and national health policy. The Bush administration is usurping public civilian agencies (such as the CDC and countless universities) and using them to play out the administration’s fantasies of a terrorist germ warfare attack. The resources to study infectious diseases are limited, and it's criminal to use them for a remote “what could be” scenario at the expense of real, ongoing health crises like AIDS, TB, hepatitis, malaria, and other diseases that are killing millions every year. RU: I never thought of CAE as a really obscure project, since I'd read various manifestos or statements by you and seen stuff about you here and there. And yet, outside the avant-garde art community, very few people know about this bizarre and outrageous case. Do you think this says something about our cluttered and diffuse culture. SK: I think you have stated the situation as well as I can. Information is ubiquitous and overwhelming. Only so much can be processed in a day. And when you think of how many outrages are occurring each day because of the war and the current U.S. constitutional crisis, who has time to follow one of the many ridiculous court cases brought by the Department of Justice? One has to be motivated by a very direct interest in the case to take notice, no matter how precedent setting the case might be. In my case, the Department of Justice is attempting to completely implode civil and criminal law, but if you are not in the arts and sciences, there’s too many other events and situations to worry about. RU: Is there some way we can make it more difficult for arbitrary authority to pick off people who are on the so-called fringes? SK: I have no idea. The FBI has been a Dr. Jekyll/Mr Hyde type of institution from its inception. While I am happy for its work against organized crime, for example, I have always been completely outraged by its continuous assault on those individuals and sometimes entire communities (as with the current attack on peoples of Islamic faith) who openly express ideological difference. The FBI has worked against socialists and communists from the 20s through the 60s, and against the equal rights movements of the same period. The COINTELPRO operations of the 60s and 70s are basically back, so exercising our rights is more risky than ever, but it’s for that very reason we must. Rights are won and kept through struggle, and in our struggle to preserve our Constitution, it pains me to say that the FBI is and has always been one of the anti-democratic enemies. RU: What do you think abour Lynn Hershman's film, Strange Culture? SK: It’s inspirational and well worth seeing. It has brought awareness about the case to new audiences. RU: Did you participate in the creative direction at all? SK: No. RU: What kind of effect do you expect from it? SK: Exactly what it’s doing — bringing an awareness of the case to people and communities that otherwise would not hear about it. RU: According to the CAE defense fund FAQ, you were originally charged under prohibitions on biological weapons, but a grand jury instead handed down indictments related to "wire fraud" and "mail fraud." And then it also states that the terrorism charges could come back to haunt you. I wonder how your attorneys are coping with all this. Are they simply trying to get across the absurdity of the whole mess, or are their any legal fine points? SK: What they have been arguing in motion hearings is that the Department of Justice is making an absurd interpretation of the mail fraud law. The DoJ has thrown away its guidelines (which state my case should not be prosecuted) and interpreted the law in a way that is unique for my situation. My co-defendant Bob Ferrell and I are the first citizens to ever be indicted for mail or wire fraud because we supposedly broke a material transfer agreement. The “defrauded” parties do not believe we did anything to harm them — the crime is a DoJ fantasy that they hope to prove. We’ll see at trial if rationality prevails. If it doesn’t, the case will set a precedent that will mean that the Justice Department can drop a major felony on someone for filling out a warranty card incorrectly and mailing it. This will be a major tool for them. Talk about being able to pick off people at will! http://www.10zenmonkeys.com/2007/09/...ism-who-cares/  Judge Rules Parts Of Patriot Act Unconstitutional Download Judge's Ruling (.pdf) AP A federal judge ruled Wednesday that two provisions of the USA Patriot Act are unconstitutional because they allow search warrants to be issued without a showing of probable cause. U.S. District Judge Ann Aiken ruled that the Foreign Intelligence Surveillance Act, as amended by the Patriot Act, "now permits the executive branch of government to conduct surveillance and searches of American citizens without satisfying the probable cause requirements of the Fourth Amendment." Portland attorney Brandon Mayfield sought the ruling in a lawsuit against the federal government after he was mistakenly linked by the FBI to the Madrid train bombings in 2004. The federal government apologized and settled part of the lawsuit for $2 million after admitting a fingerprint was misread. But as part of the settlement, Mayfield retained the right to challenge parts of the USA Patriot Act. Mayfield claimed that secret searches of his house and office under the Foreign Intelligence Surveillance Act, or FISA, violated the Fourth Amendment's guarantee that "the right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no warrants shall issue, but upon probable cause ..." Aiken agreed with Mayfield, repeatedly criticizing the government. "For over 200 years, this Nation has adhered to the rule of law -- with unparalleled success. A shift to a Nation based on extra-constitutional authority is prohibited, as well as ill-advised," she wrote. She said that by asking her to dismiss Mayfield's lawsuit, the U.S. Attorney General's office was "asking this court to, in essence, amend the Bill of Rights, by giving it an interpretation what would deprive it of any real meaning. This court declines to do so." Elden Rosenthal, an attorney for Mayfield, issued a statement on his behalf praising the judge, saying she "has upheld both the tradition of judicial independence, and our nation's most cherished principle of the right to be secure in one's own home." http://cbs5.com/breakingnewsalerts/l...269191331.html  Missouri: Police Stake Out Brett Darrow Home A young Saint Louis, Missouri motorist faces trouble with local police upset at the national attention his September 7 video of an out-of-control officer has drawn to ongoing problems within area law enforcement agencies. On Sunday, Brett Darrow filmed a Saint Louis Metropolitan Police Department cruiser staking out his home. "It was the first time I've seen it," Darrow told TheNewspaper. "But my neighbor said he's seen a lot of police down our dead end street since all of this happened." When Darrow walked outside to his 1997 Nissan Maxima, he noticed two officers sitting in a marked squad car, numbered 65. There is little question as to why the officers were there. "As I got into the car, he started to pull up the street and he and his partner just stared me down," Darrow explained. The patrol car drove away as Darrow started his car and followed. Because his camera had been set to capture night-time footage, the first 45 seconds of the video is obscured. It does, however, capture the police car making questionable turning maneuvers in order to get away. Members of the police community are on the record regarding their desire to stake out Darrow's home and harass the twenty-year-old. In late June, users of St. Louis CopTalk, an unofficial forum for Saint Louis area law enforcement, posted Darrow's home address along with messages containing apparent death threats in retaliation for the young motorist's taping of a DUI roadblock in November and a traffic ticket in June. One CopTalk user repeating the address wrote, "Every copper, City and County, should etch this little punks [sic] name in their [sic] memory. Brett Darrow, [address deleted], city of St. Louis." (View screen capture of post) This month, however, scandals within the Saint Louis Police Department which otherwise would have been a local story, gathered national attention and fueled additional resentment. Some $40,000 in cash turned up "missing" from the police evidence room on September 17. The city of St. George was forced to fire Sergeant James Kuehnlein for his threat to "come up with reasons" to "lock up" Darrow. An investigation into whether Kuehnlein's actions merit criminal charges is under way. Darrow met on Monday with a Saint Louis County Police Department detective. "I quickly learned that this was about finding something I did wrong and not the officer," Darrow said. Despite the official harassment, Darrow has been comforted by an unexpected level of support from the general public. Motorists who recognized him from various television interviews have stopped to thank him or give him the "thumbs up." A judge also dropped charges from the June traffic stop after a Saint Louis police officer failed to show up at a trial where Darrow had been prepared to defend himself with video evidence. http://www.thenewspaper.com/news/19/1988.asp  Police Wiki Lets You Write the Law Arjun Ramachandran It's said the powerful write their own laws, but now everyone can. Due to a new wiki launched by New Zealand police, members of the public can now contribute to the drafting of the new policing act. NZ Police Superintendent Hamish McCardle, the officer in charge of developing the new act, said the initiative had already been described as a "new frontier of democracy". "People are calling it 'extreme democracy' and perhaps it is," he said. "It's a novel move but when it comes to the principles that go into policing, the person on the street has a good idea ... as they are a customer," he said. "They've got the best idea about how they want to be policed." NZ Police were reviewing the old Policing Act, from 1958, which had become "anachronistic" and was "written for a completely different age, not policing of today", Superintendent McCardle said. But drafting new legislation "shouldn't just be the sole reserve of politicians", he said, so the wiki was created to invite input from members of the public. Social networks strategist Laurel Papworth, who writes a blogs on how online communities change the way society operates, said "participatory legislation" was a "great idea". "It empowers the voters to have a voice not just a vote, so that they are actually contributing to the dialogue and not just voting on the outcome," she said. But input into the NZ Police Act wiki was not being limited to New Zealand voters, Superintendent McCardle said. "The wonderful thing about a wiki is we can open it up to people all around the world - other academics and constitutional commentators interested in legislation - and make the talent pool much wider," he said. Comment on whether the idea could work for NSW Police was being sought from Police Minister David Campbell. But Ms Papworth said Australian governments had recently opened up to the public more through the use of online technology, such as forums and blogs. But she was not aware of the use of wikis to invite public contribution to legislation. Superintendent McCardle laughed off a suggestion that the initiative invited would-be criminals to write loopholes into the act to be exploited once it became law. "We have been asked if we are worried about it being defaced, but wikis generally haven't been defaced internationally - people generally are constructive and productive," he said, referring to the success of Wikipedia, the popular wiki encyclopedia. The wiki version of the Policing Act will be viewed by New Zealand parliamentarians, before an official bill is introduced into Parliament, Superintendent McCardle said. The police act wiki can be found here: http://wiki.policeact.govt.nz http://www.stuff.co.nz/4215797a10.html  Run Away the Ray-Gun is Coming : We Test US Army's New Secret Weapon Michael Hanlon "Where do I put my finger? There ... OK? Nothing's happening ... is it on?" "Yes, it's on. Move your finger a bit closer." "Er ... ow! OW!" Not good. I try again. "OWWW!" I pull my hand away sharpish. My finger is throbbing, but seems undamaged. I was told people can take it for a second, maximum. No way, not for a wimp like me.  I try it again. It is a bit like touching a red-hot wire, but there is no heat, only the sensation of heat. There is no burn mark or blister. Its makers claim this infernal machine is the modern face of warfare. It has a nice, friendly sounding name, Silent Guardian. I am told not to call it a ray-gun, though that is precisely what it is (the term "pain gun" is maybe better, but I suppose they would like that even less). And, to be fair, the machine is not designed to vaporise, shred, atomise, dismember or otherwise cause permanent harm. But it is a horrible device nonetheless, and you are forced to wonder what the world has come to when human ingenuity is pressed into service to make a thing like this. Silent Guardian is making waves in defence circles. Built by the U.S. firm Raytheon, it is part of its "Directed Energy Solutions" programme. What it amounts to is a way of making people run away, very fast, without killing or even permanently harming them. That is what the company says, anyway. The reality may turn out to be more horrific. I tested a table-top demonstration model, but here's how it works in the field. A square transmitter as big as a plasma TV screen is mounted on the back of a Jeep. When turned on, it emits an invisible, focused beam of radiation - similar to the microwaves in a domestic cooker - that are tuned to a precise frequency to stimulate human nerve endings. It can throw a wave of agony nearly half a mile. Because the beam penetrates skin only to a depth of 1/64th of an inch, it cannot, says Raytheon, cause visible, permanent injury. But anyone in the beam's path will feel, over their entire body, the agonising sensation I've just felt on my fingertip. The prospect doesn't bear thinking about. "I have been in front of the full-sized system and, believe me, you just run. You don't have time to think about it - you just run," says George Svitak, a Raytheon executive. Silent Guardian is supposed to be the 21st century equivalent of tear gas or water cannon - a way of getting crowds to disperse quickly and with minimum harm. Its potential is obvious. "In Iraq, there was a situation when combatants had taken media as human shields. The battalion commander told me there was no way of separating combatants from non-combatants without lethal force," Mr Svitak tells me. He says this weapon would have made it possible because everyone, friend or foe, would have run from it. In tests, even the most hardened Marines flee after a few seconds of exposure. It just isn't possible to tough it out. This machine has the ability to inflict limitless, unbearable pain. What makes it OK, says Raytheon, is that the pain stops as soon as you are out of the beam or the machine is turned off. But my right finger was tingling hours later - was that psychosomatic? So what is the problem? All right, it hurts, but then so do tear gas and water cannon and they have been used by the world's police and military for decades. Am I being squeamish? One thing is certain: not just the Silent Guardian, but weapons such as the Taser, the electric stun-gun, are being rolled out by Britain's police forces as the new way of controlling people by using pain. And, as the Raytheon chaps all insist, you always have the option to get out of the way (just as you have the option to comply with the police officer's demands and not get Tasered). But there is a problem: mission creep. This is the Americanism which describes what happens when, over time, powers or techniques are used to ends not stated or even imagined when they were devised. With the Taser, the rules in place in Britain say it must be used only as an alternative to the gun. But what happens in ten or 20 years if a new government chooses to amend these rules? It is so easy to see the Taser being used routinely to control dissent and pacify - as, indeed, already happens in the U.S. And the Silent Guardian? Raytheon's Mac Jeffery says it is being looked at only by the "North American military and its allies" and is not being sold to countries with questionable human rights records. An MoD spokesman said Britain is not planning to buy this weapon. In fact, it is easy to see the raygun being used not as an alternative to lethal force (when I can see that it is quite justified), but as an extra weapon in the battle against dissent. Because it is, in essence, a simple machine, it is easy to see similar devices being pressed into service in places with extremely dubious reputations. There are more questions: in tests, volunteers have been asked to remove spectacles and contact lenses before being microwaved. Does this imply these rays are not as harmless as Raytheon insists? What happens when someone with a weak heart is zapped? And, perhaps most worryingly, what if deployment of Silent Guardian causes mass panic, leaving some people unable to flee in the melee? Will they just be stuck there roasting? Raytheon insists the system is set up to limit exposure, but presumably these safeguards can be over-ridden. Silent Guardian and the Taser are just the first in a new wave of "non-lethal" weaponry being developed, mostly in the U.S. These include not only microwave ray-guns, but the terrifying Pulsed Energy Projectile weapon. This uses a powerful laser which, when it hits someone up to 11/2 miles away, produces a "plasma" - a bubble of superhot gas - on the skin. A report in New Scientist claimed the focus of research was to heighten the pain caused by this semi-classified weapon. And a document released under the U.S. Freedom of Information Act talks of "optimal pulse parameters to evoke peak nociceptor activation" - i.e. cause the maximum agony possible, leaving no permanent damage. Perhaps the most alarming prospect is that such machines would make efficient torture instruments. They are quick, clean, cheap, easy to use and, most importantly, leave no marks. What would happen if they fell into the hands of unscrupulous nations where torture is not unknown? The agony the Raytheon gun inflicts is probably equal to anything in a torture chamber - these waves are tuned to a frequency exactly designed to stimulate the pain nerves. I couldn't hold my finger next to the device for more than a fraction of a second. I could make the pain stop, but what if my finger had been strapped to the machine? Dr John Wood, a biologist at UCL and an expert in the way the brain perceives pain, is horrified by the new pain weapons. "They are so obviously useful as torture instruments," he says. "It is ethically dubious to say they are useful for crowd control when they will obviously be used by unscrupulous people for torture." We use the word "medieval" as shorthand for brutality. The truth is that new technology makes racks look benign. http://www.dailymail.co.uk/pages/liv...icle_id=482560  IBM Software to Scan Chicago Streets Robert McMillan The City of Chicago is developing a futuristic video surveillance system designed to scan city streets looking for everything from bombs to traffic jams. For the past few years Chicago has been rolling out thousands of video surveillance cameras linked by fiber-optic cables. This Operation Virtual Shield system is intended to give the city's emergency response coordination agency the ability to remotely keep track of emergencies in real time. Now, with the help of IBM Corp., Chicago's Office of Emergency Management and Communications (OEMC) is looking to expand the system's capabilities so that IBM's software can analyze the thousands of hours of video being recorded by Operation Virtual Shield. "That's really going to just throw our camera network into hyperdrive," said Kevin Smith, a spokesman with the OEMC. "Ultimately I think what this software might be able to do is simply recognize suspicious behavior and alert our operations people and, at times, our crime detections specialists as to what it sees." The software could recognize a package that had been left in a public park or a car parked where no car is supposed to be, Smith said. IBM has been pushing a similar technology called Smart Surveillance System within the retail industry as a tool to fight shoplifting. The Smart Surveillance System was spun out of IBM's T.J. Watson Research Center earlier this year. Now IBM is talking to a number of cities about rolling out similar projects, according to Sam Docknevich, a Digital Video Surveillance National Practice Leader with IBM. However none is as advanced as the Operation Virtual Shield effort. "Chicago is definitely the leading example of the value of integrating video from multiple organizations and using it to enhance public safety," he said. OEMC's Smith would not say how much the city is spending on the project or when it expects IBM's video analytics capabilities to go live. The trick will be to make the analytics software work in a useful way. "The challenge is going to be teaching computers to recognize the suspicious behavior," said Smith. "Once this is done this will be a very impressive city in terms of public safety." http://security.itworld.com/4357/070...an/page_1.html  Wide-Angled Gigapixel Satellite Surveillance High resolution images taken by satellite or aircraft are great - but the field of view in such pictures is tiny. To monitor a large area, the images have to be tiled like pieces in a jigsaw puzzle before a full picture can be built up. This can cause problems: vehicles can end up appearing more than once if they move from one image to the next between exposures, for example. Such errors creep into virtual globes like Google Earth and Microsoft Virtual Earth and online mapping tools. So a group of researchers at Sony and the University of Alabama have come up with a wide-angle camera that can image a 10-kilometre-square area from an altitude of 7.5 kilometres with a resolution better than 50 centimetres per pixel. The trick is to build an array of light sensitive chips that each record small parts of a larger image and place them at the focal plane of a large multiple-lens system. The camera would have gigapixel resolution, and able to record images at a rate of 4 frames per second. The team suggests that such a camera mounted on an aircraft could provide images of a large city by itself. This would even allow individual vehicles to be monitored without any danger of losing them as they move from one ground level CCTV system to another. The camera could have military applications too, says the team. Mounted on the underside of an unmanned aerial vehicle, the gigapixel camera could provide almost real-time surveillance images of large areas for troops on the ground. http://www.newscientist.com/blog/inv...satellite.html  Navy to Mask Coronado's Swastika-Shaped Barracks  SWASTIKA?: The buildings, constructed in the 1960s, are on the Coronado amphibious base and serve as a barracks for Seabees. From the ground, or even adjoining buildings, the configuration cannot be seen. Nor are there any civilian or military landing patterns that provide such a view. But Google Earth shows the shape clearly. Tony Perry The U.S. Navy has decided to spend as much as $600,000 for landscaping and architectural modifications to obscure the fact that one its building complexes looks like a swastika from the air. The four L-shaped buildings, constructed in the late 1960s, are part of the amphibious base at Coronado and serve as barracks for Seabees. From the ground and from inside nearby buildings, the controversial shape cannot be seen. Nor are there any civilian or military landing patterns that provide such a view to airline passengers. But once people began looking at satellite images from Google Earth, they started commenting about on blogs and websites about how much the buildings resembled the symbol used by the Nazis. When contacted by a Missouri-based radio talk-show host last year, Navy officials gave no indication they would make changes. But early this year, the issue was quietly taken up by Morris Casuto, the Anti-Defamation League's regional director in San Diego, and U.S. Rep. Susan Davis (D-San Diego). As a result, in the fiscal year that begins Oct. 1, the Navy has budgeted up to $600,000 for changes in walkways, "camouflage" landscaping and rooftop photovoltaic cells. The goal is to mask the shape. "We don't want to be associated with something as symbolic and hateful as a swastika," said Scott Sutherland, deputy public affairs officer for Navy Region Southwest, the command that is responsible for maintaining buildings on local bases. The collection of L-shaped buildings is at the corner of Tulagi and Bougainville roads, named after World War II battles. Navy officials say the shape of the buildings, designed by local architect John Mock, was not noted until after the groundbreaking in 1967 -- and since it was not visible from the ground, a decision was made not to make any changes. It is unclear who first noticed the shape on Google Earth. But one of the first and loudest advocates demanding a change was Dave vonKleist, host of a Missouri-based radio-talk show, The Power Hour, and a website, www.thepowerhour.com. In spring 2006, he began writing military officials, including then-Defense Secretary Donald Rumsfeld, calling for action. That August, he received a response from officials in Coronado, who made no promise to take action and said, "The Navy intends to continue the use of the buildings as long as they remain adequate for the needs of the service." In December, the now-defunct San Diego Jewish Times wrote about the buildings and the controversy. Soon Casuto and Davis got involved. Casuto began an on-and-off dialogue with the chief of staff to Rear Adm. Len Hering, commander of Region Southwest. He said that several members of the Jewish community had complained to him. "I don't ascribe any intentionally evil motives to this," Casuto said, referring to the design. "It just happened. The Navy has been very good about recognizing the problem. The issue is over." Davis, who is Jewish, is also pleased with the Navy's decision. During a discussion with military officials on other issues, Davis had mentioned the Coronado buildings and suggested that rooftop photovoltaic arrays might help change the overhead look. The base gets 3% of its power from solar energy and has been looking to increase that percentage. Reached in Versailles, Mo., vonKleist, the talk-show host, said he was ecstatic. "I'm concerned about symbolism," he said. "This is not the type of message America needs to be sending to the world." http://www.latimes.com/news/local/la...la-home-center  Burmese Government Clamps Down on Internet Mike Nizza Burmese bloggers are now reporting that they are running into significant hurdles to getting the word out on the government’s crackdown. “Burma is blacked out now!,” one blogger announced from Yangon, the country’s main city. More details from the post: Internet cafes were closed down. Both MPT ISP and Myanmar Teleport ISP cut down internet access in Yangon and Mandalay since this morning. The Junta try to prevent more videos, photographs and information about their violent crackdown getting out. I got a news from my friends that last night some militray guys searched office computers from Traders and Sakura Tower building. Most of the downtown movement photos were took from office rooms of those high buildings. GSM phone lines and some land lines were also cut out and very diffficult to contact even in local. GSM short message sending service is not working also. As protests built to more than 100,000, the government apparently allowed internal reports until three days into the crackdown, raising fears that it planned to intensify measures that left 9 dead on Thursday. It also had immediate effects on the information flow out of the country. “Exile groups and human rights organizations who are in touch with people inside Myanmar said they had less news today than before about clashes,” Seth Mydans of The New York Times reported from Bangkok. A blogger we wrote about on Thursday, Ko Htike, is also having major problems because of the internet cuts, losing the ability to put out a major part of his reporting so far. He said he’s not “able to feed in pictures of the brutality by the brutal Burmese military junta,” but he still hoped to find “other means.” He also seemed sick of all the attention he’s been receiving lately from The Lede and other news outlets: (Journos!! please don’t ask me what other means would be??). I will continue to live with the motto that “if there is a will there is a way”. Michelle Malkin brings more bad news for Burmese bloggers: Several popular dissident blogs had already gone dark the past few days before the “damaged underwater cable” shut down Internet accesss. The fate of one prolific Burmese blogger, Moezack, is unknown. The entire blog has been wiped. The government’s explanation, according to an official interviewed by Agence France-Presse, blames an extraordinarily timed bout with technical difficulties. “The Internet is not working because the underwater cable is damaged,” the official said. Still, several sources from inside Burma continued to provide frequent updates; you can find them on several sites we mentioned on Thursday and Cbox, which is aggregating developments in matter-of-fact bulletins that paint vivid, scary pictures. “The Police Station at South-Okkalarpa is being burnt down,” one entry says. More Web sites are referred by an anonymous Burmese blogger writing to Global Voices today. The post carries more fears of the price the bloggers may pay for trying to document the uprising: Information flow out of the country has been strictly monitored and even the amateur photographers are warned to be very careful as the Junta is hunting down the sources. http://thelede.blogs.nytimes.com/200.../index.html?hp  Burma Cyber-Dissidents Crack Censorship Stephanie Holmes Burma's bloggers are using the internet to beat censorship, and tell the world what is happening under the military junta's veil of secrecy. Images of saffron-robed monks leading throngs of people along the streets of Rangoon have been seeping out of a country famed for its totalitarian regime and repressive control of information. The pictures are sometimes grainy and the video footage shaky - captured at great personal risk on mobile phones - but each represents a powerful statement of political dissent. "It is amazing how the Burmese are able through underground networks to get things from outside and inside," says Vincent Brussels, head of the Asian section of press freedom organisation Reporters Without Borders. "Before, they were moving things hand-to-hand and now they are using the internet - proxy websites, Google and YouTube and all these things." On the inside The use of the internet as a political tool is one of the most marked differences between the latest protests and the 1988 uprising, which was brutally repressed. Thanks in part to bloggers, this time the outside world is acutely aware of what is happening on the streets of Rangoon, Mandalay and Pakokku and is hungry for more information. Burmese-born blogger Ko Htike, based in London, has transformed his once-literary blog into a virtual news agency and watched page views rise almost tenfold. He publishes pictures, video and information sent to him by a network of underground contacts within the country. "I have about 10 people inside, in different locations. They send me their material from internet cafes, via free hosting pages or sometimes by e-mail," he told the BBC News website. "All my people are among the Buddhists, they are walking along with the march and as soon as they get any images or news they pop into internet cafes and send it to me," he said. Ko Htike is one of a number of Burmese online activists, almost all based beyond the country's borders. Reporters without Borders describe how a guide for cyber-dissidents provided to young Burmese was seized upon, copied and feverishly disseminated among a growing group of the young, politically active and computer-literate. Bloggers are teaching others to use foreign-hosted proxy sites - such as your-freedom.net and glite.sayni.net - to view blocked sites and tip-toe virtually unseen through cyberspace, swapping tricks and links on their pages. Virtual space The internet has also become a virtual space for political groups who could not openly express their shared views in public. Ko Htike met his network of citizen journalists in an internet forum which was rapidly disbanded after initial contact had been made. Such forums are also used as a space to alert bloggers whenever new content - stills or video - arrives. "We normally use internet chat rooms, like Yahoo Messenger," Ko Htike said. "If they find it difficult, they call me. They don't say anything, they just give links or a code, they don't mention anything about it." Analysts agree that, although internet access is currently at less than 1% of the population, the current regime underestimated its potential. CENSORSHIP IN BURMA Burma ranks 164 of 168 states on press freedom 0.56% of population has internet access 25,000 people have official email addresses (2005) Two state-controlled internet providers "Pervasive" filtering of political websites Sources: Reporters Without Borders, OpenNet Initiative The regime stopped focusing on policing its virtual borders after a power struggle which resulted in the ousting of former Prime Minister Khin Nyunt in October 2004, explains Mr Brussels. "Khin Nyunt was a military intelligence guy, he had a big network of spies and people were quite wise about all these kind of controls. After he was removed, they no longer have much knowledge in this area," he said. "There has been the opportunity for people on the inside to use their skills. These are young journalists and geeks, they know how to by-pass the blocking and the censorship." Despite retaining total control of the country's only two internet providers and severely limiting internet usage - anyone who fails to register a computer with a state-sanctioned internet provider faces a 15-year prison term - Ko Htike says the current crisis has made the leadership highly aware of the threat posed by bloggers. False information He described how he has received personal e-mails - and protesters within Burma have received mobile phone text messages - spreading false information and rumours, for example about military crackdowns on protesters. PROTESTS MOUNT 15 Aug: Junta doubles fuel prices, sparking protests 5 Sept: Troops injure several monks at a protest in Pakokku 17 Sept: The junta's failure to apologise for the injuries draws fresh protests by monks 18-21 Sept: Daily marches by monks in Burmese cities gradually gather in size 22 Sept: 1,000 monks march to the home of Aung San Suu Kyi in Rangoon 23 Sept: Up to 20,000 march in Rangoon 24 Sept: New Rangoon march draws at least 50,000 and 24 other towns join in He is convinced these are spread by the Burmese authorities, trying to both influence protesters and hijack his website to spread government propaganda. "Many people are reading my blog so if I put through fake news on the site it will affect people. They [the government] can see the hits, they can see that people are looking at my site... that means they are scared so they are trying to manipulate me, to use people power," Ko Htike said. Compared with China's virtual and physical controls on internet use, however, Burma's systems are pretty unsophisticated, experts say. "The Burmese government has a very repressive filtering regime... but it can be a bit inconsistent - one of the internet service providers blocks only international sites, the other only regional ones," said Ian Brown, a research fellow in internet privacy and security based at Oxford University's Internet Institute. Burma's bloggers are adept at exploiting the loopholes. "It is really important; people want to know what is going on in Burma," said Ko Htike. Through his cyber-network he also aims to protect those who risk their lives to feed his blog, now banned inside the country. "I monitor the news on Burma and I can keep updating my site. If something happens then we can warn them. We can do something, we can keep people aware." Are you in Burma? Have you witnessed the protests? What is the mood like in the country? Send us your comments and experiences. You can send pictures and video to: yourpics@bbc.co.uk or to send via MMS please dial +447725100100. If you have a large file you can upload here. Read the terms and conditions At no time should you endanger yourself or others, take any unnecessary risks or infringe any laws. Name Your E-mail address Town & Country Phone number (optional): http://news.bbc.co.uk/go/pr/fr/-/2/h...ic/7012984.stm  Dan Rather Stands by His Story His lawsuit will attempt to show that CBS tried to suppress the report on Bush's National Guard Service and the Abu Ghraib abuses. Sidney Blumenthal Dan Rather's complaint against CBS and Viacom, its parent company, filed in New York state court on Sept. 19 and seeking $70 million in damages for his wrongful dismissal as "CBS Evening News" anchor, has aroused hoots of derision from a host of commentators. They've said that the former anchor is "sad," "pathetic," "a loser," on an "ego" trip and engaged in a mad gesture "no sane person" would do, and that "no one in his right mind would keep insisting that those phony documents are real and that the Bush National Guard story is true." If the court accepts his suit, however, launching the adjudication of legal issues such as breach of fiduciary duty and tortious interference with contract, it will set in motion an inexorable mechanism that will grind out answers to other questions as well. Then Rather's suit will become an extraordinary commission of inquiry into a major news organization's intimidation, complicity and corruption under the Bush administration. No congressional committee would be able to penetrate into the sanctum of any news organization to divulge its inner workings. But intent on vindicating his reputation, capable of financing an expensive legal challenge, and armed with the power of subpoena, Rather will charge his attorneys to interrogate news executives and perhaps administration officials under oath on a secret and sordid chapter of the Bush presidency. In making his case, Rather will certainly establish beyond reasonable doubt that George W. Bush never completed his required service in the Texas Air National Guard. Moreover, Rather's suit will seek to demonstrate that the documents used in his "60 Minutes II" piece were not inauthentic and that he and his producers acted responsibly in presenting them and the information they contained -- and that that information is true. Indeed, no credible source has refuted the essential facts of the story. Most cases of this sort are usually settled before discovery. But Rather has made plain that he is uninterested in a cash settlement. He has filed his suit precisely to be able to take depositions. In his effort to demonstrate his mistreatment, Rather will detail how network executives curried favor with the administration, offering him up as a human sacrifice. The panel that CBS appointed and paid millions to in order to investigate Rather's journalism will be exposed as a shoddy kangaroo court. Rather's complaint has already asserted a pattern of network submission to administration pressure, beginning with the Abu Ghraib story. In early 2004, Mary Mapes, a producer for "60 Minutes II" with more than two decades of experience, uncovered the torture at the Abu Ghraib prison in Iraq. Her sources were sound and the evidence incontrovertible, but according to Rather's complaint, "CBS management attempted to bury" the story. In a highly unusual move, then CBS News president Andrew Heyward and then senior vice president Betsy West personally intervened to demand editing changes and ever more "substantiation." Rather's suit states that "for weeks, they refused to grant permission to air the story" and "continued to 'raise the goalposts,' insisting on additional substantiation." Even after Mapes gained possession of some of the now-infamous photographs of the torture of prisoners at Abu Ghraib (a full set of which was later obtained and posted by Salon), the news executives suppressed the story, "in part," according to Rather's suit, "occasioned by acceding to pressures brought to bear by government officials." Gen. Richard Myers, then chairman of the Joint Chiefs of Staff, called Rather at his home, sources close to the case told me, telling him that broadcasting the story would endanger "national security." Myers explained to Rather that U.S. soldiers, just then poised for an assault on Fallujah, would be demoralized and suggested that Rather and CBS might threaten the outcome of the battle and the soldiers' safety. Only when Seymour Hersh, investigative reporter for the New Yorker, relying on different sources from Mapes', unearthed the Abu Ghraib story and CBS executives learned that the magazine was about to scoop the network did they grudgingly permit it to be aired. "Even then," Rather's suit states, "CBS imposed the unusual restrictions that the story would be aired only once, that it would not be preceded by on-air promotion, and that it would not be referenced on the CBS Evening News." Feeling forced against their will to broadcast a story they knew was accurate, CBS's executives did everything within their power to ensure the public would pay as little attention to it as possible by prohibiting any mention of it. CBS's self-censorship set the stage for its reaction to the Bush National Guard story. The widely accepted account that Mapes and Rather's original piece on Bush and the Guard was unproved and discredited has been based on the notion that the documents revealed were false. But three years after the heated controversy exploded, these premises appear very uncertain in the cold light of day. Upon graduation from Yale in 1968, George W. Bush was accepted into the Texas Air National Guard, known as the "Champagne Unit" for serving as a haven for the privileged sons of the Texas elite seeking to escape duty in Vietnam. Through carefully placed calls made by Bush family friends, Bush was edged ahead of a 500-man waiting list. Then, after failing to complete his required hours of flight, he requested transfer to a unit in Montgomery, Ala. But there is no proof that he ever performed any of his service there; he refused to take a physical and was grounded. Ordered to return to his Houston base, he simply disappeared. Yet he was honorably discharged in 1973, though there is no proof that he had fulfilled his obligation. During the 2000 campaign, the Boston Globe reported a number of discrepancies in Bush's National Guard record. However, the rest of the national press corps virtually ignored the Globe's stories, instead preferring to swarm around fictions about Al Gore helpfully stoked by the Bush campaign. Bush refused to make public his military records, in contrast to his principal primary opponent, Sen. John McCain, who had released his. But the press collectively let the matter pass. Nonetheless, the gaps in Bush's service as reported by the Globe had not been answered and hung in the air, if anyone cared to pursue them. After breaking the Abu Ghraib story, Mapes, who lived in Texas and had reported on Bush when he was governor, began looking into the National Guard episode. By then, Sen. John Kerry, a decorated Vietnam War hero who was awarded the Silver and Bronze stars, had emerged as the Democratic candidate. The Bush operation arranged for funding a front group called Swift Boat Veterans for Truth to mount a smear campaign that Kerry had been dissembling all these years about his medals. Kerry's campaign, like Gore's, chose not to dignify obvious lies by responding, and the press lagged behind the story as it gained traction. Discrediting Kerry's greatest biographical asset was calculated to compensate for Bush's hidden liability. In February 2004, the Washington Post followed on the Boston Globe articles of 2000, and its reporters were unable to find anyone that could corroborate Bush's claim that he had served at an Alabama air base in 1972. To an aggressive journalist like Mapes it seemed logical to examine Bush's National Guard story, which remained a mystery. The opaque story was partly illuminated by a piece in Salon, written by Mary Jacoby, on Sept. 2, 2004. Offering extensive documentation, including photographs and letters, Linda Allison, who had housed Bush during his missing year, explained that his drunken misbehavior was creating havoc for his father's political aspirations and that the elder Bush asked his old friend Jimmy Allison, a political consultant from Midland, Texas, now living in Alabama, to handle the wastrel son. "The impression I had was that Georgie was raising a lot of hell in Houston, getting in trouble and embarrassing the family, and they just really wanted to get him out of Houston and under Jimmy's wing," Linda Allison told Salon. During the time the younger Bush was under the watchful eye of the Allisons, he never went to a National Guard base or wore a uniform. "Good lord, no. I had no idea that the National Guard was involved in his life in any way," said Allison. She did, however, remember him drinking, urinating on a car, screaming at police and trashing the apartment he had rented. On Sept. 8, "60 Minutes II" broadcast its story. It featured former Texas Lt. Gov. Ben Barnes, a Democrat, who disclosed that just before George W. Bush would be eligible for the draft, a mutual friend of then Rep. George H.W. Bush asked him to help procure the younger Bush a spot in the "Champagne Unit." Barnes appeared on camera, saying: "It's been a long time ago, but he said basically would I help young George Bush get in the Air National Guard. I was a young, ambitious politician doing what I thought was acceptable. It was important to make friends. And I recommended a lot of people for the National Guard during the Vietnam era -- as speaker of the House and as lieutenant governor. I would describe it as preferential treatment." Then Rather, acting as correspondent, introduced new material drawn from the files of Col. Jerry Killian, Bush's squadron commander: "'60 Minutes' has obtained a number of documents we are told were taken from Col. Killian's personal file. Among them, a never-before-seen memorandum from May 1972, where Killian writes that Lt. Bush called him to talk about 'how he can get out of coming to drill from now through November.' Lt. Bush tells his commander 'he is working on a campaign in Alabama ... and may not have time to take his physical.' Killian adds that he thinks Lt. Bush has gone over his head, and is 'talking to someone upstairs.'" Another Killian memo contained the coup de grâce: "I ordered that 1st Lt. Bush be suspended not just for failing to take a physical ... but for failing to perform to U.S. Air Force/Texas Air National Guard standards. The officer [then Lt. Bush] has made no attempt to meet his training certification or flight physical." Within minutes of the conclusion of the broadcast, conservative bloggers launched a counterattack. The chief of these critics was a Republican Party activist in Georgia. Almost certainly, these bloggers, who had been part of meetings or conference calls organized by Karl Rove's political operation, coordinated their actions with Rove's office. Questioned for the "60 Minutes" story, White House communications director Dan Bartlett had not denied the story but simply characterized it as "dirty." The right-wing bloggers raised questions about the authenticity of the Killian documents, arguing that typewriters of the time lacked the specific superscript in the documents, that the proportional spacing was wrong and the font anachronistic, and that therefore they were likely fabricated on a computer. Various handwriting and typewriter experts weighed in, some challenging the documents' authenticity. The press almost uniformly took the absence of a universal opinion of experts as proof of the documents' falsity. Because they could not be proved with complete certainty to be authentic, they must be counterfeit. While the battle over the authenticity experts and assorted inconclusive sources continued, CBS interviewed Marian Carr Knox, who had been Col. Killian's assistant when the memos were allegedly produced. She didn't recall typing them and didn't believe Killian had written them (though various handwriting experts had verified his signature), but she also asserted, "The information in here is correct." Under fire, CBS executives reeled backward. On Sept. 20, Heyward issued an apology: "Based on what we now know, CBS News cannot prove that the documents are authentic, which is the only acceptable journalistic standard to justify using them in the report. We should not have used them. That was a mistake, which we deeply regret." And Rather chimed in: "If I knew then what I know now -- I would not have gone ahead with the story as it was aired, and I certainly would not have used the documents in question." With these self-abasing mea culpas (Rather claims in his complaint that his statement was "coerced"), the veracity of the story about Bush's past seemed to be settled in his favor. But the underlying facts of the story were not discredited; nor was the authenticity of the documents resolved. The day after these apologies CBS announced the creation of a review panel to determine "what errors occurred." Two Bush family loyalists, Richard Thornburgh, former attorney general in the elder Bush's administration, and Louis Boccardi, former executive editor and CEO of the Associated Press, were chosen to head the internal investigation. Thornburgh had been the subject of critical Rather reports, while Boccardi felt close and indebted to the elder Bush for being helpful as vice president in gaining the release of AP reporter Terry Anderson, held hostage for six years in Lebanon. Lawyers in Thornburgh's firm with no background in journalism and media performed the real work of the panel and wrote its final report. As the panel called witnesses, Sumner Redstone, CEO of Viacom (CBS's owner), declared his interest in the 2004 election. "I look at the election from what's good for Viacom. I vote for what's good for Viacom. I vote, today, Viacom," he said. In fact, Viacom had a number of crucial issues before the Federal Communications Commission, including loosening media ownership rules. "I don't want to denigrate Kerry," said Redstone, "but from a Viacom standpoint, the election of a Republican administration is a better deal. Because the Republican administration has stood for many things we believe in, deregulation and so on. The Democrats are not bad people ... But from a Viacom standpoint, we believe the election of a Republican administration is better for our company." Rather believed that the panel would conduct a fair-minded inquiry. But he learned that neither he nor Mapes would be allowed to cross-examine witnesses. They heard from some researchers on the "60 Minutes II" staff that before they had been questioned, a CBS executive had told them that they should feel free to pin all blame on Rather and Mapes. CBS had told Rather to cease investigating the story and had even hired a private investigator of its own, Erik Rigler. Rather and Mapes discovered that Rigler's investigation had uncovered corroboration for their story. Rather's complaint states that "after following all the leads given to him by Ms. Mapes, he [Rigler] was of the opinion that the Killian Documents were most likely authentic, and that the underlying story was certainly accurate." But rather than probing Rigler on his findings, the panel, to the extent its lawyers questioned him in a single telephone call, "appeared more interested whether Mr. Rigler had uncovered derogatory information concerning Mr. Rather or Ms. Mapes, as to which he had no information," according to the Rather complaint. Rigler's report was suppressed, never presented to the panel, and remains suppressed by CBS. Nor did the panel fully question James Pierce, the handwriting expert consulted by "60 Minutes" who insisted that the signature on the documents was surely Killian's. When Mapes appeared before the panel, she was harshly questioned at length about her use of the word "horseshit." On the issue of the special privileges granted to those sons of wealth in the "Champagne Unit," Thornburgh asked her, "Mary, don't you think it's possible that all these fine young men got in on their own merits?" When it came to the merits of the facts the panel elided them. It never addressed the facts at all. Instead it criticized the "60 Minutes" team for failing to "obtain clear authentication" of the Killian documents, among other "errors," though it admitted it could not prove one way or another whether they were inauthentic. Mapes and three other producers were dismissed. "60 Minutes II" was abolished. And on the day after Bush's reelection, Rather was unceremoniously fired. His contract had called for him to continue as anchor for an additional year and then to serve as a correspondent for "60 Minutes" and "60 Minutes II," but that promise was not honored. CBS believed that by severing its link with Rather it could put the whole incident behind it and begin a new happy relationship with the ascendant Republicans. An article by James Goodale, former vice chairman and general counsel of the New York Times, in the New York Review of Books on April 7, 2005, and his subsequent exchange with Thornburgh and Boccardi, went little noticed. Goodale found the panel's report filled with flaws, lacking a factual basis, revealing an absence of due diligence and due process, and substituting empty legal concepts and language for any understanding of the actual gritty practice of journalism. Goodale determined that the "underlying facts of Rather's '60 Minutes' report are substantially true." He observed, "Since the broadcast, no one has come forward to say the program was untruthful." Goodale's summation rejected the report and left its credibility in tatters: "The rest of the report, which is directed to the newsgathering process of CBS, is flawed. The panel was unable to decide whether the documents were authentic or not. It didn't hire its own experts. It didn't interview the principal expert for CBS. It all but ignored an important argument for authenticating the documents -- 'meshing.' It did not allow cross-examination. It introduced a standard for document authentication very difficult for news organizations to meet -- 'chain of custody' -- and, lastly, it characterized parts of the broadcast as false, misleading, or both, in a way that is close to nonsensical. One is tempted to say that the report has as many flaws as the flaws it believes it has found in Dan Rather's CBS broadcast." But Goodale's magisterial and experienced voice seemed to be a faint cry in the wilderness. Who, after all, cared anymore? In November 2005, Mapes published a memoir, "Truth and Duty," containing her memo to Thornburgh and Boccardi that they had failed to include in the appendix of the panel's report, although they reproduced many other memos and documents. Mapes' argument was that the Killian documents "meshed" with the facts in precise and nuanced ways. "The Killian memos, when married to the official documents, fit like a glove," she wrote. "There is not a date, or a name, or an action out of place. Nor does the content of the Killian memos differ in any way from the information that has come out after our story ... In order to conclude that the documents are forged or utterly unreliable, two questions must be answered: 1) how could anyone have forged such pristinely accurate information; and 2) why would anyone have taken such great pains to forge the truth?" But Mapes' book, like Goodale's article, was all but ignored. Rather has always been an uncomfortable figure, sometimes abrasive, sometimes strangely inappropriate or baffling, given to rustic rhetoric at odd moments, and sometimes and suddenly lapsing into teary sentimentality or bursts of patriotic doggerel. Since his confrontations as the correspondent covering the Nixon White House, conservatives have targeted him as a symbol of the despised "liberal media." However idiosyncratic, Rather stood for the remnants of CBS's tradition of speaking truth to power, as Edward R. Murrow did finally about Sen. Joseph McCarthy and Walter Cronkite did finally about the Vietnam War and Watergate. The corporate unease with Murrow's outspokenness, leading to the cancellation of his weekly program, "See It Now" (depicted in the recent film "Good Night, and Good Luck"), was little different from the unease with Rather a half-century later. At last, the corporation's necessity for demonizing Rather coincided with the long-standing conservative demonizing. When CBS replaced the edgy Rather with the sugary Katie Couric as anchor of the "Evening News," it imagined it had solved its problem, its "errors." The news would get softer, the Republicans in control of the White House and Congress would be nicer, Viacom would grab more media, and ratings would climb. Thus, dismissing Rather would yield untold dividends. Unfortunately for CBS's visionaries, none of that has worked out as planned. Couric simply lacks basic journalistic instincts and skills, and the "CBS Evening News" is at rock bottom in ratings and sinking farther. Rather could have simply allowed the statute of limitations to run out, lived off his millions, and faded away. But the incident ate at him. On one level, the Bush National Guard story is about Bush and the National Guard. On another, of course, it is about Rather's reputation. But on yet another it is about CBS's overwhelming desire to please the Bush White House and censor itself. The White House campaign against Rather has been so successful that many in the national press corps behave as though in mouthing its talking points they are demonstrating their own independent thought. On Sept. 20, the day after he filed his suit, Rather said, "The story was true." Rather's suit may turn into one of the most sustained and informative acts of investigative journalism in his long career. He is not going gentle into that good night. http://www.salon.com/opinion/blument...n_rather_suit/  Boulder High Students Walk Out During Pledge, Recite Own Version AP About 50 Boulder High School students walked out of class Thursday to protest the daily reading of the Pledge of Allegiance and recited their own version, omitting "one nation, under God." The students say the phrase violates the constitutional separation of church and state. They also say the daily reading of the pledge over the school public address system at the start of the second class takes away from education time and is ignored or mocked by some students. A state law passed in 2004 requires schools to offer the opportunity to recite the pledge each day but does not require students to participate. The protesting students, members of the Student Worker Club, want administrators to hold the pledge reading in the auditorium during each of the school's two lunch periods for any students who want to participate. Otherwise, they said, they plan to walk out each Thursday when the pledge is read and recite their version, which omits the reference to God and adds allegiance to constitutional rights, diversity and freedom, among other things. "Boulder High has a highly diverse population, not all of whom believe in God, or one God," said Emma Martens, a senior and president of the club, which has about a dozen members. "We didn't think it was fair for the whole school to have to listen to it. It's almost religious oppression," she said. Principal Bud Jenkins told the Camera newspaper on its Web site Thursday the pledge will not be moved, but added he was proud of the students for standing up for their beliefs. It was not immediately clear what discipline, if any, the protesting students would face. http://www.denverpost.com/ci_7016257#  When Jim Crow Came to Town, With Eviction Notices Manohla Dargis There are ghosts haunting Marco Williams’s quietly sorrowful documentary “Banished,” about the forced expulsion of black Southerners from their homes in the troubled and violent decades after the Civil War. Dressed in what looks like their Sunday best, in dark suits and high-collar dresses, they stare solemnly into an unwelcoming world. A couple ride in a cart along a pretty country road, and others stand awkwardly before houses with peeling paint. There are few smiles. Photography was then a serious business, though being a black landowner, part of a fragile, nascent Southern middle class, was more serious still. It’s stunning how loudly the dead can speak, and with such eloquence. I couldn’t help comparing these images with those in one of my own photo albums of a large family of stern-looking Midwesterners dressed in what looks like their Sunday best. The rough, ill-fitting suits and somber dresses look similar to those in the documentary, and the simple clapboard house looming behind this family recalls comparable homes in “Banished.” There are, once again, few smiles, though in one photo my grandfather, then around 12, looks as if he’s trying to keep one in check. Unlike the young men in Mr. Williams’s documentary, my grandfather raised a family and ran a business not far from where his photographs were taken — an upstanding white citizen in a nearly all-white land. The young black men in “Banished” never had the chance to take root. Some were falsely accused of molesting white women and were lynched. We see a few of these dead in other photographs, hanging from trees and lampposts, their bodies sometimes surrounded by a visibly excited white crowd. (A crude sign under one corpse warns not to wake him.) As Mr. Williams explains, his measured voice-over calm as ever, lynching was an instrument of terror, used against blacks as a means of control and “racial cleansing.” Mr. Williams isn’t one for hysterics or histrionics, even when seated across from a Ku Klux Klan leader who says he wouldn’t be happy if this African-American director moved in next door. The Klan leader lives in a nice-looking house adorned with white supremacist banners in Forsyth County, Ga., which in 1912 brutally expelled an estimated 1,000 of its black residents. Mr. Williams guides us through this terrible history, often while strolling on camera through the scene of the crime, talking to white residents and dredging up memories. He also uncovers some repellent images of a white mob trying to stop a peaceful, interracial civil rights march in the county in 1987. The marchers sing “We Shall Overcome.” The mob throws rocks. There is so much more to the story than can be told by this 87-minute movie, which only casts glances at Reconstruction, the question of reparations and the bitter, enduring, living legacy of slavery. Although Mr. Williams somewhat overstates his case when he says that racial cleansing has “remained hidden,” there’s no denying that this ugly chapter deserves more than an occasional well-meaning documentary. (A national day of mourning might be a good start.) The 1997 fiction film “Rosewood” recounted one such expulsion that took place in central Florida in the 1920s, and journalists, activists and descendants, including those who appear in “Banished,” have dug into the archives and sifted through the evidence. Mr. Williams has done his own part to shed needed light, though I wish he had dug longer, harder. In late 2006 The News & Observer in Raleigh, N.C., published a series about an 1898 white riot to destroy a political alliance between blacks and poor whites in Wilmington, N.C., where the literacy rates for black men were higher than those for whites. One agitator, a former Confederate soldier and the future mayor of Wilmington, vowed that he and other like-minded whites would never surrender “even if we have to choke the Cape Fear River with carcasses.” What followed was a coup d’état, possibly the only time that a municipal government was toppled in American history. Black residents were murdered; the local black newspaper was torched, and survivors exiled. Reconstruction died, and Jim Crow moved right in. BANISHED Opens today in Manhattan. Directed by Marco Williams; written by Maia Harris and Mr. Williams; director of photography, Stephen McCarthy; edited by Kathryn Barnier and Sandra Christie; music by David Murray; produced by Mr. Williams and Ms. Harris. At the Film Forum, 209 West Houston Street, west of Avenue of the Americas, South Village. Running time: 87 minutes. This film is not rated. http://movies.nytimes.com/2007/09/26/movies/26bani.html  Best Buy Adds Disclaimer To Secret Website In response to being sued and humiliated on the internet over their "secret website," reader MK says Best Buy has added a disclaimer that warns customers that the in-store kiosk doesn't display the same prices as the public website. For those of you new to this issue, Best Buy was caught using a duplicate website to fool customers who tried to compare internet prices with in-store prices. Customers who asked why the price was higher in the store were often told that "the sale must have ended" in the time it took them to drive to the store. They were then told to "check the website" to see for themselves, then were shown an identical-looking website that displayed different "in-store" prices. We think Connecticut Attorney General Richard Blumenthal said it best back in May (right after he sued Best Buy): "Best Buy gave consumers the worst deal - a bait-and-switch-plus scheme luring consumers into stores with promised online discounts, only to charge higher in-store prices," Blumenthal said. "The company commonly kept two sets of prices - one on its Internet site and an often higher set on its in-store, look-alike, available on kiosks. The in-store site was an Internet look-alike, commonly with higher prices, which were charged to consumers. Best Buy broke its promise to give the best price - an Internet version of bait-and-switch - a technological bait-and-switch-plus. "Best Buy used in-store kiosks to conceal lower online prices and renege on its price match guarantee. Consumers seeking bargains were led to believe that lower online prices had expired or never existed. Best Buy treated its customers like suckers, not patrons to be prized." We hope this disclaimer puts a stop to that sort of behavior. http://consumerist.com/consumer/upda...ite-303124.php  Knocked Off by a Bargain A consumer reporter learns the whole world is a street corner when he shops online for a set of earphones and finds a price too good to be true. David Colker I make my living writing about scams. Check-cashing schemes, Nigerian frauds, fake Viagra -- I've covered them all. And in the back of my mind was always the sense that the victims must be a bit greedy or stupid. Like me. My comeuppance came this year when I went shopping online for high-end earphones and ended up with a fake. And I don't mean crude knockoffs. I thought I was getting a brand-name product at a bargain price by being a smart shopper, just like my flea-market-loving mom taught me. Lately, fake merchandise has become a genuine menace, moving far beyond the bogus Rolexes and Louis Vuitton handbags that have been sold for decades with a wink and a nod. Counterfeit toothpaste showed up in discount stores in June and fake wine has been popping up at auctions. In May, the Food and Drug Administration warned about counterfeit versions of the Xenical weight-loss drug purchased by consumers online. The Internet opens up new vistas for hunting down the lowest possible price. And for getting scammed. "It used to be that counterfeits was what you saw on a street corner in New York," market researcher Lauren Freedman said. "Now the whole world is a street corner." When the Sennheiser CX-300 earphones arrived, they looked perfect. The black earbuds were adorned with company logos, the asymmetric cord was just the right length and the silver plug fit an iPod perfectly. They came in a snazzy Sennheiser package with text in six languages. I had wanted a set of these earphones ever since I gave them a rave review last year in The Times. They sounded great and fit snugly in the ear. Perfect for gym workouts, just in case I ever got back to the gym. List price -- $79.99. But only a fool pays list. Amazon.com had them for about $65. I wasn't about to stop there. On the same Amazon product page was a link to Amazon Marketplace, where anyone can put an item up for sale. That's where the CX-300s were being offered for less than $25. A drop from list price of more than 66% raised a warning flag, even though the seller with the best price, Wifipro, had a positive customer feedback rating. I wrote him an e-mail asking: Was the product, at his price of $24.99, used, refurbished or damaged? Wifipro's reply: "These units are brand spanking new in factory blister pack, not returns, not used and not refurbished. "They are a beautiful product at an unbelievable price." I was sold. The price was so good, I almost felt like a bandit. Indeed, it was a "beautiful product." But only, as it turns out, if you admire the work of counterfeiters. Counterfeit electronic products have a history of being so obviously flawed that they're jokes. For example, U.S. Customs and Border Protection officials in Long Beach recently displayed seized packs of what was intended to look like Duracell batteries, except that the label read "Dinacell." These days, no one in the industry is laughing much. "I've seen fakes with our case, our logo, our address, even our instruction booklet, all faithfully reproduced, " said Lou Lenzi, a senior vice president for product management at Audiovox Corp., which makes a variety of electronics. When the CX-300s arrived from Wifipro, I removed the medium-size cushions from the earbuds and tried replacing them with the smaller ones included in the package to better fit my ears. But they wouldn't stretch over the earbuds, no matter how much I pulled on them. I figured someone else must have run into the same problem, so I did a search on the Web. That's when I first came across a site: "How to spot fake Sennheiser cx300." Still no worries. The fake depicted was a crude copy. But further digging made it clear there were several different fakes in circulation. Finally, I happened upon a posting from a man who had bought a set identical to mine, also at a huge discount. He had sent a picture to Sennheiser and got a reply that the earphones "are almost certainly fake." My heart sank. Now I knew what it was like to get cheated online. It was made worse by the fact that I thought myself so clever for getting such a bargain. I sent the earphones to Sennheiser's experts, who said they were among the best counterfeits they had seen. There was a clue, right on the front of the package. "Look on the front where it says 'Blocks Outside Noise,' " said Uwe Sattler, technical director at Sennheiser. Under that, in the German translation, was the word Aussengerauche. "They forgot the umlaut -- the two little dots -- over the second 'a,' " Sattler said. Ah, the mystery of the missing umlaut. If I had been the German version of one of the Hardy Boys, I might have caught it. "The fakes," said Jeff Alexander, Sennheiser's U.S. marketing chief, "are getting so much better." And not just of Sennheiser products. Counterfeits of Audiovox's universal remote controls, sold under the RCA brand, have been cropping up worldwide. "It used to be that you needed a very sophisticated facility to produce something like that," Lenzi said, "but now the technology is so widely available." The counterfeiters start with reverse engineering to study the design and components, he said. Then, plastic injection machines and circuit board printers can be programmed to make a clone. Up to a point. The emphasis is on appearance, not functionality. "It only has to be in good-enough operating condition to function, at least some," Lenzi said. The counterfeit CX-300s varied greatly in audio quality. Andy Ukasick of Milwaukee bought a pair on EBay that he learned were fakes. "They sounded terrible," he said in an interview. "No better than what you could pick up for $3." Ian Moore of Chester, England, who got his on Amazon Marketplace, fared better. "The sound was good, but not what you expect from Sennheiser," he said. "There was no real bass." Moore sent an e-mail to the seller, questioning the product's validity. He immediately got a reply from a Mr. Hussain, offering a full refund. "Then I knew they were fakes," Moore said. "You expect the seller to say, 'How dare you.' But he was very apologetic." Ukasick also got a quick refund from his seller -- Wifipro. Iset out to find the man behind the moniker, Sidney Jacobs. It wasn't hard -- his name and return address were on the package the earphones arrived in. He operates his business in Southern California, only about 30 miles from my home. Jacobs, 66, wasn't trying to hide. His picture was in his EBay seller's profile, where he described himself as a "Vietnam-era Vet" who had worked for large corporations. "I have said goodbye to the business suits, stuffed shirts and power ties," Jacobs wrote. According to comments left on EBay and Amazon Marketplace, buyers started to identify the earphones as counterfeit in July, shortly after Jacobs began selling them. At first, he made fun of doubters. "This is a very sick person," Jacobs wrote in response to negative feedback from an EBay buyer. It was time to give Jacobs a call. He said that to start his online sales company, he bought Sennheiser earphones from an offshore distributor which he declined to identify. I told him that Sennheiser confirmed that the earphones he sold me were counterfeit. Jacobs didn't express shock but blamed the distributor. "I had asked about the legitimacy of the products," Jacobs said, "and they said 'Yes, yes. They're the real thing.' " Jacobs said he didn't know there might be a problem until several buyers questioned the authenticity of his earphones. Jacobs said they all got refunds. And with word getting around the Web about fake CX-300s, he prepared a note for customers. It was sent to potential buyers who specifically asked by e-mail if the earphones he was selling were the real thing. "My products are in original factory package," said the note. "They look great and sound great. That being said, I will not guarantee with 100% certainty that they are genuine." No such warning appeared on his selling sites. Jacobs said he couldn't send the earphones back to the distributor. And he had a tale of woe -- a son still living at home, a mother-in-law with serious health problems. "I have several thousand dollars invested in these items," Jacobs said. Besides, he was never completely convinced all his earphones were counterfeit. He pointed out that most of his customers, as evident in his feedback, were happy with the earphones they had received at a huge discount. Jacobs asked if his name could be kept out of the newspaper. I told him no. Finally, the specter of being identified as the seller of counterfeit goods outweighed the financial loss. "You have put fear in my heart," Jacobs said. The earphones had to go. "I am removing them immediately," he said, typing frantically in the background. "There, they are gone." Shortly after we spoke, $24.99 plus $4.99 for shipping was returned to my credit card account. That was a surprise. I never asked for a refund, between feeling slightly sorry for the guy and fretting about my journalistic ethics -- after all, I was getting a story out of it. Of course, counterfeits are still out there. Plenty of sellers still offer CX-300s at prices as low as $15 on the Internet. I used to love to find bargains like that. Getting scammed was a good lesson, but it also took some of the fun out of the hunt. "You know the old saying about, 'If it's too good to be true it probably isn't'?" said Freedman, the e-commerce analyst. "Well, it's true." My mom used to say that, too. It was the part of her shopping lesson I relearned the hard way. http://www.latimes.com/business/la-f...la-home-center  Real iTunes Killer: Review of Amazon's DRM-Less Music Download Store Danny Mendez Amazon's long awaited DRM-less music download store just hit the web, and, for a moment there, I thought it might have become vaporware. Thankfully, that didn't turn out to be the case, giving me a chance to put the store through its paces. Here's my review of the Amazon MP3 Download Store. Amazon is going out on a limb here, offering DRM-less MP3 tracks at 256kbps at $0.89 per song. DRM-less music download stores have been done before, but they usually lack in music selection. Amazon is looking to change the music download world by giving users the opportunity to do anything they want with their music while offering a huge selection of both popular and unpopular/underground artists, but does it do this well? Selection: What does it offer? Because of my past experience with DRM-less music stores, I was expecting disappointment when I started searching for artists. Boy, I couldn't have been more wrong. Amazon turned up multiple albums for nearly every artist I typed into the search box, and, for the few that it didn't find, it offered physical CDs for purchase through Amazon's traditional store. Some of the artists I found include: Immortal Technique, Barry White, Kanye West, Sublime, Snoop Dog, NWA Minus the Bear, Psycostick, Royksopp, Sinai Beach, Yellowman, Madonna, Eminem, Paul Oakenfold, Pink Floyd, Guns N' Roses, Underoath, Maroon 5, The Rolling Stones, He is Legend, Johnny Cash, and more. Unfortunately, and this would be expected from any download store, I was unable to find a significant amount of the much smaller bands that I listen to; however, the MP3 Download Store is still in beta form with new content being added every day. Regardless, the selection is overall impressive. Pricing: Is it worth it? Pricing for an individual song is $0.89 as opposed to iTunes, which offers singles at $0.99 a piece. Albums range anywhere from under two dollars to over over $20. Generally, I found pricing to be the same as or less than what is offered in the iTunes store. For example, DJ Tiesto's Just Be goes for $6.99 on Amazon's MP3 Download Store, but it goes for $9.99 at the iTunes store. However, Paul van Dyk's Global costs $12.99 at both stores. Never did I find an album to be more expensive at the Amazon store and I wouldn't expect it as Amazon is strongly going after value. An added benefit of downloading your music via Amazon as opposed to iTunes is the lack of DRM. Most of iTunes' music comes encoded with DRM, preventing you from using YOUR music on anything other than an iPod or the computer to which the music is registered. iTunes music also comes in AAC format at 192kbps, a music format that is not supported on many other devices. Amazon's music comes in MP3 format at 256kps, a format that is largely supported on other devices and the higher bitrate provides for better sound quality. In fairness, I should note that Apple offers a small portion of their content DRM-free at 256kbps AAC, but that only applies to any music from the record label EMI. The Download Experience In order to download music via Amazon, you first have to install the Amazon download manager, which is required for albums but not for singles. The installation was really easy on my iMac, which only required a few clicks and not even a drag-and-drop to the Applications folder. I'm sure the process would have been just as easy on a Windows machine. Similar to iTunes, Amazon lets you preview most tracks before you download them. This came in really hand as I searched for an album to purchase. I found Pauk van Dyk's Global, tested it, and went through with the purchase. I already had an Amazon account, so all I had to do is click the "Buy MP3 album with 1-Click" and it was mine. When you purchase an album, your computer downloads a very small file. Normally, you can open this file automatically in the Amazon download manager without it touching your desktop, but I accidentally downloaded it directly to my desktop. I simply double clicked the file, and the manager opened up. The time it took to download the songs took a bit longer than expected. I was expecting it to be just as quick as iTunes, but that was not the case. Although, faster than anything I've ever experienced downloading via P2P, the slower-than-iTunes download speed could have been attributed to my college network being on overhaul around this time of the day, mid afternoon. Either way, it took about 10-15 minutes to download Global, which consists of 10 eight minute songs. As each song finished downloading, the download manager placed the files conveniently in their correct artist and album folders in my iTunes music folder. Here's the Deal The Amazon MP3 Download Store is absolutely great. Even in it's beta stage I can confidently call it the best online download store - period. Simply the fact that it offers its vast selection of music without DRM makes it better than iTunes, and iTunes doesn't stand a chance when it comes to pricing. There's also no monthly fee, a feature that gives eMusic great value but forces you to pay the fee up front every month, which could easily go to waste as my problem with eMusic is that I could hardly find anything of interest to me. Apple better act quick if it wants to keep up because, as of today, all that's going for the iTunes Store is its popularity. DRM on music is dead, and any company that doesn't understand that is going to get left in the dust. But those that embrace the changing times are going to be looking at a profitable future. http://tech.blorge.com/Structure:%20...ownload-store/  An Oracle Part Man, Part Machine George Johnson IN the 12th century A.D., when the Arabic treatise “On the Hindu Art of Reckoning” was translated into Latin, the modern decimal system was bestowed on the Western world — an advance that can best be appreciated by trying to do long division with Roman numerals. The name of the author, the Baghdad scholar Muhammad ibn Musa al-Khwarizmi, was Latinized as Algoritmi, which mutated somehow into algorismus and, in English, algorithm — meaning nothing more than a recipe for solving problems step by step. It was the Internet that stripped the word of its innocence. Algorithms, as closely guarded as state secrets, buy and sell stocks and mortgage-backed securities, sometimes with a dispassionate zeal that crashes markets. Algorithms promise to find the news that fits you, and even your perfect mate. You can’t visit Amazon.com without being confronted with a list of books and other products that the Great Algoritmi recommends. Its intuitions, of course, are just calculations — given enough time they could be carried out with stones. But when so much data is processed so rapidly, the effect is oracular and almost opaque. Even with a peek at the cybernetic trade secrets, you probably couldn’t unwind the computations. As you sit with your eHarmony spouse watching the movies Netflix prescribes, you might as well be an avatar in Second Life. You have been absorbed into the operating system. Last week, when executives at MySpace told of new algorithms that will mine the information on users’ personal pages and summon targeted ads, the news hardly caused a stir. The idea of automating what used to be called judgment has gone from radical to commonplace. What is spreading through the Web is not exactly artificial intelligence. For all the research that has gone into cognitive and computer science, the brain’s most formidable algorithms — those used to recognize images or sounds or understand language — have eluded simulation. The alternative has been to incorporate people, with their special skills, as components of the Net. Go to Google Image Labeler (images.google.com/imagelabeler) and you are randomly matched with another bored Web surfer — in Korea, maybe, or Omaha — who has agreed to play a game. Google shows you both a series of pictures peeled from the Web — the sun setting over the ocean or a comet streaking through space — and you earn points by typing as many descriptive words as you can. The results are stored and analyzed, and through this human-machine symbiosis, Google’s image-searching algorithms are incrementally refined. The project is still experimental. But the concept is not so different from what happens routinely during a Google search. The network of computers answering your query pays attention to which results you choose to read. You’re gathering data from the network while the network is gathering data about you. The result is a statistical accretion of what people — those beings who clack away at the keys — are looking for, a rough sense of what their language means. In the 1950s William Ross Ashby, a British psychiatrist and cyberneticist, anticipated something like this merger when he wrote about intelligence amplification — human thinking leveraged by machines. But it is both kinds of intelligence, biological and electronic, that are being amplified. Unlike the grinning cyborgs envisioned by science fiction, the splicing is not between hardware and wetware but between software running on two different platforms. Several years ago, SETI@home became a vehicle for computer owners to donate their spare processing cycles for the intense number-crunching needed to sift radio-telescope data for signs of extraterrestrial life. Now a site run by Amazon.com, the Mechanical Turk (www.mturk.com), asks you to lend your brain. Named for an 18th-century chess-playing automaton that turned out to have a human hidden inside, the Mechanical Turk offers volunteers a chance to search for the missing aviator Steve Fossett by examining satellite photos. Or you can earn a few pennies at a time by performing other chores that flummox computers: categorizing Web sites (“sexually explicit, “arts and entertainment,” “automotive”), identifying objects in video frames, summarizing or paraphrasing snippets of text, transcribing audio recordings — specialties at which neural algorithms excel. (Not all of these Human Intelligence Tasks, or HITs, as Amazon calls them, involve serving as a chip in some entrepreneur’s machine. Hoping to draw more traffic to their sites, bloggers are using the Mechanical Turk to solicit comments for their online postings. In some cases you get precisely 2 cents for your opinion.) In his 1950 paper “Computing Machinery and Intelligence,” Alan Turing foresaw a day when it would be hard to tell the difference between the responses of a computer and a human being. What he may not have envisioned is how thoroughly the boundary would blur. How do you categorize Wikipedia, a constantly buzzing mechanism with replaceable human parts? Submit an article or change one and a swarm of warm- and sometimes hot-blooded proofreading routines go to work making corrections and corrections to the corrections. Or maybe the mercurial encyclopedia is more like an organism with an immune system of human leukocytes guarding its integrity. (Biology too is algorithmic, beginning with the genetic code.) When the objectivity of Wikipedia was threatened by tweaking from special interests — a kind of autoimmune disease — another level of protection evolved: a Web site called WikiScanner that reports the Internet address of the offender. Someone at PepsiCo, for example, removed references about the health effects of its flagship soft drink. With enough computing power the monitoring could be semiautomated — scanning the database constantly and flagging suspicious edits for humans to inspect. No one but a utopian would have predicted how readily people will work for free. We’re cheaper than hardware — a good thing considering how hard we are to duplicate. http://www.nytimes.com/2007/09/23/we...=1&oref=slogin  Victorious RIAA Defendant Gets Attorneys' Fees, Turns to Class-Action Plans Eric Bangeman Calling the RIAA's case unjustified "as a reasonable exploration of the boundaries of copyright law," a federal magistrate judge late last week awarded former RIAA defendant Tanya Andersen attorneys' fees for her nearly two-and-a-half-year fight against a copyright infringement lawsuit. RIAA spends thousands to obtain $300 judgment Andersen is a disabled single mother living in Oregon with her now 10-year-old daughter. In February 2005, she was sued by the record labels, which accused her of using KaZaA to distribute gangster rap under the handle "gotenkito." From the outset, she denied all wrongdoing, and in October of that year, filed a countersuit against the record industry, accusing it of racketeering, fraud, and deceptive business practices. The RIAA continued to press its legal claims against Andersen, despite any evidence other than an IP address tying her to the alleged infringement. Andersen even provided the name, address, and phone number of the person she believed was responsible for the "gotenkito" account. Inexplicably, the RIAA chose not to contact him for over two years, then chose to take his denial at face value, choosing instead to continue prosecuting the case against Andersen. Throughout its prosecution of the case, Andersen accused the RIAA of underhanded investigative tactics. These included what Andersen describes as inappropriate attempts to contact her daughter. In one instance, the RIAA's investigators allegedly contacted her elementary school, posing as a relative in an attempt to speak with then-eight-year-old Kylee Andersen about the alleged infringement. Even the RIAA's own forensic investigator reported that he could not find "any evidence whatsoever" that Andersen had used KaZaA. In June of this year, the RIAA finally came to the conclusion that it had an unwinnable case and decided to drop the case prior to its going to trial. The parties stipulated to a dismissal with prejudice—unusual for the RIAA, since it made Andersen the prevailing party and eligible for attorneys' fees. Andersen dismissed her counterclaims without prejudice (meaning she can refile them) after she filed a malicious prosecution lawsuit against the RIAA. In his order awarding Andersen attorneys' fees, US Magistrate Judge Donald C. Ashmanskas noted that he had to make a decision on this case "without ever addressing the merits of the claims or the counterclaims." Despite that, Judge Ashmanskas noted that there had been a "material alteration of the legal relationship of the parties," and that with the sole exception of attorneys' fees, Andersen had gotten "all the relief available to a defendant of a claim for copyright infringement." Judge Ashmanskas also cited the RIAA's admission that the "evidence uncovered during discovery proved inconsistent and inconclusive," a fact for which the labels could provide no explanation. He concludes that the RIAA lacked the prima facie evidence to support the claims of infringement. "Whatever plaintiffs' reasons for the manner in which they have prosecuted this case, it does not appear to be justified as a reasonable exploration of the boundaries of copyright law," wrote the judge. "Copyright holders generally, and these plaintiffs specifically, should be deterred from prosecuting infringement claims as plaintiffs did in this case." While Andersen's attorney adds up the bills, Andersen is seeking class-action status for her malicious prosecution lawsuit. Saying that the RIAA "has engaged in a coordinated enterprise to pursue a scheme of threatening and intimidating litigation in an attempt to maintain its music distribution monopoly," Andersen wants to make a class from those who have been wrongfully sued by the RIAA; if successful, the RIAA could find itself locked in a long and costly legal battle. http://arstechnica.com/news.ars/post...ion-plans.html  Not Much Anonymity for Unprotected File-Sharers UC Riverside researchers examine peer to peer networks The same technology that allows easy sharing of music, movies and other content across a network also allows government and media companies easy access to who is illegally downloading that content. In a paper called “P2P: Is Big Brother Watching You?” (PDF) three University of California, Riverside researchers show that a substantial number of people on file sharing networks, approximately 15 percent, are there to troll for illegal file sharing activity on behalf of the recording industry or the government. Graduate student Anirban Banerjee, and computer science professors Michalis Faloutsos and Laxmi Bhuyan, decided to find out whether file-sharers are always being observed. Over 90 days in mid-2006 they recorded file-sharing traffic on Gnutella, a common fire-sharing network. “We found that a naïve user has no chance of staying anonymous,” said Banerjee. “One hundred percent of the time, unprotected file-sharing was tracked by people there to look for copyright infringement.” However, the research showed that “blocklist” software such as (PeerGuardian, Bluetack, and Trusty Files) are fairly effective at reducing the risks of being observed down to about 1 percent. Peer to Peer networks, known as “P2P,” allow users to quickly and without cost, share movie, music and other digital files located on their individual PCs with other network users. In September 2003, the Recording Industry Association of America (RIAA) filed the first of thousands of lawsuits that targeted individuals who illegally offered copyright-protected music through P2P networks, but the action did not seem to diminish the numbers of people who shared files. The film industry is taking a similarly aggressive stance on prosecution. “P2P: Is Big Brother Watching You?” was named “best paper” at the Networking 2007 conference of the IFIP (International Federation for Information Processing) in Atlanta, GA, and was published among the conference proceedings. Since that time, the study has been the subject of some discussion at www.digg.com and www.torrentfreak.com, two popular technology-based social networking sites. “Of course no one is suggesting that illegal downloading is a good idea,” Faloutsos said. “But the P2P technology is here to stay and these industries would be better off trying to find ways to provide affordable and convenient alternatives that would allow computer users to download their products legally,” said Faloutsos. http://www.newsroom.ucr.edu/cgi-bin/display.cgi?id=1673  Downed Blogger Murray Vows to Continue Usmanov Attacks Chris Williams Former UK ambassador to Uzbekistan Craig Murray has vowed to carry on making allegations against billionaire Arsenal shareholder Alisher Usmanov, despite attempts to silence him and his supporters. Murray told The Reg: "If the man believes he was libelled then he should take me to court." Murray's blog was deleted by its host on Friday after threats from Usmanov's UK legal team. It's expected to reappear in the early hours of tomorrow on an overseas server, and will repeat the charges that drew heavy fire from specialist libel firm Schillings. The ex-diplomat says he has contacted Schillings to ask for clarification of which specific aspect of his allegations they contest, but has not received a response. "They say my book [Murder in Samarkand] is 'grossly libellous and defamatory', yet it has been widely available for a year and has sold 25,000 copies, without their actually taking any legal action," he added. Murray's criticism of Usmanov stems from his rise in Uzbekistan following the collapse of communism to become one of Russia's richest men. He denies the accusations. His profile in the UK has skyrocketed since he followed Chelsea chairman and fellow oligarch Roman Abramovich into football investment. Murray's blog entry about Usmanov, made September 2, were picked up by many political and Arsenal websites which later also received complaints from Schillings. It became the third-highest hit on Google for the search "usmanov", but was quickly removed from Murray's site after the first legal letter. Tim Ireland, who runs the political site Bloggerheads.com, which was downed along with Murray's site, has slammed Fasthosts' action (http://b-heads.blogspot.com/), and denied the claim that they refused to comply with takedown requests after he repeated Murray's allegations. Fasthosts says it acted according to standard industy practice and has declined to answer Reg questions. Ireland said Fasthosts has so far failed to provide copies of two of the three complaints made by Schillings. "We don't have any of the correspondence despite multiple requests," he said. The third complaint was made weeks after the September 2 post was removed. The takedown meant the Google robot instead indexed another piece Murray had penned in October 2005 that included the name. On contact from Fasthosts, site administrator Clive Summerfield suspended the site and wrote back to Fasthosts to suggest that it, Schillings, Ireland and Murray liase on what was acceptable. Fasthosts responded by pulling the plug on his two dedicated servers on Friday. Bloggerheads and crsigmurray.co.uk were part of a small stable of sites run by Summerfield. This connection explains the deletion of Tory mayoral hopeful Boris Johnson's site, despite it having no involvement in the Usmanov affair. The action also downed the website of the London Bach Society and an independent record label. The new hosting has been arranged separately from the rest of Summerfield's sites - Murray believes that Usmanov's lawyers are trying to make him back down by attacking others. We asked Murray if he intends to stay on Usmanov's back. He replied: "There is room on Usmanov's back for an awful lot of people. You could get even more on his stomach, and possibly lose some under the overlap of his chins." We think that's a "yes". http://www.theregister.co.uk/2007/09...manov_defiant/  Intellectual Property Laws Abused in Quest to Shutdown Lowes-Sucks.com Jacqui Cheng The tagline for home improvement superstore Lowe's may be "Let's Build Something Together," but that "something" sure isn't good PR when it comes to dealing with public criticism online. One angry customer was so dissatisfied with Lowe's work and customer service that he was spurred into putting up a web site called Lowes-Sucks.com in order to air his grievances. Lowe's was unhappy with this public display of dissatisfaction and took a "creative" approach to getting him to take it down—accusations of trademark infringement. After a bit of back and forth, Lowe's has relented by making an offer to settle out of court, but has suddenly fallen silent upon the customer's counteroffer. Let's back up a little bit. Lowe's customer and Ars Technica reader, Allen Harkleroad, had a fence installed at his home by a Lowe's "professional." Upon further inspection, however, Harkleroad discovered that the $3,500 job came complete with what he considered to be shoddy workmanship. Fence posts were loose, parts became easily disjointed, and the gate door did not fully close, among other things. Harkleroad said that his dogs were able to escape several times, and that when he complained to customer service, he was told that the installer would need to come back out to fix the fence. When he called the installer, he said that Lowe's had to tell him to go fix the fence. Harkleroad decided that he would refuse to pay the remainder of his balance until the situation was fixed, but Lowe's was having none of that. The billing department told him that it wasn't their problem and proceeded to turn Harkleroad's account over to collections. It was at this point that Lowes-Sucks.com was born, but Lowe's was having none of that either. Last week, Harkleroad received a cease-and-desist letter from the company, accusing him of unauthorized use of the company's intellectual property on his site. "Your use of the Lowe's Marks and your registration of www.Lowes-sucks.com is unauthorized by LF, distorts the goodwill of LF's federally-registered trademarks, and constitutes infringement of LF's trademark rights," reads the letter signed by Lowe's trademark manager Rebecca Green. Part of the problem with this accusation is that Harkleroad's site contains absolutely no logos, graphics, or other "marks" from Lowe's, and otherwise would not be identifiable as being related to Lowe's at all except for the name in the URL and the content of the site itself (which is unlikely to be mistaken for the company's official web site). Harkleroad also points out that the infringement notice failed to identify the alleged trademark infringements, and fails to recognize that the site is a parody. "I also might remind you that USC 15 1125(a) is in correct [sic] in regards to your claim of infringement, you need to come up with something better than that. Better go grab that US Code book you are referring from and find something that you believe matches more closely," wrote Harkleroad in response to the letter. At that point, the Electronic Frontier Foundation (EFF) hopped on Harkleroad's side to provide legal counsel and help defend him against what he claims were abuses of the law in an attempt to bully him—the story was also picked up by a number of online news outlets. Suddenly, Lowe's attorneys made Harkleroad an offer on Monday to settle the issue out-of-court, which Harkleroad discussed optimistically on his site. "My thanks to Lowe's for allowing us to (possibly) come to a mutually acceptable agreement for both parties, that is of course if this all gets finalized as I do believe it will. If it does this will be the last post or comment I make about the issue on this web site," he wrote. But that's apparently where the story has ground to a halt once again. Harkleroad tells Ars that he and his attorney made a counteroffer to the settlement, and have since not heard back. "I think they are thinking that for the most part the issue is over," he told us. He has declined to comment on the details of the offer and counteroffer, but Harkleroad says that he has not heard any word back for several days. Harkelroad's attorney, EFF staff attorney Corynne McSherry, acknowledged that the two parties are in discussions about a settlement, but declined to provide details as the "discussions are confidential." She did, however, point out that the courts have been clear that "gripe sites like this are protected—in fact, they want people to speak freely and share information about their experiences with various companies." She said that trademark holders sometimes lose sight of the point of trademark law, which is to protect consumers and provide them with good information about a company's product. Sites like Lowes-Sucks.com provide information on someone's consumer experience, she said, which is not only allowed under trademark law, but protected by the First Amendment. "There is no legal question here that they don't have a trademark claim," McSherry told Ars. This isn't the first time companies have attempted to use some arbitrary aspects of intellectual property law to silence public criticism online. Universal Music Group sent DMCA takedown notices to YouTube over a highly critical video of rapper Akon was posted by Michelle Malkin—eventually the EFF got involved and the clip was restored to YouTube. The EFF also filed a lawsuit against "paranormalist" Uri Geller for sending DMCA takedown notices over videos that were not created by him, but by another company that had created a documentary that was critical of his work and posted it to YouTube. So what is the lesson to be learned in all of this? While Harkleroad's case with Lowe's is not quite over, it appears as if the company is backing off of its trademark infringement claims (Harkleroad notes on his web site that the issue of officially retracting the claim is still being worked out between the attorneys). But the attempt to even make such a claim is still troubling, given the Internet's availability as a public soap box, where nearly anyone with grievances to air is allowed to do so. In another case where Viacom "mistakenly" misused the DMCA to have a parody taken down, the company agreed as part of its settlement with the EFF to educate its reviewers about fair use and promised not to challenge the use of its content if it is "creative, newsworthy, or transformative." The EFF isn't exactly known for backing down over cases like this, so we look forward to hearing about whatever resolution may come out of the Lowe's case. Harkleroad told us that if the two are unable to come to a resolution, he is still willing to take the case to court in Georgia. http://arstechnica.com/news.ars/post...sucks-com.html  Quake Fears, Ancient Finds Have Europe-Asia Tunnel on Nonstop Delay Julian Smith In the fifth and sixth centuries AD, Constantinople was the center of the world. Built at the mouth of the Bosporus Strait, it connected the Black Sea to the Mediterranean and linked Europe and Asia. The commerce, politics, and culture of much of the planet swirled around the basilicas and markets. Named for the first Christian Roman emperor, the city was the capital of Byzantium and the prize of marauding armies, from Crusaders to Huns. The region is still a crossroads. But now it's Istanbul, not Constantinople — a megalopolis of 10 million people that straddles East and West. And everyone has a car. Two traffic-clogged bridges cross the Bosporus, and auto exhaust chokes the streets and eats away historic architecture. The city has aboveground rail lines and a vestigial subway system, but hardly anyone rides them. So a decade ago, the Turkish government announced that it would fulfill the ancient dreams of sultans, with an ambitious plan to dig a tunnel under the strait. In fact, the Turks are trying to remake how people get around — and through — the city. The $3 billion Marmaray Project (named for the body of water just outside the strait and the Turkish word for rail) will consist of 48 miles of new railroad, 37 rebuilt train stations aboveground and three new ones below, and eight miles of tunnel connecting Istanbul's western, European side to the Asian east. Most of that underground rail line will be chewed through bedrock by digging machines wider than a 747. But one mile will be different, immersed beneath the shifting bed of the Bosporus. It'll be the deepest such tunnel in the world, under 180 feet of water and 15 feet of earth, made of 11 steel-and-concrete sections that can be as long as 440 feet and weigh 18,000 tons. When it's finished in 2012 — currently two years behind schedule — the project will change how the continents connect. Rail travelers (and rail cargo) currently have to transfer to a ferry for a three-hour journey across the city; that'll drop to less than two hours. Ideally, the tunnel will also relieve some of the pressure on those bridges. And when the Marmaray Project is integrated into a planned railway through Azerbaijan, Georgia, and Turkey, you'll be able to hop on a train in London, wave at the Hagia Sofia, and step off days later in Beijing. The project is ambitious enough to worry even the most experienced engineers, but its location could give a seismologist night sweats. All this work is taking place just 12 miles from the North Anatolian Fault, Eurasia's version of the San Andreas. Since AD 342, it has seen more than a dozen huge quakes that each claimed more than 10,000 lives. Two in 1999 together killed 18,000 people. Worse, over the last century the tremors have marched steadily west, toward Istanbul and the strait. There's another problem: The hub of this tunnel system sits on one of the greatest historic treasures of the classical world. In 2005, the dig ran into the remains of a fourth-century Constantinople port, Portus Theodosiacus. It's smack on top of what'll be an underground station on the new train line. Researchers are rushing to preserve the find, including what seems to be the only Byzantine naval vessel ever discovered, and that's preventing the contractors from starting in earnest. Delays to the tunnel's progress are expensive — $1 million a day in lost revenue. Yet Turkey can't afford to run roughshod over the delicate archaeological discovery. The country has been trying to get into the European Union for decades, and destroying priceless ancient artifacts doesn't exactly endear you to the Western world. Steen Lykke, project manager for Avrasyaconsult, the international consortium that's overseeing construction, sums it up: "I can't think of any challenge this project lacks." 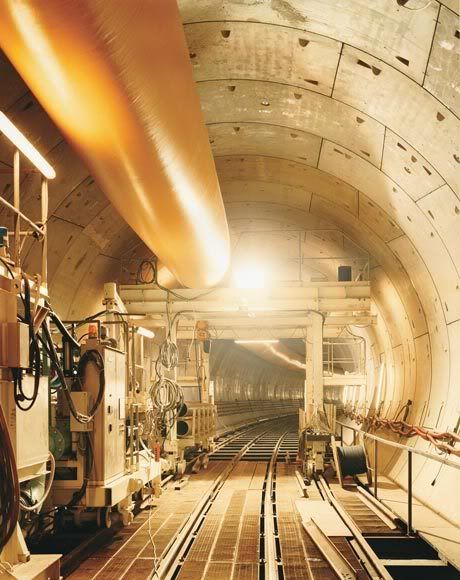 "You see this?" Claus Iversen, Avrasya consult's supervisor of marine works, waves a yard-long piece of rebar curved at one end like a shepherd's crook. His voice echoes inside a half-built tunnel section as he picks his way over the steel lattice that makes up the floor and part of the walls. "We have two guys in a building over there making a million of these. One bends, the other welds." Here at the Tuzla Shipyard just outside the city, construction workers will insert huge ballast tanks into each completed segment and cap their ends with steel doors — waterproof bulkheads. Then the segments will be put on barges and floated out to the Sea of Marmara. Once they're in position, the barge crews wait for the current to slow to less than 5 feet per second — any faster and they won't be able to safely drop the tunnel segment. When they're ready, the crews will angle the segment into the current (making it slightly more streamlined) and flood the tanks. The segment will sink, bound to the barge by steel cables that the crew controls like puppeteers. "My friends joke that I'm building concrete submarines," Iversen says. On the bottom, divers will release the cables after the segment is in place and connect it by hand to the ones already sunk. Inside the tunnel, workers will pump the water out of the ballast tanks and dismantle them, along with the steel bulkheads. There are only two segments in place so far, and they are connected to the surface by a 6-foot- diameter access hatch. All the pieces of the doors and the tanks will get carried out that way, making room for two parallel train tracks. Meanwhile, digging the parts of the tunnel under the city isn't going smoothly. Much of the substrate is either soft or rotten. "We don't talk about the rock as solid," Lykke says. "It's more like bricks piled at an angle with grease in between them." Avrasya consult is using just about every tunnel- digging technique humans have invented to make the project work — even the controversial New Austrian Tunneling Method. Designed for unstable soil, it involves using spray-on concrete called shotcrete to solidify the ground around the tunnel. Tunnels dug this way have an unnerving tendency to collapse during construction, as one did in Munich in 1994, killing four and injuring 27. There haven't been any problems yet in Istanbul. Even more ominous than the frequency of earthquakes along the 745-mile-long North Anatolian Fault is the pattern. At their most basic, quakes happen when two moving sides of a fault squeeze together. As stress builds, the fault ruptures and the ground shakes. Most of the time that relieves the stress and the fault quiets down, like champagne going flat after a dramatic cork-popping. Sometimes, though, a temblor relieves stress on one part of the fault but increases it farther down the line. The Week in Review is edited and published by Jack Spratts. Geologists call this process stress transfer, and it can lead to a string of tremors repeating like seismic dominoes. That might be why quakes along the New Anatolian have been getting closer and closer to Istanbul over the last 100 years. Since the 1939 Erzincan earthquake in eastern Turkey (magnitude 7.9), Big Ones have been migrating west. Geologists calculate that the chances of the city getting hit by a quake topping 7.0 in the next 30 years are as high as 77 percent. The tunnel's engineers are preparing for the worst. Squishy, waterlogged soil like the stuff they're digging through can liquefy during a quake, basically turning to quicksand. So builders are infusing the sand layers with a thin mortar of industrial grout down to 80 feet below the seabed. The walls of the tunnel will have both a steel shell, often used in the US, and a waterproof concrete layer, which is popular in Europe. Each is independently watertight. The whole thing will be long and narrow enough to flex "like a straw in gel" during a tremor, Lykke says. The underwater tube will connect at both ends to tunnels being bored from each side of the city; they are supposed to be done next year. At the joint between rock and water will be a giant rubber and steel gasket that'll let the structure shift without breaking during a quake. And if everything goes to hell and the tunnel gets breached, floodgates at these joints will slam down to isolate the tube and keep the train stations on either side from filling with water. The Marmaray builders say their design will withstand a 7.5 quake, bigger than the one that all but leveled Kobe, Japan, in 1995. "Tunnels are like buildings with very thick walls," says Geoffrey King, director of the tectonics lab at the Centre Nationale de la Recherche Scientifique's Institut de Physique du Globe de Paris. "That's the ideal way to earthquake-proof a building." Of course, he adds, no system is perfect. "I wouldn't like to be in such a tunnel during an earthquake." The hub of the Marmaray Project is mostly underground, the size of three football fields. Yenikapi Station will be the second stop on the European side, just over a mile from Istanbul's historic Blue Mosque in the old center of the city. The tunnel-boring machines start at Yenikapi, pass by Sirkeci Station — the deepest one, where builders are using the New Austrian method — and then hit the water. Before construction started, archaeologists surveyed the site to see what was there. This is Istanbul, after all — a 2,700-year-old city where you can't bury a cat without unearthing something older than the US. The builders expected a few artifacts, maybe an old foundation or two. But in 2005, they found a shipwreck. Then they found a massive limestone block. And stumbled upon another. And another — a line of 20 blocks extending 80 feet. It was the remains of mighty Portus Theodosiacus, lost for 1,000 years and, experts agree, the greatest nautical archaeological find in modern history. Today, station contractors work on the foundations in carefully prescribed areas, alongside hundreds of hard-hat-wearing archaeological workers swinging picks and pushing wheelbarrows amid thousands of years of history. "It's a virtual museum of ancient shipbuilding technology," says Cemal Pulak of Texas A&M and the Institute of Nautical Archaeology. He's an expert in early wooden-shipbuilding techniques and a researcher on the dig. On a walk through its maze of trenches, platforms, flooded pits, and dirt paths, he stops briefly to point at an orange sliver poking out of the dirt. "Hmm," he says, "human bone." The scope of artifacts is overwhelming. Some date back to the 6th millennium BC, the oldest settlements ever uncovered in Istanbul. Pottery fragments, shells, and pieces of bone litter the ground. Blue milk crates full of everything from amphorae to horse skulls are stacked head-high near trailers that serve as temporary offices. And somewhere in a storage facility are nine human heads, found in a bag. But the most important discoveries have been ships — fishing boats, transport vessels, cargo carriers, and what seems to be a Byzantine warship, the first ever found, all from the 7th to 10th centuries. Most of the wrecks are incredibly well- preserved, thanks to oxygen-squelching sand and silt that filled the harbor. But extracting and preserving them is an arduous process involving years of injections of polyethylene glycol, a stabilizing polymer. "All the lignins and tannins have been leached out," Pulak says, standing in front of an ancient wooden hull. "If you just dried it out, it would turn to dust." The engineers are getting impatient with all this history. The dig forced Yenikapi Station to be redesigned, which meant pushing back other elements of construction. "Honestly, is this an archaeology project or are we tunneling?" Iversen says. "We have meetings sometimes where we end up talking about the archaeological dig for half the time." When he tells locals about the new completion date for the project, they often respond with a cynical "Yeah, yeah." Contractors wonder why they should heed the construction schedule when the excavations have already caused years of delays. "Lots of equipment is just sitting around," he says. Archaeological field manager Metin Gökçay says there is no time limit on their work, although my interpreter's eyebrow rises as he translates this. "The work comes first," G k ay says. "I know how to deal with people." He's about to retire, he says, so he doesn't have to worry about getting fired. The project is byzantine — there's no other word for it. And all that complexity means tensions are high. Access to the site, once open to reporters, has become more and more restricted. It took me months to get permission to talk to the scientists; the government appears terrified of being publicly embarrassed. Under the pressure, the archaeologists are barely keeping it together. Pulak says his group is "almost on nonspeaking terms" with another team from Istanbul University's conservation department, which he thinks is too inexperienced at digging up ships. The squabbles have gotten too much for him. He says this summer is likely his last season at the dig. He's heading home to teach, fleeing a project marked by "lots of politics and lots of egos." Turkey must finish the tunnel, but it can't just bulldoze the ancient port. The country's bid to enter the European Union — pending for 40 years, since even before it was called the EU — has been held up in large measure by questions about human rights and democracy. Showing sensitivity to other cultures by honoring the heritage the past represents is good PR on that front. But to prove it is a Western-style state, Turkey also has to display a certain facility with high tech and big engineering, which means completing the project. Indeed, one of the main arguments against admitting Turkey to the EU has always been that the country isn't exactly in Europe. Geographically speaking, though, if you build the tunnel, the country is suddenly at least as tightly connected to the mainland as the UK is. Historically sensitive modernization is not impossible. Greece managed to build a metro through the heart of Athens, remodeling that classic metropolis without destroying its foundations. But in Turkey, the outcome of this tug-of-war between past and present is still uncertain. None of that tension is visible on the surface waters of the Bosporus. Instead, there's just the day-to-day action of one of the world's busiest shipping lanes. Boats and ships of every sort — ferries, cargo ships, tankers, fishing boats, luxury yachts — pass back and forth. Cruise ships the size of skyscrapers rest in port. And 800 feet off the Asian side, there's a small yellow platform, metal, surrounded by a heavy railing lined with flashing yellow lights and fitted with a warning bell the size of a basketball. In the center is the access shaft to the tunnel. It's the only way in or out, and it's so far from the shore that it feels like a shipping accident waiting to happen. "We're used to the North Sea," Iversen says. "Always, safety first." Until the tunnel borers meet the water, the platform is the only link between the tunnel and the surface world. And right now that connection feels awfully vulnerable. http://www.wired.com/science/planete...15-09/ff_quake  Magna Carta Is Going on the Auction Block James Barron The 2,500 words fill a page that is a couple of inches shorter than this one, but almost as wide. The faded letters in Latin are unreadable in places. Something that looks like a scraggly, russet-colored tail hangs from the bottom. It is the document that laid the foundation for fundamental principles of English law. Angry colonists complained long before the Boston Tea Party that King George III had violated it. The men who drafted the United States Constitution and the Bill of Rights borrowed from it. It is Magna Carta, agreed to by King John of England in 1215 and revised and reaffirmed through the 13th century. The tail dangling off the page is a royal seal. And it is about to go on sale. Sotheby’s, which today is expected to announce plans to auction it in New York in mid-December, estimates that the document will sell for $20 million to $30 million. It is the only copy in the United States and the only copy in private hands. Sotheby’s says the 16 others are owned by the British or Australian governments or by ecclesiastical or educational institutions in England. Until last week, this copy was on display in the National Archives in Washington, steps from the Declaration of Independence and the Constitution. But it was only on loan from a foundation controlled by the Texas billionaire Ross Perot, who bought it in 1984 for $1.5 million. The foundation told the archives this month that it had decided to end the loan and take back Magna Carta. Its departure came so suddenly that the archives did not have time to remodel the display case or fill it with some of the nine billion documents from the archives’ own collection. “This is surprising,” said Lewis L. Neilson Jr., the chancellor of the National Society Magna Charta Dames and Barons, a nonprofit group in Philadelphia that promotes awareness of Magna Carta, the literal translation of which is “Great Paper.” “It provides a real rallying point for emphasizing the importance of individual liberty and the rule of law, and it will be curious to see what happens to it and who’s interested in purchasing it and what they do with it.” The Perot Magna Carta dates to 1297 and was endorsed by King Edward I. The National Archives said that of the 17 original versions that still exist, 4 are from the reign of John; 8 are from Henry III; and 5 are from Edward I. Mr. Neilson said that some jurists consider the Perot Magna Carta to be the most important one because it was the one that was entered into the statute books in England. Trudy Renna, the only employee of the Perot Foundation identified on its tax return, said in a telephone interview last week that the foundation decided to sell Magna Carta to “have funds available for medical research, for improving public education and for assisting wounded soldiers and their families.” The tax return listed the foundation’s assets as $56.9 million at the end of last year and its contributions as $9.08 million, including more than $4 million for medical research at the University of Texas Southwestern Medical Center at Dallas. Mr. Perot is listed as president of the foundation and also as a director. Seven of the nine other directors are his wife, Margot; their five children; and his sister, Bette Perot. Mr. Perot, the onetime independent candidate for president of the United States, bought it from relatives of James Thomas Brudenell, the Earl of Cardigan, who led the charge of the Light Brigade in 1854, during the Crimean War. The copy was said to have been in the family’s possession since sometime in the Middle Ages. But later generations were apparently unaware of its importance. The National Archives in Washington said it was “discovered” in 1974 during an inventory at the family’s estate at Deene Park in England. The National Archives said it came into the family’s hands through Edmund Brudenell, who served as attorney general under Richard II in the 14th century, or through Sir Robert Brudenell, who was chief justice of common pleas under Henry VIII in the 16th century. By the time Mr. Perot bought the copy, it had been on the market for four years, and at least one deal had fallen through before Mr. Perot came along. At the time, Mr. Perot said he was “amazed” that it had been for sale. “It was like someone said ‘Mona Lisa,’ ” he said at the time. He sent it to Philadelphia in 1987 during the observance of the Constitution’s bicentennial, and then to the National Archives. It will be sold by David N. Redden, a Sotheby’s vice chairman who sold a copy of the Declaration of Independence for a hammer price of $7.4 million in 2000. That copy had been tucked behind a $4 flea-market painting. The buyers were the television producer Norman Lear, who created shows like “All in the Family” and “Maude,” and the Internet entrepreneur David Hayden. Mr. Redden was also one of the auctioneers at the sale of items from Jacqueline Kennedy Onassis’s estate in 1996. That auction included a $574,500 humidor from President John F. Kennedy and a $415,000 rocking chair. Mr. Redden arranged the Magna Carta auction quietly, so quietly that Sotheby’s did not tell its own employees why it was changing arrangements for other auctions. James Zemaitis, the director of Sotheby’s 20th-century design department, said he was asked to give up a room at Sotheby’s headquarters on York Avenue at East 72nd Street that he had reserved for a pre-auction exhibition of his own. “All they told me was: ‘David Redden is selling this really important document, the most important document of all. Can you give up this room for us?’ ” he recalled. “And I’m like, ‘Sure, but what is he selling, the Magna Carta?’ ” http://www.nytimes.com/2007/09/25/nyregion/25magna.html  A Street Performer Crusades for the First Amendment Anemona Hartocollis What is the purpose of the First Amendment? That was the question before a judge in Manhattan Criminal Court yesterday, as a street performer named Reverend Billy, a k a William Talen, faced charges of harassing police officers in Union Square Park by reciting the First Amendment to the Constitution. Mr. Talen — the white-suited, blond-pompadoured leader of the mock Church of Stop Shopping who is perhaps best known for his crusade against Starbucks — was arrested June 29. He had joined a protest against the city’s new permit requirements for the monthly Critical Mass bicycle rally and proposed restrictions on photographers and filmmakers in public places. He was charged with two counts of second-degree harassment, under a statute originally intended for use against stalkers. He was accused of following a group of officers while repeatedly reciting the 40-odd words of the First Amendment through a megaphone, the kind commonly used by cheerleaders. After his arrest, Mr. Talen said, he was jailed for 20 hours, first in a Gramercy Park precinct house, then in the underground Manhattan Detention Complex, popularly known as the Tombs, where he felt compelled to live up to his stage name by ministering to the less fortunate. In the precinct house, he said, he provided pastoral counseling to a young man who was crying after he was arrested for carrying a joint in his pocket. In the Tombs, one of the medical attendants recognized him and offered to put him in a “special” cell, which turned out to be for mental patients, Mr. Talen said. In court yesterday, the prosecutor told Judge Tanya Kennedy that Mr. Talen’s offense had been to shout the familiar lines beginning with “Congress shall make no law” while standing just three feet from the officers, and to ignore their requests to stop. The prosecutor, Mary Weisgerber, said his behavior was “obnoxious” by any standard. “That’s not true,” Mr. Talen piped up. Outside of court, Mr. Talen — who says that his lungs are like bullhorns because he has had operatic training — maintained that he was about 15 feet from the officers and that his account was supported by a videotape of the episode that has been preserved on YouTube. Such findings of fact — three feet or 15 feet? — may someday go to a jury. Yesterday’s hearing turned on a more scholarly question: Does reciting the First Amendment serve a legitimate purpose? Mr. Talen, 57, appeared in court looking, as he put it, more like a Puritan than a preacher in a black suit and a white shirt, a reversal of his usual outfit, and his blond hair lank instead of puffy. His wife, who is Reverend Billy’s theatrical director and who goes by the name Savitri D., was at his side. His lawyers, Norman Siegel and Earl Ward, told Judge Kennedy that the law defined harassment as engaging in a course of conduct that is not only “alarming” and “annoying” but “which serves no legitimate purpose.” Mr. Siegel argued that there could hardly be a more legitimate place than a protest rally to recite the First Amendment, with its lines barring Congress from “abridging the freedom of speech” and guaranteeing the rights “of the people peaceably to assemble.” The Court of Appeals, the state’s highest court, has ruled that for a course of conduct to have “no legitimate purpose” it must have no thoughts or ideas besides threats, intimidation or “coercive utterances,” Mr. Siegel said in a written brief. The courts have found that it is not a crime for a husband to call his wife crude and vulgar names, Mr. Siegel said, quoting a case in which a judge ruled that “the registering of displeasure with another person is protected speech.” If swearing at one’s wife can serve a legitimate purpose, Mr. Siegel said, reciting the First Amendment at a protest rally can, too. “We respectfully submit that reciting the 44 words of the First Amendment, you have a First Amendment right to do that,” Mr. Siegel added. Mr. Siegel asked Judge Kennedy to dismiss the charges, saying this was a “quintessential” case of a prosecutor acting without a basis in the law. Under the charges, Mr. Talen could be sentenced to up to 15 days in jail. Ms. Weisgerber told the judge that she needed more time to formulate a response. Judge Kennedy gave the district attorney’s office until Oct. 15 to respond in writing and set a court date for Nov. 14. If the prosecution misses that deadline, Judge Kennedy said, she will grant the motion to dismiss the charges. http://www.nytimes.com/2007/09/26/ny...=1&oref=slogin  Backstage: Sleepy Teenagers and a Grape or Two Guy Trebay 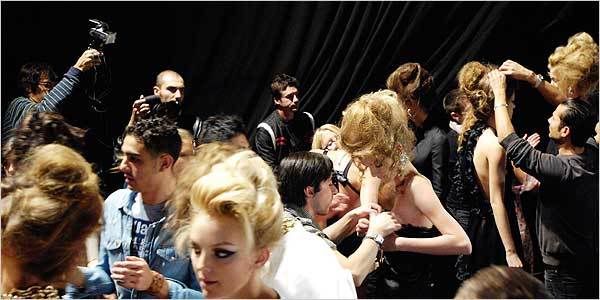 Milan “Flavia, Michaela, Janeta, Shannon, Valentina, Marcelina, Kim,” the fashion producer Alessandra Marabini-Baiocchi was chanting here Thursday morning, calling roll for a last-minute rehearsal of the spring 2008 Dsquared show. It was 7:45 a.m., and the rain drumming on the roof of a tent set up on the Milan fairgrounds was like a bass beat behind a soundtrack built around “Umbrella,” the monster dance single by Rihanna, the designers’ special “secret” guest. “Umbrella, ella, ella, eh, eh, eh,” Rihanna’s voice hiccupped on the soundtrack as Ms. Marabini-Baiocchi attempted to corral a herd of sleep-deprived and BlackBerry-hypnotized creatures from Brazil, Belarus, Poland, Canada and wherever else fantastical figures with tiny heads and coltish legs are found. “Girls, we try the finale now,” Ms. Marabini-Baiocchi said, and Flavia, Michaela, Janeta, Shannon, Valentina, Marcelina, Kim and a dozen others obediently formed a queue, looking only the slightest bit like suburban 1950s housewives, thanks to the shower caps they’d been given to protect their roller-set hair. And as they stood there — because that is a lot of what models do when they are not sitting around being prodded, poked, combed, painted, photographed and interviewed by Japanese magazine people about what exact shade and brand of lipstick they prefer — the Brazilian model Flavia Oliveira, who has an upturned nose and sexily short upper lip, talked about how she gets through the runway season. “I did 28 shows in New York, and 8 in London and 13 here already,” Ms. Oliveira said. “I try to sleep enough and eat a lot of sushi — a lot, a lot, a lot — and meat. And I don’t freak out, even though yesterday I found out that they canceled me at Dolce & Gabbana.” Two seasons ago she would have freaked out, she went on. “Now I’m not going to be crying because, you know, I still love them, I already did that show, and maybe I’m just not the face of the season for them right now.” And just then, the very-identical-twin designers, Dean and Dan Caten — né Catenacci, originally of Willowdale, Ontario, and now of Milan — danced past, exaggeratedly pony-stepping onto the set, which was tricked out to look like a set designer’s idea of an American grease-monkey’s garage, complete with hydraulic jacks, industrial shelving and two muscle cars with Italian license plates. “Looking beautiful, girls,” said Dean Caten, or maybe it was Dan, and then Katherine Ensslen, who carries the Oz-like title of director of makeup artistry for M.A.C. cosmetics, a sponsor, came by and warned: “We have to start with the makeup, my dears. It was supposed to be five minutes, and it was not five minutes.” And Ms. Marabini-Baiocchi directed the models to stride down the runway and back, then had them repeat this action before giving them the release signal so that they could bolt to the makeup area and slump into folding chairs. And there the makeup team set about painting the teenagers from Belarus, Brazil or wherever to give them a look that the beauty director Val Garland characterized as fierce Fellini flick. “Think 1970s, think late night, think Sophia Loren at her best, with a cigarette and her hair messed up,” Ms. Garland said. “She’s got a dog with a diamond collar and money to burn.” And then Ms. Ensslen came around and said, “O.K., guys, keep the speed up.” And the makeup people started drawing the cat eyes on the models just a little slower, because that is what the Spanish proverb says to do when you are in a hurry: slow down. And then the manicurists from EzFlow Nail Academy knelt beside models like Michaela Kocianova, two manicurists per girl, applying white-tipped glue-on nails that would be torn off by Ms. Kocianova, who was now yawning extravagantly, and all the others two seconds after the show. And Dan, or was it Dean, Caten came by helping some workers shoulder a folding screen into the makeup area to shield Rihanna from the cameras when she finally emerged from her trailer. And Dan, or was it Dean, Caten said to his brother, “Are you going to help?” And when his brother ignored this request by taking the opportunity to check for some lint on his blazer, Dan, or was it Dean, Caten snapped: “Oh, never mind. Shut up!” Nobody paid any attention to this, of course, because circus nerves are normal backstage, and Janeta Samp, a Polish model, wandered past the fraternal snit, her eye fixed on the catering table, which is where most of the young women get their sustenance during these days. “Sometimes we ask the driver to stop and get a sandwich,” said Ms. Samp, who went at a single strawberry with more deliberation than most people put into a five-course meal. “But mostly we eat whatever is backstage, a yogurt, a cookie. You know, whatever — a grape.” And the Catens walked past again, at what by now was 9:15, both with their heads tossed back and laughing as at the end of a wild night and not the beginning of a very long workday, an impression not diminished by their flutes of Mumm. And following them were a dozen cameras and Rihanna and her bodyguards and manager, who kept busy informing even those who had not asked that Rihanna would not be posing for pictures. And as they walked, the Caten twins were describing for their television-camera retinue the imaginary woman they saw when they first sat down at the drawing board. “She’s got her hair done, she’s got her nails done, she’s glamorous and a little messy,” one of the brothers said. “She can drink all she wants, and she doesn’t have to worry.” And why is that? “Because she’s got a driver,” Dan, or was it Dean, Caten replied. http://www.nytimes.com/2007/09/28/fa...s/28DIARY.html Until next week, - js.  Current Week In Review  Recent WiRs - September 22nd, September 15th, September 8th, September 1st Jack Spratts' Week In Review is published every Friday. Submit letters, articles and press releases in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. Questions or comments? Call (617) 939-2340, country code U.S.. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - September 22nd, '07 | JackSpratts | Peer to Peer | 3 | 22-09-07 06:41 PM |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |