
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 |
|
Join Date: May 2001
Location: New England
Posts: 10,015
|
Since 2002
  "It's fear and panic." – David Bianco "If people don’t know what rights they need to obtain and if there’s no easy way to obtain them even if they do know, exactly what do rights-holders expect? More to the point, how does suing YouTube help solve the problem?" – Shelly Palmer "There is a lot of female coding in this advertising." – Laura Jones "Why should we allow any lead to be in there?" – Patrick MacRoy "I’m not giving my grandchild any toy that’s made in China. Do we really know who is in control over there?" – Elizabeth Noe "I definitely gave Microsoft too much of a free pass on this [Vista] operating system." – Jim Louderback "Excessive secrecy invites abuse and we have seen this played out on a massive scale." – Jameel Jaffer "The Internet is the new Afghanistan." – Raymond Kelly "Looking back on it, it was all high." – Elliot Tiber "The Crying of Lot 49." – Sal Pizarro  I lost my Grandmother forty years ago this summer. Literally. She wandered out of the house on a perfect August morning and disappeared. There were no locators to hang on people back then and it was quite a job tracking her down, but like some still flickering GPS system she aimed toward home and that’s where I found her, stuck in a loop between my parents’ house and hers. It had started several years before. For my sixth birthday she bought me the greatest teddy bear I’d ever seen. It was bigger than me. I was hard on the thing though and before long his stuffing was beginning to show. I soon found out Grandma was a wiz at sewing him up. For a while. Eventually a day came when she stopped putting him back together. I was little and didn’t understand any of it. I only knew poor Teddy was leaking. She was a Raymond. The family was accomplished but at that age I wasn’t burdened with it. All I wanted was my bear. There were hushed conversations among the adults during those final years when she still lived at home. She dwindled. Eventually she had to go away and the last time I saw her she was unrecognizable. As was I. This once gentle and loving woman who would sit me down and read to me for hours no longer had any idea who I was. She was gone save her shell. By the time I began to realize just how important the continuum was from my ancestors to her she was no longer alive. She couldn’t repeat the many stories she herself had heard, like how “cousin Henry” cobbled together his little paper in the summer of 1851, some forty years before she was born. No one was left to pluck the string. Even in the last few terrible years of her life there were no memories living inside her. The problem with Alzheimer’s, beyond the obvious terror for the immediate victim, is that it also robs the identities of the children. When there is no one to tell you who you are you are no one. And so it was. By the time I was old enough to understand the special knowledge she possesed, she and it was gone. Luckily for me she had had my mother late in life and filled her up with most of it and she has done her best to pass it on to me. It’s not exactly the same but it must be enough. The family is old and there are many narratives. Like most in America it has crossed continents and burrowed deep into life both here and abroad. We have lived in this part of New England for over three hundred years and sometimes I think I feel every one of them as I walk our granite hills. As technology advances a day will come when everything we do, for better or worse, will be sharable and saved. Our entire histories as well as those of our forbears will be isolated and preserved, independent of the ravages of disease and time. There is evidence our descendents may live forever. Research on many fronts, including turtles of all things, is showing tantalizing possibilities. It is no small irony that I was raised by people who would not even imagine it and yet I here I am teetering on its cusp. As I ponder this a cousin in Boston is working on a cure for Alzheimer’s, and although he fears the job won’t be done in his lifetime, a son or daughter might continue his work and complete it. Meanwhile cousin Henry’s old New York Times building is disappearing. It’s being torn down today. There is something a little sad about seeing it go. His empty shell is making way for something new. Perhaps a residence in whose homes new lives – and histories - will be conceived. This is as it should be. Yet if the natural order of things means it is now too late to preserve the unique details of our grandmothers’ lives it will never be too late to reflect upon the sacrifices they made and the gifts they bestowed along such essential and infinite threads. Enjoy, Jack August 18th, 2007  Politicians Preach Calm as Fear, Panic Rule Brian Love and Jonathan Stempel Shares plummeted worldwide on Thursday, although U.S. stocks staged a late-session comeback, while politicians weighed in to calm financial markets swept by fears that years of runaway credit growth will end with a big blowout. The largest U.S. mortgage lender, Countrywide Financial Corp., tapped out an $11.5 billion credit line, and another lender stopped funding home loans as companies scrambled for cash and credit markets seized up. At one point, Countrywide's shares were down as much as 30 percent. "It's fear and panic," said David Bianco, chief U.S. equity strategist at UBS in New York. "People are beginning to lean toward outlooks now of all the dominoes falling, that the U.S. economy slides into recession because of this credit crunch, and it has an adverse impact on the global economy and even the globally exposed sectors." A strong rally in the last few minutes of trading left the blue-chip Dow Jones industrial average down just 16 points, erasing an earlier drop of more than 340 points. Financial stocks led the way on optimism that regulators may let the two biggest U.S. mortgage funding companies -- Fannie Mae and Freddie Mac -- play a bigger role in steadying the ailing housing industry. First Magnus Financial Corp., the 16th-largest U.S. mortgage lender, said it stopped funding home loans and taking mortgage applications. It cited the "collapse" of the secondary market where lenders typically would try to resell mortgages to generate more cash for future lending. National City Corp., a big Cleveland, Ohio-based bank, folded its home equity unit into its main mortgage unit to save money, resulting in job cuts. French President Nicolas Sarkozy, on vacation in the United States, said the global economy is enjoying its best run of growth in decades and could withstand the market turmoil, though governments should remain on guard. The White House declined to comment on the sharp moves in financial markets, and stuck to its view that the U.S. economy was fundamentally sound and should continue to grow. A report from the Philadelphia Federal Reserve Bank that showed factory activity in the U.S. Mid-Atlantic region stagnated in August raised concerns about the health of the economy and pressured stocks. GLOBAL SELL-OFF Shares plunged in Asia and Europe, and more steeply in the emerging markets of Eastern Europe, South Africa and Latin America. Demand for the government bonds of wealthy countries rose at the expense of riskier debt and credit. European shares suffered their biggest one-day fall in four years with the FTSEurofirst 300 stock index closing around 3.2 percent lower, at 1,443.89 points. Britain's Treasury said that economy was strong and well positioned to absorb market shocks. "Fear of the unknown, i.e. credit quality, is starting to trigger panic and indiscriminate selling," said Marco Annunziata, chief economist at UniCredit, a big European investment bank. Annunziata called on the U.S. Federal Reserve, which has remained more hands-off than the European Central Bank, to play a more active role to restore order. "All the markets are getting from the Fed is tough love -- a dangerous combination," he said. William Poole, president of the St. Louis Federal Reserve Bank, said on Wednesday that financial market turmoil had not undermined the U.S. economy and there was no need for the central bank to ride to the rescue with an emergency rate cut. "It's premature to say that this upset in the market is changing the course of the economy in any fundamental way," he said in an interview with Bloomberg. "Obviously, there could be an impact, but we have to rely on some real evidence." The Fed did step in with another shot of liquidity on Thursday, adding $17 billion of reserves to the banking system, and said it stood ready to do more. In Brussels, the European Commission said it would review the role of credit agencies that rate the collateralized debt obligations that have been at the center of the storm. "We have to ask ourselves about the exact role that ratings agencies have played regarding this category of risk," Sarkozy wrote in a letter to German Chancellor Angela Merkel, president of the G7 club of industrialized nations. TOLL ON GROWTH Swiss bank UBS said investors were more scared of risk than at any time since U.S. hedge fund LTCM collapsed in late 1998, according to the investment bank's measure of sentiment. Another gauge, spreads on U.S. two-year interest rate swaps, hit their highest since January 2001. In the United States, Treasury Secretary Henry Paulson said the turmoil would exact a toll on U.S. growth but that the financial system and the economy were strong enough to withstand it without a recession. Paulson told the Wall Street Journal in an interview published on Thursday that nothing should be done to protect market players against losses or restrain their risk-taking. "One of the natural consequences of the excesses is that some entities will cease to exist," he said. (Additional reporting by Kristina Cooke in New York, and Nick Edwards and Luke Baker in London) http://www.reuters.com/article/topNe...84818220070816  Apple Shares Fall 7% amid Market Declines Robert MacMillan Shares of Apple Inc. tumbled as much as 7 percent on Thursday as investors targeted the high-flying stock in a general U.S. market slide prompted by credit fears. Apple shares have gained about 34 percent since the start of the year, largely buoyed by expectations for the company's media-playing iPhone that was unveiled in January and hit store shelves in June. In that time, the S&P 500 Index has shed about 2.6 percent. "The stock's been a huge outperformer, and I think it's just (investors) taking some profits," said American Technology Research analyst Shaw Wu. "It's probably one of the few names people have made a lot of money on." "We really haven't picked up anything company-specific," he added. Bear Stearns analyst Andrew Neff, in a generally upbeat note over Apple's prospects, cited as one concern for the company the possibility that "growth rates may have peaked and could slow, which can hurt a stock's P/E multiple." But Neff maintained his estimates for the company and kept an "outperform" rating on the stock. Apple shares fell 5.2 percent to $113.63 in afternoon trading on the Nasdaq after falling as low as $111.62 earlier in the session. http://www.eweek.com/article2/0,1895,2171971,00.asp  Dell to Restate, Cut Profit by Up to $150 Million Ian King and Connie Guglielmo Dell Inc., the second-biggest personal computer maker, will restate the past three years of financial results because of accounting errors, reducing profit in the period by as much as $150 million. The restatement, which covers years from fiscal 2003 until the first quarter of 2007, will trim 2 cents to 7 cents from per- share profit, Dell said in a statement today. Sales for each year will be lowered by less than 1 percent. Dell found some teams changed accruals and reserves, estimates of expenses or losses that have occurred and haven't yet been paid, to meet quarterly goals -- sometimes at the request of unidentified senior executives. The restatement allows founder Michael Dell, who retook the helm in January, to focus on reviving sales and fighting bigger rival Hewlett-Packard Co. ``The restatement looks pretty minor,'' said Shaw Wu, an analyst at American Technology Research in San Francisco, who has a ``neutral'' rating on the stock and said he doesn't own it. ``The overhang is gone. It's good to get this out of the way.'' Dell, based in Round Rock, Texas, said in March it found evidence of misconduct and errors in its results. The SEC began a probe in August 2005, escalating it into a formal investigation in November. The Justice Department also is investigating. Dell rose 65 cents, or 2.5 percent, to $26.58 in extended trading. The shares fell 37 cents to $25.93 at 4 p.m. in Nasdaq Stock Market trading. Taking Actions Dell's investigation involved more than 375 people worldwide who evaluated more than 5 million documents, conducted more than 200 interviews of company personnel and reviewed thousands of journal entries and supporting documentation. The computer maker hasn't filed full results for the past four quarters because of the investigations. The SEC investigation is continuing, Dell said today. ``We have been taking actions,'' spokesman Bob Pearson said in an interview. ``We are putting in place training programs. The main point is to establish a strong control environment and ensure we have financial reporting integrity.'' Dell, 42, retook the title of chief executive officer after ousting Kevin Rollins amid an effort to revive sales and profit. Longtime finance chief James Schneider resigned in December. (The company plans a conference call at 5:15 p.m. central time. To listen, dial +1-877-253-8088.) http://www.bloomberg.com/apps/news?p...FY4&refer=home  The $200 Billion Rip-Off: Our Broadband Future was Stolen Robert X. Cringely This is part three of my explanation of how America went from having the fastest and cheapest Internet service in the world to what we have today -- not very fast, not very cheap Internet service that is hurting our ability to compete economically with the rest of the world. Part one detailed expected improvements in U.S. broadband based on emerging competitive factors, yet decried that it was too little too late. Part two explained how U.S. broadband ISPs are different from most overseas ISPs and how those differences make it unlikely that we'll ever regain leadership in this space. And this week's final part explains that this all came about because Americans were deceived and defrauded by many of their telephone companies to the tune of $200 billion -- money that was supposed to have gone to pay for a broadband future we don't -- and never will -- have. I feel qualified to write about this because, for a short time, I was right in the middle of it. A key term here is video dial tone, which referred in the mid-1990s to the provision of video-on-demand and cable TV-equivalent service by U.S. telephone companies at (bidirectional!) speeds up to 45 megabits per second over fiber and hybrid fiber-coax networks. Much of the publicity back then was generated by an outfit called Tele-TV, which was a video partnership of Nynex, Bell Atlantic, and Pacific Bell. Howard Stringer, former president of CBS and current CEO of Sony, ran Tele-TV, which had some ambitious plans to deploy video service to millions of homes. The company twice asked vendors to submit proposals to build set-top boxes for this ambitious network. In those days I designed set-top boxes and in the case of both Tele-TV bids, my designs came in at the lowest price, first under the name of my own start-up and then under the Fujitsu brand after Tele-TV urged me to find a big manufacturing partner. I can't claim to have actually WON either time, though, because not a single box was ever built or paid for and Tele-TV went out of business without ever actually having been IN business. At the time I had no idea what was going on, but today I know and now so will you. The National Information Infrastructure as codified in the Telecommunications Act of 1996 existed on two levels -- federal and state. As a federal law, the Act specified certain data services that were to be made available to schools, libraries, hospitals, and public safety agencies and paid for through special surcharges and some tax credits. Looking solely at the Federal side of the story, the so-called Information Superhighway still doesn't appear to have been a success, but it wasn't a criminal failure. Many schools and libraries were wired at considerable expense though the health care and public safety components never amounted to much. It is on the state level where one can find the greatest excesses of the Telecommunications Act. All 50 U.S. states and the District of Columbia contracted with their local telecommunication utilities for the build-out of fiber and hybrid fiber-coax networks intended to bring bidirectional digital video service to millions of homes by the year 2000. The Telecom Act set the mandate but, as it works with phone companies, the details were left to the states. Fifty-one plans were laid and 51 plans failed. Failure is not foreign to the information technology business. Big development projects fail all the time and I have written several times about this and how those failures come to be and how they can be avoided. But I find it hard to remember any company or industry segment ever going zero for 51. This is a failure rate so amazing that any statistician would question the motives of those even entering such an endeavor. Did they actually expect to succeed? Or did they actually expect to fail? We may never know and it probably doesn't even matter, but one thing is sure: they expected to be paid and they were. Over the decade from 1994-2004 the major telephone companies profited from higher phone rates paid by all of us, accelerated depreciation on their networks, and direct tax credits an average of $2,000 per subscriber for which the companies delivered precisely nothing in terms of service to customers. That's $200 billion with nothing to be shown for it. In a Federal Communications Commission (FCC) report from 1994 there were requests from U.S. telephone companies to provide video dial-tone service at unprecedented levels. Bell Atlantic (now part of Verizon) wanted to install service to 3.5 million homes in its service area. Nynex (now also a part of Verizon) requested permission to install service to 400,000 homes. Pacific Bell (now part of AT&T) wanted to install service to 1.3 million homes. Ameritech (now part of AT&T) wanted to install service to 1.2 million homes. GTE (now part of Verizon) wanted to install service to 1.1 million homes. Note that these applications were all prior to the Telecommunications Act of 1996 being passed, so they were covered under the prior 1934 Act. And by 1995 most of these applications had been withdrawn by the telephone companies, though the FCC oddly continued to act as though the applications were still valid. What went wrong? First there were technical problems. Bidirectional 45-megabit-per-second service was going to be harder to install and more expensive than expected, though oddly more than one Regional Bell Operating Company tried to demur because of stated fears that the proposed technology would become obsolete, not that it was too advanced. Then there were regulatory problems as the FCC tried to control deployment centrally while states and cities tended to view video dial tone as just another cable company to be taxed and regulated. Bell Atlantic switched its plans to MMDS (Multichannel Multipoint Distribution Service -- so-called "wireless cable") as did GTE, but MMDS suffered from interference by trees and was never fully reliable, though some of that spectrum is today being redeployed for WiMax networks. When the 1996 Act was finally passed, though, the idea of video dial tone had been converted to a justification for deploying ADSL. Where telephone companies had been promising EITHER 45 mbps bidirectional service OR at least the ability to carry HDTV (nominally 20 mbps) suddenly it was an acceptable alternative to substitute ADSL, which for most users would be limited to 1.5 mbps downstream and 128 kbps upstream, which isn't today considered adequate for any video service of higher quality than YouTube. This could all be credited to technology misadventure and forgotten if it weren't for the money. The telcos played games with state utility commissions, cutting deals with the states to deploy new technologies in exchange for "incentives," which were new charges and new ways of charging customers. One typical ploy was to offer to freeze basic telephone rates for a period of years (typically five) then deploy a bunch of new services, which would be sold on an a la carte basis. The problem with this is that it applied analog economics to what were now digital services. The cost of providing digital services is always going DOWN, not up, so the telcos that might have been forced to cut rates instead offered to freeze them, locking in an effective multiyear rate increase. It is an ugly story of greed and poor regulation that you can read in excruciating detail in a 406-page e-book that is among this week's links. The RBOCs cut heads, cut spending, cut construction, increased depreciation rates, failed to deliver promised services, increased telephone bills, and had booming profits as a result. Then each mega-merger brought with it new contortions that inevitably led to poorer service and higher charges. Twenty-two percent of telco equipment, for example, SIMPLY DISAPPEARED. Penalties for missing service goals were often folded into merger payments, so instead of paying the states a penalty for not doing what they had promised to, the companies paid themselves. As just a small example of the way the phone companies took advantage of ineffectual regulation, they charged an average of $1 per month per customer to run Bellcore, the research organization set up to replace Bell Labs after the 1983 split up of AT&T. But when Bellcore was later sold and the profits from that sale distributed to the telephone companies, not to the customers, ALL BUT ONE RBOC CONTINUED THE $1 CHARGE DESPITE THE FACT THAT IT NO LONGER DIRECTLY SUPPORTED ANYTHING. There are no good guys in this story. Misguided and incompetent regulation combined with utilities that found ways to game the system resulted in what had been the best communication system in the world becoming just so-so, though very profitable. We as consumers were consistently sold ideas that were impractical only to have those be replaced later by less-ambitious technologies that, in turn, were still under-delivered. Congress set mandates then provided little or no oversight. The FCC was (and probably still is) managed for the benefit of the companies and their lobbyists, not for you and me. And the upshot is that I could move to Japan and pay $14 per month for 100-megabit-per-second Internet service but I can't do that here and will probably never be able to. Despite this, the FCC says America has the highest broadband deployment rate in the world and President Bush has set a goal of having broadband available to every U.S. home by the end of this year. What have these guys been smoking? Nothing, actually, they simply redefined "broadband" as any Internet service with a download speed of 200 kilobits per second or better. That's less than one percent the target speed set in 1994 that we were supposed to have achieved by 2000 under regulations that still remain in place. http://www.pbs.org/cringely/pulpit/2...10_002683.html  Business View: Can Net Greedy-Guts Have Their Cake and Eat it? Andrew Murray-Watson It is hard to imagine, but the internet is filling up. Less than a decade ago, pioneering companies stuck huge pipes in the ground to cope with demand for data traffic that never arrived. Well, with the popularity of video sharing sites such as YouTube, as well as the dawn of internet broadcasting, internet capacity is starting to look a wee bit stretched. There is no need for alarm just yet, but the likes of BT and Tiscali, as well as AOL in the US, are firmly of the opinion that the media companies that are responsible for all this bandwidth-hungry content should contribute to the costs of upgrading the network. Failure to do so, they claim, will lead to tighter internet usage caps and higher prices for consumers. The BBC, for one, has shown little sympathy with the network owners' plight. The debate over who should pay for the distribution of content on the internet is just one aspect of the principle of net neutrality. In the UK, the ISPs have a legal duty to operate their networks for the benefit of all their customers. But what happens when an ISP is forced to limit access to one particularly bandwidth-hungry application (iPlayer, for example) to ensure all customers receive the same quality of connection? Suddenly the Net is not neutral any more and the network operator gets to decide what is allowed and what isn't. Companies that offer content as well as a broadband connection can then discriminate against their rivals' applications. Not that the ISPs are really that worried deep down. The price of internet access has been falling for years, driven lower by competition and regulatory pressure. But as spare capacity is reduced, so the value of bandwidth increases. Suddenly pipes in the ground are worth a whole lot of cash again. Security scaremongering And staying on internet-related matters, it seems that our distinguished peers in the House of Lords have discovered the web. The Lords Science and Technology Committee announced last week that the internet is now "a playground for criminals". What utter scaremongering tripe. The chairman of the committee is Lord Broers, who is so concerned about public security and wellbeing that he has never taken part in a vote on ID cards or anti-terrorism legislation, according to Public Whip, the political monitoring body. Anyway, despite admitting that the Government has no accurate figures on "e-crime", Lord Broers feels it is his place to lecture about the dangers of organised criminal gangs stalking cyberspace. "You can't rely on individuals to take responsibility for their own [internet] security", he proclaimed. Eh, sorry, just why not? That is like saying you can't rely on car owners to lock their vehicle at night or homeowners to set the burglar alarm when they leave the house in the morning. No one is ignorant of the dangers of online criminals. Yes, online identity theft and credit card fraud do exist and do cause problems. But anyone who takes sensible measures to install anti-virus software and a firewall (which incidentally arrives installed in most wireless routers) should not have a problem. The Government should be encouraging us to use the internet to communicate and to do business, not sticking a huge banner up over the web saying "Here be dragons". Trial by water Ofwat, the water regulator, is finally starting to show its teeth. It reiterated its concern last week about poor performance in key areas at Severn Trent Water, Southern Water and South East Water. As the recent floods have demonstrated, the need for water companies to invest in their infrastructure has never been greater. Water companies and the regulator decide on the level of investment and price increases over a five-year period. Ofwat then has the power to fine the companies if they fail to hit their targets. We are currently halfway through a five-year period and already the water industry is looking ahead to the next pricing settlement. Climate change will be the big battleground for the pricing review in 2009. And combating the impact of global warming with its associated extremes of weather will require increased investment. Water companies will argue that to meet this challenge they should be allowed to raise water prices to the consumer by a corresponding amount. But for that to be politically and socially acceptable, the companies have to do more to hit their targets this year and next. They must prove that they can spend extra resources efficiently. What Ofwat got wrong at the last review was to miscalculate the cost of borrowing. The regulator, when deciding what companies could charge their customers, overestimated how much it would cost to borrow the funds required to meet the industry's investment challenges. The result was higher than expected profits and disgruntled customers. Ofwat cannot afford to make the same mistake again. However, unless the industry gets its own house in order, persuading the consumer to accept much higher bills will be like trying to push water uphill. http://news.independent.co.uk/busine...cle2856776.ece  Internet Groups Warn BBC Over iPlayer Plans ISPs fear that introduction of web broadcasts will overload their networks as users download 'catch-up' TV Andrew Murray-Watson Some of the largest broadband providers in the UK are threatening to "pull the plug" from the BBC's new iPlayer unless the corporation contributes to the cost of streaming its videos over the internet. The likes of Tiscali, BT and Carphone Warehouse are all growing concerned that the impact of hundreds of thousands of consumers watching BBC programmes on its iPlayer – which allows viewers to watch shows over the internet – will place an intolerable strain on their networks. Some of the companies involved have told the BBC that they will consider limiting the bandwidth available to iPlayer – a process known as traffic shaping. The measure would limit the number of consumers who could access the iPlayer at any one time. A spokeswoman for Tiscali said: "The potential for iPlayer to suck up capacity is a concern and we need a better dialogue with the BBC about that." A senior insider at BT added: "It is certainly a live debate between ISPs [internet service providers] and the BBC. If the BBC gets the numbers it wants for iPlayer then network capacity could become an issue." Company representatives have expressed their concerns to Ashley Highfield, the director of new media and technology at the BBC. As more consumers access and post video content on the internet – using sites such as YouTube – the ability of ISPs to cope with the amount of data being sent across their networks is coming under increasing strain, even without TV broadcasters moving on to the web. Analysts believe that ISPs will be forced to place stringent caps on consumers' internet use and raise prices to curb usage. Attempts have been made by players in the industry to form a united front against the BBC by asking the Internet Service Providers' Association to lead the campaign on the iPlayer issue. However, to date, no single voice for the industry has emerged. The iPlayer will enable internet users to watch BBC programming on a seven-day catch-up basis, without charge. Once downloaded, programmes can be watched at any time for up to 30 days, with seven days to view them once started. Channel 4 and ITV have both launched internet players that have the potential to further eat into the network capacity of ISPs. New internet-only broadcasters such as Joost are also hoping to carve a niche for themselves in the UK. In a recent research note, Ian Maude, an analyst at Enders Analysis, the independent research house, said: "No broadcaster has rights clearance to distribute all its broadcast content over the internet. The BBC, for example, holds the rights for in-house produced programming, as well as catch-up TV and series stacking rights for independently produced programming from the UK, but few internet rights for acquired content, such as feature films and sports events." He added: "At launch, around 60 per cent of the BBC's weekly TV schedule will be available via the iPlayer. However, we anticipate that the strong affiliation of viewers with the broadcaster brands will drive usage of their catch-up TV services, despite less than comprehensive availability of programming." http://news.independent.co.uk/busine...cle2856766.ece  Report: Cable Companies Facing Big Bandwidth Crunch Eric Bangeman If you're starting to become frustrated with the download speed of your cable ISP or the relatively low number of HD channels available, you ain't seen nothin' yet. Your local cable provider will soon be faced with a serious bandwidth crunch, according to a new report released by ABI Research. The problem comes from more demanding applications, including high-definition video, video on demand, online gaming, and higher-bandwidth Internet applications. The result? Big problems—like fewer HD channels and sputtering download speeds—if the industry doesn't respond to the challenges in front of it. "The increasing bandwidth demands on cable operators will soon reach crisis stage, yet this is a 'dirty little industry secret' that no one talks about," said Stan Schatt, VP and research director for ABI Research. Currently, cable providers need close to 750MHz of spectrum to deliver the goods: about 676MHz for downstream applications like analog cable, digital cable, HD programming, video on demand, Internet data, and VoIP service. Upstream spectrum needs are comparatively paltry, totaling about 54MHz. 750MHz of spectrum isn't going to be enough in the future, says ABI Research. "Uploading bandwidth is going to have to increase," Schatt told Ars Technica. "And the cable providers are going to get killed on bandwidth as HD programming becomes more commonplace." Thus cable providers will need more spectrum to keep customers happy, according to the report, and it may be costly. In order to increase the amount of spectrum available, cable companies will have to make some significant hardware investments, including spectrum overlay devices that could provide up to 3GHz of spectrum. That should give cable companies bandwidth to enable cable providers to offer up to 54 HD channels (instead of just 12), increase its capacity for video on demand, and double download speeds on the ISP side of the business. It's going to be expensive work, especially for an industry that has already spent over $100 billion on infrastructure over the last decade. Beyond expanding the spectrum available to them, the cable companies have a few other ways to address the upcoming bandwidth crunch, Schatt told Ars. Those include rate shaping (controlling the rate at which data packets are transmitted), digital switching (more on that below), overlaying fiber over existing coaxial cable installations, and better MPEG-4 compression (which will lower the bandwidth overhead for HD video). IPTV the future "Digital switching is key," Schatt argues. "Ultimately, the cable companies will have to move to IPTV. They'll be brought kicking and screaming into the 21st century." IPTV is the technology of choice for AT&T's U-Verse video service. It works by treating video programming as IP data, enabling IPTV providers to send just a handful of channels at a time to a customer's house; traditional cable requires everything the provider carries to be pumped to the set-top box. Schatt believes the bandwidth savings from switching to IPTV will be enough to overcome resistance from the cable companies. Upgrading to a fiber infrastructure is a much more expensive proposition, and one more likely to occur in areas where the cable companies are facing more competition. It can happen, though—several years ago, Comcast's predecessor on the northwest side of Chicago laid fiber on top of its existing coaxial installation. The payoff is good for both cable companies and users, as it can result in more programming choices and faster Internet access. If cable companies are up to the challenge, the future looks a bit brighter for cable subscribers. They should be able to get more HD programming, faster download speeds, and better video-on-demand options. But if cable providers are unwilling or unable to address the bandwidth crunch, some of their customers will be on the lookout for Verizon and AT&T installation vans cruising through their neighborhoods. http://arstechnica.com/news.ars/post...th-crunch.html  Comcast Throttles BitTorrent Traffic, Seeding Impossible Ernesto Over the past weeks more and more Comcast users started to notice that their BitTorrent transfers were cut off. Most users report a significant decrease in download speeds, and even worse, they are unable to seed their downloads. A nightmare for people who want to keep up a positive ratio at private trackers and for the speed of BitTorrent transfers in general. ISPs have been throttling BitTorrent traffic for almost two years now. Most ISPs simply limit the available bandwidth for BitTorrent traffic, but Comcast takes it one step further, and prevents their customers from seeding. And Comcast is not alone in this, Canadian ISPs Cogeco and Rogers use similar methods on a smaller scale. Unfortunately, these more aggressive throttling methods can’t be circumvented by simply enabling encryption in your BitTorrent client. It is reported that Comcast is using an application from Sandvine to throttle BitTorrent traffic. Sandvine breaks every (seed) connection with new peers after a few seconds if it’s not a Comcast user. This makes it virtually impossible to seed a file, especially in small swarms without any Comcast users. Some users report that they can still connect to a few peers, but most of the Comcast customers see a significant drop in their upload speed. The throttling works like this: A few seconds after you connect to someone in the swarm the Sandvine application sends a peer reset message (RST flag) and the upload immediately stops. Most vulnerable are users in a relatively small swarm where you only have a couple of peers you can upload the file to. Only seeding seems to be prevented, most users are able to upload to others while the download is still going, but once the download is finished, the upload speed drops to 0. Some users also report a significant drop in their download speeds, but this seems to be less widespread. Worse on private trackers, likely that this is because of the smaller swarm size Although BitTorrent protocol encryption seems to work against most forms of traffic shaping, it doesn’t help in this specific case. Setting up a secure connection through VPN or over SSH seems to be the only solution. More info about how to setup BitTorrent over SSH can be found here. Last year we had a discussion whether traffic shaping is good or bad, and ISPs made it pretty clear that they do not like P2P applications like BitTorrent. One of the ISPs that joined our discussions said: “The fact is, P2P is (from my point of view) a plague - a cancer, that will consume all the bandwidth that I can provide. It’s an insatiable appetite.”, and another one stated: “P2P applications can cripple a network, they’re like leaches. Just because you pay 49.99 for a 1.5-3.0mbps connection doesn’t mean your entitled to use whatever protocols you wish on your ISP’s network without them provisioning it to make the network experience good for all users involved.” Customers on the other hand like to fully use their connection, and don’t agree that traffic shaping is the correct solution. One reader commented: “If you pay for an internet connection, that’s what you should get from your ISP — an internet connection. Not a connection that will let you browse the web and check email, but little else. If an ISP has issues with the amount of data a customer is transferring, then the ISP needs to address that issue with that customer, and not restrict every user in one class of traffic.” I guess this battle will go on for a while and I would advise Comcast users to try setting up a VPN connection to get around the traffic shaping, other users who find out that they are throttles might try BitTorrent encryption first, that seems to work quite well in most cases. More details about the Sandvine application can be found here. http://torrentfreak.com/comcast-thro...ng-impossible/  Video Surge Divides Web Watchers Pessimists say file swapping is creating traffic jam, but optimists, and a cisco report, call fears overblown Kevin J. Delaney and Bobby White Researchers have long warned that rapid increases in Internet usage could strain the capacity of the data lines and gear that make up the network, severely slowing traffic and even knocking out service. For years, they've been wrong as Internet-access providers and telecom carriers have added routers and other hardware to keep ahead of demand, and the data-carrying capacity of the Internet pipes has greatly expanded thanks to technical advances. But could the doomsayers be right this time? It depends on whom you ask. Prompting the latest concerns is the rapid growth of bandwidth-hungry applications like online video, file-sharing programs and Internet telephone service. Transmitting a minute of video can require 10 times the bandwidth of audio -- or more, depending on the quality. Already, peer-to-peer video swapping -- most of it illegal -- is estimated to represent in the range of more than one-third of all Internet traffic this year. U.S. Internet video sites alone transmit more data per month than was carried over the entire U.S. Internet backbone monthly in 2000, according to network gear maker Cisco Systems Inc. "One of the key possibilities for 2007 is that the Internet could be approaching its capacity," analysts at Deloitte Touche Tohmatsu wrote in a January report. "Our belief is we'll start to see some brownouts or service slowdowns or service issues," says Phil Asmundson, the national managing partner leading Deloitte & Touche USA's Telecommunications practice. But some analysts and Internet companies such as Google Inc. play down the idea that there's an impending crunch, pointing to the forecasters' poor track record of predicting such problems. There are also political implications to the debate. As part of the "network neutrality" scuffle in Washington, telecommunications companies say Internet companies should help foot the bill for more data lines and equipment if they're sending lots of video traffic at high speed to consumers One issue causing alarm is that access providers often don't have the gear in place to provide the bandwidth they promise to DSL or cable Internet customers. They practice oversubscription in the way airlines overbook planes with the expectation some people will fail to show up. Cable companies are particularly susceptible because their network design shares bandwidth among neighbors, allowing a few Internet users to degrade service by using more than their fair share. Some warn that new applications from start-ups and media companies using peer-to-peer technology to transmit TV shows online could increase any strain if they prove popular. Telephone companies face another challenge. Many own networks that are a hodgepodge of older equipment, much of which is inefficient at handling new forms of traffic like video. There are some other potentially critical spots, such as the points where data traffic from undersea lines and other big data pipes converge. Deloitte & Touche's Mr. Asmundson says major Internet hubs could struggle with the increases. Still, many say fears of significant strain are overblown. Eve Griliches, telecom analyst at research firm IDC, says five years ago analysts and engineers voiced concerns, but the result was a surge of innovation. "It feels like we are hyping again," she says. "When we did this before, we found intelligent ways to handle problems with bandwidth." Some of that innovation is now coming from network equipment makers such as Cisco Systems. The San Jose, Calif., company is expected to release new research findings today that predict Internet infrastructure capacity will keep up with traffic for the foreseeable future. Cisco and others are producing new gear aimed at better managing Internet traffic by prioritizing which bits of data are transmitted across the network. That contrasts with older equipment, which fulfilled a more basic task of moving vast amounts of data between countries and cities.  In its research, Cisco says consumer video will be responsible for a significant portion of the Internet-based traffic increases from 2006 to 2011, with video streaming and downloads increasing from 9% of all consumer Internet traffic last year to 30% in 2011. But the traffic generally isn't enough to overwhelm service providers, Cisco concludes. Google's YouTube, the most popular U.S. video-sharing site in terms of the number of views, represents only about 4% of North American consumer Internet traffic, it estimates. Network operators and access providers are "staying ahead of the curve," says Paul Bosco, vice president for video and broadband initiatives at Cisco. High-quality video delivered over the Internet to play on TV sets is a major wild card. If consumers begin downloading massive amounts of high-definition movies and TV shows, that could start clogging the so-called last-mile connections to homes. And the large size of such video files means that jams can occur even if not many people are accessing them. About 40 hours of high-definition video represent as much traffic as one million email messages. Vinton Cerf, Google's chief Internet evangelist, says changes in usage will help address the issue. "I believe people will get quite comfortable saying 'I want the following movies to watch,' and there will be systems online that will take care of scheduling and downloading and putting it on your hard drive," he says. Most involved in the debate acknowledge the perils of any predictions. Robert Metcalfe, a venture capitalist at Polaris Venture Partners who helped build the early Internet as an engineer, in a 1995 magazine column warned of a "catastrophic collapse" of the Internet in 1996. He vowed to eat his words if it didn't come to pass. There were some service outages, but Mr. Metcalfe eventually conceded he was wrong. At a 1997 conference, he put his column in a blender with liquid and slurped it down in front of the audience. Today, Mr. Metcalfe thinks online-video traffic could cause slowdowns in Internet service for consumers, but that could lead them to use online video less, resulting in a sort of equilibrium. "I've been talking about the next big Internet thing, 'the video Internet,' for years now," he says. "See -- some of my predictions do come true." http://online.wsj.com/article/SB1187...googlenews_wsj  FCC Commissioner: Pearl Jam Censorship Linked to Net Neutrality Fight Jon Stokes FCC Commissioner Michael Copps, fire-breathing advocate of network neutrality regulation and opponent of media consolidation, has taken a stand on AT&T's now infamous censorship of Pearl Jam front man Eddie Vedder's anti-Bush remarks at Lollapalooza. In an interview with OpenLeft.com's Matt Stoller, Copps supported the idea that there's a link between AT&T's deletion of Vedder's political comments from a webcast of the concert and the network neutrality fight that's brewing in the halls of Congress. "Events like this are connected to the larger issue of network neutrality, so it is very very important," Copps said in response to a question about whether or not AT&T's censorship of Vedder has any implications for network neutrality. He went on to say, "So when something like the episode occurs with Pearl Jam that you're referencing that ought to concern all of us... because if you can do it for one group, you can do it to any group and say 'Well, it's not intentional,' and things like that. But nobody should have that power to do that and then be able to exercise distributive control over the distribution and control over the content too. In the interview, Copps followed other network neutrality supporters in seizing on the incident as a prime example of the need for government regulation of companies like AT&T, in order to prevent them from censoring political speech on the larger Internet. This is in spite of the fact that from a purely technical standpoint, AT&T's censorship of Vedder on its own webcast, which is technically content that AT&T "owns" and is responsible for, has little apparent connection to network neutrality. After all, not even the most ardent net neutrality proponent would suggest that a company shouldn't be able to censor its own streaming webcasts—content that it funded and that it owns. However, in spite of the lack of a real technical or even a policy-level connection between what AT&T did to Vedder and the kind of router-level traffic shaping that net neutrality's supporters are opposed to, the censorship of Vedder's anti-Bush speech is so germane to the political, "people vs. the powerful" side of the network neutrality debate that it is a PR gaffe of the first order. AT&T's trust problems I said in a previous article on network neutrality that the efforts of some to turn net neutrality into a civil rights and free speech issue was a really bad idea, but AT&T seems bound and determined to make that connection all by themselves. The basic stance of AT&T and other telcos in the network neutrality debates is this: trust us to carry your network traffic— your video, your emails, you web surfing, and all the other stuff that you watch, read, hear, and say to friends, family, and the world via the Internet; trust us to handle the connections that you make online, be they personal, political, religious, frivolous, or whatever; trust us not to use our power over the network to insert unknown third parties and agendas into those connections that you make with the world. The tenability of this "trust us" premise was already damaged by revelations that AT&T has set up secret rooms at some of its major backbone facilities that let the NSA snoop the nation's network traffic as it goes over the wire, but (unfortunately) not everyone cares so much about faceless NSA snoops picking through their e-mail. However, this new incident, in which either the company or a party acting on the company's behalf has censored political criticism of one of the most unpopular presidents in American history, is bound to resonate with a whole new swath of the public. What's more, it appears that such political censorship is a pattern for AT&T. The Daily Swarm brings word from concertgoers, reporters, and even AT&T itself that the network has edited out the political commentary from webcasts of a whole host of concerts across the country. The bands affected by the censorship range from The Roots to The Flaming Lips, and fan emails are still pouring into blogs and media outlets alleging as-yet unreported censorship incidents. So this censorship scandal is still growing, and politically (if not technically) it strikes at the heart of the "trust us with your communications" premise that forms one of the two central pillars of the telcos' attacks on network neutrality legislation. (The other pillar is, "government regulation is scaaaarrryyyy... big, scary regulations stifle the free market...") If it continues to widen and gain real traction with the public, the concert censorship scandal may turn out to be the own goal that tips the net neutrality game into Copps and company's favor. http://arstechnica.com/news.ars/post...ity-fight.html  AT&T Neuters the BlackBerry 8820 in Favor of the iPhone Douglas Soltys Wow. I must say, this is probably the biggest piece of news we’ve ever broken here at BlackBerry Cool — and possibly the one that’s made us the angriest. We’ve just received word from one of our friends inside AT&T that the US carrier has been successful in their attempts to lockdown the GPS functionality in their upcoming BlackBerry 8820 so that the only functioning 3rd party software will be TeleNav. First, this is a major piss off to AT&T customers looking to get their hands on the BlackBerry 8820 mid-September, but what’s more important is why AT&T chose to do this. Apparently - and remember, this is coming from someone inside AT&T - the carrier didn’t want to launch a device that would seem superior (or be competitive) to the iPhone. Sounds a little crazy, until you realize that a GPS/Wi-Fi’d device with push email and no funny-texting touch screen that’s subsidized in price sounds a bit more appealing than a $500 device that enterprise customers can’t use. We’ve been told that RIM was apparently livid over the decision (and with good reason), but AT&T basically said “do it or we won’t buy the 8820 or any future devices from you” and RIM backed down. Our AT&T informant also said that this was a call made by top RIM/AT&T brass, which sheds new light on Jim Balsillie’s statement that the carriers are one of RIM’s three masters. http://blackberrycool.com/2007/08/16/005386/  Cingular's Class Arbitration Waiver Ruled "Unconscionable" By 9th Circuit Court Of Appeals Like many many companies, Cingular (AT&T) has a little thing in their contracts saying that if you use their service, you void your right to a class action lawsuit and instead have to go through "mandatory binding arbitration," which is basically an extra-judicial corporate court exempt from many of the basic rules and laws and procedures and rights of real court. Well, today, that clause was ruled "unconscionable" by the 9th Circuit Court Of Appeals. Therefore, lawsuits can proceed against Cingular and go to real court, not monkey court. Hooray! http://consumerist.com/consumer/vict...als-290806.php  German Security Professionals in the Mist German Information Security professionals were hopeful after proposed changes to the UK Computer Misuse Act Police and Justice Act amendments were suspended due to the fact that if certain clauses were enacted, it would effectively make the entire Information Security industry in the UK criminals. This hope was important because earlier this year the German Government had introduced similar language into Section 202c StGB of the computer crime laws, which would have made the mere possession of (creates, obtains or provides access to, sells, yields, distributes or otherwise allows access to) tools like John, Kismet, KisMAC, Nessus, nmap, and the ability to Google effectively a crime. Despite all efforts to peer through the mist about whether changes would be made to the proposed law, as of today it became active legislation. Penalties under the law include up to 12 months imprisonment, a fine, and potential linkage to terrorism related activities (at least as per sections 202a and 202b of the law). Despite some observers fearing a 'Kristallnacht' in the near future, and while it is likely there will be some abuses of the law (DMCA, for example), the overall effect to Information Security work and research in Germany is not likely to be all that great. That doesn't mean that changes aren't already happening. A number of security related products and groups have either closed up shop or relocated to countries of convenience, such as the Netherlands. KisMAC, an OS X wireless network discovery tool has ceased development and will soon be reappearing in the Netherlands. This was one of the first tools to suddenly cease production in a public manner. Phenoelit have also closed their German presence, though it may be possible to find their content available online in other locations. Those who can read German can see the response from the CCC, who are currently holding their Chaos Communications Camp 2007 near Berlin (think of DefCon, in a field, with tents). The CCC have decided that since the German Government took this move, that it means that there are no more security problems facing computer users. Stefan Esser, the noted PHP Security activist, has withdrawn all of the exploit code that originally accompanied the Month of PHP Bugs project. As Stefan points out: "The law does not affect our freedom of speech to report and inform about security vulnerabilities and how to exploit them. We are just not allowed to create/distribute/use software that could be used as "hacking tools"." Like many other legislative attempts to address real or perceived problems with computer-based activity, the law fails to account for reality. Others have pointed out that it is only those already engaged in illegal activity that are using 'hacking tools'. The legitimate security industry is using 'diagnostics' and other useful utilities. Already it seems that the law will have the unintended consequence of making legitimate research just that much harder, only deterring the legitimate researchers and the opportunistic attacker. The serious criminal will just keep on going with their malicious activity, probably a little bit bolder - safe in the knowledge that the German Government has just made it a little bit more difficult for them to be found. http://www.beskerming.com/commentary...ls_in_the_Mist  Study Finds Kids Justify Illegal Downloads Children in Europe are aware of the risks of illegal downloading, but often rationalize their act by saying that everyone -- including their parents -- is doing it, according to a major European Commission survey. Other excuses included: the download is for personal and private purposes; the Web sites presumably remunerate the artists; claims of harm inflicted on artists lack credibility; and DVDs and CDs are simply too expensive. Almost all of the children surveyed in the 27 European Union member countries as well as in Norway and Iceland said they expect to continue downloading. They also said the risk of downloading a virus was far more dissuasive than the risk of legal proceedings. The survey results, released Friday, found that most kids use the Internet several times a day and, while Internet use is to some extent limited by parents, most own their own mobile phones, the use of which is largely unsupervised. The survey also found that children are much more attuned to such potential online risks as security, viruses, identity theft and potential dangerous contact with strangers than parents imagine, and tend to know about the necessary precautions. http://www.reuters.com/article/techn...27122520070813  Digital Pirate or Entrepreneur? A peer-to-peer networker is convinced such practices won't be illegal in future, writes Dan Skeen. ONE gets the sense from chatting with Canadian Gary Fung that he is waiting for the tide to change. Great expectations are imbued in his answers, as if a single sweep of the moon could change his website from a black market to a media warehouse, convert his profile from digital pirate to entrepreneur, and turn the legal threats he receives into partnership offers. The 24-year-old has ample reasons for hope. The website isoHunt.com, which he created to help visitors find downloadable BitTorrent files (often containing illegally copied movies, music or software), has grown to 12 million visitors a month in just four years. While he won't disclose earnings, he says he still earns a profit despite a recent $33,000 hardware upgrade, $6640 each month for hosting, and legal fees that he has estimated at $22,000 a month. But perhaps the greatest promise lies in the shifting sands of media distribution, stirred by disruptive models including Napster and YouTube, which have many experts believing that the shared processing power of peer-to-peer (P2P) networking is the inevitable path forward for mainstream media. Mr Fung longs for the day when big media players become buyers rather than a barrier. "BitTorrent really helps make content distribution cheaper and faster," he says. "The natural progression, as we've seen with YouTube and MySpace, is a lot more media distribution is going to be done online, and that's going to converge with the client and P2P technologies." He envisions a model for fee-based "premium" torrents, where corporations distribute higher-quality torrents than those currently uploaded by amateurs, using corporate bandwidth as well as the scalable efficiency of P2P networks to deliver downloads faster. Yet aside from some pay-per-download partnerships at BitTorrent.com, the entertainment industry has been slow to embrace P2P technology. While Mr Fung waits for success and recognition, his court date awaits him. In February 2006, a lawsuit was initiated against isoHunt.com by the Motion Picture Association of America, an advocacy group representing entertainment giants including Warner Bros and 20th Century Fox. The MPAA press release cites a study by Smith Barney estimating losses of $US5.4 billion ($A6.3 billion) due to film piracy in 2005. "Mr Fung has chosen not to enter into any negotiations with anybody, but rather to steal that creativity and to use it for his own ends in an unlawful manner," MPAA spokesman John Malcolm said in a televised interview. Unlike many small enterprises that the MPAA has litigated into extinction, Mr Fung has dug in his heels, hiring a Los Angeles-based legal firm to represent him. As a portal to more than 500 terabytes of torrent files, isoHunt.com is an obvious target. The distributed nature of P2P sharing, in which hundreds of users will simultaneously upload and download the same file with each other, is a daunting challenge for the MPAA. Its strategy has been to attack the enablers, such as newsgroups listing torrent file locations and search engines that index torrent files. Mr Fung maintains that his site is nodifferent from a typical search engine like Google or Yahoo. IsoHunt.com is a searchable index of files shared by millions worldwide. When you find and connect to the latest blockbuster film on isoHunt.com, you can download a small torrent file, but this file only contains information on where the actual media content will be downloaded from. "It's all search engines," he says, pointing out that you can also find torrent files by searching Google's index. Bolstering his defence, Mr Fung employs a copyright policy modelled after the Digital Millennium Copyright Act created by US Congress in 1998, a stricter policy than required under Canadian law. When violations are submitted, he removes the listing from the search engine index, a process similar to Google's for handling copyright complaints, but with greater efficiency. "Google's process is to return documents through snail mail, whereas we use email," Mr Fung says. Mr Fung is confident he'll win his case. But that potential outcome probably won't erase his frustration with the litigious antics of an industry that, he feels, suppresses innovation in order to save a distribution model in need of reinvention. "I think copyright holders will have to accept the internet as a new way of distributing content and not just look at it as a liability," he says. For now, it's a David and Goliath-like battle. Mr Fung is accountable to perhaps even more imposing advisers, his parents. He lives at home with his parents who emigrated from Hong Kong to British Columbia, Canada, 13 years ago. "I've explained what I can to them," he says. "I think the copyright issue is something that's going to come up more and more with the internet and I think they understand that I'm already doing what I can." Mr Fung's persistence is evident, but his motives are less clear. It's hard to tell whether current profit, future potential or a simple love of new technology drives him. One thing is clear - the hobby he began as a computer science student at the University of British Columbia has become a day job, taking more than eight hours each day. In perhaps the same way that Jerry's Guide to the World Wide Web became Yahoo, Mr Fung's enterprise has changed from a hobby to a business based on an enthusiastic community of early-adopting users. With his name high on the MPAA's most-wanted list, one wonders how much long-term career risk the young man is taking on. Phil Morle, CTO of online storage company Omnidrive, has an answer for that. He cut his teeth in P2P with a popular client Kazaa, a role that earned him fame in P2P circles but also earned him an appearance in Australia's Federal Court in 2004. He believes innovation will go far in the marketplace. "P2P platforms were the origin of the two-way web," Mr Morle says. "People who have worked in the fires of P2P understand how the web is changing and will never be out of work on the modern internet." http://www.theage.com.au/news/web/bi...57427342.html#  New Jersey Attorney General Asks for Crackdown on Peer Networking Sites Kylie Comfoltey The New Jersey attorney general asked a dozen Internet social networking sites to find out whether convicted New Jersey sex offenders have created profiles on their sites. The request came after the state found at least 269 convicted New Jersey sex offenders had registered on the popular Internet social networking site MySpace.com. MySpace.com found 29,000 total profiles created by convicted sex offenders, which clearly violates the conditions of parole for such offenders. Among the peer to peer network sites that received the request from New Jersey’s AG were Xanga.com, Facebook, Community Connect, TagWorld, Bebo, MyYearbook.com, Tagged, Friendster, LiveJournal, Imeem, Hi5 and Gaia Online. The cooperation of peer to peer network sites with law enforcement can help make the internet safer. Protecting people from the dangers posed by sexual predators who may use peer to peer networking sites to contact victims is the goal. http://blog.madisonwhoswho.com/publi...tworking-sites  Controversial LimeWire Takes on iTunes P2P service turns to legit music downloads Oliver Garnham Lime Wire LLC, maker of the controversial LimeWire file-sharing software, plans to go legit with a new music download service. Founded in 2000, LimeWire is better known as a peer-to-peer (P2P) networking service that's been accused of allowing internet users to illegally download movies, TV programmes and music. The company is currently involved in a legal wrangle with the Recording Industry Association of America (RIAA), which is seeking to fine LimeWire $150,000 for every song that's downloaded using the P2P tool. But LimeWire now hopes to make a name for itself as a legitimate music download store. Initially the store will be a standalone website, also accessible from links in the file-sharing software. Future versions will allow users to browse and purchase music directly from within the LimeWire program. The first partners to provide songs to the new digital channel are IRIS Distribution and Nettwerk Productions. "We are delighted to collaborate with these forward-thinking music companies and sell their authorised content through LimeWire," said Jesse Rubenfeld, Lime Wire Chief Financial Officer. Tracks purchases from the LimeWire Store will be supplied in the MP3 format. Customers will be able to buy songs and albums 'a la carte' or as part of monthly subscription plans. http://www.pcadvisor.co.uk/news/index.cfm?newsid=10427  15 Most Popular Torrent Websites | August 2007 Here are the 15 Largest Torrent Websites ranked by a combination of Inbound Links, Google Page Rank, Alexa Rank, and U.S. traffic data from Compete and Quantcast. Although no traffic metrics are completely accurate we do believe the data below to be useful for gauging relative audience size. 1 | mininova.org 3,791,083 - Inbound Links | 726,768 - Compete Monthly Visitors | 289,540 - Quantcast Monthly Visitors | 106 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 2 | ThePirateBay.org 416,930 - Inbound Links | 800,379 - Compete Monthly Visitors | 501,754 - Quantcast Monthly Visitors | 235 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 3 | torrentspy.com 472,718 - Inbound Links | 737,968 - Compete Monthly Visitors | 247,220 - Quantcast Monthly Visitors | 190 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 4 | isohunt.com 187,755 - Inbound Links | 528,547 - Compete Monthly Visitors | 179,956 - Quantcast Monthly Visitors | 245 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 5 | Torrentz.com 290,511 - Inbound Links | 468,963 - Compete Monthly Visitors | 306,920 - Quantcast Monthly Visitors | 325 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 6 | TorrentPortal.com 692,296 - Inbound Links | 226,771 - Compete Monthly Visitors | 128,629 - Quantcast Monthly Visitors | 1,128 - Alexa Ranking. | Page Rank: 5 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 7 | BitTorrent.com 354,645 - Inbound Links | 300,792 - Compete Monthly Visitors | 201,081 - Quantcast Monthly Visitors | 1,633 - Alexa Ranking. | Page Rank: 8 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 8 | Demonoid.com 129,733 - Inbound Links | 233,203 - Compete Monthly Visitors | 62,043 - Quantcast Monthly Visitors | 364 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 9 | myBittorrent.com 233,557 - Inbound Links | 170,490 - Compete Monthly Visitors | 90,473 - Quantcast Monthly Visitors | 2,549 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 10 | Fenopy.com 727,746 - Inbound Links | 138,125 - Compete Monthly Visitors | 67,011 - Quantcast Monthly Visitors | 4,384 - Alexa Ranking. | Page Rank: 5 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 11 | BiteNova.nl 81,202 - Inbound Links | 109,900 - Compete Monthly Visitors | 87,816 - Quantcast Monthly Visitors | 4,513 - Alexa Ranking. | Page Rank: 5 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 12 | TorrentBox.com 3,163,783 - Inbound Links | 79,972 - Compete Monthly Visitors | 19,513 - Quantcast Monthly Visitors | 2,859 - Alexa Ranking. | Page Rank: 5 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 13 | meganova.org 204,757 - Inbound Links | 108,390 - Compete Monthly Visitors | 74,193 - Quantcast Monthly Visitors | 2,362 - Alexa Ranking. | Page Rank: 5 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 14 | snarf-it.org 329,741 - Inbound Links | 59,862 - Compete Monthly Visitors | 29,614 - Quantcast Monthly Visitors | 4,304 - Alexa Ranking. | Page Rank: 6 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA 15 | TorrentReactor.to 295,632 - Inbound Links | 60,678 - Compete Monthly Visitors | 27,194 - Quantcast Monthly Visitors | 5,291 - Alexa Ranking. | Page Rank: 5 15 Most Popular Torrent Websites | Posted 8/16/2007 | eBizMBA http://www.ebizmba.com/articles/torrents.html  Via Daddydirt The Good of the Many Jack http://www.torrentz.com/ Typing a query in the above page automatically runs it through several popular torrent search sites. http://www.p2p-zone.com/underground/...2&postcount=12  Easy Money Isn’t That Easy Dan Mitchell GUY KAWASAKI, venture capitalist, business pundit and Apple’s first “evangelist,” posited that it’s “easy” to become an Internet millionaire, as long as you have a good idea. You don’t even have to work hard: a couple of hours a day in your underwear should be enough. Mr. Kawasaki was host of a panel discussion June 14 at the Churchill Club, the Silicon Valley public affairs forum, titled “No Plan, No Capital, No Model ... No Problem: Companies That Defied What V.C.’s Will Tell You.” Videoand audio of the event are available on Mr. Kawasaki’s blog, How to Change the World (blog.guykawasaki.com). Mr. Kawasaki said there were two “pivotal moments” in his professional life. The first was meeting Steve Jobs and seeing a Macintosh computer for the first time. The second was “hearing James Hong explain the model for Hot or Not.” Users of Hot or Not (hotornot.com), introduced seven years ago, look at pictures of people and vote on how attractive they are. It was, Mr. Hong told the group, “a joke of an idea.” But when people thronged to the site, he realized he had a business. And it has made him and his partner, Jim Young, rich. Mr. Kawasaki said his “hero” is Markus Frind, founder of PlentyofFish.com, a free dating site. “And by the way, he makes $5 million, $6 million a year with Google ads.” But is it really so easy? Maybe sometimes, says Glenn Kelman, the founder of Redfin, the online real estate broker, but it shouldn’t be. “Hard has gone out of fashion,” Mr. Kelman wrote on Mr. Kawasaki’s blog. “Does anybody remember the old video of Steve Jobs launching the Mac? He had tears in his eyes.” (The video is on YouTube.) Mr. Jobs wasn’t choking back tears just because of his success, Mr. Kelman wrote, but also because of the “tinkering, kvetching, nitpicking, wholesale reworking, and spasms of self-loathing that go into a beautiful product.” “It was all being paid back in a rush.” In other words, you can work to achieve greatness, or you can work in your underwear for two hours a day. The two rarely go together. http://www.nytimes.com/2007/08/11/bu.../11online.html  Who Owns the Concept if No One Signs the Papers? Jason Pontin WHO owns a bright idea? If the technology associated with an idea is new and the opportunities it offers are valuable, it will have many authors — most of whom may argue over ownership. When disputes over the provenance of an idea become particularly turbid, disappointed entrepreneurs will look to the courts, which often are of little help. As Lawrence Lessig, a professor at Stanford Law School, said, “The general rule is that ideas are free unless strapped down by contract or patent.” In practice, a great idea is owned by whoever expresses that idea most successfully. Consider the case of Mark Zuckerberg, founder and chief executive of Facebook, the fast-growing social networking Web site, who is being sued by Cameron and Tyler Winklevoss, twin brothers who were founders of ConnectU, another social network. Today, Facebook enjoys much of the glamour that Google had when it was new. As of July, more than 30 million people, mostly young and college-educated, had registered on the site, according to the company. Facebook’s users share information about themselves with friends, send private messages to one another and hang out in groups formed around different interests and hobbies, where they can swap Web links and files like photographs and videos. “It is one of the sites with true utility, focused on real relationships, rather than Webcam girls with 10,000 friends,” Jonathan Abrams, the founder of Friendster, the first successful social network and now the chief executive of Socializr, an events planning Web site, wrote in an e-mail message. This utility and privacy may soon have real value. For now, Facebook is a private company: its value is whatever its investors, who include the venture capital firm Accel Partners and the angel investor Peter Thiel, a co-founder of PayPal, tell each other it’s worth. But last year, according to published reports, Yahoo offered $900 million for Facebook, which earns its money from demographically targeted advertising and sponsorships. The start-up was not for sale then, but when it is sold or floats shares in an initial public offering, Mr. Zuckerberg, who is 23, will be rich. The Winklevoss brothers and Divya Narenda, another ConnectU founder, contend that Facebook’s founder stole the idea from them. In a suit filed in 2004, the ConnectU founders accused Mr. Zuckerberg of lifting their site’s source code and business plan when he worked for ConnectU as an unpaid programmer. They are asking that Facebook’s assets be transferred to them. Here are the facts that are not disputed: In 2002, when the Winklevoss brothers were juniors at Harvard, they conceived what was initially called the HarvardConnection, which was to be a social network for the college. In November 2003, they asked Mr. Zuckerberg, who was studying computer science at Harvard, to develop the site’s software and database, promising to compensate him later if the venture prospered. Mr. Zuckerberg abandoned the project in February 2004, a month after registering the domain name thefacebook.com. By the end of that February, his new site, also a social network for Harvard, had registered half the college’s undergraduates. By April 2004, it had spread to other Ivy League schools. Very quickly, thefacebook expanded to serve other universities, then high schools, then organizations as varied as McDonald’s and the Marine Corps, and finally the general public. By contrast, ConnectU never really got started: it didn’t open until May 2004, and, overshadowed by what became, simply, Facebook, today it has no more than 70,000 registered users. In their suit and in public statements, the Winklevoss brothers contend that Mr. Zuckerberg promised to finish coding before the brothers left college in June 2004 and that he procrastinated to gain a competitive advantage. Mr. Zuckerberg and Facebook’s lawyers say that there was no binding contract between the two parties. Who is in the right? Judge Douglas P. Woodlock of United States District Court in Boston, who is considering a motion by Facebook to dismiss ConnectU’s suit, might agree with Mr. Zuckerberg. At a hearing on July 25, he scolded John F. Hornick, ConnectU’s lawyer, over what the judge saw as his inability to provide documentary evidence, saying, “Dorm-room chitchat does not make a contract.” He gave ConnectU two weeks to prepare a better case. The parties and their lawyers declined to be interviewed for this column. I SUSPECT that Facebook would not exist had it not been for ConnectU. But in an interview, R. Scott Feldmann, an intellectual property lawyer and a partner at Crowell & Moring, explained why the judge should nevertheless dismiss the case. Ideas, Mr. Feldmann explained, are protected either by trade-secret contracts or by patents and copyrights. “Trade secrets may be maintained indefinitely,” he said, but “it does not appear that ConnectU had Zuckerberg sign a nondisclosure agreement, and disclosing a trade secret to someone without doing so would ordinarily result in loss of any trade secret status.” At the same time, Mr. Feldmann said, “copyright will not protect ideas themselves, only their expression” — in a Web site’s underlying source code, for instance. But if Mr. Zuckerberg was an unpaid, casual worker at ConnectU, and not an employee, then “he owns the code,” Mr. Feldmann said. Thus, even if the ConnectU plaintiffs can prove that the codes of two social networking sites were similar (an argument that Facebook seems confident it can refute), the Winklevosses might have no claims on Mr. Zuckerberg. “On the surface, it appears ConnectU will have some challenges,” Mr. Feldmann said. Many may sympathize with the Winklevoss twins. But in the absence of any formal contract, the twins are, in effect, arguing that they have rights to Mr. Zuckerberg’s imagination and experiences. In my book, that would be a constraint on the free marketplace of ideas. http://www.nytimes.com/2007/08/12/bu...=1&oref=slogin  Facebook PHP Leaker Revealed Pete Cashmore We got an email a few minutes ago from the guy claiming to be the Facebook PHP code “leaker”: Trae McNeely, a graduate of the University of Oklahoma. Based on the link to the forum thread he provided, we were able to confirm the story below. There are rumors about who leaked the Facebook code the other day. Well your answer is me. Actually, “leaked” isn’t the correct term. I didn’t have any access to their servers and I don’t know any employees. Despite what you may think about my website I don’t hack and I’ve never had intentions to. If you look at Digg and do a little searching you’ll notice that the code was posted on this site wmdtalk at the following address http://www.wmdtalk.com/showthread.php?p=1319 which has been taken down. So I posted it thinking this is something I and other can study. Was it wise, no, risky yes! When you really sit down and think about it the source code showed up on my browser not because someone leaked it to me or I took it. The code was the fault of Facebook. They must have been updating their servers or a database was down. Now, I submitted this 2 or 3 days ago. I posted it thinking, “oh well it won’t be a big deal”. Well, within several hours I received an email threatening legal action against me. Although we were dubious of the story at first (it’s posted on a “make money” forum”), this is legit. McNeely claims that he posted the code to the forums at the weekend, and that story got posted to Digg, receiving 6 Diggs - the story is here. The forum thread was then pulled by McNeely in response to a takedown request from Facebook, but lives on in the Google cache. A screenshot is included below. The code was later reposted by FacebookSecrets, a blogspot blog, and got thousands of Diggs. But a quick check on Digg (search for PHP or another unique term) shows that the wmdtalk story was the first chronologically. In other words: McNeely was the source and FacebookSecrets was a copy. The question is: is what he did illegal, as Facebook claims? Seeing as the code was served to his browser and there was no “hack” involved, it seems unlikely. McNeely isn’t completely new to leaking sensitive data, however: he also claims responsibility for the posting of the Nicolas Berg beheading video and Kobe Bryant’s accuser’s information. http://mashable.com/2007/08/13/facebook-leaker/  Social Networking Meets Music Sites Jenna Claffey Social networking has continued to expand its empire, and music sites have become its latest victims. From January to June of 2007, the sites where listeners are able to listen to music and interact with other listeners for minimal or no cost, such as projectplaylist.com and rhapsody.com, have had a noticeable increase of unique visitors over sites where there is little interaction with other listeners, such as itunes.com and napster.com. The site with the most traffic in 2007 is projectplaylist.com, which has such features as creating your own profile, creating your own playlist, sharing playlists with friends, blogging. It also offers the option of posting your playlist on several social networking sites such as Facebook, MySpace, etc. Rhapsody.com, another site that has been gaining significant ground over the year, allows members to personalize updates and features, and visitors can view other listeners’ playlists and watch music videos for free. In contrast, iTunes.com, musicmatch.com, and napster.com have all dropped in UVs since January. These are all pay sites, except for free.napster.com, which offers only free music. However, the extent to how much listeners can personalize their players and adapt it so others can easily view their music is limited. Will these sites be able to keep up with the growing personalization fad? Stay tuned… http://blog.compete.com/2007/08/10/p...e-music-sites/  Masters of the Arcade Caught in a Replay Seth Schiesel ON a nondescript street in a typical subdivision in this suburb 12 miles northeast of Seattle, Steve Wiebe, 38, pursues a thoroughly modern goal. Many nights after his two children are in bed, he settles on a stool in his garage not far from the hot-water heater, his Craftsman lawnmower and the ceremonial paddle from his college fraternity. He turns on a video camera mounted on the wall over his shoulder, takes a breath, cricks his neck and attempts to set a world-record high score at Donkey Kong. Yes, Donkey Kong, that vintage 1981 video game and Reagan-era relic of bowling alleys, waiting rooms and pizza parlors. Under Mr. Wiebe’s precise, almost surgical command, the tubby on-screen character known as Mario, in red hat and overalls, scales ladders, leaps barrels and navigates a construction site as he tries to save a damsel in distress from the game’s eponymous ape. “I was looking for something that I could be in control of,” Mr. Wiebe, now a schoolteacher, said recently in his kitchen while he heated a bowl of clam chowder for his 10-year-old daughter. “I felt like everything in my life was being decided by others. Donkey Kong was something I could do, and if I failed, I would have no one to blame but myself.” While Mario, the mascot of the multibillion-dollar Nintendo company, has in some quarters become more recognizable than Mickey Mouse, and a symbol of a gaming industry that rivals Hollywood in its revenues and cultural influence, gamers like Mr. Wiebe have remained frozen in time. As games have grown more complex in the last 25 years, gaming itself has become a mainstream (if not totally cool) pursuit. That evolution might never have happened if not for the small cadre of early, obsessive players who fostered the pastime through its awkward years. MANY grown-up gamers have since moved on to more sophisticated fare, but a small subset of nostalgists has gravitated toward the simple, repetitive but addictive games from the genre’s Paleolithic era. While most gamers seek the flashiest graphics and deepest stories, the die-hards keep flicking joysticks on decades-old machines. Some want no greater validation than their initials on a high-score list; others spend years pursuing records that might offer pixelized immortality. “If you go to a rock concert or something, you’re just observing,” Mr. Wiebe said. “If you see a movie, it’s the same ending every time. But every time you start a game, not only can something different happen, but you’re actually involved in making it happen. That’s pretty exciting, and that’s what keeps people coming back.” Mr. Wiebe, whose personal quest for the record is the subject of a forthcoming documentary, “The King of Kong: A Fistful of Quarters,” had his first showdown with Donkey Kong as a 13-year-old in 1982 at a Pizza Haven in nearby Bellevue, just as millions of others around the world were also discovering video games. But it wasn’t until he was laid off from Boeing a decade ago that he dedicated himself to breaking the world record — 874,300 points — which was set in 1982 by a 17-year-old in South Florida named Billy Mitchell. “Video games were it back then,” said Mr. Mitchell, now 42. “They were everywhere. They were more powerful, more influential than movies or music. But more than the games themselves, it was the culture of the arcade. It was where people went to compete, to excel.” Today, Mr. Mitchell lives in Hollywood, Fla., where he operates two restaurants and makes several lines of hot sauce. But since the early ’80s he has also been the most visible of a group of players whose high-score feats on arcade games like Defender and Ms. Pac-Man have occasionally commanded the attention of the mainstream news media. His teenage self has been permanently preserved in a 1983 Life magazine portrait of the young gaming scene’s most accomplished players. (He appears in a hooded sweatshirt, squinting slightly, while standing behind a Centipede machine.) It can be easy to forget that video games were considered an exciting evocation of the modern age when they first burst into popular consciousness. When Mattel wanted to sell its home game console, the Intellivision, to picky players, the toy company hired the erudite George Plimpton as its spokesman. In the 1983 James Bond adventure “Never Say Never Again,” a tuxedo-clad Sean Connery faces off against Maximilian Largo, the evil genius played by Klaus Maria Brandauer, not at a baccarat table but at a video game in a casino. But in the late ’80s, with the advent of inexpensive, relatively powerful home consoles like the original Nintendo Entertainment System, video games retreated from the public sphere. Gaming became something you did at home, probably alone. The image of the isolated, desensitized game geek entered the vernacular. And there it has remained, at least in mainstream white culture. (In urban and black communities, the overwhelming popularity of sports video games, as opposed to fantasy and science-fiction fare, has meant that games have never been considered quite as nerdy.) Now, as the first generation to grow up with video games dips its toes into the deep pool of middle age, gaming is entering another era of respectability. Nintendo’s new Wii consoles grace the living rooms of young professionals who would never have been caught dead with an original PlayStation, while their parents play Sudoku on handheld game units. Two weeks ago, CBS became the first American broadcast network to televise competitive video games as a sport, an innovation that can rightly trace its origins to Mr. Mitchell and his arcade crew. “The Billy Mitchells of the world, they are the foundation of the pyramid for where gaming is today,” said Andy McNamara, the editor-in-chief of the video game magazine Game Informer. “These guys have kept the history alive for all these years.” And as younger players continue to rediscover first-generation games on 21st century consoles, they are also introduced to the fanatical button-pushers who helped bring them national attention. “The kids on Xbox Live don’t necessarily know who these are guys are at first,” Mr. McNamara said, “but then they download a classic game like Pac-Man or Donkey Kong, and they do a little research online, and they realize that someone like Billy Mitchell set the record before they were even born.” Meanwhile, the lives of these gamers continue to provide fodder for movies: the documentary “Chasing Ghosts: Beyond the Arcade,” which chronicles the lives of several players in that Life magazine photograph, was shown at the Sundance Film Festival this year. New Line Cinema has the rights to make a fictionalized version of “The King of Kong.” Of course, every great story needs a villain, or at least a foil. In “The King of Kong,” that role falls to Mr. Mitchell and what are portrayed as the corrupt cabal of gamers who conspire to deny Mr. Wiebe his rightful place in the digital firmament. Mr. Mitchell said he is used to these kinds of caricatures, but also said the film had been slanted to provide an easily digestible morality play. “I don’t have a problem being laughed at and being made fun of,” Mr. Mitchell said. “But I feel it’s incredibly wrong to take these people who trusted them and criminalize them when it’s clearly not the case. They take people who are dedicated to the hobby, and give their time and effort and resources, and show them to be corrupt and incompetent. It’s absolutely absurd.” For now, Mr. Mitchell has the last laugh. Last year, Mr. Wiebe set a Donkey Kong record of 1,049,100 points. But last month, in a 2-hour 39-minute marathon at the annual convention of the Florida Association of Mortgage Brokers, Mr. Mitchell topped him with a score of 1,050,200. (Mr. Mitchell agreed to play at the ’80s-themed convention after organizers made a donation to the Make-A-Wish Foundation.) Back in the garage in Redmond, Mr. Wiebe said Mr. Mitchell’s latest score was just one more barrel to leap over. “I don’t feel like my skills are deteriorating,” Mr. Wiebe said. “Actually, I keep learning new things about this game and I look forward to the competition. It’s almost scary that Billy and I could keep at this for a while.” http://www.nytimes.com/2007/08/12/fashion/12kong.html  Time to get that trench coat Spy Agency OKs Bloggers as Journalists Justin Rood Are bloggers part of the news media? The U.S. government -- led by two of its most secretive agencies -- is increasingly saying, "Yes, they are." Despite the rap that bloggers simply "bloviate" and "don't try to find things out," as conservative newspaper columnist Robert Novak once sniffed, the Central Intelligence Agency (CIA) and the National Security Agency (NSA) have altered policies to indicate they're taking blogs seriously, and a growing number of public offices are actively reaching out to the blogosphere. The CIA recently updated its policies on Freedom of Information Act requests to allow bloggers to qualify for special treatment once reserved for old-school reporters. And last August, the NSA issued a directive to its employees to report leaks of classified information to the media -- "including blogs," the order said. Experts say it's part of a trend. Earlier this year, the criminal trial of former White House aide I. Lewis "Scooter" Libby was the first time a federal court had issued press credentials to bloggers. A rotating pool of five to 10 bloggers sat alongside dozens of traditional media reporters to hear the government try and convict one-time aide to Vice President Dick Cheney on perjury and obstruction of justice charges stemming from the leak of an undercover CIA operative's identity. "'The press' has been expanded," said New York University journalism professor (and blogger) Jay Rosen. "It's not fundamentally different than other moments in earlier eras," Rosen explained. "Radio reporters had to be added to newspaper reporters, which were originally 'the press.' Public institutions had to make accommodations for television cameras when they became part of 'the press.'" While some agencies are changing their policies -- in the CIA's case, they are granting bloggers a waiver on fees for copying the documents it releases to requesters once available only to traditional media -- many press offices still dismiss bloggers' inquiries, Rosen said. The political world, however, has embraced bloggers, according to Rosen. Presidential campaigns hold lunches and meetings with their candidates and popular bloggers, and congressional offices regularly hold conference calls to share information with bloggers and answer questions. The CIA's new fee waiver for bloggers, first reported by Government Executive magazine, may be more of a symbolic gesture than anything else, however: the spy agency released a mere 344 complete documents as a result of FOIA requests in 2006, according to an April study by ScrippsNews. A CIA spokesman noted his agency had also made 1,000 "partial" releases of information to FOIA requests during that period. This post has been revised. http://blogs.abcnews.com/theblotter/...ency-oks-.html  Merv Griffin, Television Impresario, Dies at 82 Bob Thomas Merv Griffin, the entertainer turned impresario who parlayed his ''Jeopardy'' and ''Wheel of Fortune'' game shows into a multimillion-dollar empire, has died. He was 82. Griffin died of prostate cancer, according to a statement from his the family that was released by Marcia Newberger, spokeswoman for The Griffin Group/Merv Griffin Entertainment. From his beginning as a $100-a-week San Francisco radio singer, Griffin moved on as vocalist for Freddy Martin's band, sometime film actor in films and TV game and talk show host. His ''The Merv Griffin Show'' lasted more than 20 years, and Griffin's said his capacity to listen contributed to his success. ''If the host is sitting there thinking about his next joke, he isn't listening,'' Griffin reasoned in a recent interview. But his biggest break financially came from inventing and producing ''Jeopardy'' in the 1960s and ''Wheel of Fortune'' in the 1970s. After they had become the hottest game shows in television, Griffin sold the rights to Coca-Cola for $250 million in 1986, retaining a share of the profits. After they became the hottest game shows in television, Griffin sold the rights to them to the Columbia Pictures Television Unit for $250 million, retaining a share of the profits. He started spreading the sale money around in treasury bonds, stocks and other investments. He made Forbes' list of richest Americans several times and started putting money in treasury bonds, stocks and other investments. But he went into real estate and other ventures because ''I was never so bored in my life.'' ''I said, `I'm not going to sit around and clip coupons for the rest of my life,' '' he recalled in 1989. ''That's when Barron Hilton said, `Merv, do you want to buy the Beverly Hilton?' I couldn't believe it.'' Griffin bought the slightly passe hotel for $100.2 million and completely refurbished it for $25 million. Then he made a move for control of Resorts International, which operated hotels and casinos from Atlantic City to the Caribbean. That touched off a feud with real estate tycoon Donald Trump. Griffin eventually acquired Resorts for $240 million, netting a reported paper profit of $100 million. ''I love the gamesmanship,'' he told Life magazine in 1988. ''This may sound strange, but it parallels the game shows I've been involved in.'' It was in 1948 that Martin hired Griffin to join his band at Los Angeles' Coconut Grove at $150 a week. With Griffin doing the singing, the band had a smash hit with ''I've Got a Lovely Bunch of Cocoanuts,'' a 1949 novelty song sung in a cockney accent. The band was playing in Las Vegas when Doris Day and her producer husband, Marty Melcher, were in the audience. They recommended him to Warner Bros., which offered a contract. After a bit in ''By the Light of the Silvery Moon,'' starring Day and Gordon MacRae, he had a bigger role with Kathryn Grayson in ''So This Is Love.'' A few more trivial roles followed, then he asked out of his contract. In 1954, Griffin went to New York where he appeared in a summer replacement musical show on CBS-TV, a revival of ''Finian's Rainbow,'' and a music show on CBS radio. He followed with a few game show hosting jobs on TV, notably ''Play Your Hunch,'' which premiered in 1958 and ran through the early 1960s. His glibness led to stints as substitute for Jack Paar on ''Tonight.'' When Paar retired in 1962, Griffin was considered a prime candidate to replace him. Johnny Carson was chosen instead. NBC gave Griffin a daytime version of ''Tonight,'' but he was canceled for being ''too sophisticated'' for the housewife audience. In 1965, the Westinghouse Broadcasting introduced ''The Merv Griffin Show'' in syndicated TV. At last Griffin had found the forum for his talents. He never underestimated the intelligence of his audience, offering such figures as philosopher Bertrand Russell, Pablo Casals and Will and Ariel Durant as well as movie stars and entertainers. With Carson ruling the late-night roost on NBC in the late 1960s, the two other networks challenged him with competing shows, Griffin on CBS, Joey Bishop (later Dick Cavett) on ABC. Nothing stopped Carson, and Griffin returned to Westinghouse. Meanwhile, Griffin sought new enterprises for his production company. A lifelong crossword puzzle fan, he devised a game show ''Word for Word,'' in 1963. It faded after one season, then his wife, Julann, suggested another show. ''Julann's idea was a twist on the usual question-answer format of the quiz shows of the Fifties,'' he wrote in his autobiography ''Merv.'' ''Her idea was to give the contestants the answer, and they had to come up with the appropriate question.'' ''Jeopardy,'' begun in 1964, became a huge moneymaker for Griffin, as did a more conventional game show, ''Wheel of Fortune,'' starting in 1975. Mervyn Edward Griffin Jr. was born in San Mateo, south of San Francisco on July 6, 1925, the son of a stockbroker. His aunt, Claudia Robinson, taught him to play piano at age 4, and soon the boy was staging shows on the back porch of the family home. ''Every Saturday I had a show, recruiting all the kids in the block as either stagehands, actors and audience, or sometimes all three,'' he wrote in his 1980 autobiography. ''I was the producer, always the producer.'' After studying at San Mateo Junior College and the University of San Francisco, Griffin quit school to apply for a job as pianist at radio station KFRC in San Francisco. The station needed a vocalist instead. He auditioned and was hired. Griffin was billed as ''the young romantic voice of radio.'' He attracted the interest of RKO studio boss William Dozier, who was visiting San Francisco with his wife, Joan Fontaine. ''As soon as I walked in their hotel room, I could see their faces fall,'' the singer recalled. He weighed 235 pounds. Shortly afterward, singer Joan Edwards told him: ''Your voice is terrific, but the blubber has got to go.'' Griffin slimmed down, and he would spend the rest of his life adding and taking off weight. Griffin and Julann Elizabeth Wright were married in 1958, and a son, Anthony, was born the following year. The couple divorced in 1973 because of ''irreconcilable differences.'' ''It was a pivotal time in my career, one of uncertainty and constant doubt,'' he wrote in the autobiography. ''So much attention was being focused on me that my marriage felt the strain.'' He never remarried. http://theedge.bostonherald.com/tvNe...icleid=1016808  TV Meets the Web. All Is Safe. Mike Hale Just to get this out of the way: “i-Caught,” which had its premiere last week on ABC, is not a sequel to “I Spy.” It is, according to the voice-over at the beginning of the program, “what happens when Internet video comes together with television.” What happens, apparently — besides a bout of temporary show-naming insanity — is a scramble for the familiar and the reassuring. That would explain why this attempt to recapture some of the eyeballs being drawn away to video-sharing Web sites like YouTube is structured as a combination of “20/20” and “America’s Funniest Home Videos.” To make things even more comfortable, whether for older viewers unsure of what this Internet business is all about or for older television news executives, the show’s first segment was about a nature video, one that would have looked right at home on “Wild Kingdom” 40 years ago. You could imagine the editing-room conversation: “Yeah, we can do this — it’s just like television, except that we don’t have to pay a crew.” There’s one other difference, of course: that amateur video of a baby water buffalo being attacked by lions, shot in a park in South Africa by a tourist named David Budzinski and published on YouTube by his friend Jason Schlossberg, has already been viewed more than 12 million times. ABC can’t just show the video, as spectacular as it is — the moment when a water buffalo throws a lion in the air is downright amazing — so it adds some newsmagazine value by interviewing professional wildlife photographers, who testify to the video’s spectacularity; Mr. Budzinski, who tells us how he got the shot; and Mr. Schlossberg, who tells us why he put it on YouTube. Do enough people care about the stories behind viral videos to make this a viable prime-time television concept? Maybe — the premiere drew a tolerable number of viewers for a summer fill-in. And there are signs that ABC News is willing to flex some reportorial muscle on the show’s behalf: tonight’s episode is scheduled to include a segment that raises troubling questions about the Philippines-prison “Thriller” video that has drawn close to five million views on YouTube. If I were one of those ABC executives, though, I’d be concerned by a few aspects of “i-Caught” that might be influenced a little too much by the ethos of the Internet. In the “if you can’t beat them” category, the show adds up to an hourlong commercial for YouTube and MySpace, which are both owned by major media competitors of ABC. And in the “we’re all panicked, so let’s go ahead and eat our young” category, the first episode featured a cautionary report on a Web journalist who became an online laughingstock after she flubbed a live interview with Holly Hunter ... on ABC’s online news channel! This included the hard-to-watch spectacle of the young woman being grilled about her inexperience by her own network. On second thought, that was pretty great TV. I-CAUGHT ABC, tonight at 10, Eastern and Pacific times; 9, Central time. David Sloan, executive producer; Bill Weir, anchor. http://www.nytimes.com/2007/08/14/ar...on/14hale.html  In-Demand Surprise From Disney Jacques Steinberg Rachel Courtien, 12, and two friends were settling in to watch an episode of “Hannah Montana” on Disney Channel’s on-demand cable service Friday night when they were startled to see an entry for “High School Musical 2” on the menu of available offerings. They knew that this highly anticipated sequel was not scheduled to have its first official showing, on the regular Disney Channel, a basic cable channel, until Aug. 17. But there it was, a week early, as close as the push of a button. Once they had stopped screaming, Rachel said, they discovered that their cable provider, Cablevision, was quietly offering a preview of the movie in its entirety to subscribers to Disney’s on-demand service (who typically pay $4.95 a month) as a promotion at least partly intended to build buzz for the film. “Then we told each other to be quiet,” Rachel said. “Because we really wanted to watch it.” Over the next few days, as word spread, a steady parade of Rachel’s friends has filed through her home in Pelham, N.Y., to watch the movie, and she has seen it three more times. (The consensus: “Really good.”) Her experience is hardly unique. In addition to Cablevision, which makes Disney Channel on Demand available to its digital cable service’s 2.5 million subscribers, most of them in the New York City area, Verizon has been offering the “High School Musical 2” premiere as an on-demand option in the 550,000 homes nationally with access to its fiber-optic television network. This Friday’s premiere, as well as the on-demand preview, have been the talk of camps and pools — especially among preteenage and teenage girls, who are among the reasons the first “High School Musical” earned in excess of $100 million profit for the Walt Disney Company, much of it through DVD and merchandise sales. Alas, those children whose parents subscribe to other services, including Time Warner Cable, have sometimes learned the hard way that this preview is limited to Cablevision and Verizon customers. But some young viewers have sought to exercise a bit of restraint on their own. Alexa Grosbard, 10, who is attending Mill Basin Day Camp in Brooklyn, said, “Every day, all the girls in my group, we count down how many days left there are” until the “High School Musical 2” premiere. As a subscriber to Disney Channel on Demand through Cablevision, Alexa was told by her mother last Friday that she could watch the movie if she liked. She declined, because she and three friends are scheduled to watch it at another girl’s house this Friday, on Disney Channel, followed by a slumber party. “I want to be surprised at the same time as everyone else,” she said. http://www.nytimes.com/2007/08/15/ar...on/15musi.html  Fox’s Right-Wing Alternative To Daily Show Fails In January, Fox announced that it would begin airing the “Half Hour News Hour” on Sunday nights, the so-called “right-wing answer to ‘The Daily Show With Jon Stewart.‘” “You can turn on any show and see Bush being bashed,” said creator Joel Surnow, producer of Fox’s 24. “There really is nothing out there for those who want satire that tilts right.” As Fox has learned, that’s because no one wants to watch that kind of satire. TVNewser reports today that the HHNH has been canceled. In a memo to senior producers today, Fox News Corp.’s senior vice president Bill Shine announced: Joel Surnow and I have mutually decided that we will not continue the Half Hour News Hour beyond its current 15 episode run. The last show will be presented on September 16th. Shine claimed the reason for the shelving of the show was that Fox is “considering ways to retool the show for future scheduling needs.” He held out the chance that the show would air again: “There is still a chance you will see the program at some point in the future.” The first show guest-starred right-wing all-stars Rush Limbaugh and Ann Coulter as President and Vice President. The reviews for the program were consistently dismal. Its very first review, from the Orlando Sentinel, decried the “[l]aughter, of an awfully canned variety, greets all the gags. Nothing happening on screen justifies these outbursts. … If we’re lucky, we’ll never hear of this dreadful show again.” “Sometimes the humor is so heavy-handed that it seems almost like self-parody,” said the New York Times. “The 1/2 Hour News Hour is slow torture all by itself,” said the Philadelpha Inquirer. What the right-wing failed to grasp is Jon Stewart is funny not because he spins falsehoods but because he tells the truth. http://thinkprogress.org/2007/08/14/...ewshour-fails/  Helping Find Lost Alzheimer's Patients Lauran Neergaard It looks like a toy, but the bracelet locked around Bob Melnick's wrist gives his wife some peace of mind: If this Alzheimer's patient wanders off and gets lost, he's wearing a tracking beacon to help bring him home. ''I'm a marked man,'' joked Melnick, of Hainesport, N.J. ''The police can pick me up anywhere.'' Wandering is one of the most frightening symptoms of advancing dementia, and the Alzheimer's Association estimates it will happen to nearly 60 percent of patients. A mini-industry of technologies promises to find lost Alzheimer's patients -- from simple radio-wave beacons that cost $10 a month for batteries, to more-sophisticated GPS devices that can cost hundreds of dollars. Little if any independent research has been done to help determine which systems work best in different environments, and therefore are best suited to different families. ''These technologies need to be evaluated,'' said Majd Alwan, director of the Center for Aging Services Technologies, a coalition of government, universities and high-tech companies. Among considerations are where the patient lives, added Henry Kautz of the University of Rochester, who is helping develop next-generation systems. For example, the accuracy of GPS devices depends on access to satellites powering the navigation tool. ''You have to have a clear line of sight to the satellite,'' Kautz said, which can be difficult in a large city. Companies are working to boost signal strength. Radiofrequency ''tags'' are a hot topic for assisted-living facilities. Patients wear a sensor read by receivers on doors that sound an alarm when someone strolls too far. Then there's the more traditional beacon like Melnick's, which emits a radiofrequency signal for rescue workers to hunt. ''That kind of technology is the most flexible, because it doesn't require GPS or infrastructure. But it doesn't work if you don't notice the person is gone,'' Kautz said. Whatever the transmitter, there's the question of how to ensure the patient doesn't wander off without it. Some systems require carrying cell phones; others come in hard-to-remove jewelry; one company sells sneakers implanted with a GPS chip. For families, there's little guidance on how to find, or choose from, the devices. Dolores Melnick learned almost by accident that her county sheriff's department offered the radio beacon through a program called Project Lifesaver, when a relative stumbled across an Internet site. Melnick already was enrolled in the Alzheimer's Association's low-tech Safe Return program. For $20 a year, the hot line faxes photos and descriptions to law enforcement when a patient is reported missing. Patients also wear a stainless steel tag listing a number to call if they're found wandering. But after getting briefly separated in an airport, Mrs. Melnick liked the idea of more active tracking, too. When she snapped the bracelet on her husband, ''He said, 'Oh, this is so you don't lose me!''' Stay tuned: Kautz says next-generation sensors promise to help dementia patients help themselves, guiding those with early-stage Alzheimer's on city buses or reminding later-stage patients how to wash their hands. http://www.denverpost.com/healthcare/ci_6607326  Manufacturers Find Ways to Navigate Web Retailing Bob Tedeschi FOR manufacturers, the Web can be a hazardous place. Consumers expect these companies to sell their products directly online, but retailers have other thoughts. How, then, to satisfy all parties? You don’t, e-commerce executives and analysts said. Manufacturers have realized that they can sell more aggressively to consumers online, which puts them in stronger financial positions and also allows them to serve consumers more effectively. And retailers are not balking too much at manufacturers who sell online because, analysts said, Web sales are not high enough for retailers to fear that a vendor will steal a lot of business. “Retailers aren’t necessarily feeling the pinch from their suppliers’ online sales efforts,” said Dan Stanek, an analyst with TNS Retail Forward, a consulting firm. “So it’s not been as big of an issue as in the past.” Such news is especially good for smaller manufacturers, who might struggle to get their goods on retailers’ shelves, despite high demand from consumers for their products. Take PeaceWorks, a New York-based maker of specialty foods. Since it began operating in 1993, it has gained a modest following, with annual sales of more than $10 million, but it has not reached the stage where all the biggest grocery stores carry PeaceWorks items, like its Kind brand fruit and nut bars. “People would tell us that sometimes a particular flavor was not available near them,” said Daniel Lubetzky, the chief executive. “But we never wanted to be competing with our retailers, and we didn’t want to get involved with selling to one consumer at a time because we’re used to selling containerloads of product and we don’t have a huge staff for that.” Mr. Lubetzky said that several years ago, the company opted to sell directly to consumers by the case — 48 bars at $2 apiece, one flavor, no discount. “If you insisted on buying that way, we made it quite difficult for you,” he said. Last year, though, Mr. Lubetzky noticed a monthly tally of payments made by credit cards for more than $20,000 of PeaceWorks items, and asked employees why they were allowing retailers to pay by charge card. It turns out the purchases were coming from online customers. “We realized this was serious business,” Mr. Lubetzky said. “We had to embrace it.” This summer, PeaceWorks started a loyalty program, in which those who sign up for a monthly delivery of 48 bars can get a variety of flavors. A small concession, perhaps, but more than 100 people signed up, guaranteeing the company $120,000 in annual revenue. “And, obviously, our margins are very good,” Mr. Lubetzky said, since the company does not have to discount the price on the loyalty-program sales as it does when selling wholesale. PeaceWorks will also use the loyalty members to do surveys and gather other product advice, he said, compensating participants with samples, T-shirts and additional items. So far, Mr. Lubetzky said, he has not heard complaints from retailers. According to Mr. Stanek of TNS Retail Forward, merchants are in no position to complain. In recent years, Mr. Stanek said, retailers have gotten much more ambitious in selling products of their own to compete with manufacturers. These so-called private label efforts have helped merchants like Target and Wal-Mart Stores build profits and sales at the expense of vendors. Meanwhile, manufacturers like Oakley, Tommy Bahama and many others have opened their own retail outlets, saying the stores help build brand awareness, and thereby sales, for bigger merchants. Mr. Stanek said that manufacturers have also complicated matters by creating more variations of their products to satisfy niche buyers. As a result, the manufacturers are getting used to having some of their products rejected by retailers and thus have more incentive to try to move those products through the Web. There are, of course, manufacturers who leave the business of selling online completely to retailers. Callaway Golf created its Callaway Golf Interactive division after buying FrogTrader, an online retailer that sold Callaway equipment, among other things, for an undisclosed price in 2004. The company then spun out Shop.CallawayGolf.com, where consumers can order golf clubs. The twist is that a customer picks up the clubs from a local Callaway retailer. The company’s technology identifies the retailer closest to the customer and awards the sale accordingly. The company declined to comment on the system, but the benefits, Mr. Stanek said, are obvious: the sales go to the retailers and Callaway escapes the task of shipping sets of clubs to consumers. “It’s a very creative approach,” he said. Mr. Lubetzky of PeaceWorks said that its loyalty program was probably as far as the company would go selling directly online. “Our bread and butter are the retail establishments, so we want to be extra loyal,” he said. PeaceWorks’ retail distributors appear satisfied with that approach. Scott Goldshine, general manager of Zabar’s, the New York food merchant, said he had warned Mr. Lubetzky when he first heard about the online sales program. “But they have some ridiculous rules people have to follow to buy,” he said, “so it isn’t a problem for me.” Mr. Goldshine said that occasionally customers told him that they had found one of his products for a lower price online from the manufacturer. “I’ve had conversations with those manufacturers, where they’ve either raised the prices online or we’ve stopped carrying the product,” he said. “I don’t want to look like we’re ripping off our customers. That’s not our reputation.” http://www.nytimes.com/2007/08/13/te...gy/13ecom.html  At Netflix, Victory for Voices Over Keystrokes Katie Hafner Megan Funk had been on the phone for 30 minutes and had already untangled one billing knot, listened to a woman insist that she had returned a Pilates DVD when it was clear she had lost it and received one request to replace a cracked copy of “Hotel Rwanda” and another to replace a disappointing husband. Ms. Funk is one of 200 customer service representatives at the Netflix call center here, 20 miles west of Portland, where she is on the front lines of the online movie rental company’s efforts to use customer service as a strategic weapon against Blockbuster’s similar DVD-mailing service. Netflix set up shop here a year ago, shunning other lower-cost places in the United States and overseas, because it thought that Oregonians would present a friendlier voice to its customers. Then in July, Netflix took an unusual step for a Web-based company: it eliminated e-mail-based customer service inquiries. Now all questions, complaints and suggestions go to the Hillsboro call center, which is open 24 hours a day. The company’s toll-free number, previously buried on the Web site, is now prominently displayed. Netflix is bucking several trends in customer service. Booz Allen Hamilton, a management consulting firm, and Duke University studied 600 companies last year and found a continued increase not just in outsourcing, but also offshoring, in which call centers are moved overseas. “I don’t think there’s any trend to pull back,” said Matt Mani, a senior associate at Booz Allen. “This is a unique strategy for Netflix. There’s so much more competition, this is something they’ve done to get closer to the customer, because without that, there’s really no connection a customer has to Netflix.” Netflix’s decision to greet anxious consumers with a human voice, not an e-mail, is also unusual in corporate customer service. “It’s very interesting and counter to everything anybody else is doing,” said Tom Adams, the president of Adams Media Research, a market research firm in Carmel, Calif. “Everyone else is making it almost impossible to find a human.” In contrast, Blockbuster outsources a portion of its customer service, and when people do call, they are encouraged to use the Web site instead. Its call center is open only during business hours, said Shane Evangelist, senior vice president and general manager for Blockbuster Online, because the majority of customers prefer e-mail support, which is available 24 hours a day. “Our online customers are comfortable using e-mail to communicate,” he said. The decision to invest heavily in telephone customer service was an expensive one for Netflix, but it may be one advantage that the company with the familiar red envelopes has over its rival with the blue ones, analysts say. “It’s vital in a world where they’re no longer growing their customer base," Mr. Adams said. Indeed, for the first time in its eight-year existence, Netflix has found itself losing customers. It is not the quality of customer service that is driving them away, but rather the heightened competition from Blockbuster. Late last year, soon after Blockbuster introduced its Total Access program, which allows members to swap a movie they have rented online for an in-store movie, the nationwide chain began gaining on Netflix’s base of 6.7 million subscribers. By the first quarter this year, after years of outstripping Blockbuster in subscriber growth, Netflix added 480,000 new subscribers while Blockbuster signed up 780,000 new members. And in the second quarter of this year, Netflix, which prides itself on customer loyalty, lost 55,000 customers. Blockbuster added 525,000, bringing its total to 3.6 million. The Hillsboro operation, which occupies about 30,000 square feet of a low building in an office park, is intended to keep the red envelopes coming. Michael Osier, vice president for information technology operations and customer service, said he rejected cities like Phoenix, Salt Lake City and Las Vegas, which are known as call-center capitals, because of their high employee turnover rates. He settled on the greater Portland area because of the genial attitude on the part of most service workers. “In hotels and coffee shops and the airport, it’s amazing how consistent people are in their politeness and empathy,” said Mr. Osier, who is based at Netflix headquarters in Los Gatos, Calif. “There’s an operational language in the industry that people are so jaded about — phrases like ‘due to high caller volume.’ We’re very consciously trying to counter that mentality.” Netflix’s decision to eliminate the e-mail feature was made after a great deal of research, Mr. Osier said. He looked at two other companies with reputations for superb phone-based customer service, Southwest Airlines and American Express, and saw that customers preferred human interaction over e-mail messages. “My assessment was that a world-class e-mail program was still going to be consistently lower in quality and effectiveness than a phone program,” he said. When Mr. Osier presented his findings in January to fellow executives, Reed Hastings, the Netflix chief executive, sent an enthusiastic message, BlackBerry to BlackBerry, from across the room. Mr. Hastings quickly became a supporter of the e-mail elimination project. The company has tried to give the service representatives more discretion in deciding when to assuage disgruntled callers with bonus discs and account credits — and they are allowed to err on the side of generosity. More often than not, a month’s credit will be issued or a missing disc marked simply as lost, and the customer will not be charged. Netflix places no particular requirements on call duration, preferring that customer service representatives take the time they need to keep a customer happy and loyal. Ms. Funk, 36, said some people call because they are lonely. Her lengthiest call of that kind lasted 35 minutes. Others need basic help with their computers or with the Internet. Some people do not own a computer and call regularly to have a call center employee rearrange the titles in their queue. More often than Netflix might like these days, people call to cancel their subscriptions. One reason for emphasizing direct phone contact over e-mail messages is that on the phone, a Netflix employee has a fighting chance of persuading the customer to stay. And it is up to the call center representatives to help retain customers. Autumn Daste, 30, who has worked at the call center for two months, managed to halt one potential defection recently when a call was routed to her from a polite but unhappy woman in New Jersey who had not received any movies recently. Ms. Daste called up the member’s account information on her screen, including the type of service to which she subscribed, the frequency with which the member ordered movies, the number of months she had been a member, the number of times she had contacted Netflix in the past and a brief description of what those calls had been about. Ms. Daste pointed out, ever so politely, that no movies had been sent to her because the woman’s queue was empty. “There’s nothing on your list that’s of interest to me,” said the caller, referring to the 80,000 movies Netflix carries. Undeterred, Ms. Daste suggested they find a movie together. The woman mentioned one she had been wanting to see for a while, an Indian film titled “Fire.” Within seconds, Ms. Daste had it on her screen. She added it to the customer’s queue and told her she would be receiving it shortly. Customer pleased. Disaster averted. Ms. Funk has been working at Netflix for eight months, a veteran by call center standards. (Mr. Osier said his goal was to keep people there for an average of two years, twice as long as the industry average.) At $12.50 an hour, she said, the pay is slightly higher than in her previous job, in retail sales. One of the first questions customers ask, Ms. Funk said, is where she is, and they express their approval at the answer. “They like hearing it’s not being outsourced,” she said. Very few callers have asked about the disappearance of the e-mail option, she said. Disappearance of discs, though, remains a common customer anxiety. Shortly before clocking out for the day recently, Ms. Funk took a call from woman who had just found a DVD she had reported lost a few weeks earlier. It was in her husband’s car. “All right, I need to get a new husband,” she told Ms. Funk, who gave a sympathetic chortle in reply. http://www.nytimes.com/2007/08/16/bu...16netflix.html  Whole Foods Looking into Botched Release of Documents Diane Bartz Organic grocer Whole Foods Market Inc. is investigating how U.S. antitrust authorities botched a release of electronic documents involving sensitive Whole Foods information, a spokeswoman said on Wednesday. The Federal Trade Commission (FTC) failed to completely redact Whole Foods' proprietary information in a court filing on Tuesday, resulting in some of it being released. "I think it's unfortunate and unfair that privileged and confidential information" was released, said Whole Foods spokeswoman Kate Lowery in a telephone interview. "We have been looking at how this error occurred and have no further updates at this time." The filing, which briefly appeared on a public Web site Tuesday, was in support of a preliminary injunction that the FTC is seeking while it determines if Whole Foods' acquisition of Wild Oats Markets Inc for about $553.6 million would violate U.S. antitrust statutes. The filing was electronically redacted but some news organizations were able to download it and read portions of it before it was replaced with a properly redacted version. Lowery cast doubt on elements of the information released, saying, for example, that Whole Foods would not know if 30 Wild Oats stores would be closed until the merger was completed and it had access to each store's receipts and costs. Asked about assertions that suppliers had been told they could not sell to Whole Foods if they sold to Wal-Mart Stores Inc., Lowery said: "I honestly don't even know where that came from ... I've never seen or heard that." Both Whole Foods and Wild Oats have the right to terminate the deal if it is not completed by August 31. The companies are waiting for a ruling from U.S. District Court for the District of Columbia, which held hearings on the FTC's case against Whole Foods and Wild Oats on July 31 and August 1. Whole Foods asked the court for an expedited schedule so that it could have a resolution by August 31. The company said last week that it expected to get a ruling from the federal court in mid-August. http://www.reuters.com/article/ousiv...25592720070816  Medical IT Contractor Folds After Breaches Blamed for privacy breaches at five different hospitals, Verus Inc. silently closes its doors Tim Wilson Verus Inc., the IT contractor that has been implicated in security breaches at at least five different hospitals across the country, has gone out of business. The Bellevue, Wash., company, which built and maintained Websites and services on behalf of some 40 to 60 hospitals nationwide, was disbanded "eight to 10 weeks ago" when investors pulled the plug following a massive blunder that exposed many of its clients' data to the outside world, according to an executive at MedSeek, an IT contractor that is now handling many of Verus' clients. While reports of the breaches have been issued in dribs and drabs, all of the data losses can now be attributed to a single incident, in which Verus employees left a firewall down following the transfer of data from one server to another, according to David Levin, vice president of marketing at MedSeek. "All of the breaches were the result of an IT error, as opposed to any problems with the software," Levin says. "They made a huge mistake, and it literally shut the company down. It's really a cautionary tale." Verus's Website has been pulled down, and calls to the company's offices are referred to MedSeek customer service. No announcement of the shutdown, nor any explanation of the reasons behind it, appear to have been issued to the media or to Verus partners. "We're not sure if the breaches were the only reason why they closed down -- there might have been other issues as well," Levin says. "But we know we got the call to support the [Verus] customers very soon after the breach was supposed to have happened." Reports of the breaches range from mid-April to late May, but Verus has been implicated in at least five disclosures since the beginning of June: • On June 4, Stevens Hospital in Edmonds, Wash., reported the exposure of 550 patients' data through a failure in the online bill payment service operated by Verus. • On June 6, Keenewick General Hospital in Washington reported a similar breach affecting 1,000 patients, and attributed it to the Verus online bill payment service. • On June 7, Concord Hospital in New Hampshire disclosed the loss of 9,000 names because Verus had "turned off a firewall for maintenance purposes" and failed to turn it back on again. The breach was not disclosed publicly until late July (See Third Parties Fumble Data Handoffs.) • On July 24, St. Vincent's Hospital in Indiana reported a security breach that exposed data on some 51,000 patients. The hospital blamed Verus, which exposed the data while transferring data between servers. • Earlier today, Sky Lakes Medical Center in Oregon revealed that 30,000 patients' names had been inadvertently exposed in late May, when Verus didn't take sufficient precautions while transferring data from one server to another. All of the hospitals said they immediately terminated their contracts with Verus following the breach. All of the hospitals said they have yet to see any reports of hackers or criminals using the data. According to Levin, the breaches all affected hospitals using Verus's VPAC online billing system, which MedSeek does not use. Verus's hospital customers will be given a choice as to whether they want to migrate to the MedSeek platform and services, or move to some other vendor. http://www.darkreading.com/document....WT.svl=news1_1  Names in the News Get a Way to Respond Brad Stone The Internet offers immediate access to articles about every breaking news event anywhere in the world. But no one in the media business has quite figured out how to exploit that revolutionary fact. A growing number of large Web companies like Yahoo, Google and AOL and a menagerie of start-ups like Digg and Topix.net offer a comprehensive menu of news headlines that link to articles elsewhere online. These sites are called news aggregators, and though some have large audiences, the companies that run them have yet to figure out how to turn them into enduring businesses with unique identities. Nevertheless, the search giant Google, whose Google News is among the largest news aggregators, announced a business based on those who chatter about the news. It is asking the people or companies mentioned in news articles to comment on those reports. Walt Riker, the vice president for communications at McDonald’s, was asked to weigh in on a study from Stanford showing that the company’s marketing was so ingrained in the minds of preschoolers that they favored food like carrots sticks in McDonald’s wrappers over identical food without them. In his 550-word statement posted on Google News, Mr. Riker wrote that McDonald’s listens to its customers and enthusiastically promotes milk, fruit and vegetables in its ads. “More information for more consumers is a very good thing,” he said in an interview. “We were eager to participate.” Josh Cohen, the business product manager for Google News, said the feature is consistent with the company’s mission to bring as many news sources online as possible. He said the company would not edit any comments from sources. Google characterized this as an experiment. Media professionals characterized it less charitably as an effort by engineers who do not understand the impracticalities of such a project on a large scale — for instance, how do you verify a source’s identity or screen for inaccurate statements? — and the potential sensory-deadening impact of long-winded statements. A decade after Matt Drudge rose to prominence with the Drudge Report, a collection of headlines and links to provocative articles and opinions, sites with news links are blossoming all over the Web, using a variety of approaches. But the sites are often imperfect. For example, Digg.com in San Francisco lets readers vote on the articles they like the most. The frequent result is that the Digg faithful propel articles about Digg itself into the top spots. Daylife.com in New York uses search algorithms to find photos, graphics and articles from around the Web, then organizes them onto single pages on subjects like Iraq or President Bush. But sometimes the technology trips up. The page for Amazon combines articles about the rainforest with articles about the online retailer — not exactly a credibility-enhancing tactic. (The New York Times is an investor in Daylife.) Some of these sites see additional promise in letting readers pontificate about the articles in online discussion forums. Topix.net, a three-year-old news aggregator based in Palo Alto, Calif., repositioned itself in December by adding conversation forums for every city in the United States. The site attracts around 60,000 comments a day, and Chris Tolles, Topix’s chief executive, says he can charge twice the rate for ads on the pages with engaged readers as he can on his main news page. “It turns out that presenting commodity news stories is not such a good business,” he said. “It’s hard to make money on a page with the top stories of the day.” One drawback of the approach is that readers with extreme views can hijack the conversations. For that reason, last December, Yahoo closed down the chat forums related to specific articles on its news site, Yahoo News, which gets 35 million readers a month and is the most popular news site on the Web. Google News was introduced in 2002, with the boast from the company that its algorithm could pick and present the day’s main news without the intervention of human editors. Though Google had been reluctant in the past to inject an editorial level into the news business, it appeared to be trying to stimulate reader engagement with its latest move to solicit comments on article sources, which it announced in a blog posting Tuesday evening. Media analysts say that Google shies away from placing advertising on Google News because it could draw more legal scrutiny from media companies. Mr. Cohen of Google News said that the company had not put ads on the site because it had been focused on its users and on creating new features. For traditional media organizations, the question is whether they should feel threatened by the growing crop of online news aggregators that skim off advertising without producing original journalism. Martin Nisenholtz, chief executive of New York Times Digital, says that sites like Google News drive valuable traffic to the Times site. “Its very much incumbent on traditional news organizations to recognize the Web is an open environment, and they are going to survive and prosper based on being open,” he said. As for the threat Google’s new venture poses to those journalists who answer reader complaints: “I have stopped becoming worried about a lot of this,” said Deborah Howell, the ombudsman for The Washington Post and a journalist for 45 years. “It’s going to happen whether we like it or not.” http://www.nytimes.com/2007/08/13/te.../13google.html  Sony: Full PSP Power Hindered by Wi-Fi James Brightman Sony has confirmed to GameDaily BIZ that the PlayStation Portable cannot use its full CPU power at the same time that Wi-Fi is enabled, meaning that games with network gameplay cannot tap into the full 333MHz clock speed. More within... An original report on Beyond3D has revealed that the PlayStation Portable's newly unlocked 333Mhz processor speed, which is being utilized in the upcoming God of War: Chains of Olympus, actually comes with some restrictions. Although PSP firmware version 3.50 introduced a new clock control function, Beyond3D discovered that the portable's full clock speed is only available with Wi-Fi disabled, meaning that during network play the CPU clock is limited to 222MHz. GameDaily BIZ checked in with Sony Computer Entertainment America, and Dave Karraker, Sr. Director, Corporate Communications did indeed confirm the report. "The recent firmware upgrade (3.50) that removed the restriction on the PSP's CPU speed enables developers to utilize speeds either lower or higher than the default 222MHz, up to the full 333MHz clock speed. The article is correct that increased CPU speed cannot be used with the PSP's wireless feature," Karraker said. "SCEA is working closely with the development community to take full advantage of this new functionality where appropriate for their titles." As Beyond3D points out, this limitation has some implications for PSP developers: "Game titles with network play could effectively be either limited to using 222MHz only during single player mode, or to using a downgraded engine and assets for multiplayer mode, which could complicate the development process." It's not clear why this limitation is in place – speculation suggests that it's an effort to conserve battery life, which is already affected when Wi-Fi is on – but SCEA (Sony Computer Entertainment America) told us they would check in with SCE in Japan. We'll let you know what we hear. http://biz.gamedaily.com/industry/fe...00500000000012  Xbox 360 Out of Order? For Loyalists, No Worries Matt Richtel Imagine your blender breaking down twice. The vacuum cleaner giving up the ghost three times. The espresso maker repeatedly going kaput. Then imagine replacing the item with the same model over and over while keeping your brand loyalty and sanity. Stephano Nevarez can. Since he first bought his $400 Microsoft Xbox 360 in 2006, it has failed three times. Each time, he sent the game machine back to the company and waited weeks for a repair or a replacement. “There’s nothing in the house that breaks down as much,” said Stephano, a 15-year-old high school student from Salem, Ore. Yet he remains a devotee of his 360 console, the more so because he wants to play Halo 3, the latest iteration of a violent space epic due in stores on Sept. 25; it is available only for that game machine. The game, published by Microsoft, could redeem the company going into the holiday selling season. Untold numbers of 360 owners have watched their machines break down, and then, in many cases, watched the replacement consoles do the exact same thing because of a severe and widespread manufacturing flaw. But if the Xbox players keep coming back because of Halo 3, and if other gamers buy the console just for the game, then Microsoft could markedly improve its standing in its battle against rivals Sony and Nintendo. “Halo 3 is Microsoft’s most important game,” said Dan Hsu, editor in chief of Electronic Gaming Monthly, a magazine for enthusiasts. Mr. Hsu, who has seen the game, said it delivers in spades, with one caveat: “Assuming your machine does work, it does what it sets out to do.” The bar is high. Combined, Halo and Halo 2 have sold around 15 million units, making the series one of the most successful game franchises of all time. The game has spawned novels, comic books and a possible movie. The $12.5 billion console and video game business is up for grabs this year. On the console side, Nintendo is off to an unexpectedly strong start with its Wii, a game system that makes its players get up off the couch and move their bodies to direct action. It has well over 28 percent of the American console market, according to NPD Group, a market analysis firm. The Wii is currently selling at a faster pace than the 360, and the company is releasing its big games this fall, Super Mario Galaxy and Super Smash Bros. Brawl, though neither is as popular as Halo. Sony, with about 14 percent of the market, was hurt when the release date of Grand Theft Auto IV, a game it was counting on to increase console sales, was pushed back from October into the second quarter of next year. Microsoft, which has 57 percent of the market, has declined to say what is causing some of its Xbox 360 to stop working, or how many machines have been affected. It has set aside $1.1 billion for repairs, a figure that suggests to industry analysts that the problem could affect a third of the 11.6 million 360s already in the hands of consumers. Microsoft has said that it will fix any faulty Xbox 360 free of charge. The most likely explanation of where the engineers went wrong is that the 360s are poorly designed to deal with the intense heat generated by game play and that computer chips and other electronics may be popping off the motherboard, said Richard Doherty, an analyst with the Envisioneering Group, a technology assessment and market research firm. Mr. Doherty said he thinks that Microsoft, in an effort to put is machine into the market a year ahead of the Sony PlayStation 3, had skimped on product testing. He said that the failure rate among 360s is almost unheard-of among consumer electronics, where having even 1 percent or 2 percent of machines fail is considered a major problem. He has been doing surveys of video game consumers, and results suggest that their patience is waning and that news of the problems is dissuading some potential buyers, he said. Even die-hard users, he said, are wondering why they cannot take their machine to a store to have it checked out, rather than wait for it to break. “It’s dissipating a tremendous amount of momentum they built up prior to July,” Mr. Doherty said, referring to when Microsoft first publicly discussed its $1.1 billion repair fund. “This is going to get worse before it gets better.” But some financial analysts said that the eventual damage to reputation and revenue may not be so profound. Evan Wilson, an equity analyst with Pacific Crest Securities, said he thought that Microsoft’s fix-it-free policy had mollified many avid game players who have been among the first to purchase the 360. Aaron Greenberg, group product manager for Xbox 360, said the repair campaign is aggressive and that the company, while it is not discussing what has gone wrong, is not taking the failures lightly. “It’s our equivalent of the Blue Screen of Death people talk about with Windows,” he said, referring to the derogatory vernacular used to describe what happens when a PC running Microsoft’s operating system mysteriously stops working. In the case of the Xbox 360, affected users have taken to calling the problem the Three Red Rings of Death. That’s because when the 360 dies, three lights on the front of the console blink red. “It started getting really loud,” said Michael White, 27, of Montreal, a high school teacher, who said his system died in April. “You expect somebody’s expensive product to be more durable than that.” Is he infuriated? Not really. “I’m a happy customer,” he said, given it only took three weeks to repair and he likes the games on the system. Others are feeling slightly less generous — or, at least, their spouses are. “My wife told me she didn’t want me to buy anymore Microsoft consoles,” said Joshua Bridges, an accountant in Spring, Tex. “But I told her I’m a huge fan of the games that come out for this platform.” Chief among his interests is Halo 3. He said he likes the fast-twitch action, but particularly the story, which involves soldiers battling against an alien race called the Covenant for control of a destructive force called the Halo. Halo 3 is the last in a trilogy. When it comes out on Sept. 25, the avid fans will be waiting in line at video game retailers across the country. More than one million units have already been ordered. For the last three years, a team of 250 full-time and part-time designers and engineers at Bungie Studios, the development house that is owned by Microsoft, have been assembling Halo 3, said Frank O’Connor, the game’s head writer. (He declined to say how much money they spent on the game). Developers felt enormous pressure, he said, and he hopes this version will be the most popular ever, particularly given new features, like the ability of players to record and make short movies of the action they just played. “Instead of being able to say: remember the time I did that one thing? Now they’ll be able to save it and show it,” Mr. O’Connor said. One question is whether it can help Microsoft sell more consoles to mainstream consumers, or to those who may be concerned about the reliability of the 360 systems. But there is little doubt the faithful will be there in force, and thrilled about it, having forgiven Microsoft for the flaws in its console. “I’m on my third 360,” said Benjamin Lin, an 18-year-old Halo enthusiast from Seattle, “and it’s working great for me.” http://www.nytimes.com/2007/08/13/te...gy/13halo.html  Windows XP: The OS That Won't Die? Microsoft has had to create a new build of Windows XP Professional for computer makers because the six-year-old operating system's continued popularity has nearly exhausted the supply of product activation keys. Gregg Keizer Microsoft has had to create a new build of Windows XP Professional for computer makers because the six-year-old operating system's continued popularity has nearly exhausted the supply of product activation keys. The new build, dubbed SP2c, includes no fixes or feature changes, but was created simply to address the shrinking pool of product keys. XP Pro SP2c, which has been released to manufacturing, will be made available to OEMs and system builders next month, said Microsoft. "Due to the longevity of Windows XP Professional, it has become necessary to produce more product keys for system builders in order to support the continued availability of Windows XP Professional through the scheduled system builder channel end-of-life (EOL) date, wrote the Microsoft system builder team on its blog Thursday. Previously, Microsoft has set Windows XP's EOL for retailers and OEMs (original equipment manufacturers) as Jan. 31, 2008, and for small-scale systems builders a year after that. "SP2c will be released into the System Builder channel in September to provide system builders with a new, extended range of product keys," the system builder team said. The updated build applies only to Windows XP Professional; XP Home, for instance, is not affected. The move shouldn't come as a surprise; even Microsoft has predicted continuing strong sales of Windows XP. Last month, the company's chief financial officer said that he tweaked the fiscal year 2008 forecast to account for XP's longevity. Rather than count on an 85/15 split in sales between Vista and XP, said Chris Liddell, Microsoft now expects a 78/22 split, an increase of nearly 50% in anticipated XP sales. Other signs of the not-dead-yet OS's vigour have included retreats by OEMs like Dell from earlier Vista-only policies. In April, for example, Dell again began offering Windows XP as an option to consumers. It had already done the same thing for small business customers. http://pcworld.co.nz/pcworld/pcw.nsf...25733500728C08  Olympic Committee Chooses XP over Vista The popularity of Windows XP is still making things difficult for Vista. Now Vista has again suffered a major setback, with Lenovo (Olympic 2008' official sponsor) installing XP on it's machines to run the Olympic Games’ vital PC-related tasks. Vista will only be used in internet lounges set up for athletes to use during the games. Yang Yuanqing, chairman of Lenovo said, "the Olympic Games require mature, stable technologies and it's not a place to try new technologies because of the size and importance of the event. Everything must work smoothly.” The committee has also decided against using wireless technology as the reliability and the security of wireless internet made it too risky. Lenovo has already delivered 12,000 desktops (mainly ThinkCentre M55), 800 laptops (Thinkpad T60s and Zhaoyang 680s), 700 servers (SureServer models T350, R630 and R520), 2,000 printers and another 5,000 PCs for the athlete's lounges and other hospitality and marketing purposes. http://www.pclaunches.com/software/o...over_vista.php  Hasta la Vista Passing the Torch Jim Louderback After five years at Ziff Davis Media and nearly 16 years in editorial content—the last two at the helm of this terrific magazine—I've decided to try something new. I've jumped over to become CEO of Revision3, the leading Internet television network focused on developing programming for the on-demand generation. It was a tough decision. PC Magazine has a tremendous team, an amazing audience of loyal and outspoken readers, and a bright future. But I felt it was time to do something different. And I'm leaving you in good hands. Lance Ulanoff is stepping up to fill the editor-in-chief position, and he has been studying for this role essentially his entire professional life. He'll continue to deliver a strong, engaging, and captivating PC Magazine. Heck, with him in charge and a top-notch team in place, the magazine will be even better than it is today. Rest assured, you haven't heard the last of me. I will continue to write a column in PC Magazine. I still have too many issues to discuss with you. For example, my latest beef is with Vista. Maybe it was something in the water? I've been a big proponent of the new OS over the past few months, even going so far as loading it onto most of my computers and spending hours tweaking and optimizing it. So why, nine months after launch, am I so frustrated? The litany of what doesn't work and what still frustrates me stretches on endlessly. Take sleep mode, for example. Vista promised a new low-power sleep mode that would save energy yet enable nearly instantaneous resume. Poppycock. The brand-new dual-core system I built a few months ago totters off to sleep but never returns. I have to cold-start it to bring it back. This after replacing virtually every driver inside. It's gotten so bad that I've actually nicknamed it Chip Van Winkle. And I've nicknamed my primary Dell notebook Philip Marlowe. But it's not just the long sleep. My home notebook acts as if it comes from Starbucks rather than HP. It used to snooze—but now, after a recent Vista update, it never goes to sleep at all. Its new nickname: Compuccino.—next: Networking > Networking, too, gives me huge headaches. In XP, a simple right click on the system tray icon put me one click away from IP settings and connections status. Now that same icon brings up a menu of options that ultimately lead to the Network and Sharing center—sharing in the Sirius Cybernetics, "Share and Enjoy" obfuscation mode, not any sort of network sharing I'm familiar with. I've configured every PC on my home network to share drives and printers, yet owing to some undiscovered element, there's no guarantee that any of them will be visible at any given time. Take my media center PC, for example. It's supposed to serve up photos, videos, and music. Instead, it often simply drops off the network for absolutely no reason. Chip Van Winkle might be able to see it, but Compuccino can't. Another complaint: With XP, wireless network connectivity out of sleep mode was virtually instantaneous. Now it can take up to 30 seconds to reconnect, even when my systems do wake up. That's in a trusted network, a trusted zone, and a trusted system. And why does it take so long for the dialog box to pop up after I right-click on the network tray icon? Vista has replaced XP's quick reaction time with molasses. I'm always wondering if something's wrong. I could go on and on about the lack of drivers, the bizarre wake-up rituals, the strange and nonreproducible system quirks, and more. But I won't bore you with the details. The upshot is that even after nine months, Vista just ain't cutting it. I definitely gave Microsoft too much of a free pass on this operating system: I expected it to get the kinks worked out more quickly. Boy, was I fooled! If Microsoft can't get Vista working, I might just do the unthinkable: I might move to Linux. http://www.pcmag.com/article2/0,1895,2171472,00.asp  Microsoft 'Silently' Restores Root Certificates that Users Distrust and Remove Paul McNamara Kill off any one of 230 root certificates available under the default configuration of Windows XP Service Pack 2 and the operating system will "silently" revive it and restore the certificate to the trusted status that the user intended to be revoked, according to security expert/blogger Paul Hoffman. And in Windows Vista you just can't kill them, period. From a paper Hoffman posted this week: This prevents a Windows XP SP2 user from declaring a Microsoft-trusted certificate authority as untrusted unless the user turns off the Windows component that controls this feature. Note: Windows Vista works quite differently than Windows XP SP2 in this regard, and has significant but different problems with Microsoft-trusted root certificates: The user cannot mark them as untrusted. Hoffman believes these limitations could cause significant problems for some organizations. "If you are in an organization that needs to delete a root, it is very serious," he tells me. "Few corporations have felt a need for that so far, but it certainly affects government (agencies with strict crytography rules). It also has a serious effect on corporations that are worried about their competitors who happen to be Microsoft-blessed certificate authorities." As relates to Vista, the paper explains: After extensive searching, I could not find a way to remove certificate authorities trusted by Microsoft from Windows Vista. Even if there is a way to do this, there seems to be no equivalent of the Update Root Certificates program that can be turned off. ... This leaves Windows Vista users always having to accept Microsoft's silent updating of their root certificate store. "The Vista part is definitely worse, even though it is more obvious," Hoffman tells me. "Fortunately, the Vista one is the easier one for Microsoft to fix." Asked to comment on the paper's conclusions, a Microsoft public relations spokesperson told me, "We don't have any information to share at this time." In the paper, Hoffman lists a half-dozen example scenarios under which an organization would feel compelled to remove a root certificate, ranging from criminal actions on the part of the CA to a certificate having expired. The paper also suggests a number of fixes. "I wrote the security paper because nearly everyone I mentioned the problem to, even my friends at Microsoft, were surprised about how Windows dealt with the root certificates," Hoffman says. As for whether the situation represents a Windows feature or a bug? "Unfortunately, I think they did this on purpose, not thinking about the consequences," he says. "It is not a bug, as far as I can tell. There is nothing in the Microsoft documentation that says 'do X' and X is not possible." http://www.networkworld.com/community/node/17703  Vista Prevents Users Playing High-Def Content Vista requires premium content like high-definition movies to be degraded in quality when sent to high-quality outputs. Jon Brodkin Content protection features in Windows Vista are preventing customers from playing high-quality video and audio and harming system performance, even as Microsoft neglects security programs that could protect users, computer researcher Peter Gutmann argued at the USENIX Security Symposium in Boston Wednesday. "If there was any threat modeling at all, it was really badly done," Gutmann, from the University of Auckland, New Zealand, said while giving a talk on Vista content protection. "Once the enemy is the user and not the attacker, standard security thinking falls apart." Vista requires premium content like high-definition movies to be degraded in quality when sent to high-quality outputs, so users are seeing status codes that say "graphics OPM resolution too high." Gutmann calls this "probably the most bizarre status code ever." While Microsoft's intent is to protect commercial content, home movies are increasingly being shot in high definition, Gutmann said. Many users are finding they can't play any content if it's considered "premium." "This is not commercial HD content being blocked, this is the users' own content," Gutmann said. "The more premium content you have, the more output is disabled." Gutmann, who wore a white T-shirt marked with a Windows Vista logo during his presentation, first issued his criticisms several months ago with a paper titled A Cost Analysis of Windows Vista Content Protection. Gutmann's paper called Vista's content protection rules "the longest suicide note in history." Microsoft acknowledged that quality of premium content would be lowered if requested by copyright holders, the BBC reported. Microsoft defended its copyright protections after Gutmann's paper came out, saying they are common features of many playback devices, the BBC article says. The protections allow copyright holders to prevent video from being played in high definition unless users have equipment that supports the High-bandwidth Digital Content Protection (HDCP) digital rights management system developed by Intel. If PC users have graphics cards with video connections that don't support HDCP, they are out of luck. High-definition audio is also blocked in many cases, Gutmann said Wednesday. "It's taking this open architecture that IBM created 25 years ago and making it closed again," he said. In a 132-slide PowerPoint presentation, Gutmann outlined numerous features of Vista that he says are frustrating customers and programmers. New functionality related to content protection makes it hard to develop new drivers, he said. When ATI was finally able to ship Vista drivers, they crashed Windows, and Dell and Gateway had to delay Vista upgrades because they couldn't get working drivers, he said. Gutmann said hardware costs will increase because vendors can't provide Vista-approved security functionality unless Hollywood studios like MGM, 20th Century Fox and Disney grant written approval saying the content security meets their standards. A Vista function known as "tilt bits" -- like the tilt sensor in pinball machines -- requires hardware and software drivers to report every minor glitch, even ones that cause no problems, Gutmann said. "Every otherwise unnoticeable minor glitch is suddenly surfaced and turned into a showstopper," he said. Separately, all the extra encryption required to meet Vista's content protection standards means some computer components can never enter power-saving mode, he said. Thus, when you play a movie your CPU keeps running at full steam, he said. The extra power demands make it hard to reduce electricity usage. "It's a bit of an extreme claim, but you could say Windows Vista causes global warming, because it's burning so much power with all this nonsense," Gutmann said. The encryption requirements render high-end graphics processing units less effective, he said, because the best of those products emphasize graphics performance over content protection. On Vista, US$100-video cards can thus outperform those that cost $1,000. Gutmann argued that Microsoft placed content protection above all other priorities when building Vista, perhaps to gain favor and money from Hollywood. Microsoft should have instead focused this effort on security features that protect users, Gutmann said, such as encrypted paging to protect user secrets, protected content domains that keep out malware, and anti-debugging techniques to prevent rootkit hooking. New Zealand's government, which has argued that digital rights management fails to address the rights of people and government, appears to be the only government worldwide to express public concern about Vista's content protection standards, Gutmann said. http://www.pcworld.com/article/id,13...s/article.html  Microsoft to Dispute FCC on Vacant TV Airwaves Microsoft Corp. on Monday will try to convince U.S. regulators that vacant television airwaves can be used for wireless services without interfering with broadcast signals, The Washington Post reported. The unused TV airwaves would be available for other services by early 2009, when broadcasters are due to switch from analog to digital signals. In a document it plans to file with the U.S. Federal Communications Commission, Microsoft disputes the agency's recent finding that prototype Internet devices caused static on existing broadcasts, the Post said. The company said its first prototype was defective but that a new model worked successfully in a demonstration for the FCC last week, the Post said. Microsoft, computer chipmaker Intel Corp. and other companies have been pressing the FCC to make the vacant airwaves available for use without a license, while broadcasters have expressed concerns about potential interference with their signals. The companies hope the unlicensed airwaves could be used for a variety of wireless services, including high-speed Internet access, particularly in rural areas where such offerings can be scarce. In 2004, the FCC proposed creating two categories of users for the airwaves: one for low-power, personal, portable devices like Wi-Fi and a second group for fixed commercial operations. The FCC also proposed requiring that the devices include technology to identify unused spectrum and avoid interference. The FCC has said it would set final technical requirements for devices to use those airwaves without a license by October. http://www.reuters.com/article/busin...29621220070813  Microsoft: Test Shows U.S. Vacant Airwaves Usable Microsoft Corp told the U.S. Federal Communications Commission on Monday it was confident that vacant television airwaves can be used for wireless services without interfering with broadcast signals. The unused U.S. television airwaves would be available for other services by early 2009, when broadcasters are due to switch from analog to digital signals. In a document filed with the FCC, Microsoft disputed the agency's recent finding that prototype Internet devices caused static on existing broadcasts. The company said its first prototype had a defective internal component but that a new model worked successfully in a demonstration for FCC technical experts last week. "We remain confident that the unused channels in the television spectrum band can successfully be used without harmful interference to incumbent licensees such as television and wireless microphone services," Microsoft said in a statement. Microsoft, computer chipmaker Intel Corp and other companies have been pressing the FCC to make the vacant airwaves available for use without a license, while broadcasters have expressed concerns about potential interference with their signals. The companies hope the unlicensed airwaves could be used for a variety of wireless services, including high-speed Internet access, particularly in rural areas where such offerings can be scarce. In 2004, the FCC proposed creating two categories of users for the airwaves: one for low-power, personal, portable devices like Wi-Fi and a second group for fixed commercial operations. The FCC also proposed requiring that the devices include technology to identify unused spectrum and avoid interference. The FCC has said it would set final technical requirements for devices to use those airwaves without a license by October. http://www.reuters.com/article/gover...36211320070813  Local news Colleges Struggle with Mandates to Prohibit Portable Storage Brian Fonseca IT managers at colleges and universities are grappling with the problem of finding ways to better secure removable storage media in an environment that encourages information sharing. Jason Pufahl, information security team lead for IT services at the University of Connecticut, said that the needs of students and faculty prevent universities from implementing mandates that prohibit the use of unapproved portable storage media. Such mandates may be common in the corporate world, but "we don't have the flexibility to simply say all inbound traffic is locked down or we're going to allow outbound traffic on only specific ports," Pufahl said. "We just can't do that. We have to try to provide security when leaving things open, which is really difficult." UConn has had success scanning network traffic for viruses and malware using Fortigate-5000 technology from Sunnyvale, Calif.-based Fortinet Inc., though Pufahl acknowledges that it has proven ineffective against devices such as USB drives, iPods or iPhones. In recent months, some universities have been hit by incidents of lost or stolen flash memory and storage devices. In June, for example, Grand Valley State University was forced to notify 3,000 students of a stolen Zip drive. The university is currently examining password- and encryption-protected USB drives from SanDisk Corp. and Kingston Technology Co., said John Klein, associate director of academic services at the Allendale, Mich., school. Klein said schools must educate students about the dangers of using unprotected storage devices and the associated risks of losing confidential data. "It's not their home network anymore, where they are safe and cozy and warm," he said. "It's a campus network, where virtually any computer via a hacker is viewable and can be attacked." In May, a professor at Bowling Green State University in Ohio lost a flash drive containing Social Security numbers of 199 former students. The university is currently engaged in an encryption project designed to safeguard computers across campus, said a spokeswoman. "Policies are being looked at again to see what else we could be doing," she added. "These portable storage devices are just so convenient." http://www.computerworld.com/action/...&intsrc=kc_top  OU to Implement New System for Preventing Illegal File-Sharing David Hendricks Ohio University is in the process of purchasing software that can block students from sharing copyrighted music and movies, but it won’t stop students from sharing software and other illegally traded files. A product offered by California-based Audible Magic allows the university to stop just illegal file sharing, instead of all peer-to-peer programs, as it did in April. The company’s Copysense Network Application, a combination of hardware and software, can detect and block users from sending or receiving copyrighted files. Earlier this year, Brice Bible, the university’s chief information officer, implemented a policy to block all peer-to-peer traffic, stopping most file sharing. Users with a legal need to file share could ask for an exception. That policy was an abrupt change from that implemented during Winter Quarter by then-interim CIO Shawn Ostermann. At the time, he refused to block or limit file sharing on the campus network because of its legal uses. Monthly threats of legal action against college students using peer-to-peer programs to swap copyrighted music have lead universities across the country to revisit their policies on copyright infringement. With Copysense, the university has found a middle ground, said Tom Conley, a senior IT security analyst with the university. “We’re very serious about it and we’re in the process of purchasing it,” Conley said of Copysense. The new system will change how file sharers are caught but not the university’s policies on, or punishments for, illegal use of peer-to-peer programs. First time offenders will lose Internet access at the location where they plug into the Internet, or on the wireless network, until they call the IT help desk and pledge not to share copyrighted files. Second time offenders will be referred to judiciaries. Copysense works by comparing packets of data on the network to a database of known copyrighted audio, provided by record labels and film studios. That database is updated nightly, said Vance Ikezoye, Audible Magic’s president and CEO. “Think of it as a virus scanning software, but instead of viruses we look for copyrighted files,” Ikezoye said. Because Copysense works by analyzing how content sounds, it cannot filter copyrighted images and identifies movies based on their audio. This allows encrypted files to pass through its filters unmolested. Point-to-point encryption — where only the sender and a specified recipient know how to decrypt the shared information — would likely be unaffected by Audible Magic, Conley said, but any public sharing would be much more difficult to hide. This makes it unlikely that Copysense will stop tech-saavy file sharers who abandoned the university’s DC++ file sharing hub when it was shut down in May and moved to WASTE, a private file sharing network which uses formidable encryption. Standard encryption available in popular BitTorrent clients would be much less likely to escape detection. Depending on the way a network is structured, it may take two Copysense appliances to detect all copyright infringement on a network — one to analyze internal traffic and another for traffic entering and exiting the network, Ikezoye said. Conley would not specify where on the OU network the Copysense application is, but said that “its at a place on the network where it sees an awful lot of traffic.” Although Copysense was blocking copyrighted content on OU’s network at the end of Spring Quarter, Conley said a sudden Fall Quarter increase in peer-to-peer traffic could swamp the IT help desk with calls as a large number of students are caught sharing copyrighted files. Copysense can attempt to stop copyright infringement in several ways. It can stop all peer-to-peer traffic, just copyrighted content or target a specific range of Internet provider addresses — like those used by students in their dorm rooms. That flexibility allows universities to tailor the software to their own needs, Ikezoye said. The university is using Copysense only to block copyrighted content, but could use any of the application’s features. “We’re not trying to make policy, we’re trying to allow universities to enforce policy,” Ikezoye said. http://thepost.baker.ohiou.edu/artic...ews/20835.html  UC-Berkeley Students Face Tougher Piracy Rules This Fall Bay City News Service The Recording Industry Association of America's war on pirated music and videos is coming to the resident halls at University of California-Berkeley's campus. Starting this fall semester, students using campus computer networks to illegally download copyrighted audio and visual materials will automatically lose their in-room Internet connection for a minimum of one week, the university has announced. "It's our job to make sure students who live in the residence halls fully understand the consequences of illegal file-sharing," said Dedra Chamberlin, manager of residential computing services at the university. "We don't want students to end up facing a lawsuit or $3,000 fine saying, `Why didn't anyone warn me about this?' " This year the music industry group has sent more than 2,000 letters to students across the country, alerting them that they have downloaded audio files illegally. The letters provide the students with a choice: pay an early settlement fee of $3,000 to $6,000 or face possible litigation. The pre-litigation letters are part of a broad education and deterrence campaign that the association launched early this year, according to a statement released by the association. "The new process gives students the opportunity to resolve copyright infringement claims against them at a discounted rate before a formal lawsuit is filed," the statement reads. So far, letters have been sent to 16 Berkeley students. In July, the agency also sent letters to students at San Francisco State University, California State University-Monterey Bay, the University of San Francisco and Santa Clara University. For Berkeley students to register for in-room Internet service, they must now read warnings about copyright infringement and make an electronic agreement that they understand the repercussions of breaking the law. Some 6,000 Berkeley students are scheduled to attend Sunday's Cal Connect orientation workshops at residence halls where they will view video segments that depict the consequences of illegal file sharing, according to a statement released by the university. While Berkeley is among the first Bay Area universities to place such an emphasis on the repercussions of illegal downloads, other Bay Area universities have not ignored the issue. According to a Cal State East University policy, "use of any university resources by any university constituent to circumvent legitimate copyright protections or illegally access, copy or disseminate copyrighted material is unacceptable." Cal Connect workshops will be held at Berkeley from Sunday through Tuesday. http://www.siliconvalley.com/news/ci_6639429  College Life Update: P2P, File Sharing, and the RIAA Students are arriving on college campuses in the midst of a heated drive by the music industry to stem illegal music file sharing among college students. It's been a busy year for the litigious Recording Industry Association of America (RIAA), so here's what students and parents need to know about peer-to-peer (P2P) applications on college computer networks and the ramifications of uploading illegal music files. • The RIAA wants its day in court. In several courts in fact. During the 2006 school year and the first half of 2007, the RIAA has filed thousands of complaints against individuals, including students. In February, the industry group released the top 25 universities that received the most copyright complaints. • If a RIAA letter reaches individual students, with the help of the university which must match the student's IP address with a music file in question, the RIAA tells the student he must pay fees, say $3,000 to $5,000, to avoid a lawsuit. Those who don't settle often get rolled into a "John Doe" lawsuit brought by the RIAA in several jurisdictions. The RIAA has recently shifted tack, and since February has been sending letters to universities asking them to forward "pre-litigation letters" to students it claims have infringed on copyrights. The letters offer the chance to pay a "discounted" settlement for staying out of court. • The RIAA is not winning easily in court. While some federal judges are siding with industry lawyers' bids to force schools to turn over names, email address, and other contact info of implicated students, other federal judges, including this New Mexico magistrate, are ruling against RIAA motions demanding that courts force universities to reveal the identities of students. • Once you've unpacked and set up your PC, check out your school's policy toward P2P applications. They are all over the board in their approach; some are cooperating with the RIAA and linking IP addresses with complaints, while others are still taking a more stand-off approach. This Williams College file sharing page provides a sense of how many schools are getting the word out to students. • Check out this very helpful and clearly written page by the Electronic Frontier Foundation, "RIAA v. the Students: An FAQ for 'Pre-Lawsuit' Letter Targets." It's full of helpful resources and straightforward answers that will come in handy if you're ever faced with a letter from the RIAA. To steer clear of a potential legal mess, check out Robin Raskin's post on legally sharing music in dorms. And if you want to take an educated dive into file sharing, read "Wired's Education 2.0: The College Student's Guide to File Sharing." http://tech.yahoo.com/blogs/devlin/14665  Watch Streaming TV and Movies Without P2P or Torrents Jack From jimmyr.com comes this wide-ranging and informative video overview of various services and clients that allow free movie streaming and uploading: “Most colleges, schools and other places don’t actually filter these sites…” Indeed.  Philips Celebrates 25th Anniversary of the Compact Disc Press Release Exactly 25 years ago tomorrow, on August 17, 1982, Royal Philips Electronics (NYSE:PHG, AEX:PHI) manufactured the world's first compact disc at a Philips factory in Langenhagen, just outside of Hanover, Germany. The invention of the CD ushered in a technological revolution in the music industry as CDs — with their superior sound quality and scratch free durability — marked the beginning of the shift from analog to digital music technology. The CD became a catalyst for further innovation in digital entertainment, helping pave the way for the launch of DVD and the current introduction of Blu-ray optical media. The Philips factory in Germany, where the world's first CD was pressed, belonged to Polygram — the recording company owned by Philips at the time. The first CD to be manufactured at the plant was "The Visitors" by ABBA. By the time CDs were introduced on the market in November 1982, a catalog of around 150 titles — mainly classical music — had been produced. The first CDs and CD players — including Philips' CD100 — were introduced in Japan in November, followed by a US and European market introduction in March of 1983. Philips and Sony partnered to develop the CD — collaboration based on open innovation helped position the CD as standard for the music industry As early as 1979, Philips and Sony set up a joint task force of engineers to design the new digital audio disc. Many decisions were made in the year to follow, such as the disc diameter. The original target storage capacity for a CD was one hour of audio content, and a disc diameter of 115 mm was sufficient for this. However, both parties extended the capacity to 74 minutes to accommodate a complete performance of Beethoven's 9th Symphony. In June 1980, the new standard was proposed by Philips and Sony as the "Red Book," containing all the technical specification for all CD and CD-Rom standards. Piet Kramer, who at the time was a member of the optical group at Philips that made a significant contribution to the CD technology, commented on Philips' and Sony's collaborative work: "When Philips teamed up with Sony to develop the CD, our first target was to win over the world for the CD. We did this by collaborating openly to agree on a new standard. For Philips, this open innovation was a new approach — and it paid off. In the late 70s and early 80s, we never imagined that one day the computing and entertainment industries would also opt for the digital CD for storing the growing volume of data for computer programs and movies." In 1985, Philips and Dire Straits team up to promote the Compact Disc As music industry sales of CDs started to take off in 1983, more than 1,000 different titles were on the market. In 1985, one of the most famous bands in the world, Dire Straits, adopted the CD. The infamous album "Brothers in Arms," one of the first fully-digital recordings (DDD) to be brought to market, went on to become the top selling CD at the time and the third greatest selling CD of the decade. The joint collaboration with Philips entailed Philips and Dire Straits jointly promoting the sound quality of the CD to consumers. "Brothers in Arms" became the first album to sell more than one million copies in this new format, marking the success of the CD as the emerging format of choice for music quality. "The Compact Disc has proven its significance in bringing the highest quality of music to consumers who wish to enjoy scratch free music. The enormous success of the CD during the past twenty-five years has opened many new opportunities for consumers to make the most of their music at home and on the move," said Lucas Covers, Senior Vice President & Chief Marketing Officer, Philips Consumer Electronics. "It has played a pivotal role in the shift from analog music to digital, not to mention video with the emergence of DVD. Today, it's helping lay the foundation for newer technologies such as Blu-ray." Over 200 billion CDs have been sold worldwide over the past 25 years The Compact Disc, is the forefather of today's extensive family of optical discs for a wide range of applications such as CD-Rom, CD-R and CD-RW, DVD, DVD R, DVD RW and Blu-ray. Philips estimates that during the past 25 years, since the first CD was pressed at the Philips factory near Hanover, Germany, more than 200 billion CDs have been sold worldwide. Even though a single CD is only 1.2 mm thick, if all CDs ever produced were piled up, the stack of CDs would circle the earth six times. The compact disc, as well as the DVD, remains a very popular music/video carrier due to digital quality, portability and resilience to damage. For further information on the 25th anniversary of the Compact Disc, please visit: www.philips.com/newscenter http://digital50.com/news/items/BW/2...pact-disc.html  The CD, Aging in Era of Digital Downloads, Celebrates 25th Anniversary AP It was Aug. 17, 1982, and row upon row of palm-sized plates with a rainbow sheen began rolling off an assembly line near Hanover, Germany. An engineering marvel at the time, today they are instantly recognizable as Compact Discs, a product that turns 25 years old on Friday - and whose future is increasingly in doubt in an age of iPods and digital downloads. Those first CDs contained Richard Strauss' Alpine Symphony and would sound equally sharp if played today, says Holland's Royal Philips Electronics NV, which jointly developed the CD with Sony Corp. of Japan. The recording industry thrived in the 1990s as music fans replaced their aging cassettes and vinyl LPs with compact discs, eventually making CDs the most popular album format. The CD still accounts for the majority of the music industry's recording revenues, but its sales have been in a freefall since peaking early this decade, in part due to the rise of online file-sharing, but also as consumers spend more of their leisure dollars on other entertainment purchases, such as DVDs and video games. As the music labels slash wholesale prices and experiment with extras to revive the now-aging format, it's hard to imagine there was ever a day without CDs. Yet it had been a risky technical endeavor to attempt to bring digital audio to the masses, said Pieter Kramer, the head of the optical research group at Philips' labs in the Netherlands in the 1970s. "When we started there was nothing in place," he told The Associated Press at Philips' corporate museum in Eindhoven. The proposed semiconductor chips needed for CD players were to be the most advanced ever used in a consumer product. And the lasers were still on the drawing board when the companies teamed up in 1979. In 1980, researchers published what became known as the "Red Book" containing the original CD standards, as well as specifying which patents were held by Philips and which by Sony. Philips had developed the bulk of the disc and laser technology, while Sony contributed the digital encoding that allowed for smooth, error-free playback. Philips still licenses out the Red Book and its later incarnations, notably for the CD-ROM for storing computer software and other data. The CD's design drew inspiration from vinyl records: Like the grooves on a record, CDs are engraved with a spiral of tiny pits that are scanned by a laser - the equivalent of a record player's needle. The reflected light is encoded into millions of 0s and 1s: a digital file. Because the pits are covered with plastic and the laser's light doesn't wear them down, the CD never loses sound quality. Legends abound about how the size of the CD was chosen: Some said it matched a Dutch beer coaster; others believe a famous conductor or Sony executive wanted it just long enough for Beethoven's 9th Symphony. Kramer said the decision evolved from "long conversations around the table" about which play length made the most sense. The jump into mass production in Germany was a milestone for the CD, and by 1982 the companies announced their product was ready for market. Both began selling players that fall, though the machines only hit U.S. markets the following spring. Sony sold the first player in Japan on Oct. 1, with the CBS label supplying Billy Joel's "52nd Street" as its first album. The CD was a massive hit. Sony sold more players, especially once its "Discman" series was introduced in 1984. But Philips benefited from CD sales, too, thanks to its ownership of Polygram, now part of Vivendi SA's Universal Music Group. The CD player helped Philips maintain its position as Europe's largest maker of consumer electronics until it was eclipsed by Nokia Corp. in the late 1990s. Licensing royalties sustained the company through bad times. "The CD was in itself an easy product to market," said Philips' current marketing chief for consumer electronics, Lucas Covers. It wasn't just the sound quality - discs looked like jewelry in comparison to LPs. By 1986, CD players were outselling record players, and by 1988 CDs outsold records. "It was a massive turnaround for the whole market," Covers said. Now, the CD may be seeing the end of its days. CD sales have fallen sharply to 553 million sold in the United States last year, a 22 percent drop from its 2001 peak of 712 million, according to Nielsen SoundScan. Napster and later Kazaa and BitTorrent allowed music fans to easily share songs over the Internet, often illegally. More recently, Apple Inc. and other companies began selling legal music downloads, turning the MP3 and other digital audio formats into the medium of choice for many owners of Apple's iPods and other digital players. "The MP3 and all the little things that the boys and girls have in their pockets ... can replace it, absolutely," said Kramer, the retired engineer. CDs won't disappear overnight, but its years may be numbered. Record labels seeking to revive the format have experimented with hybrid CD-DVD combos and packages of traditional CDs with separate DVDs that carry video and multimedia offerings playable on computers. The efforts have been mixed at best, with some attempts, such as the DualDisc that debuted in 2004, not finding lasting success in the marketplace. Kramer said it has been satisfying to witness the CD's long run at the top and know he had a small hand in its creation. "You never know how long a standard will last," he said. "But it was a solid, good standard and still is." http://www.siliconvalley.com/news/ci_6641144  Producers Howl Over Sound Cut Out by MP3 Compression Joel Selvin Whether you know it or not, that compact disc you just copied to your MP3 player is only partially there. With the CD on its way out and computer files taking over as the primary means of hearing recorded music, the artificial audio of MP3s is quickly becoming the primary way people listen to music. Apple already has sold 100 million iPods, and more than a billion MP3 files are traded every month through the Internet. But the music contained in these computer files represents less than 10 percent of the original music on the CDs. In its journey from CD to MP3 player, the music has been compressed by eliminating data that computer analysis deems redundant, squeezed down until it fits through the Internet pipeline. When even the full files on the CDs contain less than half the information stored to studio hard drives during recording, these compressed MP3s represent a minuscule fraction of the actual recording. For purists, it's the Dark Ages of recorded sound. "You can get used to awful," says record producer Phil Ramone. "You can appreciate nothing. We've done it with fast food." Ramone, who has recorded everyone from Frank Sinatra to the Rolling Stones, was a musical prodigy who graduated from Juilliard at 16. He won the first of his nine Grammys in 1965 for the classic album "Getz/Gilberto." He is not alone in the upper ranks of his profession in decrying the state of audio, even though millions of dollars have been spent building high-tech digital recording studios. "We're pretty happy with what we send out," says engineer Al Schmitt, winner of 15 Grammys for records by artists from Henry Mancini to Diana Krall. "What happens after that, we have no control over that anymore." These studio professionals bring their experience and expensive, modern technology to bear on their work; they're scrupulous and fastidious. Then they hear their work played back on an iPod through a pair of plastic ear buds. Ask Ramone how it feels to hear his work on MP3s, and he doesn't mince words. "It's painful," he says. MP3s have won the war of the formats because of technology, not because of their audio quality. "It's like hearing through a screen door," says neuroscientist Daniel Levitin of McGill University, author of "This Is Your Brain on Music." But what is the price of inferior audio quality? Can poor audio touch the heart as deeply as better sound? John Meyer, who designs and builds some of the world's best speakers at his Meyer Sound Labs in Berkeley, Calif., doesn't think so. "It turns you into an observer," Meyer says. "It forces the brain to work harder to solve it all the time. Any compression system is based on the idea you can throw data away, and that's proved tricky because we don't know how the brain works." It could be that MP3s actually reach the receptors in our brains in entirely different ways than analog phonograph records. The difference could be as fundamental as which brain hemisphere the music engages. "Poorer-fidelity music stimulates the brain in different ways," says Dr. Robert Sweetow, head of the University of California-San Francisco audiology department. "With different neurons, perhaps lesser neurons, stimulated, there are fewer cortical neurons connected back to the limbic system, where the emotions are stored." But Sweetow also notes that music with lyrics may act entirely differently on a cerebral level than instrumental music. "The words trigger the emotion," he says. "But those words aren't necessarily affected by fidelity." Certainly '50s and '60s teens got the message of the old rock 'n' roll records through cheap plastic transistor radios. Levitin remembers hearing Sly and the Family Stone's "Hot Fun in the Summertime" on just such a portable radio, an ancient ancestor of the iPod. "It was crap, but it sounded great," he says. "All the essential stuff comes through that inch-and-a-half speaker." Levitin also says that Enrico Caruso and Billie Holiday can probably move him more than Michael Bolton or Mariah Carey under any fidelity. "If the power of the narrative of the movie isn't there," he says metaphorically, "there's only so far cinematography can take you." EMI Records announced earlier this year the introduction of higher-priced downloads at a slightly higher bit rate, although the difference will be difficult to detect. "It's probably indistinguishable to even a great set of ears," says Levitin. For digital audio to substantially improve, several major technological hurdles will have to be cleared. The files will have to be stored at higher sampling rates and higher bit rates. Computing power will have to grow. New playback machines will have to be introduced. (Ramone thinks high-definition television is the model for something that could be "HD audio.") And if the Internet is going to be the main delivery system for music in the future, Internet bandwidth will also be a factor. "The Internet is in charge now," says Ramone, "and it has all kinds of wobbles. You have wires hanging out of windows and things like that. That's just the way things have to be because the Internet is in transition." WHAT'S SACRIFICED IN THE PROCESS Various digital audio formats MP3: What has become a generic name for compressed audio files was originally taken from a set of video and audio compression standards known as MPEG (Moving Pictures Experts Group). There are many codecs, or compression programs (Apple converts CDs to an AAC file on iPods), but most reduce the file to about 6 percent of its original size. WAV: The standard computer audio file stores data at 44,100 samples per second, 16 bits per sample (although recording studios are commonly equipped with 24-bit technology). WAV files are uncompressed and written to compact discs in Red Book audio, which adapts the file for compact disc players. AIFF: Most professional audio is saved in these large files, which use about 10 megabytes for every minute of stereo audio. FLAC: This codec, favored by Grateful Dead tape traders, stands for Free Lossless Audio Code. It reduces storage space by 30 percent to 50 percent, but without compression. A full audio CD can be burned from the file, unlike from MP3s. http://seattlepi.nwsource.com/busine...p3sound13.html  Well, at least they’re still cheap Russia Throws Out Net Piracy Case BBC A former owner of Russia's music website Allofmp3.com who sold cut-price downloads of Western music has been acquitted of copyright offences. A court in Moscow ruled that Denis Kvasov and his site had operated within the bounds of Russian law. The site was attracting millions of customers before it was shut in June - under pressure from US music firms. The site has also been a thorny issue in US-Russia talks over Moscow's bid to join the World Trade Organization. 'Very bad precedent' Mr Kvasov, head of Mediaservices, which owned the website, was put on trial after EMI, Warner Music Group and Universal music companies pressed for his prosecution. But District Judge Yekaterina Sharapova on Wednesday threw out the prosecution's case. "The prosecution did not succeed in presenting persuasive evidence of his involvement in infringing copyright law," she said. During the trial, Mr Kvasov, successfully argued that he had paid royalties to a local organisation, the Russian Multimedia and Internet Society (Roms). The head of Russia's anti-piracy organisation, Konstantin Zemchenkov, said the court's verdict set a "very bad precedent". '$1 for album' The site offered downloads at far lower prices than mainstream businesses like iTunes. A starting price for a track was as low as about $0.10, while an album was offered for $1. Mediaservices has always maintained it pays royalties to Roms, but many Western firms do not recognise this organisation and refuse to accept its offers of payments. As part of protracted negotiations over Russia's entry to the WTO, an agreement in principle was reached regarding website regulation in 2006. It said: "The United States and Russia agreed on the objective of shutting down websites that permit illegal distribution of music and other copyright works. "The agreement names the Russian-based website AllofMP3.com as an example of such a website." Although Allofmp3.com disappeared in June, another Russia-based discount music site opened shortly afterwards. http://news.bbc.co.uk/go/pr/fr/-/2/h...pe/6948345.stm  Downside of Downloading Door open for IP owners to get names of those doing it illegally Derrick A Paulo GOING online to download content may soon offer less anonymity in Singapore than it used to, particularly for those getting copyrighted material illegally. According to legal experts, the laws — and copyright owners — are starting to scale the walls of privacy in the name of intellectual property (IP). The latest foothold they have secured is a court decision ordering Internet service provider (ISP) StarHub to reveal the identity of about 1,000 subscribers who have downloaded Japanese animé cartoons illegally. Animé distributor Odex, which won the case, is likely to seek compensation of up to $5,000 from these individuals and an undertaking to halt such illegal downloads, The Straits Times reported. While the enforcement net may not have been cast this wide in Singapore before, corporate counsel and Nominated MP Siew Kum Hong told Today it was "only a question of time" before widescale legal action taken elsewhere — such as those by the Recording Industry Association of America — were replicated here. "As a general principle of law, it's not new. Someone who has been wronged has the right to go to a third party to seek information. And if people are infringing copyright, rights owners are entitled to do this," he said. While anonymity has been one of the Internet's hallmarks, the latest ruling could make it easier for IP owners to police infringements online than offline, ironically, because cyber offences leave an e-trail, said Mr M Ravindran, a partner at IP law practice Ravindran Associates. "So, now that you've got a precedent on disclosure, it will be interesting to see how IP owners will react," he said. All eyes will be on a hearing tomorrow, between Odex and Pacific Internet on the same matter and also involving about 1,000 subscribers. A similar ruling could strengthen the hand of copyright owners here at the expense of privacy. Mr Siew and Mr Ravindran believe that it would be hard to argue that being in cyberspace ought to offer people protection against copyright infringement. Still, the process is not cut-and-dried. Last month, an adviser to the top European Union court said that telecom companies in Europe are not required to hand over information on clients believed to be running music-sharing websites in civil cases. Nanyang Law managing director Ng Kim Tean told Today that IP owners cannot expect the court to order ISPs to disclose customer information each time there is a suspicion of illegal downloading. To give the right of confidentiality its due weight, there should be "overwhelming evidence" of illegal downloading, he said. "And the judge has the discretion to decide what is the best court order to give. Disclosing customer information is not the only way," he added. ISPs could be asked to inform customers to stop illegally downloading content or to block such people from the websites. The last time any action was reported to have been taken against downloaders was when the police raided seven homes last October, following a tip-off by the Record Industry Association of Singapore. Three students were subsequently charged for illegal downloading and distribution. Under the Copyright Act, which was toughened in 2005, egregious downloading of music, movies and software can lead to a jail term of up to six months and fines of up to $20,000. http://www.todayonline.com/articles/205715.asp  Microsoft Licenses Audio Watermarking Tech Ed Oswald Microsoft said Wednesday that it had licensed its audio watermarking technology to Activated Content in an effort to spur the efforts behind embedding trackable "watermarks" in audio files. The process of watermarking holds many benefits, as it can potentially be used in the fight against piracy. For example, DRM-less files could carry an identifiable code in them. When these files appear on peer-to-peer networks, labels would be able to identify where they are coming from. Activated Content appears to have more than just watermarking music files in mind for Microsoft's technology, as it plans to use it in the telephony and advertising industries as well. The company plans to merge its existing proprietary technologies with Microsoft's, the companies said. "Activated Content can now be in the forefront, providing a digital link in the multibillion-dollar mobile advertising marketplace and enabling aggregators to link advertising and consumers with user-generated content," company CEO Eric Silberstein said in a statement. Microsoft's technologies were developed in its Research labs, and it said that licensing efforts are part of a broader initiative to make available technologies to companies and startups. Microsoft also believes that making the technologies broadly available will add value to a healthy IT ecosystem and provides new economic opportunities. Watermarking is not without controversy. Most recently in June Apple was criticized for using the technology in its music files, with the Electronic Frontier Foundation claiming it was a security risk. However, Apple has never given a reason for it although it is speculated it is due to piracy concerns. At least one pirater has been caught due to this practice. 27 year-old Salvador Nunez Jr. was arrested in February for uploading a copy of "Flushed Away" after watermarking details helped authorities track down the source to his PC. http://www.betanews.com/article/Micr...ech/1187202565  Actors Turned Candidates Don't Get Reruns If Fred Thompson decides to put his acting career on hold and run for President at least one television network will put remove reruns of shows where he appears. NBC says it will not schedule any of the 100-plus episodes of "Law & Order" which feature appearances by Thompson. Networks did the same thing when Ronald Reagan ran for President in 1980. If Thompson Runs for President, Don’t Look for Him in Reruns - NBC said it was ready to stop showing reruns of the episodes former Senator Fred D. Thompson appears in because of federal equal time regulations for presidential candidates. http://www.capitolhillblue.com/cont/node/3139  NewYorkCountryLawyer Cases of interest from attorney Ray Beckerman Boston Judge Denies RIAA Motion for Judgment In a Boston case, Capitol v. Alaujan, the defendant is representing herself, without a lawyer. Nevertheless, the Judge denied the RIAA's motion for summary judgment, which the RIAA had based upon the defendant's alleged failure to respond to the RIAA's Request for Admissions. The Court's decision held that the RIAA had served its requests for admission prematurely, prior to the conduct of any discovery conference. The Court also noted that the RIAA had upped the ante quite a bit, trying to get a judgment based on 41 song files, even though it had originally been asking for judgment based on 9 song files. This would have increased the size of the judgment from about $7,000 to about $31,000. The Judge scheduled a discovery conference for October 23rd, at 2:30 P.M. and ordered everybody to attend. Such conferences are open to the public. http://yro.slashdot.org/article.pl?sid=07/08/15/2228201 Foster Demands RIAA Post $210K Security For Fees A few days ago it was reported that, in view of the RIAA's one-month delay in paying the $68,685.00 attorneys fee award in Capitol v. Foster, and its lawyers' failure to respond to Ms. Foster's lawyer's email, Ms. Foster filed a motion for entry of judgment so that she could go ahead with judgment enforcement proceedings. In response to that motion the RIAA submitted a statement that it had no objection to entry of judgment, and intimated that it thought there would be an automatic stay on enforcement of the judgment, and that it would ultimately file an appeal. After seeing that, Ms. Foster's lawyer has filed a motion for the Court to require the RIAA to post $210,000 in security to cover the past and future attorneys' fees and costs that are expected to be incurred. http://yro.slashdot.org/article.pl?sid=07/08/16/134246 Class Action Initiated Against RIAA Ever since the RIAA's litigation campaign began in 2003, many people have been suggesting a class action against the RIAA. Tanya Andersen, in Oregon, has taken them up on it. The RIAA's case against this disabled single mother, Atlantic v. Andersen, has received attention in the past, for her counterclaims against the RIAA including claims under Oregon's RICO statute, the RIAA's hounding of her young daughter for a face-to-face deposition, the RIAA's eventual dropping of the case "with prejudice," and her lawsuit against the RIAA for malicious prosecution, captioned Andersen v. Atlantic. Now she's turned that lawsuit into a class action. The amended complaint seeking class action status sues for negligence, fraud, negligent misrepresentation, federal and state RICO, abuse of process, malicious prosecution, intentional infliction of emotional distress, violation of the Computer Fraud and Abuse Act, trespass, invasion of privacy, libel and slander, deceptive business practices, misuse of copyright law, and civil conspiracy. http://yro.slashdot.org/article.pl?sid=07/08/17/1728225 RIAA's "Making Available" Theory Is Tested The RIAA's argument that merely “making files available” is in and of itself a copyright infringement, argued in January in Elektra v. Barker (awaiting decision), is raging again, this time in a White Plains, New York, court in Warner v. Cassin. Ms. Cassin moved to dismiss the complaint; the RIAA countered by arguing that “making available” on a p2p file sharing network is a violation of the distribution right in 17 USC 106(3). Ms. Cassin responded, pointing out the clear language of the statute, questioning the validity of the RIAA's authorities, and arguing that the Court's acceptance of the RIAA's theory would seriously impact the Internet. The case is scheduled for a conference on September 14th, at 10 AM (PDF), at the federal courthouse, 300 Quarropas Street, White Plains, New York, in the courtroom of Judge Stephen C. Robinson. The conference is open to the public. http://yro.slashdot.org/article.pl?sid=07/08/17/2039209  Tom Cruise Film Company Raises $500 Million Bob Tourtellotte United Artists, the film company run by actor Tom Cruise and Chief Executive Paula Wagner, said on Thursday it raised $500 million through Merrill Lynch to fund 15 to 18 movies over the next five years. Wagner called the financing "a milestone event" for United Artists, which was revived last year by Cruise, Wagner and their studio partner, Metro-Goldwyn-Mayer Inc. "It leaves us perfectly poised to realize our vision of making movies that are both important and commercial," Wagner said in a statement. Financial details were not disclosed. One of Hollywood's biggest box office draws, Cruise has starred in blockbusters like "Mission: Impossible" and Oscar contenders such as "Jerry Maguire." But last year, Cruise's long-time studio partner Paramount Pictures cut its ties to Cruise and Wagner following the release of "Mission: Impossible III" -- an international hit with $264 million at overseas box offices, but only a modest success with $134 million in U.S. and Canadian ticket sales. Cruise and Wagner went to Metro-Goldwyn-Mayer where they partnered with the studio behind the James Bond movies to revive United Artists. Separately, a Metro-Goldwyn-Mayer spokesman refuted a published report that Goldman Sachs and Deutsche Bank had withdrawn from underwriting $1 billion in financing for MGM. MGM's Jeff Pryor said the studio never had a firm deal with Goldman Sachs or Deutsche Bank, so there was never a commitment from which to withdraw. "We are confident we will come to (a financing package for MGM), but we are not in any hurry to do a slate deal," Pryor said. "Slate" is used to describe a group of upcoming films. Pryor added that MGM's priority was completing the United Artists funding, which demonstrated "that even in tough market conditions, good product will always prevail." United Artists said it expects to release four to six films a year. First up is Drama "Lions for Lambs," directed by Robert Redford and set for a November release. Beyond that, World War II thriller "Valkyrie" will hit theaters in the summer of 2008. MGM is owned by a consortium of companies including private equity firms Texas Pacific Group and Providence Equity Partners, Sony Corp and Comcast Corp. http://www.reuters.com/article/compa...37815220070816  Net Movie Services Fail to Thrill Users Parks Associates says people are generally unhappy about the quality, selection and price of video downloaded from the Web. The firm just released the results of a survey on the subject, and by the looks of things the corner video store isn't in danger of going out of business very soon. Here are some key take-aways: Of the 13,000 people surveyed: *Just 16% say the selection of videos available online is good *Only 13% say video downloads are sold at a reasonable price *Fewer than one in five consumers downloading video say they plan to download videos again in the future “People don’t see a reason to use video downloading services,” says Parks' research director John Barrett in a release. "Sure, it saves a trip to the video store, but it takes longer, looks worse, and you end up watching it on a 17” screen. No wonder consumers are dissatisfied with the experience.” Parks says it surveyed people in 13 countries including those who get their video free from peer-to-peer (P2P) services like Kazaa, and those who download video from legit pay sites like iTunes. Parks' survey clearly was focused on premium content like movies, and not YouTube-style shared video, which is loved by millions around the world. http://blogs.pcworld.com/staffblog/archives/005143.html  Odd Numbers Up for 'Simpsons,' 'Bourne' Gregg Kilday Is 70 the new 50? Even more intriguing, is 50 the new 14? During the past couple of weeks, Hollywood has watched as a couple of movies that most expected to open in the $50 million range shot up to the $70 million mark. First, 20th Century Fox's "The Simpsons Movie" bowed on the weekend of July 27 to a whopping $74 million. The following weekend, Universal Pictures' "The Bourne Ultimatum" raced ahead of even the most optimistic expectations to capture $69.3 million. The massive openers spoke to several factors. Both titles were proven commodities, even if they did come from opposite ends of the entertainment spectrum. After 18 years on network TV and in syndication, the "Simpsons" clan has developed a deep fan base, many of whom have grown up with the irreverent series. While there was some question entering the movie's opening weekend about whether audiences would show up for characters they could already see for free, the opportunity for "Simpsons" fans to gather in the communal setting of their local mutliplex to laugh together at Homer's familiar catchphrases meant that the movie performed like a sequel to a proven franchise. "Bourne," of course, already had two installments behind it that have steadily built on the original appeal of the Robert Ludlum novels. And "Ultimatum" didn't play like the third film in a series that is simply spinning its wheels. The film connects all the dots in a way that repays the loyalty of fans. Two-thirds of the plot of "Ultimatum," for example, plays out between the final Moscow chase scene in the second film, "The Bourne Supremacy," and "Supremacy's" final tag scene in New York. And the new movie ends with images that summon up echoes of the opening shots in the original "Bourne Identity." Additionally, "The Simpsons Movie" and the three "Bournes" benefit from consistent creative oversight. "Simpsons" creator Matt Groening and producer James L. Brooks, who shepherded the Simpsons' transfer to TV series, led the team of experienced "Simpsons" hands who contributed to the movie. In the case of "Bourne," director Doug Liman, who directed the first film, may have seen Paul Greengrass take up his template to fashion the two that followed, but a team that includes producer Frank Marshall and screenwriter Tony Gilroy, among others, has been involved in all three films, contributing to the unity of vision. In terms of the audiences they have attracted, however, the two movies took different routes to their mega openings. Sure, both skewed toward male moviegoers; CinemaScore, in its samplings of their opening-weekend audiences, reports that "The Simpsons Movie" drew a crowd that was 63% male, while "Ultimatum's" constituency on opening weekend was 56% male. But the age of their respective audiences was another matter: Fifty-nine% of the initial "Simpsons" audience was younger than 25. In the case of "Ultimatum," Cinemascore found that 82% of its audience was over 25. In fact, a rather amazing 33% of the "Ultimatum" audience was 50-plus. That comes as a surprise only because for years the mantra surrounding summer blockbusters is that Hollywood gears them all for 14-year-old boys. It's further assumed that older audiences take their time before committing to a movie. True, there's no denying that teens often are the first wave to hit theaters on opening day. But "Ultimatum" suggests that it doesn't have to be that way all the time. Sometimes, those slow-moving fiftysomethings move almost as fast as 14-year-old kids. http://www.hollywoodreporter.com/hr/...09e49bf8256a8e  Aussies Get Lesson from Pirated "Simpsons" Movie: Can't Plug a Digital Leak Ken Fisher Australian authorities have announced that they have arrested a man believed to be responsible for leaking The Simpsons Movie to the 'Net. A Sydney-area man is alleged to have used a mobile phone to record the film in a theater on the day of its release, which he then uploaded hours later, beating the street date for the movie throughout much of the world. The low-quality copy, which hit the wires a few hours before the movie's official release in the United States, was widely reported in the media as a threat to the much-anticipated Simpsons release. Despite the gloom and doom, the movie's opening weekend smashed expectations, much to the chagrin of elements in the industry who would have liked to point to a poor debut as a sign of the evil effects of piracy. There were fears that the Simpsons were played out, but the movie did far better than expected. Quick, but not quick enough The raid was the result of joint teamwork between the Australian Federal Police (AFP), the Australian Federation Against Copyright Theft (AFACT) and Twentieth Century Fox (Fox). The three had also worked together to track the source of the film leak back in July but found that by the time they could do anything about it, it was too late. "Within 72 hours of making and uploading this unauthorized recording, AFACT had tracked it to other streaming sites and P2P systems where it had been illegally downloaded in excess of 110,000 times and in all probability, copied and sold as a pirate DVD all over the world," said Adrianne Pecotic, executive director of AFACT, in a statement. As it turns out, AFACT got a heads-up from Fox, which was monitoring P2P networks in search of the first Simpsons movie uploads. Yet even with this monitoring, it was too late to stop the leaks. AFACT said that in the short time it took to identify the leak, it had rapidly spread to other sites, and investigators even learned that it was rapidly re-edited into a French language version, and also transcoded into other formats and distributed via BitTorrent sites by two "organized release groups which facilitate file sharing." Hence, the "speedy removal" of the movie "within 72 hours of it being posted on the internet" was no removal at all, for the movie spread too fast. Once the cat's out of the bag, there's no putting it back in. Once copied, it cannot be "removed" from the Internet. The identity of the man accused of recording and uploading the film has not been released, but he is expected to appear in court in early October. There is no word on how AFACT tracked the upload to the man in question, but given that the group believes it has found the source web site, it was likely a simple IP address-based identification. http://arstechnica.com/news.ars/post...ons-movie.html  Be Kind Rewind Movie Trailer Coming Soon (or on YouTube) Peter Sciretta I don’t exactly understand how I missed it, but the trailer for Michel Gondry’s (Eternal Sunshine of the Spotless Mind, The Science of Sleep) new comedy Be Kind Rewind premiered at Comic-Con last weekend. Someone taped the screen and uploaded the video to YouTube, but I could never recommend watching a handheld video taped version (although, I personally couldn’t resist). [Please read my mini-rant about this at the end of this posting] BEFORE you start searching for it, keep on READING… You won’t have to wait much longer, the trailer is set to premiere in front of Rush Hour 3 this Friday. But fear not, you won’t have to pay for a crappy Brett Ratner movie just to see this very cool trailer. I’ve been told it will premiere online tomorrow or Thursday. Be Kind Rewind follows Jerry (Jack Black), a junkyard worker who attempts to sabotage a power plant he suspects of causing his headaches. But he inadvertently causes his brain to become magnetized, leading to the unintentional destruction of all the movies in his friend’s (Mos Def) store. In order to keep the store’s one loyal customer, an elderly lady with a tenuous grasp on reality, the pair re-create a long line of films including The Lion King, Rush Hour, Ghostbusters, When We Were Kings, Back to the Future, Driving Miss Daisy, and Robocop , putting themselves and their townspeople into it. They become the biggest stars in their neighborhood. Be Kind Rewind hits theaters on December 21st 2007 in limited markets. http://www.slashfilm.com/2007/08/07/...or-on-youtube/  Steal This TV Show — And Please Talk About It With Your Friends Wayne Friedman Some $100 million has been spent on entertainment piracy. Yet every year more network prime-time pilots can be found illegally on peer-to-peer Web sites. Is that the wrong financial formula? Some critics say sarcastically that the networks are subversively releasing them — unofficially. Networks swear they are not doing this. But perhaps they should take another look. More than a few producers — especially those with mostly under-the-radar cable programs — like promotional ideas that build unofficial buzz. So when is piracy actually a tool for underground marketing a TV show? The line is fuzzy, and you probably couldn’t get any two TV marketing people to agree on what piracy is, anyway. More than a few networks offer up previews of their pilots on the associated Internet destinations. The lone exception is ABC, which says its marketing team won’t approve sneak peeks — figuring they’ll ruin its official and traditional network “opening.” Some complain there is no universal piracy system among producers and networks — and because of that, stuff slips through the cracks. They also say that better piracy technology — that is, assigning an individual watermark for every single DVD screener that goes to each critic, TV business writer or production person who needs to get one — would be more expensive. Unlike movie studios, networks generally have 22 episodes a year to sell to viewers and advertisers. So for some network executives, letting go of one episode may not be a big problem right now — but could be a growing one. For instance, Fox had a problem with “24″ when a man pleaded guilty to uploading the first four episodes of season six illegally. Peer-to-peer network aficionados say there is little difference in networks putting out sneak previews (other than the timing) and what winds up on so-called torrent sites. The end result is the same — creating buzz, either positive or negative. I have a better idea. Networks should just save the $100 million on piracy and send out those DVD screeners — with TV commercials already included. It would be similar to what the networks already do with their TV shows on their digital platforms. Networks will get more marketing buzz, extra advertising revenue, and, no doubt, fewer viewers looking to download shows from peer sites with no easy means of fast-forwarding or editing out the commercials. Then put a message on the DVD that will get everyone’s attention: Please steal this disc. http://blogs.mediapost.com/tv_watch/?p=756  Blu-Ray Outpaces HD-DVD in U.S.: Home Media Research Blu-ray high-definition movie discs outsold films on the rival HD-DVD format by 2-to-1 in the United States in the first half of 2007, Home Media Research said on Tuesday. The division of Home Media Magazine said total sales of Blu-ray discs, using a Sony Corp-backed technology, totaled 1.6 million units from January 1 through July 1, compared with 795,000 HD-DVD discs sold in that period. HD-DVD was developed by Toshiba Corp and backed by Microsoft Corp and film studios such as Warner Bros. Both formats were launched in spring of 2006. An estimated 3.7 million high-definition discs have been sold, including 2.2 million in Blu-ray and 1.5 million in HD-DVD through the end of July, according to Home Media. A Home Media spokeswoman said Blu-ray got a further boost in August from strong sales of the "300" title. Stephen Nickerson, senior vice president, market management at Warner Home Video, reported sales of about 190,000 Blu-ray units of the film, versus 97,000 in HD-DVD since July 31. The industry-wide standards war is reminiscent of the VHS and Betamax battle. Blockbuster Inc, the largest U.S. provider of home movie entertainment, in June set out plans to line its shelves with Blu-ray DVDs, saying Blu-ray rentals were "significantly outpacing" HD-DVD rentals. http://www.reuters.com/article/compa...19176920070815  Sex Video Causes Outrage An amateur video of a northern Nigerian film actress in a sex scene has caused a public outcry in the Muslim north, prompting a movie industry body to expel actors deemed "immoral," a local newspaper reported Monday. Leadership newspaper said the eight-minute video clip, recorded for private use on a mobile phone by the actress's boyfriend and showing the two of them naked, had circulated widely among mobile phone users across the north. "This was the first time such exposure involving Hausa-Fulani persons was witnessed in the country," Leadership said, referring to the dominant ethnic groups in the generally conservative north. Muslim clerics have condemned the clip and radio programs have been full of complaints about immorality in the film industry. The actress, who was not named by the paper, has gone into hiding, Leadership said. Nigeria's hugely successful home video industry, known as Nollywood, is mostly based in the south of the country which is predominantly Christian and considered less conservative. In the past few years a Hausa-language home video industry has sprung up in the north and has also become very popular. Leadership said the Kano state Filmmakers' Association had reacted to the scandal over the sex video by expelling 17 actors deemed to have brought the industry into ill repute. The 17 were not connected to the video clip but were "thought to be involved in immoral acts such as drunkenness and fornication," the newspaper reported. Kano is among 12 northern states that started enforcing Islamic Sharia law in 2000, increasing tensions between the Muslim majority and sizeable Christian minorities all over the north. Thousands died in several bouts of sectarian violence. http://www.reuters.com/article/newsO...18548320070813  Alps Host Mass Naked Photo Shoot 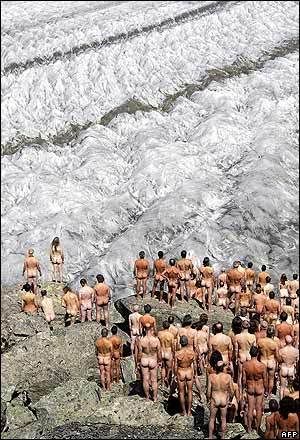 Nearly 600 men and women volunteers have stripped naked to pose for US photographer Spencer Tunick on the slope of a melting Swiss glacier. The photo shoot on the Aletsch glacier was commissioned by environmental group Greenpeace as part of a campaign to raise awareness about global warming. Despite the Alpine setting 2,300m (7545 feet) up, the temperature was well above freezing, at between 10 and 15C. Tunick specialises in such scenes, which he calls "body landscapes". His previous backdrops have ranged from Caracas to New York. The Aletsch glacier is a protected Unesco World Heritage site. http://news.bbc.co.uk/2/hi/europe/6952930.stm  Shop Targets Hunters With Camo Bibles Ed Stoddard An on-line outdoor retailer in the United States is selling camouflaged Bibles, a curious product which says a lot about American culture. "Our NIV (New International Version) Bible in Realtree camo is our best selling item, followed closely by our camo Bible cover," said David Lingner, the president of Arkansas-based Christian Outdoorsman, which sells Christian-themed hunting and angling products online. The cover of this Bible is graced by leaves and tree bark. This enables the devout who also hunt to take their Bible into the woods with them while concealing it from their prey. The C in Christian on the shop's Web site is shaped like a fish hook while the O in Outdoorsman has a cross-shaped rifle scope site inside of it. Also on offer is a camo waterproof Bible. "Water, ice or condensation will not damage this durable word of God," proclaims the on-line sales pitch. Such products are classically American and highlight cultural traits which are especially pronounced in the South. The first is a love affair with all things cam, from pick-up trucks to baseball hats to shotguns. "Men in the South love camo, it's just another way to communicate that they are an outdoorsman," said Lingner. These products also highlight the U.S. evangelical love affair with hunting, fishing and the great outdoors. Prominent U.S. evangelicals who engage in such activities include President George W. Bush and James Dobson, founder of the influential conservative Christian advocacy group Focus on the Family. A U.S. survey of licensed hunters and anglers last year commissioned by the National Wildlife Federation found half of those polled identified themselves as evangelical Christians. Evangelical Christians, who number 60 million in the United States, are a key base of support for the Republican Party, which helps to explain its stand on a number of issues including its strident opposition to gun control. Hunters don't take kindly to restrictions on their weapons of choice. Lingner said the evangelical enthusiasm for the outdoors went beyond the macho culture of the U.S. South. "Because we believe that God created all this, when we are outdoors it is really a spiritual experience and we see how awesome it is. It makes being outdoors that much more meaningful," he said. And Christ's disciples were fishermen after all. There are a number of U.S. Christian outdoor ministries including Anglers for Christ Ministries, Christian Bowhunters of America and the Christian Deer Hunters Association. Anglers for Christ Ministries said in its mission statement that it is "heeding God's call to minister to the lost and be 'Fishers of Men.'" http://www.reuters.com/article/lifes...41891720070813  Seven Days of Peace and Music. And Mud and Suds. Jack  Revellers getting down to earth at Budapest's one-week, around-the-clock Sziget (Island) Music Festival.  Then it’s good clean fun in Sziget’s foam-pool.  Author Recalls Events Leading to Woodstock Festival Julie Mollins Without Elliot Tiber there may have never been a Woodstock music festival. The legendary concert in 1969 that attracted almost 500,000 people and became a symbol of the 1960s counterculture almost didn't happen. Tiber had hosted a music concert at his parent's motel in White Lake, New York for 10 years but only a handful of people ever showed up. So when he heard that Michael Lang, an organizer of the original Woodstock Music and Art Fair, had been barred from holding his festival in a nearby community, Tiber says he offered him his concert permit, and introduced him to Max Yasgur who owned the land where it was held. In his autobiography "Taking Woodstock: A True Story of a Riot, a Concert and a Life" Tiber, 72, described the events that preceded the festival 38 years ago. He spoke to Reuters about his involvement with the event that began on August 15 and the famous people, including Truman Capote and Tennessee Williams, he met while living in Manhattan in the 1960s. Q: What was your involvement with the Woodstock festival? A: "If not for me there wouldn't have been one. When Woodstock was thrown out of the other towns ... because local townspeople were afraid of hippies, drug addicts and gays all coming to their little towns I had my permit. "I showed (Lang and his associates) the land, which was really swamp and mud and was unsuitable, and they were about to leave. And so I said, 'My friend and neighbor Max Yasgur ... he has hundreds of acres.' And we went to look at the farm and they saw this huge, big open space and had one big collective orgasm." Q: What was the high and what was the low of the concert? A: "Looking back on it, it was all high. The low at the time was the mud and the rain and no food and no water and no toilets left. The big high was that there's a five-mile lake near White Lake. The music hit the lake like a sounding board and you could hear every song, every syllable, clear as day from my grounds, which were four miles away. Q: In the book, you detail encounters with various well-known American authors and artists. How did knowing these cultural icons affect your life? A: "It opened up a whole new life that you didn't have to hide. You weren't rejected. Everybody wanted everybody? It was before AIDS and I didn't feel fat and ugly. I wasn't, but that's how I always felt because my mother always told me I was. "It opened up my eyes and my heart to finding myself and functioning as an individual rather than fitting into being a rabbi the way my mother wanted." Q: What are your thoughts on the larger impact of Woodstock on society and history? A: "It was all Vietnam and the man on the moon. We replaced Vietnam in the headlines. We replaced the man on the moon. When peace and music can replace the fortune spent on going no place in space, and the fortunes spent on the war machines -- replace it with peace and music even though it was only three days -- to me that was a major, major happening. "And it should be happening again. There will never be another (music festival) like Woodstock -- never. The idea of peace and music is a much more important set of values than this endless war stuff going on. I wish there was another Woodstock now to replace the Iraqi war values that are out there. http://www.reuters.com/article/lifes...11214320070814  They’ve Just Got to Get a Message to You Jeff Leeds As a teenage rock fan, all Dennis Vorreyer really expected of the Lollapalooza music festival in Chicago two weekends ago was the chance to see his favorite bands perform live. But he and his father, Jeffrey, who accompanied him to the festival, signed up for Lollapalooza’s text-message network, and thus learned about a guitar-playing contest taking place there. Dennis, 14, entered and won a new Gibson guitar. Tad Kubler, the lead guitarist for the Hold Steady, who was involved in the contest, then invited Dennis to perform with the band as it closed its set. “Having your cellphone everywhere is important for everybody now,” Dennis said. “I never dreamed of playing Lollapalooza.” The modern mobile phone — equipped with camera, Internet access and more — has proved to be a liability for some performers, like Akon and Beyoncé, whose regrettable moments were captured by fans and then immortalized on YouTube and similar sites. But for the fans themselves, mobile phones are becoming as important an accessory as an all-access wristband. Beyond using them to record a short souvenir, they are becoming a ticket to everything from free ringtones to V.I.P. treatment. On Gwen Stefani’s recent tour, as many as 20 percent of the audience at some shows agreed to pay 99 cents for text messages and the chance to win better seats, according to the mobile marketing company Impact Mobile. At festivals like Lollapalooza, thousands of fans sign up to receive continuous updates from concert organizers about promotions and special events. Even when there is no fee, the service comes at a price: fans must give their phone numbers to marketers. And purists — and some artists — disapprove of fans pecking out text messages or snapping pictures during performances. Still, the arrival of a new generation of phone-based activities could add a new twist to live events at a time when rising ticket prices have discouraged many concertgoers. Prince recently invited fans at a Minneapolis show to send text messages to his Web site so that everyone else could read about what they were missing. (“show just ended. I have never sweat more in my entire life,” read one message posted at 4:03 a.m.) On the Family Values hard-rock package tour, the band Korn has allowed concertgoers to vote by phone on which song should end the show. For $1.99, they can also enter a contest to win an expense-paid trip to a coming show in California. Fergie devotees who attended her recent shows could dance against a special-effects “green screen” to create a video in which they appeared with her. The resulting clip was sent to their cellphones. The introduction of more interactive features highlights how musicians — and the marketers who surround them — are trying to establish connections that continue long after a fan leaves a concert. Mathew Knowles, the manager (and father) of Beyoncé, said he expected to use the thousands of phone numbers collected on her current tour to pitch a variety of products, including a Beyoncé-themed phone. “It allows us to have that continuing dialogue and communication via the cellphone. That’s the bigger piece of the puzzle,” Mr. Knowles said. “I love the fact that all of those phones are up in the air. They want to be able to experience it after they leave. That’s a beautiful thing to me.” Some warn that concerts could quickly open a new channel for marketers to send junk mail to cellphones. “You can see this getting out of hand,” said Les Borsai, an artist manager and co-owner of Modern Mobile Marketing, one of the companies that run text promotions. But the phone information “is the most sacred piece we have. I don’t want to go and get this data and sell it to Kmart. What you want to do is build trust with the consumer.” So far, the money generated from paid, or “premium,” text-messaging events represents a fraction of a tour’s overall revenue. Marketers say that even popular music acts might ring up only $100,000 a tour. But the possibility of a new revenue stream has already touched off squabbles among concert promoters, sponsors and artists over who keeps most of the money — and the phone-number registries — that these promotions generate. Spread over several tours, the dollars could make a difference. Perry Farrell, the former Jane’s Addiction singer who was a founder of Lollapalooza, said he had heard the complaint that armies of phone-toting fans are spoiling live performances. But he said musicians who gripe about that were missing the point. “The cellphone is here,” he said. “You can choose to ignore it, you can grump at it, or you can say, ‘How can I take this amazing invention, how can I apply this and make my festival, and my life, more exciting?’ ” http://www.nytimes.com/2007/08/15/ar...ic/15conc.html Or I could turn it off and just enjoy the moment – Jack.  700MHz Auction: What's Really up for Grabs, and Why it Won't be Monopolized Nate Anderson Last week, the FCC released several hundred pages of rules for the upcoming 700 MHz spectrum auction, and they're already stirring up a bit of controversy. The Wall Street Journal ran a piece today on the fact that the rules will not prohibit a single buyer from snapping up the two national sections of the spectrum. Even though such a move is unlikely (it would be expensive, and the two bands have very different build-out requirements), the article shows the continuing fascination that people have with the auction; even rules it doesn't have can make news. Let's dig in a little deeper and get a handle on what's actually for sale. Readers who have been following the story for some time are probably aware that the FCC imposed certain open access conditions on one chunk of available spectrum, and it made another prime chunk only available to bidders willing to be involved with a public/private public safety network. Although these two chunks of spectrum have secured the most press, three other pieces of bandwidth will also be available in more than 1,000 regional licenses. How does all of this fit together? The FCC has produced a helfpul map of the available spectrum, which runs from 698-806MHz. In the image above, the yellow sections have already been auctioned off, and the gray sections are reserved for the nationwide public safety broadband network that will be constructed over the next few years. The remaining (white) A,B,C,D, and E blocks are what will be offered at auction later this year. The big action is in the C and D blocks. C covers two 11MHz chunks of spectrum that can be bid on together, making 22MHz available for national commercial use. This is the prime spectrum that Verizon and others would like to get their hands on, and it's also the bit that Google expressed interest in buying. Anyone who pays for the licenses to this block will need to abide by the two open access conditions (open devices and open applications) laid down by the FCC. The D block offers two 5MHz sections for a total of 10MHz, and it will be available nationwide. Whoever picks up this section, though, must do so as part of the Public Safety/Private Partnership established by the FCC. This means that the license holder will have to build out a nationwide wireless network that is good enough to meet public safety specifications for coverage and redundancy. The licensee will get the two (gray) public safety portions of the spectrum and will have the (white) 10MHz part to operate as a commercial network. Commercial traffic can also be carried over the public safety portion of the network so long as it is not being utilized. The A, B, and E blocks make up 30MHz in total, but the licenses for these blocks will cover only small geographic areas. The idea is to make wireless spectrum available to regional or rural wireless operators that could not otherwise afford to bid on the national spectrum. These local licenses will come with build-out requirements. Wireless operators will need to cover at least 35 percent of the territory covered by their license within four years, and a full 70 percent of the territory within 10 years. The 22MHz C block also comes with requirements: 40 percent coverage within four years, 75 percent coverage within 10. The FCC will automatically reclaimed "unserved portions of the license area" from companies that do not meet the build-out requirements. Monopolization unlikely The upshot of all of this should be clear: it's rather unlikely that any single player will swoop in and attempt to buy all of the available spectrum. The build-out requirements for each block varies significantly, meaning that were one company to try and buy the entire spectrum, it would find itself knee-deep in requirements relating to public safety and coverage quotas. There will certainly be hot competition for the C block, with its 22MHz of spectrum that could be used for national, high-speed wireless service. The D block is a little more dicey, although two new consortia (Frontline Wireless and Cyren Call) have expressed interest in running the public safety network and then reselling commercial access to other companies. It's not at all clear that big telcos have an interest in getting involved in this, especially since the D block will be subject to the most stringent build-out requirements. One telco grabbing both C and D would also be quite expensive, and companies that win a license still need a ton of cash in order to build the actual networks. As even the WSJ piece pointed out, this sort of consolidation is quite unlikely. But the telcos will certainly try to grab the 22MHz C block, both to augment their own wireless offerings but also to block companies like Google from getting a national spectrum footprint of its own. http://arstechnica.com/news.ars/post...nopolized.html  Sprint Earmarks $5B For WiMax Network Through 2010 Sinead Carew Sprint Nextel. said Thursday it could spend as much as $5 billion by the end of 2010 on a new network based on the emerging high-speed wireless technology known as WiMax. The No. 3 U.S. wireless service said it expects spending on the network through the end of 2008 to be at the low end of its previously announced estimates due to its agreement to connect its network with Clearwire, a small wireless service provider. WiMax is a wireless technology that Sprint wants to use to blanket entire cities, enabling wireless Internet access on everything from cell phones and laptops to video game players and cameras. The technology is expected to support Internet access at speeds up to five times faster than typical wireless networks, though it is still slower than wired broadband such as DSL. Some investors are concerned that Sprint is betting on a largely unproven technology. But Sprint Chief Executive Gary Forsee said the company would benefit by having an advanced network ahead of its rivals. "We in fact will have a mobile broadband network at least two years ahead of other providers that will be out there," Forsee said at a company conference in Virginia, where Sprint is showcasing the technology. Sprint's shares fell 1.8 percent to $18.30 on the New York Stock Exchange. Clearwire slipped 2.6 percent to $22.90. Sprint said it expects to spend $2.5 billion on the network through the end of 2008 compared with its earlier estimate of $2.5 billion to $3 billion. Sprint expects to reach a potential 100 million customers in that time, with the company providing coverage to 70 million people and Clearwire covering 30 million people. Sprint, which will market the new service under the Xohm brand (pronounced "zoam"), said it expects coverage to expand to 125 million people by 2010 at an additional cost of $2.5 billion, bringing the total network spend to $5 billion. But that expansion will depend on the success of the service, Sprint said. Sprint expects its WiMax network to generate positive free cash flow beginning in 2011. Free cash flow refers to operating income excluding depreciation and amortization, but including capital expenses, working capital and other cash requirements. It also expects between $2 billion and $2.5 billion in revenue from WiMax in its fiscal year 2010. Last month Sprint said it would cut the initial costs for building the network through its partnership with Clearwire. The two companies plan to connect their services and allow customers to move between their networks. Sprint also has an agreement to feature Google's Web search services via a portal tailored to WiMax devices. Barry West, president of Sprint's high speed wireless unit, said in a presentation that the company has commitments from device makers to embed 50 million units in the United States with WiMax connections over the next three years. Sprint has previously announced the top three mobile phone makers as technology partners for its plan to start offering services based on WiMax next year. These are Nokia, Samsung Electronics and Motorola. http://www.crn.com/networking/201800563  Skype Restores Service A Skype outage appears to be over nearly 14 hours after a log-in problem shut out many users. Sumner Lemon A log-in problem that shut many users out of Skype Ltd.'s popular VoIP service for nearly 14 hours appears to be over, but the company said more work remains to be done. At 3:53 a.m. GMT, Skype seemed to be operating normally, with users in Asia able to log in, view their contact lists, place calls, and send messages. However, there was no official confirmation on Skype's Heartbeat blog that the glitch responsible for the log-in problem had been resolved. "We're fixing issues in our networking software and monitoring the clients getting online with increased success," the company said in a blog post at 4:00 a.m. GMT. News of the Skype outage first came at around 2:00 p.m. GMT on Thursday, when the company announced that a "software issue" was preventing users from logging into the VoIP (voice over Internet Protocol) service and said the problem was expected to be fixed within 12 to 24 hours. Eight hours later, the company's engineers were still working on the problem. "The Skype system has not crashed or been victim of a cyber attack," the company said in a post published at 10 p.m. GMT on Thursday. Skype said the problem was the result of a "deficiency in an algorithm within Skype networking software." The problem was related to the interaction between a Skype client and the rest of Skype's peer-to-peer network, it said. At 2:15 a.m. GMT on Friday -- 12 hours after the log-in problem emerged -- Skype had still not fixed the problem, but said progress was being made. "We feel that we are on the right track to bring back services to normal," the company said in a post. Shortly after that notice was published, some Asian users reported being able to once again log in to Skype. http://www.pcworld.com/article/id,13...g/article.html  Company Says FCC Blocking Free Broadband Ed Oswald A company that is aiming to bring free broadband to the entire US is being blocked by the Federal Communications Commission, its CEO claimed Wednesday. M2Z Networks now plans to take the FCC to court over the rejection, apparently claiming the agency has not given the idea a fair study to determine its viability. M2Z's plans call for vacant radio spectrum to be used to provide high-speed Internet service to 95 percent of Americans within 10 years. The company will ask the U.S. Court of Appeals for the DC Circuit to order the FCC to make a "public interest determination" of M2Z's proposal, which has been with the agency for over a year. The company claims that regulations required the FCC to respond by May 5. "We strongly believe that the FCC should fully and fairly review the detailed record associated with M2Z's license application and its forbearance petition and make a decision consistent with the law Congress enacted," M2Z regulatory chief Uzoma Onyeije. The law to which Onyeije refers is Section 7 of the Communications Act. This states that the FCC must, within one year of receiving a petition or application regarding it, determine whether a new technology or service is in the public's interest. Comments on the petition have largely been in favor of M2Z's plans, although it has been rumored that the FCC was in the process of preparing to deny the company's petition. The agency could have solid reasoning in its denial. Regulations currently require the FCC to sell any spectrum at auction, whereas the M2Z petition essentially asks the agency to hand it over at no cost. In exchange, five percent of revenues would be handed over to the US Treasury. Also opposed to the plan are traditional telecommunications companies, who likely see the M2Z network as a serious threat to their hold on high-speed Internet services. While its basis would be free service, a premium option would also be made available which would cost about $20-30 per month. M2Z says this would generally be faster than current cable or DSL offerings. http://www.betanews.com/article/Comp...and/1187211965  First HSUPA Device Approved by FCC Scott M. Fulton It's not because "United States" begins with a later letter of the alphabet, that it lags behind most other countries on the list of those testing and approving global communications standards. By the end of this year, the UK will have two major carriers -- Vodafone Wireless and T-Mobile -- serving broadband customers with new HSUPA capacities, with at least two other carriers set to follow after the start of 2008, according to reports there. That's not a typo: The "U" in HSUPA refers to uplink capacity. Germany may be leading the world in adoption of so-called "super-3G" technology, with theoretical data uplink rates of 5.76 Mbps, compared to EDGE's phone modem-like speed of 118.4 Kbps. Nokia tried early on to get HSUPA going in the US over two years ago, ironically by leveraging interest in the technology in South America to get a rollout started in North America. Now at long last, a Belgian company called Option N.V. announced this morning it has received US Federal Communications Commission approval for an actual HSUPA device: a wireless broadband card for notebooks called the GlobeTrotter Express. Its premise: US travelers need access to high speed communications in those countries that offer it. In the meantime, it has to comply with US regulations, even if it's being used in an area where HSUPA isn't deployed yet. But if more and more users happen to have invested in such a device for such a reason, it could be the catalyst that at last gets a North American rollout going. Option N.V. isn't overstating its case. While its peak HSDPA download speed is stated to be 7.2 Mbps, it's conservatively estimating upload speeds at 2 Mbps, with fallback rates at 384 Kbps for downward compatibility. Still, that's miles ahead of current wireless capability and even most wired broadband capacity in this country. It could be the first bright spot in several months for Qualcomm, which produces the Mobile Station Modem MSM7200 chipset used in the Option N.V. device. Qualcomm began sampling this chipset as far back as April of last year, billing it as being compatible with 1xEV-DO parts. Not even the GlobeTrotter Express is an experimental technology any more: Vodafone actually started selling it to German customers last month. It's a safe bet that its US counterpart, Verizon Wireless, may be the first to offer it to its US customers, hopefully before the "5G" era begins overseas. http://www.betanews.com/article/prin...FCC/1187134681  Off to Resorts, and Carrying Their Careers John Leland STEAMBOAT SPRINGS, Colo. — Time was you could tell the urban refugees in places like this: corporate achievers who quit the rat race to open a bed and breakfast or a candle shoppe. Jim Moylan represents a new tribe in this bucolic mountain town, named for its loud sulfur spring. Mr. Moylan, 59, is a lawyer who specializes in securities and commodities work. When he moved from Chicago in 2003, he did not downscale his career for the small town, keeping his secretary and associates in Chicago and his clients around the country. He conducts his practice by fax and e-mail, just as he did in Chicago. In Steamboat Springs, Mr. Moylan dug into local affairs, joining three city committees, the Rotary Club, his church finance council and the editorial board of the daily newspaper. “I just wanted to get involved in the community,“ Mr. Moylan said, sitting in a bookstore/wine bar off the town’s main street. As technology enables people to live and work wherever they want, increasingly they are clustering in resort playgrounds like Steamboat Springs (pop. 9,315) that have natural amenities, good weather — and, now, lots of people like themselves. In places like Nantucket, the Upper Peninsula of Michigan and Teton County, Idaho, the migrants are creating hybrid communities, implanting urban incomes, tastes, careers, ambitions, restaurants, cultural activities and networking opportunities into small towns that until recently could support none of these, and for which there has been little planning and still no consensus. “You are seeing a transformation of rural communities,” said Jonathan Schechter, executive director of the Charture Institute in Jackson, Wyo., a nonprofit organization that studies small recreational towns. Into quiet resort spots the migrants have come, laptops on their knees: fund managers from New York, software developers from California, consultants, proofreaders, engineers, inventors. “The same processes that led to the suburbanization of the United States after World War II,” Mr. Schechter said, “are now producing a virtual suburbanization in places like Jackson or Steamboat Springs.” From 2000 to 2006, population in the 297 counties rated highest in natural amenities by the United States Department of Agriculture grew by 7.1 percent, 10 times the rate for the 1,090 rural counties with below-average amenities, the department reported. In towns that once emptied after the ski season or the beach season, these “location-neutral” migrants are complicating the traditional dynamic between tourists and locals. Here as elsewhere, average homes have become unaffordable for teachers, firefighters and others — the people who created the good schools and community closeness that newcomers said drew them. The rate of change “is causing a whiplash,” Mr. Schechter said, “because the towns don’t have the political and economic systems in place to deal with them.” Routt County, which includes Steamboat Springs, is one of the first places to identify these new émigrés as a source of economic growth and, paradoxically, community stability. A 2005 survey found that as many as 1 in 10 year-round households was involved in a location-neutral business. Unlike retirees and second-home buyers, who are also roosting in vacation towns, they send children to the local schools. “Without kids, you don’t have a community,” said Scott Ford, a counselor at the Small Business Resource Center at Colorado Mountain College. Cloistered in home offices, isolated from the local economy, location-neutrals are often invisible even to one another, except when they appear on local committees. Many work as hard as their urban counterparts, often juggling commitments in several time zones, but can step from their offices to a hiking trail or mountain stream. In Steamboat Springs, a pawn shop and loan store amid the expensive restaurants on the main drag illustrates the growing inequality in a region that produces few middle-income jobs. Each day 1,500 workers commute to Routt County from neighboring Moffat County, an hour away. Meanwhile, the airport, once filled with tourists, caters to people in business suits. “You’ve seen changes in politics,” said Carl Steidtmann, the chief economist for Deloitte Research, who moved from Brooklyn two years ago. “The county tipped Democratic in the last election. You see the tension in the City Council. It went from being pro-business-and-development to more conservationist.” He added, “Twelve years ago, not everyone you met had a Ph.D. or was from New York. There are still a lot of locals here, but that aspect is changing.” Peter Parsons, 45, who runs a microchip design company in Boulder, Colo., a city of 92,000 about three hours away, moved here five years ago to raise his three children in a small-town environment, keeping the company in Boulder. “It’s a real town,” Mr. Parsons said of the appeal of Steamboat Springs. “If your kids are running around, adults will see them and call you.” He has kept a Boulder telephone number and does little to remind clients he is not in the city. “I wouldn’t have been able to come here with my family if it meant opening a coffee shop,” he said. To combat isolation, he volunteered at the school and at church, and briefly moved from his home office into a town-run business incubator “in order to meet people,” he said. Now his office overlooks the ski slopes and is a short walk from a fly-fishing spot; computers vie for desk space with hand-tied flies. He still has to persuade associates that he has not slowed down or retired. “We have big discussions about what it means to be a local,” Mr. Parsons said of his fellow location-neutrals. “Some people snub anybody who hasn’t been here a long time. And some people think they know everything when they haven’t been here long.” The Routt County Economic Development Cooperative has embraced the new tribe as an asset, especially to an area with no strong industry other than tourism. Location-neutrals tend to volunteer heavily in civic organizations and local government. County interviews with 61 location-neutral businesses found they held 120 volunteer positions. But their enthusiasm has not always rubbed long-timers the right way, Mr. Ford said. “If they haven’t bonded with the community,” he said, “they begin with the ‘You people’ speeches: ‘What you people don’t understand is...’ When they start that, it’s almost impossible.” Sometimes disputes spill out in the local newspaper or its blogs, where old-timers and newcomers point fingers. Thomas Miller-Freutel, a partner in a directory-assistance startup, knows this chasm firsthand. Though he has lived here since 1990, first as owner of the Steamboat Inn, he sometimes struggles to balance his fast-paced work life with the small-town community. “I have to switch gears from what I was doing in other parts of the world to sit down and be productive as a community member,” he said. “You have to be careful not to say, ‘Look, I deal with people all over the world and this is how it’s done.’ You have to change gears in a small town.” For Bill and Stephanie Faunce, who run a marketing company for cable operators, small-town life often means starting work at 7 a.m. and quitting at 11 p.m., but with breaks to hike, ski or be with their two young children. Their goal in coming here was not to slow down but to eliminate urban distractions and pressures. “There are no stressors here,” said Mr. Faunce, 43. “In L.A., it took 90 minutes to get to the office, so we had a Mercedes and a Land Rover. Now we drive a Suburban. In three years we’ve put 15,000 miles on it.” http://www.nytimes.com/2007/08/13/us/13steamboat.html  Inside The Box Dan Mitchell A friend once advised Michael Kanellos of CNET News.com: “If you fall asleep in a meeting and wake up not knowing what’s going on, just say, ‘So where’s the value add?’ at the first pregnant pause.” Mr. Kanellos tried it, and it worked. Smarts and hard work are fine, he notes, “but sometimes the best solution is to be a pleasing, predictable suck-up.” Employing clichés is the easiest route. He ticks off several “choice inanities,” including “Be like Google” and “Just think what Apple could do with that.” http://www.nytimes.com/2007/08/18/bu.../18online.html  Security Gag Orders Unconstitutional: ACLU Edith Honan A U.S. law that requires people who are formally contacted by the FBI for information to keep it a secret is unconstitutional, a top civil liberties group told a Manhattan federal court on Wednesday. An FBI letter requesting information -- called a National Security Letter (NSL) -- is effectively a gag order because it tells the recipient the request must remain a secret, even though it needs no authorization by a judge, said Jameel Jaffer, an American Civil Liberties Union lawyer. Recipients have the right to challenge the secrecy order in court under a 2006 congressional amendment to the NSL law. But the law says that judges must defer to the FBI's view that secrecy is necessary, undermining the judiciary's check on the power of the executive branch, Jaffer said. Government lawyers argued before U.S. District Judge Victor Marrero that the FBI's need to ensure that targets are unaware of a probe outweighs the free speech rights of NSL recipients. The ACLU is fighting the government on behalf of an Internet access company that received an NSL. The company filed suit in April 2004. In September 2004 Marrero found the NSL gag violated constitutional free speech rights and struck it down as unconstitutional. The government appealed the ruling, but Congress amended the NSL provision in its reauthorization of the Patriot Act last year before an appeals court could hear the case. The revised NSL provision -- allowing the gag to be challenged in court -- has been sent back to Marrero. The FBI dropped the demand on the Internet company a year ago, but the gag remains in place. The ACLU said the Internet company was prevented from participating in the public debate surrounding the Patriot Act's reauthorization, even though it had "firsthand knowledge of this sweeping FBI power." "Excessive secrecy invites abuse and we have seen this played out on a massive scale," Jaffer told Marrero. The ACLU says that between 2003 and 2005 more that 143,000 NSLs were issued. In June the FBI said it had possibly violated the law or its rules more than 1,000 times since 2002 in collecting data with the NSL about phone calls, e-mails and financial records while investigating terrorism or espionage suspects. http://www.reuters.com/article/polit...29237120070816  Bush Administration Says Warrantless Eavesdropping Cannot Be Questioned David Kravets The Bush administration said Monday the constitutionality of its warrantless electronic eavesdropping program cannot be challenged. The government is taking that position in seeking the dismissal of federal court lawsuits against the government and AT&T over its alleged involvement in the once-secret surveillance program adopted after the Sept. 11 terror attacks. The strategy was first recognized by the U.S. Supreme Court in a McCarthy-era lawsuit. It has been increasingly invoked in a bid to shield the government from legal scrutiny. Two senior Justice Department officials, speaking on condition of anonymity in a teleconference with reporters, reiterated the administration's position that it was invoking the so-called "state secrets privilege" in arguing that the 9th U.S. Circuit Court of Appeals must dismiss the cases because they threaten to expose information authorities say is essential to the nation's security. "The case cannot be litigated in light of the national security interest involved," one official said. The officials spoke on the condition that their names would not be published because, they said, it was the government's protocol not to comment on pending litigation. The Bush administration has invoked the state secrets defense often, from spy cases and patent disputes to employment discrimination litigation. Still, two judges have ruled recently that the defense does not apply in two lawsuits challenging Bush's surveillance program. President Bush acknowledged in 2005 that the government was eavesdropping without warrants on communications in the United States as long as one of the parties to the communication was suspected of terrorism and outside the United States. On Wednesday, the government will urge the San Francisco-based appeals court to dismiss the case on grounds that the case could expose state secrets, the justice department officials said. "In our view, those claims should always be dismissed," a senior administration official said. "A year from now, a director of national intelligence, looking at all of the same information, may not make the same determination." The official added: "These are legal principals not simply being made up by the executive." The officials also said that the lawsuits should also be tossed because the plaintiffs have no direct proof they were spied on. "We cannot confirm or deny whether or not that's true," one of the officials said. Earlier this month, Congress sanctioned warrantless eavesdropping with new legislation, which is also under attack on allegations such electronic surveillance violates the Fourth Amendment's warrant requirements. The new law requires that at least one of the parties to the communication be outside of the United States and associated with terrorism. http://blog.wired.com/27bstroke6/200...dminist-1.html  Bush does it and I will too Zimbabwe President Mugabe Signs State Eavesdropping Law Blessing Zulu Zimbabwean President Robert Mugabe on Friday signed into law the controversial Interception of Communications Bill, which gives his government the authority to eavesdrop on phone and Internet communications and read physical mail. The legislation has drawn outspoken opposition from the political opposition and civil society organizations as trampling on the civil rights of Zimbabweans. Spokesman Nelson Chamisa of the opposition Movement for Democratic Change faction of Morgan Tsvangirai called it an addition to "the dictator's tool kit." Chief Secretary to the President and Cabinet Misheck Sibanda was quoted in the Government Gazette Friday as saying Mr. Mugabe has signed the bill. Secretary General Welshman Ncube of the MDC faction led by Arthur Mutambara called it a "final straw to the curtailment to the liberties of Zimbabweans." Human rights lawyer Otto Saki told VOA that the law interferes and undermines the enjoyment of rights enshrined in the constitution and is a sign Mr. Mugabe wants to consolidate his power by "any means necessary or unnecessary." But Communications Minister Christopher Mushowe said Zimbabwe is not unique in the world in passing such legislation, citing electronic eavesdropping programs in the United States, the United Kingdom and South Africa, among other countries. Under the law an interception of communication monitoring center will be set up. But Internet and other communications service providers will be required to ensure that their systems are technically capable of supporting lawful interception at all times. Those authorized to make applications for the interception of communications include the chief of defense intelligence, the director general of the president's department of national security, the commissioner of the Zimbabwe Republic Police and the commissioner general of the Zimbabwe Revenue Authority. http://www.voanews.com/english/Afric...8-03-voa58.cfm  U.S. to Broaden Spy Satellite Access UPI U.S. border patrol and law enforcement agencies will soon have access to once-classified spy satellite imagery, The Wall Street Journal reported Wednesday. The move was authorized in a May 25 memo sent to U.S. Homeland Security Secretary Michael Chertoff by Director of National Intelligence Michael McConnell, the newspaper said. Access to the surveillance will be controlled by the National Applications Office, a new Homeland Security branch that will be functioning in October, officials said. Previously, only non-intelligence agencies such as the National Aeronautics and Space Administration and the U.S. Geological Survey could request images on a case-by-case scenario, each of which had to be approved by the president. Charles Allen, the Department of Homeland Security's chief intelligence officer, told the Journal that he was aware of civil liberties concerns but also said there were misconceptions about the technology. "We have to get this right because we don't want civil-rights and civil-liberties advocates to have concerns that this is being misused in ways which were not intended," Allen told the Journal. "Contrary to what some people believe you cannot see if somebody needs a haircut from space." http://www.upi.com/NewsTrack/Top_New...e_access/9331/  U.S. Defends Surveillance to 3 Skeptical Judges Adam Liptak Three federal appeals court judges hearing challenges to the National Security Agency’s surveillance programs appeared skeptical of and sometimes hostile to the Bush administration’s central argument Wednesday: that national security concerns require that the lawsuits be dismissed. “Is it the government’s position that when our country is engaged in a war that the power of the executive when it comes to wiretapping is unchecked?” Judge Harry Pregerson asked a government lawyer. His tone was one of incredulity and frustration. Gregory G. Garre, a deputy solicitor general representing the administration, replied that the courts had a role, though a limited one, in assessing the government’s assertion of the so-called state secrets privilege, which can require the dismissal of suits that could endanger national security. Judges, he said, must give executive branch determinations “utmost deference.” “Litigating this action could result in exceptionally grave harm to the national security of the United States,” Mr. Garre said, referring to the assessment of intelligence officials. The three judges, members of the United States Court of Appeals for the Ninth Circuit, were hearing arguments in two lawsuits challenging the highly classified surveillance programs, which the administration says are essential in fighting international terrorism. The appeals were the first to reach the court after dozens of suits against the government and telecommunications companies over N.S.A. surveillance were consolidated last year before the chief judge of the federal trial court here, Vaughn R. Walker. The appeals concern two related questions that must be answered before the merits of the challenges can be considered: whether the plaintiffs can clearly establish that they have been injured by the programs, giving them standing to sue; and whether the state secrets privilege requires dismissal of the suits on national security grounds. Though the questions are preliminary, the impact of the appeals court’s ruling may be quite broad. Should it rule for the government on either ground, the legality of the N.S.A. programs may never be adjudicated. All three judges indicated that they were inclined to allow one or both cases to go forward for at least limited additional proceedings before Judge Walker. The two cases deal with different secret programs, but are broadly similar. One, a class action against AT&T, focuses mainly on accusations that the company provided the N.S.A. its customers’ phone and Internet communications for a vast data-mining operation. The lawyers in the AT&T case call that program, which the government has not acknowledged, a “content dragnet.” The second case, brought by an Islamic charity and two of its lawyers against the government, concerns a program disclosed by The New York Times in December 2005, which the administration calls the Terrorist Surveillance Program. The program, which has since been submitted to a secret court’s supervision, bypassed court warrants in monitoring international communications involving people in the United States. Last month another federal appeals court, in Cincinnati, dismissed a suit brought in Detroit by the American Civil Liberties Union, saying the plaintiffs there, including lawyers and journalists, could not prove they had been injured by this latter program. Lawyers in the two cases that were argued Wednesday say they have such proof. In the AT&T case, the plaintiffs submitted a sworn statement from a former technician for the company who disclosed technical documents about the installation of monitoring equipment at an AT&T Internet switching center in San Francisco. Mr. Garre, representing the administration, and Michael K. Kellogg, a lawyer for AT&T, said the sworn statement was built on speculation and inferences. Robert D. Fram, a lawyer for the plaintiffs, said the statement provided more than enough direct evidence to allow the case to go forward. Similarly, in the case brought by the charity, al-Haramain Islamic Foundation, the plaintiffs say the government mistakenly provided them a document, since reclaimed, that proves they were subject to surveillance without court approval. On Wednesday, Thomas M. Bondy, a Justice Department lawyer, told the court that the document “to this day remains totally classified.” In both cases, the government said the plaintiffs’ evidence was insufficient to establish standing to sue, adding that even litigating the matter would endanger national security. “Whether plaintiffs were subjected to surveillance is a state secret,” the Justice Department said in a recent brief in the Haramain case, “and information tending to confirm or deny that fact is privileged.” One of the judges on the panel, M. Margaret McKeown, seemed to endorse a lower court finding that the wiretap program was no longer secret. “We know quite a lot” about the Terrorist Surveillance Program, said Judge McKeown, who, like the third judge on the panel, Michael Daly Hawkins, was appointed by President Bill Clinton. Judge Pregerson, appointed by President Jimmy Carter, appeared irritated with the government’s arguments, and he became frustrated when Mr. Garre said he could not provide simple answers to questions about the scope of a recently amended 1978 law, the Foreign Intelligence Surveillance Act. Mr. Garre said it was a complicated law. “Can’t be any more complicated than my phone bill,” Judge Pregerson said. http://www.nytimes.com/2007/08/16/washington/16nsa.html  In Unprecedented Order, FISA Court Requires Bush Administration to Respond to ACLU's Request That Secret Court Orders Be Released to the Public Press Release In an unprecedented order, the Foreign Intelligence Surveillance Court (FISC) has required the U.S. government to respond to a request it received last week by the American Civil Liberties Union for orders and legal papers discussing the scope of the government's authority to engage in the secret wiretapping of Americans. According to the FISC's order, the ACLU's request "warrants further briefing," and the government must respond to it by August 31. The court has said that any reply by the ACLU must be filed by September 14. "Disclosure of these court orders and legal papers is essential to the ongoing debate about government surveillance," said Anthony D. Romero, Executive Director of the ACLU. "We desperately need greater transparency and public scrutiny.We're extremely encouraged by today's development because it means that, at long last, the government will be required to defend its contention that the orders should not be released." The ACLU filed the request with the FISC following Congress' recent passage of the so-called "Protect America Act," a law that vastly expands the Bush administration's authority to conduct warrantless wiretapping of Americans' international phone calls and e-mails. In their aggressive push to justify passing this ill-advised legislation, the administration and members of Congress made repeated and veiled references to orders issued by the FISC earlier this year. The legislation is set to expire in six months unless it is renewed. "These court orders relate to the circumstances in which the government should be permitted to use its profoundly intrusive surveillance powers to intercept the communications of U.S. citizens and residents," said Jameel Jaffer, Director of the ACLU's National Security Project. "The debate about this issue should not take place in a vacuum.It's imperative that the public have access to basic information about what the administration has proposed and what the intelligence court has authorized." FISC orders have played a critical role in the evolution of the government's surveillance activities over the past six years. After September 11, President Bush authorized the National Security Agency (NSA) to inaugurate a program of warrantless wiretapping inside the United States. In January 2007, however, just days before an appeals court was to hear the government's appeal from a judicial ruling that had found the NSA program to be illegal in a case brought by the ACLU, Attorney General Gonzales announced that the NSA program would be discontinued. Gonzales explained that the change was made possible by FISC orders issued on January 10, 2007, which he characterized as "complex" and "innovative." Those orders are among the documents requested by the ACLU. Since January 2007, government officials have spoken publicly about the January 10 orders in congressional testimony, to the media and in legal papers - the orders remaining secret all the while. They have also indicated that the FISC issued other orders in the spring that restricted the administration's surveillance activities. House Minority Leader John Boehner stated that the FISC had issued a ruling prohibiting intelligence agents from intercepting foreign-to-foreign calls passing through the United States. To a large extent, it was the perception that the FISC had issued an order limiting the administration's surveillance authority that led Congress to pass the new legislation expanding the government's surveillance powers. Yet the order itself, like the January 2007 order, has remained secret. The ACLU's request to the FISC acknowledges that the FISC's docket includes a significant amount of material that is properly classified. The ACLU argues, however, that the release of court orders and opinions would not raise any security concern to the extent that these records address purely legal issues about the scope of the government's wiretap authority, and points out that the FISC has released such orders and opinions before. The ACLU is seeking release of all information in those judicial orders and legal papers the court determines, after independent review, to be unclassified or improperly classified. A copy of the FISA court order, the ACLU's motion to the FISC, as well as information about the ACLU's lawsuit against the NSA and other related materials are available online at: www.aclu.org/spying In addition to Jaffer, lawyers on the case are Steven R. Shapiro, Melissa Goodman, and Alexa Kolbi-Molinas of the ACLU and Art Spitzer of the ACLU of the National Capital Area. http://www.aclu.org/safefree/spying/...s20070817.html  Your papers please! Federal ID Plan Raises Privacy Concerns Eliott C. McLaughlin Americans may need passports to board domestic flights or to picnic in a national park next year if they live in one of the states defying the federal Real ID Act. The act, signed in 2005 as part of an emergency military spending and tsunami relief bill, aims to weave driver's licenses and state ID cards into a sort of national identification system by May 2008. The law sets baseline criteria for how driver's licenses will be issued and what information they must contain. The Department of Homeland Security insists Real ID is an essential weapon in the war on terror, but privacy and civil liberties watchdogs are calling the initiative an overly intrusive measure that smacks of Big Brother. More than half the nation's state legislatures have passed symbolic legislation denouncing the plan, and some have penned bills expressly forbidding compliance. Several states have begun making arrangements for the new requirements -- four have passed legislation applauding the measure -- but even they may have trouble meeting the act's deadline. The cards would be mandatory for all "federal purposes," which include boarding an airplane or walking into a federal building, nuclear facility or national park, Homeland Security Secretary Michael Chertoff told the National Conference of State Legislatures last week. Citizens in states that don't comply with the new rules will have to use passports for federal purposes. "For terrorists, travel documents are like weapons," Chertoff said. "We do have a right and an obligation to see that those licenses reflect the identity of the person who's presenting it." Chertoff said the Real ID program is essential to national security because there are presently 8,000 types of identification accepted to enter the United States. "It is simply unreasonable to expect our border inspectors to be able to detect forgeries on documents that range from baptismal certificates from small towns in Texas to cards that purport to reflect citizenship privileges in a province somewhere in Canada," he said. Chertoff attended the conference in Boston, Massachusetts, in part to allay states' concerns, but he had few concrete answers on funding. The Department of Homeland Security, which estimates state and federal costs could reach $23.1 billion over 10 years, is looking for ways to lessen the burden on states, he said. On the recent congressional front, however, Chertoff could point only to an amendment killed in the Senate last month that would've provided $300 million for the program. "There's going to be an irreducible expense that falls on you, and that's part of the shared responsibility," Chertoff told the state legislators. Bill Walsh, senior legal fellow for the Heritage Foundation, a Washington-based conservative think tank that supports the Real ID Act, said states shouldn't be pushing for more federal dollars because, ultimately, that will mean more federal oversight -- and many complaints about cost coincide with complaints about the federal government overstepping its bounds. "They are only being asked to do what they should've already done to protect their citizens," Walsh said, blaming arcane software and policies at state motor vehicle departments for what he called "a tremendous trafficking in state driver's licenses." The NCSL is calling Real ID an "unfunded mandate" that could cost states up to $14 billion over the next decade, but for which only $40 million has been federally approved. The group is demanding Congress pony up $1 billion for startup costs by year's end or scrap the proposal altogether. Everyone must visit DMV by 2013 The Real ID Act repealed a provision in the 9/11 Commission Implementation Act calling for state and federal officials to examine security standards for driver's licenses. It called instead for states to begin issuing new federal licenses, lasting no longer than eight years, by May 11, 2008, unless they are granted an extension. It also requires all 245 million license and state ID holders to visit their local departments of motor vehicles and apply for a Real ID by 2013. Applicants must bring a photo ID, birth certificate, proof of Social Security number and proof of residence, and states must maintain and protect massive databases housing the information. NCSL spokesman Bill Wyatt said the requirements are "almost physically impossible." States will have to build new facilities, secure those facilities and shell out for additional equipment and personnel. Those costs are going to fall back on the American taxpayer, he said. It might be in the form of a new transportation, motor vehicle or gasoline tax. Or you might find it tacked on to your next state tax bill. In Texas, Wyatt said, one official told him that without federal funding, the Longhorn State might have to charge its citizens more than $100 for a license. "We kind of feel like the way they went about this is backwards," Wyatt said, explaining that states would have appreciated more input into the process. "Each state has its own unique challenges and these are best addressed at state levels. A one-size-fits-all approach to driver's licenses doesn't necessarily work." Many states have revolted. The governors of Idaho, Maine, Montana, New Hampshire, Oklahoma, South Carolina and Washington have signed bills refusing to comply with the act. Six others have passed bills and/or resolutions expressing opposition, and 15 have similar legislation pending. Though the NCSL says most states' opposition stems from the lack of funding, some states cited other reasons for resisting the initiative. New Hampshire passed a House bill opposing the program and calling Real ID "contrary and repugnant" to the state and federal constitutions. A Colorado House resolution dismissed Real ID by expressing support for the war on terror but "not at the expense of essential civil rights and liberties of citizens of this country." Privacy concerns raised Colorado and New Hampshire lawmakers are not alone. Groups like the American Civil Liberties Union and Electronic Frontier Foundation say the IDs and supporting databases -- which Chertoff said would eventually be federally interconnected -- will infringe on privacy. EFF says on its Web site that the information in the databases will lay the groundwork for "a wide range of surveillance activities" by government and businesses that "will be able to easily read your private information" because of the bar code required on each card. The databases will provide a one-stop shop for identity thieves, adds the ACLU on its Web site, and the U.S. "surveillance society" and private sector will have access to the system "for the routine tracking, monitoring and regulation of individuals' movements and activities." The civil liberties watchdog dubs the IDs "internal passports" and claims it wouldn't be long before office buildings, gas stations, toll booths, subways and buses begin accessing the system. But Chertoff told legislators last week that DHS has no intention of creating a federal database, and Walsh, of the Heritage Foundation, said the ACLU's allegations are disingenuous. States will be permitted to share data only when validating someone's identity, Walsh said. "The federal government wouldn't have any greater access to driver's license information than it does today," Walsh said. States have the right to refuse to comply with the program, he said, and they also have the right to continue issuing IDs and driver's licenses that don't meet Real ID requirements. But, Walsh said, "any state that's refusing to implement this key recommendation by the 9/11 Commission, and whose state driver's licenses are as a result used in another terrorist attack, should be held responsible." State reaction to Real ID has not been all negative. Four states have passed bills or resolutions expressing approval for the program, and 13 states have similar legislation pending (Several states have pending pieces of legislation both applauding and opposing Real ID). Chertoff said there would be repercussions for states choosing not to comply. "This is not a mandate," Chertoff said. "A state doesn't have to do this, but if the state doesn't have -- at the end of the day, at the end of the deadline -- Real ID-compliant licenses then the state cannot expect that those licenses will be accepted for federal purposes." http://www.cnn.com/2007/POLITICS/08/....id/index.html  Patti Davis: At the Airport, You Better Smile ‘Behavior Detection Officers’ are now watching passengers’ facial expressions for signs of danger. It’s a new level of absurdity for America. Patti Davis It was bound to happen. Now even a frown or grimace can get you into trouble with The Man. “Specially trained security personnel” will be watching passengers for “micro-expressions” that will reveal treacherous agendas and insidious intentions at airports around the country. These agents, who may literally hold your fate in their hands have been given a lofty, Orwellian name: "Behavior Detection Officers." Did anyone ever doubt that George Orwell’s prophecies in “1984” would arrive? In that novel, he wrote, “You had to live—did live, from habit that became instinct—in the assumption that every sound you made was overheard and, except in darkness, every movement scrutinized.” In the study of “micro-expressions”—yes, it is actually a field of study and there are some who are arrogant enough to call it a science—it has been decided that when people wish to conceal emotions, the truth of their feelings is revealed in facial flashes. These experts have determined that fear and disgust are the key things to look for because they can hint of deception. Let’s see, fear and disgust in an airport? I’m frightened and disgusted weeks before I have to show up at an airport. In fact, I’ve pretty much sworn off the whole idea of going anywhere by airplane. It’s bad enough that I might be trapped in a crowded plane with no food or water and nonworking toilets for hours; now there are security agents interpreting our facial expressions. The face police, in place at more than a dozen U.S. airports already, aren’t identified as such. But the watcher could be at curbside baggage, the ticket counter or near the metal detectors and X-ray machines. The Transportation Security Administration hopes to have as many as 500 Behavior Detection Officers on the job by the end of 2008. But what about the woman who is getting on a plane to see a dying relative? Or the man who is traveling to another state to see a cancer specialist in a last bid for extending his life? What about the guy who just had a fight with his spouse and now worries that a plane crash would mean their last words were in anger? We’ve all had the experience of having a bad day, being in a rotten mood—especially at the airport, which has become a modern-day chamber or horrors. On those days, doesn’t it seem like everyone we meet looks sour and unpleasant? The opposite is also true. When we’re happy and joyful, we look at others and see happiness in them. Or even if we don’t, we look at them kindly and with compassion. It’s human nature to look at others through the lens of our own reality. Here’s where it gets really absurd. Apparently, these Behavior Detection Officers work in pairs. One scenario is that an officer might move in to “help” a passenger retrieve their belongings after they’ve been screened. And then the officer will ask where the passenger is headed. If the passenger’s reaction sets off alarm bells in the officer’s well-trained mind, another officer will move in and detain them. Let’s be really clear here. If a stranger moved in on me like that, I’d tell that person to go to hell, throw in a few other expletives for good measure and probably give them the finger as I stomped off. Of course, I wouldn’t be stomping very far. So while TSA employees are confiscating our scissors and water bottles, they’re going to secretly be staring at us, looking for some telltale sign of terrorist intent in a grimace, a sigh, a crinkled nose? Who knows what? In the end, the Behavior Detection Officers are the ones who are really acting suspicious. Which is the truth of the matter anyway. http://www.msnbc.msn.com/id/20298840...wsweek/page/0/  Concern Over Wider Spying Under New Law James Risen and Eric Lichtblau Broad new surveillance powers approved by Congress this month could allow the Bush administration to conduct spy operations that go well beyond wiretapping to include — without court approval — certain types of physical searches of American citizens and the collection of their business records, Democratic Congressional officials and other experts said. Administration officials acknowledged they had heard such concerns from Democrats in Congress recently, and that there was a continuing debate over the meaning of the legislative language. But they said the Democrats were simply raising theoretical questions based on a harsh interpretation of the legislation. They also emphasized that there would be strict rules in place to minimize the extent to which Americans would be caught up in the surveillance. The dispute illustrates how Democrats, in a frenetic, end-of-session scramble, passed legislation they may not have fully understood and may have given the administration more surveillance powers than it sought. It also offers a case study in how changing a few words in a complex piece of legislation has the potential to fundamentally alter the basic meaning of the Foreign Intelligence Surveillance Act, a landmark national security law. Two weeks after the legislation was signed into law, there is still heated debate over how much power Congress gave to the president. It is possible that some of the changes were the unintended consequences of the rushed legislative process just before this month’s Congressional recess, rather than a purposeful effort by the administration to enhance its ability to spy on Americans. “We did not cover ourselves in glory,” said one Democratic aide, referring to how the bill was compiled. Democratic leaders have said they plan to push for a revision of the legislation as soon as September. “It was a legislative over-reach, limited in time,” said one Congressional Democratic aide. “But Democrats feel like they can regroup.” Some civil rights advocates said they suspected that the administration made the language of the bill intentionally vague to allow it even broader discretion over wiretapping decisions. Whether intentional or not, the end result — according to top Democratic aides and other experts on national security law — is that the legislation may grant the government the right to collect a vast array of information on American citizens inside the United States without warrants, as long as the administration asserts that the spying concerns the monitoring of a person believed to be overseas. In effect, they say, the legislation significantly relaxes the restrictions on how the government can conduct spying operations aimed at foreigners while also sweeping up information about Americans. “This may give the administration even more authority than people thought,” said David Kris, a former senior Justice Department lawyer in the Bush administration and a co-author of “National Security Investigation and Prosecutions,” a new book on surveillance law. Several legal experts said that by redefining the meaning of “electronic surveillance,” the new law undercuts the legal underpinnings several provisions in the Foreign Intelligence Surveillance Act, known as FISA, indirectly giving the government the power to use intelligence collection methods far beyond wiretapping that previously required court approval if conducted inside the United States. These new powers include the collection of business records, physical searches, and so-called “trap and trace” operations, analyzing specific calling patterns. For instance, the legislation would allow the government, under certain circumstances, to search the business records of an American in Chicago without a warrant if it asserts that the search concerns its surveillance of a person who is in Paris, Democratic Congressional aides and other experts said. If the administration meets several specific conditions in the new legislation, Democratic Congressional aides and outside legal experts worry that the government could, for example, seize the computer or other communications-related property of an American in Los Angeles who may have been in contact with a person in Saudi Arabia — if the person in Saudi Arabia is the subject of the government’s interest. These new powers are considered overly broad and troubling by some Congressional Democrats who raised their concerns with administration officials in private meetings this week. “This shows why it is so risky to change the law by changing the definition” of something as basic as the meaning of electronic surveillance, said Suzanne Spaulding, a former Congressional staff member who is now a national security legal expert. “You end up with a broad range of consequences that you might not realize.” But a senior intelligence official who has been involved in the discussions on behalf of the administration said that the legislation was seen solely as a way to speed access to the communications of foreign targets, not to sweep up the communications of Americans by claiming to focus onforeigners “I don’t think it’s a fair reading,” the official said. “The intent here was pure: if you’re targeting someone outside the country, the fact that you’re doing the collection inside the country, that shouldn’t matter.” But the official acknowledged that Congressional staff members had raised concerns about the law in the meetings this week, and that ambiguities in the bill’s wording may have led to some confusion. “I’m sure there will be discussions about how and whether it should be fixed,” the official said. Vanee Vines, a spokeswoman for the office of the director of national intelligence, said the concerns raised by Congressional officials about the wide scope of the new legislation were “speculative.” But she declined to discuss specific aspects of how the legislation would be enacted. The legislation gives the director of national intelligence, Mike McConnell, and Attorney General Alberto R. Gonzales broad discretion in enacting the new procedures and approving the way surveillance is conducted. The new legislation amends FISA, but is set to expire in six months. Bush administration officials said the legislation was critical to fill an “intelligence gap” that had left the United States vulnerable to attack. The legislation “restores FISA to its original and appropriate focus — protecting the privacy of Americans,” said Brian Roehrkasse, Justice Department spokesman. “The act makes clear that we do not need a court order to target for foreign intelligence collection persons located outside the United States, but it also retains FISA’s fundamental requirement of court orders when the target is in the United States.” The measure, which President Bush signed into law on Aug. 5, was written and pushed through both the House and Senate so quickly that few in Congress had time to absorb its full impact, some Congressional aides say. Though many Democratic leaders opposed the final version of the legislation, they did not work forcefully to block its passage, largely out of fear that they would be criticized by President Bush and Republican leaders during the August recess as being soft on terrorism. Yet Bush administration officials have already signaled that, in their view, the president retains his constitutional authority to do whatever it takes to protect the country, regardless of any action Congress takes. At a tense meeting last week with lawyers from a range of private groups active in the wiretapping issue, senior Justice Department officials refused to commit the administration to adhering to the limits laid out in the new legislation and left open the possibility that the president could once again use what they have said in other instances is his constitutional authority to act outside the regulations set by Congress. At the meeting, Bruce Fein, a Justice Department lawyer in the Reagan administration, along with other critics of the legislation, pressed Justice Department officials repeatedly for an assurance that the administration considered itself bound by the restrictions imposed by Congress. The Justice Department, led by Ken Wainstein, the assistant attorney general for national security, refused to do so, according to three participants in the meeting. That stance angered Mr. Fein and others. It sent the message, Mr. Fein said in an interview, that the new legislation, though it is already broadly worded, “is just advisory. The president can still do whatever he wants to do. They have not changed their position that the president’s Article II powers trump any ability by Congress to regulate the collection of foreign intelligence.” Brian Walsh, a senior legal fellow at the conservative Heritage Foundation who attended the same private meeting with Justice Department officials, acknowledged that the meeting — intended by the administration to solicit recommendations on the wiretapping legislation — became quite heated at times. But he said he thought the administration’s stance on the president’s commander-in-chief powers was “a wise course.” “They were careful not to concede any authority that they believe they have under Article II,” Mr. Walsh said. “If they think they have the constitutional authority, it wouldn’t make sense to commit to not using it.” Asked whether the administration considered the new legislation legally binding, Ms. Vines, the national intelligence office spokeswoman, said: “We’re going to follow the law and carry it out as it’s been passed.” Mr. Bush issued a so-called signing statement about the legislation when he signed it into law, but the statement did not assert his presidential authority to override the legislative limits. At the Justice Department session, critics of the legislation also complained to administration officials about the diminished role of the FISA court, which is limited to determining whether the procedures set up by the executive administration for intercepting foreign intelligence are “clearly erroneous” or not. That limitation sets a high bar, argued Marc Rotenberg, executive director of the Electronic Privacy Information Center, who also attended the Justice Department meeting. “You’ve turned the court into a spectator,” Mr. Rotenberg said. http://www.nytimes.com/2007/08/19/wa...19fisa.html?hp  Feds Pay $80,000 Over Anti-Bush T-Shirts A couple arrested at a rally after refusing to cover T-shirts that bore anti-President Bush slogans settled their lawsuit against the federal government for $80,000, the American Civil Liberties Union announced Thursday. Nicole and Jeffery Rank of Corpus Christi, Texas, were handcuffed and removed from the July 4, 2004, rally at the state Capitol, where Bush gave a speech. A judge dismissed trespassing charges against them, and an order closing the case was filed Thursday in U.S. District Court in Charleston. "This settlement is a real victory not only for our clients but for the First Amendment," said Andrew Schneider, executive director of the ACLU of West Virginia. "As a result of the Ranks' courageous stand, public officials will think twice before they eject peaceful protesters from public events for exercising their right to dissent." White House spokesman Blair Jones said the settlement was not an admission of wrongdoing. "The parties understand that this settlement is a compromise of disputed claims to avoid the expenses and risks of litigation and is not an admission of fault, liability, or wrongful conduct," Jones said. The front of the Ranks' homemade T-shirts bore the international symbol for "no" superimposed over the word "Bush." The back of Nicole Rank's T-shirt said "Love America, Hate Bush." On the back of Jeffery Rank's T-shirt was the message "Regime Change Starts at Home." The ACLU said in a statement that a presidential advance manual makes it clear that the government tries to exclude dissenters from the president's appearances. "As a last resort," the manual says, "security should remove the demonstrators from the event." http://www.boston.com/news/nation/ar...bush_t_shirts/  CNET Reporters Sue HP for Invasion of Privacy Greg Sandoval The fallout from Hewlett-Packard's boardroom leak scandal continued Wednesday as three CNET News.com reporters sued the computer maker, alleging that its investigation tactics amounted to an invasion of privacy and a violation of state rules on business practices. Complaints were filed on behalf of reporters Dawn Kawamoto, Stephen Shankland and Tom Krazit in California Superior Court for the County of San Francisco. Kawamoto's husband, plus Shankland's wife and parents also filed their own suits Wednesday, according to court documents. All seek unspecified damages. "As we have said since last fall, HP regrets these events, and we have apologized individually to those who were affected," said Ryan Donovan, an HP spokesman. "In an attempt to resolve this matter short of litigation, HP made a substantial settlement offer to the reporters, their family members and a charity of their choice. Unfortunately, rather than respond to the offer, they have decided to sue. HP is disappointed by their decision and will defend itself." The suits come nearly a year after HP's investigation methods came under scrutiny from law enforcement officials and the federal government. The company acknowledged in September that several employees spied on the three News.com reporters, as well as on journalists from BusinessWeek, The New York Times, The Wall Street Journal and Associated Press. The covert operation was an attempt to expose a media leak from the company's board. The News.com reporters had previously indicated they were likely to file suit. "Defendants conspired to and intentionally intruded into the plaintiffs solitude and private affairs," the reporters alleged in their suit. They accused HP of obtaining information about "their private affairs without their knowledge or consent." Kawamoto and Krazit declined to comment, as did a spokeswoman for CNET Networks, the publisher of News.com. Shankland was unavailable. Asked to detail what kind of damages the plaintiffs were looking for, Kevin Boyle, their attorney, declined to discuss dollar amounts. "The value of the case is going to be worth whatever (the jury) thinks it's worth," Boyle said. "We think the biggest component is going to be punitive damages, which we hope will deter HP and other companies from ever doing this again." HP investigators are accused of obtaining confidential phone records belonging to the reporters and some of their family members by misleading phone company employees, a practice known as pretexting. In Kawamoto's case, HP investigators are accused of conducting surveillance of her movements. In addition to HP, the suits name Patricia Dunn, the company's former chairman, and Kevin Hunsaker, a former HP attorney, as defendants. Following HP's disclosure of its leak hunt, Dunn resigned and Hunsaker left the company. The three News.com reporters also accuse HP of intentionally inflicting emotional distress and of violating California's business code, specifically the state's prohibition against "unfair, fraudulent and deceptive" practices. In the wake of the scandal, HP settled civil charges with the California Attorney General, agreeing to pay $14.5 million. HP also settled with the Securities and Exchange Commission in May that involved no monetary penalties or admission of guilt by HP. Criminal charges were filed by the state of California against Dunn, Hunsaker and two others but they were later dismissed. CNET News.com's Ina Fried contributed to this report. http://news.com.com/CNET+reporters+s...3-6202836.html  U.S. Money for Traffic Is Short of Bloomberg’s Plan Anahad O’Connor and William Neuman The United States Department of Transportation announced today that it had allocated $354 million to reduce traffic in New York City, giving a boost to Mayor Michael R. Bloomberg’s plan but providing significantly less money than the mayor had sought as part of his sweeping proposal. The federal funds would primarily be used for bus purchases and other improvements in mass transit. The city had also applied for approximately $180 million to pay for the installation of a system that would impose a fee on cars entering the busiest parts of Manhattan. But the Department of Transportation, under the agreement announced today, contributed only $10 million to that initiative, leaving it up to the city to come up with the bulk of the funds for the so-called congestion pricing system. Mr. Bloomberg, at a press conference shortly after the announcement, downplayed the lack of money for congestion pricing. An aide to Mr. Bloomberg said later the city may borrow the money to buy the cameras and other equipment needed. “I think rather than look at the money we didn’t get we should look at the money we did get,” the mayor said. “It’s a unique opportunity for New York and we should really say ‘thank you.’ ” Opponents of the fee on drivers, however, called the news a setback for the Bloomberg administration, and predicted it would be more difficult now for the mayor to win approval for his congestion pricing plan. Under the agreement with the city, the City Council and Legislature must sign off on the plan early next year for the federal funds to be released. “This award is important in that the overwhelming majority of the funds are dedicated to improving the public transportation system,” City Councilman David Weprin, who chairs the council’s finance committee, said. “Initiating a congestion traffic tax now is tantamount to putting the cart before the horse.” The State Legislature has created a 17-member commission that it asked to evaluate the mayor’s congestion pricing plan and make recommendations. A total of 26 cities across the country — including Dallas, Denver and Miami — submitted proposals to the federal government for money to implement traffic reduction measures. Ms. Peters said that New York City was one of five that had been chosen. At a news conference this morning, Mary E. Peters, Secretary of Transportation, said that the federal government supported Mayor Bloomberg’s plan because it was “as brass and bold as New York City itself.” “The average New York commuter now spends 49 hours stuck in traffic every year, up from 18 hours in 1982,” she said. “While some may be content to accept growing gridlock as a way of life, Mayor Bloomberg is not going to let traffic rob the Big Apple. “New Yorkers,” she added, “must understand that we must stop relying on yesterday’s ideas to fight today’s traffic jams.” The mayor’s plan was first aired in April as part of a package of proposals meant to guide the city’s growth in an environmentally sensitive way over the next two decades. In addition to investing in mass transit, especially buses, the mayor wants to charge drivers $8 and trucks $21 a day to enter or leave Manhattan below 86th Street on weekdays during the workday. Those who drive only within the so-called congestion zone would pay $4 a day for cars and $5.50 for trucks. The congestion charging plan is designed not only to cut traffic, but also to generate hundreds of millions of dollars in annual revenue that could be used to help pay for large-scale transportation projects. The traffic plan drew opposition from politicians in the four other boroughs and the suburbs, which are home to many people who regularly drive into Manhattan. In a last-minute compromise in July, days after what the city called a federal deadline for a plan, a special session of the State Legislature agreed to create the 17-member commission to study the mayor’s plan. Many of the 17 members would be chosen by Mr. Bloomberg, Gov. Eliot Spitzer and other officials who have supported the proposal. The commission would make a recommendation by Jan. 31, and after that the plan would have to be approved by the City Council and the Legislature by March 31. Under Mr. Bloomberg’s plan, E-ZPass readers would charge a majority of drivers for travel in the zone. For vehicles without E-ZPass, a system of cameras around Manhattan would photograph license plates. Drivers would be expected to submit payments to the city. http://www.nytimes.com/2007/08/14/ny...d-traffic.html |
|
|

|
|
|
#2 |
|
Join Date: May 2001
Location: New England
Posts: 10,015
|
Internet is "The New Afghanistan": NY Police Commissioner
Michelle Nichols and Edith Honan The Internet is the new battleground against Islamist extremism because it provides ideology that could radicalize Westerners who might then initiate home-grown attacks, New York police commissioner Raymond Kelly said on Wednesday. "The Internet is the new Afghanistan," Kelly said, as he released a New York Police Department (NYPD) report on the home-grown threat of attacks by Islamist extremists. "It is the de facto training ground. It's an area of concern." The report found that the challenge for Western authorities was to identify, pre-empt and prevent home-grown threats, which was difficult because many of those who might undertake an attack often commit no crimes along the path to extremism. The report identified the four stages to radicalization as pre-radicalization, self-identification, indoctrination, and jihadization, and said the Internet drove and enabled the process. Radicalization could be triggered by such things as the loss of a job, the death of a close family member, alienation, discrimination, and international conflicts involving Muslims, said the report by senior NYPD intelligence analysts. "Much different from the Israeli-Palestinian equation, the transformation of a Western-based individual to a terrorist is not triggered by oppression, suffering, revenge or desperation," it said. "Rather, it is a phenomenon that occurs because the individual is looking for an identity and a cause and unfortunately, often finds them in extremist Islam," said the report "Radicalization in the West: The Home-grown Threat." While the September 11 strike on the United States by Osama bin Laden's al Qaeda network was planned overseas, the report said the attacks had helped proliferate and accelerate radicalization, especially in the West. "More importantly, 9/11 established the current trend of committing an act in the name of global jihad as a natural culmination of full radicalization and the ultimate responsibility for the fully radicalized jihadist," it said. But starting the radicalization process does not mean everyone will progress to "become a terrorist." "Individuals who have been radicalized but are not jihadists may serve as mentors and agents of influence to those who might become terrorists of tomorrow," said the report, which analyzed five home-grown U.S. attack plots. It says Europe's failure to integrate second and third generation immigrants into society, both economically and socially, had left young Muslims more vulnerable to extremism. While economic opportunities in the United States are better and the country's Muslims are more resistant to Islamist extremism, they are "not immune to the radical message." "The powerful gravitational pull of individuals' religious roots and identity sometimes supersedes the assimilating nature of American society," the report said. http://www.reuters.com/article/newsO...24872020070815  A Gateway for Hackers The security threat in the new wiretapping law Susan Landau Current administration policy is replete with examples of quickly enacted efforts whose consequences led to the opposite effect. (Beware of what you wish for . . . .) With Congress caving last week, the National Security Agency no longer needs a Foreign Intelligence Surveillance Act (FISA) warrant to wiretap if one party is believed to be outside the United States. This change looks reasonable at first, but it could create huge long-term security risks for the United States. The immediate problem is fiber optics. Until recently, telecommunication signals came through the air. The NSA used satellites and antennas to pick up conversations of foreigners talking to other foreigners. Modern communications, however, use fiber; since conversations don't go through the air, the NSA wants to access communications at land-based switches. Because communications from around the world often go through the United States, the government can still get access to much of the information it seeks. But wiretapping within the United States has required a FISA search warrant, and the NSA apparently found using FISA too time-consuming, even though emergency access was permitted as long as a warrant was applied for and granted within 72 hours of surveillance. Avoiding warrants for these cases sounds simple, though potentially invasive of Americans' civil liberties. Most calls outside the country involve foreigners talking to foreigners. Most communications within the country are constitutionally protected -- U.S. "persons" talking to U.S. "persons." To avoid wiretapping every communication, NSA will need to build massive automatic surveillance capabilities into telephone switches. Here things get tricky: Once such infrastructure is in place, others could use it to intercept communications. Grant the NSA what it wants, and within 10 years the United States will be vulnerable to attacks from hackers across the globe, as well as the militaries of China, Russia and other nations. Such threats are not theoretical. For almost a year beginning in April 2004, more than 100 phones belonging to members of the Greek government, including the prime minister and ministers of defense, foreign affairs, justice and public order, were spied on with wiretapping software that was misused. Exactly who placed the software and who did the listening remain unknown. But they were able to use software that was supposed to be used only with legal permission. The United States itself has been attacked. In six hours in August 2006, remote attackers entered computers at the Army Information Systems Engineering Command at Fort Huachuca, Ariz.; the Defense Information Systems Agency in Arlington; the Naval Ocean Systems Center in San Diego; and the Army Space and Strategic Defense Command in Huntsville, Ala. The hackers transported more than 10 terabytes of data to South Korea, Hong Kong or Taiwan, and from there to the People's Republic of China. Each intrusion was only 10 to 30 minutes. The downloaded information included Army helicopter mission-planning-systems specifications and flight-planning software used by the Army and Air Force. U.S. communications technology is fragile and easily penetrated. While advanced, it is not decades ahead of that of our friends or our rivals. Compounding the issue is a key facet of modern systems design: Intercept capabilities are likely to be managed remotely, and vulnerabilities are as likely to be global as local. In simplifying wiretapping for U.S. intelligence, we provide a target for foreign intelligence agencies and possibly rogue hackers. Break into one service, and you get broad access to U.S. communications. The Greek wiretapping and Chinese thefts from U.S. military sites are warnings that entities other than the NSA could exploit the vulnerabilities of U.S. communications networks. Were the proposed wiretapping technology penetrated by foreign intelligence services, U.S. security and privacy could be quickly and severely compromised. In its effort to provide policymakers with immediate intelligence, the NSA forgot the critical information security aspect of its mission: protecting U.S. communications against foreign interception. So did Congress. Lawmakers granted the warrantless wiretapping only for six months -- and they need to look carefully before it endangers U.S. national security for the long term. http://www.washingtonpost.com/wp-dyn...801961_pf.html  Army Reports Brass, Not Bloggers, Breach Security Noah Shachtman For years, the military has been warning that soldiers' blogs could pose a security threat by leaking sensitive wartime information. But a series of online audits, conducted by the Army, suggests that official Defense Department websites post material far more potentially harmful than anything found on a individual's blog. The audits, performed by the Army Web Risk Assessment Cell between January 2006 and January 2007, found at least 1,813 violations of operational security policy on 878 official military websites. In contrast, the 10-man, Manassas, Virginia, unit discovered 28 breaches, at most, on 594 individual blogs during the same period. The results were obtained by the Electronic Frontier Foundation, after the digital rights group filed a lawsuit under the Freedom of Information Act. "It's clear that official Army websites are the real security problem, not blogs," said EFF staff attorney Marcia Hofmann. "Bloggers, on the whole, have been very careful and conscientious. It's a pretty major disparity." The findings stand in stark contrast to Army statements about the risks that blogs pose. "Some soldiers continue to post sensitive information to internet websites and blogs," then-Army Chief of Staff Peter Schoomaker wrote in a 2005 memo. "Such OPSEC (operational security) violations needlessly place lives at risk." That same year, commanders in Iraq ordered (.pdf) troops to register their blogs "with the unit chain of command." Originally formed in 2002 to police official Defense Department websites (.mil), the Army Web Risk Assessment Cell, or AWRAC, expanded its mission in 2005. A handful of military bloggers, including then-Spec. Colby Buzzell, were seen as providing too many details of firefights in Iraq. Buzzell, for one, was banned from patrols and confined to base after one such incident, and AWRAC began looking for others like him on blogs and .com sites. But AWRAC hunted for more than overly vivid battle descriptions. It scoured pages for all kinds of information: personal data, like home addresses and Social Security numbers; restricted and classified documents; even pictures of weapons. When these violations were found, AWRAC contacted the webmaster or blog editor, and asked that they change their sites. "Big Brother is not watching you, but 10 members of a Virginia National Guard unit might be," an official Army news story warned bloggers. Within the Army, some worried that the blog-monitoring had compromised AWRAC's original goal. "My suspicion ... is that the AWRAC's attention is being diverted by the new mission of reviewing all the Army blogs," reads an e-mail (.pdf) from the office of the Army Chief Information Officer obtained in EFF's FOIA lawsuit. "In the past they did a good job of detecting and correcting (website policy compliance) violations, but that is currently not the case." On one blog, AWRAC found photos showing bomb damage to a Humvee; on another, a description of a mountain near a base in Afghanistan; on a third, a video about "morale concerning incoming mortar." AWRAC discovered a secret presentation on the official, unclassified Army Knowledge Online network. It found a map of an Army training center in Texas on a second .mil site. A "colonel's wife's maiden name" was caught on a third. http://www.wired.com/politics/online...08/milbloggers  Server with Top-Secret Data Stolen from Forensic Telecommunications Services The Forensic Telecommunications Services (FTS) has confirmed the theft of a computer server containing thousands of top-secret mobile phone records and evidence from undercover terrorism and organised crime investigations. The company - whose clients include Scotland Yard and the Crown Prosecution Service - has assured the public that the server is security protected, and the breach will not compromise ongoing police operations. The company announced the following: FTS can confirm that the company was recently the victim of a break-in at one of our premises in Kent. As a result, some IT equipment including a server was stolen. The server, which is security protected, contained administrative data and details of some case files in relation to FTS’ forensic work. In the unlikely event that the server was accessed, non of the data stored on the server in any way compromises ongoing police operations. The information is made up of either old cases that have passed through the judicial process, or cases that are already in the judicial system and so subject to full disclosure to both defence and prosecution teams. All the data was restored within 24 hours due to FTS’ business continuity measures. As a result of this incident FTS is undertaking a full and comprehensive review of security across the whole company. FTS are working closely with the police and assisting with their investigations. As with many other similar forensic service providers who are contracted by the police, FTS will not discuss the nature of our workload. Jamie Cowper from PGP Corporation commented the situation: "What this particular case highlights is that - as well as putting internal security measures in place - organisations really need to be more cautious of the third party companies that they entrust sensitive information to. Due to the nature of its work, it is likely that the FTS has a stringent information security policy. However, any company which outsources without a thorough assessment of the threat status of all third party contractors runs the risk of rendering existing corporate security policies useless. In order to enforce an enterprise data protection strategy, organisations MUST account for every eventuality - wherever data rests. In any case, the immediate disclosure and swift action taken by the FTS following the breach is yet another positive indication that organisations are beginning to take data protection seriously." http://www.net-security.org/secworld.php?id=5418  How Search Engines Rate on Privacy Declan McCullagh Price wars are public blessings. Ask anyone who has comparison shopped between Advanced Micro Devices and Intel microprocessors or bought a cheap Harry Potter novel thanks to fierce bookseller price battles. In the last few months, the search engine business has experienced its own version of cutthroat competition: a privacy policy war, with Google, Ask.com and Microsoft vying to outdo one another in protecting their users' personal information. But it's been difficult to make direct comparisons, in part because privacy policies tend to be written by lawyers for lawyers. So CNET News.com did some of the work for you by surveying the five leading search companies. Starting on August 6, we asked them eight questions, including how long they retain search data, how they eventually dispose of it, whether they engage in behavioral targeting, and whether they use information they have from user sign-ups to guide which ads are displayed. We asked follow-ups where necessary for clarification. The verbatim results of the survey are posted in an accompanying story. The answers suggest that, based on the questions we asked, Ask.com was the most protective of user privacy. In fact, only Ask.com said it would not record what users type into its search engine. (Smaller search engines, including ixquick, said this as well, but we limited our survey to the five largest engines.) Ask.com also said it did not engage in behavioral targeting, which refers to the practice of offering advertisements based on previous searches. And the rest? Results were mixed. Google avoids behavioral targeting, but after 18 months it performs a partial anonymization of users' Internet Protocol addresses--an action that's not terribly privacy protective. Google dominates the search market: 53 percent of U.S. Web searches in June were performed on its site, according to Nielsen/NetRatings. Microsoft is better on the anonymization front. Peter Cullen, the company's chief privacy strategist, said users' Internet addresses and cookie values are "permanently and irreversibly" disassociated from the search terms after 18 months. But Microsoft does engage in behavioral targeting, while Google doesn't. Yahoo and AOL were similarly mixed. These were, nevertheless, remarkable improvements. Google, Microsoft and Yahoo told News.com, in response to an earlier survey we did in February 2006, that they kept search records for as long as the data prove useful. Now they've set expiration dates, and Ask.com went further by promising to stop recording user search histories starting later this year. Google also has shortened the lifespan of its cookies from expiring in 2038 to expiring two years from the last visit. Search privacy is important because our Googling (and Yahooing, and MSNing and so on) provides a unique glimpse into our personalities and private lives. Search terms have been used to convict a wireless hacker and lock up a man charged with killing his wife. Search engine activity is also a fertile growth area for nosy divorce lawyers and employment disputes. One relatively simple way to protect your privacy when using search engines is to configure your browser to not permit them to place cookies on your computer. (Here's an FAQ on the topic.) Another way is to route all your connections through a proxy server such as Anonymizer, Tor or Black Box Search. Market rivalry and regulatory threats What all this amounts to is that the best search engine to use, from a privacy perspective, depends on what's most important to you. Are you worried about a company publishing even anonymized search terms, as AOL did last year? Then use one that deletes your data sooner, or disable cookies for that site (at the price of not being able to use features like Web-based e-mail). Do you dislike seeing ads presented according to a computer-generated profile that was crafted based on your search terms? Then use Ask.com or Google, because the other three companies we surveyed do behavioral targeting. Worried about someone perusing your search history in person? Use software like PGP or Mac OS X's FileVault to encrypt part or all of your hard drive. In addition to the normal forces of marketplace rivalry, another recent factor has been government regulatory threats. A group of European bureaucrats, called the Article 29 Working Party, has been pressuring search companies to store information for a shorter period of time. Last year, there was even a bill introduced in the U.S. Congress that would have forced Web sites to delete personal information if not required for "legitimate" business purposes.  Behavioral targeting is another growth area--not only for search companies, but for bureaucrats and politicians as well. Google's proposed $3.1 billion acquisition of the DoubleClick ad company is being investigated by U.S. regulators after the purchase was challenged on competition and privacy grounds. Microsoft has received regulatory approval to buy online ad firm Aquantive, and Yahoo acquired online ad exchange Right Media. More recently, AOL said it was planning to acquire behavioral-targeting firm Tacoda. The companies say they're following industry standards, with both Microsoft and Yahoo noting in our survey that they perform behavioral targeting only in accordance with Network Advertising Initiative principles. But liberal groups are becoming increasingly vocal, and the Federal Trade Commission last week announced it would hold a two-day forum in November to address behavioral advertising concerns. http://news.com.com/How+search+engin...3-6202068.html  In China, a High-Tech Plan to Track People Keith Bradsher At least 20,000 police surveillance cameras are being installed along streets here in southern China and will soon be guided by sophisticated computer software from an American-financed company to recognize automatically the faces of police suspects and detect unusual activity. Starting this month in a port neighborhood and then spreading across Shenzhen, a city of 12.4 million people, residency cards fitted with powerful computer chips programmed by the same company will be issued to most citizens. Data on the chip will include not just the citizen’s name and address but also work history, educational background, religion, ethnicity, police record, medical insurance status and landlord’s phone number. Even personal reproductive history will be included, for enforcement of China’s controversial “one child” policy. Plans are being studied to add credit histories, subway travel payments and small purchases charged to the card. Security experts describe China’s plans as the world’s largest effort to meld cutting-edge computer technology with police work to track the activities of a population and fight crime. But they say the technology can be used to violate civil rights. The Chinese government has ordered all large cities to apply technology to police work and to issue high-tech residency cards to 150 million people who have moved to a city but not yet acquired permanent residency. Both steps are officially aimed at fighting crime and developing better controls on an increasingly mobile population, including the nearly 10 million peasants who move to big cities each year. But they could also help the Communist Party retain power by maintaining tight controls on an increasingly prosperous population at a time when street protests are becoming more common. “If they do not get the permanent card, they cannot live here, they cannot get government benefits, and that is a way for the government to control the population in the future,” said Michael Lin, the vice president for investor relations at China Public Security Technology, the company providing the technology. Incorporated in Florida, China Public Security has raised much of the money to develop its technology from two investment funds in Plano, Tex., Pinnacle Fund and Pinnacle China Fund. Three investment banks — Roth Capital Partners in Newport Beach, Calif.; Oppenheimer & Company in New York; and First Asia Finance Group of Hong Kong — helped raise the money. Shenzhen, a computer manufacturing center next to Hong Kong, is the first Chinese city to introduce the new residency cards. It is also taking the lead in China in the large-scale use of law enforcement surveillance cameras — a tactic that would have drawn international criticism in the years after the Tiananmen Square killings in 1989. But rising fears of terrorism have lessened public hostility to surveillance cameras in the West. This has been particularly true in Britain, where the police already install the cameras widely on lamp poles and in subway stations and are developing face recognition software as well. New York police announced last month that they would install more than 100 security cameras to monitor license plates in Lower Manhattan by the end of the year. Police officials also said they hoped to obtain financing to establish links to 3,000 public and private cameras in the area by the end of next year; no decision has been made on whether face recognition technology has become reliable enough to use without the risk of false arrests. Shenzhen already has 180,000 indoor and outdoor closed-circuit television cameras owned by businesses and government agencies, and the police will have the right to link them on request into the same system as the 20,000 police cameras, according to China Public Security. Some civil rights activists contend that the cameras in China and Britain are a violation of the right of privacy contained in the International Covenant on Civil and Political Rights. Large-scale surveillance in China is more threatening than surveillance in Britain, they said when told of Shenzhen’s plans. “I don’t think they are remotely comparable, and even in Britain it’s quite controversial,” said Dinah PoKempner, the general counsel of Human Rights Watch in New York. China has fewer limits on police power, fewer restrictions on how government agencies use the information they gather and fewer legal protections for those suspected of crime, she noted. While most countries issue identity cards, and many gather a lot of information about citizens, China also appears poised to go much further in putting personal information on identity cards, Ms. PoKempner added. Every police officer in Shenzhen now carries global positioning satellite equipment on his or her belt. This allows senior police officers to direct their movements on large, high-resolution maps of the city that China Public Security has produced using software that runs on the Microsoft Windows operating system. “We have a very good relationship with U.S. companies like I.B.M., Cisco, H.P., Dell,” said Robin Huang, the chief operating officer of China Public Security. “All of these U.S. companies work with us to build our system together.” The role of American companies in helping Chinese security forces has periodically been controversial in the United States. Executives from Yahoo, Google, Microsoft and Cisco Systems testified in February 2006 at a Congressional hearing called to review whether they had deliberately designed their systems to help the Chinese state muzzle dissidents on the Internet; they denied having done so. China Public Security proudly displays in its boardroom a certificate from I.B.M. labeling it as a partner. But Mr. Huang said that China Public Security had developed its own computer programs in China and that its suppliers had sent equipment that was not specially tailored for law enforcement purposes. The company uses servers manufactured by Huawei Technologies of China for its own operations. But China Public Security needs to develop programs that run on I.B.M., Cisco and Hewlett-Packard servers because some Chinese police agencies have already bought these models, Mr. Huang said. Mr. Lin said he had refrained from some transactions with the Chinese government because he is the chief executive of a company incorporated in the United States. “Of course our projects could be used by the military, but because it’s politically sensitive, I don’t want to do it,” he said. Western security experts have suspected for several years that Chinese security agencies could track individuals based on the location of their cellphones, and the Shenzhen police tracking system confirms this. When a police officer goes indoors and cannot receive a global positioning signal from satellites overhead, the system tracks the location of the officer’s cellphone, based on the three nearest cellphone towers. Mr. Huang used a real-time connection to local police dispatchers’ computers to show a detailed computer map of a Shenzhen district and the precise location of each of the 92 patrolling officers, represented by caricatures of officers in blue uniforms and the routes they had traveled in the last hour. All Chinese citizens are required to carry national identity cards with very simple computer chips embedded, providing little more than the citizen’s name and date of birth. Since imperial times, a principal technique of social control has been for local government agencies to keep detailed records on every resident. The system worked as long as most people spent their entire lives in their hometowns. But as ever more Chinese move in search of work, the system has eroded. This has made it easier for criminals and dissidents alike to hide from police, and it has raised questions about whether dissatisfied migrant workers could organize political protests without the knowledge of police. Little more than a collection of duck and rice farms until the late 1970s, Shenzhen now has 10.55 million migrants from elsewhere in China, who will receive the new cards, and 1.87 million permanent residents, who will not receive cards because local agencies already have files on them. Shenzhen’s red-light districts have a nationwide reputation for murders and other crimes. http://www.nytimes.com/2007/08/12/bu...curity.html?hp  One. Big. Factory. The Forbidden City of Terry Gou His complex in China turns out iPhones and PCs, powering the biggest exporter you've never heard of Jason Dean Shenzhen, China Past a guarded gate on the outskirts of this city sits one of the world's largest factories. In dozens of squat buildings, it churns out gadgets bearing technology's household names -- Apple Inc.'s iPods and iPhones, Hewlett-Packard Co.'s personal computers, Motorola Inc. mobile phones and Nintendo Co. Wii videogame consoles. Few people outside of the industry know of the plant's owner: Hon Hai Precision Industry Co. With a work force of some 270,000 -- about as big as the population of Newark, N.J. -- the factory is a bustling testament to the ambition of Hon Hai's founder, Terry Gou. In an era when manufacturing has been defined by outsourcing, no one has done more to shift global electronics production to China. Little noticed by the wider world, Mr. Gou has turned his company into China's biggest exporter and the world's biggest contract manufacturer of electronics. Hon Hai's revenue has grown more than 50% a year in the past decade to $40.6 billion last year. It is expected to add $14 billion in revenue this year. That is roughly the equivalent of Motorola's adding, within a year, the sales of CBS Corp. Throughout his company's rise, the 56-year-old native of Taiwan has maintained a low profile. Publicity, he says, risks helping competitors and alienating customers. "I hate that I [have] become famous," Mr. Gou said in a recent three-hour interview at Hon Hai's Taiwan headquarters. It was Mr. Gou's first interview with Western media since 2002, following more than five years of requests by The Wall Street Journal. "We are so big we cannot hide anymore." Hon Hai, and its massive Shenzhen plant, provides a window into the sometimes-secretive world of manufacturing in China. Confidentiality is a selling point for contract manufacturers, whose customers count on them to shield their products and plans from outsiders. Secrecy has also been a central issue in China's recent tainted-product scandal, with the often-quiet relationship between U.S. companies and their suppliers complicating regulators' hunt for the source of defective goods. Recently, citing ongoing investigations, Mattel Inc. took nearly a week to identify its Chinese provider of toys believed to contain lead paint. Hon Hai hasn't been involved in such scandals, and analysts and industry insiders say Mr. Gou has combined discretion with a solid record of quality control and competitive pricing to build a booming empire. The $43 billion market capitalization of Hon Hai -- a public company listed in Taiwan, which uses the trade name Foxconn -- is equal to that of its 10 biggest global rivals combined. Mr. Gou and Hon Hai control additional affiliates that report revenue separately. Mr. Gou is currently worth about $10 billion, a Hon Hai spokesman says. The company guards its customers' identities, although some of them are named in its Chinese-language filings to securities regulators. Hon Hai and its affiliates make products not only for Apple, Nintendo, H-P and Motorola, but also cellphones and parts for Nokia Corp., PlayStation 2 sets for Sony Corp. and computer parts for Dell Inc. Those companies did not dispute their relationship with the manufacturer. Hon Hai is also currently the exclusive supplier of Apple's iPhones and one of the few makers of iPods, Taiwan-based analysts say. Apple acknowledged that Hon Hai is a supplier but declined to comment further. At the center of Mr. Gou's empire is his walled Shenzhen facility, the Longhua Science & Technology Park, which covers about a square mile. Aside from customers, few outsiders set foot inside. A reporter visiting Longhua was barred from viewing protected areas or taking photographs of more than a few scenes.  In addition to its dozens of assembly lines and dormitories, Longhua has a fire brigade, hospital and employee swimming pool, where Mr. Gou does early morning laps when he is there. Restaurants, banks, a grocery store and an Internet cafe line the company town's main drag. More than 500 monitors around the campus show exercise programs, worker-safety videos and company news produced by the in-house television network, Foxconn TV. Even the plant's manhole covers are stamped "Foxconn." James Lee, a heavy-smoking former banker whom Mr. Gou tapped to run the plant in 1998, is Longhua's de facto mayor. Mr. Lee frets about how to provide more than 150,000 lunches every day in the 10 cavernous employee canteens (that's about 10.6 metric tons of dry rice per meal, at one bowl each). He oversees landscaping, uniform buying, dormitory building and hiring as many as 3,000 new workers a day during peak periods. His administration employs more than 1,000 security guards to keep order and prevent unauthorized visitors from sensitive areas. Administrators also battle what he calls new employees' tendency to litter. GADGET MAKER Some major customers/products of Hon Hai & its affiliates:CUSTOMER PRODUCTS Apple iPhone, some iPod models Dell Desktop PCs/parts Hewlett-Packard Desktop PCs/parts Nokia Cellphones/parts Motorola Cellphones/parts Sony PlayStation2 videogame console, PSP handheld game unit Nintendo Wii videogame console DS game unit Source: WSJ research "I have to resolve every single small problem on this campus, with the exception of production," he says over a "Foxconn Coffee" at a company restaurant. He jokes: "Would you want this job?" Now the plant's space is running out. "We never thought we would expand so fast," says Mr. Lee. The founder's personality permeates the site and company. A charismatic man who inspires intense loyalty among his lieutenants, Mr. Gou runs Hon Hai with the power of a warlord. On his right wrist he wears a beaded bracelet he got from a temple dedicated to Genghis Khan, the 13th-century Mongolian conqueror whom he calls a personal hero. "I always tell employees: The group's benefit is more important than your personal benefit," Mr. Gou says. Mr. Gou has combined a competitive drive with a business model that lets the company build much of its products in-house, saving money on parts. His zeal for cost-cutting prompted a fellow executive to quip several years ago that Mr. Gou is "worth about $2 billion in nickels and dimes." Longhua's workers tend assembly lines, in shifts, around the clock. They earn wages that seem meager by developed-world standards but are enough to keep new recruits streaming through its gates. The most basic assembly-line jobs pay about 60 cents an hour -- the legal minimum -- although workers can earn higher wages for overtime. Meals are subsidized. Most workers live rent-free in company dormitories inside the walls or off campus. Last year, a British tabloid alleged poor treatment of Longhua's workers, specifically those who make Apple's iPods there. (At the time, Apple reported that nearly one-seventh of Longhua's workers made Apple products.) The British account was followed by criticism of the company in the Chinese press. Apple sent a team to investigate, and found a handful of violations of its Supplier Code of Conduct, including over-crowding at three off-site dorms, according to a report the company issued last August. Apple, which asks suppliers to limit workers to 60 hours of labor a week except in emergencies, estimated that one-third of Longhua's workers exceeded the limit. It did not find evidence of forced overtime. Overall, Apple found Hon Hai to be in compliance with its guidelines "in the majority of areas," it said in the report. Apple declined to comment further. Hon Hai executives say conditions for their workers are better than the average in China, which helps them attract new workers. They say they have built new dorms at the plant and taken other measures to address Apple's concerns. Mr. Gou angrily dismisses the critical coverage. Mr. Gou started what would become Hon Hai in 1974. He borrowed part of the initial investment of $7,500 from his mother, who with his father had fled to Taiwan in 1949 during China's civil war. In a facility near Taipei, he began making plastic channel-changing knobs for black-and-white television sets. In the early 1980s, he expanded into the PC industry just as it started to take off. His first products were connectors, the relatively simple but ubiquitous parts that join components in a PC. Though he spoke little English or Japanese, he soon began traveling to the U.S. and Japan, seeking out customers. During the 1980s and 1990s, he says he logged so much time driving from city to city in the U.S. that he memorized the menu at Denny's. In 1988, with orders surging and costs soaring in Taiwan, Mr. Gou set up his first factory in China, where land and labor were cheaper. Decades-old tensions between Taipei and Beijing were starting to wane, and China was a decade into a massive economic overhaul. Mr. Gou chose Shenzhen, a city next to Hong Kong at the forefront of China's market reforms. He used his small-but-fast-growing Shenzhen operation in his sales pitch to prospective customers. In 1995, when Michael Dell was visiting southern China, Mr. Gou offered to arrange meetings with local officials he knew in return for the chance to drive the 30-year-old American to the airport, says Max Fang, who was then Dell's head of procurement in Asia. On the way, Mr. Gou made an unscheduled detour to show off his factory. Dell then wasn't one of the world's top five PC vendors, and Hon Hai didn't yet make parts that Dell bought directly. But Mr. Gou "knew that Michael Dell was a star of tomorrow, so he wanted to meet him," says Mr. Fang, who has known Mr. Gou since 1979. Today, Hon Hai is one of Dell's biggest suppliers, analysts and industry sources say. Mr. Gou keeps a photograph of Dell's founder on a shelf in his Taiwan office. That same year, Mr. Gou secured a larger plot of land that would become Longhua. When Mr. Fang visited a year later, it had fewer than 1,000 workers. Executive offices were housed in 20-foot shipping containers. But Mr. Fang was impressed. At the time, Dell and other PC companies tended to buy parts from several suppliers and ship them to their own factories for assembly. Mr. Gou had created a production line that let him do most of the process himself, from procuring the raw steel for PC casings to putting together the finished product. GLOBAL PRESENCE Global manufacturing locations of Hon Hai and its affiliates. TAIWAN Headquarters – Tucheng (greater Taipei) CHINA Shenyang, Liaoning Province Yingkou, Liaoning Province Qinhuangdao, Hebei Province Langfang, Hebei Province Taiyuan, Shanxi Province Tianjin City Yantai, Shandong Province Shanghai City Wuhan, Hubei Province Nanjing, Jiangsu Province Kunshan, Jiangsu Province Huaian, Jiangsu Province Hangzhou, Zhejiang Province Shenzhen, Guangdong Province Foshan, Guangdong Province Zhongshan, Guangdong Province WORLD Czech Republic Hungary Mexico Brazil India Vietnam Source: The company Over the years, Mr. Gou has expanded his portfolio to include a growing share of the PC's insides. Making its own components lets Hon Hai undercut competitors on the price of its finished products without reducing its overall margins, says Adam Pick, an analyst at iSuppli Corp., a market research firm in El Segundo, Calif. By 2000, Hon Hai's work force neared 30,000 people and its revenue topped $3 billion. Mr. Gou was expanding his soup-to-nuts strategy to more products. That year, Hon Hai set up a subsidiary called Foxconn International Holdings Ltd., now the world's biggest independent cellphone maker. In 2003, Mr. Gou launched a company that is now a leading maker of flat-panel LCD monitors. Last year, Hon Hai bought a major producer of digital cameras. Now, in some cases, Hon Hai builds much of a product and ships it to its client for the finishing touches. In others, it ships the final products directly to retailers or consumers. In all, more than 450,000 workers are now employed at Mr. Gou's plants across about a dozen provinces of China. Thousands more work in facilities run by Hon Hai and its affiliates across the globe -- including Hungary, Mexico and Brazil -- as the company sets up plants closer to its customers' operations. The company is one of the biggest exporters in the Czech Republic, where Mr. Gou bought a castle several years ago. Hon Hai is also adding operations in Vietnam and India and expanding into other sectors, including auto parts. As Hon Hai grew too large for one person to manage directly, Mr. Gou fostered a culture centered on his personality. Around Longhua, his image can be seen in large framed photos of him with Chinese officials, and on the Gou biographies stacked in the factory book store's window. Executives say he leads by example to keep products coming out on schedule and to customer specifications. Known for his 16-hour days, the founder for years would cruise the Longhua campus late into the night in a golf cart -- modified with a large bicycle horn -- stopping to spot-check production lines or help repair equipment. Company managers are expected to read and remember a document called "Gou's Quotations." (No. 133: "The important thing in any organization is leadership, not management. A leader must have the decisive courage to be a dictator for the common good.") At meetings, Mr. Gou often stands, and illustrates his ideas with black marker on a giant white paper pad. He encourages discussion, but if someone says something he considers foolish, he may order the person to stand at attention. "He'll say, 'I'm not punishing you, because I'm standing, too,'" says a senior Hon Hai manager. Industry executives and analysts say customers often start outsourcing one product line to Hon Hai and then shift more there. "You get addicted," says Mr. Fang, who left Dell in 2002 and now runs a venture capital fund that has co-invested with Hon Hai in a company called Ugobe Inc., which makes robotic toys. Competitors have struggled to keep up. Four years ago, Hon Hai was smaller by revenue than Nasdaq-listed Flextronics International Ltd., the industry's longstanding leader. Now, Hon Hai is so much larger that even after a merger announced in June between Flextronics and Solectron Corp., of Milpitas, Calif., their combined revenue will be about two-thirds that of Hon Hai. Hon Hai has its vulnerabilities. It isn't, for example, a major producer of laptop computers, which analysts say requires product-design capabilities that Hon Hai lacks. It is exposed to the risks of contract manufacturing, an intensely competitive business with thin margins. Hon Hai relies heavily on a fairly small number of customers: In the tech industry, a single product line can make or break a company's fortunes and, in turn, the well-being of a supplier. The company also faces the challenge of increasing revenue at the rate investors have come to expect. Hon Hai's sheer physical size also creates difficulties. Longhua was built quickly, and its layout wasn't well planned, says Mr. Lee, the plant director. With its increasing overcrowding, just moving all those workers around is a challenge. Mr. Lee says he once considered building a monorail but the idea proved too difficult. He says the ideal facility would have about one-fourth of the land area and perhaps one-third the workers. "It's not a good idea to be this size," says Mr. Lee, who is also in charge of building other large factories for Hon Hai. Hon Hai executives, and outside analysts, say the company has stayed nimble so far largely by splitting its operations among about a dozen smaller, semi-autonomous units. Mr. Gou says he wants to upgrade Longhua's facilities and take on more advanced work, such as research and development. That means shifting manufacturing jobs to other parts of China. Longhua is incessantly busy, but during breaks and shift changes, the activity explodes. At lunchtime on a recent sunny day, thousands of employees poured out of their buildings. They swarmed in and out of a large cafeteria and browsed in the factory book shop. A line of dozens of new employees, carrying their few possessions, snaked along a crosswalk. Most of the workers wear uniforms color-coded by their department. Others wear blue jeans and T-shirts. A number stroll in pairs, hand-in-hand. The workers are as young as 16. Zhou Ruqing, an affable 20-year-old, has worked at Longhua for just over a year as a quality inspector on an assembly line. She lives in an apartment outside the factory with her boyfriend, who also works at Longhua. Ms. Zhou came to Shenzhen in 2005 after graduating from high school in rural Sichuan province. As a mid-level assembly-line worker, she earns about $230 a month, including overtime pay. (First-year workers can make as little as $90 a month if they do not work overtime.) That doesn't include about $60 a month in housing and food subsidies, plus health insurance. In Shenzhen, that money goes far -- the rent for the small apartment she shares is less than $60 a month. Another worker, who would identify himself only as Mr. Xiao, started as an assembly-line worker almost three years ago, just after graduating from a technical school in central China, where Hon Hai recruited him. His starting salary was $44 a month at today's exchange rate. Working up to 30 days a month, he could earn up to $157 a month. "I was really tired then, too busy to rest," he said. Mr. Xiao has worked up to a more advanced post. His basic salary has doubled, although his total pay hasn't increased much, partly because he works fewer hours. He says conditions are better than they were at the time of last year's critical press attention, but "the change is incomplete." He currently works six days a week, spending his off day studying in hopes of landing a different position. Mr. Gou's role at Hon Hai is changing, too. He says he works just as hard today, but is focusing more on big strategic issues than day-to-day work. He is also devoting more time to charity -- he has pledged to eventually give away one-third of his fortune -- and dealing with changes in his personal life. His wife of many years died in 2005. Last month, his younger brother, who had headed a Hon Hai affiliate, died after a long illness. Mr. Gou has begun looking for a successor at Hon Hai, focusing on candidates in their late 30s or early 40s and asking senior managers to prove themselves by running their units assertively. There is no natural successor -- his son and daughter don't work at the company. He says his decision to begin stepping down now is inspired by Chinese history, specifically the Qianlong Emperor, who ruled from 1736 until 1796, when he was 84 years old. Qianlong greatly expanded the Qing Dynasty, making China perhaps the wealthiest country on earth. But his judgment failed in his later years, and the Qing began a decline that led to its eventual demise. "He controlled the whole of China for 60 years," says Mr. Gou. "He stayed there too long. So I want to sit back and give young people more responsibilities, when I'm still young." --Sue Feng in Beijing and Christopher Lawton in San Francisco contributed to this article. http://online.wsj.com/public/article....html?mod=blog  China Recall Toy Factory Boss Hangs Himself The boss of a Chinese toy manufacturing company involved in a Mattel recall after its products were found to contain excessive lead levels has hanged himself, Chinese media reported on Monday. Zhang Shuhong, a Hong Kong businessman in his 50s and boss of the Lida Toy Company in the southern province of Guangdong, was found dead in his factory workshop on Saturday, the semi-official Southern Metropolitan Daily said. Zhang was not a Mattel employee. About 1.5 million preschool toys made by Lida Toy, a Foshan-based contract manufacturer for Mattel Inc.'s Fisher-Price unit, were recalled across the globe by the U.S. company last week. The recalled toys included popular preschool characters such as Elmo and Big Bird and dozens of other items. The case was the latest in a deluge of product safety scares that have tainted the "made-in-China" brand. The recall was Mattel's largest since 1998 when it recalled some 10 million Power Wheels vehicles made by its Fisher-Price unit. The latest recall comes on the heels of RC2 Corp's Chinese-made wooden Thomas & Friends toy trains in June because some of them contained lead paint. Lead paint has been linked to health problems in children, including brain damage. China's quality watchdog had banned Lida from exports. A close friend of Zhang who was also one of the major paint suppliers for the company sold the problematic paint to Lida, the newspaper said. "(He) was so evil-hearted to have sold the fake paint to our boss ... our boss was ruined by his best friend," a manager of the company, surname Liu, was quoted as saying. Lida was not immediately available for comment. Calls to its factory went unanswered. Mattel spokeswoman Jules Andres said the company was "saddened" to hear of Zhang's death, but had no further comment. Police were investigating the case, the newspaper said. Chinese goods have been under fire after a chemical additive in pet food caused the death of some pets in the United States, and toxic ingredients were found in Chinese toothpaste and fish exports. Deaths of patients in Panama were blamed on improperly labelled Chinese chemicals mixed into cough syrup. (Reporting by Vivi Lin, additional reporting by Justin Grant in New York) http://uk.reuters.com/article/govern...35192020070813  Mattel Reportedly Plans Second Recall Over Chinese Paint Anne D'Innocenzio Less than two weeks after Mattel Inc. recalled 1.5 million Chinese-made toys because of lead paint, the toy industry is bracing for another blow that could give parents more reason to rethink their purchases just before the critical holiday shopping season. Mattel is set to announce the recall of another toy involving a different Chinese supplier as early as Tuesday, according to three people close to the matter who spoke on condition of anonymity because of the sensitivity of the situation. Details of the latest recall were not immediately available, but one of the three people said the toy is being recalled because its paint may contain excessive amounts of lead. Scott Wolfson, a spokesman for the Consumer Product Safety Commission, declined to comment. Mattel officials did not immediately return phone calls. A new Mattel action would mark the latest in a string of recalled products from China, ranging from faulty tires to tainted toothpaste. With more than 80 percent of toys sold worldwide made in China, toy sellers are nervous that shoppers will shy away from their products. On Aug. 1, Mattel's Fisher-Price division announced the worldwide recall of 1.5 million Chinese-made preschool toys featuring characters such as Dora the Explorer, Big Bird and Elmo. About 967,000 of those toys were sold in the United States between May and August. Mattel, based in El Segundo, Calif., apologized to customers for that recall and said the move would cut pretax operating income by $30 million. Fisher-Price "fast-tracked" the recall, which allowed the company to quarantine two-thirds of the tainted toys before they reached store shelves. In documents filed Aug. 3 with the Securities and Exchange Commission, Mattel noted that additional information became available in July on "other smaller product recalls and similar charges were recorded." Those recalls involved design problems, according to company officials questioned last week. Days after the Fisher-Price recall, Chinese officials temporarily banned the toys' manufacturer, Lee Der Industrial Co., from exporting products. A Lee Der co-owner, Cheung Shu-hung, committed suicide at a warehouse over the weekend, apparently by hanging himself, a state-run newspaper reported Monday. Lee Der was under pressure in the global controversy over the safety of Chinese-made products, and it is common for disgraced officials to commit suicide in China. In June, toy maker RC2 Corp. voluntarily recalled 1.5 million wooden railroad toys and set parts from its Thomas & Friends Wooden Railway product line. The company said that the surface paint on certain toys and parts made in China between January 2005 and April 2006 contain lead, affecting 26 components and 23 retailers. In July, Hasbro Inc. recalled Chinese-made Easy Bake ovens, marking the second time the iconic toy had been recalled this year. Before this month, Fisher-Price and parent company Mattel had never before recalled toys because of lead paint. http://news.newstimes.com/news/updat...e=news_updates  Still for Sale: Bibs with Lead  No chew! Too spicy. Tests by two firms show elevated lead levels in bibs sold at Toys 'R' Us, but retailer, Feds have not recalled item. Certain vinyl baby bibs sold at Toys "R" Us stores appear to be contaminated with lead, but this latest Chinese-made product to raise safety concerns is not being recalled. Tests conducted on the bibs for the public interest group Center for Environmental Health (CEH) as well as tests conducted separately by the New York Times showed lead as high as three times the level allowed in paint in the bibs. CEH said it tested these two bibs from a Toy R Us store and found them to be contaminated with lead. The CEH said Wednesday that it purchased the Vinyl bibs from Toys R Us and Babies R Us stores, including a bib with Disney's (Charts, Fortune 500) "Winnie the Pooh" characters and store brand bibs marketed as "Koala Baby" and "Especially for Baby" bibs. The group said in a statement that the bibs tested for lead levels that are between three and four times the legal limit for lead in paint. CEH also found a "Kidcosmic" brand vinyl bib sold in a Lisa Kline store with similarly high lead levels. In May, the Consumer Product Safety Commission (CPSC) issued a consumer safety alert - but not a recall - of baby bibs with cracked or peeling vinyl surfaces. The agency warned of a potential risk of lead exposure to infants from those products. However, the agency concluded that its risk assessment found hat none of the bibs that were tested at CPSC's laboratory would pose a risk of substantial illness to children from mouthing The CPSC recommended that parents discard bibs that were in poor condition to avoid any potential exposure to lead from swallowed vinyl. "Lead in vinyl baby bibs poses a reckless, unnecessary hazard to children at the most vulnerable age," Caroline Cox, research director at CEH said in a statement. "These companies have known for months that vinyl bibs could be a threat to children, yet they continued to put their profits ahead of children's health. We expect these bibs to be removed from store shelves immediately," she said. The CEH said it found Wal-Mart (Charts, Fortune 500) selling vinyl baby bibs tainted with lead in May and asked the retailer to stop the sale of the bibs nationwide. Regarding the CPSC's safety alert issued in May, the CEH said that the Safety Commission's report was "inaccurate and misleading." "In fact, all of the tests on the Wal-Mart, Toys R Us, Disney and Lisa Kline bibs were on new bibs," the group said. "CPSC has a chance to step up to the plate and order a national recall to protect children, but the recent past has shown that the agency is more concerned with protecting companies that make and sell poisonous products," Charlie Pizarro, associate director of CEH, said in a statement. Separately, the Times reported Wednesday that Toys "R" Us said that its own independent lab test on the bibs conducted as recently as May found them to be in compliance with safety standards for lead levels. Company spokeswoman Kathleen Waugh told the paper the bibs would be retested and held to standards tougher than federal safety rules. "Our uncompromising commitment to safety has been, and continues to be, our highest priority," she said in a written statement. The retailer is owned by private equity firms Kohlberg Kravis Roberts and Bain Capital and real estate investment trust Vornado Realty Trust (Charts). The bibs were imported from China by Hamco Baby Products, a unit of Crown Crafts (Charts). The paper reports that Hamco earlier this year imported bibs from China for Wal-Mart Stores (Charts, Fortune 500), but the retailer removed the bibs from its store shelves nationwide due to lead concerns. In Illinois, a strict lead law required their recall, the paper reported. Chinese products have raised new safety concerns in recent months, prompting a series of recalls. Mattel (Charts, Fortune 500) on Tuesday recalled more than 9 million toys made in China that had been sold in the United States, the second major recall of Chinese toys by the toymaker. There have also been recalls in recent months of Chinese-produced toothpaste, seafood, animal feed and tires for light trucks, all due to concerns about the safety of the products. Officials from the Consumer Product Safety Commission told the paper that they would prefer that there be no elevated levels of lead in bibs, but that its own test results indicate that lead, when present, was at levels low enough that a child chewing on or rubbing the bib would not get an unhealthy dose. The agency said the Toys "R" Us bibs pose a risk only if they are ripped or otherwise deteriorated. "There is a potential risk of lead exposure from babies swallowing pieces of cracked vinyl on used bibs," the agency said in a statement given to the paper, after being presented with the test results on the Toys "R" Us bibs. The lack of a recall prompted criticism by some lead safety advocates. "All lead is bad lead," Patrick MacRoy, director of the Chicago lead poisoning prevention program, told the Times. "Why should we allow any lead to be in there?" http://money.cnn.com/2007/08/15/news...ion=2007081507  Police Seize Phony Cigarettes in N.Y. Raid Frank Eltman Authorities seized nearly 60,000 cartons of cigarettes with brand names like Marlboros and Newports, half of which are suspected of being counterfeits from China, prosecutors announced Monday. Three Chinese were arrested in the raid late last week at a warehouse in the Corona section of Queens, Nassau County District Attorney Kathleen Rice said at a news conference. The cigarettes have an estimated street value of more than $3.4 million. Dozens of cartons of well-known cigarette brands -- as well as piles of cash -- were arrayed on conference tables surrounding the podium. Many of the cardboard boxes holding the cartons were stamped "Made in China." Also seized were counterfeit sneakers, as well as $350,000 in cash. Prosecutors estimated that the potential lost tax revenue from the cigarettes was more than $1 million. "When you couple the financial blow these crimes have on local budgets with the potential health risks the counterfeit cigarettes can pose to their consumers, it becomes imperative we crack rings like this one," Rice said. Queens District Attorney Richard A. Brown said the suspects were arraigned over the weekend on charges of forgery and trademark counterfeiting, as well as violations of state tax laws. They were held on bail ranging from $250,000 to $500,000, Brown said. They face up to 15 years in prison if convicted on the forgery charge, and another four years on the tax violations. Brown said the counterfeit and untaxed cigarettes are sold at a discount to "mom and pop" retail stores throughout the metropolitan region, who then resell them to customers at traditional prices. Besides the lost tax revenue, Rice noted that the counterfeit cigarettes do not adhere to New York state law, which requires that "fire safe" cigarettes include a mechanism designed to extinguish the cigarette automatically after a brief period of time. The raid and arrests followed a six-month investigation that began when police received a tip that illegal cigarettes were being sold on Long Island, Rice said. http://www.newstimeslive.com/news/st...?id=1186568834  Toy Makers Brace for a Chill in Sales Louise Story For toy makers, it is beginning to look as if it may be a rough Christmas. On Tuesday, Mattel, the world’s largest toy maker, announced its second lead-related recall this month, pulling back 436,000 toy cars fashioned after the Sarge character in the movie “Cars.” The company also recalled 18.2 million toys with small magnets that could be swallowed by children, a design flaw that was not the fault of the toys’ Chinese makers. Still, the recalls, the latest in a series involving products from China, have focused attention on the toy industry as manufacturers like Mattel and Hasbro prepare to ship millions of toys from China for the holidays. Industry analysts are worrying whether toy makers will be able to reassure parents and government officials that toys shipped here are safe. “For each additional recall and each story in the news about harmful products, the risks of impacting holiday sales increases,” said Erik Kolb, a toy industry analyst for Standard and Poor’s Equity Research. “There’s no doubt that this poses a risk to the entire industry.” Most of the dolls, electronic toys and action figures long popular with children are made in China, and pressure is mounting to increase scrutiny of imports. Chinese officials have already increased surprise inspections at toy factories there, and American regulators are considering requiring more tests in China or checking toys as they enter ports in the United States. All this extra testing has some toy makers worried that their goods might not reach store shelves on time — a delay that could cost them the bulk of their profits for the year. “This could be a disaster,” said Jeff Holtzman, president and chief executive of the Goldberger Company, which sells dolls made in China to stores like Toys “R” Us. “Everything is planned and is very time-sensitive. There are millions and millions of dollars at stake.” Increasingly, politicians are calling for tougher measures to check toys. This week, Senator Barack Obama, Democrat of Illinois and a presidential candidate, sent letters to President Bush and the United States trade ambassador expressing concern. Senator Charles E. Schumer, Democrat of New York, said there was a need for an import czar and federal inspections of Chinese factories that produce goods for export to the United States. Senator Christopher J. Dodd, a Connecticut Democrat, called on Mr. Bush yesterday to immediately freeze all imports from China. “This is not an unprecedented action,” Mr. Dodd, who is also running for president, said in an interview. “The Koreans, Japanese and the British have all used this authority when they believed the safety of their products was in question. Parents are getting up in these forums I’m attending and saying: ‘What’s going to happen here? I have to read every label. Has this been here for years, or is this new?’ They are worried.” The toy industry is in discussions with the federal Consumer Product Safety Commission and members of Congress about testing. Many options are being considered, including tests at United States ports, third-party testing in China and seals of approval for tested toys. The product safety commission has asked Congress for additional power to monitor toys coming into the country. Senator Richard J. Durbin, Democrat of Illinois who is the chairman of the Senate committee that oversees financing for the commission, has urged the agency to monitor toys at the ports. And he has co-sponsored legislation to require third-party testing of all imported toys for children under 5. “If this flood of dangerous products continues and retailers are forced to pull toy after toy from their shelves, China will become the Grinch that steals Christmas this year,” Mr. Durbin said in an e-mail message. Nancy A. Nord, the acting chairwoman of the commission, said in a news conference after Mattel’s latest recall that she expected to announce a new testing program with the toy industry soon. Ms. Nord has also been in discussions with Chinese officials about toy safety and will be host at a meeting with them early next month over safety concerns. Meantime, toy makers are trying to prove to lawmakers that they can handle the matter themselves. Carter Keithley, the president of the Toy Industry Association, called tests at ports of entry “belt and suspenders checks,” arguing that such a measure would be overly cautious. The Juvenile Products Manufacturers Association has gathered a coalition of toy makers to demand that all American import partners ban lead paint, so that it cannot accidentally end up on toys. And every major toy maker has stepped up toy testing this summer, said Frederick Locker, a lawyer who works in the toy industry. “Most toy companies are ramping up to enhance their inspections to ensure that mistakes that should not happen are not happening,” Mr. Locker said. “This is a proactive industry, not a reactive one.” Officials at companies like Lego and Wal-Mart say they are trying to reassure customers that most toys are safe. “We hope that consumers don’t jump to conclusions about toys in general just being unsafe for children, because that’s not true,” said Michael McNally, a spokesman for Lego, which does not have factories in China. But some consumers have already made up their minds. “I’m not giving my grandchild any toy that’s made in China,” said Elizabeth Noe, who lives in Ridgewood, N.J., and is expecting to become a grandmother in two months. “Do we really know who is in control over there? Do we really know who is watching those factories?” http://www.nytimes.com/2007/08/16/bu...ss/16toys.html  Trouble in China Is Good News for American Toy Manufacturers Andrew Martin Whittle Shortline Railroad , a company in Louisiana, Mo., that makes wooden trains and trucks, posted a banner on its Web site several weeks ago: “100 percent kid-safe,” it read, “with lead-free paints.” Mike Whitworth, the company’s owner, said the recent recalls of Chinese-made toys found to contain lead in their paint has been good for his business. Very good. “We are little bitty, but we are taking some leaps and bounds here,” said Mr. Whitworth, who sells his toys over the Internet and in neighborhood toy and train stores. “Actually, we have seen about a 40 percent jump since late June.” With about 80 percent of the toys sold in the United States manufactured in China, the relatively few manufacturers of American-made toys who remain have relied to some extent on snob appeal and survived mostly by emphasizing the quality of their products — even if they cost more money. But some are now pointing to another competitive advantage: you can count on them to be lead free. After struggling for years to compete against cheaper Chinese imports, several manufacturers of American-made toys said they had been inundated with calls in recent weeks from retail chains and customers inquiring about their products. The calls increased yesterday after Mattel announced its second major recall of Chinese-made toys that contain lead paint. In June, an Illinois toy manufacturer, RC2 Corporation, recalled 1.5 million Thomas & Friends toy train sets that were manufactured in China and contaminated with lead paint. “It’s created a lot of buzz,” said Mike Rainville, owner of Maple Landmark toys in Middlebury, Vt., who said his company had experienced a “nudge” in sales. “We expect the impact to manifest itself more as time goes on.” Mr. Rainville said he had become adept at answering customer inquiries about the safety of his toys. “Our brand is clearly made in Vermont,” he said. “So people understand almost inherently that what is going on in China is different from what we’re doing.” Still, he said his company conducts third-party testing of its toys to make sure that its finishes are safe. “People are not going to forget about this for at least this Christmas season,” he said. Sue Dennison, co-owner of Roy Toy, which is based in East Machias, Me., said orders were up about 25 percent over the last several weeks. “I used to get probably two e-mails a week inquiring about U.S.-made toys,” she said. “Now I’m getting four or five a day.” Ms. Dennison said her company did not use paint on its wooden toys but uses dyes that are approved for use on food. With so many mass-produced toys being made in China, most American-made toys are sold over the Internet or in independent toy stores that tend to be more expensive than major retail chains. Indeed, many neighborhood toy stores promote the fact that their toys are not mass produced but rather handmade by American manufacturers or imported from European toy makers. But those stores represent a small fraction of the toys that are sold. Cliff Annicelli, editor of Playthings, a toy industry trade publication, estimated that specialty toys represent about 5 percent of the overall toy business in the United States, which was $22 billion in 2006. He pointed out that even small toy stores may carry as many Chinese-made toys as larger retailers. Store owners, however, are likely to have better knowledge about the quality and origin of their toys than employees of large retail chains. At Kidding Around, a toy store in Manhattan, Karla Perez, the manager, said the recalls of Chinese-made toys have had little impact on the store’s business. She said her store has a loyal customer base and does not necessarily draw those who shop at retail chains like Toys “R” Us. “The Toys ‘R’ Us toys are different from what we sell,” she said. Diana Nelson, who owns Kazoo & Company in Denver, also sniffed at the quality of mass-produced toys. While her store includes many products from China, she said she assured customers that the toys were safe. Ms. Nelson predicted that the recalls of Chinese-made toys would result in bigger sales at her store and on the Internet through the end of the year. “It will be a boost for us,” she said. While Mr. Whitworth, the train maker, is enjoying his recent success, there is at least one dark cloud on his horizon. For years, the tracks sold by Whittle Shortline Railroad have been made by a woodworker, who decided to quit the business in May. It turns out that he could not compete with the Chinese. Mr. Whitworth said he was searching for a new track maker. If he cannot find one soon, he said, “I’m going to have to buy offshore track.” http://www.nytimes.com/2007/08/15/business/15toys.html  U.S. Requests WTO Ruling in Piracy Complaint Against China The Bush administration has asked the World Trade Organization to rule in a complaint against China over the piracy of copyrighted movies, music, software and books, escalating a dispute that has roiled commercial relations. The U.S. Trade Representative's office took the formal step Monday of asking the WTO to decree that China's laws fall short of international agreements, after consultations failed to resolve differences over what the United States says are weak Chinese laws to safeguard patents and copyrights. "We still see important gaps that need to be addressed," said Sean Spicer, a spokesman for Susan Schwab, the trade representative. China's copying of movies, music and software costs companies $2.2 billion in 2006 sales, according to an estimate by lobby groups representing Microsoft, Walt Disney and Vivendi. The WTO complaint, announced in April, is the first by the United States against China for breaching intellectual property rights. Under WTO rules, China can block the establishment of a three-member panel this month. If it does so, then the United States will need to request another panel next month, which China can't block. The judges typically take a year or more to rule on a complaint. The two sides held one formal consultation in June, and China has not taken any steps that address U.S. concerns, the trade representative's office said. This is one of five WTO cases the United States has brought against China and the third of those in which the United States has requested a WTO dispute settlement panel. China prefers to address disputes through negotiations and consultations because sanctions don't resolve disagreements, said Liao Xiaoqi, China's vice minister of commerce. "China will continue using legal and administrative means to strengthen our protection of intellectual property rights," Liao said. In this case, the United States says that China's threshold for prosecution is so high that it effectively allows the sale of pirated or counterfeited goods on a commercial scale without violators having to face criminal charges. Second, the United States says China allows pirated goods that are seized to be sold once the fake labels on them are removed. The United States wants those products destroyed. Third, Chinese laws do not provide copyright protection for works that are awaiting approval by censors, which allows pirates to get a head start on legitimate distributors, the United States says. In April, the United States filed a complaint about barriers it says U.S.-based movie, music, book and other copyright industries face in selling in China. http://www.iht.com/articles/2007/08/14/business/wto.php  China Bans Reporting on Bridge Collapse Charles Hutzler Communist authorities have banned most state media from reporting on the deadly collapse of a bridge in southern China, with local officials punching and chasing reporters from the scene, reporters said Friday. The harassment and the reporting ban, issued by the Central Propaganda Department, came Thursday while reporters swarmed the tourist town of Fenghuang to report on Monday's accident. Unidentified locals roughed up a group of five newspaper and magazine reporters as they interviewed families of those killed, according to a photographer and a reporter whose colleague was among the journalists involved. The collapse of the bridge, which was under construction, left at least 47 people dead, making it one of the worst building accidents in China in recent years. On Friday, rescue crews blasted massive stone and concrete columns to clear the way for a deeper search of the rubble. They uncovered six more bodies and said it unlikely any survivors would be found, the Xinhua News Agency reported. The rough treatment given the media stands at odds with the responsible, concerned image China's Communist Party leadership has tried to convey publicly in the wake of the accident and the run-up to the 2008 Beijing Olympics. Officials from President Hu Jintao on down have promised a thorough investigation into the collapse and punishment for any wrongdoing. But the accident has raised troubling questions about shoddy building and possible corruption between the officials and contractors, and by trying to control reporting on the disaster, Beijing is fueling those suspicions. "The local government does not want the media to uncover the collapse," said Li Datong, a veteran newspaperman forced from a top editing job two years ago for running reports that angered authorities. Li said he was told about the harassment in Fenghuang by reporters involved. A duty officer in the Fenghuang police department, Liu Xiajun, said reporters had made an emergency call reporting the harassment Thursday, but he said he could not elaborate. An official in the Propaganda Department's information office who declined to give his name said he was "not clear" about the ban and declined further comment. While all media in China is state controlled, some outlets have engaged in lively, aggressive reporting in recent years, taking advantage of greater social freedoms that have accompanied economic growth and seeking higher profits. Accounts of reporters being beaten by local thugs have increased, with one reporter even being beaten to death early this year. After the Propaganda Department issued the ban, editors soon phoned their crews in Fenghuang, ordering them to clear out. Editors "told them to disappear within 10 minutes from Fenghuang," the photographer who was having dinner with a group of reporters Thursday night wrote in an e-mail. The photographer and the reporter asked that they and their media not be identified for fear of reprisals by the department, China's top media censor. Under the ban, state media were ordered not to send reporters to Fenghuang or independently gather the news but to rely solely on reports by the government's Xinhua News Agency, according to the reporter. Among the reporters roughed up Thursday was one from a Xinhua-owned magazine, Liaowang Oriental Weekly, along with colleagues from People's Daily, China Youth Daily, Southern Metropolis Daily and the Economic Observer newspaper, the reporter said. "My colleague was kicked when he tried to stop local officials from beating Wang Weijian from the People's Daily," the reporter said in a telephone interview. He said the officials accused the group of conducting "unauthorized interviews." Wang declined to comment. In a further sign of how the government was trying to control reporting from Fenghuang, an account of the reporters' harassment posted on a popular Internet forum http://www.tianya.cn Friday morning was removed several hours later, the reporter said. _____ AP correspondent Alexa Olesen in Beijing contributed to this report. http://www.washingtonpost.com/wp-dyn...081700752.html  BBC Radio Ordered off Russian FM The BBC's Russian-language service will no longer be heard on Russian FM radio, after the country's media regulator ordered that it be removed. The broadcaster's last FM distribution partner in Russia, Bolshoye Radio, said it had been told to remove BBC content or risk being shut down. Two other Russian FM stations have dropped BBC programming recently. The BBC's Russian Service can still be heard online and on medium and short wave frequencies in Russia. BBC executives said they would appeal against the decision. 'Propaganda' "The BBC entered into the relationship with Bolshoye Radio in good faith," said Richard Sambrook, Director of BBC Global News. "We cannot understand how the licence is now interpreted in a way that does not reflect the original and thorough concept documents." He said the licensing agreement allowed for 18% of Bolshoye's content to be foreign-produced. Bolshoye Radio's owners, financial group Finam, told the BBC that Russia's media regulators required that all programming be produced by the station itself. A spokesman for the company said management had made the decision without outside prompting and that it was well known that the BBC was set up to broadcast foreign propaganda. "Any media which is government-financed is propaganda - it's a fact, it's not negative," the spokesman, Igor Ermachenkov, told the BBC. A BBC spokesman, Mike Gardner, said: "Although the BBC is funded by the UK government... a fundamental principle of its constitution and its regulatory regime is that it is editorially independent of the UK government." Critics say Russia is taking measures to curb media freedom ahead of parliamentary elections in December and a presidential poll in March. http://news.bbc.co.uk/go/pr/fr/-/2/h...pe/6951710.stm  Word to the wise Girl Overdoses on Espresso Coffee BBC A teenager was taken to hospital after overdosing on espresso coffee. Jasmine Willis, 17, developed a fever and began hyperventilating after drinking seven double espressos while working at her family's sandwich shop. The student, of Stanley, County Durham, was taken to the University Hospital of North Durham, where doctors confirmed she had overdosed on caffeine. She has since made a full recovery and is now warning others about the dangers of excessive coffee drinking. Ms Willis, who had thought the coffees were single measures, said the effects were so severe that she began laughing and crying for no reason while serving customers at the shop. She developed a fever and began struggling to breathe after being sent home by her father. "My nerves were all over the place. "I was drenched. I was burning up and hyperventilating. "I was having palpitations, my heart was beating so fast and I thought I was going into shock. "I did not realise this could happen to you and I only hope other people learn from my mistake." The teenager, who was allowed home after a few hours of observation, suffered side effects for days afterwards and now says she cannot stand the sight of coffee. Her father Gary, who runs The Sandwich Bar in Stanley, said: "She did not realise she was drinking double measures. "I have always stressed to my children the importance of moderation but Jasmine got caught out on this occasion." http://news.bbc.co.uk/go/pr/fr/-/2/h...ar/6944026.stm  US Curriculum to Include Online Safety Robert Jaques The US National Cyber Security Alliance (NCSA) has called on state leaders to work with schools and colleges to ensure that cyber-security, online safety and ethics lessons are integrated into every classroom. The call has been made with support from companies including CA, McAfee, Microsoft and Symantec, along with educational organisations such as the Consortium for School Networking and the State Education Technology Directors Association. Recent legislation dubbed the No Child Left Behind Act requires students to be technology-literate on completion of the eighth grade (year nine in the UK), and the NCSA argues that children should also be taught about the dangers of the web. The National School Boards Association reported that 96 per cent of school districts claim that at least some of their teachers assign homework requiring internet use. But there is still no formal education on how to stay safe, secure and ethical online, despite the fact that the internet, like the real world, has threats and dangers which students may come across in the normal course of a day. These include communications from identity thieves, online predators and cyber-bullies. A recent University of Michigan national poll on children's health issues found that adults ranked 'internet safety' as the seventh most important issue affecting children today. "As more and more children and teens grow up in an online world, it is important that they understand how to behave online," said Ron Teixeira, executive director of the NCSA. "Their safety and security depends on whether or not they talk to strangers, place personal information on social networking sites or secure their family's computer. "It is critical that states and schools implement internet safety, security and ethics lessons into current technology literacy education efforts in order to protect children from identity theft as well as the nation's online infrastructure." The NCSA is proposing cyber-awareness programmes that must incorporate the 'C3 principles' of cyber-ethics, safety and security. These include: • Cyber Ethics Lessons which teach that hacking into someone's computer and taking information is just as wrong as breaking into someone else's home • Cyber Bullying which is just as wrong as bullying someone on the playground • Cyber Safety Lessons which incorporate social behaviour tips to protect children from online dangers, such as cyber-predators, harassment, unwanted communications and cyber-bullies • Cyber Security Lessons which provide information on how to secure computers, identities and financial information http://www.itnews.com.au/News/59257,...ne-safety.aspx  You've reached this page because the site you were trying to visit now blocks the FireFox browser. The Mozilla Foundation and its Commercial arm, the Mozilla Corporation, has allowed and endorsed Ad Block Plus, a plug-in that blocks advertisement on web sites and also prevents site owners from blocking people using it. Software that blocks all advertisement is an infringement of the rights of web site owners and developers. Numerous web sites exist in order to provide quality content in exchange for displaying ads. Accessing the content while blocking the ads, therefore would be no less than stealing. Millions of hard working people are being robbed of their time and effort by this type of software. Many site owners therefore install scripts that prevent people using ad blocking software from accessing their site. That is their right as the site owner to insist that the use of their resources accompanies the presence of the ads. While blanket ad blocking in general is still theft, the real problem is Ad Block Plus's unwillingness to allow individual site owners the freedom to block people using their plug-in. Blocking FireFox is the only alternative. Demographics have shown that not only are FireFox users a somewhat small percentage of the internet, they actually are even smaller in terms of online spending, therefore blocking FireFox seems to have only minimal financial drawbacks, whereas ending resource theft has tremendous financial rewards for honest, hard-working website owners and developers.. Since the makers of Ad Block Plus as well as the filter subscriptions that accompany it refuse to allow website owners control over their own intellectual property, and since FireFox actively endorses Ad Block Plus, the sites linking to this page are now blocking FireFox until the resource theft is stopped. Netscape users can simply set their browser to IE mode to continue to enjoy the site that sent you here. FireFox users can use Internet Explorer, Opera or Netscape (in IE mode) to access it. FireFox users also have the option of using the IE Tab plug-in which uses the IE rendering engine to display pages, but also disables the Ad Block Plus plug-in. If you are offended by the Mozilla Corporation's endorsement of dishonesty please contact the Mozilla Foundation and ask them to stop empowering internet theft. http://whyfirefoxisblocked.com/ Or you could send them a donation for the great job they’re doing blocking distracting and dishonest advertising, and by the way if you’re like me and you use Opera as the FF hating writer suggests, right-clicking allows you to target-block any content, including ads on the above author’s pages. – Jack  Wall Street Hopes Flotation of the 'New Google' Will Help Battered Stock Market Richard Wray A Californian technology company US investors are already dubbing "the new Google" will this week finalise the price of its shares in one of the US market's most eagerly awaited flotations since the dotcom boom. After just over a week of investor road shows, VMware, based in Palo Alto, has already raised the price expected in its flotation on the New York Stock Exchange to between $27 (£13.40) and $29 from its original forecast of $23 to $25. At those levels the company could be worth more than $10bn. But some analysts on Wall Street believe the stock could rise to $40 or more at its opening, which could come as early as today. VMware is majority owned by the US data storage and security group EMC, but leading technology companies have recently been buying stakes. Last month Intel spent $218.5m buying shares that will give it a 2.5% stake in the business after the flotation. The internet networking company Cisco then bought 6m shares in the company for $150m, also giving it a small stake. The company has been cited by Microsoft as a potential competitor and at one point was seen as a possible takeover target for the software market leader. VMware is at the forefront of a new segment of technology called virtualisation. Rather than having software installed on an individual computer or server, where it is often vulnerable to viruses and other forms of attack unless updated regularly, virtualisation separates the hardware from the software. This means one computer or server can run various different programs - even operating systems - on the same machine. It is an updated version of the application service provider (ASP) model, which was popular in the dying days of the last dotcom boom. But while the ASP model meant merely hosting a personal computer's software on servers on the internet, virtualisation software actually sits between a computer or server's operating system and the actual hardware. As a result, sensitive parts of any system can be partitioned so that viruses and other "malware" cannot infiltrate. The "virtual" machine that is created can then be easily transferred between different computers, letting companies provide staff who "hot desk" or travel with secure access to exactly the same programs anywhere in the world. The technology makes it cheaper for large companies to run their IT systems as servers that may sit idle for hours or be under-utilised at specific times can be used for several different purposes at the same time. Virtualisation is also a hot topic for companies that supply major organisations with their IT networks, as these organisations are able to shift virtual machines around the world only if they have designed their networks correctly. VMware was founded in 1998 and bought by EMC six years later. It has more than 3,000 employees and counts all of the Fortune 100 companies among its clients. Last year it made revenues of $704m and is expected to make well over $1bn this year as sales increase. In last month's second-quarter figures from EMC, VMware reported revenues for the three months to the end of June of $296.8m, up from $156.4m in the same period in 2006. The company reckons it will make about $870m from the flotation and will use $350m to pay off debt it owes EMC. A successful flotation of VMware would be a major boost to the US stock market, which has been battered over the past weeks by the turmoil in the international credit market. VMware has Citigroup, JP Morgan and Lehman Brothers as the lead underwriters for the offering. http://business.guardian.co.uk/story...eed=technology  Lawsuit: Music Publishers v. YouTube Doesn’t Solve the Problem Shelly Palmer The National Music Publishers Association (NMPA) has joined an existing lawsuit accusing YouTube of copyright infringement. Since their purchase of YouTube, it has been open season on Google. Rights-holders know that Google is truly made-of-money and aggrieved content owners now have a target with very deep pockets to sue. Lawsuits will not solve the problem, which is: there is no easy way to identify who owns which rights in and to most pieces of music and there is no easy way to get a quote and pay them. If you don’t believe me, pick up the phone and call a recorded music company, publisher, performing rights society or someone else you think might administrate the rights you seek and tell the person who answers the phone you want to purchase public performance rights for a particular song. Good luck. Maybe, if you retain a special music clearance firm or seasoned entertainment attorney, you can complete the process of obtaining the rights to use a particular song in sync with a video you want to put online. But, even if you are successful, the process can take days or weeks and cost thousands in attorney’s fees (over and above the negotiated cost of the rights you seek). While we are on the topic, what rights should you be seeking in the first place? Let’s review: • Master Rights - the physical master recording (audio and video). These rights are usually owned by the producer, record company or movie studio that paid for the production. You must negotiate with them to use the work. • Mechanical Rights – the 9.1 cents per cut on a CD or per download that is compulsory under the current copyright laws (it is usual and customary to only realize approximately 60 percent of this amount on any give mechanical royalty) These rights are usually negotiated for and collected by The Harry Fox Agency, although they can also be negotiated independently. These royalties are usually divided up by the record company, the publisher(s), the producers, performers, composers and other interested parties. • Public Performance Rights – if the work is broadcast or streamed over the public Internet, you are entitled to your personally negotiated fee or, if you are so inclined, you may be non-exclusively represented in the USA by one of three performing rights societies, ASCAP, BMI or SESAC. Although the split is often the subject of negotiation, traditionally composers and their publishers split these fees 50/50. And, for the most part publishing companies administer and, therefore negotiate with people who wish to use the work. • Sync Rights – if the work is a piece of music that is synchronized to a piece of video (title music, theme music, background music, music for a music video, music for a film or TV show, etc.) you are entitled to a fee. Although the split is often the subject of negotiation, traditionally composers and their publishers split these fees 50/50. And, for the most part, publishing companies administer and therefore negotiate with people who wish to use the work. • Royalty Payments to Unions & Guilds – If union performers have contributed to the work (singers, musicians, etc.) there are residual payments to be made. And, even if the performers are independent, they may still be entitled to a share of the profits from their creative contributions. This depends, of course, on how egregious the terms of the non-union performers’ contracts were with the original producers of the work. Note: The list above contains the most common types of music rights. There are others such as folio, parody, moral, etc. For a complete list, contact your favorite entertainment lawyer. What to do? Well, it would be nice if the music publishing industry would invest in some database software, web interfaces, email and Adobe Acrobat. Most deals are done with fax machines and, to tell you the truth, it’s like working with stone axes and bear skins. I just obtained the rights to a very popular song for a client from the largest publisher in the world. The deal was done with paper faxes and the form was annotated in magic marker so you could read it after it had be sent back and forth six times. This would actually be funny if it weren’t true. It would also be nice if the metadata associated with files on the major download sites had rights-holder information, as opposed to useless phrases like, “Copyright 1997 Warner Bros. Music.” Go ahead, call the Warner Bros. switchboard and ask for the person in charge of public performance rights for that particular song. If you’re lucky, you will get someone on the phone who will tell you that you have to call the publisher to make a public performance deal, who is … umm … errr … who? But I’m giving credit where it’s not due. There’s no way that you get that far with a call to the main switchboard of any major recorded music company. If people don’t know what rights they need to obtain and if there’s no easy way to obtain them even if they do know, exactly what do rights-holders expect? More to the point, how does suing YouTube help solve the problem? They don’t synchronize music to video, they simply distribute other people’s works. How about spending some time and energy building the music licensing business of the present. Hey music publishers — it’s 2007! On your way to the courthouse, hop on over to Best Buy and pickup a computer or two and a book on database management and search engine optimization? That would really help. http://www.shellypalmerblog.com/?p=500  YouTube Seeks Testimony of Comics Stewart and Colbert Comedians Jon Stewart and Stephen Colbert, whose programs were once among the most viewed on YouTube, were requested by the video site to give testimony in legal proceedings as it fights a $1 billion lawsuit by Viacom Inc, according to court filings. The two hosts of the Viacom hits "The Daily Show" and "The Colbert Report" were listed as numbers three and four out of 32 people called by YouTube to give a deposition in Viacom's case against it and parent Google Inc, according to a document filed in the U.S. District Court for the Southern District of New York last week. Viacom Executive Chairman Sumner Redstone is number 8 on YouTube's list. Viacom Chief Executive Philippe Dauman and general counsel Michael Fricklas top the list. At the head of Viacom's list are Google founders Larry Page and Sergey Brin and Chief Executive Eric Schmidt. Viacom sued Google and YouTube in March after failing to reach a distribution agreement. Viacom said YouTube carried the entertainment company's programs on its site without permission. Since then, hundreds of thousands of Viacom clips, many of which feature the two comedians, have been removed from the Web's top online video service. At the time, Viacom said its Comedy Central shows were among the most viewed video clips on YouTube's service overall, which allows users to upload material. Ahead of the suit, Colbert had even urged fans to make him a star on sites like YouTube. Google has said it abides by existing laws that protect Internet services from the content uploaded by users, so long as it promptly takes down copyrighted materials that were placed there without permission after being notified. (Reporting by Kenneth Li) http://www.reuters.com/article/enter...41417520070814  Fine Threat Over T-Shirt Slogan BBC A man spotted wearing a T-shirt bearing an "offensive" slogan in a city centre has been warned he risks an £80 fine if he is caught again. Forklift driver David Pratt was told by street wardens in Peterborough he could cause offence or incite violence. The slogan on the garment read: "Don't piss me off! I am running out of places to hide the bodies." Peterborough City Council said using insulting or offensive language was an offence, even if it appeared in print. Mr Pratt, 46, an American living in Peterborough, was approached by the wardens as he waited for a bus with his wife Elly. "It is insane. I have worn it in the city centre hundreds of times", said Mr Pratt, whose wife bought him the T-shirt in Venice Beach, California. "Most people who see it just chuckle. Some people have even stopped me to tell me they like my T-shirt. "We have put this incident online on several blogs and 90% of people who have commented said they found it hilarious or that I should have the right to wear it wherever I like." Asked whether he would wear the T-shirt again, Mr Pratt replied: "I am wearing it now. If I get a written apology I will wear it in the city centre again." He continued: "It's a bummer because I like the shirt, but I am trying to get citizenship but if I get a fine I can kiss citizenship goodbye." He added: "I really don't see how the wording on my T-shirt could incite violence - it's humour, that's all it is." In a statement, Peterborough City Council said: "The incident is the subject of an official complaint to the council and is currently under investigation. "However, using offensive, abusive, or insulting language is an offence under the Public Order Act, which also applies to such language appearing in print. "In what was an amicable conversation, the street warden advised the gentleman concerned that his T-shirt could cause offence and if he was to wear it again he could run the risk of being issued an £80 on-the-spot fine from the police." http://news.bbc.co.uk/go/pr/fr/-/2/h...re/6943734.stm  Our Lives, Controlled From Some Guy’s Couch John Tierney Until I talked to Nick Bostrom, a philosopher at Oxford University, it never occurred to me that our universe might be somebody else’s hobby. I hadn’t imagined that the omniscient, omnipotent creator of the heavens and earth could be an advanced version of a guy who spends his weekends building model railroads or overseeing video-game worlds like the Sims. But now it seems quite possible. In fact, if you accept a pretty reasonable assumption of Dr. Bostrom’s, it is almost a mathematical certainty that we are living in someone else’s computer simulation. This simulation would be similar to the one in “The Matrix,” in which most humans don’t realize that their lives and their world are just illusions created in their brains while their bodies are suspended in vats of liquid. But in Dr. Bostrom’s notion of reality, you wouldn’t even have a body made of flesh. Your brain would exist only as a network of computer circuits. You couldn’t, as in “The Matrix,” unplug your brain and escape from your vat to see the physical world. You couldn’t see through the illusion except by using the sort of logic employed by Dr. Bostrom, the director of the Future of Humanity Institute at Oxford. Dr. Bostrom assumes that technological advances could produce a computer with more processing power than all the brains in the world, and that advanced humans, or “posthumans,” could run “ancestor simulations” of their evolutionary history by creating virtual worlds inhabited by virtual people with fully developed virtual nervous systems. Some computer experts have projected, based on trends in processing power, that we will have such a computer by the middle of this century, but it doesn’t matter for Dr. Bostrom’s argument whether it takes 50 years or 5 million years. If civilization survived long enough to reach that stage, and if the posthumans were to run lots of simulations for research purposes or entertainment, then the number of virtual ancestors they created would be vastly greater than the number of real ancestors. There would be no way for any of these ancestors to know for sure whether they were virtual or real, because the sights and feelings they’d experience would be indistinguishable. But since there would be so many more virtual ancestors, any individual could figure that the odds made it nearly certain that he or she was living in a virtual world. The math and the logic are inexorable once you assume that lots of simulations are being run. But there are a couple of alternative hypotheses, as Dr. Bostrom points out. One is that civilization never attains the technology to run simulations (perhaps because it self-destructs before reaching that stage). The other hypothesis is that posthumans decide not to run the simulations. “This kind of posthuman might have other ways of having fun, like stimulating their pleasure centers directly,” Dr. Bostrom says. “Maybe they wouldn’t need to do simulations for scientific reasons because they’d have better methodologies for understanding their past. It’s quite possible they would have moral prohibitions against simulating people, although the fact that something is immoral doesn’t mean it won’t happen.” Dr. Bostrom doesn’t pretend to know which of these hypotheses is more likely, but he thinks none of them can be ruled out. “My gut feeling, and it’s nothing more than that,” he says, “is that there’s a 20 percent chance we’re living in a computer simulation.” My gut feeling is that the odds are better than 20 percent, maybe better than even. I think it’s highly likely that civilization could endure to produce those supercomputers. And if owners of the computers were anything like the millions of people immersed in virtual worlds like Second Life, SimCity and World of Warcraft, they’d be running simulations just to get a chance to control history — or maybe give themselves virtual roles as Cleopatra or Napoleon. It’s unsettling to think of the world being run by a futuristic computer geek, although we might at last dispose of that of classic theological question: How could God allow so much evil in the world? For the same reason there are plagues and earthquakes and battles in games like World of Warcraft. Peace is boring, Dude. A more practical question is how to behave in a computer simulation. Your first impulse might be to say nothing matters anymore because nothing’s real. But just because your neural circuits are made of silicon (or whatever posthumans would use in their computers) instead of carbon doesn’t mean your feelings are any less real. David J. Chalmers, a philosopher at the Australian National University, says Dr. Bostrom’s simulation hypothesis isn’t a cause for skepticism, but simply a different metaphysical explanation of our world. Whatever you’re touching now — a sheet of paper, a keyboard, a coffee mug — is real to you even if it’s created on a computer circuit rather than fashioned out of wood, plastic or clay. You still have the desire to live as long as you can in this virtual world — and in any simulated afterlife that the designer of this world might bestow on you. Maybe that means following traditional moral principles, if you think the posthuman designer shares those morals and would reward you for being a good person. Or maybe, as suggested by Robin Hanson, an economist at George Mason University, you should try to be as interesting as possible, on the theory that the designer is more likely to keep you around for the next simulation. (For more on survival strategies in a computer simulation, go to www.nytimes.com/tierneylab.) Of course, it’s tough to guess what the designer would be like. He or she might have a body made of flesh or plastic, but the designer might also be a virtual being living inside the computer of a still more advanced form of intelligence. There could be layer upon layer of simulations until you finally reached the architect of the first simulation — the Prime Designer, let’s call him or her (or it). Then again, maybe the Prime Designer wouldn’t allow any of his or her creations to start simulating their own worlds. Once they got smart enough to do so, they’d presumably realize, by Dr. Bostrom’s logic, that they themselves were probably simulations. Would that ruin the fun for the Prime Designer? If simulations stop once the simulated inhabitants understand what’s going on, then I really shouldn’t be spreading Dr. Bostrom’s ideas. But if you’re still around to read this, I guess the Prime Designer is reasonably tolerant, or maybe curious to see how we react once we start figuring out the situation. It’s also possible that there would be logistical problems in creating layer upon layer of simulations. There might not be enough computing power to continue the simulation if billions of inhabitants of a virtual world started creating their own virtual worlds with billions of inhabitants apiece. If that’s true, it’s bad news for the futurists who think we’ll have a computer this century with the power to simulate all the inhabitants on earth. We’d start our simulation, expecting to observe a new virtual world, but instead our own world might end — not with a bang, not with a whimper, but with a message on the Prime Designer’s computer. It might be something clunky like “Insufficient Memory to Continue Simulation.” But I like to think it would be simple and familiar: “Game Over.” http://www.nytimes.com/2007/08/14/sc...tier.html?8dpc  Books A World Without Humans? It All Falls Apart Janet Maslin THE WORLD WITHOUT US By Alan Weisman 324 pages. Thomas Dunne Books/St. Martin's Press. $24.95. The abundant doomsday plotlines in “The World Without Us” make it a useful conversation piece, if a grim one. Traveling down many different avenues of scientific research, Alan Weisman postulates the complete disappearance of mankind from planet Earth. Then he extrapolates about what would happen without us. By his estimate most of our leavings would rot and crumble; much of our damage would take eons to undo. There’s one tiny bit of good news. Depleted sea species might recover if we would do them a favor and go away. Over all, this book paints a punishingly bleak picture. Entries in its index indicate the scope of its pessimism. For instance: “Birds, plate glass picture windows and”; “Central Park, coyotes in”; “Earth, final days”; “Embalming, arsenic and”; “Human race, robots and computers as replacements”; “Great Britain’s shoreline, rubbish along”; “PCBs, and hermaphroditic polar bears.” “Dessication,” “Meltdowns” and “Slash-and-burn” also play their roles here. Mr. Weisman speaks to the darkest parts of our collective imagination as well as some of the strangest. Consider the lowly exfoliant. These lotions contain tiny plastic particles that are meant to scrub. But they wind up fulfilling other purposes, like clogging the innards of the tiny sea creatures that ingest them. This book cites research on bottom-feeding lugworms, barnacles and sand fleas as evidence of the damage the particles do. All three species became terminally constipated from ingesting this man-made microlitter. Very early in the book Mr. Weisman makes his argument personal by describing how a house would fall apart. Your house. “Back when they told you what your house would cost, nobody mentioned what you’d also be paying so that nature wouldn’t repossess it long before the bank,” he writes. As with many of the book’s other conclusions, this one is accompanied by a hint of unseemly glee. The more elaborately Mr. Weisman paints a worst possible outcome, the better he has made his case. And the more triumphant he sounds. It is one thing to imagine one house with a leaking roof, burgeoning mold, rusting nails, broken windows and small animals gnawing on the drywall. But this book hypothesizes more avidly about decay on a grander scale. When Mr. Weisman wonders what would happen to New York City, he foresees rewilding (the return of wolves and bears), plants forcing their ways through the sidewalk and water damage to the underground infrastructure. “Before long, streets start to crater,” he writes, with scarily apt foresight. “As Lexington Avenue caves in, it becomes a river.” Lexington Avenue has lately shown us what he means. This book’s global-scale dismay about humanity’s environmental impact is its most important theme. But it’s Mr. Weisman’s more marginal facts that give “The World Without Us” so much curiosity value. Which would last longer in storage: a) money in a vault, or b) paintings in a museum? Bear in mind that museums might have skylights that could leak, basements that could flood and larvae of the black carpet beetle. And choose a third option: c) ceramics, since they are chemically similar to fossils. Ancient ceramics have a built-in advantage because they have already withstood the test of time. When it comes to antiquity Mr. Weisman can draw on tangible evidence to back up his speculation. He marvels at the scope and durability of the large underground city of Derinkuyu in Cappadocia, Turkey, especially in comparison to showier monuments with less staying power. There is also hope for the endurance of Mount Rushmore and for Egypt’s Khufu pyramid, although the latter “should not look very pyramidal at all” a million years from now. “The Panama Canal,” on the other hand, “is like a wound that humans inflicted on the Earth — one that nature is trying to heal,” according to a superintendent of its locks on the Atlantic side. And a disintegrating coral reef in the Pacific is on “the slippery slope to slime.” From the gyre that is the Great Pacific Garbage Patch to the flower-growers of Kenya to the Rothamsted Research Archive in Britain, a repository for more than 300,000 soil samples, Mr. Weisman covers a huge amount of terrain. His research is prodigious and impressive. So is his persistence, even though he knows full well about the carnage our cellphone transmission towers inflict on unsuspecting birds and the ill effects that embalmed human corpses have on soil. Compared with the founder of Vhemt — the Voluntary Human Extinction Movement, a group with the motto “May we live long and die out” — Mr. Weisman is a veritable beam of sunshine. “The World Without Us” has an arid, plain, what-if style and an air of relentless foreboding. The book is coaxed from subject to subject by ominous transition phrases. (“But that wouldn’t be the biggest problem” is a typical one.) Its delivery of bad news is strangely uniform in tone, given the vast difference in scale among the catastrophes anticipated here. The threats posed by condominium-buying British retirees to the island of Cyprus, or by the “serial killers” that are common house cats, aren’t nearly as grave as what could happen to the oil fields and pipelines of Houston if they went unattended. In Houston, without man, there would be “a race to see whether their bottoms corrode first, spilling their contents into the soil,” writes Mr. Weisman, “or their grounding connectors flake away.” That is, poison or explosion. http://www.nytimes.com/2007/08/13/books/13masl.html  Review Hitachi's Deskstar 7K1000 Hard Drive  The Terabyte has landed Geoff Gasior IMAGINE ONE THOUSAND thousand thousand thousand bytes. A terabyte, if you will. But more than just that—a milestone in storage capacity that hard drive manufacturers have been chasing for years. After more than a decade of living in a world of gigabytes, the bar has finally been raised by Hitachi's terabyte-capacity Deskstar 7K1000. Being first to the terabyte mark gives Hitachi bragging rights, and more importantly, the ability to offer single-drive storage capacity 33% greater than that of its competitors. Hitachi isn't banking on capacity alone, though. The 7K1000 is also outfitted with a whopping 32MB of cache—double what you get with other 3.5" hard drives. Couple that extra cache with 200GB platters that have the highest areal density of any drive on the market, and the 7K1000's performance could impress as much as its capacity. Has Hitachi achieved a perfect balance of speed and storage with its Deskstar 7K1000? We've tested it against nearly 20 competitors—including its closest 750GB rivals from Seagate and Western Digital—to find out. http://www.techreport.com/reviews/20...0/index.x?pg=1  Selling Television Sets by Turning Up the Glamour Eric Pfanner WHILE audiences might have to wait until autumn to see “My Blueberry Nights,” the first English-language feature from the Hong Kong director Wong Kar-wai, they can catch a shorter film from Mr. Wong while shopping for fashionable clothing or jewelry in Paris. The five-minute film is actually an advertisement for a new television from Philips Electronics, a high-end flat-screen model called Aurea. The film, a spy story shot in Shanghai, will be shown in the Paris boutiques of the fashion label Lanvin and the jeweler Lorenz Bäumer — on Aurea televisions, of course. The decision to produce a short film with an art-house director like Mr. Wong shows how brands are trying to break away from their reliance on 30-second television spots, which some marketers fear have lost their effectiveness. Now, even televisions are being marketed without recourse to television. Meanwhile, the move by Philips to involve luxury goods purveyors like Lanvin and Bäumer reflects a desire by consumer electronics companies to differentiate their products in an intensely competitive marketplace by trying to give them some of the glamour of the fashion business. “The idea is to be more exclusive, to be very different from your traditional kind of advertising,” said Sandrine Huijgen, marketing director for consumer electronics at Philips. “We don’t see Dior advertising a lot on television.” Philips said it might run a few television spots in markets where it cannot be avoided. But most of the $68 million that Philips expects to spend in Europe through the end of the year will be used in other media, said Rudy Provoost, chief executive of the consumer electronics division. In early August, for instance, the Aurea campaign got under way with a seven-page insert in Vogue in Britain. The print ads, shot by a fashion photographer, Vincent Peters, show a model cozying up to a brightly lighted Aurea screen that mirrors her image. Instead of technobabble about HDTV, L.C.D. or plasma screens, the ads include only the Philips and Aurea names and the tag line: “Simplicity is a light that seduces the soul.” “There is a lot of female coding in this advertising,” said Laura Jones, global client managing director at the advertising agency DDB, a unit of Omnicom Group, which worked on the Aurea campaign along with the media planning agency Carat. “Before, televisions have always been sold based on pixels or that sort of thing.” Philips is not alone in moving away from a masculine approach to selling consumer devices, embracing the presumably more female world of fashion. LG, the South Korean electronics company, is selling a mobile phone under the Prada brand name. The Samsung ads for high-end televisions play up the sleek design of the products, sometimes by way of models in slinky black dresses. Sony, meanwhile, has raised the bar for high-concept advertising in the television market with an international campaign for its Bravia flat-panel sets. The first ad in the series, which has not been shown in the United States, featured tens of thousands of colorful rubber balls bouncing through the streets of San Francisco. A second ad showed buckets of paint splattering against a housing project in Glasgow. A new ad in the campaign was shot in early August in New York using brightly colored rabbits made out of modeling clay. The Bravia campaign has attracted a great deal of attention on the Internet, even in the United States, where a separate television campaign has been used. While the Aurea campaign focuses on the sets’ use of light, Sony plays up the Bravia’s rendition of color. Philips trails Sony and Samsung in the market for flat-panel L.C.D. televisions like the Bravia and the Aurea. Samsung had 16.8 percent of the market in the first quarter of 2007, compared with 12.6 percent for Sony and 12.2 percent for Philips, according to iSuppli, a market research firm. With its unusual ad campaign for the Aurea, can Philips close the gap? In the film by Mr. Wong, a female agent sent to kill a character named Light is instead seduced by him. Now, Philips must hope that not too many customers get similarly sidetracked — spending their money on Lanvin fashions or Bäumer jewelry instead. http://www.nytimes.com/2007/08/14/bu...ia/14adco.html  In depth Windows Is Free The impact of pirated software on free software Dave Gutteridge A recent column on Zdnet, by Adrian Kingsley-Hughes, discussed the reasons why people won't change from a retail operating system to a free one. The implication is that Linux can't even give away their software. That sounds pretty dire. Windows retails for around 200 US dollars, give or take depending on which version and where you buy. If the above statement by Mr Kingsley-Hughes was true, it means that Linux is so bad that people would gladly pay 200 dollars to avoid it. Do users really think Linux is that lame? This article is not to defend Linux and counter the points that Mr Kingsley-Hughes made. Instead, the intention here is to simply use his article as a starting point to discuss in depth an issue which, so far as I've ever seen, is missing almost entirely from the debate over Windows versus Linux versus Mac. Mr Kingsley-Hughes gives five essential points to explain what is so bad about Linux that it can't even succeed for free. On the whole, users aren't all that dissatisfied with Windows (I agree). Too many different versions of Linux (I sort of agree). People want certainty that hardware and software will work (I agree that's what people want, but I don't read the situation the same way that Mr Kingsley-Hughes does). As far as most people are concerned, the command line has gone the way of the dinosaur (It has for me, I love the GUIs. But, I'll get into this more below). Linux is still too geeky (Linux developers are still too geeky, sure. I totally agree that the people mainly developing and advocating Linux often don't see users' needs the way users see their needs.) All the above reasons have some truth in them, but consider how the price comparison makes those points seem so much worse. I Certainly Wouldn't Use Linux if it was as Bad as All That Take the point that Linux relies too heavily on command line interface. I would probably pay 200 dollars for a nice graphical interface instead of having to run my computer at the command line all the time. But would I pay 200 dollars instead of using an interface that had nice graphics 99% of the time, and a command line for the occasional configuration? I think I'd rather spend that 200 bucks on something else, like maybe a new MP3 player. Throw in the fact that every few years I'll have to spend another hundred bucks or so on upgrades, and I'll handle the 1% of command line time. When you add in the fact that I might, just maybe, be making a one-for-one trade of blue error screens for command line issues, then I'm definitely leaning towards not spending 200 bucks. As I type this article, I'm using OpenOffice, a free equivalent of Microsoft Office, on Ubuntu Linux, which has a very slick graphical user interface. Much like Windows Vista, I can spin around my desktop, make my windows go all wobbly when I move them. I love nice graphics and I'm no fan of obscure command line code. I certainly don't feel like I opted for a world of command line frustration. Neither does my girlfriend, who makes a better example, since she's the type of user who all of us computer experts mean when we say "user". Her Compaq laptop, which had a pre-installed version of Windows XP, would die and go into the Blue Screen Of Death every time it tried to go into sleep mode. She asked if I could fix it. I said I could, but it would mean a change in interface. Of course, I was speaking about installing Linux. I didn't tell her about Linux or open source or free software, not because I was trying to be clever. I didn't tell her because she doesn't care. She wants to be able to log into Hotmail, transfer songs to her MP3 player, and watch Youtube. She doesn't care whether all this happens on Windows or whatever. Now she uses Ubuntu, and she never, ever, touches the command line. Of course, she comes to me if she can't do something, like change her desktop background. But she came to me for instructions on what to do with Windows too, so she's just as well off in Linux as she was in Windows. At the same time, I'm not going to tell you that in the two years since I switched from Windows to Ubuntu that I have been able to do everything with a graphical user interface. I tend to be a lot more demanding of my computer than my girlfriend is, so I'm pushing the bleeding edge in order to make things work exactly as I want. I've had all sorts of set up issues, from my Wacom tablet to my SD card reader, to my dual monitors, and more. And personally, I don't really know much about the command line in Linux, or want to, so every time there was a problem I asked for help on my local Linux user group and they helped me get it all working in the end. My point, however, is that while I have had my share of hassles, the vast majority of my time in front of my computer is just doing uncomplicated stuff that requires no command line. More than 99% of my time on Linux is spent in a nice graphical interface that is, in my opinion, better than Windows. Why would I pay 200 bucks, plus future fees, to save myself that 1% of hassle? Can Windows really claim to be 100% hassle-free anyway? Is it really worth 200 US dollars more? Keep in mind that when you're saying that Windows is worth 200 dollars more than Linux, you're saying the differences are worth that much, not the whole thing. So if you can check your email on both, surf the web on both, listen to music on both, do spreadsheets on both, but only play 3D computer games on Windows, then what you're saying is that 3D computer games alone are worth 200 dollars to you. That may be fair enough in the case of playing games. I know gamers who would gladly pay 200 dollars more for the right gaming environment. But once I had someone tell me that they didn't want to switch to Linux because their printer model wasn't supported. Their printer was a little older and would have been easy to upgrade to a newer, Linux compatible model, for about 120 dollars. So, they were effectively trying to claim that they would rather pay 200 dollars in order to save themselves from paying 120 dollars. Which is obviously a claim that can only be made by a sane person if they're really bad at math, or their copy of Windows wasn't actually 200 dollars. The Elephant in the Room The fact is that there's a distortion in the idea that Linux can't be given away. There's something wrong in the idea the price difference between Windows and Linux is representative of the actual quality difference. There's an elephant in the room that no one is talking about. Windows is free. I'm not talking about the fact that Windows comes pre-installed in most computers, with its price hidden in the cost of the hardware. That contributes to the idea of Windows being free, but that's not the elephant in the room. The elephant in the room that no one is talking about is cracked software. People treat Windows as being free not because they didn't have to buy the copy that came with their computer. People think of Windows as free because when they need a copy, they can get it from a guy they know. Someone has a copy they can just burn to a CD for you. Or you can get it on the peer-to-peer networks. How pervasive is cracked software? That's of course hard to quantify. No one is going to set down in any kind of public record that they use cracked software. Which is probably why it's notably absent from so much debate about operating systems. So any estimate is speculative, based on extrapolation from indirect data. Look, for instance, at the file sharing networks. You can log on almost any Bittorrent web site, at any time of the day, and there will be thousands of people participating in the sharing of Windows Vista. Or XP. Or whatever version you want. How many people are therefore using cracked copies of Windows? I have no idea, except that it's a lot. With that in mind, let's take a little time to really explore the impact of free. How Tempting Should Free Be? Recently, when shopping for a portable music player, I narrowed down the possibilities to two main choices. One was the iPod Nano, the other was the iAudio player by Cowon. You may not have heard of that second brand. I certainly hadn't until I started shopping around for portable players. The Cowon iAudio was cheaper, by about 20%. It actually played more file formats, but there was an issue of brand familiarity that made me hold back a bit. I gave it about a day to be sure I wanted to buy it. In the end, price trumped other considerations. The Cowon iAudio was good enough, and cheaper. To arc closer towards towards my point, consider what the difference would be if the iAudio had been completely free. I can tell you how it would have influenced my decision. I would have taken it home immediately, not even a moment's delay. Brands and design be damned, I would have taken the free option. If one music player were free and another one expensive, the gap in quality would have to be huge to justify paying for the one with the price tag. Is the difference between Linux and Windows really that big? Above I said that 99% of the time I use a nice graphical interface in Linux that I think is better than Windows. And in the 10 or more years I used Windows before switching, I know that Windows gave me enough of the famous Blue Screen Of Death to balance out the occasional need to go to the command line that Linux imposes on me. As far as I'm concerned, I think the two are on equal ground. When you compare all the good points of Windows, Linux, and Mac, and the bad points of blue error screens, command lines, and little bomb icons, the difference is close enough to keep the hardcore zealots arguing for hours. But you and I aren't zealots, we just want to do stuff with our computers like look at YouTube and get email. So we won't nitpick about features. Instead, even though I think Linux is just as good as Windows, maybe even better, I'll propose for the sake of argument that Linux is 80% to 90% as good as Windows. As I said about the Cowon iAudio compared to the iPod, it's close enough for me to not want to spend the difference. If we can agree on the concept of close enough, let's turn to other consumer products again. We expect that market forces will shape prices so that, so long as it's still profitable, a product that is slightly inferior in features or quality will be priced less than a product of more quality and features. This isn't always true, but it's an okay starting point. It's a believable idea that some companies can stay competitive by lowering their price to stay on the market alongside slightly better quality products. Consumers only have so much money to go around, and will often trade off quality for a good price. In fact, some companies engage in a practice called "dumping" where they lower their price drastically so that they aren't even making a profit. They do that because if they can cheapen their product enough, consumers will overlook a lot of deficiencies and cast aside brand loyalties in favour of price. Then, when the company has a foothold in the marketplace, they can slowly try to increase their prices and quality, with the aim of eventually turning a profit. The Inevitable Comparison With Cars In around 1988, the Korean car company Hyundai gained entry into the US and Canadian car market with this practice, and although they got called on it (dumping is technically illegal), in the long run the strategy seems to have worked. It's strong evidence that price will trump differences in quality. Imagine for a second that Hyundai had made their cars available for free. There would not have been one Hyundai left in the show rooms. Just about everyone would have one. I would have got one. Wouldn't you? I mean, a Hyundai was at the time definitely not the same quality as similar Toyota and Honda models, but would that have mattered? I mean, come on. A free car is a free car. My contention is that if a product can gain entry into a marketplace by lowering its price to increase its appeal, then a free product that is close enough in quality to its priced competitors should spread like wildfire. And yet, that has not happened with Windows and Linux. 200 US dollars is enough money to give most, if not all, consumers pause as to whether or not they can or should fit it into their budget. I can definitely appreciate having an extra 200 US dollars in my wallet. Remember the concept of close enough for free. What if those free Hyundai cars came without radios, and didn't even have any dashboard space to install one? I'd still get one. Wouldn't you? Free. And close enough. What if Hyundai had made their cars free, but didn't advertise? I imagine the rate of consumption of Hyundai cars would have started slower. Even so, it strikes me as inevitable that word of mouth would have eventually compensated until every single cash-strapped teenager with a new driver's license was out on the road with their new, free, Hyundai. Suppose Hyundai didn't offer a warranty or service of any kind. Now would you refuse their free cars? I don't know about you, but free is still a pretty big trump card for me. So long as the product I was picking up for free did not fail so poorly in its task as to cause harm or be completely useless, I would pick it up. And yet, returning from the Hyundai analogy to the Linux reality, free Linux has not swept the market and become a large chunk of the marketplace. And I'm not even speculating on Linux suddenly becoming dominant. I'm just saying, it would have a big chunk of the market. Dare I say more than the Mac? Hopefully the points I've made above have precluded the idea that Linux is not spreading faster simply because Linux falls down on some technical point. If I haven't drilled in my point enough already, here it is again. Linux is close enough to any other major operating systems that its price should have made it irresistible to a huge segment of consumers. There are enough consumers out there for whom 200 dollars is worth keeping, and whose computer needs would be easily met with Linux. But they use Windows, because they were able to do so and keep their 200 US dollars. I'm Not Going To Name Names Intellectually, people know Windows is not really for free, of course. And some people do actually buy the packaged Windows CDs in a box. Some even line up all night outside of the stores when the next version comes out. But, I can't help but notice that among all my friends, all sorts of people I know from various walks of life, almost no one has paid for it. They usually know a guy who gives them a copy. They don't really ask where it's from. My friend bought a used laptop and it had Windows on it already. Not to mention it had the latest Adobe Creative Suite and Microsoft Office. All that, for about 300 US dollars. Did that price really include the software? Did the seller need to be compensated for anything other than the laptop? I know that all that software is cracked, but whether my friend thought about it or not, he didn't go out of his way to ask. I started to perceive this issue of Windows being for free shortly after switching to Linux. Of course, I knew cracked copies of Windows existed when I was using Windows. But the market implications didn't have any bearing on me until I started using completely legally free software that was as good or better than the costly alternatives, and wondering why more people weren't making the same choice. It became obvious to me when I would recommend Linux to people. As that "computer guy" who friends call up for technical advice, the opportunity to suggest using Linux instead of Windows comes up often enough. Since most of my friends do very basic things like surf the web, check email, and word processing that any operating system would handle just fine, Linux would be a reasonable choice. I would talk about how they could do everything they were already doing, but for free. But the look in their eyes at the mention of the word free was clear. They already had a free operating system, so they weren't impressed by switching to something else that was free. How do I know that's what the look in their eyes meant? Because it wasn't the look in their eyes that would have been there if I had offered them a free MP3 player or some other consumer good that can't be simply copied and shared. Here's another example. One time, a friend called me with an offer. He would pay me 50 bucks to get his laptop working again. Specifically, what he wanted was to back up all his data, reformat his disk, re-install Windows, and then restore his data. I asked if he still had the original install disks for Windows. He stammered a bit, and asked if I might not simply have some on hand I could use. He didn't mind if it was a different version of Windows - subtle code for hoping for a more recent version. The fifty dollars was for my labor. He didn't see getting a copy of Windows as a cost-associated item. It was no big deal, either he had a copy of Windows or I did, or he figured I knew a friend who did. I felt kind of uncomfortable about the proposition, so I said no. If he had asked me this more recently, I would have offered to put Linux on his computer. But he probably would have said no, because it would seem like a more expensive offer to him. He would have compared free, unfamiliar Linux to free, comfortable Windows. The cost of getting used to the new environment, as easy as it might be, is probably more tangible to him than the money he technically should be spending but won't. These aren't deliberate criminals who walked into a store, looked at a box of Windows, considered the price and then figured they'd go home and get a pirated version off of the Internet. It just doesn't work that way. Windows is so ubiquitous that someone, somewhere, has a copy they can just give you. People think of getting a copy from a friend before they think of buying. Heck, someone will usually offer before you thought of buying. I've sat at dinner tables with people who are by no means computer geeks, where one says they need to update their version of Windows. Maybe it's because their computer crashes a lot and they think upgrading might help. Maybe they bought a web cam or something that only has plug and play ability in the newer version. Someone, also not a computer geek, says they have a copy. A promise is made to hand it over later. The person with the copy to give likewise got it from someone else. It's as if Windows is just something that's around. If the value of the goods being exchanged is brought up as a concept at all, it's about the cost of the blank CDs. For example, the receiver might offer to provide a few blanks so the one doing the copying won't be out of pocket. A fifty cent CD is a cost item, but the copy of Windows on it isn't. Freer Than Free In fact, a free copy of Windows might even be freer than free. What I mean by that is, unlike most tangible consumer goods, pirated software is often easier to obtain and set up than making a legitimate purchase. A friend of my father obtained a legitimate copy of Windows XP from a local guy who sells custom computers. He tried to install it but he was confused by the different serial codes, authorization keys, and verification checks to pass through. My father, who is quite good with computers, tried to help. When they finally had it all sorted out on which number went where, it turned out that the length of one of the serial codes didn't match the length of the input fields. They tried calling a customer service number, but, after working their way through 1-800 numbers and option menus, the net result was that the situation was not solvable with automated service and there were no live operators available because it was late Friday night. They tried to persist in figuring it out themselves, but were stopped cold when some maximum limit of install attempts was reached and it refused any further action. Eventually, a few days later with the help of the guy who originally provided the copy of Windows, it all got sorted out and my dad's friend can enjoy his legitimate copy of Windows. This was an extreme case, but when you consider that he could have downloaded and installed a cracked version within hours, you start to get a sense of what I mean by "freer than free". To do it the legitimate way, say by buying online or having to trudge out to a brick-and-mortar store, he would get no more convenience than obtaining a pirated copy. At worst, getting an illegal copy would take much less time than the couple of days he actually experienced in doing things the legal way. How to be a Pirate Microsoft would no doubt blame the existence of pirated copies for this whole situation. And they wouldn't be wrong about the causes. But in terms of results, they then become part of a general push towards pirated software. All the security measures when one installs legitimate software makes a user feel like they're being punished for being good, the same way moviegoers who go to the theatres feel like they're not the ones who should be sitting through warnings not to download movies. The hardest part about getting cracked software is justifying it to yourself. And when I say hard, I mean relative to the other obstacles to getting cracked software, so really it's not hard at all. Clearly, all indications are that many people will often trade in a little morality for something that's valuable to own and free to get. To make the exchange of principles for goods, one has to cut a deal with their conscience by forming the right justification. I think most people simply wonder, what's the harm? Theft is usually distasteful not as much because of the gain of the thief but more because of the loss of the owner. In software, the guy who gave it to you didn't lose anything. And the company that originally made it? Microsoft seems to be doing all right, so surely this little individual act of sharing stuff among friends is no big deal. But what happens when you add up all the individuals doing this? As mentioned above, it's hard to put real numbers on it. I'm going by a lot of anecdotal evidence here. And I have to admit for a while I wasn't so sure of my position. Which Numbers Mean More? In fact, I was shaken in my convictions by a conversation I had with my friend Ken who was considering switching from Windows to Linux. He was using Windows 2000 and was starting to feel the limitations of having less and less hardware and software available for a version that was fading into history. But he was skeptical about switching to Vista with all its DRM issues. He was really interested in Linux because he's one of the category of people that doesn't use pirated software. So for him, the prospect of saving the cost of a new operating system was worth at least some of research. As we talked about Linux, I mentioned the general points that I'm discussing here. He was shocked - shocked! - at the idea that there were that many people using cracked copies of Windows. I left that conversation wondering if his viewpoint was wrong, or was mine? What about those people who stay up all night to buy a copy of Windows when the new version is released? What about the sales figures? But then what about the claims by software companies of revenues lost to piracy? What about the numbers of users on peer-to-peer networks? What do all the numbers mean, and which numbers mean more? On the one hand, the fact that he was surprised by this whole idea of cracked Windows being the main reason why Linux isn't more successful even though it's free, made me realize that maybe it's not as obvious as I thought it was. That's when I thought about writing this article. But as I started writing, I was haunted a little by the fear that my perception of the ubiquity of cracked software was out of proportion. Then, another small experience made me confident that I was firmly planted in reality. More anecdotal evidence, and I know the failings of anecdotal evidence. But I still take away from this anecdote enough conviction in my premise to stand by it. Dancing Pirates It was a couple months after my meeting with Ken, and I was spending a Monday afternoon sitting in a Starbucks writing on my laptop. There were three people, two women and a man, sitting at a table near to me. I couldn't help but overhear their conversation, as they were the only people really talking at the time. They were dancers, talking about making a web site for their dance troupe. One of the women was apparently both a dancer and a web designer. The other woman was interested in doing a little web design of her own. After hearing a couple of key phrases, I abandoned my effort to be polite and not eavesdrop, and went into full listening mode. The woman who was clearly the most computer literate of the three casually offered to give the other a copy of Dreamweaver. Just give it to her. The receiving woman didn't balk at being given a piece of proprietary software worth 400 US dollars. No, she merely said thanks and wondered if it wasn't too much trouble. The man joked something about burning software all the time, so it was no big deal. The receiving woman reciprocated by saying that she also frequently burned and shared software. This last comment was said in a way as to convey the assurance that this favour could be reciprocated. These aren't people who would for even a second consider snatching a copy of Dreamweaver from the shelf of a software store and dashing out the door. They know what they are doing is sort of not right on some level, but it just doesn't feel that wrong. They are indifferent to the crime because the ease and pervasiveness of sharing software has obscured the value of the items they're giving away. They assure themselves they aren't really doing anything wrong because, after all, if the woman dancer wasn't offered a free copy, then she simply would never use it. She's not depriving the source company of any profit because it's not profit they would ever see from her anyway. That kind of logic, and there is some logic in it, helps obscure the cost of software in the minds of the casual cracked software user. Consider how different the whole interaction would be if the woman receiving the pirated software was offered a 400 dollar stolen iPod. I'm typing this as they speak, actually, and while they deviated from the topic for a bit, they're back to it. The woman receiving the software just confirmed that the version of Flash she's getting is version 8. She didn't need to know the version of Dreamweaver, just that it's the latest. Oh, and she was offered Photoshop, but she already has it. And now, as they finish up the details of the transaction, they are talking about the particulars of using the crack and how to install it. Just before they got up to leave, they described the crack as a "hassle". If a bunch of dancers are so comfortable with the use of cracked software that they discuss circumventing authentication as being something merely in the way of using software they assume to be allowed to use for free, one can only imagine how pervasive the use and culture of cracked software is. So pervasive that the humour newspaper "The Onion" made the ironic headline "Photoshop Actually Bought", the implication being that to not purchase it was the norm. The Mac Effect... Really? At this point, we've gone a long way without mentioning something that Mr Kingsley-Hughes discussed in a follow up article, Three More Things That The Linux Community Doesn't Get. There he talked about "The Mac Effect". The idea was that people are capable of switching, and the fact that they chose Mac and not Linux, and paid for it, was supposed to be further evidence that Linux was not delivering a decent product. But really, there's no difference between Windows and Mac OS. Mac has cracked software too. I know people who stay within the realm of Mac for the same reasons a lot of Windows users stay with Windows - so they can continue to have access to shared software within their circle of friends who also use Mac. Keep in mind that a lot of people think they're getting Mac OSX for free in the same way they think Windows comes with a computer for free. It just happened to be in the hardware they bought. They don't think of the computer as being potentially a couple hundred bucks less if it has Linux or no pre-installed OS. Then, when it comes time to upgrade the Mac OS, just ask that guy in your circle of friends who always has the latest Mac stuff. Or, you could head out on any peer-to-peer network, and you'll find the latest version, no problem. Some people clearly do that. As I'm writing this right now, I'm looking at about 74 people seeding and 206 people sharing the latest Mac OSX on the infamous Pirate Bay web site. I could download it and have ready to install on a Mac in a couple of hours. I don't suppose there are many who would mind waiting a couple of hours in order to save themselves the 130 US dollar price listed on store.apple.com. The Most Effective Form of Anti-Piracy But here's where we should mention the real cap on the sharing of cracked software. There are some people who do the honest thing and pay for their software because they fear cracked copies. Are they worried about Microsoft or Apple anti-piracy SWAT teams bursting through their windows and dragging them off in the middle of the night? No, they just don't want to get a computer virus. All through this I've been speaking about how people can just go online and download things. While that takes a little know-how of where and how to do that, it's clearly common knowledge. The proof is in all the people downloading TV shows, movies, and music from peer-to-peer networks, enough to make copyright infringement news become commonplace. So, knowing how to get stuff on the net is common and it's not that there is anything technically stopping your average computer user from using the same interface they use to get music in order to get software. But many don't do that. They stick to audio and video downloads knowing they can't get a computer virus from an MP3 or AVI file. There is enough fear, uncertainty, and doubt about getting a virus through downloaded software that most people want to get it from their buddy who says "I'm running it, and it's fine". And there are clearly enough of those buddies around. (Or maybe dance troupes are particularly intent on sharing software). As should be clear by now, computer viruses on peer-to-peer networks are nowhere near stopping people from sharing software. It just hands more focus back to the friend-to-friend network that happens face-to-face, which is as common as ever. Really I just bring it up because I believe that the threat of getting a virus is more effective than security measures in keeping people from sharing software on the Internet with complete impunity. I have no idea how cracked software becomes available in the first place. Somewhere upstream are actual computer pirates I suppose. By "actual", I mean someone who alters the software so that it's shareable, not merely someone who shares it. Shady programmers in Russia who cleverly get new releases and reverse engineer the security out? Employees inside Microsoft who trade them in some kind of software black market? Disgruntled employees maybe? I have no idea. Don't really need to know, either. Neither do the dancers. Whatever the source, the distribution is so widespread that software in general, including Windows, is not viewed as an expensive consumer product. It's viewed as being for free. So when someone looks at Linux, all they see is the unfamiliarity of it, and nothing there that's so good to make them switch from Windows. After all, they're not saving anything or gaining anything by switching. What If Windows Wasn't Free? This raises interesting questions. If Microsoft were to somehow develop the security system that ensured every single user of Windows paid for it, then how many people would start considering the actually legal free and close enough option? Theoretically, if everyone who had a cracked copy of Windows now switched to a legitimate copy of Linux, then the user base might be expansive enough that all sorts of things might change. Game companies might start offering their titles for Linux. Hardware manufacturers might distribute Linux drivers as often as they do Mac and Windows drivers. Then more people might find Linux even easier. Perhaps the situation might snowball. Perhaps people who had held back because of lacking features or incompatible hardware would have their concerns solved. Those same people who were about to pay for Windows would consider going for the free option. Microsoft might actually lose some sales and market share, and they'd feel it in their bottom line. I'm not one for conspiracy theories, but the next logical question is, assuming I've made some sense up to now, isn't it in ultimately in Microsoft's interest to allow pirated copies of Windows to be out there? The feasibility of that strategy would depend on how well Microsoft could balance out letting pirated copies exist for general use, so that people felt it was the operating system, while at the same time ensuring that a substantial section of the market, mainly companies probably, would not want to bother with any potential legal hassles. Personally, I don't think that is Microsoft's strategy. It comes with some risks that I think they would deem too high. One leaked memo about acknowledging the benefit of pirated software would cause chaos in all sorts of ways. But maybe they don't have to have any kind of official position. If cracked software helps keep Windows in business, and virus threats are more effective than security measures in keeping cracked software from eating too much into Microsoft's bottom line, then one might argue that the main mechanisms for Microsoft's success come from outside Microsoft. Just enough piracy to maintain dominance. Just enough of a virus threat to keep it from getting out of control. That can't be said with certainty, but it's food for thought. But in any case, my point here is not about the causes of why Windows is "free", just with the results. My contention is that Linux would win over the hearts and minds of more, maybe most, users if their wallets were actually involved in the decision to choose one or the other. You Can Tell Who's Paying My friend Ken, who I mentioned earlier, is evidence of that. Unlike a lot of people I know, he really does reach for his wallet when he upgrades his OS, and that's why he proactively came to me with questions about Linux. I don't know if he'll actually adopt Linux, but he's very seriously considering it, because, like most people, if he can save a couple hundred bucks, he will. What he's not doing is just casually dismissing Linux out of hand like most people who are strangely far less interested in free software than they would be in anything else for free. Enough people feel no connection to their wallets when considering operating systems to perpetuate the unspoken assumption that Windows is free. And as a result, Linux is forced to make its case based on much more nebulous, personally biased, and complicated comparisons about which one is "better" or "worse". And that's a debate that can never be pursued objectively, with objective results. Or at least, my experience in hearing people argue about it is that it never stays objective for long. This idea that Windows is, to most everyone, effectively free, is in my opinion the single most significant factor in explaining why Linux isn't doing better than it is. I'm not even saying that Linux would or should necessarily dominate or wipe out Windows. I'm only saying that if the market for operating systems operated under the same rules as other consumer goods, then Linux would have a larger share of the market. If every user who had a cracked copy of Windows had a legitimate version of Linux instead, what would the percentage of computers running Linux be? More than there are now, that's for sure. What can be done with this information? Perhaps one of the conclusions that can be made is that the best strategy for proponents of free operating systems is to help develop better protection for paid software. What Microsoft can do with the information is a more interesting question. I doubt any of their payment and security schemes will ever really stop the cracked copies from being around. Vista was supposed to come with verifications that would be impossible to avoid. But you can go online right now and download copy of Vista that will appear as authenticated to the Genuine Advantage system. In any case, the more successful their defenses become, the more people really have to reach for their wallet when considering whether or not to upgrade, the wider the door of opportunity opens for Linux to step in and say "you can still do everything you do now for free". What if Microsoft were to recognize that and adopt a different strategy. Free copies of Windows for home use? Corporate packages that are paid? My guess is that most of their money comes from company purchases anyway. It seems possible to me that they could switch to a model that allows free personal use and paid corporate use with little to no impact on their bottom line. Because it would just be an official adoption of what may already be the reality. I'm not anticipating that happening any time soon, because a paradigm shift of that proportion will meet resistance on many levels due to the needs of a large profit-driven organization with many employees and shareholders. However, I'm here to talk about products, not production, so the inertia Microsoft would face in making Windows more free is outside the scope of this article. But, just supposing for a minute that they could, then by making their software at least partially free, or free to a point, they can slow down the free competition to a crawl and stay in business for a long, long time. Just like free copies of Windows are holding off free copies of Linux right now. What Can You Do With This Information? In closing, I'd like to just leave you with something to think about. If you're using a cracked copy of Windows, you have at least one less reason to feel guilty. After all, you may be keeping Microsoft in business in a roundabout, unintended way. You can't admit to them that's what you're doing, though, which makes it a strange position to be in. And at the same time, another thing you might be doing in a roundabout way is slowing down the development of software that you could use both for free and without any moral or legal ambiguities. How you justify all that in your mind is up to you. For me, I've developed a policy whenever it comes to debates on Linux, Windows, and Mac. As a long time user of Windows and Mac, who has switched to Linux, I can tell you that any debate based on feature, security, or stability comparisons between Linux, Mac, and Windows is a battle of grey perceptions, not black and white certainties. As such, they are eclipsed entirely by the issue of the market distortions of software piracy. You can prefer one or the other for any reason you like. But to convince me that Linux isn't good enough to take for free, you'd have to not only show me side-by-side comparison where Windows did what Linux couldn't, but, more importantly, I won't even start the discussion with you unless you show me your proof of purchase (for every copy of Windows you have for personal use, and all your applications) to convince me that in your mind the features you're comparing were actually worth 200 US dollars or more. http://tlug.jp/articles/Windows_Is_Free  Children's Reviews of OLPC XO Technology Wayan Vota While we can endlessly debate One Laptop Per Child on OLPC News, what really matters will be the opinions and adoption of XO technology by children. And recently children have been expressing their views on the matter. Gabe, focused on XO activities First up is Chris Schmidt's experience with giving an OLPC XO to a friend's young son: I snapped a dozen pictures of Gabe (mercy_rain's son) and SJ Klein (OLPC Manager of Content) with the OLPC. Note that Gabe had never seen one of these things before, and with practically no help from the adults, he had started painting, typing, and playing with the webcam, cackling quite evilly the whole time. The photo set is damn cute, a visual statement to the XO's appeal. Then twelve year old "SG" made a surprisingly well-written literary statement about the $100 laptop" on Freedom to Tinker: My expectations for this computer were, I must admit, not very high. But it completely took me by surprise. It was cleverly designed, imaginative, straightforward, easy to understand (I was given no instructions on how to use it. It was just, “Here. Figure it out yourself.”), useful and simple, entertaining, dependable, really a “stick to the basics” kind of computer. It’s the perfect laptop for the job. Great for first time users, it sets the mood by offering a bunch of entertaining and easy games and a camera. SG also sets the mood for another laptop prototype test, this time maintenance. Nicholas Negroponte's OLPC XO maintenance plan is for children to do 95% of technical support. Apparently Mitch Bradley even believes that a 10-year old could replace an XO motherboard. To prove the concept, Joel Stanley set up a motherboard replacement challenge, with Philip (10) and his sister Sophie (8), which you can watch or read about: Now watching that test after Gabe's and SG's reactions, you could be persuaded that One Laptop Per Child doesn't really need an implementation plan, that Negroponte's dreams can be a reality without intensive teacher training or cultural integration. But before these privileged kids' experiences allow you discount my fears of Humpty Dumpty on a million unit scale, remember the real OLPC demographic. Nicholas Negroponte wants poor, uneducated children in the developing world to learn learning using the OLPC XO. Children who are not intimately familiar with computers and laptops by age 12, who cannot look to Joel Stanley for help, and are not blessed with parents who know SJ Klein. Children who will need more than just OLPC magic to eliminate poverty with education. http://www.olpcnews.com/implementati...echnology.html  Half of Web Time Spent Viewing Content: Study Content online is king. Internet users spend nearly half their time online viewing news or entertainment content, surpassing activities such as sending e-mails, shopping or searching for information, according to a study released by the Online Publishers Association on Monday. The four-year study, conducted by Nielsen/NetRatings, tracked a 37 percent increase in amount of time spent viewing content such as online videos or news, surpassing a 35 percent rise in using search engines like Google Inc.. The abundance of content and faster online speeds accounted for the spike, the study said. A proliferation of social networks such as News Corps' MySpace and Facebook have helped boost content viewing as well. Overall, viewing content accounts for 47 percent of time spent online in 2007, up from 34 percent in 2003. Web search accounted for 5 percent of time spent online in 2007 from 3 percent in 2003. Time spent on commerce sites such as Amazon.com fell 5 percent and accounted for 15 percent of time spent in 2007. Time spent on communications such as e-mail fell 28 percent to 33 percent of time spent online in 2007, down from 46 percent in 2003. The popularity of instant messaging such as AOL Instant Messenger, which lets users send quick messages rather than e-mails, accounted for the drop in the amount of time spent corresponding, the study said. (Reporting by Kenneth Li, editing by Deborah Cohen) http://www.reuters.com/article/techn...35166120070813  Five Myths and Mysteries About Black Web Surfing Mark Ontkush You might have been following the recent debate about surfing a black web, even received a viral email or two on the topic. We have discussed some facts and figures around using a black Google, and other alternatives sites such as Blackle. In spite of all the recent press, mysteries and myths still abound, here are 5 of the most common. 1. Every monitor uses 74 watts to display a white background, and only 59 watts to display a black background. Answer: Nope, and it's probably the biggest misconception. The original post that started this whole thing pulled these numbers from the US department of energy, but these numbers almost certainly refer to CRT monitors only. 2. Ok, well, every CRT monitor saves 15 watts then going from white to black. Answer: The amount of energy saved here is depends on many factors, including the size, type, and manufacturer of the specific monitor. A study conducted in 2002, the infamous Roberson Study, found that different CRT monitors saved between 4 and 30 watts going from white to black, a big range. A new study by Techlogg on 4 CRT monitors found that they all did save energy, but the range was narrower and the savings was smaller (only between 7 and 11 watts). It is likely that CRT monitors are getting more efficient. 3. What about LCD monitors? I keep hearing that is makes no difference what color they display, or that they even use more energy displaying black over white. Answer: Another big misconception. LCD monitors have a light behind the screen that is always on, so white is usually the most efficient color to produce; you just let the light shine through. Black on the hand requires the light to be completely blocked, and this takes energy. So, on the face of it, white would always be cheaper than black to create on LCD screens. Turns out this is mostly true, and on average, takes less than a watt of energy to do. But there more, because some clever LCD manufacturers check how dark the screen is, and if it's very dark they dim the backlight; this saves energy. The Roberson study found this was true for every LCD monitor, Techlogg found it was primarily true for monitors over 24 inches wide. This doesn't save much energy, tops 4 watts, but it does save some. So, LCD technology has changed over time, and it is true that the differential between displaying white and black is much tighter than CRT monitors, a few watts at most. 4. Very interesting. So that solves it, since about 75 percent of the monitors in the world are LCD monitors, and since it doesn't really save a lot of of energy to display black over white (some even cost energy), the whole energy saving argument is a wash. Answer: It is true that there are a large number of LCD monitors out there, and that for the majority of them it doesn't make a whole lot of difference energy wise to show black vs. white. Sites such as Techlogg and Infoworld used these numbers to demonstrate that the technique was ineffective. In fact, this very argument proves that the technique works! The reason is that energy consumed by the LCD monitors is dwarfed by the massive savings from the other 25 percent of monitors, the power guzzling CRT monitors. If you want, you can try this experiment to convince yourself of this fact. Get three lcd monitors and plug them into a power strip. Then get one CRT monitor, and plug that into the same power strip. Plug the power strip into your testing equipment, then plug that into the wall outlet. Now turn on all the machines and get them all connected to the Internet; show an all white screen on all of them, and take a reading from your test equipment. Now show an all black screen on all of them. Read your testing equipment again. You have two readings now, the second should be lower than the first. For another explanation, read Pablo Paster's posting on the topic. 5. Great, so it works! Does it work on any site? Answer: Yes, the energy saving principle will work on any site. Google is often referenced (they get over 500 million hours of use each year) but other good candidates would be Yahoo, MySpace, and YouTube. :: TriplePundit ::Infoworld http://www.treehugger.com/files/2007...things_you.php  Beyond batteries: Storing Power in a Sheet of Paper Researchers turn everyday paper into resilient, rechargeable energy storage device Press Release Researchers at Rensselaer Polytechnic Institute have developed a new energy storage device that easily could be mistaken for a simple sheet of black paper. The nanoengineered battery is lightweight, ultra thin, completely flexible, and geared toward meeting the trickiest design and energy requirements of tomorrow’s gadgets, implantable medical equipment, and transportation vehicles. Along with its ability to function in temperatures up to 300 degrees Fahrenheit and down to 100 below zero, the device is completely integrated and can be printed like paper. The device is also unique in that it can function as both a high-energy battery and a high-power supercapacitor, which are generally separate components in most electrical systems. Another key feature is the capability to use human blood or sweat to help power the battery. Details of the project are outlined in the paper “Flexible Energy Storage Devices Based on Nanocomposite Paper” published Aug. 13 in the Proceedings of the National Academy of Sciences. The semblance to paper is no accident: more than 90 percent of the device is made up of cellulose, the same plant cells used in newsprint, loose leaf, lunch bags, and nearly every other type of paper. Rensselaer researchers infused this paper with aligned carbon nanotubes, which give the device its black color. The nanotubes act as electrodes and allow the storage devices to conduct electricity. The device, engineered to function as both a lithium-ion battery and a supercapacitor, can provide the long, steady power output comparable to a conventional battery, as well as a supercapacitor’s quick burst of high energy. A sample of the new nanocomposite paper developed by researchers at Rensselaer Polytechnic Institute. Infused with carbon nanotubes, the paper can be used to create ultra-thin, flexible batteries and energy... The device can be rolled, twisted, folded, or cut into any number of shapes with no loss of mechanical integrity or efficiency. The paper batteries can also be stacked, like a ream of printer paper, to boost the total power output. “It’s essentially a regular piece of paper, but it’s made in a very intelligent way,” said paper co-author Robert Linhardt, the Ann and John H. Broadbent Senior Constellation Professor of Biocatalysis and Metabolic Engineering at Rensselaer. “We’re not putting pieces together – it’s a single, integrated device,” he said. “The components are molecularly attached to each other: the carbon nanotube print is embedded in the paper, and the electrolyte is soaked into the paper. The end result is a device that looks, feels, and weighs the same as paper.” The creation of this unique nanocomposite paper drew from a diverse pool of disciplines, requiring expertise in materials science, energy storage, and chemistry. Along with Linhardt, authors of the paper include Pulickel M. Ajayan, professor of materials science and engineering, and Omkaram Nalamasu, professor of chemistry with a joint appointment in materials science and engineering. Senior research specialist Victor Pushparaj, along with postdoctoral research associates Shaijumon M. Manikoth, Ashavani Kumar, and Saravanababu Murugesan, were co-authors and lead researchers of the project. Other co-authors include research associate Lijie Ci and Rensselaer Nanotechnology Center Laboratory Manager Robert Vajtai. The researchers used ionic liquid, essentially a liquid salt, as the battery’s electrolyte. It’s important to note that ionic liquid contains no water, which means there’s nothing in the batteries to freeze or evaporate. “This lack of water allows the paper energy storage devices to withstand extreme temperatures,” Kumar said. Along with use in small handheld electronics, the paper batteries’ light weight could make them ideal for use in automobiles, aircraft, and even boats. The paper also could be molded into different shapes, such as a car door, which would enable important new engineering innovations. “Plus, because of the high paper content and lack of toxic chemicals, it’s environmentally safe,” Shaijumon said. Paper is also extremely biocompatible and these new hybrid battery/supercapcitors have potential as power supplies for devices implanted in the body. The team printed paper batteries without adding any electrolytes, and demonstrated that naturally occurring electrolytes in human sweat, blood, and urine can be used to activate the battery device. “It’s a way to power a small device such as a pacemaker without introducing any harsh chemicals – such as the kind that are typically found in batteries – into the body,” Pushparaj said. The materials required to create the paper batteries are inexpensive, Murugesan said, but the team has not yet developed a way to inexpensively mass produce the devices. The end goal is to print the paper using a roll-to-roll system similar to how newspapers are printed. “When we get this technology down, we’ll basically have the ability to print batteries and print supercapacitors,” Ajayan said. “We see this as a technology that’s just right for the current energy market, as well as the electronics industry, which is always looking for smaller, lighter power sources. Our device could make its way into any number of different applications.” The team of researchers has already filed a patent protecting the invention. They are now working on ways to boost the efficiency of the batteries and supercapacitors, and investigating different manufacturing techniques. "Energy storage is an area that can be addressed by nanomanufacturing technologies and our truly inter-disciplinary collaborative activity that brings together advances and expertise in nanotechnology, room-temperature ionic liquids, and energy storage devices in a creative way to devise novel battery and supercapacitor devices," Nalamasu said. http://www.eurekalert.org/pub_releas...-bbs080907.php  Nokia Warns Consumers of Battery Overheating Risks Tarmo Virki Nokia warned consumers that 46 million batteries used in its mobile phones could overheat and offered to replace them for free while it negotiates with battery maker Matsushita over who would bear the costs. The world's top cell phone maker said about 100 such incidents had been reported globally, but no serious injuries or property damage had been reported. "Nokia has identified that in very rare cases the Nokia-branded BL-5C batteries ... could potentially experience overheating initiated by a short circuit while charging, causing the battery to dislodge," it said on Tuesday. Nokia said it was working closely with Matsushita Electric Industrial Co. Ltd., which made the batteries in question between December 2005 and November 2006, to investigate the problem. Replacing the batteries would have some financial impact, but Matsushita would pay part of the costs, Nokia said. Analyst Richard Windsor of Nomura estimated the cost to Nokia at a maximum of 100 million euros ($137 million). "Historically, when there's been a problem of this nature the supplier has had to pay," he said. Research firm Gartner said one such battery would cost around $4. Nokia's U.S. shares were down 24 cents or 0.79 percent at $30.34 after noon on the New York Stock Exchange. Its European shares closed down 1.55 percent, helping nudge the DJ European technology index down 0.84 percent. Some U.S. cell phone analysts said the warning would be unlikely to either hurt Nokia's market share or boost its main rivals such as Motorola Inc., Samsung Electronics Co. or LG Electronics. But Jyske Bank downgraded its rating on Nokia shares to "reduce" from "buy," saying every third Nokia user would now have to check their phone's batteries. "I think this will hurt Nokia's brand a lot and that's the most precious asset Nokia has," Jyske analyst Soren Linde Nielsen said. According to Interbrand, Nokia's brand is valued at $33.7 billion, making it the world's fifth most valued brand after the likes of Coca-Cola and Microsoft. Splitting The Costs Mobile phone maker Sony Ericsson, owned by Sony Corp. and Ericsson, said it depends mostly on batteries from Sony and does not use Matsushita batteries. Last year, Sony was hit by hefty costs to recall 9.6 million laptop PC batteries that could overheat and catch fire. A representative for LG said she did not know of any LG cell phones that were affected. Motorola officials were not immediately available for comment. Samsung representative Kim Titus said the company had not sued regarding batteries from Matsushita in any of its handsets and would not be affected. The "BL-5C" is Nokia's most widely used battery, powering its low-end 1100 series phones and multimedia handsets N70 and N91, among others. Several suppliers have made a total of more than 300 million of them for Nokia. Nokia said it had issued a product advisory (http://www.nokia.com/batteryreplacement) to consumers based on preliminary findings from its investigation. "By reacting swiftly and responsibly, and by being fully transparent, we believe that consumers will continue to view Nokia as a responsible and trustworthy brand," Robert Andersson, Nokia's head of customer and market operations, told Reuters. Matsushita said there had been a rare problem in the manufacturing process rather than in the design of the batteries. It said the effect on its earnings was uncertain. "We are still in discussion with Nokia about how to divide the replacement cost," said Matsushita spokesman Akira Kadota. Nokia spokeswoman Marianne Holmlund said that in similar cases in the car industry, less than half of consumers eligible for replacement had used the option. In 2003, a Belgian consumer organization said some Nokia batteries had a short circuit risk, but the Finnish firm denied those claims and said media reports of exploding phone batteries were all related to counterfeits. (Additional reporting by Mayumi Negishi in Tokyo, Georgina Prodhan in Frankfurt, Tehri Kinnunen in Helsinki and Sinead Carew in New York) http://www.reuters.com/article/domes...00572220070814  'Dance Dance Immolation' Steps Up the Heat  At a warehouse in Oakland, Calif., Saturday night, video gamers got shot in the face with fire--all in the name of what some would call fun. The fun, in this case, was an evening of Dance Dance Immolation. DDI is derived from Dance Dance Revolution, the popular video game that tests players' dance moves and is being incorporated into middle school physical education programs. DDI, however, combines the movements with flamethrowers--needless to say, it's for grown-ups only. http://news.com.com/2300-1043_3-6188...g=nefd.gallery  Good morning Mr. Phelps Videos Purchased from Google to Self-Destruct Wednesday Scott M. Fulton In a move that may have some wondering whether the proverbial left hand knows what the other left hand is doing, Google issued a notice to its Google Video customers last week informing them that it is discontinuing its video sales business on Wednesday. But that wasn't all: The notice explicitly says that videos purchased or rented, and then downloaded to customers' PCs will no longer be viewable on or after August 15. In other words, if you were to use this page to search for a video within a specific price range today, regardless of what you pay for it, due to DRM restrictions it will not play after Wednesday. As a way of compensating for customers' grievances, the company is offering them coupons good toward purchases through other online retailers that use Google Checkout. Based on early reports, the value of the coupons is roughly equivalent to the amount of their purchases. However, in order for customers to redeem them, they must make purchases of the same amount or more, and they must do so within 60 days of August 15. The move comes just after Universal Music Group indicated its intention to sell MP3 tracks without DRM through Google and perhaps others, though not iTunes. Google's official explanation, as cited by the Associated Press, is that the company believes more in the compensating power of advertising support alongside video than in charging users directly. "The current change is a reaffirmation of our commitment to building out our ad-supported...models for video," the AP report quotes Google spokesperson Gabriel Strickler as saying. There is some data to back Strickler up. According to a comScore Media Metrix report last month, Google accounted for 21.5% of the US' streaming media traffic, with Fox Interactive's sites (mostly MySpace) a distant second at 8.1%. That's streams, such as the embedded kind that appears in Web pages, not VOD or direct downloads. If the money in video is to be made in exploiting audience size for advertising, some might rightfully ask how come audio doesn't work the same way. Of course, all this diverts from what could be the major question in customers' minds: Weren't their video purchases supposed to be permanent? Strickler's comments appear only to be addressing shareholders' concerns, not customers. One of those customers is Boing Boing's Cory Doctorow, who wrote last Friday, "This is a giant, flaming middle finger, sent by Google and the studios to the customers who were dumb trusting enough to buy DRM videos. How many of these people will trust the next DRM play from Google (no doubt coming soon from YouTube) or the studios?" Apparently not every customer is so worried. A member of the Broadband Reports forum who invested $17.12 on replay videos of NBA basketball games, wrote on Saturday, "I'm being reimbursed for $20 so I actually come out ahead. Losing that video is no big deal anyway." http://www.betanews.com/article/prin...day/1186971575  Google Selleth then Taketh Away, Proving the Need for DRM Circumvention Ken Fisher It's not often that Google kills off one of its services, especially one which was announced with much fanfare at a big mainstream event like CES 2006. Yet Google Video's commercial aspirations have indeed been terminated: the company has announced that it will no longer be selling video content on the site. The news isn't all that surprising, given that Google's commercial video efforts were launched in rather poor shape and never managed to take off. The service seemed to only make the news when embarrassing things happened. HD DVD cracks: there's no going back Yet now Google Video has given us a gift—a "proof of concept" in the form of yet another argument against DRM—and an argument for more reasonable laws governing copyright controls. How could Google's failure be our gain? Simple. By picking up its marbles and going home, Google just demonstrated how completely bizarre and anti-consumer DRM technology can be. Most importantly, by pulling the plug on the service, Google proved why consumers have to be allowed to circumvent copy controls. A consolation prize Google contacted customers late last week to tell them that the video store was closing. The e-mail declared, "In an effort to improve all Google services, we will no longer offer the ability to buy or rent videos for download from Google Video, ending the DTO/DTR (download-to-own/rent) program. This change will be effective August 15, 2007." The message also announced that Google Checkout would issue credits in an amount equal to what those customers had spent at the Google Video store. Why the quasi-refunds? The kicker: "After August 15, 2007, you will no longer be able to view your purchased or rented videos." See, after Google takes its video store down, its Internet-based DRM system will no longer function. This means that customers who have built video collections with Google Video offerings will find that their purchases no longer work. This is one of the major flaws in any DRM system based on secrets and centralized authorities: when these DRM data warehouses shut down, the DRM stops working, and consumers are left with useless junk. Furthermore, Google is not refunding the total cost of the videos. To take advantage of the credit Google is offering, you have to spend more money, and furthermore, you have to spend it with a merchant that supports Google Checkout. Meanwhile, the purchases you made are now worthless. To do it right, Google should either provide users with non-DRMed copies of the videos they bought, or they should refund the money entirely. The current option is hardly acceptable, however. Would you buy a TV, a car, a book, or anything if the guy who sold it to you could take it back at any moment so long as he offered you a coupon? Did you buy Kobe Bryant's 81-point game to commemorate that bit of NBA history? Enjoy staring at an unplayable file come Wednesday. But hey, at least you get $2 back to go buy underwear! Copyright Office, here we come Since the death of the commercial part of Google Video will render thousands and thousands of purchases useless, the Library of Congress will have no choice but to consider the matter when they return to their triennial review of the DMCA. To date, the Library of Congress has granted exceptions to the anti-circumvention clause of the DMCA in instances where DRM has rendered something completely unusable, such as eBook DRM which can render eBooks useless for handicapped people. Recent exceptions from the last review are detailed here. Of note: the right to bypass DRM on products that no longer work properly was considered but rejected last time around. Now, thanks to Google, we have a case study, a real-world example we can point to and say: "Hey, this isn't right." It features one of the world's most innovative and financially powerful technology companies bagging out on users. It features thousands of consumers buying DRMed goods in earnest, and it ends with a bang; Google decides to exit the market, leaving consumers with a load of useless goods. Needless to say, this could happen with any player. Google could float its store if it wanted to, but it is exiting the business. What happens when Amazon does the same? Or Apple, or the next guy? If this isn't further proof that parts of the DMCA should be gutted, at the very least it is a strong sign that the Library of Congress needs to address this issue. Congress should be thinking about this brave new world of "unproperty" where you're charged good money to "buy" products that, in reality, you're only renting until AverageCorp gets bored of the business. http://arstechnica.com/news.ars/post...umvention.html  Demise of DRM, Economics of File Sharing and Persistent Security Risks Digital Rights Management (DRM) may be fading as Universal Records joins EMI in testing the DRM-free music downloads. According to MP3.com: The world's largest music company--home to the likes of U2, 50 Cent, and Eminem--is set to begin testing sales of DRM-free downloads, a move that signals a continuing shift in the major record labels' antipiracy strategy in the face of anemic CD sales. But if record companies think illegal file sharing is the problem with their sales, they'd better take a look at a study entitled The Effect of File Sharing on Record Sales: An Empirical Analysis which doesn't support the idea that file sharing is eating into profits. The authors of the paper cryptically explain their methods: We match an extensive sample of downloads to U.S. sales data for a large number of albums. To establish causality, we instrument for downloads using data on international school holidays. Downloads have an effect on sales that is statistically indistinguishable from zero. Our estimates are inconsistent with claims that file sharing is the primary reason for the decline in music sales during our study period. Translation: people who illegally copy music wouldn't buy it anyway so don't count them as lost sales. So where are we now? Record companies have started to throw in the towel on DRM and if Universal dumps DRM completely it is likely others will follow. File sharing will continue because it seems that it's done independently of what the record companies do anyway. What may change is attitudes about file sharing and P2P clients. Here is a possible scenario: 1. Record companies dump DRM completely. 2. More customers assume it's OK to share music files, after all they aren't prevented from sharing 3. The number of P2P file sharing clients grows 4. Too few users keep their clients patched and organizations don't manage P2P on their networks as they should. 5. P2P becomes an even more viable option for malware distribution than it is today 6. Creative attackers start to use P2P as an infrastructure for botnet and other rogue applications, kind of like the current rush to build Facebook applications. For every silver lining, there seems to be a cloud. http://www.realtime-websecurity.com/...cs_of_fil.html  Universal To Acquire V2 Music Group FMQB Universal Music Group has announced its intent to acquire Richard Branson's V2 Music Group, which includes V2 Records. The label is home to artists such as Stereophonics and Paul Weller, and V2 also owns and operates Co-Operative Music, its in-house licensing organization that includes independent labels like Bella Union, City Slang and Wichita Recordings and artists such as Bloc Party, Peter Bjorn and John, and Go Team! Terms of the proposed transaction were not disclosed, although a source told Reuters that the purchase price was about 7 million pounds ($14 million). A separate source said the offer was likely higher since rival bids ran as high as the mid-teens millions. The sale is still subject to regulatory approval. In making the announcement, Chairman and CEO of Universal Music International Lucian Grainge said, "V2 is recognized as a pioneer in independent music with a diverse artist roster that spans many musical genres. As such, V2’s roster will complement our existing business. By applying our expertise in artist development and in the digital space, we’ll be able to maximize and enhance the opportunities for its artists even further." http://fmqb.com/Article.asp?id=456209  iTunes Now Selling John Lennon Tracks AP Apple Inc. has begun selling downloads of tracks from 16 of John Lennon's post-Beatles albums, including "Working Class Hero" and "John Lennon/Plastic Ono Band," on iTunes, the company said Tuesday. The albums represent Lennon's recording output while he was with Capitol Records, a unit of Britain's EMI Group PLC. While many of the late singer-songwriter's solo recordings have been available for download commercially elsewhere, this marks the first time they have been available on Apple's market-leading online music service. Songs on two albums - "Lennon Legend" and "Acoustic" - were being made available for download exclusively on iTunes, the company said. Video content was also being included with the purchase of some of the albums for a limited time. The Lennon tracks will also be available without copy-protection restrictions and in higher-quality audio for $1.29 each. Regular versions are priced at 99 cents each. "John would have loved the fact that his music will now be available in a format suited to a new generation of listeners," Lennon's widow, Yoko Ono, said in a statement released by Apple. http://seattlepi.nwsource.com/pop/14...non_Songs.html  Rutgers Player Sues Imus, CBS UPI A Rutgers University women's basketball team member from New York has sued Don Imus and CBS, saying his disparaging on-air remarks damaged her reputation. The suit by Kia Vaughn, who claimed the shock jock's sexist and racist statements about the team defamed her, was filed Tuesday just hours after Imus settled his $120 million breach-of-contract suit with CBS, USA Today reported Wednesday. "This is basically about vindicating my client's good name," Vaughn's attorney, Richard Ancowitz, told the newspaper. "This is not a situation she ever asked for, and she would love to turn the clock back. But unfortunately she can't, because of what Don Imus said on April 4." Imus was taken off the air for calling the Rutgers women's basketball team "nappy headed ho's." The settlement with CBS has fueled speculation about Imus' return to radio. Vaughn's lawsuit, thought to be the first by a player in the matter, alleged Imus, former on-air partner Bernard McGuirk and CBS, which broadcast his syndicated radio show, were responsible for damaging her character and reputation. A dollar amount was not listed. http://www.upi.com/NewsTrack/Enterta...imus_cbs/3634/  Picks up 20 mil Imus Settles With CBS, May Make Comeback Pat Milton Don Imus has reached a settlement with CBS over his multimillion-dollar contract and is negotiating with WABC radio to resume his broadcasting career there, according to CBS and a person familiar with the negotiations. Imus and CBS Radio reached a settlement that would pre-empt the dismissed radio personality's threatened $120 million breach-of-contract lawsuit, CBS spokesman Dana McClintock said Tuesday. No terms of the settlement were disclosed. The person familiar with the talks told The Associated Press that Imus is taking steps to make a comeback with WABC-AM. The person, who spoke on condition of anonymity because the news had not been announced, also said the deal with CBS calls for a ''non-disparaging'' agreement that forbids him from speaking negatively about his former employer. The settlement and possible comeback come more than four months after Imus created an uproar over his racist and sexist comments about the Rutgers women's basketball team. Just before his dismissal, Imus signed a five-year, $40 million contract with CBS Radio (owned by CBS Corp.). Famed First Amendment lawyer Martin Garbus said in May that Imus planned to sue CBS for $120 million in unpaid salary and damages. WFAN, the New York radio station that was Imus' flagship, also announced Tuesday that former NFL quarterback Boomer Esiason will take over the morning time slot along with Craig Carton, a New Jersey radio personality. WABC is a talk-radio station that features political and topical shows with such stars Sean Hannity and Rush Limbaugh. Imus, 66, was dismissed April 12 after describing the Rutgers women's basketball team as ''nappy-headed hos'' on his nationally syndicated radio program, which was also simulcast on MSNBC. (General Electric Co.'s cable TV channel now has the ''Morning Joe'' program with Joe Scarborough.) Garbus had said Imus would sue for the contract's unpaid part. He cited a contract clause in which CBS acknowledged that Imus' services were ''unique, extraordinary, irreverent, intellectual, topical, controversial.'' The clause said Imus' programming was ''desired by company and ... consistent with company rules and policy,'' according to Garbus. http://www.whotv.com/Global/story.as...29709&nav=2HAB  NAB Shows Performance Royalty Impact With Mock Airplay Invoice FMQB The National Association of Broadcasters (NAB) has created a "mock invoice," sent to radio stations, as part of its fight against the proposed performance royalty on terrestrial radio. The letter suggests contacting your Congressman and runs down a series of arguments against the royalty. Among the points, the NAB says that "imposing a tax of this size on free, local radio stations will cripple smaller radio stations" and "the big record labels like to hide behind their artists, but at least half of all fees end up in the pockets of foreign record label conglomerates, while the rest is divided up among the stakeholders. Often, the artists only receive a few pennies out of every dollar." The mock invoice tells stations that they can expect to pay out 10-35 percent of gross revenue to the labels "for the honor of airing their music, making mega-stars out of their artists and putting money in their pocket through free promotion of their music and concert tours." The entire "invoice" can be read here in PDF format. http://fmqb.com/Article.asp?id=457018  Max Roach, a Founder of Modern Jazz, Dies at 83 Peter Keepnews Max Roach, a founder of modern jazz who rewrote the rules of drumming in the 1940’s and spent the rest of his career breaking musical barriers and defying listeners’ expectations, died early today in Manhattan. He was 83. His death was announced today by a spokesman for Blue Note records, on which he frequently appeared. No cause was given. Mr. Roach had been known to be ill for several years. As a young man, Mr. Roach, a percussion virtuoso capable of playing at the most brutal tempos with subtlety as well as power, was among a small circle of adventurous musicians who brought about wholesale changes in jazz. He remained adventurous to the end. Over the years he challenged both his audiences and himself by working not just with standard jazz instrumentation, and not just in traditional jazz venues, but in a wide variety of contexts, some of them well beyond the confines of jazz as that word is generally understood. He led a “double quartet” consisting of his working group of trumpet, saxophone, bass and drums plus a string quartet. He led an ensemble consisting entirely of percussionists. He dueted with uncompromising avant-gardists like the pianist Cecil Taylor and the saxophonist Anthony Braxton. He performed unaccompanied. He wrote music for plays by Sam Shepard and dance pieces by Alvin Ailey. He collaborated with video artists, gospel choirs and hip-hop performers. Mr. Roach explained his philosophy to The New York Times in 1990: “You can’t write the same book twice. Though I’ve been in historic musical situations, I can’t go back and do that again. And though I run into artistic crises, they keep my life interesting.” He found himself in historic situations from the beginning of his career. He was still in his teens when he played drums with the alto saxophonist Charlie Parker, a pioneer of modern jazz, at a Harlem after-hours club in 1942. Within a few years, Mr. Roach was himself recognized as a pioneer in the development of the sophisticated new form of jazz that came to be known as bebop. He was not the first drummer to play bebop — Kenny Clarke, 10 years his senior, is generally credited with that distinction — but he quickly established himself as both the most imaginative percussionist in modern jazz and the most influential. In Mr. Roach’s hands, the drum kit became much more than a means of keeping time. He saw himself as a full-fledged member of the front line, not simply as a supporting player. Layering rhythms on top of rhythms, he paid as much attention to a song’s melody as to its beat. He developed, as the jazz critic Burt Korall put it, “a highly responsive, contrapuntal style,” engaging his fellow musicians in an open-ended conversation while maintaining a rock-solid pulse. His approach “initially mystified and thoroughly challenged other drummers,” Mr. Korall wrote, but quickly earned the respect of his peers and established a new standard for the instrument. Mr. Roach was an innovator in other ways. In the late 1950s, he led a group that was among the first in jazz to regularly perform pieces in waltz time and other unusual meters in addition to the conventional 4/4. In the early 1960s, he was among the first to use jazz to address racial and political issues, with works like the album-length “We Insist! Freedom Now Suite.” In 1972, he became one of the first jazz musicians to teach full time at the college level when he was hired as a professor at the University of Massachusetts at Amherst. And in 1988, he became the first jazz musician to receive a so-called genius grant from the MacArthur Foundation. Maxwell Roach was born on Jan. 10, 1924, in the small town of New Land, N.C., and grew up in the Bedford-Stuyvesant section of Brooklyn. He began studying piano at a neighborhood Baptist church when he was 8 and took up the drums a few years later. Even before he graduated from Boys High School in 1942, savvy New York jazz musicians knew his name. As a teenager he worked briefly with Duke Ellington’s orchestra at the Paramount Theater and with Charlie Parker at Monroe’s Uptown House in Harlem, where he took part in jam sessions that helped lay the groundwork for bebop. By the middle 1940’s, he had become a ubiquitous presence on the New York jazz scene, working in the 52nd Street nightclubs with Parker, the trumpeter Dizzy Gillespie and other leading modernists. Within a few years he had become equally ubiquitous on record, participating in such seminal recordings as Miles Davis’s “Birth of the Cool” sessions in 1949 and 1950. He also found time to study composition at the Manhattan School of Music. He had planned to major in percussion, he later recalled in an interview, but changed his mind after a teacher told him his technique was incorrect. “The way he wanted me to play would have been fine if I’d been after a career in a symphony orchestra,” he said, “but it wouldn’t have worked on 52nd Street.” Mr. Roach made the transition from sideman to leader in 1954, when he and the young trumpet virtuoso Clifford Brown formed a quintet. That group, which specialized in a muscular and stripped-down version of bebop that came to be called hard bop, took the jazz world by storm. But it was short-lived. In June 1956, at the height of the Brown-Roach quintet’s success, Brown was killed in an automobile accident, along with Richie Powell, the group’s pianist, and Powell’s wife. The sudden loss of his friend and co-leader, Mr. Roach later recalled, plunged him into depression and heavy drinking from which it took him years to emerge. Nonetheless, he kept working. He honored his existing nightclub bookings with the two surviving members of his group, the saxophonist Sonny Rollins and the bassist George Morrow, before briefly taking time off and putting together a new quartet. By the end of the 50’s, seemingly recovered from his depression, he was recording prolifically, mostly as a leader but occasionally as a sideman with Mr. Rollins and others. The personnel of Mr. Roach’s working group changed frequently over the next decade, but the level of artistry and innovation remained high. His sidemen included such important musicians as the saxophonists Eric Dolphy, Stanley Turrentine and George Coleman and the trumpet players Donald Byrd, Kenny Dorham and Booker Little. Few of his groups had a pianist, making for a distinctively open ensemble sound in which Mr. Roach’s drums were prominent. Always among the most politically active of jazz musicians, Mr. Roach had helped the bassist Charles Mingus establish one of the first musician-run record companies, Debut, in 1952. Eight years later, the two organized a so-called rebel festival in Newport, R.I., to protest the Newport Jazz Festival’s treatment of performers. That same year, Mr. Roach collaborated with the lyricist Oscar Brown Jr. on “We Insist! Freedom Now Suite,” which played variations on the theme of black people’s struggle for equality in the United States and Africa. The album, which featured vocals by Abbey Lincoln (Mr. Roach’s frequent collaborator and, from 1962 to 1970, his wife), received mixed reviews: many critics praised its ambition, but some attacked it as overly polemical. Mr. Roach was undeterred. “I will never again play anything that does not have social significance,” he told Down Beat magazine after the album’s release. “We American jazz musicians of African descent have proved beyond all doubt that we’re master musicians of our instruments. Now what we have to do is employ our skill to tell the dramatic story of our people and what we’ve been through.” “We Insist!” was not a commercial success, but it emboldened Mr. Roach to broaden his scope as a composer. Soon he was collaborating with choreographers, filmmakers and Off Broadway playwrights on projects, including a stage version of “We Insist!” As his range of activities expanded, his career as a bandleader became less of a priority. At the same time, the market for his uncompromising brand of small-group jazz began to diminish. By the time he joined the faculty of the University of Massachusetts in 1972, teaching had come to seem an increasingly attractive alternative to the demands of the musician’s life. Joining the academy did not mean turning his back entirely on performing. In the early ‘70s, Mr. Roach joined with seven fellow drummers to form M’Boom, an ensemble that achieved tonal and coloristic variety through the use of xylophones, chimes, steel drums and other percussion instruments. Later in the decade he formed a new quartet, two of whose members — the saxophonist Odean Pope and the trumpeter Cecil Bridgewater — would perform and record with him off and on for more than two decades. He also participated in a number of unusual experiments. He appeared in concert in 1983 with a rapper, two disc jockeys and a team of break dancers. A year later, he composed music for an Off Broadway production of three Sam Shepard plays, for which he won an Obie Award. In 1985, he took part in a multimedia collaboration with the video artist Kit Fitzgerald and the stage director George Ferencz. Perhaps his most ambitious experiment in those years was the Max Roach Double Quartet, a combination of his quartet and the Uptown String Quartet. Jazz musicians had performed with string accompaniment before, but rarely if ever in a setting like this, where the string players were an equal part of the ensemble and were given the opportunity to improvise. Reviewing a Double Quartet album in The Times in 1985, Robert Palmer wrote, “For the first time in the history of jazz recording, strings swing as persuasively as any saxophonist or drummer.” This endeavor had personal as well as musical significance for Mr. Roach: the Uptown String Quartet’s founder and viola player was his daughter Maxine. She survives him, as do two other daughters, Ayo and Dara, and two sons, Raoul and Darryl. By the early ‘90s, Mr. Roach had reduced his teaching load and was again based in New York year-round, traveling to Amherst only for two residencies and a summer program each year. He was still touring with his quartet as recently as 2000, and he also remained active as a composer. In 2002 he wrote and performed the music for “How to Draw a Bunny,” a documentary about the artist Ray Johnson. http://www.nytimes.com/2007/08/16/ar...-roach.html?hp  See Who's Editing Wikipedia - Diebold, the CIA, a Campaign John Borland On November 17th, 2005, an anonymous Wikipedia user deleted 15 paragraphs from an article on e-voting machine-vendor Diebold, excising an entire section critical of the company's machines. While anonymous, such changes typically leave behind digital fingerprints offering hints about the contributor, such as the location of the computer used to make the edits. In this case, the changes came from an IP address reserved for the corporate offices of Diebold itself. And it is far from an isolated case. A new data-mining service launched Monday traces millions of Wikipedia entries to their corporate sources, and for the first time puts comprehensive data behind longstanding suspicions of manipulation, which until now have surfaced only piecemeal in investigations of specific allegations. Wikipedia Scanner -- the brainchild of CalTech computation and neural-systems graduate student Virgil Griffith -- offers users a searchable database that ties millions of anonymous Wikipedia edits to organizations where those edits apparently originated, by cross-referencing the edits with data on who owns the associated block of internet IP addresses. Inspired by news last year that Congress members' offices had been editing their own entries, Griffith says he got curious, and wanted to know whether big companies and other organizations were doing things in a similarly self-interested vein. "Everything's better if you do it on a huge scale, and automate it," he says with a grin. This database is possible thanks to a combination of Wikipedia policies and (mostly) publicly available information. The online encyclopedia allows anyone to make edits, but keeps detailed logs of all these changes. Users who are logged in are tracked only by their user name, but anonymous changes leave a public record of their IP address. The organization also allows downloads of the complete Wikipedia, including records of all these changes. Griffith thus downloaded the entire encyclopedia, isolating the XML-based records of anonymous changes and IP addresses. He then correlated those IP addresses with public net-address lookup services such as ARIN, as well as private domain-name data provided by IP2Location.com. The result: A database of 5.3 million edits, performed by 2.6 million organizations or individuals ranging from the CIA to Microsoft to Congressional offices, now linked to the edits they or someone at their organization's net address has made. Some of this appears to be transparently self-interested, either adding positive, press release-like material to entries, or deleting whole swaths of critical material. Voting-machine company Diebold provides a good example of the latter, with someone at the company's IP address apparently deleting long paragraphs detailing the security industry's concerns over the integrity of their voting machines, and information about the company's CEO's fund-raising for President George Bush. The text, deleted in November 2005, was quickly restored by another Wikipedia contributor, who advised the anonymous editor, "Please stop removing content from Wikipedia. It is considered vandalism." A Diebold Election Systems spokesman said he'd look into the matter but could not comment by press time. Wal-Mart has a series of relatively small changes in 2005 that that burnish the company's image on its own entry while often leaving criticism in, changing a line that its wages are less than other retail stores to a note that it pays nearly double the minimum wage, for example. Another leaves activist criticism on community impact intact, while citing a "definitive" study showing Wal-Mart raised the total number of jobs in a community. As has been previously reported, politician's offices are heavy users of the system. Former Montana Senator Conrad Burns' office, for example, apparently changed one critical paragraph headed "A controversial voice" to "A voice for farmers," with predictably image-friendly content following it. Perhaps interestingly, many of the most apparently self-interested changes come from before 2006, when news of the Congressional offices' edits reached the headlines. This may indicate a growing sophistication with the workings of Wikipedia over time, or even the rise of corporate Wikipedia policies. Wikipedia founder Jimmy Wales told Wired News he was aware of the new service, but needed time to experiment with it before commenting. The vast majority of changes are fairly innocuous, however. Employees at the CIA's net address, for example, have been busy -- but with little that would indicate their place of apparent employment, or a particular bias. One entry on "Black September in Jordan" contains wholesale additions, with specific details that read like a popular history book or an eyewitness' memoir. Many more are simple copy edits, or additions to local town entries or school histories. One CIA entry deals with the details of lyrics sung in a Buffy the Vampire Slayer episode. Griffith says he launched the project hoping to find scandals, particularly at obvious targets such as companies like Halliburton. But there's a more practical goal, too: By exposing the anonymous edits that companies such as drugs and big pharmaceutical companies make in entries that affect their businesses, it could help experts check up on the changes and make sure they're accurate, he says. For now, he has just scratched the surface of the database of millions of entries. But he's putting it online so others can look too. The nonprofit Wikimedia Foundation, which runs Wikipedia, did not respond to e-mail and telephone inquiries Monday. http://www.wired.com/politics/online...8/wiki_tracker  Wikipedia is Only as Anonymous as Your IP Virgil Griffith, a good friend and fellow hacker, reminds us today that anonymity on the internet does not really exist. With his newly released search tool Wikiscanner, you can search an index of 35 million Wikipedia edits by IP, allowing you to find edits coming from within organizations like the CIA or the EFF (bonus if you can find something about Kevin Bankston smoking). Finding out that someone from the Fox News network changed this: The lawsuit focused a great deal of media attention upon Franken's book and greatly enhanced its sales. Reflecting later on the lawsuit during an interview on the [[National Public Radio]] program ''[[Fresh Air]]'' on [[September 3]], [[2003]], Franken said that Fox's case against him was "literally laughed out of court" and that "wholly (holy) without merit" is a good characterization of Fox News itself. into The lawsuit focused a great deal of media attention upon Franken's book and greatly enhanced its sales. Reflecting later on the lawsuit during an interview on the liberal [[National Public Radio]] program ''[[Fresh Air]]'' on [[September 3]], [[2003]], Franken said that Fox's case against him was the best thing to happen to his book sales. is quite amusing. Time for crowdsourcing to find the gems in there and report them over at Wired's wikiwatch. http://radar.oreilly.com/archives/20...dia_is_on.html  Dutch Bloggers Due in Court over Filming Under Skirts Two Dutch news bloggers caught filming under women's skirts in a car park in order to warn the public of the intimate views afforded by see-through stairs must appear in court, according to their blog. A court spokesman in Alkmaar, where the pair have been called to appear in October, said they had been charged with filming people without permission after someone complained. The bloggers say the women knew that they were being filmed. The subterranean car park in the northern Dutch town of Heerhugowaard has a transparent ceiling in its stairwell, allowing people to look up at shoppers passing above. The Geen Stijl blog said they were only filming to see whether the local council had done anything about the transparent ceiling after the issue was brought to their attention several months before. The two bloggers could face a two-month prison sentence, according to Dutch news agency ANP. http://www.reuters.com/article/oddly...80160520070814  British Rail Passengers to Get Free Wi-Fi Ride Andy McCue Rail passengers on the London-to-Scotland east coast main line will get free Wi-Fi as part of National Express' 1.4 billion-pound ($2.8 billion) winning bid to run the franchise. National Express plans to take over the rail route from GNER in mid-December after fending off competition for the franchise from Arriva, FirstGroup, Stagecoach and Virgin Trains. GNER completed the approximately $6.5 million installation of Wi-Fi broadband connectivity on all 41 of its east coast trains last year, and although the service has been free for first-class passengers, those in standard (coach) are charged either $5.96 per half hour or $20.11 for a full day's use. But in addition to faster journey times, National Express has also promised to extend free Wi-Fi to passengers in standard class as part of its seven-year contract. The on-board Wi-Fi uses a combination of a satellite link and mobile 3G/GPRS networks to maintain 100 percent connectivity, even when going through tunnels. Now on News.com Road Trip 2007: Thousands of miles, tons of tech Family togetherness a la videoconference Far from 'The Jetsons,' air cars for commuters Extra: Getting serious about gaming A server from Swedish company Icomera on the train provides a 2MB satellite downlink, which is combined with the mobile connectivity. Wireless access points are then fitted at the end of each carriage on a train, which connect to the main onboard satellite server and can support about 40 simultaneous users in each carriage at a time. National Express said it will also build a simpler "one-stop shop" Web site to highlight the cheapest tickets available, introduce smart cards by 2010, provide real-time travel updates to mobile phones, and allow passengers to print tickets at home or use "m-tickets" through their mobile phones. Andy McCue of Silicon.com reported from London. http://news.com.com/British+rail+pas...3-6202446.html  The Road to Clarity Joshua Yaffa “So, what do you see?” Martin Pietrucha I asked, turning around in the driver’s seat of his mint green Ford Taurus. It was a cold day in January, and we were parked in the middle of a mock highway set on the campus of Pennsylvania State University in State College. Pietrucha is a jovial, 51-year-old professor of highway engineering. His tone was buoyant as he nodded toward the edge of the oval stretch of road where two green-and-white signs leaned against a concrete barrier. What I saw, Pietrucha knew, was what we all may see soon enough as we rush along America’s 46,871 miles of Interstate highways. What I saw was Clearview, the typeface that is poised to replace Highway Gothic, the standard that has been used on signs across the country for more than a half-century. Looking at a sign in Clearview after reading one in Highway Gothic is like putting on a new pair of reading glasses: there’s a sudden lightness, a noticeable crispness to the letters. The Federal Highway Administration granted Clearview interim approval in 2004, meaning that individual states are free to begin using it in all their road signs. More than 20 states have already adopted the typeface, replacing existing signs one by one as old ones wear out. Some places have been quicker to make the switch — much of Route I-80 in western Pennsylvania is marked by signs in Clearview, as are the roads around Dallas-Fort Worth International Airport — but it will very likely take decades for the rest of the country to finish the roadside makeover. It is a slow, almost imperceptible process. But eventually the entire country could be looking at Clearview. The typeface is the brainchild of Don Meeker, an environmental graphic designer, and James Montalbano, a type designer. They set out to fix a problem with a highway font, and their solution — more than a decade in the making — may end up changing a lot more than just the view from the dashboard. Less than a generation ago, fonts were for the specialist, an esoteric pursuit, what Stanley Morison, the English typographer who helped create Times New Roman in the 1930s, called “a minor technicality of civilized life.” Now, as the idea of branding has claimed a central role in American life, so, too, has the importance and understanding of type. Fonts are image, and image is modern America. As a teenager in Portland, Ore., Meeker ran a small business out of his parents’ house making signs for local stores, cutting letters out of Plexiglas with a band saw. He majored in fine art at the University of Oregon and went on to get a master’s degree in graphic and industrial design at Pratt Institute in New York. In the mid-80s, Meeker created a uniform signage system for the country’s rivers and other navigable waterways for the Army Corps of Engineers. More than 200 people were drowning nationwide each year, most of them during the 30 to 40 minutes around dawn and dusk when sign visibility is especially poor. Graphic design traditionally focuses on problems of layout, but Meeker wondered if the issue wasn’t more basic — namely, the sign surface had to be brighter. He approached 3M, the Minnesota-based manufacturer whose products include Scotch tape and the Post-it note, and proposed the idea of using an unreleased line of yellow fluorescent sign material that would keep its shine during the dark morning and evening hours. “I am just like anybody else who sees a problem with a civic issue and sets out to fix it,” he told me as we sat one afternoon in the living room of his home in the Westchester County suburb of Larchmont. “I’ve always thought that design can be a form of social activism.” In 1989, after his success with the waterways project, the State of Oregon approached Meeker with a commission to think up a roadside sign system for scenic-tour routes. The problem sounded modest enough: Add more information to the state’s road signs without adding clutter or increasing the physical size of the sign itself. But with the existing family of federally approved highway fonts — a chubby, idiosyncratic and ultimately clumsy typeface colloquially known as Highway Gothic — there was little you could add before the signs became visually bloated and even more unreadable than they already were. “I knew the highway signs were a mess, but I didn’t know exactly why,” Meeker recalled. Around the same time Meeker and his team were thinking about how to solve the problem of information clutter in Oregon, the Federal Highway Administration was concerned with another problem. Issues of readability were becoming increasingly important, especially at night, when the shine of bright headlights on highly reflective material can turn text into a glowing, blurry mess. Highway engineers call this phenomenon halation and elderly drivers, now estimated to represent nearly a fifth of all Americans on the road, are most susceptible to the effect. “When the white gets hit, it explodes, it blooms,” Meeker, who has the air of a scruffy academic, went on to say. He placed two road signs side by side on his couch and shined a flashlight at each in quick succession. In the path of the moving beam, the first, a white-on-black street sign from the early 1900s, remained dark; its letters became momentarily lighter but not much brighter. As he moved the light to the second sign, a more modern white-on-blue sign taken from a nearby intersection, its whole surface brightened, sending back waves of light and giving the letters a fuzzy, white glow. Repeated at 70 miles per hour, especially for drivers with impaired vision, the effect is not only annoying but also dangerous. The government’s highway engineers proposed increasing the size of the letters by 20 percent. But larger letters would mean even larger signs, a costly and cumbersome venture that would do little but increase visual clutter on the roadway. “You’re talking about billions of dollars,” Meeker said, explaining that on signs what is taller is also wider. “It wouldn’t just be a question of replacing the signs and all their support structures, but you would have to widen lanes and redo overpasses to make room for these things.” Meeker wasn’t working for the federal highway agency, but in his mind the problem of clutter on signs in Oregon and the federal government’s concern with halation seemed intertwined. Along with researchers from the Pennsylvania Transportation Institute, a highway-research body attached to Penn State that was also interested in questions of sign legibility, Meeker again approached 3M — the manufacturer of most of the country’s reflective sign material — with the idea of joint studies on the relationship between typeface design and halation. What started as a project to organize information for tourist routes in Oregon would soon turn into an all-consuming quest, and one that marked the first time in the nation’s history that anyone attempted to apply systematically the principles of graphic design to the American highway. Road signs first appeared in ancient Rome as stone markers counting the distances to various cities in the empire. In the age of the automobile, they began popping up on the side of the road a little more than a decade after the Ford Motor Company released its first Model T. Auto clubs and state highway departments placed the markings with little thought toward uniformity or consistency, and issues of typography were barely considered. The text that did appear on these early signs was largely hand-painted and all in uppercase, simply because no one could effectively draw lowercase letter forms by hand. Explaining the task of drawing letters, Meeker said: “All capital letters are either straight lines or curved lines. The worst-case scenario is pretty much ‘B.’ ” But lowercase letters, maddening knots full of arcs and curves, present a more serious challenge to the Sunday-afternoon road-sign painter. Hand-drawn signs were difficult to read at night, not because of the halation but because there was simply no shine to catch the driver’s attention. To try to remedy this, municipal sign makers began sprinkling handfuls of coarse sand on the freshly painted letters, followed by experiments with marbles. The first truly reflective sheeting came later, in the early 1940s, when 3M introduced sign material made with a patchwork of glass beads laminated under a plastic film. Until the 1920s, when the development of die-cut technology allowed for the shaping and cutting of thin metal alloy, signs were often idiosyncratic, with layouts and typefaces varying by city and region. But as the popularity and accessibility of long-distance road travel increased, so, too, did the need for coherent nationwide standards. Federally approved fonts first appeared in the 1935 edition of the Manual on Uniform Traffic Control Devices, the bible of federal road and highway standards that dictates the size, shape and placement of road signs. In 1956, President Dwight D. Eisenhower announced his goal of an expanded Interstate System, and highway engineers worked quickly to fashion a rough alphabet by rounding off the square edges of the block lettering created during die-cut sign making. Today, there are six Highway Gothic typefaces in the official Federal Highway Administration series. Most prevalent on the modern highway is the fifth typeface in the family, Series E-Modified, and it is with this that Clearview is most often directly compared. The letter shapes of Highway Gothic weren’t ever tested, having never really been designed in the first place. “It’s very American in that way — just smash it together and get it up there,” says Tobias Frere-Jones, a typographer in New York City who came to the attention of the design world in the mid-1990s with his Interstate typeface inspired by the bemusing, awkward charm of Highway Gothic. “It’s brash and blunt, not so concerned with detail. It has a certain unvarnished honesty.” The quirky appeal of imperfection does give Highway Gothic its fans, who share highway lore and trade vintage road signs on the Internet. To highway enthusiasts like Richard Moeur, who runs a Web site devoted to traffic signs, the existing highway typeface has become evocative of the wonder of the open road. Moeur mentioned one example of the classic highway look “in the wild,” as he calls it, on a stretch of Interstate 40 on the road into Flagstaff, Ariz.: “There it is, in big 16-inch letters and a 3-foot tall Interstate shield, on a sign 10 feet tall by 16 feet wide — ‘I-40 WEST Los Angeles.’ “That sense of possibility has always meant a lot to me,” he says. “For some, a sign is just a utilitarian object. For others, it’s a symbol of connectivity.” Meeker initially assumed that the solution to the nation’s highway sign problem lay in the clean utilitarian typefaces of Europe. One afternoon in the late fall of 1992, Meeker was sitting in his Larchmont office with a small team of designers and engineers. He suggested that the group get away from the computer screens and out of the office to see what actually worked in the open air at long distances. They grabbed all the roadsigns Meeker had printed — nearly 40 metal panels set in a dozen different fonts of varying weights — and headed across the street to the Larchmont train station, where they rested the signs along a railing. They then hiked to the top of a nearby hill. When they stopped and turned, they were standing a couple hundred feet from the lineup below. There was the original Highway Gothic; British Transport, the road typeface used in the United Kingdom; Univers, found in the Paris Metro and on Apple computer keyboards; DIN 1451, used on road and train signage in Germany; and also Helvetica, the classic sans-serif seen in modified versions on roadways in a number of European countries. “There was something wrong with each one,” Meeker remembers. “Nothing gave us the legibility we were looking for.” The team immediately realized that it would have to draw something from scratch. Two designers working with Meeker, Christopher O’Hara and Harriet Spear, set out to create the new typeface, initially based on hand-drawn traces of Highway Gothic. “We wanted to take out the goofiness, to restore some sort of rational relationship to type design,” O’Hara told me. “There are a lot of things about it that don’t make any sense.” O’Hara and Spear started by opening the font up, carving out the cramped interior areas of the letters that trapped light and gave Highway Gothic its notoriously fuzzy quality. The first indication of success came a few months later, in January 1993, when Meeker took O’Hara’s early sketches to Penn State for some human testing. He showed the drawings to Pietrucha and his colleague Philip Garvey, a researcher with a background in human psychology. In Clearview’s first public test, Garvey sat in an office chair in the basement of the Pennsylvania Transportation Institute, with Clearview displayed on a computer screen at the opposite end of the long hallway. To simulate halation, they turned off all the lights and blurred the letters on the monitor. Clearview certainly looked better, but could they prove it? Intrigued by the early positive results, the researchers took the prototype out onto the test track. Drivers recruited from the nearby town of State College drove around the mock highway. From the back seat, Pietrucha and Garvey recorded at what distance the subjects could read a pair of highway signs, one printed in Highway Gothic and the other in Clearview. Researchers from 3M came up with the text, made-up names like Dorset and Conyer — words that were easy to read. In nighttime tests, Clearview showed a 16 percent improvement in recognition over Highway Gothic, meaning drivers traveling at 60 miles per hour would have an extra one to two seconds to make a decision. Word of the Penn State tests soon reached the Texas Transportation Institute, which conducted its own tests and then requested 25 computer disks with Clearview for further testing. “I knew we were onto something,” Meeker says. “But we were still too raw. We needed some polish.” He began asking around for recommendations in the tightly knit world of type design. A friend mentioned the name of James Montalbano, an upstart type designer who had already received some renown for drawing custom fonts for magazines like Glamour and Vanity Fair. Montalbano, now 53 years old, works from a studio on the top floor of a brownstone near the Brooklyn waterfront. He has close-cropped hair and constant stubble, as well as the lumbering, punch-you-in-the-ribs demeanor of a high-school woodshop teacher, a job he in fact held for a year after graduating from Kean University in Union, N.J. In kindergarten in Jersey City, he was scolded for his stubborn insistence on drawing two-tiered lowercase “a” ’s. But it wasn’t until he took a continuing-education class with the type designer Ed Benguiat at the School of Visual Arts in Manhattan in the late 1970s that Montalbano discovered his talent for creating his own type. At their first meeting, a hot, muggy day in the summer of 1995, Meeker came to Montalbano’s apartment to show the early sketches of Clearview. “It was stiff — there wasn’t any sort of grace to it,” Montalbano told me last winter of his initial impressions of the raw typeface. The stem weights were inconsistent, meaning the font looked bolder in some letters and lighter in others, and the baseline levels of the letters were uneven, giving it a wobbly, slightly boozy look. Montalbano recalls interrupting Meeker’s impassioned presentation. “I don’t know much about all this legibility theory,” he remembers saying. “But I do know about poorly drawn type.” He was hired immediately and set to work to sculpture Meeker’s initial drawings into a complete, sellable typeface. “The fundamental flaw of Highway Gothic is that the counter shapes are too tiny,” Montalbano told me, referring to the empty interior spaces of a typeface, like the inside of an “o.” When viewed from a distance, and especially at night under the glare of high-beam headlights, the tightly wound lowercase “a” of Highway Gothic becomes a singular dense, glowing orb; the “e,” a confusing blur of shapes and curved lines. Meeker puts it more bluntly: “They look like bullets that you couldn’t put a pin through.” Montalbano smoothed out the rough, imprecise edges of O’Hara and Meeker’s first version, widening the counter shapes even further. He understood that Clearview’s success would come not from where its shapes are on the sign but precisely in where they are not — the open spaces in Clearview’s letters are what make it so readable. It is as if, as Pietrucha put it that morning on the test track at Penn State, “we put the typeface on a diet”. But selling the government on the idea of adopting Clearview as a road sign font was another matter. Over several years Meeker and Pietrucha went to meetings at the Federal Highway Administration; they would end each one by setting up a row of sample highway signs in the long hallways of the agency’s headquarters. The government’s own engineers were impressed with Clearview, but any immediate progress was slowed by the inevitable forces of inertia and bureaucracy in Washington. “We’d go in each time excited,” Meeker says of their presentations to federal officials. “And we’d leave each time thinking, ‘Why did we even bother?’ ” At times, Clearview receded to the background as both Meeker and Montalbano busied themselves with other, more immediately fruitful design work. But they would keep returning to the font for minor changes: an adjustment in thickness here, a change in letter spacing there. “Those guys are tinkerers,” Pietrucha says of Meeker and Montalbano. “They were always playing around, wondering how we could optimize it. We had something we called Clearview, but was there a Clearer-view? Or a Clear-est view?” Type is just as much about psychology as geometry. A letter’s shape, its curves, the way it sits next to other letters — all these factors give a font its personality and in turn create an emotion and connotation for the reader. Clearview is a sans-serif face, meaning the terminal points of its letters lack any ornamental lines, wedges and other shapes. It wasn’t until the 1920s that sans-serif came into wide use with typefaces like Futura and later, in the ’50s, Helvetica, but they are now the typeface style of choice for any design job requiring a clean, vaguely futuristic aesthetic. The clear, pristine shapes of sans-serif fonts grab the eye in an instant, lending themselves to advertising copy and large, punchy headlines as well as highway signs. But in large blocks of text, the detailed edges of the letter forms in serif fonts give the type an easy-to-follow flow reminiscent of cursive script, making them the preferred typeface for newspapers, magazines and books. There are some typefaces that work for selling estate jewelry and others that seem to fit in best pushing high-tech toys. Volkswagen’s aggressively plain ads for the Beetle ushered in a new era of straightforward and minimalist advertising in the ’60s. “The Creative Revolution,” as it came to be known in the advertising world, was set off by a few words — “Lemon” and “Think Small” were among the most popular slogans — written in Futura, a typeface chosen for its bare style that spoke to Volkswagen’s message of simple claims and precision engineering. Decades later, in the early 2000s, a light and nimble lowercase typeface style defined the waning years of the dot-com boom. Its casual, approachable look quickly appeared in the logos of corporate behemoths like Cingular, British Petroleum and Accenture. Stodgy or irreverent, timely or timeless, typography helps establish the ethos and identity of a brand — and it can have a similar effect on the highway. “Type on the roadway is very much like the corporate identity of a country,” says Graham Clifford, a friend of Montalbano’s who runs his own branding and design firm in New York. Clifford, who is English, mentioned the ubiquity of British Transport, which has been used in his country since the late 1950s. In the decades since its adoption, it has appeared on T-shirts and in advertisements, much as Highway Gothic has come to infuse the American consciousness. Phil Baines, a London-based typographer, once called British Transport “the house style for Britain.” Other countries have their own style, too. Clifford told of a trip he took with his wife, driving from England through Wales, then crossing by ferry to Ireland and up to Northern Ireland. Many signs in and around Dublin were written in a quirky local script; the markers in Belfast, however, were uniformly British Transport. “The change in typeface lets you know you’re in a different place,” Clifford said. It can also let you know you’re in a different time. In 1941, Hitler abandoned the ornate blackletter typeface that had been a text standard in Germany since the Gutenberg era. Party propaganda was then printed in a roman serif typeface, giving the Nazi regime a starkly modernist identity. “Typography is all about tone of voice,” Clifford says. “Do I shout at people? Do I whisper at people? Do I scream from the rooftops? Am I talking to a woman? To a man?” Highway Gothic conjures the awe of Interstate travel and the promise of midcentury futurism; Clearview’s aesthetic is decidedly more subdued. “It’s like being a good umpire,” Pietrucha says, suggesting that one of Clearview’s largest triumphs will be how quietly it replaces Highway Gothic sign by sign in the coming years. “It will completely change the look of the American highway, but not so much that anyone will notice.” As Montalbano tweaked Clearview’s design, a problem continued to gnaw at him. Thicker, darker letters are more recognizable on signs, but they can also lead to dense, bloblike shapes that tend to blur, especially at night — the main downfall of Highway Gothic. How could he increase Clearview’s profile, Montalbano wondered, without repeating the same designs mistakes of its predecessor? The answer would come thanks to a branding crisis at the National Park Service. In the summer of 1998, the park service had just received some alarming news: According to one survey, the vast majority of Americans were under the false impression that Smokey Bear worked for the National Park Service and not the Forest Service. At the time, the park service was using a mismatched collection of a half-dozen typefaces on its road signs, wayposts and other printed materials. A signature typeface, it reasoned, would help to solve its brand-recognition problem. The park service hired Montalbano and Meeker to come up with one. After considering various existing faces, Montalbano ended up drawing a stately looking serif that he dubbed Rawlinson, his wife’s last name. “My father-in-law worked for the Forest Service,” he told me, “so I thought I’d name the park service font after him, just to keep the confusion alive.” They sent the typeface to Penn State for testing; it came back showing only a 2 percent improvement in legibility over Clarendon, the serif font in use at the time on the park service’s road signs. Montalbano received a call from a worried Meeker. “We knew that no bureaucracy would ever change anything for a 2 percent improvement,” Montalbano says. To increase recognition at longer distances, Montalbano tried pulling up the height of the lowercase letters, bringing them almost level with the height of the capitals. In typographic jargon, this measure is known as the x-height, based on the level of the top of the lowercase x, and even more than the shapes of the letter forms themselves, it can give a typeface an individual character. Montalbano explained this idea over lunch at a cafe across the street from his office in Brooklyn. “If a word is set in all caps, all you will see are little white rectangles,” he said, scribbling a quick “HELLO” on a napkin. The word looked heavy, almost industrial. “But this has a definite profile,” he continued, and then he drew “Hello” again on another napkin, this time in a mix of upper- and lowercase letters, its peaks and curves and dips setting off all the necessary clues in the subconscious. He held the paper in front of me. As he slowly pulled it farther away, the individual letters became harder to read, but the shape of the word remained distinct. “Your brain,” he concluded, “knows the shape of the word.” With an increased x-height, Rawlinson showed a significant improvement in legibility while taking up 15 percent less sign space than the heavy, powerful-looking Clarendon. “I called Don up right away and told him, ‘I want to apply this same idea to Clearview,’ ” Montalbano said. Meeker and Montalbano staged a demonstration a few weeks later at the Penn State test track, spending a few thousand dollars of their own money to print up highway signs with the new version of Clearview. They invited representatives from the Federal Highway Administration and transportation officials from half a dozen states. The group stood on the tarmac and stared at a side-by-side comparison of Clearview and Highway Gothic. “Signs that you’d be hard pressed to read at 700 feet were legible at 900 or 1,000 feet,” Montalbano said. “People were really freaked out”. Clearview, then, had succeeded in its mission: It made signs easier to read from a distance and reduced the distracting nighttime blur of halation. But its most visible debut came not on the highway but on the oversize billboards of Times Square. On New Year’s Day 2006, AT&T revealed its redesigned brand image. Clearview was featured in headlines, billboards and advertising copy, as well as on huge banners plastered around Midtown Manhattan. The company wanted to project “a more welcoming and transparent image,” says Wendy Clark, a senior vice president in charge of advertising at AT&T. For more than a decade, the company had been using Gill Sans, a leaden, staid typeface from the 1920s. Market research showed that many consumers identified the old AT&T with attributes like “monolithic” and “bureaucratic” — an image problem it hoped to fix, in part, with a new typeface. “Clearview is approachable,” says Craig Stout, a creative director at Interbrand, the agency that oversaw the AT&T campaign. “It isn’t shouting at you to get your business.” A year after AT&T began using Clearview for all its advertising and corporate communications, Interbrand conducted a follow-up survey, asking consumers, “Do you consider AT&T to be a technologically savvy brand?” Positive responses had doubled. “The highway stuff is what got me into it, but it’s the font’s other applications that have me really excited,” Montalbano says. In addition to creating a parallel Clearview type family for standard design applications, he is also working on converting it into foreign scripts. There is already a special Latin alphabet designed for Eastern European languages. The Week in Review is edited and published by Jack Spratts. Maxim Zhukov, a Russian typographer, is adapting the type design for translation into Cyrillic. That a typeface originally inspired by a problem with tourist signage in Oregon could one day line the cavernous halls of the Moscow metro is not so much a testament to Clearview’s functional, universal appeal as it is to typography’s strange and enigmatic power of reincarnation. “The real life of a font is mysterious and unpredictable,” Zhukov says. Certainly that has been the case with Clearview. Oregon, as it happens, has yet to adopt the typeface. A couple months ago, Meeker’s 12-year-old son, Eric, had his own unplanned encounter with the typeface. He had a homework assignment due in his seventh-grade English class, Eric told me, and in a rush, he printed a document — a fictionalized journal entry from the Civil War — from a computer in his dad’s downstairs office. Hurrying out the door, he didn’t notice it had printed in Clearview. A few days later, his teacher handed the assignments back. “Great job,” he said to Eric. He paused, then added, “There was just something about it that made it so easy to read.” http://www.nytimes.com/2007/08/12/ma...12fonts-t.html  Ex-Adman Says He Began Poe Toast UPI In a twist on the tell-tale heart tale, a former adman said he started the homage of roses and cognac laid at the Baltimore grave of writer Edgar Allan Poe. Sam Porpora, a 92-year-old Poe devotee, said he began the tradition in the late 1960s as a publicity stunt to aid the church that owned Westminster cemetery, where the author is said to be buried, the Baltimore Sun reported Wednesday. Once he "restored Poe to greatness," Porpora said he retired from the toasting business and wasn't sure who kept up the midnight presentation since. Others differ with Porpora's recollection. Jeff Jerome, Poe House and Museum curator, said his research indicated the ritual dates to 1949, the 100th anniversary of the death of the writer, who died mysteriously in Baltimore at age 40. Through the years, several people have claimed the connection, Jerome told the Sun but few had Porpora's credentials. He was a parishioner of Westminster Church, a caretaker for the adjoining cemetery and its longtime tour guide. "He is very enthusiastic about Poe and Baltimore history," said Jerome, who added he can't substantiate Porpora's claim. http://www.upi.com/NewsTrack/Enterta...oe_toast/4128/  Knowledge Networks Pays $300,000 to Settle Internal Copyright Complaint Firm's marketing group distributed press packets to employees containing newspaper and magazine articles under copyright Grant Gross Analyst firm Knowledge Networks has agreed to pay $300,000 to settle a complaint that it distributed news articles to its employees without permission of the copyright owners, a trade group announced Thursday. The Knowledge Networks settlement is the first under the Software & Information Industry Association's Corporate Content Anti-Piracy Program, launched in October. Knowledge Networks' marketing group had been distributing press packets to some employees on a regular basis, the SIIA said. Those packets contained articles under copyright and owned by SIIA members such as the Associated Press, United Press International, and publishing company Reed Elsevier, the trade group said. SIIA litigation counsel Scott Bain called Knowledge Networks a "reputable company that made a very costly mistake." One of SIIA's goals for the settlement is to deter copyright infringement and educate other companies about the need for compliance programs, he said. A Knowledge Networks spokesman declined to talk about the case in detail. "We are happy the matter has been resolved amicably," said spokesman Dave Stanton. Knowledge Networks, based in Menlo Park, Calif., has agreed to take steps to avoid further problems, including sending its staff to an SIIA copyright course, SIIA said. In a statement distributed by SIIA, Knowledge Networks said it regretted the actions. "[We] disseminated copies of relevant newspaper and magazine articles in the good faith belief that it was lawful to do so," the company said in the statement. "We now understand that practice may violate the copyright rights of those publications. We regret that those violations may have occurred and we are pleased that this matter has now been resolved." Asked if internal distribution of news articles was commonplace at many companies, SIIA's Bain disagreed. "Companies do not do this all the time," he said. "Some companies have compliance procedures in place to keep it from happening." Compliance procedures include staff designated for licensing and compliance, sufficient budgets for the content licensing needs of the company, education programs for staff, deals with major content outlets, and strict policies and internal penalties for violating copyright, Bain said. SIIA learned about the situation through a confidential tip, the trade group said. The person who reported Knowledge Networks will receive a $6,000 reward. http://www.infoworld.com/article/07/...mplaint_1.html  Lifejackets for Newspapers Henry Blodget, the CEO and Editor-n-Chief of Silicon Alley Insider, has conducted a hypothetical analysis of the economics of newspapers gone solely digital, called Running the Numbers: Why Newspapers Are Screwed. Blodget leads in with a obvious caution about the distinction between the online and off-line economies in advertising: Newspaper content generates way more revenue in the physical world than it does online, because offline it can be packaged with classifieds and display ads and actually sold. In the online world, meanwhile, it has to be given away, and because classified ads are now run by classified sites and newspaper sites are only one of dozens of places where people get news, the advertising opportunity is comparatively tiny. So warned, he sets up the scenario: [L]et's pretend that, tomorrow morning, every print reader stops buying the paper, and, instead, reads it online. To be safe, let's further assume that each offline "subscription" actually encompasses two or three readers. In other words, let's pretend that, tomorrow, print circulation goes to zero, and online readership jumps by 2.5 million. What would happen to the business? 1. The company would eliminate paper, distribution, printing, and all other physical production costs. 2. Online inventory (and, therefore, revenue) would increase by about 33% (7.5mm to 10mm users) 3. Content creation costs would stay the same. (The site would have to pay the freight for all the content it now gets for free). 4. All print revenue--ads and circulation--would vaporize. Mr. Blodget then itemizes the necessary assumptions, or variable settings, for costs and revenues, all of which are fairly conservative, and most-likely over-generous towards newspapers. The results? Revenue drops by more than half, 40%-50% of employees get fired, and the company still loses money. Using the NYT's Q2 numbers and these assumptions, for example, revenue would have dropped from $789 million to $285 million. More importantly, EBITDA (earnings before interest, taxes, depreciation, and amortization) would have dropped from $118 million to -$64 million. Which means that management would just be getting ready to fire a few hundred more people. While perhaps an extreme portrait, this is not necessarily an unrealistic extension of the prevailing expectations for news delivery in the near term. Perhaps it takes a mogul to raise a newspaper. http://radar.oreilly.com/archives/20...ckets_for.html  San Jose Semaphore's Message Atop Adobe Building Is . . . Sal Pizarro  The code is cracked. And for anyone who thought a simple message was being transmitted by the rotating disks atop the Adobe tower in downtown San Jose, boy, were you wrong. The message of San Jose Semaphore is the entire text of the Thomas Pynchon book, "The Crying of Lot 49." The solution was discovered by two Silicon Valley tech workers, Bob Mayo and Mark Snesrud, who received a commendation at San Jose City Hall today. Using both the rotating disks and the art project's audio broadcast, they deciphered a preliminary code based on the James Joyce novel, "Ulysses," which was the key to solving the entire message. It took them about three weeks. "It was not a real easy thing to figure out," said Snesrud, a chip designer for Santa Clara based W&W Communications. Ben Rubin, the New York artist who developed the project, applauded the duo's "computational brute force" in finding the message. "I'm especially glad the code was cracked and that it was done in a very classical way," Rubin said. The Pynchon book, written in the mid-1960s, is set in a fictional California city filled with high-tech campuses. It follows a woman's discovery of latent symbols and codes embedded in the landscape and local culture, Rubin said. The semaphore is made up of four 10-foot wide disks, which are composed of 24,000 light-emitting diodes. The disks each have a dark line going from one end to another and twirl around every eight seconds to create a new pattern. It made its debut on Aug. 7, 2006 as part of the ZeroOne digital art festival. Rubin said there are no plans to stop the semaphore or change its message - at least for the time being. "It'll change the way people look it," Rubin said of having the solution known. "Maybe in a few years, we'll revisit it." http://www.mercurynews.com/search/ci_6620943  The Times’s First Home Is Being Torn Down David W. Dunlap  After enduring a century and a half of change in Lower Manhattan, decrepit and anonymous, the birthplace of The New York Times is now being torn down, brick by brick. By an odd turn of history, the demolition of The Times’s oldest home occurred just as the company settles into its seventh and newest headquarters, a 52-story tower across Eighth Avenue from the Port Authority Bus Terminal. Yesterday, a worker armed with an appropriately 19th-century demolition tool — a sledgehammer — sat astride the south wall of 113 Nassau Street, between Ann and Beekman Streets, pounding chunks of the structure into dust. “Little old building,” Margaret Moffatt said wistfully as she walked by on her lunch hour with some colleagues, one of whom, Henry Raven, was a bit more sarcastic. “Making way for progress,” he said. (Actually, it may be making way for a 28-story residential building, to judge from applications filed with the city’s Department of Buildings. The owners did not respond to telephone messages yesterday.) What Ms. Moffatt and Mr. Raven did not know — few New Yorkers do — is that Volume 1, Number 1 of The New-York Daily Times, four pages for one penny, was published at 113 Nassau Street on Sept. 18, 1851. The newspaper stayed there until 1854, when it moved a bit closer to City Hall. This six-story building was, in other words, a journalistic log cabin. And it was not much more accommodating. There was no glass yet in the windows on the evening when The Times first went to press. Breezes blew through the place, extinguishing the candlelight. “All was raw and dismal,” Augustus Maverick wrote in his 1870 biography of Henry J. Raymond, the founding editor. Raw and dismal it remained. What little architectural integrity the building possessed was all but wiped away in the 1970s when it became a McDonald’s. The property was put up for sale in 2004. The New York Times Company had no interest in buying it. There was no serious talk of landmark designation. From 113 Nassau Street, Raymond declared in his first editorial that The Times would present “all the news of the day from all parts of the world” and appear “for an indefinite number of years to come.” He said something else on that long-ago September day: “No newspaper, which was really fit to live, ever yet expired for lack of readers.” Where these words were written is now a pile of rubble. http://www.nytimes.com/2007/08/15/nyregion/15times.html Until next week, - js.  Current Week In Review  Recent WiRs - August 11th, August 4th, July 28th, July 21st, July 14th, July 7th Jack Spratts' Week In Review is published every Friday. Submit letters, articles and press releases in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. Questions or comments? Call (617) 939-2340, country code U.S.. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|
|

|
|
|
#3 |
|
Madame Comrade
Join Date: May 2000
Location: Area 25
Posts: 5,587
|
What a beautiful editorial, Jack. Classy, poetic writing.
 - tg 
__________________
My Blog: Reflections on P2P Revolution |
|
|

|
|
|
#4 |
|
Thanks for being with arse
Join Date: Jan 2002
Location: The other side of the world
Posts: 10,343
|
I enjoyed that story as well Jack
My old Grandmother is still kicking around at 95 but she can't remember who any of us are she has half a dozen great grand children and a few great great grand children..but I don't think she remembers any. I would love to see her before she goes but she just wouldn't be able to remember me.. and I was her first grandkid! hehe oh well such is life... I feel like theres a good chance I will go that way...my Dad is 80 and I think he maybe is starting to some signs of it.. |
|
|

|
|
|
#5 |
|
Join Date: May 2001
Location: New England
Posts: 10,015
|
thanks guys.
tg, it's good to see you around! and multi, 95 eh? sounds like some good genes in there too.  - js. |
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - April 14th, '07 | JackSpratts | Peer to Peer | 1 | 11-04-07 11:26 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |