
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 |
|
Join Date: May 2001
Location: New England
Posts: 10,016
|
Since 2002
  "That's alright, let me answer his question." – John Kerry "In the end it doesn’t matter how many people toil on a work of art, or how much money is spent on it. The artist’s freedom includes the right to say, 'This is not a work of art unless I say so.'" – Roberta Smith "I steal music too, I'm not gonna say I don't." – Trent Reznor "I'm guessing that 'asstunnel' is what you get when a European whose first language isn't English tries to say 'asshole.' It seemed awkward when I first read the response, but the expression has since grown on me." – Ryan Paul "So far the story has only been on techie, geek web sites where everybody already hates us." – Jay Mairs "If they want to get their revenue up they should slash their prices." – Jarret A. Zafran "MediaDefender's entire business model has been based on recognition of the inescapable fact that litigation cannot stop the spread of content on the Internet, so it is ironic that the company has turned to legal threats." – Ryan Paul "I realized, oh my gosh, I'm sitting here, I'm a fat 50-year-old mom and I've managed to scoop al-Qaida. It gets really challenging when you're trying to do that and cook spaghetti at the same time." – Laura Mansfield "He's probably thinking something like, 'I wish they'd stop tasering this guy so I could go home and watch this guy getting tasered on YouTube.'" – Stephen Colbert "You’re not Jesus, are you?" – Rainey "Want a nut! Want a nut! Nnn ... uh ... tuh." – Alex September 22nd, 2007  Tor Anonymity Server Admin Arrested Chris Soghoian In a recent blog posting, a German operator of a Tor anonymous proxy server revealed that he was arrested by German police officers at the end of July. Although he was released shortly afterwards, information about the arrest had been kept quiet until his lawyers were able to get the charges dropped. Tor is a privacy tool designed to allow users to communicate and browse anonymously on the Internet. It's endorsed by the Electronic Frontier Foundation and other civil liberties groups as a method for whistle blowers and human rights workers to communicate with journalists. Tor provides anonymous Web-browsing software to hundreds of thousands of users around the world, according to its developers. The largest numbers of users are in the United States, the European Union and China. The police were investigating a bomb threat posted to an online forum for German police officers. The police traced one of the objectionable posts on the forum to the IP address for Janssen's server. Up until his arrest, Alex Janssen's Tor server carried more than 40GB of random strangers' Internet traffic each day. Showing up at his house at midnight on a Sunday night, police cuffed and arrested him in front of his wife and seized his equipment. In a display of both bitter irony and incompetence, the police did not take or shutdown the Tor server responsible for the traffic they were interested in, which was located in a different city, more than 500km away. Janssen's attempts to explain what Tor is to the police officers initially fell on deaf ears. After being interrogated for hours, someone from the city of Düsseldorf's equivalent of the Department of Homeland Security showed up and admitted to Janssen that they'd made a mistake. He was released shortly after. Germany is clearly not going out of its way to make computer security researchers and activists feel too welcome. Germany recently passed a law that "renders the creation and distribution of software illegal that could be used by someone to break into a computer system or could be used to prepare a break in. This includes port scanners like nmap, security scanners like nessus [as well as] proof of concept exploits." Back in summer 2006, German authorities conducted a simultaneous raid of seven different data centers, seizing 10 Tor servers in the process. Agents took the servers believing them to be related to a child porn investigation. Furthermore, in 2003 a German court ordered the developers of the Jap anonymity system, a completely different project than Tor, to create a back-door in their system to be used in national security investigations. This event does raise some interesting legal questions. If 40GB of other people's Internet traffic flows through your own home network, can authorities, be they the RIAA or FBI, reasonably link anything that has been tracked to your computer's IP address to you? Does setting up a Tor server give you the ultimate plausible deniability card? "No officer, that BitTorrent download wasn't mine. It was from one of the thousands of people who route their Internet traffic through the anonymizing sever on my home network." The ability to have a believable claim to plausible deniability is something that some of us have been attempting to get for a while by having an open wireless access point at home. And 40GB of Internet traffic from perfect strangers may be more significant in the eyes of a court than the possibility of one or two of your neighbors connecting to your wireless network. All of this, for now, remains theoretical. No Tor-related case has made it to the courts.. but it's just a matter of time until one does. http://www.cnet.com/surveillance-sta...79225-46.html?  Copying of DVDs, CDs Verboten Digital copies of TV programs banned Erik Kirschbaum Germany's upper house of parliament on Friday approved a controversial copyright law, which makes it all but illegal for individuals to make copies of films and music, even for their own use. The Bundesrat pushed aside criticism from consumer protection groups and passed the law, which makes it illegal for anyone to store DVDs and CDs without permission. The law also covers digital copies from IPTV and TV broadcasts. Consumer groups and the Green Party had campaigned in vain to include a "bagatelle exemption," so that the measure would not "criminalize" youths and other private users. The law is set to take effect in 2008. The law goes beyond previous legislation brought in by the German government to help the entertainment industry. Germany's federal justice minister Brigitte Zypris claimed that the legislative reform brought German law into line with European Union codes. http://www.variety.com/article/VR1117972434.html  German "Anti-Hacker" Law Forces Hacker Sites to Relocate Nate Anderson Germany isn't the place to go if you're 1) a Scientologist or 2) a computer security researcher with a penchant for writing code. We reported earlier on Germany's new "anti-hacker" law, but now that the law has gone into effect, we're starting to see the results. Already a number of security projects have relocated or shut down to avoid any possibility of prosecution under the broadly-worded statute. The new law, dubbed "202c" after the section of the German legal code it occupies, bans the distribution and possession of software which has as its primary goal the circumvention of security measures. The Chaos Computer Club, one of the oldest and largest hacker groups in the country, denounced the law, saying, "Forbidding this software is about as helpful as forbidding the sale and production of hammers because sometimes they also cause damage." It's not fully clear how the new law will be applied, but several developers are taking a cautious approach. KisMAC, a wireless sniffer and encryption cracker for Mac OS, went dark in late July; now, the KisMAC web site has a politically-charged message for visitors. "One of the major exporters in the world prohibits production and distribution of security software (StGB §202c)," it reads. "From a nation of poets and thinkers to a nation of bureaucrats and ignoramuses." Still, KisMAC will live on. The site promises a move to a Dutch server soon, and relocating to servers outside the country appears to be a popular option. Phenoelit, a group that publishes securty exploits and maintains a large list of default passwords, has moved its material to a US server because "of the new law that makes possessing 'hacker tools' illegal." The Chaos Computer Club, not pleased with the law or its effects, has turned its home page into a message, but there's no sign that modifications to the law might be coming. Fortunately for bored hackers, file-swapping remains only a "petty offense" in Germany. http://arstechnica.com/news.ars/post...-relocate.html  German Music Industry Gets eDonkey Nodes Removed from the Web Following the granting of a number of interim injunctions by regional courts in Hamburg, Cologne, Düsseldorf, Leipzig and Frankfurt, one operator has removed its eDonkey servers from the internet. This is according to a press release from the Deutsche Phonoverbände (IFPI). Because the nodes removed are the major global nodes, this had had a "considerable adverse impact on usage of file-sharing applications." Further interim injunctions against operators of file-sharing application servers for alleged breaches of copyright are to be served in the next few days. The IPFI also obtained interim injunctions against server operators in July. Because eDonkey servers do not themselves offer files for sharing, the copyright owners bringing the action have based their argument on the legal construct of liability for impediment. According to IFPI spokesperson Stefan Michalk, these injunctions are indeed again based on liability for impediment. "Donkey Server No. 1" to "Donkey Server No. 6" have been taken off the web. The host of the server considers itself to have been forced to shut down the servers in order to avoid further injunctions, for the costs of which it would have been liable, because of the, in its opinion, artificially high value of the litigation for the seven interim injunctions so far granted, averaging 195,000 euros. It has "emphatically" told heise online that it had added the filter requested by the opposing party's lawyers immediately upon being made aware of this, and thus long before interim injunctions were obtained. Shutting down the servers did not represent acceptance of any legal obligation. http://www.heise.de/english/newsticker/news/96264  Turkey Blocks Pirate Bay Smaran Turkey has banned what’s arguably the most well known BitTorrent site in existence. Since about a week, The Pirate Bay has become inaccessible in the country. According to a reader from Turkey and the site’s admins, a recent ruling might have caused TPB to be banned. If it’s any consolation, The Pirate Bay is not alone in being blocked. In March, YouTube was banned for hosting videos that insulted the founder of modern Turkey. To the relief of many Turks, the ban only lasted two days, as Google promptly pulled down the videos. And last month, WordPress.com was blocked because some of its users were charged with defamation of a Turkish author. The first we heard of the Pirate Bay block was two days ago, when Cenk, a long-time reader of TorrentFreak from Turkey, e-mailed in to let us know that The Pirate Bay was no longer accessible in his country. Cenk states that since last Monday, government has shut down all access to thepiratebay.org. However, the press has said nothing on the matter. “I did not hear about thepiratebay.org getting sued or anything and even there was no news on the newspaper or anywhere,” he wrote. We asked the TPB guys if they knew anything about this. According to them, it has been blocked “for over a year.” They’re “not sure if it’s the whole country or just the major ISPs,” but “there was some court ruling over it.” That court ruling, we’ve discovered, has ordered Türk Telekom, Turkey’s largest ISP, to block The Pirate Bay, though why exactly is still unknown to both the site’s admins and users of the site in Turkey. There is a comical irony to this all, given that Turkey is the home of some of the most famous real life pirates history has seen, those of the Barbary coast. One can only guess that they have yet to set sail in the intertubes. http://torrentfreak.com/the-pirate-b...ked-in-turkey/  Iran Blocks Access to Google Iran has blocked access to the Google search engine and its Gmail email service as part of a clampdown on material deemed to be offensive, the Mehr news agency reported on Monday. "I can confirm these sites have been filtered," said Hamid Shahriari, the secretary of Iran's National Council of Information. He did not explain why the sites were being blocked. Google, Gmail and several other foreign sites appeared to be inaccessible to Iranian users from Monday morning. Iran has tough censorship on cultural products and internet access, banning thousands of websites and blogs containing sexual and politically critical material as well as women's rights and social networking sites. The rules are applied by Internet Service Providers who use filtering programmes to prevent access to the banned sites. The programmes work by honing in on key words which trigger the blocking of a site, which means that some perfectly anodyne sites are inaccessible as well as more sensitive ones. The filtering aims to prevent Iranians from accessing decadent material posted abroad, a similar goal to the ban on satellite dishes which are subject to period crackdowns. Iran is in the midst of one of its toughest moral crackdowns in years, which has already seen thousands of women warned for failing to obey Islamic dress rules. http://news.yahoo.com/s/afp/20070917...kVj vhewjtBAF  Australia Seeks to Censor the Web THE Federal Police commissioner will have the power to block and ban websites believed to be crime or terrorism related under an internet censorship amendment bill introduced into Parliament today. The bombshell web ban bill was tabled in the Senate at 9:58am, without prior notice. Communications Minister Senator Helen Coonan proposes to expand the "black list" of internet addresses (URLs) currently maintained by the Australian Communications and Media Authority (ACMA) to include terrorism and cyber-crime sites. At present, ACMA has the power to act against websites containing pornography or offensive content. Under the proposed amendment, Federal Police will inform ACMA of websites to be blocked, and the agency must then notify the relevant internet service providers. ISPs will be required to "take reasonable steps" to prevent users accessing the website or content. Australian Privacy Foundation chair Roger Clarke expressed disbelief that "the government of any country in the free world could table a Bill of this kind". "Without warning, the Government, through Senator Coonan, is proposing to provide Federal Police with powers to censor the internet," Dr Clarke said. "Even worse, ISPs throughout the country are to be the vehicle for censorship, by being required to block internet content." Greens Senator Kerry Nettle said the Bill would give the Police Commissioner "enormous power over what political content Australians can look at" on the web. "This gives the Commissioner sweeping powers which could potentially be applied to millions of websites," she said. "The Government has dropped the Bill into the Senate on the eve of an election with virtually no explanation." Senator Nettle said environmental organisations such as Greenpeace had been accused of crime or terrorism-related actions. "Will the Police Commissioner call for Greenpeace's website to be shut down?" The requirement to filter or block content would impose another enormous burden on local ISPs at a time when the IT industry faced growing costs related to other national security legislation, she said. Meanwhile, Senator Coonan today extended the Government's $189 million NetAlert - Protecting Australian Families Online program to agencies such as Medicare, Centrelink, Child Support and the Tax Office. Information about internet filtering and the free content filters from NetAlert will be promoted through the agency shopfronts as part of the plan to prevent children accessing inappropriate material online. http://www.australianit.news.com.au/...-15318,00.html  Thailand Seeks to Block YouTube Videos Again Thailand is seeking to block clips on video-sharing Web site YouTube that accuse the chief royal adviser of masterminding last year's bloodless coup, a top Justice Ministry official said on Friday. The government, which lifted a five-month ban on YouTube in August after it agreed to block clips deemed offensive to revered King Bhumibol Adulyadej, was seeking a court order to block two video clips posted recently on www.youtube.com. "In the next couple of days, we will seek a court order to block those links deemed to cause public confusion and threaten national security," Yanaphon Youngyuen, head of the Justice Ministry's Internet crimes unit, told Reuters. "While awaiting the court order, we are seeking cooperation from Internet service providers to block those links," he said. The two-part postings, entitled "The Crisis of Siam," and running 10:42 minutes and 6:06 minutes, accuse former Prime Minister Prem Tinsulanonda of plotting the September 2006 coup, not the generals who took credit. Such allegations against Prem, now Privy Council chief, have been made by supporters of ousted Prime Minister Thaksin Shinawatra during demonstrations and denied repeatedly by the generals and the government they appointed. "Pa has been through such allegations many times and everyone knows what the truth is," Prem's spokesman, Vice Admiral Prajun Tampratheep, said of the 87-year-old former leader. Last month, the Communications Ministry lifted a ban on YouTube after its owner, Google, installed filters to stop Thais from accessing clips deemed to insult 79-year-old King Bhumibol, a serious offence in Thailand. YouTube said in May it had decided, after an agreement with the Thai government, to block some offending clips but took several months to implement it. Thailand sent YouTube's management a list of 12 video clips it deemed offensive. Six of the clips were removed by their creators or because they violated YouTube's "code of service", YouTube said in a statement. The first king-bashing clip appeared a few days after a 57-year-old Swiss man received a 10-year jail sentence for spraying graffiti on pictures of the King on his birthday in December -- a rare conviction of a foreigner. Bhumibol, the world's longest-reigning monarch who has been on the throne for more than 60 years, granted a pardon and the Swiss man was deported. YouTube was not available for immediate comment on Thailand's latest attempt to block access to some of its clips. http://www.reuters.com/article/media...24089220070921  China Leads Asia in Malicious Online Activity Victoria Ho China leads Asia in malicious online activity, racking up 42 percent of the action in the first half of 2007, up from 39 percent last year. According to Symantec's biannual Internet security threat report released on Wednesday, China topped the Asia-Pacific region, including Japan, in malicious activity, producing the most malicious code, spam zombies, bots and attacks between January 1 and June 30. China's bot-infected computers made up 78 percent of those in the region. Taiwan had the next highest number of bots, but only at 7 percent. China's high level of malicious activity can be attributed to its high rate of counterfeit software. Noting that the majority of China's Windows users use counterfeit versions, Ooi Szu Khiam, a senior security consultant at Symantec Singapore, said during a press briefing: "If you don't have a genuine version, you can't register for patches, and those who don't patch their systems are open to a growing number of exploits." Ooi added that users become "sitting ducks" as they leave themselves open to malicious attacks by not applying security patches. Offering another reason for China's vulnerability, Ooi said: "Resources to build infrastructure is finite, so not enough spending may be directed to securing the networks." Building a proper security system requires a "multiple and mutually supportive defensive system," Ooi said. A security system needs to be secured at all points, including the ISP, network and device. The amount of spam originating from China, which makes up 25 percent of APJ-originating spam, puts China at the top of the list, Ooi said, noting that this volume is driven largely by the vast number of botnets and spam zombies. "All you need to do is install a spam plug-in for your botnet, and the botnet is in action," he said. "Many bots are designed to be used mainly to send spam." Victoria Ho of ZDNet Australia reported from Sydney. http://www.news.com/China-leads-Asia...3-6209172.html  China Claims Man Dies After Three-Day Internet Session A Chinese man dropped dead after playing Internet games for three consecutive days, state media said on Monday as China seeks to wean Internet addicts offline. The man from the southern boomtown of Guangzhou, aged about 30, died on Saturday after being rushed to the hospital from the Internet cafe, local authorities were quoted by the Beijing News as saying. "Police have ruled out the possibility of suicide," the newspaper said, adding that exhaustion was the most likely cause of death. It did not say what game he was playing. China, worried about the spread of pornography and politically incorrect content, has banned the opening of new cybercafes this year and issued orders limiting the time Internet users can spend playing online. In April, President Hu Jintao launched a campaign to rid the Internet of "unhealthy" content and make it a platform for Communist Party doctrine. http://news.yahoo.com/s/nm/20070917/...8aCQkYNQqOOrgF  Poll Shows Support for Banning Items from China Rob Varnon American companies that have been profiting by slapping their brands on Chinese-made goods might want to institute some quality control -- or find some factories in the United States -- fast. A Sacred Heart University national poll of consumer sentiment about imported goods showed more than 80 percent of people surveyed agreed with suspending Chinese imports of food and other products until they meet U.S. standards. In the survey, released Tuesday, even more people said they "have confidence in American-made and distributed products and food." Shoppers at Stop & Shop Supermarket on the King's Highway in Fairfield and at Kmart on Route 1 in Milford mostly agreed with the survey's findings. John Davis of Bridgeport came out of Kmart empty-handed Tuesday and said he understands the way his fellow Americans feel, especially after problems were discovered with toothpaste from China. But it's difficult to boycott the goods, he said. "Everything you see is made in China," Davis noted. He also said there's a human price on Chinese products that people should be thinking about, because many of those goods were once made here. "They're putting people out of work every day," he said. SHU International Business professor Balbir Bhasin said the real danger for companies is if people like Davis act on their feelings. Bhasin did not conduct the poll. The key question, Bhasin said, is "How much risk are they likely to see while lowering the cost to the consumer and raising profits?" At this point, according to Bhasin, companies need to take action. He said they should probably try to enforce quality control abroad, but if the problems continue, it might create enough momentum to make it worthwhile for companies to bring production back to this country. There are two basic assumptions in going offshore, he said. "It's cheaper" and "others can do it better." But the major recall of Chinese-made toys by Mattel shows foreign-made products might not be better after all. The poll also asked about food items and whether people were checking labels for the country of origin. The survey said a year ago only 52 percent of Americans checked the labels on food, but today more than 68 percent do. Most people coming out of the Stop & Shop in Fairfield agreed with Kristen Masterson, who said, "It's important to know what you're putting in your body." Masterson said her concern is nutrition, not country of origin. She isn't willing to abandon foreign-made goods just yet, noting it's the quality of the individual product that counts. Masterson said she drives a Japanese car because it is a quality vehicle. Todd Martin, an economic consultant to Bridgeport-based People's United Bank, said despite the high support in the poll for bans and buying American, it's unlikely to lead to real changes in where things are made. He said consumers just haven't shown a willingness to boycott those goods in the past. http://www.newstimeslive.com/news/st...&source=tabbox  Brits Mull Broadband Help The UK government is considering intervening in the way broadband is rolled out, in an effort to speed up the deployment of super-fast services. Stephen Timms, Minister for Competitiveness, ordered a summit to look at the role of government in providing next-generation broadband. While other countries are investing in new ways to deliver higher bandwidth, the UK is seen as lagging behind. Mr Timms said broadband infrastructure was one of his "personal priorities". "Today we face a new challenge. Other countries are starting to invest in new, fibre-based infrastructure, delivering considerably higher bandwidth than is available in the UK today," Mr Timms told the Broadband Stakeholder Group and others attending a meeting on Tuesday evening. "I have decided to chair a high level summit later this year to consider the circumstances that might trigger public sector intervention and the form that intervention might take," he said. Huge costs The event was organised by the Broadband Stakeholder Group to outline its own plans to improve the way next-generation broadband is rolled out in the UK. According to Richard Allan, a member of the Broadband Stakeholder Group and director of government affairs at Cisco, the UK needs to act now in order to keep its place in the top 25% of broadband nations. "That should be one of the targets that the government sets if it wants to stay economically competitive," he said. Mr Allan believes that the UK should have 40% of its citizens connected to fibre that can deliver broadband speeds of up to 100Mbps (megabits per second) by 2012. "The current copper-based system is limited by ADSL which means 24 megabits under very good conditions," he said. It is estimated that upgrading the whole of the UK to a fibre-based network could cost £10-15bn. While other countries, including France, Germany and Italy are already looking at ways of improving the so-called access or last-mile network which connects to people's homes, there is so far little investment in the UK. According to Mr Allan, the reasons for this are part-historical. "There is evidence that the cost of civil engineering work in the UK is particularly high," he said. He believes government intervention in lowering these costs as well as help with planning laws and providing the necessary ducting for fibre would be a step in the right direction. In some countries ducts for fibre have been made available via municipal sewers although Mr Allan is not sure this is the solution in the UK. "Traditionally UK sewers are deeper and they are not municipally owned but there are other ways to keep the disruption of digging up roads to a minimum, for example with micro ducts which sees fibre blown through long runs," he said. The BSG is also calling on Ofcom to provide a regulatory framework to support investment in next-generation networks. http://news.bbc.co.uk/go/pr/fr/-/2/h...gy/7001413.stm  Virgin Mobile Sued Over Ad Andrew D. Smith What would you do if a company grabbed a goofy picture of your kid off the Internet, slapped some snarky text on it and used it to sell mobile phone service half a world away? Susan Chang decided to sue. Attorneys for Ms. Chang, who lives in Bedford with her 16-year-old daughter Alison, have filed a state court case against Virgin Mobile USA, Virgin Mobile Australia and Creative Commons Corp., a nonprofit organization that licenses the sharing of photographs from the Web site Flickr.com. Alison was washing cars for a church fundraiser in April when a youth counselor snapped a picture of her flashing a "peace" sign. The counselor posted the picture on Flickr, where it came to the attention of ad execs working for Virgin Mobile Australia. According to Ms. Chang's attorneys, VMA's "Are You With Us or What?" campaign features edgy captions written over more than 100 public photos from Flickr. "The caption 'Monks are Boring' is superimposed over a group of monks," their filing reads. In another ad, " 'People who talk in lifts have bad breath' appears above an image of six adults in an elevator." The photo of Alison, which the counselor had posted on Flickr, appeared on at least one bus shelter in Adelaide, Australia, with the caption "Dump your pen friend." Her mom's attorneys suspect it was used in other places, including on one of VMA's Web sites. The team has asked courts here to let them examine VMA's books to determine that ad's distribution and its effectiveness. Such information, they say, will determine the size of the requested damages. "If a company uses your face in its ads without your consent, then you're entitled to whatever money those ads generate for the company," said Ryan Zehl, an attorney for Ms. Chang and a partner at the Houston firm Fitts Zehl LLC. "It's Texas law." However, the relevance of Texas law remains in question. Unless Virgin Mobile Australia posted the photo of Alison on its Web site, the picture may never have appeared commercially in the U.S. But Mr. Zehl insists both on the relevance of Texas law and the culpability of Virgin Mobile's American affiliate. Virgin Mobile Australia could not be reached for comment; their counterparts at Virgin Mobile USA insist the case has nothing to do with them. "We are an entirely separate company with no say whatsoever in any advertisement run in Australia," spokeswoman Jayne Wallace said. "Each company with the Virgin Mobile name is entirely autonomous." Whoever bears the blame, Mr. Zehl claims that Alison's age makes them particularly culpable. The complaint says the ad caused Alison "to experience and suffer humiliation, severe embarrassment, frustration, grief and general mental anguish damages, all of which, in reasonable probability, will subsist in the future. "Furthermore," it continues, "Alison has sustained damage and injury to her reputation and good name in the community, which exposes her to contempt and ridicule among her peers, neighbors, relatives and friends, and impairs, among other things, her ability to gain acceptance to the universities of her choice." Asked why he was taking such an embarrassing matter to Alison's hometown newspaper, a move that will only increase the ad's exposure, Mr. Zehl said that both news reports and the suit itself would dispel any notions that Alison had sold her dignity by consenting to appear in an insulting ad. "It's about clearing her name," Mr. Zehl said of the girl, who is currently running for student council at Trinity High School in Euless. Mr. Zehl did not make his clients available for comment, but Alison's feelings are on view at Flickr.com, where she kicked off a three-month discussion of privacy and copyright law with a post below a picture of the ad that reads, "Hey that's me! No joke. I think I'm being insulted." The Changs' suit demonstrates how privacy issues force companies to exercise caution about using images, said Paula Bruening of law firm Hunton & Williams. She also serves as the deputy director of the Center for Information Policy Leadership, which was started by the firm and studies privacy issues around the globe. "There's going to be a lot of sensitivity about any images of children," she said, though the suit seems to hinge on copyright law, which is very nuanced and difficult to speculate about. "As a company, I'd think it would be more important to be extra careful when the image is of a child." Photographers also must think carefully about sharing images online, she said. In this case, the counselor has joined the Changs' lawsuit against Virgin Mobile. The risk to companies extends beyond lawsuits, said Martin Abrams, executive director of the center. "Marketers need to be much more careful about how they acquire and what they do with images and digital data," he said. "There are risks today we didn't even imagine 10 years ago." Staff writer Eric Torbenson contributed to this report. http://www.dallasnews.com/sharedcont...1.35bdb09.html  Comcast Clarifies High Speed Extreme Use Policy Micheal Mullen A few downloads and a marathon WoW session won't end your high-speed days with Comcast. Earlier this week, we heard a radio report that talked about a few people who were losing their high-speed Internet access through Comcast. The company cited that these users went above and beyond the average use of most users and branded the former customers as "excessive users." In what appeared fishy, the report said that Comcast would not define how the company defined the term. Now that the three current next gen consoles offer online connectivity for downloads, competition and system updates, we were worried that our own personal "download every demo that will fit on the Xbox 360 hard drive" might get us banned too. Charlie Douglas, a spokesperson for Comcast Corporation, called back to clarify what "excessive usage" means and why the company's actions to end its relationship with these customers is good for gamers. First, Douglas defines Comcast's "excessive use" as any customer who downloads the equivalent of 30,000 songs, 250,000 pictures or 13 million emails in a month. In short, even if you played a marathon World of Warcraft session for weeks while downloading the massive amount of demos on Xbox 360 and sprinkled with the not so massive amount of demos on the PlayStation Network, you are still not close to getting banned. Douglas said that Comcast's actions to cut ties with excessive users is a "great benefit to games and helps protect gamers and their game experience" due to their overuse of the network and thus "degrading the experience." Comcast has been a big supporter of gaming for years with its Game Invasion news, information and game purchasing web site and its well-known G4 TV network, which televises some of gaming's biggest events. http://biz.gamedaily.com/industry/news/?id=17434  Web Users Could Slash Cost of Putting Video Online Tom Simonite Internet users may have to help distribute online video clips to combat the growing costs delivering such content. That’s the conclusion of researchers at Microsoft who have studied how peer-to-peer networks could reduce costs for sites like YouTube that spend millions every month to make videos available over the web. Cheng Huang and Jin Li from Microsoft Research in Redmond, Washington, US, worked with Keith Ross of Polytechnic University in New York, US. They used nine months' worth of records from the MSN video site servers to work out how to reduce the costs of meeting around 60 million requests for clips every month. "The current model is not really sustainable," Ross told New Scientist, "Microsoft is certainly interested in the possibility of using peer-to-peer technologies, where users distribute video amongst themselves." Video sharing sites currently pay for bandwidth on a "per bit" basis. So the more popular they are, they more they pay for bandwidth. Canadian researchers estimate that Google-owned YouTube pays out around 2 million US dollars a month distributing clips, in addition to other costs such as servers and staffing costs. Small sacrifice The MSN video data spanned a period from April to December 2006 when users made over 520 million requests for more 59,000 videos. The Microsoft team used it to simulate how web users could share the video they were watching with each other, perhaps using a plug-in for a conventional browser such as Internet Explorer. Instead of downloading the clip they wanted from an MSN server, they would receive it from other users who were already watching it. The data showed that each user would only need to donate a small part of their upload capacity for the network perform as well as the current setup. Switching to a peer-to-peer technology could cut the costs of distributing video by more than 95 per cent, say the researchers. MSN's servers would only need to provide new clips for the first time, or when making up any shortfalls. Costs halved The team also suggest a way to prevent Internet Service Providers' costs jumping when their users start uploading much more data. The trick is to allow sharing only between people with the same provider, when data transactions are free. That restriction would cut the pool of sharers into smaller groups, meaning MSN’s servers would have to do more to fill any gaps in the service. But costs could still fall by more than half, simulations showed. Comcast, one of the largest US ISPs, already limits users of peer-to-peer network BitTorrent in this way, says Cameron Dale, from Simon Fraser University, Canada. "It's an interesting idea and one that is not hard to implement," he says. The Microsoft research was presented at the SIGCOMM 2007 conference in Kyoto, Japan, in August. http://technology.newscientist.com/a...eo-online.html  Microsoft Suffers Decisive EU Antitrust Defeat David Lawsky and Michele Sinner Microsoft suffered a decisive antitrust defeat in Europe on Monday, sending its shares down 2 percent in pre-market trade. A European Union court backed a European Commission ruling that Microsoft, the world's largest software maker, illegally abused its market power to crush competitors. Europe's top competition regulator said the ruling could lead to a "significant drop" in Microsoft's 95 percent market share. Shares in the U.S. software giant fell before the opening bell in New York on the Luxembourg-based court's ruling. The stock was down 2.2 percent at $28.40 in pre-market trading. "Its clearly a major defeat for Microsoft. There is no doubt it will spur the Commission on to regulate Microsoft much more significantly," said Chris Bright, a British competition lawyer. They will find that future innovation by Microsoft will be hampered quite significantly." The second-highest EU court dismissed the company's appeal on all substantive points of the 2004 antitrust ruling and upheld a record 497 million euro ($689.9 million) fine. A jubilant Competition Commissioner Neelie Kroes said the EU executive now expected to see a "significant drop" in Microsoft's overwhelming market share. The court said Microsoft was unjustified in tying new applications to its Windows operating system in a way that squeezed out rivals and harmed consumer choice. The verdict may be appealed only on points of law and not of fact and may force Microsoft to change its business practices. The ruling also gives Kroes a green light to pursue other antitrust cases and complaints involving Intel, Qualcomm and Rambus, and to issue draft new antitrust guidelines that were put on ice pending the ruling. "Microsoft must now comply fully with its legal obligations to desist from engaging in anti-competitive conduct," Kroes said in a statement. Asked how the Commission would assess the result, she told a news conference: "A market level of much less than 95 percent would be a way of measuring success ... You can't draw a line and say exactly 50 (percent) is correct, but a significant drop in market share is what we would like to see." Her spokesman later clarified that a fall in market share would be a logical consequence of fairer competition. Downbeat The court endorsed Commission sanctions against Microsoft's tying together of software and refusal to give rival makers of office servers information to enable their products to work smoothly with Windows. It annulled only the EU regulator's imposition of a Microsoft-funded trustee to monitor compliance. "The Court of First Instance essentially upholds the Commission's decision finding that Microsoft abused its dominant position," a court statement said. Microsoft General Counsel Brad Smith was downbeat at the courtroom, promising the company would obey the ruling in full. He told reporters there was no decision yet on whether to appeal to the European Court of Justice. "It is clearly very important to us as a company that we comply with our obligations under European law," Smith said. "We will study this decision carefully and if there additional steps we need to take in order to comply with it, we will take them." Microsoft, which had argued that it was entitled to protect is intellectual property from rivals, has used every recourse in every case brought against it by governments and regulators. The company has weathered a series of defeats in antitrust cases in the last decade and sees legal setbacks as almost part of its business model and a price for its near-monopoly. Microsoft has already moved to new battlegrounds such as seeking to set technical standards across the industry, while bundling more new features into its new Vista desktop software. Kroes declined to discuss the implications of the ruling for a pending complaint against Vista but said the Commission would have something to say soon. Rivals welcomed the EU court decision as a signal that authorities do not intend to allow Microsoft to pursue anti-competitive practices with impunity. The Commission ordered the company to sell a version of Windows without the Windows Media Player application used for video and music, which few have bought, and to share information allowing rivals' office servers to work smoothly with Windows. A spokesman for Microsoft opponents, the European Committee for Interoperable Systems, said the ruling confirmed Microsoft had abused its near-monopoly in computer operating systems and set ground rules for the company's behavior. Another winner was the Free Software Foundation, which makes free, open software for work group servers. "Microsoft can consider itself above the law no longer," said Georg Greve, president of the FSF Europe. The judges ordered Microsoft to pay the lion's share of the costs of the Commission and of business rivals. Since the original decision, the Commission has fined Microsoft a further 280.5 million euros, saying it had failed to comply with the interoperability sanction. The EU regulator is considering a further fine for non-compliance. (additional reporting by Georgina Prodhan in Frankfurt, Jonathan Cable in London, Mark John in Luxembourg, Sabina Zawadzki and William Schomberg in Brussels) http://www.reuters.com/article/topNe...39839820070917  EU Official Lambasts U.S. Justice Dept on Microsoft David Lawsky European Union Competition Commissioner Neelie Kroes said on Wednesday that a top U.S. Justice Department official's criticism of an EU court decision against Microsoft was "totally unacceptable". Assistant Attorney General Thomas Barnett said after the Court of First Instance (CFI) ruled against the world's biggest software maker on Monday that its decision could chill innovation and discourage competition. "It is totally unacceptable that a representative of the U.S. administration criticized an independent court of law outside its jurisdiction," Kroes told reporters. "The European Commission does not pass judgment on rulings by U.S. courts, and we expect the same degree of respect." Kroes's statement raised the stakes in a split over the Microsoft case between the Bush administration and the European Commission. The Commission has a history of cooperation with the U.S. Federal Trade Commission and the Justice Department since patching up differences over an EU decision in 2001 to block General Electric's takeover of Honeywell. On Monday, the CFI in Luxembourg upheld a landmark 2004 Commission decision that the U.S. giant abused the near-monopoly power of its Windows operating system to damage competitors, along with a 497 million euro ($695 million) fine. Kroes has defended the order by her predecessor, Mario Monti, that Microsoft sell a version of Windows without its Media Player audiovisual software, and share information to enable rival makers of servers to operate smoothly with Windows. Barnett, the Justice Department's top antitrust official, disparaged the EU's policy. "We are ... concerned that the standard applied to unilateral conduct by the CFI, rather than helping consumers, may have the unfortunate consequence of harming consumers by chilling innovation and discouraging competition," he said in a written statement on Monday. Barnett said the United States protects competition, not competitors. Some of Microsoft's main U.S. competitors complained to the European Commission. Other U.S. rivals sparked a similar antitrust case against Microsoft in the United States by complaining to the Justice Department in the 1990s. A U.S. Court of Appeals found in 2001 that Microsoft violated the Sherman Act antitrust law. Since then, some states have criticized the Justice Department for backing off. Kroes said Microsoft may appeal against the EU decision. "If the parties to a case are unhappy with the Court of First Instance ruling, they can appeal to the Court of Justice, and that is well known by those parties," she said. Microsoft has not said if it will do so. http://www.reuters.com/article/compa...26927820070919  MediaDefender Phone Call and Gnutella Tracking Database Leaked Ernesto The leak of MediaDefender’s emails caused quite some controversy, Ironically, in a recently leaked phone call, a New York attorney and MediaDefender discuss the security of their email-server. Whilst there is some initial confusion as to where the leak may have originated, they eventually write it off as some technical problem. The leaked phone call shows that they are unsure about their network protection, their IDS etc. One of the parties is on a VOIP connection which may explain how the leak was obtained. Similar to the e-mail leak, a group called “MediaDefender-Defenders” released the file, and in the .nfo file we read: MediaDefender-Defenders proudly presents some more internal MediaDefender stuff… more will follow when time is ready. MediaDefender thinks they’ve shut out their internals from us. Thats what they think. The subject of the call is rather serious. MediaDefender is apparently involved in an ongoing Child Porn investigation. Their job is to identify child-porn images and report the IPs of the offending computers back to the government. A tricky project since it would mean that they actually have to download and rate the illegal content. This wont be the end of the leaks according to the “MediaDefender-Defenders”, they claim that more will follow when time is ready. In addition the the phone call, a huge MySQL database dump from a MediaDefender server was leaked on BitTorrent as well. The database shows tracking and decoy file information for the Gnutella network which is used by P2P clients such as LimeWire. All this leaked information is a huge blow for MediaDefender, and it will undoubtedly cost them a lot of time and money to clean this up. Interestingly, no evidence can be found that MediaDefender is actually involved in prosecuting or gathering evidence against filesharers (as we reported earlier). Their core business is releasing fake files and polluting the filesharing networks. http://torrentfreak.com/more-mediade...-leaks-070916/  Tiny Security Update, MediaDefender Blocked and Banned! Bogaa As most of you guys know, yesterday 6621 emails were leaked from MediaDefender. Although we haven't read all of those emails we did make a discovery, it seems that they were using auto-submit tools to upload fake torrents. From now on everybody has to type in a security text (captcha) before we accept any submission. We also came across a large list of ip's (box-banned) and fake trackers (will be removed soon as we need to create a script) (special thanks to Brokep from TPB for the other list). Stay tuned for updates Update: We managed to remove all fake trackers from our database, a total of 5000 torrents were removed, we will run the scripts on a hourly cronjob to make sure the database stays clean. For those of you interested in the fakes, we have a export file with all removed and reported torrents: http://www.meganova.org/fakefile.php Update: For those of you who dont know how to find real torrents, read our previous post with a few good tips on how to detect fakes: 10 Greatest tips for finding real torrents Greets, Bogaa http://www.meganova.org/sitenews/article/17.html  MiiVi Admit They Will Report Pirates to ‘Proper Authorities’ enigmax Buried away in the leaked MediaDefender emails is the End User License Agreement for MiiVi. Like most EULAs it’s long and boring but this one has a sting in its tail. If MediaDefender catch you engaging in copyright infringement with the MiiVi app, they state in black and white that they will report you to the relevant authorities. According to Wikipedia, a EULA or ‘End User License Agreement’ is a software license agreement which ‘indicates the terms under which an end-user may utilize the licensed software’. The EULA usually comes either in paper form (with some software, game etc )and can be recognized as a booklet with tiny dense type with mostly legal terms only lawyers understand, or the digital type that appears when you install some software. Most PC users will be familiar with the box where you have to select ‘Yes’ or ‘No’ to declare that you have read the mountains of legalese, understood it and are prepared to adhere to the rules. It can be presumed that most people who are presented with EULAs don’t read them and it’s a safe bet that the people who installed MiiVi didn’t read its EULA either. Some may have - but most eyes would’ve glazed over after the first paragraph: Miivi desktop application - License Agreement & Terms of Use THIS VERSION OF MIIVI SOFTWARE AND ANY OTHER RELATED SOFTWARE, UPGRADES OR UPDATES AND ALL RELATED SERVICES (THE “PRODUCT”), ARE LICENSED TO YOU BY MIIVI INC. (”MIIVI”) SUBJECT TO THE TERMS AND CONDITIONS OF THIS LICENSE AGREEMENT & TERMS OF USE (THE “AGREEMENT”). PLEASE READ THIS ENTIRE AGREEMENT CAREFULLY. BY CHECKING THE “I HAVE READ AND I ACCEPT THE MIIVI SOFTWARE LICENSE AGREEMENT & TERMS OF USE” CHECK BOX, OR BY INSTALLING OR USING THIS PRODUCT YOU AGREE TO BE BOUND BY THE TERMS OF THIS AGREEMENT. IF YOU DO NOT AGREE TO ALL OF THE TERMS OF THIS AGREEMENT, PLEASE DO NOT ACCESS/USE THE PRODUCT, DO NOT INSTALL OR USE THE PRODUCT AND IMMEDIATELY DELETE ANY COPY OF IT FROM ALL STORAGE MEDIA. Boring….but not if you skip through a little to a section in the ‘User Conduct’ section: User Conduct. You agree to abide by all applicable local, state, national and foreign laws, treaties and regulations in connection with the Product, and your use thereto. You agree not to use, endorse, or in any other way allow use of the Product to: [edited to remove non-relevant section] (d) copy, reproduce, store, transmit, post, submit, publicly display or manage any material that may infringe the intellectual property rights or other rights of third parties, including trademark, copyright, patent or right of publicity; In itself, this section is no big deal. After the ‘Grokster Decision‘, anyone getting involved with the marketing of media distribution software needs to be very careful that they are not seen to be encouraging piracy. However, it’s a part of the ‘Measures and Enforcement’ section (in conjunction with the above) which grabs the attention: Your failure to comply with any of the provisions mentioned under the User Conduct section or any other provision of this Agreement, automatically nullifies any obligation Miivi may have to contact you or provide you with any notice required by this Agreement or by law. You hereby agree, that if Miivi believes, in its own discretion, that you directly may be connected with such activities, Miivi may be required to disclose such a conduct and the suspected infringing user’s (i.e., your) Data or Information to the proper authorities. So in it’s own words, if MiiVi believes ‘in its own discretion’ that a MiiVi user infringed copyrights of a third party - a civil offense even in the copyright-tough United States - the company would take it upon themselves to seek out the copyright holder and provide them with the MiiVi user’s information, presumably so that action could be taken against them. The fact that MiiVi would’ve been able to monitor for copyright infringements at all would be quite a surprise to the majority of its users. The rest would understand it would be easy - if an anti-piracy company was running the project. Although there still appears to be no hard evidence that entrapping pirates was the sole purpose of the project, the fact that MiiVi is presenting itself as the copyright equivalent of judge-and-jury does not sit well. If the wording said that MiiVi would take action if required by law (such as with a DMCA take-down request) it would be an irritant, but would probably be accepted as a necessary evil. However, this pro-active stance where one is reported to ‘proper authorities’ at the discretion of an unconnected 3rd party (over a civil issue), is something else entirely. Holding private data is a very serious business, so much so that handing over such information to a 3rd party in the UK and EU would probably constitute a criminal breach of data protection laws. Finally, a statement in the EULA that is likely to raise a wry smile or two: …..You agree not to use, endorse, or in any other way allow use of the Product to: [edited to remove non-relevant section] (b) harvest, collect, gather or assemble information or data regarding other users, including e-mail addresses, without their consent; It seems that EULAs might be worth reading after all. http://torrentfreak.com/miivi-admit-...rities-070918/  Ahem MediaDefender Damage Control: Cease and Desist! Markus After the big leak of last week, today mediadefender is desperately trying to establish some level of damage control. This morning we received an email from their lawyers stating that the domain registrar should hand over our personal information. So here is an open letter to MediaDefender. Dearest little asstunnels, Let me start of by thanking you for your pitiful attempt to have your emails removed from the entire internet (the thing that says www.). In no way we feel obligated to fulfill your request, as a matter of fact any organization that tries to harm this site and the bittorrent user in general can expect nothing more from us but a big fuck you! In case you haven't noticed, this site is located in Europe (I hope you can point it out on a map) where your stupid copyright claims have no base. But fair is fair you guys did suffer over the past week so here's bit of advice to you guys: Fuck you! Fuck you again! Fuck you again and again and again! Fuck you again and again and again && again! There is no way you can stop this, your emails have been published on more then a centillion websites. And if there is anyone who is going to start a lawsuit it will be us suing you for attempts to sabotage the integrity of this site and many others. Update: We just launched MiiVi Have a very nice day, Markus http://www.meganova.org/sitenews/article/18.html  Lesson From Tor Hack: Anonymity and Privacy Aren't the Same Bruce Schneier As the name implies, Alcoholics Anonymous meetings are anonymous. You don't have to sign anything, show ID or even reveal your real name. But the meetings are not private. Anyone is free to attend. And anyone is free to recognize you: by your face, by your voice, by the stories you tell. Anonymity is not the same as privacy. That's obvious and uninteresting, but many of us seem to forget it when we're on a computer. We think "it's secure," and forget that secure can mean many different things. Tor is a free tool that allows people to use the internet anonymously. Basically, by joining Tor you join a network of computers around the world that pass internet traffic randomly amongst each other before sending it out to wherever it is going. Imagine a tight huddle of people passing letters around. Once in a while a letter leaves the huddle, sent off to some destination. If you can't see what's going on inside the huddle, you can't tell who sent what letter based on watching letters leave the huddle. I've left out a lot of details, but that's basically how Tor works. It's called "onion routing," and it was first developed at the Naval Research Laboratory. The communications between Tor nodes are encrypted in a layered protocol -- hence the onion analogy -- but the traffic that leaves the Tor network is in the clear. It has to be. If you want your Tor traffic to be private, you need to encrypt it. If you want it to be authenticated, you need to sign it as well. The Tor website even says: Yes, the guy running the exit node can read the bytes that come in and out there. Tor anonymizes the origin of your traffic, and it makes sure to encrypt everything inside the Tor network, but it does not magically encrypt all traffic throughout the internet. Tor anonymizes, nothing more. Dan Egerstad is a Swedish security researcher; he ran five Tor nodes. Last month, he posted a list of 100 e-mail credentials -- server IP addresses, e-mail accounts and the corresponding passwords -- for embassies and government ministries around the globe, all obtained by sniffing exit traffic for usernames and passwords of e-mail servers. The list contains mostly third-world embassies: Kazakhstan, Uzbekistan, Tajikistan, India, Iran, Mongolia -- but there's a Japanese embassy on the list, as well as the UK Visa Application Center in Nepal, the Russian Embassy in Sweden, the Office of the Dalai Lama and several Hong Kong Human Rights Groups. And this is just the tip of the iceberg; Egerstad sniffed more than 1,000 corporate accounts this way, too. Scary stuff, indeed. Presumably, most of these organizations are using Tor to hide their network traffic from their host countries' spies. But because anyone can join the Tor network, Tor users necessarily pass their traffic to organizations they might not trust: various intelligence agencies, hacker groups, criminal organizations and so on. It's simply inconceivable that Egerstad is the first person to do this sort of eavesdropping; Len Sassaman published a paper on this attack earlier this year. The price you pay for anonymity is exposing your traffic to shady people. We don't really know whether the Tor users were the accounts' legitimate owners, or if they were hackers who had broken into the accounts by other means and were now using Tor to avoid being caught. But certainly most of these users didn't realize that anonymity doesn't mean privacy. The fact that most of the accounts listed by Egerstad were from small nations is no surprise; that's where you'd expect weaker security practices. True anonymity is hard. Just as you could be recognized at an AA meeting, you can be recognized on the internet as well. There's a lot of research on breaking anonymity in general -- and Tor specifically -- but sometimes it doesn't even take much. Last year, AOL made 20,000 anonymous search queries public as a research tool. It wasn't very hard to identify people from the data. A research project called Dark Web, funded by the National Science Foundation, even tried to identify anonymous writers by their style: One of the tools developed by Dark Web is a technique called Writeprint, which automatically extracts thousands of multilingual, structural, and semantic features to determine who is creating "anonymous" content online. Writeprint can look at a posting on an online bulletin board, for example, and compare it with writings found elsewhere on the Internet. By analyzing these certain features, it can determine with more than 95 percent accuracy if the author has produced other content in the past. And if your name or other identifying information is in just one of those writings, you can be identified. Like all security tools, Tor is used by both good guys and bad guys. And perversely, the very fact that something is on the Tor network means that someone -- for some reason -- wants to hide the fact he's doing it. As long as Tor is a magnet for "interesting" traffic, Tor will also be a magnet for those who want to eavesdrop on that traffic -- especially because more than 90 percent of Tor users don't encrypt. http://www.wired.com/politics/securi...y_matters_0920  Kiss Your Privacy Goodbye Jack Kapica Do you use your computer to download music from Apple’s iTunes or Napster? Use Symantec’s Norton SystemWorks to protect your computer? Watch a film, say Disney’s Pirates of the Caribbean or Ray, the Ray Charles bio pic? If so, and if you live in Canada, your privacy might have been violated. Music download services, e-books and software, says the Canadian Internet Policy and Public Interest Clinic (CIPPIC) of the Faculty of Law at the University of Ottawa, use digital rights management technologies, or DRM, to protect their intellectual property. And some of them violate federal law, the Personal Information Protection and Electronic Documents Act (PIPEDA). The practice, CIPPIC says, is “widespread.” CIPPIC has just released a study called Digital Rights Management and Consumer Privacy: An Assessment of DRM Applications Under Canadian Privacy Law, which looked at the DRM technologies used in 16 digital products and services. CIPPIC found that that many mechanisms to protect intellectual property sold here actually pose threats to your privacy. CIPPIC stopped short of recommending that software and entertainment using these DRM technologies be banned from Canada. In carefully chosen words, CIPPIC staff counsel and chief investigator David Fewer said the organization “found non-compliance with even basic requirements of PIPEDA, Canada’s federal private sector privacy law.” CIPPIC’s study, financed by the Office of the Privacy Commissioner of Canada, observed DRM mechanisms tracking usage habits, surfing habits and technical data. Even e-book software was guilty of profiling individuals (one Ottawa library audio book included software from DoubleClick, an online marketing company). Apparently many software makers have decided that your IP address is public information, which it can collect, use and disclose to anyone they wish. Or to anyone willing to pay for it. And why are we not aware of this? Because companies using DRM to deliver content often don’t tell you what they are collecting and what they will do with the information once they get it. This is a violation of the basic requirements of PIPEDA. How can you tell if your private information is being harvested? It depends on whether you’re using “autonomous” or “Net-dependent” DRM. Autonomous protection is often in the form of inserting a CD key to unblock the program or content, and it doesn’t have to connect to any one outside the user’s location. Most autonomous protection doesn’t. But Net-dependent DRM is a growing practice involving Internet authentication — such as Microsoft’s Genuine Advantage system (though CIPPIC did not test Microsoft programs in its study). Not all the autonomous protection schemes communicate with external computers during the course of the operation of the DRM, but all of the Net-dependent ones do. Worse, many of the Net-dependent digital products CIPPIC looked at involved companies such as Akamai Technologies and DoubleClick, companies that process information, deliver content, offer Web analysis or deliver advertising. In one nasty discovery, Napster, the music-purchasing company, says it monitors its customers’ communications to “check for obscenity, defamation or other types of abusive language, as well as for content that may infringe our rights or the rights of others.” CIPPIC notes dryly that “is clearly not information that the individual provides to Napster.” In the case of Volume 2 of the Pirates of the Caribbean movie, CIPPIC found it had to install the Interactual Player, software that plays DVDs on computers, when it inserted the movie to play. The software’s configuration window offered a tab marked “Privacy.” CIPPIC cancelled all agreements to information transfers, but still found that communications had been set up with InterActual’s servers, the results of a cookie placed in the computer, and InterActual might have discovered the computer’s IP address, Web browser and operating system information. And you thought you were talking only to sweet Uncle Walt. Under PIPEDA, companies that demand personal information must tell the customer what personal information they collected, how they intend to use it and reveal who would see that information. Most organizations either ignore PIPEDA restrictions such as these, or phrase their small print in such a way as to be extremely vague. Or they use a sneaky method of dealing with the matter. If you install Symantec’s Norton SystemWorks, you are offered a look at Symantec’s privacy policy covering SystemWorks. But an important part of SystemWorks is another program called LiveUpdate, which updates the software and virus data files on a daily basis. LiveUpdate has a separate privacy policy, CIPPIC says, but it’s not visible to anyone who installs the program. I hope CIPPIC keeps up this monitoring of DRM systems. We need to ask such upstanding companies such as Symantec and Disney just what the heck they think they’re doing to Canadians. Perhaps the Privacy Commissioner, who financed the study, can put some pressure on these companies. After all, our privacy is as important to us as their intellectual property is to them. http://www.theglobeandmail.com/servl...tory/WBcyberia  Big Brother is Watching Us All Humphrey Hawksley The US and UK governments are developing increasingly sophisticated gadgets to keep individuals under their surveillance. When it comes to technology, the US is determined to stay ahead of the game. "Five nine, five ten," said the research student, pushing down a laptop button to seal the measurement. "That's your height." "Spot on," I said. "OK, we're freezing you now," interjected another student, studying his computer screen. "So we have height and tracking and your gait DNA". "Gait DNA?" I interrupted, raising my head, so inadvertently my full face was caught on a video camera. "Have we got that?" asked their teacher Professor Rama Challapa. "We rely on just 30 frames - about one second - to get a picture we can work with," he explained. Tracking individuals I was at Maryland University just outside Washington DC, where Professor Challapa and his team are inventing the next generation of citizen surveillance. They had pushed back furniture in the conference room for me to walk back and forth and set up cameras to feed my individual data back to their laptops. Gait DNA, for example, is creating an individual code for the way I walk. Their goal is to invent a system whereby a facial image can be matched to your gait, your height, your weight and other elements, so a computer will be able to identify instantly who you are. "As you walk through a crowd, we'll be able to track you," said Professor Challapa. "These are all things that don't need the cooperation of the individual." Since 9/11, some of the best scientific minds in the defence industry have switched their concentration from tracking nuclear missiles to tracking individuals such as suicide bombers. Surveillance society My next stop was a Pentagon agency whose headquarters is a drab suburban building in Virginia. The Defence Advanced Research Projects Agency (Darpa) had one specific mission - to ensure that when it comes to technology America is always ahead of the game. Its track record is impressive. Back in the 70s, while we were working with typewriters and carbon paper, Darpa was developing the internet. In the 90s, while we pored over maps, Darpa invented satellite navigation that many of us now have in our cars. "We ask the top people what keeps them awake at night," said its enthusiastic and forthright director Dr Tony Tether, "what problems they see long after they have left their posts." "And what are they?" I asked. He paused, hand on chin. "I'd prefer not to say. It's classified." "All right then, can you say what you're actually working on now." "Oh, language," he answered enthusiastically, clasping his fingers together. "Unless we're going to train every American citizen and soldier in 16 different languages we have to develop a technology that allows them to understand - whatever country they are in - what's going on around them. "I hope in the future we'll be able to have conversations, if say you're speaking in French and I'm speaking in English, and it will be natural." "And the computer will do the translation?" "Yep. All by computer," he said. "And this idea about a total surveillance society," I asked. "Is that science fiction?" "No, that's not science fiction. We're developing an unmanned airplane - a UAV - which may be able to stay up five years with cameras on it, constantly being cued to look here and there. This is done today to a limited amount in Baghdad. But it's the way to go." Smarter technology Interestingly, we, the public, don't seem to mind. Opinion polls, both in the US and Britain, say that about 75% of us want more, not less, surveillance. Some American cities like New York and Chicago are thinking of taking a lead from Britain where our movements are monitored round the clock by four million CCTV cameras. So far there is no gadget that can actually see inside our houses, but even that's about to change. Ian Kitajima flew to Washington from his laboratories in Hawaii to show me sense-through-the-wall technology. "Each individual has a characteristic profile," explained Ian, holding a green rectangular box that looked like a TV remote control. Using radio waves, you point it a wall and it tells you if anyone is on the other side. His company, Oceanit, is due to test it with the Hawaiian National Guard in Iraq next year, and it turns out that the human body gives off such sensitive radio signals, that it can even pick up breathing and heart rates. "First, you can tell whether someone is dead or alive on the battlefield," said Ian. "But it will also show whether someone inside a house is looking to harm you, because if they are, their heart rate will be raised. And 10 years from now, the technology will be much smarter. We'll scan a person with one of these things and tell what they're actually thinking." He glanced at me quizzically, noticing my apprehension. "Yeah, I know," he said. "It sounds very Star Trekkish, but that's what's ahead." http://news.bbc.co.uk/go/pr/fr/-/2/h...nt/6995061.stm  'Virtual Fence' in Arizona Remains Unworkable Because of Glitch AP Three months after its scheduled debut, the first high-tech virtual fence at the nation's borders remains unused because of a continuing software glitch. Homeland Security Secretary Michael Chertoff says more testing is expected in October. Nine 98-foot towers with radar, sensors and sophisticated cameras have been built across 28 miles close to the Mexican border near Sasabe, southwest of Tucson. It's an area heavily used by illegal immigrant and drug smugglers. Arizona remains the busiest border point for illegal crossings from Mexico. The towers, each a few miles apart, are intended to deter or detect border-crossers and potential terrorists and help Border Patrol agents catch them. Chertoff says he's withholding a remaining payment to the contractor, Boeing Company, until the pilot project works. A company spokeswoman says Boeing is working to solve some remaining technical issues. http://kvoa.com/Global/story.asp?S=7100636&nav=HMO6  Tens of Thousands of CCTV Cameras, Yet 80% of Crime Unsolved Justin Davenport London has 10,000 crime-fighting CCTV cameras which cost £200 million, figures show today. But an analysis of the publicly funded spy network, which is owned and controlled by local authorities and Transport for London, has cast doubt on its ability to help solve crime. A comparison of the number of cameras in each London borough with the proportion of crimes solved there found that police are no more likely to catch offenders in areas with hundreds of cameras than in those with hardly any. In fact, four out of five of the boroughs with the most cameras have a record of solving crime that is below average. The figures were obtained by the Liberal Democrats on the London Assembly using the Freedom of Information Act. Dee Doocey, the Lib-Dems' policing spokeswoman, said: "These figures suggest there is no link between a high number of CCTV cameras and a better crime clear-up rate. "We have estimated that CCTV cameras have cost the taxpayer in the region of £200million in the last 10 years but it's not entirely clear if some of that money would not have been better spent on police officers. "Although CCTV has its place, it is not the only solution in preventing or detecting crime. "Too often calls for CCTV cameras come as a knee-jerk reaction. It is time we engaged in an open debate about the role of cameras in London today." The figures show: • There are now 10,524 CCTV cameras in 32 London boroughs funded with Home Office grants totalling about £200million. • Hackney has the most cameras - 1,484 - and has a better-than-average clearup rate of 22.2 per cent. • Wandsworth has 993 cameras, Tower Hamlets, 824, Greenwich, 747 and Lewisham 730, but police in all four boroughs fail to reach the average 21 per cent crime clear-up rate for London. • By contrast, boroughs such as Kensington and Chelsea, Sutton and Waltham Forest have fewer than 100 cameras each yet they still have clear-up rates of around 20 per cent. • Police in Sutton have one of the highest clear-ups with 25 per cent. • Brent police have the highest clear-up rate, with 25.9 per cent of crimes solved in 2006-07, even though the borough has only 164 cameras. The figures appear to confirm earlier studies which have thrown doubt on the effectiveness of CCTV cameras. A report by the criminal justice charity Nacro in 2002 concluded that the money spent on cameras would be better used on street lighting, which has been shown to cut crime by up to 20 per cent. Scotland Yard is trying to improve its track record on the use of CCTV and has set up a special unit which collects and circulates CCTV images of criminals. A pilot project is running in Southwark and Lambeth and is expected to be rolled out across the capital. The figures only include state-funded cameras. The true number, once privately run units and CCTV at rail and London Underground stations are taken into account, will be significantly higher. http://www.thisislondon.co.uk/news/a...ved/article.do  Video Leads to Firing of Mo. Officer AP A police sergeant whose berating of a driver was captured on videotape has been fired. Aldermen in the town of St. George, a St. Louis suburb, voted 5-0 in a closed meeting Monday to fire Sgt. James Kuehnlein. Notice of the firing was posted Wednesday at City Hall. Kuehnlein's attorney, Travis L. Noble, said the officer received a letter Thursday detailing the reasons for his firing. Noble said he would review the letter with Kuehnlein before deciding on a course of action. Brett Darrow, 20, had a video recorder inside his car when Kuehnlein approached him in a commuter lot in the early hours of Sept. 7. In a video that was widely viewed on the Internet, Kuehnlein is heard taunting and threatening Darrow, sometimes shouting and using profanity. "It's what I wanted the whole time," Darrow told the St. Louis Post-Dispatch. "The conduct was not forgivable." Police Chief Scott Uhrig said he recommended that Kuehnlein be fired based both on his language in the tape and because he violated department policy when he failed to tape the encounter himself with his police car's camera. http://www.charlotte.com/nation/story/287167.html  Report: Insiders Cause More Computer Security Problems Than Viruses Nate Anderson The Computer Security Institute has just released the 2007 edition of its long-running "Computer Crime and Security Survey," and it offers some dreary news for overworked computer security admins: average losses from attacks have surged this year. More surprising is the finding that the single biggest security threat faced by corporate networks doesn't come from virus writers any more; instead, it comes from company insiders. CSI has been running this survey for over a decade and has seen average losses from security breaches drop every year from 2002 to 2006. Investments in security seemed to be paying off; in 2006, the average breach cost companies an estimated $168,000, way down from five years earlier. But in 2007, the numbers skyrocketed. Each breach this year costs an estimated $350,454 to repair. Financial fraud and viruses caused most of the monetary losses, but both have fallen in frequency over the last few years. Only 12 percent of all respondents reported financial fraud at their institutions. Viruses, which used to plague 90 percent of all companies in 2001, now affect only 52 percent. It's internal users who are now causing the greatest number of problems, though they may also cause minimal damage. Hiding porn on an office PC, using unlicensed software, and abusing e-mail all count as security incidents, though all pale in comparison to one successful phishing trip. These sorts of internal incidents can be pesky, though, and 59 percent of all respondents had to deal with them in the last year. The CSI study has a major weakness: it's an "informal" study distributed to CSI members and conference-goers. The estimates of money lost to damages are, in one author's own words, "estimates." "Some of them," in fact, "are probably altogether approximate guesses." Still, the study has been sampling this group of computer security people for a decade, so the report's conclusions seem to accurately track their perceptions of security; whether they represent reality is another question. But as the report notes correctly that "when a group of professionals reports a significant reversal in a five-year trend of diminishing losses, we should be inclined to perk up our ears." http://arstechnica.com/news.ars/post...n-viruses.html  Theft of Information… and Why KRIPOS Fucks it Up. Kate Goriar Recently, quite a lot of information about individuals have been aloft in Norway. The government seems to ignore the problem, and just silence the people complaining and uncovering the problem. Traditionally, identity theft has not been much of a problem in Norway, but this has changed the last few years, and this incident could pave the road for really large scale identity theft. A short time-line of the events so far Here’s a short time-line, since most foreigners probably ain’t familiar the background of the case. It is accurate as far as I know. November 2006 Norwegian government agency Datatilsynet informs several Norwegian telephone operators of security holes in the operators websites. Middle of June, 2007 Holes still unpatched. First attack against Talkmore takes place. Roughly 20000 names and birth numbers is leaked. July 28., 2007 A proof-of-concept (PoC) code snippet is released to the public. This PoC-code utilises a security hole in Tele2’s web pages. The PoC was written by a 16 year old Norwegian. July, 29. Major Norwegian newspaper, dagbladet, covers it July, 30. Tele2 patches hole. Still not patched by at least two other phone operators. July, 30-31. 4500 names are fetched from other operators in Norway. August, 3-4. 63000 names are leaked from GoBergen, a subsidiary of Combitel August, 8. Tele2 Norway sends letters to 60000 Norwegians, informing about the leak. In this letter, Tele2 claims they were cracked. Tele2 reports the incident to KRIPOS, Norwegian criminal police. September, 13. KRIPOS, Norwegian criminal police branch, raids 52 persons across Norway. Common denominator for these 52 cases is that they have tried the PoC code, or in some other way fetched data from phone operators The last incident is quite interesting. Notable persons, like Gisle Hannemyr maintains that nothing illegal is being done. What birth numbers means in Norway In Norway, each individual is identified by his birth-date, noted in the form ddmmyy. In addition, 5 digit personnummer is tacked on at the end, to uniquely identify persons. This is not quite the Norwegian version of the American Social Security Numbers, but it’s the best analogy I can think of. The purpose of the birth number is to identify a individual. It has historically been treated as a secret, although the laws clearly says it is not sensitive or secret information. For example, one can: • Order mail readdressing from Norwegian postal service. • Order mobile phone service from operators. • Start bank accounts in f.ex. SkandiaBanken. The security hole The algorithm for generating/checking birth numbers is public. There’s no reason for why not, since it would be trivial to reverse engineer, and a quite useful tool to (legitimately) check if a birth number is entered correctly. By starting off with a date of birth you’re interested in, you can quickly generate all valid birth numbers for that date, using the algorithm. Then, you feed the generated numbers into altinn.no, the website for reporting income and alike to the Norwegian government. Altinn has security hole #1: they confirm whatever you have a real number, assigned to a living person, or simply a number not in use. Security 101 says that a system should respond in exactly the same way whatever the user-name/credentials is incorrect or not. Then, you take the validated numbers over to a website like Tele2’s, and feed them into the order form there. To make it easy, it was enough to enter ones birth number, and the system fetched your name and address from the central Norwegian Registry Office, maintaining records of all living and dead people. This is security hole #2, and by far the biggest: by assuming that a birth number is enough to authenticate a person, you let everyone with access to other peoples birth numbers authenticate as that person. The core problem is indeed that a birth number is a identificator, not a authenticator. In short: no cracking was done. In reality, the PoC-code only automated what you could have done with a normal calculator and a web browser! The core problem The really sad part about this story is that the core of the problem gets no attention. You can still steal one persons identity with just the social security number. Tele2 and the other companies has clearly broken Norwegian law (paragraph §13, part 1 of Personopplysningsloven, law about handling of information on individuals, for those interested), they have been reported to the police but the case got rejected. In Norway, you need a permit from Datatilsynet to store sensitive information about individuals and plan to use them in a business/organisation-related setting. You don’t need any kind of permit to compose a database over individuals for your own, private use. However, Kripos don’t buy that. Any serious hacker cracking a site(!) must be harmful, and must be raided, even if he only got away with maybe a few hundred of the total hundred thousands. Another scary part is that some bloggers that have have covered the case, and spoken in favor of the people that have used the program has been brought in for questioning by the police. They probably want to know their sources and to harass them. And again: The funny thing is that the program just automated something you could do with your web browser and a bit of patience… So KRIPOS decides to go after those who have used it, and probably (according to several people) not broken a single law. However, Tele2 and other operators, which have clearly broken Personopplysningslove, §13, part 1, has got no reaction so far. POL §13.1 places the burden of protection on the owner of the database in question. (Lars, 16, the author of the program has not yet been caught.) http://bitsex.net/2007/09/norwegian-police-fucks-up/  ChiliRec - Cool New Swedish Netradio Aggregator Service TankGirl Do you like to listen to netradio channels and sometimes streamrip tracks from them? If so, do not miss this cool new Swedish site ChiliRec. It's like 80 streamrippers working on parallel and collecting all the stuff for you to pick from. It keeps recording even when you close your browser and remembers you with just a cookie, no registration needed. And you don't have to waste any HD space for all that ripping, they save all the tracks (after a few hours there are already thousands of them!) and your playlists for you. If you want to download any single tracks to your own HD, it takes just a click. This is probably way too good to be legal, but on the other hand it hasn't been declared illegal yet...   http://www.p2p-zone.com/underground/...072#post258072  Get Paid to Stick it to the Man EFF Seeks Staff Intellectual Property Attorney Cindy Cohn We're hiring! EFF is seeking an intellectual property staff attorney for its legal team. Responsibilities will include litigation, public speaking, media outreach, plus legislative and regulatory advocacy, all in connection with a variety of intellectual property and high technology matters. Qualified candidates should have at least four years of legal experience, with knowledge in patent law and at least one other IP specialty (copyright, trademark, trade secret). Litigation experience is preferred, including significant experience managing cases, both overall case strategy and day-to-day projects and deadlines. Candidates should have good communication skills and interest in working with a team of highly motivated lawyers and activists in a hard-working nonprofit environment. Strong writing and analytical skills as well as the ability to be self-motivated and focused are essential. Tech savviness and familiarity with Internet civil liberties and high tech public interest issues preferred. This position is based in San Francisco. Interested applicants should submit a resume, writing sample, and references to ipjob@eff.org. http://www.eff.org/deeplinks/archives/005441.php#005441  RIAA Sends Another Wave Of Settlement Letters Susan Butler The RIAA sent a new wave of 403 pre-litigation settlement letters on behalf of the major record companies to 22 universities today. The labels also filed 24 copyright infringement lawsuits against individuals who previously received letters but did not settle the claims. The letters are part of the education and deterrence campaign the RIAA launched earlier this year, which focuses on illegal file sharing on college campuses. The program gives students the opportunity to resolve infringement claims against them at a discounted rate before a formal lawsuit is filed. Each letter informs the school of the forthcoming infringement suit against one of its students or personnel who used the school's computer network, and then requests the university administrators to forward the letter to the appropriate user. Today's lawsuits were filed in federal courts against individuals who allegedly shared unauthorized music files on the computer networks of the University of California Santa Cruz; Florida International University; University of South Florida; Cornell University; Morehead State University; University of Maryland College Park; North Carolina State University; North Dakota State University; Syracuse University; Ithaca College; University of Massachusetts Amherst; Columbia University; Ohio University; Kent State University; and Marshall University. The RIAA is also resuming its university advertising campaign, placing full-page ads that were created by college students in college newspapers across the country. With the ads, the trade group hopes to encourage fans to enjoy online music legally while reminding students of the legal, privacy and security risks associated with illegal downloading. The eighth wave of letters were sent in the following quantities to 22 schools including: Arizona State University (35 pre-litigation settlement letters), Carnegie Mellon University (13), Cornell University (19), Massachusetts Institute of Technology (30), Michigan State University (16), North Dakota State University (17), Purdue University - West Lafayette and Calumet campuses (49), University of California - Santa Barbara (13), University of Connecticut (17), University of Maryland - College Park (23), University of Massachusetts - Amherst and Boston campuses (52), University of Nebraska - Lincoln (13), University of Pennsylvania (31), University of Pittsburgh (14), University of Wisconsin - Eau Claire, Madison, Milwaukee, Stevens Point, Stout and Whitewater campuses (62). http://www.billboard.biz/bbbiz/conte...aafd53d458f14b  Rae J Schwartz Moves to Dismiss Complaint in Elektra v. Schwartz Ray Beckerman In Elektra v. Schwartz, the Brooklyn case against a Queens woman with Multiple Sclerosis, the defendant is making a motion to dismiss the complaint for failure to state a claim for relief (technically a motion for judgment on the pleadings pursuant to Fed. R. Civ. P. 12(c)), based upon the recent decision in Interscope v. Rodriguez. http://recordingindustryvspeople.blo...o-dismiss.html  Coop Discourages Notetaking in Bookstore Gabriel J. Daly Taking notes in class may be encouraged, but apparently it can get you kicked out of the Coop. Jarret A. Zafran ’09 said he was asked to leave the Coop after writing down the prices of six books required for a junior Social Studies tutorial he hopes to take. “I’m a junior and every semester I do the same thing. I go and look up the author and the cost and order the ones that are cheaper online and then go back to the Coop to get the rest,” Zafran said. “I’m not a rival bookstore, I’m a student with an I.D.,” he added. Coop President Jerry P. Murphy ’73 said that while there is no Coop policy against individual students copying down book information, “we discourage people who are taking down a lot of notes.” The apparent new policy could be a response to efforts by Crimsonreading.org—an online database that allows students to find the books they need for each course at discounted prices from several online booksellers—from writing down the ISBN identification numbers for books at the Coop and then using that information for their Web site. Murphy said the Coop considers that information the Coop’s intellectual property. Crimson Reading disagrees. “We don’t think the Coop owns copyright on this information that should be available to students,” said Tom D. Hadfield ’08, a co-creator of the site. According to UC President Ryan A. Petersen ’08, discussions with an intellectual property lawyer have confirmed Crimson Reading’s position. ISBN data is similar to phone book listings, which are not protected by intellectual property law, Petersen added. Every book title has a unique ISBN number, short for “international standard book number.” The alleged new rule is just the latest hurdle for Crimsonreading.org. During a meeting of the Committee on Undergraduate Education last March, Petersen proposed creating a centralized database of ISBN numbers for all courses, streamlining the process for professors and cutting the costs for the Coop. The proposal, which could have also made it easier for Crimson Reading to collect information, was nixed. “There’s a very lucrative and sensitive relationship between the Coop and University Hall that is stopping students from saving money on textbooks,” Hadfield said. Zafran, after his altercation with the Coop, does not feel much sympathy for the store. “If they want to get their revenue up they should slash their prices,” Zafran said. “I think if anything, this policy will have the reverse effect because if students aren’t allowed to comparison-shop, students will just get all their books online,” he said. http://www.thecrimson.com/article.aspx?ref=519564  MPAA Head Wants Deeper Relationship (Read: Content Filtering) with ISPs Nate Anderson It's no secret that US content owners want the "middlemen" of the Internet economy to better police their networks and services for material that infringes copyright. The problem, from a legal perspective, is that ISPs like AT&T and Comcast and content hosts like YouTube have the explicit legal go-ahead not to do this; they operate in a tranquil Caribbean "safe harbor" that exempts them from the crushing responsibility to filter and analyze every bit of content passing through their control. But some companies have expressed interest in doing such filtering voluntarily, and MPAA boss Dan Glickman praised them for it at a conference in Washington yesterday. "Their revenue bases depend on legitimate operations of their networks and more and more they're finding their networks crowded with infringed material, bandwidth space being crowded out," Glickman said."Many of them are actually getting into the content business directly or indirectly. This is not an us-versus-them issue." He went on to say that the movie business wants to "deepen our relationship" with ISPs. NBC Universal has been one of the big drivers behind this push to outsource the work of filtering to the ISPs. NBC's general counsel Rick Cotton recently told the FCC that ISPs should be forced to "use readily available means to prevent the use of their broadband capacity to transfer pirated content." Otherwise, corn farmers could be harmed. An exec at GE, which owns NBC Universal, later praised the idea in a keynote speech to the telecommunications industry and indicated that his company was quite serious about it. Rather amazingly, given the money and time that will be required to implement such a system, AT&T has agreed to start filtering content at some mysterious point in the future. Other ISPs could well follow suit, as most of the major networks are owned by or affiliated with companies that also have a voracious need for content (just think of how both cable companies and telcos like AT&T and Verizon need access to channels for their various TV offerings, if you need an example). The companies want to keep on good terms with content owners, but there may also be some legitimate concern about the impact illicit traffic has on their networks. Cracking down on illegal file-sharing—should that prove to be technically possible—could help with both of these issues. Net neutrality rules, if passed, might throw up some roadblocks. It's no wonder, then, that NBC and the MPAA as a whole are opposed to such rules. http://arstechnica.com/news.ars/post...with-isps.html  One Anti-Piracy System to Rule Them All Brad Stone Hollywood appears to have a preliminary winner in its bake-off of anti-piracy technologies. For the last year, the film industry, through its Palo Alto-based R&D joint venture MovieLabs, has been testing a dozen so-called “digital fingerprinting” technologies. The technology purports to scan file sharing sites, Internet providers and peer-to-peer networks to identify copyrighted material. “Fingerprinting Performance” (Leonard Kleinrock, 2007) Yesterday in Los Angeles, people affiliated with the Motion Picture Association of America talked about the ongoing tests at a day-long anti-piracy workshop that the MPAA co-hosted with the University of California. In his introductory keynote at the event, UCLA professor and Internet pioneer Leonard Kleinrock showed a single slide that suggested that one of the anti-piracy filtering companies had outperformed the other 11, with the highest number of matches of infringing content and lowest number of false-positives. But professor Kleinrock and MPAA execs declined to name the participating companies or who had scored best on the test, saying that secrecy was a precondition for their participation in the tests. Nevertheless, afterwards, executives from Santa Clara, Calif-based Vobile were crowing in the hallways of the Universal Hilton Hotel. The two-year old company’s technology, called Video DNA, has apparently bested others from the Royal Philips Electronics, Thomson Software & Technology, and the highest profile digital fingerprinting company, the Los Gatos, Calif.-based Audible Magic, which has deals to filter video sharing sites like YouTube and Microsoft’s Soapbox. The MPAA told Business Week in the spring that Vobile was doing “very well” on the tests. Movie Labs stress-tested the anti-piracy systems by loading hundreds of hours of copyrighted video content into the databases of the various filters, and then by flooding them with thousands of video files, some distorted, darkened and cropped, to try to scuttle their ability to find matches. In the next phase of the ongoing tests, MovieLabs will see if the systems can handle ever larger quantities of copyrighted works. Theoretically, adding more songs, TV shows and movies in their databases could slow down these systems—and the Internet video sites that use them— since it could take longer to find possible matches. MovieLabs has been sharing tests results with its member movie studios since the summer. MovieLabs chief executive Steve Weinstein says the technology is ready for prime time. “In a year you’re going to see many Internet companies using it. This technology has shown its viability.” http://bits.blogs.nytimes.com/2007/0.../index.html?hp  Foster, Thornton Stumble at Box Office Dean Goodman Jodie Foster blew away the box office competition with her vigilante thriller "The Brave One," but the poorly reviewed film's performance paled against her recent efforts. According to studio estimates issued on Sunday, the "Death Wish"-style movie sold about $14 million worth of tickets across the United States and Canada during its first three days of release. Among her recent headlining releases, "Flightplan" opened to $25 million in 2005, while "The Panic Room" debuted with a career-best $30 million in 2002. Foster was not the only Oscar laureate to underwhelm moviegoers. Billy Bob Thornton opened at No. 3 with the comedy "Mr. Woodcock," another film rooted in revenge. Garnering even worse reviews than "The Brave One," it earned $9.1 million. "The Brave One" was released by Warner Bros. Pictures, and "Mr. Woodcock" by New Line Cinema. In a climate of diminished expectations, the Time Warner Inc.-owned studios said they were satisfied with their respective films. Hollywood studios take advantage of the traditional post-summer lull in September to dump unheralded product on the market so that they can then focus on their year-end Oscar hopefuls. Last weekend's champion, the Western remake "3:10 to Yuma," slipped to No. 2 with $9.2 million. After 10 days, the Russell Crowe-Christian Bale vehicle has earned a modest $28.6 million, having cost about $55 million to make. It was distributed by Lionsgate, a unit of Lions Gate Entertainment Corp. Rankings could change when final data are issued on Monday. The top 10 contained one other new release, the South Korean monster movie "Dragon Wars," which failed to scare up business with a $5.4 million opening at No. 4. "Pretentious Fantasy" "The Brave One" stars Foster as a New York radio journalist who is seriously beaten in Central Park, and decides to clean up the city one thug at a time. Irish filmmaker Neil Jordan directed, and Terrence Howard plays a cop on her trail. The Baltimore Sun described it as a "pretentious payback fantasy." As is usually the case with Foster movies, women made up the majority of the audience (55 percent). Almost three-quarters were aged over 30, and 80 percent of viewers termed the film "excellent" or "very good," the studio said. Foster, 44, who averages a headlining role in a major studio release about once every two years, won Oscars for "The Accused" and "The Silence of the Lambs." "Mr. Woodcock," in which Thornton plays a sadistic gym coach engaged to marry the mother (Susan Sarandon) of one of his former victims (Seann William Scott), was originally shot by Australian filmmaker Craig Gillespie more than two years ago. The release was delayed by reshoots, and then a decision to hold it back for Thornton's New Line film "The Astronaut Farmer," which opened to $4.5 million in February. Critics almost unanimously ripped "Woodcock," with the nation's best-known reviewer, Roger Ebert of the Chicago Sun-Times, one of the rare exceptions, according to the Rotten Tomatoes movie site (http://www.rottentomatoes.com) It becomes the third consecutive box office disappointment for New Line, following "Rush Hour 3" and "Shoot 'Em Up." Among other recent Thornton releases, "School for Scoundrels" opened to $8.6 million last year, "The Bad News Bears" $11.5 million in 2005, and "Friday Night Lights" $20 million in 2004. Thornton won an Oscar for writing "Sling Blade," while Sarandon was honored for "Dead Man Walking." http://www.reuters.com/article/enter...39825420070916  Red Carpet Meets Harsh War David Carr At the beginning of the month, an eager crowd gathered in Midtown Manhattan at the Morgan Library to see “Alive Day Memories,” an HBO documentary that featured interviews of grievously wounded veterans conducted by James Gandolfini, the star of “The Sopranos.” People were sipping cocktails in the sumptuous surroundings when suddenly one of the guests — a veteran with brain injuries in a wheelchair who was in the documentary — began screaming profanely. Guests looked at one another nervously, frozen with hors d’oeuvres in hands, as they waited for the shouting to subside. (The veteran was quickly comforted by his friends.) But that shocking bit of human theater does raise a question: Are audiences ready for the steady stream of movies and documentaries that bring a faraway war very close? “In the Valley of Elah,” a mystery about a returning veteran who disappears, starring Tommy Lee Jones and directed by Paul Haggis, opened last Friday. It will be followed into theaters over the course of the fall and winter by “Grace Is Gone,” “Stop Loss,” “Nothing Is Private,” “Lions for Lambs,” “Charlie Wilson’s War,” and “Redacted.” They all take as their central concern the price of America’s military and security activities since the attacks of Sept. 11. HBO, which has already waded into bloody waters with “Baghdad ER” and “Alive Day,” has commissioned “Generation Kill,” written by David Simon, creator of “The Wire.” All of this is undoubtedly well intended, but will it be well attended? “I have no idea,” Mr. Haggis said last week after a screening of “In the Valley of Elah.” “We all certainly hope so. When I first started working on this in 2003, I thought I would be in for the fight of my life.” He added that he went through more than a dozen “War Is Not the Answer” signs on his lawn in the liberal enclave of Santa Monica, Calif., because they were stolen or defaced. “But the tide seems to be turning.” That tide is bringing a wave of films about a war that most Americans wish would go away. In a New York Times/CBS News Poll this month, 62 percent of the respondents said the war was a mistake. When the CBS News anchor Katie Couric recently went to Iraq, even landing an interview with President Bush, the evening broadcast clocked record low ratings for the week. A study released last week by the Project for Excellence in Journalism comparing the mainstream news agenda with user-news sites like Reddit, Digg, and Del.icio.us found that when citizens did the editing, war news made up just 1 percent of the content. Hollywood, which is bringing a reflexively liberal, antiwar agenda to most of these projects, has some assets, most notably stars like Mr. Jones for “In the Valley of Elah,” Tom Cruise in “Lions for Lambs” and Tom Hanks in “Charlie Wilson’s War.” These are not small bets from tiny indie companies. Many of the war-themed works include A-list actors and directors, budgets in the $25 million range, and major studios including Universal, Paramount and Warner Brothers. Clearly, media companies are hoping that asking questions about the war is good for business, in addition to being good for the republic. These movies may land with some impact during the Oscar season as the academy loves citing important films. But historically, audiences enter the theater in pursuit of counter-programming as an antidote to reality. They’d generally prefer to see Meryl Streep inhabiting Anna Wintour in “The Devil Wears Prada” rather than playing a seasoned reporter who covers a country that seems to be in the midst of melting down, as she does in “Lions for Lambs.” And these films have to compete not only with one another, but also with the drumbeat of the news media’s daily coverage of the Iraq war. Another I.E.D., another four Americans dead. Now, who wants popcorn with that? “These movies have a chance to work because the American public hasn’t been able to see anything from this war like they did during Vietnam,” said Tom Bernard, co-president of Sony Pictures Classics, which is behind “Standard Operating Procedure,” a documentary being made by Errol Morris. “People have no idea what the texture of life is like over there, and these films can give them that look.” Mr. Bernard argues that because of embedding rules for journalists and the dangers of covering the conflict, the visual context of the war has been lost, although citizens who have seen the photographs from Abu Ghraib or the checkpoint stops that have gone terribly awry would say they have seen plenty. The first numbers are in for “Alive Day,” and Sheila Nevins of HBO said the audience of a bit more than a million was a robust one for a documentary. But she said a documentary brought with it an expectation that reality would not only intrude, but also serve as a focal point. “They are extensions of news reports, really,” she said. “Paying money at the door of a movie theater to see the suffering of others is different than watching it on television. It is a much tougher sell in a theater.” The Vietnam War, another American conflict that divided the country and shattered many young lives, produced some important films that people saw in droves. But “Coming Home,” “Platoon,” “Apocalypse Now” and “The Deer Hunter” came years after the fact. Moviegoers will pay money to stare at the raw externalities of war, but they seem less willing to look if the wounds are too fresh. At the HBO event, people lined up to get a word with the injured vets, thanking them for their service and willingness to share their stories. But as those stories become alarmingly commonplace, the line at the theater may not be so robust. http://www.nytimes.com/2007/09/17/bu...ia/17carr.html  Kid Nation Debuts with Tough Choice for its Stars: a TV or Toilet After howls of protest by parental psychologists and allegations that it was prime-time child abuse, Kid Nation premiered in the US last night, the new reality show in which 40 children are abandoned in a ghost town for 40 days without parental supervision. The show had drawn heavy criticism for using child performers – some even accused the series of breaching child labour laws – with one mother claiming that her daughter suffered burns to her face and four other children treated for accidentally drinking bleach. That was until last night, when television critics and Americans watched episode one for the first time. If you discount the camera crews, producers, doctors, psychologists (all off camera) in this mocked-up pioneer ghost town in the New Mexico desert, there was hardly an adult in sight. The programme’s creator, Tom Foreman, acknowledged last month that William Golding's Lord of the Flies was part of its creative inspiration. But on last night's evidence, Piggy would have had a ball in "Bonanza City". It was deeply controlled and sanitised. The children, aged 8 to 15, are dropped in the desert and told to drag wagons filled with provisions to Bonanza City. It had one latrine. After a competition to pump water (this is on day three, when the man in charge returns and suggests they divide into colour-coded teams, red, blue and green, bandannas provided), they are rewarded with a choice: seven more outhouses or a television. They choose the toilets. Cheers all round. The community has been assigned four team leaders – the "town council" – who were told in secret that after the first week they must decide who should be awarded a $20,000 solid-gold star. The winner at a communal meeting is Sophie, 14, who has single-handedly shown everyone else how to cook pasta and stop grumbling. She is given a special key to the one telephone in Bonanza City to phone her parents and break the news. They scream with delight. The pumping competition has also divided the four teams into classes. The winners are "upper class", and don't have to do anything. Second place created a "merchant" team. They get to run the candy shop and dry-goods store. The third-place team became the town's cooks. Fourth were the labourers who had to clean the toilets. They were also paid the least. They seemed to take it with good grace but a washing-up war seemed to be brewing for episode two. The most far-sighted child was the youngest, Jimmy, 8. He hated it from the start. He spotted Greg, the eldest at 15 – and therefore revered by most – as the nasty brute that he was. "Greg thinks he's cool but he isn't," Jimmy said on day one. On day four the children were allowed to leave if they wanted. All stayed, except Jimmy. "I think I'm way to young for this," he said. He was wasn't. Just the most sensible. http://entertainment.timesonline.co....cle2495670.ece  Reading, Writing and Raunch: Mean Girls Rule Prep School Alessandra Stanley It seems preposterous even to type the following sentence: The television version of “Gossip Girl” on CW tonight does not quite live up to the novels. Some will be relieved, since this series of young-adult novels by Cecily von Ziegesar — about rich Upper East Side teenagers who drink martinis, smoke marijuana, shop and shoplift and cut class to have sex in Park Avenue penthouses — is “Reefer Madness” for parents. It is possibly the scariest tableau of prep school privilege since Robert Chambers requested another round at Dorrian’s Red Hand in 1986. It’s not what the show is missing that misses the point of the books; it’s what it adds — namely parents. Josh Schwartz, creator of “The OC,” is an executive producer and writer of “Gossip Girl,” and helped turn it into an East Coast version of that other show: “The EC.” It’s a sleek, glossy, musically enhanced soap opera centered on wealthy, gorgeous high school students who connive and cavort to the sound of Rihanna, Justin Timberlake, Peter Bjorn and John, Angels & Airwaves, and Timbaland. The television version does not violate the books’ basic principles: The anonymous Gossip Girl is an unseen narrator (Kristen Bell, “Veronica Mars”) who blogs about the movements and misdeeds of Serena (Blake Lively), her B.F.F. Blair (Leighton Meester) and other friends as they drink, smoke pot and hook up at trendy clubs. But the CW adaptation pumps up the importance of parents, particularly Rufus, father to Dan (Penn Badgley) and Jenny (Taylor Momsen), middle-class Brooklyn kids who chafe beneath the scorn of their more glamorous classmates. In the novels Rufus is a minor figure, a scraggily failed poet with bad hygiene; here he is played by Matthew Settle as a former rock musician with romantic problems of his own, including a history with Serena’s snobby mother. The blending of adult and teenage story lines was crucial to “The OC,” but here it is a glaring violation of the genre. “Gossip Girl,” along with similar series like “The A-List” and “The Clique,” is Mean Girl lit, mass-market paperbacks that put “Sex and the City” in a teenage context, with lots of sex and erotic brand names like Prada, Absolut and St. Barts. And while these works are often criticized as a devolution from Judy Blume’s coming-of-age novels, they are actually closer to children’s literature. Like “Peter Pan,” “Alice’s Adventures in Wonderland” or the “Harry Potter” series, these novels are fantasies and projections of an imaginary world where parents are dead or peripheral, and lost boys and girls struggle on their own with good and evil, or in this case, Bergdorf Goodman and evil. Even the characters’ names — Blair Waldorf and Serena van der Woodsen — are as fancifully evocative as those found in children’s books, like Willy Wonka in “Charlie and the Chocolate Factory” or the candy magnate Lord Skrumshus in “Chitty Chitty Bang Bang,” Ian Fleming’s novel for children. (Fleming, whose spy James Bond met up with one Pussy Galore, never quite outgrew that name game.) Parents matter on “Gossip Girl,” and their negligence veins the narrative as if to explain their children’s excesses. CW specializes in young-adult television, and certain public-trust habits are hard to break, like enriching spoiled, bratty characters with poignant back stories to make them more sympathetic — or justifiable to media monitoring groups like the Parents Television Council. Oh, and also, Serena and Blair don’t smoke cigarettes. It is an odd crick in our culture that a show geared toward younger viewers will depict minors drinking alcohol and doing illegal drugs, but draw the line at cigarettes. Good citizens complain about the power of the tobacco lobby in Washington, but in Hollywood it seems that the anti-tobacco lobby is stronger, and even more intimidating to industry executives than Mothers Against Drunk Driving, or for that matter, the federal Drug Enforcement Administration. The show even assigns Serena, back from boarding school under mysterious circumstances, a younger brother who attempted suicide and is misunderstood by all but his caring, if troubled, sister. (In the novels he is older, at Yale and an object of female lust, not psychotherapy.) Children’s book protagonists skirt past private wounds; they are too busy exploring Narnia or Neverland and fending off witches, pirates and Indian chiefs — or hostile saleswomen at Bendel’s. Only adult fiction indulges the grown-up delusion that children are interested in their parents’ personal lives. The mothers and fathers in “Gossip Girl” novels like “Because I’m Worth It” and “Nothing Can Keep Us Together” are peripheral figures, shallow socialites, divorcées and Wall Street tycoons who provide credit cards, neglect and a few bare-bones plot points, much the way Mr. Darling’s decision to chain Nana, the nanny watchdog, in the yard gave Peter Pan his chance to fly away with Wendy and the boys. That “Gossip Girl” novels have no underlying moral lesson is exactly the point; the tale of Hansel and Gretel has no redeeming social message either, except perhaps to beware of candy. http://nytimes.com/2007/09/19/arts/t...goss.html?8dpc  'Brady Bunch' Star Reveals All About Lesbian Fling With TV Sister?  Jan, Jan, Jan! Wholesome former The Brady Bunch star Maureen McCormick is set to reveal the beloved 70s TV series' most shocking secret in a new book - she and her on-screen sister had a lesbian fling. McCormick's tell-all, "Here's The Story," won't hit bookstores until 2008, but publishers are already buzzing about the big reveal. As well as talking candidly about her well-documented eating disorder and drug problems in the book, TV's Marcia Brady will come clean about a romance she had with co-star Eve Plumb, who played her sister Jan on the hit show. A source tells the National Enquirer, "The most explosive comments will be how the then-blonde, blue-eyed cutie developed a crush on Eve Plumb, which led to some sexual play. This book will certainly come as a shocker. While Maureen is not a lesbian, she reveals there were some sexual hijinks going on behind the scenes. It's bizarre because she played such a virginal character on the show." http://www.starpulse.com/news/index....ll_about_lesbi  Who says it only takes three minutes? Yale Student Faces Voyeurism Charges Over Sex Tape AP A Yale sophomore is facing criminal charges, including voyeurism, for allegedly showing his four roommates a video of himself and his then-girlfriend having sex. Casper Desfeux, a Copenhagen, Denmark native, told police he recorded the incident without the woman's knowledge using a camera on his Apple MacBook, according to the arrest warrant affidavit. The woman, who is also a Yale student, found out about the video from one of Desfeux's roommates, according to police. Desfeux, 20, a sophomore residing in Davenport College, told police he activated the camera because he just "wanted to see if it worked." Police say the woman brought the charges to prevent the sexually explicit video footage from being disseminated around the university or on the Internet. The arrest warrant states she was "very emotionally upset" over the incident. Desfeux was to be arraigned Thursday in Superior Court on voyeurism and dissemination of voyeuristic materials. Desfeux told Yale police he never sent the video to anyone because, at 45 minutes, it was too lengthy to process. He also said he did not make any still photos from it. Police have seized the laptop, camera and other items, which are being held in the evidence room of the Yale Police Department until they can be delivered to the state police forensic laboratory for examination, according to the affidavit. http://www.newstimeslive.com/news/st...?id=1186571494  "Not Tonight, Honey, I'm On the Internet" Jacqui Cheng Americans of all ages can't go very long without the Internet—in fact, they prefer the Internet over everything else, including their friends and one of nature's most primal instincts. The world's fourth-largest advertising agency, JWT, made the findings in a survey of 1,011 American adults, and discovered that the Internet has become such an integral part of our lives that some of us are willing to make major sacrifices for it. Survey respondents were asked how long they could go without an Internet connection and still feel "OK." 15 percent of the group admitted to being weak-willed and said that they would only be able to last a day or less without feeling isolated and disconnected from the world. Another 21 percent didn't do much better, saying they could only go a couple of days, with 19 percent saying they could go "a few days." Only about 18 percent of the group said that they could go a week or more without being connected, according to the results seen by Ars Technica. Notably, respondents over the age of 55 were just as likely to say that they live part of their lives online as those under 35 (43 and 44 percent, respectively), and roughly half of both age groups said that they feel like "something is missing" if they cannot access the Internet. But that's not the juicy part. The old adage that sex is on people's minds x times per second may still be true, but that apparently didn't outweigh the desire for the Internet in 20 percent of the survey's respondents. Members of this group said that they knowingly spent less time having sex as a result of Internet use, and another 28 percent of the group acknowledged that they spent less time with their friends because of the amount of time spent online or playing with gadgets. "Sorry, I can't go out tonight. I've got a killer new iPod to check out." (Wait, I think I might have actually said that to someone once...) That said, young people were much more likely to integrate Internet access into their everyday lives so that they could actually leave the house and face the daystar every so often—that is, they were much more mobile with the help of laptops and other connected gadgets. "Older Americans are happy to sit in the same place to go online, while younger people expect to be able to connect anywhere at any time, without being tethered to a particular location or time frame," said JWT executive VP Marian Salzman in a statement sent to Ars. "Mobility represents the next big shift. Consumers who have integrated digital technologies into their life now want to move into connectivity whenever they feel like it." With both wired and wireless broadband becoming more ubiquitous throughout the US, it truly is hard for some of us to imagine our lives without constant connectivity. With Americans admitting to being addicted to e-mail and data that BlackBerry users are increasingly chained to work, it's clear that finding a balance between being connected and still having a life has become a new challenge for many of us. http://arstechnica.com/news.ars/post...-internet.html  Yikes Chris Crocker Close To Getting TV Deal TomZ The "LEAVE BRITNEY ALONE!!" guy has signed a production deal. And I am this close to moving to Canada. The 19-year old Crocker signed with the production company 44 Blue, which plans to develop a "docusoap" focusing on "the Chris Crocker experience." Crocker, who lives with his grandmother in Tennessee, had already developed a strong following on the Internet -- mainly via MySpace -- before he broke out last week with the now-infamous "LEAVE BRITNEY ALONE!!!" video. The clip has been viewed over 8 million times on YouTube in just one week. "Chris first got on our radar a year ago," said Rasha Drachkovitch, President of 44 Blue. "[The show] is going to pretty much be the 'Chris Crocker experience.' We consider him a rebel character that people will find interesting. He's going to be a TV star." http://www.shoutmouth.com/index.php/...etting_TV_Deal  Suit Seeks "A La Carte" Channel Choices Alex Veiga The U.S. pay-TV industry amounts to a cartel because it maintains profits by offering channels in prepackaged tiers rather than "a la carte," according to a lawsuit filed Thursday in Los Angeles. The federal lawsuit names every major cable and satellite television system operator as well as every major cable and broadcast television network. "The antitrust laws protect the right of choice," antitrust lawyer Maxwell M. Blecher said. "Here the customer is denied that choice." The complex web of contractual arrangements among service providers and networks amounts to a monopoly or cartel that has "deprived consumers of choice, caused them to pay inflated prices for cable television and forced them to pay for cable channels they do not want and do not watch," Blecher wrote in the complaint filed on behalf of cable subscribers in several states. The complaint, which alleges a conspiracy to monopolize as well as violations of federal antitrust laws, names nine plaintiffs, but Blecher wants the U.S. District Court to certify it as a class action. Calls to the National Cable and Telecommunications Association, a trade group for the U.S. cable television industry, were not immediately returned. Blecher contends cable and satellite television subscribers should be able to pay only for the channels they actually want to watch. Federal Communications Commission Chairman Kevin Martin has said such a system would require federal legislation. The cable TV industry has argued that such an a la carte system would lead to higher prices, less programming diversity and fewer channels in part because advertising revenue would fall. Such a system also would require more customer service representatives and raise the costs of billing and marketing, the industry has said. Blecher's lawsuit seeks unspecified damages and wants the court to force cable operators to tell subscribers they can purchase channels individually. Blecher estimated as many as 80 million people receive bundled cable or satellite television packages and could be a party to the case should it receive class-action status. The companies named in the suit are NBC Universal Inc., Viacom Inc., The Walt Disney Co., Fox Entertainment Group Inc., Time Warner Inc., Comcast Cable Communications Inc., Cox Communications Inc., The DirecTV Group Inc., Echostar Satellite LLC, Charter Communications Inc. and Cablevision Systems Corp. ___ Associated Press Writer John Dunbar in Washington contributed to this report. http://news.yahoo.com/s/ap/20070920/...ble_tv_lawsuit  CBS Is Sued by Rather Over Ouster Jacques Steinberg Dan Rather, whose career at CBS News ground to an inglorious end 15 months ago over his role in an unsubstantiated report questioning President Bush’s Vietnam-era National Guard service, filed a lawsuit yesterday against the network, its corporate parent and three of his former superiors, including Sumner M. Redstone, the executive chairman of CBS. Mr. Rather, 75, asserts that the network violated his contract by giving him insufficient airtime on “60 Minutes” after forcing him to step down as anchor of the “CBS Evening News” in March 2005. He also contends that the network committed fraud by commissioning a “biased” and incomplete investigation of the flawed National Guard broadcast in order to “pacify the White House.” Asked yesterday in his lawyer’s office why he was taking such action now, Mr. Rather said he had been unable to let go of numerous lingering questions about the Guard report and CBS’s handling of its fallout. In recent months, he said he had even assembled “a team” of associates at his own expense — he declined to say whether it included private investigators — that had turned up new information. Among his findings, he said, was that a private investigator hired by CBS after the report’s broadcast had unearthed evidence that might exonerate him, at least in part. “I’d like to know what really happened,” he said, his eyes red and watering. “Let’s get under oath. Let’s get e-mails. Let’s get who said what to whom, when and for what purpose.” The suit, which seeks $70 million in damages, names as defendants CBS and its chief executive, Leslie Moonves; Viacom and its executive chairman, Mr. Redstone; and Andrew Heyward, the former president of CBS News. In a statement CBS said, “These complaints are old news and this lawsuit is without merit.” Mr. Heyward said he would not comment beyond the CBS statement. A Viacom spokesman said he had no comment. In the suit, filed in State Supreme Court in Manhattan, Mr. Rather charges that CBS and its executives made him “a scapegoat” in an attempt placate the Bush administration, though the formal complaint presents virtually no direct evidence to that effect. To buttress this claim, Mr. Rather quotes the executive who oversaw his regular segment on CBS Radio as telling Mr. Rather in November 2004 that he was losing that slot, effective immediately, because of “pressure from ‘the right wing.’ ” Mr. Rather also continues to take vehement issue with the appointment by CBS of Richard Thornburgh, an attorney general in the administration of the elder President Bush, as one of the two outside panelists given the job of reviewing how the disputed broadcast had been prepared. For both Mr. Rather and CBS, the filing of the suit threatens to once again focus attention on one of the darker chapters in the history of the network and its storied news division, at a moment when its flagship evening news program continues to lag. Mr. Rather’s permanent successor as evening news anchor, Katie Couric, has remained stuck in third place in the network news ratings since taking over the broadcast a year ago. She has not only attracted fewer viewers than Charles Gibson of ABC and Brian Williams of NBC, but has thus far failed to bring in the new viewers that were part of her mandate. The portrait of Mr. Rather that emerges from the 32-page filing bears little resemblance to his image as a hard-charging newsman. By his own rendering, Mr. Rather was little more than a narrator of the disputed broadcast, which was shown on Sept. 8, 2004, on the midweek edition of “60 Minutes” and which purported to offer new evidence of preferential treatment given to Mr. Bush when he was a lieutenant in the Air National Guard. Instead of directly vetting the script he would read for the Guard segment, Mr. Rather says, he acceded to pressure from Mr. Heyward to focus instead on his reporting from Florida on Hurricane Frances, and on Bill Clinton’s heart surgery. Mr. Rather says in the filing that he allowed himself to be reduced to little more than a patsy in the furor that followed, after CBS concluded that the report had been based on documents that could not be authenticated. Under pressure, Mr. Rather says, he delivered a public apology on his newscast on Sept. 20, 2004 — written not by him but by a CBS corporate publicist — “despite his own personal feelings that no public apology from him was warranted.” The panel led by Mr. Thornburgh, as well as Louis Boccardi, a former chief executive of The Associated Press, did not single out Mr. Rather for the broadcast’s failures, but did fault several producers and executives for rushing the report to broadcast without sufficient vetting. Mr. Rather now leads a weekly news program on HDNet, an obscure cable channel in which he is seen by a small fraction of the millions of viewers who once turned to him in his heyday. Mr. Rather’s suit seeks $20 million in compensatory damages and $50 million in punitive damages. Among the pivotal points of contention in his complaint are the definitions of the words “full-time” and “regular.” As quoted in the filing, Mr. Rather’s contract — which he signed in 2002, and which stipulated he be paid a base salary of $6 million a year as anchor — entitled him to a job as a “full-time correspondent” with “first billing” on the midweek edition of “60 Minutes,” should he leave the anchor chair before March 2006. As it turned out, Mr. Rather did leave the anchor chair a year early, and was indeed reassigned to “60 Minutes II.” When that broadcast was canceled a few months later, Mr. Rather’s contract called for him to move to the main “60 Minutes” broadcast on Sunday evening, where he would “perform services on a regular basis as a correspondent.” During the 2005-6 television season, Mr. Rather had eight segments broadcast on the main “60 Minutes,” half that of other correspondents. “He was provided with very little staff support, very few of his suggested stories were approved, editing services were denied to him, and the broadcast of the few stories he was permitted to do was delayed and then played on carefully selected evenings, when low viewership was anticipated,” the filing contends. Theodore O. Rogers, the head of the labor and employment group for the law firm of Sullivan & Cromwell, said that this could be the strongest of Mr. Rather’s arguments. “Potentially, if he could point to evidence that when they negotiated, there was an established meaning of ‘regular’ that was breached, there could be a claim,” said Mr. Rogers, who is not involved in the case. Among the most egregious indignities he suffered, Mr. Rather says, was the network’s response to his request to be sent as a correspondent to the scene of Hurricane Katrina in the fall of 2005. “Mr. Rather is the most experienced reporter in the United States in covering hurricanes,” his lawyers write in the suit. “CBS refused to send him,” thus “furthering its desire to keep Mr. Rather off the air.” http://www.nytimes.com/2007/09/20/bu.../20cbs.html?hp  Rather Expected to Report Boeing 787 Unsafe Boeing Co's new carbon-composite 787 Dreamliner plane may turn out to be unsafe and could lead to more deaths in crashes, according to a report by veteran journalist Dan Rather to be broadcast in the United States on Tuesday. The new plane, which is mostly made from brittle carbon compounds rather than flexible aluminum, is more likely to shatter on impact and may emit poisonous chemicals when ignited, Rather will report based on interviews with a former Boeing engineer and various industry experts, according to a transcript of the show. "The problem is all the unknowns that are being introduced and then explained away as if there is no problem," said Vince Weldon, a former Boeing engineer, in an interview to be broadcast as part of Rather's report. Weldon compares a recent crash in a standard aluminum plane where the dented but intact fuselage kept fire at bay and allowed the passengers to leave the plane alive. "With a composite airframe, the fuselage would not crumple, it would shatter ... that shattered hole would be there for the fire that's going into the airplane," Weldon says in the interview. "Instead of everyone getting out, it would be a far less positive result." Weldon says he was fired by Boeing after a 46-year career because of his persistent complaints about the design of the 787. He claims he represents the view of others at Boeing who were afraid to speak out. Boeing, which did not provide officials for on-camera interviews in Rather's report, said on Tuesday Weldon's claims were not valid and the plane would not fly if it is not safe. "We've looked at Mr. Weldon's claims. We've had technical committees review them. We do an exceptional amount of testing," said Lori Gunter, a spokeswoman for Boeing's commercial plane unit. "Absolutely, these materials are safe. They are tested, they will be certified." She said the Federal Aviation Administration (FAA) must find the 787 to be as crashworthy as aluminum planes, and the plane was doing well in those tests so far. She declined to comment on the circumstances of Weldon's departure from Boeing. First Flight Delayed Boeing's lightweight, fuel-efficient 787, which has become its most successful plane launch ever, is set for its first test flight between mid-November and mid-December after a three month delay due to a shortage of bolts and problems programming the flight control software. The first 787 is due to be delivered to Japan's All Nippon Airways in May next year, meaning it will have at most six months of flight tests, much shorter than previous jetliner programs. Boeing's rival Airbus, owned by European aerospace company EADS, is also working on a composite fuselage for its new A350 jet, but it is some years behind Boeing in the design and production process. In Rather's report, Weldon and other experts also argue that the carbon-composite fuselage would not survive a lightning strike as well as aluminum, would emit toxic fumes when burning, and could easily be damaged without any visible sign. Weldon says Boeing was misrepresenting to airlines the ease of maintenance on carbon fuselage planes. The report cites experts referring to Airbus planes that had carbon parts with problems that were not easily visible. Rather's report also includes aviation experts who see little or no problem with the 787. "I'm excited to ride on the 787. I'm excited to fly in composite aircraft," says Joseph Rakow, an engineer at consulting company Exponent Inc, in an interview in the report. Todd Wissing, a commercial pilot, says he would fly the 787 as long as the composite materials are rigorously tested. "We put safety as our top priority," says Wissing in the report. "We use the 21st Century inspection methods with these new materials. Then we have complete confidence that we can get in that airplane with our passengers and go fly because that's what we can do." The report by former CBS News anchor Dan Rather is the latest edition of "Dan Rather Reports", broadcast on HDNet, a subscription-only television channel that about 4 million Americans are able to view. Last year Rather left CBS after a scandal over his reporting on President George W. Bush's military record. http://www.foxnews.com/story/0,2933,297248,00.html  NBC to Offer Downloads of Its Shows Bill Carter NBC Universal said yesterday that it would soon permit consumers to download many of NBC’s most popular programs free to personal computers and other devices for one week immediately after their broadcasts. The service, which is set to start in November after a test period in October, comes less than three weeks after NBC Universal said it was pulling its programs out of the highly successful iTunes service of Apple Inc. That partnership fell apart because of a dispute over Apple’s iTunes pricing policies and what NBC executives said were concerns about lack of piracy protection. NBC’s move comes as companies throughout the television business search for new economic models in the face of enormous changes in the business. Networks continue to lose audience share, and viewers — especially many of the highly prized viewers under 30 years old — are increasingly demanding control of their program choices, insisting on being able to watch shows when, where and how they want. At the same time viewers are finding more and more ways, like TiVo machines, to avoid watching the commercials that have long provided the bulk of television revenue. Jeff Gaspin, the president of the NBC Universal Television Group, said, “The shift from programmer to consumer controlling program choices is the biggest change in the media business in the past 25 or 30 years.” NBC makes many of its popular shows available online in streaming media, which means that fans can watch episodes on their computers. Under the new NBC service, called NBC Direct, consumers will be able to download, for no fee, NBC programs like “Heroes,” “The Office” and “The Tonight Show With Jay Leno” on the night that they are broadcast and keep them for seven days. They would also be able to subscribe to shows, guaranteeing delivery each week. But the files, which would be downloaded overnight to home computers, would contain commercials that viewers would not be able to skip through. And the file would not be transferable to a disk or to another computer. The files would degrade after the seven-day period and be unwatchable. “Kind of like ‘Mission: Impossible,’ only I don’t think there would be any explosion and smoke,” Mr. Gaspin said. The programs will initially be downloadable only to PCs with the Windows operating system, but NBC said it planned to make the service available to Mac computers and iPods later. In a second phase of the NBC rollout, customers would pay a fee for downloads of episodes that they would then own, and the files would be transferable to other devices. NBC hopes to offer this service by mid-2008, depending on how quickly the company can put in place the secure software necessary to allow payment by credit card. The latter system is what is already available through iTunes. Chris Crotty, an analyst for iSuppli, an independent firm that specializes in analysis of new electronic media, said of the NBC move, “I think it’s a stretch.” He argued that consumers have shown they are extremely happy with the iTunes service and that it would not be attractive to consumers to have to range far and wide over a number of services to find the programs they want to download. “It’s not just a shift from a supermarket to a mom-and-pop story, it’s a shift to one store that only sells bread, another store that only sells dairy products. The consumers have decided they want to get their content from iTunes.” Mr. Crotty said NBC had come across to consumers as “highly greedy” in its dispute with Apple. Apple reported that NBC was insisting it raise the price of some downloads on NBC shows to $4.99 from the $1.99 iTunes charges for all programs. NBC hotly denied that, saying that the disagreement was over what Mr. Gaspin termed the wholesale price that Apple was charging, not the retail price. NBC wanted a better wholesale price for its heavily downloaded shows, like “The Office,” the biggest seller on iTunes. But, Mr. Gaspin said, “piracy was and is our No. 1 priority.” He said that the music industry had been devastated by the free exchange of music, much of it facilitated by iTunes. Apple representatives did not respond to requests for comment last night. Mr. Gaspin said that one important attraction of the NBC service was the option it would offer consumers to receive programs on a temporary basis free, but including commercials, as well as the choice to pay a fee for episodes without commercials and own the programs. NBC hopes to extract significant revenue both ways, though it is not estimating what kind of money the service may generate. Nor did NBC Universal project what the service would cost. Mr. Gaspin noted that none of this meant that NBC was moving away from its traditional model of a nightly schedule of programs supported by advertising. He pointed to sales of television sets, driven by high-definition equipment, which are soaring to levels, he said, that surpass those of the biggest booms in color set sales. "Our research shows that 83 per cent of the viewers would still rather watch on a TV than a PC," Mr. Gaspin said. But he acknowledged that the numbers were different for younger viewers, a trend stirring much of the concern about the business’s future. "What we don’t know is if habits will change when people get to their 40s," Mr. Gaspin said. But he added, "I don’t think anyone would argue with the idea that the customer is going to be in control." http://www.nytimes.com/2007/09/20/bu.../20nbc.html?hp  ABC's AOL Pact Marks Web's Growing TV Allure Rebecca Dana Walt Disney Co.'s ABC became the latest major network to strike a deal with AOL allowing its full-length prime-time shows to be available free on the Time Warner Inc.-owned portal. ABC shows will be available on AOL starting today, a few weeks before NBC Universal and News Corp.'s Fox are expected to launch their jointly owned online venture Hulu, which will make NBC and Fox programs available on several major Web portals including AOL. CBS shows are already available on AOL. CBS is a unit of CBS Corp.; NBC is a unit of General Electric Co. ABC's deal highlights how the online strategy of the major TV networks has evolved over the past 18 months, reflecting rapid growth in the number of people watching online video and increasing advertiser interest. In May of last year, ABC became the first of the major networks to offer its most popular shows in full and free on the Web. Most of the other networks followed. Initially the networks' focus was to stream shows on their own Web sites, but media companies have changed tack this year, striking deals with major portals to ensure that as broad an audience as possible sees the show. Hulu, for instance, will allow viewers to watch NBC and Fox shows on AOL, Microsoft Corp.'s MSN, News Corp.'s MySpace and Yahoo Inc. Hulu is expected to start offering programs in October, although a precise date hasn't been announced. NBC yesterday announced an additional online service for its TV shows called NBC Direct, enabling viewers to download ad-supported episodes free from NBC.com. ABC's agreement goes into effect days before the networks' fall season kicks off, ensuring ABC fans will be able to watch some of the network's new shows, such as "Pushing Daisies," as well as older shows such as "Grey's Anatomy." The shows will be available one day after they air on broadcast television, and approximately four episodes of every show will be available for viewing at one time. ABC and AOL will share revenue from the arrangement under terms neither company would discuss. Anne Sweeney, president of the Disney-ABC Television Group, said the deal with AOL marks a new phase in the network's digital strategy: opening up ABC programming to as large an audience as possible, but in a way that would protect the network's shows from piracy and appeal to both advertisers and affiliates. As part of the deal, ABC will use "geo-targeting" to embed one local ad appropriate for each viewer alongside three national ads in each hour of programming. The deal is a welcome one for affiliates, which have feared being on the losing end as networks move their content online. "The single most significant impediment to stations being able to take good advantage of this opportunity has been the inability to target the viewing that occurs in their markets," said Ray Cole, chairman of the ABC Television Affiliates Association. http://online.wsj.com/article/SB119024219680633034.html  Fox To Offer Free Shows On Apple iTunes Douglas A. McIntyre Not to one to be out-flanked by NBC or ABC, News Corp's Fox unit will offer some of its most popular shows free on Apple iTunes. According to the LA Times, it is "a move that highlights the TV industry's race to harness the Internet and try out potential business partners." The new effort by Fox seems a bit misguided. The ability to watch first run TV on an iPod could actually pull audience away from TV viewership and put pressure on ad rates. The idea of charging some nominal fee, like $.99, would at least put a level of value on the shows. Fox may be gambling that allowing the free downloads will promote TV viewership, by adding "buzz". But, what consumer is going to check out the show on an iPod and then watch it on home television as well? http://www.247wallst.com/2007/09/news-corps-fox-.html  FOX Censors the Flying Nun Amil Niazi Sally Field won a Primetime Emmy recently, and she took the opportunity to get sanctimonious. Her acceptance speech was vaguely anti-war and she tripped her way through the words in a way both touching and deluded. If you watched in Canada, you caught the end of her speech where she boldly claimed “if mothers ruled the world, there would be no more goddamn wars.” So what, right? She’s no Hanoi Jane. But for Americans, the Big Brotherly FOX Network found Sally’s words disgraceful and censored out the end of her speech, displacing it with a very awkward cut away and dead air. Prompting many to think, holy shit what a weird thing to do. Kathy Griffin was another victim of unnecessary censorship, when her joke about Jesus at the Creative Emmy fell flat on the ears of the Catholic League and resulted in the entire bit being removed from re-broadcasts. FOX censors are claiming they cut away from Fields because of the word goddamn, but that seems a rather thin excuse considering their programming generally displays more vulgar behaviour and language than an old-timey whorehouse. Not to mention that a majority of the shows nominated for awards that night regularly feature a barrage of cussing, sexing and mob-style shooting. All things considered, it would appear that FOX installed its version of fair and balanced coverage, and vetoed the musings of an aging actress because she was speaking out against an already unpopular war. Her words came on the heels of a trying week for anyone still deluded enough to think there were any positives remaining in the battle against terrorism. For a beleaguered network that had long ago embraced a shady administration, FOX was merely taking orders, albeit standing orders that at this point don’t necessarily need to be voiced. Blathering though Fields may be, and as frequently unfunny as Griffin generally is, both have every right to speak their minds. Celebrities are a distraction for the masses, but also serve as a kind of retarded megaphone for those who don’t have access to a soapbox. Through their well-meaning diatribes many people are able to relate their long-standing frustration at having been punished for too long by pro-war pundits and mega-Christian talking heads. As painful as it is to side with a woman like Kathy Griffin, it’s more painful to see the vitriol so many ruddy-faced Catholics have spewed against her. Considering the countless years we have endured alcoholic, narcissistic and promiscuous celebrities and politicians thanking God for their success, it seems only fair that someone come out with an opposing view. Just as there’s no harm in Gidget speaking out, not against wars, but for mothers. Are her neutered sentiments really going to cause children to start worshiping Satan, or whatever it is the censors are trying to prevent when they bleep otherwise harmless words? But truly the most deplorable fact in this whole mess is that the so-called guardian of America’s purity is also the same network that picked up The Simple Life when it was slated for cancellation. For shame FOX, for shame. http://onlymagazine.ca/Mental-Health/1403/hanoi-sally  BitTorrent 6 Released with uTorrent Capabilities Kristen Nicole BitTorrent, which acquired uTorrent late last year, has just released BitTorrent 6, the first version that combines the two services, incorporating uTorrent functionality with BitTorrent’s open-source base (uTorrent was a closed-source service). With BitTorrent 6, you’ll see that the user interface now resembles that of uTorrent’s, including the menu bar. Its system resources now run with uTorrent capability, which is faster and takes up less space than BitTorrent. BitTorrent 6 is a complete overhaul from its previous incarnation. The interface is the same as µTorrent’s, except for three toolbar icon changes that look more like variations than outright differences. The contents of the menus in the menubar are now identical to µTorrent as well, which means that advanced functionality like tweaking your Web UI has finally come to the BitTorrent client. Despite the obvious changes and integration with BitTorrent 6, the end goals of BitTorrent in regards to uTorrent still are unclear. Some speculate that the two will remain separate, and BitTorrent could be promoted as a destkop program while uTorrent could continue to be a lightweight, portable option. In other uTorrent news, the service has recently launched an iPhone option. http://mashable.com/2007/09/21/bittorrent-utorrent/  EMusic, a Song-Download Site, to Offer Audiobooks Andrew Adam Newman The company that has given Apple’s iTunes the most competition in the song-download arena will now compete with it in selling audiobooks, too. Beginning tomorrow, eMusic, which is second to iTunes in music download sales, will offer more than a thousand books for download, with many of them costing far less than on iTunes. For example, “The Audacity of Hope,” read by author Barack Obama, will cost $9.99 on eMusic compared with $18.95 on iTunes. The retail price for a five-CD version of the same book is $29.95. The biggest selling point for eMusic is also its biggest point of controversy: the site uses the MP3 format, which works on any digital player but lacks the technology, known as digital rights management, that protects copyrighted material from unlimited duplication. By contrast, iTunes only works on an iPod, and songs downloaded from the service can be burned onto a CD only once and cannot be transmitted over the Internet. EMusic’s lack of piracy protection is the reason no major music label has signed on with it, and why only a few audiobook publishers have so far. But the site is enormously popular: although dwarfed by Apple, which has 71 percent of the music-download market, eMusic, which has 10 percent, still sells more than twice as many songs as competitors like Napster, Rhapsody and WalMart.com. It is owned by Dimensional Associates, an arm of JDS Capital Management. Some publishers are just dipping in a toe. Random House Audio, for example, will be selling about 500 titles, roughly 20 percent of its catalog, through eMusic. “We’re very interested in testing this, but we didn’t think it was appropriate to put all of our titles in a test program,” said Madeline McIntosh, the group’s publisher. Like her counterparts in the music business, Ms. McIntosh is concerned about piracy, but doubts it will be as big an issue for audiobooks, which draw an older audience and are unwieldy to circulate. Unabridged audiobooks sold in stores often comprise more than a dozen CDs, and, in digital format, the enormous files cannot be e-mailed as easily as single songs. “If we see that piracy of our products is increasing, we would stop,” Ms. McIntosh said, adding that her company monitors file-sharing networks and that there will be a “watermark” on eMusic files. “But I don’t expect that working with eMusic would lead to an increase.” “Our customers don’t steal music,” said David Pakman, chief of eMusic, of the company’s 300,000 subscribers, who pay from $9.99 (for 30 songs) to $19.99 (for 75 songs). “A lot of them are technically sophisticated, but they’re not prone to piracy.” Nevertheless, some publishers have no interest in signing on with eMusic. “I think it’s a mistake,” said Brian Downing, publisher of Recorded Books, which is more than 25 years old and whose authors include Philip Roth and Jodi Picoult. “I think our obligation to protect the files and protect the authors is a big one.” Hachette Audio will start by selling only about 15 titles on the site, but that includes bestsellers like “America (The Book): A Citizen’s Guide to Democracy Inaction” by Jon Stewart. At the other end of the spectrum is Penguin Audio, which will sell on eMusic all the audiobooks it currently makes available in a digital format on iTunes, about 150 titles. “Publishers have been waiting for other companies to play ball,” said Patti Pirooz, the executive producer. Most publishers have been playing ball with Audible Inc., which pioneered downloadable audiobooks 12 years ago and sells its wares through iTunes and its own Web site, audible.com. Audible sells about 15,000 audiobooks and another 20,000 recordings of public radio shows and periodicals like The Wall Street Journal and The New York Times. Audible has its own proprietary digital format, which plays on both iPods and non-Apple devices, but still cannot be duplicated except to copy onto CDs just once. Spokesmen from Audible and Apple declined to comment on eMusic. Since it was founded in 1995, Audible has grown steadily. It went public in 1999, and its 2006 revenues of $82.2 million were up 30 percent over the previous year. But this growth has not translated into profit: Audible has lost money in seven of the last eight years, including $8.4 million last year. In 2006, Audible earned 24 percent of its income selling content on iTunes, compared with 11 percent in 2004. While eMusic will offer fewer titles than Audible sells on its site or through iTunes, it will do better on price. A one-book-a-month subscription to eMusic is $9.99; the same on Audible is $14.94, while a two-books-a-month subscription is $22.95. As for the issue of intellectual property, Mr. Pakman of eMusic said that his company’s expansion into audiobooks signaled growing acceptance of the easy-to-copy MP3 format in general. “Here you have Random House, the largest publisher in the U.S., taking part in this,” Mr. Pakman said, noting that Random House’s parent company, Bertelsmann, also owns BMG Music. “What they’re doing is prioritizing the need for sales and growing the market share over copy protection. It speaks to the larger trend that media companies are now getting comfortable with something they probably should have done seven or eight years ago.” http://www.nytimes.com/2007/09/17/bu...audiobook.html  Apple’s Ringtones and Copyright Law Apple's iTunes ringtones and the complex world of copyright law Daniel Eran Dilger While I’m no huge fan of the “all singing, all dancing” mobiles that announce every incoming call by belting out a section of a song--particularly since they tend to use songs that I don’t want stuck in my mind for the next hour--ringtones are extremely popular and a big money business, so they’re not going away anytime soon. The latest version of iTunes now allows users to select from a half million songs in the iTunes Store that can be “upgraded” from a regular 99 cent track to a ringtone by paying another 99 cents to carve out a user-defined, 30 second clip as a ringtone that can be synced to the iPhone. Suddenly, everyone who was cool with Verizon Wireless charging $2.50 and up for individual ringtones came out of the woodwork to castigate Apple for selling ringtones as a 99 cent upgrade, and only for songs it sold within iTunes; by default, you can’t make a ringtone from songs ripped from your own CDs using iTunes. Of course, you actually can do this by changing the filetype of the song and assigning it a metadata tag, but Apple doesn’t tell you this, and doesn’t really want users to exploit this because it will send it back into negotiations with the labels again. The Ringtone Circus. Remember that Apple appeared poised to deliver a ringtone sync function in iTunes back in January, but then pulled the feature and later backed away further by adding new legalese to the iTunes terms of service that excluded downloads from being used as ringtones. Clearly, the record companies jumped on ringtones as a whole of stack of potential profits that could not be allowed to go without remuneration. Apple makes very little from sales of music in iTunes; the vast majority of revenues are funneled back to the record companies, which then devise how to avoid paying their talent and keep as much as they can. At stake are the complex copyright laws involving derivative works, performing rights, and reproduction rights. Apple’s iTunes breaks open a whole can of worms because it is changing the market for music and video. The Complex World of Copyright. Copyrights were designed to make sure that the creator of an original work would be compensated for copies, whether they be exact copies or derivative works based on their original. For example, a movie based on a play or a novel has to respect the copyrights held by the original work, because much of the value of that derivative work comes from the original. In the music industry, groups like ASCAP license performing rights of music created by composers, songwriters, lyricists, and music publishers. Bands playing their music have to pay royalties, which are commonly split between the writer of the song and the author of its lyrics. In addition to live bands, any commercial playback of music also requires performing rights licensing. Music played during a TV show, over the radio, or even in a restaurant requires obtaining a license and paying fees. Publishing music requires a different set of permissions referred to as mechanical rights. CD and record manufacturers pay music owners fees to create copies of a given work. When musicians perform and their work is captured as a “master recording,” the reuse of that work must be licensed under master use rights. There are also synchronization rights involved in incorporating a music recording into a film or video performance or a commercial, and grand rights for using recordings as part of a dramatic performance such as a musical, opera or ballet. The music business is therefore based upon a series of complex legal relationships between writers, performers, distributors, and the groups that represent each of their rights and their legal obligations. Consumers Left Mystified; Fair Use Left Undefined. Outside of the complex world that funds artists and their work, the idea of paying a license to play or use a song in different contexts is hard to grasp. Laws to define protections for producers were worked out long ago to make sure artists would get paid, but the rights of consumers haven’t been so carefully defined. Consumers’ rights are based on the general idea of “fair use,” which isn’t a right defined in law. Instead, it’s a general defense against claims of copyright infringement. If the recording industry were to sue an individual for copying music from their CDs onto their iPod, they would likely lose because the idea of fair use generally determines that consumers can use their own music in reasonable ways. Unfortunately, fair use has not been upheld in clear court precedents or in law to the point where it can really be called a right. This leaves things enshrouded in a grey fog where consumers assume that anything they can do with “their music” is fine, while the music industry seeks to find new ways to sell its products. Ask Not For Whom the Ring Tones. Writing about Apple’s iTunes ringtones, John Gruber of the Daring Fireball cited Engadget, which reported that “the RIAA wanted to be able to distribute ringtones of its artists without having to pay them big money to do so (surprised?), and it won a decision last year before the Copyright Office saying that ringtones weren’t ‘derivative works,’ meaning they didn’t infringe on the copyright of the songwriter.” Engadget, known for shooting from the hip rather than the brain, didn’t really understand whole story. From its report, Gruber concluded, “So if you have the right to play a song, you have the right to use it as a ringtone on your phone.” Gruber blamed a “complicated, confusing mess of a ringtone policy” on Apple, and suggested the company should have simply handed out tools to create ringtones from any users. Incidentally, that’s apparently what Apple was going to do back in January. Derk Nek of Epplegacks explained that--unfortunately--what the RIAA actually won in the case cited by Engadget was instead the right to collect money for ringtones without distributing those fees to the artists they represent. There was no establishing that ringtones are not protected intellectual property, so the RIAA will continue collecting royalty fees, because distributing songs or portions of songs requires mechanical rights. Playing a ringtone might also--in the mind of the RIAA and the letter of the law--require performing rights. Ringtone Performing Rights. Nek added, “I produce porn for a smattering of online websites. In one of our scenes, a ‘talent agent’ gets a phone call on his cell saying the girl will be right up, and of course the scene continues as expected. We put this file online and no complaints... until we went to release it on DVD. “With the internet if there's a complaint, you simply pull the file like it never existed, or re-edit it like it never existed in it's previous form. With a DVD there's a hard copy that's on retail shelves, which means a retailer, distributor, production company and owner of the content is liable. We were told the ringtone had to go because we didn't have the rights to have to redistributed in our DVD release. Dumb, but understandable.” “The thing about studios, networks, and labels, is they'd like nothing better but to track every pair of eyes and ears that views or hears their content, and charge based on that rather than unit. They consider a ringtone, which could be heard in a crowded cafe, subway, or street corner, something that would be a public performance of the work, and thus feel they need to be compensated. Dumb, but the truth as far as I can deduce.” Do You Have A License for that Ringtone? In addition to carefully watching every performance in order to catch any playback of any bit of music that was not paid for with the appropriate license, music industry also monitors Apple to make sure it does not confer any suggestion that users might use the labels’ music in ways that might leave money on the table. When they saw that Apple might allow users to put songs on phones, they flipped a nut and sent in lawyers to iron out a contract covering iPhone ringtones. Apple negotiated a far lower price than any other ringtone distributor, but the labels are worried that consumers might figure out how to create their own ringtones, just as they were able to figure out how to put music from CDs onto computers and MP3 players, a practice that got out of hand and resulted in more music being handed around for free than legally paid for. Nek added, “The iPhone is a hardware product which Apple derives substantial profits from, ringtones are something people want but the current state of copyright law in the states makes much more unfair than it should be.” The Wrestling Between Apple and the Labels and Studios. Nek also outlined another example of the distribution skirmish between Apple and its content producers: the fight over TV downloads from NBC/Universal. “NBC just demanded of Apple that to get Heroes for the iTS, they'd need to buy two episodes of those shows no one downloads like Passions or Friday Night Lights. Apple says that this would force them to sell Heroes at $4.99 not because NBC wants that much for each episode, but because Apple isn't in the business of losing money selling a popular show for $1.99 when they had to buy two very unpopular shows at $1.49 each on which they won't make back their investment. So instead of going ahead and selling video files of less resolution than are available at no cost on torrent sites for that $4.99 price to keep them in the black, Apple told NBC to walk. “NBC also expressed that they wanted Apple to crack down on their customer base who were walking around with devices full of stolen content, read: ‘iPods can play unprotected AAC and MP3, MPEG-4 and H.264 video files and we want you to switch to only DRM'd content so we know that every track and video file on those devices was paid for’. Again, Apple told them to walk. If all Apple was concerned with was profit, then they would've accepted the terms because it costs them nothing to keep files on the iTunes Store and a certain percentage would keep on buying TV Shows at the inflated price, which in turn would keep selling iPods and Apple TVs so people could view them. But Apple saw in these terms from NBC a very anti-consumer agenda, and made their stance on any such terms by NBC or other studios plain. “For Apple to put a ringtone editor into iTunes and have it work with the user's existing library would be in a consumers best interest definitely, but it would also be illegal as far as I understand the mickey mouse laws. Apple didn't become number three in music sales by pursuing illegal business plans, they did it by offering a better product at a competitive price. They competed against piracy with the iTunes Music Store and won. They're now competing against current mobile service providers ringtone products and are going to win.” A Legal Problem Your Representatives Don’t Care About. It is fortunate that it is in Apple’s own interests to defend the rights of consumer. The reality of copyright law isn’t going to go away however. Its complexity is seldom discussed in the simpleton arguments that suggest that the RIAA should vanish and that “the artists” are somehow magically going earn a living without a complex system to funnel money back to them as their work is copied and performed, particularly when most music is traded around for free. If the government had any interest in representing the rights of citizens as consumers, we’d have clear and fair consumer rights spelled out in law, and the music industry would have to respect them. Instead, the government is working for the industry, setting up a police state of criminal codes designed to enforce the anti-consumer laws already on the books. It doesn't help that they’re also distracted by efforts to legislate morality and criminalize free speech. Until citizens start to care about what their government is doing, these problems won’t be solved, and we’ll be stuck having to sweat copyright infringement when our mobiles ring. Of course, that should really be the least of our worries when our government is serving the moneyed interests of industry before the rights and protections of its citizens. http://www.roughlydrafted.com/RD/Tec...gh t_Law.html  RIAA Abandons "Making Available" in Amended Complaint in Rodriguez Case Ray Beckerman Here are some further developments relating to Interscope v. Rodriguez, the San Diego, California, default judgment case in which the RIAA's complaint was dismissed for failure to state a claim. Interscope v. Rodriguez On August 23, 2007, the RIAA filed an amended complaint. Interestingly, the amended complaint (a) leaves out the phrase "making available", (b) adds a phrase that plaintiffs "identified an individual" distributing files, even though their expert witness's deposition testimony in UMG v. Lindor specifically negated any claim that "an individual" was detected, and (c) adds a curious phrase that the defendant was "the individual responsible for that IP address at that date and time", a phrase which would be of dubious significance in a copyright infringement context. On August 30, 2007, the case was reassigned to Judge Hayes, due to Judge Brewster's impending retirement. Amended Complaint* August 30, 2007, Order of Reassignment* Elektra v. Barker Ms. Barker's attorneys wrote to Judge Karas, before whom is pending Ms. Barker's own motion to dismiss complaint, notifying him about the August 17, 2007, decision in Rodriguez. September 8, 2007, Letter of Ray Beckerman to Hon. Kenneth M. Karas Enclosing Copy of Interscope v. Rodriguez* Warner v. Cassin Ms. Cassin's attorneys wrote to Judge Robinson, before whom is pending Ms. Cassin's own motion to dismiss complaint, notifying him about the August 17, 2007, decision in Rodriguez. September 8, 2007, Letter of Ray Beckerman to Hon. Stephen C. Robinson Enclosing Copy of Interscope v. Rodriguez* http://recordingindustryvspeople.blo...lating-to.html  Practice Tip: I recommend that defendants' lawyers consider making motions to dismiss complaint or motions for judgment on pleadings Ray Beckerman In May of this year, the United States Supreme Court came down with the decision in Bell Atlantic v. Twombly, --US --, 127 S. Ct. 1955 (May 21, 2007) which established a "plausibility" standard for federal pleadings. In Interscope v. Rodriguez, it was held that the RIAA's boilerplate complaint, which it has been using in all of its cases for the past 4 years, and which robotically alleges only the magic incantation of "downloading, distributing and/or making available for distribution", is insufficient under the Twombly standard, and the Court dismissed the complaint. Thereafter the highly predictable RIAA lawyers, who handle these cases "programatically" (to use their leader Matthew Oppenheim's terminology), filed an amended complaint which gives us a valuable insight into how they intend to negotiate the post-Twombly, post-Rodriguez era. The amended complaint robotically inserts -- where the magic incantation used to be -- new boilerplate which is taken mostly word for word from the RIAA's boilerplate form of interrogatory answers (See e.g. page 5 of interrogatory answers in UMG v. Lindor). The new boilerplate abandons the "making available" language, and says that at a certain date and time they "detected" an individual downloading and 'distributing' files, who was doing so continually. Clearly, the new boilerplate complaint is "implausible" on its face, since (a) it is fundamental that they did NOT detect an individual (their own expert has admitted as much under oath), (b) they cannot point to a SINGLE instance of the defendant actually copying anything or actually distributing anything to someone else, (c) it is impossible for any individual to do anything "continually", and (d) distributing is a term of art under 17 USC 106(3), the elements of which are not spelled out factually as they are required to be under Twombly. Accordingly I urge all practitioners who have a "making available" complaint to move to dismiss pursuant to Fed. R. Civ. P. 12(b)(6), or, if the time to do so has passed, to move for judgment on the pleadings pursuant to Fed. R. Civ. P. 12(c), on the basis of Twombly and Rodgriguez. If the RIAA counters by filing an amended complaint with the new "detecting an individual" boilerplate, that, too, is clearly the type of "formulaic" and implausible pleading that Twombly forbids, and should be dismissed as well. http://recordingindustryvspeople.blo...mend-that.html  NPR’s Long, Hard Look at the RIAA p2pnet news | RIAA News:- “I don’t think we’ve suddenly had a massive morality shift, where tens of millions of Americans who wouldn’t shoplift a CD in a store have suddenly lost their moral compass and are rampaging out there, eager to break the law.” Or ….. “There are tools, in terms of, uh, uh, authentication here, and, uh, uh, I’m not a technician so I’m, I’m, I really can’t go into that in great detail.” The first remark came from leading EFF (Electronic Frontier Foundation) lawyer Fred von Lohmann in a documentary on American Public Media’s Marketplace. The second was from RIAA (Recording Industry Association of America) spin-doctor-in-chief Mitch Bainwol, both of whom were interviewed for a three-part American Public Media Marketplace series which kicks off: The recording industry has gotten serious about illegal file sharing. In the last four years it has filed thousands of lawsuits. But, as Bob Moon reports in a special series, even those targeted by mistake, like Tanya Andersen, get no reprieve. It takes a long, hard - and commendably objective - look at Warner Music, EMI, Vivendi Universal and Sony BMG’s bitter and relentless assault on the men, women and children who keep the money rolling in and whom the Big 4 are calling criminals and thieves. But even as the major labels desperately try to sue them into once again becoming the compliant cash-cow ‘consumers’ of the physical 1970s, the technically intelligent customers of the 21st digital century are dangerously determined to exercise their rights to choose freely. Part I, No pause in music industry’s tough play, aired on Monday, Part II, Free? Illegal? … What’s the difference? Music biz’s future rests on key changes, was broadcast on Tuesday, and Part III, Music biz’s future rests on key changes, was heard yesterday afternoon, wrapping the three-part series. Featured, in addition to von Lohmann, are: » Tanya Andersen, the disabled Oregon mother who’s looking for class-action status in a case she wants to bring against the Big 4’s RIAA (Recording Industry Association of America) . » Lory Lybeck, Andersen’s lawyer, a deft hand who’s consistently challenging the Big 4 enforcement organisation’s legal teams » Ray Beckerman, the New York attorney who was one of the first to act for RIAA victims and who today runs Recording Industry vs The People, a blog caring detailed reports of cases, together with links to stories and commentaries covering them » Bainwol » Peter Jenner, the former Pink Floyd manager who currently represents an artists’ coalition in London » Felix Oberholtzer from the Harvard University Business School, who, with colleague Koleman Strumpf from the University of Kansas School of Business, first firmly gave the lie to corporate music industry claims that files shared equal sales lost. Their paper, The Effect of File Sharing on Record Sales: An Empirical Analysis, remains a milestone “It was challenging to try to sort through a lot of seemingly contradictory angles to all of this, coming from different directions, frankly,” the series presemnter, Bob Moon, told p2pnet shortly after the final segment aired. “One example is something we just didn’t end up with enough time to explain as we were heading into production,” he said, going on: As we know, the recording companies have now stipulated - and a judge has ruled “with prejudice” - that there was no case against her. It just adds yet another confusing layer if you try to explain that they’re now arguing their motion to have her countersuit thrown out, at least in part, on the idea that she really was an online pirate who should have had no expectation of privacy. It really raises the problem of how detailed can a story be before your listener starts losing track of everything. The answer to that is probably: as detailed as necessary, and that’s exactly how it’s starting to be, thanks entirely to the Net which gives online citizen media and reporters the space and the freedom to be as verbose is they need to be. In Part I, No pause in music industry’s tough play —- Tanya Andersen relates how she reacted to a letter, “warning that she had breached undisclosed copyrights and owed hundreds of thousands of dollars” which she initially believed was a scam, “until she phoned someone at what the industry calls its “settlement support center’,” says Marketplace, going on: ANDERSEN: You know, I told them, “Look, take my computer. Look at that. I can prove to you I didn’t do this.” And he said, “What do you guys expect us to look at everyone’s computers that says they’re innocent?” The first lawyer she consulted offered some advice that turned her stomach: ANDERSEN: “Just let ‘em take a judgment against you and file bankruptcy.” And I told him, “Why should I have to do that? That’s not fair.” And he said, “I didn’t say it was fair. It’s how you have to deal with those people.” So it was back on the phone to the “settlement center,” where she says a support rep listened sympathetically. ANDERSEN: He ended up telling me, “Well, you can write a letter to my bosses, but no guarantee. Once they start a lawsuit, they just don’t back off.” LORY LYBECK: And that’s when her life went down the rabbit hole. That’s Lory Lybeck. Andersen’s lawyer: LYBECK: Lo and behold, somebody shows up at her door with a federal lawsuit, saying “We’re going to ruin you. We’re going to sue you for over a million dollars.” He bases that on the industry’s past demands for up to $750 per song. He says Andersen was accused of trading 1,046 music files. Lybeck responded with a counterclaim in the fall of 2005, and Andersen says after that things really got ugly. It was right around the time she moved to a new home, and her apartment manager got a call: ANDERSEN: He told them he couldn’t release my personal information. They told him that he would either give it to them or he was going to get in a lot of trouble. It terrified me. Come to find out, they were trying to serve Kylee. Her daughter, who was just 7 years old when the file-sharing supposedly happened. Andersen’s lawyer says he was able to confirm that call came from the recording industry’s law firm. What remains a mystery is something else that he says happened around the same time: LYBECK: Calls were made to Kylee’s elementary school, under the pretext of somebody calling saying they were Kylee’s grandmother, and was she there that day? I haven’t tracked that call directly back to the law firm, but it was most disturbing, especially since Tanya checked, and grandma made no such calls. The head of the Recording Industry Association of America refused to comment on any specific case, but Mitch Bainwol did tell us this. MITCH BAINWOL: I would remind you that folks, when they have a legal dispute, often can be creative with the way they portray the facts. In Part II, Free? Illegal? … What’s the difference? “I often run into musicians and artists who say, ‘Thank you for what you’re doing,” states Bainwol. ” ‘We know you take hits for this, but it’s about my future, it’s about my dream. And I know that our property has to be respected’.” Says Jenner: It’s the same way that when you see lots of civilians being killed in a war, you know that’s bad for your war. And I think it’s the same if you’re harming individuals randomly. No one disputes that millions around the world continue to engage in unauthorized sharing of music. But critics complain the industry is using desperation tactics that haven’t solved the problem and, they charge, are both legally and morally dubious. Say Beckerman: The RIAA doesn’t conduct an investigation to find out whether someone committed a copyright infringement. It conducts an investigation to find out who paid the bill for an Internet-access account. And that’s where their investigation should begin, but in their weak minds that’s where it ends. Lybeck picks up the thread: Parents are falsely accused of downloading music and are sued inappropriately for downloading music every day. MOON: Aren’t they responsible for what their kids do? LYBECK: No, the law certainly doesn’t support that, unless they’re benefitting from it in some way. When parents do decide to fight, he says, lawyers show no shame training their legal guns on the children. Lybeck points out the industry has sued kids as young as 12 — nevermind something the head of Warner Music, Edgar Bronfman, told an interviewer. LYBECK: He was being questioned as to whether his children had downloaded music, and he frankly admitted they had. “But don’t worry, I’ve had some very stern conversations with them, and they’re not going to do it anymore.” Which, out of fairness, a lot of parents would like to have that opportunity, rather than being pestered and abused and threatened with financial ruin with a federal lawsuit. The industry might actually be tempting youngsters, and even adult fans, to try out the very file-sharing sites it’s battled for years to shut down. You can hear this confusion as the head of the RIAA lays out his case for us. Initially, he argues flatly that “free” means “illegal.” BAINWOL: The reality is, almost everybody understands that the practice of taking copyrighted works for free is illegal. But what about when the industry is giving away its own free songs? . . . This summer, a deal was announced to flood file-sharing sites with 16 million free downloads, reportedly from the popular rapper Plies. Trouble is, fans were left guessing exactly which track would be legally free. And until the file is actually downloaded, there’s no way to be sure that it’s the “authorized” version that includes an embedded ad. Sprint pays for its logo to appear whenever the song is played. The label that’s reportedly offering these free songs is one of the same companies that’s been suing to discourage file sharing. Question the head of the RIAA on this haziness and — listen closely — Mitch Bainwol starts making subtle exceptions. BAINWOL: Teenagers today understand that if you get something for free, in all probability, unless it’s explicitly legal, it’s not. FRED VON LOHMANN: How’s the fan supposed to know? That’s Fred Von Lohmann of the Electronic Frontier Foundation. He complains the moving lines could lure unsuspecting fans into being sued. And it’s not just the file-sharing sites that leave him confused. Some online bulletin boards also offer free MP3 music files, seemingly with the industry’s blessing: VON LOHMANN: Promotional CDs get sent to these MP3 bloggers all the time, really encouraging people to post some stuff on the Internet, get some buzz going. There are some independent artists who take a much more open-minded view to file sharing. Many fans have no idea whether their favorite artist is on an independent label or on a major label. This is just an area of continuing confusion. We tried asking the industry’s top representative how the average law-abiding teenager — or even his own organization — might tell the difference between what’s legal and what’s not. But even Mitch Bainwol didn’t seem to know clearly: BAINWOL: There are tools, in terms of, uh, uh, authentication here, and, uh, uh, I’m not a technician so I’m, I’m, I really can’t go into that in great detail. I’d be happy to get you somebody who can. Check the press release http://investor.news.com/cnet?GUID=2...er&Ticker=ARTD announcing those free ad-supported downloads we mentioned and it simply says, “The tracks are indistinguishable from illegal, pirated content.” Despite this left-hand, right-hand confusion, and questions about his industry’s tactics, Bainwol told us he’s convinced the ongoing lawsuit campaign against music fans continues to be a valuable educational tool. In Part III, Music biz’s future rests on key changes, —- the recording industry’s “top lobbyist, Mitch Bainwol,” insists his organisation is trying to adapt and support the technologies fans have embraced, “even in the face of ridicule that it’s too little, too late”: Mitch Bainwol: We are seeking to monetize all sorts of distribution channels. I find it ironic when we do what critics want us to do, we get criticized for that. Online sales are steadily rising, and Bainwol sees that as a reason to keep on suing unauthorized file-sharing fans. He says that legal pressure helps give legitimate Internet sales what he calls “the traction they need.” He’s convinced history will record his industry’s tactics as pivotal. Bainwol: It took some pretty gutsy actions by the music industry and others to establish that, in fact, intellectual property is worthy of protection. ‘Cowardly’ might be a better word than ‘gutsy’, and meanwhile, Von Lohmann sums in an opinion Bainwol and the people who pay his salary will do well to consider deeply: I think 10 years from now, everyone will look back at this entire episode with shame. I can’t believe it ever got so bad and we were so unimaginative, unable to transition to a new model, that we actually started treating our customers - our fans - as the enemy. If nothing else, the series will sensitise people who may never have heard of the bizarre RIAA sue ‘em all marketing campaign to some of the issues. Each segment attracted the largest number of listeners as Marketplace aired them and this morning, all three were at the top of the online lists. Moon says flagship afternoon show Marketplace and the early Marketplace Morning Report are heard by an audience of more than 8.1 million unique listeners during the week, and on more than 330 public radio stations nationwide. The program is also distributed worldwide by American Forces Radio and also has the largest audience of any business program in the United States, on radio or television, says American Public Media. http://www.p2pnet.net/story/13371  User-News Sites Offer Diverse Stories, Some Questionable Sources Joe Garofoli During a week this summer when the mainstream press focused on the immigration debate in Congress and a failed terrorism plot in the United Kingdom, the most popular stories on news sites where the users rank their favorites, like San Francisco's Digg, was - aside from chatter about Apple's new iPhone - not dominated by any one news story. And that's part of their allure. The 24-hour news cycle doesn't exist on rapidly growing user-news sites like Digg, Del.icio.us or San Francisco-based Reddit. Neither do the small cabal of editors who decide what news readers and viewers should see on traditional print and broadcast outlets. Instead, the readers of these user-news sites collectively and continuously contribute to the creation of a digital "front page" of their favorite stories - pushing to prominence news that may get scant airing on traditional print, broadcast or cable outlets, where space and airtime is finite and, they say, risk-taking is more rare. This changing approach to news consumption is highlighted in a study released today by the Project for Excellence in Journalism, a Washington, D.C., think tank. It compared the stories on the above three leading user-news sites, along with Yahoo News' Most Recommended, Most Viewed and Most E-mailed stories, with the project's daily content audit of 48 print, cable, online, network TV and radio news outlets. The study, a snapshot of a week's worth of news consumption, shows the growing interdependence between traditional news outlets and online user-news sites. It also illustrates how the news looks a lot different when audience members pick what story they want to read or recommend, as opposed to a professional journalist. "The traditional news outlet wants to put a lot of gravitas on their front page. They want the readers to eat their spinach," said Kourosh Karimkhany, general manager of Wired Digital, which owns Reddit. Technology allows users to create their own news "agenda" from multiple online sources, rendering a traditional front page increasingly "irrelevant," he said. Instead, on these growing sites - Digg welcomed 19.5 million unique visitors last month - consumers rely on the "wisdom of crowds" (other readers) to figure out what are the top stories of the day. The study found that the news items on these sites are "more diverse, more transitory and often draw on a very different and perhaps controversial list of sources." It found that 40 percent of the stories on user-news sites originated on blogs and 24 percent came from mainstream sites like BBC News. Only 5 percent came from wire services. So the immigration debate never was a top-10 story on Digg or Del.icio.us during the week of June 24, the study's focus period. It appeared just once that week among the top stories on Reddit. "The best way to get a sense of trend among these sites is not to look at specific news events, but at broad topic areas such as politics, crime and foreign affairs," the study found. And the focus on user-news sites is a lot different than editor-chosen news sites. The study found roughly 40 percent of the stories on Digg and Del.icio.us were devoted to technology and science. Lifestyle stories were the second most popular on user-news sites. While the war in Iraq accounted for 10 percent of the stories from the nation's top mainstream news outlets, it was only 1 percent of the stories on the three user-news sites. At traditional outlets, the top-10 list of stories that week - topics like Iraq, the Supreme Court decisions and a major fire near Lake Tahoe - accounted for 51 percent of all the stories. "What it hints at is that the range of topics are broader and more varied (on user-news sites)," said Tom Rosenstiel, director of the Project for Excellence in Journalism. However, Rosenstiel said, it also shows that "more sources may or may not be completely dependable." On these user-news sites, items may be posted from a blog or other online source that doesn't come with the "assurance of a professional journalist saying, 'I made seven calls on this, and it's legitimate.' Or, 'It's a scam.' " And while traditional journalists often concentrate on ongoing coverage of the same issue, the variety of stories turning up on user-news sites may show that "maybe a lot of readers aren't as interested in those turn-of-the-screw type of stories," Rosenstiel said. But the study doesn't portend the end to traditional journalism, said Jay Adelson, CEO of Digg. On his site, its 2 million registered users submit and vote on content, "digging" the stories they prefer and "burying" those they don't. Stories with the most "diggs" go to the top of the page, creating a constantly evolving news source. "In the current form, it is a very symbiotic relationship" between user-news sites and traditional media, he said. "What this study shows is that the online news consumer consumes news differently." Instead of cuddling up to one newspaper or checking out the evening news, today's consumer is checking out 15 to 20 sources - from the New York Times and The Chronicle to ABC to a blog, said Reddit's Karimkhany. Indeed, many traditional news outlets mark their stories with one or more user-news icons, inviting their readers to "Digg" that story. "It's not so much that people are shunning news. I think people are reading more," said Karimkhany, a graduate of the Columbia School of Journalism and a former reporter for mainstream outlets like Reuters and Bloomberg News. "What Reddit does is much what a traditional newsroom does. Except that instead of having four or five men in their 40s and 50s decide what goes on the front page, thousands of people do." But while this changing environment has brought many more news outlets into the picture, it has also cut into revenues for traditional outlets - which traditionally have been the home of most investigative reporting, because they had the resources to do so. Said Adelson: "What I wonder about is what is going to happen to investigative journalism." Online resources Project for Excellence in Journalism study www.journalism.org User-news sites in the survey Digg.com Begun in December 2004, Digg's audience is more male (57 percent) than female. It is also had the youngest audience of the three user-news sites in the study, with just under half (47 percent) of all users between ages 18 and 34. The content is entirely user-driven. Registered users submit and vote on content, "digging" those they like and "burying" those they don't. The stories with the most "diggs" move to the top of the page, with the order changing almost every minute. Del.icio.us Founded in late 2003, Del.icio.us was acquired by Yahoo in December 2005. It has more female (55 percent) users than male (45 percent) users. It also skews the oldest, with the lowest percentage (35) of users under 35. Del.icio.us is also 100 percent user-driven, but works a little differently than Digg. Del.icio.us is a social "bookmarking" Web site, which lets users "tag" content they find most interesting. So when users find a piece of content (or an entire Web site) that they want to share - whether they find it on Del.icio.us or on an outside news outlet - they "tag" it and add a list of keywords to describe the story. Reddit.com Founded in 2005 and later acquired by Conde Nast Publications last October, it is the newest of the three user-news sites. It had the highest percentage (64) of men and almost as many users (45 percent) 18 to 34 as Digg did during the week the study conducted its research. Its content selection is based on user submissions followed by "up" or "down" votes. Next to each of the 25 stories on Reddit's home page there is an up and a down arrow for users to vote for or against the content. Stories with the most "up" votes rise to the top. Source: Project for Excellence in Journalism http://sfgate.com/cgi-bin/article.cg.../MNPDS3RE6.DTL  Does Social Media Make You Dumb? Nick Gonzalez The “Mainstream Media” has had somewhat of an antagonistic relationship with “New Media”. Journalists have bemoaned blogging on several occasions, stating simply that “Journalism requires journalists”. Once again journalists are gracing us with another study linking the success of the social news sites to the downfall of society. The study, conducted by the Project for Excellence in Journalism (PEJ), compared the mainstream media’s headlines for one week against those of a host of user-news sites. Specifically: “PEJ took a snapshot of coverage from the week of June 24 to June 29, 2007, on three sites that offer user-driven news agendas: Digg, Del.icio.us and Reddit. In addition, the Project studied Yahoo News, an outlet that offers an editor-based news page and three different lists of user-ranked news: Most Recommended, Most Viewed, and Most Emailed. These sites were then compared with the news agenda found in the 48 mainstream news outlets contained in PEJ’s News Coverage Index.” The comparison looked at the top stories (by percentage) from their news index compared to the top headlines (by percentage) for the social sites. The study found that while the mainstream media talked about important issues like immigration (10%) and Iraq (6%), the only story gaining traction on social news sites was the iPhone. No surprise there. The study does concede that these user generated newsfeeds may not mirror the important news of the day because they may serve has an auxiliary source. However, it ignores the sheer volume of news that passes across their front pages. While mainstream news sites have a limited staff of journalists and real estate to highlight the days news, Digg and its cohorts can link to these stories with plenty of room for LOL Cats photos. For example, Putin’s dissolution of the Russian government made the top 10 of Digg today. So did the iPhone unlock. Moreover, the study of social sites reveals what users are actually reading, whereas the mainstream news statistics point only at what they’re writing. Much of that “hard-hitting” journalism may not be getting the readership the coverage suggests. Where PEJ sees this as a clean stream of news, I see an echo chamber. Similar to when the music industry went online, users are no longer forced to buy in a bundle. Instead they can select the stories/tracks that appeal to them without subsidizing the content they don’t want. http://www.techcrunch.com/2007/09/12...make-you-dumb/  Times to Stop Charging for Parts of Its Web Site Richard Pérez-Peña The New York Times will stop charging for access to parts of its Web site, effective at midnight tonight. The move comes two years to the day after The Times began the subscription program, TimesSelect, which has charged $49.95 a year, or $7.95 a month, for online access to the work of its columnists and to the newspaper’s archives. TimesSelect has been free to print subscribers to The Times and to some students and educators. In addition to opening the entire site to all readers, The Times will also make available its archives from 1987 to the present without charge, as well as those from 1851 to 1922, which are in the public domain. There will be charges for some material from the period 1923 to 1986, and some will be free. The Times said the project had met expectations, drawing 227,000 paying subscribers — out of 787,000 over all — and generating about $10 million a year in revenue. “But our projections for growth on that paid subscriber base were low, compared to the growth of online advertising,” said Vivian L. Schiller, senior vice president and general manager of the site, NYTimes.com. What changed, The Times said, was that many more readers started coming to the site from search engines and links on other sites instead of coming directly to NYtimes.com. These indirect readers, unable to get access to articles behind the pay wall and less likely to pay subscription fees than the more loyal direct users, were seen as opportunities for more page views and increased advertising revenue. “What wasn’t anticipated was the explosion in how much of our traffic would be generated by Google, by Yahoo and some others,” Ms. Schiller said. The Times’s site has about 13 million unique visitors each month, according to Nielsen/NetRatings, far more than any other newspaper site. Ms. Schiller would not say how much increased Web traffic the paper expects by eliminating the charges, or how much additional ad revenue the move was expected to generate. Those who have paid in advance for access to TimesSelect will be reimbursed on a prorated basis. Colby Atwood, president of Borrell Associates, a media research firm, said that there have always been reasons to question the pay model for news sites, and that doubts have grown along with Web traffic and online ad revenue. “The business model for advertising revenue, versus subscriber revenue, is so much more attractive,” he said. “The hybrid model has some potential, but in the long run, the advertising side will dominate.” In addition, he said, The Times has been especially effective at using information it collects about its online readers to aim ads specifically to them, increasing their value to advertisers. Many readers lamented their loss of access to the work of the 23 news and opinion columnists of The Times — as did some of the columnists themselves. Some of those writers have such ardent followings that even with access restricted, their work often appeared on the lists of the most e-mailed articles. Experts say that opinion columns are unlikely to generate much ad revenue, but that they can drive a lot of reader traffic to other, more lucrative parts of The Times site, like topic pages devoted to health and technology. The Wall Street Journal, published by Dow Jones & Company, is the only major newspaper in the country to charge for access to most of its Web site, which it began doing in 1996. The Journal has nearly one million paying online readers, generating about $65 million in revenue. Dow Jones and the company that is about to take it over, the News Corporation, are discussing whether to continue that practice, according to people briefed on those talks. Rupert Murdoch, the News Corporation chairman, has talked of the possibility of making access to The Journal free online. The Financial Times charges for access to selected material online, much as The New York Times has. The Los Angeles Times tried that model in 2005, charging for access to its arts section, but quickly dropped it after experiencing a sharp decline in Web traffic. http://www.nytimes.com/2007/09/18/bu...a/18times.html  AOL Moving Headquarters to New York Louise Story AOL will move its headquarters from its sprawling campus in Dulles, Va., to New York next spring as the online company tries to retool itself as an advertising company that competes with the likes of Google, Yahoo and Microsoft. The move, announced today, speaks to how much the online world has changed around AOL, which became a high-flying Internet stock in the 1990s by providing dial-up Internet connections in millions of American households. AOL, which is part of Time Warner, will base all of its advertising sales out of New York through a group the company is calling Platform A. That group will be lead by Curtis G. Viebranz, the former chief executive of Tacoda, an advertising targeting company that AOL acquired in July for a reported $275 million. AOL also said in a memo to company employees today that Mike Kelly, president of AOL Media Networks and a longtime Time Warner executive, will leave AOL after the transition. He was brought in to head ad sales at AOL in 2004. As with most of AOL’s recent history, the move to New York symbolizes a shift away from the company’s roots, and analysts said it could portend coming job layoffs of some of the company’s 4,000 employees based in northern Virginia. A year ago, executives announced the company would make its Web portal and e-mail services free and generate money through advertising rather than by providing those services and Internet connections to subscribers. Since then, AOL has acquired a string of online advertising technology companies, including Tacoda, and revamped its Web content to try to attract more visitors. “AOL’s leadership in this space was theirs to lose years ago, and they did lose it,” said Shar VanBoskirk, an analyst at Forrester Research. “This move is a great one, but my concern is: is it too little, too late?” AOL executives put a good face on the move, which is certain to be disruptive in Virginia. AOL executives did not say how many employees would move from Virginia to the new 152,000-square-foot office, leased at 770 Broadway, just south of Union Square. Time Warner’s corporate headquarters is about three miles uptown, at Columbus Circle. “If you’re going to be in the advertising business, you have to be in New York because that’s where all the agencies are, that’s where all of the media money is controlled, on Madison Avenue,” said Randy Falco, chairman and chief executive of AOL. In an interview, AOL executives explained that they see the company’s advertising revenues coming more in the future not only from its branded Web site but also from thousands of publishers’ sites across the Internet that let AOL sell ads on their pages. AOL will use targeting technology from Tacoda to capture data about consumers’ Web surfing and translate that information into a road map for delivering different ads to different people each time they log on. AOL will also use that data to sell ads in its Advertising.com unit, which delivers ads to its own network of outside publisher sites. “There’s really been a shift in advertising to the network business,” said Ron Grant, AOL’s chief operating officer. “Portals aren’t really big enough to meet the needs of advertisers.” http://www.nytimes.com/2007/09/17/te...7cnd-adco.html  MySpace to Discuss Latest Effort to Customize Ads for Members Brad Stone Members of the booming social network Web sites treat their individual profile pages as a creative canvas for personal expression. The social networking companies see those pages as a lush target for advertisers — if only they could customize the ads. Although Internet companies have talked about specifically aiming their ads since the inception of the Web, so far advertising on social networks has been characterized by mass-marketed pitches for mortgages and online dating sites. But MySpace, the Web’s largest social network and one of the most trafficked sites on the Internet, says that after experimenting with technology over the last six months it can tailor ads to the personal information that its 110 million active users leave on their profile pages. Executives at Fox Interactive Media, the News Corporation unit that owns MySpace, will begin speaking about the results of that program this week. They say the tailoring technology has improved the likelihood that members will click on an ad by 80 percent on average. “We are blessed with a phenomenal amount of information about the likes, dislikes and life’s passions of our users,” said Peter Levinsohn, president of Fox Interactive Media, who will talk about the program at an address to investors and analysts at a Merrill Lynch conference in Los Angeles on Tuesday. “We have an opportunity to provide advertisers with a completely new paradigm.” MySpace’s rival, Facebook, also says it is experimenting with ad customization with the help of Microsoft, which signed with the up-and-coming social network last year to provide display ads on the service. To the consternation of privacy advocates, who say Internet users are unaware of such activity, the social networks regard these detail-stocked profile pages as a kind of “digital gold,” as one Fox executive put it last year. The companies hope that customizing ads to their members’ stated enthusiasms will improve the effectiveness of the ads and recruit new advertisers who want to pitch their messages to refined slices of the online audience. Fox executives also hope the technology can help MySpace recapture some of the momentum and attention that has recently gone to Facebook. Richard Greenfield, the managing director of Pali Research, predicts that MySpace’s fledgling program will help increase MySpace’s current revenue to $70 million a month from $40 million a month by next year. “This is a critical evolution of the MySpace business model envisioned from the day News Corporation bought it,” Mr. Greenfield said. A 100-employee team inside the Fox Interactive Media offices in Beverly Hills, called the “monetization technology group,” has designed computer algorithms to scour MySpace pages. In the first phase of the program, which the company calls “interest-based targeting,” the algorithms assigned members to one of 10 categories that represents their primary interest, like sports, fashion, finance, video games, autos and health. The algorithms make their judgments partly on certain keywords in the profile. A member might be obvious by describing himself as a financial information enthusiast, for example. But more than likely the clues are more subtle. He might qualify for that category by listing Donald Trump as a hero, Fortune magazine as a favorite publication or “Wall Street” as a favorite movie. The system also looks at the groups members belong to, who their friends are, their age and gender, and what ads they have responded to in the past. “Our targeting is a balance of what users say, what they do and what they say they do,” said Adam Bain, the chief technology officer at Fox Interactive. MySpace evidently does not completely trust the technology. Every two weeks, 200 temporary workers, which the company calls “relevance testers,” come to Fox Interactive’s offices to manually check member profiles against the categories they have been assigned to. The company said that several national advertisers are trying out the service, though they declined to name them. Fox Interactive executives say that some kinds of ads benefited more than others. Clicks on tailored auto ads more than doubled and clicks on music ads jumped by 70 percent. For the last two months, Fox Interactive has also experimented with the second phase of its targeting program, called “hyper targeting,” in which it further divides the 10 enthusiast categories into hundreds of subcategories. For example, sports fans are divided into subgroups like basketball, college football and skiing, while film enthusiasts are further classified by their interest in genres like comedies, dramas and independent films, and even particular actors and actresses. For now, Fox’s advertising sales representatives are selling the new kinds of ad abilities. In November, according to Michael Barrett, Fox Interactive Media’s chief revenue officer, the company will set up an automated online system to allow smaller companies to aim at MySpace users with their ads without ever talking to a human being at Fox. A punk band performing in Seattle, for example, could publicize a performance by looking up all the people on MySpace who live in that area who are punk fans. MySpace also plans to give its advertisers information about what kind of people its ads have attracted. “We want them to leave knowing more about their audience then when they came into the door,” Arnie Gullov-Singh, a senior director at Fox Interactive. That is precisely the goal that worries some privacy advocates. They argue that users of social networks like MySpace and Facebook are not aware they are being monitored and that current ad-targeting is only the first step in what has become a huge arms race to collect revealing data on Internet users. “People should be able to congregate online with their friends without thinking that big brother, whether it is Rupert Murdoch or Mark Zuckerberg, are stealthily peering in,” said Jeff Chester, executive director at the Center for Digital Democracy in Washington. His organization will ask the Federal Trade Commission, during a planned hearing on Internet privacy in November, to investigate social networks for unfair and deceptive practices, he said. MySpace and Facebook executives argue that they are harming no one. They say that they are using information their members make publicly available, and contrast their ad targeting with efforts by Yahoo, America Online and Microsoft, whose advertising technologies follow people around the Web and try to deduce what they are interested in based on what sites they are looking at. Fox executives also say they are planning on letting users opt-out of the ad-targeting program on MySpace, though it means those members will see fewer relevant ads. At least one MySpace member has no problems with the new technology. Mark Gong, a 26-year-old photojournalist from Washington, runs the 3,000-member Wanderlust group on MySpace and on his profile expresses an interest for foreign films like “Lost in Translation” and “The Spanish Apartment.” Not surprisingly, that has defined him as a prime target for travel ads on MySpace from companies like ShermansTravel.com, a travel deal site. “I’m not opposed to advertising,” Mr. Gong said. “They have got to make money.” But he also says he hopes MySpace spends the extra cash on making the site more reliable and fending off the Facebook threat. He says many members of his group have flocked to Facebook in the last two months and that even he is logging into Facebook more often. “Everybody I know is switching to Facebook,” he said. “MySpace has its work cut out for it.” http://www.nytimes.com/2007/09/18/te...18myspace.html  Review: MySpace Phenom Colbie Caillat Sells Out the Fillmore Aidin Vaziri MySpace has proven itself a great place to meet perverts and catch up with people you hated in high school, but its value as a music-marketing tool remains largely up in the air. Yes, Lily Allen and the Arctic Monkeys supposedly sprang to life thanks to the behemoth social-networking site, but the fact that 98 percent of the people reading this right now just saw those names for the first time kind of negates their success. Colbie Caillat may prove to be an exception. The 22-year-old Malibu native was working at a tanning salon last year when a friend helped her post a couple songs, including "Bubbly" and "Tailor Made," on her MySpace page, where she quickly racked up more than 10 million plays and acquired nearly 200,000 new friends. In July, Caillat's first full-length album, "Coco" (Universal), was released on an old-fashioned record label, making a Top 5 premiere on the Billboard charts. While Kanye West and 50 Cent were battling it out on the cover of Rolling Stone and at the MTV Video Music Awards last week, Caillat quietly slipped ahead of both to top the iTunes download chart. Of course, it may all come down to the fact that she looks just like Rachel from "Friends" on the album cover. But playing a sold-out show at the Fillmore on Saturday sure seemed like a good place to get a running start on a career. Wearing a simple brown dress and low pump sandals, Caillat looked as if she had just strolled into the venue after a shopping trip a few blocks up Fillmore Street. Meanwhile, the only sizable group of guys hanging out in the lobby before the show ended up being her backing band. Their casual confidence probably had a lot to do with her voice, an incredibly earthy and rich instrument that's impossible to dismiss. Naturally, the producers of "American Idol" passed on it, not once but repeatedly. Caillat claims that her interest in music ignited at age 11 after hearing Lauryn Hill's take on "Killing Me Softly." But her education started much earlier - her father Ken Caillat ran his own label and co-produced Fleetwood Mac's "Rumors" and "Tusk." His professionalism clearly made a bigger impression than Hill's raw soul. The songs on "Coco" deal mostly in familiar emotional hang-ups, sentiments that are so ordinary that everyone in the room could latch onto them: Love hurts; pregnant women glow; dreams are dreamy. Her love-struck hit "Bubbly" is an unmistakable descendant of Jack Johnson's "Bubble Toes," built around breezy acoustic guitars, shuffling rhythms and an easy-to-swallow seaside melody. Whether about downing alcohol to overcome depression ("Midnight Bottle") or grappling with a relationship that's falling apart ("Battle"), Caillat's songs all sound like different strains of the same thing, impossible to tell apart. Tellingly, Caillat's fans never stopped chattering during her set, even as they paused to sing along to their favorite lines from the album. When she talked, Caillat came across just like them, a casual acquaintance from the dorm room down the hall: "This is a song about wishing someone felt the same way as you." When she moved, she didn't dance so much as sway with the people at the foot of the stage. But the rapturous reception she got from the girls in the crowd - some possibly just excited to be attending their first concert - confirmed her emergence as a real-life Internet phenomenon. Even when she bravely threw out "Bubbly" before the encore and then struggled to fill the hourlong set with what sounded like a bloodless cover of Bob Marley's "One Drop" ("This song has an island beat, reggae feel to it," she said), they loudly cheered her on just as they would any other friend in their Top 8. To see a video clip of Colbie Caillat performing at the Knitting Factory, go to www.youtube.com/watch?v=_hvpX3QvzLg http://sfgate.com/cgi-bin/article.cg.../DDEIS7E2K.DTL  Kenny Chesney Charts Every Song on New Album DirtySouthMouth Every single song from Kenny Chesney's brand new album, Just Who I Am: Poets & Pirates, has charted, according to the Nielsen numbers. At the same time, the first two actual singles from the album, "Never Wanted Nothing More" and "Don't Blink," are both in the top 15 of Billboard's country singles chart. With the rest of the tracks on the album, Kenny also holds the No. 37, 43, 44, 53, 55, 56, 58, 65 and 73 spots on the chart. Someone is making bank. On top of all of this, Kenny also holds the No. 1 spot, as he wrote Rascal Flatts' current No. 1 single, "Take Me There." Pretty funny when you consider the fact that he didn't land a single writing credit on Just Who I Am. Maybe he didn't beat Kanye West or 50 Cent on the Billboard 200, but dude's certainly got something to shout about. In other Kenny Chesney news, the Detroit Free Press reported today that two police officers from the area have been accused of stealing cowboy hats from a KC concert. The two officers, Gregg Richard Anderson and Frank Cazazos where charged with larceny between $200-1000. Both men were fired from the city of Wayne Police Department. http://www.shoutmouth.com/index.php/news/Nas_Challenges_Bill_O'Reilly_to_a_Debate  Making a Career After a Monster Hit Ben Sisario Many songwriters would kill for the predicament that James Blunt is in: famous for one song, and only one. That hit, “You’re Beautiful,” is a dewy ballad about catching a glimpse of a former girlfriend in the subway. Critics loathed it, but it reached No. 1 from Latvia to Latin America and helped Mr. Blunt’s debut album, “Back to Bedlam,” sell 11 million copies around the world. As last year’s combination wedding song, television soundtrack song and supermarket background music, “You’re Beautiful” was more than popular — it was ubiquitous. This kind of success can be an albatross for a new artist, and even Mr. Blunt, who yesterday released his second album, “All the Lost Souls” (Custard/Atlantic), and has sold out shows at the Highline Ballroom in Chelsea tonight and tomorrow night, doubts that he can ever score such a hit again. “I sold a hell of a lot the first album,” he said recently over steak frites at a trendy meatpacking district restaurant, where every female head seemed to turn as he walked in. “I can’t possibly compete with that on the second album. It’s impossible to do.” Mr. Blunt, 33, a throwback to the 1970s soft-rock golden age, says he is uncomfortable with the marketing of one song at the expense of all others. But given the industry’s sales slump, it has become even more crucial for record labels to promote singles relentlessly and to gain maximum exposure by licensing them for television shows, commercials and ringtones. All of which poses a quandary for Mr. Blunt’s label in its post-“You’re Beautiful” campaign: Is it better to play it slow and steady to groom Mr. Blunt as a career artist or to shoot for another smash? That first smash came relatively easily. “Back to Bedlam,” released in Mr. Blunt’s native Britain in 2004 and in the United States the next year, had a whiff of Coldplay in its big, swelling refrains and earnest falsetto vocals. And Mr. Blunt had stubbly good looks and an intriguing back story. A former British Army officer in Kosovo who was once one of Queen Elizabeth’s personal guards, he was picked by the songwriter and producer Linda Perry (Christina Aguilera, Pink) to be the first artist on her label, Custard. In Britain two singles preceded “You’re Beautiful.” But Atlantic Records, which issues Mr. Blunt’s music in America in partnership with Custard, released that song first. Though it stalled on the charts at the beginning, a flurry of commercial licensing made it inescapable on television. It was used in a Sprint ad campaign, in prime-time dramas like “Smallville” and “ER,” on daytime soaps, in promo spots for “Extreme Home Makeover” and even in the 2006 Winter Olympics. That exposure helped its popularity on radio, and after seven months it hit No. 1. To date the album has sold 2.6 million copies in the United States. As Ms. Perry sees it, all that licensing backfired: “You’re Beautiful” became as hated as it was loved. “When you have a really big song and you want to see some legs on a record,” she said, “you don’t start putting that song in commercials and on TV shows and keep oversaturating it. Because that’s when people get sick of it.” The backlash was harsh. Mr. Blunt became a tabloid regular — his tendency to be photographed alongside scantily clad young women didn’t help — and was ruthlessly jeered in the music press. (His album was named worst of the year by the British music magazine NME.) And in a sign of true notoriety, his name entered the lexicon of Cockney rhyming slang as a particularly crude insult. Mr. Blunt professes a cool equanimity about his treatment by the news media, but doesn’t deny his playboy reputation. During the interview he received a text message from his friend and fellow bon vivant Kid Rock. (“We spent some good times in Cannes this year,” Mr. Blunt said.) And he lives on the Spanish island of Ibiza, famous for its huge, wild dance clubs. “We’d have dinner at midnight,” he said of his life there, “and I’d be thinking about going to a bar at 2 in the morning. And then we’d think about hitting a club between 3:30 and 4, and the club would close at 8. I’d come back at 9 in the morning and I’d write songs.” If “All the Lost Souls” is any indication, the popular ridicule has had little effect on him. It sticks closely to the formula that made “Back to Bedlam” such a big seller: gentle guitars and piano, breathy vocals, melodramatic sweep, a slight tinge of morbidity. “The person who has to live with this album is me,” he said. “It doesn’t matter how far up the charts it gets. It doesn’t matter if it sells. I really like it.” But his business representatives differ on the promotional plan. Ms. Perry says that the gradual roll-out in Europe saved him from being considered a one-hit-wonder there. Mr. Blunt made an appeal to Lyor Cohen, the domestic chairman of Atlantic’s parent company, the Warner Music Group, asking him to avoid pushing any single too hard and to emphasize the new album as a whole. Mr. Cohen was sympathetic, but only to a point. “Ultimately we’re not as romantic,” he said. “You need to get the impressions at radio to bring attention to it.” The entire album can be streamed free, or purchased for $9.99, on Mr. Blunt’s MySpace page. And Mr. Blunt is not above shooting for big hits. One of the stronger new songs, “Carry You Home,” was written with Max Martin, the Swedish pop maestro behind blockbusters by the Backstreet Boys, Britney Spears and Kelly Clarkson. Mr. Cohen said fears of piracy kept him from sending out the songs on “All the Lost Souls” for licensing in advance of the album’s release. But now that the album is out, the saturation can begin. “We will license these records, in movies, TV and commercials,” he said. “Trust me, you will hear these records.” http://nytimes.com/2007/09/19/arts/m...blun.html?8dpc  Q & A with Trent Reznor of Nine Inch Nails Trent Reznor of Nine Inch Nails lets rip at ignorant record companies to NEALA JOHNSON From May ON stage at the Metro on Monday night, it seemed you're enjoying being a rock star again. True? It's funny you'd say that 'cos that was not one of my favourite shows. It went downhill at one point. Yeah. I enjoy playing these days. I try to make the most of it and sometimes it's great fun and sometimes, like Monday night when it was crippled with technical problems, it made it not fun. I couldn't hear what was going on, s--- was breaking . . . Fools in the crowd were yelling . . . Yeah, mixed feelings about that. I mean, if you want me to go off on a tangent . . . I'm kind of in a weird space right now. I'm not real centred. We've been touring for a long time. I went from the record right into the tour, nine weeks in Europe in winter, which I don't recommend in any circumstance for anybody. I'm moving. There's some stuff in my personal life that's up. It must be an odd time then to have a new album, Year Zero, out? It's a very odd time to be a musician on a major label, because there's so much resentment towards the record industry that it's hard to position yourself in a place with the fans where you don't look like a greedy asshole. But at the same time, when our record came out I was disappointed at the number of people that actually bought it. If this had been 10 years ago I would think "Well, not that many people are into it. OK, that kinda sucks. Yeah I could point fingers but the blame would be with me, maybe I'm not relevant". But on this record, I know people have it and I know it's on everybody's iPods, but the climate is such that people don't buy it because it's easier to steal it. You're a bit of a computer geek. You must have been there, too? Oh, I understand that -- I steal music too, I'm not gonna say I don't. But it's tough not to resent people for doing it when you're the guy making the music, that would like to reap a benefit from that. On the other hand, you got record labels that are doing everything they can to piss people off and rip them off. I created a little issue down here because the first thing I did when I got to Sydney is I walk into HMV, the week the record's out, and I see it on the rack with a bunch of other releases. And every release I see: $21.99, $22.99, $24.99. And ours doesn't have a sticker on it. I look close and 'Oh, it's $34.99'. So I walk over to see our live DVD Beside You in Time, and I see that it's also priced six, seven, eight dollars more than every other disc on there. And I can't figure out why that would be. Did you have a word to anyone? Well, in Brisbane I end up meeting and greeting some record label people, who are pleasant enough, and one of them is a sales guy, so I say "Why is this the case?" He goes "Because your packaging is a lot more expensive". I know how much the packaging costs -- it costs me, not them, it costs me 83 cents more to have a CD with the colour-changing ink on it. I'm taking the hit on that, not them. So I said "Well, it doesn't cost $10 more". "Ah, well, you're right, it doesn't. Basically it's because we know you've got a core audience that's gonna buy whatever we put out, so we can charge more for that. It's the pop stuff we have to discount to get people to buy it. True fans will pay whatever". And I just said "That's the most insulting thing I've heard. I've garnered a core audience that you feel it's OK to rip off? F--- you'. That's also why you don't see any label people here, 'cos I said 'F--- you people. Stay out of my f---ing show. If you wanna come, pay the ticket like anyone else. F--- you guys". They're thieves. I don't blame people for stealing music if this is the kind of s--- that they pull off. Where does that extra $10 on your album go? That money's not going into my pocket, I can promise you that. It's just these guys who have f---ed themselves out of a job essentially, that now take it out on ripping off the public. I've got a battle where I'm trying to put out quality material that matters and I've got fans that feel it's their right to steal it and I've got a company that's so bureaucratic and clumsy and ignorant and behind the times they don't know what to do, so they rip the people off. Given all that, do you have any idea how to approach the release of your next album? I've have one record left that I owe a major label, then I will never be seen in a situation like this again. If I could do what I want right now, I would put out my next album, you could download it from my site at as high a bit-rate as you want, pay $4 through PayPal. Come see the show and buy a T-shirt if you like it. I would put out a nicely packaged merchandise piece, if you want to own a physical thing. And it would come out the day that it's done in the studio, not this "Let's wait three months" bulls---. When your US label, Interscope, discovered the web-based alternate reality game (ARG) you'd built around Year Zero, were they happy for the free marketing or angry you hadn't let them in on it? I chose to do this on my own, at great financial expense to myself, because I knew they wouldn't understand what it is, for one. And secondly, I didn't want it coming from a place of marketing, I wanted it coming from a place that was pure to the project. It's a way to present the story and the backdrop, something I would be excited to find as a fan. I knew the minute I talked to someone at the record label about it, they would be looking at it in terms of "How can we tie this in with a mobile provider?" That's what they do. If something lent itself to that, OK, I'm not opposed to the idea of not losing a lot of money (laughs). But it would only be if it made sense. I've had to position myself as the irrational, stubborn, crazy artist. At the end of the day, I'm not out to sabotage my career, but quality matters, and integrity matters. Jumping through any hoop or taking advantage of any desperate situation that comes up just to sell a product is harmful. It is. Is the Year Zero ARG something labels will copy now? Well, their response, when they saw that it did catch on like wildfire, was "Look how smart we are the way we marketed this record". That's the feedback I've gotten -- other artists who've met with that label ask 'em about it: "Yeah, you like what we did for Trent? Look what we did for Trent". They've then gone on to try to buy the company that did it to apply it to all their other acts. So, glad I could help them out. I'm sure they still don't understand what it is that we did or why it worked. But I will look forward to the Black Eyed Peas ARG, that should be amazing. Year Zero (Universal) out now. http://www.news.com.au/heraldsun/sto...006024,00.html  Catching Up With The Latest Pop Songs TomZ Between radio, TV and the Internet, there's a ton of new music coming out these days. Unless you're paying constant attention, chances are some of it has slipped under your radar. For all you pop music fans with no time on your hands, I've compiled some of the latest pop hits to help keep you up-to-date. And for those of you who despise pop music, well, I've tried to make fun of the songs, too. Hopefully there's a little something for everyone. The Hits Timbaland f/ Keri Hilson "The Way I Are" You often hear about recluses, a.k.a. people who don't go out in public. Generally this classification is used for people of generations past, like famous reclusive author J.D. Salinger, or for psychos like the Unabomber. But these are the extreme cases. What really makes a person a recluse? I'm gonna throw this out there, and you can either take it or throw it right back: If you have never heard this song, not even once, then I would say that you are officially a recluse. Pink "Who Knew" Pink made a video about a carnival and didn't include fried dough, people with missing teeth, or a shirt that says "The Man (Up Arrow), The Legend (Down Arrow)." What's next, a video about baseball that doesn't include bats? Kat DeLuna "Whine Up" This is probably my favorite song about whining up. Kat of the Moon deserves a lot of credit for her breakthrough summer. The Up-and-Comers Backstreet Boys "Inconsolable" When this song came out I was bracing myself for a billion lame "Backstreet's Back" jokes from every media outlet in the country. It hasn't happened. I'm both shocked and proud. Good work, America. Nickelback "Rockstar" Earlier this year, the Shop Boyz had a hit rap song called "Party Like a Rockstar." R. Kelly's latest album has a song called "Rock Star." Hannah Montana, Prima J, Everclear, Ja Rule, N.E.R.D. and Yellowcard have all released songs with "Rock Star" in the title, as have several others. The point? Two things, actually. First off, we as a society need to get together and decide whether Rockstar is one word or two. I'm voting for one word, and here's why. Two words ("Rock Star") implies that you are both play rock, and are a star. This wouldn't apply to rappers or pop stars, even though some of them are just as deserving of the title. On the other hand, the singular "Rockstar" takes on a meaning all its own. What makes someone a Rockstar? Well, that's a discussion for another time. But regardless, in my opinion, the phrase "Rock Star" focuses more on the rock, while "Rockstar" focuses more on the star. The second issue is -- and all you young artists listen up -- that the word "Rockstar" is ridiculously overused. Once that girl from "Real World Denver" started using the phrase constantly, it should have been banned for at least 5 years. Since the government won't step in, I'm telling you. No more calling yourself a "Rockstar" (or a "Rock Star") until 2012. If you do, we will automatically assume that you aren't a Rockstar. If you are a repeat offender, we will be forced to assume you suck. You can refer to others as Rockstars, just not yourself. In 2012, you can use the phrase again, but only in moderation. In the meantime, feel free to start popularizing the term "Rapstar." (I can't believe I get paid to think about stuff like this.) Maroon 5 "Wake Up Call" The girl in this video looks like a sluttier version of Anne Hathaway, which is funny, because I'm pretty sure Adam Levine is wearing Prada. I actually like this song, which means it'll never be big (historically speaking, my approval of a song is equivalent to the Kiss of Death). Plies f/ T-Pain "Shawty" On the flip side, I can't stand this song, so you know it'll be a huge hit. Does T-Pain have a clause in his contract that says any song he's involved with has to be about strippers or shawty's? And is "Shawty" the lyrical compliment of "Rockstar?" Will "Pimps "& Ho's" parties be replaced by "Rockstars & Shawties" parties? Vanessa Carlton "Nolita Fairytale" At first I thought "Nolita" referred to a young girl who wasn't a slut. Like, it was the 2007 equivalent of a "Hollaback Girl." I ain't no Lolita... I'm a NO-Lita! Turns out it's a neighborhood in New York City. Oh well. The Brand New Fall Out Boy "I'm Like A Lawyer With The Way I'm Always Trying To Get You Off (Me & You)" Great title. Sadly, the director of this video committed one of the cardinal sins of video-making. Never, EVER stop the song in the middle of the video, unless your name is Hype Williams (and even then, try to avoid it). You are not making a movie. You are making a 4-minute visual clip to entertain our eyes and counteract our ADD while we listen to a song. A video should be an accompaniment to a song. It shouldn't override the song. This song will be a massive, massive hit.* All they needed to do was show the band playing in some abandoned warehouse with the singer looking out a window next to a candlelit box of letters from a mysterious ex-girlfriend before posing on a mountaintop, like every other rock video, and they would've been fine. Instead, we've got a drum circle breakdown. Too bad. *See Maroon 5 for more info on this prediction Kanye West f/ T-Pain "Good Life" Welcome to the Good Life, where we sip champagne and wear pink sweaters! I can't say enough about Kanye's new album and this song in particular. T-Pain even broke his contract for this one. This is my pick of the week, although I'm not sure what that means. Gwen Stefani f/ Damian Marley "Now That You Got It" One of the main reasons I got hired at Shoutmouth was because of an article I had written about Gwen's song "Hollaback Girl." The whole point of the article was that the song was incredibly awful, and yet I couldn't help but love it. I compared it to a car that went over 100,000 miles and was back at zero; it was so terrible that it was amazing. I feel the same way about this song, to a slightly lesser degree. Embrace it now or be annoyed for the next 6 months. Token Rock Pick Finger Eleven "Falling On" A great rock song with crossover potential. Token Indie Pick Rilo Kiley "Moneymaker" A lot is made over singer Jenny Lewis' looks, but the band is actually pretty decent too. Even if this chorus does sound a little like "Jukebox Hero." The Classic Rock Song of the Week The Eagles "The Long Run" Videos from the ‘70s are funny. The Classic Hip Hop Song of the Week Wreckx-N-Effect "Rumpshaker" In 2022, will people hold the same admiration for MIMS' "This Is Why I'm Hot" as people my age hold for Wreckx-N-Effect? I think it could happen, and that's scary. And finally, The Classic Pop Song of the Week Britney Spears "I'm a Slave 4 U" After seeing Britney's VMA disaster, I feel like we all need to revisit the glory days. Also, you may have heard the rumors that Britney will be apologizing for her VMA performance during the Emmy's tomorrow night. I've gone ahead and prepared an apology speech for her. Hopefully she'll use this... Hello, American public. Many of you witnessed my unfortunate performance at the MTV Video Music Awards last weekend. I would like to issue an apology to all of you, and everyone else who has been following my recent hardships. Sorry. Sorry for giving you ten years of hit songs. Sorry for making every girl in America stop wearing flannel shirts and start dressing like a stripper. Sorry for providing millions of Internet pages for dudes in their basements to beat off to. Sorry for paving the way so that Christina Aguilera, Jessica Simpson, Mandy Moore, and every other hot singer of the 2000s could be famous. Sorry for giving everyone at TMZ.com a job. Sorry for having two kids, still maintaining 6% body fat, then wearing underwear and dancing on national TV. Then, she can rip off her face John Travolta-style, reveal that she's actually Jesus Christ come back to Earth, give some speech about remembering what's truly important in life, and then turn Susan Lucci into a giant bottle of wine and get the party started. Her popularity would be greater than ever before. http://www.shoutmouth.com/index.php/..._(9/15_Edition)  Radio Listeners May Want Less of "Gimme More" Susan Visakowitz Britney Spears' new single, "Gimme More," came roaring out of the gates on CHR (contemporary hit radio)/top 40 radio, debuting at No. 25 on Billboard sister publication Radio & Records' format chart for the week ending September 2 and endowing Spears with the second-best start of her career. But that was before MTV's Video Music Awards (VMAs). "Gimme" scored Most Increased Plays on the format during its first week out, racking up 1,062 spins. Day by day, the song climbed from 225 plays on CHR/top 40 on September 5 to 269 on September 7. Then came Spears' awkward and generally panned performance September 9 on the VMAs. The following day, "Gimme" got a jolt, jumping to 336 spins as talk of Spears' VMAs showing made the water cooler rounds. But on September 11, "Gimme" took its first spill on radio, falling to 331 spins. Will Spears' VMAs rendition ultimately undermine any momentum that her first single in three years was building? A Zomba label rep said radio is getting both negative and positive calls about the song since the telecast, but some programmers expect the latter won't last. "After the hilarious performance at the VMAs, there has been even more buzz about the song," KRQQ Tucson, Ariz., DJ Seth O'Brien said. "But I think this performance will be the running joke of Britney's attempt at a comeback. I bet we will see a drop in interest (in "Gimme") after a few days." http://www.reuters.com/article/enter...22585920070916  iProof Universal Jumps to SpiralFrog's Free Downloads: iPods Not Welcome Jason Mick Universal and SpiralFrog are dancing to a different tune...and it's not playing on an iPod (Source: elsevier.nl) Spiralfrog.com launched its free ad-supported download service today, and there's some interesting quirks Spiralfrog.com launched today, providing music fans with a legal avenue to download some free music. The only catch -- the music is supported by the site's advertising revenues, so your clicks keep those tracks downloading. Chairman and founder of New York-based SpiralFrog Inc., Joe Mohen announced "We believe [SpiralFrog] will be a very powerful alternative to the pirate sites, with SpiralFrog you know what you're getting ... there's no threat of viruses, adware or spyware." The site, which has been beta tested for months, currently carries about 800,000 tracks and 3,500 music videos available for free download. You must sign up for a free account and provide demographic information in order to gain access to the media. You must also use your account each month in order to keep it active, which is intended to prevent users from simply downloading and not returning to the site. The site intends to have over 2 million tracks available within the next several months. Most of the media on the site is from Vivendi SA's Universal Music Group, the largest record company in the world, and the only music label to currently have jumped at SpiralFrog's business plan. In July DailyTech reported that Vivendi had jumped ship from Apple's iTunes service, declining to renew their contract, deciding to seek revenue from alternative sources. Now it appears that one such alternative source is SpiralFrog. An interesting detail has emerged. Files from SpiralFrog are digitally protected and can be played on mp3 players, but cannot be burned to CDs. There is another minor detail, though -- the files cannot be played on Apple's wildly popular iPod MP3 players. The move to not allow its content to be played on iPod's appears to be a clear snub by the Universal Music Group, similar to NBC's recent move of its television content from iTunes to Amazon.com. Apple has not commented on this development. For many, though, SpiralFrog.com presents an intriguing new business model that may present a legal alternative to file sharing or spending large amounts of money on CDs or paid download services, such as iTunes. http://www.dailytech.com/Universal+J...rticle8905.htm  iPod Classic Will Be Supported As recently reported on Slashdot, Apple, in its infinite wisdom, has added a checksum to the iPod database apparently to restrict non-iTunes products (like Amarok via libgpod) from having the ability to add music. To me this sounds pretty familiar. This is the same thing they did to iTunes 4.5 to make it harder for other apps to read off their DAAP shares, they changed it again in iTunes 7; open source apps are still unable to read iTunes 7 DAAP shares. But there's better news on this iPod front. From #gtkpod today: <wtbw> okay guys <wtbw> i think we're done. <wtbw> let me code something just to check [30 minutes later] <wtbw> can i hear a fuck yeah? <wtbw> works for both mine and xamphears :> wtbw suggested donations from thankful users go to Cancer Research UK. Really the only "correct" solution is for folks to stop using Apple products. The iPod might have its own version of DAAP's iTunes 7 which has a checksum more difficult (apparently) to crack. But for the time being, things are fine. http://www.monroe.nu/archives/110-iP...Supported.html  Apple Blacklisting Hacked iPhones? Jason D. O'Grady I received the following email from a colleague: Speaking of hacks, Today I went into an Apple store with a less than two week old iPhone that had the green tint camera problem. Because it had been “hacked” with some 3rd party apps and was running T-Mobile they refused to service it, said the warranty was voided and “blacklisted” the phone against future service, or return! Only after asking for the manager and having several conversations with her, did they finally allow me to return it, but charged me a 10% restocking fee… Pretty Scary! Didn’t Steve and Woz get their start in college by selling a device that would “hack” pay phones and give people free long distance? So while he eventually got Apple to return the iPhone (after paying the restocking fee, that is), the lesson here is to do a restore of your iPhone and re-install the factory AT&T SIM before bringing into an Apple Store for service. That’s the beauty of software-only hacks, after all! http://blogs.zdnet.com/Apple/?p=882 |
|
|

|
|
|
#2 |
|
Join Date: May 2001
Location: New England
Posts: 10,016
|
Winamp Goes Where iTunes Doesn’t Dare
Ryan Jarrett Winamp, that staple of media players, will soon turn 10! And its not letting it pass without a bang. On the 10th of October at 10:10am, Winamp 5.5 (PC-only) will be released sporting two new and potentially controversial features: support for mp3 blogs and the ability to stream your music collection over the Internet (a Beta version is available here). Cashing in on the growing popularity of mp3 blogs, and the lack of tools to take advantage of them, Winamp’s Media Monitor can be used in conjunction with the software’s built-in browser to access any mp3s linked to on a blog page, presented as a playlist or even downloaded to your library. Winamp also includes handy links to a dozen or so music blogs to get you started. The second major new feature is the Winamp Remote. This acts like a local media server, cataloging your tracks and videos and then enabling you to access them from another device, including other PCs running Winamp or via a web browser, various mobile devices, and game consoles (Playstation 3, XBox 360 or Nintendo Wii). However, unlike iTunes, sharing isn’t restricted to devices on the local network, and instead you can also share your music over the Internet. To make this relatively simple, Winamp prompts you to send an email (or SMS text message) to a friend to let them access your playlists from their computer (they’ll need to create a free account to verify their identity, but only once). In this regard, Winamp Remote makes iTunes’ network sharing features seem rather puny and inflexible. Also new to version 5.5 is the “Bento” skin. This is a move away from Winamp’s traditional multi-windowed interface (the default skin), which can be confusing and cluttered at times. Instead, the new skin only has one window which is more in keeping with other media management software. The rest of Winamp performs as you’d expect it. It is still a very good media player; responsive, highly customisable, able to cope with many formats and yet still has a low demand on system resources. It will synchronise with a number of portable media players, including iPods*, making it a potential replacement for iTunes or Windows Media Player. Obviously, its still a beta version so there are some niggles with the program — it locked the interface for the duration of one track, although it had worked fine previously, and there are a couple of error messages when you close the program. Winamp continues to evolve, and the new and bold features are a worthy update in which to mark the application’s tenth anniversary. http://www.last100.com/2007/09/17/wi...s-doesnt-dare/  Mozilla President Kicks Ballmer, Trashes DRM, Quotes Spiderman Mike Butcher INTERVIEW: Tristan Nitot, president of Mozilla Europe, is a disarmingly casual guy, especially over a good lunch in a high-class London restaurant. But despite the relaxed delivery, he doesn’t pull his punches. Nitot is co-founder (with Peter Van der Beken) and president of Mozilla Europe, a non-profit organization whose goal is to develop and promote its open source software and, increasingly, that of others. He previously worked on the Netscape project for more than seven years. He is also founder of OpenWebGroup initiative. Nitot is passionate about what he sees as Microsoft’s opposition to the Internet’s development when it stopped development of the Internet Explorer browser for five years after 2001. He believes this acted as a serious barrier to the development of the Web in general, not just the open source movement. “IE was getting more and more obsolete in development terms. The Internet was stalling because of this,” he says. It was technologies like Netscape’s Netcaster, which acted as the core of what became RSS that helped open up the Web again. But Mozilla’s Firefox itself has come in for criticism. The next version of the Firefox browser will be 3.0. How does he react to criticisms that Firefox is slowly becoming bloated? “No, Firefox is getting speedier and speedier. Developers ask for new applications inside Firefox all the time but the early Mozilla Suite of 2003 - which wrapped up a browser, email client, HMTL editor and IRC all in one - showed that it was often too complicated a proposition for the Internet user.” He says Mozilla is working hard at finding a balance: “We don’t want to incorporate features for the sake of features - only where it makes sense for the user experience.” How does he view Apple’s Safari (a strategy Apple came up with long before Mozilla had got its act together with Firefox)? “My dream is that they eventually pick the Mozilla / Gecko / Webkit combination and give up Safari,” he says. “We see Safari and Firefox as allies in bringing diversity to the Web.” Later he goes further: “We are not against Microsoft, but we are against Microsoft’s monopoly [of the browser market].” So is Steve Ballmer a block on innovation at Microsoft? “Could be, yes,” says Nitot with a smile. He relates his view - held by many - that Microsoft’s attack of the web is directly related to the threat the Web poses to its desktop applications, as evidenced in recent times by Zoho and Google’s apps. But has he heard of the Blue Monster movement inside Microsoft to engage better with the open source community (also at Gaping Void)? In a word, no. But Nitot does recognise the sentiment: “My perception is that at the lower levels of Microsoft, there are people who are just like me. They understand the Net and the power of Web standards. They understand that, as Spiderman says, with great power comes great responsibility.” Does he extend his belief in open source to the open sourcing of content as well as code? What does he think about DRM? “I don’t think DRM has a future. Treating your customers like thieves is bad business practice. Today the customer is not ‘king’, they are considered thief first.” He relates a story about his young son being visibly upset by a DRM-enabled music CD which would not play on his older model HiFi. “It is stupid to think that the key to a DRM system won’t leak. So if it becomes more painful for a legitimate customer to use a product than it is for the pirates then that’s a problem,” he says. And the future for Mozilla? Nitot believes there will be greater emphasis put on embedded Mozilla code into both mobile devices and ones for the developing world like the OLPC. Nitot - replete with smile - will be appearing next at the Mozilla 24 event where Mozilla will hold a global conference via beaming in speakers and audiences globally. http://uk.techcrunch.com/2007/09/13/...tes-spiderman/  I.B.M. to Offer Office Software Free in Challenge to Microsoft’s Line Steve Lohr I.B.M. plans to mount its most ambitious challenge in years to Microsoft’s dominance of personal computer software, by offering free programs for word processing, spreadsheets and presentations. The company is announcing the desktop software, called I.B.M. Lotus Symphony, at an event today in New York. The programs will be available as free downloads from the I.B.M. Web site. I.B.M.’s Lotus-branded proprietary programs already compete with Microsoft products for e-mail, messaging and work group collaboration. But the Symphony software is a free alternative to Microsoft’s mainstay Office programs — Word, Excel and PowerPoint. The Office business is huge and lucrative for Microsoft, second only to its Windows operating system as a profit maker. In the 1990s, I.B.M. failed in an effort to compete head-on with Microsoft in personal computer software with its OS/2 operating system and its SmartSuite office productivity programs. But I.B.M. is taking a different approach this time. Its offerings are versions of open-source software developed in a consortium called OpenOffice.org. The original code traces its origins to a German company, Star Division, which Sun Microsystems bought in 1999. Sun later made the desktop software, now called StarOffice, an open-source project, in which work and code are freely shared. I.B.M.’s engineers have been working with OpenOffice technology for some time. But last week, I.B.M. declared that it was formally joining the open-source group, had dedicated 35 full-time programmers to the project and would contribute code to the initiative. Free office productivity software has long been available from OpenOffice.org, and the open-source alternative has not yet made much progress against Microsoft’s Office. But I.B.M., analysts note, has such reach and stature with corporate customers that its endorsement could be significant. “I.B.M. is jumping in with products that are backed by I.B.M., with the I.B.M. brand and I.B.M. service,” said Melissa Webster, an analyst for IDC, a research firm. “This is a major boost for open source on the desktop.” I.B.M. executives compare this move with the push it gave Linux, the open-source operating system, into corporate data centers. In 2000, I.B.M. declared that it would forcefully back Linux with its engineers, its marketing and its dollars. The support from I.B.M. helped make Linux a mainstream technology in corporations, where it competes with Microsoft’s Windows server software. I.B.M. is also joining forces with Google, which offers the open-source desktop productivity programs as part of its Google Pack of software. Google supports the same document formats in its online word processor and spreadsheet service. I.B.M. views its Symphony desktop offerings as part of a broader technology trend that will open the door to faster, more automated movement of information within and between organizations. A crucial technical ingredient, they say, is the document format used in the open-source desktop software, called the OpenDocument Format. It makes digital information independent of the program, like a word processor or spreadsheet, that is used to create and edit a document. OpenDocument Format is based on an Internet-era protocol called XML, short for Extensible Markup Language, which enables automated machine-to-machine communication. For example, an individual investor might create a spreadsheet with automated links to market information, and prices at which he or she wants to buy or sell shares in particular stocks. The person would get an alert by e-mail or cellphone message of price swings, and could create the document for a buy or sell order with a keystroke. Or, in a doctor’s office, patient records could be linked to hospital, clinic and other databases and updated automatically. Microsoft has the same vision of software automation, but it champions its own document format, called Office Open XML. Earlier this month, Microsoft failed in its initial effort to have Office Open XML ratified as a global technical standard by the International Organization for Standardization in Geneva. The OpenDocument Format, backed by I.B.M., Google, Sun and others, was approved by the standards organization last year. I.B.M. clearly regards its open-source desktop offerings as a strategic move in the document format battle. “There is nothing that advances a standard like a product that uses it,” said Steven A. Mills, senior vice president of I.B.M.’s software group. The Lotus Symphony products will support the Microsoft Office formats as well as the OpenDocument Format. But analysts note that technical translators are not entirely foolproof; Symphony software may easily translate the words from a Microsoft Word document, but some of the fonts and formatting may be lost. For many users, that may not matter, they say, but for others it might. Betsy Frost, a general manager in Microsoft’s Office business, said users valued “full compatibility” with previous versions of their Office documents as well as the ease of use and familiarity of Microsoft products. And she noted that there are 500 million Office users worldwide. Any inroads I.B.M. and its allies make against Microsoft, analysts say, will not come easily. “Three major players — I.B.M., Google and Sun — are now solidly behind a potential competing standard to Office,” said Rob Koplowitz, an analyst at Forrester Research. “But it’s a tough road. Office is very entrenched.” http://www.nytimes.com/2007/09/18/te...gy/18blue.html  Free Software Made Mandatory: IT Practicals of SSLC Exam Sabloo Thomas T’PURAM: Free software has been made mandatory for IT practicals of SSLC examination slated for March, 2008. The Director of Public Instruction (DPI) has issued orders making free software compulsory. It says Linux Operating System should be used for IT education in eighth, ninth and tenth standards. Till last year, schools had the freedom to conduct the examinations either in free software or in Microsoft platform. For the purpose, fully Linuxbased text books have been prepared for standard X and Linux-based supplementary text books have been prepared for standard VIII and standard IX. Text books for the purpose have been prepared by SCERT and Free Software Foundation of India under the guidance of IT@school project. The DPI has also decided to initiate various programmes for popularising free software. As part of it, various programmes were arranged to observe International Software Freedom Day on Saturday. A small introductory lecture will be delivered in the school assemblies across the state on Monday, followed by a pledge. An outline of the introductory lecture and the pledge have been circulated to the schools. A digital painting competition for students of eighth standard will be conducted on the day using TUX paint, XPaint and GIMP software. The topic of the painting competition will be ‘my school and surrounding.’ A presentation competition using Open Office Impress will be conducted for students of ninth and tenth standard in the topic ‘IT and its benefits to the common man.’ Both the competitions will be of one and half hour duration. The prize winning paintings will be compiled at the State -level and uploaded on the website www.education.kerala.gov.in. http://www.newindpress.com/NewsItems...apuram&Topic=0  Snowed By SCO Daniel Lyons In the print edition of Forbes there's a great (albeit sometimes painful) tradition of doing "follow-through" articles where a reporter either takes a victory lap for making a good call or falls on his sword for making a bad one. Online publications don't typically ask for follow-throughs. But I need to write one. For four years, I've been covering a lawsuit for Forbes.com, and my early predictions on this case have turned out to be so profoundly wrong that I am writing this mea culpa. What can I say? I grew up Roman Catholic. The habit stays with you. The case is SCO Group v. IBM. In March 2003, SCO sued IBM claiming that IBM took code from Unix--for which SCO claimed to own copyrights--and put that code into Linux, which is distributed free. Last month a judge ruled that SCO does not, in fact, own the Unix copyrights. That blows SCO's case against IBM out of the water. SCO, of Lindon, Utah, is seeking bankruptcy protection. In June 2003, a few months after SCO Group sued IBM over the Linux operating system, I wrote an article that bore the headline: "What SCO Wants, SCO Gets." The article contained some critical stuff about SCO but also warned that SCO stood a chance of winning the lawsuit. "SCO may not be very good at making a profit by selling software. ... But it is very good at getting what it wants from other companies," I wrote. I wrote that because in the 1990s SCO's predecessor company, Caldera, ran a similar shakedown on Microsoft, making claims about the old DOS operating system. I was briefed by Caldera's lawyers on that case, but I never took them seriously. Then they won a settlement. Whoops. This time, I figured I should at least give SCO the benefit of the doubt. I flew to Utah and interviewed their managers. I attended a SCO conference in Las Vegas and did more interviews. They told me all sorts of things, like they'd found a "smoking gun" that proved IBM was guilty, and that they were preparing to sue big Hollywood companies that use Linux server farms to make movies. I reported what they said. Turns out I was getting played. They never produced a smoking gun. They never sued any Hollywood company. Over time my SCO articles began to carry headlines like, "Dumb and Dumber," "Bumbling Bully" and "SCO gets TKO'd." But I still thought it would be foolish to predict how this lawsuit (or any lawsuit) would play out. I even wrote an article called "Revenge of the Nerds," which poked fun at the pack of amateur sleuths who were following the case on a Web site called Groklaw and who claimed to know for sure that SCO was going to lose. Turns out those amateur sleuths were right. Now some of them are writing to me asking how I'd like my crow cooked, and where I'd like it delivered. Others in that highly partisan crowd have suggested that I wanted SCO to win, and even that I was paid off by SCO or Microsoft. Of course that's not true. I've told these folks it's not true. Hasn't stopped them. The truth, as is often the case, is far less exciting than the conspiracy theorists would like to believe. It is simply this: I got it wrong. The nerds got it right. SCO is road kill. Its lawsuit long ago ceased to represent any threat to Linux. That operating system has become far too successful to be dislodged. Someday soon the SCO lawsuits will go away, and I will never have to write another article about SCO ever again. I can't wait. http://www.forbes.com/2007/09/19/sof...0919lyons.html  Oh, Everyone Knows That (Except You) Abby Goodnough IN this era of blogosphere gossip, viral e-mail and infinite YouTube video archives, the open secret — unacknowledged by its keeper, theoretically hush-hush but widely suspected or known — arguably should be a thing of the past in public life. But the case of Larry E. Craig, the Idaho senator arrested when an undercover police officer said he made overtures to him for sex, suggests otherwise. Though rumors had long swirled around the conservative Republican senator, the mainstream news media pointedly overlooked them until last week, when Roll Call broke the news of his arrest in June. Most notably, The Idaho Statesman investigated reports about Mr. Craig for months after a gay blogger published a claim last fall that the senator had had sex with men, but decided against running uncorroborated accusations that Mr. Craig denied and continues to deny. As much traffic as the speculation generated on blogs before Mr. Craig’s arrest, it gained currency — that is, it became a “story” suitable for national publication and broadcast — only when it was backed by an arrest report. The same went for former Representative Mark Foley of Florida, who was long rumored to be gay but whose open secret was widely exposed only after his sexually explicit electronic messages to former Congressional pages surfaced last fall and forced his resignation. And for Jim McGreevey, the married New Jersey governor whose homosexuality was suspected for years in local circles, but was left pretty much untouched by the news media. Only after disclosing an affair with a man he had once appointed to a six-figure state job did he resign. Old-fashioned as it seems, there are still tacit rules about when an open secret can remain in its own netherworld, without consequence to the politician who keeps it. But now that any whisper can become a global shout in an instant, how much longer can those rules apply? And should they, anyway? “What fascinates me is the question of, if it didn’t get out for all this time, what does it mean?” said Jeff Jarvis, a journalism professor who now blogs on media and politics on buzzmachine.com. “Does it mean journalists are doing a good job, or does it mean they are doing a bad job?” Jack Bass, who is on the faculty at the College of Charleston and who co-wrote “Strom: The Complicated Personal and Political Life of Strom Thurmond,” said that at one time, politicians whose open secrets were exposed could use the fact to their advantage, on the theory that they were too outrageous to be believed and reflected badly only on the rumormonger. When a small South Carolina paper declared during Mr. Thurmond’s 1972 re-election campaign that he had fathered a child with a black woman — a fact not confirmed until after his death in 2003 — Mr. Thurmond distributed copies of the provocative headline to sympathetic voters. He won the race. In the mainstream media, the recent standard for pursuing open secrets has been murky, but generally guided by the notion that private behavior matters when it is at odds with public declarations. Mr. Foley’s bawdy flirtation with pages was fair game not least because he had sponsored legislation seeking to protect children from online predators. Mr. Craig supported a 2006 amendment to the Idaho Constitution barring gay marriage and civil unions and has voted in Congress against gay rights. Other secrets remain just that, usually because the politician in question has not been perceived as crossing an obvious line into hypocrisy, or he denies the rumors and no one can substantiate them. Perhaps no one wants to. They may not even be true. “Most so-called open secrets are things we don’t really know the truth about,” said Alan Ehrenhalt, executive editor of Governing magazine. Regardless, he said: “It’s human nature not to pry into dark corners if you don’t have to. Most people would rather just let things be.” And so it happens that a lot of states have lawmakers widely known for heavy drinking or sleeping with aides, whether or not the supposition is proved. One state official has long been rumored to be gay, and newspapers have investigated tips on his relationships. But only bloggers have published details, with little traction. Rick Wilson, a Republican consultant based in Florida who has worked for Rudolph W. Giuliani, the former New York mayor, and Katherine Harris, the former Florida congresswoman, among others, said that most states have their own expressions for the circumstances under which open secrets stay secret. In Florida, he said, it’s the “Three County Rule” — no girlfriends within three counties of your home district. In New York, it’s the “Bear Mountain Compact” — nobody talks about what politicians do with their free time once they’ve crossed the Bear Mountain Bridge en route to Albany from points south. “There’s a similar phrase in every state I’ve worked in,” Mr. Wilson said. “In a lot of cases it’s because the principals involved are powerful, and a lot of the people who know are aides or staff or lobbyists or even reporters who rely on these people for access. So you end up with this feeling of, ‘It’s just business, it’s not affecting their work.’ Once it starts affecting their work, then the rules change.” Given the power of the Internet, though, the standards could now easily shift with each new salacious rumor reported online. One of the Internet’s main assets, its supporters say, is that it is unfiltered — but that allows sewage leaks of sorts, too. Mr. Jarvis said bloggers constantly had to hone their judgment about when to ignore a rumor, write their own piece on it or — often the best choice, he said — link to another blog’s report on it. “I believe we should do what we do best and link to the rest,” he said. “A link is not necessarily an endorsement, but a way to say ‘you go judge for yourself.’ ” Let the blogger beware, though, of “link bait” — provocative or downright outrageous postings that some bloggers write merely to lure traffic. As an antidote, a growing number of bloggers make it their chief goal to debunk scurrilous rumors circulating on the Web. Take Snopes.com, which calls itself “the definitive Internet reference source for urban legends, folklore, myths, rumors and misinformation.” Its section on politics has subcategories devoted to Bill and Hillary Clinton, John Kerry, Barack Obama and President Bush. “It’s not strong enough yet,” Mr. Jarvis said of the online debunking trend, “but it’s part of a new architecture of the Web that is necessary.” Michael Kinsley, founding editor of the online magazine Slate, said he used to believe that journalism should have an “intermediate standard” for publishing rumors — one that did not require firm corroboration. At one point, he said, he even defended Matt Drudge, the Internet gossip, for saying that 80 percent of what he published was accurate. He regrets that stance. “I argued at the time that the Internet was the right place for that,” he said. “But at this point, the Internet is the mainstream media, so I think it should be as accurate as possible.” Mr. Kinsley said attitudes toward open secrets have changed since the 1980’s, when he covered a well-known Democrat’s early presidential bid and quit The New Republic when it wouldn’t publish what he said was a solidly reported piece he wrote about the candidate’s philandering. “My argument back then was it was elitist censorship for journalists not to publish what they knew about politicians because they were worried voters wouldn’t handle the information with as much sophistication as they thought appropriate,” he said. “Now, it turns out the prudes tend to be the Washington establishment journalists and the people who take a more sophisticated view are the voters.” As proof, he offered the Monica Lewinsky scandal, which had little long-term effect on Mr. Clinton’s popularity. Mr. Jarvis echoed that view, saying any expectation that politicians will be moral leaders is naïve. “There is always a taint of, if not corruption, then compromise about them,” he said. “This idea that they are moral leaders is moronic.” http://www.nytimes.com/2007/09/02/we...goodnough.html  In the Shadow of Horror, SS Guardians Frolic Neil A. Lewis Last December, Rebecca Erbelding, a young archivist at the United States Holocaust Memorial Museum, opened a letter from a former United States Army intelligence officer who said he wanted to donate photographs of Auschwitz he had found more than 60 years ago in Germany. Ms. Erbelding was intrigued: Although Auschwitz may be the most notorious of the Nazi death camps, there are only a small number of known photos of the place before its liberation in 1945. Some time the next month, the museum received a package containing 16 cardboard pages, with photos pasted on both sides, and their significance quickly became apparent. As Ms. Erbelding and other archivists reviewed the album, they realized they had a scrapbook of sorts of the lives of Auschwitz’s senior SS officers that was maintained by Karl Höcker, the adjutant to the camp commandant. Rather than showing the men performing their death camp duties, the photos depicted, among other things, a horde of SS men singing cheerily to the accompaniment of an accordionist, Höcker lighting the camp’s Christmas tree, a cadre of young SS women frolicking and officers relaxing, some with tunics shed, for a smoking break. In all there are 116 pictures, beginning with a photo from June 21, 1944, of Höcker and the commandant of the camp, Richard Baer, both in full SS regalia. The album also contains eight photos of Josef Mengele, the camp doctor notorious for participating in the selections of arriving prisoners and bizarre and cruel medical experiments. These are the first authenticated pictures of Mengele at Auschwitz, officials at the Holocaust museum said. The photos provide a stunning counterpoint to what up until now has been the only major source of preliberation Auschwitz photos, the so-called Auschwitz Album, a compilation of pictures taken by SS photographers in the spring of 1944 and discovered by a survivor in another camp. Those photos depict the arrival at the camp of a transport of Hungarian Jews, who at the time made up the last remaining sizable Jewish community in Europe. The Auschwitz Album, owned by Yad Vashem, the Israeli Holocaust museum, depicts the railside selection process at Birkenau, the area where trains arrived at the camp, as SS men herded new prisoners into lines. The comparisons between the albums are both poignant and obvious, as they juxtapose the comfortable daily lives of the guards with the horrific reality within the camp, where thousands were starving and 1.1 million died. For example, one of the Höcker pictures, shot on July 22, 1944, shows a group of cheerful young women who worked as SS communications specialists eating bowls of fresh blueberries. One turns her bowl upside down and makes a mock frown because she has finished her portion. On that day, said Judith Cohen, a historian at the Holocaust museum in Washington, 150 new prisoners arrived at the Birkenau site. Of that group, 21 men and 12 women were selected for work, the rest transported immediately to the gas chambers. Those killings were part of the final frenetic efforts of the Nazis to eliminate the Jews of Europe and others deemed undesirable as the war neared its end. That summer the crematoriums broke down from overuse and some bodies had to be burned in open pits. A separate but small group of known preliberation photos were taken clandestinely of those burnings. Auschwitz was abandoned and evacuated on Jan. 18, 1945, and liberated by Soviet forces on Jan. 27. Many of the Höcker photos were taken at Solahütte, an Alpine-style recreation lodge the SS used on the far reaches of the camp complex alongside the Sola River. Though they as yet have no plans to exhibit the Höcker album photos, curators at the Holocaust Memorial Museum have created an online display of them on the museum’s Web site (ushmm.org) that will be available this week. In many cases they have contrasted the Höcker images with those from the Auschwitz Album. In one, SS women alight from a bus at Solahütte for a day of recreation; meanwhile, in a picture from the Auschwitz Album taken at about the same time, haggard and travel-weary women and children get off a cattle car at the camp. Museum curators have avoided describing the album as something like “monsters at play” or “killers at their leisure.” Ms. Cohen said the photos were instructive in that they showed the murderers were, in some sense, people who also behaved as ordinary human beings. “In their self-image, they were good men, good comrades, even civilized,” she said. Sarah J. Bloomfield, the museum’s director, said she believed that other undiscovered caches of photos or documents concerning the Holocaust existed in attics and might soon be lost to history. The donor, who had asked to remain anonymous, was in his 90s when he contacted the museum, and he died this summer. He told the museum’s curators that he found the photo album in a Frankfurt apartment where he lived in 1946. The photos of the Auschwitz Album were discovered by Lili Jacob, a Hungarian Jew who was deported in May 1944 to Auschwitz, near Krakow in Poland. She was transferred to another camp, Dora-Mittelbau in Germany, where she discovered the pictures in a bedside table in an abandoned SS barracks. She was stunned to recognize pictures of herself, her rabbi and her brothers aged 9 and 11, both of whom she later discovered had been gassed immediately after arrival. Höcker fled Auschwitz before the camp’s liberation. When he was captured by the British he was carrying false documents identifying him as a combat soldier. After the 1961 trial of Adolf Eichmann in Israel, West German authorities tracked down Höcker in Engershausen, his hometown, where he was working as a bank official. He was convicted of war crimes and served seven years before his release in 1970, after which he was rehired by the bank. Höcker died in 2000 at 89. http://www.nytimes.com/2007/09/19/ar...n/19photo.html  The Mystery of Hitler’s Globe Goes Round and Round Michael Kimmelman Hitler’s globe is missing. Wolfram Pobanz, a 68-year-old retired cartographer, is positive that it’s not the one in the Deutsches Historisches Museum, with the Russian bullet hole through Germany, and he can prove it. Neither is it the one in the Märkisches Museum, the Berlin history museum nearby, nor the one in a geographical institute across town, which first caught Mr. Pobanz’s eye 40-odd years ago when he was a student. “We called it the Führer globe,” he remembered. It planted the seed of his fascination with the Columbus Globe for State and Industry Leaders, as this enormous model was called — a far cry from the inflatable version that Charlie Chaplin bounced around in “The Great Dictator,” which mocked Hitler’s megalomania and created the indelible vision of a fascist tyrant doing a pas de deux with the planet. Manufactured in two limited editions in Berlin during the mid-1930s (the second edition changed Abyssinia to Italian East Africa), the real Columbus globe was nearly the size of a Volkswagen and, at the time, more expensive. A standard wood base was designed to support it, but custom furniture stands were made for Hitler and other Nazi leaders. Mr. Pobanz has been methodically tracking them down. White-haired, large, jowly and bespectacled, an unstoppable St. Bernard of enthusiasm for all things globe-related, he came the other day to the Deutsches Historisches Museum with a stack of books and photocopied evidence in his satchel, happy to lay it all out. “He’s a very serious man with a passion for this particular type of globe,” said the museum’s director, Hans Ottomeyer. Mr. Ottomeyer had mentioned Mr. Pobanz in passing during a conversation about Berliners with remarkable obsessions. Mr. Pobanz’s full story turns out to be a mystery. Besides the globes in Berlin, he said, there are two Columbus globes in public collections in Munich. Fellow globe hunters, put on the scent by word of his pursuit, have turned up several more in private hands and elsewhere, outside Germany. None, however, is from Hitler’s office in the New Reich Chancellery, the globe that inspired Chaplin. In Chaplin’s satiric film the globe is a balloon, an emblem of megalomania, which suddenly bursts in the fictional tyrant’s face. The image became a cinematic touchstone: art transformed into political symbol, shaping history. Hitler, more than any modern tyrant, grasped the power of visual signs. He cooked up the Nazi Party uniform and the flag and hired Albert Speer to design the New Chancellery, where the giant Columbus globe, with a sharp-cornered, stepped wood base, was parked in Hitler’s quarters. Newsreels and still photographs from the time the building opened, in 1939, show visitors trekking down marbled passageways more than four football fields long to reach the Führer. It was Chaplin’s genius, in 1940, to exploit the symbolism of the globe. “It has been a trait of megalomaniacs throughout history to use the arts to control thought, gain respectability, bolster their power and memorialize themselves,” Frederic Spotts, a historian of modern Germany, observes in his book “Hitler and the Power of Aesthetics.” But Hitler went “beyond the others,” he writes, and “defined and legitimized his rule in cultural terms.” Chaplin’s sight gag, you might say, gained weight precisely by playing off Hitler’s use of visual symbols. Funny thing is, “Hitler probably didn’t think anything about the globe,” Mr. Pobanz said. “There’s no picture of Hitler beside the globe. He controlled all photographs of himself. If the globe had actually meant anything special to Hitler, there would surely be a photograph.” “For me this is not about Hitler, it’s about the correctness of the situation,” he insisted. When a Berlin newspaper last year called the Deutsches Historisches Museum’s globe “the Globe of the Mass Murderer,” he simply felt, as a scholar, that the record should be set straight. Whether he would be going to the same lengths to uncover the pedigree of a globe attributed to Konrad Adenauer or John Foster Dulles, he didn’t say. Instead, he said, “I don’t know how many of these globes were made because the Columbus factory was destroyed in 1943, along with its archives.” Mr. Pobanz pulled out a photocopy of a drawing he had unearthed for a custom base, designed by the Munich studio of Paul Ludwig Troost. Troost was Hitler’s favorite architect during the early 1930s. “This base was made for Ribbentrop’s Foreign Ministry,” he said. It was identical to the one for the globe at the Deutsches Historisches Museum. “So this globe could only have been made for Ribbentrop,” he said. He did not pause to contemplate if the provenance made much difference, morally speaking. “The globes designed for the New Reich Chancellery had a more angular base,” he said, then unveiled a different photocopy. About the two globes in Munich, he explained, one came from Hitler’s offices there (also with a bullet hole in it, American). So that is a Hitler globe, but it’s still not the model ordered by Speer for the New Reich Chancellery, which Chaplin immortalized. The second globe in Munich came from a Nazi administrative building. Both pedigrees are documented, Mr. Pobanz said. He then leapt into a list of international globe organizations. Mr. Pobanz belongs, he explained, to the International Coronelli Society for the Study of Globes, through which “I’ve heard about a globe in Breslau, and another in Warsaw.” Meanwhile Globusfreund (Friend of the Globe) magazine, based in Vienna, he said, has been pressing him to publish his research. The unmistakable anxiety of a man contemplating a prospective deadline suddenly flashed across his face. “I can’t,” he said. “I’m still collecting evidence.” First interested in maps and globes because of their artistry and technical complexity, as a boy he made field trips in Germany and long bicycle tours across Europe. “Maps contain the imagination of the world,” he said. “You can’t go to all the places, but you can travel in your mind.” He lives alone, he said. He has no family. Before tackling this Hitler globe mystery, he specialized in maps from the Soviet Union and East Germany, tracking down errors planted to throw off enemies from military sites. The suggestion that he’s a map detective seems to offend his sensibility. He opened a blue folder of papers to a photocopy showing a group of Russian soldiers in the New Reich Chancellery in May 1945, crowded around Hitler’s globe. “I don’t know where it is,” he said, studying the image for a second. “Maybe it’s in Moscow.” http://www.iht.com/articles/2007/09/19/arts/globe.phpl  Good, Bad or Ugly: A Legend Shrouded in Gunsmoke Remains Hazy Manohla Dargis Before a bullet shattered his skull in 1882, Jesse James cut a bloody swath through parts of the Midwest and the South, leaving a trail of corpses and favorable press notices in his wake. Bad man, poor man, bushwhacker, thief, James was as American as apple pie and the Confederate flag he wrapped himself in like an excuse. That bard of the great unwashed, Woody Guthrie, compared him to Robin Hood, and decades later Bruce Springsteen kept the fires burning, singing about a homespun legend as seductive as it is false. The lachrymose new film “The Assassination of Jesse James by the Coward Robert Ford” adds another gauzy chapter to the overtaxed James myth, if not much rhyme or reason, heart or soul. Topped by Brad Pitt wearing boot-black hair and a faraway stare, this is a portrait of the murderer as a middle-aged man as seen through the curious mirror of celebrity. At a well-seasoned 34, James lives in an ordinary house in an ordinary town, where he sits in his backyard smoking cigars and handling snakes, a devil playing at preacher. His days with Confederacy guerrillas are long gone, as are most of his crimes. Among his closest companions now is his greatest fan, Bob Ford, a gunslinger slyly played by Casey Affleck. As its title announces, “The Assassination of Jesse James by the Coward Robert Ford” is about a murder, the last violent chapter in a cruelly violent life. As such, it’s also about a celebrity stalker, a kind of Mark David Chapman in spurs who nurses an annihilating love for the object of his obsession. It’s an obsession fueled and fanned by the media, including the sympathetic newsmen who saw James as a heroic anti-Reconstructionist, and the fiction writers who memorialized and even exalted the brutal exploits of his gang. Like a schoolgirl with a crush, Bob Ford keeps his treasured Jesse James dime novels in a box under his bed. When he caresses the cover of one book, it’s as if he were tenderly stroking a lover’s cheek. If there was more to Bob’s love, you won’t find it here, despite a coy bathtub scene that finds James luxuriating in milky water while the younger man hovers uncertainly nearby. “You want to be like me or do you want to be me?” asks James, casting his glance back at the man others would later brand Judas. In this nearly all-male world of camaraderie and gunsmoke, where little women bustle discreetly in the background (including Mary-Louise Parker as James’s wife, Zee), the ways of the flesh, of heaving, stinking, struggling humanity, have little place. For all their exploded bone and ravaged pulp, their trickles and rivulets of blood, the men in this film aren’t as much bodies as beautiful, empty signifiers. In his last — and first — feature film, “Chopper” (2000), the New Zealand-born director Andrew Dominik seemed on the same wavelength as his raucous, at times queasy, entertaining subject, the ultrabrutal criminal reprobate of the title, played by Eric Bana. Neither overtly sympathetic nor disapproving, the filmmaker presented his villain as a larger-than-life but unequivocally human grotesque. Using color like an Expressionist, he bleached the screen a sizzling white that turned blood red nearly black and splashed on hues of bilious green and urine yellow as if to suggest that Chopper’s fluids had leaked from his body to contaminate his surroundings. The colors sicken and beguile, as does the human riddle at their center. There’s a different riddle in “The Assassination of Jesse James,” staring into a florid sunset, slashes of red cutting across the sky. Dressed in near-all black, the question mark known as Jesse James stands away from the camera, knee-deep in a golden, grassy field stirred by the wind or perhaps just an off-screen mechanical fan. It’s a striking, pleasing image, whatever the case, pretty as a picture postcard, a vision of man and nature that brings to mind Thoreau at Walden Pond or more precisely Terrence Malick’s “Days of Heaven.” James is also facing West, of course, toward the last frontier, home to cowboys and Indians and prospectors of all types, including, soon enough, those who will wield movie cameras, not six-shooters. If he had lived, James might have saddled up for the movies, and, indeed, his own son played him in the 1921 film “Jesse James Under the Black Flag.” When “The Assassination” opens in September 1881, shortly before his final train robbery and seven months before his death, James was already a star of sorts, a living if fast-aging legend, a favorite newspaper subject, a government target and the featured attraction in hundreds of dime novels with titles like “The James Boys and the Vigilantes.” Mr. Pitt is himself a supernova luminary, of course, and part of the attraction of this film is how his celebrity feeds into that of his character, adding shadings to what is, finally, an overconceptualized if under-intellectualized endeavor. It’s a curious performance, at once central and indistinct, but then, so too is the character. Based on the novel of the same title by Ron Hansen, the film introduces James at the beginning of his end. Hunkered down in some woods, surrounded by darkly dressed men and leafless birch trees, and framed by Roger Deakins’s impeccable, stark, high-contrast cinematography, he looks a vision. This isn’t just Jesse James — it’s also Jim Morrison at the Whisky in 1966 with a dash of Laurence Olivier, a touch of Warren Beatty and more than a hint of Ralph Lauren. It’s the beautiful bad man, knowing and doomed, awaiting his fate like some Greco-Hollywood hero, rather than the psychotic racist of historical record. The movies have their truths, which rarely align with those of history. Taken on its own narrow, heavily aestheticized and poetic-realist terms, then, “The Assassination of Jesse James by the Coward Robert Ford” works. The cinematography may speak to Mr. Dominik’s yearning for meaning and importance more than it does of his outlaw, but the visuals often dazzle and enthrall. (The images that approximate the blurred distortions characteristic of pinhole photography are especially striking.) They also distract and, after a while, help weigh down the film, which sinks under the heaviness of images so painstakingly art directed, so fetishistically lighted and adorned, that there isn’t a drop of life left in them. Instead of daguerreotype, Mr. Dominik works in stone. The question of whether the world or cinema needs another monument to an American gangster, a thug who lived by the gun and repeatedly killed in cold blood, remains unanswered by the film and its makers. And perhaps that isn’t a question worth asking. This is, after all, meant to be an evening’s entertainment, and its burdens should remain modest even if its goals are not. Its revelations, aside from Mr. Affleck’s performance, which manages to make the character seem dumb and the actor wily and smart, are nonexistent. The true story of Jesse James, despite all the dime novels and B movies, remains untold, perhaps because in its savagery it really is as American as apple pie and, as such, unspeakably hard to tell. “The Assassination of Jesse James by the Coward Robert Ford” is rated R (Under 17 requires accompanying parent or adult guardian). Gun violence, rude language. THE ASSASSINATION OF JESSE JAMES BY THE COWARD ROBERT FORD Opens today in New York, Los Angeles and Toronto. Directed by Andrew Dominik; written by Mr. Dominik, based on the novel by Ron Hansen; director of photography, Roger Deakins; edited by Dylan Tichenor and Curtiss Clayton; music by Nick Cave and Warren Ellis; produced by Brad Pitt, Dede Gardner, Ridley Scott, Jules Daly and David Valdes; released by Warner Brothers Pictures. Running time: 150 minutes. WITH: Brad Pitt (Jesse James), Casey Affleck (Robert Ford), Sam Shepard (Frank James), Mary-Louise Parker (Zee James), Paul Schneider (Dick Liddil), Jeremy Renner (Wood Hite), Zooey Deschanel (Dorothy) and Sam Rockwell (Charley Ford). http://movies.nytimes.com/2007/09/21/movies/21assa.html  Out today New DVDs Dave Kehr CRUISING Controversial when it opened in 1980, William Friedkin’s “Cruising,” a thriller about the search for a serial killer in that era’s flourishing world of New York gay leather bars, generated only a murmur when it returned to theaters this month as a prelude to its DVD release today. The Village Voice, which led the protest against Mr. Friedkin’s film even as it was being shot in the West Village, greeted the rerelease with condescension colored by a certain nostalgia: “Nothing at the orgy is as shocking as the smile on everyone’s face,” the critic Nathan Lee wrote, lamenting the post-AIDS decline of Mr. Friedkin’s vividly depicted Sin City. A lot, of course, has changed for gays in America since “Cruising” made its debut. But times have also changed for serial killers: The shadowy figure that “Cruising” deploys as an embodiment of pure evil has become, thanks to “The Silence of the Lambs” and television shows like “Dexter,” a surreptitious figure of identification for the audience. Movies now invite us to react to the serial killer’s power and remorselessness not with revulsion, but with laughter and perhaps even envy. Hannibal Lecter is less a monster than he is a stand-up comedian, and snappy one-liners are not what interest Mr. Friedkin. Instead, his enduring theme is the reality of evil and its uncomfortable proximity to sex, a theme the world embraced when he adapted William Peter Blatty’s theological best seller, “The Exorcist,” in 1973. But applying a similar gothic approach to “Cruising” — a film noir that turns into a horror movie — got Mr. Friedkin in trouble, and not only the political kind. Al Pacino, still wreathed in the saintly idealism of “Serpico,” plays Steve Burns, a rookie cop who, in exchange for a fast-lane promotion, agrees to go undercover in the S&M bars of the meatpacking district in search of a psycho preying on gay men. Like all good noir heroes, he finds himself drawn to the killer he is tracking, an effect registered by Mr. Friedkin’s deft use of tracking shots tied to Burns’s point of view. (“I like to watch,” he says at one point.) The bars are portrayed as a kind of hell, photographed in a near-monochromatic black-and-blue color scheme, with an emphasis on heat, humidity, human sweat and sulfuric cigarette smoke. Though some scenes were fogged up to avoid censorship for the initial release, they are now presented as Mr. Friedkin shot them. The film seems to be moving toward a generalized guilt, proposing new suspects at every turn — a homophobic but secretly gay policeman (Joe Spinell), a police captain with a mysterious agenda (Paul Sorvino), the psychotically jealous roommate (James Remar) of a lovable theater queen (Don Scardino) and ultimately Burns himself — all contained in the faceless figure of a man in a leather mask who pops up at key moments. “Cruising” only falters when it reverts from horror mode to the police beat and fingers a disappointingly trite perpetrator. In interviews Mr. Friedkin has suggested that he wanted the movie to be “nearly abstract,” with an ending that left the murders unsolved. But Hollywood was not ready for that in 1980, and is probably less ready now. (Warner Home Video, $19.97, R) VINCENT PRICE MGM Scream Legends Collection MGM DVD, the current custodians of the American International library, have repackaged three out-of-print Vincent Price double-feature discs and added a terrific new transfer of Michael Reeves’s cult favorite “Witchfinder General” (1968) to create a tribute to this plummy-voiced stalwart of horror films. The films in this package belong to the later stage of Price’s career, when he had essentially become a comic actor, executing entertainingly campy pirouettes. The boxed set includes “The Abominable Dr. Phibes” (1971) and its 1972 sequel, “Dr. Phibes Rises Again,” two very stylish mad-doctor romps filmed in colorful Art Nouveau interiors by the director Robert Fuest; a double feature of Douglas Hickox’s “Theater of Blood” (1973), with Price as a hammy Shakespearean avenging himself on the critics who disparaged his work, and Jim Clark’s “Madhouse” (1974), in which Price parodies himself as an aging horror star; and two anthology films, Roger Corman’s three-part “Tales of Terror” (1962), based on stories by Edgar Allan Poe, and Sidney Salkow’s “Twice-Told Tales” (1963). “Tales of Terror” is still lots of fun; Price is paired with Peter Lorre for an adaptation of “The Black Cat” that veers almost immediately into “The Cask of Amontillado.” The transfers are old, and some are showing their age, but all are watchable. In this context “Witchfinder General” stands out like Raymond Chandler’s proverbial tarantula on a slice of angel food cake. It was the third and final feature by Michael Reeves, a promising talent who was in his early 20s at the time of filming and who died in 1969 of barbiturate poisoning. Along with George Romero’s “Night of the Living Dead,” also released in 1968, “Witchfinder General” stood at the head of a new breed of politically minded horror films that would extend through the ’70s. (Several have recently been remade with their political subtexts stripped away.) As violently anti-authoritarian as anything made by Jean-Luc Godard (“Weekend”) or Pier Paolo Pasolini (“Porcile”) in those turbulent times, the film locates its axis of evil firmly at the intersection of church and state. The setting is the English Civil War, and Price’s character, based on a historical figure, is an agent of the Protestant Parliamentarians who goes from village to village, extracting confessions from accused witches with the help of his enthusiastically sadistic partner (Robert Russell). Not surprisingly, a large number of the suspects are young, female and helpless. There is no trace of campiness in Price’s performance, which, with that in “Edward Scissorhands,” remains his best work as an actor. American International released “Witchfinder General” in the United States as “The Conqueror Worm,” the title of a Poe poem, in the hope of associating the film with its popular Poe cycle. The new anamorphic transfer replaces the title and eliminates a precredit sequence of Price reading the poem. More important, it uncovers photographic values that weren’t apparent in American International’s notoriously cheap theatrical prints, and also restores an orchestral score by Paul Ferris that was eliminated for copyright reasons from previous United States video releases. For collectors who already own the other Price films in the boxed set, MGM has made “Witchfinder General” available as a stand-alone release. (MGM DVD, boxed set, $39.98; “Witchfinder,” $14.98, not rated) ALSO OUT TODAY DEATH PROOF The “extended and unrated” version of Quentin Tarantino’s half of the “Grindhouse” double feature; this formally brilliant little film plays much better on its own. (Genius Products, $29.95, unrated) WE ARE MARSHALL The trials and triumphs of an underdog football team. The coach is played by Matthew McConaughey. McG directed. (Warner Home Video, $28.98, PG) ROBINSON CRUSOE ON MARS Paul Mantee is the astronaut stranded on Mars with only a monkey for a companion in Byron Haskin’s enduring fantasy favorite of 1964. (Criterion Collection, $39.95, not rated) http://www.nytimes.com/2007/09/18/mo...deo/18dvd.html  Student Arrested, Tasered at Kerry Event University of Florida Student Arrested, Tasered at Kerry Forum After Asking About Election AP University of Florida student Andrew Meyer struggles with University Police as officers try to remove him from a question and answer session with Sen. John Kerry, D-Mass., in Gainesville, Fla. Meyer attempted to speak at the forum after the question and answer session had ended, university officials said. A University of Florida student was Tasered and arrested after trying to ask U.S. Senator John Kerry about the 2004 election and other subjects during a campus forum. Videos of the incident posted on several Web sites show officers pulling Andrew Meyer, 21, away from the microphone after he asks Kerry about impeaching President Bush and whether he and Bush were both members of the secret society Skull and Bones at Yale University. "He apparently asked several questions he went on for quite awhile then he was asked to stop," university spokesman Steve Orlando said. "He had used his allotted time. His microphone was cut off, then he became upset." As two officers take Meyer by the arms, Kerry, D-Mass., is heard to say, "That's alright, let me answer his question." Audience members applaud, and Meyer struggles to escape for several seconds as up to four officers try to remove him from the room. Meyer screams for help and asks "What did I do?" as he tries to break away from officers. He is forced to the ground and officers order him to stop resisting. Meyer says he will walk out if the officers let him go. As Kerry tells the audience he will answer the student's "very important question," Meyer struggles on the ground and yells at the officers to release him, crying out, "Don't Tase me, bro," just before he is Tasered. He is then led from the room, screaming, "What did I do?" Meyer was charged with resisting an officer and disturbing the peace, according to Alachua County jail records. No bond had been set. Meyer was scheduled to appear in court Tuesday morning, a jail official said. It was not known if Meyer had an attorney. Orlando said university police would conduct an internal investigation. "The police department does have a standard procedure for when they use force, including when they use a Taser," Orlando said. "That is what the internal investigation would address whether the proper procedures were followed, whether the officers acted appropriately." http://www.abcnews.go.com/US/wireStory?id=3616977  Kerry Condemns Heckler Arrest ABC News' Rick Klein Reports: Sen. John Kerry on Tuesday comdemned the arrest of a University of Florida student at one of his speeches, saying that he was engaged in a "good healthy discussion" with 21-year-old Andrew Meyer when he was Tasered and taken into custody. "In 37 years of public appearances, through wars, protests and highly emotional events, I have never had a dialogue end this way," Kerry said in a statement. "I believe I could have handled the situation without interruption, but I do not know what warnings or other exchanges transpired between the young man and the police prior to his barging to the front of the line and their intervention. I asked the police to allow me to answer the question and was in the process of responding when he was taken into custody." "I was not aware that a taser was used until after I left the building," he continued. "I hope that neither the student nor any of the police were injured. I regret enormously that a good healthy discussion was interrupted." For politicians, hecklers come with the territory. But the arrest and detention of Meyer at Kerry speech on Monday stood out in at least two respects: Police acted aggressively in trying to silence Meyer, and the entire incident was captures on video -- making it an immediate Internet and TV sensation. Videos show Meyer being pulled away from the microphone after as he sought to ask Kerry, D-Mass., a rambling series of questions that touch on allegations of voting improprieties in the 2004 election, possible impeachment of President Bush, Iran, and Kerry’s membership in Yale's secret Skull and Bones society. Kerry sought to answer at least some of Meyer’s questions even as Meyer was dragged off by campus police -- and after police used a Taser to try to subdue him as he was being arrested. "Help me! Help!" Meyer says. "What are you doing! Get off of me! Don't Taser me, bro! Oh my God! Oh my God!" Meyer was jailed overnight on charges of disturbing the peace and resisting an officer. As word spread of his arrest, his friends used his Website as a clearinghouse for supporters to learn about the incident, and to organize a rally on his behalf on the University of Florida campus at noon ET today. The University of Florida has scheduled a news conference to discuss the incident at 3 pm ET today. University spokesman Steve Orlando defended the officers' actions in an interview with the Associated Press, but said an internal investigation would be conducted to make sure they acted appropriately. "He apparently asked several questions -- he went on for quite awhile -- then he was asked to stop," Orlando said of Meyer. "He had used his allotted time. His microphone was cut off, then he became upset." Typically, hecklers and aggressive questioners are handled informally at political events. Shouts of "boo" or political chants drown out someone who dominates a forum, and peer pressure normally is enough to regain order. But sometimes, law-enforcement officials take a more aggressive tack. During the 2004 campaign, protesters were occasionally ushered off of the premises by Secret Service officers assigned to protect President Bush. In one incident, in West Virginia in July 2004, two protesters at a Bush event say they were arrested for refusing to cover up their anti-Bush T-shirts. In another, post-campaign incident that drew wide publicity, two people were ejected from a presidential event in March 2005 in Denver. In a lawsuit, they claim they were kicked out even before the president arrived because they drove up in a car with a bumper sticker that said, "No more blood for oil." In this year's presidential race, security has been a major concern early on. One candidate, Sen. Hillary Rodham Clinton, D-N.Y., gets Secret Service protection because of her status as a former first lady, while another, Sen. Barack Obama, D-Ill., has been assigned protection because of concerns over his safety. Kerry, who was the Democrats’ nominee in 2004, is no longer assigned Secret Service protection, and does not bring his own security to events. That left University of Florida police in charge of security -- to notable results on Monday. http://blogs.abcnews.com/politicalra...ts-rally-.html  Colbert: Today's Kids Don't Know How to Help Except by Linking Mike Aivaz and Muriel Kane Stephen Colbert added his own slant to the story of a University of Florida student tasered by campus police after he became obnoxious in asking questions following a John Kerry speech. "Look at these guys in the back," Colbert said, highlighting one frame from the video of the event. "You don't need a Fox body language expert to tell you that kid in orange is bored. He's probably thinking something like, 'I wish they'd stop tasering this guy so I could go home and watch this guy getting tasered on YouTube.'" "I don't know whether the tasered gentleman had a legitimate point to make or was just being an ass," continued Colbert. "One thing you can't argue is that his cause was joined by hordes of no one. ... Students used to be a rebellious bunch. ... Today's kids are so different." "The kids in that auditorium who sat idly by as their fellow student was seized, thrown to the ground, and tasered didn't lack the courage to help," Colbert went on. "They're just so used to watching videos like 'Crazy guys thrown out of lecture hall' that they didn't know how to help other than to link to it. I'm sure that guy in the orange is going to spring into action as soon as he gets home and fires up his blog." "And that's what's so great about this new kind of activism," Colbert concluded. "It's convenient. Just like masturbation. It's better than sex because it's on your own time. So ... make me proud, young people. Continue waging your protests from the polite distance of your home computers. Make 'the Man' wish he'd never visited your site. And if a fellow-student is denied the right to speak, remember, the best way to stand shoulder-to-shoulder with him is by sitting alone in your seat." http://rawstory.com/news/2007/Colber..._how_0920.html  Sieg Rupert Fox Anchor: 'Officers Should be Commended' for Tasering Student David Edwards and Jason Rhyne Weighing in with his legal opinion regarding police officers' tasering of a University of Florida student, attorney and Fox News anchor Gregg Jarrett said no excessive force was used during the incident. "He is resisting. And the videotape really doesn't lie--it speaks volumes about what's going on," said Jarrett, referring to video of the event that is circulating around the internet. "The law doesn't allow you to resist police officers when they ask you to do something," he added. The tasered student, Andrew Meyer, was wrestled to the ground by officers after asking Sen. John Kerry a question during a school forum. "Now you may have a beef with them being there in the first place and trying to escort you out--you can argue that later--but when they ask you to do something, you have to do it. That's the law," Jarrett said. Reviewing the videotape of the arrest, which played throughout the interview, Jarrett pointed to moments that he says show Meyer is clearly resisting arrest. "There he is raising his arms," he said as he watched. "Yeah he may be saying 'I'm not doing anything,' but he is...he is repeatedly resisting." Asked about an eyewitness report of the incident reported earlier in the segment, which indicated Meyer may have told officers he would cooperate if they let him stand up, Jarrett was incredulous. "Why should they believe him?" the anchor asked. "He has already demonstrated in the previous minute that he is not going to do what he says he's going to do." The tasering, according to Jarrett, was good police protocol."The taser device actually is a method by which you decrease the level of force by subduing somebody, not increasing the level of force...these police officers out to be commended for what it is they did." Regarding the possibility of future lawsuit from Meyer, Jarrett said the student didn't have a case, adding that no jury would sympathize with him as he was being "utterly obnoxious." Earlier in the program, witness Matthew Howland, who was on the scene during the scuffle, said at one point Meyer told officers he'd cooperate. "Andrew said 'I'm not resisting. If you let me up, I'll walk out of here with you right now," Howland told Fox. " But they kept him on the ground and about 20 seconds later they tased him." Howland later said that after the tasing, Meyer was taken to the lobby of the auditorium, where police asked for his name and other information--requests the student refused. "He doesn't give up his information like his name because he says he's scared--he doesn't want to give them any more information." http://rawstory.com//news/2007/Fox_a...nded_0918.html  Cheney Jumps Into Fray Over MoveOn Ad Katharine Q. Seelye The controversy over MoveOn.org’s ad in The New York Times entered its second week yesterday as Vice President Dick Cheney joined the fray.Mr. Cheney, defending Gen. David H. Petraeus, commander of American forces in Iraq and the object of MoveOn’s ad, said: “The attacks on him by MoveOn.org in ad space provided at subsidized rates in The New York Times last week were an outrage.” Apart from condemning MoveOn, critics have accused The Times of showing a liberal bias by agreeing to run MoveOn’s ad, which asked: “General Petraeus or General Betray Us?” They have also said the paper gave MoveOn favored treatment by charging it a “discount” rate, even though it ran the ad on the day that MoveOn wanted, which should have cost it more, and by giving the ad top positioning. Steph Jespersen, director of advertising acceptability at The Times, said that accepting an ad “does not in any way reflect the official position of The New York Times nor do we need to agree or endorse our advertiser’s message or opinion.” He said that the advertising department accepts ads from across the political spectrum and accepted the MoveOn ad, because it met the department’s standards. The group was charged the paper’s normal rate for stand-by ads. “We only decline or alter an opinion ad when the message is clearly discriminatory, illegal, libelous or hate speech,” Mr. Jespersen said in an online conversation with Times readers. He said in a telephone interview later that in the MoveOn ad, the phrase “betray us” was posed as a question and was therefore not perceived as libelous. He also said in his online conversation that the advertising department accepted the ad “because it is our ongoing desire to keep our advertising columns as open as possible to the public, which we believe is a First Amendment responsibility.” MoveOn has said it paid $65,000 for the ad. While The Times does not discuss its fees for specific ads, it has said it charges $65,000 for full-page, black-and-white “advocacy” ads that run on a seven-day “standby” basis. That means that while the client can express a preference that the ad run on a certain day, there is no guarantee that it will. If a client specifies the day, the cost is higher: $181,000 with an 8 percent discount for a full-page ad, or about $167,000. “The lower cost of such ads reflects the flexibility that gives us,” Mr. Jespersen said of the seven-day window. “Any political or advocacy group calling up today to request a standby ad would be quoted the same rate that MoveOn.org paid.” Rudolph W. Giuliani, a Republican presidential candidate who is among those who criticized the MoveOn ad, paid the same rate for his own advocacy ad that ran in the Friday editions of The Times. The price is even less, about $51,000, if an advertiser will accept a 14-day window in which an ad might run. The Times offers about 30 different prices for ads, depending on their size, placement, color, timing and whether the advertiser is a high-volume customer. There are no “standby” rates for color ads because the presses cannot accommodate color on short notice. Critics have said that the MoveOn ad, which ran last Monday, was not subject to “standby” rules because it used the word “today” in the text, suggesting advance knowledge that the ad would run on Monday, when General Petraeus began his testimony to Congress. But Mr. Jespersen said that the advertising department routinely notifies advertisers a day in advance that the ad will run in the next day’s paper. And at that point, he said, “the advertiser can make minor changes in the text.” The Giuliani campaign was notified the day that it sought to place its ad that it would be running the next day. Among the critics has been the American Spectator, which wrote: “The New York Times in the past has rejected ‘advocacy’ ads from Swift Boat Veterans for Truth, as well as from the National Right to Life Committee, despite the fact that both would have qualified for the same ‘special advocacy, stand by’ rates.” Mr. Jespersen said in the telephone interview that the advertising department had rejected a right-to-life ad because it contained an illustration that did not meet the paper’s standards of taste. “It had nothing to do with the message of the group,” he said. As for the Swift Boat veterans group, which in the 2004 presidential campaign questioned Senator John Kerry’s military record, it never tried to place an ad with The New York Times, according to Mike Russell, communications director for the Swift Boat group. “There was never an effort to mock up an ad for The New York Times and there was never any refusal for any ad copy because none was submitted,” Mr. Russell said. Mr. Jespersen estimated that the advertising department turns down perhaps two or three percent of ads that are submitted each year. The department usually explains why the ad is rejected, he said, and the advertiser sometimes makes changes to meet the standards. Critics have also complained that MoveOn received favored treatment because its ad was put in a “top spot” in the newspaper. The ad ran on page 25 of the A section; Mr. Giuliani’s ad ran on Page 9 of the A section. Advertisers generally consider the front of a section or back of a section to be the most valuable spot in papers like The Times, which does not run ads on its front page. The next-most valuable spot is Page 3 of the A section, which is the first inside page that most readers see. In The Times, that spot has long been occupied by Tiffany. http://thecaucus.blogs.nytimes.com/2.../index.html?hp  Working hard in Washington Senate Condemns Ad Nick Juliano The Senate voted by a wide margin Thursday to condemn a controversial anti-war advertisement accusing Gen. David Petraeus of betraying the country. Only 24 Democrats, including presidential candidate Hillary Clinton, voted against the symbolic resolution. Sen. Barack Obama (D-IL) and Sen. Joe Biden (D-DE), both of whom also are seeking their party's presidential nomination, joined Sen. Maria Cantwell (D-WA) in declining to take a position for or against the MoveOn ad. Since last Monday, when the "General Petraus or General Betray Us?" ad ran on a full page of the New York Times, Republicans have launched relentless attacks on MoveOn and any Democrats who refused to outright condemn the ad's message. "The focus of the United States Senate should be on ending this war, not on criticizing newspaper advertisements," Obama said. "This amendment was a stunt designed only to score cheap political points while what we should be doing is focusing on the deadly serious challenge we face in Iraq. It's precisely this kind of political game-playing that makes most Americans cynical about Washington's ability to solve America's problems. By not casting a vote, I registered my protest against this empty politics. I registered my views on the ad itself the day it appeared." In a statement released Thursday Obama continued, "All of us respect the service of General Petraeus and all of our brave men and women in uniform. The way to honor that service is to give them a mission that is responsible, not to vote on amendments like the Cornyn amendment while we continue to pursue the wrong policy in Iraq." President Bush entered the fray himself Thursday, calling the ad "disgusting" and an attack on the military. Sen. Gordon Smith, a Republican who favors a timetable for removing US troops from Iraq, blamed the MoveOn ad for keeping Republicans aligned with the White House in voting against measures to de-escalate the war. "It was stupid on their part and disgraceful," the Oregon Republican told the Associated Press. Thursday's Senate resolution was sponsored by conservative Sen. John Cornyn (R-TX). who took time away from questioning Petraeus to condemn the ad as "reprehensible slander" during a Senate hearing last Tuesday. Earlier Thursday Sen. Barbara Boxer (D-CA) introduced a resolution that would've condemned all attacks on troops and veterans, including those from MoveOn and conservative groups that disparaged former Sen Max Cleland and John Kerry in 2002 and 2004. That resolution fell nine short of the 60 votes needed to end debate on it. Obama voted in favor of that measure, an hour before the vote on Cornyn's bill he skipped. In substantive votes Thursday, Democrats failed to attract enough Republican supporters to end a filibuster on Sen. Jim Webb's amendment to a defense spending bill that would have given US troops as much time at home as they are stationed in a warzone. Currently some troops are subject to 15-month tours of duty with only a year off in between. Webb was among the Democrats who supported the measure condemning MoveOn. http://rawstory.com//news/2007/Democ...veOn_0920.html  The President Of Hypocrisy Logan Murphy In light of President Bush’s disgraceful presser today, Keith Olbermann decided to make a Special Comment on tonight’s Countdown and wow, did he make the most of it. Olbermann blasts the president for his cowardly and un-American behavior of pimping General Petraeus as a political hack and hiding behind him to deflect criticism. To say that Keith took the president to the woodshed would be an understatement: So the President, behaving a little bit more than usual, like we’d all interrupted him while he was watching his favorite cartoons on the DVR, stepped before the press conference microphone and after side-stepping most of the substantive issues like the Israeli raid on Syria in condescending and infuriating fashion, produced a big-wow political finish that indicates, certainly, that if it wasn’t already — the annual Republican witch-hunting season is underway. “I thought the ad was disgusting. I felt like the ad was an attack not only on General Petraeus, but on the U.S. Military. “And I was disappointed that not more leaders in the Democrat party spoke out strongly against that kind of ad. “And that leads me to come to this conclusion: that most Democrats are afraid of irritating a left-wing group like Move-On-Dot-Org — or **more** afraid of irritating them, than they are of irritating the United States military.” “That was a sorry deal.” First off, it’s “Democrat-ic” party, sir. You keep pretending you’re not a politician, so stop using words your party made up. Show a little respect. Secondly, you could say this seriously after the advertising/mugging of Senator Max Cleland? After the swift-boating of John Kerry? But most importantly… making that the last question? So that there was no chance at a follow-up? So nobody could point out — as Chris Matthews so incisively did, a week ago tonight — that you were the one who inappropriately interjected General Petraeus into the political dialogue of this nation in the first place! Deliberately, premeditatedly, and virtually without precedent, you shanghaied a military man as your personal spokesman — and now you’re complaining about the outcome, and then running away from the microphone? Eleven months ago the President’s own party — the Republican National Committee — introduced this very different kind of advertisement, just nineteen days before the mid-term elections. Bin Laden. And Zawahiri’s rumored quote of six years ago about having bought “suitcase bombs.” All set against a ticking clock, and finally a blinding explosion… and the dire announcement: “These are the stakes - vote, November 7th.” That one was ok, Mr. Bush? Terrorizing your own people in hopes of getting them to vote for your own party has never brought as much as a public comment from you? The Republican Hamstringing of Captain Max Cleeland and lying about Lieutenant John Kerry met with your approval? But a shot at General Petraeus — about whom you conveniently ignore it is you who reduced him from four-star hero to a political hack — that merits this pissy juvenile blast at the Democrats on national television? Your hypocrisy is so vast, sir, that if we could somehow use it to fill the ranks in Iraq you could realize your dream — and keep us fighting there until the year 3000. The line between the military and the civilian government is not to be crossed. When Douglas MacArthur attempted to make policy for the United States in Korea half a century ago, President Truman moved quickly to fire him, even though Truman knew it meant his own political suicide, and the deification of a General who history suggests had begun to lose his mind. When George McClellan tried to make policy for the Union in the Civil War, President Lincoln finally fired his chief General, even though he knew McClellan could galvanize political opposition - as he did… when McClellan ran as Lincoln’s presidential opponent in 1864 and nearly defeated our greatest president. Even when the conduit flowed the other way and Senator Joseph McCarthy tried to smear the Army because it wouldn’t defer the service of one of McCarthy’s staff aides, the entire civilian and Defense Department structures — after four years of fearful servitude — rose up against McCarthy and said “enough” and buried him. The list is not endless — but it is instructive. Air Force General LeMay — who broke with Kennedy over the Cuban Missile Crisis — and was retired. Army General Edwin Anderson Walker — who started passing out John Birch Society leaflets to his soldiers. Marine General Smedley Butler — who revealed to Congress the makings of a plot to remove FDR as President — and for merely being approached by the plotters, was phased out of the military hierarchy. These careers were ended because the line between the military and the civilian is… not… to… be… crossed! Mr. Bush, you had no right to order General Petraeus to become your front man. And he obviously should have refused that order and resigned rather than ruin his military career. The upshot is — and contrary it is, to the MoveOn advertisement — he betrayed himself more than he did us. But there has been in his actions a sort of reflexive courage, some twisted vision of duty at a time of crisis. That the man doesn’t understand that serving officers cannot double as serving political ops, is not so much his fault as it is your good, exploitable, fortune. But Mr. Bush, you have hidden behind the General’s skirts, and today you have hidden behind the skirts of ‘the planted last question’ at a news conference, to indicate once again that your presidency has been about the tilted playing field, about no rules for your party in terms of character assassination and changing the fabric of our nation, and no right for your opponents or critics to as much as respond. That, sir, is not only un-American — it is dictatorial. And in pimping General David Petraeus, sir, in violation of everything this country has been assiduously and vigilantly against for 220 years, you have tried to blur the gleaming radioactive demarcation between the military and the political, and to portray your party as the one associated with the military, and your opponents as the ones somehow antithetical to it. You did it again today, sir, and you need to know how history will judge the line you just crossed. It is a line — thankfully only the first of a series — that makes the military political, and the political, military. It is a line which history shows is always the first one crossed when a democratic government in some other country has started down the long, slippery, suicidal slope towards a military junta. Get back behind that line, Mr. Bush, before some of your supporters mistake your dangerous transgression, for a call to further politicize our military. — Good night, and good luck. http://www.crooksandliars.com/2007/0...-of-hypocrisy/  Terrorist Leader Threatens to Behead Madonna, Britney Spears TomZ While Osama bin Laden is busy pushing back the release of his new video like it were Chinese Democracy, another terrorist leader is stepping up to the plate to fill the void of dickheaded threats. Muhammed Abdel-Al has released a brand new book called -- and I swear I couldn't make this title up -- Schmoozing With Terrorists: From Hollywood to the Holy Land Jihadists Reveal their Global Plans - to a Jew! Abdel-Al is spokesman and senior leader of The Popular Resistance Committees, a Palestinian terrorist group based in the Gaza Strip. It's really only one committee, but no one has the guts to tell him. In his book, Abdel-Al calls Madonna and Britney Spears "prostitutes" and threatens to behead the pop singers. Here is an excerpt (via NME): If I meet these whores I will have the honor - I repeat, I will have the honor - to be the first one to cut the heads off Madonna and Britney Spears if they will keep spreading their satanic culture against Islam. If these two prostitutes keep doing what they are doing, we of course will punish them. Now, few people know this, but I'm actually a Palestinian terrorist leader in my spare time. It's a thankless job, but what can I say, my hot tub doesn't pay for itself. Anyway, I wanted to release the following statement as a follow-up to Abdel-Al's message: As my colleague Muhammed Abdel-Al has so beautifully illustrated, pop stars like Madonna and Britney Spears are spreading the message of Satan to the unsuspecting masses. Because people have no choice over what they watch and listen to -- at least that's how it is within my organization, so I assume such is the case with the rest of the planet -- the population is being destroyed by the illicit, Satanic ways of Madge and Brit-Brit. Also, did you see the Video Music Awards? Britney looked soooo skanky in that outfit. I would love to have the great privilege of beheading these harlots, should our paths one day cross. And hopefully they will, cause I'm totally going to Britney's comeback tour. I mean, I can't afford the Ticketmaster surcharges (curses to those heathens as well, LOL!), but I'm hoping maybe I can finagle something off Stubhub. Anyhoo, where was I? Oh yeah, Britney's new single is mediocre at best... and death to invalids! Now, if you'll excuse me, I have to go strap a bomb to a six year old. Peace, playa! http://www.shoutmouth.com/index.php/...itney_Spea rs  Britney Spears Calls Herself a 'Fat Pig' TomZ After her disasterous performance at the Video Music Awards this past Sunday night, Britney Spears took a lot of heat for looking out of shape. According to US Weekly, Britney herself may agree with this sentiment. US claims that, after completing her performance and walking offstage, Britney said, "Oh, my God, I looked like a fat pig! I looked like a fat pig!" Britney's problems at the VMA's may be her own fault. Allegedly, Britney chose her own outfit, and yelled at her hairstylist, causing him to quit just 30 minutes before the VMA's started. Also, it seems that Britney passed on the chance to share the VMA stage with Justin Timberlake. Producer and frequent Timberlake collaborator Timbaland told MTV that a Britney-Justin performance would have been "the best thing that ever happened" and would "help her out a whole lot." He added: It'll never happen. Nah. It could've, but it won't. Timbaland went on to offer some career advice for Spears: She needs a story. She has no comeback story. That's the problem. She has to have a team. She needs to come back with Justin doing records; [then we'd see headlines like,] 'She went back to her ex and she's making smashes.' [But instead she got] so big-headed and [was] like, 'Screw you, screw you, I don't need nobody.' She should humble herself and make a phone call and say, 'I'm sorry.' She knows what she's sorry about. She needs to say, 'I was wrong,' and it'll definitely move forward. That's all she has to say. This explains a lot. It looked like the VMA's were thrown together the night before. Hell, I've been to beer pong tournaments that were more well planned out. But perhaps it wasn't MTV's fault. Maybe they had a plan, but Spears refused to participate in that plan. Who knows? That would make sense, though. Spears recently fired her manager, and she's launching her "comeback" attempt when many people think she should take some time off. Now she's turning down Justin Timberlake collaborations and firing her hairstylist? It's highly possible that she just does whatever she wants, regardless of others' advice. When is the last time someone said "no" to her about anything? Someone needs to step up and say "listen bitch, you're embarrasing yourself, now shut up and follow the plan that your record label and management have laid out for you so you don't end up looking like a two-dollar stripper on Xanax on national TV again." OK, maybe they should phrase it differently, but you get the point. As for the "fat" thing, I may be in the minority here, but I think Spears looked fine. Sure, she was thicker as compared to old Britney Spears (i.e., "The Snake"), but if you put her on the street with a random collection of girls, she still would have been 95th percentile. I would challenge any female from US Weekly or any other tabloid to put on those same clothes and dance around on stage, and we'll see how they look. (This isn't to prove a point. I just want to see more girls dancing around in stripper clothes.) http://www.shoutmouth.com/index.php/news/Britney_Spears_Calls_Herself_a_'Fat_Pig'  25 Million People Register for Led Zeppelin Reunion Gig DirtySouthMouth Guess what? People love Led Zeppelin. NME.com says the group is so well loved that the website to register for reunion show tickets received 120 million hits yesterday after registering 25 million people for the ticket ballot. For the record, that's more than three times the population of London. Tickets for the show will be randomly allocated using the ballot system. Registration is open until Monday, September 17, at noon and there will be 20,000 tickets available beginning at around $250 a piece. Winning registrants will be informed after October 1. As for the show, it is set for November 26, including sets from Pete Townshend, Foreigner and Paolo Nutini. Bill Wyman and The Rhythm Kings will back up all three of those acts and will play its own set. The show is a tribute to late Atlantic Records founder Ahmet Ertegun and money from the show will be for the Ahmet Ertegun Education Fund, which pays for scholarships in the UK, US and Turkey. Here's what Robert Plant had to say about Ertegun: During the Zeppelin years, Ahmet Ertegun was a major foundation of solidarity and accord. For us he was Atlantic Records and remained a close friend and conspirator. His performance stands alone as our tribute to the work and the life of our long-standing friend. http://www.shoutmouth.com/index.php/...in_Reunion_Gig May Add Second Show If you didn't click your way into the registration process for those Led Zeppelin tickets, don't get too bent out of shape. Rumors are swirling that a second show might be in the works. Plus, isn't Jason Bonham kind of not as good as John Bonham? According to some reports, the Led Zeppelin frontman is trying to convince the other members in the band to play a show in Belfast at Ulster Hall. The venue is looking for a band to christen its reopening on November 2008 and Plant would like to oblige. The venue is known as the place the band debuted "Stairway To Heaven" in 1971, a debut that was celebrated at a 1996 25th anniversary party in the venue. Ticket registration for the band's November 26 show at London's O2 Arena ended today, September 19, at noon BST. The registration was opened for an additional 48 hours after demand for tickets crashed the registration site. So, keep your fingers crossed and your browsers open for the Belfast show. http://www.shoutmouth.com/index.php/...d_Reunion_Show  Stars Join Forces to Salute (and Support) a Rock Legend  Robert Plant and Fats Domino Nate Chinen One Saturday night in May, Fats Domino took the stage before a full house at Tipitina’s, the club that has become, like him, a New Orleans institution. His half-hour set made headlines for a few reasons. It was Mr. Domino’s first show since Hurricane Katrina hit in 2005. It was a benefit for the Tipitina’s Foundation, a nonprofit organization devoted to restoring the city’s musical culture and helping its musicians. Besides that, it was Fats Domino, and these days that’s more than reason enough. Mr. Domino, 79, made many of the rhythm-and-blues hits that laid the groundwork for rock ’n’ roll. He’s also something of a recluse, and a perfectionist known to cancel appearances without warning or cause. Yet he is still a presence in the city he has always called home. “For lack of a better way of putting it,” Irma Thomas, known as the Soul Queen of New Orleans, said recently, “he’s a living, walking legend among us in New Orleans. Between him and Louis Armstrong, they were the first big names to put us on the musical map.” On Sept. 25, Vanguard Records will release “Goin’ Home: A Tribute to Fats Domino,” making use of some other big names, including B. B. King, Paul McCartney, Robert Plant, Willie Nelson, Neil Young and Norah Jones. They appear alongside New Orleans heroes like Dr. John and Allen Toussaint. The foundation will dedicate a portion of the proceeds to the renovation of Mr. Domino’s publishing office, adjacent to his spacious house in the Lower Ninth Ward, which was severely damaged by the flooding after Katrina. He had to be rescued by helicopter from his home; he lost several pianos and most of his possessions, and looters stole most of his gold records from the 1950s. Of course, even without the flood it would not have been hard to rally support for Mr. Domino. “He’s been around all this time, and I’ve never read or heard anything bad about him,” Mr. King said recently. “And as far as I’m concerned, he’s just a great musician, and a lovable person.” “Goin’ Home” arrives roughly one year after “Alive and Kickin’,” Mr. Domino’s first album in more than a decade, which was also released as a benefit for the Tipitina’s Foundation. “He really wanted to put it out through our organization,” said Bill Taylor, the foundation’s executive director. “He was aware of what we were doing, and he reached out to us.” Over a bowl of gumbo at Cochon, a Cajun restaurant in the warehouse district, Mr. Taylor described the process behind “Goin’ Home,” for which he receives credit as executive producer. “The first hurdle was that I had no idea what I was doing,” he said. “I had never done anything like this.” But Mr. Taylor set his sights high from the start: his first request was to Yoko Ono, to use a version of “Ain’t That a Shame” that John Lennon recorded in 1973. “Within like a week, she gave us permission,” he said. “Then Elton John signed on next. And at that point there was enough star power behind it that the dominoes started falling pretty quick.” (His domino metaphor did not seem intended as a pun.) With more than 30 tracks, recorded not just in New Orleans but in places like Los Angeles, Las Vegas and Kingston, Jamaica, the album presented some fearsome logistics. Further complicating matters was Mr. Taylor’s decision to feature New Orleans musicians. In the spirit of the tribute concerts that followed Katrina, “Goin’ Home” includes novel pairings like Joss Stone and Buddy Guy with the Dirty Dozen Brass Band; Mr. King with Ivan Neville’s Dumpstaphunk; and Lenny Kravitz with the Rebirth Brass Band. Mr. Taylor often paired songs with artists. Elton John is a natural on “Blueberry Hill,” as are Tom Petty on “I’m Walkin’ ” and Randy Newman on “Blue Monday.” Los Lobos offer a solid update of “The Fat Man,” one of the earliest rock ’n’ roll records. Mr. McCartney does his best Fats impression on “I Want to Walk You Home,” backed by Mr. Toussaint on piano. More than a few of the album’s tracks came together serendipitously. Mr. Plant had agreed to record a track with the Cajun group Lil’ Band o’ Gold, but when he arrived in New Orleans the acclaimed Soweto Gospel Choir was headlining at Tipitina’s. A meeting was arranged, and Mr. Plant also recorded “Valley of Tears” with the choir, in a hushed style that calls Paul Simon’s “Graceland” to mind. “So you have the Led Zeppelin guy with a South African gospel choir doing a Fats Domino song,” Mr. Taylor said. “It’s an example of what happens here musically every day.” On Sept. 29, some of the album’s local luminaries, including Ms. Thomas, Dumpstaphunk and Big Chief Monk Boudreaux of the Mardi Gras Indians, will play at a release party at Tipitina’s. Like the album, the show will celebrate not just Mr. Domino’s legacy but also the remarkable songwriting partnership he enjoyed with the trumpeter Dave Bartholomew. Mr. Domino, who now lives in Harvey, La., in a gated community on the west bank of the Mississippi River, rarely gives interviews, though he has said he was honored by “Goin’ Home.” But in one of the chance coincidences that seem to happen often in New Orleans, a reporter on his way to the airport in a taxicab lucked into what passes for an interview with Mr. Domino. The driver, Walter Miles, turned out to be Mr. Domino’s chauffeur. “I drive him all over,” he said. “We talk to each other two or three times a day.” With that, Mr. Miles dialed a number on his cellphone and passed the phone to the back seat. There was Mr. Domino, with his unmistakable New Orleans drawl. What followed was less an interview than genial small talk. “Where you from?” he asked, getting right to the heart of the matter. http://www.nytimes.com/2007/09/22/ar...ic/22fats.html  Researchers Improve Ability to Write and Store Information on Electronic Devices New research led by the U.S. Department of Energy's Argonne National Laboratory physicist Matthias Bode provides a more thorough understanding of new mechanisms, which makes it possible to switch a magnetic nanoparticle without any magnetic field and may enable computers to more accurately write and store information. Bode and four colleagues at the University of Hamburg used a special scanning tunneling microscope equipped with a magnetic probe tip to force a spin current through a small magnetic structure. The researchers were able to show that the structure's magnetization direction is not affected by a small current, but can be influenced if the spin current is sufficiently high. Most computers today use dynamic random access memory, or DRAM, in which each piece of binary digital information, or bit, is stored in an individual capacitor in an integrated circuit. Bode's experiment focused on magneto-resistive random access memory, or MRAM, which stores data in magnetic storage elements consisting of two ferromagnetic layers separated by a thin non-magnetic spacer. While one of the two layers remains polarized in a constant direction, the other layer becomes polarized through the application of an external magnetic field either in the same direction as the top layer (for a "0") or in the opposite direction (for a "1"). Traditionally, MRAM are switched by magnetic fields. As the bit size has shrunk in each successive generation of computers in order to accommodate more memory in the same physical area, however, they have become more and more susceptible to "false writes" or "far-field" effects, Bode said. In this situation, the magnetic field may switch the magnetization not only of the target bit but of its neighbors as well. By using the tip of the Scanning Tunneling Microscope (STM), which has the potential to resolve structures down to a single atom, the scientists were able to eliminate that effect. Bode and his colleagues were the first ones who did such work with an STM that generates high spatial-resolution data. "If you now push just a current through this bit, there's no current through the next structure over," Bode said. "This is a really local way of writing information." The high resolution of the STM tip might enable scientists to look for small impurities in the magnetic storage structures and to investigate how they affect the magnet's polarization. This technique could lead to the discovery of a material or a method to make bit switching more efficient. "If you find that one impurity helps to switch the structure, you might be able to intentionally dope the magnet such that it switches at lower currents," Bode said. Results of this research were published in the September 14 issue of Science and related research was published earlier this year in Nature. Funding for this work was provided by Deutsche Forschungsgemeinschaft and the European Union project ASPRINT. This work was conducted prior to Bode's arrival at Argonne. His research at Argonne will be predominately funded by DOE's Office of Basic Energy Sciences. With employees from more than 60 nations, Argonne National Laboratory brings the world's brightest scientists and engineers together to find exciting and creative new solutions to pressing national problems in science and technology. The nation's first national laboratory, Argonne conducts leading-edge basic and applied scientific research in virtually every scientific discipline. Argonne researchers work closely with researchers from hundreds of companies, universities, and federal, state and municipal agencies to help them solve their specific problems, advance America 's scientific leadership and prepare the nation for a better future. Argonne is managed by UChicago Argonne, LLC for the U.S. Department of Energy's Office of Science. http://www.newswise.com/articles/view/533374/?sc=swtn  Intel Previews a New Family of Power-Saving Chips Laurie J. Flynn Intel gave the first public demonstration on Tuesday of a new generation of computer processors that significantly increase performance without consuming more power. The company’s chief executive, Paul S. Otellini, told developers at its semiannual technology conference that Intel expected to finish the new family of chips in the second half of 2008, in keeping with its promise of a new chip architecture every other year. The new family of chips, code-named Nehalem, will use as many as eight processing cores and will offer better graphics and memory-control processing. Intel had been late to respond to technological challenges in energy efficiency and heat consumption, and it has spent the better part of two years racing to catch up with its smaller but feisty competitor, Advanced Micro Devices. A year ago, Intel announced a painful corporate overhaul, including a round of cost-cutting that reduced the work force by 10 percent and trimmed $5 billion in expenses. Since then, the company has begun to regain lost market share, and last week raised its sales forecast for this quarter. As part of the corporate revamping, Intel executives last year outlined what they called a tick-tock strategy, referring to the development of a new chip architecture every other year and to a new manufacturing technology in the alternate years. Mr. Otellini said the strategy would accelerate the pace of innovation. The manufacturing-technology innovation, a new silicon technology component, is almost ready. Intel’s Penryn family of processors, to be introduced on Nov. 12, will be the industry’s first high-volume 45-nanometer processors. (the current standard is 65 nanometers.) Mr. Otellini said the company planned to introduce 15 new 45-nanometer processors by the end of the year and 20 more in the first quarter of 2008. A.M.D. has said it will move to 45-nanometer technology in mid-2008. “We expect our Penryn processors to provide up to a 20 percent performance increase while improving energy efficiency,” Mr. Otellini said. He said that 32-nanometer technology, which is on track to begin production in 2009, would offer even greater performance. The 32-nanometer chips use transistors so small that more than 4 million of them could fit on the head of a pin. “Smaller is better, smaller is cheaper,” Mr. Otellini said. The company also disclosed plans for a new graphics-oriented product, called Larrabee, which will compete with products from Advanced Micro Devices and Nvidia and Advanced Micro’s ATI graphics unit. Larrabee will include 12 cores, or computing brains. On Monday, A.M.D. unveiled its own strategic change: a desktop chip with three cores, unusual in an industry that tends to grow in even numbers, routinely doubling performance. The announcement came as a surprise to analysts, as the company had promoted the advantages of four processors only last week. A.M.D. executives, referring to a recent survey by Mercury Research, said that quad-core processors accounted for only 2 percent of all desktop computer systems, suggesting that they had been slower to catch on than expected. It is hoping that its new three-core chip, called Phenom, will appeal to midrange customers who are looking for better performance than dual-core systems can provide, but do not see the need for quad-core systems. A corporate vice president, Robert Brewer, predicted that “it’s naturally going to resonate with customers,” who he said would appreciate having another choice. But Nathan Brookwood, principal analyst with Insight 64, a consulting firm in Saratoga, Calif., said the triple-core chip could prove confusing to customers. It is due in the first quarter of 2008, the quarter after Advanced Micro is scheduled to release its quad-core chip. In some cases, the triple-core chip may actually perform faster than a quad core. http://www.nytimes.com/2007/09/19/te...gy/19chip.html  USB 3.0 Brings Optical Connection in 2008 Stephen Shankland Intel and others plan to release a new version of the ubiquitous Universal Serial Bus technology in the first half of 2008, a revamp the chipmaker said will make data transfer rates more than 10 times as fast by adding fiber-optic links alongside the traditional copper wires. Intel is working fellow USB 3.0 Promoters Group members Microsoft, Hewlett-Packard, Texas Instruments, NEC and NXP Semiconductors to release the USB 3.0 specification in the first half of 2008, said Pat Gelsinger, general manager of Intel's Digital Enterprise Group, in a speech here at the Intel Developer Forum. In an interview after the speech, Gelsinger said there's typically a one- to two-year lag between the release of the specification and the availability of the technology, so USB 3.0 products should likely arrive in 2009 or 2010. A prototype shown at the speech is working now, and USB 3.0 will have optical and copper connections "from day one," he added. The current USB 2.0 version has a top data-transfer rate of 480 megabits per second, so a tenfold increase would be 4.8 gigabits per second. Many devices don't need that much capacity, but some can use more, including hard drives, flash card readers and optical drives such as DVD, Blu-ray and HD DVD. The fastest flash card readers today use IEEE 1394 "FireWire" connections that top out at 800 megabits per second. In addition, USB 3.0 will offer greater energy efficiency, Gelsinger said. It will be backward compatible, so current USB 2.0 devices will be able to plug into USB 3.0 ports. http://www.news.com/8301-10784_3-9780794-7.html  How Computers Transformed Baby Boomers Computers once filled entire rooms. Now they fit in our pockets. How a generation formed our tech landscape. Steven Levy This summer I was talking to some young Google employees, and at one point the conversation somehow turned to the antediluvian document-creation processes of an older generation: mine. So I (born 1951) told these twentysomethings that there was a time when people wrote on machines called typewriters, beginning at the beginning and plowing through until the end, at which point they would mark up the manuscript with pen or pencil for the next run through the typewriter. If there was a need to recast a couple of sentences or even an entire paragraph, you would type on a new sheet of paper, cut the new text from the page with scissors and use Elmer's glue to paste it over the original not-so-hot lines. "Oh!" said one of the Googlers, of 1980s vintage. "So that's where 'cut-and-paste' came from!" The moment neatly captured the gap between the world that boomers grew up in and the inescapably digital world of today. Those in the postwar generation once rolled their eyes when its parents or grandparents would spin Lincoln-esque coming-of-age anecdotes that hinged on the absence of television, interstates and air conditioning. But now they find themselves spanning perhaps the biggest technological divide in history. "There certainly were big earlier transformations like the automobile, radio and TV, so it would be hard to say the previous generation had a static environment," says Microsoft cofounder Bill Gates. "But you can actually keep a straight face and say the amount of change in these last 30 years has been greater." No, we don't have flying cars, we don't talk philosophy with robots and our meals do not consist of colored capsules containing all we need to survive. But we do have robots sweeping the floor and a chess machine that whupped the world's greatest human player. And we have Microsoft Office, instant messaging, DVDs, iPods, BlackBerrys, Amazon, eBay, Google and credit cards that pay for chewing gum by means of infrared waves. The big news is digital: an amazing amount of stuff that used to happen in the physical world can now be done virtually. Like cut-and-paste, many of the realities boomers grew up with are today's metaphors. In fact, it can be argued that the best-known baby boomer of all is the computer itself. Like many boomers, the general-purpose computer was born in the years following World War II, grew up in a restrictive environment and went batty as a young adult. Now, like the generation it grew up alongside, the computer has assumed a leadership role, while still maintaining an unruly edge. But it would be unfair to say that the computer has transformed the lives of boomers and leave it at that. The boomers themselves can take credit for shaping the course of this technology if not the entire direction of the digital revolution. Gates is among a cadre of industry pioneers now in their 50s. But several decades ago they were tech-savvy kids who seized the moment when their elders had no clue. In the 1950s, computers were like ... the 1950s. They were giant monochrome machines tended by people wearing white shirts and black ties. They filled a room and were used for tasks like accounting, codebreaking and statistical calculations. Icons of the conformist age, there was nothing personal about them. They filled up a room and cost millions of dollars. They weren't hard to use—they were impossible to use. They were tended by a sort of priesthood who jealously limited access. Even after huge breakthroughs in transistors and microprocessors in the early 1970s, those in charge of companies like IBM or Digital Equipment Corporation felt that nothing could be more absurd than a personal computer. Who could possibly want a computer of one's own? What would you use it for? In the 1960s and early 1970s, many in the counterculture absolutely loathed computers and everything about them. They were seen as part of the Defense Department's War Machine, and also associated with depersonalization of a mass society. But boomer math nerds, who figured out how to finagle computer time, didn't care. There was also a geographic exception to those political objections. In Northern California—home of the chip industry and lots of defense work—the idea arose that computers could empower people. Two texts proved to be crucial in pushing the vision toward action. The first was Ted Nelson's "Computer Lib," a messy manifesto urging enlightenment through computers. The other was the January 1975 issue of Popular Electronics, which broke the news of the first personal computer, the Altair 8800 (a primitive device that came in a kit and had no keyboard or monitor). Excitement about the Altair led political activist Fred Moore to organize a group called the Homebrew Computer Club, which first met in March 1975. It would generate dozens of companies, including Apple Computer. What really led the boomers to become pioneers of the PC revolution was a sense of possibility. "They saw the technology as mind-expanding," says John Markoff, author of "What the Dormouse Said: How the 60s Counterculture Shaped the Personal Computer Industry." "It was one of a series of quests going on, part of an attempt to break out of the confines of the suburban realities of the 1950s." That was certainly the case for Steve Jobs (born 1955), raised in the suburban Valhalla of 1960s Silicon Valley where your next-door neighbor could, and did, bring you straight-from-the-fab microchips to play with. He attended Reed College, dropped out, went to India, and wound up back in Silicon Valley, where he reconnected with his high school buddy Steve Wozniak (born 1950). Woz, as he was called, was a classic tech geek, relatively unaffected by the counterculture. When he showed Jobs the device he was working on—a computer he built to dazzle the wireheads at the Homebrew Computer Club—Jobs became his partner. Then Jobs convinced a reluctant Woz, who was married, to quit his job at Hewlett-Packard to form Apple, a company Jobs named on a whim. Naturally, the values of their generation were reflected in their approach to designing products (notably the Apple II that became the first mass-market PC) and building their company. When Jobs orchestrated the release of Apple's groundbreaking 1984 Macintosh computer, he struck the cultural chords familiar to his generation, urging people to view it not as a product but a movement. Even earlier in the game was Bill Gates (born 1955), who wasn't very political but with the help of his high school buddy Paul Allen (born 1953) put together the pieces and saw something big was about to happen. He was a Harvard sophomore in 1974 when Allen showed him that issue of Popular Electronics. "We said, 'Oh, my God, it is going to happen without us?' " and right then the two vowed to write software for the Altair. "We wrote our slogan—a very modest slogan—'a computer in every home and on every desktop—in 1975," says Gates. "We were kind of brash in a certain way." Very boomer-esque. Didn't he find it odd that people who actually ran computer companies couldn't see it that way? "There's some benefit to youth," he says. "It's a lot like physics—Einstein saw relativity, the others didn't—but then he didn't understand quantum dynamics, that next generation came along, and he became the old guard. There's something about these wild changes—a personal computer being software-centric and personal, and a software industry that was high volume and low cost—that are hard to see." And is there a more canonical boomer's tale than that of Mitch Kapor (born 1950), who majored in psychology at Yale, was heavily involved in the campus radio station, and after graduation became ... a teacher of Transcendental Meditation. But ever since he'd come across a copy of "Computer Lib" in a Harvard Square bookstore, he was fascinated by computers, particularly the promise they had to empower ordinary people. He began designing software, and then, around the time the IBM PC was launched, came out with an idea to make spreadsheets more powerful. His product was Lotus 1-2-3, and when he sought funding for his company, in a long letter to venture capitalist Ben Rosen he presented his idealistic vision of a humanitarian company. There are things as important to me as profit, he wrote. Now, he says, "It was my equivalent of 'Don't Be Evil' " [the unofficial Google motto]. Google, is only one of the more recent high-tech companies to capture our attention, our imagination and our free time. Generations following the boomer pioneers founded Internet giants like Amazon and eBay, and now another Harvard dropout, Mark Zuckerberg (born 1984), heads Silicon Valley's new heartthrob, Facebook. All have adopted the grow-fast template of the boomer pioneers. None of this would have happened if the technology itself had not ripened, and it was for the first time possible to build personal computers and write software for them. But the other element was the generational nature of its innovators. The magic was that those two factors came together, and as a result, the early lives of boomers will become as quaint to their grandchildren as the tales of the boomers' own forefathers were to them. http://www.msnbc.msn.com/id/20789352/site/newsweek/  Misleading RCMP Data Undermines Counterfeiting Claims Michael Geist My weekly Law Bytes column (Toronto Star version, Ottawa Citizen version, homepage version) focuses on the growing attention paid to counterfeiting and the use of misleading data as part of the debate. The RCMP has been the single most prominent source for claims about the impact of counterfeiting in Canada since its 2005 Economic Crime Report pegged the counterfeiting cost at between $10 to 30 billion dollars annually. The $30 billion figure has assumed a life of its own with groups lobbying for tougher anti-counterfeiting measures regularly raising it as evidence of the dire need for Canadian action. U.S. Ambassador to Canada David Wilkins cited the figure in a March 2007 speech critical of Canadian law, while the Canadian Anti-Counterfeiting Network, Canada's leading anti-counterfeiting lobby, reported in April that the "RCMP estimates that the cost to the Canadian economy from counterfeiting and piracy is in the billions." Yet despite the reliance on this figure - the Industry Committee referenced it in its final report - a closer examination reveals that the RCMP data is fatally flawed. Responding to an Access to Information Act request for the sources behind the $30 billion claim, Canada's national police force last week admitted that the figures were based on "open source documents found on the Internet." In other words, the RCMP did not conduct any independent research on the scope or impact of counterfeiting in Canada, but rather merely searched for news stories on the Internet and then stood silent while lobby groups trumpeted the figure before Parliament. A careful examination of the documents relied upon by the RCMP reveal two sources in particular that appear responsible for the $30 billion claim. First, a March 2005 CTV news story reported unsubstantiated claims by the International Anti-Counterfeiting Coalition, a global anti-counterfeiting lobby group made up predominantly of brand owners and law firms, that some of its members believe that 20 percent of the Canadian market is "pirate product." That 20 percent figure - raised without the support of any evidence whatsoever - appears to have been used by IACC to peg the cost of counterfeiting in Canada at $20 billion per year. Second, a 2005 powerpoint presentation by Jayson Myers, then the Chief Economist for the Canadian Manufacturing and Exporters, included a single bullet point that "estimated direct losses in Canada between $20 billion and $30 billion annually." The source for this claim? According to Mr. Myers, it is simply 3 to 4 percent of the value of Canada's two-way trade. Indeed, unsubstantiated and inflated counterfeiting numbers appear to be nothing new. The International Chamber of Commerce has long maintained that counterfeiting represents 5 to 7 percent of global trade (those figures were also raised before the Canadian House of Commons committees). However, a recent study by the independent U.S. Government Accountability Office found that of 287,000 randomly inspected shipments from 2000 to 2005, counterfeiting violations were only found in 0.06 percent - less than one tenth of one percent. Moreover, the GAO noted that despite increases in counterfeiting seizures, the value of those seizures in 2005 represented only 0.02 percent of the total value of imports of goods in product categories that are likely to involve intellectual property protection. Similarly, this year the Organization for Economic Co-operation and Development (OECD), which counts most industrialized countries as members, issued a comprehensive report on counterfeiting that placed the global cost at $200 billion annually. That analysis, which makes suggestions that Canadian counterfeiting costs $30 billion each year even more implausible, was less than a third of what some business groups had previously claimed. In fact, the OECD report concluded that while counterfeiting was an issue in all economies, it is most common in economies "where informal, open-air markets predominate." This suggests that far from being a hot-bed of counterfeiting, Canada is rarely the source of counterfeit products and it consumes far less than many other countries worldwide. Before Ottawa embarks on further anti-counterfeiting legislative action, it first requires accurate, non-partisan data. Not only has such information been missing from the Canadian debate, but it is the RCMP that has astonishingly been a primary source of unreliable, unsubstantiated data. In doing so, it has undermined both its own credibility as well as that of the House of Commons committee counterfeiting reports. http://www.michaelgeist.ca/content/view/2243/135/  Doesn’t own a computer Copyright Office Chief: I'm a DMCA Supporter Anne Broache There's still a lot of hatred out there for a controversial law known as the Digital Millennium Copyright Act, but don't count the U.S. Copyright Office chief in that camp. "I'm a supporter; I think it did what it was supposed to do," Register of Copyrights Marybeth Peters said of the 1998 law at an appearance at the Future of Music Policy Summit here. "No law is ever perfect, but I remain a supporter." The DMCA, among other things, dictates that "No person shall manufacture, import, offer to the public, provide, or otherwise traffic in any technology, product, service, device (or) component" that is primarily designed to bypass copy-protection technology. For that reason, it has long been unpopular among some hackers, programmers and open-source devotees--not to mention consumer groups that believe it unduly inhibits fair use rights. "I'm not ready to dump the anticircumvention," Peters said in response to a question from an audience member who suggested as much. "I think that's a really important part of our copyright owners' quiver of arrows to defend themselves." The law also requires that the Copyright Office meets periodically to decide whether it's necessary to specify narrow exemptions to the so-called anticircumvention rules. (Last year, the government decided it's lawful to unlock a cell phone's firmware for the purpose of switching carriers and to crack copy protection on audiovisual works to test for security flaws or vulnerabilities.) Peters told summit attendees that at first she thought it was "stupid" to put the Copyright Office in the position of deciding whether certain locked content was problematic, but she eventually came around. "It does bring attention to certain activities that maybe aren't so great," said the self-proclaimed "Luddite," who confessed she doesn't even have a computer at home. "In hindsight, maybe that's not such a bad thing." Peters indicated she was less thrilled, however, about a portion of the DMCA that generally lets hosting companies off the hook for legal liability, as long as they don't turn a blind eye to copyright infringement and remove infringing material when notified. That's one of the major arguments Google is attempting to wield in fighting high-profile copyright lawsuits, including one brought by Viacom, against its YouTube subsidiary. "Shouldn't you have to filter? Shouldn't you have to take reasonable steps to make sure illegal stuff that went up comes down?" she said. She added, without elaborating further, "I think there are some issues." http://www.news.com/8301-10784_3-9779996-7.html  Hacker Finally Publishes Notorious Apple Wi-Fi Attack Researcher David Maynor has published details of the controversial Apple Wi-Fi hack he disclosed at last year's Black Hat conference. Robert McMillan More than a year after claiming to have found a way to take over a Macintosh computer using a flaw in the system's wireless card, David Maynor has published details of his exploit. The details were included in a paper published in the September issue of Uninformed.org, an online hacking magazine. The lengthy paper describes how to run unauthorized software on a Macintosh by taking advantage of a flaw in Apple's AirPort wireless drivers. Apple patched the bug in September 21 without crediting Maynor for discovering the problem. Instead, Apple's engineers found the bug during an internal audit, the company said. Maynor and researcher Jon Ellch first described this type of problem during an August 2006 presentation at the Black Hat security conference in Las Vegas. He was widely criticized by the Apple community for failing to back up his claims with technical details, and for presenting a video demonstration that used a third-party wireless card instead of the one that ships with the Mac. On Tuesday, Maynor said that at the time of the Black Hat demonstration, he had found similar wireless bugs in a number of wireless cards, including Apple's AirPort and that he had been told to use the third-party card in the video because it was deemed "the least offensive to people." So why publish the Mac hack now? Maynor said that he had been under a nondisclosure agreement, which had previously prevented him from publishing details of the hack. The security researcher wouldn't say who his NDA was with, but that agreement is no longer in force, allowing him to talk about the exploit. "I published it now because I can publish it now," he said. By going public with the information, Maynor hopes to help other Apple researchers with new documentation on things like Wi-Fi debugging and the Mac OS X kernel core dumping facility. "There's a lot of interesting information in the paper that, if you're doing vulnerability research on Apple, you'd find useful." Maynor will soon publish a second paper on Uniformed.org explaining how to write software that will run on a compromised system, he said. As for his detractors, who will say that this disclosure comes too late, Maynor says he just doesn't care what they think. "Let them tear me apart all they want but at the end of the day the technical merit of the paper will stand on its own." http://www.computerworld.com.au/inde...0;fp;4;fpid;16  Cyber-Threats Outpace Security Measures, Says McAfee CEO Staff writers McAfee CEO David DeWalt says cyber-crime has become a US$105 billion business that now surpasses the value of the illegal drug trade worldwide. Despite the increase in government compliance requirements and the proliferation of security tools, companies continue to underestimate the threat from phishing, data loss, and other cyber vulnerabilities, new McAfee CEO David DeWalt said Tuesday. In a keynote address at the InformationWeek 500 conference in Tucson, DeWalt said "it's amazing how low the awareness is of cyber-security threats" among both government officials and corporate executives. "As the world has flattened, we've seen a significant amount of emerging threats from increasingly sophisticated groups attacking organizations around the world." Citing recent highly publicized corporate data breaches that have beset major companies like Ameritrade, Citigroup, and Bank of America, DeWalt said that cyber-crime has become a US$105 billion business that now surpasses the value of the illegal drug trade worldwide. Last week Internet stock trading company TD Ameritrade Holding said that one of its databases had been hacked by a thief who obtained personal information on some of its customers. Yesterday, an attorney launching a class-action lawsuit against Ameritrade claimed the online brokerage knew that someone had compromised its database as early as one year ago. An Ameritrade spokeswoman told InformationWeek that all of the company's 6.3 million accounts opened before July 18 of this year were exposed. Worldwide data losses now represent US$40 billion in losses to affected companies and individuals each year, DeWalt says. But law enforcement's ability to find, prosecute, and punish criminals in cyberspace has not kept up: "If you rob a 7-11 you'll get a much harsher punishment than if you stole millions online," DeWal remarked. "The cross-border sophistication in tracking and arresting cyber-criminals is just not there." Looking ahead to new forms of threat detection and enterprise data security, DeWalt outlined five major trends that will reshape the security industry and transform how companies secure their corporate and customer information in the next few years. The first is industry consolidation, as the large number of small vendors become acquired or give way to larger companies. "The security market will go through the same transition that other industries have," DeWalt said. "Right now you've got 50 or 60 vendors out there, and customers are faced with the questions of how do you integrate all those solutions, and create interoperability between them? It's not sustainable." With vendor consolidation will come the transition from multiple security agents on desktops and laptops to what McAfee terms "unified threat management," with a "single pane of glass" that allows IT managers to monitor and manage systems and devices across the entire network through a single console or platform. Second, the increase in cyber-threats has fueled a rapid growth in compliance requirements as the federal government tries to mandate higher levels of security and protection of sensitive consumer and patient data. "There's a lot of legislation around industries forcing them to comply with various standards for customer protection," said DeWalt, including payment-card industry regulations, Sarbanes-Oxley reporting requirements for public companies, and the 1996 Health Insurance Portability and Accountability Act. In fact, along with many corporate executives in the U.S., DeWalt believes that "the pendulum has swung too far" toward increased government oversight of corporations and the customer data they control, causing American companies to lose their competitive edge to businesses in other countries with less-stringent compliance requirements, particularly in Asia. The third important trend is the movement of security protection from the perimeter of corporate networks toward the data layer itself: "Traditional security has always been concentrated on the perimiter, on endpoint devices, particularly with firewalls," DeWalt noted. "The focus now is on thinking about data-oriented security" by classifying certain types of data so that it cannot leave the corporate network or company-owned devices. That is especially important because some 70% of all data losses are caused by insiders of one sort or another. Fourth, companies are facing new challenges as server virtualisation spreads across many industries and many types of industries. "Virtualisation is an amazing juggernaut in terms of security risk," said DeWalt, listing non-compliant virtual machines, VM-aware threats that can subvert countermeasures, the propagation of infected virtualization images, and "hyperjacking," or the potential for a single breach to offer simultaneouos access to many machines across a virtualized environment as some of the emerging risks. "Managing and protecting a single physical endpoint is much different than managing security virtually," DeWalt said. Finally, the emergence of new platforms and devices presents cyber-criminals with new targets for hacks and phishing scams. Mobile devices such as smartphones and voice-over-IP systems are inherent more vulnerable than traditional clients and telephony services. McAfee and its competitors are bringing out new products and technology to deal with these emerging threats, said DeWalt, but the advantage for the moment still lies with the evildoers in cyberspace. "We're in inning two of a nine-inning game here," he concluded. http://www.itnews.com.au/News/61497,...cafee-ceo.aspx  Hacker Finds Serious Flaw in Adobe PDF The security researcher said he would not release code that shows how a PDF attack works until Adobe provided a patch for the problem. Robert McMillan The hacker who discovered a recently patched QuickTime flaw affecting the Firefox browser says he has found an equally serious flaw in Adobe Systems Inc.'s PDF file format. "Adobe Acrobat/Reader PDF documents can be used to compromise your Windows box. Completely!!! Invisibly and unwillingly!!!," wrote Petko Petkov, in a breathless Thursday blog posting. "All it takes is to open a PDF document or stumble across a page which embeds one." Petkov said he had confirmed the issue on Adobe Reader 8.1 on Windows XP and that other versions may be affected. The security researcher said he would not release code that shows how this attack works until Adobe provided a patch for the problem, but he has already sent other software developers scrambling for bug fixes over the past week. On Sept. 12, Petkov reported that attackers could run unauthorized software on a Firefox user's PC by exploiting a flaw in Apple Inc.'s QuickTime media format. Mozilla Corp. offered a partial fix for this problem on Tuesday but said Apple would ultimately have to address the issue in its QuickTime media player. And on Tuesday Petkov posted code showing how Windows Media Player files could be used to make Web surfers susceptible to Internet Explorer bugs, even if they were running another browser such as Firefox or Opera. Microsoft Corp. has said it is investigating this issue. If Petkov's PDF claims are true, it could be bad news for business users, who are used to opening PDF attachments without thinking twice, said Andrew Storms, director of security operations with nCircle Network Security Inc. Though some attackers have crafted pdf attacks in recent years, Petkov's code could also be more effective than typical exploits, Storms added. "Historically, those other exploits have been targeted for specific versions of Adobe Reader," he said via instant message. "According to the information, this affects all versions. It's an inherent architectural problem in the way files are read." http://www.pcworld.com/article/id,13...s/article.html  Internet Security Moving Toward "White List" A sea change in how computers are guarded is on the way, with anti-virus vendors looking to reverse their protection philosophy Peter Nowak Internet security is headed toward a major reversal in philosophy, where a "white list" which allows only benevolent programs to run on a computer will replace the current "black list" system, which logs and blocks an ever-growing list of malevolent applications, internet security giant Symantec Corp. says. The number of malicious software attacks, including viruses, Trojans, worms and spam, is rising exponentially, dwarfing the number of new benevolent programs being developed, making it increasingly difficult for security firms to keep up. The solution, according to Symantec's Canadian vice-president and general manager, Michael Murphy, is to reverse how protection against such attacks is provided. Under the current system, a security firm discovers a new threat, adds it to its black-list database and updates its customers' anti-virus software to combat the problem. A "white list" would instead compile every known legitimate software program, including applications such as Microsoft Word and Adobe Acrobat, and add new ones as they are developed. Every program not on the list would simply not be allowed to be function on a computer. "This is the future of security technology," Murphy said at a presentation of the company's twice-yearly security report on Friday. The trick is to develop a "global seal of approval." A white list would likely require co-operation and funding from a majority of players in the technology industry. Industry observers think it is a good idea, but it raises several issues. The oversight body would have to be neutral, mindful of open-source software — which is quickly and often modified — and speedy in its approval process. "The bad guys are moving quickly and the good guys are moving quickly and the innovators are moving quickly. If the judges are taking months to judge things, then that's not fair to anybody," says Bill Munson, vice-president of the Information Technology Association of Canada. "That's not in the industry's or society's interest." In its security report, Symantec said the incidence of malicious code was up drastically in the first six months of 2007. Symantec found more than 212,000 new malicious code threats, up 185 per cent from the last six months of 2006. Trojans, or programs that appear to perform one function in order to hide a malicious one, made up 54 per cent of the volume of the top 50 malicious code reports, up 45 per cent over the prior six months. Trojans are particularly on the rise in North America, Murphy said, because Canadian and U.S. internet markets are more highly developed and thus protected from less-sophisticated and easy-to-identify attacks, such as spam and basic viruses. Hackers beginning to steal from victims The other big trend, Murphy said, is that hackers are no longer perpetrating attacks just for fun. Rather, these people are increasingly looking to extract money from their victims. "This is a sea change," he said. ""It's not just a pimply-faced boy in his parents' basement. That certainly may be part of the situation, but now it's for profit." Would-be hackers can buy software toolkits that allow them to create their own phishing attacks, where the criminal tricks a person into disclosing sensitive information such as a bank account number, for about $1,250. The black market for stolen information gleaned through such an attack can be lucrative, with an e-mail password selling for up to $350 US while a bank account number can fetch up to $400 US, Murphy said. In the first six months of 2007, Symantec found 8,011 distinct credit cards being advertised for sale on the black market, but that number represented only a small portion of the total being sold. The advertised card numbers are used only to attract buyers, who then purchase numbers in bulk, which are not advertised. Symantec said about 85 per cent of the stolen card numbers in circulation are American in origin, but did not disclose how many came from Canada. Overall, Canada has fared well in combating malicious attacks, particularly spam. In the past, Canada has ranked as high as fifth in the world in terms of the volume of spam that is received, but internet service providers here have done an excellent job of attacking it, Murphy said, with the country dropping to 12th in the latest study. However, the bad news is that spam still accounts for 61 per cent of the world's e-mail, up from 59 per cent in the previous period. http://www.cbc.ca/news/background/te...hite-list.html  FBI Boosts Servers for Faster Fingerprint, Identity Searches Layer 8 The Federal Bureau of Investigation's Criminal Justice Information Services (CJIS) Division today awarded Lockheed Martin a $16 million contract to upgrade its Hewlett Packard Superdome Unix servers.CJIS is the FBI's central repository for criminal justice information services; the CJIS division operates national-level crime data systems that furnish name checks, fingerprints, criminal history data and other information to law enforcement officials. Keeping its systems on the leading edge should help CJIS with its goal of delivering getting timely and relevant criminal justice information to the FBI and all others in the law enforcement community. The new and upgraded servers will be part of the FBI’s Integrated Automated Fingerprint Identification System. IAFIS maintains the largest biometric database in the world, containing the fingerprints and corresponding criminal history information for more than 47 million subjects in the Criminal Master File, according to the FBI Web site. The fingerprints and corresponding criminal history information are submitted voluntarily by state, local, and federal law enforcement agencies.With the contract announced today, Lockheed Martin's Enterprise Solutions and Services business unit will build on its existing contract with the CJIS program, by providing HP Uplift Kits for 15 Superdome servers and 1 Flatsdome server. Uplift kits will add additional processors and additional processor speed to the Superdomes that were originally installed in 2003 by Lockheed Martin. Lockheed Martin will also add a PA-8900 Superdome server to the Clarksburg, W. Va. facility as part of a project to modernize computer and communications technology at CJIS. CJIS is located on 986 acres of land in Clarksburg, W. Va.. The complex includes a 500,000-square foot main office building. Constructed in a modular design, this building is nearly the length of three football fields. It features a 600-seat cafeteria and a 100,000-square-foot computer center. It is also home to National Crime Information Center, an electronic clearinghouse of criminal justice information that can be tapped into by a police officer in a squad car and by any of the 90,000 agencies now connected to the massive computerized database. The system handles an average of 5.5 million queries daily, with responses in fractions of a second, the FBI says. Lockheed Martin is also the prime systems integrator for the FBI’s overarching $423 million advanced information management and sharing system Sentinel project. At the heart of the system is moving off two aging IBM mainframes and onto servers support Web applications. The four-phase project with contractor Lockheed Martin is scheduled to wrap up in 2011 at a total cost of about $305 million. Not expected to be complete until 2001, The FBI says Sentinel will deliver an electronic information management system, automate workflow processes for the first time, and provide a user-friendly web-based interface to access and search across multiple databases. Sentinel will help the FBI manage information beyond the case-focus of the existing Automated Case Support (ACS), and will provide enhanced information sharing, search, and analysis capabilities. Sentinel will also facilitate information sharing with members of the law enforcement and intelligence communities. http://www.networkworld.com/community/node/19755  US Intelligence Chief Seeks More Changes in Eavesdropping Law Pamela Hess No Americans' telephones have been tapped without a court order since at least February, the top U.S. intelligence official told Congress Tuesday. But National Intelligence Director Mike McConnell could not say how many Americans' phone conversations have been overheard because of U.S. wiretaps on foreign phone lines. "I don't have the exact number ... considering there are billions of transactions every day," McConnell told the House Judiciary Committee at a hearing on the law governing federal surveillance of phone calls and e-mails. McConnell said he could only speak authoritatively about the seven months since he became DNI. In a newspaper interview last month, he said the government had tapped fewer than 100 Americans' phones and e-mails under the Foreign Intelligence Surveillance Act, which requires warrants from a secret intelligence court. McConnell is seeking additional changes to the law, which Congress hastily modified just before going on vacation in August based in part on the intelligence chief's warnings of a dire gap in U.S. intelligence. The new law eased some of the restrictions on government eavesdropping contained in the 1978 Foreign Intelligence Surveillance Act, to let the government more efficiently intercept foreign communications. Under the new law, the government can eavesdrop, without a court order, on communications conducted by a person reasonably believed to be outside the United States, even if an American is on one end of the conversation - so long as that American is not the intended focus or target of the surveillance. Before McConnell can convince Congress to make the Protect America Act permanent - and agree to even more changes easing the provisions of FISA - he first has to allay concerns that the law passed so hastily earlier this year does not subject Americans to unwarranted government surveillance. "The right to privacy is too important to be sacrificed in a last-minute rush before a congressional recess, which is what happened," said Rep. John Conyers, D-Mich., the panel's chairman. Democrats worry that the law could be interpreted to open business records, library files, personal mail, and homes to searches by intelligence and law enforcement officers without a court order. Assistant Attorney General Kenneth L. Wainstein said the new surveillance powers granted by the Protect America Act apply only when the assistance of a communications company is needed to conduct the surveillance. Therefore, he said, the government could not use the law to search homes, open mail or collect business records because no communications provider would be involved in such a transaction. Many Democrats in Congress are now seeking to narrow what they consider to be overly broad language by rewriting the law. Wainstein warned that inserting specific prohibitions on government surveillance to protect civil liberties could have unintended consequences. "Anytime you put in limiting language, you've got to make sure it doesn't have unintended limiting consequences," Wainstein said. McConnell said that as long as his office can examine every word of the new language to scrub it for unintended consequences, he would be open to the changes. However, Bush administration officials say concern about the new powers is unfounded. They contend the Protect America Act only allows the government to target foreigners for surveillance without a warrant, a change that was needed because of changes in communications technology. Addressing the controversy over the law, the Justice Department and the White House Tuesday issued a "myth and facts" paper meant to ease the concerns of civil liberties advocates and privacy groups that believe it gives the government broader powers than intended. Rep. Jerrold Nadler, D-N.Y., chairman of the subcommittee on the Constitution, Civil Rights and Civil Liberties, called the effort a troubling "charm offensive." "Let's have some truth in advertising. The act gives the president almost unfettered power to spy without judicial approval - not only on foreigners but on Americans," Nadler said. McConnell said the new eavesdropping powers are needed not just to spy on terrorists but also to defend against more traditional potential adversaries. He told the panel that China and Russia are aggressively spying on sensitive U.S. facilities, intelligence systems and development projects, and that their efforts are approaching Cold War levels. McConnell and Wainstein pushed for other changes in the law, including granting retroactive immunity to telecommunications companies which may have helped the government conduct surveillance prior to January 2007 without a court order under the so-called Terrorist Surveillance Program. Wainstein said there are 40 to 50 lawsuits filed against telecommunications companies that are pending in U.S. courts. http://hosted.ap.org/dynamic/stories...EAST&TEMPLATE=  U.S. Airport Screeners Are Watching What You Read Ryan Singel International travelers concerned about being labeled a terrorist or drug runner by secret Homeland Security algorithms may want to be careful what books they read on the plane. Newly revealed records show the government is storing such information for years. Privacy advocates obtained database records showing that the government routinely records the race of people pulled aside for extra screening as they enter the country, along with cursory answers given to U.S. border inspectors about their purpose in traveling. In one case, the records note Electronic Frontier Foundation co-founder John Gilmore's choice of reading material, and worry over the number of small flashlights he'd packed for the trip. The breadth of the information obtained by the Gilmore-funded Identity Project (using a Privacy Act request) shows the government's screening program at the border is actually a "surveillance dragnet," according to the group's spokesman Bill Scannell. "There is so much sensitive information in the documents that it is clear that Homeland Security is not playing straight with the American people," Scannell said. The documents show a tiny slice of the massive airline-record collection stored by the government, as well as the screening records mined for the controversial Department of Homeland Security passenger-rating system that assigns terrorist scores to travelers entering and leaving the country, including U.S. citizens. The so-called Automated Targeting System scrutinizes every airline passenger entering or leaving the country using classified rules that tell agents which passengers to give extra screening to and which to deny entry or exit from the country. The system relies on data ranging from the government's 700,000-name terrorism watchlist to data included in airline-travel database entries, known as Passenger Name Records, which airlines are required to submit to the government. According to government descriptions, ATS mines data from intelligence, law enforcement and regulatory databases, looking for linkages in order to identify "high-risk" targets who may not already be on terrorist watchlists. ATS was started in the late 1990s, but was little known until the government issued a notice about the system last fall. The government has subsequently modified the proposed rules for the system, shortening the length of time data is collected and allowing individuals to request some information used by the scoring system. The government stores the PNRs for years and typically includes destinations, phone and e-mail contact information, meal requests, special health requests, payment information and frequent-flier numbers. The Identity Project filed Privacy Act requests for five individuals to see the data stored on them by the government. The requests revealed that the PNRs also included information on one requester's race, the phone numbers of overseas family members given to the airlines as emergency contact information, and a record of a purely European flight that had been booked overseas separately from an international itinerary, according to snippets of the documents shown to Wired News. The request also revealed the screening system includes inspection notes from earlier border inspections. One report about Gilmore notes: "PAX (passenger) has many small flashlights with pot leaves on them. He had a book entitled 'Drugs and Your Rights.'" Gilmore is an advocate for marijuana legalization. Another inspection entry noted that Gilmore had "attended computer conference in Berlin and then traveled around Europe and Asia to visit friends. 100% baggage exam negative.... PAX is self employed 'Entrepreneur' in computer software business." "They are noting people's race and they are writing down what people read," Scannell said. It doesn't matter that Gilmore was reading a book about drugs, rather than Catcher in the Rye, according to Scannell. "A book is a book," Scannell said. "This is just plain wrong." The documents have also turned Scannell against the Department of Homeland Security's proposal for screening airline passengers inside the United States. That project, known as Secure Flight, will take watchlist screening out of the hands of airlines, by having the airlines send PNR data to the government ahead of each flight. While earlier versions included plans to rate passenger's threat level using data purchased from private companies, DHS now proposes only to compare data in the PNR against names on the watchlist, which largely disarmed civil libertarians' opposition to the program. That's changed for Scannell now, who sees Secure Flight as just another version of ATS. "They want people to get permission to travel," Scannell said. "They already instituted it for leaving and entering the country and now they want to do it to visit your Aunt Patty in Cleveland." The Department of Homeland Security did not respond to a request for comment. http://www.wired.com/politics/online...light_tracking  Bush Calls for Expansion of Spy Law David Jackson Saying older surveillance laws were "dangerously out of date," President Bush pressed anew Wednesday for Congress to pass permanent legislation that allows intelligence agencies to carry out warrantless surveillance on all communications of a foreign terror suspect. Legislation passed by Congress last month "has helped close a critical intelligence gap, allowing us to collect important foreign intelligence and information about terrorist plots," Bush said after he was briefed at the National Security Agency. "The problem is the law expires on February 1 — that's 135 days from today. The threat from al-Qaeda is not going to expire in 135 days," Bush said. Bush's comments come one day after the nation's intelligence chief told Congress that fewer than 100 Americans have become surveillance targets because they were initially overheard communicating with foreign terror suspects. "How many Americans' phones have been tapped without a court order? The answer is none," Director of National Intelligence Mike McConnell told the House Judiciary Committee. The law that expires in February allows intelligence agencies to carry out warrantless surveillance on all communications of a foreign terror suspect, even if a U.S.-based person is on one end of the call. Congressional Democrats say the new law's wording could promote warrantless spying on Americans. The law is written "so broadly and loosely that it permits the government to intercept … anyone even thought to be abroad," Judiciary Committee Chairman John Conyers of Michigan said at Tuesday's hearing. The House Intelligence Committee is expected to begin considering changes to the warrantless wiretapping law next month. McConnell and the Bush administration also want the law expanded to include immunity from lawsuits for telecom companies that helped intelligence agencies carry out spying. Democrats, including Intelligence Committee Chairman Silvestre Reyes, D-Texas, want stricter rules covering surveillance of Americans. "These restrictions would impede the flow of information that helps us protect our people," Bush said Wednesday. "These restrictions would reopen gaps in our intelligence that we had just closed." At NSA, Bush received private briefings from intelligence officials and mingled with employees in the National Threat Operations Center. While cameras and reporters were in the room, the large video screens that lined the walls displayed unclassified information on computer crime and signal intelligence. Along one wall at NSA is a sign that says, "We won't back down. We never have. We never will." Contributing: Richard Willing; Associated Press http://www.usatoday.com/news/washing...dropping_N.htm  NSA to Defend Against Hackers Privacy fears raised as spy agency turns to systems protection Siobhan Gorman In a major shift, the National Security Agency is drawing up plans for a new domestic assignment: helping protect government and private communications networks from cyberattacks and infiltration by terrorists and hackers, according to current and former intelligence officials. From electricity grids to subways to nuclear power plants, the United States depends more than ever on Internet-based control systems that could be manipulated remotely in a terrorist attack, security specialists say. The plan calls for the NSA to work with the Department of Homeland Security and other federal agencies to monitor such networks to prevent unauthorized intrusion, according to those with knowledge of what is known internally as the "Cyber Initiative." Details of the project are highly classified. Director of National Intelligence Mike McConnell, a former NSA chief, is coordinating the initiative. It will be run by the Department of Homeland Security, which has primary responsibility for protecting domestic infrastructure, including the Internet, current and former officials said. At the outset, up to 2,000 people -- from the Department of Homeland Security, the NSA and other agencies -- could be assigned to the initiative, said a senior intelligence official who spoke on condition of anonymity. The NSA's new domestic role would require a revision of the agency's charter, the senior intelligence official said. Up to now, the NSA's cyberdefense arsenal has been used to guard the government's classified networks -- not the unclassified networks that now are the responsibility of other federal agencies. NSA officials declined to discuss specific programs but said cybersecurity is a critical component of what they do. "We have a strong history in information assurance and national security," said NSA spokeswoman Andrea Martino, who added that the agency will continue to play a role in cyberdefense. Homeland Security spokesman Russ Knocke said that "as the lead agency responsible for assuring the security, resiliency and reliability of the nation's information technology and communications infrastructure, our department is working to unify further and integrate the security framework for cyber operations throughout the federal government." Since the existence of its warrantless domestic eavesdropping program was revealed in 2005, the NSA and other U.S. intelligence agencies have been mired in a controversy over domestic intelligence activities. The Homeland Security Department recently came under fire amid Bush administration plans to broadly expand the use of satellite imagery to assist in federal, state and local law enforcement. Current and former intelligence officials, including several NSA veterans, warned that the agency's venture into domestic computer and communications networks -- even if limited to protecting them -- could raise new privacy concerns. To protect a network, the government must constantly monitor it. "This will create a major uproar," predicted Ira Winkler, a former NSA analyst who is now a cybersecurity consultant. "If you're going to do cybersecurity, you have to spy on Americans to secure Americans," said a former government official familiar with NSA operations. "It would be a very major step." A former senior NSA official said the difference between monitoring networks in order to defend them and monitoring them to collect intelligence is very small. The former officials spoke on condition of anonymity to protect relationships with intelligence agencies. Another former NSA official said that if the government wants to prevent cyberattacks, it makes sense to tap the agency's skills. "I've got to be able to at least look at something to determine: Do I have a threat or don't I have a threat?" the former NSA official said. "It's important that you have the best thinkers with the deepest experience working these problems on behalf of the nation." O. Sami Saydjari, a cybersecurity consultant, said the privacy concerns are real. He said intelligence agencies should be part of the solution, because they have the expertise needed to develop a national cybersecurity system, but that privacy advocates also should be part of the planning process. Computer specialists have warned for years about cyberattacks. But experts say efforts to guard against them have not gained momentum at the national level, at least in part because the public envisions a cyberattack as nothing more than a big computer crash. Those who monitor such threats said the danger has grown as control systems for potential terrorist targets have become increasingly connected to the Internet. A cyberattack could cut access to power, banking and telecommunications systems across much of the country, said Saydjari, president of the Cyber Defense Agency, a consulting firm. "The hostile groups have caught on to most of the things we're worried about," said Scott Borg, director of the U.S. Cyber Consequences Unit, a nonprofit research institute that advises the government and the private sector. "It's been remarkable in the last, really, two years how much all these things that people like me have been worried about have been bit by bit rediscovered and reinvented in the hacker world." Potential cyberattacks are being discussed in chat rooms in languages that include English, Arabic, Russian and Punjabi, he said. Terrorists and others already know many of the country's vulnerabilities, Borg said, adding that he is extremely concerned about the ability to hack into computer systems controlling nuclear power plants. A government task force issued a stark warning this year that the threat of a cyberattack to U.S. infrastructure, which can be launched from a computer anywhere in the world, is "very real and growing rapidly." In June, an alleged Chinese hacking effort shut down e-mail in Defense Secretary Robert M. Gates' office for several days. Simulation exercises, such as one dubbed Dark Angel and sponsored by the group Professionals for Cyber Defense, showed in 2003 how a cyberattack could shut down most of the nation's power grid, Saydjari said. There is growing interest among hackers in capturing information on "smart cards" that allow access to buildings and critical computer systems and using that information to gain access to the system, according to Borg. Cybersecurity has long been an orphaned responsibility in the federal government, with various agencies having some part in it. The NSA has largely been left out, because its focus has been on protecting military networks. Proposals to break off the NSA's information security branch and assign it a broader role beyond the intelligence agencies fell flat, former NSA officials say. Amit Yoran, the Homeland Security Department's first chief of cybersecurity, said in an interview that while the government has made progress, federal efforts have been "somewhat spotty" overall. Among the main challenges, he said, is that the Homeland Security Department has been given responsibility for the problem but lacks the authority and expertise to compel other agencies and the private sector to follow its lead. The new cybersecurity effort aims to build, in part, on an existing NSA program, code-named Turbulence, which has had a troubled start, the senior intelligence official said. http://www.baltimoresun.com/news/nat...l_tab01_layout  Terror Watch: A Secret Lobbying Campaign The secret lobbying campaign your phone company doesn't want you to know about Michael Isikoff and Mark Hosenball The nation’s biggest telecommunications companies, working closely with the White House, have mounted a secretive lobbying campaign to get Congress to quickly approve a measure wiping out all private lawsuits against them for assisting the U.S. intelligence community’s warrantless surveillance programs. The campaign—which involves some of Washington's most prominent lobbying and law firms—has taken on new urgency in recent weeks because of fears that a U.S. appellate court in San Francisco is poised to rule that the lawsuits should be allowed to proceed. If that happens, the telecom companies say, they may be forced to terminate their cooperation with the U.S. intelligence community—or risk potentially crippling damage awards for allegedly turning over personal information about their customers to the government without a judicial warrant. “It’s not an exaggeration to say the U.S. intelligence community is in a near-panic about this,” said one communications industry lawyer familiar with the debate who asked not to be publicly identified because of the sensitivity surrounding the issue. But critics say the language proposed by the White House—drafted in close cooperation with the industry officials—is so extraordinarily broad that it would provide retroactive immunity for all past telecom actions related to the surveillance program. Its practical effect, they argue, would be to shut down any independent judicial or state inquires into how the companies have assisted the government in eavesdropping on the telephone calls and e-mails of U.S. residents in the aftermath of the September 11 terror attacks. “It’s clear the goal is to kill our case," said Cindy Cohn, legal director of the Electronic Frontier Foundation, a San Francisco-based privacy group that filed the main lawsuit against the telecoms after The New York Times first disclosed, in December 2005, that President Bush had approved a secret program to monitor the phone conversations of U.S. residents without first seeking judicial warrants. The White House subsequently confirmed that it had authorized the National Security Agency to conduct what it called a “terrorist surveillance program” aimed at communications between suspected terrorists overseas and individuals inside the United States. But the administration has also intervened, unsuccessfully so far, to try to block the lawsuit from proceeding and has consistently refused to discuss any details about the extent of the program—rebuffing repeated congressional requests for key legal memos about it. "They are trying to completely immunize this [the surveillance program] from any kind of judicial review,” added Cohn. “I find it a little shocking that Congress would participate in the covering up of what has been going on." But congressional staffers said this week that some version of the proposal is likely to pass—in part because of a high-pressure lobbying campaign warning of dire consequences if the lawsuits proceed. Director of National Intelligence Mike McConnell seemed to raise the stakes recently when he contended in an interview with the El Paso Times that the private lawsuits could “bankrupt these companies.” Among those coordinating the industry’s effort are two well-connected capital players who both worked for President George H.W. Bush: Verizon general counsel William Barr, who served as attorney general under 41, and AT&T senior executive vice president James Cicconi, who was the elder Bush's deputy chief of staff. Working with them are a battery of major D.C. lobbyists and lawyers who are providing "strategic advice" to the companies on the issue, according to sources familiar with the campaign who asked not to be identified talking about it. Among the players, these sources said: powerhouse Republican lobbyists Charlie Black and Wayne Berman (who represent AT&T and Verizon, respectively), former GOP senator and U.S. ambassador to Germany Dan Coats (a lawyer at King & Spaulding who is representing Sprint), former Democratic Party strategist and one-time assistant secretary of State Tom Donilon (who represents Verizon), former deputy attorney general Jamie Gorelick (whose law firm also represents Verizon) and Brad Berenson, a former assistant White House counsel under President George W. Bush who now represents AT&T. Because of the extreme secrecy surrounding the warrantless surveillance program, few if any of the lobbyists and lawyers are prepared to speak publicly about their role. “My client requires me not to talk to the press,” said the normally loquacious Black when asked by NEWSWEEK about his lobbying for AT&T. Berman and Berenson also declined comment. Gorelick confirmed that she is providing "strategic advice," not lobbying for Verizon. Coats and Donilon did not respond to requests for comment. But according to three industry sources, these and other players have been conferring with each other over legislative strategy and targeting key lawmakers and staffers, especially those on the House and Senate Intelligence and Judiciary Committees. The lobbyists have set up meetings and arranged conference calls, pressing the argument that failure to provide protection to the companies could interfere with the vital assistance they say the telecom industry has provided the intelligence community in monitoring the communications of Al Qaeda and other terrorist operations overseas. The case for new legislation retroactively giving telecoms companies protection against private lawsuits—including lawsuits already pending—was outlined this week by Kenneth Wainstein, assistant attorney general for national security. At a House Judiciary Committee hearing chaired by Rep. John Conyers, a Michigan Democrat, Wainstein said that giving telecoms companies retroactive liability was a matter of "general fairness." "I think it's sort of fundamentally unfair and just not right to—if a company allegedly assisted the government in its national-security efforts, in an effort to defend the country at a time of peril, that they then get turned around and face tremendously costly litigation and maybe even crushing liability for having helped the United States government at a time of need ... it's just not right," Wainstein testified. Wainstein also claimed that "every time we have one of these lawsuits, very sensitive information gets discussed and gets leaked out, disseminated out in the public. And our adversaries are smart, both the terrorists who might be over in, you know, someplace in the Middle East are smart, and then the governments that might be our adversaries are tremendously sophisticated, and they're gleaning all this information that gets out." Wainstein also said that a telecom company's overseas assets could be threatened if its collaboration in U.S. espionage efforts were confirmed in a court case. The campaign for industry protection was initially launched last summer when administration and industry officials first tried to get the immunity provision included in the Protect America Act—a measure passed by Congress and signed by President Bush on Aug. 5 that allowed the surveillance program to continue and temporarily gave the National Security Agency expanded eavesdropping powers. At the time, Democrats in Congress balked at including the kind of sweeping retroactive civil immunity protections that the industry sought. But then, on Aug. 15, a three-judge panel of the Ninth Circuit Court of Appeals in San Francisco heard oral arguments in a Justice Department motion to block the Electronic Frontier Foundation lawsuit against AT&T. More than 40 other civil suits filed against the telecoms—many of them seeking billions of dollars in damages—had been consolidated with the EFF lawsuit. But the Justice Department had sought to block the lawsuits under the “state privilege” doctrine, which can require the dismissal of suits that might endanger national security. The three-judge panel, made up entirely of Democratic appointees, seemed openly skeptical of the Justice Department’s arguments, prompting many court observers to conclude that the panel was likely to issue a ruling permitting the lawsuits to proceed. At one point in the proceedings, one of the judges, Harry Pregerson, a Jimmy Carter appointee, appeared annoyed with the Justice Department lawyer, Gregory Garre. The judge wanted Garre to provide direct answers to questions about the scope of the just-passed surveillance law, according to press reports. When Garre tried to explain that the law was complicated, Pregerson shot back: “Can’t be any more complicated than my phone bill.” The administration is keeping up pressure on Congress for quick action on the new version of the surveillance law—including an immunity provision for telecoms—which will take effect when the Protect America Act expires early next year. Congressional staffers say that Democrats are likely to go along with some version of the proposal. But Democratic leaders, who say they were stampeded into passing the law last summer, are insisting on having more thorough hearings and forcing the administration to turn over documents on the surveillance program. If the telecoms want immunity, some Democrats say, the White House should at least say what it is they need immunity for. http://www.msnbc.msn.com/id/20884696/site/newsweek/  Senate Fails on Habeas Corpus Today the US Senate fell four votes short of restoring Habeas Corpus, the fundamental constitutional right of individuals to challenge government detention, which the Republican Congress revoked in last year's Military Commissions Act. Fifty-six senators supported a procedural move to tie the Habeas provision to legislation authorizing defense spending--a step that requires sixty votes. ADVERTISEMENT The amendment was sponsored by Judiciary Chairman Patrick Leahy, Senator Arlen Specter, who voted for the legislation that the amendment attempts to reverse, and Senator Chris Dodd, who blasted today's vote. "Each of us in the Senate faced a decision either to cast a vote in favor of helping to restore America's reputation in the world, or to help dig deeper the hole of utter disrespect for the rule of law that the Bush Administration has created. Unfortunately, too many of my colleagues chose the latter," he said. Backers of the amendment and human rights organizers say they will continue to press for habeas restoration. Leah Adler, an organizer with Working Assets, wrote today that activists should focus on the U.S. House, which will "likely consider legislation to restore habeas corpus in the next few weeks." Today's vote also suggests a new Senate majority for Habeas Corpus. (Last Congress, a similar amendment did not even break 50 votes.) And yes, it is a sad sign that we are reduced to counting votes for which members of Congress are upholding their oath to support the Constitution. http://news.yahoo.com/s/thenation/20...ation/15234404  Success I am proud to announce that the baseless charges brought against me by the Brooklyn, Ohio Police Department were dropped this morning and the process of expunging my record has begun. Although I knew that this was a possible outcome for the last ten days, I didn’t acquire the certainty until late yesterday afternoon. I was not at liberty to make this announcement yesterday since the process had not formally been completed. This brings to a formal conclusion my criminal defense which began when I was arrested on September 1st, 2007 at a Circuit City for refusing to provide a police officer with my driver’s license. The fact that my charges were dropped reaffirms the assertion which I’ve made since the beginning: US citizens are not and should not be required to provide paper identification when asked by law enforcement, in most circumstances. In Ohio this right is specifically protected by Ohio Revised Code 2921.29 which states that a person may not be arrested for refusing to provide a law enforcement officer with anything other than a verbal representation of their name, address and date of birth. In other words, if you are walking along a sidewalk and a police officer has reason to question you, you must verbally state your name, address and date of birth, but you can’t be arrested for refusing to show your driver’s license. (Or for that matter your fishing license, marriage license, liquor license, etc.) Ten days ago I had a decision to make. I was presented with an offer to have my charges dropped in exchange for signing a document which asked the following of me: » I would not file a Section 1983 civil suit against the Brooklyn police department for infringing on my civil rights. » I would not make any disparaging remarks about the police department, with financial repercussions for doing so. » I would not discuss the details of this agreement. These conditions were completely unacceptable to me. I wanted to fight the charges in court and I wanted to win based on the merits of my case. I felt that it was important to set a legal precedent that would help others in the future. Although I was never interested in suing the police department, signing such a document went against my principles and against the very reasons I decided to take a stand in the first place. I was mad to say the least. In the days that followed a few things changed. First, I learned that the prosecutor was more interested in protecting the city against a civil law suit than she was in silencing my speech. Prosecutor Hillary Goldberg was willing to drop my charges and expunge my record if I promised not to sue. Although this was welcome news I still wanted to fight the charges in court in order to set a legal precedent for others. Then, I learned that Ohio already had two legal precedents that dealt with the very issue of whether or not refusing to provide a driver’s license is grounds for obstructing official business. (Google “State v. McCrone” and “Middletown v. Hollon” for more details.) The legal precedent created by a court victory would not have filled a needed legal gap. At this point I was stuck between two choices. Behind Door #1 was an eight to twelve month legal battle, three or more separate hearings including a jury trial, potential legal fees in the dozens of thousands of dollars and a lot of duress for my best witnesses: my family. Behind Door #2 was the immediate drop of the matter in exchange for giving up the right to seek civil damages against the police department. At 2:00am one night I received a phone call from a family member which sealed the deal. For personal matters I can’t divulge who called or what was said, but I’ll simply state that a loved one told me something on the phone which left me with no choice. My family had become too entangled in my mess and I couldn’t put them through a lengthy and stressful legal process. My principles are important to me, but so is my family. Based on what I was told over the phone I immediately knew that I couldn’t put my family through a drawn out legal ordeal. On top of the emotional strain it was putting on my family, it would have forced my Sister to fly out from California on one or two occasions, and it would have forced my Father to cancel scheduled business trips to Europe. My family was caught in the crossfire. I took a stand against Circuit City when I refused to show my receipt. I took a stand against Officer Arroyo when I refused to show my driver’s license. I wanted to take a stand against Prosecutor Goldberg in court, but it just wasn’t meant to be. In the end I forfeited my right to sue the police department in exchange for the matter being dropped. Considering that I never intended to sue the police department in the first place, this was a concession that I felt comfortable with. Although he won’t publicly admit it, I’m sure that Officer Arroyo knows he made a mistake. For the record, I do not believe that Officer Arroyo is a bad person, and other than my arrest I have no reason to believe that he is a bad police officer. I think that Officer Arroyo was embarrassed and insulted when I refused to obey his unlawful command, and I think that he was not familiar enough with Ohio State law. Hopefully this incident will make him more knowledgeable about the law and more understanding of others in the future who choose to assert their rights. I think the same is true for Prosecutor Goldberg. She’s a smart woman who knows the law, and she clearly realizes that she had no case against me. However, her back was put against the wall by all of the media attention which the case received and I suspect that she felt that she had no choice but to either push forward with the charges or seek protection against a civil suit. I wanted a verbal apology from the police department but quickly learned that this would never happen. Fortunately actions speak louder than words. Dropping my charges and expunging my record is perhaps the best form of an apology that I could receive, and it’s the apology that I’ve chosen to accept. The Cleveland Plain Dealer reported on my agreement with the prosecutor in today’s issue. When I read their take on what happened I was outraged. Michael Sangiacomo of the Plain Dealer claimed that I “agreed that a police officer did nothing wrong in arresting [me] after [i] refused to show [my] driver’s license.” This is an outright lie. I never said such a thing and would never say such a thing. In fact, I’ve never even spoken with Michael Sangiacomo. He emailed me looking for a quote and I referred him to my attorney. As far as I know Michael Sangiacomo hasn’t even seen the release that I signed with the prosecutor. I consider the outcome of my legal battle to be a victory, yet today’s paper portrays it as defeat. Understandably I received a lot of hate mail today from people who read the Cleveland Plain Dealer article and were horrified to see that I “caved” under pressure. If I was a third party to the situation I think I would have given Michael Righi a piece of my mind as well. The article is wholly unfair, and a complete misrepresentation of the release that I signed with the prosecutor. I uploaded a PDF version of the release and I encourage you to read it and decide for yourself. Although the police department did not admit guilt in the release, nowhere in it did I claim that they were justified in their actions. Finally, I would like to address the donations which I accepted over the past few weeks. I received a total of $5,197.23 USD after PayPal expenses. I’m still a little unsure of what my total legal fees will be, but I expect that they will be in the $7,500-$10,000 range. (I’ve already paid $7,500 to one attorney, and I’m waiting for a bill from a second attorney for related legal assistance.) I am extremely grateful to the people that donated money. The donations represented more than just money to me. They represented emotional support in a time when it was much needed, and I’d like to thank everybody again who donated. The smallest single donation was 1 penny (a symbolic gesture), and the largest single donation was $200. Every contribution made was a pat on the back and it really helped me get through a tough couple of weeks. That said, I have received a lot of flak over the money. Some people have accused me, an “upper middle class 26 year old”, of asking for money in the first place. Some people have gone as far as to accuse me outright of running a scam. I agreed to accept donations via PayPal because a number of people emailed me wanting to know how they could help, and I wanted to give them an easy way in which they could make themselves involved. I said from the beginning that I would donate any excess money to the ACLU. As it turned out my legal expenses were at least $2,000 more than the money donated. In the end, I have decided to donate the entire $5,197.23 to the ACLU of Ohio. I am doing this for a few reasons. First, I would like to end the question of my intentions once and for all. This has never been about money or attention. I stood up for my rights because they are important to me and for no other reason. Second, even if my legal fees rise to $10,000 I am fortunate enough to be in a position where I can afford this. Although it’s unjust that anybody should have to pay a dime to exert their constitutional rights, $10,000 is still a small price to pay compared to what others have sacrificed in the past and are sacrificing today. Finally, I want to do something to help prevent injustices from happening against others in the future. Although I don’t support the ACLU in all of its endeavors, I do believe that they are the best organization fighting for civil rights in the United States today. Even though the ACLU wasn’t able to help me with my ordeal, I hope that the money I send them will allow them to help others in the future. I’ve learned more in the last three weeks than I have in the last three years. This post has only just begun to scratch the surface of what unfolded since September 1st, 2007. I have funny stories, sad stories and outright infuriating stories from the last few weeks which I hope to eventually tell you more about. Until then, thanks for your support. -Michael http://www.michaelrighi.com/2007/09/20/success/  Australia 'Cracked Top-Secret US Jet Fighter Codes' Don Woolford KIM Beazley has told how Australia cracked top-secret American combat aircraft codes while he was defence minister in the 1980s. "We spied on them and we extracted the codes," Mr Beazley told Parliament during his valedictory speech today. Mr Beazley, who was defence minister from 1984 to 1990, said that when he took over the job he soon learned that the radar on Australia's Hornets could not identify most potentially hostile aircraft in the region. In other words, Australia's frontline fighter could not shoot down enemies in the region. Mr Beazley said he was greatly tempted to "belt" the Liberals with this and lay to rest their claim to be best at managing defence. "I shut up, I said nothing," Mr Beazley said. "I went to the US and for five years, up hill and down dale, with one knock-down, drag-out after another, with Cap Weinberger, Dick Cheney, Paul Wolfowitz, I tried to get the codes of that blasted radar out of them. "In the end we spied on them and we extracted the codes ourselves and we got another radar that could identify (enemy planes). Mr Beazley said the Americans were Australia's most important ally. "But they are a bunch of people you have to have a fight with every now and then to get what you actually need out of them," he said. Mr Beazley said that the story of getting the Hornet codes was well known within Defence, but not beyond it. He said the problem was that the old codes related to Warsaw Pact aircraft, rather than ones in Australia's region. The Americans kept saying they'd provide the codes, but never did. "So we tried to crack the codes so we could enhance them," Mr Beazley said. "And we made a lot of progress." Mr Beazley said the Americans knew what the Australians were doing and were intrigued by the progress they made. http://www.news.com.au/story/0,23599...478-2,00.html#  S.C. Mom Scoops al - Qaida With Its Videos Sagar Meghani Once her son is off to school, Laura Mansfield settles in at her dining room table with her laptop and begins trolling Arabic-language message boards and chat rooms popular with jihadists. Fluent in Arabic, the self-employed terror analyst often hacks into the sites, translates the material, puts it together and sends her analysis via a subscription service to intelligence agencies, law enforcement and academics. Occasionally she comes across a gem, such as when she found a recent Osama bin Laden video -- before al-Qaida had announced it. ''I realized, oh my gosh, I'm sitting here, I'm a fat 50-year-old mom and I've managed to scoop al-Qaida,'' said Mansfield, who uses that name as a pseudonym because she receives death threats. She sometimes spends 100 hours a week online, and she often finds items after word has begun spreading on the Arabic forums of an imminent release. ''It's really important to understand what the jihadists think and how they're planning on doing things,'' she said. ''They're very vocal. They tell us what they're going to do and then they go out and do it.'' Mansfield tips off her intelligence sources when she does find something new, part of an informal working relationship with the government. ''When I send them something, it's welcome,'' she said. ''They thank me.'' There have been times when an impending video release has kept her from a planned shopping trip with her daughter. ''It gets really challenging when you're trying to do that and cook spaghetti at the same time,'' she said. http://ap.google.com/article/ALeqM5i...SYO4HqWF4sPv4g  Leaked Media Defender E-Mails Reveal Secret Government Project Ryan Paul Peer-to-peer (P2P) poisoning company MediaDefender suffered an embarrassing leak this weekend, when almost 700MB of internal company e-mail was distributed on the Internet via BitTorrent. The e-mails reveal many aspects of MediaDefender's elaborate P2P disruption strategies, illuminate previously undisclosed details about the MiiVi scandal, and bring to light details regarding MediaDefender's collaboration with the New York Attorney General's office on a secret law enforcement project. We have been reviewing the data for days and will have multiple reports on the topic. MediaDefender specializes in file-sharing mitigation—practices that disrupt and deter infringing uses of P2P file-sharing networks. Music labels and movie studios pay the company millions of dollars to temporarily impede the propagation of new releases in order to compel consumers to pursue legitimate commercial distribution channels. MediaDefender accomplishes this task by using its array of 2,000 servers and a 9GBps dedicated connection to propagate fake files and launch denial of service attacks against distributors. The e-mail was leaked to the public by a group that calls itself MediaDefender-Defenders. In a text file distributed with the mail, the group explains how the e-mails were obtained and why they are being distributed. Apparently, MediaDefender employee Jay Mairs forwarded all of his company e-mails to a Gmail account, which was eventually infiltrated. "By releasing these e-mails we hope to secure the privacy and personal integrity of all peer-to-peer users," writes the group behind the disclosure. "So here it is; we hope this is enough to create a viable defense to the tactics used by these companies." It's not surprising that MediaDefender was targeted in this manner. The company was accused of using shady tactics earlier this year when BitTorrent community site TorrentFreak revealed that the anti-piracy company was surreptitiously operating a video upload service called MiiVi that offered high speed downloads of copyright-protected content. Critics accused MediaDefender of using the site to perpetrate an entrapment scheme, an allegation that the company has vigorously denied. MediaDefender founder Randy Saaf personally assured Ars that MiiVi was an internal project that was never intended for public use. Back in July when we covered the MiiVi scandal, we knew Saaf's story didn't quite add up, and now the general public has evidence that blows holes in Saaf's claims. The MediaDefender e-mails leaked this weekend confirm beyond doubt that the company intentionally attempted to draw traffic to MiiVi while obscuring its own affiliation with the site. The e-mails also show that MediaDefender immediately began to recreate the site under a different name and corporate identity soon after the original plan was exposed. The rise of MiiVi Shortly after the public launch of MiiVi in June, developer Ben Grodsky e-mailed Saaf and his colleagues to inform them that the site was beginning to receive traffic. "We have some success! 12 people have signed up on [the] page. 7 have installed [the] app," wrote Grodsky. "This is from about 3,000 uniques from limewire redirects." Grodksy sent another user count status update a week later revealing that the site had drawn 19,000 unique visitors from LimeWire redirects. He also informed Saaf that his team was "working on putting Google Analytics all over MiiVi" in order to "better track what people are doing on the site." MediaDefender went to great lengths to obscure its affiliation with MiiVi. "I don't want MediaDefender anywhere in your e-mail replies to people contacting Miivi," Saaf instructed company employees. "Make sure MediaDefender can not be seen in any of the hidden email data crap that smart people can look in." Grodsky and Saaf also began discussing new ways to drive traffic to the MiiVi site. "If we want more users, Dylan's eDonkey messages would get us a lot of Europeans that are a little bit older crowd," Grodsky wrote. "I would like it if our pictures were indexed with goggle [sic]. We need to get as much search traffic as we can," Saaf replied. Developer Dylan Douglas also suggested some Google ranking improvement strategies. "We should come up with a bunch of keywords and a description for the hidden metadata entries to increase traffic," Douglas told the MiiVi developers. In late June, Grodsky began considering ways to leverage the MiiVi client application infrastructure. "Do you think it would break a lot and take more time than its [sic] worth for the MiiVi application/installer also to act like Serge's Proxy client and spoof on eMule?" Grodsky asked Saaf. "We don't want to do this at this time," Saaf replied. "Good idea, but we don't want to give it a spyware stigma." The disclosure Chaos ensued at the company when TorrentFreak disclosed MediaDefender's affiliation with MiiVi in early July. "Looks like the domain transfer screwed us over," Grodsky wrote in an e-mail which also contained a link to TorrentFreak's article. "What needs to happen?! Do you want the server pulled?" he asked Saaf. "This is really fucked," Saaf replied. "Let's pull miivi offline." Shortly after the server was shut down completely, Grodsky sent a follow-up e-mail noting that the story was beginning to spread. He dutifully requested "damage control" instructions from Saaf and discontinued the LimeWire redirect campaign. MediaDefender's damage control program went into full swing shortly after that. When Douglas pointed out that information about MiiVi had been added to the MediaDefender Wikipedia page, Saaf decided that he wanted it taken down. "Can you please do what you can to eliminate the entry? Let me know if you have any success," Saaf wrote. "I will attempt to get all references to miivi removed from wiki," developer Ben Ebert replied. "We'll see if I can get rid of it." After a statement Saaf sent to Digital Daily was included in a blog entry, Saaf sent an e-mail to a handful of MediaDefender employees asking if it would be a good idea to post it to the Digg.com news site. He also suggested possibly having MediaDefender employees post comments. Referring to the Digg community, MediaDefender co-founder Octavio Herrera replied, "They aren't going to believe you." MediaDefender developers also discussed ways to downplay the story or spin it to dull the impact. "If the major news outlets aren't interested in the story, I would take that as an indication that the VAST majority of people don't give a shit about this story," Mairs wrote. "However, if they do think it's worth writing about, we definitely want to get our side of the story in the mainstream media, so I think Randy's plan of going to the big tech media outlets is a good one. So far the story has only been on techie, geek web sites where everybody already hates us. If the story stays on these sites, we should let it die." Saaf sent Mairs a private reply in response, expressing his personal opinion about the media backlash surrounding the spyware allegations. "Truth is I don't give a crap about most of this shit," Saaf wrote. The resurrection Despite the serious failure of MiiVi, MediaDefender decided to try again. "Looks like we'll just have to take 2-3 weeks of downtime and do some cosmetic work and relaunch," wrote MediaDefender employee Ty Heath in an e-mail to the MiiVi development team. "Plus creating another DBA (or better yet incorporating under a new name), getting a new domain, getting another Verisign certificate, getting a new IP range, etc.," Grosdky replied. In an e-mail titled "MiiVi redux," Grodsky asks Saaf if he wanted to "do the incorporating from scratch idea for the MiiVi replacement" instead of the doing-business-as arrangement used for MiiVi. "If so," wrote Grodsky, "I have no idea what the turn-around is on creating a complete corporate entity and we would need a name for the new corp." Grodksy's first step was establishing a new mailing address using a mail service in Las Vegas. "I called the place (www.maillinkplus.com) and verified the name(s) on the box and the name(s) that receive the mail can be different from the name of the company that's paying by check. They also e-mail nightly if there's mail and someone on their staff inputs the FROM address on the envelope to a database that will show us when we login who we got mail from and then we can pick to have those article [sic] forwarded to us per item," wrote Grodsky. "Worst case scenario paranoia craziness, does anyone have objections with this mail box place being the foundation for all the materials that would have to do with the to-be-named MiiVi?" One point that came up during MiiVi resurrection planning was the potential value of the traffic generated by the negative publicity. "We are leaning toward dumping the URL and just re-launching with a new URL? Are we being too hasty because you can't buy 1,000,000 pages linking to you in Google returns." Michael Potts, who works for MediaDefender parent company ARTISTDirect, suggested putting a link to the new site on a page at the MiiVi domain so that the new site benefits from MiiVi's high Google rank. After an extensive naming discussion, MediaDefender finally decided to bring back MiiVi under the name Viide. In an e-mail to Potts, Grodsky wrote, "When you get a chance, we would love you to start taking a look at www.viide.com. That is the current home of our MiiVi site. We have totally locked-down the site, while we improve the look and feel from [what] the blogosphere saw." The next step was purging Viide of all references to MiiVi before the official launch. "I'm not sure if you guys are planning on going live with the Viide domain name... but in case you are... you might want to remove all references of Miivi on the homepage of viide.com before it gets Googled or someone public comes across it," wrote former MediaDefender developer Tabish Hasan in an e-mail sent to the MiiVi development team. Development on Viide was ongoing in the most recent e-mails included in the leaked collection. Providing data for use by law enforcement agencies In the collection of leaked e-mails, there are several discussions with representatives of the New York Attorney General's office, including intelligence analyst Bradley J. Bartram and senior special investigator Michael G. McCartney. MediaDefender is in the process of devising a system that will enable the Attorney General's office to remotely access MediaDefender's data about P2P users. In an e-mail that McCartney sent to Mairs last month, the investigator explained that the matter was "being overseen by the highest members of [the] agency" and was considered somewhat urgent. Although the full scope of the project cannot be extrapolated from the e-mails, the information available indicates that MediaDefender intends to provide the Attorney General's office with information about users accessing pornographic content. Other kinds of information could be involved as well. The e-mails clearly indicate that the data provided by MediaDefender was intended to be used for law enforcement purposes. In an e-mail to Mairs, Bartram says that the system must be specifically designed "to satisfy the legal and evidentiary requirements" before use. "On your end, the peer-to-peer crawler will be identifying files matching the established search criteria from various hosts," wrote Bartram. "This data will then be collected, filtered for New York resident ip addresses (to the accuracy limits imposed by geo-query tech). The data will then be transferred to us where; on our end, a separate piece of software will use that data to connect into the network and download the file from a host and store it on our servers for evidence retention and further analysis." It is not clear whether or not the project with the Attorney General's Office has any connection with the MiiVi project. At this time, we have not uncovered any substantial evidence to indicate that such a connection exists. Some evidence in the e-mails indicates that the system devised by MediaDefender in collaboration with the Attorney General's Office was targeted by a hacker. "[A]n ip from, what appears to be sweden, connected to the server using your username, made two failed password entries and then disconnected 4 seconds after the initial connection," Bartram informed MediaDefender. "Considering the nature of the information being collected, I would like to restrict access as much as possible." McCartney followed up soon after with an e-mail to Grodsky and Mairs. "Is this one of your engineers? Because if not, this is very disturbing! Who ever [sic] this was obviously had the non standard port as well as your user name to attempt these logins," wrote McCartney. "This leads me to believe that your system is compromised and/or our communications were either sniffed or accessed providing this fella with much of the relevant information to attempt access. As of now, all out side [sic] access has been disabled until we can figure this out further." It is possible that the individual who attempted to infiltrate the server is associated with the organization behind the MediaDefender e-mail leak. McCartney's concerns represent the only instance in the MediaDefender e-mails where anyone expresses suspicion that the messages are being intercepted and obtained by a third party. Universal Music Group contract One of the most informative documents included in the leaked e-mails is a draft of MediaDefender's confidential contract with Universal Music Group. The contract reveals exact details of MediaDefender's pricing structure and services and provides insight into which P2P networks the company is targeting. MediaDefender charges $4,000 for one month of protection for an album, and $2,000 for one month of protection for a track. Clients are also given access to MediaDefender's reports and statistical analysis. In the contract, the company claims that it "will perform Services against approximately twelve million" file-sharing users at any given time and will target the fifteen most popular P2P networks. Targeted networks include FastTrack, Gnutella, IRC, Usenet, DirectConnect, eDonkey, MP2P, Kademlia, Overnet, BitTorrent, SoulSeek, and Shareaza. The contract also provides detailed explanations of MediaDefender's efficacy testing practices. Other odds and ends There is simply too much information in the MediaDefender e-mails for us to cover in detail. We leave further analysis of the data as an exercise to the reader. We did encounter, however, a few other things worthy of note. There are detailed statistics that illuminate the efficacy of MediaDefender's file-sharing mitigation tactics and an extensive discussion of new techniques used by the company. The e-mails, unfortunately, also contain some highly sensitive financial information, including a spreadsheet with the salaries, Social Security numbers, and home addresses of individual MediaDefender software developers. There are also e-mails that discuss MediaDefender's competition intelligence activities, where they attempt to discover file-sharing mitigation tactics used by competitors like MediaSentry. The e-mails contain information about the personal life of MediaDefender employees as well. One particularly ironic example can be found in an e-mail sent by Mairs, the MediaDefender employee whose technical ineptitude was ultimately responsible for the leak. "I was out of the office yesterday because my son stuck something up his nose and I had to take him to urgent care. I guess we know where he gets his smarts from Conclusion The cold war being waged between MediaDefender and P2P copyright infringers is rife with mutual deception, but one fact shines through all of the layers of obfuscation: MediaDefender consistently underestimates the ingenuity, resourcefulness, and dedication of its adversaries. In this case, it could cost the company everything. Internet users are beginning to demand a higher level of transparency and accountability from companies that operate within the Internet ecosystem. Companies like MediaDefender that rely on secrecy and discretion unintentionally invite scrutiny by attempting to hide. Although many of MediaDefender's innermost secrets have been laid bare by this leak, there are many aspects of the company that remain shrouded in mystery. The ultimate purpose of the MiiVi site, for instance, is still an enigma. In some ways, the information in these e-mails raises more questions about MiiVi than it answers. It is likely that many additional details about MediaDefender's operations will be disclosed to the public as new secrets are uncovered in the e-mails. The rate at which these e-mails propagate across the Internet may also stand as a testament to the difficulty of trying to stand between consumers and their torrents. http://arstechnica.com/news.ars/post...t-project.html  MediaDefender Anti-Piracy Tools Leaked Ernesto The MediaDefender-Defenders have released the source code for the “trapping” and decoy software that MediaDefender uses to spread fake files on P2P networks. Similar to the previously released e-mails, tracking database and phone call this leak is also spread by the group that goes by the name “MediaDefender-Defenders“. In the .nfo that was posted with the torrent we read: The source is complete for their operations regarding Kazaa, bittorrent, gnutella etc. This system is now released for the public in order to identify the decoys they set up. A special thanks to the MD employee that gave this to us. It appears that this leak was not collected from the e-mails. The MD-Defenders themselves claim that a MD employee handed over the files to them, but this hasn’t be verified by other sources at this point. This leak contains a wealth of information and seriously harm MediaDefender’s future operations. BitTorrent tracker owners and other admins who are involved in managing P2P networks can utilize the leaked information to brace themselves against companies like MediaDefender, who try to pollute their networks with fake files. From the leak it seems that MediaDefender is active on virtually every P2P network, including Usenet. Not surprisingly, most applications are dedicated to BitTorrent, which is probably their main target because of its popularity. Application names BTPoster, BTSeedInflator, BTDecoyClient and BTInterdictor make it quite obvious what they are supposed to do. At this point it is still unclear who the MediaDefender-Defenders are and how they got their hands on all this information. MediaDefender has announced that the FBI will be investigating the source of the leaks. To be continued? Update: A list of leaked utilities is now available: AresDataCollector, AresLauncher, AresProtector, AresSupernode, AresUDPDataCollector, AutoUpdater, AutoUpdaterSource, BTClient, BTDataCollector, BTDecoyClient, BTInflationDest, BTInterdictor, BTIPGatherer, BTPoster, BTRemover, BTScraper, BTScraperDLL, BTSearcher, BTSeedInflator, BTTorrentGenerator, BTTorrentSource, BTTracker, BTTrackerChecker, CVS, DCMaster, DCScanner, DCSupply, DistributedKazaaCollector, DllLoader, ED2KSupplyProcessor, EdonkeyIpBanner, FastTrackGift, FastTrackGiftDecoyer, GnutellaDecoyer, GnutellaFileDownloader, GnutellaProtector, GnutellaSupply, KademliaProtector, KazaaDBManager, KazaaLauncher, KazaaSupplyProcessor, KazaaSupplyTaker, KazaaSwarmerDest, KazaaSwarmerDistributedSource, KazaaSwarmerDownloader, KazaaSwarmerSource, MediaMaker, MediaSwarmerDest, MediaSwarmerSource, MetaMachine, MetaMachineHashSetCollector, MetaMachineSpoofer, MI-GnutellaSupply, MovieMaker, NameServer, NetworkMonitor, OverNetLauncher, OvernetProtector, OvernetSpoofer, P2PFileIndexer, PioletDC, PioletPoisoner, PioletSpoofer, SamplePlugIn, SLSKSpooferDLL, SoulSeekClient, StatusDest, StatusSource, SupernodeCollector, SupernodeController, SupernodeDistributer, SupplyProcessor, TKCom, TKFileTransfer, TKLauncher, TKProjectManager, TKSyncher, UsenetPoster, UsenetSearcher, WatchDogControllerDestination, WatchDogControllerSource, WinMxDC, WinMxLauncher, WinMxProtector, wma generator http://torrentfreak.com/mediadefende...leaked-070920/  P2P Sites Ridicule MediaDefender Takedown Notices in Wake of e-Mail Leak Ryan Paul Peer-to-peer (P2P) poisoning company MediaDefender has sent a flurry of takedown notices and legal threats to P2P web sites that are facilitating the propagation of a 700MB archive of internal MediaDefender e-mail that was leaked onto the Internet this week. The e-mails, which were obtained by a group that calls itself MediaDefender-Defenders, reveal that the company attempted to deceive the public after the disclosure of its affiliation with the MiiVi site and was providing information about file-sharing network users to the New York State Attorney General's office. MediaDefender is now in damage control mode and hopes to slow the spread of the e-mails by intimidating P2P site operators. MediaDefender is represented by Sheppard, Mullin, Richter & Hampton (SMR&H), which is recognized one of the top law firms in the United States. The P2P sites are unimpressed with the empty threats. Although MediaDefender president Randy Saaf was eager to tell us a fabricated cover story after the MiiVi incident, MediaDefender has not responded to our numerous requests for comment this week. Similarly, the New York General Attorney's office has declined to provide a response to our inquiries. MediaDefender has, however, contacted several popular P2P sites, including isoHunt, which provided us with a complete record. "Despite security precautions by our client, a person or persons illegally accessed MediaDefender's email and other files," says a cease and desist notice sent to isoHunt and seen by Ars. In the notice—which cites various sections of the Computer Fraud and Abuse Act, the Electronic Communications Privacy Act, and the California Computer Data Access and Fraud Act—SMR&H attorney Robert S. Gerber requests that isoHunt "immediately and permanently cease and desist from posting, distributing or otherwise making available MediaDefender's trade secrets and confidential information." The popular P2P site's formal response to SMR&H is filled with caustic wit and considerable legal expertise. "If Mr. Gerber is truly as experienced in IP law as his bio claims he is," asks the isoHunt administrator in his response, "why is it that he is incapable of composing a DMCA takedown notice as per USC Title 17 Section 512?" The isoHunt administrator explains that Gerber failed to adequately specify the allegedly infringing content as required by law. The administrator also helpfully provides a link to a valid sample complaint so that SMR&H will be less likely to send the improper information in their second attempt. The following is an excerpt of the isoHunt administrator's response: "This e-mail serves as a counter notification under USC Title 17 Section 512 (c)(3)(A)(iii) that you have failed to properly identifying links to content that allegedly infringes your copyright/trademark/rights (or, in this case, has something to do with really embarrassing trade secrets *and* employee social security numbers) AND you have failed to address your e-mail to the appropriate agent, namely copyright@isohunt.com, so I invite you and your clients to take a long walk off a short pier, since you and/or your clients might actually manage to NOT get something that simple wrong." In closing, the isoHunt administrator says that the he will comply with the request if it is properly submitted. "Despite us being located in Canada, if you do actually figure out how to compose a valid DMCA notice, we will honor it," he concedes, "just as soon as we're done laughing at you." Torrent site Meganova received an identical letter from SMR&H, but responded publicly and with a bit less civility. "Dearest little asstunnels, Let me start off by thanking you for your pitiful attempt to have your e-mails removed from the entire internet," Meganova's response says. "In case you haven't noticed, this site is located in Europe (I hope you can point it out on a map) where your stupid copyright claims have no base. But fair is fair you guys did suffer over the past week so here's bit of advice to you guys: F*** you! F*** you again! F*** you again and again and again!" (I'm guessing that an "asstunnel" is what you get when a European whose first language isn't English tries to say "asshole." It seemed awkward when I first read the response, but the expression has since grown on me.) A web site named after the organization behind the leak, MediaDefender-Defenders, has set up HTML archive that includes all of the e-mails, largely uncensored, but with minor modifications to protect MediaDefender employees from identity theft. The site also published an e-mail allegedly sent by Saaf himself. "I am the CEO of MediaDefender," the message says. "We have begun our civil and criminal investigations into the stolen e-mails from our company. We are meeting with the FBI on monday. Your IP address has been logged. I hope it was worth the thrill." The site has been running intermittently since its launch, and the disruptions are thought to be the result of massive traffic coupled with a denial of service attack apparently launched by MediaDefender. Attempting to stop the spread of the e-mails is an exercise in futility at this point. MediaDefender's entire business model has been based on recognition of the inescapable fact that litigation cannot stop the spread of content on the Internet, so it is ironic that the company has turned to legal threats. In the past, we have seen attempts to stifle the dissemination of information on the Internet backfire and compel activists to promote broader distribution. Given that reality, MediaDefender might want to lay off of the threats for the time being. http://arstechnica.com/news.ars/post...mail-leak.html  Interview with MediaDefender Defenders.com Thomas Mennecke Unless you've been residing under a rock of monumental proportions, it should come as little surprise that MediaDefender's very confidential and private internal emails were intentionally leaked online. The contents compose of approximately 700 megabytes of email correspondence, a phone conversation between a law enforcement official and employees of MediaDefender, a list of IP addresses MediaDefender uses, and decoy file statistics used against the Gnutella network. MediaDefender, as many people are aware, is an organization that intentionally floods P2P networks with corrupt or false files. Music and movie studios hire MediaDefender with the intention of discouraging file-sharers from downloading unauthorized files. MediaDefender has existed for the better part of 7 years, with a success rate that is now called into deep question. In one segment of the leaked emails, a MediaDefender employee shares the humor when a music executive questions whether his label's music is showing a decline in sharing on college campuses. Additionally, MiniNova's latest blog entry demonstrates MediaDefender's frustration while attempting to corrupt their torrent index. The security failure surrounding MediaDefender is one of the most damaging intelligence leaks in recent Internet history. While likely to be downplayed by some, the sheer amount of intelligence divulged is colossal. The information contained within the 700 megabyte mbox file contains strategy, IP addresses used by MediaDefender, and tactics used against certain P2P networks. It's true enough however, that those who downplay the blunder may actually be correct. eMule (eDonkey2000) and BitTorrent appear difficult to corrupt, thanks in large part to the comment and moderation system of those running indexing sites. In that respect, MediaDefender's already weak effectiveness is irrelevant of the leak. The windfall of the massive leak is taking on a culture of its own. MediaDefender-Defenders, those behind the attack, are considered heroes among many in the Internet community. Their efforts against one of the more disliked anti-P2P organizations has had a galvanizing effect and given a substantial victory to the opposition in the online copyright wars. The attack has elevated the conflict, as it demonstrates that the music and movie industry's efforts and agents are not immune to counter-intelligence manipulation. So who's part of this micro-culture surrounding MediaDefender-Defenders? There's MediaDefender-Defenders.com, a collaborative project by two individuals looking to effectively disseminate the leaked information. They are not in any way connected to the MediaDefender-Defenders, however they do seek to carry on their message by simplifying access to the leaked information. The site contains all the currently leaked information with a small twist. "Forrest F.", who works on content of the site, managed to convert the mbox file into an organized and simplified web based thread - allowing otherwise unknowledgeable users to read the leaked contents. "[The mbox file is] just big, and very hard to read. So after Googleing a few things, I found this: http://www.mhonarc.org. It's a Perl Script that does the job, after some heavy tweaking, I started converting -- it was 8 hours before it was done. I pretty much had taken a book that all the pages where out of order and chaos, and turned it into something easy to read. Also, I was brave; I don't know what the FBI/lawyers could [have] done to me." Forrest F.'s endeavor hasn't been without its fair share of hiccups so far. His original domain, jrwr.hopto.org, was forced offline by his ISP, leaving his hopes nearly abandoned. However, an unnamed individual donated the MediaDefender-Defenders.com domain, and Forrest F. found a new host in Norway. Even under his initial domain, Forrest F. realized his idea would be successful. "After some reading I was like "The Public needs to know this!" So I put it on a slow server in my own home, it was up for 17 hours - 1.4 million hits!" Additionally, MediaDefender-Defenders.com has received two legal threats - one from MediaDefender's legal consul, and one from an individual who claims to be the CEO of the embattled company, Randy Saaf. The legal threat, which appears legitimate, threatens civil and criminal action for posting the material online. However, Forrest F. doesn't appear concerned. "Since the server is in Norway, We don't have to really worry." Yet in a concerning development, MediaDefender-Defenders.com was knocked offline yesterday in a suspicious Denial of Service attack. Remedying this situation, Forrest F. and his crew found refuge with none other than The Pirate Bay, who is hosting the site with prq.se. Since the switch, the site has been stable and with much fewer problems. And with over 2 Gbps throughput capacity, the new host should be able to handle the increasing load. In a style reminiscent of The Pirate Bay, MediaDefender-Defenders.com has a public reaction page to their legal threats. Although MediaDefender and their legal counsel are no doubt taking this breech very seriously, it appears that MediaDefender-Defenders.com is following The Pirate Bay's lead, as it too believes that it's safe in Scandinavia. http://www.slyck.com/story1586_Inter...r_Defenderscom  The Pirate Bay Files Charges Against Media Companies Thanks to the email-leakage from MediaDefender-Defenders we now have proof of the things we've been suspecting for a long time; the big record and movie labels are paying professional hackers, saboteurs and ddosers to destroy our trackers. While browsing through the email we identified the companies that are also active in Sweden and we have tonight reported these incidents to the police. The charges are infrastructural sabotage, denial of service attacks, hacking and spamming, all of these on a commercial level. The companies that are being reported are the following: Twentieth Century Fox, Sweden AB Emi Music Sweden AB Universal Music Group Sweden AB Universal Pictures Nordic AB Paramount Home Entertainment (Sweden) AB Atari Nordic AB Activision Nordic Filial Till Activision (Uk) Ltd Ubisoft Sweden AB Sony Bmg Music Entertainment (Sweden) AB Sony Pictures Home Entertainment Nordic AB Stay tuned for updates. http://thepiratebay.org/blog/86  Google Plans New Undersea "Unity" Cable Across Pacific Grahame Lynch Google is planning a multi-terabit undersea communications cable across the Pacific Ocean for launch in 2009, Communications Day has learned. The Unity cable has been under development for several months, with a group of carriers and Google meeting for high-level talks on the plan in Sydney last week. Google would not strictly confirm or deny the existence of the Unity plan today, with spokesman Barry Schnitt telling our North American correspondent Patrick Neighly that "Additional infrastructure for the Internet is good for users and there are a number of proposals to add a Pacific submarine cable. We're not commenting on any of these plans." However, Communications Day understands that Unity would see Google join with other carriers to build a new multi-terabit cable. Google would get access to a fibre pair at build cost handing it a tremendous cost advantage over rivals such as MSN and Yahoo, and also potentially enabling it to peer with Asia ISPs behind their international gateways - considerably improving the affordability of Internet services across Asia Pacific. Communications Day cannot confirm the identity of the other carriers working with Google, although we have learned that both Asia Netcom and Telstra have discussed the concept with the California-based search and online advertising giant. One source suggested that the main player behind the planned Asia America Gateway cable - Telekom Malaysia - has not been invited to participate in talks. The same source speculated that at least half a dozen companies are party to the plans. The exact route for the cable is not yet finally determined although there are plans for a configuration using two separate routes to provide network diversity. It would potentially also be able to service Australia via interconnect to new and existing cables in Guam and Hawaii. The Unity name was first revealed in public in early September when Level 3 executive Mike Saunders listed it as one of several new cables planned across the Pacific in a Singapore conference presentation. Saunders' presentation warned of the potential for the new cables to create a new trans-Pacific capacity bubble, although he did not link Unity to Google. His presentation said Unity was planned for a service launch in 2009. Google also hinted at its ambitions in job advertisements earlier this year. In one for a submarine cable negotiator, it specified a job description that said in part "These negotiators will work closely with vendors to identify highly cost-effective solutions under the most favorable commercial and technical terms possible. They will also be involved in new projects or investments in cable systems that Google may contemplate to extend or grow its backbone." Google's infrastructure ambitions are no secret. The company has committed substantial expenditure on dark fibre and a network of data centres across the United States, and also recently indicated its interest in bidding for new 700MHz spectrum allocations there. Communications Day reported on 8 February that Google had begun peering with ISPs, enabling them to reduce their reliance on transit services via Tier 1 non-peering major IP networks such as Level 3 and AT&T. Asked to comment on its hire of submarine cable specialists, Google told Communications Day "It should come as no surprise that Google is looking for qualified people to help secure additional network capacity. In some parts of the world, these people will work with submarine cables because there is a lot of ocean out there." Another source said that Google's move could be disruptive to the capacity industry as it takes a major source of traffic - and revenue - out of the general market place. http://www.commsday.com/node/186  A Hole in the Earth, a Hole in a Pocket 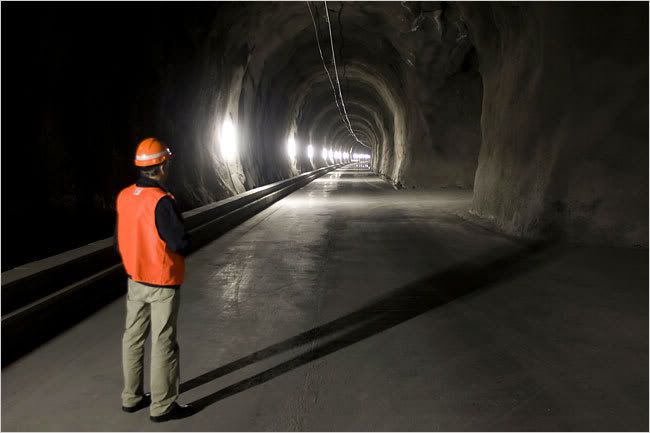 John Tagliabue With all the tunnels that pierce them, the Swiss Alps have often been likened to an enormous Swiss cheese. That comparison was awakened in recent months when a 22-mile rail tunnel was opened near this Alpine town. Costing $3.5 billion, the tunnel supplements a 19th-century tunnel through the Lötschberg, the mountain in whose shadow Frutigen lies. But the new one differs from older tunnels by piercing the base of the mountain, rather than its upper reaches. In addition to the main tunnel, for rail traffic, the mountain has been laced with 20 miles more of tunnel for maintenance and emergencies. “You can say it’s a true Swiss cheese,” said Patrick Belloncle, a spokesman for BLS, the Swiss company that built and operates the tunnel, ferrying visitors in a van through service tunnels that flank the main railway tunnel. But the Lötschberg tunnel is only part of an ambitious program to protect the Alps, a Swiss national heritage, from environmental damage. The environmental problem arises because the Alps lie right between two of Europe’s most dynamic economic regions, northern Italy and southern Germany, which have threatened to overwhelm the mountains with truck traffic. So more than a decade ago, the Swiss voted to impose steep tariffs on trucks passing through their country. They also voted to ban the construction of four-lane highways in the Alps. By last year Switzerland had collected more than $1.1 billion in tolls. The money has been used to improve older tunnels and build new ones to put freight on rails, either directly or by putting truck trailers onto flatbed rail cars. But when the Swiss go, they go first class. When the tunnel is fully operational in December, it will accommodate not just 70 freight trains a day, but as many as 30 passenger trains, capable of going 120 miles per hour, cutting an hour off the trip from Basel, in northern Switzerland, to the south. The Swiss are not finished, either. They are now busily digging an even more ambitious 35-mile tunnel under the St. Gotthard Pass to the east, to supplement two existing 19th-century tunnels, to be completed by 2016. By 2009, the Swiss want to reduce the number of trucks that pass over the country’s north-south roads to 650,000 a year, from 1.4 million in 2000, which would continue a long decline in truck traffic. Since 1995, such traffic has swollen by 40 percent in the European Union, but has declined by 8 percent in Switzerland. Of course, all of this digging was a boon for little Frutigen, whose squat wooden chalets, liberally sprinkled with geraniums, shelter hikers in summer and skiers in winter. “There was quite a bit of noise and dust,” said Peter Josi, 40, who works at the garden center and grocery store near Frutigen’s remodeled train station. “On the other hand, the workmen came and shopped here.” Bert Wäfler, 23, who works out of a small wooden shop jammed with bicycles for sale and hire, recalled wistfully the busy days of construction, when the town was flooded with 1,200 or so workers, many of them employees of big Austrian contractors. “Lots of Austrians worked on the tunnel, and they needed bikes to get around,” he said. “On weekends they had free time, but couldn’t go home to Austria, so they rented bikes.” “Now it’s quieter,” he said. “Only a few Austrians are here. It didn’t really bring us very much.” Karl Klossner agrees that for some, the party is over. Mr. Klossner, 56, the part-time speaker of Frutigen’s town council, recalled how big contractors from abroad came and created jobs. “Not only in construction, in retail, too,” he said. “Construction workers shopped here, they ate in the restaurants, and in the evening they went out to drink a beer.” He added, “I think it’s fair to say that we lived above our means.” But the tunnel brought some lasting benefits as well, and the town intends to exploit them, said Mr. Klossner, a civil engineer with the rank of colonel in the Swiss Army. The gash in the mountain to build the tunnel has freed up warm underground waters that the town wants to channel into a new center for raising warm-water fish, like sturgeon, and tropical fruit. When the $21 million center is finished, Mr. Klossner said, it could produce as much as six tons of Swiss caviar a year and 60 tons of tropical fruit. http://www.iht.com/articles/2007/09/...ope/tunnel.php  World’s Languages Dying Off Rapidly John Noble Wilford Of the estimated 7,000 languages spoken in the world today, linguists say, nearly half are in danger of extinction and are likely to disappear in this century. In fact, they are now falling out of use at a rate of about one every two weeks. Some endangered languages vanish in an instant, at the death of the sole surviving speaker. Others are lost gradually in bilingual cultures, as indigenous tongues are overwhelmed by the dominant language at school, in the marketplace and on television. New research, reported today, has identified the five regions of the world where languages are disappearing most rapidly. The “hot spots” of imminent language extinctions are: Northern Australia, Central South America, North America’s upper Pacific coastal zone, Eastern Siberia and Oklahoma and Southwest United States. All of the areas are occupied by aboriginal people speaking diverse languages, but in decreasing numbers. The study was based on field research and data analysis supported by the National Geographic Society and the Living Tongues Institute for Endangered Languages, an organization for the documentation, revitalization and maintenance of languages at risk. The findings are described in the October issue of National Geographic magazine and at www.languagehotspots.org. At a teleconference with reporters today, K. David Harrison, an assistant professor of linguistics at Swarthmore College, said that more than half of the languages have no written form and are “vulnerable to loss and being forgotten.” When they disappear, they leave behind no dictionary, no text, no record of the accumulated knowledge and history of a vanished culture. Dr. Harrison; Gregory D. S. Anderson, director of the Living Tongues Institute in Salem, Ore., and Chris Rainier, a filmmaker with the National Geographic Society have traveled in recent years to many parts of the world, the beginning of what they expect to be a long-term series of projects to identify and record endangered languages. The researchers interview and make recordings of the few remaining speakers of a threatened spoken language, and collected basic word lists. The projects, some of which extend over three to four years, involve hundreds of hours of audio recordings, development of grammars and preparation of children’s readers in the subject language. The research has especially concentrated on preserving language families that are on their way out. In Australia, where nearly all of the 231 spoken aboriginal tongues are endangered, the researchers came upon such tiny language communities as the three known speakers of Magati Ke, in the Northern Territory, and the three Yawuru speakers, in Western Australia. In July, Dr. Anderson said, they met the sole living speaker of Amurdag, a language in the Northern Territory that had already been declared extinct. “This is probably one language that cannot be brought back, but at least we made a record of it,” Dr. Anderson said, noting that the Amurdag speaker strained to recall words he had last heard from his late father. Many of the 113 languages spoken in the Andes Mountains and Amazon basin are poorly known and are rapidly giving way to Spanish or Portuguese, or in a few cases, to a more dominant indigenous language. In this region, for example, a group known as the Kallawaya use Spanish or Quechua in daily life, but also have their own secret tongue, used mainly for preserving knowledge of medicinal plants, some of which were previously unknown to science. “How and why this language has survived for more than 400 years, while being spoken by very few, is a mystery,” Dr. Harrison said news release. The dominance of English threatens the survival of the 54 indigenous languages of the Northwest Pacific plateau of North America, a region including British Columbia, Oregon and Washington. Only one person remains who speaks Siletz Dee-ni, the last of many languages once spoken on a reservation in Oregon. In Eastern Siberia, the researchers said, government policies have forced speakers of minority languages to use national and regional languages, such as Russian or Sakha. Forty Native American languages are still spoken in Oklahoma, Texas and New Mexico, many of them originally used by indigenous tribes and others introduced by Eastern tribes that were forced to resettle on reservations there, mainly in Oklahoma. Several of the languages are moribund. Another measure of the threatened decline of many relatively obscure languages, Dr. Harrison said, is that speakers and writers of the 83 languages with “global” influence now account for 80 percent of the world population. Most of the thousands of other languages now face extinction at a rate, the researchers said, that exceeds that of birds, mammals, fish or plants. http://www.iht.com/articles/2007/09/19/asia/talk.php  Arrrrr tichokes Tomorrow You'll Pay a Buccaneer for Corn? Paul Majendie Put a parrot on your shoulder, strap on a peg leg, hit the rum and start bellowing "Shiver me Timbers" -- Wednesday is International Talk Like A Pirate Day. "Pirates of the Caribbean" star Johnny Depp is not the only over-the-top buccaneer allowed to have fun. September 19 is your once-a-year chance to don an eye patch, sport a ridiculously large hat and keep on saying "Arrrrr. It all started back in the 1990s as a cult joke between two American friends -- John "Ol Chumbucket" Baur and Mark "Capn Slappy" Summers -- but really took off when syndicated columnist Dave Barry got to hear about their surreal festival. "We tap into that need for whimsy in people's lives," Summers says of the 24-hour celebration of quirkiness when they urge all self-respecting swashbucklers to show "pirattitude." International Talk Like a Pirate Day (TLAPD), which adopted Treasure Island star Robert Newton as its patron saint, now attracts fans from as far afield as Britain and Australia and even boasts a special Wikipedia site on the Internet. The day even has its own unofficial anthem -- American Tom Smith has written and recorded "Talk Like a Pirate Day" -- and Canadian sketch comedy troupe Loading Ready Run produced an educational video on how to swashbuckle with the best of them. Ol Chumbucket and Capn Slappy are bombarded with requests for TLAPD interviews and proudly boast on their own website that they are even now being immortalized in computer games. "That's fairly cool and geeky," Ol Chumbucket decided. Pirate fans around the world have rallied round, showing that surreal silliness is alive and well. An American soldier stationed in Iraq promised that "to celebrate, myself and others will wear an eye patch all day." Sydney, Australia is staging a harbor cruise with "flagons of grog at pub prices and prizes to treasure for the dandiest of outfits." A bar in Venice, Italy is holding an olive stone-spitting contest for would-be buccaneers. A Brazilian fan even sent a letter of support in a bottle while one overjoyed Argentinian whose birthday falls on the same day said "It will be difficult to talk in Spanish like pirates but we will try." http://www.reuters.com/article/oddly...88712020070918  Alex Wanted a Cracker, But Did He Want One? George Johnson IN “Oryx and Crake,” Margaret Atwood’s novel about humanity’s final days on earth, a boy named Jimmy becomes obsessed with Alex, an African gray parrot with extraordinary cognitive and linguistic skills. Hiding out in the library, Jimmy watches historical TV documentaries in which the bird deftly distinguishes between blue triangles and yellow squares and invents a perfect new word for almond: cork-nut. But what Jimmy finds most endearing is Alex’s bad attitude. As bored with the experiments as Jimmy is with school, the parrot would abruptly squawk, “I’m going away now,” then refuse to cooperate further. Except for the part about Jimmy and the imminent apocalypse (still, fingers crossed, a few decades away), all of the above is true. Until he was found dead 10 days ago in his cage at a Brandeis University psych lab, Alex was the subject of 30 years of experiments challenging the most basic assumptions about animal intelligence. He is survived by his trainer, Irene Pepperberg, a prominent comparative psychologist, and a scientific community divided over whether creatures other than human are more than automatons, enjoying some kind of inner life. Skeptics have long dismissed Dr. Pepperberg’s successes with Alex as a subtle form of conditioning — no deeper philosophically than teaching a pigeon to peck at a moving spot by bribing it with grain. But the radical behaviorists once said the same thing about people: that what we take for thinking, hoping, even theorizing, is all just stimulus and response. Was Alex only parroting when he showed off for Alan Alda on “Scientific American Frontiers” (one of the PBS productions the fictional Jimmy might have seen)? “What color smaller?” Dr. Pepperberg asked the parrot as she held up two keys. “Green,” he responded. Alex also seemed to understand concepts like “bigger,” “different” and “same.” Presented with a tray of colored cutouts — the numerals 1 to 6 — he could tell you which one was gray: “Four.” Many linguists argue that only human brains have the ability to nest ideas within ideas to form the infinitely recursive architecture of thought: When you’re done eating breakfast would you look in the box at the back of the table for the yellow rubber glove with the middle finger turned inside out? Alex could pull together a few simple concepts. Show him a group of objects and he could tell you, “What color is wood and four-corner?” or, “What shape is paper and purple?” Dr. Pepperberg was hoping to train Alex to spin his own recursions, informing her that the nut was “in the blue cup that’s on the tray” or “in the yellow box on the chair.” “I wish we had gotten further,” Dr. Pepperberg wrote in an e-mail message. “We were just beginning to get him to designate things like ‘in’ and ‘on.’ ” The deepest recursion is consciousness — knowing that you know and that you know that you know. In his recent book, “I Am a Strange Loop,” Douglas Hofstadter proposed that the richness of a creature’s mental representations be used to take the measure of its soul. The unit Dr. Hofstadter whimsically proposed is the “huneker,” named for James Huneker, a music critic who wrote that Chopin’s 11th Étude, in A minor, (Op. 25) was so majestic that “small-souled men, no matter how agile their fingers, should not attempt it.” If your average person’s soulfulness weighs in at 100 hunekers with a hamster down near 10, Alex hovered somewhere above the halfway mark. But there were moments when he seemed to reach for the top. In an talk on Edge.org, Dr. Pepperberg told of an effort to teach the parrot about phonemes using colored tokens marked with letter combinations like sh and ch. “What sound is green?” “Ssshh,” Alex answered correctly, and then demanded a nut. Instead he got another question. “What sound is orange?” “Ch.” “Good bird!” “Want a nut!” Alex demanded. The interview was over. “Want a nut!” he repeated. “Nnn ... uh ... tuh.” Dr. Pepperberg was flabbergasted. “Not only could you imagine him thinking, ‘Hey, stupid, do I have to spell it for you?’ ” she said. “This was in a sense his way of saying to us, ‘I know where you’re headed! Let’s get on with it.’ ” She is quick to concede the impossibility of proving that the bird was actually verbalizing its internal deliberations. Only Alex knew for sure. Next to infinity, one of the hardest concepts to grasp is zero. Toward the end of his life Alex may have been coming close. In a carnival shell game, an experimenter would put a nut under one of three cups and then shuffle them around. Alex would pick up the cup where the prize was supposed to be. If it wasn’t there he’d go a little berserk — a small step, maybe, toward understanding nothingness. A bigger leap came in an experiment about numbers, in which the parrot was shown groups of two, three and six objects. The objects within each set were colored identically, and Alex was asked, “What color three?” “Five,” he replied perversely (he was having a bad attitude day), repeating the answer until the experimenter finally asked, “O.K., Alex, tell me, ‘What color five?’ ” “None,” the parrot said. Bingo. There was no group of five on the tray. It was another of those high huneker moments. Alex had learned the word “none” years before in a different context. Now he seemed to be using it more abstractly. Dr. Pepperberg reported the result with appropriate understatement: “That zero was represented in some way by a parrot, with a walnut-sized brain whose ancestral evolutionary history with humans likely dates from the dinosaurs, is striking.” In a well-known essay, “What Is it Like to Be a Bat?” the philosopher Thomas Nagel speculated about the elusiveness of subjectivity. What was it like to be Alex that last night in his cage? We’ll never know whether there really was a mind in there — slogging its way from the absence of a cork-nut to the absence of Alex, grasping at the zeroness of death. http://www.nytimes.com/2007/09/16/we...f=weekinreview  Following His Trail to Danger and Joy  A. O. Scott There is plenty of sorrow to be found in “Into the Wild,” Sean Penn’s adaptation of the nonfiction bestseller by Jon Krakauer. The story begins with an unhappy family, proceeds through a series of encounters with the lonely and the lost, and ends in a senseless, premature death. But though the film’s structure may be tragic, its spirit is anything but. It is infused with an expansive, almost giddy sense of possibility, and it communicates a pure, unaffected delight in open spaces, fresh air and bright sunshine. Some of this exuberance comes from Christopher Johnson McCandless, the young adventurer whose footloose life and gruesome fate were the subject of Mr. Krakauer’s book. As Mr. Penn understands him (and as he is portrayed, with unforced charm and brisk intelligence, by Emile Hirsch), Chris is at once a troubled, impulsive boy and a brave and dedicated spiritual pilgrim. He does not court danger but rather stumbles across it — thrillingly and then fatally — on the road to joy. In letters to his friends, parts of which are scrawled across the screen in bright yellow capital letters, he revels in the simple beauty of the natural world. Adopting the pseudonym Alexander Supertramp, rejecting material possessions and human attachments, he proclaims himself an “aesthetic voyager.” Mr. Penn serves as both his biographer and his traveling companion. After graduating from Emory University in 1990, Mr. McCandless set off on a zigzagging two-year journey that took him from South Dakota to Southern California, from the Sea of Cortez to the Alaskan wilderness, where he perished, apparently from starvation, in August 1992. “Into the Wild,” which Mr. Penn wrote and directed, follows faithfully in his footsteps, and it illuminates the young man’s personality by showing us the world as he saw it. What he mostly saw was the glory of the North American landscape west of the Mississippi: the ancient woodlands of the Pacific Northwest, the canyons and deserts farther south, the wheat fields of the northern prairie and Alaska, a place that Mr. McCandless seemed to regard with almost mystical reverence. Mr. Penn, who did some of the camera work, was aided by the director of photography, Eric Gautier, who previously turned his careful, voracious eye on the wilds of South America in Walter Salles’s “Motorcycle Diaries.” That movie, like “Into the Wild,” finds epic resonance in a tale of youthful wandering and proposes that a trek through mountains, rivers and forests can also be a voyage of self-discovery. Mr. Salles’s film, in which Gael García Bernal played Che Guevara, found a political dimension in its hero’s journey. And while Chris’s fierce rejection of his parents’ middle-class, suburban life contains elements of ideological critique, Mr. Penn and Mr. Krakauer persuasively place him in a largely apolitical, homegrown tradition of radical, romantic individualism. An enthusiastic reader (with a special affinity for Tolstoy and Jack London), Chris is in many ways the intellectual heir of 19th-century writer-naturalists like John Muir and especially Henry David Thoreau, whose uncompromising idealism — “rather than love, than money, than fame, give me truth” — he takes as a watchword. (Had he survived, Mr. McCandless might well have joined the ranks of latter-day nature writers like Edward Abbey and Bill McKibben.) His credo is perhaps most succinctly stated by Thoreau’s mentor Ralph Waldo Emerson, who advised that “the ancient precept, ‘Know thyself,’ and the modern precept, ‘Study Nature,’ become at last one maxim.” One problem with this strain of American thought is that it sometimes finds expression in self-help nostrums and greeting-card sentiments. “If you want something in life, reach out and grab it,” Chris says to Tracy (Kristen Stewart), a teenage girl who develops a crush on him, collapsing Self-Reliance into something like an advertising slogan. But the movie’s theme, thankfully, is not so simple or so easily summed up in words. Mr. Penn, even more than Mr. Krakauer, takes the Emersonian dimension of Chris McCandless’s project seriously, even as he understands the peril implicit in too close an identification with nature. The book took pains to defend its young protagonist against the suspicion that he was suicidal, unbalanced or an incompetent outdoorsman, gathering testimony from friends he had made in his last years as evidence of his kindness, his care and his integrity. The film, at some risk of sentimentalizing its hero, goes further, pushing him to the very brink of sainthood. After Chris offers wise, sympathetic counsel to Rainey (Brian Dierker), a middle-aged hippie he has befriended on the road, the older man looks at him with quiet amazement. “You’re not Jesus, are you?” he asks. Well no, but it’s a comparison that Mr. Penn does not entirely discourage. (Note the final, man of sorrows image of Mr. Hirsch’s face and also an earlier shot of him floating naked in a stream, his arms extended in a familiar cruciform shape.) At the same time, though, “Into the Wild” resists the impulse to interpret Chris’s death as a kind of martyrdom or as the inevitable, logical terminus of his passionate desire for communion with nature. Instead, with disarming sincerity, it emphasizes his capacity for love, the gift for fellowship that, somewhat paradoxically, accompanied his fierce need for solitude. Though he warns one of his friends against seeking happiness in human relationships — and also rails incoherently against the evils of “society” — Chris is a naturally sociable creature. And “Into the Wild” is populated with marvelous actors — including Mr. Dierker, a river guide and ski-shop owner making his first appearance in a film — who make its human landscape as fascinating and various as its topography. The source of Chris’s wanderlust, and of the melancholy that tugs at the film’s happy-go-lucky spirit, is traced to his parents (William Hurt and Marcia Gay Harden), whose volatile marriage and regard for appearances begin to seem contemptible to their son. (His feelings for them are explained in voice-over by his younger sister, Carine, who is played by Jena Malone.) Fleeing from his mother and father, Chris finds himself drawn, almost unwittingly, to parental surrogates: a rowdy grain dealer in South Dakota (Vince Vaughn), a retired military man in the California desert (Hal Holbrook) and Rainey’s companion, Jan (Catherine Keener), who seems both carefree and careworn. Chris reminds some of these people of their own lost children, but all of them respond to something about him: an open, guileless quality, at once earnest and playful, that Mr. Hirsch conveys with intuitive grace. “You look like a loved kid,” Jan says, and “Into the Wild” bears that out in nearly every scene. He is loved, not least, by Mr. Penn, who has shown himself, in three previous films (“The Indian Runner,” “The Crossing Guard” and “The Pledge”) to be a thoughtful and skilled director. He still is, but this story seems to have liberated him from the somber seriousness that has been his hallmark as a filmmaker until now. “Into the Wild” is a movie about the desire for freedom that feels, in itself, like the fulfillment of that desire. Which is not to say that there is anything easy or naïve in what Mr. Penn has done. “Into the Wild” is, on the contrary, alive to the mysteries and difficulties of experience in a way that very few recent American movies have been. There are some awkward moments and infelicitous touches — a few too many Eddie Vedder songs on the soundtrack, for example, when Woody Guthrie, Aaron Copland or dead silence might have been more welcome — but the film’s imperfection, like its grandeur, arises from a passionate, generous impulse that is as hard to resist as the call of the open road. “Into the Wild” is rated R (Under 17 requires accompanying parent or adult guardian). It has profanity, brief nudity and some violent or otherwise upsetting scenes. INTO THE WILD Opens today in New York and Los Angeles. Directed by Sean Penn; written by Mr. Penn, based on the book by Jon Krakauer; director of photography, Eric Gautier; edited by Jay Cassidy; score by Michael Brook with songs and additional music by Eddie Vedder and Kaki King; production designer, Derek R. Hill; produced by Mr. Penn, Art Linson and Bill Pohlad; released by Paramount Vantage. Running time: 140 minutes. WITH: Emile Hirsch (Christopher McCandless), Marcia Gay Harden (Billie McCandless), William Hurt (Walt McCandless), Jena Malone (Carine), Brian Dierker (Rainey), Catherine Keener (Jan Burres), Vince Vaughn (Wayne Westerberg), Kristen Stewart (Tracy) and Hal Holbrook (Ron Franz). http://movies.nytimes.com/2007/09/21...wild.html?8dpc  After Test Runs, an Armory Is Ready to Declare, ‘Artists, Start Your Engines’ Carol Vogel As giant billows of smoke began filling the cavernous drill hall of the Seventh Regiment Armory one recent evening, there was no panic. Rather, there were shouts of exultation, along with what sounded like a chorus of foghorns. “Look, it’s going in the right direction,” said Doreen Remen, a founder of the Art Production Fund, a nonprofit organization that presents unusual public art projects. With her co-founder, Yvonne Force Villareal, and the artist Aaron Young she gazed upward with relief as the smoke began filtering out the open windows along the rafters. Four smoke machines had been brought in to simulate the conditions that could develop as 10 motorcycles ride around the 55,000-square-foot drill hall simultaneously. For Thursday evening’s test run the belching, thunderous machines had some competition: Wink 1100, a professional stunt rider who performed the trick sequences in the 2003 movie “Biker Boyz.” The Week in Review is edited and published by Jack Spratts. Wearing Tom Ford sunglasses, baggy blue jeans and a red-and-blue sweatshirt, he was enveloped in his own haze of smoke as he spun the wheels of his Honda CBR 954 on a designated patch of painted plywood. It was the prelude to a turning point in the Seventh Regiment Armory’s 128-year history: the first performance art piece ever presented there, masterminded by Mr. Young. Tonight 10 motorcycle stunt riders wearing sunglasses will ride for seven minutes on 288 panels of painted plywood covering the drill hall floor as 500 invited guests, including members of Hells Angels, watch from the bleachers above. With neon lights attached to the undersides of their bikes, the riders will follow synchronized movements choreographed by Mr. Young. The burnouts from their tires will yield colorful swirls, zigzags and snake patterns on the plywood panels, which have been coated in seven layers of fluorescent reds, pinks, oranges and yellows and then sealed with two coats of black acrylic. Titled “Greeting Card,” after a 1944 Jackson Pollock painting that has its own tangle of spirals, the work is described as both a performance piece and an action painting. When the riders have finished, they will have created a giant fluorescent multicolored floor piece that will remain on public view through Sunday. A film of the performance will be shown on a plasma screen in the hall. It is the first in a series of art exhibitions and performances planned for the building by a new nonprofit group, the Seventh Regiment Armory Conservancy, which in December took over management of the crenellated red-brick behemoth on Park Avenue between 66th and 67th Streets from New York State. The group still plans to hold the art and antiques fairs that have attracted throngs for decades, but Rebecca Robertson, the conservancy’s president and chief executive, suggested that the armory could become even more of a cultural destination. “The armory is neither a white-box gallery nor a proscenium stage,” she said. “Here you make it up. Luckily this space allows work that can’t be seen anywhere else in the city.” For now, she said, the conservancy is in the research and development phase. Still, workers have been cleaning the neglected building, and air-conditioning has been installed in the drill hall for the first time, eliminating the need for the special trucks that once piped in cool air during art and antiques fairs. The $150,000 budget for “Greeting Card” is being covered by a group of sponsors that include Tom Ford, the fashion designer, and Sotheby’s. Mr. Young, 35, a conceptual artist and sculptor, first began talking with the Art Production Fund about the piece last December at the Art Basel Miami Beach fair. “We didn’t think we could do this in New York,” Ms. Villareal said. “It required a large space with the audience watching the performance from above.” But as soon as she and Ms. Remen heard that the armory was seeking art projects, they met with Ms. Robertson. “Her reaction was, ‘Bring it on,’ ” Ms. Villareal said. Working at minimum wage, gallery assistants and students from Barnard and Columbia spent three days last week painting the panels. “It was like camp,” Ms. Remen said. Thursday evening’s smoke experiment was one of many trials and rehearsals. To ensure that the smoke from the motorcycles will not endanger the audience, the glass has been removed from the 28 windows high in the rafters of the drill hall. Still, guests are warned in small letters on the bottom of the performance invitation: “A ventilation system has been installed to reduce the smoke and exhaust. Earplugs will be provided for the noise. If you are sensitive to either, please request a protected viewing space.” In addition to a glassed-in room for warier viewers, the Art Production Fund will furnish the audience with face masks. Mr. Young said that given the challenges of the synchronization and the safety concerns, nothing had been left to chance. A month ago he did tests in an empty parking lot in the Bronx near Yankee Stadium. To inspire the riders involved in “Greeting Card,” he gave each a photocopy of the Pollock painting. “The spiral motion is the template,” he said. The 10 bikers — five stunt riders from Team G Unit along with five friends — will each have a designated 23- by 43-foot area on which to perform zigzags, power slides and circles. The neon lights on the bottom of each bike will allow the audience to follow the movements through the smoky haze. “I want it lit like a boxing rink, very hard-edged,” Mr. Young said. “Hopefully this will appeal to people who know nothing about motorcycles or about art,” he said as he examined shreds of tire rubber embedded in some of the wood panels, a byproduct of Wink’s brief motorcycle whirl. Although Mr. Young does not ride himself, it is not his first artistic encounter with motorcycles. In 2000, as a student at the San Francisco Art Institute, he created a piece called “High Performance,” enlisting a group of cyclists he met at a local motorcycle bar called the Zeitgeist. “I got them drunk until they said yes,” he recalled. The riders performed burnouts in a studio that was once used by Diego Rivera. The result was a 3 1/2-minute video that was eventually acquired by the Museum of Modern Art. When it is time for the 288 panels to leave the armory, Mr. Young plans to select about 20 of them to sell through the Art Production Fund. He and the fund will split the proceeds. Before the panels are sold, he plans to seal each one with a coat of clear resin. “That way it will keep the hot melted rubber fixed,” he said. Even though the ride itself will last only seven minutes, he explained, the panels will be “archival.” http://www.nytimes.com/2007/09/17/ar...gn/17armo.html  Local blues Is It Art Yet? And Who Decides? Roberta Smith North Adams, Mass. WHEN a museum behaves badly, it’s never pretty. But few examples top the depressing spectacle at the Massachusetts Museum of Contemporary Art. I refer to Mass MoCA’s decision to exhibit “Training Ground for Democracy,” an immense but incomplete work of installation art, despite strenuous opposition from Christoph Büchel, the Swiss artist who conceived it and oversaw its construction until his relationship with the museum dissolved in acrimony early this year. By opening this show without his assent, the museum has broken faith with the artist, the public and art itself. The legal principles at stake in this dispute will be argued on Friday when lawyers for the museum and Mr. Büchel face off in federal court in Springfield, Mass. Each side hopes for a summary judgment against the other. The Büchel project was an inspired, nervy move for Mass MoCA, which has struggled to find its voice since it opened eight years ago in a rehabilitated mill complex in downtown North Adams. It was the first American museum to commission one of Mr. Büchel’s dense, fraught creations, which compress masses of material and objects into historically charged labyrinthine environments through which viewers walk, climb and crawl. And the pairing made perfect sense, given that Mass MoCA has one of the largest galleries of any museum in the United States — known as Building 5 — and annually stages big installations there. “Training Ground for Democracy” was to be assembled at the museum’s expense, with its staff members seeking out and installing items on a long list in collaboration with Mr. Büchel. His outsize list included a two-story Cape Cod cottage, a leaflet-bomb carousel, an old bar from a tavern, a vintage movie theater and various banged-up rolling stock (a trailer, a mobile home, a bus, a truck). Nine full-size shipping containers were requested. There was even to be a re-creation of Saddam Hussein’s spider hole. But things did not go smoothly. By the end of January, and well past the scheduled Dec. 16 opening date, Mr. Büchel had departed for good and begun accusing the museum of interference, unprofessionalism and wasting his time. The museum said it had tried mightily to gather everything on Mr. Büchel’s wish list but balked at acquiring a burnt-out fuselage of a 737 airliner. It pointed out that it had spent more than double the show’s $160,000 budget; Mr. Büchel countered that an amount had never been agreed upon. Mass MoCA argues that it has a responsibility to deliver a show to its public. “At some point the realities of our budget, resources and staff imposed themselves,” Joe Thompson, the museum’s director, told The New York Times. Now the components of “Training for Democracy” loom as if in a desolate ghost town, surreally camouflaged by plastic tarps in Building 5. Mass MoCA says it shrouded the elements pending a court decision that it hopes will allow it to display the installation. Mass MoCA may have been a little naïve about what it was getting into with Mr. Büchel. Artists can be difficult and demanding, and the bigger the artwork, the greater the stress on all sides. And while Mr. Büchel’s environments are huge in scale, they are also often guided by a sense of horror vacui, and so obsessively detailed that they might best be described as panoramic collage. They’re like bristling three-dimensional history paintings: messy offices, banal living rooms, sinister hideouts, piles of old appliances or towers of newspapers, with each space telling its own story. It is as if the detritus of dozens of sad lives has been warehoused yet remains in use. Everyone has just gone out to lunch, or has been arrested. Occasionally there are moments of respite. In an installation that Mr. Büchel carved into Michelle Maccarone’s crumbling two-story gallery on the Lower East Side in 2001, for example, I spent a calm moment crouched in a child’s classroom chair while facing a blackboard that ran floor to ceiling — the room was only four feet high — wondering what on earth would come next. Since Mr. Büchel walked off the Mass MoCA project in January, accusations have flown back and forth like poison arrows, and it’s hard to sort out who did or didn’t do what and when. Mr. Thompson, director of Mass MoCA, said the museum had “clearly bent over backwards” for Mr. Büchel. Yet by opening the show, covered, last spring against Mr. Büchel’s wishes and now seeking a court’s go-ahead to remove the tarps, the museum renders all of that moot. If an artist who conceived a work says that it is unfinished and should not be exhibited, it isn’t — and shouldn’t be. End of story. (His lawyer cites a federal law that says as much, the Visual Artist Rights Act. But Mass MoCA argues that the law applies only to finished works of art.) It’s hard for a museum to recover when it forfeits the high ground. To this day the Corcoran Gallery of Art remains infamous for canceling its 1989 exhibition of Robert Mapplethorpe photographs after his work was denounced by Senator Jesse Helms, Republican of North Carolina. To conservatives’ horror, the show had been partly financed by the National Endowment for the Arts. The meltdown at Mass MOCA is sad for all concerned, yet is also a reflection of the changes wrought since the late 1960s, as installation art evolved from renegade form into an institutional staple of ever-bigger galleries and museums. Although museums still focus most of their energy on finished works that they believe should be shown or collected, they now routinely function as patrons, using their budgets to help artists create works from scratch. They have happily become producers because these days installation artworks are often crowd pleasers, circuslike in their appeal. Viewers gasp at their scale or their sensational optical effects, as with “Sleepwalker,” the Doug Aitken video display on the Museum of Modern Art’s facades last winter. Yet the experience can be very superficial. It’s strange to think that these big temporary installations may be the only contemporary art that some people know or enjoy. And there are dangers, including the possibility that in controlling the purse strings, a museum starts thinking of itself as a co-author who knows what the artist wants better than he or she does. Yes, artists can be formidably difficult. The larger the artwork, the bigger the ego. Maybe Mr. Büchel was behaving like a diva. But what some call temper tantrums are often an artist’s last, furious stand for his or her art. Initially I felt some sympathy for Mass MoCA. I was impressed that it had the courage to be the first American museum to take on Mr. Büchel, whose outsize ambition has anted up ideas implicit in Kurt Schwitters’s Merzbau environments of the 1930s, Arman’s “Le Plein” of 1960 and Gordon Matta-Clark’s sliced buildings of the ’70s. But when the museum became set on opening the unfinished piece over Mr. Büchel’s objections, my sympathy evaporated. And when I visited MassMoCA, my sentiments curdled. The shrouded non-Büchel is a kind of museological car crash. You can’t stop looking, but tarps or no tarps, you also want to avert your eyes, especially if you are familiar with his previous work. Mr. Büchel contends that the display damages his reputation. It will certainly give people unfamiliar with his obsessive, history-driven aesthetic an inaccurate sense of his art, and this is indeed a form of damage. But by opening this strange quasi display, MassMoCA does even more damage to itself and to its reputation as a steward of art and as a conduit between living artists and the public. My first thought while walking among the tarps is that no one working at the museum had ever seen a finished Büchel, which would be pretty astonishing, especially since a very large Büchel installation was on view in London while things were unraveling in North Adams. Titled “Simply Botiful,” this 13,000-square-foot London piece was commissioned by the artist’s primary dealer, Hauser & Wirth, in its huge warehouse in the Coppermill neighborhood. Interestingly, the gallery says it cost £80,000, or about $162,000, and was assembled by Mr. Büchel and 12 assistants and workers in three weeks. This might seem to suggest that when given full artistic control, Mr. Büchel delivers. At Mass MoCA, meanwhile, there is a sense of something gone deeply awry. In one of two smaller galleries in Building 5, the museum has removed the bar that was part of the Büchel piece to make way for “Made at Mass MoCA,” a self-serving, slapped-together display of photographs of previous installations. It accomplishes little but to suggest the frequent vacuity of those projects and underscore the possibility that the Büchel was too big a reach for the museum. Beyond that and up a flight of stairs, things get stranger still. Here you’ll find a wall covered with Mr. Büchel’s extensive wish list, which conceptually conveys something of the surface density, historical references and regional evocations he planned to incorporate. Requested are accouterments for Mass and Baptism; a hospital bed and related medical equipment; eight voting booths; hundreds of old tires; piles of old computers; 1,000 beverage cups from a race track; 1,000 feet of barbed wire; 12 grenades and 35 pounds of bullet casings; eight body bags and 75 white protective suits; four prosthetic legs; decorations and campaign buttons from election rallies; a concession stand, popcorn and popcorn buckets; Christmas lights; and 16 large bags of corn leaves and husks. The list scrolls along in chapterlike clusters of related items, evoking recent events in or involving the United States, including the 2000 presidential election, Hurricane Katrina and the war in Iraq. On the opposite wall newspaper articles and editorials about the controversy are pinned to the wall, although a scathing indictment of Mass MoCA by The Boston Globe’s art critic is absent. The museum deserves to be scathed. Although there may be parts of the installation proper that Mr. Büchel considers finished, what is visible above and below the tarps today is barely the skeleton of a Büchel. It’s just a lot of stuff. You are reminded of Hollywood, where directors (that is, artists) are routinely denied “final cut.” Of course, Renaissance popes often had final cut too. But I prefer to invoke the spirit of Robert Rauschenberg, who, when asked to contribute to a show of portraits of the Paris dealer Iris Clert in 1961, sent a telegram that read, “This is a portrait of Iris Clert if I say so.” Never underestimate the amount of resentment and hostility we harbor toward artists. It springs largely from envy. They can behave quite badly, but mainly they operate with a kind of freedom and courage that other people don’t risk or enjoy. And it can lead to wondrous things. In the end it doesn’t matter how many people toil on a work of art, or how much money is spent on it. The artist’s freedom includes the right to say, “This is not a work of art unless I say so.” http://www.nytimes.com/2007/09/16/ar...gn/16robe.html  Museum Can Show Disputed Artwork, Judge Rules Randy Kennedy A federal judge ruled yesterday that the Massachusetts Museum of Contemporary Art has the right to display an immense unfinished installation by Christoph Büchel, a Swiss artist whose relationship with the museum fell apart early this year, leading to a bitter public battle over control of the work and over artists’ rights in general. The judge, Michael A. Ponsor, in Federal District Court in Springfield, Mass., said that the museum’s display of the work would not, as Mr. Büchel argued, violate the Visual Artists Rights Act of 1990, which provides that an artist has the right to “prevent the use of his or her name as the author of the work of visual art in the event of a distortion, mutilation, or other modification of the work.” In this case, one watched closely by the art world for the effect it might have on the relationship between museums and artists who create huge, complex works, Judge Ponsor said that the artist rights act did not apply, in essence because it has no provision to prohibit showing an unfinished work of art simply because it is unfinished. As long as the museum, known as Mass MoCA, made clear to visitors that the work was not completely realized, there was no reason the installation could not be shown, the judge said. Joseph C. Thompson, the director of the museum, which is in an old mill complex in North Adams, Mass., said in a telephone interview that he was happy with the decision. But he added that his institution would now think long and hard about what to do with the work inside its Building 5, which covers an area the size of a football field and includes such Büchel components as a wrecked police car, a carnival ride rigged with bomb casings, a dilapidated two-story house, a mobile home and a rusted oil tanker. “We very much appreciate the fact that the court granted us the right to use our discretion and we’ll use it very carefully,” said Mr. Thompson, who added that he would consult with art scholars, people who helped work on the installation and many of the museum’s visitors before he decided whether to open the unfinished installation or dismantle it. “It’s not a decision that we’ve reached yet,” he said, but added: “Our mission is to help make new work and we’re very anxious to move forward.” In May, just after it went to court against Mr. Büchel, the museum opened a show it called “Made at Mass MoCA,” that allowed visitors to enter Building 5 but shielded Mr. Büchel’s work almost completely from view by hanging pieces of tarp in front of it. Several art critics and scholars have been highly critical of the museum’s decision to go to court and allow access to the shielded work, contending that artists should have broad power over the disposition of their work. “In my view, under no circumstances should a work of art be shown to the public until the artist has determined that it is finished,” Robert Storr, dean of the Yale University School of Art, wrote in an affidavit filed in the case. Donn Zaretsky, Mr. Büchel’s lawyer, said in an e-mail message that he and his client were “obviously very disappointed in the judge’s ruling, and we’re exploring our options for appeal.” Even in the ever more expensive and complicated world of large contemporary installations, the kind of fight that has been waged between Mr. Büchel and Mass MoCA is unusual. Mr. Büchel has become well known for creating elaborate, politically provocative environments for viewers to wander, and sometimes to crawl, through. His conception for the work in Massachusetts, to be called “Training Ground for Democracy,” was that it would mimic and mock, in some ways, the kind of training that is used by the United States military to help soldiers adapt to situations in unfamiliar cultures. In one part of the installation, for example, a space appeared to be a dressing room to be shared by both rioters and riot police, as if they were all simply playing a part. But after work began last fall on the installation, one of Mr. Büchel’s most ambitious, relations between the artist and the museum deteriorated and finally degenerated into an angry standoff. The artist contends that the museum badly mishandled the project and did not follow his instructions, allowing costs to climb. The museum contends that Mr. Büchel was difficult to work with almost from the start and made many demands and changes to the project as it was being built, causing an initial budget of $160,000 to more than double. In e-mail exchanges made public as part of the case, Mr. Büchel referred to his time spent in North Adams working on the exhibition as an “acid bath” and called those he worked with there “jerks.” He argued in court papers that, after he left Massachusetts last December and stopped working on the project, the museum continued to work on it for four months without his supervision, causing “intentional and willful modification and distortion” to the installation. Mr. Thompson asserted yesterday that even as relations with Mr. Büchel deteriorated and lawsuits were filed, the museum tried to respect the artist’s work. “We did not simply back up a dump truck and destroy these materials and partial constructions,” he said. “And we did not cavalierly fling open the doors to the gallery.” http://www.nytimes.com/2007/09/22/ar...22moca.html?hp Until next week, - js.  Current Week In Review  Recent WiRs - September 15th, September 8th, September 1st, August 25th, August 18th Jack Spratts' Week In Review is published every Friday. Submit letters, articles and press releases in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. Questions or comments? Call (617) 939-2340, country code U.S.. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|
|

|
|
|
#3 | ||
|
Formal Ball Proof
Join Date: May 2000
Posts: 2,948
|
Quote:
Quote:
 |
||
|
|

|
|
|
#4 |
|
Join Date: May 2001
Location: New England
Posts: 10,016
|
this whole thing reminds me of a propaganda piece from mao’s old ministry of disinformation. nothing here the us isn't trying, it's just a bit more akward.
- js. |
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |
| Peer-To-Peer News - The Week In Review - June 24th, 06 | JackSpratts | Peer to Peer | 1 | 22-06-06 12:02 PM |