
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 | |
|
Join Date: May 2001
Location: New England
Posts: 10,016
|
Since 2002
  "The bad news is that the Internet is big, and it's anonymous." – Fox CEO Jim Gianopulos "When I blow I think of times and things from outa the past that gives me an image of the tune. Like moving pictures passing in front of my eyes. A town, a chick somewhere back down the line, an old man with no name you seen once in a place you don’t remember." – Louis Armstrong "You can’t play nothing on trumpet that doesn’t come from him." – Miles Davis  November 28th, 2009  Mininova Deletes All Infringing Torrents and Goes ‘Legal’ Ernesto Mininova, the largest torrent site on the Internet, has removed all torrents except those that were uploaded through its content distribution service. Mininova’s founders took the drastic decision after they lost a civil dispute against Dutch anti-piracy outfit BREIN, and were ordered to remove all infringing torrents from the site. Mininova’s decision to delete all infringing torrents from its index marks the end of an era that started five years ago. In December 2004, the demise of the mighty Suprnova left a meteor crater in the fledgling BitTorrent landscape. This gaping hole was soon filled by the dozens of new sites that emerged to fulfil the public’s increasing demands for torrents. Mininova became the most successful of all. Mininova was founded in early 2005 by five Dutch students, just a month after Suprnova closed its doors. The site started out as a hobby project created by tech-savvy teenagers, but in the years that followed the site’s founders managed to turn it into a successful business that generated millions of dollars in revenue. With increased popularity also came numerous complaints from copyright holders, who saw their intellectual property being shared by users of the site. For years Mininova has complied with these takedown requests, but earlier this year the Dutch anti-piracy outfit BREIN decided to take the torrent site to court nonetheless, demanding that the operators proactively filter torrents pointing to copyrighted material. The case went to court in June and a few weeks later the verdict was announced. The judge ruled that Mininova is not directly responsible for any copyright infringements, but ordered it to remove all torrents linking to copyrighted material within three months, or face a penalty of up to 5 million euros. To avoid having to pay these penalties, the Mininova team saw no other option than to disable access to all torrents except those that were uploaded to their content distribution platform. This means that only approved uploaders can share torrents through the site for now. During the last few months, Mininova has extensively tested several filtering techniques, but none of these proved 100% effective. “It’s very unfortunate that we’re forced to take this action, but we saw no other option,” Mininova co-founder Niek told TorrentFreak. Mininova still hasn’t decided yet whether they will appeal the verdict, Niek further told TorrentFreak. They have appealed the verdict pro-forma, which gives the company more time to decide whether they will indeed continue with the appeal. As it looks now, a successful appeal is the only option for Mininova to bring all torrents back. The implications of Mininova’s decision will have a huge impact on the BitTorrent community. The millions of Mininova users and uploaders have to look for a new home, but perhaps even more importantly, Mininova had the largest collection of user-submitted torrents that were used by dozens of smaller torrent indexers. More information on the consequences and background of Mininova’s decision will be addressed in a follow up article. http://torrentfreak.com/mininova-del...-legal-091126/  30,000 Internet Users to Receive File-Sharing Cash Demands enigmax As many as 25,000 BT and 5,000 customers of other ISPs will be receiving shock letters demanding big payments during the coming weeks. Lawyers in the UK have been granted more court orders which force ISPs to hand over the details of individuals who they say have been monitored sharing hardcore pornography. For regular readers of TorrentFreak, this fresh news can hardly come as a surprise. The supposed anti-piracy scheme originally pioneered in the UK in conjunction with lawyers Davenport Lyons rolls on, but now in the hands of ACS:Law and their partners DigiProtect. Although there is an insistence that the project is aimed at reducing piracy, in reality piracy is the scheme’s lifeblood, providing healthy profits for all concerned, except the original rightsholders that is. On November 19th at the Royal Courts of Justice in London, ACS:Law made NPO (Norwich Pharmacal Order) applications in order to force ISPs to hand over the names and addresses of subscribers the company claims infringed their client’s rights. The NPO’s related to approximately 25,000 IP addresses harvested from UK ISP BT’s subscriber base and a further 5,000 from various other ISPs, covering approximately 291 movie titles. Present at the hearing before Chief Master Winegarten (CMW) were Andrew Crossley and Terence Tsang from ACS:Law, representatives from UK ISP BT and three representatives from consumer outfit Which?, who previously made official complaints regarding the conduct of Davenport Lyons. Also present were two individuals previously wrongly accused, who are regulars at the support site BeingThreatened.com. Before the hearing began, CMW noted that he had received letters of complaint from the public about the scheme. As reported to TorrentFreak by those present, during the hearing Andrew Crossley made some interesting comments. After CMW expressed interest in what happens to an accused infringer after the court order is granted and a letter sent, Crossley said that his company was not suggesting that the recipient is definitely guilty in all cases, but the Internet account holder who receives the letter could perhaps help them to identify the person who had actually carried out the infringement. It is worth noting that ISP account holders are not liable for copyright infringement carried out on his/her connection if a) they did not carry it out themselves or b) did not authorize any infringement. If they did neither they can simply write back to ACS:Law explaining that the accusation against them has been made in error. Furthermore, if the account holder does not know who did carry out the infringement, they should state in their reply that is the case. It is then up to ACS:Law to find the real infringer based on their evidence they hold. This is impossible for them without the account holder pointing the finger. In justifying his application for the court order, Crossley said that they do it because “businesses are failing, jobs are being lost,” while citing dubious IFPI statistics (95% of all music is pirated) to justify his case. CMW asked Crossley how long the scheme would continue for, who replied “…for as long as P2P file-sharing continues Master.” Another NPO was applied for by ACS:Law on behalf of a new-comer to the scheme, a company called Media C.A.T. Ltd. Little is known about them and their website is currently suspended, but searches reveal that the company is involved in the premium SMS market – one page states “Premium Rate Telephone Riches – How To Make £500 A Week” – quite what they have to do copyright holders and anti-piracy is unclear. It does appear, however, that their Managing Director Lee Bowden has previous links to Andrew Crossley and, just like him, will be in this for the money. When CMW asked why rightsholders were dealing with Media C.A.T and not directly with DigiProtect, Crossley said that “[Media C.A.T] happen to operate in the UK…dealing with UK companies…” In referring to the scheme ACS:Law and DigiProtect operate in respect of these hardcore porn titles, Crossley tried to suggest that they were doing a public service by helping to prevent the sharing of restricted movies on P2P. CMW responded by noting that “[this is] not a moral crusade” and that in his opinion, ACS:Law and DigiProtect were doing this “…because you want the money.” Recipients of past and future letters are invited to view the excellent BeingThreatened website, whose users provided invaluable help in compiling this report. http://torrentfreak.com/30000-intern...emands-091125/  Protests Grow Over Digital Bill BBC The Digital Economy bill has sparked a wave of protest among consumers and rights groups. Soon after the bill began its journey through Parliament on 19 November, many expressed worries about parts of it. The bill suggests the use of technical measures to tackle illegal file-sharing that could involve suspending the accounts of persistent pirates. Critics fear this and other powers the bill reserves could damage the UK's growing digital economy. The Digital Economy Bill is the end result of the consultation and research that went into the creation of the Digital Britain report that was published in June 2009. As well as trying to tackle illegal file-sharing, the wide-ranging legislation also proposes a shake-up of the radio spectrum and a classification system for video games. Left out is the proposal for a broadband tax to fund next-generation broadband that will be handled in the Finance Bill due in early 2010. The proposals on file-sharing have garnered most criticism. One of the first responses was the creation of a petition on the Number10.gov.uk website. Set up by Andrew Heaney, TalkTalk's head of strategy and development, it calls for the abolition of the proposal to disconnect illegal filesharers. By 24 November, the petition had gathered more than 16,000 signatures. The number of signatures got a boost from Stephen Fry who used micro-blogging site Twitter to direct people to it. Wrote Mr Fry: "Dear Mandy, splendid fellow in many ways, but he is SO WRONG about copyright. Please sign and RT {retweet]". Jim Killock, executive director of the Open Rights Group, which campaigns on digital issues, said: "It's quite a shocking bill. We're extremely worried about it." Mr Killock said Section 17 of the Bill was worrying because it gave the Secretary of State "reserve powers" to draft fresh laws to tackle net-based copyright infringement without needing parliamentary approval. "It could destabilise business and destabilise innovation," said Mr Killock. "It means entirely trusting to bureaucrats and politicians to get it right." Mr Killock said membership of the Open Rights Group had jumped by 20% in the run-up to the publication of the Bill. He said protests were being co-ordinated in many places such as Facebook and other social media sites. He predicted that the protests would soon lead to some form of civil unrest, be that lobbying, a protest march or public meetings. DIGITAL ECONOMY BILL # Legal framework for tackling copyright infringement via education and technical measure # Oftcom given powers to appoint and fund independently funded news consortia # New duties for Ofcom to assess the UK's communications infrastructure every two years # Modernising spectrum to increase investment in mobile broadband # Framework for the move to digital radio switchover by 2015 # Updating Channel 4 functions to encompass public service content, on TV and online # Age ratings compulsory for all boxed video games for those over 12 years US digital rights group The Electronic Frontier Foundation declared that giving the Secretary of State such powers amounted to the creation of a "pirate finder general" that could enact "draconian" copyright enforcement controls. The Bill envisages that any proposed change to copyright law should be opened up to public comment before it is made. In a bid to defuse some of the criticisms, the Department for Business, Innovation and Skills created a webpage entitled: "Filesharing: some accusations and some answers". It pointed out that some of the criticisms levelled at the Bill were unfounded. It said it had not been drafted at the behest of the music industries. It added that "technical measures" to slow down or suspend net connections would not be imposed without those accused going through a tribunal system that assesses their case. The Internet Service Providers Association (ISPA) also issued a statement saying that it "strongly opposes" the measures introduced to tackle file-sharing. Said ISPA: "Rather than focusing blindly on enforcement, the government should be asking rights holders to reform the licensing framework so that legal content can be distributed online to consumers in a way that they are clearly demanding." Law firm Eversheds said the copyright plans seem "hurriedly put together and not clearly thought-through" and warned that they could have "unforeseen effects." It added: "Critics... may have taken some comfort from the fact that the proposals have yet to wend their way through an already congested legislative timetable before the next election, meaning it is questionable whether they will ever become law." http://news.bbc.co.uk/go/pr/fr/-/2/h...gy/8374732.stm  Reding Warns Spain Against Internet Cut-Off Leigh Phillips EU telecoms chief Viviane Reding has warned that the European Commission would take action against Spain if the government moves to cut the internet access of content pirates. "Repression alone will certainly not solve the problem of internet piracy; it may in many ways even run counter to the rights and freedoms which are part of Europe's values since the French Revolution," information society commissioner Reding told a conference of the Spanish Telecommunications Market Commission (CMT) in Barcelona telecoms on Monday. "If Spain cuts off internet access without a procedure in front of a judge, it would certainly run into conflict with the European Commission," she said. Earlier this year, France introduced new legislation that cuts off internet access to copyright scofflaws and the UK is expected to present similar legislation in the coming weeks. Spain is also understood to be looking into such measures, but the government has yet to announce any new laws. This month, the European Parliament and the Council of Ministers, representing the member states, came to an agreement on a wide-reaching package of telecoms laws that included a provision that outlawed internet access cut-off without an official procedure. Some internet civil libertarians feared at the time that the language in the agreement was still too soft to prevent such laws, but it appears the commission has taken the ball and is running with it. "The new internet freedom provision now provides that any measures taken regarding access to and use of services and applications must always respect the fundamental rights and freedoms of citizens," Ms Reding reminded the Spanish CMT. "Effective and timely judicial review is as much guaranteed as a prior, fair and impartial procedure, the presumption of innocence and the right to privacy." "We need to find new, more modern and more effective ways in Europe to protect intellectual property and artistic creation. "Repression alone will certainly not solve the problem of internet piracy; it may in many ways even run counter to the rights and freedoms which are part of Europe's values since the French Revolution." Ms Reding said that she had been "following with interest the discussions in Spain" and warned the government not to consider measures that ran afoul of the European-level protections of the rights of internet users. "I would like to stress the need for any possible legislative initiative to comply with the agreement reflected in the Telecoms Reform Package." The commissioner then went on to criticise France's ‘Hadopi' law, so-called for the government agency tasked with the struggle against internet piracy. The agency first sends a warning email to a suspected pirate, then a letter in the post and then a special copyright judge orders the suspension of access. "The case of France has shown that national constitutional law may raise even more immediate barriers," she said. "I therefore invite the Spanish authorities to consult very closely with the European Commission before heading into a direction which could soon turn out to be a blind alley." She argued that the development of a single European market for online content was a superior path to take to counter internet piracy, lamenting the fragmentation of copyright law across the EU. "The lifting of impediments to the cross-border online distribution of creative works will improve the supply of attractive and affordable services that are legal. In turn, this will reduce the temptation for consumers to indulge in the illicit consumption of copyright-protected material." http://euobserver.com/?aid=29041  Senators Begin Questioning ACTA Secrecy Despite some sweet talk from Hollywood about how important ACTA and its secret negotiations are to America (and, once again, no, the secrecy is not at all "normal," as some industry lawyers would have you believe), it looks like some Senators are finally beginning to question how ACTA is being handled. Senators Bernie Sanders and Sherrod Brown have sent a letter to US Trade Rep Ron Kirk asking for ACTA documents to be made public. The letter points out that "the public has a right to monitor and express informed views on proposals of such magnitude" especially considering that "there are concerns about the impact of ACTA on the privacy and civil rights of individuals, on the supply of products under the first sale doctrine, on the markets for legitimate generic medicines, and on consumers and innovation in general." The letter also takes on the bogus claims of state secrets in protecting ACTA documents: Quote:
http://www.techdirt.com/articles/200...41197061.shtml  Fox Exec Wants U.S. to Join France on Internet Piracy Crackdown Karolina Tagaris The chief executive of Fox Filmed Entertainment said Monday the U.S. should join France in cutting off the Internet connection of users who repeatedly download copyright-protected films. CEO Jim Gianopulos said Internet piracy is the single biggest threat to the film industry worldwide, and independent films are the hardest hit. "The bad news is that the Internet is big, and it's anonymous," Gianopulos told a news conference in Athens. But he said Internet service providers can track down subscribers whose IP address — the unique number assigned to every computer that connects to the Internet — has been spotted downloading films illegally and issue warnings. Gianopulos said punishing repeat offenders would help create "a level playing field" for filmmakers. "If we can do that, it would be a big victory against piracy," he said, cautioning that taking away the small percentage of profit many films make threatens the industry. Gianopulos said that it is equally important to inform young people about the problem of piracy. "It is important to show them that there is a connection between what they're doing and theft, and what they're doing and people's jobs," Gianopulos said. He was in Greece for a lecture, and talks with Greek film industry professionals. France has already created what it says is the first government agency to track and punish online pirates. Advertisement The European Parliament initially opposed efforts by European Union governments to cut off a user's Internet connection without a court order — but the two sides reached a compromise this month and EU lawmakers and governments agreed on new rights for Internet. Film and record labels have heavily lobbied the 27-nation bloc, demanding better enforcement of copyright rules to protect profits that are shrinking in the face of online file-sharing, in which people swap music files without paying. http://www.siliconvalley.com/news/ci...nclick_check=1  Day 22: Film Studios Issue Ultimatum to ISPs Ry Crozier Internet service providers that shirked responsibilities to prevent copyright infringement on their networks should consider exiting the business, the Federal Court heard today. As the copyright case between the film industry and ISP iiNet approached its conclusion, the studio's barrister Tony Bannon SC suggested ISPs that did not want to deal with infringement notices should "get out of the business." "Businesses such as ISPs want to enjoy the benefit of being able to make money out of the provision of internet service facilities and they enjoy that benefit. But it carries with it a responsibility," Bannon told the court. "They provide a facility that is able to be used for copyright infringement purposes. If they don't like having to deal with copyright notices then they should get out of the business. "They're quite happy to deal with customer complaints or shaping accounts when it comes to making money, but there's a responsibility which is a requirement of law - one of which is the Copyright Act." iiNet came under heavy criticism from the studios over its alleged failure to take any "reasonable steps" to combat infringement on its network. "If an ISP in a case says ‘this is what we tried to do, we tried to deal with notices and these are the systems we use. We cant deal with every one' - let's assume [the ISP] get 100 of these notices per week and tried to process 25 percent of them. "So they come to court and say ‘this is our reasonable response'. That may be one thing," Bannon hypothesised. "But in circumstances where they do nothing, where they say they can't send a single notice to anybody, it's like saying they can't stop physical violence happening to the person next to them because there's physical violence happening all around the world. "This might be a more testing case if they say ‘we have this procedure, we are responding, it's unreasonable to make us do more'. But that doesn't arise in circumstances where they are not taking any steps." Bannon claimed that it wouldn't "take much with to say if they started taking action", terminated a customer or two and advertised the fact, it would in all likelihood reduce the number of notices it was receiving. http://www.itnews.com.au/News/161447...m-to-isps.aspx  Mobile Industry 'Cannot Identify Pirates' Identifying unlawful file-sharers to comply with proposed law is not currently possible for mobile operators, industry chief says Mobile operators are unable to comply with proposed anti-copyright theft legislation that requires them to identify unlawful file-sharers, the head of an industry body has said. In the wake of the Digital Economy Bill, published on Friday, Mobile Broadband Group chief Hamish MacLeod told ZDNet UK that the government's plans to force ISPs to hand over customer data to rights holders and potentially disconnect persistent infringers would apply to mobile operators. However, he said, operators have a "problem with identification [of unlawful downloaders] to the telephone". Whereas fixed-line ISPs map one IP address to each subscriber, "in the mobile space that IP address belongs to the mobile operator", MacLeod said on Monday. "[Operators] are not allocating one IP address per customer," MacLeod said. "They can't backtrack, as things stand, to identify the customer. They would be required to build the databases that would be able to do that mapping, and that would be very costly." According to the Department for Business, Innovation and Skills (BIS) consultation that preceded the bill, the development of the databases would cost the whole industry around £35m, or £7m per operator on average. MacLeod said the cost of these databases would, under the terms of the bill, be shared between the operators and rights holders. However, he said operators should "ideally not" have to bear any of this cost themselves, and the cost-sharing arrangement would need to be discussed with officials and rights-holders. Fixed-line ISPs have already voiced their opposition to the government's plans, partly based on unwillingness to disconnect users without trial, and partly based on the idea that they should have to bear some of the costs associated with helping rights holders launch civil suits against infringers. Whatever happens, no disconnections would take place until 2011 at the earliest, pending the passage of the bill and a subsequent one-year period during which non-technical measures would be tried out, to see if they sufficiently reduce unlawful file-sharing. However, MacLeod said, mobile operators do not expect to have to hand over customer data or disconnect users at all, because not many people file-share copyrighted material over mobile broadband connections due to their relatively low speeds. According to the terms of the bill, ISPs will only be forced to comply with the government's copyright crackdown if a certain — as yet undefined — threshold of unlawful file-sharing is identified on their networks. "Our expectation is that we will not meet the threshold in the first instance because people are doing this [unlawful file-sharing] on fixed internet connections," MacLeod said. "If there's a low level of activity to go on, we would not expect [to have to comply]". ZDNet UK has asked all the major UK operators for their reactions to the Digital Economy Bill's copyright clauses, but only Vodafone has responded. "If Vodafone comes into scope (i.e. there are sufficient notifications to merit inclusion) then anonymised customer data will have to be passed on," a spokesperson for the operator said in an email. The absence of an infrastructure for identifying people who unlawfully download copyrighted content over mobile networks is not the only problem facing the crackdown, according to telecoms analyst Dean Bubley, of Disruptive Analysis. "You've got anonymous prepay as well," Bubley told ZDNet UK on Monday. "Although in some countries they force people to register prepay cards, that's a pretty huge break [from UK regulations]." Bubley pointed out that 3 and other operators that sell "shrinkwrapped" 3G dongles and SIM cards with data capabilities largely serve the very people whom the government is trying to get online. "On one hand, the government's trying to encourage internet connectivity — bridging the digital divide — but a lot of people in lower socioeconomic groups are on prepay, and the vast majority are anonymous," Bubley said, adding that it was technically possible to cut off a mobile subscriber's internet access without disconnecting their voice and text communications. Bubley also noted potential issues arising from new bandwidth-sharing smartphone applications such as JoikuBoost, which lets users combine their 3G connections — irrespective of which operators the individual users subscribe to — over Wi-Fi. "You're not only sharing your Wi-Fi — it's load-balancing across multiple connections," Bubley said. "You can, in theory, have four mobile broadband connections and the four smartphones or PCs turn themselves into a collective hotspot. "Let's say there's an iPhone app that does network or P2P connection-sharing between multiple uplinks. You try figuring out who's downloaded what from whom." http://news.zdnet.co.uk/communicatio...9899832,00.htm  Virgin Media to Trial Filesharing Monitoring System Chris Williams Virgin Media will trial deep packet inspection technology to measure the level of illegal filesharing on its network, but plans not to tell the customers whose traffic will be examined. The system, CView, will be provided by Detica, a BAE subsidiary that specialises in large volume data collection and processing, and whose traditional customers are the intelligence agencies and law enforcement. The trial will cover about 40 per cent of Virgin Media's network, a spokesman said, but those involved will not be informed. "It would be counter-productive because it doesn't affect customers directly," he said. CView will operate at the centre of Virgin Media's network on aggregate traffic, the spokesman emphasised, and seek only to determine the proportion of filesharing traffic that infringes copyright. The system will look at traffic and identify the peer-to-peer packets. In a step beyond how ISPs currently monitor their networks, it will then peer inside those packets and try to determine what is licensed and what is unlicensed, based on data provided by the record industry. Virgin Media emphasised that it is seeking to measure the overall level of illegal filesharing, not to keep records on individual customers. Data on the level of copyright infringement will be aggregated and anonymised. Nevertheless, the trial - which has no scheduled end date - is likely to prove controversial. CView's deep packet inspection is the same technology that powered Phorm's advertising system, which allowed monitoring and targeting of individual internet users. It too was trialled - by BT - without customers' consent or knowledge. Detica is also understood to be in talks with other major ISPs with a view to wider trials of CView. To begin with at least, Virgin Media's implementation will focus on music sharing. The ISP is preparing a legal download service in partnership with Universal, the largest of the four major record labels, which it hopes will be the "carrot" to Lord Mandelson's "stick" of technical measures against those who persistently infringe copyright. "Understanding how consumer behaviour is changing will be an important requirement of Virgin Media's upcoming music offering and, should they become law, the Government's legislative proposals will also require measurement of the level of copyright infringement on ISPs' networks," said Jon James, Virgin Media's executive director of broadband. As part of Lord Mandelson's "stick", the Digital Economy Bill, which the government is hoping to pass before the election, requires Ofcom to measure the effect of its anti-illegal filesharing provisions. As we reported last week, Detica has also tried to pitch CView as an accurate method for regulators to use. At the launch of the Bill on Friday, however, a senior civil servant suggested that a crude estimate based on the level of illegal filesharing observed by rights holder organisations could be used. In the pitch document, Detica said that as well as aggregate data, CView could be used to categorise filesharers and apply technical measures against them, or target them to be sold legal alternatives. Virgin Media's spokesman said it has no plans to use such features. The Register will meet Detica executives next week to discuss CView. Post your questions about the system in comments. http://www.theregister.co.uk/2009/11..._media_detica/  Telcos to FCC: Give Us Billions, But Don't Make Us Share Lines AT&T and Verizon are up in arms about a "slanted" survey of global broadband practices done for the FCC which concludes that mandatory line-sharing rules produce better Internet speeds and penetration rates. Is it possible the US could (again) force ISPs to open their networks? Matthew Lasar It was a report that went right to the roots of United States broadband policy, so it should come as no surprise that it's getting hammered by the telecommunications industry. Harvard's Berkman Center study of global broadband practices, produced at the FCC's request, is an "embarrassingly slanted econometric analysis that violates professional statistical standards and is insufficiently reliable to provide meaningful guidance," declares AT&T. The study does does nothing but promote the lead author's "own extreme views," warns a response from Verizon Wireless. Most importantly, it "should not be relied upon by the FCC in formulating a National Broadband Plan," concludes the United States Telecom Association. Reviewing the slew of criticisms, Berkman's blog wryly notes that the report seems to have been "a mini stimulus act for telecommunications lawyers and consultants." (Interestingly, not everything the Berkman study observes is repugnant to the telcos—hint: big direct public subsidies.) But the ISPs have good reason to go after Harvard scholar Yochai Benkler's survey on "Next Generation Connectivity" around the world, because if the Federal Communications Commission does endorse the study's conclusions in its impending National Broadband Plan, that document might say something like this: FCC line-sharing policy since 2002 has taken the United States off track when it comes to broadband deployment. The agency should reverse course and require AT&T, Verizon, Qwest, Comcast, Time Warner Cable, and the other big ISPs to open their networks to smaller providers of residential broadband service at regulated wholesale rates. This will foster competition, lower prices, and more innovative broadband offerings across the country, as it has elsewhere. That's what's at stake in this debate, and it's not a pretty prospect for Big Telecom. But first, let's recap how we got to this point. Head-to-head In 2005, the Supreme Court ruled in the Brand X case that the FCC had acted legally when it reclassified cable modem services three years earlier as "information" rather than "telecommunications" systems. Off the "common carrier" hook, big cable no longer had to provide network access to smaller rivals. Following the high court's decision, the FCC extended the same logic to the telcos as well, declaring that the move would allow "wireline broadband Internet access providers to respond quickly to consumer demand with efficient, innovative services and spur more vigorous head-to-head competition with broadband services provided over other platforms." Since then, this policy has been accepted as a given; that is, until the FCC asked the Berkman Center to take a look at broadband regulation and development practices around the world to help it formulate its National Broadband Plan. "Talking about 'unbundling,' or more broadly open access in the United States today is a bit like wearing bellbottoms or talking about a national healthcare system," the Berkman study noted. Nonetheless, the Center's report concluded that elsewhere, those policies "are almost universally understood as having played a core role in the first generation transition to broadband in most of the high-performing countries"—a class that doesn't include the US, in large part because of the "information services" decisions the FCC made between 2002 and 2005. France, on the other hand, is a member of the high speed club. The Berkman report even argues that by opening up its main provider, France Telecom, to smaller competitors, the country overtook Germany in the broadband penetration race and put France in the "first tier of speed . . . with substantial availability of 100Mbps service." Deutschland generally offers 50Mbps to consumers, the survey says. And Japan is definitely in the winner's circle. Why? Berkman argues that applying unbundling and open access policies to the country's dominant provider, NTT Corporation, allowed competitors like Yahoo!BB to break into the market with free DSL modems, lower prices, and innovative offerings, "most disruptive of which was bundling free VoIP with broadband access as early as 2001." "Today Yahoo!BB has slightly over a third of the DSL market," the report notes, "NTT has another third, and the remainder is shared among other providers, mostly KDDI and eAccess." Ditto for Britain, whose "functional separation" policies forced British Telecom to set up a division that sold open access to smaller providers. This didn't result in the level of success that France has enjoyed, but it has allowed the United Kingdom to offer consumers low prices for high speed service. Canada, on the other hand, only undertook "half-hearted efforts" in these areas. "Its results," Berkman concludes, "have been weaker than those of other countries we review here." Decides for itself So what are the main criticisms of the report? Verizon and AT&T argue that by coming to its own conclusions, the Berkman study deviated from its mandate to survey the existing literature on global broadband deployment and use. The study is "merely an advocacy piece for the previously expressed policy opinions of its principal author," Verizon charges. The telco cites FCC National Broadband Plan coordinator Blair Levin's comment, when announcing that the FCC had commissioned the report, that "we don’t want to reinvent the wheel. Knowing what has already been learned will improve our ability to deliver the best possible National Broadband Plan." But Verizon says that wheel reinventing was clearly the agenda. "Rather than perform a comprehensive review of the literature as it was tasked to do," its filing protests, "the Berkman Paper reinvents its mission." Ditto, says AT&T. The survey "purports to decide for itself" the state of global broadband, rather than conducting a neutral survey of the literature. Both companies also say that the Berkman study tends to gloss over or ignore literature that doesn't support its main thesis. They fault Berkman for not including, among other documents, a study by Scott J. Wallsten and Stephanie Hausladen suggesting that unbundling policies tend to discourage investment in fiber connections (the report does mention earlier Wallsten writings). But Verizon's biggest objection is to the Berkman study's characterization of the United States as a "middle-of-the-pack-performer" when it comes to providing broadband services. Based on Office for Economic Cooperation and Development data, Berkman places the United States at 15th place in penetration (per 100 people) and 19th in various high speed contests. These observations obscure the fact that Verizon has taken a leading role in fiber investment, Verizon charges, that the US leads in offering consumers broadband service from two wireline platforms, and that it's a pioneer in wireless broadband. No cookie cutter Ironically, while both telcos chide Berkman for coming to its own conclusions about what global broadband deployment practices work best, they also offer the FCC some conclusions of their own. In fact, AT&T draws its recommendations from the very report it criticizes. Beyond the Berkman study's conclusions, Verizon notes, open access and unbundling would be a bad policy for the United States, largely because of the rural nature of much of the country. "The problem in these rural and low-density areas is that they have been unable to attract even a single entrant," the telco argues. "Imposing unbundling will not only fail to solve this problem, but will only make things worse: if the economics do not currently support a single provider, they are even less likely to support multiple (and potentially an unlimited number of) providers." The answer, Verizon recommends, is to subsidize broadband deployment in those areas. "That is what other countries have done to deliver broadband to all of their citizens, and it is one of the steps the Commission should take as well." Here, at last, is something that other countries do that Verizon appears to support. In a similar vein, AT&T sympathetically agrees with Berkman's observation that in various nations direct public investment in broadband has played a significant role, especially in South Korea, Japan, and Sweden. In the case of South Korea, the tab may have come to the equivalent of US$443 billion, AT&T notes. This is not to say that the United States "should adopt identical programs," of course. "There are no cookie cutter solutions here," AT&T observes. But "there are lessons to be learned from the experience of other countries, and one of those lessons appears to be that direct government encouragement can facilitate deployment and drive penetration." Good to know that there's at least one observation that Berkman can make without drawing fire from the telcos. The FCC must submit its National Broadband Plan to Congress by February 17. http://arstechnica.com/telecom/news/...and-report.ars  How Science is Shackled by Intellectual Property Ownership rights pose a real danger to scientific progress for the public good John Sulston The idea of ownership is ubiquitous. Title deeds establish and protect ownership of our houses, while security of property is as important to the proprietors of Tesco and Sainsbury's as it is to their customers. However, there is a profound problem when it comes to so-called intellectual property (IP) – which requires a strong lead from government, and for which independent advice has never been more urgently required. The David Nutt affair has illustrated very well the importance of objective analysis of complex social issues. The myth is that IP rights are as important as our rights in castles, cars and corn oil. IP is supposedly intended to encourage inventors and the investment needed to bring their products to the clinic and marketplace. In reality, patents often suppress invention rather than promote it: drugs are "evergreened" when patents are on the verge of running out – companies buy up the patents of potential rivals in order to prevent them being turned into products. Moreover, the prices charged, especially for pharmaceuticals, are often grossly in excess of those required to cover costs and make reasonable profits. IP rights are beginning to permeate every area of scientific endeavour. Even in universities, science and innovation, which have already been paid for out of the public purse, are privatised and resold to the public via patents acquired by commercial interests. The drive to commercialise science has overtaken not only applied research but also "blue-skies" research, such that even the pure quest for knowledge is subverted by the need for profit. For example, it is estimated that some 20% of individual human genes have been patented already or have been filed for patenting. As a result, research on certain genes is largely restricted to the companies that hold the patents, and tests involving them are marketed at prohibitive prices. We believe that this poses a very real danger to the development of science for the public good. The fruits of science and innovation have nourished our society and economy for years, but nations unable to navigate our regulatory system are often excluded, as are vulnerable individuals. We need to consider how to balance the needs of science as an industry with the plight of those who desperately need the products of science. Clearly it is vitally important that we continue to protect science and enable it to flourish. Science and the many benefits that science has produced have played a crucial part in our history and produced vast improvements to human welfare. It would be remiss if we failed to recognise the importance of science as an industry and investment in research to national and regional economic development; but against these economic concerns (individual, corporate and national) an overriding consideration must be the interests of the public and of humanity present and future. Science as an industry may be booming, but the benefits of science need to be more efficiently and more cheaply placed in the service of the public. This is of particular concern in the developing world, where drugs that are routinely available in high-income countries are unaffordable or inaccessible, and treatments for diseases of the poor are simply not being developed due to lack of a viable market. Existing inequities in knowledge capital make developing nations hostage to more technologically advanced countries for their basic health and development needs, and restrict the participation in research that would allow them to redress this imbalance. For science to continue to flourish, it is necessary that the knowledge it generates be made freely and widely available. IP rights have the tendency to stifle access to knowledge and the free exchange of ideas that is essential to science. So, far from stimulating innovation and the dissemination of the benefits of science, IP all too often hampers scientific progress and restricts access to its products. The Manchester Manifesto, produced by an interdisciplinary and international group of experts and published today, explores these problems and points the way to future solutions that will more effectively protect science, innovation and the public good. It calls on all interested parties to find better ways of delivering the fruits of science where they are most needed. This article is co-authored with Sarah Chan and Professor John Harris http://www.guardian.co.uk/commentisf...ctual-property  Apple Asks Judge to Shutter Psystar's Clone Business Wants injunction that bars Mac OS X systems, says it's owed $2.1M in damages Gregg Keizer Apple wants a federal judge to shut down Psystar's Mac clone operation and order the company to pay more than $2.1 million in damages, according to court documents. The move was the first by Apple since U.S. District Court Judge William Alsup ruled that Psystar violated Apple's copyright and the Digital Millennium Copyright Act (DMCA) when it installed Mac OS X on clones it sold. Alsup's Nov. 13 order, which granted Apple's motion for summary judgment and quashed Psystar's similar request, was a crushing blow to the Florida company's legal campaign. In a motion filed Monday, Apple asked Alsup to grant a permanent injunction that would force Psystar to stop selling any computer bundled with Mac OS X; using, selling or even owning software that lets it crack Apple's OS encryption key to trick Mac OS X to run on non-Apple hardware; and "inducing, aiding or inducing others in infringing Apple's copyright." Apple also asked Alsup to award it $2.1 million in damages, even though Apple acknowledged that it's unlikely to collect from the financially-strapped company. "Psystar's whole business is premised on stealing from Apple," the motion read. "Psystar pirates Apple's software, circumvents Apple's technological protection measures and illegally benefits from the good will and reputation Apple has built. Psystar's conduct, if permitted to continue, will both tarnish Apple's reputation for excellence and lead to the proliferation of copycats who also will free ride on Apple's investments, infringe Apple's intellectual property rights and cause further irreparable injury." Apple argued that the injunction is the only way to make Psystar stop infringing its copyright. "Psystar has announced its intention to continue infringing (and to contribute to the infringement of) Apple's copyrights in, and circumventing the technology protections measures in, the current upgrade of Mac OS X, version 10.6," said Apple. Psystar previously conceded that Apple could get an injunction to bar it from using Mac OS X, but said that that would apply only to Mac OS X 10.5, aka Leopard, not the newer Snow Leopard. Like Apple, Psystar has moved beyond Leopard and has been putting Snow Leopard exclusively on its clones since that operating systems' release last August. At that time, Psystar sued Apple in a Florida federal court, claiming Apple illegally tied Snow Leopard to Mac hardware, essentially a repeat of moves it made in Alsup's California court during 2008. Alsup tossed out Psystar's countersuit last year -- the clone maker's first major legal defeat -- but in September 2009, he ruled for Psystar by refusing to stop the Florida lawsuit. Apple this week again urged Alsup to disregard the Florida-based clone maker's slight-of-hand over Snow Leopard. "Psystar's admission that it has moved on to infringing subsequent versions of Mac OS X confirms that any injunction must extend beyond Mac OS X Leopard," Apple said in the motion for an injunction. Philip Schiller, Apple's head marketing executive, spelled out the company's stance in a statement appended to the motion. "Apple should not be required to file a new lawsuit to stop Psystar from infringing Apple's intellectual property each time Apple releases a new version of Mac OS X," Schiller said in his declaration. "Requiring Apple to file multiple lawsuits to stop the same infringing conduct would be unfair, expensive, and a waste of the Court's and the parties' resources." Besides the injunction, Apple is seeking $2.1 million in damages, less than half what it said was the maximum, as a sop to "a swift resolution of the issues." But it admitted it might have trouble collecting even the smaller amount. "There is compelling evidence that Psystar will not be able to pay any statutory damages," it said in the Monday motion. Apple cited the bankruptcy filing Psystar made last summer, then withdrew, as proof that Psystar may not be able to pay the money. It also used that purported inability to pay as another argument for an injunction. Psystar and Apple have been tangling in court since July 2008, when Apple sued the clone maker over copyright and software licensing violations. Psystar started selling Intel machines with Mac OS X preinstalled in April 2008. While Apple didn't spell out the impact on Psystar if an injunction were granted, it hinted that one would drive the small firm out of business, saying that by its estimates, 80% of the company's business is in Mac clones. It had no sympathy for Psystar, however. "A defendant whose entire business is premised on misappropriation of Apple's intellectual property cannot claim it suffers hardship by being forced to stop such infringement," Apple contended. "Psystar has illegally profited from Apple's efforts rather than investing in developing its own products and building its own good will," Apple said. Alsup will hear oral arguments Dec. 14 from both parties on Apple's request for an injunction. The case is slated to go to trial in January 2010. http://www.computerworld.com/s/artic...clone_business  Microsoft Issues Takedown Notices Over Spilled COFEE Microsoft has issued takedown notices to multiple websites hosting the company's Computer Online Forensic Evidence Extractor (COFEE), which helps law enforcement officials grab data from password protected or encrypted sources. Emil Protalinski Microsoft has been issuing takedown notices for publicly hosting its leaked Computer Online Forensic Evidence Extractor (COFEE) tool. The company sent off "Demand for Immediate Take-Down: Notice of Infringing Activity" to companies hosting websites that offered the tool. The e-mails all start with the following standard statement: "Microsoft has received information that the domain listed above, which appears to be on servers under your control, is offering unlicensed copies of, or is engaged in other unauthorized activities relating to copyrighted works published by Microsoft." One of the websites that received legal threats from Redmond is Cryptome.org, a great repository for information about freedom of speech, cryptography, spying, and surveillance. According to e-mail correspondences posted on Cryptome, Microsoft contacted Network Solutions, which hosts Cryptome, and since John Young, the owner of the website, wasn't too keen on losing his whole website for the sake of a single 15MB file, he removed the download link and sent Network Solutions a notice of compliance. Every single Microsoft application that leaks out to the Web is available on BitTorrent networks and various underground corners of the Internet, and Microsoft can't really take care of all of them, though this move is consistent with the company's promise to pursue unauthorized distribution of its code. Of course, a few takedown notices will do little against those who really want to get their hands on the tool, though it will make it a tad harder to get at for those who are not very tech-savvy. Microsoft first revealed the tool back in April 2008, and in April 2009, the company announced that it will aid global law enforcement in fighting cybercrime by providing its COFEE tool free of charge to International Criminal Police Organization's (Interpol) Global Security Initiative (GSI), a project that addresses international security challenges, and the participating 187 countries. Microsoft managed to keep the lid tightly sealed until earlier this month, when pirates decided it was time to leak the tool to the Web and let more than just government crime-fighters use it. The COFEE application uses common digital forensics tools to help law enforcement officials at the scene of a crime gather volatile evidence of live computer activity that would otherwise be lost in a traditional offline forensic analysis. In other words, it lets officers grab data from password-protected or encrypted sources. The forensics tool works best with Windows XP but Microsoft is working on a new version of COFEE for next year that fully supports Windows Vista and Windows 7. http://arstechnica.com/microsoft/new...lled-cofee.ars  Hollywood Wants to Outsource Copyright Enforcement: iiNet Andrew Colley IINET yesterday accused Hollywood studios of trying to "outsource" its copyright enforcement to internet firms as it continued to battle in the Federal Court against claims it authorised illegal file-sharing on its network. The Perth-ISP's lead barrister Richard Cobden SC argued that the studios' demand that iiNet pass infringement notices on to customers amounted to an unreasonable request to police its customers. The trial is widely viewed as statutory test that could have major ramifications for internet companies here and overseas. The Australian Federation Against Copyright Theft (AFACT) – which has bought the case on the studios' behalf – argues that by refusing to take "reasonable steps" to act on the notices iiNet had breached copyright laws that make authorising infringements illegal. But Mr Cobden told the court that it would be an "inappropriate and certainly unreasonable step to suggest that their copyright enforcement branch should be outsourced to the ISPs." He told the court that the studios were asking iiNet to take on "radically more onerous" steps to prevent infringement by customers than had been sought in previous cases involving online copyright infringement in Australia. The studios were asking for a change to iiNet's entire business model that would require complex systems and processes for handling thousands of infringement notices issued by music and movie owners around the world, he argued. He also reiterated iiNet's claim that parts of the Telecommunications Act bridged to privacy laws that prevented the company from "using" information on its systems to enforce the notices. Mr Cobden put the arguments forward as he spent his second day presenting closing submissions to the court on the ISP's behalf. His arguments were intended to support a central pillar in iiNet's defence. Throughout the trial the ISP has repeatedly argued that there were no reasonable steps that the ISP could take to prevent infringement taking place on its network. The ISP claims that termination did not genuinely give iiNet power to prevent acts of infringement as customers would simply churn to other providers. AFACT has argued that iiNet's customers consented to have their information used for copyright enforcement activity as part of their service agreements in line with telecommunications laws. AFACT also presented evidence that other internet providers, including iiNet subsidiary Westnet, passed the notices on to customers without facing the legal and logistical obstacles that the ISP argues are in place. The trial continues on November 24 when the Internet Industry Association (IIA) is expected to appear to make an application to be heard in the case under the court's amicus curiae (friend of the court) provisions. http://www.theaustralian.com.au/aust...-1225800094356  Study Shows Resistance Growing To Radio Royalty Bill FMQB A new report from Washington Research Group Concept Capital says that is it becoming less likely that the Performance Rights Act, which would force radio stations to pay royalties for playing music, will become law. In recent months, the House and Senate Judiciary Committees have approved the legislation, and a meeting was held between broadcasters and record labels to engage in mediated discussions over a possible compromise. However, Concept Capital says the odds are dropping for the legislation to pass in the 2009-10 Congress. The research group reduced its estimate from 60 percent to 40 percent odds of the bill passing in the next 12 months. The report outlines four reasons why the possibility is less likely, first saying that broadcasters are doing an effective job of building opposition to the legislation. The NAB has gotten 27 Senators and 253 House members to sign a resolution opposing the Performance Rights Act. Secondly, broadcasters have gotten traction with arguments that a new fee could have damaging consequences for a large number a radio stations – particularly in a difficult advertising environment – and that a disproportionate share of endangered stations are minority-owned. The report also notes that we are entering an election year, and individual members are typically more sensitive to broadcasters’ policy agenda as voting season nears. And lastly, broadcasters have new leadership in Washington. Former Republican Senator Gordon Smith recently took the helm of NAB, and his stature, bipartisan reputation and skill set are a positive factor for broadcasters in the radio royalty battle. The report from Concept Capital concludes, "We do not rule out the possibility of some kind of breakthrough or legislative maneuver that would allow the bill to move forward. The bills’ chief supporters (the Senate and House Judiciary Committee leaders) remain very committed to moving a bill. And the royalty bill has now progressed farther than it has in any prior congress, so risk clearly remains for broadcasters. But our sense is the momentum has shifted away from passage." http://www.fmqb.com/article.asp?id=1601209  Warner Music Posts Surprise Loss as Costs Rise Warner Music Group, the world's third largest music company, on Tuesday reported a surprise quarterly loss as higher interest expense and operating costs cut into the record label's margins. Top selling artists in the period included Jay-Z, Madonna and Japanese acts Kobukuro and Superfly, but the company noted that the shrinking demand for CD's and the weak economy hurt its revenue and is likely to affect future results. The New York-based company posted a net loss of $18 million, or 12 cents a share, in the fiscal fourth quarter ended Sept 30, compared with a year-earlier profit of $6 million, or 4 cents a share. Revenue rose 1 percent to $861 million, ahead of analyst forecasts, boosted primarily by growth in Japan, France and Germany. International gains were offset by weakness in the U.S. and Latin America. The company's operating loss excluding charges for job cuts was 3 cents a share as computed by Thomson Reuters I/B/E/S, compared with an average profit estimate of 5 cents per share on revenue of $820.3 million. Warner Music's total costs and expenses in the fourth quarter increased by 2 percent, and its margin from continuing operations declined 1.5 percentage points to 6.3 percent. Like other music companies, Warner Music is struggling with shrinking sales of recorded music as fewer fans buy albums on CDs. The transition to downloaded music has led to a decline in revenue throughout the industry as fans increasingly buy lower-priced individual songs from Web retailers like Apple Inc's (AAPL.O: Quote, Profile, Research, Stock Buzz) iTunes Music Store. Warner Music said its digital music sales rose 10 percent from the prior year to $184 million, or 21 percent of total revenue in quarter. Shares of Warner Music were not yet trading on Tuesday after closing at $7.06 yesterday on the New York Stock Exchange. (Reporting by Yinka Adegoke and Franklin Paul; Editing by Derek Caney) http://www.reuters.com/article/ousiv...5AN23120091124  Music Stores See Dream Week with Boyle, Lambert Ed Christman U.S. music retailers are realizing a dream week with Susan Boyle's "I Dreamed A Dream" ringing cash registers far beyond expectations and Adam Lambert's album stirring sales after his sexually charged TV performance. Label and distribution executives project that based on early sales returns at major retailers and pre-orders at direct marketers like Amazon and QVC, Boyle's album is in contention to beat this year's top debut-week seller, Eminem's "Relapse." That record sold 608,000 units in the week ending May 24, according to Nielsen SoundScan, representing the best overall sales week for an album this year. While projections for Boyle's album start at the 550,000 unit mark, some executives are reluctant to guess how high it will go. If big box retailers "have stock on Black Friday, who knows how well the album can do," said one industry watcher who thinks the album will sell at least 700,000 copies this week. Lambert's "For Your Entertainment" also is outperforming expectations despite --or perhaps because of -- his risque performance at Sunday's American Music Awards in which the gay singer kissed one male musician and pushed the head of another into his crotch. Industry sources project "For Your Entertainment" could sell about 225,000 units in its initial week in stores. Likewise, Lady Gaga and her three-pronged attack on consumer purses is much stronger than expected. Her new "The Fame Monster" deluxe edition and "The Fame" original version could sell a combined 150,000 records, while "The Fame Monster" EP is expected to top 200,000 units, sources said. Estimates are based on a Tuesday release date, while this past week new releases came out a day early on Monday, due to the U.S. Thanksgiving holiday weekend. Also impacting sales is the busiest shopping day of the holiday season, so-called 'Black Friday,' the day after Thanksgiving. How well Boyle's album performs will, in part, be impacted by replenishment on shelves. Sources said many stores are on the verge of being sold out, and re-orders have been placed. Based on past performances of hot-selling titles, the record's distributor, Sony Music Entertainment, likely will keep pace with demand but is scrambling to allocate product daily and make multiple shipments to each account. According to Hastings Entertainment senior vice president of merchandising, Alan Van Ongevalle, the Boyle album is outperforming expectations at the chain, which has never performed well in mainstream pop albums like hers. "Last week, John Mayer was our No. 1 record and that is in a genre we do reasonably well in, and so far in one day has done more than he sold all week," Van Ongevalle said. QVC said it had pre-orders of more than 81,000 units, its best sales performance in 10 years, while Amazon says the album has generated its largest global pre-order in its history. Amazon doesn't disclose numbers, but sources say its U.S. pre-order alone reached 80,000 units. Meanwhile, Rihanna's "Rated R" is seen as an underperformer so far in its debut week. One purchasing chief called the sales level "weird," given that Rihanna has made several appearances on TV recently to promote the album and talk about last February's attack on her by ex-boyfriend, singer Chris Brown. (Editing by Bob Tourtellotte) http://www.reuters.com/article/enter...5AO4CE20091125  Swedes Start Buying Music; are Anti-P2P Laws Working? Digital music sales in piracy-loving Sweden have soared this year. The music industry says that it's all about tough new laws and court prosecutions, but some major labels are seeing worldwide increases. Nate Anderson Is Sweden, the only country to have sent a member of the Pirate Party to the European Parliament, finally giving up its swashbuckling ways? When Sweden's IPRED anti-piracy law went into effect earlier this year, Internet traffic across the country plummeted overnight—a sign that P2P users, fearing exposure at last, were abandoning their existing copyright infringement tools. The Pirate Bay defendants were found guilty by a Swedish court earlier this year, and the site's ISP are now under assault by the music and movie industries. The music business insists that the measure are working. Music's major labels say that sales of digital downloads are up 18 percent in the first nine months of 2009 in Sweden. Ludvig Werner, head of the trade group IFPI Sweden, told the UK's Guardian newspaper that it didn't matter if people still wanted to pirate; the point was, they were doing less of it. "It's like speeding, put up cameras and people will start to ease off the gas pedal. Even if it doesn't change the attitudes, they find legal alternatives because they don't want to get caught," said Werner. Dueling explanations As with most statistics in the Copyright Wars, these are hard to evaluate. Digital music sales are up, but has copyright infringement also dropped? IFPI doesn't know. In fact, there are reasons to suspect that legal actions like IPRED aren't the only drivers of Sweden's uptick in music sales. As we reported yesterday, UK-based music label EMI has reported a worldwide revenue increase of 4.6 percent in its recorded music business through 2009 to date; surely this can't just be chalked up to tougher antipiracy laws in small countries like Sweden and South Korea? And Swedish Internet traffic data bounced back soon after the IPRED law came into force and now exceeds the level from the beginning of 2009. Credit also has to go the music industry for licensing its music far more widely, often to innovative Scandinavian companies like Spotify and Nokia, which is offering the Comes With Music plan on selected phones. But who knows? Perhaps IPRED and The Pirate Bay prosecution were real drivers of the change in Sweden; we've certainly seen surveys in the UK that suggest online infringers will alter their behavior once the veil of anonymity is stripped away (which was the point of IPRED). If true, the data could help prove a music industry mantra: tougher enforcement can yield results (i.e., battling the pirates is not a hopeless endeavor). On the other hand, it seems to suggest that only minimal legal tools are needed. IPRED made it possible for rightsholders to subpoena ISPs and get subscriber names and information; The Pirate Bay case was brought under copyright law. New Internet disconnection laws, ISP filtering schemes, and similar invasive measures weren't required. http://arstechnica.com/tech-policy/n...ws-working.ars  Billy Bragg, Canadian Songwriters Push for New Approach to Downloading Jennifer Ditchburn There were no iPods, peer-to-peer file sharing sites or digital copyright wars back when Billy Bragg first belted out "Waiting for the Great Leap Forward," but the tune seems completely a propos to his latest political fight. The British alt rocker teamed up with Safwan Javad of Canada's Wide Mouth Mason, the Canadian Association of Songwriters and the NDP's Heritage critic Charlie Angus Friday to push for a new approach to dealing with music downloads. "The Wii is not going back in the box," Bragg told reporters, lamenting that kids these days save up for video games before albums. "Technology is moving forward and we've got to go forward with it." Bragg and a host of other artists in Europe and across Canada would like to see new ways to pay performers for music available on the Net while still protecting downloaders who are sharing the product. He said that music labels will often sell music catalogues to Internet sites and artists don't get a cut. "We have a slogan that where money is made, artists must be paid. What's implicit in that slogan is that we should go after those people who are making profit from giving our stuff away for free or selling it online," Bragg said. "The other edge of that particular argument is that people who are sharing files...really should not be within the reach of the copyright law." The Canadian government consulted Canadians and industry figures last fall about proposed changes to its sorely outdated copyright laws after facing overwhelming opposition to a bill tabled last year. Bill C-61 would have made it illegal for any Canadian to circumvent digital copyright "locks" put on pieces of audio or video, rendering it impossible for people to share material with impunity. One of the ideas offered by Angus would be to charge a levy on the purchase of any MP3 player, such as the government did when Canadians purchased blank CDs or cassettes. The idea then was to collect the money and then compensate artists for material that was used when people made their old "mixed tapes." Don Quarles of the songwriters association said another possibility would be to charge Internet users an extra fee on their monthly bill. The money raised would go into a pot that is redistributed to artists. How the downloaders would be differentiated from those who didn't exchange music remains to be explained. "A license fee of a few dollars a month paid by those who wish to file share would create a new business model, one that creates good value for the consumer and ease of access to the music, while ensuring the music creators and rights holders are farily compensated for the use and enjoyment of their work," said Quarles. Bragg, a longtime supporter of the labour movement, treated striking workers outside the Museum of Civilization in Gatineau, Que. to a free concert in the rain. The 420 employees of that institution and the Canadian War Museum, members of the Public Service Alliance of Canada, have been on strike for two months. http://www.google.com/hostednews/can...hYrpbI9yHK-bBQ  The End of Music Glenn Branca We seem to be on the edge of a paradigm shift. Orchestras are struggling to stay alive, rock has been relegated to the underground, jazz has stopped evolving and become a dead art, the music industry itself has been subsumed by corporate culture and composers are at their wit’s end trying to find something that’s hip but still appeals to an audience mired in a 19th-century sensibility. For more than half a century we’ve seen incredible advances in sound technology but very little if any advance in the quality of music. In this case the paradigm shift may not be a shift but a dead stop. Is it that people just don’t want to hear anything new? Or is it that composers and musicians have simply swallowed the pomo line that nothing else new can be done, which ironically is really just the “old, old story.” Certainly music itself is not dead. We’ll continue to hear something approximating it blaring in shopping malls, fast food stops, clothing stores and wherever else it will mesmerize the consumer into excitedly pulling out their credit card or debit card or whatever might be coming. There’s no question that in music, like politics, the bigger the audience gets the more the “message” has to be watered down. Muzak’s been around for a long time now but maybe people just can’t tell the difference anymore. Maybe even the composers and songwriters can’t tell the difference either. Especially when it’s paying for a beach house in Malibu and a condo in New York. Of course, we could all just listen to all of our old albums, CD’s and mp3’s. In fact, nowadays that’s where the industry makes most of its money. We could also just watch old movies and old TV shows. There are a lot of them now. Why bother making any new ones? Why bother doing anything new at all? Why bother having any change or progress at all as long as we’ve got “growth”? I’m just wondering if this is in fact the new paradigm. I’m just wondering if in fact the new music is just the old music again. And, if that in fact it would actually just be the end of music. http://opinionator.blogs.nytimes.com...-end-of-music/  The Voice That Helped Remake Culture Michiko Kakutani POPS A Life of Louis Armstrong Terry Teachout Illustrated. 475 pages. Houghton Mifflin Harcourt. $30. Louis Armstrong, a k a Satchmo, a k a Pops, was to music what Picasso was to painting, what Joyce was to fiction: an innovator who changed the face of his art form, a fecund and endlessly inventive pioneer whose discovery of his own voice helped remake 20th-century culture. His determination to entertain and the mass popularity he eventually achieved, coupled with his gregarious, open-hearted personality, would obscure the magnitude of his achievement and win him the disdain of many intellectuals and younger colleagues, who dismissed much of what he did after 1929 as middlebrow slumming, and who even mocked him as a kind of Uncle Tom. With “Pops,” his eloquent and important new biography of Armstrong, the critic and cultural historian Terry Teachout restores this jazzman to his deserved place in the pantheon of American artists, building upon Gary Giddins’s excellent 1988 study, “Satchmo: The Genius of Louis Armstrong,” and offering a stern rebuttal of James Lincoln Collier’s patronizing 1983 book, “Louis Armstrong: An American Genius.” Mr. Teachout, the drama critic of The Wall Street Journal and the chief culture critic of Commentary magazine, writes with a deep appreciation of Armstrong’s artistic achievements, while situating his work and his life in a larger historical context. He draws on Armstrong’s wonderfully vivid writings and hours of tapes in which the musician recorded his thoughts and conversations with friends, and in doing so, creates an emotionally detailed portrait of Satchmo as a quick, funny, generous, observant and sometimes surprisingly acerbic man: a charismatic musician who, like a Method actor, channeled his vast life experience into his work, displaying a stunning, almost Shakespearean range that encompassed the jubilant and the melancholy, the playful and the sorrowful. At the same time, Mr. Teachout reminds us of Armstrong’s gifts: “the combination of hurtling momentum and expansive lyricism that propelled his playing and singing alike,” his revolutionary sense of rhythm, his “dazzling virtuosity and sensational brilliance of tone,” in another trumpeter’s words, which left listeners feeling as though they’d been staring into the sun. The author — who worked as a jazz bassist before becoming a full-time writer — also uses his firsthand knowledge of music to convey the magic of such Armstrong masterworks as “St. Louis Blues,” “Potato Head Blues,” “West End Blues” and “Star Dust.” During his lifetime Armstrong performed with virtually everyone, from early jazz pioneers like Sidney Bechet, Joe Oliver, Bix Beiderbecke, Johnny Dodds and Kid Ory, on through more recent masters like Leonard Bernstein and Johnny Cash. His freewheeling incandescence as both an instrumentalist and vocalist would influence not just every trumpet player to come but also countless composers, bandleaders and singers as varied as Frank Sinatra and Bing Crosby, Ella Fitzgerald and Billie Holiday. “Even before his face became known to the readers of newspapers and illustrated magazines — and, later, to filmgoers and TV viewers,” Mr. Teachout writes, “Armstrong was the first jazz musician whose voice was heard by large numbers of people. In this way he emerged from behind the anonymity of the recording process and impressed his personality on all who heard him, even those who found most instrumental jazz to be unapproachably abstract. It was the secret of his appeal, and he knew it. So did the many singing instrumentalists who followed in his footsteps, hoping to lure some of the same listeners who smiled at the sound of his gritty tenor voice, which deepened as he grew older but was always as recognizable as a fingerprint.” Although Armstrong’s life story has been told many times before, Mr. Teachout does a nimble job of reconjuring the trajectory of Armstrong’s experience, which coincided with — or was in the vanguard of — so many formative events in 20th-century Afro-American history, from the Great Migration that brought many Southern blacks North to cities like Chicago to the Harlem Renaissance of the 1920s and ’30s. He recounts the travails of touring that Armstrong experienced in a still segregated South, to his acclamation in Europe in the ’30s and ’40s and the mainstream American success he finally achieved in the ’50s. The reader gets a dramatic snapshot in this volume of Armstrong’s life on the mean streets of New Orleans, where he grew up, the illegitimate son of a 15-year-old country girl, among gamblers, church people, prostitutes and hustlers; his adventures in gangland Chicago and Jazz Age New York; the rapid metamorphosis of this shy, “little frog-mouthed boy who played the cornet” into the most influential soloist in jazz; and the long, hard years on the road, crisscrossing the United States dozens of time, playing so many one-nighters that he often came off the stage, in his own words, “too tired to raise an eyelash.” In addition, Mr. Teachout does a fluent job of explicating Armstrong’s apprenticeship under Joe Oliver and Fletcher Henderson; his seminal work with the Hot Five; and the key business roles played by his wife Lil and his mobbed-up manager, the former boxing promoter Joe Glaser, in shaping his career. As Mr. Teachout astutely points out, Armstrong’s trumpet playing, like his singing and copious writings (including two published memoirs and countless letters, which he pecked out on a typewriter he brought with him on the road), was the means for Armstrong to reflect on all that he had witnessed. “I seen everythin’ from a child comin’ up,” he said once. “Nothin’ happen I ain’t never seen before.” “When I blow I think of times and things from outa the past that gives me an image of the tune. Like moving pictures passing in front of my eyes. A town, a chick somewhere back down the line, an old man with no name you seen once in a place you don’t remember.” This belief in music as a deeply felt and personal expression is one reason Armstrong avoided using musical terminology when speaking about his work and it’s one reason he said that he disliked bop (like other cooler, more modern forms of jazz), complaining that it “doesn’t come from the heart,” that it’s “all just flash.” Boppers and avatars of the cool, in turn, rejected Armstrong’s desire to entertain the audience — to mug and clown on stage. And yet even Miles Davis, who in rejecting Satchmo’s crowd-pleasing ways went so far as to turn his back on the audience, acknowledged that the history of jazz radiated out from Louis Armstrong: “You can’t play nothing on trumpet,” Davis said, “that doesn’t come from him.” http://www.nytimes.com/2009/11/24/books/24book.html  Waldo Hunt, King of the Pop-Up Book, Dies at 88 Margalit Fox On the flat, foursquare pages of a printed book, Waldo H. Hunt could part the Red Sea. He could make hearts beat, lungs fill and bones rattle. He could make dinosaurs rear up, ships set sail and bats quiver in belfries. An advertising man turned novelty-book packager, Mr. Hunt was almost single-handedly responsible for the postwar revival of the pop-up book in the United States. For decades the country’s leading producer of the books, he is widely credited with having taken a long dormant, long marginalized and long unprofitable publishing genre and making it a thriving, ubiquitous industry. Mr. Hunt, who lived in Springville, Calif., died on Nov. 6 at 88. His death, in Porterville, Calif., was of congestive heart failure, his family said. Mr. Hunt’s company, Intervisual Books, produced many of the best-known pop-up books of the modern era, among them “The Human Body,” by Jonathan Miller and David Pelham (Viking Press, 1983), featuring movable internal organs; “The Honeybee and the Robber” (Philomel, 1981), a moving picture book by Eric Carle; and the pop-up version of “Harry Potter and the Chamber of Secrets” (Scholastic, 2002). One of Mr. Hunt’s books, Jan Pienkowski’s “Haunted House” (Heinemann, 1979), received the Kate Greenaway Medal, a prestigious British prize for children’s book illustration. It was a highly unusual honor for a pop-up book. Besides working for commercial publishers, Mr. Hunt produced everything from pop-up books to greeting cards, table decorations and store displays for clients like National Geographic, Hallmark Cards and the Walt Disney Company. Mr. Hunt was also an avid collector of movable books — a term encompassing pop-ups books and those otherwise set in motion — amassing more than a thousand antique and contemporary titles. In 2002 his collection formed the basis of an exhibition, “Pop Up! 500 Years of Movable Books,” at the Los Angeles Central Library. That year Movable Stationery, the newsletter of the Movable Book Society, an organization of scholars and enthusiasts, called Mr. Hunt “the paterfamilias of pop-up.” Waldo Henley Hunt, familiarly known as Wally, was born on Nov. 28, 1920, in Chicago and reared in California. He briefly attended Stanford University before serving in the Army during World War II. After the war he started his own advertising agency, eventually called W. H. Hunt & Associates, in Los Angeles. In the mid-1950s Mr. Hunt sold his agency to Compton Advertising, a large New York concern, staying on as its Los Angeles manager. Growing disenchanted with the industry, he formed a new company, Graphics International, with a colleague in the early ’60s. But Mr. Hunt did not find his company’s true direction until after he came across the work of Vojtech Kubasta, a master Czech paper engineer of the mid-20th-century whose pop-up castles and cathedrals seemed to leap off the page. Through Graphics International Mr. Hunt began producing pop-up advertising inserts for magazines, including the Wrigley Zoo, a memorable series of chewing-gum ads featuring a three-dimensional menagerie. But before he could crack the trade-book market, he had to overcome two longstanding hurdles: institutional bias and prohibitive cost. “For the longest time, children’s books in general were considered the stepchild of publishing,” Robert Sabuda, a noted pop-up-book artist, said in a telephone interview on Monday. “Pop-up books were considered the stepchild of children’s books.” Movable books have been around at least since the late Middle Ages. Originally aimed at adult readers, they employed cutting-edge technology — glue, paper, scissors — to illustrate three-dimensional concepts like anatomy, astronomy and landscaping. By the Victorian era, magnificent pop-up fairy-tale books were widely produced for children. Until the early 20th century, the world’s finest movable books were made by German printers for English publishing houses. With the coming of World War I, the collaboration stopped, Ann R. Montanaro, the director of the Movable Book Society and the author of “Pop-Up and Movable Books: A Bibliography” (Scarecrow Press, 1993), explained by telephone on Monday. By the time Mr. Hunt entered the field, she said, pop-ups were published in this country only rarely, and most were of poor quality. As a result, Mr. Hunt had to counter the pervasive belief that pop-up books were no more than shoddy toys. He also had to counter the high cost of making them: each book needed to be assembled painstakingly by hand, the method still used today. “It’s very time-consuming and very involved,” David A. Carter, a well-known pop-up book artist, said on Monday. “The engineering changes from spread to spread and book to book. So it’s not something that can be designed on an assembly line.” Mr. Hunt took the assembly work abroad, first to Japan and later to Latin America, where costs were lower. After Graphics International secured the contract to produce “Bennett Cerf’s Pop-Up Riddles” (Random House, 1965), his entrée into the book world was assured. Graphics International was later sold to Hallmark; in the mid-1970s Mr. Hunt founded what became Intervisual Books. The company, which employed a world-class team of artists, designers and paper engineers, was sold several years ago to Dalmatian Press, a children’s book publisher. Mr. Hunt’s first two marriages ended in divorce. He is survived by his third wife, the former Patricia Elliott; their daughters, Kimberly Hunt and Jamie Hunt; a daughter, Marsha Hunt, from his second marriage; a brother, Randy; and three grandchildren. Today bookstores are awash in pop-up books, produced by a bevy of packagers around the country. “None of this would exist without Wally,” Mr. Sabuda said. “None of us would be able to be here doing this now if Wally hadn’t truly blazed the way for us to come up after.” http://www.nytimes.com/2009/11/26/arts/26hunt.html  Price War Brews Between Amazon and Wal-Mart Brad Stone and Stephanie Rosenbloom Ali had Frazier. Coke has Pepsi. The Yankees have the Red Sox. Now Wal-Mart, the mightiest retail giant in history, may have met its own worthy adversary: Amazon.com. In what is emerging as one of the main story lines of the 2009 post-recession shopping season, the two heavyweight retailers are waging an online price war that is spreading through product areas like books, movies, toys and electronics. The tussle began last month as a relatively trivial but highly public back-and-forth over which company had the lowest prices on the most anticipated new books and DVDs this fall. By last week, it had spread to select video game consoles, mobile phones, even to the humble Easy-Bake Oven, a 45-year-old toy from Hasbro that usually heats up small cakes, not tensions between billion-dollar corporations. Last Wednesday, Wal-Mart dropped the price of the oven to $17, from $28, as part of its “Black Friday” deals. Later the same day, Amazon cut its price, which had also been $28, to $18. “It’s not about the prices of books and movies anymore. There is a bigger battle being fought,” said Fiona Dias, executive vice president at GSI Commerce, which manages the Web sites of large retailers. “The price-sniping by Wal-Mart is part of a greater strategic plan. They are just not going to cede their business to Amazon.” Retailers are already fighting for every dollar consumers spend this holiday season. Sales are not expected to drop as much as they did last season, but the National Retail Federation, an industry group, predicts that they will decline 1 percent, to $437.6 billion. Of course, Wal-Mart and Amazon are fundamentally different companies, and for now, at least, Amazon poses little immediate threat to the behemoth from Bentonville, Ark. Wal-Mart, with $405 billion in sales last year, dominates by offering affordable prices to Middle America in its 4,000 stores. Amazon is a relative schooner to Wal-Mart’s ocean liner, with $20 billion in sales, mostly from affluent urbanites who would rather click with their mouse than push around a cart. This fight, then, is all about the future. Rapid expansion by each company, as well as profound shifts in the high-tech landscape, now make direct confrontation inevitable. Though online shopping accounts for only around 4 percent of retail sales, that percentage is growing quickly. E-commerce did not suffer as deeply as regular retailing during the economic malaise, and it is recovering faster than in-store shopping. People are also shopping on smartphones and from their HDTVs. Amazon, based in Seattle, has harnessed all of these trends, and is also behaving more like a traditional retailer. This fall it expanded its white-labeling program, slapping the Amazon brand onto audio and video cables and other products, and introduced same-day shipping in seven cities, trying to replicate the instant gratification of offline shopping. For rivals both real and putative, Amazon is expanding its slice of the retail pie at what must be an alarming rate. In the third quarter of this year, regular retail sales dipped by about 4 percent and e-commerce over all was flat. But Amazon sales shot up 24 percent, sending its shares soaring. More important for Wal-Mart, sales in Amazon’s electronics and general merchandise business — which competes directly with much of the selection in Wal-Mart stores — were up 44 percent. Wal-Mart does not break out Web sales, but it has been reported that its online business produces revenue of several billion dollars. “If you are Wal-Mart, you want to have your proportional piece of this change in consumer behavior,” said Scot Wingo, chief executive of ChannelAdvisor, which helps retailers sell online. “You can even paint a scenario where e-commerce one day is 15 percent of all shopping, and that could really start to erode Wal-Mart’s offline business.” That is why many analysts are unsurprised that Wal-Mart executives have placed Amazon squarely in their sights, with public throw-downs in interviews and pointed discounting. It began last month with what appeared to be a public-relations-oriented competition on book prices, with both companies (along with Target, based in Minneapolis) dropping prices on books like “Under the Dome,” by Stephen King, to below $9. The companies then began jousting over the prices of DVDs. Less visibly, there were isolated skirmishes, some of which also lowered prices in Wal-Mart’s stores. Wal-Mart offered a $15 gift card with a purchase of the new video game Call of Duty: Modern Warfare 2 — and Amazon matched soon after. Wal-Mart and Amazon then both offered the Xbox 360 gaming console for $199 — with a $100 gift card thrown in. Last week, they both began offering the new Palm Pixi phone for around $30 — nearly $175 off the suggested retail price. Of course, online retailers have always competed on price, monitoring rivals’ sites for changes and adjusting accordingly. “We’ve grown up in a supercompetitive environment where customers can check prices with one click, and we like it that way,” said Craig Berman, an Amazon spokesman. But rhetoric from Wal-Mart itself has stoked the flames of rivalry. In an interview last week, Raul Vazquez, the president and chief executive of Walmart.com, asserted that the site was growing faster than Amazon’s; suggested that Amazon Prime, a two-day-shipping service that costs $80 a year, was too expensive; and said that it was “only a matter of time” before Wal-Mart dominated Web shopping. “Our company is based on low prices,” Mr. Vazquez said, laying down a challenge. “Even in books, we kept going until we were the low-price leader. And we will do that in every category if we need to.” Friction between the two companies is not entirely new. In the late 1990s, Amazon assembled at least some of its knowledge of retail supply chains by hiring away Wal-Mart employees. Wal-Mart sued, and the two companies settled privately. In a battle over prices, Wal-Mart is on more familiar turf. With its unmatched size, Wal-Mart has more leverage than anyone to negotiate better terms with suppliers. Offering the lowest price “is in our DNA,” Mr. Vazquez said. Among Amazon’s advantages are a sophisticated distribution network built specifically for Web shopping, the thousands of outside sellers who offer products on Amazon.com, and a recognizable online brand. Amazon’s customers also do not pay sales tax in most states, a crucial advantage that companies like Wal-Mart, and their lobbyists, are trying to eliminate. Jeffrey P. Bezos, Amazon’s chief executive, is fond of saying that retailing is a big market with room for many winners. But for Ms. Dias, from GSI Commerce, Wal-Mart’s campaign against Amazon is overdue. As an executive at the now-defunct Circuit City chain, and as an adviser to traditional retailers today, she says she has watched many companies overlook the long-term threat posed by Amazon. “We have to put our foot down and refuse to let them grow more powerful,” she said. “I applaud Wal-Mart. It’s about time multichannel retailers stood up and refused to let their business go away.” http://www.nytimes.com/2009/11/24/business/24shop.html  Whack-A-Mole Security: Bad Policy, Bad Legislation Daniel Castro The recent disclosure of a confidential Congressional document has at least one congressman calling for a ban on peer-to-peer (P2P) file sharing software, but a closer look at the problem reveals that this effort would merely be treating the symptoms, not the disease. First some background. Last month the Washington Post revealed that more than thirty members of Congress and staffers were under investigation for possible ethics violations, including for "accepting contributions or other items of value... in exchange for an official act." While this revelation was shocking, perhaps even more shocking was the means by which this information was leaked -- the information was downloaded from the Internet. As detailed by the Washington Post and the Committee on Standards of Official Conduct in the U.S. House of Representatives, a low-level committee staffer had saved a copy of a confidential House ethics committee report on her personal computer while working from home. Unfortunately, the staffer was also running a peer-to-peer file sharing program and inadvertently saved the file in a folder that was shared with other users. By saving the file in a shared folder, the staffer made the document available to all other users on the publicly accessible file sharing network. While only one report from July was reported by the Washington Post, the Standards Committee noted that the potential disclosure involved several confidential documents. The initial reaction from House leaders was tempered. The Standards Committee issued a statement reminding House Members, Officers and employees to maintain good information security practices when handling sensitive materials and noted that "no matter how robust our cybersecurity systems are, they remain subject to individual error." The statement also emphasized that the disclosure took place on the staffer's personal computer, that the staffer was no longer employed by the committee, and that no House information systems were compromised. Case closed? Not so fast. Some members of Congress are jumping on the media attention surrounding the ethics leak to enact a legislative ban on peer-to-peer file sharing software. Rep. Edolphus Towns (D-NY) has introduced the Secure Federal File Sharing Act which would prohibit the use of peer-to-peer software on all computer systems run by the Federal government or its contractors. In addition, the legislation directs the Office of the Management and Budget (OMB) to address the use of P2P software on the home computers of government employees used for work purposes. To be fair, this is not a completely reactionary move. Congress has held a number of hearings over the years detailing instances of sensitive and confidential information being revealed over peer-to-peer networks--including Social Security numbers, financial records, and even location information about a safe house for the first family. In fact, the latter incident spurred Rep. Towns to first announce his call for a ban on the use of peer-to-peer software on all government networks. It is hard to fault the Congress for misunderstanding the problem when some of the press reports surrounding the incident have often been misleading or inaccurate. In fact, most of the press seems to blame the disclosure on the peer-to-peer software, rather than on human error or the bad policies and practices that led to the disclosure. And some reports are simply erroneous and reflect a poor understanding of the technology. For example, according to the Wall Street Journal, by using a peer-to-peer network the staffer "allowed someone to hack into her computer and obtain the document." That's like saying by publishing an article on its website, the Wall Street Journal allowed its readers to hack into their web server and read the news. To be clear, using peer-to-peer file sharing software exposes users to a number of risks. First, P2P software is often used by Internet users to download and distribute copyrighted content, an illegal act for which individuals can and should be held responsible. Second, the files shared on P2P networks often contain malware -- viruses, spyware, and other malicious software that can steal the user's private data and turn an infected PC into part of a botnet. But peer-to-peer software, by itself, did not cause the confidential Congressional document to be leaked to the press. Some have argued that peer-to-peer software presents a unique threat because users are often unaware that the software is sharing files on their personal computer. For this reason, Reps. Mary Bono Mack (R-CA), John Barrow (D-GA) and Joe Barton (R-TX) introduced the Informed P2P User Act (H.R. 1319) earlier this year which would require peer-to-peer software to give users conspicuous notice and obtain consent before sharing files from a user's PC. First, most file sharing software does not share your entire hard drive, but just a few select folders. In addition, P2P software is already evolving and responding to their users' demands for more control and notice over how files are shared and preventing accidental disclosure of private information. Finally, while more notice may reduce some accidental file disclosures, incidents such as the recent leak of Congressional documents stem from misconfigured settings or operator error, not a lack of notice. But the legislative response from Rep. Towns is more troubling. The congressman has argued that "We can no longer ignore the threat to sensitive government information that insecure peer-to-peer networks pose. Voluntary self-regulations have failed so now is the time for Congress to act." However, the committee staffer revealed confidential information by mistakenly saving the document in a shared file folder. This mistake was human error. If the staffer had accidentally emailed those documents--say by inadvertently clicking on the wrong attachment--would members of Congress now be calling for a ban on email? Of course not. The underlying problem is not that the staffer was running a P2P program on her computer, but that the sensitive documents had virtually no access controls on them to prevent their unauthorized use. After the staffer was allowed to take the document home as an unsecured file, the confidential information could have been leaked in many different ways--from a lost USB drive to a stolen laptop to a snooping roommate. If the file would have even had basic password protections enabled, probably none of the ensuing drama would have happened. A properly encrypted file, even if lost or made publicly available, would remain secure and confidential. Unfortunately, this type of response is typical when organizations face a data breach, as executives scramble to fix the immediate problem without taking time to understand the bigger issues. This whack-a-mole approach to information security problems is bad strategy for an organization and bad policy for the Congress. Good information security practices depend on IT leaders forming a solid understanding of risk and taking action to manage those risks. For example, in this case, the risk here is not peer-to-peer file sharing, but rather inappropriate disclosure of confidential information. A better approach would be to review the policies and procedures for access to confidential information. Questions to ask include: * Who should be given access to sensitive information? * Should employees be permitted to take sensitive documents out of the office? * If so, what controls are in place to ensure that the data stays secure? * If not, what controls are in place to ensure files remain in the office? * Are sufficient penalties in place to punish those who violate these policies? * Are the known risks acceptable, and if not, what else should be done? Certainly people are not perfect and some data breaches will still occur even with better policies and technology. And prohibiting P2P software probably makes sense for most agencies, but it is only a small part of a bigger problem. Rather than narrowly focusing on P2P, policymakers should be promoting broad strategies for sound information security policies across government. For example, rather than legislate that government IT executives should have a full accounting of P2P use on their network, they would be better off mandating that these IT executives need to have information security programs in place that give them detailed network intelligence so they can inventory what applications are running on their computers and track suspicious outbound and inbound network connections. In addition, government-wide policies should be developed to promote secure teleworking. As teleworking becomes more common the perimeter for enterprise security becomes wider and the amount of control that IT administrators can exert over remote PCs becomes weaker, thus creating a new threat environment. Government best practices in this area would be helpful to small and large businesses in the private sector. Policymakers should use this experience as an opportunity to push for substantial progress on information security practices, not merely small mandates banning a particular type of software. http://www.huffingtonpost.com/robert..._b_364794.html  India to Set Up Automatic Monitoring of Communications The pilot for the project will start in June, a minister said John Ribeiro India plans to set up a centralized system to monitor communications on mobile phones, landlines and the Internet in the country, a minister told the Rajya Sabha, the upper house of Parliament, on Thursday. Indian laws allow the interception and monitoring of communications under certain conditions, including to counter terrorism. A pilot of the new Centralized Monitoring System (CMS) is to be started by June next year, subject to clearances by other government agencies, Gurudas Kamat, Minister of State for Communications and Information Technology told the Rajya Sabha, according to an announcement by the government's Press Information Bureau. The CMS will have central and regional databases to help central and state-level enforcement agencies intercept and monitor communications, the government said. It will also have direct electronic provisioning of target numbers by government agencies without any intervention from telecom service providers, it added. It will also feature analysis of call data records and data mining of these records to identify call details, location details, and other information of the target numbers. The current system used by the government for call monitoring can be easily compromised because of the requirement of manual intervention at many stages, the minister said. Interception using the new system will also be instant, he added. The statement by Kamat comes on the anniversary of a terrorist attack on a number of sites in Mumbai, including two premium hotels, a railway station, and a Jewish community center. The terrorists are believed to have used mobile communications and the Internet extensively to plan and execute their attacks. The government brought into force earlier this year the Information Technology (Amendment) Act 2008, an amendment to an earlier law, which broadened the government's powers to intercept and monitor communications. Some experts have argued that the government should set up an organization like an ombudsman to ensure that information collected during surveillance is not misused. http://www.goodgearguide.com.au/article/327850  SWIFT - EU to Grant USA Nearly Unlimited Access to all EU Banking Data brusselsblogger The EU justice and home affairs minister are about to agree on a large-scale banking data sharing plan with the United States. The agreement will have a massive impact on the privacy of banking data of European businesses and citizens. Background of the deal It’s everything about SWIFT, a company that handles the bank transactions for thousands of bank, inluding most European banks. SWIFT is based in Belgium but has also a branch in the USA. Under the TFTP programme the US government forced the US branch (which mirrors all data based in Belgium) to allow government access to all these bank transactions in order to help anti-terrorism operations. SWIFT is now moving all its data centers outside the EU and the US, to Switzerland. In order to continue allowing the US authorities accessing all banking data a high level agreement between the EU and the USA is currently being negotiated. It is likely to be agreed on in the EU council of minister meeting next Monday, 30 November 2009. Why is the SWIFT deal dangerous? The move of SWIFT the data server to Switzerland would be an excellent opportunity to stop the nearly unlimited access of US authorities on EU bank transactions. But EU justice and interior minister are apparently keen agree a deal as soon as possible, on 30 November. Why 30 November? Because one day later, on 1 December 2009, the EU’s Lisbon Treaty will be in force and would allow the European Parliament to play a major role in the negotiations of the deal with the USA. A deal one day before will be a slap in the face of democracy in the EU. SWIFT handles 15 mio bank transactions daily for more than 9000 banks worldwide. Nearly every transnational bank transaction within the EU is recorded in the SWIFT data centers, including amount, sender, recipient, and transaction comments. The agreement will even allow to transmit “other personal data”. This will allow US authorities to establish a huge data mining database, allowing to query every substantial business link within the EU. No question that the United States will never admit that openly. But data protection agreements should not be based on hope but on principles. The current draft is based on hope. Is there no opposition to the deal? When German media reported about the deal about 2 weeks ago some opposition to the deal was raised. Germany, France and Austria seem to had important data protection concerns. Finally it was reported that Germany would even block the deal. Two weeks later all the opposition apparently has disappeared and Germany will now abstain from the vote on Monday, paving the way for the agreement coming into force. MEPs in the European Parliament have raised concerns as well, but if the deal is agreed before 1st December, there will be no way for them to have a say. No reciprocity The most suprising fact related to the EU negotiations with the US is the missing demand of reciprocity. In other words: while the US will be able to access EU banking data no access to US banking data by EU auhtoirties is being foreseen. Open questions It is unclear to me what exact legal form the agreement with the United States will have. To my knowledge it will probably not require any ratification by national parliaments. It needs to be seen whether procedures against the deal will be able to be launched at the European Court of Justice. They could potentially be based on the EU’s current, rather strict data protection legislation. http://brusselsblogger.blogactiv.eu/...-banking-data/  Computer Hacker Gary McKinnon to be Extradited to US • Alan Johnson quashes last-ditch attempt to halt extradition • Family fear hacker with Asperger's is at serious risk of suicide Afua Hirsch Computer hacker Gary McKinnon, who has Asperger's syndrome, is at serious risk of suicide, relatives said today, after the home secretary rejected a last-ditch attempt to prevent his extradition to the US. In a letter today Alan Johnson ordered McKinnon's removal to the US on charges of breaching US military and Nasa computers, despite claims by his lawyers that extradition would make the 43-year-old's death "virtually certain". "The secretary of state is of the firm view that McKinnon's extradition would not be incompatible with his [human] rights," said the letter, dated 26 November. "His extradition to the United States must proceed forthwith." The decision, described by lawyers as "callous", has prompted fresh fears about McKinnon's well-being. The letter rejected new expert medical evidence that McKinnon's health had deteriorated dramatically since losing his case in the high court in July, and meant that extradition would violate his right to life. "Gary is at risk of suicide, I'm extremely worried about him," said McKinnon's mother, Janis Sharp. "This government is terrified of speaking up to America, and now they are allowing vulnerable people to be pursued for non-violent crime when they should be going after terrorists." Mckinnon's lawyer, Karen Todner, said she planned to start a judicial review of the home secretary's decision. "We cannot give up because in some ways it's like dealing with a death row case, and we genuinely believe Gary's life is at stake here," she said. McKinnon, from north London, was accused in 2002 of using his home computer to hack into 97 American military and Nasa computers, causing damage that the US government claims will cost more than $700,000 (£425,000) to repair. This year the high court rejected arguments that the extradition would violate his rights, after lawyers argued the prospect of up to 60 years in a "supermax" jail would cause mental harm because he has Asperger's and a depressive illness. Johnson insisted that he had received a guarantee from the US government that McKinnon would be assessed by doctors and psychologists were he transferred to prison there, and that he would receive "appropriate medical care and treatment", including counselling and medication. The assurances were given in a letter this February from the US department of justice, which was seen by the court. The home secretary also said that should McKinnon be convicted in the US and seek to serve his sentence in Britain, the UK government would "progress his application at the very earliest opportunity". Lawyers had also argued that McKinnon could be prosecuted in the UK on lesser charges of computer misuse, preventing his extradition. "The CPS wanted to prosecute Gary, but they were told from the very top to stand aside and let America take him," said Sharp. Critics say an extradition treaty designed to speed up extradition between the two countries works in favour of Americans and fails to adequately protect Britons. Geoffrey Robertson QC, one of Britain's most eminent human rights lawyers, told the Guardian: "To send a British citizen to the US, without any right to bail, to face 10 years in prison for a crime for which he would be unlikely to receive any custodial sentence if tried here amounts to 'cruel and unusual' punishment' in breach of our 1689 Bill of Rights. The home secretary should not hide behind the weasel words of the European Convention when he should be following the law laid down by our own historic bill of rights." McKinnon's legal team had hoped to join his case to that of Ian Norris, a retired business chief facing extradition to the US on charges of obstructing justice through his alleged role in an illegal cartel. His case will be heard in the supreme court on Monday. It was argued unsuccessfully that McKinnon's case raised similar legal issues and should be considered by the supreme court panel. Attempts to be heard in the supreme court failed however, although McKinnon'sHis legal team said they would be seeking a judicial review of yesterday's decision. Sharp said: "We thought with Obama it would be different. Now the first person in the world to be extradited to the US for computer misuse is going to be a guy with Asperger's." http://www.guardian.co.uk/world/2009...radition/print  Wikileaks Says it has Half a Million 9/11 Pager Messages Kevin Poulsen The document-leaking site Wikileaks says it’s preparing to release 500,000 intercepted pager messages from a 24-hour period encompassing the September 11 terrorist attacks. Site operators say they plan to start rolling out the texts beginning at 3am New York time (8am GMT), paced to display as they were broadcast at the corresponding time on September 11, 2001. American Airlines Flight 11 crashed into the World Trade Center’s North Tower at 8.46am local time, and United Airlines Flight 175 hit the South Tower 17 minutes later. “Text pagers are mostly carried by persons operating in an official capacity,” reads the description on the site. “Messages in the archive range from Pentagon and New York Police Department exchanges, to computers reporting faults to their operators as the World Trade Center collapsed.” A sample of the alphanumeric pages appeared on the site last night: 8:36:03 AM IRAQ SAYS IT SHOOTS DOWN U.S. RECONNAISSANCE PLANE 8:51:31 AM Andrew.Terzakis@pentagon.af.mil|Please call Pentagon Weather|UNCLASSIFIED Please call Pentagon Weather…….reference 1030 Meeting…..703-695-0406 ANDREW J. TERZAKIS, Lt Col, USAF D 8:53:44 AM “NYPD Ops Div” <|1 PCT WORLD TRADE CENTER|— 1 PCT - WORLD TRADE CENTER - POSSIBLE EXPLOSION WORLD TRADE CENTER BUILDING. LEVEL 3 MOBILIZATION TO CHURCH AND VESSY. 9:24:48 AM DOLLAR TUMBLES VS EURO, YEN AFTER WTC EXPLOSION 9:24:59 AM NYC WTC’S: WMS TKT 191100495. SWITCHES SEEM TO BE OKAY . OVERLOADS IN SM 9 OF SOUTH TOWER FROM HIGH 9:31:51 AM N.Y.C. TKT#191100488 - WTC HAS BEEN HIT BY AN AIRPLANE AND A BOMB. CURRENTLY B6 IS BEING EVACUATED. NCC HAS RECEIVED MULTIPLE ALARMS OPTICAL / ENVIORNMENTAL. UPDATES WILL FOLLOW. RYAN P/L NCC 800-824-8049 9:32:52 AM FANNIE MAE DELAYS BENCHMARK BILL,CALLABLE NOTE ANNOUNCEMENT DUE TO WTC BLASTS 9:50:03 AM it’s reported that a US military helicopter circled the building then crashed into or next to the Pentagon - it’s not clear to whether it was the White House or the Pentagon - they are being evacuated 7:05:57 AM Please don’t leave the building. One of the towers just collapsed! PLease, please be careful. Repeat, 11:00:30 AM BOMB SQUAD PLS REPORT TO EDIC..PER T913..OPS/JL 11:13:04 AM Lines to Washington & Saudi are blocked or jammed. Couldn’t get thru. Jim at the FBI had no info - he suggested we watch Fox or CNN. Chris. 11:20:52 AM Eddie and Paul are okay. Paul is still trapped in his building which is next to the WTC. 11:29:13 AM pewells|I’m OK. I saw the whole thing. Was on the roof looking at the first fire when I saw the second plane plow into the second tower. Unbelievable, literally…I was inside when they collapsed. Still in my apt, nowhere to go…This is the end of the world as we know it… 11:39:47 AM jtamer|You are needed in the WAR room asap. 3:25:54 PM im not dealing with this shit today….i will call johnston in early……ford shut down there plants and im not answering why we are still working….fuck this. FROM: RYDER LITTLEJOHN (x18914) (3 5:20:30 PM Honey wanted to tell you how much i love you. I was alittle worried.I Don’t want to lose you now that I got you back. You mean everything to me. You have my whole heart and life. Ilove you so much, 6:05:05 PM We are bombing Afganistan. Pene 6:58:58 PM 1) my nephew’s ok, 2) there’s a dead body at the main gate, 3) US denies responsibility for bombing in Afghanistan. Over and out. Wikileaks didn’t identify the source of the messages, but the site has a solid track record for releasing authentic information. Unencrypted pager traffic has been subject to interception by hackers and others for years — an easy video tutorial made the rounds just last May. But Wikileaks implies this data came from an organised collection effort. “While we are obligated ... to protect our sources, it is clear that the information comes from an organisation which has been intercepting and archiving national US telecommunications since prior to 9/11.” http://www.wired.co.uk/news/archive/...-messages.aspx  Proper Use of English Could Get a Virus Past Security Robert Blincoe Hackers could evade most existing antivirus protection by hiding malicious code within ordinary text, according to security researchers. One of the most common ways of hijacking other people's computers is to use "code-injection" attacks, in which malicious computer code is delivered to and then run on victims' machines. Current security measures work on the assumption that the code used has a different structure to plain text such as English prose. Now a team of researchers has highlighted a potential future theatre in the virus-security arms race by working out how to hide malware within English-language sentences. Josh Mason of John Hopkins University in Baltimore, Maryland, and his colleagues developed a way to search a large set of English text – mostly composed of more than 15,000 Wikipedia articles and roughly 27,000 books from the online library Project Gutenberg – for combinations of words that could be used in code. Their program highlighted the text to be used in the instruction set in bold, while leaving the sections to be skipped in plain text, as in the following example: There is a major center of economic activity, such as Star Trek, including The Ed Sullivan Show. The former Soviet Union." Code Stands Out It's not the first time the potential weakness has been recognised, but many computer security experts thought the rules of English word and sentence construction would make the task impossible. In machine code – the raw code that microprocessor chips understand – combinations of characters not seen in plain text, such as strings of mostly capital letters, are required. "There was not a lot to suggest it could be done because of the restricted instruction set [of machine code]," said Mason. "A lot of people didn't think it could be done." John Walker, managing director of UK security consultancy Secure-Bastion, said the research highlighted a basic weakness in antivirus tactics, and that hackers would undoubtedly try to exploit it. "There is no doubt in my mind that antivirus software as we know it today has gone well past its sell-by date," he said. Nicolas Courtois, a security and cryptology researcher at University College London, said malicious code in this form would be "very hard if not impossible to detect reliably". Shell game Hackers call the part of a code-injection attack that is used to gain control of a vulnerable computer "shell code". Because this is usually written in machine code, Mason and colleagues dubbed their technique "English shell code". They presented their research (PDF) at the ACM Conference on Computer and Communications Security in Chicago earlier this month, being careful to leave out some of their methodology to avoid helping malicious hackers. "I'd be astounded if anyone is using this method maliciously in the real world, due to the amount of engineering it took to pull off," said Mason. He added that he and his colleagues developed the proof of concept to highlight the weakness and to encourage the development of security measures before hackers worked out how to use similar techniques. http://www.newscientist.com/article/...ef=online-news  New Attack Fells Internet Explorer The zero-day flaw is unreliable, but Symantec expects reliable exploits in the 'near future' Robert McMillan A hacker has posted attack code that could be used to break into a PC running older versions of Microsoft's Internet Explorer browser. The code was posted Friday to the Bugtraq mailing list by an unidentified hacker. According to security vendor Symantec, the code does not always work properly, but it could be used to install unauthorized software on a victim's computer. "Symantec has conducted further tests and confirmed that it affects Internet Explorer versions 6 and 7," the company wrote on its Web site Saturday. "We expect that a fully-functional reliable exploit will be available in the near future." Security consultancy Vupen Security has also confirmed that the attack works, saying it worked on a Windows XP Service Pack 3 system running IE 6 or IE7. Neither company was able to confirm that the attack worked on Microsoft's latest browser, IE 8. Symantec did not report that the attack is being used by cyber-criminals, but because Internet Explorer is so popular, this type of code is highly coveted by hackers. If the software does pop up in online attacks, it will put pressure on Microsoft to rush out an emergency patch, ahead of its regularly scheduled Dec. 8 security update. Microsoft could not be reached Saturday for a comment on the issue. Together, IE 6 and IE 7 command close to 40 percent of the browser market. The flaw lies in the way Internet Explorer retrieves certain Cascading Style Sheet (CSS) objects, used to create a standardized layout on Web pages. For the attack to work, the hacker would have to lure a victim to a Web page that contained maliciously encoded JavaScript, Symantec said. This technique has emerged as a favorite way for hackers to install their malicious software on computers in recent years. "To minimize the chances of being affected by this issue, Internet Explorer users should ensure their antivirus definitions are up to date, disable JavaScript and only visit Web sites they trust until fixes are available from Microsoft," Symantec said. http://www.networkworld.com/news/200...-internet.html  Google Search Results Significantly Poisoned Cyveillance Hundreds of Thousands of Links Leading to Malware Found in Google Results Cyveillance has discovered a complex attack vector that uses Google search results to distribute malicious software (malware) to unsuspecting Internet users. Using this attack vector, users click on links within Google search results and are routed to sites that attempt to download malware to their computers. The attack method also relies on inattentive webmasters who do not update the software on their sites and often unknowingly provide the material that appears in the search results. The common string albums/bsblog/category is found in the URLs for all these blogs. By simply using the Google search parameter allinurl, along, you can see how many other sites contain the same string. As can be seen in the image above, more than 260,000 URLs are presented in Google’s search index leading to blogs similar to the ones illustrated in our example. Beware: if you were to visit one of the above blogs after clicking on the URLs in Google search results, then you would be taken to two different websites. The second site would attempt to install fake anti-virus software on your computer. (For safety purposes, we are not directly linking to infected search results, but if you enter the query shown in the image, you can recreate the above results.) Readers can simply copy and paste the destination URL into your browser to direct it to the desired website, you would be taken to the boring but otherwise harmless blog posting like those pictured earlier in this discussion. The attack only happens when the compromised blog site determines that you arrived by way of Google by checking the HTTP referrer. An earlier search similar to the one above produced 104,000 infected URLs: As you can see, only a small portion of sites in the search results carry a warning provided by Google. The reason for the small number of warnings is likely because the actual attacks do not take place on the website URLs in the search results, but on the sites you’re redirected to thereby decreasing the chances that Google will designate the destination sites as harmful. Digging Deeper On all the infected sites found there is rogue blog publishing software installed, sometimes in the popular online photo gallery software Coppermine. (The most recent version of Coppermine we observed being used in this attack was 1.4.24, and Coppermine is now on release 1.4.25.) These rogue blogs automatically and regularly publish new posts that are titled with esoteric terms like “las vegas rental no credit check”, “real world melinda and danny”, or “uninvited song lyrics alanis morrissette morissette”. These posts are intentionally not titled just with simple terms that are very popular like “Britney Spears”, “Obama” or “Paris Hilton” to avoid having to compete in search rankings with the millions of pages which already exist for these topics. Instead, the authors of this exploit take advantage of the long-tail of search where rare combinations of search terms in aggregate make up a very large portion of the queries made by web surfers in search engines. In fact, a surprising amount of internet searches contain four and five words, and the authors of this attack appear to have titled their blogs’ titles with this in mind to be exposed to as many potential victims as possible. No words are to be found in these blog posts. The content of each post consists solely of images that are found among images.google.com results of queries for the same terms found in the post’s title. Each of the images are then presented inside the new blog post and contain alt and title tags which also match the post’s title in an attempt to maximize the relevancy in Google’s eyes for any query matching those terms. For example, if one of these blog postings was titled “common and kanye west”, the blog posting would simply contain four or five of the images shown in the results of a Google image search for “common and kanye west”, and each of these images would in turn be given alt and title tags that read “common and kanye west”. The repetition of the same terms in the post title and image tags is a clumsy but straightforward mechanism of suggesting to Google that the page contains highly relevant information about those topics, hoping that Google will then present these pages to searchers. When the searchers click on these links in Google search results, the blog will redirect that visitor to the fake anti-virus installation site. The Attack The fake anti-virus site displays what appears to be the results of a computer scan, warning the user that “31 Malware programms was found!” (sic). The fake notifications display illegitimate Windows anti-virus warnings regardless of the user visiting the site on a Macintosh, as happened in the pictured example. Interestingly however, it did correctly dynamically insert this researcher’s computer’s IP address into the image (which has now been blurred out). Clicking on anything in the fake infection findings, including the blue framed popup, will result in a file named Inst_58s6.exe being downloaded to the user’s computer. Where the Wild Things Are The path from the infected websites to the fake anti-virus software drop sites is swift and likely not noticed by the user. A user will click on one of the innocent-looking Google search results and is transported to a “middle man” domain like ionisationtools.cn or moored2009.cn. The server at these domains will then redirect the web surfer to a final destination where the fake anti-virus is pushed on the user, as described above. The middlemen domains like ionisationtools.cn or moored2009.cn are “live” for just a day or two and quickly go offline. Their DNS records briefly point to the free DNS service provider EveryDNS.net. The actual fake anti-virus drop sites are found on domains such as: * premium-protection6.com * file-antivirus3.com * checkalldata.com * foryoumalwarecheck4.com * antispy-scan1.com All these domains observed by Cyveillance were registered with Chinese registrar TodayNIC.com and like the middlemen sites above, these domains are registered one or two days before the inbound Google search traffic will be arriving, suggesting that the software now directing search traffic from the infected websites may know in advance where the drop sites will be in advance. Only Google? It appears that Google is the only search engine with knowledge of these infected sites. We learned this by taking several domains that contained the infected Coppermine installs and used Bing’s site: command and Yahoo!’s Site Explorer; neither of these search engines returned any URLs which contained this particular exploit in action, suggesting that Google is the only major search engine being used as the attack vector by these malware distributors. It is possible that the attackers took advantage of the ability to submit .xml sitemaps in Google to stimulate the search engine to visit and index the rogue blogs’ postings. A suitable .xml file was found on the sites examined to support this technique. What Can Be Done? Cyveillance recommends that Google investigate all URLs in its main index which contain albums/bsblog/category or bmsblog/category in the URLand take the appropriate action to minimize the potential danger to users. Additionally, webmasters need to ensure that software is constantly kept up-to-date with the latest revisions and site content is periodically reviewed for potential malicious activity. While not necessarily practical, users can minimize the exposure to the attack vector described in this writing by copying and pasting the link in the Google search results directly in their browser rather than a directly clicking on the search result link. Additional steps to minimize the harm from the attack vector are ensuring all computer software is up-to-date and practicing safe Web surfing habits. Heading in to 2010 and beyond, Cyveillance will continue to make the investments in personnel and technology needed to warn the Internet community of new threats, protect our customers, and stay one step ahead of the bad guys. http://www.cyveillanceblog.com/gener...search-results  Microsoft, News Corp Weigh Web Pact: Source Microsoft Corp has had talks with News Corp about a tie up, which would involve News Corp getting paid to take its news websites off Google Inc, a source familiar with the matter said on Sunday. News Corp, which owns such papers as the Wall Street Journal and the Sun, started the discussions, which were at an early stage, the source said. News Corp Chief Executive Rupert Murdoch has said he wants to make people pay for access to his news websites. Other publishers including The New York Times are also searching for ways to charge for news online, convinced that they must not give news through search engines such as Google and Yahoo Inc. Microsoft has also talked with other online publishers about removing their sites from Google, according to the Financial Times, which first reported the development. "This is all about Microsoft hurting Google's margins," the FT quoted a website publisher, who had been approached by Microsoft. Microsoft, which relaunched its search engine as Bing this year, has been looking for ways to challenge market leader Google. Earlier this year, it signed a 10-year global web search partnership with Yahoo, a deal that U.S. and European antitrust regulators are evaluating. Microsoft could not reached for comment late on Sunday. News Corp declined to comment. The source is anonymous because the talks are not public. (Reporting by Robert MacMillan; writing by Paritosh Bansal; Editing Lincoln Feast) http://www.reuters.com/article/techn...5AM02W20091123  Murdoch Courts Trouble if he Blocks Google on News Robert MacMillan Rupert Murdoch has spent months complaining that Google is ruining the newspaper business, and now he wants to do something about it. But, his proposal is a gamble, and one that could hurt News Corp instead of helping it. Murdoch is considering removing News Corp's news from Google's Web search results, and is talking to Microsoft Corp about listing the stories with its Bing search engine instead. Microsoft would pay for the privilege, sources have told Reuters, but it was not clear how much. If Murdoch pulled this off, he will likely be followed by other newspaper publishers looking for ways to make money when all the old ones are waning in the digital age. Newspaper owners resent Google because the Internet company makes money from the advertisements that it displays next to news search results. News Corp's proposal is a way to get a cut of the action. Risks include destroying ad revenue most news websites depend on if traffic goes down because Google users can't find the stories. It's also not clear how regulators would feel about such a move. "You're immediately cutting off audience," said Jeff Jarvis, media blogger and author of the book "What Would Google Do?" Google brings as much as 14 percent of incoming traffic to News Corp's U.S. news websites, including the New York Post and Fox News, Bernstein analyst Jeffrey Lindsay estimated. If News Corp blocked access to Google, he wrote in a note to investors, it would hurt only News Corp. Many people find their news on Google, which has 65 percent of the U.S. search market according to comScore. Newspaper publishers whose websites depend on advertising sales want lots of visitors, and need Google to supply them. Google provides news organizations about 100,000 clicks a minute, said company spokesman Gabriel Stricker. "Each of those visits offers a business opportunity for the publishers to show ads, win loyal readers and sell subscriptions," he said. Making Microsoft's Bing search engine the only way to look for news would slice away visitors and lower the amount of money news websites could charge advertisers. There is little chance people will abandon Google, which has become such a giant that its name is also a verb. "Consumers do not expect search engines to be exclusive," Forrester analyst Shar VanBoskirk wrote. "If they can't find something through search, it may as well not exist." Web Suicide? Microsoft declined to comment, but in theory would like partnering with News Corp to increase Bing's share of the lucrative search advertising market at Google's expense. Microsoft had a 10 percent share of the U.S. search market in September, according to comScore. Some shareholders worry Microsoft might pay more money to News Corp and publishers than the privilege is worth. "I don't want Microsoft to throw a lot of money toward News Corp, and I don't know why News Corp would do this to themselves," said Kim Caughey, senior analyst at investment fund Fort Pitt Capital Group, which holds Microsoft shares. There could also well be U.S. government scrutiny over an exclusive deal between News Corp and Microsoft, or any sort of joint action by news publishers, at the expense of other Internet companies or consumers. News Corp declined to comment, and sources close to the discussions emphasized talks so far are ideas, nothing more. Nine of the largest U.S. newspaper publishers also refused to comment. Other U.S. publishers, if they joined in, would feel more pain because they are far smaller than News Corp and depend on ad sales more than anything else, analysts said. "It's nothing short of suicidal," Jarvis said. Risking suicide might not seem so crazy to publishers. Many people say they face creeping death as readers drop print subscriptions and ad revenue falls. As many deal with looming piles of debt, they must consider some radical moves after laying off thousands of workers. "They cannot survive at the scale they are accustomed to online unless they can find a new economic model," said Tom Rosenstiel, head of the Project for Excellence in Journalism. "If it works, Google might say, 'wait a second, it's very important for us to maintain our market share of search'," he said. "Google has an interest in the news industry surviving." Cartel Betting on that is risky. "The only way such a strategy would hurt Google in our view is if all of the major newspapers and the major news sources including the AP and Reuters were to agree to a watertight cartel," Lindsay wrote in his Bernstein note. Jarvis agreed. "It would be a mosquito bite on the elephant's butt," he said. Also, consumers could complain about media companies choking off access to news, something that would spark ire from Congress to the White House, analysts said. It could carry the whiff of collusion among news outlets to fix prices, something publishers fear being accused of. "None of this sounds to me to be pro-competitive or efficient," said David Balto of the Center for American Progress, a former Federal Trade Commission policy director. One possible outcome of News Corp threatening to drop Google could be detente: a common way for publishers to get paid for news that search engines from Google to Yahoo make available to readers, said Outsell analyst Ken Doctor. "I don't think the endgame for anybody here is to expect that Google's going to get turned off... although you never know," he said. (Reporting by Robert MacMillan, additional reporting by Bill Rigby in Seattle and Diane Bartz in Washington, editing by Tiffany Wu) http://www.reuters.com/article/newsO...5AN02U20091124  News Corp. Joined by Rivals Weighing Google Block Greg Bensinger and Brian Womack Publishers of the Denver Post and the Dallas Morning News may pull some of their stories from Google Inc.’s news site, a move that would emulate News Corp.’s Rupert Murdoch. News Corp. is considering blocking Google’s search engine from displaying its news articles and is talking to Microsoft Corp. about displaying stories on its Bing site, people familiar with the situation said yesterday. MediaNews Group Inc., the Post’s publisher, will block Google News when it starts charging readers in Pennsylvania and California for online content next year, Chief Executive Officer Dean Singleton said in an interview. Morning News owner A.H. Belo Corp. may introduce online subscription fees and also block Google, Executive Vice President James Moroney said. “The things that go behind pay walls, we will not let Google search to, but the things that are outside the pay wall we probably will, because we want the traffic,” Singleton said. Newspaper publishers, grappling with a collapse in the print-ad market, are considering Web-site charges and are pushing back against Google, which displays headlines and excerpts from stories on its free news site. News Corp., whose Wall Street Journal already charges for online subscriptions, has also said that it plans more paid content. While newspapers have complained about Google using their news to attract users and boost revenue, fewer than 1 percent have opted out of the service, Josh Cohen, head of Google’s news division, said in an interview. Value in Traffic A significant number of publishers would have to block access to their content to produce a notable impact on Google’s search results, said Greg Sterling, principal at consulting and research firm Sterling Market Intelligence in San Francisco. “It’s a tree-in-the-forest kind of thing,” he said. “I don’t think people would notice” if a lone publisher took the action. “There’s value in that traffic and I think publishers recognize that value,” Cohen said. “The reason they’re not opting out is they’re getting something from that relationship.” Google Chief Executive Officer Eric Schmidt said in an interview this month that his company, owner of the most popular Internet search engine, would like to keep news providers on its site. “We do worry about it, and we think it would be a bad outcome” for newspapers to leave Google, Schmidt said. “We would encourage them to stay in our program.” Gabriel Stricker, a Google spokesman, declined to comment yesterday on any talks between News Corp. and Microsoft, as well as the other newspapers potentially opting out of Google News. Paid Models Murdoch, News Corp.’s chairman and CEO, said in an interview on Sky News Australia this month that he may remove the company’s content from Google searches. The company’s newspapers include the Times of London and the New York Post. MediaNews, based in Denver, will block Google News from the content it puts behind a so-called pay wall early next year at newspapers in Chico, California, and York, Pennsylvania, Singleton said. A.H. Belo, based in Dallas, hasn’t decided if it will block Google News and any action isn’t “imminent,” said Moroney, who is also publisher of the Morning News. Blocking Google would be part of a larger strategy, he said. Belo is considering models for charging for some of its Web content and plans to implement a pay wall within six months at either the Morning News, Rhode Island’s Providence Journal or Riverside Press-Enterprise, published in California, Moroney said. That may require Web readers to go directly to the newspaper’s site to read stories, he said. ‘Not Monetized’ “This is traffic that’s not being monetized to any great degree,” Moroney said. “It’s akin to a person who drops into town, buys one copy of your newspaper and leaves town again and yet you spend a whole bunch of time building your business around that type of customer.” Google, based in Mountain View, California, added 74 cents to $583.09 at 4 p.m. New York time in Nasdaq Stock Market trading. Belo jumped 36 cents, or 8.2 percent, to $4.76 on the New York Stock Exchange. MediaNews is closely held. Google News gathers stories from the Web and displays their headlines, photos and the first few lines with links to the full articles on the original publishers’ Web sites. Google has also faced international criticism from media companies over the service. In 2007, Belgian newspapers won a copyright suit blocking Google from linking to their articles on Google News. Fewer than 100 publishers have completely blocked their content from Google News search results, Cohen said. “You can point back to the traffic that we’re sending and the fact that so few of those publishers have opted out as a pretty strong case that there’s value being delivered back to these publishers,” Cohen said. Moroney said more publishers are “focused on attracting the really engaged consumers who come multiple times and stay for lots of minutes every time” rather than the casual online reader who happens upon a news site by chance. U.S. newspaper publishers lost 28 percent of their print and online ad revenue in the third quarter from a year earlier, the Newspaper Association of America reported this month. http://www.bloomberg.com/apps/news?p...d=aRVlZEzbmNu0  BBC: We Won't Charge for Online News Corporation says it has 'no intention' of charging – as Times and Sun owner News Corporation prepares to put up a paywall Michael Lyons The BBC has today said it has "no intention" of charging for online news, in a declaration that is unlikely to please James Murdoch and his father Rupert as they prepare to start charging for News Corporation content on the internet. Sir Michael Lyons, the BBC Trust chairman, said the corporation has "no intention of diluting BBC commitment to universal access to free news online" as he outlined the areas director general Mark Thompson's ongoing strategic review will cover. The BBC's internet news operations came under fire in August at the MediaGuardian Edinburgh International Television Festival from James Murdoch, chairman and chief executive of News Corporation in Europe and Asia, who accused the corporation of "throttling" the market and preventing its competitors from launching or expanding their own services online. News International, the News Corp subsidiary that owns the company's British newspapers, including the Sun and the Times, is planning to start charging for its journalism online. Lyons said today that the BBC Trust "recognises external concerns over scale and growth of BBC online operations". But he added: "Equally, it's an immensely popular service with audiences and an important tool for the economy." Lyons said he wanted Thompson to ask what "licence fee payers really expect to get from their licence fee and what they might be surprised to see the BBC doing in the online world". He indicated that some areas, such as the iPlayer and news online, are safe when he asked: "Beyond the core offer of news, sport, education, children's and the iPlayer, which parts of the online service are essential to the BBC's mission and which could be stopped?" However, Lyons also questioned the future of content created for online that is not directly related to specific BBC programmes, asking, "where should the boundary be drawn" between this and "the online expression or extension of BBC programming"? Lyons also said the BBC Trust has asked Thompson to look at how the corporation should "serve all audiences" with "fresh and new" programmes, not a "diet of the predictable and comfortable", while "nurturing home-grown talent... across the full range of genres". Other questions include "does increased quality and distinctiveness come at a price?" and how can the BBC be "more open", both for "programme-makers and for audiences". Another concern expressed by the trust is that "if it spreads itself too thinly the BBC may lose focus on the core mission to provide fresh, new, high-quality content". The BBC is consulting its rivals about the strategic review, which was announced by Lyons in September, and Thompson is due to deliver his initial thoughts in the new year. John McVay, the Pact chief executive, said: "Rather than making cuts in content, the BBC should look at its own fixed overheads and in-house capacity. Looking to make cuts online and on-air is not the compact the BBC has with the licence fee payer." http://www.guardian.co.uk/media/2009...ge-online-news  Group of Magazine Publishers Is Said to Be Building an Online Newsstand Brian Stelter A consortium of magazine publishers including Time Inc. and Condé Nast are plan to jointly build an online newsstand for publications in multiple digital formats, according to people with knowledge of the plans. The formation of a new company to run the online newsstand — sometimes characterized as an “iTunes for magazines” — may be announced in early December. Time, Condé Nast, Hearst and Meredith all intend to be equity partners in the new company, although the deals have not yet been signed. In the face of slumping print circulations for many magazines, the publishing houses are eager to exert some control over digital readership, said people at the companies, who spoke on condition of anonymity because they were not authorized to talk about the plans. Some newspaper owners have also expressed interest in the joint venture. In other media sectors, rivals have already formed joint ventures for the Web. Several television networks are stakeholders in Hulu, an online television and film Web site. Some music labels are partners in Vevo, a music video site powered by YouTube that will make its debut next month. The new magazine company would, in theory, make it easy to buy print and electronic copies of publications like The New Yorker, Sports Illustrated, Esquire and Better Homes and Gardens from a single Web site. While mostly leaving the hardware to others, the alliance of competing publishers would develop software standards for magazine viewing on iPhones, BlackBerrys, e-book readers and other platforms, people with knowledge of the plans said. Executives have talked about an iTunes model for magazines for months. The New York Observer reported Tuesday that John Squires, the Time Inc. executive, would become the new company’s interim chief executive while the partners looked for a permanent head. In June, Ann Moore, the Time Inc. chairwoman, gave Mr. Squires the responsibility of creating a digital road map for the company. “It’s increasingly clear that finding the right digital business model is crucial for the future of our business,” Ms. Moore said in a memorandum at the time. She added, “We need to develop a strategy for the portable digital world and to refine our views on paid content.” A Time Inc. spokeswoman declined to comment Tuesday. The magazine industry has been generally slow in experimenting with digital products, but they have shown more interest this year in extending the print experience and audience. This month Condé Nast became one of the first publishers to repurpose an entire magazine issue for the iPhone, selling a copy of GQ as an application for $2.99. “We know that the world of digital is far grander than display advertising,” Charles H. Townsend, Condé Nast’s chief executive, said at a demonstration of the application last month. Stephanie Clifford contributed reporting. http://www.nytimes.com/2009/11/25/bu...dia/25mag.html  In Chicago, Ex-Editor Fights Back Richard Pérez-Peña James E. O’Shea spent most of his career at The Chicago Tribune, but he was ousted from the Tribune Company in a highly publicized clash over staff cuts, and these days he’s finding plenty of fault with his old paper. Now, he is competing head-to-head with the Tribune as editor of a new local news venture in Chicago, a small band of people that includes other Tribune alumni and Tribune critics. It has all the elements of an ink-stained grudge match, a journalistic version of Brett Favre leading the Vikings against the Packers, right? “No, I don’t have any interest in any of that,” said Mr. O’Shea, who was the managing editor of The Tribune and later the top editor of a sibling paper, The Los Angeles Times, where he was forced out in early 2008. “I would be doing this even if I had never worked for them, and I saw a need. We’ve got to figure out how to do serious journalism and pay for it, and that’s what’s motivating me.” A few years after they began appearing around the country, Internet-based local news organizations have grown in number, size, financing and credibility. Now, some of those organizations are drawing big-name journalists, including veterans of the established news outlets they are competing with — sometimes even hiring people directly from those organizations. Last month, Jim Brady, formerly the editor in charge of The Washington Post’s Web site, was named to head a local news site in Washington, to begin publishing early next year. The Texas Tribune, a site dedicated to that state’s government and politics, started operations this month with a staff of editors and reporters drawn mostly from leading news sources around the state. But the most striking example so far is the Chicago News Cooperative, created last month, with Mr. O’Shea as editor; James Warren, another former Chicago Tribune managing editor, as a regular columnist; Ann Marie Lipinski, a former top editor of The Tribune, on its advisory board; and five former Tribune reporters so far, including two hired away from the paper. Journalists at the start-ups insist they have no personal animus, much less revenge, though they tend to share a view that their cities are increasingly ill-served by their shrinking newspapers. The papers still have vastly more resources, and say they are not worried by the challengers, most of them nonprofits dependent on wealthy donors and foundation grants. But it spices up the competition when the players know one another well, the established organizations have to worry about newcomers poaching their talent and some of the insurgents are openly critical of their former papers. In Chicago, there are other potential irritants: Mr. Warren and Mr. O’Shea did not leave the company on friendly terms, and starting on Friday, the news cooperative began producing a two-page section twice a week for a Chicago edition of The New York Times, which hopes to win over disaffected readers in the region. “Let’s put it this way, it’s not my paper,” Mr. O’Shea said of The Tribune. “I wish them all the luck in the world, I don’t want to see them get hurt, but it doesn’t have the heft and the seriousness that it had.” That is mild compared with the assessment of Mr. Warren, dismissed from The Tribune last year and now the publisher of The Chicago Reader, a weekly. “In their mind, they’ve made it a more populist, local, utilitarian paper, and I think they’ve made it narrower, more lightweight, fueled by reflexive suspicion of the traditional ideas of serious journalism,” he said. “It’s a different value system. There’s a fabulous staff at The Tribune, but I think they’re just underserved by their leaders.” Even so, “I’ve got no desire to weaken anybody” or exact retribution, he said. “I want as many healthy news outlets as possible.” He and Mr. O’Shea said the idea for the news cooperative came from Peter Osnos, a journalist and author who never worked for The Tribune. Gerould W. Kern, editor of The Tribune, said that in addition to becoming more locally focused, his paper was doing more substantive investigative reporting than ever before. He said he could not address the motives of people in the news cooperative, but that he viewed it as just a competitor and not as a threat. “There’s more competition every day, all the time, from every direction,” he said. “So our view is, we will compete with anyone, any time, any place, and we believe that we will win. I believe in competition.” He added, “I think there’s room for more than one business model,” but in the long run, he has more faith in a for-profit business like The Tribune. At the earliest local news sites, like The New Haven Independent and Voice of San Diego, both started in 2005, even the top editors had worked at smaller organizations, or had been freelancers or had worked in other cities. Many sites still resemble that model. Later, there were major exceptions like MinnPost in Minneapolis-St. Paul and The St. Louis Beacon, both run primarily by journalists who had worked for the big papers in those markets. But in most cases, those people had left the papers years earlier, through voluntary buyouts. “There was never really any tension between us,” said Margaret Wolf-Freivogel, a high-ranking editor at The St. Louis Post-Dispatch who took a buyout in 2005, and has been the editor of The Beacon since it began in early 2008. “We want them to do well, for the city’s sake, and we’re still friends with many people who work there.” Mr. Brady, formerly of The Washington Post, had only positive things to say about his old paper, which he left early this year. He will head a local news venture for Allbritton Communications — the same company that owns Politico, a three-year-old news operation founded by two former Post journalists that has become a force in covering national politics. Mr. Brady said he left The Post voluntarily — “It was all very collegial” — after a reorganization made the paper’s Web site much less independent of its main newsroom. But when he begins hiring, he said, he expects to make offers to some current Post employees. Recently, some local news sites have shown that they can hire people who are still working for the competing major news organizations — a sign that the sites are taken seriously and can pay competitive salaries, and that at least some journalists think they have futures. The Chicago News Cooperative hired David Greising, a business columnist, and Dan Mihalopoulos, a City Hall reporter, from The Tribune, and both men said they would have been unlikely to have made the leap to the Web even two years ago. Both expressed love of the paper and gratitude for the experience it had given them, and also some disappointment at the ways it had changed. “The business trends aren’t friendly, and I understand the need that management felt to change gears and try something different,” Mr. Greising said. “This new work isn’t about trying to get even with anybody. It’s about creating an alternative way to do good journalism.” http://www.nytimes.com/2009/11/23/bu...a/23local.html  Anonymous Gossip Sites Sophia Yan So here's what free speech has come to on campus: "Name the freshman sluts!" an anonymous post demands on the Indiana University page of a multischool gossip site. So-and-so "has herpes!" proclaims an unsigned post on Texas Christian University's page. Among the profundities on the University of Alabama page: "Frats=fags." Horny guys, lowbrow debates and run-of-the-mill spam all seem to be in abundant supply on CollegeACB.com (the acronym stands for Anonymous Confession Board). But what sets this site--and others like it--apart from the coarse commentary found on YouTube or, for that matter, a political blog are the personal attacks against private citizens, often with last names included, that leave victims with little recourse aside from demanding that the anonymous comments be taken down. (See a video of the CollegeACB founder.) What used to be whispered on campuses is now broadcast, in the most cowardly way, for anyone with an Internet connection to see. Beverly Low, dean of first-year students at Colgate University, describes the phenomenon as an "electronic bathroom wall." The posts--which are often suffused with racism, sexism and homophobia--can be so vicious and juvenile that Ben Lieber, dean of students at Amherst College, likens them to "the worst of junior high." And yet even the most élite universities are struggling with the problem of anonymous gossip sites. Some sites are homegrown and deal only with one school. Others are sprawling entities, catering to hundreds of schools and offering features like search capability and, at one enterprising site, the option to vote on how truthful an anonymous post is. The biggest multischool site, JuicyCampus, was receiving thousands of hits a day when it folded in February--after advertisers pulled out. This happened around the time that two state attorneys general began investigating the site for possibly violating consumer-protection laws and its own terms of use. But wannabe sites are eager to replace the once mighty JuicyCampus. So eager, in fact, that the defunct site was paid by ACB to redirect traffic to the upstart gossip hub. It may have worked. ACB logged a record 480,000 hits in one day in early November; a slow day brings half as much traffic, according to owner Peter Frank, a sophomore at Wesleyan University who runs ACB out of his dorm room. The 19-year-old English major defends the site as a "student-controlled discussion space where the communities dictate what's talked about." Though the site does not "call for salacious gossip," he says, on a busy day he receives 40 requests to take down posts and "on a bad day, just a couple." He does not have moderators or police the site. But he follows up on complaints about individual posts. "If it says your name, we'll take it off," he says. Hundreds of individuals and several schools have sent Frank requests to delete comments or even to remove a college from his site. For example, Washington and Lee University asked him in October to delete almost all threads about the school, but Frank refused. "I am not looking out for the school's best interests," he says. "I'm looking out for the students' best interests." So colleges and universities have gone to war by other means. Students at North Carolina Central University urged their peers to boycott gossip sites. At Mount Holyoke College, where a localized gossip site generated a lot of hurt and anger, administrators held workshops to encourage students to talk things out face to face. Millsaps College went so far as to block access to JuicyCampus from its computers. But schools must walk a fine line between protecting free speech and protecting students from one another. Liz Braun, Mount Holyoke's dean of students, says that from an administrative standpoint, it's a "very slippery slope." Even at Wesleyan, administrators have to tread lightly. The school told Frank he could not use its servers for his business, but, says director of media relations David Pesci, "We have other students who are entrepreneurs on campus who have businesses, and quite frankly, as long as they are conducting those businesses within the laws assigned to those areas, there's not much that we can get involved with." So far at least, the law is on Frank's side. Although individuals can sue newspapers and other traditional-media outlets for making false or defamatory statements, the Communications Decency Act of 1996 shields website operators from liability for user-generated content, except for copyrighted materials like movies and music. But that doesn't mean anonymous commenters are home free. This fall, two former Yale law students settled a lawsuit they brought against several people the women claimed had defamed them in anonymous comments on a law students' online discussion board. It took two years of tough litigation, but the women were able to identify some of the posters and obtain a settlement, the terms of which remain confidential. "It's true that the actual authors would potentially be liable for posting libel," Frank says of ACB. "But libel is difficult to prove. I just really don't see it happening, but we'll cross that bridge when we come to it." And what about Frank? "I'm untouchable," he says. http://www.time.com/time/magazine/ar...942971,00.html  Time Warner Cable Asks Help on Rising Program Fees AP Time Warner Cable Inc. is asking the public for help as it tries to curtail increases in the programming fees it has to pay to carry cable channels and broadcast stations on its systems. The nation's second-largest cable TV operator unveiled an advertising campaign Wednesday asking cable subscribers to vote online on whether it should ''roll over'' or ''get tough'' in negotiations over the fees. Time Warner Cable said it would use the results of the survey in upcoming contract renewal talks. Deals expiring this year include those with The Weather Channel; most of News Corp.'s Fox stations and FX cable channel; Sinclair Broadcast Group Inc.'s TV stations; and Scripps Networks Interactive Inc., which owns Food Network and HGTV. It's not clear whether the public response will be any good when past ads accusing programmers of price-gouging haven't stopped fee increases. And the survey is far from scientific, as people will be choosing to participate; legitimate surveys generally choose respondents at random. Cable, satellite TV operators and phone companies that offer TV programming have to pay fees to the owners of cable channels. More recently, broadcast stations have been asking for fees, too. Previously, the owners of these stations had non-cash arrangements, such as an agreement by the cable TV operator to carry a new cable channel owned by the same company as the station. Barry Faber, general counsel of Sinclair, said TV stations charge a ''bargain'' compared with cable channels that don't get the same amount of viewers, such as ESPN, TNT, TBS and USA. Cable operators have ''misallocated the money they spend to acquire programming by paying more for programming that's not as popular,'' he said. David Blumenthal, a spokesman for The Weather Channel, said it has a strong relationship with Time Warner Cable and expects to be ''partners'' for a long time to come. Sinclair owns 58 stations in 35 markets, including San Antonio, Texas, Tampa, Fla., and Las Vegas. News Corp. declined to comment. Scripps did not immediately return calls for comment. Time Warner Cable, which is based in New York, said some outlets have asked for as much as four times what they pay now in programming fees, which can run a few cents per viewer to $4 per subscriber for ESPN. If an agreement isn't reached, the cable operator may have to drop a channel from its lineup, something that happens from time to time in such past disputes. The cable operator said it paid $3 billion in programming fees in the first nine months of the year. http://www.nytimes.com/aponline/2009...able-Fees.html  Smash "Twilight" Sequel Enters Record Books The "Twilight" sequel scored the third-biggest opening weekend of all time at the North American box office on Sunday, as millions of young women swooned over the complex love triangle involving a high school girl, a vampire and a werewolf. "The Twilight Saga: New Moon" earned an estimated $140.7 million during its first three days of release across the United States and Canada, closely held distributor Summit Entertainment said, crushing industry expectations. The record for an opening is $158 million, set last year by the Batman sequel "The Dark Knight." The 2007 movie "Spider-Man 3" follows with $151 million. "New Moon" replaced "Pirates of the Caribbean: Dead Man's Chest" ($136 million) at No. 3. The vampire romance is well on its way to exceeding the $193 million total of its predecessor, "Twilight," which was released exactly a year ago. Summit Entertainment said "New Moon" also set an opening-day record with Friday sales of $72.7 million, surpassing the $67.2 million haul of "The Dark Knight." That tally was bolstered by record-breaking midnight sales of $26.3 million. The old mark was set earlier this year by "Harry Potter and the Half-Blood Prince" with $22.2 million. A Few More Men The closely held studio said "New Moon" also earned $118.1 million from 25 foreign markets. Data from individual countries were not immediately available. Exit-polling data in North America indicated that women accounted for 80 percent of the audience and half the audience was under 21. Summit said male moviegoers increased their share by a couple of percentage points, and the new film also brought in a few more older women. "New Moon" revisits the dangerous romance between high school student Bella Swan (Kristen Stewart) and vampire Edward Cullen (Robert Pattinson). After falling in love with each other in "Twilight," Bella and Edward break up in "New Moon." Bella hooks up with Jacob Black (Taylor Lautner), an American Indian who is also a werewolf. Jacob protects Bella, but she still longs for the gentle blood-sucker Edward. Chris Weitz directed the $50 million project. Reviews were largely scathing, but the franchise is considered critic-proof. Indeed, the stars have become sex symbols whose real-life romances with each other (Stewart and Pattinson) or with country star Taylor Swift (Lautner) have long been gossip-column fodder. Fans lined up outside theaters days before the sequel opened. The "Twilight" film franchise is based on a series of four novels of the same name by Stephenie Meyer, which her publisher says have sold 85 million copies worldwide. A third film, "Eclipse," is due in June. Also new at the box office was the Sandra Bullock family drama "The Blind Side" at a distant No. 2 with $34.5 million, the best opening of her career. The fact-based movie was released by Time Warner Inc's Warner Bros. Pictures on behalf of independent producer Alcon Entertainment. Bullock plays a Tennessee housewife who transforms a homeless black teenager into a high-school football star. The cartoon "Planet 51" opened at No. 4 with a modest $12.6 million, playing almost exclusively to parents and young children. Last weekend's champion, the disaster movie "2012," fell to No. 3 with $26.5 million, taking its 10-day haul to $108.2 million. The picture led the foreign box office for a second weekend with $100.5 million; its foreign tally soared to $341.1 million. Both "Planet 51" and "2012" were released by Columbia Pictures, a unit of Sony Corp. Walt Disney Co's stop-motion adaptation of "A Christmas Carol" fell three places to No. 5 with $12.2 million in its third weekend; its tally stands at $79.8 million. (Editing by Bill Trott and Jackie Frank) http://www.reuters.com/article/enter...5AK14C20091123  Pants on Fire The movie studios have a new Holy Grail, it seems: Federal Communications Commission permission to cable companies to shut down the analog streams on video-on-demand movie programming. As Ars readers know, we've been covering this issue for a while. But the Motion Picture Association of America's latest letter to the FCC pulls out all the stops, rhetoric-wise, calling criticisms of this scheme "complete and utter nonsense that only can be intended to stir up baseless fears among consumers that their equipment will suddenly go dark and be unusable for any purpose." These are "deplorable claims," the MPAA told the FCC on Monday. Plus they "distort the truth." They're also "simply and irrefutably untrue," the trade association adds (in case you didn't get it yet). False untruthfulness The main target of MPAA's outrage is the advocacy group Public Knowledge, one of whose spokespersons, Harold Feld, has an ongoing video series called "Five Minutes With Harold Feld," in which the aforementioned offers his takes on "incredibly boring and wonky things" and tries "to make them slightly less boring, because this stuff is important." The allegedly offensive five-minute video in question deals with what MPAA wants, which is technically called "Selectable Output Control"—shutting down the analog stream to HDTVs and other devices because it is less secure (copyable) than digital streams, which can be scrambled. The FCC currently prohibits the practice. The studios say they want to plug the "analog hole" with SOC because it will allow them to offer the public pre-DVD VoD movie releases with less threat of piracy. The problem, as Feld's video on this subject points out, is that a considerable amount of analog only connected equipment won't be able to receive these offerings. "And for this," Feld skeptically declares, "we're going to break 25 million television sets, and break your TiVO, and break your Slingbox, and make sure you can't use it on VoD anymore, because [Feld looking especially skeptical here] it's so important to get these movies to video-on-demand earlier." Feld's "deplorable claims" are "absolutely, 100 percent untrue," MPAA counters. "The use of SOC would have no impact whatsoever on the ability of existing television sets, Tivos, Slingboxes or any other consumer product to work in exactly the same fashion that such devices work today. While products with only unprotected outputs and inputs would not be able to receive the new early window offerings that would be made possible by the SOC waiver, no device would be broken. Nor would any consumer be unable to receive traditional VOD in the same way that he or she does today." A considerable amount of time in this debate is being spent rather theatrically denouncing words that clearly function as metaphors. As we've pointed out, although SOC won't render analog-only HDTVs and other home theater equipment "broken," as in "physically damaged with wires poking out of the set," it will disable the ability of this gear to access what will immediately become the most valuable offering on television: pre-DVD release VoD movies. What's the problem anyway? The rest of MPAA's filing is a long list of ways that movies are copied and illegally distributed on the Internet—further proof positive that the studios need SOC. Among other claims, the filing insists that real time duplication of HBO per-per-view events on various websites represents clear evidence that "thieves steal this content through unprotected outputs." From this litany, a disinterested reader might conclude that Hollywood's efforts to stop this activity have been amazingly unsuccessful, and the producers might want to reconsider their approach to the problem. MPAA, for example, decries the fact that "literally every DVD that MPAA member studios released for rental or purchase during the past year has been made available for unlawful downloading or streaming online." If that is the case, why does the MPAA extol the virtues of its DVD Content Scramble System (CSS) before the United States Copyright Office? CSS and other "protection technologies" have allowed content producers to "distribute their valuable content in higher quality, more convenient digital formats," MPAA wrote in the office's latest proceeding on exemptions to the Digital Millennium Copyright Act. As a result, "DVDs have become one of the most widely adopted consumer electronics products in history, and the pace of adoption has been unprecedented. Consumers have greater access to movies and TV shows than ever before." It doesn't seem to matter. In Hollywood-think on this issue, the solution to each apparent technology/regulation failure is a new tech fix that requires new rules and a new explanation of why it won't hurt consumers. TV watchers, MPAA notes, are already used to not seeing stuff on their cable boxes. So what's the problem? "A typical subscriber today already encounters numerous instances where a particular channel or service is not available. For example, a given consumer might not subscribe to a cable company’s high-definition service or might not receive premium channels (such as HBO). In either case, if consumers were to attempt to access one of these channels, they would receive an on-screen message advising them that their service does not include access to the requested content." MPAA goes so far as to suggest that if SOC isn't granted, individual movie studios will begin releasing pre-DVD content on non-cable distribution alternatives—such as SONY's experiments with encrypted Internet streams sent directly to its Bravia HDTVs (Hancock already streams and Cloudy With a Chance of Meatballs is coming next). Thus, the trade group warns, "it is denial of the waiver that could result in a scenario in which millions of consumers would have to buy new equipment to receive new content offerings." That is, of course, assuming that consumers would bother to do so, given the enormous amount of content they can already get over the 'Net. Not-so-subtle Needless to say, Public Knowledge is taking strong exception to statements that pretty much call the group a pack of liars. MPAA's latest commentary "utterly fails to demonstrate that anybody steals content through the analog hole," PK's Gigi Sohn declared in a commentary published this morning. And "by attacking Public Knowledge and specifically Harold's integrity, it is a not-so-subtle effort to spin the debate over this waiver as 'copyleft' Public Knowledge versus 'reasonable' Hollywood, which only wants this itsy bitsy waiver so that it can provide the 'pro-consumer' benefit of making movies available on video on demand a few weeks earlier than they are now." Sohn notes that a wide variety of organizations besides PK oppose SOC, including the Consumer Electronics Association and the Independent Film and Television Alliance. No one knows how much their concerns count with the new FCC, which has yet to take a stand on this controversial issue. http://arstechnica.com/tech-policy/n...-are-lying.ars  Toshiba Employee Arrested in Japan for Selling Digital TV Copying Software Joshua Williams A Toshiba employee in western Japan has been arrested by police for selling software that allows users to copy digital TV content indefinitely. This is the first disclosed case in Japan of an arrest for software that breaks copy limits on such content, the Japanese media has reported. Tetsuya Masumura was arrested on November 25th in Ehime prefecture on charges of copyright violations for selling software that would override the “Dubbing10” digital content management system, allowing for users to make unlimited copies of recorded programming, according to the Yomiuri. Dubbing10 is programming used in a number of recent recording and playback devices in Japan that essentially allows for digital programs to be copied a limited number of times in devices for personal use. It was introduced in July of 2008 to settle complaints that the prior system, which only allowed a single copy, was too restrictive. Police told the media that Masumura was selling copies of the restriction-removal software online as downloads or CDs that he would mail out. Police said sales came with instructions to allow for easy use for even beginners. Masumura is accused in two specific instances, one where he sold a CD-R to a man for 850 yen (~$8USD) and another where he sold a download to a teenager for 650 yen (~$6USD). In the second case the teenager reportedly then resold the software approximately 240 times, earning about 145,000 yen (~$1640 USD), the Mainichi reported. It is believed that over a period of a year, Masumura sold the software to at least 714 people, potentially generating hundreds of thousands of yen in earnings. He reportedly admitted to police that he did it for “extra pocket cash.” However, he also said “I didn’t make the software myself,” according to a report from 47news.jp. Masumura is said to have worked for the large electronics manufacturer Toshiba for over 15 years. In a public statement on the 25th, Toshiba said the issue is “truly regrettable” and that they intend to make a “stringent response” based on police investigation. http://www.examiner.com/x-16352-Japa...ying-software#  Popular Author’s Audiobook Tries a New Format: Vinyl Andrew Adam Newman 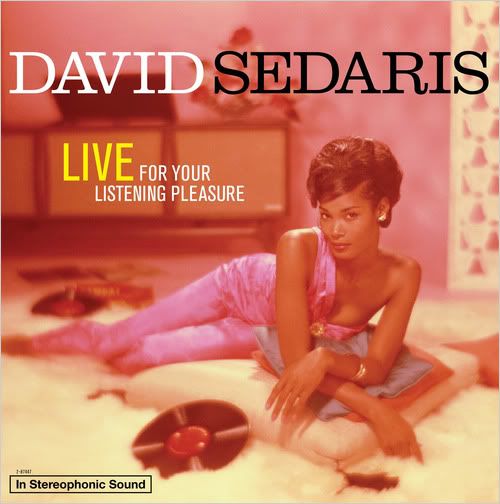 As physical formats and devices have shrunk, revenues for the audiobook industry have grown, since it is more convenient to listen to an iPod while exercising and commuting than fiddling with CDs. Digital downloads grew to 21 percent of the industry’s total sales in 2008, from 6 percent in 2004, according to the Audiobook Publishers Association. It is all the more odd, then, that Hachette Audio recently announced that the latest audiobook by David Sedaris, “Live for Your Listening Pleasure,” which features readings before audiences, would be available on the least portable of formats: vinyl. Reminiscent of Blue Note albums from the 1950s and 1960s, the cover features a photograph of a woman sprawled on a white shag rug with a come-hither look, albums strewn about. Albums are enjoying something of a renaissance, posting $57 million in sales in 2008, more than double the previous year and the best for the format since 1990, according to the Recording Industry Association of America. The format is so rare for audiobooks, however, that the Audiobook Publishers Association has never even tracked its sales. But Maja Thomas, senior vice president for digital and audio publishing at the Hachette Book Group, said she was drawn to the idea precisely because it was quirky. Mr. Sedaris’s “audience is very attuned to irony and is going to find this funny,” Ms. Thomas said. The 31-minute album, which will be released on Jan. 5 and cost $24.98, will include only two of the five essays on the CD version of the audiobook, but will feature a code enabling purchasers to digitally download the entire program. Hachette was less kind to another past-its-prime format in 2008. Upon releasing “Sail,” a novel by James Patterson and Howard Roughan, in a cassette version, it declared it would no longer release in the format and held a mock funeral for cassettes in its Manhattan office. “We had a funeral for one format, but you can think of this as the ultimate zombie,” Ms. Thomas said. “The record is coming back from the dead.” http://www.nytimes.com/2009/11/23/bu...a/23vinyl.html  A Translator Tool With a Human Touch Noam Cohen HOW hard can it be, as the joke goes, to speak Chinese? (Six-year-olds do it all the time.) Yes, it turns out that learning languages is one of those skills that humans, even relatively young ones, master seemingly magically. It is all enough to make a mainframe computer jealous. At I.B.M., a team of nearly 100, including mathematicians and software developers, is working on a project to create an automatic translation tool, so-called machine translation, that has the speed and accuracy to be used in instant-messaging between speakers of two different languages. The project, called n.Fluent, is intended to teach the computer terminology that is specific to I.B.M.’s businesses, and, more significantly, allow the computer to learn what it has been doing wrong. To that end, the company is extracting and organizing contributions from I.B.M.’s 400,000-member work force spread across more than 170 countries, adding a human touch to the project. Over a two-week period last month, the company issued a “worldwide translation challenge” to its employees, using a points-based system to award the biggest contributors prizes that were converted to charitable donations. About 6,000 I.B.M. employees made improvements in 11 languages to more than two million words of text translated by n.Fluent. So, when a machine translation from French produces, “MTTP is the time of 30 minutes and it is steadily declining since January 2006,” a human correction comes up with this improved English version: “The MTTP delay is 30 minutes and it has been steadily declining since January 2006.” “From this parallel data, we update the models,” said Salim Roukos, an I.B.M. researcher in language-related technology at its T.J. Watson Laboratory in Yorktown Heights, N.Y., home of the n.Fluent project. “You want to learn the idiomatic expressions — when you say someone has kicked the bucket, you don’t want that translated word for word.” • So far, n.Fluent is used only by I.B.M. employees, but the intention is to create a product that can be sold to other businesses. Efforts like this at I.B.M., as well as social networking tools behind the company’s firewalls, amount to a new twist on “crowdsourcing,” the term I.B.M. officials use to describe them. In addition to the n.Fluent project, I.B.M. has its own companywide version of Wikipedia (Bluepedia), with contributions from 1,300 employees. Perhaps the most innovative social networking experiment at I.B.M., according to Irene Greif of the I.B.M. Center for Social Software in Cambridge, Mass., is Dogear, a tool similar to Delicious that allows employees to share links and tagging on the Internet as well as on the I.B.M.-only intranet. The project itself was a bit of an experiment, and I.B.M. developers tweaked further, she said. This led to Dogear, a system of tags and descriptions contributed by 10 percent of users. It has become more popular than I.B.M.’s own internal search engine. “A small crowd, a self-selected crowd can often be useful,” Ms. Greif said. This highlights the differences between what is occurring at I.B.M. and other large companies and what traditionally constitutes crowdsourcing. I.B.M. employees are not just any “crowd”; they have expertise and a loyalty to their employer that any old posse wrangled up on the Internet may not. In fact, crowdsourcing may be the wrong way of thinking of such internal corporate projects. Employee-sourcing? Maybe that catch-all term “collaboration” is the best way to think of what social networking technology can bring to the workplace. After all, collaboration is an old goal for employees and employers. In the case of the n.Fluent project, programmers are not trying to have a computer master the “rules” of a language, but rather are looking for statistical patterns between two sets of translated texts and among the words themselves. For example, Mr. Roukos said, the text of a Canadian parliamentary debate in French and English can help programmers to “build statistical models based on the parallel corpus.” • It is language’s fluidity and unpredictability that thus far make translation resist simple computer-based solutions. Which means that for the foreseeable future, translation experts will also need to become experts on collaboration. “One of the reasons we’ve got senior-level executives behind this is that it is kind of a Harvard Business School case study of how the crowds inside the company help you develop a better product,” said David Lubensky, another researcher on the n.Fluent project. “We should be able to replicate this over various domains.” For example, initially, all rewards to contributors were in the form of donations to one of seven worldwide charities. Over time, the team heard that some contributors “would personally want some trinket,” he said. And now small gifts are awarded as well. Something any 6-year-old could have told you. http://www.nytimes.com/2009/11/23/te...gy/23link.html  Opera Accused of Censorship, Betrayal by Chinese Users Opera Mini browser stumbles in China Steven Millward Opera, the maker of Web browsers such as the popular "Opera Mini" for Java-based mobile phones, has been accused of betraying its users in China, by apparently caving in to top-level demands to stop allowing China-based users to use the international version of the Opera Mini browser. This stems from a unique feature of Opera Mini, where the traffic is sent via Opera's own servers, for the speed and convenience of its users, most of whom use the slowest GPRS mobile connection. But in China, the pleasant side effect of that rerouting has been that Opera Mini is effectively allowing users in China to easily circumvent the so-called Great Firewall of government-implemented Web filtering. Thus, Chinese users, up until yesterday, were merrily logging into Facebook--which has been blocked here pretty much all year--on their mobile phones using Opera Mini. Not any more. Of course, the Norwegian software company is not the one who enforces the nationwide censorship of hundreds of Web sites--it's yet another company which has had to comply with local laws and idiosyncrasies, however uncomfortable it feels about this--but now Opera has become somewhat complicit in it. Anyone now trying to access any Web site at all on the Opera Mini browser (versions 4 or 5 Beta), when inside China, gets the "friendly" notice, in Chinese and English: "For better browsing experience, please upgrade to Opera Mini China version on mini.opera.com." That message, however, is clearly a lie, as the Chinese version of the browser no longer reroutes traffic via Opera's 100 proxy servers worldwide. So, it'll be slower than before. Instead, the newly enforced Chinese-language version uses only locally based servers, and hundreds of Web sites are now inaccessible with it. That's hardly a "better browsing experience". So, Opera's users in China are now being held at software update gunpoint, and must use the Chinese-language version of their browser. According to a recent Opera press release, China is number 4 on its list of the most Opera Mini users worldwide. So that's a large number of angry customers today who are being forced to "upgrade" to an inferior version of the browser, and many Chinese users are feeling betrayed, as if they're second-class users. PR nightmare for Opera On Twitter today and yesterday--yes, there are clever ways of getting on Twitter in China, without a VPN--many of the tweets using the "gfw" (Great Firewall) hashtag were talking about Opera Mini, why the international version was no longer working, and some were even venting anger at Opera for seemingly kowtowing to an oppressive law. Here are a selection of the tweets: @stinson--"Got hit by Opera's forced upgrade too. Disgraceful if Opera chose to cooperate with censorship." @stinson--"Just noticed the URL for the Opera Mini redirect: "/error/blocked_country/china.html" @ullrich--"How Opera betrays it's Chinese users http://ow.ly/EcsW" @roadtom--[Translation] "...national web-filtering has been built by Cisco and is now being helped by Opera" @toadloading--[Translation] "Opera has also been hit by The Wall..." The grim reality... In practice, Opera likely had little choice but to comply with local laws, and make a new version for Chinese users that cannot access all the "filtered" sites, same as any other Web browser. Google, Yahoo, and Microsoft (with Bing, especially) have all likewise faced compromises when doing business in China, and have suitably modified and "harmonized" their search results in the Chinese versions of their search engines. I contacted Opera's director of Communications at its Oslo HQ just over 24 hours ago, via email, but have had no response (though it is the weekend). The only dialog with a member of the Opera team has been via Twitter, where one of Opera's "Desktop QA" people spoke out. Though, by that individual's admission, he does not work on the Mini browser, and is not familiar with the situation. Nonetheless, @opvard defended Opera's enormously difficult situation: "Regarding Opera and the #gfw of China I'd guess that [the] only alternative to this would be no Opera Mini at all for China... What do u suggest that Opera does about China? Ignore [the] government & be completely blocked instead?" Between a rock and a hard place, indeed. The Opera staffer, @opvard, did later concede that more communication with users would've been nicer, and speculated that Opera may not be able to reveal how exactly it got its arm twisted so that it complied. On a final note, the Chinese-language version of Opera Mini 4, and 5, works fine in China, minus the blocked sites; but life goes on, and Opera can be relieved if it doesn't lose any Chinese users over this confusion. But a weird spinoff is that if you're a foreigner in China, your non-Chinese language version of Opera Mini will not work. To quote Homer Simpson: "D'oh!" http://asia.cnet.com/blogs/sinobytes...tm?id=63015016  Obama Wants Computer Privacy Ruling Overturned David Kravets The Obama administration is seeking to reverse a federal appeals court decision that dramatically narrows the government’s search-and-seizure powers in the digital age. Solicitor General Elena Kagan and Justice Department officials are asking the 9th U.S. Circuit Court of Appeals to reconsider its August ruling that federal prosecutors went too far when seizing 104 professional baseball players’ drug results when they had a warrant for just 10. The 9th U.S. Circuit Court of Appeals’ 9-2 decision offered Miranda-style guidelines to prosecutors and judges on how to protect Fourth Amendment privacy rights while conducting computer searches. Kagan, appointed solicitor general by President Barack Obama, joined several U.S. attorneys in telling the San Francisco-based court Monday that the guidelines are complicating federal prosecutions in the West. The circuit, the nation’s largest, covers nine states: Alaska, Arizona, California, Hawaii, Idaho, Montana, Nevada, Oregon and Washington. “In some districts, computer searches have ground to a complete halt,” the authorities wrote. “Many United States Attorney’s Offices have been chilled from seeking any new warrants to search computers.” The government is asking the court to review the case with all of its 27 judges, which it has never done. If the court agrees to a rehearing, a new decision is not expected for years, and the August decision would be set aside pending a new ruling. Either way, the U.S. Supreme Court has the final say. The controversial decision, which the government said was contrary to Supreme Court precedent, outlined new rules on how the government may search computers. Ideally, when searching a computer’s hard drive, the government should cull the specific data described in the search warrant, rather than copy the entire drive, the court said. When that is not possible, the authorities must use an independent third party under the court’s supervision, whose job it would be to comb through the files for the specific information, and provide it, and nothing else, to the government, according to the ruling. The government said the decision was already chilling at least one rape case in Washington State. “Federal agents received information from their counterparts in San Diego that two individuals had filmed themselves raping a 4-year-old girl and traded the images via the internet,” the government wrote. “The agents did not obtain a warrant to search the suspects’ computers, however, because of concerns that any evidence discovered about other potential victims could not be disclosed by the filter team. The agents therefore referred the case to state authorities.” The circuit’s ruling came in a case that dates to 2004, when federal prosecutors probing a Northern California steroid ring obtained warrants to seize the results of urine samples of 10 pro baseball players at a Long Beach, California drug-testing facility. The players had been tested as part of a voluntary drug-deterrence program implemented by Major League Baseball. Federal agents serving the search warrant on the Comprehensive Drug Testing lab wound up making a copy of a directory containing a Microsoft Excel spreadsheet with results of every player that was tested in the program. Then, back in the office, they scrolled freely through the spreadsheet, ultimately noting the names of all 104 players who tested positive. The government argued that the information was lawfully found in “plain sight,” just like marijuana being discovered on a dining room table during a court-authorized weapons search of a home. But the court noted that the agents actively scrolled to the right side of the spreadsheet to peek at all the players test results, when they could easily have selected, copied and pasted only the rows listing the players named in the search warrant. Four players whose names were seized, and who were not linked to the BALCO investigation, have been leaked to The New York Times. They are Alex Rodriguez, David Ortiz, Manny Ramirez and Sammie Sosa. Two dissenting judges wrote that the majority was also sidestepping its own precedent in which the circuit court had denied the suppression of child pornography evidence found on a computer during a search for the production of false identification cards pursuant to a valid warrant. In 2006, the 9th Circuit originally sided with the government in a 2-1 decision, which the court overturned with an 11-judge “en banc” panel in August. http://www.wired.com/threatlevel/200...ng-overturned/  Right and Left Join to Take On U.S. Over Criminal Justice Adam Liptak In the next several months, the Supreme Court will decide at least a half-dozen cases about the rights of people accused of crimes involving drugs, sex and corruption. Civil liberties groups and associations of defense lawyers have lined up on the side of the accused. But so have conservative, libertarian and business groups. Their briefs and public statements are signs of an emerging consensus on the right that the criminal justice system is an aspect of big government that must be contained. The development represents a sharp break with tough-on-crime policies associated with the Republican Party since the Nixon administration. “It’s a remarkable phenomenon,” said Norman L. Reimer, executive director of the National Association of Criminal Defense Lawyers. “The left and the right have bent to the point where they are now in agreement on many issues. In the area of criminal justice, the whole idea of less government, less intrusion, less regulation has taken hold.” Edwin Meese III, who was known as a fervent supporter of law and order as attorney general in the Reagan administration, now spends much of his time criticizing what he calls the astounding number and vagueness of federal criminal laws. Mr. Meese once referred to the American Civil Liberties Union as part of the “criminals’ lobby.” These days, he said, “in terms of working with the A.C.L.U., if they want to join us, we’re happy to have them.” Dick Thornburgh, who succeeded Mr. Meese as attorney general under President Ronald Reagan and stayed on under President George Bush, echoed that sentiment in Congressional testimony in July. “The problem of overcriminalization is truly one of those issues upon which a wide variety of constituencies can agree,” Mr. Thornburgh said. “Witness the broad and strong support from such varied groups as the Heritage Foundation, the Washington Legal Foundation, the National Association of Criminal Defense Lawyers, the A.B.A., the Cato Institute, the Federalist Society and the A.C.L.U.” In an interview at the Heritage Foundation, a conservative research group where he is a fellow, Mr. Meese said the “liberal ideas of extending the power of the state” were to blame for an out-of-control criminal justice system. “Our tradition has always been,” he said, “to construe criminal laws narrowly to protect people from the power of the state.” There are, the foundation says, more than 4,400 criminal offenses in the federal code, many of them lacking a requirement that prosecutors prove traditional kinds of criminal intent. “It’s a violation of federal law to give a false weather report,” Mr. Meese said. “People get put in jail for importing lobsters.” Such so-called overcriminalization is at the heart of the conservative critique of crime policy. The U.S. Chamber of Commerce made the point in a recent friend-of-the-court brief about a federal law often used to prosecute corporate executives and politicians. The law, which makes it a crime for officials to defraud their employers of “honest services,” is, the brief said, both “unintelligible” and “used to target a staggeringly broad swath of behavior.” The Supreme Court will hear three cases concerning the honest-services law this term, indicating an exceptional interest in the topic. Harvey A. Silverglate, a left-wing civil liberties lawyer in Boston, says he has been surprised and delighted by the reception that his new book, “Three Felonies a Day: How the Feds Target the Innocent,” has gotten in conservative circles. (A Heritage Foundation official offered this reporter a copy.) The book argues that federal criminal law is so comprehensive and vague that all Americans violate it every day, meaning prosecutors can indict anyone at all. “Libertarians and the civil liberties left have always had some common ground on these issues,” said Radley Balko, a senior editor at Reason, a libertarian magazine. “The more vocal presence of conservatives on overcriminalization issues is really what’s new.” Several strands of conservatism have merged in objecting to aspects of the criminal justice system. Some conservatives are suspicious of all government power, while others insist that the federal government has been intruding into matters the Constitution reserves to the states. In January, for instance, the Supreme Court will hear arguments in United States v. Comstock, about whether Congress has the constitutional power to authorize the continued confinement of people convicted of sex crimes after they have completed their criminal sentences. Then there are conservatives who worry about government seizure of private property said to have been used to facilitate crimes, an issue raised in Alvarez v. Smith, which was argued in October. “A joint on a yacht, and the whole thing is forfeited,” said Paul Cassell, a law professor at the University of Utah and a former federal judge appointed by President George W. Bush. Some religious groups object to prison policies that appear to ignore the possibility of rehabilitation and redemption, and fiscal conservatives are concerned about the cost of maintaining the world’s largest prison population. “Conservatives now recognize the economic consequences of a criminal justice leviathan,” said Erik Luna, a law professor at Washington and Lee University. The roots of the conservative re-examination of crime policy might also be found in the jurisprudence of Justices Antonin Scalia and Clarence Thomas. The two justices, joined by liberal colleagues, have said the original meaning of the Constitution required them to rule against the government in, among other areas, the rights of criminal defendants to confront witnesses. “Scalia and Thomas are vanguards of an understanding by the modern right that its distrust of government extends all the way to the criminal justice system,” said Douglas A. Berman, a law professor at Ohio State University. The court will hear another confrontation clause case, Briscoe v. Virginia, in January. It is a sequel to a decision in June that prosecutors may not use crime lab reports without live testimony from the analysts who prepared them. The conservative re-evaluation of crime policy is not universal, of course. Two notable exceptions to the trend, said Timothy Lynch, director of the Cato Institute’s criminal justice project, are Chief Justice John G. Roberts Jr. and Justice Samuel A. Alito Jr. “Roberts and Alito are coming down consistently on the side of the government in these criminal justice cases,” Mr. Lynch said. Some scholars are skeptical about conservatives’ timing and motives, noting that their voices are rising during a Democratic administration and amid demands for accountability for the economic crisis. “The Justice Department now acts as a kind of counterweight to corporate power,” said Frank O. Bowman, a law professor at the University of Missouri. “On the other side is an alliance between two strands of conservative thinking, the libertarian point of view and the corporate wing of the Republican Party.” Mr. Meese acknowledged that the current climate was not the ideal one for his point of view. “We picked by accident a time,” he said, “when it was not a very popular topic in light of corporate frauds.” http://www.nytimes.com/2009/11/24/us/24crime.html  Volunteers Log Off as Wikipedia Ages Wikipedia.org is the fifth-most-popular Web site in the world, with roughly 325 million monthly visitors. But unprecedented numbers of the millions of online volunteers who write, edit and police it are quitting. That could have significant implications for the brand of democratization that Wikipedia helped to unleash over the Internet -- the empowerment of the amateur. Volunteers have been departing the project that bills itself as "the free encyclopedia that anyone can edit" faster than new ones have been joining, and the net losses have accelerated over the past year. http://online.wsj.com/article/SB125893981183759969.html  Mobile Web Surge Continues in October: Opera Tarmo Virki Global mobile data traffic continued to surge in October, growing at the fastest pace in seven months, Internet browser company Opera Software said on Wednesday. Data traffic through Opera's mobile browser -- which packages up to 90 percent of the data to save network bandwidth -- rose 16 percent in October from September, the company said. Tech-savvy consumers have used cellphones to access Internet on the go for long, but the mobile Internet market has really boomed since 2007 introduction of Apple's iPhone. "When things really started to get off was when Steve Jobs stood up and said: Now you can get Internet in your pocket," said Opera's chief financial officer, Erik Harrell. "The iPhone has opened the eyes of operators for revenue potential of Web browsers and I think Google has done the same." Wireless operators are eager to increase revenue from Internet browsing and the social networking boom as revenue from traditional voice calls is declining, but they are facing increasingly congested networks. This is helping browsers like Opera, which use proxy servers to package data and send only a small amount through wireless networks. "There is a rapidly growing trend on the market toward proxy-based browsers," Randy Cavaiani, vice president for marketing and business development at browser firm Novarra, said in a recent interview. "If a handset maker is looking to acquire technology, they would look at strength of the server," he said. Nokia and other top phone makers have increasingly focused on developing their own browsers, but most players in the industry are certain Blackberry-maker RIM's August deal to buy browser firm Torch will not be the last one. "Opera's future will depend on key technology players assessing their options and deciding on a make or buy strategy." Opera has 39.6 million users of its Opera Mini browser who all access the Internet through Opera's servers -- giving the company usage data -- and who generated 263 million megabytes of data traffic for operators worldwide last month. Opera continues to lead the global mobile browsing market, controlling 26.4 percent of the market in November so far, according to Web analytics firm StatCounter. The iPhone browser and Nokia browser follow with 22.1 percent and 19.7 percent of the market. Opera's browser is used extensively in emerging countries, with its market share above 50 percent in countries like Russia, Indonesia, India and Ukraine. (Editing by Steve Orlofsky) http://www.reuters.com/article/techn...5AO0KM20091125  A New Approach To Wi-Fi In Flight Small firm develops cost-effective system W.J. Hennigan Billions of dollars and scores of top engineers with the world's largest aerospace company couldn't get it to fly. But a 25-employee company in Los Angeles may have found a way to make in-flight Internet take off. Row 44 is outfitting U.S. airlines with inexpensive devices that allow passengers to access the Internet while flying. Earlier this year, Southwest Airlines Co. and Alaska Airlines began offering Row 44's service. It isn't the first time wireless Internet has been offered on an airline. In 2000, Boeing Co. launched an Internet system called Connexion for large airliners. But after sinking more than $1 billion into development, few passengers were willing to pay the $30 connection fee. Several international carriers were offering the service on a handful of long-haul flights, but Boeing pulled the plug in late 2006, saying the business wasn't financially viable. So why does Row 44 think it can succeed when an aerospace giant, with significantly deeper pockets, fell short? For one thing, Row 44 didn't have to build a multibillion-dollar satellite system. It's piggybacking on an existing network. Also, the size of the company has allowed it to quickly adopt the latest technological advancements that have made equipment lighter and cheaper. And because many people carry Internet-ready devices, demand is higher than ever, said Tim Farrar, president of consulting and research firm Telecom Media and Finance Associates. Row 44 is named after the last row on a DC-10 commercial jet, considered the most uncomfortable part of the plane because the seats are in front of the bathroom and don't recline. Row 44's in-flight Internet could make flying more enjoyable — even for the unlucky folks in the last row. The company got off the ground in 2004 when co-founder Gregg Fialcowitz, also the president, was launching CopperVision, a satellite TV provider. Through the endeavor, he formed a relationship with Hughes Network Systems LLC, which operates a network of telecommunications satellites. As Fialcowitz became more familiar with the technology, he was struck with the idea that Hughes' satellite technology could apply to airliners — one of the few places at the time that did not have Wi-Fi capability. He shared the idea with his friend, John Guidon, a British technology entrepreneur with a private pilot's license. The pair approached Hughes about using its satellite network for in-flight Internet. Hughes liked the idea. Row 44 "opens up a worldwide opportunity for Hughes to supply our advanced broadband satellite technology and services," said Arunas Slekys, Hughes' vice president of corporate marketing. But Fialcowitz had to convince airlines and investors that Row 44 isn't Boeing's Connexion. Row 44's equipment weighs about 150 pounds; the Connexion equipment weighed about 1,000 pounds, adding to airlines' operating costs. The total cost of equipping a plane with Connexion ran close to $1 million. Row 44 costs about $200,000. http://www.courant.com/business/hc-i...0,406309.story  Meet a Real Pirate Radio DJ from the '60s: Rick Crandall of St. Petersburg Steve Persall Half a lifetime ago, Rick Crandall was a rock 'n' roll radio pirate. Today, the St. Petersburg resident is an Internet radio pioneer. For four months in 1966, Crandall spun records on a rusty freighter in the North Sea, beaming a beat to Great Britain that was banned by the BBC. Crandall lived the renegade life portrayed — not always accurately, he says — in the movie Pirate Radio. Crandall was the first American DJ hired by Swinging Radio England, transmitting 50,000 watts of music by the Rolling Stones, the Kinks and other rising acts under the radio name "Rick Randall." "The sex, drugs and silly stuff they did, that's nothing I remember," Crandall, 67, said recently. "Maybe it was going on and I just missed it. Maybe it was (happening) on other pirate radio ships. "And it never seemed like (the actors) were actually on a ship bobbing in the water. We would play records and that (phonograph) needle would fly off the record when we hit some of those swells. Then it would come right back down again, usually in the groove." These days, Crandall still skirts radio conventions as creator of Music Tampa Bay (www.musictampabay.com), a Web site begun in 2005 to showcase local musical talent. The library consists of nearly 1,000 songs by diverse acts including Mojo Gurus, Maggie Council and Geri X. As a former DJ for several Tampa Bay stations — including 1970s rocker WLCY-AM — Crandall understands the need for Music Tampa Bay. "Local artists always wanted to get their music played on (WLCY)," he said. "We always kind of laughed them off. "After a while, I started thinking there's something fundamentally wrong with that. Broadcasting is supposed to operate in the public interest, to serve the local community. Yet we never play local artists on the air. I had this uneasiness until it dawned on me to put on an Internet radio station where nobody can tell me what to do." Like the musicians Crandall spotlights, Music Tampa Bay struggles to be heard. "I don't have a large audience yet — probably no more than 20 or 30 (listeners) at any given time," he said. "But it's certainly making ripples. Finally, there's a way for this music to be heard. That's all (the musicians) really want." All that British teenagers wanted in the 1960s was to hear the Beatles, the Who and other pop stars that the state-owned BBC network wouldn't play. Pirate radio ships such as Swinging Radio England's vessel offered the only chances while politicians considered them dangerous to the status quo. "We weren't technically illegal; we just weren't legal," Crandall said. As the movie depicts, British officials scrambled for ways to shut down pirate radio ships. In retaliation, Swinging Radio England changed its ship's name from the Olga Patricia to Laissez-Faire to send Parliament a message: Leave us alone. "Anything to get us run out of the water, which eventually they did," Crandall said. By then, homesickness had led Crandall back to St. Petersburg, where he had graduated from Dixie Hollins High School in 1960 before entering the Air Force. A string of U.S. radio and television gigs followed until his 2008 retirement. Memories of rocking the high seas never faded, nor Crandall's pride in being part of rock 'n' roll history that Pirate Radio recalls. "If the pirates hadn't come along in England," he said, "we'd have never heard the Beatles in this country, or the Stones, the Who, or any of the big acts that came over here. I just never imagined all of this would come back at this point in my life." http://www.fmqb.com/goout.asp?u=http...he-60s/1053902  Mininova Limits its Activities to Content Distribution Service Published on November 26, 2009 in Mininova-related news. Hi all, Today is an important day in the history of Mininova. From now on, we are limiting Mininova.org to our Content Distribution service. By doing so, we comply with the ruling of the Court of Utrecht of last August. Unfortunately the court ruling leaves us no other option than to take our platform offline, except for the Content Distribution service. According to the verdict (Dutch link) we have to prevent uploads of torrents to Mininova that refer to certain titles or to similar-looking titles. We’ve been testing some filtering systems the last couple of months, but we found that it’s neither technically nor operationally possible to implement a 100% working filter system. Therefore, we decided that the only option is to limit Mininova to Content Distribution torrents from now on. We are still considering an appeal at this moment. We launched our Content Distribution service in 2007. This service allows producers and artists to easily publish and distribute their content for free through Mininova. The launch of Content Distribution has proven to be a success. Countless content owners have used Content Distribution to distribute their content (e.g. albums and documentaries) for free to millions of users. For example, the Dutch band Silence is Sexy released their complete album on Mininova and received the Interactive Award 2009 for doing so. The Dutch television broadcaster VPRO decided to start using Content Distribution in 2009 in order to distribute documentaries. We would like to thank you for your support. Especially everyone that contributed to Mininova receives a big “thank you!” for the effort! We hope to keep welcoming you on Mininova and our other projects (e.g. Snotr, Dispostable). Thanks! The Mininova staff http://mnstat.com/images/blog/index.html  10 Alternatives To Mininova TorrentWatcher After nearly five years of loyal service, Mininova disabled access to over a million torrent files when it partly shut down its website. Starting today, only approved publishers are able to upload files to the site, but luckily there are plenty of alternatives and potential replacements BitTorrent users can flock to. With an impressive 175,820,430 visits and close to a billion page views in the last 30 days, Mininova set a record that they will be unable to break in the near future. Last August a Dutch court ruled that Mininova had to remove all links to ‘infringing’ torrent files, with disastrous consequences. Since it is technically unfeasible to pre-approve or filter every potentially infringing torrent file, the Mininova team decided to throw in the towel and only allow torrents to be submitted by approved uploaders. This move resulted in the deletion of more than a million torrents, many of which were not infringing any copyrights at all. Thankfully, there are still plenty of alternatives for those BitTorrent users who are looking for the latest Ubuntu, OpenSUSE or Fedora release. Below we provide a random list of public torrent sites that are still open, but there are of course hundreds more sites we could have included. If your personal favorite is missing, feel free to post it in the comments below – preferably with your reasons why it should be included in any upcoming lists. 1. Vertor 2. Torrentzap 3. Torrentreactor 4. ExtraTorrent 5. KickassTorrents 6. BTjunkie 7. isoHunt 8. yourBitTorrent 9. The Pirate Bay 10. ShareReactor Update: The owner of another torrent site, Monova, told TorrentFreak that he has reserved all Mininova usernames for people who want to make the switch to his site. The account names can be claimed here. Also, we replaced some sites in the original top 10 because they went down or started to serve trojans. http://torrentfreak.com/10-alternati...ninova-091126/ Until next week, - js.  Current Week In Review  Recent WiRs - November 21st, November 14th, November 7th, October 31st Jack Spratts' Week In Review is published every Friday. Submit letters, articles, press releases, comments, questions etc. in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - November 21st, '09 | JackSpratts | Peer to Peer | 0 | 18-11-09 08:36 AM |
| Peer-To-Peer News - The Week In Review - November 14th, '09 | JackSpratts | Peer to Peer | 0 | 11-11-09 08:09 AM |