
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 |
|
Join Date: May 2001
Location: New England
Posts: 10,016
|
Since 2002
  "An ISP is not a court; and its customers will never have a chance to defend themselves against the recording industry's accusations and 'proof.' To whom, without judicial oversight, has the ISP obligated itself to provide meaningful due process and to ensure that the standard of proof has been met?" – EFF "Handley's case is deeply troubling, because the government is prosecuting a private collector for possession of art. In the past, CBLDF has had to defend the First Amendment rights of retailers and artists, but never before have we experienced the Federal Government attempting to strip a citizen of his freedom because he owned comic books." – Charles Brownstein January 31st, 2009  Sweden Mulls Tougher File Sharing Measures Sweden wants to give police more power to go after those suspected of illegal file sharing even if the crimes are only fineable offences. Currently, police can only get information on who is spreading copyrighted material or attempt to go after other criminal activity on the internet if the crimes are severe enough to be punished by a prison sentence. But the government wants to alter regulations to make it easier for police to track down parties suspected of more garden variety file sharing, reports the Svenska Dagbladet newspaper. On Friday, the Ministry of Justice is set to receive an interim report on from the police suggesting that law enforcement be allowed to get information about suspected file sharing even if the crime only warrants a fine. Those opposed to a new controversial file sharing bill, based on the European Union's Intellectual Property Rights Enforcement Directive (IPRED), have complained that private companies and individual copyright holders have the ability to go after those accused of illegal file sharing. The interim report also suggests that police be forced to seek a court order during preliminary investigations in order to get access to email and telephone records. According to the commission which prepared the report, the change strengthens the rule of law. Current rules allow police to approach internet service providers and telecom operators directly if the suspected crime carries a prison sentence of two years or more. On the other hand, however, Sweden’s security police (Säpo) and other agencies involved in intelligence gathering would not need to turn to a court. However, individual privacy would be maintained by other means, writes the paper. http://www.thelocal.se/17024/20090120/  Irish ISP Agrees to Disconnect Repeat P2P Users "Three strikes" rules have come to Ireland in a sudden and unexpected way, as the country's largest ISP settles a court case brought by the music industry and agrees to take action on file-swappers. Repeat offenders will be disconnected from the 'Net. Nate Anderson One of Ireland's largest ISPs, Eircom, has capitulated to the major music labels and agreed to implement a full "graduated response" program—complete with disconnections. Users get two warnings regarding file-sharing, and a third violation brings down the banhammer. The music industry has already said that it intends to pursue the same agreement with Ireland's other ISPs. The dispute began some time ago when the Irish branches of EMI, Warner, Universal, and Sony filed suit against Eircom. They charged that the ISP was essentially aiding and abetting piracy by doing things like advertising its services on The Pirate Bay, and the labels believed they could get a judge to force the ISP to install network monitoring equipment. With the trial finally under way at Dublin's High Courts this week, the labels and Eircom got together and hashed out a settlement instead of proceeding to judgment, and it's a settlement that keeps network sniffing gear out of Eircom's network. Instead, the ISP has agreed to send warnings and eventually to disconnect its users based on IP addresses provided by the music industry's investigators. As with most graduated response programs, the deal keeps the music industry from gaining direct access to subscriber data or to ISP networks. Instead, investigators use common tools to observe file-sharing, then log the IP addresses in question (those that belong to Eircom, at least) and pass them to the ISP. Eircom looks up the account associated with that address at the time in question, then shoots out a warning. Warning number one is friendly enough. Warning number two says that a disconnection will happen if the activity continues. Warning number three drops the A-bomb. Weighing the evidence While such graduated response mechanisms have the potential to be a huge improvement of massive litigation against end users, the process is generally understood to need some form of appeal or defense. It's not clear from the reporting coming out of Ireland that the Eircom agreement contains any such provisions. It appears that the music industry hands over its evidence, Eircom evaluates it, and a decision is made. Users, at least for now, seem to be shut out. The need for a fair judicial process (even if a judge is not actually involved) is one that even Cary Sherman of the RIAA made clear in his recent interview with Ars on the topic of graduated response, which he is trying to hammer out on a voluntary basis in the US. And when it comes to a sanction as severe as disconnection, the UK made clear this week that it saw huge legal problems with turning such a process over to industry bodies. But Eircom has agreed to the plan on a voluntary basis, without any government pressure. The move lead the Electronic Frontier Foundation to blast the ISP over its claim that it will consider the evidence presented by the music industry before shutting anyone off. "The difference is that an ISP is not a court; and its customers will never have a chance to defend themselves against the recording industry's accusations and 'proof,'" said an EFF blog post. "To whom, without judicial oversight, has the ISP obligated itself to provide meaningful due process and to ensure that the standard of proof has been met?" Eircom has apparently accepted the idea that the ISP has some responsibility for the actions of its users online. Assuming that the labels bring lawsuits against smaller ISPs, it is not yet clear whether any will be willing to risk the expense and hassle of a trial, especially when the music industry is seeking far-reaching judicial orders that would mandate network content filtering. Given the stakes, ISPs might well decide that graduated response, even with the tough disconnection penalty, is better than risking a loss in court. The agreement sets Ireland alone, so far as we can tell. While the French HADOPI law could bring government backing to the three strikes idea (complete with disconnections), Eircom may be the only ISP in the world voluntarily cutting P2P users off without court orders. It also means that Irish labels are pursuing—and Eircom has agreed to—a plan that was explicitly rejected by the European Parliament last year (though the European Commission watered down this stance when it went over the bill in question). While graduated response is now on the US radar screen, it's a delicate issue here. Our own attempts at getting answers about which ISPs might be involved have been met with stony silence (except from Verizon, which is not involved). In Europe, the debate is much more robust, as the UK, France, and Ireland all know, and it has been going on for years. Eircom's willingness to disconnect users will certainly embolden both sides. The music industry will use one victory to push for more, while opponents will push even harder for the EU and national governments to put limits on the sanctions process. http://arstechnica.com/telecom/news/...-p2p-users.ars  British Music Pirates Will Not be Disconnected from the Internet Patrick Foster Internet service providers will not be forced to disconnect users who repeatedly flout the law by illegally sharing music and video files, The Times has learnt. Andy Burnham, the Culture Secretary, said last year that the Government had “serious legislative intent” to compel internet companies to cut off customers who ignore warnings not to pirate material. However, in an interview with The Times, David Lammy, the Intellectual Property Minister, said that the Government had ruled out legislating to force ISPs to disconnect such users. Speaking ahead of the publication of a report on the future of Britain's digital industries, Mr Lammy said that there were very complex legal issues wrapped up in enforced disconnection. He added: “I'm not sure it's actually going to be possible.” Plans to combat internet pirates were stalled after a consultation by the Department for Business Enterprise and Regulatory Reform (BERR) showed there was no consensus between ISPs and the music industry as to how to deal with the seven million British internet users who share files illegally each year. The BPI, the body that represents the British record industry, wants all ISPs to sign up to a “three-steps policy” by which repeat offenders are disconnected if they fail to stop sharing copyrighted material. Lord Carter, the Communications Minister, is to reveal his thoughts on the problem of illict file sharing in his Digital Britain report. The document was due to be released today but, because of a “ministerial quagmire”, is expected to be released on Thursday. Suggestions have emerged that Lord Carter will order the founding of a “rights agency”, funded by a levy on service providers, to address the problem of piracy, or that he may suggest additional charges on customers' broadband bills to compensate the music industry. However, industry sources said that changes between various drafts of the document meant that some options may have fallen out of favour. In July last year the music industry and ISPs drew up a memorandum of understanding in which the ISPs agreed to send 1,000 letters a week for three months to combat users caught sharing files illegally. The memorandum also created a series of working groups dedicated to bringing the two industries together to solve the problem of illegal peer-to-peer networks, which the music industry says costs its members £180million a year. The ISPs believe that new business models and greater public education will help to solve the problem. They oppose any solution that involves new regulatory burdens being imposed on them. The Government, with the support of the music industry, favours a co-regulatory resolution, under which both parties agree to a code of conduct which is backed up by a regulator, such as Ofcom. Mr Lammy, who has begun a big consultation entitled Developing a Copyright Agenda for the 21st Century, said that there was a big difference between organised counterfeiting gangs and “younger people not quite buying into the system”. He said: “We can't have a system where we're talking about arresting teenagers in their bedrooms. People can rent a room in an hotel and leave with a bar of soap - there's a big difference between leaving with a bar of soap and leaving with the television.” He said he hoped the memorandum of understanding would mean that the Government did not have to apply “the heavy hand of legislation”. Music industry figures said they were disappointed by Mr Lammy's comments. One senior figure said: “The relative cost of stealing a bar of soap from an hotel might be small, but if it came to seven million people nicking the soap each year, which is what we have in the music industry, I'm sure that hotel chain would do something about it.” ISPs, on the other hand, welcomed the news. British Telecom said: “We're still hopeful that an amicable solution, without the need for legislation, can be reached. It doesn't make sense to try to get people online and at the same time scare them away.” http://entertainment.timesonline.co....cle5586761.ece  Google Calls for UK Copyright Reforms Vicky Frost Google today called for UK copyright reforms that allow individuals limited use of copyrighted work in order to create new content. "Fair use" laws in the US – which cover use of music for sampling, for example – were included in the 2006 Gowers review of UK intellectual property but have not been incorporated into British law. "Copyright reform in this context is crucial," said Google UK's public policy manager, Richard Sargeant, speaking on a panel at the Oxford Media Convention on the role of ISPs in policing the net. "We look with respect at the system of fair use rights that exists in the US. Europe doesn't have anything similar, which makes it much more difficult for people to see what they can and can't do." Sargeant was part of a panel that included John Whittingdale, chair of the culture media and sport select committee, who suggested that the media regulator Ofcom might form part of the solution to policing piracy on the web. The music industry wants to see internet service providers take a bigger role in acting against web users who download illegal content. But they have yet to reach agreement with ISPs on the scope of that role. "ISPs are not the police and must never become the police of the internet," said Nick Lansman, secretary general of the Internet Service Providers' Association. Whittingdale suggested that Ofcom could have a role as arbiter between creative industries and ISPs. "The obvious body to do that is Ofcom," he said. "It would probably have to be the body to do it." http://www.guardian.co.uk/media/2009...yright-reforms  Sources: AT&T, Comcast May Help RIAA Foil Piracy Greg Sandoval and Marguerite Reardon AT&T and Comcast, two of the nation's largest Internet service providers, are expected to be among a group of ISPs that will cooperate with the music industry in battling illegal file sharing, three sources close to the companies told CNET News. The Recording Industry Association of America, the lobbying group representing the four largest recording companies, said last month that it had enlisted the help of ISPs as part of a new antipiracy campaign. The RIAA has declined to identify which ISPs or how many. It's important to note that none of the half dozen or so ISPs involved has signed agreements. The companies are "skittish" about negative press and could still back out, said the sources. But as it stands, AT&T and Comcast are among the companies that have indicated they wish to participate in what the RIAA calls a "graduated response program." Typically, ISPs have stayed away from getting involved in copyright enforcement. The ISPs working with the RIAA will forward take-down notices to network users accused of illegal file sharing and in an unprecedented move, will establish a series of responses for chronic copyright violators.These responses will gradually grow in severity as the number of violations go up and may include suspension of service or even service termination. Each ISP will decide its own response. An RIAA spokesman declined to comment, and a Comcast representative said he wouldn't confirm the company's participation. An AT&T spokesman said this: "While I'm not in a position to comment on the RIAA announcement, we believe that consumer education is a key component to enabling customers to find and use legal methods to access the content they want...we have also consistently said that automatic cutoff of our customers is not something we would do." There are still plenty of details left to work out, the sources said. The RIAA has yet to address how it would help ISPs make up for the revenue they would lose by kicking people off their networks or who would pay the costs of sending take-down notices. The RIAA may disclose participating ISPs as soon as next month, according to a music industry source, adding that AT&T and Comcast are expected to be part of the group. If AT&T and Comcast do join, the RIAA will have plenty of muscle to wage a new assault on piracy. The music industry said last month that it would no longer battle piracy by filing lawsuits against individuals. Instead, the big recording companies seek to create a new line of defense at the network level. And at least on paper, the plan is a potent one. Broadband providers are the gatekeepers of Internet access and have their hands on all the controls. News that Comcast and AT&T would likely join the fight against illegal file sharing was greeted warmly by Rick Carnes, president of the Songwriters Guild of America. "Perhaps we have a chance to rebuild the music business after a period of tremendous looting," Carnes said. "You can't have a marketplace without property rights. Certainly (the ISPs) rolled out broadband based on movie and music downloads, legal and illegal and claimed (exemption from any legal responsibility), but at this point I think they realize being good partners with the content industry is a better idea. I really want to salute them for doing that." The move is part of the music industry's global campaign to sway broadband providers to join in protecting copyright material. The entertainment industry has been trying to get laws passed throughout the world that would force ISPs to implement a "three strikes" policy. Under such a policy, repeat offenders would be given three notices to stop infringing on copyright before a service provider cuts off Internet access. Such a "three strikes" policy was implemented in France in 2007. The way it works is that ISPs issue warning messages to customers downloading files illegally. And if users ignore those messages, their accounts could be suspended or closed altogether. Italy is considering a similar policy, according to the blog TorrentFreak. But in the U.K. a "three strikes" law appears to be losing support. The The Times of London reported Monday that passage of such a law is unlikely given that ISPs there don't want the added regulation. The newspaper reported that David Lammy, the intellectual property minister, said a law that requires ISPs to disconnect users had too many legal issues surrounding it. That said, ISPs in the U.K. have agreed to work with the movie and music industries to help stop piracy. In July last year, ISPs agreed to a memorandum of understanding with the music and film industries in which ISPs agreed to send 1,000 letters a week for three months to combat users caught sharing files illegally, The Times reported. Here in the U.S. ISPs have been reluctant to send letters or cut off service. And so far only in a couple of isolated agreements has an ISP agreed to help content owners police and enforce copyright infringement. In 2005, Verizon struck the stealth deal to win favor with Disney management. Verizon is building out a TV network and is striking content deals with movie studios and TV networks. In exchange for forwarding notices to suspected illegal file sharers, Disney gave Verizon the rights to transmit 12 of Disney's TV channels over its broadband network. The problem with these agreements is how to enforce them. If notices are sent automatically, there's no way to tell if a user has received it. Representative of the Electronic Frontier Foundation have reserved judgment until they hear the RIAA's plan detailed. They want to know how ISPs will protect users from being wrongly accused and whether ISPs will blackball users who have been kicked off other networks. Another big question that EFF asks is how far will the policing efforts eventually go? Will network operators be responsible for identifying illegal content on their networks and then be asked to stop it from traversing its broadband pipes? AT&T has previously stated that it's been testing technology that does just that. The company hasn't announced plans to use the filter technology. But the company has been working with members of the Motion Picture Association of America and the RIAA over the past year to figure out ways in which it can curb the flow of illegal content on its network. Sources told CNET News that the RIAA hasn't asked any ISP to peer into packets or be responsible for monitoring their networks for piracy. The RIAA will continue to identify alleged copyright violators and report them to their ISPs. http://news.cnet.com/8301-1023_3-10151389-93.html  Big Brother Filter Plan Insults Parents Underlying the Rudd Government's plan to screen the internet is an offensive message: that parents cannot be trusted to mind their children online. Adult supervision should be front and centre of the effort to improve online safety, a responsibility accepted by most parents, grandparents, teachers and carers. But the Communications Minister, Stephen Conroy, seems to think differently: filtering content at internet service provider level is "central to the Government's plan to make the internet a safer place for children". There is no technological substitute for adult supervision and it's irresponsible and misleading to infer otherwise. Mandating a so-called "clean feed" has the potential to create a dangerous false sense of security, leading parents to believe ongoing supervision and vigilance is no longer needed. The minister must start listening to the experts, who have repeatedly made the point that most predatory risks to children lurk in those areas of the online world this kind of filtering will do little to combat. Technical advice suggests chat rooms, email and peer-to-peer networks are the most dangerous. Law enforcement agencies around the world have revealed that pedophiles use peer-to-peer networks to exchange explicit videos and images outside the world wide web. Experts have also shown how the techno-savvy can use various techniques - including encryption - to bypass filters, leaving web sites you would expect to be blocked, open for all to see. The most powerful and effective weapon against illegal behaviour online is the same as that for illegal behaviour in the real world: sophisticated law enforcement. The successful operation against a child pornography network by the Australian Federal Police late last year, which resulted in more than 20 arrests, demonstrates that. This crucial capability must not be neglected in favour of an unproven filtering concept experts say will be easy to get around, will not block some offensive content while blocking some acceptable sites, and will slow down the internet for everyone in the process. Wouldn't the $40 million earmarked for the compulsory filtering policy be better spent on funding and resources for law enforcement, to better equip agencies to strike at the heart of child pornography production and distribution? There are other, more practical filtering options for individual computers, which allow choice, but this government doesn't appear to want that. Labor has closed the program established by the former Coalition government, which provided free, PC-based filters to all families. These filters allowed families to complement their online safety arrangements with software tailored to their individual needs, without compromising overall internet performance. Senator Conroy says too few people used the program. But take-up is driven by demand, and while some parents choose to use a content filter, others, for their own reasons, don't. I installed a content filter on our family's computer and believe it is a worthwhile additional safeguard to help protect my children from being exposed to explicit content. You would think the take-up rate of the free filter program would tell the Government something about where internet filtering lies in terms of priority to families, but apparently not. If anything, the minister seems to be using it to somehow justify Labor's heavy-handed "big brother" approach. As the debate about Labor's controversial policy has raged, Senator Conroy has remained cryptic and vague, raising suspicion by talking about filtering not just illegal material, but also "unwanted" content that he refuses to specify. He has also resorted to unedifying inferences against those who dared question his plan. When a Greens Senator, Scott Ludlam, asked some perfectly reasonable questions during a senate estimates hearing last October, Senator Conroy responded: "I trust you are not suggesting that people should have access to child pornography." Newspapers have reported that the minister's office tried to silence industry figures who had publicly spoken out against content filtering. Last month Senator Conroy finally released a damning expert report on ISP-level filtering, which he had sat on since February. Meanwhile, we wait for filtering trials to start, trials that have been delayed and which have next-to-no support among the industry. Telstra BigPond - Australia's largest ISP - has refused to take part, comparing internet filtering to "like trying to boil the ocean". The third largest, iiNet, is prepared to participate to highlight flaws. No decent Australian would argue against the broad aim of making the online world as safe as possible. But Labor's fixation with compulsory, centralised filtering - which tells parents they are incapable of protecting their children - is not the answer. http://www.smh.com.au/news/opinion/b...471392459.html  ISPs Clustered for Filtering Trials Fran Foo PARTICIPANTS in the federal Government's controversial mandatory internet filtering scheme will start live trials in batches, instead of en masse. Sixteen expressions of interest for the trial have been received from small, medium and large ISPs, and the Department of Broadband, Communications and the Digital Economy is considering which providers should be invited to take part in the test. It is understood that since the size of the ISPs vary, they could be grouped together in blocks; the start and end date for trials would differ depending on the groupings. Live trials will be conducted by Enex TestLab, the Melbourne outfit that conducted the first laboratory, or closed, trials of internet filtering products under the Howard regime. Ideally, ISPs will participate in the pilot for a minimum of six weeks. Communications Minister Stephen Conroy hopes to introduce two forms of content filtering: a mandatory scheme based on a blacklist of illegal web pages, and an optional "clean feed" of links that would automatically block certain types of content, such as adult material. It would be up to individual ISPs to select customers for trials on the blacklisted pages, collated and managed by the Australian Communications and Media Authority (ACMA). ISPs have the option of testing network performance against a list of approximately 10,000 sites but without involving customers. Optus, for example, has only chosen to trial the blacklist, which comprises 1370 URLs based on 1125 separate domains. The list is compiled based on complaints lodged with ACMA by members of the public. According to ACMA, 864 web pages relate to content falling under the RC classification, including 674 pages containing child sexual abuse content. The RC classification restricts depictions of child pornography, bestiality, excessive violence or sexual violence, detailed instruction in crime, violence or drug use, and/or material that advocates terrorism acts. Labor's promise to censor the internet was a key election commitment. However, details of Labor's censorship policy will only be developed after the live trials and consultations with stakeholders, Senator Conroy has said in answer to parliamentary questions on notice. Access to search engine tools will not be blocked to prevent circumvention of the filter, the minister said. Child protection lobbyists want more engagement between Government and children who are major stakeholders in the internet filtering debate. As reported yesterday, Save the Children Australia and the National Children's and Youth Law Centre have yet to be convinced of the effectiveness of a mandatory filter and would wait until the Government's youth advisory group was consulted. "We're agnostic about the mandatory filtering trials," Save the Children child rights adviser Holly Doel-Mackaway said. "If it's an opt-in filter we would agree." Following its election, the Government set up a youth advisory group comprising 15 schools to guide it on cyber-safety policies. Ms Doel-Mackaway called on the Government to take children's input seriously when forming policy. "We want the children's comments to be documented and made public," she said. The department has yet to say when trials would kick-off. http://www.australianit.news.com.au/...-15306,00.html  Virgin Puts 'Legal P2P' Plans on Ice Historic deal consigned to history Andrew Orlowski Exclusive Big label pressure has forced British cable ISP Virgin Media to suspend plans to introduce a legal music sharing service for its subscribers, just weeks ahead of its launch, The Register has learned. The radical initiative, tentatively branded as "Virgin Music Unlimited", represented a major investment for the ISP, and would have been the first such attempt to monetise P2P file sharing in an ISP partnership in either Europe or the USA. However, 11th hour "anti-piracy" demands by major record labels including Universal Music and Sony Music meant Virgin could no longer launch the service as it had envisaged. Labels demanded that Virgin block uploads and downloads of songs from subscribers' PCs, sources suggest. Since the system is designed to encourage file sharing, the demand removed the service's USP. Virgin is believed to be particularly disappointed at the collapse of the initiative. The ISP had been the first to co-operate with the music business-ISP Memorandum of Understanding (MoU) signed last July and send warning letters to file sharers. It had also made a significant investment in the Music Unlimited initiative, estimated at eight figures. When Virgin's boss recently announced a significant investment in deep packet inspection, he also hinted at "monetizing the intelligence" of the network, a statement that erroneous reports at the time claimed was a reference to Phorm. In fact, it referred to radical iniatives such as VMU. The withdrawal of major label support has serious strategic implications for Virgin: the ISP is left with a stick, but no carrot. Why Virgin almost made history While VMU had yet to be formally announced, it was being closely watched by both ISPs, the music business, and fans. While they are reluctant to be seen to be monitoring their users, ISPs receive no incremental revenue from the vast quantities of infringing material that flow across their networks, which is a disincentive to invest in better network infrastructure. VMU was seen as a way to capture some incremental revenue voluntarily from users, increase customer loyalty, and decrease "churn". Similarly, many parts of the music business now express the view that prosecuting users and attempting to halt behaviour fails to bring in any revenue. Meanwhile, P2P remains a taboo: the one form of consumer behaviour that hasn't been given a legitimate revenue opportunity. Millions have been spent over the past ten years in prosecuting users, and rather less on building legitimate services that capture revenue voluntarily from this behaviour. For their part, consumers appeared to be keen on a service never previously legally available. In a survey last year 80 per cent of downloaders and 63 per cent of non-downloaders expressed an interest in a legal P2P service that allowed them to keep songs. The reaction Sony had not responded to a request for comment at press time. Speaking off the record, a source close to the recording industry stressed that ISPs must abide by the obligations in the MoU and that government regulation was likely if they didn't. From that unprompted statement, it's possible to infer that major labels still fear losing control, and have pinned their hopes on changing behaviour rather than creating services that generate new revenue streams. A Virgin Media spokesman told us the company doesn't comment on "rumour or speculation," but Virgin's technology partner PlayLouder MSP confirmed the deal was off but declined to elaborate. A source said that interest from UK and European ISPs in launching a legal P2P subscription service was higher than ever. http://www.theregister.co.uk/2009/01...al_p2p_on_ice/  Cox To Try New Traffic Shaping Scheme Gary Kim Cox Communications, the third-largest U.S. cable company, is instituting traffic shaping policies starting February 9, 2009 in its Kansas and Arkansas markets. Under the new policy, Cox will give momentary priority to Internet traffic it judges to be time-sensitive, such as Web pages, streaming video and online games, at times when congestion is high. Less time-sensitive traffic, such as file uploads, peer-to-peer and Usenet news groups, may be delayed momentarily, but only when the local network is congested, Cox says. Cox expects to apply the new technology to all of its consumer Internet subscribers later this year if it proves successful in Kansas and Arkansas. The company’s congestion management plan is designed to ensure that if congestion reaches a certain level, action is taken so that customers continue to have a good experience, and is viewed as a simple matter of intelligent network management. Cox also takes such measures as blocking spam and helping to make our customers less susceptible to viruses and other online hazards as part of those policies. Of course, some will view the move as an inappropriate interference with customer rights to access lawful content. Still, Cox expects any congestion-related delays would be very brief and most likely not even noticeable to customers. When the congestion conditions end, Cox would not apply the congestion management techniques. Initially, all the traffic on the Cox network will be divided into two categories: time-sensitive and non-time-sensitive. Cox says it plans to classify VoIP, e-mail, Web surfing, instant messaging, streaming audio and video, games, virtual private networks or any other service not specifically mentioned as "non-time sensitive" as time sensitive. Non-time-sensitive traffic includes file transfers such as FTP, network storage bulk transfers, peer to peer traffic, software updates and Usenet access. Cox says it is possible the techniques could change over time as demand changes. Cox in the past has used other schemes, but the new program is based on the time-sensitive nature of the Internet traffic itself, not specific protocols, as such, to avoid classification methods that target specific protocols such as P2P. The company emphasizes that its approaches are based strictly on the time-sensitivity of the traffic that is using the network, not the owner or source of the traffic. http://cable.tmcnet.com/topics/cable...ing-scheme.htm  Google, Partners Release Net Neutrality Tools Google and partners unveil a set of Internet performance measurement tools. Grant Gross Google and a group of partners have released a set of tools designed to help broadband customers and researchers measure performance of Internet connections. The set of tools, at MeasurementLab.net, includes a network diagnostic tool, a network path diagnostic tool and a tool to measure whether the user's broadband provider is slowing BitTorrent peer-to-peer (P-to-P) traffic. Coming soon to the M-Lab applications is a tool to determine whether a broadband provider is giving some traffic a lower priority than other traffic, and a tool to determine whether a provider is degrading certain users or applications. "Transparency is our goal," said Vint Cerf, chief Internet evangelist at Google and a co-developer of TCP/IP. "Our intent is to make more [information] visible for all who are interested in the way the network is functioning at all layers." The tools will not only allow broadband customers to test their Internet connections, but also allow security and other researchers to work on ways to improve the Internet, Cerf said. Current Internet performance tools "are geeky to the extreme," he said during a Washington, D.C., forum on the M-Lab tools. The M-Lab project, launched Wednesday, comes after controversy over network management practices by Comcast and other broadband providers. Earlier this month, two officials at the U.S. Federal Communications Commission questioned why Comcast, the largest cable modem provider in the U.S., was exempting its own VoIP (voice over Internet protocol) from traffic congestion slowdowns, but not offering the same protections to competing VoIP services. The FCC letter to Comcast came after commissioners ruled in August that the broadband provider's decision to slow some P-to-P traffic violated the agency's network neutrality rules prohibiting broadband providers from blocking or slowing Internet traffic or applications. News reports in late 2007 unveiled Comcast's practice of slowing some BitTorrent traffic. Comcast later said it was slowing traffic only at times of peak congestion, but the FCC and other groups disputed that the traffic management was limited. Comcast declined to comment on the M-Labs effort. The set of tools will allow broadband customers to measure their providers' performance, said Michael Calabrese, director of the Wireless Future Program at the New America Foundation, a think tank involved in the M-Lab project. Consumers "deserve to be well-informed" about their broadband performance, he said. Some of the M-Lab tools have already been released, but participants in the project plan to further develop the tools and host them on servers around the world, added Sascha Meinrath, research director at the Wireless Future Program. All the M-Lab tools will be released under open-source licenses, allowing others to modify and improve them, he said. People on either side of a debate on whether the FCC or U.S. Congress should develop network neutrality rules should welcome the tools, said Ed Felten, director of the Center for Information Policy and a computer science and public policy professor at Princeton University. It took months for policymakers to gather solid information on Comcast's network management practices, but net neutrality advocates can use the tools if they suspect broadband providers of interfering with traffic. "If you believe that network neutrality government regulation is not needed, if you believe that the market will handle this ... then you should also welcome Measurement Labs," Felten said. "What you are appealing to is a process of public discussion ... in which consumers move to the ISP [Internet service provider] that gives them the best performance. It's a market that's facilitated by better information." However, one ISP industry source, who asked not to be identified, questioned whether the tools would accurately point to the cause of broadband problems. Spyware or malware on computers can affect browser performance, and problems with the wider Internet can cause slowdowns, the source said. The M-Labs partners seemed to bypass broadband providers when putting together their tools, the source added. "It may appear that issues that are occurring off an ISP's network may be the ISP's problem," the source said of the tools. "It's important for groups like this to collaborate, not only among themselves, but also with ISPs." http://www.goodgearguide.com.au/arti...utrality_tools  Charter Turns Internet Dial To 60 Mbps Operator Launches DOCSIS 3.0-Based Service First in St. Louis Todd Spangler Looking to grab broadband bragging rights, Charter Communications this week will launch 60-Mbps downstream Internet service in its home market of St. Louis. The Ultra60 service -- the fastest residential service available from any cable or telecommunications company in the U.S. -- will initially be available to 100,000 homes in western St. Louis County and surrounding areas. The company expects to enter other markets with the service, which will provide upstream speeds of up to 5 Mbps, later in 2009. The service uses the cable industry's next-generation modem technology, DOCSIS 3.0, to combine multiple channels together to provide higher connection speeds. "The strategy that we have always followed and implemented is that we want to be the speed leaders in the markets we serve," Charter chief technology officer Marwan Fawaz. "Launching a DOCSIS 3.0 product allows us to not just keep that lead but expand it." Separately, it looks increasingly likely that Charter is heading for bankruptcy. Having the operator tout itself as the fastest broadband provider in the country could help soften the public-relations blow of announcing a major restructuring. Ultra60 will cost $129.99 per month bundled with TV or phone and $139.99 per month as a standalone service. In St. Louis, Ultra60 will blast past the telco competition, AT&T's U-verse Internet DSL, which provides top downstream speeds of 18 Mbps. By cranking up to 60 Mbps, Charter also will be able to claim -- for the time being -- that it can speed past Verizon Communications' FiOS Internet service. The telco, which competes with Charter in parts of California and Texas, offers 50 Mbps downstream to around 10 million homes. Also maxing out at 50 Mbps is Comcast, which has been the most aggressive MSO in deploying what it calls "wideband" cable-modem service. The biggest U.S. cable operator is offering 50-Mbps tiers to 10 million premises in markets including Chicago, Philadelphia, Boston, Atlanta and Seattle for $139.95 per month with cable TV service. Is the 60-Mbps watermark about bragging rights? "That's fair to say," Fawaz replied. "We don't want to necessarily match our competitors -- we want to beat them.... Competitively we think it's the right speed in our markets." He noted that DOCSIS 3.0 technology allows speeds even greater than that, theoretically providing 160 Mbps downstream via four bonded channels and more than 300 Mbps with eight. DOCSIS 3.0 will help cable operators defensively in areas where Verizon offers FiOS and let them play offense where DSL is the rival. "You have to match Verizon step for step," said Patti Reali, an independent cable industry analyst. And while the slumping economy will make a premium-priced service a tough sell, "there will still be a segment of the market that will look for a Cadillac service," she added. As part of upgrading to DOCSIS 3.0, Charter expects to increase the top speeds of its Max tier from 16 Mbps to 20 Mbps downstream in all its markets. According to Fawaz, Charter will not impose bandwidth-usage caps on any of its high-speed Internet subscribers. By contrast, Comcast's policies limit users to 250 Gigabytes of data consumption per month. Charter's marketing for Ultra60 will be locally focused and include ads in billing statement, e-mails, cross-channel spots and radio promotion. In pitching Ultra60 to customers, Charter will underscore its superiority to DSL -- providing a connection about 40 times as fast -- and its ability to let subscribers perform multiple activities at once (such as downloading music, watching a movie trailer, and surfing the Web all at once). However, for now, most U.S. consumers are happy with their existing broadband service, according to a recent survey of more than 1,000 consumers by research firm In-Stat. Most people seemed to be just fine with 5 Mbps of actual measured download speed, said Gerry Kaufhold, principal analyst with In-Stat, which like Multichannel News is owned by Reed Business Information. "It's unlikely that 60 Mbps -- or anything in excess of 10 Mbps -- is going to have much market traction to get people to switch their broadband carrier," he said. Fawaz acknowledged that not every Charter broadband subscriber will be upgrading to the DOCSIS 3.0-based services. But, he said, "We feel there's a portion of the customer base that will want it. Probably not a huge number, but enough to make it interesting." Charter is using the DOCSIS 3.0 modular cable modem termination system from Cisco Systems in its headends. The MSO has qualified three cable modems, from Motorola, Cisco and Ambit Microsystems. In conjunction with the Cisco modular CMTS, Charter will use two universal edge QAM platforms, Harmonic's Narrowcast Services Gateway and Cisco's RF Gateway 10. http://www.multichannel.com/article/...To_60_Mbps.php  Revenue Rose 12% in Quarter for Verizon Wireless Matt Richtel Verizon, the telecommunications company, reported fourth-quarter sales on Tuesday that fell short of Wall Street projections as layoffs and other cost-cutting took a toll on the telephone and Internet business. The company said that consumers and companies were cutting landlines at an accelerating rate, leading to a sharp decline in profit in that part of its business. The wireless side of Verizon’s business, which in recent years has buoyed the company, had mixed results. Revenue and profit margins grew, but fewer customers joined Verizon Wireless than a year ago, and a slightly higher percentage of customers left. Overall, Verizon reported sales of $24.6 billion in the fourth quarter, just shy of the $25 billion forecast by Wall Street analysts. In the period a year ago, the company reported sales of $23.6 billion. For the fourth quarter, the company reported net income of $1.7 billion or 61 cents a share, a figure that excluded one-time charges. On that basis, a consensus of Wall Street analysts had projected a profit of 61 cents a share. A year ago, the company had net income of $1.8 billion or 62 cents a share. “Given all the financial turmoil, we feel pretty good about the results,” said Denny Strigl, president and chief operating officer of Verizon. Compared with the period a year ago, revenue increased 12 percent for Verizon Wireless, which is 55 percent owned by Verizon and 45 percent by the Vodafone Group. That business benefited from an increase in the average amount paid by subscribers — $51.72 a month, up 1.4 percent from a year ago. And wireless operations profit margins rose sharply to 47.2 percent from 43.6 percent a year ago. At the same time, Verizon Wireless gained 1.4 million net subscribers in the fourth quarter of 2008, down from 2 million in the same period a year earlier. Plus, the its churn rate — the rate at which it lost customers — rose to 1.34 percent in the fourth quarter from 1.21 percent a year earlier. Mr. Strigl said the increase was caused by layoffs and other cuts that led corporations to take back devices and cut off service from employees. The landline business was hurt by the economy and by larger systemic changes in the telecommunications industry. In the fourth quarter, Verizon lost 911,000 corporate and homeowner landlines. For the year, landlines fell to 36.2 million from 39.9 million, a 9.3 percent drop, and one consistent with trends in the industry. The shrinking business hurt the bottom line: operating margins on the landline side of the business fell to 25.4 percent, down from 28.4 percent in the period a year ago, said Craig Moffett, an analyst with Sanford C. Bernstein & Company. Another area of mixed performance for Verizon was the continued $18 billion rollout of FIOS, the high speed network that delivers television, Internet and other data services. In the fourth quarter, the company added 303,000 television subscribers, up from 226,000 added a year ago, and 282,000 broadband customers, up from 244,000 added a year ago. But investors and analysts are asking whether the growth will ultimately be sufficiently profitable for Verizon to justify the rollout. Mr. Moffett says early indications suggest that Verizon has a long way to go to prove that FIOS can offset revenue loss in the rest of the landline business and stanch the decline in profit. “They’re now five years into a massive investment,” Mr. Moffett said, arguing that FIOS profits do not appear destined to be worth the investment. “What they have to show for it are slightly lower revenue declines than they otherwise would, but even further margin compression.” http://www.nytimes.com/2009/01/28/te...28verizon.html  Blumenthal Wants Connecticut Regulators To Block AT&T Job Cuts Lynn Doan It was 18 degrees out, but the mob was fired up. Angry about impending layoffs, hundreds of chanting, fist-raising AT&T workers flicked on flashlights and marched to the state Capitol one recent night demanding an end to job cuts. Their rallying cry was, in some ways, like any other union protest. But this demand is more than a slogan. It is a very real, legal measure backed by some of Connecticut's most powerful politicians, and it thrusts the state into a national debate over corporate regulation. AT&T said last month that it would pare its Connecticut workforce, which totals about 6,800, by 400 jobs and transfer another 60 jobs to Michigan. A day after the news broke, Attorney General Richard Blumenthal, flanked by union leaders, implored state regulators to block the cuts with the force of law while the state investigates the impact on customer service. His request, supported by a growing list of state officials, has sparked a heated debate focused on one question: Should — or, perhaps more important, — can government forbid a private corporation to lay off workers?The question comes as federal officials decide how to rescue entire industries, as the financial crisis fuels a push to establish stricter and more active regulation, and as an incoming president vows to do just that. In Connecticut, where unemployment rates have reached the highest levels since 1993, this question is making tempers flare on both sides as state officials desperately try to save local jobs and companies struggle to stay afloat. Blumenthal has insisted repeatedly that the state Department of Public Utility Control has the legal power to stop AT&T from cutting jobs because it could drastically diminish the company's customer service — one facet of the telecommunication industry that the state still regulates. "We're pushing the DPUC to do their job and to regulate the way they're supposed to regulate," said Bill Henderson, local chapter president of the Communications Workers of America. "We're not asking for anything more than what the law says." AT&T argues that blocking its plans is in direct violation of the U.S. Constitution's commerce clause, which gives the power to regulate interstate and international commerce only to Congress. More to the point in Connecticut, the company says, eliminating these jobs will not hurt customer service because the work will be done better elsewhere. "This is not about AT&T. This is not about Blumenthal. This is about the kind of message Connecticut is sending to business — a state that has no positive job growth and [has] people who are falling over themselves to prove that they're pro-consumer by showing they're anti-business," AT&T spokesman Dave Mancuso said. Even if a state order were legal, it would hurt Connecticut, he said. "Look at the states where companies are investing," he said, "and I think you'll see very different dynamics." Telecom analysts agree that a state ban on layoffs, if upheld in court, could reshape Connecticut's business climate. "All of a sudden, they're going to take a big, strong company, and they're going to squeeze it dry," said Jeff Kagan, an independent telecom analyst based in Atlanta. "If every state tried to exercise the same control, this company would be doomed. It wouldn't have any control over its future or any control over being competitive." State regulators have so far denied Blumenthal's requests, without listing specific reasons. 2-Way Frustration The issue of AT&T's customer service is sticky. Blumenthal and other consumer advocates have said the company's record is abysmal, while AT&T has said it is meeting or exceeding standards. The company has maintained that the 60 job transfers to Michigan will improve customer service, because workers will be using a more efficient system there to field and dispatch calls. Customers shouldn't notice a difference in service from the reported 400 job cuts either, an AT&T spokesman said, because they serve the company's landline business, which shrank by 4 million access lines nationwide in the first nine months of 2008. "When you lose that many access lines, you need fewer employees to support that work," spokesman Walt Sharp said. The company is offering new positions to all 460 Connecticut employees whose jobs are being eliminated, Mancuso said, though there's no promise that they'll remain in the same department, or in the same state. Gov. M. Jodi Rell sent a letter to regulators and AT&T criticizing the job eliminations, but has stopped short of calling for an order against the cuts. Blumenthal's call for a stay on layoffs has only intensified AT&T's growing frustration with operating in Connecticut. During an economic conference in September, AT&T's eastern regional manager urged government officials to scale back regulation and let the company do its job. "We don't need policy-makers stepping in and telling us how to do it or where to do it," Chad Townes said at the conference, where he spoke about a controversy over AT&T's U-verse television service. 'I Love AT&T' A state move to block corporate layoffs would be extremely rare, but Christiaan Hogendorn, an associate professor of economics at Wesleyan University, said there are examples in U.S. history. In the days of railroad and airline regulation, he said, an airline wasn't allowed to lay off employees until its plans were approved by a government commission. "If we were talking about an unregulated company, I'd say, 'No way could the government do this.' But with a regulated company, in theory, the authority is there," said Hogendorn, who studies the telecom industry. Because AT&T has a regulated monopoly in landline phones, he said, "they're obligated to provide service at a certain quality level in exchange for that. And the idea that customer service is related to the number of employees is pretty sound." Surrounded by AT&T workers chanting "Governor Blumenthal" at the recent rally in Hartford, the attorney general made yet another call to action. "There's a rumor going around that the AG doesn't like AT&T. ... Well, I love AT&T," he said. "And when they start paying fair wages, when they start keeping jobs here, when they start playing by the rules, Connecticut will love AT&T." As Blumenthal's rhetoric gains traction in the political arena and unions back him, the DPUC may find a larger fight on its hands. "AT&T isn't a regular business. We're not talking about mom-and-pop stores. We're not talking about even a Wal-Mart for that matter. We're talking about a company that operates under the regulations of the state," state Comptroller Nancy Wyman said at the union rally.The company says its job cuts — including a nationwide paring of 12,000 positions, or 4 percent of the total, are a result of plummeting landline sales, combined with the effects of the recession. The trend is clear: AT&T's total sales from wireless service, which employs far fewer people in Connecticut, were up by about 15 percent for most of 2008, for the first time surpassing landline voice service, which was down 8 percent. But union officials and politicians say the company's record-high profits paint a different picture. Total revenues were up by 3.3 percent for the most recent quarter AT&T has reported. And last month, the company increased its annual shareholder dividend by 4 cents to $1.64 a share, marking its 25th consecutive increase — a record unmatched by any other major telecom company, AT&T said. Peter W. Murphy, a financial adviser in Southington and AT&T shareholder, said he was shocked when the company raised its dividend, just as it was gearing up to slash jobs. "I am appalled by the level of both greed by AT&T senior management and their lack of compassion towards their employees," he wrote in an e-mail to The Courant. Some say it's not a matter of greed, but survival. Though parts of AT&T are regulated, the company is increasingly operating in a competitive marketplace that demands lower costs and lower prices. "In order for them to be competitive with other carriers, this is what they have to do," Kagan, the telecom analyst, said. "If they have to start worrying about how many jobs they have to leave in how many states ... the company would be doomed." http://www.courant.com/business/hc-a...,2453493.story  House Panel Backs $3 Billion Internet Stimulus Kim Dixon The House Energy and Commerce Committee backed including about $3 billion in grants to expand Internet service as part of a larger economic stimulus bill, including a provision requiring "open access" in wireless service and on the Internet. The Democratically-controlled committee on Thursday cleared the provisions aimed at expanding high-speed Internet and wireless service in rural and hard-to-serve areas over objections from several Republican members. Another $3 billion sought for broadband expansion in rural areas will be considered by the House Agriculture Committee. The Democrats' overall $825-billion stimulus plan is expected to go before the full House next week for a vote. The massive package includes tax cuts plus funding for roads, mass transit, healthcare and other projects. Some Republicans on the commerce panel tried to block the $3 billion Internet provision, saying it would not stimulate the economy. "This is not an economic stimulus, it's a massive spending bill," said Joseph Pitts, a Republican from Pennsylvania. A provision opposed by mobile phone companies would require Internet service providers that receive grant money to abide by so-called "open access" principles, which bar providers from discriminating against applications and content requiring more bandwidth. "These are public dollars and networks built with this funding should be open," said Rep. Anna Eshoo, a California Democrat with many technology companies in her district. The public interest group Free Press defines openness as prohibiting "discrimination against any lawful content" and giving consumers freedom of choice among Internet providers. Lawmakers who support the funding say it will create jobs to help jumpstart the ailing economy. A Brookings Institution study found that every one percentage point increase in broadband penetration per year could yield 300,000 jobs. Potential recipients of the grant money include Internet service providers AT&T Inc, Verizon Communications and Comcast Corp. Rural telephone companies could also apply, such as CenturyTel Inc, Windstream Corp and Frontier Communications Corp. Despite start-up costs funded by the government, "you still have operational costs. It will be a tough decision (for the companies) given the economics of serving these areas," said Paul Glenchur, an analyst at Stanford Washington Group. Democratic Rep. Henry Waxman of California, chairman of the House panel, said the $3 billion in grants was aimed at "service providers, infrastructure companies, or a state or unit of local government." The House Energy and Commerce Committee, which has jurisdiction over most Internet and telecommunications issues, is also reviewing $20 billion in healthcare information technology for the stimulus bill. (Editing by Tim Dobbyn) http://www.washingtonpost.com/wp-dyn...012202247.html  Government Blocks Release of Documents on Secret IP Enforcement Treaty Despite Obama's order for openness, americans still kept in the dark about ACTA EFF The Office of the United States Trade Representative (USTR) is withholding hundreds of documents about a secret intellectual property enforcement treaty currently under negotiation between the U.S. and more than a dozen other countries. In a pending federal lawsuit, the Electronic Frontier Foundation (EFF) and Public Knowledge are demanding that background documents on the Anti-Counterfeiting Trade Agreement (ACTA) be released under the Freedom of Information Act (FOIA). But the USTR has claimed that more than 1300 pages should be withheld because they implicate national security or expose the USTR's deliberative processes. The USTR has released only 159 pages for public viewing. ACTA raises serious concerns about citizens' civil liberties and privacy rights. The contents and text of ACTA remain secret, but a document leaked to the public last year shows that ACTA could include stronger criminal measures, increased customs border search powers, and requirements for Internet service providers to cooperate with copyright holders. Some public suggestions from content companies have included requiring ISPs to engage in filtering of their customers' Internet communications for potentially copyright-infringing material, mandatory disclosure of personal information about alleged copyright infringers, and adoption of "Three Strikes" policies requiring ISPs to automatically terminate customers' Internet access upon a repeat allegation of copyright infringement. "ACTA could lead to new invasive monitoring of Internet communications by your ISP and raises serious potential due process concerns for Internet users," said EFF International Policy Director Gwen Hinze. "Because ACTA is to be adopted as an Executive Agreement, it will bypass normal processes of Congressional oversight. Therefore, it is crucial that citizens have access to information about its contents in a timely manner. The USTR's decision to withhold documents that citizens are entitled to see as a matter of law prevents citizens from evaluating ACTA's impact on their lives and expressing their opinions to their political leaders before it's a fait accompli." Despite the vast amount of relevant information that was withheld, the documents that were released disclosed some interesting information about ACTA, including records revealing U.S. government policy that ACTA documents should only be shown to government officials or others who work closely with a country's consultation process. The records also show that the U.S. government intends to "hold ACTA documents in confidence for a fixed period after negotiations conclude." But not everyone has been kept in the dark about ACTA. Officials from the USTR met privately with the major U.S. proponents of the treaty: the Global Leadership Group of the International Chamber of Commerce's Business Action to Stop Counterfeiting and Piracy and the Coalition Against Counterfeiting and Piracy at least three times in 2008. EFF and Public Knowledge first made their FOIA request of the USTR in June of 2008. After the agency dragged its feet in responding, EFF and Public Knowledge filed suit in federal court in Washington, DC, in September of 2008. EFF plans to ask the court to stay further action in the case pending the release of new guidelines by the Attorney General implementing President Obama's January 21 memorandum stating that all agencies "should adopt a presumption in favor of disclosure, in order to renew their commitment to the principles embodied in FOIA, and to usher in a new era of open Government." "We are disappointed with the USTR's response so far," said Public Knowledge Staff Attorney Sherwin Siy. "With the guidance of this new policy, we hope that the USTR will reassess its less-than-forthcoming compliance with our FOIA request and provide the public with the much-needed transparency and accountability about this important global agreement." For the significant documents released under FOIA: http://www.eff.org/fn/directory/6661/328 For more on this case: http://www.eff.org/cases/eff-and-pub...owledge-v-ustr For more on ACTA: http://www.eff.org/issues/acta/ http://www.eff.org/press/archives/2009/01/29  Michael Copps Named Acting Chairman Of FCC FMQB After the resignation of FCC Chairman Kevin Martin, President Barack Obama has named Michael Copps as acting Chairman of the agency. Copps has served as an FCC commissioner since 2001. Democratic sources have been reporting that technology executive Julius Genachowski will ultimately be picked to head the agency, although it is unclear when it will be announced, or when Senate confirmation hearings will occur. "I am honored to be designated as Acting Chairman of the FCC," said Copps on Thursday. "I thank President Obama for his confidence in me and for this opportunity to serve. I know that I have a truly gifted and terrific team to work with. I pledge every effort I am capable of to help steer the Commission through its current transition to new leadership." FCC Commissioner Jonathan Adelstein released a statement saying, "I am thrilled to congratulate my good friend and trusted colleague, Michael Copps, on his designation as Acting Chairman of the Federal Communications Commission. The FCC will benefit from his leadership, experience, and abiding commitment to the public interest. He understands that public service is a sacred trust with the American people, and he has repeatedly demonstrated his sterling character, willingness to build consensus, and deep commitment to serve all Americans. During our six years on the Commission, he has consistently worked to ensure that consumers reap the benefits of a responsive and diverse media, robust and ubiquitous broadband Internet access, and reliable public safety communications. With the transition to digital television almost upon us, he will provide urgently needed guidance to put us back on track." NAB President/CEO David Rehr also issued a statement, commenting, "NAB salutes Michael Copps for being selected Acting Chairman of the FCC. We respect Chairman Copps for his tenacious commitment to the public interest, and we look forward to working with him and the other Commissioners." http://fmqb.com/Article.asp?id=1123590  News Groups Urge Court to OK Webcast of Trial AP Fourteen news organizations, including The Associated Press and The New York Times Co., are urging an appeals court to allow online streaming of oral arguments in a music downloading lawsuit the recording industry filed against a Boston University graduate student. A brief filed yesterday in the 1st US Circuit Court of Appeals argues that allowing audiovisual webcasting of the case is in the public interest. The news organizations countered a petition by the Recording Industry Association of America opposing webcasting from the courthouse in its lawsuit, which alleges copyright infringement. The Times Co. owns The Boston Globe. The webcast was sought by Charles Nessen, a Harvard Law School professor representing BU student Joel Tenebaum. Last week, US District Judge Nancy Gertner, who authorized the webcasting of arguments in the case, delayed the hearing to allow the appeals court to consider the webcast. http://www.boston.com/ae/media/artic...cast_of_trial/  Muxtape Returns from RIAA-Induced Hiatus Josh Lowensohn Muxtape, the upload-your-own mixed-tape service, came back on the scene on Tuesday. Founder Justin Ouelette had originally shuttered it last August in order to keep the RIAA off his back after licensing attempts and paperwork had overwhelmed him. The new version of the service, which does not allow users to upload music from their hard drives, instead relies on bands to submit their own tracks for listeners to play on Muxtape--and Muxtape only. There are a dozen bands to start with, all of which have been hand-picked by the service's creators. Bands that are interested in getting their music onto the service will be able to sign up once the service relaunches in earnest. According to Wired, artists will then be able to sell their tracks from places like Amazon MP3 and iTunes by paying Muxtape a fee. There has been, however no mention of whether that fee will be per referral or on a subscription basis. Until the official relaunch, users who were previously registered with the service will find that their log-in credentials no longer work. Likewise, you're unable to assemble any of the tracks into a custom playlist--one of the highlights of using the service. http://news.cnet.com/8301-17939_109-10151266-2.html  ‘It was a mistake’ Springsteen Takes The Rap For Selling CD Through Wal-Mart AP The Boss is owning up to a mistake. In an interview with Sunday's New York Times, Bruce Springsteen says he shouldn't have made a deal with Wal-Mart. This month, the store started exclusively selling a Springsteen greatest hits CD. Some fans were critical because Springsteen has been a longtime supporter of worker's rights, and Wal-Mart has faced criticism for its labor practices. Springsteen told the Times that his team didn't vet the issue as closely as he should have, and that he "dropped the ball on it." Springsteen went on to say: "It was a mistake. Our batting average is usually very good, but we missed that one. Fans will call you on that stuff, as it should be." Springsteen released his new CD "Working on a Dream" this week and is performing the halftime show at the Super Bowl. http://www.courant.com/entertainment...,3742737.story  Free Monty Python Videos on Youtube Lead to 23,000% DVD Sale Increase Devindra Hardawar Following up on our previous news regarding Monty Python material on iTunes, Mashable is now reporting on a staggering increase of Monty Python DVDs sold on Amazon soon after the Python crew made all of their material free on Youtube. And by staggering, I mean 23,000% worth. Mashable notes that Monty Python’s DVDs climbed to the #2 spot on Amazon’s Movie’s and TV Bestseller List, and you don’t have to be a genius to follow that the sales were probably influenced by the Amazon links found on all of their Youtube clips. When launching their massive Youtube effort, Monty Python made their intentions fairly clear: “We’re letting you see absolutely everything for free. So there! But we want something in return. None of your driveling, mindless comments. Instead, we want you to click on the links, buy our movies & TV shows and soften our pain and disgust at being ripped off all these years.” With this news, it seems their “crazy plan” was a success—and why wouldn’t it be? After all, most of their sketch material is tailor made for the typical Youtube viewer, and it’s not as if they would have been better served by a traditional television marketing campaign. While I’m glad that the Monty Python crew is getting richer (they certainly deserve it), I’m more interested in what this massive success spells for the entertainment industry. Could it be, despite all of the RIAA and MPAA’s clamoring about piracy killing their business, that free and less restrictive content is actually the answer to their woes? We’ve seen other entertainment artists have similar success with free content, and it seems the music industry is finally wising up to DRM-free music, so it’s not as if the possibility is altogether foreign. Wired’s Chris Anderson argues this point in a recent cover story, and I would have to agree with him. At this point offering a certain amount of content for free (as we see on Hulu, Last.FM, and countless other sites and services) seems like one of the best ways to convince consumers to actually pay for media. All of this points to a simple, yet seemingly elusive, fact: Treating your consumers like criminals may not be the best way to convince them to buy your shit. Just sayin. http://www.slashfilm.com/2009/01/23/...sale-increase/  YouTube Close to Video Deal for Pro Talent Brian Stelter YouTube and the William Morris Agency, the Hollywood talent agency, are close to signing a deal that would place the company’s clients in made-for-the-Web productions. The deal would underscore the ways that distribution models are evolving on the Internet. Already, some actors and other celebrities are creating their own content for the Web, bypassing the often arduous process of developing a program for a television network. The YouTube deal would give William Morris clients an ownership stake in the videos they create for the Web site. Two people close to the talks, who spoke on condition of anonymity because they were not authorized by their companies to speak publicly about the deal, described the arrangement as YouTube’s most sweeping attempt to date to add professionally produced videos to its Web site, which mostly features amateur videos uploaded by users. The people cautioned that the deal had not been completed. Representatives for YouTube and William Morris declined to comment Wednesday evening. The addition of more videos by A-list actors, musicians and other stars would bolster YouTube’s identity as a next-generation entertainment source and, more important for the site’s parent company, Google, could help answer a riddle it is trying to solve: how to wring cash from the hundreds of millions of videos it hosts free. YouTube’s audience is enormous; the measurement firm comScore reported that 100 million viewers in the United States visited the site in October. But, in part because of copyright concerns, the site does not place ads on or next to user-uploaded videos. As a result, it makes money from only a fraction of the videos on the site — the ones that are posted by its partners, including media companies like CBS and Universal Music. The company has shown interest in becoming a home for premium video in recent months by upgrading its video player and adding full-length episodes of television shows. But some major television networks and other media companies are still hesitant about showing their content on the site. The Warner Music Group’s videos were removed from the site last month in a dispute over pay for its content. Fred Davis, a senior partner at Davis, Shapiro, Lewit & Hayes, an entertainment law firm that advises digital media companies including YouTube, said professionally produced content was especially important to companies like YouTube because it could attract users in ways that amateur productions could not. By becoming a partner with a talent agency, YouTube is demonstrating that it wants to be a major destination for Hollywood content. Its sponsorship of a live concert in November, YouTube Live, sent the same message. A deal with William Morris would be a significant step in that direction. The agency represents a number of prominent clients like the actors Denzel Washington and Russell Crowe and the producers J. J. Abrams and Michael Bay. Last week, the company signed former Secretary of State Condoleezza Rice as a client for potential book deals, speaking appearances and other projects. Mr. Davis said agencies like William Morris were “quite active” in cultivating creators for original projects for the Web. “Some of this talent are existing traditional media talent who are looking to expand into Web properties. Some talent will be using the Web as their first frontier,” he said. “Although everyone realizes that the monetization of this content is not quite there yet, everyone also realizes the huge potential as the digital media business matures.” http://www.nytimes.com/2009/01/29/bu...29youtube.html  National Geographic to Launch Record Label Nat Geo Music to release ‘modern music from around the globe.’ Dylan Stableford The National Geographic Society announced today that it will launch a full-service record label, Nat Geo Music—which also serves as the music division the company established in 2007. The label will “record, release and promote modern music from around the globe” from a variety of artists and genres, the company said, and be distributed globally through various distribution partnerships. Mat Whittington, a former record executive and concert promoter, has been tapped to head up the label, reporting to National Geographic Entertainment president David Beal. “Despite the challenging climate, there is an enormous appetite for music,” Whittington said in a release. “And we know that the National Geographic brand can deliver amazing new artists to this global audience.” The appetite for recorded music in the U.S., however, is shrinking. According to Nielsen Soundscan, which tracks retail sales data, album sales were down 14 percent in 2008. Music sales worldwide didn’t fare much better, falling about 7 percent, according to the International Federation of the Phonographic Industry. (Digital music downloads did grow last year, but at a slower rate than 2007.) National Geographic’s flagship magazine, meanwhile, saw ad pages fall 6.5 percent, according to the Publishers Information Bureau. (Ad pages for National Geographic Adventure and Kids fell 0.8 and 21.6 percent, respectively; National Geographic Traveler posted a 3.1 percent ad page gain. http://www.foliomag.com/2009/nationa...h-record-label  CBLDF To Serve As Special Consultant In PROTECT Act Manga Case The Comic Book Legal Defense Fund has signed on as a special consultant to the defense of Chistopher Handley, an Iowa collector who faces up to 20 years in prison for possession of manga. The Fund adds its First Amendment expertise to the case, managed by United Defense Group's Eric Chase, and will also be providing monetary support towards obtaining expert witnesses. Handley, 38, faces penalties under the PROTECT Act (18 U.S.C. Section 1466A) for allegedly possessing manga that the government claims to be obscene. The government alleges that the material includes drawings that they claim appear to be depictions of minors engaging in sexual conduct. No photographic content is at issue in Handley's case. "Handley's case is deeply troubling, because the government is prosecuting a private collector for possession of art," says CBLDF Executive Director Charles Brownstein. "In the past, CBLDF has had to defend the First Amendment rights of retailers and artists, but never before have we experienced the Federal Government attempting to strip a citizen of his freedom because he owned comic books. We will bring our best resources to bear in aiding Mr. Handley's counsel as they defend his freedom and the First Amendment rights of every art-loving citizen in this country." Mr. Handley's case began in May 2006 when he received an express mail package from Japan that contained seven Japanese comic books. That package was intercepted by the Postal Inspector, who applied for a search warrant after determining that the package contained cartoon images of objectionable content. Unaware that his materials were searched, Handley drove away from the post office and was followed by various law enforcement officers, who pulled him over and followed him to his home. Once there, agents from the Postal Inspector's office, Immigration and Customs Enforcement Agency, Special Agents from the Iowa Division of Criminal Investigation, and officers from the Glenwood Police Department seized Handley's collection of over 1,200 manga books or publications; and hundreds of DVDs, VHS tapes, laser disks; seven computers, and other documents. Though Handley's collection was comprised of hundreds of comics covering a wide spectrum of manga, the government is prosecuting images appearing in a small handful. Putting the case into context, Burton Joseph, CBLDF's Legal Counsel says, "In the lengthy time in which I have represented CBLDF and its clients, I have never encountered a situation where criminal prosecution was brought against a private consumer for possession of material for personal use in his own home. This prosecution has profound implications in limiting the First Amendment for art and artists, and comics in particular, that are on the cutting edge of creativity. It misunderstands the nature of avant-garde art in its historical perspective and is a perversion of anti-obscenity laws." Eric Chase and his team at the United Defense Group have been vigorously defending Handley, and scored a major First Amendment victory earlier this year when the judge found portions of the PROTECT Act unconstitutional in his ruling on a motion to dismiss. District Judge Gritzner of the Southern District of Iowa found that subsections 1466(a)(2) and (b)(2) of 18 U.S.C. 1466A unconstitutional. Those sections make it a crime to knowingly produce, distribute, receive, or possess with intent to distribute, "a visual depiction of any kind, including a drawing, cartoon, sculpture, or painting," that "is, or appears to be" a minor engaged in sexual conduct. Judge Gritzner found that those sections restrict protected speech and are constitutionally infirm. Handley now faces charges under the surviving sections of 1466A, which will require a jury to determine whether the drawings at issue are legally obscene. The material cannot be deemed obscene unless it meets all three of the criteria of the Miller test for obscenity: "(a) whether the average person, applying contemporary community standards would find that the work, taken as a whole, appeals to the prurient interest; (b) whether the work depicts or describes, in a patently offensive way, sexual conduct specifically defined by the applicable state law; and (c) whether the work, taken as a whole, lacks serious literary, artistic, political, or scientific value." The jury must answer all three questions in the affirmative in order to convict. Eric Chase recognized the importance of the case, and of the CBLDF's contribution to it, in a statement to the CBLDF: "This case represents the latest in a string of efforts by the Department of Justice to encroach on free speech. The United Defense Group is committed to fighting to maintain the protections guaranteed in the Constitution, and we appreciate the CBLDF's support in this fight." http://www.cbldf.org/pr/archives/000372.shtml  Judge's Ruling That WoW bot Violates DMCA is Troubling Glider, a popular WoW bot, took another hit on Wednesday as a federal judge ruled that the product went beyond copyright infringement to being a circumvention device under the DMCA. The decision raises serious questions about the legal status of interoperability and competition in the software industry. Timothy B. Lee Blizzard notched another victory in its legal campaign against World of Warcraft bots when a judge on Wednesday ruled that a leading bot violates the Digital Millennium Copyright Act. MDY Industries LLC, the firm that develops and sells the Glider bot, already suffered a major setback last summer when the judge granted Blizzard summary judgment on several key issues. This week's decision deals with the issues the judge believed could not be decided until the conclusion of this month's trial. The judge ruled that Glider violated the DMCA's ban on "circumvention devices," and he also found that MDY's founder, Michael Donnelly, was personally liable for the actions of his firm. As we've noted before, Blizzard's legal arguments, which Judge David G. Campbell largely accepted, could have far-reaching and troubling implications for the software industry. Donnelly is not the most sympathetic defendant, and some users may cheer the demise of a software vendor that helps users break the rules of Blizzard's wildly popular role playing game. But the sweeping language of Judge Campbell's decision, combined with his equally troubling decision last summer, creates a lot of new uncertainty for software vendors seeking to enter software markets dominated by entrenched incumbents and achieve interoperability with legacy platforms. DMCA hairsplitting World of Warcraft includes software called a "warden" that scans a user's computer looking for bots such as Glider. Blizzard contends that Glider violates the provision of the DMCA that prohibits "trafficking" in software that is "primarily designed or produced for the purpose of circumventing a technological measure that effectively controls access to a work" protected by copyright. Judge Campbell has distinguished between the actual bits stored on the World of Warcraft disk (which he called the "literal elements" of the game) and the interface elements the user encounters as he's actually playing the game (which he dubbed "non-literal elements"). In his ruling last summer, Judge Campbell ruled that Glider did not violate the DMCA with respect to the "literal elements" because Warden did not "effectively control" access to those elements: they are stored, unencrypted, on the World of Warcraft disk. But he deferred until this month's trial the question of whether Glider violated the DMCA with respect to the "non-literal elements." In Wednesday's ruling, Judge Campbell found that Warden did effectively control access to the "non-literal elements." That is, while Warden does not prevent users from accessing the individual elements of the game separately, it does effectively bar users from accessing all of the elements together while playing the game. Therefore, Judge Campbell concluded, MDY violated the DMCA when it evaded warden's checks. MDY argued that these "non-literal elements" did not constitute a distinct copyrighted work, and therefore could not trigger DMCA liability. The firm offered two arguments. First, the law only grants protection to works that are fixed in a tangible medium, and MDY argued that the "non-literal elements" were too ephemeral to qualify. The judge rejected this argument, holding that it was sufficient that the "non-literal elements" could be recorded by screen-capture software, even if Glider didn't actually do so. Second, MDY argued that the "non-literal elements" were not created solely by Blizzard, but by the interaction of Blizzard's software with the user. Hence, if the game experience was copyrighted, it would be the joint work of Blizzard and its users. The judge tersely rejected this argument as well. The other question Judge Campbell considered is whether Michael Donnelly, MDY's founder and Glider's author, should be personally liable for the infringing activities of his firm. Donnelly contended that because copyright is unclear in this area, and because he believed his conduct to be legal, that he should not be personally liable for the infringing activities of his firm. Judge Campbell rejected this argument, holding that Campbell was aware of his firm's actions and should have known that they were illegal. Ars talked to two legal experts at Public Knowledge, a public interest organization that filed an amicus brief in the MDY case last year. Staff attorney Sherwin Siy compared Wednesday's decisions to past decisions that tried to use the DMCA to limit competition in the garage door opener and printer industries. He noted that the purpose of warden seemed less to control access to a copyrighted work than to a network service—quite a different thing. Siy's colleague Jef Pearlman agreed, warning that if the courts weren't careful, we could end up in a situation where "because anything can contain copyrighted works, any access to anything becomes a DMCA violation." Siy and Pearlman also expressed skepticism at the notion that these "dynamic, non-literal elements" constitute a distinct copyrighted work. The in-game experience is assembled from a variety of disparate elements, including files already on the user's hard drive, instructions from Blizzard's server, and the decisions of the various players. Judge Campbell's ruling seems clearly out of step with the stated purpose of the DMCA. When Congress passed the DMCA in 1998, it was concerned with the specter of mass file-sharing on the Internet. Yet in this case, there is no file-sharing in sight. Glider is designed to be used by legitimate Blizzard customers who not only paid for their copies of World of Warcraft, but pay a monthly fee for access to Blizzard's servers as well. Blizzard is using the DMCA not to stop illicit file sharing, but as an all-purpose tool to control their users' behavior. Next stop: Ninth Circuit It's a safe bet that the ruling will be appealed to the United States Court of Appeals for the Ninth Circuit, the appeals court that has decided many key high-tech copyright cases. Although Wednesday's ruling will be among the issues considered by the Ninth Circuit, the core of the argument will likely focus on the issues Judge Campbell decided last summer, especially the relationship between copyright law and contract law. Blizzard argued, and Judge Campbell agreed, that when users violated the World of Warcraft EULA, they no longer had a license to play the game and were therefore guilty of copyright infringement. As Siy noted in a blog post last year, Blizzard's theory, if taken literally, would mean that violating any of the rules in the EULA and Terms of Service, such as choosing a screen name that didn't meet Blizzard's guidelines, would be an act of copyright infringement. And distributing software that helps users infringe copyright itself constitutes secondary copyright infringement, which could expose MDY to copyright law's draconian "statutory damages" of $150,000 per act of infringement. The law gives aggrieved parties to contract disputes much less potent powers. Copyright was never intended as an alternative mechanism for contract enforcement. If that theory is allowed to stand, it would dramatically strengthen end-user license agreements and create enormous liability for those who break them. That would eviscerate the first sale doctrine and create tremendous legal risks for firms and free software projects that reverse-engineered other firms' products for purposes of interoperability. MDY may not be the world's most sympathetic defendant, but there's a lot more at stake in this case than World of Warcraft bots. http://arstechnica.com/gaming/news/2...-troubling.ars  Sony and Toshiba Report Losses for Quarter Bettina Wassener Sony and Toshiba on Thursday reported losses for the last quarter, and Nintendo lowered its profit forecast, as the current earnings season revealed the extent of the erosion in corporate and consumer demand. Sony warned last week that it expects a full-year operating loss of 260 billion yen, or $2.9 billion, and announced it was doubling its cost savings measures, reflecting the urgency being felt by its chief executive, Howard Stringer, as the economic outlook worsens. The figures announced Thursday showed the bulk of the bleeding is taking place in its key electronics division. Sony’s operating loss for the quarter was nearly 18 billion yen, a 95 percent drop from the 236 billion yen profit a year earlier. Nearly 16 billion yen of that stemmed from the electronics division which includes the Sony television brands that have been suffering increasing competition. Toshiba announced an operating loss of 158.8 billion yen for the quarter, down from a profit of 42.1 billion yen a year earlier, and far worse than analysts had expected. Toshiba also warned that, for the full year ending March, it now expected an operating loss of 280 billion yen, rather than the 150 billion yen profit it had previously forecast. The games maker Nintendo also lowered its forecast, saying it now expected an operating profit of 530 billion yen rather than 630 billion yen. The announcements reflected the dilemma Japan’s export industry in the face of sagging demand in the shrinking Japanese, U.S. and European economies, worsened by a strong yen that makes Japanese goods more expensive abroad. Like much of the rest of the word, Japan has seen its recession deepen during the last three months of 2008 — recent trade data showed exports plummeted in December, down 35 percent from a year earlier — and most economists agree that a tangible recovery is now not on the cards until next year. Earlier on Thursday, the deputy governor of Japan’s central bank, Kiyohiko Nishimura, said he expected the economy to gradually recover from October, but warned of a possible delay, and cautioned that the steps taken by policy makers around the world to prop up ailing economies might not be enough. Continued market tensions and last year’s stock market rout also have made Japanese banks less willing to lend, hampering small and mid-sized businesses in particular. Japanese companies have been racing to cut output and lower costs, and more job cut announcement and profit warnings are expected to become a familiar feature of the current earnings season. Still, the magnitude of Sony’s profit warning last week — its second in three months -- surprised many observers Mr. Stringer used unusually strong language — and made a rare personal appearance at a press conference — to outline the extent of the challenges ahead and justify the painful cuts. Mr. Stringer, who took over in 2005 as the first non-Japanese executive leading the electronics and entertainment conglomerate, acknowledged that the company had been “putting off unpleasant decisions” and that it now had to “move in a hurry.” Over the past few years, the playing field has changed, with Sony now no longer competing solely against traditional Japanese electronics companies, but also against South Korean manufacturers like Samsung and LG Electronics, which have expanded their product portfolios. Those companies are also cushioned by the weak won, which makes those products cheaper in export markets. In addition, Mr. Stringer, hinting at infighting between divisions, stressed the need for speedier decision-making. “Too often we have been late to market with new products,” he said. “This practice cannot be tolerated going forward.” The main challenge, analysts say, is for Mr. Stringer to implement the changes. “They now need to do what they say,” said David Gibson, consumer electronics analyst at Macquarie in Tokyo. http://www.nytimes.com/2009/01/30/te...es/30sony.html  Watch Out Wikipedia, Here Comes Britannica 2.0 Stephen Hutcheon In a move to take on Wikipedia, the Encyclopedia Britannica is inviting the hoi polloi to edit, enhance and contribute to its online version. New features enabling the inclusion of this user-generated content will be rolled out on the encyclopedia's website over the next 24 hours, Britannica's president, Jorge Cauz, said in an interview today. He also used the opportunity to take a swipe at Britannica's upstart nemesis and Google for helping to promote Wikipedia via its search rankings. "If I were to be the CEO of Google or the founders of Google I would be very [displeased] that the best search engine in the world continues to provide as a first link, Wikipedia," he said."Is this the best they can do? Is this the best that [their] algorithm can do?" Mr Cauz, who is visiting Australia, said the changes were the first in a series of enhancements to the britannica.com website designed to encourage more community input to the 241-year-old institution and, in doing so, to take on Wikipedia in the all important search engine rankings. "What we are trying to do is shifting ... to a much more proactive role for the user and reader where the reader is not only going to learn from reading the article but by modifying the article and - importantly - by maybe creating his own content or her own content," he said. Mr Cauz said that any changes or additions made to Britannica entries online would have to be vetted by one of the company's staff or freelance editors before the changes were reflected on the live site. He said the encyclopedia had set a benchmark of a 20-minute turnaround to update the site with user-submitted edits to existing articles, which are written by the encyclopedia's paid expert contributors. Many of those changes will eventually appear in the printed version of the encyclopedia, which is published every two years. In addition to the community editing features, Britannica.com will enable approved users to add their own creative input which will sit beside the authorised articles. Wikipedia, which ranks among the world's top-10 most visited websites, is maintained by volunteers from all over the world and anyone with an internet connection can create and edit articles and publish them on the site. Would-be editors on the Britannica site will have to register using their real names and addresses before they are allowed to modify or write their own articles. Mr Cauz characterised Wikipedia as containing "plenty of cracks on it in terms of the quality". "It's very uneven, the facts are not always correct, the model contains a lot of pitfalls." Damning his competitor with faint praise, he said a big problem was that many users considered Wikipedia to be "fine" or "good enough". "What is really unfortunate is that when it comes to knowledge - which is really what makes humans evolve or not evolve into the future - we tend to be non-discriminating. And that's really the troublesome thing." Asked if he looks at Wikipedia, he said he spent several hours a day online. "I think it would be impossible not to look at Wikipedia when one goes to Google. It's the most symbiotic relationship happening out there," he said. "It's very much used by many people because it covers many topics and it's the No.1 search result on Google. It's not necessarily that people go to Wikipedia." (Google's PageRank search algorithm is designed to look for the most relevant and cited web page and often that happens to be a Wikipedia entry). Encyclopedia Britannica was first published in 1768 - two years before Captain James Cook's discovery of Australia. Founded in 1994, the Britannica.com's database contains articles comprising more than 46 million words - not counting other forms of media content. Founded in 2001, Wikipedia is now available in more than 250 languages and attracts about 700 million visitors annually. The English editon alone contains nearly 2.7 million articles. http://www.smh.com.au/articles/2009/...471469973.html  All Lies? Scientists Threatened with Legal Action Over Lie Detector Article Francisco Lacerda, a professor of phonetics at Stockholm University, is one of two scientists threatened with legal action after the publication of a scientific article condemning the use of lie detectors. The Israeli company Nemesysco, which manufactures detectors, has written in a letter to the researchers' publishers that the researchers may be sued for libel if they continue to write on this subject in the future. One year ago, Francisco Lacerda, a professor of linguistics at Stockholm University, and Anders Eriksson, professor of phonetics at the University of Gothenburg, published an article in the International Journal of Speech Language and the Law, a magazine for voice experts working for the police and security services. The article entitled "Charlatantry in forensic speech science" gave an overview of the last fifty years of research in the field of lie detectors. The article's conclusion is that there is no scientific evidence to show that lie detectors actually work. Article withdrawn In the autumn, Equinox, the British publisher of the magazine, were canvassed by the Israeli company Nemesysco Limited, a manufacturer of lie detectors. Following this the company demanded that the article be withdrawn, which the publishers duly did. In the online version of the journal only an abstract of the article is now available, along with a clarification from the publisher. "It is incredibly serious that they are trying to silence us in this way. I have never heard of anything like it. We have apparently damaged their business," says Francisco Lacerda to the Swedish newspaper Dagens Nyheter. The article was aimed directly at the company's lie detector patent," said Francisco Lacerda to Dagens Nyheter, "We showed that the invention cannot work. The article had a journalistic tone and was rather provocatively written. We wanted to prove that the technology behind the lie detector is a scam." Publisher faced with threat of prosecution In a letter to the publisher Nemesysco's lawyers wrote that the authors of the article could be sued for defamation if they wrote on the subject again. The publishers accepted the lawyers' angle on the article, "We would like to warn the authors that they should not publish the article in another forum and that if they send in a similar article to another journal, they can be sued for defamation," writes the publisher, cited by Dagens Nyheter. The letter was sent also to Francisco Lacerda and Anders Eriksson. "It's obviously very uncomfortable. We don't know where this may end. At the same time, it is my responsibility as a researcher to share my findings. The company has not put forward any counter arguments, but has chosen to simply try to silence us," says Francisco Lacerda. In a letter to the Dagens Nyheter newspaper Nemesysco write that the Swedish researchers slander the company. Pseudo-science "The biggest problem is the completely bizarre use that the authorities and insurance companies in Britain make of these pseudo-detectors. This situation has arisen because serious researchers, who, understandably, have not wanted to use their time to even respond to this obviously pseudo-science, have left the stage free for less careful players, who proclaim Nemesysco's message," says Francisco Lacerda to Stockholm University's editorial team. International media attention At the same time, Nemesysco's actions have led to even greater media attention for the two Swedish professors' research. "It was hardly their intention. But since the article was withdrawn, I have received lots of mail and requests for copies of the article. The article would not have been read to this extent if the company had simply ignored it in silence," says Francisco Lacerda to the http://www.su.se/english/about/news_...h_legal_action  Wife Murdered for Facebook Status Edward Richardson had sent text messages to his estranged wife A man murdered his estranged wife after becoming "enraged" when she changed her marital status on Facebook to "single". Edward Richardson, 41, of Mayfield Road, Biddulph, was found guilty of stabbing Sarah Richardson to death. He killed the 26-year-old hairdresser at her parents' home in Brown Lees, Staffordshire, on 12 May, 2008, Stafford Crown Court heard. Richardson tried to kill himself after the attack and was sentenced to life with a minimum of 17 years in prison. Fiona Cortese, of the Crown Prosecution Service, said: "Richardson became enraged when Sarah changed her marital status on Facebook to single and decided to go and see her as she was not responding to his messages. "He gained entry by breaking the front door window and made his way into the property. Sarah Richardson had worked as a hairdresser in Sandbach "Once inside he found Sarah in her bedroom and subjected her to a frenzied and brutal attack with a knife and then attempted to take his own life. "We hope that today's guilty verdict will go some way to easing the pain of Sarah's family and friends after losing her in such a violent and abrupt way." In a statement, Mrs Richardson's parents, Beryl and Alan Boote, said: "There simply aren't the words to describe how Sarah's death, and the awful way in which she died, has affected us. We all miss her so much. "Sarah was the loveliest daughter anyone could wish for. She was honest, loyal and sweet, and everyone loved her." http://news.bbc.co.uk/2/hi/uk_news/e...re/7845946.stm  White House Exempts YouTube from Privacy Rules Chris Soghoian Update: 12 hours after posting this story, the White House (partially) reversed itself. The rather dubious YouTube-only waiver from federal Web privacy rules has been maintained, but the White House Web site has been updated to limit the exposure of visitors to YouTube's tracking efforts to only those people who actually click the "play" button on a YouTube video. For more details on the new changes, read this blog post. The new Web site for Obama's White House is already drawing attention from privacy activists and tech bloggers. While the initial focus has been on the site's policies relating to search engine robots, a far more interesting tidbit has so far escaped the public eye: the White House has quietly exempted YouTube from strict rules relating to the use of cookies on federal agency Web sites. The new White House Web site privacy policy promises that the site will not use long-term tracking cookies, complying with a decade-old rule prohibiting such user tracking by federal agencies. However, the privacy policy then reveals that Obama's legal team has exempted YouTube from this rule (YouTube videos are embedded at various places around the White House Web site). While the White House might not be tracking visitors, the Google-owned video sharing site is free to use persistent cookies to track the browsing behavior of millions of visitors to Obama's home in cyberspace. No other company has been singled out and rewarded with such a waiver. In a blog post back in November, I criticized the Obama transition team's Change.gov Web site for its use of embedded YouTube videos. At the time, I stated that the practice might violate long-standing federal rules that forbid federal agencies from using persistent tracking cookies on their Web sites. It turns out that I was wrong: the transition team was technically not a federal agency and thus not bound by the anti-cookie rules. Now that Obama is president, his official Web site is required to abide by the cookie regulations. Furthermore, as of Wednesday afternoon, several YouTube videos have been embedded on the White House blog. As soon as a visitor surfs to one of the blog pages that contain a YouTube video, a long-term tracking cookie is automatically set in the user's browser--even for those users who do not click the "play" button. Someone on the Obama legal team seems to have read my previous blog post, as they've modified the White House privacy policy to specifically exclude YouTube's tracking cookies from federal rules that would otherwise prohibit their use: "For videos that are visible on WhiteHouse.gov, a 'persistent cookie' is set by third party providers when you click to play the video. This persistent cookie is used by YouTube to help maintain the integrity of video statistics. A waiver has been issued by the White House Counsel's office to allow for the use of this persistent cookie." YouTube and cookies Each time a new user visits YouTube, a unique permanent tracking cookie is issued by the Web site to the user's browser, which it stores. Whenever the user later revisits YouTube, that cookie is transmitted to the video-sharing site, allowing it to identify users and monitor their video viewing habits. YouTube is also able to set and access a user's tracking cookie when she visits a third-party Web page that has embedded a video stored on the YouTube site (such as a blog or other Web site), even if the user never clicks the play button. The moment that the flash file containing the video player is downloaded from YouTube's servers and displayed in the user's browser as part of another Web page, the cookie is transmitted to YouTube's servers. Considering how widespread the practice of embedding YouTube videos has become, this gives Google an amazing amount of data on the Web-browsing activities of hundreds of millions of Internet users--many of whom may not realize that such tracking data is being collected. The White House policy is not being followed The YouTube-related text in the new White House privacy policy implies that not all users will be tracked by YouTube. The policy notes that: "If you would like to view a video without the use of persistent cookies, a link to download the video file is typically provided just below the video." As of Thursday morning, this statement is false. In multiple tests by this blogger with both Internet Explorer and Firefox, merely visiting pages on the White House blog causes YouTube to set a long-term tracking cookie in the browser--even if the user does not press the play button to start the video. After eight months, this cookie will be automatically deleted by the user's browser--unless, of course, the user visits another Web page somewhere else on the Internet containing a YouTube-embedded video, in which case, the eight-month cookie clock is reset. Given how widespread YouTube video embeds have become, this cookie essentially lasts forever. While it is obvious that I am rather critical of this entire affair, I am willing to give the Obama Web team the benefit of the doubt in one area: the fact that their current Web infrastructure does not deliver on the promises made by their privacy policy. The Obama White House Web site is only two days old, and so it is certainly possible that the team simply hasn't gotten around to deploying a more privacy-preserving system for YouTube video embeds. Protecting users who do not click "play" from automatically receiving a cookie is certainly possible; the Electronic Frontier Foundation in 2008 released a wrapper script for YouTube videos that provided this very feature. Let us hope that the Obama team deploys such a technology in due course. Can YouTube be justified as a "compelling need"? For the past 10 years, federal agencies have been prohibited from using tracking cookies on their Web sites, except in a few special cases. The Office of Management and Budget rule M-03-22 states that: "Agencies are prohibited from using persistent cookies or any other means (e.g., web beacons) to track visitors' activity on the Internet except .... [when there is] a compelling need." The question we must now focus on is this: Is the need for Obama to use embedded videos hosted by YouTube (and not, say, another company's video-streaming platform that does not force cookies upon its users) a use that can be reasonably described as compelling? Presumably, this has been justified on the basis that YouTube forces cookies on the visitors of any Web site that embeds one of its videos. However, while Joe or Jane blogger has no bargaining power with YouTube/Google, the federal government certainly does. In just the past couple weeks, YouTube has launched dedicated pages for both the House and Senate to show off their own videos, and the site also recently started allowing users to directly download copies of some videos. This latter feature has not yet been widely deployed across the site, and is seems to be limited to videos posted by Obama's team. Given the famously close connections between Obama and Google, you'd think his tech team could negotiate for a cookie-less way to embed videos. At a technical level, this would be an easy enough change, even if it would deny Google the ability to collect even more information on millions of Americans. Cookies and other federal agencies Finally, the new White House YouTube rule may have a far broader impact on the way that federal agencies use Web 2.0 content. Simply put, if another federal agency embeds a YouTube video in its Web site without first having the agency's legal team issue a waiver, have federal rules been violated? Up until this week, federal agencies have been free to embed Web 2.0 content in their own sites without any real need to consider the privacy risks posed to end users. The fact that the White House Counsel has felt it necessary to issue such a waiver for YouTube videos appearing on the White House Web page could be reasonably interpreted to mean that such a waiver is now required for all embedded Web 2.0 content that might force cookies upon end users. This is certainly new legal ground. Consider, for example, the Transportation Security Administration, which has posted YouTube videos to its blog numerous times over the past year. Its privacy policy makes no mention of YouTube cookies. Could this lead to issues for the TSA Web team, or perhaps even congressional investigations? Given my own history with TSA, I certainly hope so. http://news.cnet.com/8301-13739_3-10147726-46.html  A Look at the Evolving Laptop Display Rob Galbraith In July 2007, we wrote an assessment of the matte display in the MacBook Pro 15 inch. At the time, Apple was beginning the transition to LED backlights in its laptop line, and what we found was the display was incrementally better than the company's previous offerings in this size and offered a decent platform for assessing and doing basic adjusting of pictures in the field. In short, the screen was good and it responded well to hardware profiling but overall accuracy was a couple of notches below a good desktop display. Still, we concluded that Apple was making one of the finest laptop screens we'd seen for use in a pro digital photography workflow. Eighteen months have elapsed since then, and the laptop display landscape has changed plenty. Apple has switched to a glossy-only display design for most of its portable lineup, Lenovo has released a laptop with a screen calibrator built into the palmrest while netbooks have evolved into surprisingly useful tools for some types of photography. To that end, we've gathered and tested the displays in three current laptops: the late-2008 MacBook Pro 15 inch, Lenovo ThinkPad W700 and Dell Inspiron Mini 9. Well, make that four laptops. Rounding out the testing is the IBM/Lenovo ThinkPad T60, whose 1400 x 1050 pixel FlexView display has nearly a cult following among laptop afficionados. While discontinued - and not always readily available when it was still officially an option - this laptop's display is so well regarded by those outside the world of photography that when we needed to replace a Windows laptop in the fall of 2007, we opted for this computer with this screen. If only to see what all the fuss was about. What follows is an assessment of the screens in these four road machines, done in a manner similar to our July 2007 report. We looked at a total of 81 pictures, gathered over time to evaluate computer displays, both desktop and laptop. The photos themselves are a mix of black and white and colour, some with muted shades and some that are richly saturated, some that are moody and some that are high key. Several of the photos are in three different colour spaces - sRGB, Adobe RGB and ProPhoto RGB. In all cases the displays were profiled with a monitor profiling package consisting of a colorimeter or spectrophotometer for screen measurements and software to create the profile. The profiling tools we used are described at the end of the article. The key point to remember for now is that we did all evaluations with a profile loaded that produced the best result, so that each display was putting its best foot forward. Our reference monitor was an Eizo ColorEdge CE240W, a colour-accurate desktop monitor that has been an essential part of our photo viewing, editing and printing workflow for some time. Apple MacBook Pro 15 inch Released in the fourth quarter of 2008, this computer's display incorporates an all-glass front designed to minimize flex in the lid. And that it does, as the lid is both impressively thin and impressively rigid. The rest of this portable computer is typical of the current Apple: it's sleek, skinny and beautiful to behold. Unfortunately, at least from a photographer's perspective, a few things were lost in the transition to the sleek new design, including a FireWire 400 port, one USB 2.0 port and a matte display option. Aperture and Photoshop CS4 users will appreciate the beefier graphics subsystem, while the keyboard and trackpad are nice. Outside of that, there's little in the way of real innovation in this model that specifically targets or benefits the field shooter. But it's still a Mac. This means it's well put together and it runs the Mac OS plus various Mac-only applications, which for some - including us - is a benefit. This also means we needed to see if its glossy screen was both tolerable to use, profilable and at least on par with the quality of the previous generation MacBook Pro 15 inch. The result is a mix of good news and bad news. Starting on a positive note, the display quality is comparable to what we've seen before in earlier editions of the LED-backlit MacBook Pro 15 inch. Screen brightness is impressively even, as is black and white photo rendering, while overall colour accuracy is decent. Deep shadow posterization, a common laptop screen problem, is present but kept to a minimum. The only significant colour error is in reds and oranges, which are considerably skewed in both hue and saturation and really don't look right on this display. Secondarily, and far less noticeable, are slight yellow and blue shifts in open shadows. The above assumes a fixed, head-on viewing position. Gazing at the screen from a higher or lower angle produces a noticeable skin tone colour and brightness shift, while a yellow cast intrudes when looking in from the left or right. Sum it up, and what you have is a very good 15.4 inch (diagonal), 1440 x 900 pixel screen. Good, that is, for a laptop. Its characteristics are very similar to the MacBook Pro 15 inch we wrote about in July 2007, and others we've set up since. The display has some colour quirks that put it one or two steps below a good desktop display, and it's important to maintain a consistent, front-and-centre viewing angle, but as with the previous generation of this Apple laptop, display quality is absolutely acceptable and usable for image assessment and simple Photoshop edits in the field, as long as you're aware of the display's particular blend of strengths and weaknesses. And as long as the ambient light is subdued. The glass sheet in front of the screen is about as reflective as it could be, which means that in a coffee shop, on an airplane or even a typical office, the glossiness is either a minor irritant or a major distraction, depending on the surroundings and your tolerance for screen reflections. During testing we used the late-2008 MacBook Pro 15 inch in all three environments, and that was enough to conclude that it's not for us. This is not the first glossy laptop display of this size we've used, but it's by far the most reflective. If you roll your cursor over the photo below, you'll see an example of this in an environment that rates as only mildly reflective, and the resulting reflections are at the minor irritant level. In an airplane with a mix of window shades open and closed, for example, the reflections become much worse, obscuring sections of not just darker photos but all photos, as well as the Photoshop panels and other interface elements around the periphery. It's a major distraction. All in all, the late-2008 MacBook Pro 15 inch has a decent, profilable display, much like the previous generation of this model, but is marred by an omnipresent glare from its mirror-like front. Note: Some online sleuthing turns up the fact that Apple may be sourcing display panels for this Mac from more than one manufacturer. The panel in the unit we tested is model "9C84" (as described in the metadata of its default monitor profile), while there are apparently units of the same Mac with "9C85" panels. Do these two different panels also differ in display quality and profilability? We don't know. If you must have this computer, or you've already taken the plunge and find that you can't get comfortable with its ultraglossy display, you may wish to investigate TechRestore's matte screen alternative. The U.S.-based computer repair outfit's US$199 service sees the glass front removed and the glossy panel underneath replaced with a matte panel and bezel surround. We saw the result, nicknamed the MatteBook Pro by the company, earlier this month at the Macworld Expo trade show in San Francisco, and it looks really well done. A representative said that the matte panel they swap in is the same as the one they take out, except for the glossy finish (though this doesn't necessarily guarantee that the display's characteristics will be an exact match or that it will respond the same way to profiling). A lower-tech option is a matte screen protector, such as Anti-Glare Film from Power Support. Dell Inspiron Mini 9 We ordered this netbook a couple of months ago because it was the right size, weight and price to tote along on remote camera installations, where a laptop can be an invaluable tool in confirming that the wireless link is a-ok, that the camera is positioned and configured correctly and so on. But it can be a pain, if not downright impractical on occasion, to drag along a full-size laptop for this. When the Inspiron Mini 9 arrived, it quickly became clear it was going to be useful for a lot more than setting up remotes. This pint-sized wonder has sufficient oomph for a variety of tasks, and once we got it outfitted with 2GB RAM and a 32GB SSD it has become a constant companion that we've used to import, select and transmit JPEGs, edit short video clips plus the usual netbook stuff like email, web browsing and even video chats using the built-in camera. Its 1.6GHz Intel Atom-series processor chokes on RAW conversions - it'll do them, if you're really patient - but for photo browsing and basic image editing steps the performance is okay. Rounding out this featherweight computer are three USB ports (which are fast for USB in our testing), 802.11g Wi-Fi, 10/100 Ethernet, VGA monitor out and Bluetooth. The only truly bothersome feature of the Mini 9 that's brought about by its small size has been the cramped keyboard, and that's mostly because of the odd placement of the right Shift key. To have a computer this capable, that is also small enough and light enough to slip into pretty much any camera bag, it has been a workflow-altering experience. Thanks in part to the Mini 9, I've personally switched to using the Think Tank Photo Streetwalker Pro for light duty gear carrying. As you can see in the photo below, the diminutive Dell slips easily into this compact, narrow photo backpack and leaves plenty of room for a carry-about camera kit (the Mini 9 is on the left side of the bag in the photo on the right). Our infatuation with the Mini 9 extends to its 8.9 inch (diagonal), 1024 x 600 pixel, LED-backlit display. For a computer that starts at about US$300 in the U.S. right now, we had modest expectations. As it turns out, the display profiles well, neutrals are reasonably neutral with minimal colour shifting in whites, grays or blacks and overall colour accuracy is very good for a laptop. Overall hue accuracy, in fact, is better than the late-2008 MacBook Pro 15 inch. The only real colour hangups are oversaturated reds and oranges, including skin tones to some extent, plus there's a slight pink shift in lighter reds. Some shadow posterization is visible too, but it's not significant. All in all, this display is delivering more quality than one could reasonably hope for from a machine in this price class. You won't see the fairly rosy picture being described above unless you're looking straight at the screen. The Mini 9's optimum viewing position is the only position in which you get the screen's full goodness. Bad things happen when the viewing angle shifts up, down, left or right, with the up/down angles bringing about big brightness and colour shifts. The left/right viewing angles are more forgiving, to a point; exceed a certain angle and image reversal kicks in. There is also some unevenness in brightness top to bottom, though this is mitigated by the fact the screen isn't terribly tall. Other than the restrictive viewing position, the only other sign the Mini 9 contains an inexpensive panel is the pronounced ghosting when moving windows around. This doesn't, however, impact how photos look on the display (nor does it impair the watching of movies). Like the late-2008 MacBook Pro 15 inch, the Mini 9's display is glossy, and it's not available in a matte surface. The small size of the screen, and its comparatively duller glossiness, means that reflections are less of a problem. That's understating it: most of the time we're not even aware of its gloss, let alone bothered by it. The Mini 9 is a low-budget gem for a number of reasons, including its photography-friendly LED-backlit display. IBM/Lenovo ThinkPad T60 The ThinkPad series from Lenovo is their business laptop line. Trouble is, somebody forgot to mention that to the designers, because both the T60, and the W700 discussed next, incorporate displays geared to pro photography. In its heyday back in 2006-2007, the T60 could be configured with a 14.1 inch, 1400 x 1050 pixel, matte-surface FlexView display featuring in-plane switching (IPS) panel technology. Why does the panel technology matter? Briefly, there are three broad categories of LCD panel types: twisted nematic (TN), vertical alignment (VA, and variants like PVA and MVA) and IPS. Each has different strengths, with IPS panels generally providing good colour reproduction and the widest viewing angles. We know of no IPS screens in current-model laptops, ThinkPads or otherwise, and it's a shame, because our T60's FlexView display has some killer attributes. They include: • Even screen brightness There is slight darkening in the upper corners, otherwise it's about as even from edge to edge as a better quality desktop display. • Nearly perfect neutrals Our Eizo ColorEdge 240W is almost entirely free of noticeable colour casts from black to white, and the T60's FlexView display nearly matches the Eizo. It's easily the best laptop screen we've encountered for viewing black-and-white photos. • Wide, wide viewing angle Like all laptop displays, this one has a viewing position sweet spot. Move your head a bit away from that sweet spot and photos appear darker and flatter. But only slightly, the shift is quite subtle. Move your head far away from the sweet spot and photos retain their slightly darker and slightly flatter appearance. In fact, looking from the extreme left, extreme right or practically straight down, the onscreen appearance of a picture doesn't really change from being slightly darker and slightly flatter than the straight-on view. Trying placing a print in front your laptop's display, then viewing that from a variety of angles, and you'll have an idea of how wide this display's viewing angle is. It's really cool. Colour accuracy is also very good, but not quite at the level of the three attributes listed above. That's for one reason: reds are much too saturated, by approximately 20 points or so in some photos. Also, we're not sure how much longer this monitor is going to deliver the goods. That's because maximum screen luminance, which was at about 180 cd/m2 when we got it, has already faded to about 135cd/m2, and once it dips below about 110 cd/m2 it will be getting too dim to be usable for accurate photo viewing in anything other than low ambient light. Overall, the ThinkPad T60's 1400 x 1050 pixel FlexView display is sweet, and it set a new standard in laptop displays in its time. A purchase of a used T60 equipped with this same display, however, may not be the best idea, unless you can find one with a backlight that hasn't faded much. Lenovo ThinkPad W700 Last but definitely not least is the ThinkPad W700. The W700 is Lenovo's effort to create a notebook computer that would have the key features photographers told them they wanted, from fast RAW conversions to a built-in CompactFlash reader and everything in-between. And Lenovo has delivered: the W700 is a powerful photo processing machine that, when tricked out with all the options, includes a 2.53GHz Intel Core 2 Quad Extreme processor, 8GB RAM, NVIDIA Quadro FX 3700M graphics, 17 inch (diagonal), 1920 x 1200 pixel, matte-surface display with dual fluorescent (CCFL) backlights, twin RAID-configured hard drives, three video out ports (VGA, Dual-Link DVI and DisplayPort), CompactFlash slot, ExpressCard 34 slot, a miniature Wacom tablet and a custom HueyPro calibrator in the palmrest. The W700ds variant adds a 10.6 inch, 768 x 1280 pixel LED-backlit second display that slides out from behind the main one. Accessorize: The optional CompactFlash slot. Click photo to enlarge (Photo by Rob Galbraith/Little Guy Media) Hands On: The W700's trackpad, optional built-in calibrator and Wacom tablet. Click photo to see a larger view of the built-in calibrator (Photo by Rob Galbraith/Little Guy Media) It sounds like a photographer's dream come true. But be careful what you wish for: by giving photographers almost everything on their wish list, Lenovo has created a PC that is so darned big it seriously stretches the definition of a portable computer. Some wide angle perspective distortion in the photo leading off this article underplays its size. A truer photo of the ThinkPad W700 is below, with a Mini 9 for scale. This is a computer to enjoy in the office, hotel room or at the event, but is too unwieldy for use on most planes, trains and automobiles that you might take to travel to these places. The ThinkPad W700 is the antithesis of the Mini 9. So yes, we're not crazy about the size. Whatever criticisms we have about that, however, melt away when the computer is switched on and a photo is opened across its 17 inch display. Unlike every other laptop we've ever looked at, the W700 shows no significant colour accuracy errors at all, is only a touch less neutral through white, grey and black than the T60 FlexView and reveals just a hint of deep shadow posterization. Overall colour accuracy is on par with a fine desktop display. Coaxing the display to give this level of accuracy is simple, thanks to the built-in Pantone calibrator (which is an embedded version of a Huey colorimeter utilizing a custom filter set tuned to the W700 display). Profiling is as easy as launching the included hueyPro application, closing the lid, waiting 70 seconds for three short beeps to signal the end of the measurement process, opening the lid, choosing a colour temperature and gamma and that's it. From the time you think of profiling the display to the time you're done is three minutes, tops. As you'll read in the testing notes section ahead, we worked through a handful of monitor profiling packages with each computer. We set out to do the same with the W700, but once we saw how good the results were from the built-in Huey we couldn't think of a compelling enough reason to continue. The calibrator is a US$70 option. It's worth all of that and more. The screen is also exceptionally sharp. This is explained partly by its 1920 x 1200 pixel resolution; that's a lot of pixels to stuff into a 17 inch (diagonal) display, which means each pixel is particularly small. Its contrastiness is also a contributing factor. But there's something else good going on in this display that makes sharp pictures and text look especially edgy. The Mini 9 and ThinkPad T60 also have sharp displays, while the late-2008 MacBook Pro 15 inch's display is slightly softer. All three, however, don't look as superbly crisp as the W700. The W700's display is really, really good, but it's not perfect. We've not been able to find out what kind of panel it uses, but Wes Williams, Worldwide ThinkPad Product Marketing Manager at Lenovo, was able to tell us what it's not: IPS. This probably partly explains the areas in which it trails the T60's FlexView display, including: • Screen unevenness The W700's display darkens noticeably in the upper corners, and has an overly light strip that runs almost the full width of the lower edge. For evenness, this display is average at best. • Colour shifts with viewing angle Changing your head position up or down brings about an obvious change in skin tones (and anything else in the red/yellow/orange range), while a yellowy-red cast intrudes when looking at the screen from the extreme left or right. That said, the colour shifts in this screen brought on by a change in viewing angle we'd rank as being less than most, even if the T60's FlexView display is better. The W700 has many fine features for photographers, but the standout feature is the combination of its display and easy-to-use embedded calibrator (we say more about the calibrator and its software in the testing notes section on the next page). Note: the W700 is available with either a standard 17 inch display (called 17" WXGA+ LCD 200 NIT on Lenovo's order pages) or the twin-backlight premium one we tested (which goes by 17" WUXGA 400NIT TFT). Also note that we haven't tested the slide-out second screen of the W700ds. Conclusion For the longest time, Apple laptop displays ruled the roost around here. With very few exceptions, going back to the days of the PowerBook G4, portable Macs were considerably more colour accurate than any of the dozens and dozens of PC laptops we'd profiled during workshops and on-site training. The difference between Apple gear and everybody else's was stark. Thanks to Lenovo, however, and Apple's decision to standardize on the glossiest of glossy screens (only the soon-to-be-shipping MacBook Pro 17 inch will be available in what Apple calls an "antiglare" version), Macs are no longer at the top of the laptop display heap in our minds. The late-2008 MacBook Pro 15 inch doesn't top the rankings in this test, that much is obvious. But, which computer's display rates the best, and where the other three fall, is dependent on how comfortable you are with getting your head into the display's best viewing position each time you want to make colour critical decisions. We would choose a colour accurate display with a more restricted viewing position over one that showed some colour errors but allowed more viewing position flexibility. You, on the other hand, may favour a more forgiving viewing angle and can live with a few shades that are not right. Neither approach is the better one, but you do have to have an opinion about this for these rankings to hold much meaning, since you can have a really wide viewing angle or really good colour accuracy, but not both in the same laptop screen in this test. Ordering the displays with an emphasis on colour accuracy, the list looks like this: 1. Lenovo ThinkPad W700 2. IBM/Lenovo ThinkPad T60 3. Dell Inspiron Mini 9 4. Apple late-2008 MacBook Pro 15 inch 5. Ordering the displays with an emphasis on viewing angle flexibility, the list becomes: 6. IBM/Lenovo ThinkPad T60 7. Lenovo ThinkPad W700 8. Apple late-2008 MacBook Pro 15 inch 9. Dell Inspiron Mini 9 It's important to remember that, even though the late-2008 MacBook Pro 15 inch doesn't keep up in either colour accuracy or viewing angle with laptops from IBM/Lenovo, its display is still quite good and still falls on the right side of the line of acceptable display quality for field use by a working photographer, at least in ambient light that discourages reflections. When we wrote about this in July 2007, we said that evaluating laptop displays "means not worrying too much about subtle colour errors and instead looking out for display weaknesses that could cause mistakes like selecting a less-than-optimum white balance during RAW conversion, making a tonal adjustment in Photoshop that renders the picture lighter or darker than it ought to be or correcting for an apparent hue problem that doesn't actual exist in the picture, only in how the screen displays the picture." In other words, when we do these types of evaluations, a laptop screen with a small handful of display quality limitations is acceptable. And as it happens, all four of the screens in this test fall into that category. Well, with the same dim-lighting proviso mentioned several times already. In ambient light environments which induce screen reflections, the late-2008 MacBook Pro 15 inch's glossy screen moves deep into the not acceptable category. If you yearn for a laptop display that rises above acceptable, one whose colour accuracy matches a good desktop display, there's only one in this test: the ThinkPad W700. In fact, for us, it could just about replace a desktop display for colour critical work and even soft proofing for print in Photoshop (a task that lays bare any weirdnesses in a screen and its monitor profile). Just about, but not quite: Practically any good 24 inch desktop monitor (that is, one with the same 1920 x 1200 pixel resolution) will eclipse the W700 in screen evenness and viewing angle flexibility, including the Eizo ColorEdge CE240W used as the reference monitor for this article. So, given the budget, a separate external monitor will still be desirable. The fact that the W700's screen can even be discussed as a possible desktop screen replacement, though, is a testament to what Lenovo has achieved. On balance, it's the best laptop display we've ever seen, rivaled only by the ThinkPad T60 and its 1400 x 1050 pixel FlexView display from a couple of years ago. Coming up the middle is the Dell Inspiron Mini 9, the laptop whose price tag should mean it can't compete on screen quality, but somehow does. For those who can accept that its usable viewing angle is quite narrow, it rewards with surprisingly good colour accuracy. Testing notes Two of the computers in this article are ones we own, the other two are on extended loan, which means we've had time to profile most with a full range of monitor profiling tools as well as use all four of them at home, on the road and in the air. Measure Up: From left to right, the Datacolor Spyder 3, X-Rite ColorMunki, X-Rite Eye-One Pro and X-Rite DTP-94 (Photo by Rob Galbraith/Little Guy Media) Profiling The sensor + software combinations we employed to profile the late-2008 MacBook Pro 15 inch, Dell Inspiron Mini 9 and IBM/Lenovo ThinkPad T60 are (white point, gamma and white luminance is in parentheses): • Datacolor Spyder3 colorimeter and Spyder3ELITE (6000K, 2.2, max. luminance and 120cd/m2) • X-Rite DTP-94 colorimeter and ColorEyes Display Pro (6000K, L*, max. luminance and 120cd/m2, both 16 bit and matrix profiles) • X-Rite Eye-One Pro spectrophotometer and ColorEyes Display Pro (6000K, L*, max. luminance and 120cd/m2, both 16 bit and matrix profiles) • X-Rite Eye-One Pro spectrophotometer and Eye-One Match (6000K, 2.2, max. luminance and 120cd/m2, Laptop mode) • X-Rite ColorMunki spectrophotometer and ColorMunki Photo (6500K, 2.2, max. luminance) And for the ThinkPad W700: • Built-in calibrator with included hueyPro (6500K, 2.2, max.luminance) • X-Rite Eye-One Pro spectrophotometer and Eye-One Match (6500K, 2.2, max. luminance and 120cd/m2, LCD and Laptop modes) The best profile for the late-2008 MacBook Pro 15 inch was generated with the X-Rite Eye-One Pro spectrophotometer and Eye-One Match, followed closely by the same instrument with ColorEyes Display Pro. Strangely, the Eye-One Pro wouldn't work with this computer - it would lose the connection to the Mac after the instrument's calibration step - unless we connected it through a USB hub. The best profile for the ThinkPad T60 was generated with the X-Rite Eye-One Pro spectrophotometer and ColorEyes Display Pro software, followed closely by the same instrument with Eye-One Match. The best profile for the Dell Inspiron Mini 9 was generated with the X-Rite Eye-One Pro spectrophotometer and Eye-One Match software. We don't want to turn this into a monitor profiler review. It's worth noting, though, that while monitor profiling hardware and software has improved immensely over the years, there are still differences between the packages. If we were forced to choose only one combination to use on all desktop displays, it would be the X-Rite Eye-One Pro spectrophotometer and ColorEyes Display Pro. For most laptops it would be the X-Rite Eye-One Pro spectrophotometer and Eye-One Match, because this program's laptop mode conjures up a decent profile even from so-so laptop screens. But for the W700, the optional built-in calibrator is extremely easy to use, makes a first-class profile, and on an otherwise pricey machine it's a mere US$70 option in the U.S. It's a testament to how well a low-cost sensor can be made to work when its designers have the opportunity to tweak it for a specific display. Improving a good thing That said, in the name of ease of use the W700's hueyPro software has forsaken a key feature: calibrating the display to a specific white luminance value. The software forces screen brightness to maximum luminance before profiling (you see the computer's brightness indicator appear on screen briefly when this happens), and thereafter doesn't provide a way to target a white luminance value. Assuming typical office lighting, leaving the screen at full brightness means photos will appear noticeably lighter and more contrasty than they actually are; bringing down white luminance is a must to achieve the level of colour accuracy this display can deliver. This means some manual intervention is necessary after the profile has been created if you want to run the display at, for example, a more realistic white luminance of 120cd/m2. Turning the screen brightness down isn't difficult to do, but how much to dim it will be a wild guess if you don't have an alternate sensor and software you can use to measure white luminance with. To do this, we started up Eye-One Match on another computer, placed the Eye-One Pro on the W700's display and then proceeded to figure out that three presses of the brightness down function key gets white luminance in the ballpark at about 130cd/m2. As the backlights fade over time, though, so too will the amount of screen brightness adjustment needed, so this is only a temporary guideline (and one that may not be correct for your W700, depending on the age of its backlights). Alternatively, you could gradually turn down the brightness while comparing the same photo on the W700's display with a display connected to some other computer (obviously, this works only if that display is colour accurate and has been properly set to the white luminance value you're aiming for). Both are clunky workarounds to replace a feature that should be in the software, but isn't. Gamuts Three dimensional gamut renderings for each display are below. Roll your cursor over each one to see a comparison with the sRGB colour space. Turn up the Volume: Three dimensional gamut renderings of the four displays discussed in this article A display's gamut volume is one piece of information about its capabilities, one that can easily be misinterpreted or overinterpreted. The W700's gamut is the largest of the four, which fits with Lenovo's claim that its twin CCFL backlights offer a wider gamut than most laptop displays. In fact, this is the first laptop we've seen whose gamut nearly matches sRGB - most are much smaller. So, the W700's comparatively wide gamut is one of the explanations for its stellar colour accuracy, and the gamut rendering backs that up. On the other hand, the late-2008 MacBook Pro's gamut volume exceeds that of the Mini 9, but in reality it's the latter computer's display that is more colour accurate. How the display responds to profiling, and where the display places the colours within its available gamut, has a greater impact on how true its colours appear. The gamut renderings are included here by popular request. Beware of placing too much emphasis on them, as they are not a reliable indicator of a screen's ability to present colours accurately. They simply show its gamut. Final caution Similarly, you'll want to not put too much emphasis on how the quarterback portrait looks in the photos of the laptop displays in this article. That is, you won't be able to match up our comments about the display characteristics with what you see in the pictures, because shooting angles, lighting and the vagaries of trying to make a picture of a picture on a computer screen all prevent that. The real photo is below, so you can see what the colours in it actually look like. As long as you have a good monitor and good profile for it of course! http://www.robgalbraith.com/bins/mul...9320-9876-9881  Rs 500 Laptop Display on Feb 3 Akshaya Mukul NEW DELHI: A $10 laptop (Rs 500) prototype, with 2 GB RAM capacity, would be on display in Tirupati on February 3 when the National Mission on Education through Information and Communication Techology is launched. The $10 laptop project, first reported in TOI three years ago, has come as an answer to the $100 laptop of MIT's Nicholas Negroponte that he was trying to hardsell to India. The $10 laptop has come out of the drawing board stage due to work put in by students of Vellore Institute of Technology, scientists in Indian Institute of Science, Bangalore, IIT-Madras and involvement of PSUs like Semiconductor Complex. “At this stage, the price is working out to be $20 but with mass production it is bound to come down,” R P Agarwal, secretary, higher education said. Apart from questioning the technology of $100 laptops, the main reason for HRD ministry's resistance to Negroponte's One Laptop Per Child (OLPC) project was the high and the hidden cost that worked out to be $200. The mission launch would also see demonstration of e-classroom, virtual laboratory and a better 'Sakshat' portal that was launched more than two years ago. Sources also said that the ministry has entered into an agreement with four publishers — Macmillan, Tata McGraw Hill, Prentice-Hall and Vikas Publishing — to upload their textbooks on 'Sakshat'. Five per cent of these books can be accessed free. The mission, with an 11th plan outlay of Rs 4,612 crore, is aimed at making a serious intervention in enhancing the Gross Enrolment Ratio in higher education. The mission has two major components. One, content generation through its portal 'Sakshat', and two, building connectivity along with providing access devices for institutions and learners. In this context, government would give Rs 2.5 lakh per institution for 10 Kbps connection and subsidise 25% of costs for private and state government colleges. The mission would seek to extend computer infrastructure and connectivity to over 18,000 colleges in the country, including each department of nearly 400 universities and institutions of national importance. The mission would focus on appropriate e-learning procedures, providing facility of performing experiments through virtual laboratories, online testing and certification, online availability of teachers to guide and mentor learners, and utilization of EduSat and DTH. http://timesofindia.indiatimes.com/I...ow/4049914.cms  OLPC 2.0: After Layoffs, One Laptop Foundation Reboots With New Focus and Big Plans Robert Buderi For those inspired by Nicholas Negroponte’s vision of bringing affordable computing to every child on the planet, it was a sad day early this month when the One Laptop Per Child Foundation he founded announced it was laying off half its staff and undertaking a significant reorganization. Negroponte himself isn’t crying, though—he is working on plans for the future: OLPC 2.0, you might call it. Only a bullet-point sketch was presented on the OLPC blog, but Negroponte and OLPC President Charles “Chuck” Kane met with me last week in Harvard Square to explain more. We covered how the layoffs came about, particularly the failure of the Give One, Get One (G1G1) program and where that leaves the organization financially. And they shared plans to spin out operations in Latin America, where OLPC has been most successful, while beefing up efforts in Africa and the Middle East—as well as their thoughts on the next generation of XO laptops, including the foundation’s technical goals and commercial competition from netbooks. While Negroponte and Kane painted an optimistic picture, pointing to the fact that the one millionth OLPC laptop will be deployed in the field in February, I found them candid about the hard lessons learned and challenges the organization faces. As Negroponte told me, his passion for the project and its importance is as strong as ever, but the foundation is at a turning point in its evolution and must focus better on where it can make big differences. “That’s the thing to keep in mind, and to make sure we don’t just perpetuate ourselves for perpetuation’s sake if some aspects of OLPC have run their course—and to recognize that and not try to be an incrementalist.” The most vivid example of this philosophy, to me, was Negroponte’s comparison of the XO and netbooks. XOs cost about $225 apiece. Netbooks, which are produced by companies like Acer and Lenovo, among others, run about $300 to $450 but offer more memory and graphics power and larger screens. So, one could ask, won’t the normal, cost-curve-squashing evolution of computers obviate what OLPC is trying to do, and more efficiently than a non-profit? Negroponte replies that OLPC is not trying to compete with commercial computer makers but instead asking, “What are the things the normal commercial market won’t be pushing?” In the case of netbooks, he says, “You could arguably say we really created the netbook market. But if you look at the netbooks, they really copied the easy part. They didn’t copy low power, they didn’t copy mesh networks, they didn’t copy sunlight-readable displays. All three things are absent from every single netbook.” To understand the points Negroponte ticked off, recall that XO laptops operate on very low power, which can be generated by pulling on a cord that plugs into the computer—a valuable feature in places where people pay by the minute for electricity, or electricity is unreliable. “You’ve got to be in the two-watt regime in order for it to be something you can power by hand,” Negroponte says. Netbooks, by contrast, require more like 20 watts, he says. OLPC laptops are also able to link together into wireless mesh networks that can easily pass data between computers, and include displays that can be read in glaring sunlight—again, features incredibly useful in developing nations and things Negroponte says the commercial market really isn’t focused on. But we’re getting slightly ahead of the story. Before diving into the technology or future plans for OLPC, we started with what went wrong. Give None, Get None The G1G1 effort was crafted to spur consumers in developed nations to buy XO laptops for schoolchildren in emerging nations. Consumers could buy one, which would be sent to a school of OLPC’s choosing, and then get another laptop to keep or send wherever they wanted. In the 2007 holiday season, Negroponte told me, the program took in $37 million. This past season, the foundation partnered with Amazon to sell the laptops and increased its advertising and marketing efforts substantially—to two or three times what they were in 2007, or close to $20 million, virtually all of it pro bono. Yet, sales fell off a cliff, coming in at about $2.5 million. Negroponte attributes “almost all” of the falloff to the poor economy, though others have theorized that the computers themselves had lost their appeal. That was a huge blow to OLPC’s operating budget. But on top of the G1G1 nosedive, corporate sponsors of the organization also dropped out. Nortel, one of the biggest, recently filed for Chapter 11. EBay and SES, a network of satellite operators, had already ended their support. “There are a couple [others] at the moment whom I’m not expecting to renew,” Negroponte says. “They’re all cutting budgets and laying off people.” Negroponte does not believe that people are turning away from the mission, or the vision, of OLPC. “I don’t think anybody has looked at OLPC and suggested to themselves that it’s no longer [viable]…I don’t think that’s happened,” he says. Negroponte describes OLPC as having two economies. One is built around the laptops, the cost of producing them and the value they bring. The other, much smaller economy “is OLPC itself, which on the high months was burning about $1 million a month,” Negroponte says. “I never imaged that the smaller economy would be an issue. But it’s fueled by two things–Give One, Get One and corporate sponsorship.” The dramatic falloffs in those two programs necessitated the layoffs, which were designed to bring OLPC operating costs to under $500,000 per month, probably closer to $350,000, according to Kane (both Kane and Negroponte work pro bono). The OLPC president joined the organization last May—he had previously held executive positions at RSA Security and several other companies and helped negotiate RSA’s 2006 sale to EMC—with the job of bringing more financial structure and business-savvy management to the organization. The layoffs and refocusing are part of that effort. “You’re looking at a project that’s totally visionary that has to be converted into a business in he next phase: it’s already past that phase, and that’s the huge challenge,” Kane says. “To make it a business, you have to do certain actions that make it feel not non-profit anymore.” He says the foundation currently has enough cash to operate at least a year at its new staffing level. The Laptop Economy—Poised for New Growth? When it comes to the laptop economy, things seem far brighter. With roughly a million laptops in the field at a cost of about $225 apiece, Negroponte says he thinks of that economy as worth roughly $225 million. And he and Kane believe it is poised for more growth. The reorganization this month was designed to focus on opportunities in new markets, while turning relatively mature and already successful programs over to more business-like operations outside the foundation. “The bulk of our success to date has been in Latin America,” especially in Uruguay and Peru, says Kane. By the end of this year, he says, Peru will have 600,000 XOs, while Uruguay will have 350,000. The maturity of the Latin American market—which he described as being in rollout mode, versus the seed stage—has spurred the OLPC to relinquish its management of programs in the region. “We’ve decided to, for lack of a better term, spin out that region and manage it out of Miami.” says Kane. The spinoff into a separate entity is the first step in what Kane described as OLPC evolving into autonomous operating regions as XOs find success in different geographies. “I foresee OLPC from a sales and delivery as being a regional thing,” he says. The foundation doesn’t have the resources to run a support infrastructure for the computers it deploys around the world. But in places like Uruguay and Peru, he says, various government or organizational authorities “want to take over that responsibility…That is a requirement, really, for it to be successful.” Under the structure Kane foresees, OLPC will take orders and circulate them to the various operating regions for fulfillment. “That’s what I’m focused on right now, is establishing autonomous regions,” Kane says. Meanwhile, the core of OLPC will focus on bringing XOs to new markets. Negroponte, who was on his way to a regional meeting in Amman, Jordan, after our session, says the foundation is poised for big payoffs in the Middle East, where he is exploring partnerships with a number of organizations to help get XOs into the hands of children—including Palestinian refugees—who otherwise have little opportunity for computer access. OLPC also has operations in Afghanistan and Pakistan, and Negroponte is talking with officials in Iraq as well. “I expect it to gel over the next month,” he says of the overall Middle East effort. “This meeting this week is very important.” Another big area of focus is Africa, especially Rwanda, where OLPC is deploying a full-time staffer. “Rwanda really is the poster child,” Negroponte says, describing President Paul Kagame as “very much behind” the OLPC program. The Rwandan leader initially ordered 10,000 XOs, then upped it to 100,000. The program now makes up a large fraction of the country’s education budget, according to Negroponte. The successes in Uruguay, Peru, and Rwanda will breed other successes, Kane predicts. “Now we have visible proof of concept in these areas and very delighted projects, and so that of course drives other opportunity,” he says, pointing to a growing presence in India and China, both huge potential markets that OLPC moved into since he joined. “Amazingly we have a lot of deals that are starting to pop right now,” he says. Of Mesh Networks, Sweet Words About Sugar, and 1M Digital Books To date, OLPC has designed, developed, and manufactured its laptop largely on its own, and now has a 500,000-strong backlog at the manufacturing facility in Shanghai where the XO is assembled. It’s not exactly in a non-profit’s wheelhouse to be running such an operation, and “in a perfect world we wouldn’t have built this computer ourselves,” Negroponte says. Neither he nor Kane, however, think the basic situation will change in the near term. “As much as we’d love to I don’t think we can just get out of it,” Kane says. “It’s not clear who would partner in a not-for-profit scenario.” That said, OLPC is changing the way it designs its machines, hopefully pointing the way to getting out of the manufacturing business farther down the road. The next version, XO 2.0, is some 18 months out. Rather than doing the whole design in-house, the new plan is to outsource as much of the work as possible. Ideally, “what we should do is build something akin to a reference design that other people can freely use,” says Kane. “The idea would be to hand off 2.0 so that partners would manufacture the product and sell the product through their own channels.” Beyond pursuing plans for XO 2.0, three other “technology initiatives” were highlighted in Negroponte’s restructuring announcement: no-cost connectivity, shedding development responsibility for the XO’s Sugar graphical interface, and a project to create a million digital books. Each is a story in its own right, but we only covered the basics in our conversation. No-cost connectivity refers to finding a way for XO laptops to access the Internet free of charge. Nortel was among the companies previously helping OLPC bring Internet access to schools with XOs through satellites or other means, and I presume that SES was also part of that effort, though Negroponte didn’t mention them. In any event, a lot of work needs to be done on this front, and Kane says success will likely take the form of a business arrangement rather than a technical solution. On the Sugar front, the foundation recently released an update of the graphical interface originally deployed with the XO that fixed bugs and incorporated a lot of what was learned in Peru and Uruguay. But, says Kane, “At that point, given our limited resources, we more or less passed Sugar back to the [open source] community.” This is not a surprise, as OLPC officials last spring announced plans to make a version of the laptop that runs Microsoft Windows rather than its original Linux-Sugar software stack. The decision highlighted a visible split between Negroponte and Walter Bender, the onetime OLPC president of software and content, who, as Wade described it last April, left the organization over the decision to “de-emphasize radical projects like Sugar and to work more closely with the mainstream computing industry.” Bender went on to form Sugar Labs to continue development of the interface independently. Kane and Negroponte stressed, though, that Sugar might be able to work in conjunction with Windows, just as it does with Linux. “Sugar is terrific software for early childhood learning,” says Kane. “There’s a lot of elements that make it very unique and very powerful.” He says OLPC hopes to keep working closely with Bender and Sugar Labs in the future. “We believe that the future product that’s produced out of there will be very instrumental in what we have to offer.” The last technical initiative involves the creation of a vast library of one million digital books that can be read via open source reader software that works on the XO. The reader is being developed by Brewster Kahle, director and co-founder of the Internet Archive. Negroponte and Kane say OLPC is not deeply involved in the project but is working jointly on aspects of the technology. You can see a video of Kahle talking about his reader and the XO here. A Great Thing to Be a Part Of After giving his take on all the core issues facing OLPC, Negroponte had to leave to catch his plane. Before he left, I asked him about the future challenges. “Going forward, I’m fond of saying, our first four years we behaved like Apple,” he says. The XO, he says, is “designed beautifully, it’s in the Museum of Modern Art, it’s the best of breed. In the next four years, we’ve got to behave like Google and get to lots of people doing lots of things that are really for learning, for kids and for the developing world.” As far as progress so far, including the ups and downs, he says, “We had no choice and no regrets.” After Negroponte had gone, Kane and I spoke a little while longer. “One of the things that I admire most about Nicholas is that he never ever steps back and appreciates what has been achieved,” he relates. “Because he feels as though that’s a breather that takes away from what you can achieve in the future. I’ve never seen an organization so blind to what’s been accomplished.” And it’s what can still be accomplished that keeps Kane coming to work for free. “This is the moment [when] we have the most opportunity to have an impact in many, many countries,” he says. “To do what we can do and have an impact on the world in a profound way is a great thing to be a part of.” http://www.xconomy.com/boston/2009/0...and-big-plans/  Less is Moore There is strong demand for technologies that do the same for less money, rather than more for the same price FOR years, the computer industry has made steady progress by following Moore’s law, derived from an observation made in 1965 by Gordon Moore, a co-founder of Intel, now the world’s biggest chipmaker. His original formulation was rather technical, and was based on the number of transistors that could be crammed onto a chip, but it was adopted as a road map by the industry, so that it became a self-fulfilling prophecy. In practice, it boils down to the following: the cost of a given amount of computing power falls by half roughly every 18 months; so the amount of computing power available at a particular price doubles over the same period. This has resulted in a geometric increase in the processing power of desktop computers, laptops, mobile phones, and so forth. Constant improvements mean that more features can be added to these products each year without increasing the price. A desire to do ever more elaborate things with computers—in particular, to supply and consume growing volumes of information over the internet—kept people and companies upgrading. Each time they bought a new machine, it cost around the same as the previous one, but did a lot more. But now things are changing, partly because the industry is maturing, and partly because of the recession. Suddenly there is much more interest in products that apply the flip side of Moore’s law: instead of providing ever-increasing performance at a particular price, they provide a particular level of performance at an ever-lower price. The most visible manifestation of this trend is the rise of the netbook, or small, low-cost laptop. Netbooks are great for browsing the web on the sofa, or tapping out a report on the plane. They will not run the latest games, and by modern standards have limited storage capacity and processing power. They are, in short, comparable to laptops from two or three years ago. But they are cheap, costing as little as £150 in Britain and $250 in America, and they are flying off the shelves: sales of netbooks increased from 182,000 in 2007 to 11m in 2008, and will reach 21m this year, according to IDC, a market-research firm. For common tasks, such as checking e-mail and shopping online, they are good enough. Many companies, it seems, would also prefer computers to get cheaper rather than more powerful. The recession is hurting the computer industry, albeit not as badly as the bursting of the dotcom bubble did in 2000-01 (see article), but those companies that enable their customers to benefit from the flip side of Moore’s law, and do the same for less, will be best-placed to ride out the storm. A good example of this is virtualisation: using software to divide up a single server computer so that it can do the work of several, and is cheaper to run. The more powerful that machine, the more computers it can replace and the less, in effect, each “virtual” machine costs. The rise of “good enough” computing The “good enough” approach also works with software. Supplying “software as a service”, via the web, as done by Salesforce.com, NetSuite and Google, among others, usually means sacrificing the bells and whistles that are offered by conventional software. Google Docs lacks the fancy features of Microsoft Word, for example. But hardly anyone uses all those features anyway, and Google Docs is free. Once again, many users are happy to eschew higher performance in order to save money. Even Microsoft has cottoned on: the next version of Windows is intended to do the same as the last version, Vista, but to run faster and use fewer resources. If so, it will be the first version of Windows that makes computers run faster than the previous version. That could be bad news for computer-makers, since users will be less inclined to upgrade. But they are less inclined to do so already. Moore’s law has not been repealed, but more people are taking the dividend it provides in cash, rather than processor cycles. http://www.economist.com/opinion/dis...ry_id=12932356  $200 Laptops Break a Business Model Brad Stone and Ashlee Vance The global credit crisis may have caused the decline in consumer and business spending that is assaulting the giants of high tech. But as the dominant technology companies try to emerge from this slump, they may find themselves blaming people like David Title just as much as they blame Wall Street. Mr. Title, a 35-year-old new-media manager at a film production company in New York, has dropped his cable subscription and moved to watching most of his television online — free. While shopping for a new laptop for his girlfriend recently, he sidestepped more expensive full-featured computers and picked a bare-bones, $200 Asus EeePC laptop, also known as a netbook. “We’ve reached one of those moments in tech history when there are low-priced and free alternatives that are both user-friendly and reliable enough to make the switch,” Mr. Title said. “Then there’s the extra bonus of saving some cash.” Silicon Valley has been gripped by a growing sense that the economic retreat might do more than depress earnings. There is too much ingrained optimism here to think that the tech sector will not bounce back, stronger than before. But the fear now is that consumers like Mr. Title, and businesses operating with the same cost-cutting mind-set, will erode the high-margin businesses of the information technology industry — slowing some technologies and companies but giving new momentum to others. A normally confident Steven A. Ballmer, chief executive of Microsoft, expressed this very fear last week after announcing the company’s first big reduction of its work force. “Our model is not for a quick rebound,” he said. “Our model is things go down, and then they reset. The economy shrinks.” This has happened before. The dot-com bust earlier in the decade dragged down high-fliers like Sun Microsystems and America Online but set the stage for a new generation of Web powerhouses like Google and other innovative Internet software companies like Salesforce.com, founded on disrupting the status quo. The recession of the early 1990s sent I.B.M., then the dominant force in technology, into a five-year tailspin. But it also propelled Microsoft and Compaq, later acquired by Hewlett-Packard, and Dell to the forefront of computing. Indeed, Silicon Valley may be one of the few places where businesses are still aware of the ideas of Joseph Schumpeter, an Austrian economist who wrote about business cycles during the first half of the last century. He said the lifeblood of capitalism was “creative destruction.” Companies rising and falling would unleash innovation and in the end make the economy stronger. Recessions “can cause people to think more about the effective use of their assets,” said Craig R. Barrett, the retiring chairman of Intel, who has seen 10 such downturns in his long career. “In the good times, you can get a bit careless or not focused as much on efficiency. In bad times, you’re forced to see if there is a technology” that will help. So who’s up, who’s down and who’s out this time around? Microsoft’s valuable Windows franchise appears vulnerable after two decades of dominance. Revenue for the company’s Windows operating system fell for the first time in history in the last quarter of 2008. The popularity of Linux, a free operating system installed on many netbooks instead of Windows, forced Microsoft to lower the prices on its operating system to compete. Intel’s high-power processors are also under assault: revenue tumbled by 23 percent last quarter, marking the steepest decline since 1985. Meanwhile, more experimental but lower-cost technologies like netbooks, Internet-based software services (called cloud computing) and virtualization, which lets companies run more software on each physical server, are on the rise. Penny-pinching shoppers like Mr. Title could have the most immediate effect on the tech industry, particularly if more people consider canceling their cable subscriptions to watch video online, or drop their landline telephones to depend on their cellphones or on Internet calling services like Skype. Many consumers appear ready to abandon the costly desktop computer altogether. Analysts expect PC sales to fall in 2009 for just the second time in the last two decades, with desktops falling even faster than they did in 2007 or 2008. The only bright spot in the PC industry is netbooks. Analysts at the Gartner research company said shipments rose to 4.4 million devices in the third quarter of 2008, from 500,000 units in the first quarter of last year. Analysts say sales could double this year despite a deep worldwide recession. Two lumbering giants, Hewlett-Packard and Dell, missed the first wave of these tiny, stripped-down machines, allowing Acer of Taiwan to grab market share. Acer pushed Apple out of the No. 3 spot behind H.P. and Dell as sales soared 55 percent. Dell and H.P. are making the devices now. Even the mighty Apple, whose iPod and iPhone revenue had helped insulate it from the first phase of this recession, reported last week that revenue from its desktop line fell 31 percent from the same period a year ago. “The day of the Rolls-Royce laptop and the high-end computer may not be totally over,” said Charles King, an independent technology industry analyst in Hayward. Calif. “But certainly the audience for that type of product is getting smaller and smaller.” Companies have also started to examine what they can do without and what they can do differently, and their choices may alter the competitive and lucrative landscape of business computing. Hoping to save money, Arista Networks, a start-up based in Menlo Park, Calif., has much of its internal technology processes online, or “in the cloud.” Instead of buying its own hardware and software systems from the likes of Microsoft and Oracle, it opted for e-mail and online document services from Google and online sales and manufacturing software from Netsuite, based in San Mateo, Calif. It is spending a fifth of what it would be for traditional technology, said Jayshree Ullal, Arista’s chief executive. She smells a trend. “I think 80 percent of the new high-tech and small to mid-size companies are doing what we’re doing,” she said. A spate of start-ups have seized on cloud computing. Companies like Intacct offer online accounting software as an inexpensive alternative to Microsoft’s products, and giants like Amazon.com sell access to data centers for business operations. Amazon has outpaced the traditional hardware makers with such services. The number of virtualized new servers has doubled over the last three years, which has driven the revenue of VMware, one of the leaders in this cost-saving technology, to an estimated $1.88 billion last year from $387 million in 2005. The makers of open-source software also continue to benefit from the growing appeal of their often cheap, if not free, products. Sun Microsystems distributes 65,000 downloads a day of its MySQL database, which has turned into the favored business software of new companies. The job search engine Indeed.com shows a thriving job market for MySQL and Linux developers. Linux has proved popular as well on a new crop of smarter devices — be they phones, TVs or set-top boxes — that have captured software developers’ imaginations. The new products they build will undoubtedly challenge the status quo. “Companies like Intel, Qualcomm and Texas Instruments that make chips for these devices are hiring Linux talent as quick as they can,” said Jim Zemlin, executive director of the nonprofit Linux Foundation. “They know the future is netbooks and mobile Internet devices.” http://www.nytimes.com/2009/01/26/te...y/26spend.html  Free Internet-Calling Services Join the Cellphone App Market Bob Tedeschi For years, software providers have offered ways to make free calls from cellphones, and most of them even work. The problem is putting the software on your phone. It is not that carriers want to make it hard for subscribers to load Skype, Fring and other free-calling apps onto phones, although the networks obviously bristle at the idea of giving their customers a way to make free calls (also known as “voice over Internet protocol” or telephony). The bigger issue is that until recently, carriers have made it painfully hard to load anything onto your phone, whether it is sophisticated software or a simple ring tone. But since Apple buried its spurs in the backside of the industry by creating an application store that actually works — thereby compelling other companies to follow suit — these free-calling applications are almost within the reach of the average smartphone user. Of the many free-calling applications, Fring, a start-up based in Israel, and Skype, the standard-bearer of the free-calling realm, are among the more user-friendly. But even then, the applications are not yet worth the inconvenience unless you plan to make a fair number of international phone calls and can put up with less-than-perfect call quality (or far worse). Here is how it works: It helps to have a device that has Wi-Fi, because the call quality is best when carried over the Internet, not through the carrier’s pipes. (Skype offers a version that works with a smartphone’s cellular-data connection, but it says it “can’t guarantee voice quality” for those.) Once the application is loaded and started, the software typically displays its own keypad. As long as you are in a Wi-Fi hot spot, you can make free calls directly to other members of the particular service — Fring-to-Fring calls, say, or Skype-to-Skype. Or you can call landlines through Skype at cheap rates once you have a prepaid account. Skype and Fring users are assigned ID numbers or names, and when they are used for dialing, the calls go over the service’s Internet servers. If a telephone number is used, instead of an ID number, the call is partly routed over phone lines, then to Skype’s Internet servers, which hand it off again to a local carrier to connect the call on the other end. That is why users see strange local numbers on their caller ID for incoming calls, rather than the name or number of a friend. There are a few caveats to the service. Skype first offered this software to Windows Mobile users nearly three years ago. Those users can download it by going to Skype.com and following the “mobile” links. PC users can download the Skype mobile software to a computer, sync their handset with the machine and transfer the application to the phone. Mac users cannot download the software to their computer — they have to use their phone’s browser to go to Skype’s download site. Depending on the phone, this can be a breeze or maddeningly difficult. I used an LG Incite, and let’s just say it was not a breeze. For those without a Windows Mobile phone, Skype recently introduced Skype Lite, which runs on dozens of Nokia and Samsung phones with Symbian software, as well as a few Motorola Razr models. On Skype.com, these users can type in their mobile numbers and Skype will send a message to the phone with a link to download the software. But the real news with Skype Lite is that it also runs on the G1, from T-Mobile, also known as the Google phone, which operates on the Android software platform. If you own the G1, you need only visit the “Market,” Android’s app store. Click on the Skype application, which is free, and a few seconds later you are ready. The company is also working on an iPhone app, but in the meantime, Skype users who have iPhones have another free Internet calling option: Fring. In addition to letting you call other Fring members free, the service also connects you to Skype, which is great if you have a phone that does not work with Skype’s mobile app, and you want to use Skype to call landlines or mobile phones on the cheap. A Skype call to someone within the continental United States is about 2 cents a minute. A call to Japan from the United States costs the same. It is worth noting that you can also download Fring to the latest versions of the iPod Touch, turning your iPod into a poor man’s iPhone. I left myself a voice mail message using the service, and the audio on the iPod sounded distant and grainy, and was briefly inaudible at times. A far bigger problem was that I couldn’t make outbound calls to landlines or other mobile phones using my Skype account on the iPod Touch or the iPhone, despite the fact that the account was fully funded. I sent an e-mail message to Fring’s customer support, which promised to reply within 48 hours. Sure enough, the next day I received an e-mail message explaining that the company was aware of the problem and was working to fix it. In the meantime, it suggested merely adding a plus sign to the beginning of the number. It worked. I then switched over to the iPhone for a comparison of how Fring might sound without a headset — and on an actual phone — and the quality was significantly better, especially on a Fring-to-Fring call. The audio was still a bit grainy and the call dropped a few times over a matter of 15 minutes, but I could easily see this as an alternative to expensive international calls. And that is really what is important here. If you are in a long-term relationship with someone overseas, say, or on a work assignment and away from your family, these applications can help give you some semblance of connectivity without killing your budget, and without forcing you to haul around a laptop for free VoIP calls. QUICK CALLS Verizon Wireless subscribers who have weak cell signals at home can end that frustration, for a price. This week, the company began selling its Network Extender, which, for $250, creates a miniature cell site. The device plugs into your broadband Internet connection and creates a signal coverage area of about 5,000 square feet. One drawback: the Network Extender does not offer a high-speed, 3G connection to your phone, so services like the VCast media application will not work. ... You can now pay a cab fare with a cellphone, thanks to a new application from RideCharge. Register your credit card information with the service and use it to book a cab in about 20 metropolitan areas. In addition to iPhone and BlackBerry apps, the company offers this free service through its Web site (RideCharge.com). RideCharge adds $1.50 to the bill for each ride arranged by the service. ... Which has more calories: a yogurt with 78 calories in a tablespoon, or one with 43 calories for every 2 ounces? Apples2Oranges, a new iPhone app ($5), will answer these and other pesky questions about consumer goods. Or you can try another service, KGB. Send any question by text message to KGBKGB/542542, and a researcher will answer it by text message, for 50 cents a pop. http://www.nytimes.com/2009/01/29/te...h/29smart.html  Slicing Decades of Video for New Life on the Web Brian Stelter Media companies are rushing to repackage their videos for the Internet, and some say they can hardly keep up with advertiser demand for more. Video clips of TV shows and behind-the-scenes outtakes are omnipresent online — but how do they get there? Part of the answer is here, at the headquarters of Discovery Communications, where a small team of editors mines the 23-year-old video vault of the Discovery Channel for animal attacks, dinosaur animations and scientific oddities. Old shows that ordinarily would not be repeated on Discovery or its other cable channels can be repackaged online, turning every week into “Shark Week,” three minutes at a time. As users spend more time watching videos with advertisements attached, they are fast becoming an incremental moneymaker for media companies. While the young medium is not impervious to the economic slowdown, the research firm eMarketer forecasts a 45 percent gain in online video spending in 2009, evidence of the sharp rise in video production for the Web. Perhaps that explains why the words “brighter digital future” are scribbled in blue ink on a whiteboard next to Josh Ferg’s desk. Mr. Ferg is one of eight producer-editors, or preditors for short, who create bite-size video for the Web at Discovery. Despite the unfortunate job title — “I think ‘Dateline NBC’ has kind of ruined it,” Mr. Ferg joked, referring to the newsmagazine’s “To Catch a Predator” franchise — Discovery views the team as an important part of its Internet strategy. The producer-editors made about 4,500 videos for Discovery’s Web sites last year, helping the company record eight million video views in November. While the online advertising market has slowed considerably because of the weak economy, the executive vice president for digital media at Discovery, Josh Freeman, said advertisers’ demand for video remained robust. Asked whether the ads were lagging behind the content creation, he responded: “In video? Not a chance.” When Mr. Freeman arrived from AOL in mid-2007, he said, he concluded that Discovery “was just leaving money on the table” in online video. Now, he says, the company is playing catch-up. To a greater extent than most media companies, Discovery owns the global rights to the content it broadcasts. Because the company owns 13 networks in the United States, including TLC, Animal Planet and the Science Channel, it has untold thousands of hours of footage. And because many of its TV episodes are timeless, the clips can still be relevant to Internet users years after their original broadcast. “Cheetahs are still killing gazelles the same way they did 3,000 years ago,” Doug Craig, the senior vice president for digital media production, said, “and on top of that, we don’t have to pay residuals.” To that end, Discovery has added six temporary employees to “maximize the library,” Mr. Craig said. They are repackaging old shows into short clips for the how-to Web site HowStuffWorks, a recent acquisition by Discovery, and Discovery’s other platforms. That gives Mr. Ferg and the other full-time producer-editors time for more complex projects. Sometimes they blend several videos to create original series with new graphics and narration. Recent examples include “Jaws and Claws,” about the relationship between predator and prey, and “Strange Science,” about all sorts of bizarre phenomena. The Science Channel recently shortened the latter segments into 30-second vignettes. Almost every video is shorter than five minutes. “Killer Clips,” a series of 30- to 40-second clips of animal takedowns, have proved especially popular on the Animal Planet Web site. But Mr. Ferg avoids the term clipping because, he says, it oversimplifies the process. “It’s always about a story,” he said, whether that story is an hour or a minute long. When the producer-editors want to repackage shows from long ago, the continuing digitization of the Discovery archives allows them to mine the vault ever deeper. An archive in Sterling, Va., stores 1.3 million tapes of old episodes; when a producer wants to clip something from one of those tapes, it is brought to an editing center a few blocks from Discovery’s headquarters and a digital copy is created. All of the shows are fodder for online clips. Mr. Freeman particularly enjoys the super-slow-motion “Time Warp” videos that show the impact of a boxer’s punch or a burst of fireworks. The half-hour show lends itself well to one-minute variations. Some of the videos seem destined for wide popularity. Placing them on sites like YouTube clearly helps. The Discovery series “MythBusters” is probably the most popular show for clips. A video of one of the co-hosts, Adam Savage, inhaling helium and explaining the voice-adjusting effects has attracted more than a million views on YouTube. In the coming months, Discovery will begin selling ads for its videos on YouTube, adding another source of revenue for the company. On a recent day, Discovery.com’s short videos featured ads from consumer products companies, electronics makers and the United States Army. The online video industry continues to suffer from a lack of specified ad formats and standardized measurements, but Mr. Freeman is optimistic about ad money. “Those dollars are going to come,” he said. “I want to be there when they do.” http://www.nytimes.com/2009/01/26/te...t/26vault.html  HDTV Owners not Watching in HD Jared Newman Though the number of U.S. homes with HDTVs continues to rise, almost half of those homes aren't watching high definition programming, a new study found. In-Stat reports that 17 million of the 39 million U.S. households with HDTV, or 43.6 percent, don't watch in HD. The finding is based on a recent survey of consumers and defines "HD programming" as paid high definition services from cable and satellite providers and free broadcasting over the air. Packaged media, such as Blu-ray disc and video games, are not included. Michael Paxton, an analyst for In-Stat, told CDFreaks that there are two main reasons why so many HDTV owners are still watching in standard definition. Cost was a major factor, with consumers saying they didn't want to fork over extra fees to lease an HD set-top box or to get HD channels. Also, consumers often said the amount of high definition programming wasn't enough to justify the extra effort. Those answers aren't tied to any particular U.S. region or demographic, Paxton said. "It's pretty much across the board for all people," he said. "We get the same answers why they're not viewing HD programming on their HDTV sets." In-Stat has been measuring this statistic for three years, and predictably, the number of people watching HD programming has come a long way. At the end of 2005, 19.1 million people had HDTVs installed, but only 6.8 million of those households watched high definition programming. Back then, Paxton said, a lot of people simply didn't realize they were watching in standard definition. Education on the difference between standard and high definition has improved since then, and that issue is no longer a major reason why consumers don't get HD. Paxton stopped short of revealing how much he thinks HD programming will rise in popularity this year. That information, he said, must be saved for the full study, which costs a cool $2,995 to read. http://www.cdfreaks.com/news/15452-H...ing-in-HD.html  Technology Gets a Piece of Stimulus Steve Lohr The time-tested way for governments to create jobs in a hurry is to pour money into old-fashioned public works projects like roads and bridges. President Obama’s economic recovery plan will do that, but it also has some ambitious 21st century twists. The $825 billion stimulus plan presented this month by House Democrats called for $37 billion in spending in three high-tech areas: $20 billion to computerize medical records, $11 billion to create smarter electrical grids and $6 billion to expand high-speed Internet access in rural and underserved communities. A study published this month, which was prepared for the Obama transition team, concluded that putting $30 billion into those three fields could produce more than 900,000 jobs in the first year. The mix of proposed spending is different in the House plan, but the results would be similar, said Robert D. Atkinson, president of the Information Technology and Innovation Foundation, which did the study. Beyond creating jobs, advocates say, government investment in these technology fields holds the promise of laying a lasting foundation for more business innovation and efficiency, while helping to create new digital industries. “The appeal of these kinds of investments is that you not only get the stimulative effect but also build a platform for productivity gains and long-term growth,” said Blair Levin, a former senior official at the Federal Communications Commission who was a technology policy adviser on the Obama transition team. During the campaign and afterward, Mr. Obama has championed policies to promote electronic health records, better broadband networks and power grids that use computers and sensors to fine-tune electricity use. But the standard for including any initiative in the economic recovery plan is that it be “timely, targeted and temporary,” while also creating jobs, Mr. Levin said recently in an address to the Congressional Internet Caucus, an advisory group. Not every investment in these technology fields, he said, fits those criteria. The technology industry is not typically viewed as a prolific job producer. Much of its manufacturing is highly automated. But bringing technology to services fields like health care, telecommunications and energy can be labor intensive and thus generate jobs. At the top of the jobs pyramid, the design of new technology is done by scientists and engineers with advanced degrees. The installing, tweaking and maintaining of that technology in specific industries involve a far broader base of workers with a range of training, skills and education. “There is a huge implementation phase to the adoption and use of these kinds of technologies locally,” said John Irons, an economist and research director at the labor-oriented Economic Policy Institute in Washington. “The jobs involved do tend to span the spectrum of skills and income levels. And they are not going to be outsourced offshore.” The job-generation estimate by the Information Technology and Innovation Foundation translates into more than 30,000 jobs created for each $1 billion of government investment — roughly similar to projections for public works spending. But proponents of spending on digital infrastructure say the beneficial spillover effects are greater than for conventional public works. The high-tech investments, they say, can be the contemporary equivalent of federal financing for highways in the 1950s, which fostered the growth of businesses like automakers and national retail chains. For years, technology policy in the United States has focused mainly on broad measures like federal spending on basic research and tax credits for private investment in research and development. Mr. Obama has vowed to increase spending on basic research and make R.& D. tax credits permanent. But the administration’s plan for large programs tailored to specific industries is a departure. How investments and incentives are structured, experts say, will be crucial to companies, consumers and taxpayers. The danger of such an approach, some economists warn, is that industry-specific government programs can tilt markets to the advantage of some companies and disadvantage of others, putting Washington on the path of picking winners and losers. The other criticism is that, while these projects may be worthy for the long term, they should not be part of a short-term economic recovery plan. All three fields, said Robert E. Hall, an economist at Stanford, involve “a bunch of specialists, where if we raised spending quickly, the limited number of competent suppliers would be in short supply and get increased incomes,” benefiting some companies more than the economy as a whole. “We should not pour government money into these areas,” said Mr. Hall, who is a senior fellow at the Hoover Institution, a conservative research group. The issues surrounding electronic health records illustrate the policy challenges of targeted programs. Mr. Obama has advocated spending $50 billion over five years to accelerate the use of such records and the sharing of health information across a national network. The computerized records, when used properly, are an indispensable tool for measuring, tracking and improving patient care — yet only about 17 percent of the nation’s doctors are using them. They are commonplace at large medical groups, but 75 percent of doctors practice in small offices of 10 physicians or fewer. Doctors often benefit from inefficiency, because the dominant fee-for-service payment system means they are paid for doing more — more doctor visits, tests, surgical procedures, pills. “Paying to put computer hardware and software in physicians’ offices isn’t going to do anything unless you change the incentives in the system,” said Dr. David J. Brailer, former national health information technology coordinator in the Bush administration. There are some experiments with a pay-for-performance approach, in which Medicare gives medical groups bonus payments for meeting certain benchmarks of quality care. Monitoring that performance requires electronic health records. Yet to date, these have been isolated tests. “You want to pay for achievement — better health quality and efficiency,” said Dr. David Blumenthal, director of the Institute for Health Policy at the Harvard Medical School, who advised the Obama campaign. “But in the transition period, before financial incentives are reformed, you need to provide incentives or grants to use electronic health records because this technology is sort of the opening wedge to reform.” Those eligible for grants to buy technology, a member of the Obama transition team said, will include inner-city and rural hospitals and small doctor practices. But most money, he said, will go to incentive payments to improve quality and safety of care. Still, creating effective programs to accelerate the use of health information to improve care will be difficult. And the move toward a national health information network, where patient data is more widely shared among providers and insurers, must include strong safeguards to address concerns about the privacy of personal health information, if Congress is to approve the proposed financing. Some health experts say a shortage of skilled people is a bottleneck in any rapid push toward electronic records. In suburban Philadelphia, Greg Beese is head of the Logic Group, a 15-person technology support firm, whose clients include 15 doctors’ offices. He says he looks forward to an acceleration of the use of electronic health records. A person with solid technology skills, he said, can master the health care knowledge in a couple of months on the job. “It’s not like we’d have to send them back to school for two years.” http://www.nytimes.com/2009/01/26/te...6techjobs.html  Revolution, Facebook-Style Samantha M. Shapiro Only a few hours after Israel’s first air strike against Hamas positions in the Gaza Strip late last month, more than 2,000 protesters marched through the streets of downtown Cairo, carrying Palestinian flags. This began what would become weeks of protests, in which thousands of Egyptians of all different political leanings gathered in Egypt’s main cities, in public squares and at mosques and universities. Hundreds were arrested. In every city, the biggest presence at the protests was the Muslim Brotherhood, the Islamist political organization, active in many countries throughout the Middle East, that seeks to govern according to Islamic law. Other, smaller demonstrations were put together, sometimes spontaneously, by leftist groups and student organizations. Anti-Israel demonstrations in Arab capitals are nothing new. From Amman to Riyadh, governments have long viewed protests against Israel as a useful safety valve to allow citizens to let off steam without addressing grievances closer to home. But in Egypt, this time, the protests were different: some of the anger was aimed directly at the government of President Hosni Mubarak. In defiance of threats from the police, and in contravention of a national taboo, some demonstrators chanted slogans against Mubarak, condemning his government for maintaining diplomatic relations with Israel, for exporting natural gas to the country and for restricting movement through Egypt’s border with Gaza. As the street protests went on, young Egyptians also were mobilizing and venting their anger over Gaza on what would, until recently, have seemed an unlikely venue: Facebook, the social-networking site. In most countries in the Arab world, Facebook is now one of the 10 most-visited Web sites, and in Egypt it ranks third, after Google and Yahoo. About one in nine Egyptians has Internet access, and around 9 percent of that group are on Facebook — a total of almost 800,000 members. This month, hundreds of Egyptian Facebook members, in private homes and at Internet cafes, have set up Gaza-related “groups.” Most expressed hatred for Israel and the United States, but each one had its own focus. Some sought to coordinate humanitarian aid to Gaza, some criticized the Egyptian government, some criticized other Arab countries for blaming Egypt for the conflict and still others railed against Hamas. When I sat down in the middle of January with an Arabic-language translator to look through Facebook, we found one new group with almost 2,000 members called “I’m sure I can find 1,000,000 members who hate Israel!!!” and another called “With all due respect, Gaza, I don’t support you,” which blamed Palestinian suffering on Hamas and lamented the recent shooting of two Egyptian border guards, which had been attributed to Hamas fire. Another group implored God to “destroy and burn the hearts of the Zionists.” Some Egyptian Facebook users had joined all three groups. Freedom of speech and the right to assemble are limited in Egypt, which since 1981 has been ruled by Mubarak’s National Democratic Party under a permanent state-of-emergency law. An estimated 18,000 Egyptians are imprisoned under the law, which allows the police to arrest people without charges, allows the government to ban political organizations and makes it illegal for more than five people to gather without a license from the government. Newspapers are monitored by the Ministry of Information and generally refrain from directly criticizing Mubarak. And so for young people in Egypt, Facebook, which allows users to speak freely to one another and encourages them to form groups, is irresistible as a platform not only for social interaction but also for dissent. Although there are countless political Facebook groups in Egypt, many of which flare up and fall into disuse in a matter of days, the one with the most dynamic debates is that of the April 6 Youth Movement, a group of 70,000 mostly young and educated Egyptians, most of whom had never been involved with politics before joining the group. The movement is less than a year old; it formed more or less spontaneously on Facebook last spring around an effort to stage a general nationwide strike. Members coalesce around a few issues — free speech, economic stagnation and government nepotism — and they share their ideas for improving Egypt. But they do more than just chat: they have tried to organize street protests to free jailed journalists, and this month, hundreds of young people from the April 6 group participated in demonstrations about Gaza, some of which were coordinated on Facebook, and at least eight members of the group were detained by police. As with any group on Facebook, members can post comments or share news articles, videos or notes on the group’s communal “wall.” The wall of the April 6 group is constantly being updated with new posts, and the talk is often heated and intense. On a recent afternoon, members were discussing photographs that had just been posted on the Muslim Brotherhood Web site of a mass protest in Alexandria against Israel’s actions in Gaza, in which thousands of members of the brotherhood took to the streets. “They are real men!” posted a young woman using the alias Mona Liza. “Something like this should happen in Cairo,” another member typed. “People should go to the streets of Cairo until the Jewish crusaders’ government falls.” Another member dissented: “We need strong actions, not protests like the brotherhood’s where they sing religious songs and go home.” Ahmed Maher, a 28-year-old engineer who is one of the group’s unofficial leaders, weighed in. “There are ideas about a big protest for Gaza right now,” he wrote. The April 6 group should join that protest, he agreed, but “we should link it to our demands, which are of course different from other peoples’ demands, like those of the brotherhood.” It was a crucial point: unlike many protest groups in Egypt that were angry about Gaza, Maher saw Gaza as a way to stoke and focus discontent against Mubarak and his government. Maher saw Egypt’s relationship with Israel as one symptom of a larger set of problems — censorship, corruption, joblessness and government incompetence — whose solution would lie not in resistance in Gaza but in democratization at home. “We should link politics with economic and social problems to show that our suffering is caused by a corrupt regime,” Maher wrote. The fact that tens of thousands of disaffected young Egyptians unhappy with their government meet online to debate and plan events is remarkable, given the context of political repression in which it is occurring. Organized groups opposed to Mubarak’s National Democratic Party have long lived under constant surveillance by the government; their leaders are regularly jailed. As a result, most Egyptian opposition groups remain small and are often plagued by infighting. And although about a third of Egypt’s population is between 15 and 29, young Egyptians have for years been politically disengaged. A 2004 study by the Ahram Center for Political and Strategic Studies found that 67 percent of young people weren’t registered to vote, and 84 percent had never participated in a public demonstration. In its official statement, the April 6 movement takes pains to emphasize that it isn’t a political party. But the movement has provided a structure for a new generation of Egyptians, who aren’t part of the nation’s small coterie of activists and opinion-makers, to assemble virtually and communicate freely about their grievances. When I spoke earlier this month to Samer Shehata, an assistant professor of Arab politics at Georgetown University, he said that it was no surprise that young Egyptians have chosen to put their political energy into a group that is not part of the Egyptian political process. “The state of the opposition in Egypt is so pathetic that existing parties have lost all credibility,” he told me. “They’ve been around for a long time and produced nothing.” The April 6 Facebook group, he said, “has credibility because it hasn’t sold out to the regime or played the pathetic, limited game of politics the regime engages in.” ON A THURSDAY AFTERNOON last fall, I made my way to a Cinnabon cafe in Nasr City, a well-to-do district of Cairo, to meet with one of the founders of the April 6 Facebook group, a 30-year-old woman named Esraa Abdel Fattah Ahmed Rashid, who works as a training coordinator for a company that makes Islamic DVDs. The Cinnabon was subdued: a few pairs of young women and one or two married couples were scattered around the seating area with open laptops and frothy, sweet drinks. Sean Paul’s “Temperature” played at a tasteful volume, low enough that the dance-hall lyrics about “the right tactics to turn you on” were nearly indecipherable. Rashid was wearing a meticulously coordinated outfit: brown pants, sandals, T-shirt, eyeliner and a baby blue tunic with overlapping light blue and brown head scarves. Rashid has a round face, a high-pitched voice and a plucky sense of determination — Reese Witherspoon in a hijab. Her husband works in Dubai most of the year, and while he is away, she lives with her mother. She originally joined Facebook to keep up with friends; she joined groups for fans of the Egyptian singer Mohammed Mounir and the national soccer team, another for discussions of the Koran and others that offered updates on the latest styles in pajamas and modest wedding dresses. But her relationship with Facebook evolved in ways she could not have predicted. Last spring, the general strike that Rashid and her friends organized on Facebook landed her in jail, on talk shows and in newspapers around Egypt and abroad. She was now widely known around Egypt — even by people who didn’t use the Internet — as the Facebook Girl, and she told me that she was logged into the site pretty much any time she wasn’t working or sleeping. (Like most of the Internet activists I met in Egypt, Rashid spoke little English, and we communicated mostly through an interpreter.) The April 6 movement has its roots in Egypt’s brief burst of political freedom in 2005 and 2006, which came after the Bush administration put pressure on the Mubarak regime to hold its first multiparty election. Although the election was far from free, it created new opportunities for activists to organize and demonstrate, and out of the campaign a loose coalition of socialist, leftist and Islamist groups emerged called Kefaya (“enough” in Arabic). They focused on direct action and rarely discussed ideology, but they were united on one issue: that Hosni Mubarak should not be allowed to transfer power to his son Gamal. Kefaya organized street protests to pressure Mubarak to step down, hold free elections and allow the Egyptian judiciary to remain independent. Some demonstrations attracted as many as 10,000 people. This flare-up of political activity coincided with the moment Egyptians were starting to gain access to the Internet in large numbers. Home computers and Internet cafes were becoming more popular, and the cost of getting online was dropping, thanks to a government initiative intended to encourage technological innovation in Egypt. The new technologies and political movements grew symbiotically. Shortly before Kefaya started, Wael Abbas, who is now one of Egypt’s most influential bloggers, set up a Web site called Egyptian Awareness, and it quickly became the main source of information on Kefaya’s activities, which were largely ignored by the state-run media. Abbas and a few other early adopters of blog technology worked simultaneously as political advocates and crusading journalists. In 2006, Abbas posted cellphone-video footage of a police officer sodomizing a screaming minibus driver with an iron rod, which ultimately led to the officer’s conviction. Another prominent blogger and friend of Abbas’s, a woman in her early 30s named Nora Younis, posted stories about sexual harassment of women who participated in street demonstrations, which helped spur Egypt’s mainstream media to cover the issue. (Younis worked briefly for The New York Times as a stringer.) Political blogs became essential reading for opposition parties; in 2005, Al Dustur, a weekly paper opposed to the regime, started a blog page, which reprinted important posts for readers without Internet access. During the 2005 election campaign, Esraa Rashid started volunteering at the headquarters of El Ghad, a liberal democratic party that was founded in 2004 by Ayman Nour, a wealthy lawyer and member of Parliament. Nour came in second in the election, behind Mubarak, with 7 percent of the vote; he is currently in jail for forgery charges that his supporters insist are bogus. Rashid told me that she loved working at the Ghad office, but she and some of her friends in the youth wing grew impatient with the party bureaucracy. Like most political parties in Egypt, El Ghad has a strict hierarchy, and before deciding to stage an event, the leaders would carefully weigh a number of factors, including internal office politics and their current standing with the Mubarak regime. Members of the youth wing, Rashid told me, didn’t have much say in that process, or much interest in the endless deliberations. So she and some friends turned to Facebook as a quicker, easier way to plan their own events and protests. Rashid’s first foray into using Facebook for organizing was to coordinate a small demonstration around the opening of a movie about corruption and torture called “Heya Fawda” or “This Is Chaos.” Rashid invited all her friends on Facebook to the event; they invited more friends; and in the end, about 100 people showed up. To Rashid, the event was a huge success; exhilarated, she and friends from El Ghad planned a few more events the same way. THEN LAST MARCH, Rashid got a text message on her phone from Maher, the 28-year-old engineer and activist, suggesting that young Egyptians should do something to support the workers in Mahalla al-Kobra, an industrial town, who were planning to strike on April 6. For more than a year, workers around Egypt had been striking, periodically, to protest high rates of inflation and unemployment, but they never coordinated their protests. Rashid and Maher met when they were both part of the Ghad youth wing, but Maher had left the party to devote himself more fully to the youth movement of Kefaya. Unlike Rashid, he had been active in street protests and had been arrested. Rashid loved the idea of doing something to support the workers, and she called Maher immediately. She suggested they create an open group on Facebook to brainstorm ideas. On March 23, Rashid set up the April 6 Strike group on Facebook with herself and Maher as administrators. Rashid expected this protest would develop more or less like her movie outing. But almost as soon as she set up the group, there were 16 members; when she refreshed the page a few minutes later, there were more than 60. The next day, more than 1,000. Rashid watched with fear and excitement as thousands of people, then tens of thousands, started joining and posting to the group. Eventually, the number reached 76,000. As the group’s administrators, she and Maher could approve messages as they were posted, and it was their responsibility to delete spam or inappropriate posts; the two took turns monitoring the site day and night. The group never developed a unified plan of action for April 6. Rashid initially proposed that people stay home and not buy anything in solidarity with the workers — unless they weren’t afraid of protesting, in which case they should take to the streets. One girl suggested that everyone who protested on the street should give flowers to the security forces to disarm them, an idea Rashid supported. Maher started sending so many messages to the group that Facebook canceled his account; the site’s automated filters presumed him to be a spammer. That left Rashid as the group’s sole administrator. As the April 6 group grew, its call for a strike was endorsed by a variety of groups — political parties, labor groups, the Muslim Brotherhood, student organizations, the Kefaya movement. On the streets, supporters handed out leaflets and sprayed graffiti to make non-Internet users aware of the action. Members who identified themselves as government security agents joined the April 6 group, too, posting comments under the insignia of the Egyptian police, and as April 6 approached, the government issued a strong warning against participation in the strike. Rashid told me that she was scared to go out on the street that day. She would have stayed home, she said, but she felt she owed it to all the people she’d been communicating with to come out. She posted her plans on Facebook; on the day of the strike, she said, she’d meet people at the Kentucky Fried Chicken in Tahrir Square downtown. She told people what she’d be wearing and gave out her cellphone number. On April 6 in Mahalla, thousands of workers rioted, tearing down a Mubarak billboard. There were many arrests and at least three deaths. When Rashid headed out toward Tahrir Square, she was shocked to see police and military vehicles blocking off streets; soldiers and police officers, it seemed, were everywhere. As Rashid approached the Kentucky Fried Chicken, she found it was surrounded by police. She called some friends and told them to meet her at a nearby cafe to decide what to do next. Police swept in and arrested Rashid at the cafe; they took her to jail, where she stayed for more than two weeks. Rashid was not prepared for a jail term. She had never been away from her mother for even a day without checking in, and although her mother knew she did clerical work for El Ghad, she had no idea that Rashid had been involved in organizing a general strike. Rashid’s mother was beside herself, and she appeared on TV, begging the authorities to release her daughter. While Rashid was in prison, members of the April 6 Strike Facebook group replaced their profile pictures with an image of Rashid with the words “Free Esraa!” printed below. And when Egypt’s prime minister, Ahmed Nazif, came to speak at Cairo University about the government’s technology initiatives, a 20-year-old member of the April 6 group named Blal Diab stood up and heckled him, urging him to free Rashid and other jailed activists from the April 6 movement. “They are the same young people who used the Internet to express their opinions!” he yelled, to thunderous applause. (One of Diab’s friends captured the whole thing on his cellphone, and the video was shared widely over YouTube and on blogs.) Rashid’s release from prison was shown on live television, and it was quite a show. She ran out the door of the jail into her mother’s arms, wailing. An unbelievable amount of screaming and crying ensued. Rashid’s mother tilted her face to the sky and issued a continuous stream of praise and thanks to Allah. Rashid said, tearfully, that she didn’t expect that posting on the Internet would get her sent to jail, and that if she’d known what would happen, she wouldn’t have done it. “They treated me well!” she sobbed. “They let me remain a girl. I missed you, Mom. I prayed to God every day.” When Rashid started playing the video on her laptop for me, she had to get up and walk away. Watching it still makes her cry. ETHAN ZUCKERMAN, a research fellow at Harvard’s Berkman Center for Internet and Society, told me that the April 6 movement illustrates what he calls the “cute-cat theory of digital activism.” Web sites or proxy servers created specifically for activists are easy for a government to shut down, Zuckerman says, but around the world, dissidents thrive on sites, like Facebook, that are used primarily for more mundane purposes (like exchanging pictures of cute cats). Authoritarian regimes can’t block political Facebook groups without blocking all the “American Idol” fans and cat lovers as well. “The government can’t simply shut down Facebook, because doing so would alert a large group of people who they can’t afford to radicalize,” Zuckerman explained. When I spoke to Wael Nawara, a 47-year-old Ghad activist who is a co-founder of the party, he explained why, for him, getting on Facebook was such a big eye-opener. If you look at Egyptian politics on the surface, he said, you might think that the Muslim Brotherhood is the only alternative to the Mubarak regime. But “Facebook revealed a liberal undercurrent in Egyptian society,” Nawara said. “In general, there’s this kind of apathy, a sense that there is nothing we can do to change the situation. But with Facebook you realize there are others who think alike and share the same ideals. You can find Islamists there, but it is really dominated by liberal voices.” Interestingly, young Islamists in Egypt have also started blogging in ways that challenge their elders, often posting critical comments about the senior leadership of the Muslim Brotherhood. In the past, this kind of internal dialogue was suppressed by the brotherhood’s leadership, or at least hidden from view, since the brotherhood’s newspapers were outlawed. But the official leaders of the brotherhood and younger malcontents have both found a happy home on the Internet. Abdel Monem Mahmoud, one of the most prominent young Muslim Brotherhood bloggers, recently wrote a scathing critique of an article by a brotherhood leader arguing that all politicians must be devoted Muslims. And when the brotherhood circulated a draft of a political platform — the first step toward becoming an official political party — a 28-year-old brotherhood member named Mustafa Naggar used his blog to publish critiques of the platform’s prohibition against electing women or Coptic Christians to the presidency. A somewhat-grudging alliance has developed among some of the young Islamist bloggers and their secular-liberal compatriots over issues of free speech and the rights of opposition parties. I met Naggar one afternoon in a Cairo coffee shop just after he had recited the midday prayer. He told me Wael Abbas and Nora Younis’s blogs are required reading for him; he visits them every day to stay current, although, he said, it really bothers him that Abbas often uses curse words in his posts. When I spoke to Asmaa Aly, a feminist blogger, she said that she was put off by the practice of many brotherhood members never to touch women other than their wives. “I could never be friends with someone who won’t shake my hand!” she said emphatically. But she added that if a brotherhood blogger was jailed, she would definitely show up for a protest. In Washington, there is increasing interest in the April 6 Youth Movement. James Glassman, the outgoing under secretary of state for public diplomacy, told me he followed the group closely. “It’s not easy in Egypt, and in other countries in the Middle East, to form robust civil-society organizations,” he said. “And in a way that’s what these groups are doing, although they’re certainly unconventional.” Other State Department officials told me they believe that social-networking software like Facebook’s has the potential to become a powerful pro-democracy tool. They pointed to recent developments in Saudi Arabia, where in November a Facebook group helped organize a national hunger strike against the kingdom’s imprisonment of political opponents, and in Colombia, where activists last February used Facebook to organize one of the largest protests ever held in that country, a nationwide series of demonstrations against the FARC insurgency. Not long ago, the State Department created its own group on Facebook called “Alliance of Youth Movements,” a coalition of groups from a dozen countries who use Facebook for political organizing. Last month, they brought an international collection of young online political activists, including one from the April 6 group, as well as Facebook executives and representatives from Google and MTV, to New York for a three-day conference. IN RECENT MONTHS, Ahmed Maher has edged Rashid out of the leadership role they initially shared. When she was in jail, Rashid gave Maher the password to be the administrator of the April 6 Facebook group. He changed it, and ever since, he has declined to tell her the new password. Soon after Rashid was released from jail, she was married and left for her honeymoon. In May, Maher says, state-security officers picked him up and beat him intermittently for 12 hours to try to get him to give up the password for the Facebook group. Abbas posted pictures of Maher’s bruised back on his blog, and an opposition newspaper printed Maher’s account of the incident. Maher and other April 6 members set up a variety of steering groups for the movement, each of which is also on Facebook; using the wall, steering-group members discuss and vote on the direction the movement should go next. The new steering groups are not open to everyone, as the original group is, and Rashid has not been invited to join. Some Egyptian bloggers and activists told me they resented Rashid’s emotional display when she was released from jail — particularly the fact that she said she wouldn’t have organized the protest if she’d known she would be arrested for it. (Rashid later recanted that apology at a meeting of the April 6 group; she quoted a lyric from a Mohammed Mounir song: “I didn’t need to repent; loving Egypt is not a sin.”) Abbas told me that other female activists, including the blogger Asmaa Aly, had been arrested before — Aly spent a month in jail in 2006 for participating in a Kefaya-organized sit-in for judicial independence — and when they were released, they didn’t cry or apologize. “What the hell was she saying?” Abbas asked, referring to Rashid’s televised apology. “The girl is chicken. I am sorry to say stuff like that, but people are going to think that everyone who is active online is chicken like her. We are in the streets taking videos and photos. We aren’t only sitting in our bedroom in our pajamas.” (Once, looking at Rashid’s Facebook profile with her, I pointed out that Facebook’s software had included Wael Abbas on her page, under a tab labeled “People You May Know.” Rashid looked at his picture and shook her head. “We will not be friends,” she said firmly.) Ahmed Maher and a number of his friends in the activist-blogger community spoke with respect about what Rashid had accomplished, but they agreed with Abbas that she didn’t have the right stuff to run the movement. Some activists working with Maher questioned her lack of experience and said it wouldn’t be appropriate for a woman to lead the group, given that the government had tortured Ahmed Maher and sent Rashid to prison once already. Rashid says she is not happy about any of this. When she and I met in early October, she said that a month earlier, at the beginning of Ramadan, she told Maher he had until the end of the holiday to give her back the password. Now Ramadan had just ended. “The longer he takes, the more forceful my response will be,” she said fiercely. It was in many ways the unideological, unedited voice that Rashid represented — someone who described herself as “a girl who loves Egypt” and who thought giving flowers to the police might be a good idea — that attracted people to the April 6 movement in such numbers. Young people were drawn to the fact that the movement wasn’t part of Egypt’s calcified party politics. (“I am involved in no parties, never,” one teenage boy told me at a protest. “I just go to Facebook events, wherever they are. I’m in the Facebook Party.”) But for April 6 to keep growing, some say, that may have to change. As Amr Hamzawy, an Egyptian political scientist who is currently a senior associate at the Carnegie Endowment for International Peace, told me: “Just saying you are against Mubarak automatically gets a certain number of people behind you, but it’s not enough. Kefaya wasn’t capable and ready for the next step. They needed to put forth a positive platform as well as a critique of Mubarak in order to move beyond the base of elites in Cairo. April 6 will have to do this. It will have to become more organized in order to succeed where Kefaya failed.” THE APRIL 6 STRIKE was a success partly because it had its roots offline, among a cohesive, organized group of laborers; their protest was then vastly amplified by the Facebook activists. A number of the events created last summer and fall by the April 6 Youth Movement did not succeed in the same way. Protests were typically attended by only a few dozen of the group’s supporters and often shut down by the police before they even began. Back in July, Maher tried to organize a “flash mob” on the beach in Alexandria that would sing patriotic songs and fly a kite with the Egyptian flag painted on it. But on the day of the protest, Maher and his crew of about 30 young people were stopped by the police before they were even able to finish unfurling their kite. This month, as the university exam period began to cut into members’ free time, the group’s involvement in Gaza protests seemed to diminish. The decline in turnout led to a flurry of accusations, reflections and recriminations on Facebook. On Jan. 10, a young woman named Asmaa Mahfouz posted an angry screed on the April 6 site titled, “Are you all fed up, or what?” She accused members of opting out of protests because they thought things couldn’t change, no matter how many strikes and demonstrations were organized. “Is this a reasonable way of thinking???!!!” she wrote, punctuation marks flying. “Is it reasonable???? No, no, no, nooooo, absolutely not!” A young man named Mahmoud Dahshan Ahmed replied that he thought the group needed to coordinate with the Muslim Brotherhood if they were to have an impact. “Frankly, I am fed up,” he wrote. “What is the point of us demonstrating and marching from noon till 6 p.m., when nothing ever changes?” By organizing online, the April 6 movement avoids some of the pitfalls of party politics in Egypt — censorship, bureaucracy, compromise with the regime. But whenever the movement’s members try to migrate offline, they find they are still playing by Egypt’s rules. They almost never meet in real life, certainly not in large groups, and when they do, the police often show up. Online, members of the movement are casting votes on the Web site’s walls, publishing notes with their views on the political situation and creating groups to draft a constitution for their movement. But what does it mean to have a vibrant civil society on your computer screen and a police state in the street? When I spoke to Nora Younis, she described the April 6 strike as a practice session for the new generation. “It’s a rehearsal for a bigger thing,” she said. “Right now, we are just testing the power of each other.” http://www.nytimes.com/2009/01/25/ma...loggers-t.html  Snark Attack!: David Denby's New Book Chronicles Web-Fueled Meanness David Sarno In his new book, "Snark," David Denby dons a lab coat and rubber gloves and plays taxonomist with the kind of odious and repellent writing the Web has come to produce. Denby, who is a film critic for the New Yorker, makes a point that many online readers might readily agree with: There's a lot of writing out there that's pointlessly mean, cheap, empty and thoughtless — and it's getting old. But the book goes further, suggesting that snarky bloggers, journalists and commenters have become a kind of intellectual scourge that's "ruining our conversation" — and it's this grander, more damning claim that deserves scrutiny. I spoke with Denby about his book, the Web and whether snark — which he sees as a kind of journalistic "pinkeye" — is spreading as fast as he would like us to believe. Q: A few reviewers have snarked that you've had trouble succinctly defining the term "snark." Want to give it another shot? A: Well, the contemporary version is the kind of nasty, insidious, rug-pulling, teasing insult, which makes reference to some generally understood shared prejudice or distaste. It's metastasized as a pop writing form. And the Internet, of course, spreads this stuff around virally, so it replicates itself and goes everywhere. ... Q: Dang Internet! A: Everyone I know in journalism is in a panic at all levels. Old media types like me are worried that our beloved publications are going to subside into just electronic versions. And they'll have much less authority than they do in hard copy. In other words, once they're only on the Web, they'll just seem like a point of view rather than an authority. Q: I see what you're getting at. But why would one medium (print) confer inherently more authority than another (the Web) — if what's being said is the same? Aren't ideas ideas, and words words, no matter if they're on a piece of paper or a screen? A: I'm afraid the great papers and newsmagazines will decline in authority for two reasons: When they're no longer uniquely there, on the breakfast table, in our hands with morning coffee, they will join an immense chorus of voices clamoring for our attention — there will be a flattening-out effect; and second, I wonder if they will continue to do some special things like investigative reporting, the beautifully crafted sports story, the long book, concert and movie review that they've done well in the past. Q: To be a skeptic for a moment: If you think of the Web as a giant cherry tree, with millions of blogs and news sources, academic journals and discussion groups, you could really cherry-pick examples to illustrate just about any trend you'd like. And to be sure, there are enough snarky cherries to fill a fleet of dump trucks. But the Web also has enabled plenty of high-level discourse too. Is it fair to say that the claim that snark is infecting the national conversation might be a bit exaggerated? A: The Internet is the greatest revolution in democratic practice since popular suffrage. Everyone knows that, and I am just as dependent on the Internet as anyone else. In the wake of a democratic revolution like that, there's both an enormous explosion of information and expression, much of it useful or fun, and also an explosion of pent-up rage, social anguish, resentment, bilious, other annihilating nastiness, prejudice and all the rest of the dark side. If that stuff is destroying conversation threads, screwing up people's reputations, spreading around unchecked rumor or just snark, it's worth pointing to it and saying, "Stop lousing up my revolution." The point of the book is to protect the best kind of humor by criticizing the worst. Q: We're talking a lot about trends in media rather than just bad or nasty writing. It seems like you might be saying that snark is a kind of symptom of the decay of quality journalism. A: Absolutely. To tell you the truth, I wrote the book in a sweat last spring and summer, and I wasn't totally conscious of what was really bothering me. Q: Well OK, for any of us who write online, whether it's articles, blog posts or comments in a discussion thread, is there a litmus test for snark we can apply to our words before we press 'publish'? A: Well that's hard, but let me try. If you're going to attack someone personally, ask yourself whether the writing creates a fresh image, whether it has a physical quality which brings it to life. The trouble with snark is that it doesn't engage. It's almost bulimic: It takes something into its mouth and then regurgitates it. So that's something you can ask yourself: Am I really engaging with the subject or am I just trying to show off and be clever? Dorothy Parker always said she revised four words for every three that she wrote. And that can be very hard when there's this one-hour deadline to write 1,000 words. So I think snark is inherent in that hyper deadline pressure. Q: You don't talk much about the world of movie criticism in the book. Is snark a danger in your world too? A: When you're talking about criticism, your words are a performance and you're judging someone else's performance. Certainly if you think something is terrible, you have the obligation to entertain the audience, especially if you're writing at any length. So it seems snark is going to creep into that with even the best intentions at times. But there's a difference between what's purely destructive and what's criticism. If you describe something clearly — no matter how nasty you are — I don't think that's snark; I think that's criticism. Q: You're not carving out a snark exception for movie critics, are you? A: In libel law, you can say virtually anything in criticism because it's considered fair comment. But I don't think you should use that as an excuse for writing badly. Put it that way. Q: OK then. You say in the book that snarky writers are "cutting the path of their own extinction." Do you think, as a rhetorical strategy, it might lose its oomph any time soon? A: The trouble with snarking writers is that if they don't up their game at some point, styles and humor change, and they'll get fired. Don't underestimate the cynicism and pragmatism of editors. They'll use you because snark creates a little storm every time it appears, but then they lop you off when styles and humor change. So if individual writers don't develop something more serious to say about human nature, rather than just reflecting the zeitgeist in the media world, they're not going to last. http://www.courant.com/features/book...,4566110.story  EU Could Force Microsoft to Bundle Firefox with Windows The European Commission could force Microsoft to bundle Firefox with future versions of Windows. The revelation came as part of Microsoft's quarterly filing with the Security and Exchange Commission. Among the statements is a clause outlining the penalties being considered by the European watchdog, which recently ruled that Microsoft is harming competition by bundling Internet Explorer with Windows. The most interesting situation outlined in the filing would see either Microsoft or computer manufacturers forced to install Firefox, Chrome, Opera and Safari by default alongside Internet Explorer on new Windows-based PCs. "While computer users and OEMs are already free to run any web browsing software on Windows, the Commission is considering ordering Microsoft and OEMs to obligate users to choose a particular browser when setting up a new PC," the company reports in the filing. "Such a remedy might include a requirement that OEMs distribute multiple browsers on new Windows-based PCs. We may also be required to disable certain unspecified Internet Explorer software code if a user chooses a competing browser." Non-compliance would see the EU impose a "significant fine based on sales of Windows operating systems in the European Union", the filing further notes. Microsoft has two months to respond to the charges, after which the EC will make its final ruling on the matter. The software company can also request a hearing and says it's considering this alternative. Should Microsoft be charged, the penalty could come into effect in time for the release of Windows 7, which is expected either later this year, or early 2010. http://www.pcpro.co.uk/news/245994/e...h-windows.html  NZ Man Finds US Army Files on MP3 Player A New Zealand man has found confidential United States military files on an MP3 player he bought at an op shop in the US. Chris Ogle, 29, from Whangarei, bought the player from an Oklahoma thrift shop for $NZ18 ($A14.50), and found the files when he hooked it up to his computer, TV One News reported on Monday night. The 60 files on the player contained the names and personal details of American soldiers, including ones who served in Afghanistan and Iraq. There was also information about equipment deployed to bases and a mission briefing. "The more I look at it, the more I see and the less I think I should be," Ogle said. Victoria University strategic studies director Peter Cozens said one of the first rules of military endeavour was to not give the opposition information that could compromise your position. "This is just slack administrative procedures which are indeed a cause of embarrassment. It's the sort of thing which ought not really be in the public domain, he said. Ogle said the player never worked as a music player and he would hand it over to the US Defence Department if asked. http://news.theage.com.au/breaking-n...0126-7pxt.html  Canada Post Plays Grinch in Censorship Row Michael Geist Late last year, Canada Post and the Public Service Alliance of Canada became embroiled in a heated strike over sick-pay benefits. In the midst of the dispute, several PSAC members took direct aim at Canada Post CEO Moya Greene, recording a short parody video titled The Greench. The video, which was posted on YouTube, adapted the well-known Dr. Seuss tune You're a Mean One, Mr. Grinch to criticize Greene and the company. While the creation of a protest video is not particularly noteworthy, what followed soon after is. Just as the video began to attract some attention, YouTube removed it after receiving a complaint from Canada Post alleging the video violated the company's copyright. The case highlights a common occurrence under United States law, which allows copyright owners to file complaints with Web hosts such as YouTube if they believe the site is hosting infringing content. Under the law, the Web host avoids liability if it immediately removes the content. No court or independent third party reviews the infringement claim since nothing more than a complaint that meets certain criteria is needed. The statutory requirements include providing a statement that the complainant has a "good faith belief that use of the material in the manner complained of is not authorized by the copyright owner, its agent or the law." YouTube may simply have been following the law, but the decision caught The Greench creators by surprise since the song featured original lyrics based on an obvious parody of the Seuss character. Moreover, it was not the Dr. Seuss rights holders who filed the complaint, but rather Canada Post. When asked about the case, a Canada Post spokesperson stated the claim was based on the inclusion of a picture of the Grinch character with a discoloured headshot of Greene that appears for nine seconds in the video. The strike may have concluded, but the reverberations from the video takedown have not, since Canada Post may have opened itself up to possible liability with its claims of copyright infringement. Last year, a California court ruled Universal Music could face liability for demanding the removal of a home video featuring a two-year-old dancing in their family's kitchen with the song Let's Go Crazy by Prince playing in the background. Stephanie Lenz, the mother of the two-year-old in the video, fought back by suing the music company for wrongly filing the takedown demand. The court concluded copyright owners should consider whether the use of their work could qualify as "fair use" in order to meet the good faith belief standard. The same claim would seemingly be available to The Greench creators, since their brief use of the Greene photo would surely qualify as fair use under U.S. law. Should The Greench creators pursue the case, a ruling against Canada Post might serve as a disincentive against the use of takedown notices that appear rooted in attempts to censor rather than enforce copyright. Indeed, the incident is not the first time a Canadian company has tried to use the U.S. notice-and-takedown system to quell online criticism. In 2007, Telus demanded that YouTube remove 23 videos, including several featuring original union songs. YouTube took down the videos, but a legal challenge to Telus' claim is currently before the courts in California. As the cases wind their way through the legal system, they provide an important reminder about the dangers associated with the notice-and-takedown rule. Canada has yet to implement such an approach and the experience to date reinforces concerns that legally mandated removal of content from the Internet without court oversight opens the door to abusive practices that may have little to do with protecting the rights of copyright owners. http://www.thestar.com/article/577112  Mobile Broadband Providers Promise More Clarity Over Download Speeds Richard Wray Consumers are to be given much more information about the connection speeds they can expect to receive when they sign up to mobile broadband services under a new code of conduct being drawn up by the UK's networks. Sales of mobile "dongles" – devices that enable PCs and laptops to access the internet using a mobile phone network rather than a landline – have rocketed, with over a million sold last year as prices came down to as little as £10 a month. But customers are becoming frustrated with slow download speeds and patchy network coverage, especially inside buildings. Several mobile phone companies have seen return rates increase recently. The code also comes at a crucial time for the mobile broadband market. Using mobile networks to access the internet will play an important role in communications minister Lord Carter's ambition to have a universal broadband service by 2012. His initial report into "Digital Britain", to be published next week, will include a promise to provide broadband for all by using wireless networks to fill in gaps in the fixed-line coverage. Research by regulator Ofcom last year showed that mobile broadband is significantly slower than fixed-line, with customers being offered headline speeds of up to 7.2Mb per second, but receiving just 1Mb per second. That is too slow to watch standard-definition video services such as the BBC's iPlayer. In contrast, the average actual fixed-line broadband speed is 3.6Mb per second. Complaints from fixed-line customers that the speeds they were receiving bore little resemblance to those advertised caused regulator Ofcom to threaten legislation last year. Providers quickly thrashed out a voluntary code of conduct, which came into force last month, under which they must provide an accurate estimate of actual maximum speed. ISPs must also explain to customers the factors that determine the actual broadband speeds they can receive and give guidance on how to improve their connections. Now the mobile phone operators are looking to see off the potential threat of regulation in mobile broadband with their own code. It will focus on hints and tips for consumers that will help improve the performance of their mobile broadband service. But the operators are unlikely to be able to provide customers with a clear estimate of the speed they can expect to receive. That is because the performance of the mobile phone networks depends not only on exactly where the user is located but on how many other people are using the network at the same time. http://www.guardian.co.uk/technology...d-mobilephones  Internet Users Worldwide Surpass 1 Billion Dawn Kawamoto McDonald's restaurants and global Internet usage share something in common: more than 1 billion served within a month. Global Internet usage reached more than 1 billion unique visitors in December, with 41.3 percent in the Asia-Pacific region, according to a report released Friday by ComScore. The study looked at Internet users over the age of 15 who accessed the Net from their home or work computers. Europe grabbed the next largest slice of the global Internet audience, with 28 percent, followed by the United States, with an 18.4 percent slice. But Latin America, while comprising just 7.4 percent of the global Internet audience, is the region to watch, noted Jamie Gavin, a ComScore senior analyst. "The U.S. is slowing down in its growth and momentum, but Latin America, with social networking and the mobile Internet, is expected to gain momentum over the next few years," Gavin said. He noted that while population plays a role in aiding certain regions to lay claim to a larger Internet audience, another equally important factor is the ability of the Internet to easily cross borders and take root. A closer look at countries within the regions reveals that China accounted for the most Internet users worldwide, with a 17.8 share of unique visitors. The United States ranked second, with 16.2 percent, and Japan ranked a distant third, at 6 percent. Across specific Internet properties, Google carried a sizable share of the global Internet market, visited by 77 percent of the worldwide audience, or nearly 776 million users. Microsoft Web sites were used by 64.2 percent of users worldwide, and Yahoo sites 55.8 percent, according to ComScore. Sites run by Time Warner's AOL, meanwhile, were used by 27.1 percent of the worldwide Internet audience. http://news.cnet.com/8301-1023_3-10149534-93.html  Irish Government to Spend $362 Million on Broadband Infrastructure Drew Clark The government of Ireland on Thursday announced a “National Broadband Scheme” to deliver broadband throughout the island nation, investing €223 million (U.S. $362 million) on high-speed internet infrastructure. Ireland currently has over 1.2 million subscribers to broadband, according to the government of Ireland, which provides a detailed map of broadband availability by location, by company and by speed. The National Broadband Scheme will provide broadband to the remaining 10% of Ireland’s population — or approximately 33% of the area of the country. (See Ireland’s map.) Under the plan, Ireland aims to have 100% coverage by September 2010, with half of the area under the scheme will be covered by the end of 2009. The Irish government’s announcement comes at a time when the United States Congress is considering a potential U.S. $6 billion investment in broadband infrastructure as part of the stimulus package. See BroadbandCensus.com’s Broadband Wiki for coverage. With a population of 4.2 million, the $362 million Irish investment amounts to a per capita investment in broadband of $87 per Irish citizen. If the $6 billion figure passed by the House Appropriations Committee continues, the proposed investment would amount to a per capita investment in broadband of $20 per United States citizen. In other words, the proposed $6 billion investment is less than four times smaller, on a per-capita basis, than the Irish investment announced on Thursday. According to the Irish government, the $362 million will come from a combination of Exchequer funds, EU co-financing and from the private sector. It is expected to create 170 direct jobs. Hundreds more will be protected and created as the availability of broadband increases the investment and enterprise in the targeted areas, said the Irish government. Announcing the scheme, Communications Minister Eamon Ryan said, “For too long, rural Ireland has been without this essential service.Today’s announcement is a boost for the rural economy. Now businesses throughout the country can have ready access to the national and international markets. Employment will be created and sustained. Quality of life will improve for rural residents and communities will be strengthened.” Following the conclusion of a competitive tendering process, the $362 million contract was awarded to the company named ‘3,’ a Hutchinson Whampoa company. Robert Finnegan, CEO of 3, commented: “3 is delighted to have won the NBS tender - it’s great news for 3 and for rural Ireland. We’ll be rolling out our first class broadband network bringing internet services to thousands of homes and businesses across the country.” ‘3’ will extend its network to provide mobile wireless broadband services into the NBS area. Initially, the service will have a minimum download speed of 1.2 Megabits per second (Mbps). At least two upgrades of speeds are planned during the lifetime of the contract. These product upgrades will be carried out at no cost to the customer, said the government. “Over five years we’ll be investing 223 million euros and creating around 170 new jobs giving Ireland’s economy a welcome boost,” Finnegan continued. “There has never been a more important time for people to get connected as Ireland strives to sharpen its competitiveness. 3 has already played an important part in bringing Ireland up to speed in the broadband league tables and we look forward to further strengthening 3’s market leading position with the most innovative and services and best value price plans available.” http://broadbandcensus.com/blog/?p=1295  Wikipedia Considers Limiting User Edits Jennifer Guevin Just as Encyclopedia Britannica is moving in the direction of user-based entries, Wikipedia might soon be clamping down on theirs. Wikipedia is apparently considering instituting a new editorial process that would put better safeguards in place and require all updates to be approved by a "reliable" user. The so-called Flagged Revisions process would allow registered, trusted editors to publish changes to the site immediately. All other edits would be sent to a queue and would not be published until they get approved by one of Wikipedia's trusted team of editors. The proposal comes in the aftermath of a false entry that was posted by a user, saying Senators Ted Kennedy and Robert Byrd had died after an inaugural luncheon last week. On his public discussion page, Wikipedia founder Jimmy Wales said, "This nonsense would have been 100 percent prevented by Flagged Revisions," adding that the system gives the site the flexibility to cover breaking news stories quickly while avoiding some of the shenanigans it's seen in the past. The German version of Wikipedia has been using the system for a while now (partially since May and fully since August, according to one Wikipedia user). But Wales himself points out one major problem with the German model, citing delays of up to three weeks before edits get approved and go live. "Our version should show very minimal delays (less than 1 week, hopefully a lot less)," wrote Wales, "because we will only be using it on a subset of articles, the boundaries of which can be adjusted over time to manage the backlog." Which subset of articles would be flagged and exactly how those boundaries would be set isn't clear from the discussion. Wales writes in his comments that 60 percent of users who responded to a poll approved of the move. Think Wikipedia's plans are a bad idea? There's time to give your input. Wales has asked people opposed to the Flagged Revisions plan to propose other workable solutions to the problem of wiki malfeasance. http://news.cnet.com/8301-1023_3-10149648-93.html  GateHouse Media Case Against NYTimes Goes to Trial Denise LaVoie On one side is GateHouse Media, one of the nation's largest publishers of community newspapers. On the other is The New York Times Co., the parent company of The Boston Globe and its Boston.com Web site. The two publishers will square off in federal court this week in a case that is being closely watched by journalists, bloggers and Internet users. GateHouse filed a copyright infringement lawsuit last month, claiming that the Globe's new community Web sites use online material from GateHouse without permission. GateHouse claims Boston.com violates copyright and trademark laws by taking GateHouse's newspaper headlines and lead sentences published on its "Wicked Local" Web sites. GateHouse alleges that Boston.com offers links that send readers directly to "Wicked Local" stories _ bypassing ads posted on home pages that help fund its operation and creating confusion on the source of the original reporting. Last fall, Boston.com launched three "Your Town" community Web sites that cover the cities of Newton, Waltham and Needham. The Globe said that the three towns were the first in a series of more than 100 "hyperlocal" Web sites it plans. In its lawsuit, GateHouse claims that Boston.com is building community-oriented sites that rely on the work of GateHouse reporters. News organizations and bloggers say the case could have far-reaching implications for determining how much content one news organization or Web site can use from another. "It's certainly being followed within the journalism community, but this is huge in new media and blogging because God help us if a judge or a jury starts to lay down rules as to what constitutes acceptable linking practices and what isn't," said Dan Kennedy, an assistant journalism professor at Northeastern University who has been blogging about the case on Media Nation. Gregory Reibman, the editor-in-chief of the metro unit of GateHouse Media New England, said in an affidavit that many online readers only read headlines and lead sentences and do not click through to the full stories. He said that when readers do click through from the "Your Town" links, they bypass the ads on Wicked Local's home pages. "If the Boston Globe wants to compete with us in Newton and the other communities we serve, they should approach it fairly," Reibman said in the affidavit. "They should hire and pay their own journalists. They should generate their own original content and nurture their own contacts within the community." Ira Levy, an attorney for The New York Times Co., declined comment on the case before trial. Anthony Scibelli, an attorney for GateHouse Media, also declined comment. Catherine Mathis, a spokeswoman for The New York Times Co., declined comment on Friday, but said earlier that the company believes GateHouse's claims are "without merit." "Boston.com's local pages, like hundreds of other news sites, aggregate headlines and snippets of relevant stories published on the Web. They link back to the originating site where the interested user can read the entire article," Mathis said in a statement on Dec. 22. "Far from being illegal or improper, this practice of linking to sites is common and is familiar to anyone who has searched the Web. It is fair and benefits both Web users and the originating site." Bill Mitchell, director of Poynter Online, said the case is about more than just linking. "I think it's a very tricky, interesting issue because on the one hand if I were in GateHouse's shoes, I'd feel well-served by links from the bigger Boston.com. On the other hand, the extent to which users find themselves sufficiently satisfied just by looking at the Globe hyper local site, that really undercuts what GateHouse is trying to do," Mitchell said. GateHouse, based in Fairport, N.Y., owns 97 daily newspapers, 400 other publications and 260 related Web sites reaching more than 10 million people in 21 states. Its Massachusetts publications include The Patriot Ledger, The Enterprise, the Newton TAB and the Daily News Tribune of Waltham. The trial is scheduled to start Monday in U.S. District Court. http://www.washingtonpost.com/wp-dyn...012501212.html  NYT, Gatehouse Release Settlement Details Robert Weisman GateHouse Media Inc. will set up technical barriers preventing Boston.com, the Boston Globe's website, from automated "scraping" of GateHouse content, and Boston.com has agreed to honor those barriers under a settlement disclosed this morning in a widely watched lawsuit filed by GateHouse against The New York Times Co. Gatehouse, based in Fairport, N.Y., operates 125 community newspapers in Massachusetts. It filed the lawsuit on Dec. 22, charging copyright infringement. At issue was the practice of posting headlines and short excerpts of text along with links to stories on other sites. Boston.com recently launched three "Your Town" websites serving Newton, Waltham, and Needham, which compete with the "Wicked Local" sites run by Gatehouse. The Times Co., which owns the Globe and Boston.com, also agreed in the settlement to remove headlines and lead sentences from GateHouse stories previously posted on Boston.com's Your Town sites. The parties notified a judge of the settlement in US District Court in Boston, where a trial had been set to begin today. The settlement reflected the reality that GateHouse can technically block Boston.com's computer program from retrieving stories for conversion to links from GateHouse's Wicked Local blogs, which cover dozens of communities across Massachusetts. GateHouse had not previously established an effective barrier to prevent such scraping of its stories. There was no agreement by the Times Co. to stop using headlines and snippets from non-GateHouse stories it links to. "We stand by our position that the use of headlines and ledes is fair use, and we will continue to link appropriately," said Bob Kempf, vice president of product and technology for Boston.com. As such, the settlement left unresolved the legal issue issue that drew the attention of news and technology companies, as well as Internet bloggers: whether news websites - especially aggregation sites, including Google News and Yahoo News - can continue with their current practice of posting headlines and lead sentences for stories they link to from other sites. Boston.com will be able to refer to stories from GateHouse sites, as it has done in the past, and to manually "deep link" to individual articles without presenting the links with headlines or lead sentences. "This agreement is not binding on anyone else," said David Ardia, director of the Citizen Media Law Project at Harvard's Berkman Center for Internet and Society. "It has no legal precedent per se. But it could persuade a judge in another case that what Boston.com was doing here was not defensible under fair use" in copyright law. No damages were awarded under today's settlement, and each party agreed to pay its own legal fees. Neither the Times Co. nor GateHouse admitted wrongdoing. Ardia, however, described the settlement as a victory for GateHouse. "They seem to have achieved everything they wanted to in their lawsuit except for receiving monetary damages," he said. "It does result in the cessation of Boston.com using GateHouse content as it has done." As for discontinuing the use of headlines and lead sentences from Wicked Local stories, Kempf said Boston.com has traditionally respected the decisions of third-party content providers that use technical barriers to block their content. "We are reaffirming our longstanding practice of respecting technical barriers," he said. "We've always complied with those barriers and will continue to do so. I would not characterize implementation of such readily available protocols as a victory [for GateHouse]." Kempf said the Globe's website will continue to expand its "hyperlocal" Your Town sites to other communities. "We've been very encouraged by the initial reponse to the hyperlocal sites from both audience and advertisers," Kempf said. "So we're going forward with the local sites - full speed ahead." Despite today's settlement, Kempf said a big part of Boston.com's local strategy will continue to be aggregating content from a broad spectrum of local sources, from independent blogs to high school and college sites, to community calendars and sports events. Kirk A. Davis, president and chief operating officer of GateHouse Media, said that the settlement reaffirmed the value of original reporting. "I think the settlement provides GateHouse with all the essential relief on the issues that caused us to bring this action in the first place," Davis said. "We're completely satisfied with the outcome." Davis said GateHouse had attempted in the past to block Boston.com from scraping its content, but to no avail. He declined to elaborate. To read the full agreement between GateHouse and the Times Co., please click here. http://www.boston.com/business/ticke...tehouse_r.html  Internet Users in Jiangsu Face up to $731 Fine for Online Privacy Breach Chen Shasha Internet users in Jiangsu Province that reveal personal information of other individuals online will face fines of up to RMB 5,000 ($731) and a six-month block on their IP address, according to a provincial regulation released on Jan. 18. The newest online privacy regulation, released by the Jiangsu provincial government at the 11th People's Congress of Xuzhou City, covers the release of sensitive information online such as addresses, occupations, salaries and women's ages. This marks the first detailed online privacy regulation in China. In addition, the regulation also states that all Internet bars and hotels with online access in Xuzhou City must ask users to register using their real name, and records must be kept for at least 60 days. Any Internet bars and hotels that do not adhere to the new regulations will have their business license revoked. China began to introduce regulations to protect personal information in 2008, when the Chinese government added an article to the country's Criminal Law in August, prohibiting the distribution of personal information collected by companies or individuals of those working in the financial, telecommunication and health care industries. Interfax commentary: More provinces are likely to follow Jiangsu's lead and issue online privacy regulations, as 2008 saw a sharp rise in the number of lawsuits relating to online privacy breaches. The new policy will be a major blow to companies that sell personal data and thus will impact China's SMS (short message service) advertising market. However, it is unlikely to deal with the rise in human flesh searches in China, although search engines are already working on a technological solution to the problem. http://tmt.interfaxchina.com/news/1226  Get Naked!: They're Folk Singers And, Yes, They're Naked Lini S. Kadaba Cello players, of course, really can't complain. And the surfer babe with the sultry voice ensures comfort — by the acre — as she peeks out from behind her board, Shore waters lapping at her heels. A banjo, though, looks awfully skimpy as the only cover for the bare breasts of Peggy Seeger, the septuagenarian activist songmaker who is Ms. October in the latest Naked Folk calendar. "That's real intimacy," allowed Jayne Toohey of Media, Pa., a jovial free-lance photographer who conceived the pinup project to promote folk music and benefit musicians. "You would never expect that I'd travel around the country photographing naked musicians." Yet, she does, by the dozens. This year, after a year's hiatus, marks Toohey's return to making Naked Folk calendars aimed at funding health insurance for self-employed musicians through the Folk Alliance, a Memphis nonprofit. The naked calendar genre took off with the 2003 movie "Calendar Girls," which chronicled the true-life tale of several British women who (sort of) bare all to raise money for cancer research. Since then, photos of firemen, socialites, even Rotarians in the near-buff (with tasteful concealment of the most private of parts) have covered kitchen walls and office cubicles, often for the good of charity fund-raisers. So why not naked folk artists? Toohey, 51, a longtime folkie, got the idea in 2002, soon after she was hired to shoot a CD cover of Full Frontal Folk, a then all-female, Philadelphia band. She told the chicks: "Girls, with that name, you gotta get naked." Four women stood sideways in a compact row, arms and hands strategically positioned. The mildly titillating, waist-up picture got Toohey and a friend thinking of folk favorites they wouldn't mind seeing in the flesh, so to speak. "We laughed about it a lot," she said. Toohey, who has long haunted music festivals with her Nikon, asked a musician or two whether they would pose naked for her. Some actually answered in the affirmative. "These are normal people," she said, many of them middle-aged. The pleasant redhead doesn't know why exactly, but people say they trust her. Her first calendar, featuring Grammy-nominated Janis Ian in her 50s on its cover, came out in 2005. Toohey, who takes the plunge herself with an author photo, has produced Naked Folk ($20) each year since then, except last year. John "Mr. May 2007" Flynn, a singer and songwriter who lives in Wilmington, Del., got naked (well, he did have on a teeny-weeny brief behind that log he's splitting with a sledgehammer) after a lengthy courtship. "I was playing hide-and-seek with her for a long time," he said. "If there was ever a reason God invented clothes, it was probably for folk singers. We're not a group that people are clamoring to see." Finally, he woke up one day, looked in the mirror, and thought, "It's not going to get any better." His challenge? "It took more bug spray than I thought." Oh, and his wife drove up in the middle of the shoot. "I forgot to tell her," he said. "She's a good woman." Toohey has captured musicians standing in snow, riding bareback, sitting at a bar, or curled in front of the fireplace in her living room. Along the way, she learned that many musicians struggle to afford health insurance. "It's so outrageously expensive," she said. That led to her commitment to donate calendar proceeds toward an insurance fund. So far, profits have been nil, she said. Toohey sold about 800 calendars in 2007, and she said she actually loses money on the project, which costs about $20,000 a year to produce. "I've pretty much put my heart and soul and bank account into it," she said. Ironically, she cannot afford health coverage for herself, she said. Louis Meyers, executive director of the Folk Alliance, praised the calendars. One of his favorite shots in the 2009 lineup spotlights singer and songwriter Jim Photoglo (March). The veteran performer is usually rather reserved. Yet there he stands, in nothing but an apron and chef's hat in his kitchen as he croons into a soup ladle. "It's the one that makes me laugh the hardest," Meyers said. Besides the chuckles, Meyers said the calendar — the latest is replete with notable folk history dates and festival schedules — can help expose the public to the breadth of talent embodied in folk music. It's not just "old guys with banjos around campfires," he said. "It is so much more. ... It's become the adult alternative." Many Folk Alliance members anticipate the calendar, he said. Some musicians have been known to proudly proclaim: "I got naked for Jayne." Folkies collect the calendars, and the images can serve as archival portraits, especially for musicians such as U. Utah Phillips (May 2006), who have since gone to that big folk festival in the sky. To recruit, Toohey passes out GET NAKED buttons at gatherings. In reality, subjects might have a bit more cover than it would appear. A few keep underwear or swim trunks on, though Toohey has no qualms about ordering the offending article off if it interferes with the shoot. More often, she positions props, like that bowl of mangoes, just right. "It's the illusion," she said. "You're covered. Some are very covered." Her goal now is to snag a celebrity name, maybe an Arlo Guthrie. Or a Jackson Browne. "That would make a great shot," she said, imagining the bare-skinned possibilities. http://www.courant.com/features/hc-w...,1148880.story  Senate Approves Digital TV Delay The Senate voted on Monday to delay next month’s transition to digital television until June 12 because some viewers would not be ready for the switch. The voice vote followed a call by President Obama’s administration to postpone the Feb. 17 date for major TV stations to stop sending traditional analog signals. Similar legislation awaits action in the House on Tuesday. Senator John D. Rockefeller IV, Democrat of West Virginia who leads the commerce committee, said last week that he had reached agreement with Senator Kay Bailey Hutchison of Texas, the top Republican on the panel, on the legislation. Some Republicans had opposed a delay, saying it would cause confusion by changing a long-planned date. A federal program to subsidize digital equipment that some viewers will need has fallen short of money, and last week the government reported a waiting list of 1.4 million households. More than 6.5 million homes are not able to receive digital TV programming, the Nielsen Company said last week. The figure is a decrease from last month, when Nielsen said almost 8 million could not receive it. http://www.nytimes.com/2009/01/27/bu...27digital.html  House Defeats Bill to Delay Digital TV Switch Brian Stelter Two days after the Senate unanimously approved a four-month delay of the digital television transition, the House of Representatives did not pass the same proposal on Wednesday, “leaving the current Feb. 17 deadline intact for now,” the Associated Press reports. “The 258-168 vote failed to clear the two-thirds threshold needed for passage in a victory for GOP members,” according to the AP. The legislation’s failure means that the nation’s television stations will have to switch from analog to digital broadcasting by Feb. 17, unless Congress takes other steps to delay the transition. House Democrats may bring the bill up for a regular floor vote next week. That vote would only require majority support to pass. “Wednesday’s vote took place under a special procedure that required two-thirds support for passage,” the AP reported. Earlier this month, calling the government funds to support the switch “woefully inadequate,” the Obama administration called on Congress to delay the Feb. 17 date. The switch requires consumers without a digital-ready TV who rely on over-the-air signals to install converter boxes for their TV sets. The Nielsen Co. estimates that more than six million households are still unready for the switch. Some lawmakers have argued that a delay would only exacerbate the confusion about the transition. And local stations have noted that they have already budgeted funds for next month’s switch. Keeping their analog signals on the air for four more months would require more money for power and maintenance costs. “In my opinion, we could do nothing worse than to delay this transition date,” said Joe Barton of Texas, the top Republican on the House Commerce Committee. “The bill is a solution looking for a problem that exists mostly in the mind of the Obama administration.” In a statement Tuesday, the Senate Commerce Committee chairman, John D. Rockefeller IV, said he was deeply disappointed by the Republicans’ move to block the transition. “Instead of delaying the transition to ensure that the most vulnerable among us have the ability to prepare for the transition, they have made certain that far too many consumers across the country will wake up on February the 18th and find that their television sets have gone dark and access to news, information, and vital emergency alerts will be unavailable,” he said. “It did not have to be this way — this situation was unnecessary and avoidable.” http://tvdecoder.blogs.nytimes.com/2...-tv-switch/?hp  Senate Approves Digital-TV Delay, Again The U.S. Senate unanimously passed another bill on Thursday to delay the national transition to digital television. Efforts to move the transition date to June 12 from February 17 are fueled by worries that an estimated 20 million mostly poor, elderly, and rural households are not technically ready for the congressionally mandated switch. President Barack Obama supports a delay in the switch. Earlier this week, the Senate passed another bill delaying the DTV transition, but the measure failed in the House of Representatives. The bill is essentially the same that previously passed the Senate, but with a few minor modifications from the House. Senate Commerce Committee Chairman John Rockefeller, a West Virginia Democrat, and Texas Republican Kay Bailey Hutchison worked out the compromise bill. Hutchison said the delay was voluntary and television stations could go ahead if they wished with digital transmission on February 17 as scheduled and drop analog transmission. The measure now goes back to the House. "The House will have a second chance next week to implement this delay. I am hopeful they will pass this bill so we can send it to President Obama," Rockefeller said. Broadcasters are moving from analog to digital signals to give public safety officials more spectrum, especially useful for emergencies, and to improve viewing quality. Only those who watch television on older sets that receive analog signals, and do not get cable, must act to prevent their screens from going black. About 6.5 million households are not ready for the transition, according to the latest data from Nielsen Ratings. http://news.cnet.com/Senate-approves...orsPicksArea.0  Digital TV Beckons, Many Miss the Call Jacques Steinberg Vesta Clemmons, who is 77 and lives alone, relies on the battered Zenith television in her tiny apartment here as more than just a lifeline to the outside world. “It’s like a friend,”” she said in her living room, which is also her dining room and bedroom. “I would feel very isolated without it. I get lonesome anyway.”” So Ms. Clemmons was concerned to learn from a public-service campaign that after Feb. 17 the rooftop antenna connected to her television would no longer function properly, and thus neither would her TV — unless she bought and installed an adaptor. On that day the country’s broadcast stations have long been scheduled to shut down the old-fashioned, analog signals that have carried their programming since the days of Milton Berle, and replace them with high-definition digital signals that offer a clearer picture, among other benefits. But less than a month before the Feb. 17 deadline, so many American households have yet to take the necessary steps to continue to watch over-the-air television — more than 6.5 million, according to Nielsen Media Research — that Congress has considered giving them more time. On Monday night the Senate passed a bill, supported by President Obama, that would extend the deadline until June 12. The House of Representatives took up the same measure on Wednesday but failed to muster the two-thirds majority needed for it to pass on a fast-track procedural vote. Its fate is now unclear. Regardless of when the switchover takes place, viewers with cable or satellite systems, and many others with digital televisions purchased after 2004, need not do anything in anticipation of the deadline, nor will they notice much of a change afterward. But for those older and low-income viewers like Ms. Clemmons who still use set-top rabbit ears or rooftop antennas to pull in images of “The Oprah Winfrey Show” or “The Young and the Restless,” the switchover to digital television has often proven a bewildering and cumbersome burden. That so many viewers here and around the country risk losing something as basic as a free television signal is a function, at least in part, of the government’s failure to anticipate that those most affected would be among the nation’s most frail and vulnerable. Further aggravating the confusion and uncertainty has been that a coupon program established by Congress to defray the cost of converter boxes — each American household is entitled to two $40 vouchers, which cover most, if not all, of the cost of the adaptors — ran out of money in early January, leaving hundreds of thousands of applicants to languish on a waiting list. (The program has already issued more than $1 billion worth of coupons.) Ms. Clemmons, a woman whose slight frame and white mane belie her taste in music — Pink Floyd, Ozzy Osbourne and Nine-Inch Nails are her favorites — said she had made several attempts to call the government’s toll-free number in recent days to request a coupon and had not been able to get through. Ultimately she received peace of mind from an unlikely source: Meals on Wheels. For several months now, drivers and volunteers for the Houston-area program have been delivering and installing digital converter boxes for its clients — as a side dish alongside the baked chicken and stewed peaches that are their usual fare. Ms. Clemmons’s turn came last week. In Houston, which is the nation’s 10th-largest television market and whose flat topography makes it relatively easy to watch TV with only an antenna, the problem is particularly acute: 1 in 10 households remains out of compliance, by Nielsen’s estimates, ranking it behind only Albuquerque and Dallas. Mindful of the need for such efforts, Consumers Union, the nonprofit advocacy group and publisher of Consumer Reports, is among those that lobbied Congress to put off the Feb. 17 deadline by four months. It has estimated the cost of replenishing the coupon program alone at nearly $1 billion, said Gene Kimmelman, vice president for international affairs. To defray the cost of the efforts by Meals on Wheels here, Interfaith Ministries for Greater Houston, the social service organization that administers the program, appealed last year to congregants in churches and synagogues around the city to donate the converter coupons they may have already received; more than 1,500 people answered that call. “After I heard about the process of what it would take for a person to get the coupon, and get the boxes, I was pretty livid,” said Bridget Samuel, chief operating officer for Interfaith. “I still go out on the routes making deliveries. Most of them are sitting in front of their TVs. They’re watching ‘Price Is Right.’ They’re watching ‘Judge Judy.’ That’s their company.” Meals on Wheels is hardly the only entity in Houston, or around the country, that has been trying to bring viewers’ outdated equipment into compliance. The National Association of Broadcasters estimates that its stations and networks, have, collectively, allotted more than $1 billion worth of advertising time to raise public awareness. The CBS affiliate here, KHOU-TV, ran a series of tests during its local newscasts in which viewers were told that the analog signal was about to be temporarily replaced by the digital one — and that if their screens go to a test pattern, they should call the phone number listed to learn how to get up to date. When KHOU and several other local stations ran the tests one day in December, nearly 14,000 viewers called the hot line in response. When the test was rerun on Jan. 6, 8,000 more calls were logged. KHOU also joined with a local grocery chain, H-E-B, for a series of promotional events at which thousands of customers lined up to apply for coupons, and, if they already had them, to buy converter boxes. Most were able to do so at no personal expense, with H-E-B having priced the boxes at $40, the value of the coupons. (Other electronics retailers have been charging as much as $100.) Through surveys of its nearly 4,000 clients, Meals on Wheels identified Ms. Clemmons as among those needing assistance. And so, on Jan. 21, Samantha Greenwood, the program’s assessment coordinator, arrived to install her converter box. As it turned out, Ms. Greenwood couldn’t get the converter, which is about the size of a cable box and is connected to both the antenna and TV, to work, because of some wiring problems in the back of Ms. Clemmons’s Zenith. But she vowed that her husband, an engineer, would return well before the Feb. 17 deadline to solve the problem. Ms. Clemmons, who risks losing access to “World News with Charles Gibson,” her favorite news program, said she would be waiting. Earlier that morning Ms. Greenwood had fared better in the apartment of Ramona DeFore, a widow in the same building who is also 77. On her own Ms. DeFore had gotten a coupon and a box but had been baffled as to how to connect it to her Magnavox TV, a set so old she couldn’t remember when she had bought it. After Ms. Greenwood made the connection successfully, Ms. DeFore was able to tune in Channel 2, the local NBC affiliate, for the first time in years. “I think Phil is on 2,” she said, with obvious excitement, in reference to “Dr. Phil.” “I’ve missed him. I wish I had him a few years back, when I had my husband.” http://www.nytimes.com/2009/01/29/ar...on/29ears.html  Awash In a Stream Of Movies David Pogue Any movie, any time. Is that too much to ask? It’s technically possible. It’s what the people want. It will make the movie companies rich. And yet not a single legal source of movies — hotel, plane, pay-per-view, video store, Apple TV, Vudu box, Internet downloads, nothing — offers instant delivery of any movie you want. Netflix comes close. It’s got the “any movie” part covered, since it stocks virtually every movie ever released on DVD — about 100,000 titles. As for “any time,” well, Netflix is best known as a DVD-by-mail company. You can freely rent and return DVD movies all month long for a fixed monthly fee ($9 to check out one movie, $14 for two at a time); they come and go in bright red, postage-already-paid mailing envelopes. There are no late fees or penalties. But “any time” boils down to “in a day or two,” because you have to wait for the movie to come in the mail. But Netflix has been clawing its way out of its dependence on the postal system with a feature called Watch Now — and it’s especially worth watching now. Phase 1. Twelve months ago, Netflix revealed the original Watch Now. It let you, a regular Netflix subscriber, watch any of 1,000 streaming movies on your Windows PC, on demand, without having to download them first. In the following months, the catalog grew to 12,000 movies; more are constantly added. Mac software came next. The monthly hours-of-watching limit was eliminated; now any Netflix member with a plan of $9 or more can watch unlimited streaming movies, for no extra charge. No extra charge is a crazy, game-changing concept. It transforms movie consumption from à la carte into all you can eat. You can watch favorite scenes of individual movies, or try a movie for 15 minutes and then change your mind. In short, you can movie surf, without ever worrying about running up your bill. Still, a desk chair in front of a PC is not what most people would call the ultimate home theater setup. Phase 2. Eight months ago, Netflix and Roku introduced a tiny TV-connected box ($100) that does only one thing, but very well: it lets you watch Netflix streaming movies on your TV instead of your PC. Since a remote control and a TV screen make a clumsy system for browsing and searching the catalog, you still pick the movies you want using your Mac or PC, at Netflix.com. Whatever assortment of titles you choose online appears instantly on your TV’s list of available movies. The Roku box is great. But let’s face it: It’s another remote to learn, another gadget to connect and more wires around the TV. Phase 3. About six months ago, things began to get really interesting. The Roku box was basically just a plastic box o’ software — software that could be built into machines that are already connected to your TV. One by one, the announcements came: Netflix instant movies became a TiVo feature. An Xbox 360 feature. A Blu-ray DVD player feature (LG and Samsung). Even a feature built right into the TV sets themselves (LG and Vizio, starting this spring). There’s genius to this master plan; everybody, apparently, wins. Consumers get a better on-demand movie deal than they’ll find anywhere else: $9 a month, unlimited. Netflix attracts millions more subscribers. And the equipment manufacturers gain a marketable new feature without having to spend another nickel on hardware. You shouldn’t be surprised, in other words, if this instant Netflix thing becomes a huge, megalithic hit, a dominant movie delivery system, a more-or-less standard feature of home theater setups. To find out what that future will look like, I’ve made an enormous sacrifice in the name of science. I’ve spent several months watching movies, using three of the first Netflix-enhanced products: my own TiVo, an Xbox 360 and an LG Blu-ray player (the BD300). Here’s what I found. TiVo: The Netflix feature quietly installed itself in the TiVo’s menus one night, without my awareness or involvement. On the TiVo menu, you choose Video on Demand; you’re shown a list of services like YouTube and Amazon Unbox. Choose Netflix, and bam: there’s your list of Watch Now movies, in a scrolling vertical list. Hit Play to play one. (This works on TiVo HD, HD XL and Series 3 models.) Xbox 360: Assuming you’ve upgraded your Xbox with Microsoft’s most excellent November software update, Netflix is now part of your game console. Log in, choose the Video Marketplace page, click Netflix and there’s your Netflix movie list, gorgeously represented as colorful DVD cases, which flip past as you browse (something like Apple’s Cover Flow feature in iTunes). There’s one crushing downside, however: you have to pay Microsoft $50 a year for this feature, which is absurd. (That gains you a Gold membership, which also includes other perks.) LG BD300: The BD300 is a Blu-ray DVD player ($333 bought online). It’s black and shiny and slim, with a beautiful main menu that offers five icons: Movie, Netflix Streaming, Photo, Music and Setup. You don’t need a manual to figure out where to go to see your Watch Now movie list. On all of these machines, each movie remembers exactly where you left off watching, even if it was on a different machine. Amazing. Now, instant fixed-fee access to 12,000 movies and TV shows is giddy and life-changing. There are, however, some disappointments. First, you need a high-speed Internet connection to your TV setup. The faster the service, the better video quality you get; hi-def TV shows, in particular, look fantastic on a decent cable modem. Second, remember that these movies are streaming. They’re not stored on a hard drive (unlike the Apple TV, Vudu box or Blockbuster’s rival MediaPoint box). So every time you fast-forward or rewind, there’s a 10-second pause for “rebuffering.” Fortunately, most people don’t scan through movies often; usually, you just sit back and let them play. And when you do scan, little thumbnail images of the movie scenes flash by, one for every 10 seconds of movie, so you have some guidance as you skim. The third problem is that, as with all Internet downloads, you miss out on a lot: surround sound, subtitles, alternative endings, director’s commentaries and other DVD supplements. Fourth, and biggest, problem: not all of those 12,000 movies are, ahem, what you’d call Oscar material. There’s an awful lot of chaff, and no new DVD releases at all. (Thanks to the ridiculous Hollywood system of “release windows,” Internet services can’t offer new movies until after they have had their runs on pay-per-view, hotels, DVD “new release” periods and so on.) On the other hand, that still leaves several thousand great marquee movies to choose from (including the entire Starz Play catalog of 1,200 fairly recent hits: “Ratatouille,” “Superbad,” “No Country for Old Men” and the like). Furthermore, you’re still a Netflix DVD-by-mail customer; if you’re craving a movie that just came out on DVD, you can still get it by mail. Actually, there’s one more point worth noting — not a technical one, but a psychological one. There’s a side effect of “any movie, any time” that not many people consider. Once you stop having to pay for movies individually, once you’re able to freely movie surf, you lose the risk of making the wrong decision — and some of the joy at having made a good one. In short, movies become a little less special. Nonetheless, the industry has been trying to sell us on Internet movie downloads for years, and yet it’s remained a techie niche until now. It took Netflix to figure out how to crack the technology code, bringing us tantalizingly close to the “any movie, any time” future that’s surely just around the corner. http://www.nytimes.com/2009/01/29/te...h/29pogue.html  Hollywood Studio Alliance to Deliver Online Films on Demand AFP A Viacom-led alliance of Hollywood studios says that by year's end it will launch a website where Internet users can view exclusive films or television shows on demand. Viacom's joint venture dubbed Studio 3 Networks said the "next-generation entertainment service" will be called epix and offer productions from Paramount Pictures, Metro-Goldwyn-Mayer Studios, United Artists, and Lionsgate films. "With epix, we are creating an entirely new category of entertainment service for consumers that is unlike anything that currently exists," said Studio 3 president Mark Greenberg. "Epix is the first brand to hold exclusive exhibition rights to movie content that can be delivered anywhere, anytime." Films available at launch will include the recent Brad Pitt hit "The Curious Case of Benjamin Button" along with "Iron Man" and a "Pink Panther" sequel starring Steve Martin. Directors' notes, outtakes, audition clips and other extras will accompany online films. The online service is to kick-off with a library of more than 15,000 works as well as offer original television programming. "Epix is a powerful entertainment service for a new generation of Americans," Greenberg said when the news was announced Tuesday at a television conference in Las Vegas. "Fueled by a team that has created programming for specific target groups, including Nickelodeon and MTV, we are bringing a unique understanding of the way Americans want to watch and interact with entertainment today." Those involved in the venture hoped to also arrange for epix to extend to a television or cable channel. http://www.google.com/hostednews/afp...zMSmrpnnb4XVKQ  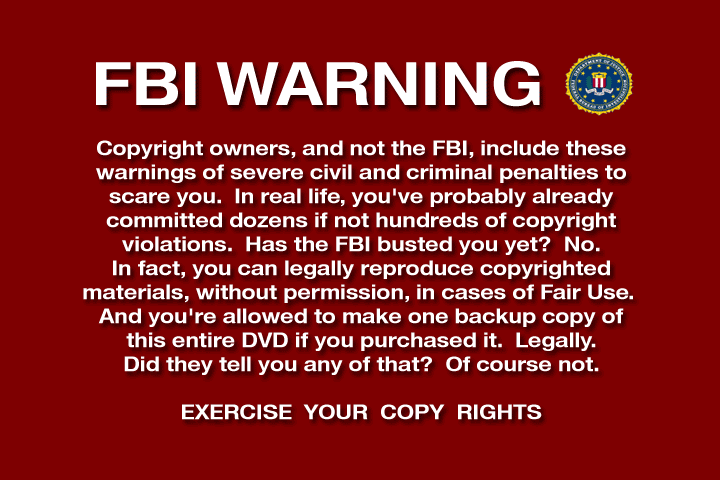  Attenborough Reveals Creationist Hate Mail for Not Crediting God Riazat Butt Sir David Attenborough has revealed that he receives hate mail from viewers for failing to credit God in his documentaries. In an interview with this week's Radio Times about his latest documentary, on Charles Darwin and natural selection, the broadcaster said: "They tell me to burn in hell and good riddance." Telling the magazine that he was asked why he did not give "credit" to God, Attenborough added: "They always mean beautiful things like hummingbirds. I always reply by saying that I think of a little child in east Africa with a worm burrowing through his eyeball. The worm cannot live in any other way, except by burrowing through eyeballs. I find that hard to reconcile with the notion of a divine and benevolent creator." Attenborough went further in his opposition to creationism, saying it was "terrible" when it was taught alongside evolution as an alternative perspective. "It's like saying that two and two equals four, but if you wish to believe it, it could also be five ... Evolution is not a theory; it is a fact, every bit as much as the historical fact that William the Conqueror landed in 1066." Attenborough, who attended the Wyggeston Grammar School for Boys in Leicester in the 1930s, said he was astonished at manifestations of Christian faith. "It never really occurred to me to believe in God - and I had nothing to rebel against, my parents told me nothing whatsoever. But I do remember looking at my headmaster delivering a sermon, a classicist, extremely clever ... and thinking, he can't really believe all that, can he? How incredible!" In 2002, Attenborough joined an effort by clerics and scientists to oppose the inclusion of creationism in the curriculum of state-funded independent schools receiving private sponsorship, such as the Emmanuel Schools Foundation. http://www.guardian.co.uk/world/2009...orough-science  New Law Will Require Camera Phones to 'Click' Michael Horton A new bill is being introduced called, Camera Phone Predator Alert Act, which would require any mobile phone containing a digital camera to sound a tone whenever a photograph is taken with the camera's phone. It would also prohibit such a phone from being equipped with a means of disabling or silencing the tone. While its a good gesture, I do not believe having such a law would deter criminals from hacking their camera phones to take pictures in inappropriate ways. Also, the real criminals would not even use a camera phone but would probably use other devices such as a hidden camera. Regardless, at least with the bill signed into law it would allow prosecution and jail time for individuals that get caught with a camera phone that does not make the noise. One question does remain, what if you have a camera phone that doesn't make the noise at all or is suppressible? Would older phones still be covered under this new law? http://techfragments.com/news/318/Te..._to_Click.html  Recession Rocks Hollywood's Showbiz Papers Alex Dobuzinskis For more than 75 years, Daily Variety and The Hollywood Reporter have battled to be the movie industry's top newspaper, but recent layoffs due to the recession and competition from Internet blogs has Hollywood wondering if it will soon become a one paper town. Publishers of the showbusiness newspapers say advertising has plunged, even during the current Oscar season when movie studios pay well to hype their films with cover page ads. Moreover, the papers face increased competition from bloggers providing a daily diet of Hollywood news and gossip, such as Nikki Finke's DeadlineHollywoodDaily.com, Tina Brown's TheDailyBeast.com and David Poland's MovieCityNews.com. Daily Variety and The Hollywood Reporter continue to compete vigorously through tough economic times. "I think it's going to be a battle royale, and there may only be one a year from now," said Jonathan Taplin, a professor at the Annenberg School for Communication at the University of Southern California. On Monday, Daily Variety owner Reed Business Information, a unit of Reed Elsevier Plc, said the economic slump forced it to lay off some 30 workers at the paper and its sister publications. Those sister papers include weekly Variety, which is the grand dame of showbiz reporting having started in 1905 and spawned Daily Variety in 1933. Last year, Reed put the publications on the sales block. The Hollywood Reporter was founded in 1930 and is now owned by media research firm Nielsen Co., which provides marketing and other media business information, as well as TV ratings. It has cut its staff to slightly less than 90, about half the level five years ago, said publisher Eric Mika. The Show's Not Over, Yet Neil Stiles, publisher of the Variety Group, said he does not concern himself with his competitor or doomsday predictions for the newspapers. "I don't give it any thought at all as to whether there will be one or two," he said. Still, without giving figures Stiles said awards season ads are "markedly down," and he doubts his paper's award ads will migrate to the Web because studios get more punch from print. "It hangs around in an agent's office, people see it," Stiles said. "It's very visible in a very tangible way. Online tends to be more of a question where someone would have to go online to find it." Mika also defended his paper saying, "I don't think advertisers and readers want just a single point of view." Losing one of the historic papers, known for their own style of news jargon, would rip a hole in Hollywood culture. Reading the trades remains a daily ritual for studio executives, producers, writers, directors and actors. Winking headlines like Daily Variety's "Katz-and-Mouse Game Over," describing the rift between Jeffrey Katzenberg and then-CEO of Walt Disney Co. Michael Eisner, speak volumes to Hollywood insiders. But Taplin, among others, said the papers are rapidly becoming outmoded as readers go to blogs that provide an edgier version of film and TV news. MovieCityNews editor Poland said he expects The Hollywood Reporter will become a Web-only news outlet, and Daily Variety will cut back to publishing twice weekly. Both have long histories, and can raise revenue online from their archives. "It probably is part of the salvation of these titles in the long run, whoever owns them and whatever format they're in," he said. In fact, during the holidays The Hollywood Reporter went to a Web-only version for 12 separate days. Still, it has not announced any plans to embrace the Web as a day-to-day model. As they say on television: stay tuned. Reuters and The Hollywood Reporter operate a joint entertainment news service. (Reporting by Alex Dobuzinskis: Editing by Bob Tourtellotte) http://www.reuters.com/article/wtMos...50T3AN20090130  Charles H. Schneer, Sci-Fi Film Producer, Dies at 88 Margalit Fox Charles H. Schneer, a noted film producer who for a quarter-century helped the Oscar-winning special-effects wizard Ray Harryhausen lay waste to Washington, San Francisco, Rome and many other places, died on Wednesday in Boca Raton, Fla. He was 88. His daughter Stacey Lee confirmed the death, saying her father had been ill for many years. A resident of Delray Beach, Fla., Mr. Schneer divided his time between London and Florida for more than four decades before settling full time in the United States a few years ago. When the two joined forces in the early 1950s, Mr. Schneer was a young producer who badly wanted to make a picture in the giant-octopus-rips-down-the-Golden-Gate-Bridge tradition. In Mr. Harryhausen, an innovative but still little-known animator, he found his man. Together, they made a dozen science-fiction and fantasy films that endure as cult classics, notable for combining live action with Mr. Harryhausen’s distinctive stop-motion animation. They include “Earth vs. the Flying Saucers” (1956); the Sinbad trilogy, comprising “The Seventh Voyage of Sinbad” (1958), “The Golden Voyage of Sinbad” (1974) and “Sinbad and the Eye of the Tiger” (1977); and “The Three Worlds of Gulliver” (1960). Their last film together was “Clash of the Titans” (1981), which, despite a cast of titans including Laurence Olivier, Claire Bloom, Maggie Smith and Ursula Andress, had a lukewarm reception. Their most famous collaboration was “Jason and the Argonauts” (1963), a retelling of the Greek myth that featured an army of walking, swashbuckling skeletons, memorably animated by Mr. Harryhausen. Mr. Harryhausen received the Gordon E. Sawyer Award, a special Academy Award for lifetime technical achievement, in 1991. Charles Hirsh Schneer was born on May 5, 1920, in Norfolk, Va., and moved with his family to Mount Vernon, N.Y., as a youth. He earned a bachelor’s degree from Columbia University in 1940 and in World War II served with the Army Signal Corps, making training films at its studio in Astoria, Queens. After the war, he worked for Universal and Columbia Pictures in Hollywood and later formed his own company, Morningside Productions. Besides his daughter, Ms. Lee, of Boston, Mr. Schneer is survived by his wife, the former Shirley Sussman; another daughter, Lesley Silver of London; a sister, Babette Schneer Katz of Mamaroneck, N.Y.; three grandchildren; and four great-grandchildren. A third daughter, Bettine Greifer, died in 2001. Mr. Schneer was at Columbia Pictures when he met Mr. Harryhausen. At the time, Mr. Harryhausen was an unheralded animator whose most recent film, “The Beast From 20,000 Fathoms” (1953), had been made on a shoestring budget of $200,000, just $10 a fathom. But Mr. Schneer loved the picture, and the two men joined forces with “It Came From Beneath the Sea,” released in 1955. The movie was Mr. Schneer’s octopus dream film come to life — almost. Because of financial constraints, the octopus was really a hexapus, with six arms where eight should have been. “The rumor got around that sometimes there were less,” Mr. Harryhausen said Monday by telephone from his London home. “If the budget was cut any more, we would have had a tripod.” The length of time Mr. Harryhausen’s painstaking animation required (a single picture could take several years) freed Mr. Schneer to produce other films. Among them was “Hellcats of the Navy” (1957), the only movie in which Ronald Reagan and his wife Nancy Davis appear together. Mr. Schneer also produced a biopic about the Nazi rocket scientist Wernher von Braun, released in the United States in 1960 as “I Aim at the Stars.” (The comedian Mort Sahl made short work of the title, amending it to read: “I Aim at the Stars — but Sometimes Hit London.") A hands-on producer, Mr. Schneer contributed enthusiastically to the story lines of his films, Mr. Harryhausen said on Monday. He scoured the papers for accounts of the paranormal, of which there was no shortage in the 1950s. He accompanied his crews on location, and at least once helped stave off an embarrassing anachronism. The film was “Jason and the Argonauts,” shot on the Italian coast. In one scene, the script called for Jason’s ship, the Argo, to sail around a bluff and into view. But as the cameras rolled, to everyone’s astonishment, Sir Francis Drake’s galleon the Golden Hind sailed by instead. It had been launched by a British film crew also shooting in the area. As Mr. Harryhausen recalled in an article he wrote for The Guardian in 2003, Mr. Schneer rose to the occasion at once. “Get that ship out of here!” he cried. “You’re in the wrong century.” http://www.nytimes.com/2009/01/27/movies/27schneer.html  Jim Horne, a Familiar Face in Ads From the 1950s, Dies at 91 Bruce Weber It was a time when information didn’t fly around the world in a nanosecond; when images were captured on film, not computer chips; when television commercials were performed live; when product advertising supplied newspapers and magazines with a rich and steady lifeblood. It was also a time when it was still possible to be a famous face without a famous name. In fact, Jim Horne may have been asked more often than anyone else, “Don’t I know you from somewhere?” For about 15 years beginning in the late 1940s, Mr. Horne was ubiquitous, perhaps the most widely seen male model in the country, appearing in hundreds of advertisements in magazines and newspapers, on billboards and catalog covers, in television commercials and industrial brochures. He died on Dec. 29 in Manhattan, at 91. His wife of 45 years, Francesca Marlowe Horne, said the cause was cancer, but added that he also had congestive heart failure. Mr. Horne had been an actor with bit parts in Hollywood movies before moving to New York City and establishing a second career. He had a chiseled jaw, a distinctively rounded hairline, a seemingly permanent pompadour, a gleaming California smile and an athlete’s physique. It was an image that photographers and advertisers found easily adaptable to a number of stereotypes of the day: the dashing ladies’ man, the dapper dandy, the devoted dad, the suburban husband, the businessman commuter, the country club sophisticate and the one Mr. Horne, an avid fisherman, preferred: the rugged outdoorsman. He was employed to help sell an extraordinarily eclectic range of products: automobiles and underpants; exercise equipment and mothproofing; hair tonic and gasoline; beer, blended whiskey and milk; pajamas, raincoats, cardigan sweaters, Panama hats, and suits with two pairs of pants for $44.95. He appeared in ads for Macy’s, Abraham & Straus and Alexander’s; for York, L & M, Lucky Strike and Marlboro cigarettes (he was a Marlboro man before the Marlboro man); for Burberry, Chrysler, Budweiser, Van Heusen, Remington, The Saturday Evening Post and, in a stunningly glamorous print ad with the legendary model Suzy Parker, Grand Marnier. In the summer of 1957, when Apparel Arts, a men’s fashion magazine, decided to create a new identity for itself after more than a quarter century, it chose Mr. Horne for the cover of the magazine’s first issue under its new name: Gentlemen’s Quarterly. He appeared there in a jaunty striped jacket peering rakishly from behind a tropical plant. He was, in the lexicon of the day, a man’s man, and in the lexicon of today, a hottie. “Oh, was he ever!” his wife said. James Wesley Horne Jr. was born on March 28, 1917, in Glendale, Calif. His father was a prolific director of both silent films and talkies, best known for his work with Laurel and Hardy, including “Big Business” and “Way Out West.” His mother, Cleo Ridgely, was an actress and a great beauty from whom, it was generally acknowledged, Mr. Horne inherited his looks. His twin sister, June, grew up to marry the actor Jackie Cooper. Mr. Horne had small, sometimes uncredited parts in about two dozen films, including “Gunga Din” and “A Place in the Sun.” He auditioned for the part of Joe Bonaparte, the violinist who wants to be a boxer, in the film version of Clifford Odets’s play “Golden Boy,” but the role went instead to another unknown actor, William Holden, who shortly thereafter became Mr. Horne’s bunkmate in Army basic training. Mr. Horne served in Europe in World War II, becoming a combat photographer and earning two Bronze Stars. After returning to California, he continued to work in the movies and began modeling as well. By the early 1950s, as televisions became more common in American homes, advertisers seized on the new medium and began looking for models who could act a little. It was an opportunity that wasn’t lost on Mr. Horne, and he moved to New York City, where he was soon immersed in bookings. This was an era of growth in advertising, especially on television, where many commercials were broadcast live, resulting in a lot of nuttiness. Once, as Mr. Horne performed in an ad for the hair tonic Brylcreem, his comb stuck on a thread in his pocket. When he whipped it out to slick back his pompadour, he accidentally flung it across the room. Male models were something of a new breed, weirdly anonymous and perceived by many as suspicious or threatening; once, dressed spiffily for work and passing an hour in a bar while he waited for a photographer who was late for an appointment, Mr. Horne was badly beaten by thugs who didn’t appreciate his taste in clothes. In general, male models also didn’t get fabulously rich; as late as 1965, Mr. Horne’s hourly rate was $50. But the job allowed him to lead the high life, traveling with pals like Mickey Mantle, whom he met at Toots Shor’s restaurant, and Clark Gable, a sometime fishing companion. Mr. Horne’s first marriage ended in divorce. He never had children and is survived by his wife, a former model herself, who became international director of the Barbizon School of Modeling. In 1980, under the name Francine Marlowe, she wrote “Male Modeling: An Inside Look” (Crown). Mr. Horne’s modeling career continued sporadically through the 1960s, especially in print ads featuring products for “mature” men. In the mid-1960s, he became a sales manager and spokesman for an apparel company, and he later established his own business, manufacturing leather belts. He learned the lesson of how evanescent celebrity could be without a famous name. Few, if any, of his photographs still strike a familiar chord. Well, maybe one does: a jokey shot taken in 1953 (whose rights he signed away), showing him with a sour, headachey expression of generic woe; it has been used dozens of times, even in the last decade, in ads for aspirin, tax services, hangover remedies and other stress relievers. His wife said it didn’t bother him that this was the image that survived. “To him it was a job you did,” Mrs. Horne said. “And then you went fishing.” http://www.nytimes.com/2009/01/25/bu...a/25horne.html  Lynyrd Skynyrd Keyboard Player Billy Powell Dies Aged 56 Billy Powell, the keyboard player for blues-rock band Lynyrd Skynyrd has died in Florida aged 56. Gervase de Wilde The musician was found dead at his Florida home by paramedics on Wednesday January 28 after he called them to complain of breathing difficulties. The day before he had missed an appointment with a doctor for a heart examination. Powell, who was born in Texas, went to school in Florida with the future bassist for Lynyrd Skynyrd, Leon Wilkeson, and initially found employment as the band’s roadie. He worked for them until 1972, when singer Ronnie Van Zant heard him play his own version of the band’s hit Free Bird and invited Powell to join Lynyrd Skynyrd as their keyboard player. Their self-titled debut was released the following year and the band achieved huge popularity during the rest of the decade with hit songs like Free Bird and Sweet Home Alabama. Lynyrd Skynyrd were struck by tragedy in 1977 when their private jet crashed into a swamp in Mississipi. Although Powell was seriously injured, he survived, unlike fellow members Ronnie Van Zant and Steve Gaines. In the years that followed the crash, Powell played keyboard in a Christian rock band called Vision. He toured with Lynyrd Skynyrd in 1987 when the band reformed with Van Zant’s brother Johnny on vocals and remained with them till his death. Powell’s wife Ellen and four children survive him. http://www.telegraph.co.uk/culture/m...s-aged-56.html  John Updike, Prize-Winning Writer Of 'Rabbit' Novels, Dead At Age 76 Hillel Italie John Updike, the Pulitzer Prize-winning novelist, prolific man of letters and erudite chronicler of sex, divorce and other adventures in the postwar prime of the American empire, died Tuesday at age 76. Updike, a resident of Beverly Farms, Mass., died of lung cancer, according to a statement from his publisher, Alfred A. Knopf. A literary writer who frequently appeared on best-seller lists, the tall, hawk-nosed Updike wrote novels, short stories, poems, criticism, the memoir "Self-Consciousness" and even a famous essay about baseball great Ted Williams. He was prolific, even compulsive, releasing more than 50 books in a career that started in the 1950s. Updike won virtually every literary prize, including two Pulitzers, for "Rabbit Is Rich" and "Rabbit at Rest," and two National Book Awards. Although himself deprived of a Nobel, he did bestow it upon one of his fictional characters, Henry Bech, the womanizing, egotistical Jewish novelist who collected the literature prize in 1999. His settings ranged from the court of "Hamlet" to postcolonial Africa, but his literary home was the American suburb. Born in 1932, Updike spoke for millions of Depression-era readers raised by "penny-pinching parents," united by "the patriotic cohesion of World War II" and blessed by a "disproportionate share of the world's resources," the postwar, suburban boom of "idealistic careers and early marriages." He captured, and sometimes embodied, a generation's confusion over the civil rights and women's movements, and opposition to the Vietnam War. Updike was called a misogynist, a racist and an apologist for the establishment. On purely literary grounds, he was attacked by Norman Mailer as the kind of author appreciated by readers who knew nothing about writing. But more often he was praised for his flowing, poetic writing style. Describing a man's interrupted quest to make love, Updike likened it "to a small angel to which all afternoon tiny lead weights are attached." Nothing was too great or too small for Updike to poeticize. He might rhapsodize over the film projector's "chuckling whir" or look to the stars and observe that "the universe is perfectly transparent: we exist as flaws in ancient glass." In the richest detail, his books recorded the extremes of earthly desire and spiritual zealotry, whether the comic philandering of the preacher in "A Month of Sundays" or the steady rage of the young Muslim in "Terrorist." Raised in the Protestant community of Shillington, Pa., where the Lord's Prayer was recited daily at school, Updike was a lifelong churchgoer influenced by his faith, but not immune to doubts. "I remember the times when I was wrestling with these issues that I would feel crushed. I was crushed by the purely materialistic, atheistic account of the universe," Updike told The Associated Press during a 2006 interview. "I am very prone to accept all that the scientists tell us, the truth of it, the authority of the efforts of all the men and woman spent trying to understand more about atoms and molecules. But I can't quite make the leap of unfaith, as it were, and say, 'This is it. Carpe diem (seize the day), and tough luck.'" He received his greatest acclaim for the "Rabbit" series, a quartet of novels published over a 30-year span that featured ex-high school basketball star Harry "Rabbit" Angstrom and his restless adjustment to adulthood and the constraints of work and family. To the very end, Harry was in motion, an innocent in his belief that any door could be opened, a believer in God even as he bedded women other than his wife. "The tetralogy to me is the tale of a life, a life led an American citizen who shares the national passion for youth, freedom, and sex, the national openness and willingness to learn, the national habit of improvisation," Updike would later write. "He is furthermore a Protestant, haunted by a God whose manifestations are elusive, yet all-important." Other notable books included "Couples," a sexually explicit tale of suburban mating that sold millions of copies; "In the Beauty of the Lilies," an epic of American faith and fantasy; and "Too Far to Go, which followed the courtship, marriage and divorce of the Maples, a suburban couple with parallels to Updike's own first marriage. Plagued from an early age by asthma, psoriasis and a stammer, he found creative outlets in drawing and writing. Updike was born in Reading, Pa., his mother a department store worker who longed to write, his father a high school teacher remembered with sadness and affection in "The Centaur," a novel published in 1964. The author brooded over his father's low pay and mocking students, but also wrote of a childhood of "warm and action-packed houses that accommodated the presence of a stranger, my strange ambition to be glamorous." For Updike, the high life meant books, such as the volumes of P.G. Wodehouse and Robert Benchley he borrowed from the library as a child, or, as he later recalled, the "chastely severe, time-honored classics" he read in his dorm room at Harvard University, leaning back in his "wooden Harvard chair," cigarette in hand. While studying on full scholarship at Harvard, he headed the staff of the Harvard Lampoon and met the woman who became his first wife, Mary Entwistle Pennington, whom he married in June 1953, a year before he earned his A.B. degree summa cum laude. (Updike divorced Pennington in 1975 and was remarried two years later, to Martha Bernhard). After graduating, he accepted a one-year fellowship to study painting at the Ruskin School of Drawing and Fine Arts at Oxford University. During his stay in England, a literary idol, E.B. White, offered him a position at The New Yorker, where he served briefly as foreign books reviewer. Many of Updike's reviews and short stories were published in The New Yorker, often edited by White's stepson, Roger Angell. By the end of the 1950s, Updike had published a story collection, a book of poetry and his first novel, "The Poorhouse Fair," soon followed by the first of the Rabbit books, "Rabbit, Run." Praise came so early and so often that New York Times critic Arthur Mizener worried that Updike's "natural talent" was exposing him "from an early age to a great deal of head-turning praise." Updike learned to write about everyday life by, in part, living it. In 1957, he left New York, with its "cultural hassle" and melting pot of "agents and wisenheimers," and settled with his first wife and four kids in Ipswich, Mass, a "rather out-of-the-way town" about 30 miles north of Boston. "The real America seemed to me 'out there,' too heterogeneous and electrified by now to pose much threat of the provinciality that people used to come to New York to escape," Updike later wrote. "There were also practical attractions: free parking for my car, public education for my children, a beach to tan my skin on, a church to attend without seeming too strange." http://www.courant.com/features/book...,7100076.story  Italian Writer Raises Case Against "Button" Eric J. Lyman "The Curious Case of Benjamin Button" got a little stranger Friday after an attorney representing an Italian office worker filed legal papers alleging that the screenplay was based on a story she wrote in 1994. The David Fincher film, nominated for 13 Oscars, features Brad Pitt in the role of Benjamin Button, a man who ages backward. It was inspired by -- but not based on -- a 1921 short story by F. Scott Fitzgerald. Adriana Pichini, a Roman office worker, said the film seems to be based on a story she wrote 15 years ago called "Il ritorno di Arthur all'innocenza" (Arthur's Return to Innocence). The story was officially registered with the proper Italian copyright authorities in 1994 and even sent to publishers in the U.S., but was never published. According to Gianni Massaro, Pichini's lawyer, a file was opened with the Rome Tribunal Court, which means a judge will watch the film and read the story. If the judge determines there are enough similarities to warrant an investigation, the court will launch one. Massaro, a fixture in the Italian cinema industry and a former president of the Italian audiovisual association ANICA, said in an interview that he is not sure if Pichini will seek financial damages against Fincher, screenwriter Eric Roth and the film's producers. "At this point it's still a matter of principle," Massaro said. "What happens next will depend on what the judge rules." It is not clear what authority an Italian court would have in this case, though Massaro noted that the film's producers, Hollywood studios Paramount Pictures and Warner Bros. Pictures, both have Italian operations. No timetable has been set for the judge's viewing. The rest of Italy will be able to see the film when it goes into nationwide release February 13. http://www.reuters.com/article/enter...50U01020090131  Self-Publishers Flourish as Writers Pay the Tab Motoko Rich The point may soon come when there are more people who want to write books than there are people who want to read them. At least, that is what the evidence suggests. Booksellers, hobbled by the economic crisis, are struggling to lure readers. Almost all of the New York publishing houses are laying off editors and pinching pennies. Small bookstores are closing. Big chains are laying people off or exploring bankruptcy. A recently released study by the National Endowment for the Arts found that while more people are reading literary fiction, fewer of them are reading books. Meanwhile, there is one segment of the industry that is actually flourishing: capitalizing on the dream of would-be authors to see their work between covers, companies that charge writers and photographers to publish are growing rapidly at a time when many mainstream publishers are losing ground. Credit for the self-publishing boomlet goes to authors like Jim Bendat, whose book “Democracy’s Big Day,” a collection of historical vignettes about presidential inaugurations, enjoyed a modest burst in sales in the hoopla surrounding President Obama’s swearing-in. After failing to secure a traditional publishing deal in 2000, Mr. Bendat, a public defender in Los Angeles, paid $99 to publish the first edition of his book with iUniverse, a print-on-demand company. He updated the book in 2004 and 2008, and has sold more than 2,500 copies. IUniverse takes a large cut of each sale of the book, currently on Amazon.com for $11.66. As traditional publishers look to prune their booklists and rely increasingly on blockbuster best sellers, self-publishing companies are ramping up their title counts and making money on books that sell as few as five copies, in part because the author, rather than the publisher, pays for things like cover design and printing costs. In 2008, Author Solutions, which is based in Bloomington, Ind., and operates iUniverse as well as other print-on-demand imprints including AuthorHouse and Wordclay, published 13,000 titles, up 12 percent from the previous year. This month, the company, which is owned by Bertram Capital, a private equity firm, bought a rival, Xlibris, expanding its profile in the fast-growing market. The combined company represented 19,000 titles in 2008, nearly six times more than Random House, the world’s largest publisher of consumer books, released last year. In 2008, nearly 480,000 books were published or distributed in the United States, up from close to 375,000 in 2007, according to the industry tracker Bowker. The company attributed a significant proportion of that rise to an increase in the number of print-on-demand books. “Even if you’re sitting at a dinner party, if you ask how many people want to write a book, everyone will say, ‘I’ve got a book or two in me,’” said Kevin Weiss, chief executive of Author Solutions. “We don’t see a letup in the number of people who are interested in writing.” The trend is also driven by professionals who want to use a book as an enhanced business card as well as by people who are creating books as gifts for family and friends. “It used to be an elite few,” said Eileen Gittins, chief executive of Blurb, a print-on-demand company whose revenue has grown to $30 million, from $1 million, in just two years and which published more than 300,000 titles last year. Many of those were personal books bought only by the author. “Now anyone can make a book, and it looks just like a book that you buy at the bookstore.” To be sure, self-publishing is still a fraction of the wider publishing industry. Author Solutions, for example, sold a total of 2.5 million copies last year. Little, Brown sold more than that many copies of “Twilight” by Stephenie Meyer just in the last two months of 2008. But in an era when anyone can create a blog or post musings on Facebook or MySpace, people still seem to want the tangible validation of a printed book. “I wanted the satisfaction of holding the book in my hands,” Mr. Bendat said. As a result of his iUniverse book, the British news channel Sky News asked Mr. Bendat to provide live commentary on Inauguration Day. A group of Washington hotels ordered 500 copies to give to guests who were in town for the event. “O.K., it’s not a best seller,” Mr. Bendat said, “but I’m happy for what’s happening.” Vanity presses have existed for decades, but technology has made it much easier for aspiring authors to publish without hefty upfront costs. Gone are the days when self-publishing meant paying a printer to produce hundreds of copies that then languished in a garage. Now, for as little as $3, an author can upload a manuscript or collection of photos to a Web site, and order a printed book within an hour. Many books will appear for sale on Amazon.com or the Web site of Barnes & Noble; others are sold through the self-publishing companies’ Web sites. Authors and readers order subsequent copies as needed. The self-publishing companies generally make their money either by charging author fees — which can range from $99 to $100,000 for a variety of services, including custom cover design and marketing and distribution to online retailers, or by taking a portion of book sales, or both. Some, like Lulu Enterprises and CreateSpace from Amazon.com, allow the author to create the book free, but then make their money on a small printing markup and a profit split with the author. For some authors, the appeal of self-publishing is that they can put their books on the market much faster than through traditional publishers. Of course, authors who take this route also give up a lot. Not only do they receive no advance payments, but they also often must pay out of their own pockets before seeing a dime. They do not have the benefit of the marketing acumen of traditional publishers, and have diminished access to the vast bookstore distribution pipeline that big publishers can provide. Still, many self-publishing companies allow authors to take more than the traditional royalty of 15 percent of the cover price on hardcovers and 10 percent or less on paperbacks. Michelle L. Long, an accountant who advises small businesses, published “Successful QuickBooks Consulting,” a guide for others who want to help businesses use a software package made by Intuit through CreateSpace a little more than a year ago. She said she had earned 45 to 55 percent of the cover price on each sale and had made $22,000 in royalties on the sale of more than 2,000 copies. During an economic downturn, books tailored to such narrow audiences may fare better than titles from traditional publishers that depend on a more general appeal. “A lot of this niche content is doing fairly well relative to the rest of the economy because it’s very useful to people who have a very specific need,” said Aaron Martin, director of self-publishing and manufacturing on demand at Amazon. For many self-published authors, the niche is very small. Mr. Weiss of Author Solutions estimates that the average number of copies sold of titles published through one of its brands is just 150. Indeed, said Robert Young, chief executive of Lulu Enterprises, based in Raleigh, N.C., a majority of the company’s titles are of little interest to anybody other than the authors and their families. “We have easily published the largest collection of bad poetry in the history of mankind,” Mr. Young said. Still, the dream of many self-published authors is that they will be discovered by a mainstream publishing house — and it does happen, however rarely. When Lisa Genova, a former consultant to pharmaceutical companies, wrote her first novel, “Still Alice,” a story about a woman with Alzheimer’s disease, she was turned down or ignored by 100 literary agents. Ms. Genova paid $450 to iUniverse to publish the book and sold copies to independent bookstores. A fellow author discovered the book and introduced Ms. Genova to an agent, and she eventually sold “Still Alice” for a mid-six-figure advance to Pocket Books, an imprint of Simon & Schuster, which released a new edition this month. It had its debut on the New York Times trade paperback fiction best-seller list on Sunday, at No. 5. Ms. Genova likened her experience to that of young bands or filmmakers using MySpace or YouTube to attract a following. “It’s really tough to break into the traditional model of doing things,” she said. Louise Burke, publisher of Pocket Books, said publishers now trawl for new material by looking at reader comments about self-published books sold online. Self-publishing, she said, is “no longer a dirty word.” Diamonds in the rough, though, remain the outliers. “For every thousand titles that get self-published, maybe there’s two that should have been published,” said Cathy Langer, lead buyer for the Tattered Cover bookstores in Denver, who said she had been inundated by requests from self-published authors to sell their books. “People think that just because they’ve written something, there’s a market for it. It’s not true.” http://www.nytimes.com/2009/01/28/bo...elfpub.html?em  Amazon’s Kindle 2 Will Debut Feb. 9 Brad Stone Mark your calendars, e-book fans: Amazon.com will introduce the next generation of its popular Kindle reader in New York City on Feb. 9. The company sent out e-mails Tuesday announcing a press conference on that date at the Morgan Library & Museum in New York. And Amazon.com confirmed that its founder and chief executive, Jeffrey P. Bezos, will host the event. Amazon would not comment in any more detail about the coming announcement, but the Kindle’s detail page on Amazon.com tells the story. It now says the electronic book reader will ship in four to six weeks. It previously suggested a wait of 11 to 13 weeks. The device has been out of stock since November, after Oprah Winfrey touted the device on her show. The announcement seems to confirm our suspicions that the original Kindle has been obsolete since that time and that everyone who purchased the device over the holidays from Amazon.com — or put their name on a waiting list — will receive the newer version. There has already been much speculation about the upcoming Kindle. If the leaked photos on the gadget site Boy Genius Report are to be believed, the new device corrects some of the design flaws of the first model, adding round buttons instead of those strange angular ones, and smaller side buttons to avoid accidental page turns. But the biggest changes may be inside the device. The new Kindle likely uses the new Broadsheet microchip from Epson and E-Ink, which makes the display technology for the Kindle. E-Ink’s chief executive, Russell J. Wilcox, described the technology to me a few weeks ago, saying that it breaks the screen into 16 pixel sets and can update them in parallel, allowing for faster screen refreshes and a generally more responsive screen. He added that the technology was somewhat analogous to putting a better graphics card in a computer and would help e-readers become better full-featured devices. “It’s the same brightness, it looks the same reading a page, but it’s night and day for user activity for anything than other than reading,” Mr. Wilcox said. “If you are reading a book, you are just going to read page by page and it might not make that much of a difference. But if you want to do anything else with your device, zooming in, look up words, whatever, you really appreciate the speed. It’s a major change.” The new Sony Reader 700, which touts a touch screen, already uses the Broadsheet chip. http://bits.blogs.nytimes.com/2009/0...ebut-feb-9/?hp  Click and Jane Virginia Heffernan “Did you like this book?” asks the computer. It’s a customer-satisfaction question, but it seems more profound than that. We hesitate. Ben, my 3-year-old son, shoots me a puzzled look. The answer should be yes. Ben enjoys what’s on the screen right now: Starfall, an online medley of free learn-to-read activities. But he doesn’t like the question. “It’s not a book,” he explains, emphatically, to the laptop. “It’s more like a movie or a video.” Oh, God. I knew it. In a hundred ways, we pretend that screen experiences are books — PowerBooks, notebooks, e-books — but even a child knows the difference. Reading books is an operation with paper. Playing games on the Web is something else entirely. I need to admit this to myself, too. I try to believe that reading online is reading-plus, with the text searchable, hyperlinked and accompanied by video, audio, photography and graphics. But maybe it’s just not reading at all. Just as screens aren’t books. I kind of like that Ben is not remotely fooled by Starfall’s booklike graphics. The site is loaded with all kinds of biblio-iconography: title pages, tables of contents, frontispieces, page numbers and covers. But, to him, nothing that plays on a screen is a book. And though 20th-century critics like Roland Barthes encouraged readers to see textual experience as play, it’s quite possible that nothing that plays is a book. In their book “Freakonomics,” Stephen J. Dubner and Steven D. Levitt write that kids who grow up in houses packed with books fare better on school tests than those who grow up with fewer books. But they also contend that reading aloud to children and limiting their TV time has no correlation with success on tests. If both of these observations hold, it’s worth determining what books really are, the better to decisively decorate with them. The widespread digitization of text has complicated the matter. Will Ben benefit if I load my Kindle with hundreds of books that he can’t see? Or does he need the spectacle of hard- and softcover dust magnets eliminating floor space in our small apartment to get the full “Freakonomics” effect? I sadly suspect he needs the shelves and dust. Anyway, Ben doesn’t distinguish between my Kindle and a BlackBerry. My immersion in the Kindle is not (to him) an example of impressive role-model literacy. It’s Mom e-mailing, or texting, or for all he knows playing video games. In fact, the only time he describes what he and I do together as “reading” is when we’re sitting with a clutch of pages bound between covers, open in front of us like a hymnal. Starfall, a lovably cluttered site, includes games (match “d” with a picture of a drum) with its offerings, and perhaps the proximity of these games to the site’s “books” (artless plot summaries called “The Wooden Horse” or “The Little Red Hen”) is what leads to a category error. But there’s also the pesky fact that the pictures in Starfall’s would-be picture books tend to fidget. They’re animated. Something about an audience of kids apparently makes it hard for authors to refrain from animating: if an image for children can be made to dance around, it usually does. One More Story, a subscription-only online children’s library that first appeared in 2005, takes exception to this treatment of images. The site, which maintains a sublicensing arrangement with 13 publishers, offers only picture books that have already been published. It does not use cartoons of any kind. You can find “The Snowy Day” on One More Story, as well as “The Poky Little Puppy” and “Stellaluna.” “The books are never animated,” Carl Teitelbaum, a onetime “Sesame Street” contributor who created the site, explained to me by e-mail message. “We do not alter the text or the illustrations at all.” But One More Story also demonstrates that — as Barthes and his fellow critics might have put it — every translation entails a reworking. It’s impossible to render books as pixels without making changes. “We do take the text out of the page and place it in a text box in a size type that children can easily follow,” Teitelbaum conceded. Moreover, voice-over is added, so a child can have a book read to him. One More Story does not use facsimiles of the lettering in a book, even if a book is hand-lettered or idiosyncratically lettered. Nonetheless, Teitelbaum explained: “We try to match the typeface with the typeface in the book so going to the actual books will be a smooth transition. We sometimes go in for close-ups, the way your eye might, when the text refers to a portion of the illustration.” Hmm. All this reconceptualization, and scoring and even sound effects: sounds like filmmaking to me. And yet. While some movie devices show up on One More Story, great pains are taken to preserve — even enhance — the booklike feel of the works in the online library. The gutter of the book is shown, the pages are slightly curved and shadows are used to create an impression of depth. It’s kind of funny to go to the trouble to radically reconceive a book for new distribution and display, only to have to add back some of its humblest physical qualities. “This realistic portrayal is very intentional,” Teitelbaum explained. “When a child has a positive experience, we want that child to know that they have just read a book, not seen a cartoon or video game.” I’d like that, too. I’d like for Ben to sit with One More Story and come away with the impression that he’d been read beautiful books all afternoon. But Ben tends to ask for One More Story when he wants privacy, the same state of mind in which he likes videos. Books, by contrast, are for when he feels snuggly. Which brings up something significant about books for a 3-year-old: whatever else preschool reading is, it’s intimate. Before you can read, you get to see books mostly when you’re cuddled up with an adult or jostling with other kids in a circle. In one significant sense, then, One More Story may be closer to true reading than even the ink-on-paper books (with real gutters!) that I read aloud: Ben can do it himself. As he maneuvers the computer trackpad and he shoos me away so he can study (for the 10th time) “Sidney Won’t Swim” on One More Story, I’m not sure he’s developing an appreciation for books. But he is learning how to enrich his solitude, and that is one of the most intensely pleasurable aspects of literacy. http://www.nytimes.com/2009/02/01/ma...-medium-t.html  Cooling Chips with Thermoelectrics Researchers have made ultrathin refrigerators for microprocessors. Kate Greene If you could remove the layers of circuitry in your computer and touch the main processor while it's running a video, you would feel its blistering heat, which can exceed 100 °C. Such heat, a natural by-product of shuttling electrons through transistors, can impede performance and even damage the processor in the long run. Traditionally, engineers have used simple copper plates to pull away the heat, and fans or liquid-based cooling systems. But these systems are bulky and can sap energy. Now researchers at Intel, RTI International of North Carolina, and Arizona State University have shown that it's possible to build an efficient microrefrigerator that can target hot spots on chips, saving power and space, and more effectively cooling the entire system. Their work also demonstrates, for the first time, that it is possible to integrate thermoelectric material into chip packaging, making the technology more practical than ever before. A paper detailing the research was just published in Nature Nanotechnology. The fundamental technology used to chill the chip, a thermoelectric cooler, isn't new, explains Rama Venkatasubramanian, senior research director at the Center for Solid State Energetics at RTI International. In a Nature paper from 2001, he and his team showed that a material called a nanostructured thin-film superlattice has superior thermal properties to other types of thin thermoelectric materials: the superlattice conducts electricity well but impedes the flow of heat. When an electric current zips through the material, its temperature can drop to about 55 °C. "People have been talking about using high-efficiency thermoelectric materials for cooling hot spots on chips for years," says Intel manager Ravi Prasher. He says that part of the reason he and his colleagues were able to succeed is because they used a material that has shown exceptional thermal properties, and they relied on Intel's knowledge of chip packaging to build an integrated thermoelectric system that was engineered to fit within the confines of a chip's housing. To put the microrefrigerator in the chip package, the engineers integrated the cooler onto a square of copper, just like the type that's already used in chip packaging to disperse heat. Usually this piece of copper is in close contact with the chip, but the researchers put the 0.4-millimeter-square cooler in between the chip and the copper. When the microrefrigerator was turned on, it cooled a localized region on the chip by about 15 °C. This is significant, says Venkatasubramanian, because generally speaking, for each five-degree increase in chip temperature, there is a marked decrease in reliability and performance of a chip. In the demonstration, the researchers only used one microrefrigerating unit but foresee using three or four per chip, to cover the hottest areas. However, the performance wasn't even close to the maximum amount of cooling that the microrefrigerator is capable of when it's not confined to the chip housing. "We've found good performance," Venkatasubramanian says, "but there are still a lot of challenges." When engineers put the cooler inside the package, there are a number of additional contact points where the cooler is connected to the copper plate and packaging electronics, he says. Prasher explains that the thermal characteristics of these contacts play a significant role in reducing the cooler's efficiency: "By itself, [reducing resistance of thermal contacts] is a significant research area." People are exploring different types of solder and even carbon nanotubes to reduce the resistance at the interface, he says, but the problem still has to be resolved. Regardless, Ali Shakouri, a professor of electrical engineering at the University of California, Santa Cruz, is impressed by the work so far. "This is a good achievement," he says. "The idea [that] there's an uneven distribution of temperature in a microprocessor, and that by selectively cooling certain locations you can do a better job and save power, has been around for a while, but it hadn't been demonstrated on a chip before." Shakouri notes that as the microprocessor industry moves toward using multiple cores or processing centers on a chip, the problem of hot spots will get worse, because workloads are shifted from core to core, creating more transient hot spots. Fans, used in many computers today, don't respond quickly or effectively. "If you could selectively have microrefrigerators throughout a multicore chip," he says, "you could lower power and increase performance." The researchers don't have a timeline for commercialization. Right now, even though the cooler could be incorporated into traditional chip packaging, it would still be prohibitively expensive. After all, says Venkatasubramanian, adding a cooler is essentially adding a completely new layer of electronics to a chip. He says that if the cost and scalability of these coolers can be addressed, then he's confident that they'll find a market. http://www.technologyreview.com/computing/22016/?a=f  Google Error Sends Warning Worldwide Liz Robbins Google’s Internet search service malfunctioned for nearly 55 minutes Saturday morning, upending users around the world with search results that carried false safety warnings and Web links that did not work. The company acknowledged Saturday that all searches produced links with the same warning message: “This site may harm your computer.” Clicking on any of the links led to an error message stating that the desired site could not be reached. “What happened?” Google explained in its blog. “Very simply, human error.” Google said it periodically updates its list of sites suspected of carrying dangerous software that could harm computers, and that Saturday morning a Google employee mistyped a Web address for one such site, causing all sites to be flagged harmful. There was some momentary tension when Google seemed to imply that the glitch was caused by StopBadware.org, the company that helps Google determine which sites are unsafe. Google later posted a statement that took the blame for the error. “We have a good ongoing relationship with StopBadware.org,” a Google spokesman, Gabriel Stricker, said in a telephone interview. “In our post, we tried to clarify our role in this error.” Google is not known for glitches, but there have been other recent ones. Google Maps had a software glitch last month that sent drivers trying to get to different points within Staten Island, specifically zip codes 10302 and 10308, on a 176-mile detour to Schenectady instead. The glitches in Google Maps and Google search were unrelated, Mr. Stricker said. As for Saturday’s search engine failure, he added: “Our Web search is extremely reliable, and that’s why when an interruption occurs, even if it’s for a matter of minutes, for a Saturday morning, people notice it.” http://www.nytimes.com/2009/02/01/te...google.html?hp  A Tool to Verify Digital Records, Even as Technology Shifts John Markoff Simple-to-use digital technology will make it more difficult to distort history in the future. On Tuesday a group of researchers at the University of Washington are releasing the initial component of a public system to provide authentication for an archive of video interviews with the prosecutors and other members of the International Criminal Tribunal for the Rwandan genocide. The group will also release the first portion of the Rwandan archive. This system is intended to be available for future use in digitally preserving and authenticating first-hand accounts of war crimes, atrocities and genocide. Such tools are of vital importance because it has become possible to alter digital text, video and audio in ways that are virtually undetectable to the unaided human eye and ear. The researchers said history was filled with incidents of doctoring, deleting or denying written records. Now, they say, the authenticity of digital documents like videos, transcripts of personal accounts and court records can be indisputably proved for the first time. “The closest analogy are the revisionist histories of the Holocaust, where there are assertions that people weren’t put in camps and put in ovens,” said Batya Friedman, a professor of computer science at the Information School at the University of Washington. “It doesn’t take a rocket scientist to say that in a period of time some people will say there really weren’t 800,000 people who were massacred with machetes.” Designing digital systems that can preserve information for many generations is one of the most vexing engineering challenges. The researchers’ solution is to create a publicly available digital fingerprint, known as a cryptographic hash mark, that will make it possible for anyone to determine that the documents are authentic and have not been tampered with. The concept of a digital hash was pioneered at I.B.M. by Hans Peter Luhn in the early 1950s. The University of Washington researchers are the first to try to simplify the application for nontechnical users and to try to offer a complete system that would preserve information across generations. Both because of the rapid pace of innovation and the tendency of computers to wear out in months or years, the likelihood that digital files will be readable over long periods of time is far less certain even than the survival of paper documents. Computer processors are quickly replaced by incompatible models, software programs are developed with new data formats, and digital storage media, whether digital tape, magnetic disk or solid state memory chips, are all too ephemeral. Several technologists are already grappling with the evanescent nature of digital records. Danny Hillis, a computer scientist, helped found the Long Now project in 1996, warning about the possibility of a “digital dark age.” The group is now designing a clock that will “tick” annually and that is designed to have a life span of 10,000 years. It is intended as a counterpoint to the “faster/cheaper” ethos of today’s increasingly computerized world. Mr. Hillis has argued that before the rise of digital information people valued paper documents and cared for them. Since then, there has been progressively less attention paid to the preservation of information. Now information is routinely stored on media that may last for only several years. To that end, another computer scientist, Brewster Kahle, founded the Internet Archive in 1996 in an effort to preserve a complete record of the World Wide Web and other digital documents. Similarly, in 2000 librarians at Stanford University created LOCKSS, or Lots of Copies Keep Stuff Safe, to preserve journals in the digital age, by spreading digital copies of documents through an international community of libraries via the Internet. However, Ms. Friedman distinguishes her design work from those who have focused on the simple preservation of digitized materials. Instead, she said she was trying to design complete digital systems that would play a role in strengthening social institutions over time by creating a digital historical record that offered continuity across multiple life spans. “Building a clock is iconic,” she said. “What is really different is that we are trying to solve socially significant, real-world problems.” Because problems like genocide, H.I.V. and AIDS, famine, deforestation and global warming will not be solved in a single human lifetime, she argues that information systems designed to ensure continuity across many generations are a necessity. To ground the group’s research in a real-world situation, the researchers began by building an archive of video interviews with the judges, prosecutors and other members of the International Criminal Tribunal for Rwanda. The goal was to design a system that would ensure that the information was secure for more than a century. Last fall Ms. Friedman traveled with a group of legal experts and cinematographers to Arusha, Tanzania, where the tribunal is based, and to Kigali, Rwanda, to conduct video interviews. After capturing five gigabytes of video in 49 interviews, the group began to work on a system that would make it possible for viewers to prove for themselves that the videos had not been tampered with or altered even if they did not have access to powerful computing equipment or a high-speed Internet connection. Despite the fact that there are commercial applications that make it possible to prove the time at which a document was created and verify that it has not been altered, the researchers wanted to develop a system that was freely available and would stand a chance of surviving repeated technology shifts. At the heart of the system is an algorithm that is used to compute a 128-character number known as a cryptographic hash from the digital information in a particular document. Even the smallest change in the original document will result in a new hash value. In recent years researchers have begun to find weaknesses in current hash algorithms, and so last November the National Institute of Standards and Technology began a competition to create stronger hashing technologies. The University of Washington researchers now use a modern hash algorithm called SHA-2, but they have designed the system so that it can be easily replaced with a more advanced algorithm. Their system will be distributed as part of a CD known as a “live CD,” making it possible to compute or verify the hash just by inserting the disk in a computer. The disk will also include software components that will make it possible to view documents and videos that may not be accessible by future software. The problem is complex, said Michael Lesk, a professor in the department of library and information science at Rutgers University, because not only must you be able to prove that the information has not changed in its original format, but you must also be able to prove that once the format is altered, the original digital hash is still valid. The Long Now Foundation is developing a software tool to easily convert documents between digital formats, said Stewart Brand, a co-founder of the project. “The idea is to be able to change anything into anything else,” he said. http://www.nytimes.com/2009/01/27/science/27arch.html  Businesses Risk $1 Trillion Losses From Data Theft: Study Businesses risk losing over $1 trillion from loss or theft of data and other cybercrime, according to a study released on Thursday by security technology firm McAfee Inc. The California-based company launched the survey after detecting a rapid acceleration of malicious software, or "malware," last year, CEO David DeWalt told Reuters. Malware increased by 400 percent in 2008, he said. "This was a very insidious type of malware that was designed either to steal your data, steal your identity, steal your money, and in many cases the scale as well as the sophistication was very alarming," DeWalt said in an interview at the meeting of the World Economic Forum in Davos, Switzerland. The survey of 800 companies in 8 countries showed that 80 percent of malware aimed to make a financial gain, in contrast to traditional viruses and worms which just had nuisance value. In the survey, 42 percent of companies said that laid-off employees were the single biggest threat to their data security. The increase in the availability and power of removable storage, such as mobile phones, laptops, and USB sticks, has made data loss or theft easier. And global supply chains mean that sensitive data is often stored abroad. DeWalt said the survey showed that the average company has $12 million of data stored outside its home country -- often in countries with little intellectual property law. Data lost accidentally or through theft can be expensive to replace or damaging to a company's reputation or brand. In April last year, discount retailer TJX said it would pay up to $24 million as part of a settlement with MasterCard over a security breach that put credit card data for tens of millions of shoppers at risk. The British government has been repeatedly embarrassed by losses of data, such as when the tax authority, HM Revenue and Customs, lost data on 25 million people exposing them to the risk of identity theft and fraud. (Reporting by Jonathan Lynn; editing by Simon Jessop) http://www.reuters.com/article/techn...50S2FX20090129  Student Withdrawn from UK School Over CCTV in Toilets Officials: Cameras were installed in bathrooms following incidents of 'major concern' A Teenage pupil has been withdrawn from her school after CCTV cameras were installed in the pupils' toilets. Anthony White, from Llandysul said the cameras at Ysgol Dyffryn Teifi in Ceredigion were an "outrageous invasion" of his daughter Jade's privacy. Jade, 14, said: "I am not going back while the cameras are there. It must be against the law to have them there." Mr White said: "The school is being pathetic. They don't need security cameras in toilets - certainly not in schools." Ceredigion Council said it had installed the cameras after incidents of "major concern". Spokeswoman Anwen Francis said: "Any such viewing of CCTV footage is undertaken by senior members of staff having Criminal Records Bureau (CRB) clearance." http://www.securityinfowatch.com/onl...n=305&id=19760  What the Web Knows About You How much private information is available about you in cyberspace? Social Security numbers are just the beginning. Robert L. Mitchell She had me at hello ... or just about. Our conversation had barely started when privacy activist Betty Ostergren interrupted me to say that she had found my full name, address, Social Security number and a digital image of my signature on the Web. I had set out to discover just how much information I could find about myself online, and Ostergren, who runs the Virginia Watchdog Web site, was my very first call. If this was what could be uncovered in just a few minutes, what else would I find? Quite a bit, as it turns out. What information is available about you in cyberspace? Where does it come from? What risks does it present and what, if anything, can you do to protect yourself? To answer those questions I decided to use my own identity, Robert L. Mitchell, a national correspondent at Computerworld, as my research subject. Starting with the information Ostergren had turned up about me, I spent a few weeks combing through more than two dozen public and private resources on the Web and visiting many other Web sites to build a dossier on myself. I conducted both free and paid searches. I contacted a private investigator for tips on my investigation. And I spoke with data aggregators and privacy experts. I quickly discovered that while the quantity of publicly available information about individuals to be found online is vast, it is riddled with inaccuracies. For example, I changed my primary residence more than a year ago, but many databases online still have my old address. In other cases, the information is just plain wrong. Having a common name like Robert Mitchell -- or a famous one like Bill Gates -- makes the job a lot harder. While nuggets of information about you can be pulled up quickly, filtering out all of the data that is not actually about you and sorting out what is accurate is time-consuming. It requires a lot of digging. But I was starting with a key piece of data -- my Social Security number -- and that makes finding relevant data a bit easier. As I gathered more data, I also reran many searches to get different -- and more targeted -- results. Here's what I found and where I found it. Information discovered: Full legal name, address, Social Security number, spouse's name and Social Security number, price paid for home, mortgage documents, signature Much of the publicly available information on individuals online is sourced from online county, state and federal government records databases, and this is where Ostergren found my Social Security number. She hadn't purchased it from a hacker chat room or from shady characters in Russia. She got it by browsing an image of a mortgage document stored in a county database located in a building half a mile from my house. Dossier Name: Robert L. Mitchell Title: National Correspondent Company: Computerworld Information discovered online: Full legal name Date of birth Social Security number Current property addresses Personal phone numbers Business phone numbers Previous addresses and phone numbers dating back to 1975 (except for cell phone numbers) Real estate property deed descriptions and addresses Property tax record from 2004 Assessed value of home from 1997 Identifying photographs Digital image of signature Mortgage documents (current and previous) and a legal agreement Computerworld affiliation, stories and blog posts Employment history Resume with educational background going back to high school Sex offender status (negative) Affiliations with several nonprofits Editorial award Spouse's name, age and Social Security number Names of friends and coworkers Names, addresses, phone numbers and first six digits of Social Security numbers for neighbors past and present Parents' names, address, phone and first five digits of Social Security numbers What I haven't found ... yet: Driver's license number Vehicle registrations Banking records Medical records Detailed demographic data from marketing databases Insurance claims history Vehicle registrations Property records for land in Florida Voter registration record/political affiliation Mother's maiden name City and state of birth Over the past five years, bulk scanning and online publishing of such documents have proliferated in many states. In many cases, including New Hampshire -- my state of residence -- little or no attempt has been made to redact sensitive personal data such as Social Security numbers before moving those records online. The public is blissfully unaware that these documents, which were once accessible only in dusty books inside the walls of the registry of deeds, are now freely available over the Web to anyone in the world with a click of a mouse. Ostergren says that this information is a treasure trove for data aggregators, brokers and criminals. Unlike financial and medical records, which are regulated, Social Security numbers gathered from public records come with no strings attached. They can be republished anywhere with impunity. "You're in a state that is spoon-feeding Social Security numbers to everybody," Ostergren says. In the county where I live, legal documents from 1975 and on have been scanned and placed for public viewing on the Web. No registration or payment is required to view those records, although there is a charge to print official copies. The database includes thousands of records on New Hampshire citizens, including tax liens, federal liens, divorce papers, financing statements, military discharge papers, death certificates -- even a mobile home warranty. Any legal document filed with the registry is fair game. In these records I found names, addresses, Social Security numbers, dates of birth, signatures, children's names, educational backgrounds, blood types, work histories and other personal data. Newer mortgage documents no longer contain Social Security numbers (mine was from 2001), but many other documents still do -- including death certificates and tax liens. In my case, fortunately, just one document on file -- the old mortgage -- contained my Social Security number. Revelations from the rest of my government database searches were less sensational. State and county court documents are public records. In many states, those records are already online and available for public viewing on the Web. New Hampshire's county court records have not been put online, but the state has plans to do so, according to a county official. Lauren Noether, bureau chief for consumer protection and antitrust at the New Hampshire Department of Justice, says it's just a matter of time before those records are available online. But she is concerned because standards for what information appears in legal documents have changed over time. "I had an individual call to tell me that their child's name was in [an old] child abuse indictment. Nowadays we don't do that," she says. Noether amended the document, but she worries that bulk scanning and publishing of all historical records would bring many other inappropriate disclosures into public view. Like many states, New Hampshire has a child sex offender registry. I am not a sex offender, but for the purposes of this story (I am the subject of the investigation, after all) I ran my name through anyway. As expected, I wasn't on the list, but it was chilling to find three other Mitchells listed there. My next stop was the federal Public Access to Court Electronic Records (PACER) database, which contains U.S. District, Appellate and Bankruptcy court records. Here the government wants to know who is searching. The registration process for users involves entering your Social Security number, date of birth and other data. I found myself trolling through dozens of records of people who were not me, at a cost of $.08 per page of results. I pulled up a total of 119 records, including 51 Robert L. Mitchell bankruptcies. Another Robert L. Mitchell had been arrested for kidnapping. But nothing matched the Robert L. Mitchell I was researching. The PACER system required that I conduct a separate search for each jurisdiction. CriminalSearches.com is a commercial site that aggregates the same information so that you can do a single search across all jurisdictions -- and it's free. I executed a free search on the Web site. Apparently, I have a clean record in all 50 states. I also searched state and county databases for the state in which I reside. Database aggregators such as LexisNexis pull information from all of the various local, state and federal databases and roll them up for easier searching, but you need to buy a subscription to use such services. Computerworld has a LexisNexis subscription, but that costs money. While I did fork over $.08 a page for PACER results, that amounted to less than a dollar. At this point in my investigation, I wanted to see how much I could find for nothing -- or next to nothing -- before resorting to fee-based services. Information discovered: Employer name, job title, age, month and date of birth, phone numbers, wife's name and age, historical addresses and phone numbers, personal e-mail address, identifying photographs, employment history I continued my investigation with the people and business search Web sites, including ZabaSearch, WhitePages.com, PeopleFinders.com, US Search, Intelius, Switchboard and PublicInfoGuide.com. The initial searches were free, although each service charged a premium for some of the data it uncovered. As I found out, you get what you pay for. I gathered plenty of data on Robert L. Mitchells, but most of the data wasn't relevant to the Robert L. Mitchell I was investigating. Each search yielded multiple results, including some records with outdated information about me and others with totally inaccurate data. In some cases, aggregated data clearly had been mismatched, which appeared to be the result of mashing together two different Robert Mitchells into one identity. ZabaSearch pulled up only an e-mail address I don't use and another that no longer exists, but it did find my mailing address, which it displayed on a satellite map. WhitePages.com had my name and phone number associated with a wrong address. Switchboard incorrectly described my home telephone number as unlisted. PublicInfoGuide.com found a residential address but listed four "relatives" that I never knew I had. PeopleFinders returned an address and phone number in another state where I had lived 20 years ago. Social Security numbers and the law Is it really legal to post Social Security numbers online? That depends on who's posting them. If the source of my Social Security number had been a financial institution, it would be regulated by the Gramm-Leach-Bliley Act, which states that the information can't be disclosed to third parties without notifying the consumer, and the Fair Credit Reporting Act, which controls the access to individuals' financial information for the purposes of marketing credit offers. Ironically, public records disclosure of Social Security numbers -- on death certificates, mortgages, military discharge papers, criminal records and other documents -- isn't restricted. (See "FAQ: Is your county posting your Social Security number online?") In fact, the government is required to make the records public -- although there is nothing in the law that states that the data must be published on the Web. And while some documents, such as death certificates, are required to include Social Security numbers, others, such as mortgages, are not. To make matters worse, anyone can republish Social Security numbers if they were already published on a public government Web site, according to a recent court ruling in Virginia. But there is hope: On Jan. 6 of this year, U.S. Sens. Judd Gregg (R-N.H.) and Dianne Feinstein (D-Calif.) introduced legislation, called the Protecting the Privacy of Social Security Numbers Act, that would prohibit anyone -- including the government -- from displaying Social Security numbers on the Web. In some cases, part of the search results, such as the full address or e-mail address, was deliberately omitted. PeopleFinders located a Robert L. Mitchell in the correct town but wanted $1.95 for the full address. As up charges go, that was cheap: US Search wanted $10 to divulge the full address. I found it unnecessary to pay for these results, since different sites tended to provide different information upfront -- I could piece together all the bits of free information from various sites. My Computerworld affiliation didn't turn up initially, nor did my business phone lines or my cell phone number. A search at ZoomInfo produced my correct title and Computerworld affiliation, but the work history was a comedy of errors, including incorrect titles and a stint as a PC World contributor that I must have forgotten. Under "Education," the results simply said "MSN dial-up." Information discovered: Age, phone numbers, Computerworld affiliation, Computerworld stories, blog posts, identifying photos, social network and nonprofit affiliations, editorial award I continued my research with the commercial search engines, including Google, Yahoo Search, Microsoft's Live Search, Dogpile and Vivisimo's Clusty. I used combinations of my name, job title, business name and location, and I concerned myself with only the first few pages of results. As I encountered new information, I added it to my search criteria and ran searches again and again. The search engines divulged my age, phone numbers, my identities on three social networking sites and dates when I had signed up, my positions with two nonprofit organizations, links to Computerworld stories, blog links, a few snarky remarks about my stories and an announcement that a Computerworld story I wrote won an ASBPE award in 2007. For good measure, I also searched the Techmeme, Technorati and Computerworld sites directly, assembling a long list of stories I had authored, as well as comments about those stories and contact information. Information discovered: Computerworld publicity photos, Flickr photos Here I stuck with Google Image Search and Flickr. The 429 Google image results included dozens of Robert L. Mitchell photos, but the correct one was buried five screens down in the results. Also, displayed were photos of people whom I have interviewed for Computerworld stories. A Google image search for Robert L. Mitchell. Where am I? Click to view larger image. Flickr searches on variations of my name produced no photos of me, but I was able to find my account by searching members with the name "Robert Mitchell." On the third screen, my photo appeared next to an account name. By matching that photo with the Computerworld publicity photo, I was able to identify myself. From there, I was able to view several hundred publicly shared photos associated with that account. But like much of the content on Flickr, those images are untagged. Finding photos of me in the long list was a painstaking process. Information discovered: Computerworld stories, blog posts, social network friends and co-workers Here I searched individual social networking sites, as well as two search tools that promise to provide information from social networking sites: Delver and iSearch. iSearch produced the same results I'd seen elsewhere. Click to view larger image. With iSearch, users can search for social network content by name or by screen name. A name search on "Robert L. Mitchell" produced the same people search results I had seen before, and searches on all my screen names produced no results. A spokesperson stated that iSearch, a service launched by Intelius last September, was still building up the database for the service. Delver, another social network search engine, indexes content and ranks its relevance based on what your social network of "friends" have to say about it. It indexes content from MySpace, Blogger, LinkedIn, YouTube, Hi5, FriendFeed, Digg and Delicious, as well as profile data from Facebook. A search on "Robert L. Mitchell" brought up 47,755 Web links. I found no personally identifying information but did find links to stories I have written. I concluded by searching individual social networking sites. I didn't get much here, but private investigator Steve Rambam, who runs the Pallorium investigative agency in Brooklyn, N.Y., says the amount of self-contributed data available on many individuals is enormous. "If you have a MySpace page, and Friendster, LinkedIn, Plaxo, Yahoo 360 and Monster.com, and you use Twitter and Flickr, in 90 seconds I'll have your photo, your likes and dislikes, where you live, what you do and so on -- all contributed by you," says Rambam. That search, he says, provides as much information as he used to gather during a 12-month investigation in pre-Web days. If that sounds scary, the technology also has its limits. "You have the best defense against a casual investigation: a common name," says Rambam. To find people like me on social networking sites requires logging onto each one individually and using advanced search features to try to narrow down the field. "Even then there are dozens of records that would have to be manually examined," Rambam says. But that just slows him down. "It would probably take a full day to compile a decent dossier on you," he says, while a unique name takes just a few minutes. Information discovered: Address history to 1985; real estate purchase dates, assessed values and mortgagors; 2004 property tax bill; nonprofit affiliations; Flickr account details; published stories; parents' names, address, phone number and first five digits of Social Security numbers; current and past neighbors' names, addresses, phone numbers, dates of birth and first six digits of Social Security numbers At this point, I decided to invest a little money to see what premium searches would buy me. Since no one had come up with my cell phone number, I decided to start small, with a US Search reverse phone lookup -- which means you provide the number and the company traces its owner. US Search indicated that the information was available on my number -- for a fee of $14.95. I pulled out my credit card and purchased the report. US Search could not find any data initially. The next day it sent an e-mail that attributed the phone to "Josh (last name unavailable)." Address information was limited to a town name, which was incorrect. US Search refunded my money. I tried other sites, also without success. One possible reason why: I never provide my cell phone number online or use it for business transactions. Things did not go so well with USATrace.com, which claimed to offer an "SSN Search" background report on any Social Security number for $37.99. I had picked the company at random from a long list of businesses that came up after I ran a Google search on "Social Security number trace." The company processed my transaction, but I received no report. Over the next few days, several phone calls and e-mails went unanswered. I ended up challenging the charge on my credit card bill -- a process that eventually resulted in a refund from American Express. Caveat emptor. I then approached Intelius, a bigger name that also provides data to business partners such as ZabaSearch. Intelius waived its $49.95 background search charge for the purpose of this story. I requested a few extra bells and whistles, which would have brought the total cost to $77. Among other things, the report included searches of criminal records, civil judgments, sex offender records, address history, real estate property records and death certificates. Intelius gets its information from public records, marketing databases and information that is scraped off the Web, says Ed Petersen, co-founder and executive vice president at Intelius. Much of the information is purchased from other data providers. Inaccuracies in the data and the abundance of data on people who were not me made combing through the 67 pages of results a bit of a chore. After removing the irrelevant content, I was disappointed to find that the report contained just one piece of data that I had not found through my previous, free searches: a June 2004 property tax bill in the amount of $1,857. Despite the fact that I'd entered my address and Social Security number, the bulk of the report consisted of state and federal criminal records of 156 Robert Mitchells from all over the country, none of which were me. It included incorrect names of "relatives" as well as records with my correct phone number attached to the wrong address and vice versa. It did not find my primary legal residence address or phone number at all. (We moved one year ago.) The business records section of the report did not turn up my position at Computerworld or my business phone number. Intelius did aggregate a lot of data about me that I had already discovered, and might have saved some research time. However, I would still have had to do additional work to resolve the inconsistencies and other errors. Next I tried a service called ReputationDefender, which tracks both what is being said about you (the MyReputation service; $9.95 per month) and personal information available about you on the Web (MyPrivacy; $4.95 per month). After a few days, the service uncovered my residential phone numbers, information about my work with a nonprofit organization, details of my Flickr account and a couple of Web sites I set up. Finally, I tried searching public records through LexisNexis. Computerworld's subscription includes a search function that combines data from public records databases ranging from motor vehicle records to court documents to hunting and fishing licenses. While much of the information LexisNexis returned was the same as what I'd found previously, it produced more information overall, and data accuracy was somewhat better. LexisNexis returned the most accurate information. Click to view larger image. I came away with a listing of past and present neighbors' addresses, phone numbers and partial Social Security numbers and a historical list of my real estate property transactions that included the amount paid, date of purchase and mortgage lender name. I found the assessed value for my residence for the year 1997. Also available: my mother's and father's names, ages, address, phone number and partial Social Security numbers. While LexisNexis allows voter registration list searches, no information appeared for my name in New Hampshire. Voter registration lists have been consolidated into a central database to meet federal requirements. Currently, that database is exempted from New Hampshire's Right-to-Know Law, but legislators have given the Democratic and Republican parties exclusive access to it, says New Hampshire State Representative and privacy advocate Neal Kurk, a Republican. "The parties take this information and sell it to candidates, and you can be sure that a disc containing all of this information goes to various marketers or charities or whoever," he says. So far, though, it wasn't accessible to me. I also could have searched for other, more sensitive data, such as driver's license and motor vehicle registrations, on LexisNexis. Access to that data is controlled by government regulations, but to see it I simply had to pick a "permissible" use (litigation, debt recovery, insurer, etc.) from a drop-down list. While LexisNexis' terms and conditions do state that it keeps track of who has accessed regulated data, as far as I could tell, anyone can conduct a search without any verification of a permissible use claim. At other sites, permissible use is simply a generic checkbox item under Terms and Conditions. At US Search, for example, the terms of use state that "By purchasing US Search services you agree that ... You will use the Service only for appropriate, legal purposes, and in compliance with all applicable federal, state and local laws and regulations." Not too reassuring. What else is out there? Did I find everything that was out there? Private investigator Rambam says the information I gathered in a few days of work was just the tip of the iceberg of what is available about individuals online. Rambam runs PallTech, an investigative database service for law enforcement and security professionals. Its 25 billion records on individuals and businesses include aggregated public records, telephone listings, marketing data, and more sensitive, regulated data such as vehicle registrations. A single query performs 62 different searches and produces an average of 230 pages of results in 90 seconds, Rambam says. He quickly found my Social Security number, driver's license number, vehicle registrations, date of birth, e-mail address and other information. PallTech's database isn't open to the public, but Rambam says much of the same information is out there for anyone who's determined to find it. For example, I didn't find my medical records or banking records online; both types of information are regulated. But, says Rambam, "Any competent social engineer can get that information. There's just too many places where it's available." For instance, Rambam says he once tracked down a subject by calling pharmacies near the person's address, posing as the subject and asking if his prescription was ready. He quickly learned both the name of the prescription and the doctor who prescribed it. By calling the doctor's office, he was then able to get the time and date of the subject's next appointment. While all this is illegal (he did it with the subject's permission, as part of a friendly bet) and he says most professional investigators don't do that today, he's certain that scammers use the technique. I also didn't find my state of birth or mother's maiden name online, but Rambam says that I could have found the information with a little more work. (For example, I didn't think to look on genealogy Web sites.) "The downside to all of this publicly available information is that it's now a lot easier to social engineer somebody," he says. If someone has access to a profile of personal information about you as well as your network of friends, that makes it easier for someone to pose as you to gain access to more sensitive data. And much more personal information is tucked away in marketing databases, says Rambam. Data aggregators such as ChoicePoint and Acxiom, he says, maintain giant databases of information about individuals for risk management and marketing purposes. To find out more, I spoke with Jennifer Barrett, global privacy officer at Acxiom, a large data aggregator and marketing services provider in Little Rock, Ark. Acxiom specializes in helping businesses build complete demographic profiles of their customers. It builds large, proprietary data warehouses that match up the client's marketing data on its customers (what they bought) with "intelligence" on those customers (who they are) that includes demographic data, interests, what types of products the subjects like to buy and so on. (For details, see "How much do marketers really know about you?") Acxiom and some other data aggregators do allow consumers to request, for a fee, a report summarizing the basic identifying and background screening information that the company has about them in its databases. (Acxiom does not release this information without a signed form and a personal check for $5 with name and address information printed on it that matches the name and address of the subject of the request.) I wanted to find out what details Acxiom had on me, so I made the request (the company waived the fee for the purposes of this story); however, the report I received did not include the full search results. Interestingly, Barrett cites privacy as the reason Acxiom didn't reveal more of the data it owns about me. Search results often return information on other people who are linked to the subject's data in some way, such as through a common address or phone number. "It divulges details on other individuals and would invade their privacy," she says. But Acxiom does allow consumers to opt out of its marketing databases. How much do marketers really know about you? Database aggregators like Acxiom gather intelligence about consumers from sources that include surveys, product registrations, and magazine subscription data, says Barrett. "If you subscribe to a cooking magazine, we know someone likes to cook in your household," she says. Many businesses sell or rent that data to Acxiom. It's an urban myth that companies like Acxiom collect data from everywhere and can pull out anything they want about you, she says. "People call us and expect us to have the fact that they bought a blue shirt from Lands End last night." Actually, Barrett says, Acxiom buys generalized data from companies with which individuals have made a purchase, such as in the cooking example above. But Paul Stevens, director of policy and advocacy at the nonprofit Privacy Rights Clearinghouse, believes that the amount of detail gathered about individuals is far more extensive than most people would imagine. While the data Acxiom gathers isn't likely to end up in the hands of identity thieves, he says that if people knew just how much aggregators know about them it would probably make them uneasy. "Some of these database aggregators know more about us than we know about ourselves," Stevens says. Rambam agrees. "Where this all gets a little creepy is when they aggregate all of this data together and have an extraordinary profile of you," he says. "Marketing companies know your religion, your sexual orientation, the names of your family members, what magazines you read, when and how often you go to the supermarket, what candidates you contribute to. It is a window into your soul." But access to information in marketing databases is tightly controlled, says Acxiom's Barrett. "Our clients get far more scrutiny [from regulators, privacy advocates and the public] of where are you getting this data and is it legal" than ever before, she says. Acxiom's clients expect the company to provide data that has been legally obtained, and to deliver it within a context that meets regulatory guidelines for each type of request, says Barrett. In fact, she says, Acxiom screens clients that request access to the more sensitive data it collects and may provide different levels of access to client employees based on their business role and their need to know. Assessing the risks Perhaps the biggest risk that accompanies the proliferation of personal information on the Web is the increased danger that the information will be used for identity fraud. Although overall identity fraud has trended down somewhat, 8.4 million people were victims of identity fraud last year, according to Javelin Strategy & Research, which publishes an annual survey report on the subject. Of the information available about me on the Internet, the most troubling was my Social Security number, blatantly posted online by my own county government, for the convenience of lawyers, insurance agents -- and petty criminals interested in identity theft. Today, you need more than just a Social Security number to commit identity fraud, but a criminal who has that number is off to a great start. "Various arrest records released by law enforcement have included criminals' confessions of using bulk scans of both paper and electronic records access," says Javelin president James Van Dyke. While I was able to have my Social Security number redacted from the county Web site record by filling out a form with the Registry of Deeds, there's no telling if that information was already scraped by thieves. (On the plus side, the information from the county database didn't show up on Google or other search sites, probably because it resides in a database and must be queried rather than appearing on a Web page that is easily indexed by Web crawlers.) I had my Social Security number redacted on the county Web site. Identity thieves can also cobble together Social Security numbers from different sources that publish different parts of the Social Security number as an identifier. For example, subscribers to LexisNexis can find the first five digits of a subject's nine-digit Social Security number, while Acxiom provides the last four digits in its reports (although that's harder to obtain, since Acxiom screens its customers). Federal tax liens use the full Social Security number, and state tax liens use the last four, says Ostergren. Both are publicly available on paper records, and in many cases the data is being republished on the Web. Once a thief has the number, it can be used to unlock more data about you that can be used for identity theft. The sheer breadth of information available about individuals online is also a concern. According to Rambam, having access to that much information makes it easier for criminals to obtain other identity authentication factors such as a mother's maiden name. But others say that even having one or two authentication factors for an individual is no longer a guarantee of success in identity theft. Improved processes and consumer awareness are key reasons why new account fraud has remained flat in the past year, according to Javelin, and faster detection has caused account fraud losses to decrease by 21% from 2007 to 2008. Barrett says that the number of authentication factors required is on the increase, and varies with the risk involved. Accessing an online subscription to the Wall Street Journal would require fewer authentication factors than would accessing a bank account. In fact, most financial institutions now require multiple authentication factors to open an account -- or even to process an address change. "If there's a high degree of risk it can be seven or eight or nine factors. If it's not it might be three or four. But it's not one or two." As a test, I called my business credit card company and my bank. The credit card vendor asked for my account number and mother's birth date to access my account. To change my address, I also needed to provide my full name and the credit card's four-digit security code. That's four factors. When I called my local bank with the same request, the representative asked for my name, middle initial, city of birth and mother's maiden name. (According to a security executive from the bank, representatives may also ask the branch location where you opened the account and how long you've had the account.) The representative did not ask for my account number, and she divulged my current address during our conversation. But are four authentication factors today really more secure than two were 10 years ago? Four may be the new two. Because so much data about me is readily available online, right out of the gate I had found online two of the four factors needed to change the billing address for my credit card. But I still needed the physical card to determine the card number and security code. More worrying was the fact that I had tracked down three of the four authentication factors needed to change my address with the bank (which is now reviewing its policies). While both institutions require four authentication factors, the fact that the answers to some of those "authentication" questions about me are readily available online mitigates their value. In this case, an identity thief is two authentication factors away from cracking my credit card account and just one away from messing with my bank account data. The banks might do well to increase the number of authentication factors in use -- even though it presents an inconvenience to customers. The challenge will be figuring out what questions to ask in a world where almost everything there is to know about you is publicly available online. Privacy may be dead, as Rambam likes to say, but individuals can play a role in reducing their information footprint and shaping the information that is available about them. Keep reading our special report for steps you can take to control data about you. http://www.computerworld.com/action/...icleId=9125058  12 Tips for Managing Your Information Footprint Take an active role in controlling your personal data. Robert L. Mitchell When it comes to managing personal information online, most people are their own worst enemies. Many of us fail to adequately protect our personal data before it gets online, but once information makes its way to the Internet, it can be quickly replicated and is often difficult, if not impossible, to remove. For example, in four weeks of on-and-off reporting and online searches using publicly available online records and tools, I was able to find my current and past addresses and phone numbers, date of birth, Social Security number, employment history, identifying photographs, a digital image of my signature and much more. See "What the Web knows about you" for all the gory details. You can take an active role in managing data about you, whether it resides in marketing lists, government databases, telephone directories or credit reports. Here are some tips. 1. Think before you disclose personal information about yourself online on business networking sites such as LinkedIn, job listing sites such as Monster.com, and social networking sites such as MySpace and Twitter. How much do you want to disclose about your employment history, likes and dislikes, and where you are at any given time? Do you really want everyone to know when you're not at home, how long you'll be out and when you'll be back? 2. Don't give out your Social Security number -- anywhere -- unless absolutely required. 3. Don't use real information about yourself for authentication, recommends private investigator Steve Rambam. Instead, he suggests making up answers to commonly asked security questions such as a mother's maiden name. 4. Know what's out there about you. Do a search online using search engines, government Web sites and other resources cited in "What the Web knows about you" to get an idea of what information about you is available online today. If your Social Security number appears in a public records database, ask the agency in charge of the database if they will redact it from the record on your behalf. You can also ask Web site owners to have sensitive information redacted and any potentially damaging inaccuracies corrected. 5. Keep up with new data about you as it is published on the Web. Alert services such as Google Alerts are designed to continuously search the Web to track topics you're interested in, but you can also use them to find out what information about you is being published on the Web. Configure the service to search the Web for instances of personally identifying information such as your name, address, phone number, Social Security number, and so on. When Google finds matches, it will send you an e-mail with links. 6. Consider requesting a fraud alert from one of the three major credit reporting agencies (Experian fraud alert, TransUnion fraud alert or Equifax fraud alert) if you discover sensitive data such as your Social Security number on a public Web site or service. If you request a fraud alert with any of the three agencies, it will notify the others on your behalf. 7. Also consider requesting a security freeze, which takes a fraud alert one step further. It means that no one can access your credit report without your explicit consent, which makes it difficult for fraudsters to open up new accounts in your name. This is a new option that has only become broadly available in the past year. A freeze must be placed with each of the three major credit reporting agencies, and you must unlock access to your credit report (for a fee) when a lender, insurance company or other party requests the information. True, it's inconvenient. You pay a small fee to freeze your credit report at each of the three reporting agencies. Then you pay another fee each time you unlock it. But you'll have the security of knowing exactly who is trying to access your credit report -- and for what reasons -- every time. 8. Request a copy of your credit report at AnnualCreditReport.com and review it for errors. Ignore the sales pitches for credit monitoring products. Identity fraud monitoring services, including those sold by the three credit reporting agencies and others, can provide peace of mind, but they're pricey for what you get and most tell you only after someone has compromised your identity. 9. Opt out of the marketing databases at the big data aggregators such as ChoicePoint and Acxiom. Unfortunately, the companies usually won't take requests from third-party services like Reputation Defender, which attempt to do this on your behalf; you have to contact each one yourself. You can also ask to see the profile they have of you and ask for changes if the data is incorrect. They won't, however, pull information about you that's used for "risk purposes," such as for insurance underwriting or litigation. While you can opt out of Web people search and background checking services such as Intelius and US Search, there are simply too many to contact. Intelius will honor your request, but Ed Petersen, co-founder and executive vice president, says it's not worth the effort. "You're tilting at windmills. I'm not the original source of the data, [and] there's a lot of companies like Intelius out there." This is one reason why it's so important not to let these data bits get out there in the first place. 10. Protect your cell phone number. If you don't want it in public database records, don't give it out for business transactions. "If you never put it down anywhere, then it is not going to be in the public records," says Petersen. Using an unlisted phone number reduces, but does not eliminate, the number of places where your telephone number will appear online. Every time you give out the number, as may be requested for purchases, registrations and other business transactions, it goes into databases that may be sold to aggregators. 11. Don't participate in surveys or fill our product registration cards. It's not required for warranty service (all you need is your receipt), and the information you submit goes right into marketing databases. 12. Think twice before signing up for retail store loyalty cards -- and read the privacy policy. Are the incentives worth it if the business is tracking your every purchase? In many cases, the business will keep that information for its own use. In other cases, some or all of that data may be shared with business partners, marketing companies or data aggregators. For more privacy tips, read the Privacy Rights Clearinghouse's Privacy Basics and Opt-Out Strategies page. http://www.computerworld.com/action/...icleId=9125098  When You Watch These Ads, the Ads Check You Out AP Watch an advertisement on a video screen in a mall, health club or grocery store and there's a slim — but growing — chance the ad is watching you too. Small cameras can now be embedded in the screen or hidden around it, tracking who looks at the screen and for how long. The makers of the tracking systems say the software can determine the viewer's gender, approximate age range and, in some cases, ethnicity — and can change the ads accordingly. That could mean razor ads for men, cosmetics ads for women and video-game ads for teens. And even if the ads don't shift based on which people are watching, the technology's ability to determine the viewers' demographics is golden for advertisers who want to know how effectively they're reaching their target audience. While the technology remains in limited use for now, advertising industry analysts say it is finally beginning to live up to its promise. The manufacturers say their systems can accurately determine gender 85 to 90 percent of the time, while accuracy for the other measures continues to be refined. The concept is reminiscent of the science-fiction movie "Minority Report," in which Tom Cruise's character enters a mall and finds that retinal scanners identify him and prompt personalized ads that greet him by name. But this technology doesn't go nearly that far. It doesn't identify people individually — it simply categorizes them by outward appearances. So a video screen might show a motorcycle ad for a group of men, but switch to a minivan ad when women and children join them, said Vicki Rabenou, the chief measurement officer of Tampa, Fla.-based TruMedia Technologies Inc., one of the leaders in developing the technology. "This is proactive merchandising," Rabenou said. "You're targeting people with smart ads." Because the tracking industry is still in its infancy, there isn't yet consensus on how to refer to the technology. Some call it face reading, face counting, gaze tracking or, more generally, face-based audience measurement. Whatever it's called, advertisers are finally ready to try it, said advertising consultant Jack Sullivan, a senior vice president of Starcom USA in Chicago. "I think you're going to see a lot of movement toward it by the end of this year in the top 10 markets," he said. Because face tracking might feel reminiscent of Big Brother, manufacturers are racing to offer reassurances. When the systems capture an image of who's watching the screen, a computer instantly analyzes it. The systems' manufacturers insist, however, that nothing is ever stored and no identifying information is ever associated with the pictures. That makes the system less intrusive than a surveillance camera that records what it sees, the developers say. The idea still worries Lee Tien, a senior staff attorney with the Electronic Frontier Foundation, a civil-liberties group in San Francisco. Tien said it's not enough to say some system is "not as bad as some other technology," and argues that cameras that study people contribute to an erosion of privacy. In general, the tracking systems work like this: A sensor or camera in or near the screen identifies viewers' faces by picking up shapes, colors and the relative speed of movement. The concept is similar to the way consumer cameras now can automatically make sure faces are in focus. When the ad system pinpoints a face, it compares shapes and patterns to faces that are already identified in a database as male or female. That lets the system predict the person's gender almost immediately. "The most important features seem to be cheekbones, fullness of lips and the gap between the eyebrows," said Paolo Prandoni, chief scientific officer of Quividi, a French company that is another player in face-tracking technology. Others include Studio IMC Inc. in New York. The companies say their systems have become adept at determining a viewer's gender, but age is trickier: The software can categorize age only in broad ranges — teens, younger to middle-aged folks and seniors. There's moderate demand for ads based on ethnic information, but the companies acknowledge that determining ethnicity is more challenging than figuring out gender and age range. Prandoni provided The Associated Press a limited version of Quividi's software, which uses an ordinary webcam to stream video to a computer. The trial version tracked gender only, using color-coded circles to distinguish male and female faces. The sample size was too small to be statistically significant, but it was accurate about 80 to 90 percent of the time. That might be as precise as the systems ever get, said Deborah Mitchell, a professor of consumer psychology at the University of Wisconsin-Madison. Even the human brain can't always determine gender, age or ethnicity. Still, "even if it gets to 70 percent accuracy, that's still giving you a wealth of information," said Mitchell, who teaches in the Wisconsin School of Business. That information is certainly valuable to Bill Ketcham, the chief marketing officer of Adspace Networks Inc. His New York company sells video advertising on 1,400 video screens at 105 malls around the nation. Adspace is testing six TruMedia systems at malls in Winston-Salem, N.C., Pittsburgh and St. Louis. The kiosks display a daily list of top 10 sales at the mall, as well as paid advertising that comes largely from movie studios and TV networks. A 15-second video ad that replays across Adspace's national network can cost as much as $765,000 per month. So advertisers expect rigorous information about who sees the spots — information that face tracking can now provide, Ketcham said. For now, at least, Adspace isn't changing the ads based on who's watching — Ketcham said the kiosks' audiences are so large that it wouldn't be practical to personalize ads to individuals. While advertisers like the face-tracking technology, another privacy advocate, Harley Geiger, questions whether it should be used on consumers without their knowledge. Geiger, staff counsel for the Center for Democracy & Technology in Washington, D.C., said advertisers should be telling consumers what details about them are being collected and for what purpose. "With the technology proliferating, now or the short-term is the time to consider privacy protections," he said. "If you don't build it in at an early stage it becomes very difficult to build it into an already established system." http://tech.yahoo.com/news/ap/200901...e/tec_nosy_ads  AdSweep Blocks Ads in Google Chrome and Opera Kevin Purdy AdSweep is a user script that blocks a good number of ads on some major websites, and works from a simple file you plug into your Opera or Google Chrome files. The instructions for installing the single AdSweep.user.js file in your Opera or Chrome browser are laid out step-by-step on AdSweep's main page. Opera users have a mostly graphical process, while Chrome users will have to check their version and then make a few tweaks to enable user scripts. The site notes that AdSweep will work for Firefox as well, along with Safari and Internet Explorer with some third-party add-ons, but each of those platforms has their own ad-blocking solutions, like Firefox's uber-popular Adblock Plus. Chrome users can also use a proxy solution like the previously detailed Privoxy to get annoying ads out of their way. We have to say it—the site you're reading right now is, of course, supported by advertising, and we'd ask that you keep them displayed if you dig what we do here. But AdSweep is pretty easily tweaked with, since it's just one file, and can be used for blocking of extremely annoying ads. It's a free download, works where Opera and Chrome can install. http://lifehacker.com/5140947/adswee...rome-and-opera  Coming Soon: Full-Disk Encryption for all Computer Drives Drive makers settle on a single encryption standard Lucas Mearian The world's six largest computer drive makers today published the final specifications(download PDF) for a single, full-disk encryption standard that can be used across all hard disk drives, solid state drives (SSD) and encryption key management applications. Once enabled, any disk that uses the specification will be locked without a password -- and the password will be needed even before a computer boots. The three The Trusted Computing Group (TCG) specifications cover storage devices in consumer laptops and desktop computers as well as enterprise-class drives used in servers and disk storage arrays. "This represents interoperability commitments from every disk drive maker on the planet," said Robert Thibadeau, chief technologist at Seagate Technology and chairman of the TCG. "We're protecting data at rest. When a USB drive is unplugged, or when a laptop is powered down, or when an administrator pulls a drive from a server, it can't be brought back up and read without first giving a cryptographically-strong password. If you don't have that, it's a brick. You can't even sell it on eBay." By using a single, full-disk encryption specification, all drive manufacturers can bake security into their products' firmware, lowering the cost of production and increasing the efficiency of the security technology. For enterprises rolling out security across PCs, laptops and servers, standardized hardware encryption translates into minimum security configuration at installation, along with higher performance with low overhead. The specifications enable support for strong access control and, once set at the management level, the encryption cannot be turned off by end-users. Whenever an operating system or application writes data to a self-encrypting drive, there is no bottleneck created by software, which would have to interrupt the I/O stream and convert the data "so there's no slowdown," Thibadeau said. "Also, the encryption machinery uses no power. When it reads data from the drive, it displays it to the user in the clear. It's completely transparent to the user," he said. The TCG includes Fujitsu, Hitachi GST, Seagate Technology, Samsung, Toshiba, Western Digital, Wave Systems, LSI Corp., ULink Technology and IBM. Related Blog: Michael Horowitz: Hard disk passwords offer great security for free "In five years time, you can imagine any drive coming off the production line will be encrypted, and there will be virtually no cost for it," said Jon Oltsik, an analyst at Enterprise Strategy Group. Here are the three specifications: • The Opal specification, which outlines minimum requirements for storage devices used in PCs and laptops. • The Enterprise Security Subsystem Class Specification, which is aimed at drives in data centers and high-volume applications, where typically there is a minimum security configuration at installation. • The Storage Interface Interactions Specification, which specifies how the TCG's existing Storage Core Specification and the other specifications interact with other standards for storage interfaces and connections. For example, the specification supports a number of transports, including ATA parallel and serial, SCSI SAS, Fibre Channel and ATAPI. Several of the drive manufacturers, including Seagate, Fujitsu and Hitachi, already support the standard on some of their drives. Hitachi, for instance, is shipping its internal Travelstar 5K500.B laptop drives with full-disk encryption. Several encryption management software vendors, including Wave Systems, WinMagic Inc. and CryptoMill Technologies, have also announced product certification for the standard. Brian Berger, a marketing manager with Wave Systems and chair of the TCG marketing work group, said the specifications call for the use of Advanced Encryption Standard (AES). Vendors are free to choose either AES 128-bit or AES 256-bit keys depending on the level of security they want. Neither have been broken. "Things like key manageability and patch management become things of the past," he said. "You don't have to worry about what version of encryption software is running or what [encryption appliance] your system's plugged into. When encrypted drives are under management, users can't turn off encryption, so there's no chance of users losing machines with valuable data on them after having turned off encryption." The effort to create the encryption specifications, which began six years ago, focused on full-disk encryption, which protects data on a computer by encrypting all of the information on the computer's hard drive regardless of what partition it's on. In order to gain access to the information, users would first have to supply a password, which, in turn, would be used to unlock a key used to decrypt the data. "You can use these [enabled] drives to childproof your laptop because it operates outside of Windows. Windows hasn't even booted yet. Your kid can't crack it unless [he] has the password. You can leave the laptop at home and rest assured a 14-year-old can't get on it," Thibadeau said. IT departments will also be able to repurpose drives using the encryption standard by cryptographically erasing them with a few keystrokes. Cryptographic erasure changes the cryptographic key, thus making data permanently inaccessible. "The specific way in which encryption is done inside the drive doesn't matter for interoperability," said Jorge Campello, senior manager of architecture and electronics at Hitachi. "What matters is how they drives are configured and how access control is configured. So any drive, in conforming to these standards, will have the same interface commands." http://www.computerworld.com/action/...&intsrc=kc_top  Western Digital 2TB Caviar Green Drive Preview Dave Altavilla Late last week Western Digital briefed us on their forthcoming release of a new addition to their Caviar Green family of hard drives. No we're not talking some sort of exotic sushi or cracker-bound fish egg here either but rather a new, rather humongous and environmentally more friendly hard drive from WD, that can be considered an "industry first". Today marks the day that standard rotational media breaks the 2TB barrier. Let's spell that out a bit more clearly again here; T-W-O full Terabytes of SATA-based storage on a single, standard 3.5" hard drive. Those of you on the consumer side of the market, hording gigs of music, movies, pictures and other media just got a bunch more breathing room to play with. And those of you in the enterprise space now have a new option to consider with respect to bulk, low-cost, power-efficient storage. Perhaps that rack just got a little smaller or the need to cool it a little less? Today Western Digital is announcing their WD20WEADS drive, otherwise known as the WD Caviar Green 2.0TB. With 32MB of onboard cache and special power management algorithms that balance spindle speed and transfer rates, the WD Caviar Green 2TB claims a top rung spot on the density-per-square-inch and power-efficiency ladders. We've had an engineering sample here in house for a few days and have done some preliminary testing on it. We'll be offering a full performance evaluation with the final revision of this new drive in the coming weeks but we have a sneak peek for you here. Let's start with the specifications and then we'll take a closer look at the vital signs. Specs: • Capacity: 2TB (400Gb/sq.in. areal density) • 32MB cache buffer • Variable spindle speed • 3.5-inch form-factor • 500GB/platter, 4-platter design • 3Gb/sec SATA with NCQ • SATA power connector only • PMR head technology • RoHS compliant Though our test system and the OS sees the drive as 1.81TB, as you can see here, there are over 2 trillion bytes of available capacity on this new, freshly formatted hard drive, with 147MB used just for the file system alone. Below are some quick and dirty performance numbers with HD Tach and SANDRA. We should underscore that we're testing a pre-release engineering sample here, so performance figures could scale higher as firmware revision are made to the product. A quick glance at the numbers here show this new big-boy Caviar Green drive from WD offering more than competitive performance versus the likes of Samsung's Spinpoint F1 and Seagate's Barracuda 7200.11 -- both 7200RPM-based products. HD Tach shows an average read speed of 90MB/s and average writes at 80MB/s. We'll be digging into performance metrics with other tools like IOMeter in the days ahead but this early view certainly looks good for a disk with this sort of capacity. We'll be looking at power as well but WD claims this drive drops in somewhere around 7 Watts under read/write load and 5 Watts at idle. With the ever-increasing demand for bulk storage, this new WD drive offers a smaller carbon footprint as well, with a full 2TB available in a single 3.5" drive. MSRP for the new ginormous Caviar is set at $299. You can catch the official press release from WD, here. Stay tuned for the full HH monty with WD's new big-bad Caviar, coming soon. http://hothardware.com/News/WD-2TB-C...Drive-Preview/  Mozilla Contributes $100,000 to Fund Ogg Development Mozilla has donated $100,000 to help fund a collaborative initiative with the Wikimedia Foundation to improve open standards-based technology for video on the web. Ryan Paul Open Web standards have evolved considerably over the years and browser compatibility is better than ever, but one important area where standards are just starting to catch up is support for streaming video. Proprietary browser plugins are used extensively across the web to play video from popular sites. This creates serious lock-in risk and gives proprietary software vendors like Adobe a lot of control over the medium. Although alternatives such as Microsoft's Silverlight are beginning to change the game and force Adobe to open up, there still isn't a viable, vendor-neutral, standards-based alternative that can shift the balance of power over to end-users and tear down some of the walls that limit how video content is experienced on the Web. Mozilla and the Wikimedia Foundation have launched an initiative to help improve the quality of open, standards-based video technology. Mozilla has given the Wikimedia Foundation a $100,000 grant intended to fund development of the Ogg container format and the Theora and Vorbis media codecs. These open media codecs are thought to be unencumbered by software patents, which means that they can be freely implemented and used without having to pay royalties or licensing fees to patent holders. This differentiates Ogg Theora from many other formats that are widely used today. The Ogg development improvements will be coordinated by the Wikimedia Foundation. The organization uses Ogg for virtually all of its rich media, which makes it one of the largest open media format adopters on the Internet. In a statement published at the organization's Web site, Wikimedia deputy director Erik Möller expressed his support for the initiative and explained that open formats are needed to ensure the availability of free content in unrestricted formats. "Open standards for audio and video are important because they can be used by anyone for any purpose without royalties, and can be inspected and improved by an open community. Today, video and audio on the web are dominated by proprietary technologies, most frequently patent-encumbered codecs wrapped into closed-source player widgets," Möller writes. "Wikimedia and Mozilla want to help to build a web where video and audio are first class citizens: easy to use and manipulate by anyone, without compulsory royalty schemes or other barriers to participation." Mozilla is integrating support for the Ogg format directly into Firefox 3.1, so the next version of the popular open source web browser will be able to play Ogg media without requiring any plugins or external software. The Ogg format will be supported through Firefox's implementation of the HTML 5 video element, which allows video to be seamlessly interwoven with conventional HTML content and manipulated through the DOM. Mozilla has recently demonstrated the video element feature being used for streaming video. Opera is also integrating standards-based video support into its browser and has a working implementation of Ogg for HTML 5. Although the technology is starting to fall into place, it will take time for the standard to be supported broadly enough to encourage adoption by sites that stream rich media. The lack of DRM support inherent in the open implementation will also likely impede adoption by major commercial content creators. Standards-based solutions may never manage to displace Flash, but the first big steps need to be taken for this to even be a possibility. http://arstechnica.com/open-source/n...evelopment.ars  The Best E-Mail Program Ever How Gmail destroyed Outlook. Farhad Manjoo As of this week, Gmail has reached perfection: You no longer have to be online to read or write messages. Desktop programs like Microsoft Outlook have always been able to access your old mail. There is a certain bliss to this; if you've got a pile of letters that demand well-composed, delicate responses (say you're explaining to your boss why you ordered that $85,000 rug), unplugging the Internet can be the fastest way to get things done. That's why offline access is a killer feature—it destroys your last remaining reason for suffering through a desktop e-mail program. Google's not alone in providing this option. Microsoft's Windows Live Mail, Yahoo's Zimbra, and the mail app made by the Web startup Zoho, among other services, also provide some measure of untethered e-mail access. For now, Google calls this addition "experimental"—you've got to turn it on explicitly, and the company is asking users to report any bugs—but I found it easy to set up and a delight to use. To get offline access, you first need to download and install a small program called Google Gears (except if you're using Google's Chrome browser, which comes with Gears built in). Then, after you enable Gmail's offline capability, the system will download two months of your most recent messages, which should take 30 minutes to an hour. Now you're good to go: When you're offline, type www.gmail.com into your browser, log in—yes, Gears enables you to log in even when you don't have a Web connection—and there's your e-mail. Though I work from home and rarely find myself away from a hot Wi-Fi connection, I shut off my router and parked myself on my couch for about an hour yesterday. I loaded up Gmail on my laptop, and it responded seamlessly—I could read, search through, and respond to any message I'd received during the last two months, all through the familiar Web interface. Eureka! I'll never again be mailless on a plane, a subway, or anyplace else where you don't have the Web but do have a lot of time to kill. Now that Gmail has bested the Outlooks of the world, it's a good time to assess the state of desktop software. There are some things that work better on your computer (your music app, your photo editor, your spreadsheets), and there are some that work better online (everything else). Over the last few years, we've seen many programs shifting from the first category to the second—now you can get spreadsheets and photo editors online, though they're still not as good as programs hosted on your computer. But e-mail has crossed the line completely. Hosted services like Gmail are now the most powerful and convenient way to grapple with a daily onslaught of mail. If you're still tied to a desktop app—whether Outlook, the Mac's Mail program, or anything else that sees your local hard drive, rather than a Web server, as its brain—then you're doing it wrong. The shift has been a long time coming. On July 4, 1996, Sabeer Bhatia and Jack Smith, two techies who met while working at Apple, launched Hotmail, the first free e-mail service on the Web. The date wasn't accidental—from the beginning, Web-based e-mail sought to liberate people from the strictures imposed by traditional providers (ISPs, universities, and employers, all of whom required some official affiliation before they gave you an e-mail address). Hotmail would give an inbox to anyone—you could even sign up for multiple addresses—and pretty soon it was impossible to find a soul who didn't e-mail. But it was a terrible hassle to actually use Hotmail—which Microsoft purchased in 1997—or the rival e-mail systems built by Yahoo, AOL, and the various other Web portals that dominated the last tech boom. Back then, Web-based e-mail was a great idea executed poorly. Internet connections, Web browsers, and Web-design technologies were slow and flaky; you waited an eternity to load up a message, you could easily lose a draft of a long e-mail if something went amiss with your modem, and you had a limited amount of storage space. Web e-mail was a redoubt of amateurs. If you were serious about your inbox, you kept it on your desktop. Desktop e-mail presented its own challenges, though. People who were serious about e-mail tended to archive all their messages. But desktop e-mail apps performed poorly when overloaded with mail; Outlook, for instance, crawled to halt if you stuffed it with just a few tens of thousands of messages, which for some people is only a few months' worth. What's more, keeping all your mail in one place was both annoying and not very safe. You couldn't easily check your messages on multiple computers. And what if you wanted to switch to a new computer? Or what if a power surge crashed your drive? As a journalist working during the Internet bust, my particular worry was getting a pink slip. If my boss suddenly asked me to turn in my company-provided laptop, all my e-mail—both professional and personal correspondence going back years—would be gone. By the time Gmail launched in summer 2004, I was desperate for an alternative to Outlook. (I had tried pretty much every other desktop e-mail app.) From the moment I logged on, I found it liberating. Gmail's interface was quick and intuitive, unlike any other major online service at the time. (Gmail did borrow some design ideas from Oddpost, an ahead-of-its-time Web e-mail app developed in 2002; Yahoo bought Oddpost in 2004.) Gmail was the first to display multiple messages on the same subject as threaded conversations—a design idea that user-interface experts had long been saying would make e-mail easier to use. Switching to Gmail also freed me from worrying about how I preserved my mail—Google, whose servers are much more secure than my own computer, was taking care of backups for me. What separates Gmail from its rivals is a basic design philosophy: It's built for power e-mailers. Late last year I visited the Gmail team at Google's Mountain View, Calif., headquarters. Keith Coleman, Gmail's program manager, told me that from the beginning, Google aimed to build something suitable for people who got a ton of mail—because in the future, everyone will get a ton of mail. Gmail's main features are all catnip for folks who find themselves buried under the weight of their inbox. There's a search engine worthy of the Google name, a slate of keyboard shortcuts that make organizing your messages brutally efficient, and a crowdsourced spam detector that keeps out unwanted messages. Best of all, Gmail is fast—you can switch between messages and folders quicker than you can in any other e-mail program, even desktop-based systems. Coleman told me that the team is constantly measuring and tweaking the responsiveness of its interface. (The software gives coders a readout of how long, on average, various tasks take to complete.) The Gmail managers are also gaga over user-interface tests: Before instituting any major feature, developers bring users into a whiz-bang lab outfitted with cameras and eye-tracking software to see how people react to the new stuff. Lately Coleman and his staff have been improving Gmail at a breakneck pace. They added a way to let people chat by voice and video, and they put out "themes" that personalize the appearance of your e-mail screen. Last summer, they launched Gmail Labs, a repository of add-on programs that run alongside Gmail. Offline access is one of these many Labs features; you can also add a to-do list, buttons to send people quick canned responses, a mini-program for sending text messages to cell phones, and a "gadget" for monitoring your Google Calendar and Google Docs from your e-mail. All these add-ons were created by Google programmers, but Coleman says that Gmail is also experimenting with letting outside developers add stuff. Google seems to be trying to create more than just a great e-mail program; with all these add-ons, Gmail is becoming a sort of e-mail platform whose users benefit from the best ideas in mail management. And that gets to what's so exciting about being a Gmail user right now. The app keeps getting better. You might say that's true of desktop systems, too; Outlook is not as clunky as it was five years ago, and, no doubt, it'll be better five years from now. But so will Gmail—and because it's online, you'll get those improvements faster, and without having to install any software. Now that you can use Gmail anywhere—even when you're beyond the reach of broadband—there's no longer any reason to suffer. http://www.slate.com/id/2210090/?from=rss  Spam Rises 150 Per Cent in Two Months Murad Ahmed THE number of junk emails being sent to computer users around the world has risen more than 150 per cent in two months, as spammers fight back against efforts to shut them down. In November, the level of spam junk emails fell dramatically after the plug was pulled on McColo, an American company accused of providing the gateway for much of the world’s junk emails. But, in just a few weeks, the world’s biggest junk-email gangs appear to have regrouped, as spam emails have now almost recovered to the same levels as before McColo was shut down. According to data compiled by Google, computer users can expect to receive more unsolicited emails this year than ever before. Spam or junk emails are unsolicited messages sent in bulk. Most are advertisements for dubious products and fake get-rich-quick schemes. Google’s analysis of spamming activity showed that the average PC user that was not protected with adequate anti-virus software would have received 45,000 spam messages in 2008, up from 36,000 from the previous years. The research showed that on the day that saw the highest volume of spam last year, in April, some users were receiving an average of 100 emails every minute. The company said that all indicators suggest that the problem will continue to get worse as spam attacks become "more frequent and more ingenious". In November, McColo was taken offline in what was seen at the time as a significant victory against junk emailers. Security researchers accumulated evidence of alleged spamming activities at McColo, and persuaded its internet providers to get the web-hosting service to be taken down. This apparently left junk email gangs scrambling to find new ways to send their messages, but as Spam surges once again, it looks as though junk-emailers are up-and-running once more. It is notoriously difficult to target and shut down sources of spam. Investigators have to prove that company officials know that crimes are being committed through their servers. web-hosting companies often argue that they do not monitor how customers use their services. In the case of McColo, it appears that spam senders used the company’s servers to send commands to huge numbers of computers that they had in effect hijacked. Spammers use networks of these compromised computers -- known as "botnets" -- to amass enough computing power to send millions of messages a day. The vast majority of owners of those machines do not know their computers are secretly being used for this purpose. But spammers need a way to communicate with these computers plus a web-hosting company willing to look the other way. http://www.australianit.news.com.au/...013044,00.html  Kyrgyzstan Knocked Offline Christopher Rhoads A Russian "cyber-militia" has effectively knocked the central Asian republic of Kyrgyzstan offline in recent days, according to an Internet security expert, in the latest apparent example of geopolitical tensions playing out on the Web. Since Jan. 18, the country of 5.3 million has come under a massive cyber-attack, according to Don Jackson, director of threat intelligence at Atlanta Internet security firm SecureWorks Inc. The denial-of-service attack -- which swamps Web sites with so many hits that they are forced to shut down -- has targeted the two main Internet service providers in the country, which account for more than 80% of Kyrgyzstan's bandwidth, according to Mr. Jackson. The episode has shut down Web sites and made emailing impossible, he said. "We are concerned about this in terms of our own readiness and preparedness," said Mr. Jackson. Less than 20% of the Kyrgyz population is online; such an attack would have a bigger impact on the economy of a place like the U.S., with nearly 75% of the country online, according to internetworldstats.com. A spokesman at the Russian embassy in Washington couldn't be reached for comment. The Kyrgyz government couldn't be reached for comment. U.S. officials couldn't immediately be reached for comment. Theories for the reason behind the current attack in Kyrgyzstan center on the U.S. use of an air base in the country to help with its military operations in Afghanistan. Another theory is that the attack was directed at the fledgling Kyrgyz opposition movement, which has used the Internet to express its discontent. http://online.wsj.com/article/SB123310906904622741.html  U.S. Claims Victory in WTO Complaint on China Piracy Doug Palmer The United States claimed victory on Monday in a groundbreaking World Trade Organization case against China for failing to protect and enforce copyrights and trademarks on a wide range of goods. "Today, a WTO panel found that a number of deficiencies in China's IPR (Intellectual Property Rights) regime are incompatible with its WTO obligations," acting U.S. Trade Representative Peter Allgeier said in a statement. "We will engage vigorously with China on appropriate corrective actions to ensure that U.S. rights holders obtain the benefits of this decision." Washington launched the dispute in 2007 out of frustration at rip-offs of films, branded goods and other trademarked property openly available in Chinese cities. The International Intellectual Property Alliance, a coalition of U.S. music, movie, book and software industry groups, conservatively estimates that piracy in China costs them more than $3.7 billion in lost sales. The WTO ruling means China and other nations "can't simply go through the motions" of protecting intellectual property, but must provide effective results, Neil Turkewitiz, an executive vice president at the Recording Industry Association of America, said in a statement. The United States persuaded the dispute settlement panel that China violated WTO rules by barring copyright protection for movies, music and books that have not been approved by state censors for legitimate sale, Allgeier said. "China restricts access to many legitimate titles, but that doesn't stop the pirated distribution of virtually all U.S. films in China," Dan Glickman, president of the Motion Picture Association of America, said in a statement. The panel also said it was "impermissible" for China to allow public auction of counterfeit goods seized by Chinese customs authorities, with only the requirement that the fake brand or trademark be removed from the good, Allgeier said. The United States failed to persuade the WTO panel on one main point of its case: that Chinese copyright pirates and counterfeiters have no fear of criminal prosecution because the government's threshold for bringing a case is too high. That was "disappointing," but the panel established a market-based analytical approach that should help WTO members avoid or resolve future disputes over obstacles to criminal enforcement of counterfeiting and piracy, Allgeier said. The U.S. recording industry also welcomed the ruling "that enforcement must be effective not only in law but in practice, and that standards of effectiveness change over time and reflect the realities of the marketplace," Turkewitz said. Both the United States and China can appeal the panel ruling, the results of which leaked when a confidential preliminary report was released in October. (Editing by Sandra Maler and Cynthia Osterman) http://www.washingtonpost.com/wp-dyn...012601954.html  Government Delays UK Net Report BBC Communications Minister Lord Carter was expected to publish interim findings on the UK's digital economy on 24 January. But a spokeswoman for the Department of Culture, Media and Sport said the report would now appear "before the end of the month". The Digital Britain report examines a range of issues affecting internet users such as security and and safety and "promoting content standards". The full report and action plan will be unveiled in late spring 2009. In the run-up to the interim report being revealed Culture Secretary Andy Burnham said the government was looking at regulating the internet to "even up" the imbalance with television. The report is examining a number of different areas, including broadband development, public service broadcasting and digital radio. It is thought the report may set minimum broadband speeds and impose obligations on telecom suppliers to provide universal coverage. Currently, communication providers are only enjoined to provide a functional internet connection that can run at a minimum speed of 28.8 kilobits per second. The report is also expected to examine illegal file-sharing of movies, music and TV and appraise ways of tackling it. Digital divide Speaking before a House of Commons' committee last month, Lord Carter outlined the government's commitment to providing broadband for all. "We do not yet get universal coverage and in my view we should have it," he said. In late September 2008, the EU said it was considering bringing forward its review of the basic telecoms services that European citizens should expect. The report is also expected to show that the digital divide is no longer a geographical issue with towns connected and rural areas cut off. Instead areas of digital exclusion are likely to mirror those of social deprivation. However, broadband experts have warned that any moves to create next generation networks that run at very high speeds may only serve to deepen the digital divides in the UK. http://news.bbc.co.uk/2/hi/technology/7848028.stm  Take Bacon. Add Sausage. Blog. Damon Darlin FOR a nation seeking unity, a recipe has swept the Internet that seems to unite conservatives and liberals, gun owners and foodies, carnivores and ... well, not vegetarians and health fanatics. Certainly not the vegetarians and health fanatics. This recipe is the Bacon Explosion, modestly called by its inventors “the BBQ Sausage Recipe of all Recipes.” The instructions for constructing this massive torpedo-shaped amalgamation of two pounds of bacon woven through and around two pounds of sausage and slathered in barbecue sauce first appeared last month on the Web site of a team of Kansas City competition barbecuers. They say a diverse collection of well over 16,000 Web sites have linked to the recipe, celebrating, or sometimes scolding, its excessiveness. A fresh audience could be ready to discover it on Super Bowl Sunday. Where once homegrown recipes were disseminated in Ann Landers columns or Junior League cookbooks, new media have changed — and greatly accelerated — the path to popularity. Few recipes have cruised down this path as fast or as far as the Bacon Explosion, and this turns out to be no accident. One of its inventors works as an Internet marketer, and had a sophisticated understanding of how the latest tools of promotion could be applied to a four-pound roll of pork. The Bacon Explosion was born shortly before Christmas in Roeland Park, Kan., in Jason Day’s kitchen. He and Aaron Chronister, who anchor a barbecue team called Burnt Finger BBQ, were discussing a challenge from a bacon lover they received on their Twitter text-messaging service: What could the barbecuers do with bacon? At the same time, Mr. Chronister wanted to get attention for their Web site, BBQAddicts.com. More traffic would bring in more advertising income, which they needed to fund a hobby that can cost thousands of dollars. Mr. Day, a systems administrator who has been barbecuing since college, suggested doing something with a pile of sausage. “It’s a variation of what’s called a fattie in the barbecue community,” Mr. Day said. “But we took it to the extreme.” He bought about $20 worth of bacon and Italian sausage from a local meat market. As it lay on the counter, he thought of weaving strips of raw bacon into a mat. The two spackled the bacon mat with a layer of sausage, covered that with a crunchy layer of cooked bacon, and rolled it up tight. They then stuck the roll — containing at least 5,000 calories and 500 grams of fat — in the Good-One Open Range backyard smoker that they use for practice. (In competitions, they use a custom-built smoker designed by the third member of the team, Bryant Gish, who was not present at the creation of the Bacon Explosion.) Mr. Day said his wife laughed the whole time. “She’s very supportive of my hobby,” he said. The two men posted their adventure on their Web site two days before Christmas. On Christmas Day, traffic on the site spiked to more than 27,000 visitors. Mr. Chronister explained that the Bacon Explosion “got so much traction on the Web because it seems so over the top.” But Mr. Chronister, an Internet marketer from Kansas City, Mo., did what he could to help it along. He first used Twitter to send short text messages about the recipe to his 1,200 Twitter followers, many of them fellow Internet marketers with extensive social networks. He also posted links on social networking sites. “I used a lot of my connections to get it out there and to push it,” he said. The Bacon Explosion posting has since been viewed about 390,000 times. It first found a following among barbecue fans, but quickly spread to sites run by outdoor enthusiasts, off-roaders and hunters. (Several proposed venison-sausage versions.) It also got mentions on the Web site of Air America, the liberal radio network, and National Review, the conservative magazine. Jonah Goldberg at NationalReview.com wrote, “There must be a reason one reader after another sends me this every couple hours.” Conservatives4palin.com linked, too. So did regular people. A man from Wooster, Ohio, wrote that friends had served it at a bon voyage party before his 10-day trip to Israel, where he expected bacon to be in short supply. “It wasn’t planned as a send-off for me to Israel, but with all of the pork involved it sure seemed like it,” he wrote. About 30 people sent in pictures of their Explosions. One sent a video of the log catching fire on a grill. Mr. Day said that whether it is cooked in an oven or in a smoker, the rendered fat from the bacon keeps the sausage juicy. But in the smoker, he said, the smoke heightens the flavor of the meats. Nick Pummell, a barbecue hobbyist in Las Vegas, learned of the recipe from Mr. Chronister’s Twittering. He made his first Explosion on Christmas Day, when he and a group of friends also had a more traditional turkey. “This was kind of the dessert part,” he said. “You need to call 911 after you are done. It was awesome.” Mr. Chronister said the main propellant behind the Bacon Explosion’s spread was a Web service called StumbleUpon, which steers Web users toward content they are likely to find interesting. Readers tell the service about their professional interests or hobbies, and it serves up sites to match them. More than 7 million people worldwide use the service in an attempt to duplicate serendipity, the company says. Mr. Chronister intended to send the post to StumbleUpon, but one of his readers beat him to it. It appeared on the front page of StumbleUpon for three days, which further increased traffic. Mr. Chronister also littered his site with icons for Digg, Del.icio.us and other sites in which readers vote on posts or Web pages they like, helping to spread the word. “Alright this is going on Digg,” a commenter wrote minutes after the Explosion was posted. “Already there,” someone else answered. Some have claimed that the Bacon Explosion is derivative. A writer known as the Headless Blogger posted a similar roll of sausage and bacon in mid-December. Mr. Chronister and Mr. Day do not claim to have invented the concept. But they do vigorously defend their method. When one commenter dared to suggest that the two hours in the smoker could be slashed to a mere 30 minutes if the roll was first cooked in a microwave oven, Mr. Chronister snapped back. “Microwave??? Seriously? First, the proteins in the meats will bind around 140 degrees, so putting it on the smoker after that is pointless as it won’t absorb any smoke flavor,” he responded on his site. “This requires patience and some attention. It’s not McDonald’s.” http://www.nytimes.com/2009/01/28/dining/28bacon.html  Open Source Question for Schools Andrew Miller asks whether open source software can help schools use their budgets more efficiently Looking around the British Education Training and Technology show, BETT 2009, it was clear by the sheer size of the event, that an awful lot of money is being spent on technology in education. With Open Source Software (OSS) freely available, covering almost every requirement in the national curriculum, a question has to be asked why schools do not back it more fully, possibly saving millions of pounds. As the name suggests, OSS is community-driven software with its source code open to all. Anyone can modify the software according to their needs and then share these modifications with everyone else. When many people hear OSS they think Linux - the alternative operating system that comes in many flavours such as Ubuntu, openSUSE or Fedora. Linux has long been used to power servers, but open source extends to all manner of projects. Web browser Firefox and the OpenOffice software suite are great examples of this. Open promotion In the education sector, OSS is promoted and used by only a handful of self-motivated technologists looking to stretch their technology budget. Critics say Becta - the government agency that oversees the procurement of all technology for schools - has not done enough to promote OSS. Peter Hughes, head of procurement agreements at Becta, told the BBC that more would be done. "As an organisation, we have been criticised for not adequately covering open source solutions and our predominance of proprietary solutions, such as those by Microsoft. "We have therefore responded to this pressure and in our role of strategy and delivery of technology in education, we've made an effort to stay balanced and have focused on facilitating effective choice for schools," he said. At the end of 2008 Becta collaborated with the government's procurement services organisation OGCbuying.solutions to approve 12 suppliers, all of which can outfit schools with open source software. Becta considers the appointment of Sirius a "major step forward" and that it sent a message to the community that "we're taking OSS seriously". John Spencer, Sirius head of business development, told the BBC that there was a deep ignorance of open source, not just in schools, and that Linux suffered an image problem. "Many schools are frozen in time from the year 2000, when it became obvious computer literacy was not going to be optional but then they haven't moved on. "They don't want to move away from what they know, not just to Linux but equally to Vista and Office 2007 as well. Good teachers will always be looking to move forward but they are so busy that they are often conservative," said Mr Spencer. Sirius has already installed open software in many schools around the UK. One project in a Twickenham school allows netbooks and notebooks owned by the school or a pupil to be booted up across the network to give them access to the files and programs they need. "The network cost half that of the RM offers and the reduction in power consumption allows the system to pay for itself in under 3 years," said Mr Spencer. Competiton time Another Becta initiative revolves around the opensourceschools.org.uk website which launched in late 2008. It aims to provide basic information and best practice guidelines for teachers using OSS. However, Becta has some reservations. "We want teachers to realise that they can be and should be considering OSS as a viable alternative," said Mr Hughes. "That said, schools still need to do their homework. There can be just as many caveats with open source as there are with proprietary solutions." So what do the big software firms think about open source software encroaching on their patch? Steve Beswick, director of education for Microsoft UK, told the BBC that while open source software may, on face value, offer savings, there could be hidden costs, both financial and otherwise. "A lot of people are trained in Microsoft-based technologies, so there may be increased costs in re-training to learn how to use open source solutions," he said. Mr Beswick claimed that Microsoft was not against open source, and was "committed to interoperability" illustrated, he said, by the support for the Open Document Format in Service Pack 2 of Office 2007. He also mentioned the work Microsoft has done getting IIS, its flagship web server software, to work with the PHP web scripting language. The Schools Minister, Jim Knight, echoed Becta's view. In a statement, he said: "Schools and colleges must be able to make an informed choice about the software they need - be it open source or proprietary - and to be aware of the total cost of ownership of that software, including sustainable support and training. "I see it as Becta's role to work with open source and proprietary software providers to ensure that schools and colleges can make the most effective use of that software to support teaching and learning." So what does the open source community make of this? Gerry Gavigan, the chairman of the Open Source Consortium, told the BBC that a shift to open source software would require a change in thinking. "Ongoing training costs don't go away merely because of a change from proprietary software to free and open source software. "What does change is liberation from the training costs associated with an externally encouraged or enforced upgrade cycle," he said. Another issue frequently raised is that of technology lock-in, one of the biggest arguments used by open source advocates as to why Windows is still prevalent. "Something that isn't always taken into account when calculating software procurement costs, is the ongoing costs costs arising from licensing or technology lock-in," said Mr Gavigan Mr Gavigan felt that the free nature of open source software sometimes worked against it. "Announcing you have spent amazing sums of money trying to tackle a problem has more impact with your audience than saying you have used a free solution. There is an unfortunate myth that if it doesn't cost anything, it isn't worth anything" he said. Web world However, some schools are taking on OSS. Highworth Grammar School, in Ashford, is offering both licensed and open source software to students. The school's network manager, Marc Blake, said that while it was important for pupils to be aware of alternatives to Windows, it was worth acknowledging that pupils live in a world dominated by Microsoft. But, he told the BBC, significant savings could be made by using some open source alternatives. "We offer both Office 2003 and OpenOffice, so that people have a choice. I'd estimate 98% of people choose Microsoft Office over OpenOffice, but at least that choice is there," said Mr Blake. "For our school to upgrade to Office 2007, it will cost around £27,000 as a one-off cost, but that doesn't include the cost of re-training and updating all the associated worksheets and teaching material." "To get the equivalent of Moodle [a free source of e-learning software] for our 1200 students would have cost in excess of £3,000 per year. You don't get the professional support, but if you're willing to take that on, it's great money saving," he added. One of Mr Blake's main concerns with moving to Linux was whether it would work with some of the newer web technologies. However, although the school does have several Linux-based Asus EeePCs which are used predominantly for Web 2.0 projects. At this years BETT, a significant proportion of educational software went Web 2.0, in an attempt to stay cross-platform compatible. Schools could make significant savings by using open source, but this also requires a significant investment of time, research and training. But using a combination of both commercial and open source, such as that employed by Highworth School, can help to reduce costs while still giving students a choice. That's got to be good news for any school's report card. http://news.bbc.co.uk/go/pr/fr/-/2/h...gy/7847377.stm  Teachers Need An Open Source Education Matt Hartley Remember back in 2008 when a teacher named "Karen" made a remark about using Linux holding her students back? The idea apparently being that students using Linux must somehow be participating in something that is illegal. Later, apologies ensued despite new wounds on both sides of the issue being created. Seems to me that this is not just individuals in the proprietary software realm who have no idea how open source software works. Apparently the group of misinformation junkies now includes teachers as well. Free as in freedom, not as in free lunch Even with the recent growth in adoption with open source software on proprietary platforms, there are still countless people in places of authority who have no idea that there is such as thing as free/open source software (FOSS). And to be completely fair, it is easy to see how a teacher might become confused when they are surrounded by mainstream media talking heads that spend more time trumpeting the threat of "software piracy" than their FOSS alternatives. Even "freeware" can be passed out illegally as it often contains a license statement that generally indicates its creators must give express permission for the created works to be passed around freely. So you might then understand how an uninformed teacher might be in a good position to jump to sudden conclusions when one of their students is passing around a disc containing "unknown software" on it to their peers. In reality, these same students are utilizing their freedom of choice to select legal alternatives to proprietary software. This translates into completely circumventing pirated software altogether. This software, licensed with one of the various open source licenses, is permitted to be passed around to a student's peers for casual use. Nothing nefarious is taking place in allowing this to happen. Unfortunately, most teachers today are totally unaware of this. What makes this entire teacher/student confusion even worse is that there is heavy speculation that people who work within the IT sector for the same school districts as the misinformed teachers, are doing their part to encourage this type of behavior to travel even further than mere software sharing. IT Professionals that need to be "taken to school" Try to suggest to a Linux user that they should try and remove Linux from their PC, that Linux user is going to likely laugh at you. Yet apparently, there have been reports that this is actually taking place. The problem is that Linux users themselves are seen as a rogue element in a world maintained by Microsoft certified administrators. These admins, often working off of their "vast Linux experience" derived from a twenty minute adventure into some random Linux distro from a few years ago, are choosing to contribute to the misinformation already in existence. Some people have alleged that they are making up half-truths about what happens to those who go "full time" into this platform or even just disallowing any connectivity to use their network at all. This presents a problem should any of these students happen to come from strong Linux-using households, which might translate into bringing their Linux-based notebook to the local community college. So is this a worldwide problem or just a problem for U.S. schools? While I have seen reports and article indicating this does happen all over, the bulk of the hot air appears to rise from within U.S. shores mostly. Are US based schools alone in their ignorance? These days, U.S. schools are better at making sure everyone is "Microsoft compliant" than they are making sure their students are able to read before high school. Not to worry though, these same students have mastered the ability to click "Big E icon" so that they get themselves onto MySpace and Facebook. This, coupled with their talent for using the latest proprietary security suite to remove the random malware threats, will definitely make U.S. students a force to be reckoned with in the world marketplace as they mature. In the meantime, areas such as Central/South America are making the switch to Linux in record numbers. Grade school students in much poorer countries are learning to use their own problem solving skills to bypass operating system "gotchas" as they come up, while U.S. high school students are working on leveling up their characters in World Of Warcraft! Even in nearby Canada, I see news every month that a new school district is switching over to open source alternatives as Microsoft is simply not where they want to spend their educational budget. Now stop me here, but something seems wrong with this situation. We have U.S.-based teachers and system administrators explaining to young tech-minded students that they need to use Windows, should they wish to compete in the world today. Also keep in mind we are hoping to prep these same students to compete in a world where Linux and Windows are being heavily used. Granted, we often see articles claiming how Linux has weak usage numbers. Yet when pressing on as to how in the world you track an operating system that provides no real means of tracking it, those same media sources seem to suddenly clam up. In other words, no one really has any hard percentages and those making up pie charts with shadowy claims need to consider the fact that they’re not telling the whole truth. But I digress. With the current educational budget that U.S. schools have at their disposal, it seems like there must be plenty of money to spend on software and hardware upgrades! The savings in having U.S. schools still running Windows 98 and 2000Pro is clearly providing more cost effectiveness than hiring multiple operating system ready administrators that can work with more than just Windows, right? It's not like these admins are spending more time dealing with malware than improving the computing environment for students? Oh wait, they are. A simple proposal Let me make a proposal. How about allowing kids who wish to learn more about using Linux do so, on their own time. Perhaps even by giving them some extra school credit, as is sure beats boring them to tears with subjects for extra credit that they’re not showing any interest with anyway. This costs the schools nothing, best of all it serves to help with the student's problem solving skills. In addition, I would suggest that teachers and the school’s Microsoft trained IT staff consider studying up on the subject of Linux before trying to pass futile judgments over it. While I wholeheartedly agree that Linux is not a platform for everyone, it is something that is gaining widespread adoption worldwide and those who are able to use it along with proprietary operating systems will be a much stronger position to succeed within the work place. Besides, any Linux user can plop themselves in front of a Windows box and get to work in a matter of a few minutes. Can we say the same for any casual Windows user trying to do the same thing with Linux? Not without a "Big E" on the desktop, most likely. http://itmanagement.earthweb.com/osr...-Education.htm  Why the U.S. Lost Its WTO IP Complaint Against China. Badly. Michael Geist The World Trade Organization yesterday released its much-anticipated decision involving a U.S. complaint against China over its protection and enforcement of intellectual property rights. The U.S. quickly proclaimed victory, with newspaper headlines trumpeting the WTO panel's requirement that China reform elements of its intellectual property laws. For its part, China was conciliatory and offered to work with the international community to resolve the concerns raised by the decision. Reuters notes that the Chinese reaction is far less combative than it has been other issues. Why the muted response? I suspect that it is because anyone who bothers to work through the 147 page decision will find that the headlines get it wrong. The U.S. did not win this case, but rather lost badly. China is required to amend elements of its copyright law, but on the big issues of this case - border measures and IP enforcement - almost all of the contested laws were upheld as valid. Further, the ramifications of this case extend well beyond China's laws into other areas such as ACTA, since it points to the considerable flexiblity that countries have in meeting their international obligations on these issues. The case centred on three key issues: 1. Does China's copyright law provide appropriate protection for all works in compliance with international copyright law (Berne Convention as incorporated by TRIPS)? 2. Do China's border measures, which allow customs officials to donate, auction, or sell to the rights holder confiscated goods, violate TRIPS? 3. Does China's IP enforcement system, which sets a minimum threshold for criminal prosecution, violate TRIPS? On the first issue, the panel ruled that China's copyright laws do violate Berne by failing to provide copyright protection to all works. China maintained that it denied protection for certain works whose contents are "unconstitutional or immoral." The panel ruled that this was not good enough - international copyright requires protection for all works, though other laws may be implemented to address content restrictions (ie. as Canada noted in its third party submission - "Members can prohibit the publication and distribution of a work but . . . Members do not have a right to deny copyright protection to them."). This issue is a clear win for the U.S. (therefore the proclamation of victory), though this particular concern was certainly the least important of the three issues. The other two more important issues were near total losses for the U.S. On border measures, the U.S. argued against the current Chinese law that provides customs officers with a range of possible methods for disposing confiscated counterfeit products. Virtually all of these measures were upheld, with the panel noting at one point that "China's border measures provide a level of protection higher than the minimum standard required by . . . the TRIPS Agreement." With the exception of one practice (removal of trademark from counterfeit trademarked goods), the panel upheld all of China's border measures including the distribution of confiscated goods to the Red Cross, the resale of the goods to rights holders (if they are interested), the auction of certain goods, or the destruction of the goods. The Chinese IP enforcement system, which sets a minimum threshold for criminal enforcement, was a huge issue for the U.S. and it lost badly on it. The U.S. argued that the high thresholds render prosecution impossible in many cases (Canada joined the U.S. with a similar argument). The panel rejected the U.S. claims, in part due to a lack of evidence. Indeed, the U.S. submitted a series of newspaper articles as the basis for some of its claims, to which the panel responded: "the Panel does not ascribe any weight to the evidence in the press articles and finds that, even if it did, the information that these press articles contain is inadequate to demonstrate what is typical or usual in China for the purposes of the relevant treaty obligation." With that, the Panel found that China does not violate its TRIPS obligation that "Members shall provide for criminal procedures and penalties to be applied at least in cases of wilful trademark counterfeiting or copyright piracy on a commercial scale." This represents a major loss for the United States as well as for the countries such as Canada that supported the U.S. in the case. It also holds the prospect of larger ramifications for initiatives such as te Anti-Counterfeiting Trade Agreement, which are premised on the need to address concerns around border measures and IP enforcement. Rather, the decision highlights the reality that international copyright and trade law provide considerable flexibility that do not necessitate new treaties or additional legal obligations. http://www.michaelgeist.ca/content/view/3645/125/  Windows 7 to be 'Thoroughly' Tested by Antitrust Regulators Changes in the OS generate new documentation to check compliance with '02 agreement Gregg Keizer Technical advisers to the antitrust regulators who monitor Microsoft Corp.'s compliance with a 2002 antitrust settlement will test Windows 7 "more thoroughly" than earlier versions of the operating system were tested, according to a recently-released status report filed with the federal judge watching over the company. The three-member panel of computer experts that works for state antitrust officials has had a copy of Windows 7 since at least last March, but in December 2008, Microsoft delivered additional documentation to the technical committee. In the report, submitted last Wednesday to U.S. District Judge Colleen Kollar-Kotelly, antitrust officials with the Department of Justice, 17 states and the District of Columbia said that Microsoft had given notice that "changes to the protocols in Windows 7" required 30 new and 87 revised technical documents. Microsoft has been under a microscope since it struck a deal in 2002 that required the company to document communication protocols so that other developers, competitors included, could craft software that works smoothly with Windows clients and servers. The decree also set up the technical committee and forced Microsoft and state and federal antitrust officials to deliver regular reports to Kollar-Kotelly. The newest report spelled out changes the committee, dubbed "TC" by the court, will make to test Windows 7, the successor to Vista. "In light of the number of new documents that need to be reviewed, the TC is going to shift its focus to direct review of the documents by the TC's engineers as the most efficient method of identifying issues with the documentation," read the status report. "The revised strategy will enable the TC to review the new Windows 7 and system documents more thoroughly than it would otherwise, which is particularly desirable given the significance of these new documents to the project as a whole." Originally, the consent decree Microsoft signed was to expire in November 2007. Several states objected, however, and after months of legal back-and-forth, Kollar-Kotelly in January 2008 extended her oversight by another two years, to Nov. 12, 2009. Microsoft is also facing renewed scrutiny from the European Union, which two weeks ago filed preliminary charges against the company, accusing it of violating antitrust laws since 1996 by bundling the Internet Explorer browser with Windows. http://www.computerworld.com/action/...icleId=9126859  Sweet Deal to Promote Tweeny-Bop Girl Group Brooks Barnes  In their drive to become the Next Big Thing in teenage entertainment, the Clique Girlz have had more opportunities than most. The youthful trio, backed by Interscope Records and the powerful Creative Artists Agency, have opened for the Jonas Brothers and appeared on “Today,” where Al Roker called them “Hannah Montana times three.” They sang in last year’s Macy’s Thanksgiving Day Parade, and Interscope has flooded YouTube with over 30 videos. None of those sparks have started a fire. Instead, the Clique Girlz — Destinee Monroe, 14; her sister, Paris, 12; and their best friend, Ariel Moore, 14 — are in danger of washing out of the entertainment industry before their first full CD comes to market. So far, at least, digital downloads have been anemic, and play on Radio Disney, where programming is based on listener requests, has been modest at best. But the Clique Girlz, who hail from Egg Harbor Township, N.J., have been thrown what could turn out to be a lifeline — and from no lesser a judge of talent than Michael D. Eisner, the former chief executive of the Walt Disney Company. Topps, the candy and collectibles company that Mr. Eisner bought in 2007, has signed the Clique Girlz as commercial spokeswomen for Baby Bottle Pop, one of the Top 10 nonchocolate candy brands. The candy has two parts, a nipple-shaped lollipop top and a bottle-shaped container filled with fruit-flavored powder. Consumers are meant to lick the top and dip it into the powder. The performers will have their photo on Topps packaging, appear in television ads on Nickelodeon, Cartoon Network and Toon Disney, and in a print campaign set for teeny-bopper must-reads like Twist magazine. Topps will also emphasize the group on the Baby Bottle Pop Web site (babybottlepop.com), offering webisodes, ring tones, games and a tour tracker, starting next month. The centerpiece of the deal calls for the group to “re-imagine” the Baby Bottle Pop ad jingle, well-known among 6- to 12-year-old girls. “They haven’t popped yet, but the elements are there, and we’re superexcited,” said Ari Weinstock, director of marketing for Topps. The Jonas Brothers signed a nearly identical life-support deal with Topps in the period between getting dropped by Sony and being signed by Walt Disney Records in the summer of 2007. Mr. Weinstock credits the campaign with helping the band catch Disney’s eye. A spokeswoman for Disney Records declined to comment. Steve Berman, president of marketing for Interscope, described the partnership as a “fantastic opportunity.” Interscope, by the way, does not agree that the outlook for the group is gloomy, with Mr. Berman saying the label has held the girls back on purpose. “We don’t want this group to go to mainstream radio until we really have solidified them in the market,” he said. Interscope has released multiple Clique Girlz singles, but doesn’t plan to unveil a full album until summer. It may sound routine — teenage band signs marketing deal with candy company — but the partnership underscores the difficulty the music industry is having when it comes to introducing successful acts for the children’s market. Even when the big labels have potential stars on board, they are struggling more than ever to capitalize on them. Disney has shown with the Jonas Brothers, Miley Cyrus (a k a Hannah Montana), “High School Musical” and, to a lesser degree, Demi Lovato and Selena Gomez, that there is a huge demand for such confection. But without Disney’s child-oriented radio, television and theme-park platform at their disposal, labels like Interscope are left scrounging up whatever mass-marketing opportunities they can. There are few more crucial tasks for the music business than developing new teenage acts. Prepubescent children, media executives say, are among the few remaining reliable buyers of music. Last year, 10- to 14-year-olds spent about $1.2 billion on CDs and song downloads, according to the Recording Industry Association of America. For Topps, signing up the Clique Girlz carries little risk. If the band doesn’t strike a chord soon, Topps moves on. But if sales are as strong as Interscope hopes, the Baby Bottle Pop brand could get a boost. The Jonas Brothers certainly gave it one: Mr. Weinstock, citing Nielsen figures, said sales of the candy increased 7 percent in 2007 over the previous year, and increased 12 percent in 2008. “Quite impressive for a mature brand,” he said. The Clique Girlz have more at stake. “The teen market used to look down on blatant marketing partnerships like this,” said Matt Britton, a managing partner at Mr. Youth, a New York marketing firm. “Now, because the music industry is in such bad shape, overt efforts to manufacture buzz are expected. But it still has to ring true.” http://www.nytimes.com/2009/01/28/ar...ic/28cliq.html  Save Sirius Group Calls For Satcaster Subpoena FMQB Save Sirius, an organization of shareholders upset with the fallout of the Sirius-XM merger, is now calling for a Congressional subpoena into the merged company. Orbitcast reports that Michael Hartleib, who heads up Save Sirius, has written a letter to Sen. Sam Brownback (R-KS), saying that the satcaster's protected documents are "nothing more than an attempt to obfuscate a crime." In the letter, Hartleib says that "It is my opinion that it is without question [Mel] Karmazin misled, willfully withheld and omitted information from members of Congress. As I am sure you are aware, withholding relevant information and/or intentionally misleading members of Congress is considered perjury under its definition...These documents need to be subpoenaed by Congress as I believe the protected status is nothing more than an attempt to obfuscate a crime." He adds that, "It is my opinion these two companies have colluded and conspired to restrain free trade in violation of our Nation's Anti-Trust Laws including but not limited to the Sherman Act." Hartleib later says that "The failure of the FCC to release these documents makes them complicit in a multi-year conspiracy to restrain free trade and has allowed these companies to consolidate the entire SDARS spectrum which has been their goal from at least 2002. Despite there being a law prohibiting the combination of the two SDARS' licenses, within mere months after becoming operational in 2002." He calls for "a full investigation into the breakdown of the FCC and how it is these two companies were able to ignore their Federal Mandate for over ten years and make a Federal Regulatory Agency a coconspirator." Also, last week's reported Sirius XM price increases have been officially announced. On both XM and Sirius' websites, the new pricing rates have been confirmed. You can see the announcements on XM's site here and on Sirius' here. And in related news, The Globe and Mail reports that "the door is now open" for Sirius Canada and XM Canada to merge as well. Acording to the paper's sources, investment banking firms have been hired by both satcasters to look into merger options. http://www.fmqb.com/Article.asp?id=1130206  YouTube Users Caught in Warner Music Spat Greg Sandoval Corey Vidal is no pirate, but he's been branded one as a result of the licensing spat between Warner Music Group and YouTube. On YouTube, Vidal posted a humorous video tribute to John Williams, the man who scored the soundtracks for such blockbuster films as Indiana Jones, and Star Wars. In his clip he included some of Williams' music. By now, everybody knows that YouTube removes videos that violate copyright law. What's different about Vidal's work getting pulled is that when he posted it in October, he was permitted to use Warner's music. Until last month, YouTube had an agreement with Warner Music--one of the four largest recording companies--that allowed video creators to include the label's content in their clips. Last month, talks to renew the deal broke down and that means YouTube and its users no longer have access to Warner's library. For this reason, the case is much different than YouTube's high-profile fight with Viacom or run-of-the-mill piracy that once flourished on the site. Sources close to the situation say YouTube is close to finalizing a new agreement with Sony Music. In 2007, Viacom and YouTube failed to come to terms on a licensing deal and Viacom requested that YouTube pull its content. In that case, there was no prior agreement. Most of the people who posted Viacom's films or TV shows to YouTube did so without authorization. In this situation, YouTube fans used Warner Music's songs for two years with the label's blessing. Now, through no fault of their own, the videos that YouTube users made in good faith are being yanked. "I don't understand who I'm harming," said Frank Stallone, a 41-year-old former DJ who is quick to point out that he is not the less-famous brother of the box office draw. Stallone's video was removed for using 45 seconds from "Forget Me Nots," a 1982 song from Patrice Rushen. "If anything, people are hearing the 45-second tease they haven't heard in a while and they'll want to go out and buy the song," he said. Warner Music declined to comment, but YouTube had this to say: "While we work with music labels and publishers to keep music on the site, sometimes our negotiations don't pan out," said a spokesman for the company. "In those cases, we try to give people options when they receive a copyright claim. Instead of automatically blocking videos, we give uploaders the choice to dispute the claim (in the case of Fair Use, for example), use our AudioSwap tool to replace the track with one from our library of pre-cleared music, or to replace the video with a new version with no sound." If nothing else, the situation serves as a warning to those who think that because YouTube obtains rights to music or films one day, the agreements will last forever. That's just not how these deals work. That hasn't stopped some YouTube's fans from posting angry videos denouncing the situation at YouTube. Most of the protest videos take aim at Warner and the other three top recording companies. While all four of the big labels are in discussions about renewing licensing agreements, Warner is the only one scuffling publicly with YouTube. In fact, sources close to the situation say YouTube is close to finalizing a new agreement with one of Warner's chief rivals: Sony Music. The situation illustrates how Web services and entertainment companies are learning hard lessons as they cover uncharted ground. It's doubtful that Warner Music or YouTube intended to alienate their customers. Presumably Warner Music wants more concessions from YouTube and the Web's No. 1 video site wants to pay less. What they likely didn't consider when they penned their initial contract was what would happen to users if they failed to agree on a new deal. Vidal, a 22-year-old from the Canadian province of Ontario, is more than happy to help them understand. Vidal makes his living by creating YouTube videos. He's a member of the company's YouTube Partners program. This allows him to sell some of the advertisements that accompany his clips and pocket the money. He says that his videos see about 3.4 million to 4 million views per month and YouTube is his only source of income. As for how much he makes, Vidal only will say it's enough for him to live comfortably. Vidal hit the jackpot with his tribute to Williams. YouTube featured it on the site's front door. He says for a time the clip was generating a million views each day and was nominated for a "People's Choice Award" at CBS, parent company of CNET News. But on January 18, Vidal's cash cow went down. YouTube sent him a notice that said Warner Music had claimed his video had infringed on the label's copyright. Vidal doesn't dispute that the label owns the rights to the music he used. "I'll share the money I made with them but I just want my video back up." But he has so many questions about whether his video truly violates copyright law and if so, what part of the video infringes? That's the other problem raised by the quarrel between Warner Music and YouTube. When users are dragged into it, there's few places to get answers. Vidal said he called Warner Music and talked to about half a dozen people in the eight days since his video was removed. He has yet to hear back why exactly the video was pulled down or whether he and the record company can strike a separate deal. To its credit, Viacom set up a support hot line to help answer questions and address disputes when it began pulling content from YouTube. That's what Stallone, the former DJ, says he needs. He says he doesn't think using 45 seconds of a song is breaking any law, but he doesn't have anywhere to go to get legal help. Also, he said he was discouraged by some of the language in the takedown notice YouTube sent him. Specifically, this passage: "There are very few valid reasons for disputing a claim," YouTube wrote in the notice. "Submitting an invalid dispute can result in penalties against your account." Stallone wants to know how he's supposed to determine what an invalid dispute is? YouTube users should not assume copyright holders are always correct when they accuse someone of a violation, according to Fred von Lohmann, senior attorney for the Electronic Frontier Foundation, a watchdog group that advocates for the rights of Internet users. In the Viacom case, for instance, the company acknowledged erring in a small number of cases. In another case, a Pennsylvania woman is suing rocker Prince and Universal Music for accusing her of copyright violation for including a brief snippet of Prince's music in a video of her baby. Universal and Prince dropped their copyright claims against the woman and her video has returned to YouTube. I'm no lawyer, but Stallone's case sounds very similar. http://news.cnet.com/8301-1023_3-10150588-93.html  Performance Royalty Battle Returns FMQB The fight over bringing a performance royalty rate to terrestrial radio is set to return. Four members of the House of Representatives have sent a letter out to their colleagues, asking them not to sign a new version of the Radio Freedom Act, which would protect stations from the proposed new rates. The letter states that, "In the coming days, you will likely be presented with a resolution supported by radio broadcasters, which advocates protections for the radio industry but in effect denies performers payment for their work. While the resolution will be framed in terms of preventing a "tax," "fee," or "burden" on local radio stations, in reality, the only payment broadcasters would be required to make would be for the use of someone else's property. This resolution is extremely detrimental to thousands of people and businesses, to the protection of American intellectual property abroad, to the economy and the balance of trade. We urgently ask that you not sign on to this resolution and welcome your participation in the full discussion on this issue that will be before the Judiciary Committee in the coming weeks." The House members add that the "fundamental purpose of the resolution is to prevent a fair compromise on the issue of compensating another person for the use of their property. The resolution unjustifiably exaggerates hardship to small stations and public service offerings. It falsely suggests that businesses such as bars, restaurants, sporting, retail and entertainment venues will be affected. It touts that any incidental "promotional benefit" that may be received by a performer from radio play should exempt radio completely from paying to use his or her works - as if any other business in America could use this claim to avoid paying to use another's property without consent." The letter notes that the Performance Rights Act "presents a fair and balanced approach that does not affect establishments and venues, provides major accommodations for small broadcast stations (75 percent of all stations) to protect against hardship, and provides outright exemptions for religious and talk radio. It will not tax or burden broadcasters, but rather will establish balance between those who create music and those who play it for the health and future of both industries. Certainly, there may be promotional benefit in the broadcast of music. The Performance Rights Act appropriately accounts for any promotional benefits in the rate that will be set." The House members conclude by urging their colleagues "to refrain from cosponsoring the resolution and ask that you encourage the parties to work together toward an acceptable solution. There is a reasonable balance to be found. We also hope you will consider joining us in supporting the Performance Rights Act. We look forward to working with you on this issue in this Congress." The letter was signed by Rep. John Conyers, Jr., Chairman of the House Committee on the Judiciary; Howard L. Berman (D-CA), Chairman, Committee on Foreign Affairs; Darrell Issa (R-CA), Ranking Member, Government Oversight and Reform Committee and Congresswoman Marsha W. Blackburn (R-TN). In response to the letter, NAB EVP Dennis Wharton released the following statement, "It is implausible to suggest that a government-imposed bailout of foreign record labels estimated to cost up to $7 billion would not cause serious economic harm to U.S. radio stations. The media business faces the worst advertising economy in decades, and thousands of loyal, hard-working people have lost their job in radio the last few months. If Congress wants to ensure more job losses and put at risk the countless charitable and public service efforts of local radio stations, passing the performance tax would be the best recipe." http://fmqb.com/Article.asp?id=1123595  Thieves Pick $11,000 Worth of Guitars in NJ AP Some guitar owners in three northern New Jersey towns are singing the blues after thieves have made off with their instruments. Eleven guitars, worth more than $11,000, have been stolen in six separate burglaries in Summit, Roselle Park and Montclair. They include expensive brand names like Fender, Gretsch, Ibanez, Martin and Squire. The thefts began in November in Montclair. The most recent heist was Tuesday at an apartment in Roselle Park, where police say masked thieves beat and kicked two men who were home during the break-in. The thieves walked out with $7,000 worth of guitars. Police are scouring online auction sites as they try to track the thefts. http://www.newstimes.com/national/ci_11589788  Dutch Treat: Pay for Some Content, Pirate the Rest Jart Armin There may be an upside to illegal file sharing: The Institute for Information Law in the Netherlands reports that the average downloader buys more DVDs, music, and games than people who never download. Illegal downloaders represent 45 percent of consumers who purchase content legally, the institute recently reported. The Institute estimates some 4.7 million Dutch Internet users 15 years and older downloaded hacked and pirated DVDs, games, and music in the last 12 months. This would imply a staggering 25 percent of the Dutch population (from the 2008 figure of 16.5 million) who view illegal downloading and sharing as socially acceptable, even as they're also legally acquiring content in parallel. The report also said that it appeared many are unclear about the potentially illegal nature of such downloads. Most thought that downloading copyrighted music and movies is okay for personal use, but thought that downloading games was possibly illegal. In the case of the many Dutch operated peer-to-peer (P2P) networks now mostly based on USENET, such rip-offs are often not only downloaded, but the material is then automatically made available to others. Of course, what the report did not cover is much of the "Warez" are often associated with organized cyber crime. The Netherlands has now become one of major centers for hosting rip-offs, scams, and other cyber crime. The key Dutch host for badness was until recently Ecatel, especially after McColo went down. Several border gateway protocol (BGP) peers have suspended agreements with Ecatel over the high volume of spam bots and malware it was hosting. Ecatel's been supplanted in bad hosting by LeaseWeb in Amsterdam. In a recent case in an Amsterdam court, LeaseWeb was ordered to take down sites that list Bit Torrent/edonkey files. This followed international pressure from the Motion Picture Association of America (MPAA), the International Federation of the Phonographic Industry (IFPI), and The Business Software Alliance (BSA) -- however USENET groups have now proved a useful alternative. Apart from the Warez (copyrighted works traded in violation of copyright law) and related cybercrime, this whole issue comes down to a personal and ethical decision for all of us. Since the film, music, and software industries are pressuring ISPs to disclose Warez users -- i.e., the illegal downloaders -- many are unsure just how proper (or legally dubious) their online activities really are. To sort this out, see which one of these completely unscientific profiles best describes your personal Warez ethics: A. All file sharing is wrong. You never know what tracking trojans, viruses, or malware can also be encrypted and hidden within the file, using modern steganography (the art of covered or hidden writing). B. I download freeware, shareware, and media files where the Website says I can. I never use USENET and, of course, spend a couple of hours reading all the Creative Commons, licenses, copyright, and terms-of-use notices first. C. I've reformed. Now that many ISPs are reporting such details to MPAA, IFPI, etc., and there's larger possibility of prosecution, it's too risky. D. I outsmart the online police by using Tor as a personal proxy. However, I did not know many Tor nodes internationally are now actually operated by governmental agencies and anti-piracy organizations, just to monitor my downloading activity. E. I am Dutch -- it is my constitutional right. There is no chance of personal prosecution, and anyway, all copyrighted property is theft, according to Karl Marx. So how did you rate? Confused? Well, you can legally download the full 142-page report here from The Institute for Information Law. But it may not help much -- it's only available in Dutch. Maybe there's a pirated translation program somewhere on BitTorrent that can help. http://www.internetevolution.com/aut...doc_id=170903& Until next week, - js.  Current Week In Review  Recent WiRs - January24th, January 17th, January 10th, January 3rd Jack Spratts' Week In Review is published every Friday. Submit letters, articles, press releases, comments, questions etc. in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - January 24th, '09 | JackSpratts | Peer to Peer | 0 | 21-01-09 09:49 AM |
| Peer-To-Peer News - The Week In Review - September 22nd, '07 | JackSpratts | Peer to Peer | 3 | 22-09-07 06:41 PM |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |