
 |
|
|||||||
| Peer to Peer The 3rd millenium technology! |
 |
|
|
Thread Tools | Search this Thread | Display Modes |
|
|
#1 | |||
|
Join Date: May 2001
Location: New England
Posts: 10,017
|
Since 2002
  "Dead-Tree Editions Sell Out" – Corey Kilgannon November 8th, 2008  An Obama Presidency: Good, Bad News for Technology Declan McCullagh When Barack Obama becomes president in January with a strongly Democratic Congress, he'll have the chance to push a technology policy that relies more on government subsidy and regulation than that of his immediate predecessor. In Washington and Silicon Valley circles, betting has already begun on who will be the nation's first "chief technology officer." Could it be Google CEO Eric Schmidt, who conveniently endorsed Obama? Or Vint Cerf? If there's an opening for a Beltway type, perhaps ex-regulator Reed Hundt, who's been a proxy for the president-elect? Obama wants the CTO to "ensure that our government and all its agencies have the right infrastructure, policies and services for the 21st century," plus protecting the security of .gov computer networks. That's a pretty tall task for one person, although there's some precedent; President Clinton handed much authority for Internet regulation to Ira Magaziner after his administration's health care debacle. Any administration will find health care to be a massive project, especially one that likely will be distracted by the Iraq occupation and a recession. Enacting new government regulations aimed at health care records and their electronic storage is an obvious first step that's already been kicking around Congress for a while. On copyright, the conventional thinking is that Democrats are more likely to align themselves with the recording and movie industries' wishes. That may not be the case here: it was John McCain who talked up more aggressive enforcement of copyright law domestically, while Obama said "we need to update and reform our copyright and patent systems to promote civic discourse, innovation, and investment while ensuring that intellectual property owners are fairly treated." That is, of course, intentionally vague. Obama was also vague when we asked him whether he wants to amend the Digital Millennium Copyright Act to let Americans make a single backup copy of a DVD or computer game they legally purchase. He said only that he'd support it "in concept." Internationally, though, Obama would not take an obviously different approach than the policies that the Bush administration has followed and that a McCain administration would have. His Web site says that "China fails to enforce U.S. copyrights and trademarks" and that additional international enforcement and standards are needed. Congress and free trade For technology firms, a substantial downside--and one that's difficult to overstate--is how hostile a solidly Democratic Congress and White House could be toward free trade. Obama doesn't have the ideological bias toward free trade that Clinton had and is certain to face strong protectionist pressure from within his own party. After a handful of Democrats joined Republicans to approve the Central America Free Trade Agreement in 2005, the 15 dissidents were hounded by their own party and by labor activists. Only a rare politician would take that risk again. Democrats' populist streak could hurt technology companies in other ways as well. Obama has promoted more aggressive antitrust actions, which could hurt Silicon Valley companies like Yahoo and Google that are already reeling from the scrutiny of a supposedly free-market Republican administration. Additionally, Obama has only promised to expand the H1-B visa program temporarily. More tax dollars diverted to universal broadband is a goal often promoted by the Democratic party, and Obama's CTO would at the very least influence how such a goal is met. The Obama campaign has enthusiastically called broadband access the way to a more perfect democracy, and Democratic members of Congress like Rep. Anna Eshoo of California have promoted the idea. Eshoo's resolution, however, does little beyond call for more work to be done. Finding the funds to create wider broadband access could be a challenge; it would have to be paid for by higher taxes, reduced spending elsewhere, or running up the federal deficit. Michael Powell, former chairman of the Federal Communications Commission, said at a forum in September that it is unrealistic to entertain the "idea that there's money to get people to dig up streets and put in fiber. National broadband policy is probably going to have to be a lot more subtle." Net neutrality is another open question. It was a striking difference between the two major party presidential candidates: Obama wanted new government regulation of the Internet, and McCain was skeptical. Some prominent technologists including Cisco Systems' Robert Pepper, Carnegie Mellon University's Dave Farber, and Internet founding father Bob Kahn are skeptical too. Because politicians tend not to like to seek out trouble, a resolution will probably wait until a federal appeals court deals with Comcast's appeal of a related order by the FCC. Comcast claims the FCC does not have the authority to impose Net neutrality regulations and didn't even follow its own rules when levying them in the first place. If the court sides with the FCC, it will sap energy from a push for extensive new Net neutrality laws; if the decision goes the other way, look for Congress to get involved. Net neutrality is, after all, the very first issue addressed in Obama's technology policy platform. House Speaker Nancy Pelosi (D-Calif.) has talked up the idea, and Sen. Byron Dorgan (D-N.D.) introduced related legislation last year. CNET's Stephanie Condon co-authored this article. http://news.cnet.com/8301-13578_3-10082672-38.html  Air Force Aims to 'Rewrite Laws of Cyberspace' Noah Shachtman The Air Force is fed up with a seemingly endless barrage of attacks on its computer networks from stealthy adversaries whose motives and even locations are unclear. So now the service is looking to restore its advantage on the virtual battlefield by doing nothing less than the rewriting the "laws of cyberspace." It's more than a little ironic that the U.S. military, which had so much to do with the creation and early development of internet, finds itself at its mercy. But as the American armed forces become increasingly reliant on its communications networks, even small, obscure holes in the defense grid are seen as having catastrophic potential. Trouble is that even a founding father can't unilaterally change things that the entirety of the internet ecosystem now depends on. "You can control your own networks, rewrite your own laws," says Rick Wesson, CEO of the network security firm Support Intelligence. "You can't rewrite everybody else's." But the Air Force Research Laboratory's "Integrated Cyber Defense" program, announced earlier this month, is part of a larger military effort to accomplish just that. "The 'laws' of cyberspace can be rewritten, and therefore the domain can be modified at any level to favor defensive forces," announces the project's request for proposals. Some of the rewrites being considered: • Making hostile traffic inoperable on Air Force networks. • Locating and identifying once-anonymous hackers. • Enabling Air Force servers to evade or dodge electronic attacks, somehow. It's part of a larger Air Force effort to gain the upper hand in network conflict. An upcoming Air Force doctrine calls for the service to have the "freedom to attack" online. A research program, launched in May, shoots for "gain access" to "any and all" computers. A new division of information warriors is being set up under Air Force Space Command. "Our mission is to control cyberspace both for attacks and defense," 8th Air Force commander Lt. Gen. Robert Elder told Wired.com earlier this year. Apparently. At the moment, though, online aggressors have the edge on the military's network protectors, the Air Force says. "Defensive operations are constantly playing 'catch up' to an ever-increasing onslaught of attacks that seem to always stay one step ahead," says the Air Force Research Laboratory's "Integrated Cyber Defense" request for proposals. "In order to tip the balance in favor of the defender, we must develop a strategic approach to cyber defense that transcends the day to day reactive operations." "[M]ost threats should be made irrelevant by eliminating vulnerabilities beforehand by either moving them 'out of band' (i.e., making them technically or physically inaccessible to the adversary), or 'designing them out' completely," the request for proposals adds. "Can we create a cyberspace with different rules?" asks Paul Ratazzi, a technical advisor at the AFRL's Information Directorate. "Let's challenge those fundamental assumptions on how these things work, and see if there's a better way." For instance, it's extraordinarily difficult to find the hacker behind a cyberattack today. Network traffic can be run through dozens of different proxies and anonymizers; "botnets" of enslaved computers can be controlled from the other side of the world; millions of PCs spew out malicious data without their owners ever catching on. AFRL would like to see a way to change existing network protocols, to make it easier to trace and locate the source of an online threat. Or perhaps today's protocols can be tailored, to make military networks "technically or physically inaccessible" to malicious traffic. "We'll start with blue," says Information Directorate chief Donald Hanson, using the military term for friendly forces. "If you're not blue, you can't come in." Hanson is also interested in finding ways to dodge electronic attacks, rather than figure out new ways to stop them, or lock them out. "A lot of our [defenses] up to now have been about defeating an attack," he says. "We'd rather avoid it altogether." Digital radios communicate today by "frequency-hopping" -- jumping across multiple bands of the spectrum. Perhaps the Air Force's online traffic could do something similar. There are some network precedents for the idea, Wesson explains. So-called "honeypot" servers are used to lure in hackers with fake targets to attack. But the hackers are often aware which IP addresses are really honeypots. So hosted servers are used to mask those addresses -- and, with a secure network "tunnel," run the traffic back to the honeypots. "If you can do that with honeypots, you can do it with all kinds of other things," Wesson says. Hanson refused to comment on that technique. But Ross Stapleton-Gray, with the Packet Clearing House research group, isn't sure cyberstrikes can be avoided, really. "The way networks work, it's always going to be easier for a nimble attacker than a nimble defender," says Ross Stapleton-Gray, with the Packet Clearing House research group. "There's always a scarcity of bandwidth -- somewhere. There are always chokepoints -- somewhere." http://blog.wired.com/defense/2008/1...orce-aims.html  French Internet Law Clashes with EU Position Leigh Phillips The French Senate has overwhelmingly voted in favour of a law that would cut off access to the internet to web surfers who repeatedly download copyrighted music, films or video games without paying. Under the so-called three strikes or "graduated response" legislation - which still needs approval by the lower house before it becomes French law - illegal downloaders are first sent an email warning them of their infraction. They are subsequently sent a warning letter in the post. If after this second warning they continue to illegally download copyrighted content, the internet service provider will cut off access to the internet for a year. The legislation passed with a massive cross-party majority of 297 votes to 15. Only a handful of conservatives, centrists and socialists voted against, while the Communists abstained. In passing the bill, the senators rejected an amendment proposed by senator Bruno Retailleau of the right-wing MPF party replacing internet cut-off with a fine. Mr Retailleau accused the bill of being too severe. "Cutting access to the internet is discriminatory," he said, pointing out that often internet access comes bundled with television and fixed-line telephone services and that it is impossible to just cut off the internet. He added that the internet has become an "essential commodity" that allows people access to social services and that their removal would be "traumatic for a family." But the culture minister had earlier warned against the amendment, saying that the introduction of a fine was more severe a punishment. "The principle of a financial penalty changes the philosophy [of the bill], from instructive to repressive," Christine Albanel said. Companies and other enterprises where multiple computers have access to one network however, would instead be required to install firewalls to prevent workers from illegal downloading. The legislation is the transposition into law of an extra-parliamentary initiative of President Nicholas Sarkozy from last November, the so-called Olivennes accord, in which some 40 stakeholders from the music, cinema and internet service provision sectors agreed that repeat illegal downloaders would have their internet cut off by ISPs. However, the accord was essentially a gentleman's agreement between the parties and without legislative weight. The bill sets up a tussle between France and Brussels. In September, the European Parliament approved by a large majority an amendment outlawing internet cut-off. The amendment, part of a wider telecoms bill, was then defended by information society commissioner Viviane Reding after President Sarkozy earlier this month sent European Commission President Jose Manuel Barroso a letter requesting he work to overturn the parliament's decision. http://euobserver.com/9/27026  British Black Boxes to Record Every Email and Website Visit Internet "black boxes" could be used to record every email and website visit made by computer users in Britain, it has been reported. Graham Tibbetts Under Government plans to monitor internet traffic, raw data would be collected and stored by the black boxes before being transferred to a giant central database. The vision was outlined at a meeting between officials from the Home Office and Internet Service Providers earlier this week. It is further evidence of the Government's desire to have the capability to vet every telephone call, email and internet visit made in the UK, which has already provoked an outcry. Richard Thomas, the Information Commissioner, has described it as a "step too far". The proposal is expected to be put out to consultation as part of the new Communications Data Bill early next year. At Monday's meeting in London representatives from BT, AOL Europe, O2 and BSkyB were given a presentation of the issues and the technology surrounding the Government's Interception Modernisation Programme (IMP), the name given by the Home Office to the database proposal. They were told that the security and intelligence agencies wanted to use the stored data to help fight serious crime and terrorism. Officials tried to reassure the industry by suggesting that many smaller ISPs would be unaffected by the "black boxes" as these would be installed upstream on the network and hinted that all costs would be met by the Government. One delegate at the meeting told the Independent: "They said they only wanted to return to a position they were in before the emergence of internet communication, when they were able to monitor all correspondence with a police suspect. The difference here is they will be in a much better position to spy on many more people on the basis of their internet behaviour. Also there's a grey area between what is content and what is traffic. Is what is said in a chat room content or just traffic?" Ministers have said plans for the database have not been confirmed, and that it is not their intention to introduce monitoring or storage equipment that will check or hold the content of emails or phonecalls on the traffic. A spokesman for the Home Office said: "We are public about the IMP, but we are still working out the detail. There will a consultation on the Communications Data Bill early next year." http://www.telegraph.co.uk/news/ukne...ite-visit.html  Australian Internet Filters Have Backdoor Adam Turner The Australian government wants to introduce draconian censorship and cripple internet speeds with a mandatory filtering system which any child can bypass in five minutes - Adam Turner shows how easy it is. Communications Minister, Senator Conroy, is pandering to a handful of fundamentalist luddites with his plans to introduce mandatory internet filtering at the ISP-level. The government's own research reveals the filters will slow down everyone's internet access by 20 to 75 per cent, which makes a joke of plans to build a faster national network. Of perhaps greater concern is the fact that supporters of filtering are already talking about expanding it to include other stuff they don't like, such as online gambling and "illegal" sites. Censorship is a slippery slope and the fact the government has tried to censor people speaking out against the filtering plans should be ringing alarm bells. The government already tried giving away free desktop filtering software, but no-one wanted it. Now it wants to inflict filtering on everyone by introducing it at the ISP-level. The government's own research has shown filtering is not foolproof, yet talk of a "clean feed" could give many Australians a false sense of security when online and actually make them less safer rather than more. The biggest joke is that plans for filtering won't stop anyone who is determined to access banned content, as there are free and easy ways to bypass any efforts at censoring the web in Australia. One simple trick is to use a free web proxy, which acts as a middle man between you and the site you want to see. You'll find a long list of free web proxies and other such sites at FreeProxy.ru. Just enter the name of the site into a proxy site's search box - such as banned-site.com, and the proxy site will then call up the site for you. This way banned-site.com doesn't know who you are, but also your ISP doesn't know you looked at banned-site.com. Kids are already using these kinds of sites to bypass school filters so they can access Facebook from the classroom. It won't take horny teenagers long to use such sites to bypass ISP-level filtering. Another trick for bypassing filters is to dig an encrypted tunnel to the United States. It sounds complicated, but it's free and ridiculously easy to do and not even your ISP can see what you're up to. Two popular free VPN applications are HotSpot Shield (Mac and Windows) and AlwaysVPN (Mac, Windows, Linux). They add an advertising banner to your browser, but if you're prepared to spend $5 per month you could look at Witopia or VPN out. You don't need to know anything about networking and there's no messy configuration, you run the installers and they just work. These applications give you dual citizenship as, with the click of a button, your computer looks like it's in the United States. This means you can access US-only content from sites such as Rhapsody, Pandora, YouTube and Hulu. It also means you're bypassing any content filtering performed by your Australian ISP, and there's nothing they can do about it. Such tools are not illegal. They're primarily designed to protect your privacy when you connect to an insecure wifi hotspot. If mandatory filtering is introduced in Australia, you can expect many of the local ISPs to start bundling a VPN service with their internet packages - of course just so their customers are "safe" online, not so they can bypass the filters. Australia's plans for mandatory content filtering will screw up the internet and give right wing nutjobs the power to censor what we see, yet it won't actually stop people who want to access banned sites. If you're concerned about the government's plans for filtering the internet, it's time to speak up before it's too late. Visit NoCleanFeed.com, run by Electronic Frontiers Australia, for information on how to voice your concerns. Do it quickly, before some holier-than-thou git decides you're not allowed to see that site either. http://www.pcauthority.com.au/BlogEn...-backdoor.aspx  Telstra Dodges Broadband Debate Andrew Colley TELSTRA has been accused of attacking free speech after it attempted to silence voices in the debate over the federal Government's $4.7 billion national broadband network. Telstra wholesale group managing director Kate McKenzie pulled out of a national broadband conference scheduled to start in Sydney today because the self-styled media and communications group was unable to convince organisers to drop two speakers from the event. John Pozoglou, head organiser for Terrapin's Broadband World Australia 2008 conference, said Ms McKenzie had agreed to participate in a panel discussion at the event but pulled out after conference organisers refused to drop the executive chairman of the anti-Telstra lobby group, the Competitive Carriers Coalition (CCC) David Forman, and telecommunications analyst Paul Budde from the session. Telstra wanted a representative from its telecommunications equipment supplier Alcatel-Lucent to appear in Mr Forman's place, Mr Pozoglou said. It's understood Telstra also wanted Mr Budde dropped as moderator for another event in which Terria and Telstra were expected to showcase their bids for the network. A Telstra spokesman conceded the carrier had pulled out of the event because it was unable to reach agreement with Terrapin on the composition of the panel. He said the need to adhere to confidentiality conditions attached to the federal Government's network tender process had also been a consideration. "It was originally envisaged that this conference would occur after the lodgement of proposals under the national broadband network request for proposals. With the later lodgement date, this is no longer the case. The combination of the need to maintain confidentiality under the national broadband network RFP and the inability to reach agreement on a fair and balanced panel meant that regrettably Telstra was no longer in a position to participate," the spokesman said. In July, Communications Minister Stephen Conroy flagged an extension to the deadline to lodge proposal for the network and the Government set the November 26 deadline on September 2. Mr Pozoglou said Telstra withdrew from the event last week. He rang Telstra wholesale's corporate affairs spokeswoman to find out why they were withdrawing "as they'd been aware of the speakers and the schedule and the content for a long time". "Her response was that they thought that we'd deliberately set up the conference to be anti-Telstra in nature." Telstra said the only way it would participate was if we removed Paul Budde and used a moderator of Telstra'a choosing. "The second demand was that we remove David Forman from the panel session completely," Mr Pozoglou said. The disputed session was a panel on open access network regulation in Australia, which was expected to include Ms McKenzie, Mr Forman and Mr Budde. IiNet regulatory affairs spokesman Steve Dalby and a fifth speaker from Optus were also expected to participate in the panel, representing the Terria consortium. Mr Budde described Telstra's actions as a "shocking and a clear disregard of freedom of speech." "I would like to publicly thank and congratulate Terrapin on maintaining their independent position in this sad case. This is a brave thing to do, as we all know the sheer market power Telstra has," Mr Budde said. The accusation comes as Telstra is moving from being a carrier to a media and communications company. It has established a website nowwearetalking.com.au, which has engaged in attacks on several media organisations. Mr Forman said Telstra's actions were a further warning that the federal Government should curb the company's power. "Telstra is acting in the only way it knows how - by using its market power to try to force people to do what it wants. It can no sooner change than a leopard can change its spots. "This incident illustrates yet again that the Government must introduce structural separation of the telecommunications industry," Mr Forman said. Optus spokesman Maha Krishnapillai said: "This is symptomatic of Telstra trying to use its market power to dictate its terms of engagement, not only with industry, not only with conferences but also with government." At the very least that has been hard won wisdom for Terrapin, Mr Pozoglou said. "We'd be absolutely silly not to learn from this experience. "Moving forward, if we're to have Telstra speaking at our conferences we'd have to take account of where the political lines are and who they might have some sort of grievance against." http://www.australianit.news.com.au/...013041,00.html  Treaty Consultation Process Snubs Public Michael Geist Earlier this year, many Canadians were taken aback by reports of a secret trade agreement that conjured up images of iPod-searching border guards and tough new penalties for everyday activities. The Anti-Counterfeiting Trade Agreement – being negotiated by Canada, the United States, Japan, the European Union and a handful other countries – generated sufficient public concern such that then-Industry Minister Jim Prentice specifically denied any links between the treaty and proposed new legislation. While the ACTA debate has largely disappeared from the public radar screen, talks continue. Over the summer, I reported about attempts to establish a private consultation committee composed of industry groups that excluded public interest organizations. The status of the consultation committee remains unknown, but newly obtained documents under the Access to Information Act provide additional insights into the secretive nature of the negotiations as well as the results of a limited public consultation conducted by the Department of Foreign Affairs in the spring. The documents confirm that the U.S. and Japan have emerged as the primary supporters and drafters of the treaty. Countries have met three times in recent months to discuss the treaty with those two countries providing draft treaty language to the other participants just prior to the formal meeting. In late May, the U.S. and Japan forwarded draft treaty language on new border measures provisions to the Canadian delegation, two weeks before a round of talks in Washington. According to Australian officials, subsequent meetings in Geneva and Tokyo addressed statutory damages and criminal provisions for unauthorized camcording. The next meeting is set for Brussels in December with Internet issues on the agenda. Although bits of information about the meetings have leaked out, participating countries have gone to great lengths to keep the talks under wraps. Countries are prohibited from discussing the substance of discussions and all documents are subject to strict confidentiality conditions. Secret negotiations are common for trade deals, but international intellectual property agreements have traditionally been conducted in a more transparent manner. Internal government documents also shed light on the results of a brief Canadian consultation on ACTA. Launched in April, the Department of Foreign Affairs consultation invited the public to express views on the treaty and the negotiation process. While the Foreign Affairs has yet to reveal results of the consultation, an internal draft report summarizing the responses notes "individual Canadian citizens were generally critical of Canada's role in the formal negotiation of ACTA." Individual responses cited the lack of transparency associated with the process, the absence of evidence that a new treaty is needed, the exclusion of developing countries from the negotiations, and the concern that ACTA might undermine Canadian law. The consultation also generated responses from 13 Canadian business associations. Many received personal invitations to participate in the consultation from government departments as Canadian Heritage alone notified 23 groups it considers its stakeholders. These business groups were not only generally supportive of ACTA, but some asked for the inclusion of provisions that would necessitate significant changes to Canadian law. One submission recommended provisions mandating that Internet service providers terminate access in cases of repeated allegations of infringement. To date, it appears that ACTA is pushing Canada toward a host of new international commitments drafted by officials in Washington and Tokyo with virtually no public input. With the next round of talks only weeks away, these revelations reinforce the need for new Industry Minister Tony Clement and Canadian Heritage Minister James Moore to open the process to greater scrutiny. http://www.thestar.com/sciencetech/article/529251  Phone Company: Heavy Internet Users to Pay More Peter Svensson Phone company Frontier Communications Co. will probably charge its subscribers a dollar or two per gigabyte of Internet traffic if they go over the monthly allotments the company plans to introduce next year, Frontier's chief executive said Friday. The company is at the forefront of what CEO Maggie Wilderotter believes is a trend among Internet service providers toward billing for the amount of data subscribers use, rather than all-you-can-eat monthly plans. Frontier provides service mainly in rural areas of 25 states. Rochester, N.Y. is its largest market. The company caused confusion and some dismay among customers earlier this year, when it said it would charge for Internet use above 5 gigabytes per month, starting next year. U.S. Internet users have no experience with tracking their usage. There have been few caps in place on downloads, and the existing caps have been so high that they affected only a tiny fraction of users. Frontier's planned cap would apply to the total amount of data that users download and upload in a given month. A traffic allowance of 5 gigabytes is enough for thousands of Web pages, or tens of thousands of e-mails, but could be exceeded by the download of three DVD-quality movies. Wilderotter said Frontier was looking at providing higher monthly limits, perhaps 20 gigabytes per month, in more urban markets like Rochester and Elk Grove, Calif., where usage is higher than rural areas. The company will also sell plans with higher download caps for higher prices, Wilderotter told The Associated Press, at increments like 10, 20 and 50 gigabytes. That sort of tiered pricing for Internet usage is being tested in Texas by Time Warner Cable Inc., which is also Frontier's competitor in Rochester. "All networks are going to have to move to that paradigm in order to stay profitable," Wilderotter said at a conference in New York. "The business model that we're using today really has our light users subsidizing our heavy users," she said. Internet usage can vary enormously from household to household. As an example, Wilderotter said 23 of its customers take up 28 percent of the network capacity in a town in West Virginia. Charging the heavy users more is fairer and makes sure that the company gets a return on investments in capacity upgrades, she said. The change to usage-based pricing, if it gains momentum, could have implications for companies like Netflix Inc. and Apple Inc. that are selling movie downloads, since those take up a lot of capacity. Comcast Corp., the country's largest cable company, on Oct. 1 made official a 250 gigabyte monthly limit, far higher than Frontier is contemplating. Previously, Comcast had a secret limit of similar size. Wilderotter said Comcast's move to set a high limit was likely a result of regulators coming down on the company for interfering with certain types of traffic from its subscribers. "I think it was more their way to appease being in the doghouse with the Federal Communications Commission," the CEO said. A Comcast spokeswoman said the company had no comment on Wilderotter's assertion. http://www.washingtonpost.com/wp-dyn...103102904.html  AT&T Starts Metered Billing Trial In Reno 20-150GB cap depending on tier, $1 per gigabyte overage fee Karl Bode Earlier this year, AT&T began laying the political and public relations groundwork for a shift toward metered billing, throwing comments to the press about how such a shift was "inevitable," while company lobbyists began dropping vague hints that a billing shift was coming. Last summer, executives at the company announced that the telco would be conducting a metered billing trial this fall. The time for that trial has arrived, and Broadband Reports has learned that Reno, Nevada will be the lucky first market. Last Friday, AT&T filed this notice with the FCC that confirms the nation's largest ISP will be conducting a metered billing trial in Reno. Existing flat-rate profits weren't to AT&T CTO John Donovan's liking, the exec complaining last summer that "traffic on our backbone is growing 60 percent per year, but our revenue is not." Earlier this year I floated the idea that the FCC's investigation of Comcast benefited AT&T in more ways than one, and the FCC's supposed love of transparency was in part aimed at opening the door to metered billing. AT&T's filing with the FCC is clear to highlight how much this new metered move is about AT&T's love of "transparency," not protecting U-Verse TV revenues from Internet video, or ramping up already impressive profits: Quote:
Should customers in Reno exceed the 150GB usage limit, AT&T is currently considering charging them an additional $1 per gigabyte. That's in line with Time Warner Cable's current metered usage trial, news of which we first broke earlier this year. Unlike Comcast, who also has implemented caps of 250GB per month, AT&T will be offering up a usage tool to impacted customers. The company will also provide some kind of automated alert (perhaps banner injection technology?) once a customer hits 80% of their monthly allotted capacity. From the AT&T FCC filing: Quote:
According to documents, AT&T may extend the trial into additional markets later this year, so Reno customers won't be the only lucky netizens to experience AT&T's new broadband profit vision. According to AT&T, it's for your own good. "This local market trial underscores our commitment to bring bigger, faster and smarter broadband networks to more and more communities at affordable rates," an announcement is expected to read. Update: AT&T Spokesman Seth Bloom contacts me to add: "One minor point I’d make - we may extend the trial to ONE other market by the end of the year...not markets plural..." http://www.dslreports.com/shownews/A...-In-Reno-98856  UK Music Industry and ISPs Near Illegal File Sharing Agreement MarkJ UK Music's chief executive, Feargal Sharkey, claims that progress has been made on a deal between the industry and broadband Internet Service Providers (ISP) to tackle illegal file sharing. Music Week states that the comments came during yesterdays annual Internet Service Providers' Association (ISPA) conference in Eversheds: Quote:
The initial agreement approved a principal of sending warning letters to customers that have been accused of downloading illegal music or movies. However little has been heard of the deal since then, although some ISPs have tested warning letters with suspected customers. http://www.ispreview.co.uk/news/EkkVlpulpAWVgKjyMP.html  House Arrest for Film Pirate Verashni Pillay In a landmark victory against film piracy, a man has been sentenced to three years house arrest and a suspended jail term after police seized 2 500 DVDs from his East London home. "Most of the sentences that we get in the courts are suspended sentences so the deterrent effect isn't that great," said James Lennox, CEO of The Southern African Federation Against Copyright Theft (Safact). "So we hope this is the beginning of a trend," he told News24. Safact was formed by companies in the entertainment industry and works with police, Customs, the Department of Trade and Industry and the Justice Department in enforcing intellectual property rights. Significant ruling Martin Scheepers was first charged for offences under the Copyright Act after the East London SAPS Specialised Commercial Crime Unit raided his house in February 2008, seizing pirated copies of films. He was sentenced on Thursday in the East London Magistrate's Court. "He must serve the full three years house arrest and there's an additional three years in prison which has been suspended for five years," said Lennox. While under house arrest Scheepers will also serve 16 hours community service every month, and is banned from using alcohol or drugs. Lennox said the level of piracy in South Africa was "unacceptably high", with Gauteng the worse affected area, followed by Cape Town and Durban. But he added that noticeable progress was being made in the fight against piracy, particularly in Gauteng. Safact says film and game piracy in South Africa costs legitimate business some R400m each year. South Africa is party to most international conventions protecting intellectual property and the Counterfeit Goods Act and Intellectual Property Laws Amendment Act prohibit dealing in counterfeit goods. http://www.news24.com/News24/South_A...419112,00.html  No More Pirated DVDs from China...Maybe Dong Ngo If you've been copying DVDs using some made-in-China DVD player, think about taking good care of the device, as you might not be able to buy a replacement. The Motion Picture Association of America on Friday announced that its member companies have won a breach of contract lawsuit against China-based DVD player manufacturer Gowell Electronics Limited. The U.S. District Court for the Central District of California issued a permanent injunction that prohibits the manufacturer from violating any term of the Content Scramble System license agreement. The lawsuit started in June of 2008 after an MPAA investigation revealed that Gowell was manufacturing and selling DVD players that lacked the appropriate implementation of the CSS license agreement. CSS technology is a security measure that controls unauthorized access to and copying of copyrighted content on DVDs. The CSS license mandates the content protection that enables film studios to provide consumers with more than 84,000 DVD titles, including 12,000 new titles last year alone. The motion picture studios are third-party beneficiaries of the CSS license and may enforce it against licensees who fail to comply with its terms. While this is the ninth such case in which a court has issued a permanent injunction banning future violations of the license, this time the plaintiffs are allowed to review and test any new or re-engineered products that incorporate the CSS technology before going to market. According to the MPAA, worldwide motion picture industry losses total more than $11 billion annually to hard goods piracy, including bootlegging and illegal copying. MPAA member companies have now won three injunctions against noncompliant DVD player manufacturers and six against companies in the IT area. They intend to continue pursuing other violators vigorously through future litigation. Personally, I think it's interesting how MPAA counts the money it doesn't make as losses. I am not so sure if the Chinese company would comply 100 percent with the court order, either. And even if it does, I don't know what good that would do to general consumers, like you and me. http://news.cnet.com/8301-1023_3-10080559-93.html  MySpace, MTV Test Piracy-Profit Plan Andrew Wallenstein A new technology that essentially allows content owners to profit from piracy will get a high-profile test this month from MySpace and MTV Networks. Instead of triggering the usual take-down notices, copyright-infringing footage of select MTV Networks programing uploaded by MySpace subscribers would be automatically redistributed with advertisements that would generate revenue for the companies. MTV Networks is the parent company of such channels as MTV, BET, Comedy Central, Spike and Nickelodeon. MySpace is turning to third-party tech firm Auditude to deliver the technology through a combination of patented assets: a sophisticated ad-serving platform with a video-fingerprinting system that cross indexes billions of seconds of TV and online footage in seconds. "This is a game-changer," said Jeff Berman, president of sales and marketing at MySpace. "We're going from a world of no to a world of yes while protecting the rights of the copyright holder." MTV Networks is allowing only a mix of a handful of current and archived series to be tracked by Auditude, including MTV series "Punk'd" and "True Life" as well as even more Comedy Central series, including "The Daily Show With Jon Stewart," "The Colbert Report" and "Reno 911." The Auditude technology is similar to a system already being employed by the only site that has more traffic than MySpace: YouTube. The site's Content Identification tool gives content owners the choice of removing infringing material or serving an ad. In success, these systems have profound implications for the online video marketplace. With marketers reluctant to sign on to anything that doesn't deliver TV-sized audiences, the prospect of reclaiming pirated content would in theory exponentially expand the reach of programing carrying their ads. The MTV Networks initiative comes even as its parent company, Viacom, remains embroiled in a long-running legal battle with Google over claims that YouTube enabled massive copyright infringement of the conglomerate's content. Mika Salmi, president of global digital media at MTV Networks, drew a distinction between the efforts of MySpace and YouTube. "This deal with MySpace is quite different," Salmi said. "MySpace has always respected copyright and is more progressive about copyright in our mind. The way we're pushing this out with Auditude and MySpace is different than with YouTube or our past associations there." The ads served through Auditude are called "attribution overlay," a semitransparent strip that covers the lower third of the video player. Although the exact formatting of the overlay will vary as the companies experiment, it will identify the channel that provides the program as well as links to either see a full-length episode or purchase a download. In addition, the overlay can convey a separate brand message from an advertiser that could trigger a second video within the player. http://www.reuters.com/article/techn...4A20P520081103  New MP3 Logo Gets Online Support BBC  Seven of Britain's largest music download sites have got together to promote a new "MP3 compatible" logo. It aims to raise the profile of the open MP3 music format and show people what they can do with their downloads. The trade body behind the initiative said it should also help consumers identify legal sites. The Entertainment Retailers Association devised the logo, which emphasises the fact that MP3 files can be played on any digital player. Boom time HMV, Woolworths, 7digital, Digitalstores, Tescodigital, Tunetribe, and Play.com have all signed up to the scheme, which will show consumers that the MP3 download will play on PCs, Macs, and portable music players. According to October figures from the Official UK Charts Company, single track downloads were up 41% and album downloads increased 69% from the previous year. 7digital's Ben Drury said that online sales "have been booming" because users "love the freedom of MP3". "The beauty of an MP3 file is that once you have bought it, you don't need to be a computer genius or a lawyer to make it work and you are not locked in to a relationship with a single retailer or hardware manufacturer," he said. The British record industry's trade association, the BPI, is also backing the scheme. Geoff Taylor, BPI chief executive, said: "This logo will not only help give consumers confidence that the music files they are buying will play on a wide range of devices, but will also help them know that they are legal and that artists are getting paid." It is hoped the MP3-compatible logo will form the blueprint of an international standard and ERA is also seeking support from manufacturers of MP3-compatible digital music players. http://news.bbc.co.uk/1/hi/technology/7708268.stm  Apple Faces More Pressure Over iPod Exclusivity in Norway Norway's consumer mediator said Thursday he would take US electronics manufacturer Apple's iTunes before a government agency for failing to make its online store compatible with music players other than its iPod. "iTunes has shown a lacking will to comply with our demand and we are now preparing to try this case in the Market Council," Consumer Ombudsman Bjoern Erik Thon said in a statement. At the end of September, Thon gave Apple until November 3 to respond to his demands that it break the exclusive link between its iPod music player and online iTunes store. In 2006, Norway was among the first countries in the world to insist that Apple break that link. Apple has added several precisions to its user conditions, explaining to consumers how to burn songs onto compact discs and then convert them to the MP3 format so they can be played on other devices, but the Consumer Ombudsman has said that is not enough. "iTunes maintains its previous views in its response to the Consumer Ombudsman. The company is in other words unwilling to make changes to make music in the iTunes Store available to all music players," the agency said in its statement http://uk.news.yahoo.com/18/20081106...d-e0bba4a.html  Report: EMI To Outsource U.S. Ops? FMQB According to a report, EMI is exploring the possibility of outsourcing its distribution, sales and marketing operations in the United States in an attempt to cut its losses. The company could save as much as $300 million a year if it completely outsourced its American marketing and distribution operation, a source told Fortune. Sources also said that EMI is talking to Warner Music Group, Sony Music Entertainment and Universal Music Group about assuming those functions in the U.S. Others said that all EMI wants to do in the U.S. is outsource its CD distribution to retailers like Wal-Mart and Best Buy. It wouldn't be the first time something like this has happened at EMI. In September, the company turned over the distribution and marketing of its physical and digital releases in Hong Kong, Indonesia, Malaysia, Singapore, Korea and Thailand to Warner Music Group. The news of similar talks for EMI's U.S. operations comes after the company reported a steep loss of £757 million, or $1.2 billion, on October 24. The report was for the fiscal year ending March 31 and included an introduction from Lord Birt, a former BBC executive who is now an advisor to Terra Firma head Guy Hands, who controls EMI. Birt said that despite the losses, "continuing underperformance from EMI Music" and "the absence of rosy assurances about the future," all hope is not lost. The report "does not signal any lack of confidence in EMI, but sets out the problems that were faced in the year." Birt added that EMI's costs were too high and that its system was unable to tell how profitable its individual music acts were. EMI's year-to-date market share of current U.S. album sales is 8.2 percent, which is down from 9.1 percent during the same time last year. http://fmqb.com/Article.asp?id=965815  Peruvian-Born Singer Yma Sumac Dies in Los Angeles AP Yma Sumac, the Peruvian-born soprano who wowed international audiences in the 1950s with her stunning vocal range and modern take on South American folk music, has died. Sumac died Saturday at an assisted-living home in Los Angeles after an eight-month bout with colon cancer, Sumac's friend and personal assistant Damon Devine said Monday. Few biographical details are clear about the reclusive, raven-haired songstress. She was surrounded by rumors about her life and origins, many of them myths of her own making. Yma Sumac (EE mah SOO mak) said she was born in 1927, but Devine said her birth certificate read 1922 and she was 86. She claimed to be a descendant of the Inca emperor Atahualpa, and played up her Andean origins. Dubbed the ''Peruvian Songbird'' and the ''Nightingale of the Andes,'' Sumac's soaring, warbling voice -- reported to span well over three octaves -- was matched by her flamboyant outfits, studded with gold and silver jewelry, designed to make her look like an Incan princess. Los Angeles Times music critic Don Heckman called her ''a living, breathing, Technicolor musical fantasy -- a kaleidoscopic illusion of MGM exotica come to life in an era of practicality.'' Sumac's birth name was Zoila Augusta Emperatriz Chavarri del Castillo. Devine said she was born in Cajamarca, Peru, on Sept. 13, 1922. Sumac married Moises Vivanco, a composer, bandleader and early collaborator who was captivated by her voice, in 1942, the same year she first appeared on the radio. ''She is five singers in one,'' Vivanco told the Associated Press in 1951. ''Never in 2,000 years has there been another voice like hers.'' She changed her name to Imma Sumack, with the spelling shortened to Yma Sumac when she came to the United States and signed with Capitol records. Her first album for Capitol, ''Voice of the Xtabay'' in 1950, sold half a million copies and launched a decade of fame that included memorable performances at Carnegie Hall and the Hollywood Bowl in an era when American audiences had a hunger for all things ''exotic.'' Sumac appeared in the Sammy Fain Broadway musical ''Flahooley,'' playing an Arab princess in 1951, and in the films ''Secret of the Incas'' with Charlton Heston in 1954 and ''Omar Khayyam'' in 1957. Her American fame would largely fade in the 1960s. She made a rock album called ''Miracles'' in 1971, reissued in 1998 as ''Yma Rocks!'' She lived in Peru and Los Angeles in recent decades, and had few friends. ''She was reclusive and untrusting,'' Devine said. ''She lived a very, very solitary life.'' Devine, a professional makeup artist who befriended Sumac 11 years ago, said he would apply her makeup in her elaborate 1950s style every day during her illness. He said the more her mind faded with age, the more she dwelled on her musical heyday. ''It was always, always, always the 50s,'' Devine said. ''After a while her memory sort of stopped after the late 50s.'' Sumac earned a cult following among alternative and lounge music fans in the 1990s, and her music appeared on the soundtracks of many movies, including ''The Big Lebowski.'' When asked a question about legendary French singer Edith Piaf in an AP interview earlier this year, comedian Jon Stewart quipped: ''She's no Yma Sumac.'' An exhaustive anthology of Sumac's music, ''Queen of Exotica,'' was released in 2005. Sumac and Vivanco divorced in 1965. She is survived by their son, Charles. http://www.nytimes.com/aponline/arts/AP-Obit-Sumac.html  Author Michael Crichton Has 'Died Unexpectedly' Prolific novelist and "ER" creator Michael Crichton has passed away. He was 66. Perhaps best known for being the author of Jurassic Park and its sequel The Lost World, which were turned into a hugely successful movie franchise, his numerous books have sold over 150 million copies worldwide. In what his family calls an unexpected death, it was revealed that he was waging a private battle against cancer. "While the world knew him as a great storyteller that challenged our preconceived notions about the world around us -- and entertained us all while doing so -- his wife Sherri, daughter Taylor, family and friends knew Michael Crichton as a devoted husband, loving father and generous friend who inspired each of us to strive to see the wonders of our world through new eyes," his family tells ET. "He did this with a wry sense of humor that those who were privileged to know him personally will never forget." http://www.etonline.com/news/2008/11/67369/  Professors’ Liberalism Contagious? Maybe Not Patricia Cohen An article of faith among conservative critics of American universities has been that liberal professors politically indoctrinate their students. This conviction not only fueled the culture wars but has also led state lawmakers to consider requiring colleges to submit reports to the government detailing their progress in ensuring “intellectual diversity,” prompted universities to establish faculty positions devoted to conservatism and spurred the creation of a network of volunteer watchdogs to monitor “political correctness” on campuses. Just a few weeks ago Michael Barone, a fellow at the conservative American Enterprise Institute, warned in The Washington Times against “the liberal thugocracy,” arguing that today’s liberals seem to be taking “marching orders” from “college and university campuses.” But a handful of new studies have found such worries to be overwrought. Three sets of researchers recently concluded that professors have virtually no impact on the political views and ideology of their students. If there has been a conspiracy among liberal faculty members to influence students, “they’ve done a pretty bad job,” said A. Lee Fritschler, a professor of public policy at George Mason University and an author of the new book “Closed Minds? Politics and Ideology in American Universities” (Brookings Institution Press). The notion that students are induced to move leftward “is a fantasy,” said Jeremy D. Mayer, another of the book’s authors. When it comes to shaping a young person’s political views, “it is really hard to change the mind of anyone over 15,” said Mr. Mayer, who did extensive research on faculty and students. “Parents and family are the most important influence,” followed by the news media and peers, he said. “Professors are among the least influential.” A study of nearly 7,000 students at 38 institutions published in the current PS: Political Science and Politics, the journal of the American Political Science Association, as well as a second study that has been accepted by the journal to run in April 2009, both reach similar conclusions. “There is no evidence that an instructor’s views instigate political change among students,” Matthew Woessner and April Kelly-Woessner, a husband-and-wife team of political scientists who have frequently conducted research on politics in higher education, write in that second study. Their work is often cited by people on both sides of the debate, not least because Mr. Woessner describes himself as politically conservative. No one disputes that American academia is decidedly more liberal than the rest of the population, or that there is a detectable shift to the left among students during their college years. Still, both studies in the peer-reviewed PS, for example, found that changes in political ideology could not be attributed to proselytizing professors but rather to general trends among that age group. As Mack D. Mariani at Xavier University and Gordon J. Hewitt at Hamilton College write in the current issue, “Student political orientation does not change for a majority of students while in college, and for those that do change there is evidence that other factors have an effect on that change, such as gender and socioeconomic status.” That may be, said Daniel Klein, an economist at George Mason, but those results don’t necessarily mean there isn’t a problem. Mr. Klein, whose research has shown that registered Democrats vastly outnumber Republicans among faculty in the humanities and social sciences at American colleges and universities, maintains that the focus on the liberal-conservative split is misdirected. Such terms are vague and can be used to describe everything from attitudes about religion and family to the arts and lifestyles, he said. The real issue, said Mr. Klein, who calls himself a libertarian, is that social democratic ideas dominate universities — ideas that play down the importance of the individual and promote government intervention. Such “academic groupthink” means that the works of such thinkers are not offered enough, he argues. “A major tragedy is that they’re not getting exposed to the good stuff,” he said, citing the works of John Stuart Mill, Adam Smith, Friedrich Hayek and Milton Friedman. “Even if we had hard, definite evidence that students weren’t influenced by their professors, there is still reason for great concern about the composition of the faculty,” Mr. Klein added. K. C. Johnson, a historian at the City University of New York, characterizes the problem as pedagogical, not political. Entire fields of study, from traditional literary analysis to political and military history, are simply not widely taught anymore, Mr. Johnson contended: “Even students who want to learn don’t have the opportunity because there are no specialists on the faculty to take courses from.” “The conservative critics are inventing a straw man that doesn’t exist and are missing the real problem that does,” he added. Anne Neal, the president of the American Council of Trustees and Alumni, which closely follows this issue, agrees that “it is not about left and right.” Many researchers and critics also agree that a better grounding in American history and politics is important. “It wasn’t too long ago that schools and universities required civic education and American history,” Mr. Fritschler noted. “Almost all of those requirements have evaporated.” A number of organizations that have a large base of conservative supporters, like Ms. Neal’s council and the National Association of Scholars, have been promoting a return to traditional courses in western civilization and American history. Mr. Fritschler said that perhaps the most insidious side effect of assumptions about liberal influence has been an overall disengagement on campus from civic and political affairs, and a reluctance to promote serious debate of political issues. If anything, he added, the problem is not too much politics, but too little. http://www.nytimes.com/2008/11/03/books/03infl.html  Court Wrestles with TV Profanity Case Mark Sherman A divided Supreme Court spent an hour on Tuesday talking about dirty words on television without once using any. There was no apparent consensus on the court about what to do in the dispute between the broadcast networks and the Federal Communications Commission over celebrities' one-time uses of profanity on live television during hours when children are likely to be watching. The court's first major broadcast indecency case in 30 years deals with whether the government can ban these "fleeting expletives." The court could avoid deciding whether the FCC policy violates the Constitution and instead determine that the FCC did not adequately explain why it changed its mind in 2004 and instituted the ban. The words in question begin with the letters "F" and "S." The Associated Press typically does not use them. "The reason these words shock is because of their association with a literal meaning," Chief Justice John Roberts said, suggesting his support for the policy. Roberts is the only justice with young children at home. Justice Antonin Scalia, who has more than 20 grandchildren, also said he sees nothing wrong with clamping down on the use of bad words on television and blamed the networks for coarsening the language. On the other side, Justice John Paul Stevens indicated that he believes Americans are more tolerant of vulgarities than they were when the court ruled 30 years ago that the FCC could keep profanities off the airwaves between 6 a.m. and 10 p.m. It was hard to tell where the court is heading because three justices — Samuel Alito, Anthony Kennedy and Clarence Thomas — said little or nothing. For many years, the FCC did not ordinarily enforce prohibitions against indecency unless there were repeated occurrences. But in 2004, the commission changed the rules after Bono, Cher and Nicole Richie used familiar but profane words during awards programs in 2002 and 2003. A federal appeals court in New York threw out the ban, saying the FCC didn't provide enough explanation, and the government appealed to the Supreme Court. The appeals court also said, but did not rule, that the new policy probably is unconstitutional. The FCC has authority to regulate speech on broadcast radio and television stations, but not the Internet, cable and satellite TV. C-SPAN asked the court to release a recording of the arguments for airing shortly after their conclusion. The court grants such requests from time to time, but turned down C-SPAN with no explanation. The case is FCC v. Fox Television Stations, 07-582. Fox Television Stations is owned by Rupert Murdoch's News Corp.[/i] http://ap.google.com/article/ALeqM5i...t0BZgD9488Q780  "Little House on the Prairie," Adults-Only Version! Finland has rated the DVD release of the much-loved children's television series "Little House on the Prairie" suitable for adult viewing only. To save money, Universal Pictures decided not to submit the series to state inspection, the company's Finland marketing manager Meri Suomela told Reuters on Wednesday. Finnish authorities charge 2 euros ($2.57) per minute for assessing the correct age limit on films and television series. Distributors who forego this can only sell their shows with a sticker saying "Banned for under-18s." "Long series can get quite expensive to check, and some use this exemption in the law to their advantage," said Matti Paloheimo, Director at the Finnish Board of Film Classification. "Such unchecked material should not be shown to children publicly," he added. Little House on the Prairie, which ran from 1974 to 1983, portrayed life in the U.S. West in the late 1800s and was based on the Laura Ingalls Wilder's children's book of the same name. It remains popular in Finland, and is still shown weekly on Sunday mornings on state-owned broadcaster YLE. (Reporting by Sakari Suoninen; Editing by Louise Ireland) http://www.reuters.com/article/newsO...4A572J20081106  Study Links Teen Pregnancy to Sexy TV Shows Andrew Stern Exposure to some forms of entertainment is a corrupting influence on children, leading teens who watch sexy programs into early pregnancies and children who play violent video games to adopt aggressive behavior, researchers said on Monday. Researchers at the RAND research organization said their three-year study was the first to link viewing of racy television programing with risky sexual behavior by teens. "Our findings suggest that television may play a significant role in the high rates of teenage pregnancy in the United States," said Anita Chandra, a behavioral scientist who led the research at RAND, a nonprofit research organization. "We're not saying we're establishing causation, but we are saying this is one factor that we were able to prospectively link to the teen pregnancy outcome," Chandra said in a phone interview. The researchers recruited adolescents aged 12 to 17 and surveyed them three times between 2001 and 2004, asking about television viewing habits, sexual behavior and pregnancy. In findings that covered 718 teenagers, there were 91 pregnancies. The top 10th of adolescents who watched the most sexy programing were at double the risk of becoming pregnant or causing a pregnancy compared to the 10th who watched the fewest such programs, according to the study published in the journal Pediatrics. The study focused on 23 free and cable television programs popular among teenagers including situation comedies, dramas, reality programs and animated shows. Comedies had the most sexual content and reality programs the least. "The television content we see very rarely highlights the negative aspects of sex or the risks and responsibilities," Chandra said. "So if teens are getting any information about sex they're rarely getting information about pregnancy or sexually transmitted diseases." Teen Pregnancy On Decline Teen pregnancy rates in the United States have declined sharply since 1991 but remain high compared to other industrialized nations. Nearly 1 million girls aged 15 to 19 years old become pregnant yearly, or about 20 percent of sexually active females in that age group. Most of the pregnancies were unplanned, the report said. Young mothers are more likely to quit school, require public assistance and live in poverty, it said. "Television is just one part of a teenager's media diet that helps to influence their behavior. We should also look at the roles that magazines, the Internet and music play in teens' reproductive health," Chandra said, acknowledging still other factors can influence teen sex habits. Living in a two-parent family reduced the chances of a teen getting pregnant or causing a pregnancy. Black teenagers, and those with discipline problems, had higher risks. The report suggested broadcasters provide more realistic portrayals of the consequences of sex and that parents limit their children's access to sexually explicit programing. A second study in the journal added to existing evidence that youths who play violent video games -- a worldwide trend with American children averaging 13 hours of video gaming a week -- led to increased physically aggressive behavior. Researchers from the United States and Japan evaluated more than 1,200 Japanese youths and 364 Americans between 9 and 18 years old and found a "significant risk factor for later physically aggressive behavior ... across very different cultures." Aggressiveness in children is also associated with violence later on, according to the study by researchers from Iowa State University in Ames, the National Institute on Media and the Family in Minneapolis and Ochanomizu University and Keio University in Tokyo. (Editing by Todd Eastham) http://www.reuters.com/article/domes...4A20HL20081103  Tool to Help Fight Child Porn Jennifer Foreshew TECHNOLOGY that has been likened to a "random breath test" for computers and laptops for illicit images or video has captured the interest of law enforcement bodies nationally, including the Australian Federal Police. The tool has been developed at Perth's Edith Cowan University in partnership with Western Australia Police, which is in the early stages of beta-testing the technology. The system enables frontline officers - regardless of computer competency or level of training - to know on the spot if a computer contains illicit images or video. Its main purpose is to capture users of child pornography. The tool, which has received additional input from the AFP, is planned for release early next year. Known as Simple Image Preview Live Environment (SImPLE), the tool is heralded as the new frontier fighting cybercrime. It uses a cut-down version of a Linux kernel and can be deployed on almost any standard operating system. WA Police computer crime squad Detective Senior Sergeant Tim Thomas said the tool would enable investigators to more quickly access information relevant to cases. "Assuming that SImPLE goes the way we hope, we would plan for a very wide deployment in the agency," he said. SImPLE would also reduce the volume of work computer forensic specialists were being asked to perform. Some 30-60 per cent of the case load for computer crime specialists globally relates to child pornography. "If the project is satisfactorily completed, we would certainly be encouraging its release as widely as possible because it is going to improve policing and services to the community," Sergeant Thomas said. Craig Valli, co-director of the university's security research group SECAU, based in the School of Computer and Information Science, said a final release version of the tool was expected by the end of February. Associate Professor Valli said a range of government agencies, including Customs, had shown interest in the tool. "Particularly for Customs at the border, that sort of stuff is a problem," he said. Professor Valli, who is also head of the university's School of Computer and Information Science, said police required a simple tool that could eliminate the need for highly trained experts to undertake initial profiling of evidence. "The design concept is that any police person with adequate training could use the tool, so that when they go into a crime scene they can quickly review a computer for illicit images or videos," he said. "It is not digging down into the hard drive to find anything that has been deleted, it is just what is topically available." Professor Valli said computers that were seized were usually bagged, tagged and taken to a lab to be investigated. "This cuts out that loop because it allows officers to preview the computer. "If they find evidence this allows them to write images to a disc and take it to a judge straight away." SImPLE is a Linux-bootable CD that is put into the CD-ROM drive of a computer or laptop and boots into its own forensically clean environment. "The disc goes into the CD-ROM drive of the PC and if files are found, the user connects a USB-DVD writer to the back of the computer, and the images that are stored in memory in the RAM of the computer are written to the DVD," Professor Valli said. "Nothing gets written to the original evidence at all, which is the key." This means the technology can be used in court and an accused cannot challenge it on the basis of forensics. SECAU was also considering another purpose-built CD to search financial documents for use by a fraud squad or those hunting terrorists using keywords. The team is exploring commercialisation opportunities for the tool, using a low-cost licence model. "We are talking to people about commercialising it in Britain and further afield as well," Professor Valli said. The AFP planned to test and evaluate the final SImPLE product when it was completed, a spokesman said. http://www.australianit.news.com.au/...-15306,00.html  Violent Video Games Linked to Child Aggression Anne Harding About 90 percent of U.S. kids ages 8 to 16 play video games, and they spend about 13 hours a week doing so (more if you're a boy). Now a new study suggests virtual violence in these games may make kids more aggressive in real life. Kids shouldn't play games where hunting down and killing people is the goal, says one expert. Kids in both the U.S. and Japan who reported playing lots of violent video games had more aggressive behavior months later than their peers who did not, according to the study, which appears in the November issue of the journal Pediatrics. The researchers specifically tried to get to the root of the chicken-or-egg problem -- do children become more aggressive after playing video games or are aggressive kids more attracted to violent videos? It's a murky -- and controversial -- issue. Many studies have linked violence in TV shows and video games to violent behavior. But when states have tried to keep under-18 kids from playing games rated "M" for mature, the proposed restrictions have often been challenged successfully in court. In the new study, Dr. Craig A. Anderson, Ph.D., of Iowa State University in Ames, and his colleagues looked at how children and teen's video game habits at one time point related to their behavior three to six months later. The study included three groups of kids: 181 Japanese students ages 12 to 15; 1,050 Japanese students aged 13 to 18; and 364 U.S. kids ages 9 to 12. The U.S. children listed their three favorite games and how often they played them. In the younger Japanese group, the researchers looked at how often the children played five different violent video game genres (fighting action, shooting, adventure, among others); in the older group they gauged the violence in the kids' favorite game genres and the time they spent playing them each week. Japanese children rated their own behavior in terms of physical aggression, such as hitting, kicking or getting into fights with other kids; the U.S. children rated themselves too, but the researchers took into account reports from their peers and teachers as well. In every group, children who were exposed to more video game violence did become more aggressive over time than their peers who had less exposure. This was true even after the researchers took into account how aggressive the children were at the beginning of the study -- a strong predictor of future bad behavior. The findings are "pretty good evidence" that violent video games do indeed cause aggressive behavior, says Dr. L. Rowell Huesmann, director of the Research Center for Group Dynamics at the University of Michigan's Institute for Social Research in Ann Arbor. There are two ways violent media can spur people to violent actions, said Huesmann, who has been studying violence in media and behavior for more than 30 years. Read about the celebrity-mom slugfest over vaccines First is imitation; children who watch violence in the media can internalize the message that the world is a hostile place, he explains, and that acting aggressively is an OK way to deal with it. Also, he says, kids can become desensitized to violence. "When you're exposed to violence day in and day out, it loses its emotional impact on you," Huesmann said. "Once you're emotionally numb to violence, it's much easier to engage in violence." Read how children may not outgrow bipolar disorder But Dr. Cheryl K. Olson, co-director of the Center for Mental Health and the Media at Massachusetts General Hospital in Boston, isn't convinced. "It's not the violence per se that's the problem, it's the context and goals of the violence," said Olson, citing past research on TV violence and behavior. There are definitely games kids shouldn't be playing, she said, for example those where hunting down and killing people is the goal. But she argues that the label "violent video games" is too vague. Researchers need to do a better job at defining what is considered a violent video game and what constitutes aggressive behavior, she added. "I think there may well be problems with some kinds of violent games for some kinds of kids," Olson said. "We may find things we should be worried about, but right now we don't know enough." Further, she adds, playing games rated "M" for mature has become "normative behavior" for adolescents, especially boys. "It's just a routine part of what they do," she says. Read why food allergies in children are on the rise Her advice to parents? Move the computer and gaming stuff out of kids' rooms and into public spaces in the home, like the living room, so they can keep an eye on what their child is up to. Dr. David Walsh, president of the National Institute on Media and the Family, a Minneapolis-based non-profit, argues that the pervasiveness of violence in media has led to a "culture of disrespect" in which children get the message that it's acceptable to treat one another rudely and even aggressively. "It doesn't necessarily mean that because a kid plays a violent video game they're immediately going to go out and beat somebody up," Walsh says. "The real impact is in shaping norms, shaping attitude. As those gradually shift, the differences start to show up in behavior." http://www.cnn.com/2008/HEALTH/famil...ids/index.html  Surfing Violent Websites Linked to Violent Behavior Young people exposed to violent media are more likely to lash out violently themselves, new research published in Pediatrics shows. "Our findings add to the growing evidence that violence in the media is related to aggressive behavior, including seriously violent behavior among youths," Dr. Michele L. Ybarra of Internet Solutions for Kids in Santa Ana, California and her colleagues report. "Reduction in youths' exposure to violent media should be viewed as an important aspect of violence prevention." Many studies have examined exposure to violent media and violent behavior among young people, Ybarra and her team note in their report. In fact, they point out, the American Academy of Pediatrics calls media violence "the single most easily remediable contributing factor" to youth violence. The researchers examined the relationship between media violence and "seriously violent behavior," defined as shooting or stabbing someone, robbing someone, or committing aggravated assault or sexual assault, in a survey of 1,588 young people 10 to 15 years old. The average age was 13 years old and 48 percent were girls. Five percent of those surveyed reported having engaged in some type of seriously violent behavior over the past year, while 38 percent said they had visited at least one type of violent website. With each additional type of violent website a study participant reported viewing, the likelihood of violent behavior increased by 50 percent. Young people who said that "many, most or all" of the Internet sites they frequented featured "real people fighting, shooting or killing" were five-times more likely than their peers who didn't visit violent websites to engage in seriously violent behavior. The odds of violent behavior also rose with the number of types of violent media a young person consumed, but the effect of violent TV, movies, music, games or Internet cartoons was much smaller than that of Internet violence depicting real people. The interactive nature of the Web may be behind its apparently more powerful influence when compared with types of violent media, Ybarra and colleagues suggest. But the current study doesn't answer the question of whether violent media is turning kids violent, whether violence-prone youth are more likely to seek out violence on the Internet, or "more probably," whether a bit of both is going on, the researchers say. http://www.washingtonpost.com/wp-dyn...110501161.html  #@*!!! Anonymous Anger Rampant on Internet Todd Leopold There's a whole world of people out there, and boy, are they pissed off. The anonymity of the Internet encourages online ranting, from election-season tirades to mockery of celebrities. On political blogs, the invective flies. Posters respond to the latest celebrity gossip with mockery or worse. Sports fans set up Web sites with names that begin with "fire," hoping coaches, athletic directors and sportscasters lose their jobs. And though there are any number of bloggers and commenters who attempt to keep their postings and responses on a civil level, all too often interactive Web sites descend into ad hominem attacks, insults and plain old name-calling. Indeed, there are even whole sites devoted to venting, such as justrage.com (one screed there was titled, "I don't give a flying f***, so f*** you") and mybiggestcomplaint.com. This is not a world Emily Post would want to be caught in after dark. "The Internet can be a great tool," said Sara Black, a professor of health studies at St. Joseph's University who takes a particular interest in online bullying. "Like any tool, it can also be misused." See examples of Internet anger » One reason for the vitriol that emerges on the Web, experts say, is the anonymity the Internet provides. Commenters seldom use their real names, and even if they do, the chance for retaliation is slim. "In the [pre-Internet era], you had to take ownership [of your remarks]. Now there's a perception of anonymity," said Lesley Withers, a professor of communication at Central Michigan University. "People think what they say won't have repercussions, and they don't think they have to soften their comments." Contrast that with a face-to-face conversation, or even a phone conversation, where you can judge people's moods from facial movements or vocal inflections, observes University of Texas psychology professor Art Markman. "It's hard to be aggressive when you're face to face," he said. Moreover, he points out, aggression often carries a subtext of power. "A lot of times, real anger is an attempt to get control over a situation where the person doesn't usually have it," he said. In that respect, comments to blog posts are attempts to strike back. Those power games are innately grasped by children and teens, with schools serving as a perennial social laboratory. Cheryl Dellasega, a Penn State women's studies professor, ticks off hypothetical examples that could have come straight from the scripts to "Mean Girls" or "Heathers." "Girls who are getting teased come home and let their [aggressors] have it by putting something on their blog and starting a rumor campaign," she said. And instead of rumors simply making the rounds among peer groups -- which can be bad enough -- "they go out to a much bigger group, a worldwide group. The impact is devastating, and it's as easy as clicking a button." "Kids don't realize that one post can destroy somebody's life forever," she added. Indeed, such incidents have made headlines. In 2006, 13-year-old Megan Meier committed suicide after becoming attracted to a boy on MySpace who then turned on her. The boy turned out to be a hoax created by a neighbor family that included a former friend of Meier's. In August, The New York Times Magazine did a story about trolls, some barely out of their teens, who antagonize others for the sake of "lulz": "Lulz is watching someone lose their mind at their computer 2,000 miles away while you chat with friends and laugh," one ex-troll told the publication. Adults aren't immune by any means. A Japanese woman, angry at her online "husband," killed his avatar after he divorced her. A South Korean actress committed suicide after being harassed by online rumors following a divorce. Celebrity gossip sites are full of snarky comments about stars; reaction from readers is often brutal, turning the story into the online equivalent of a pile-on. Markman is quick to observe that he doesn't believe there's more anger out there. But, he said, "there are more ways of expressing it on the Internet." "We've all had interactions with unpleasant people, but we don't confront them. We take it out elsewhere," he said. "What the Internet has created is groups of people where there are no repercussions with being too aggressive." Indeed, though electronically transmitted anger has parallels throughout human history -- the bitter letter, the village gossip -- the speed at which it travels, and the number of people who may come in contact with it, is something new, says St. Joseph's Black. "[Electronic] media can increase potential for violence in a number of ways," she said in an e-mail interview. "First, it introduces ideas (good and bad) that people may not have come up with on their own. Second, it is easier to depersonalize the victim, facilitating perpetration. Third, aggressive behaviors may be reinforced with points, attention or status, especially in games." Withers has seen that first hand. She teaches a course on the "dark side of communication" at Central Michigan, involving "the mean or evil things we do on a day-to-day basis," as she describes it: cheating, for example, or lying. As part of the course, several of her students work on a collaborative project with students at other schools, and they come together in Second Life, the virtual reality environment. If someone isn't pulling his or her weight, says Withers, others can be harsh in their judgments -- harsher than in real life, because the anger is expressed at the person's avatar. Sidebar: Dealing with anger in Second Life Which led at least one of Withers' students to forget that the avatar was attached to a real person. "One student went off on another student and she was sitting in the classroom a few rows behind him," she said. "He knew she was there, but didn't -- there was that distancing." Is there a way to restore civility to the Internet? Among children and teenagers, say Dellasega and Black, it's up to parents to exercise control. "I think parents need to take responsibility," Dellasega said. "They give kids computers and leave them alone. ... When a child is 8 or 9, the computer should be in a public place. Kids should understand that using a computer is a privilege, not a right." Schools can also play a role, she says. Black adds that parents should set clear rules on behavior and build empathy in their kids by having them reach out to those who are different. As for adults, human nature dictates that people will always lash out at others, whether it's over a perceived insult or simply because of a power differential. Web sites may ban the worst offenders, but they'll almost always pop up elsewhere, using a different name, e-mail address or even computer. "Some people are just bitter and angry," said psychiatrist Dr. Terry Eagan, medical director of the Moonview Sanctuary in Santa Monica, California. "Sometimes, they're against everyone, other times against a specific group. That person can get really stimulated and can say all sorts of horrible things. But I don't think it's not like they didn't exist before." Whether the problem will get control of us, or we will get control of the problem, is in the way we face up to it, he says. Anger, he says, is rolled up with anxiety and fear, and nothing creates more fear like a lack of understanding. "I tell patients that I'd rather know everything about people; information is powerful," he said. "When the climate of the world is more fear-based, it permeates everything." http://www.cnn.com/2008/TECH/11/03/a...net/index.html  New Detergent Washes Away Stains of Murder: Study Ben Harding A new generation of cleaning products could help criminals get away with murder by making bloodstains invisible to forensic tests, Spanish researchers said Wednesday. A team at the University of Valencia found that new washing powders and other chemicals that generate oxygen rather than use chlorine erase telltale traces of hemoglobin, the protein inside blood that transports oxygen around the body. Police often rely on blood-splattered clothing to link a murderer to a crime. Even after 10 washes, forensic experts have been able, up to now, to identify blood using a cocktail of chemicals to unmask the stains. But new detergents like Reckitt Benckiser's 'Vanish' that contain the active ingredient sodium carbonate peroxyhydrate produce a fizz of oxygen bubbles that degrade blood even though the stain may remain visible to the naked eye, according to the study published in the German journal Naturwissenschaften and reported in the New Scientist. Fernando Verdu, a forensic scientist at the University of Valencia, said his three-member team would next investigate if the new oxygen-producing chemicals also destroyed DNA, which can provide crucial evidence in murder investigations. "The majority of criminals are not that smart. They don't do things as you expect them to and read this kind of news. It is very simple to commit a crime, the difficult part is to not get caught," said Verdu. http://www.reuters.com/article/scien...4A498620081105  Four Google Officials Likely to Stand Trial in Italy Jeremy Kirk Google is awaiting confirmation that four employees will face charges in Italy for failing to stop the publishing of a video of a disabled teenager being bullied. The employees will face charges of defamation and failure to exercise control over personal data, with court proceedings to start Feb. 3 in Milan, according to Reuters, citing anonymous sources. Prosecutors appear concerned that the video also highlighted the boy's disability, which could run afoul of data protection rules, said Marco Pancini, Google's European public policy counsel. Google does not know the exact charges yet, Pancini said. The company said in a statement it is disappointed information was leaked to the media before Google was notified. The three-minute video in question depicts four youths harassing a boy with Down's Syndrome and eventually hitting him in the head with a pack of tissues. It was posted in September 2006 on Google Video, one of the company's video upload sites. Google removed the video within a day after it received a complaint from the Italian Interior Ministry, which has a department that investigates Internet-related crime. By that time, the video garnered around 12,000 hits. Google maintains charges against the employees are unwarranted, Pancini said. Europe's E-commerce Directive exempts service providers from prescreening content before it is publicly posted, he said. Also, the video was technically uploaded to a Google server in the U.S., not in Italy, Pancini said. "It was a terrible video," Pancini said, adding that Google is concerned about the case's impact on censorship on the Internet. The defendants include David C. Drummond, a Google senior vice president, corporate development and chief legal officer. Pancini said Drummond did paperwork to create Google Italy, but has never lived in the country. http://www.pcworld.com/businesscente..._in_italy.html  On Security, Microsoft Reports Progress and Alarm John Markoff Microsoft plans to report on Monday that the security of its Windows operating system has significantly improved, while at the same time the threat of computer viruses, frauds and other online scourges has become much more serious. The company blames organized crime, naïve users and its competitors for the deteriorating situation. In the latest edition of its twice-a-year “Security Intelligence Report,” Microsoft said that the amount of malicious or potentially harmful software removed from Windows computers grew by 43 percent during the first half of 2008. The company said improvements in security for its Windows Vista operating system and security updates to the previous Windows XP system had made such software a less attractive target for attackers. Instead they have shifted their attention to security holes in individual programs. During the first half of the year, 90 percent of newly reported vulnerabilities involved applications, and only 10 percent affected operating systems, according to the report. Microsoft executives said they were pleased with the progress made since the company was shaken by a series of destructive programs that spread rapidly around the world over the Internet beginning in 2003. But they said that unless software development practices change throughout the industry, any improvements in the security of Windows would be meaningless. “This story is real,” said George Stathakopoulos, general manager for Microsoft’s Security Engineering and Communications group, referring to the improvement in the company’s engineering practices. “Now we have a third-party problem and it’s something we have to go solve.” Security researchers said they were sympathetic to Microsoft’s plight. “The only thing that Microsoft can patch is their own software,” said Patrik Runald, chief security adviser for F-Secure, a computer security firm in Finland. “That’s not what the bad guys are using to get into computers these days. It’s certainly a challenge.” Microsoft and the computer industry have also been unable to solve the so-called dancing pony problem. That refers to the propensity of many computer users to click on enticing links in their e-mail or to visit seductive but malicious Web sites, leaving them vulnerable to Trojan horse downloads and other infections. Over the last three years the computer security industry has been fighting a losing battle, as the ability of computer criminals to profit from identity theft and a variety of other scams has led to the development of a robust underground industry generating viruses and other so-called malware. Microsoft has tried to combat the problem by building a variety of safeguards into its operating systems and its Internet Explorer browser, with mixed success. The User Account Control feature of Windows Vista, which popped up an endless stream of warnings that irritated users, proved to be one of the key factors in the poor reception for Vista. Last week in Los Angeles, the company said it had entirely reworked the user interface of its new Windows 7 operating system to minimize user frustration. In comparing Web browser vulnerabilities in Windows XP and Windows Vista in the first half of the year, the new report found that while Microsoft could be blamed for half of the top 10 vulnerabilities in Windows XP, the top 10 browser vulnerabilities under Vista all came from third-party add-on software from companies like Apple and RealNetworks. A companion report published by Jeffrey R. Jones, a Microsoft security director, claims that Microsoft is fixing security-related bugs about three times as fast as three of its rivals: Apple, Ubuntu and Red Hat. An Apple spokesman, Bill Evans, said Microsoft had previously issued similar reports and declined to comment beyond saying that the data was not supported by users’ experience of infections. Microsoft has a unique vantage point from which to monitor the world of malware and other threats because it receives automated data both from free software it has given to users, like the Malicious Software Removal Tool, and from specialized Internet reporting systems that monitor threats. It also receives data about crashes on more than a half-billion personal computers. The current report indicates that malware infection rates are generally higher in developing countries and regions than in developed ones. Infection rates range from 1.8 for every 1,000 computers in Japan to above 76.4 for every 1,000 in Afghanistan. The United States had an infection rate of 11.2 infected computers for every 1,000 scanned, an increase of 25.5 percent in the last six months. http://www.nytimes.com/2008/11/03/te...3security.html  Windows 7 Pre-Beta Hits BitTorrent Suzanne Tindal The pre-beta version of Microsoft's Windows 7 operating system released to developers at the Professional Developers Conference has already made it onto prominent BitTorrent sites, where thousands of enthusiasts around the world are currently downloading it. Well-known BitTorrent sites such as The Pirate Bay and Mininova were at the time of publication Friday hosting multiple downloads of the newly aired operating system--both the 32-bit and 64-bit versions. On The Pirate Bay, one copy of the 32-bit build had more than one thousand people uploading it, and almost 7,000 people on the way to downloading it. The 64-bit version was less popular, with the earliest copy available on the site having only around 100 people hosting a copy and around a thousand still downloading it. There were complaints that the version offered wasn't the latest build, but instead the stable one given the delegates and therefore didn't have the revised taskbar. Complaints also abounded about how slow the download was considering the lack of people seeding the file. The most popular link for the 32-bit version of Windows 7 on Mininova had a similar number of people downloading and uploading the file as that on The Pirate Bay, although the 64-bit version on this site was a rare breed with only one copy boasting 30 seeds and around 150 leechers. Some people weren't excited. "There is nothing (sic) new in it," wrote one commenter. "I wouldn't recommend this to download. Waste of time. Happy with Vista." Others called for a reality check. "Seriously people. This was just a PRE-beta release that was given out at a trade show so writers would write about the new version. This SHOULD NOT be downloaded with the intent of using it as an everyday system. It is just so writers could get a feel for what was to come." Businesses might wonder what the new operating system will mean for their business. "I was in Redmond three weeks ago and had a sneak peek," said Peter Menadue, who holds the role of global director of solutions and technology, Microsoft solutions business within systems integrator Dimension Data. "I think they've done a stellar job. Sinofsky's a genius," he added, referring to Microsoft's Steven Sinofsky, senior vice president of the Windows and Windows Live engineering group. He said that what didn't come out in the press coverage about Windows 7 were all the bits of the operating system that would be interesting to enterprise, with aspects like application security, data security, and application deployment getting a facelift. The support for virtualization was something Menadue flagged as being of interest to business, as well as Microsoft's pledge to maintain application and driver compatibility with Vista. Dimension Data will get the M3 code for Windows 7 before the end of the year, which will allow it to start an early deployment program internally. Menadue said there had been a lot of interest in the operating system because there had been much less information than there was on previous releases, with Microsoft carefully controlling what reached the press, but added that with the current climate, companies were focused "on the here and now." These comments were echoed by Jo Sweeney, adviser at analyst firm Intelligent Business Research Services. "What tends to happen (in times like these) is that IT professionals get much more focused on proving and not improving," he said. "People will (move to) Windows 7 because if they can put greater management features into it, it will solve some of the problems of desktop computing." More than 80 percent of IT costs go into the day-to-day running of IT, Sweeney said--keeping all the PCs running, making sure everyone has the right patches--and Microsoft's dynamic IT strategy, in which Windows 7 is a part, will make that easier by allowing the separation of applications and user profiles from the operating system. This will allow anyone anywhere on the network to access their profile. People doing best-practice desktop management will already have realized those improvements, Sweeney said, with Microsoft's direction being a reaction to the market, although he admitted it was a good one. "How do they execute?" he asked. "Question mark." http://news.cnet.com/8301-10805_3-10080700-75.html  What Ray Ozzie Didn't Tell You About Microsoft Azure Behind the whiteboard of confusion Ted Dziuba Fail and You Unveiled earlier this month at Microsoft's Professional Developer Conference by Chief Whiteboard Operator Ray Ozzie, the Azure Services Platform confused damn near everyone. But after days of collaboration with the top minds in both industry and academia, El Reg is proud to announce that we have finally figured out what Microsoft Azure is. The Azure Services Platform is a clusterfuck of software that can be broken down into four basic parts: Windows Azure, .NET Services, SQL Services, and Live Services. To get a general idea of what each is, you should probably read the sixteen-page white paper. It is designed to compete with Amazon's Web Services and Google's App Engine - that is, once it gets over one slight hitch: tl;dr. The Four Letters of the Apocalypse tl;dr stands for “too long; didn't read,” and it is going to change communication as we know it. Product managers at both Amazon and Google have figured out what tl;dr means to their respective businesses, but the idea is clearly lost on Microsoft. When a developer is evaluating different hosted computing platforms for his next application, the merits of each one are decided by how well they are explained: Amazon EC2: We have a lot of servers, and we run Xen on them. You get virtual machines. Google App Engine: Run your Python code on our machines. You can use our scalable database, too, but you need to learn how it works. Microsoft Azure: OK, so first there's this operating system called Windows Azure that your apps are going to run on and will also be your development environment. There's some data storage that goes along with that, but it's not very useful, so we have the SQL Service. That doesn't really give you SQL, but something sorta similar. Ignore it for now. Still with me? There's also .NET Services that lets you connect applications together somehow, and Live Services because we needed something to keep Ray Ozzie busy. Wrap that all up, tape it together with some C# programming, and that's the platform. Fortunately for Microsoft, decision makers don't choose a hosted application platform based on specifications. They choose based on the number of stock photos of clouds and the amount of sans-serif blue typeface you have on your webpage. In that regard, Redmond is the clear winner. More Components Means More Whiteboard Action Documentation issues aside, it seems that Microsoft has actually produced something useful - once you separate the signal from the noise. Here's how it breaks down: • Windows Azure is the operating system on which your applications will run, sort of. It's more of a manager for virtual machines. It can run on your developer workstation and in Microsoft's data center. Programming for Windows Azure is done in .NET, but Ruby, PHP, and Python will soon be supported. For the time being, tour coding should be done in Visual Studio, but Eclipse support is also on the way. • Windows Azure protects you from scary shit like managing operating systems. You deploy your application straight to the data center, and it's all run in virtual instances of Windows Server 2008. Marshalling that virtualization is Windows Azure's job. Microsoft has understood that every time a developer needs to configure services on a machine, they fuck it up and need to page the ops people. To make matters easier on everyone, they've only provided two roles for Windows Azure machines: one to handle HTTP requests and one to do everything else. With these two roles, you can do both web applications and asynchronous background processes. • Windows Azure also provides you with some neutered data storage. You can store both structured and unstructured data, but nowhere do you get relational semantics. If you want to do anything remotely practical with this platform, you'll need to use the SQL Service. • Giving you access to a straight-up hosted Microsoft SQL Server would be too useful, so in the Azure platform, you get a weak abstraction over it. You can query this data store with a LINQ-like language over REST or SOAP. Why not provide you with just an SQL server? Because scaling an SQL server arbitrarily is a real pain in the nuts, and you can scrape by with this abstraction. I hope you're not too dependent on stored procedures. That will learn you to tightly couple your data and your business logic, fucker. • The engineers should have just stopped there, but there are more components to the Azure platform that are just there for show. First, the .NET Services part, which is more of a marketing tool than a useful piece of software. .NET Services let you expose web endpoints for your services so that you can connect your application to other applications out there. The idea is that businesses can easily interoperate with one another with this “service bus.” Good theory, but probably not worthy of an abstraction. .NET Services also provides a fairly convoluted federated identity system based on SAML. The path to a generalized authentication scheme is always watered with tears. • Ray Ozzie has been rewriting the same data-synchronization application for years, and over that time, he's become very good at re-branding it as something that people need. The last time we heard, it was called Hailstorm, and now it's Windows Live Mesh. In the Azure platform, it's called Live Services, and it was likely thrown into the mix because Ozzie needed something to do. It serves no practical purpose in the greater scheme of the system and can be safely ignored. A Thunderhead Is A Cloud, Too This is all within one standard deviation of the average amount of fail in any given Microsoft product. In fact, I think it stands a better chance than Google's or Amazon's offering. Let's say you're a business decision maker, and you got yourself on this cloud computing kick. Who would you rather buy your cloud resources from? 1. A company whose main business is books 2. A company whose main business is text advertisements 3. A company whose main business is business software Or maybe you should just stick with the one that has the best cloud graphics. http://www.theregister.co.uk/2008/11/03/dziuba_azure/  Conn. Teen's Computer Research Takes Him to MIT New Fairfield High senior to compete for national science award Eileen FitzGerald New Fairfield High School senior Tim Balbekov heads to the Massachusetts Institute of Technology this weekend with computer research he completed this summer for fun. He'll compete for a national science award. Balbekov teamed up with Texas high school junior Srikrishna Raghavan on research that revealed the sequence of computer instructions affects the speed of the program. "We were programming the computer to do the same thing but in a different order, and it had a profound effect," the 17-year-old said during an interview at his school Monday. "There is a lot of potential if you improve the efficiency and performance.'' In the simplest terms, Balbekov said the computer has different types of memory and the goal is to write a program to use the fast memory all the time. Balbekov said he entered his and Raghavan's research for the Siemens Competition in Math, Science & Technology as a chance to practice writing the results of science research. He was thrilled to learn they were regional finalists. "It was pretty humbling," he said about the honor, which earned him a $1,000 scholarship and another $2,000 for New Fairfield High School's math and science program. "We're very proud of him and his accomplishment," New Fairfield Superintendent Joseph Castagnola said. "Being a regional finalist is a fantastic award for him, and all the credit goes to him and the teachers who surround him daily." The regional finalists present their research at events that begin Friday at MIT and at the University of Notre Dame, the University of Texas at Austin, Carnegie Mellon University, California Institute of Technology, and Georgia Institute of Technology. The winners of the regionals will compete at the national finals Dec. 5 to 8 at New York University in New York City. Balbekov came to the U.S. from Russia with his parents when he was 6 years old and lived in Stamford until moving to New Fairfield two years ago. He's been interested in computers since fifth grade and taught two weekend courses at MIT in 10th and 11th grade -- in Russian language and culture and video game programming. He attended a three-week summer program at Drexel University in Philadelphia this summer, where he worked with professor Jeremy Johnson, who paired him with Raghavan. He said both of them had to learn college-level algebra to begin their research. Balbekov's project was among 1,205 entered in this year's Siemens Competition. There were 311 students from 33 states named semifinalists, and Balbekov was among 96 students named regional finalists. The Siemens Competition is a signature program of the Siemens Foundation. The annual competition is administered by the College Board and awards college scholarships ranging from $1,000 to $100,000 in individual and team categories. The foundation hopes to inspire students to pursue their interest in math and science and celebrate their achievements. "I've seen the kids get calls from colleges who recruit them right after the competition," foundation president James Whaley said Monday. He said 70 percent of the winners come from public schools where their teachers encouraged and inspired them to pursue math and science. "It's a great honor for him (Balbekov) to make it to the regional finals," Whaley said. "He becomes part of our alumni network." The contest New Fairfield High senior Tim Balbekov is among 96 students selected as regional finalists for this weekend's Siemens Competition in Math, Science & Technology at Massachusetts Institute of Technology. Regional finalists compete at one of six universities and the winners go on the national final Dec. 8 at New York University. The Siemens Competition awards college scholarships of $1,000 to $100,000 in individual and team categories. http://www.newstimes.com/ci_10907075  Not Free at Any Price Why I switched to the OLPC—and why I dropped it Richard M. Stallman The One Laptop Per Child project, launched by MIT professor Nicholas Negroponte in 2003, was supposed to lead millions of children around the world to information technology and freedom. The plans aimed for low cost, enabling many children to use the machines, and free software, so they would have freedom while using them. I thought it was a good idea; I even planned to use one myself when I found in the OLPC’s promise of free software a way to escape the proprietary startup programs that all commercial laptops used. But just as I was switching to an OLPC, the project backed away from its commitment to freedom and allowed the machine to become a platform for running Windows, a non-free operating system. What makes this issue so important, and OLPC’s retreat from free software so unfortunate, is that the “free” in free software refers to freedom of knowledge and action, not to price. A program (whatever job it does) is free software if you, the user, have the four essential freedoms: • Freedom 0: The freedom to run the program as you wish. Some proprietary software packages come with licenses that restrict even the use of authorized copies. • Freedom 1: The freedom to study the source code—the algebra-like statements that specify what the program does—and then change it to make the program do what you wish. For instance, you could add new features to suit your taste. Or, if the program has malicious features, as Windows and MacOS do, you could remove them. • Freedom 2: The freedom to redistribute exact copies when you wish. We call this the freedom to help your neighbor. • Freedom 3: The freedom to distribute copies of your modified versions when you wish. We call this the freedom to contribute to your community. To exercise freedoms 1 and 3 requires programming, but you can take advantage of them indirectly without knowing anything about coding. If you want the program changed, you can give a copy to the programmer of your choice (exercising Freedom 2), the programmer can implement the changes you asked for (exercising Freedom 1), and give you the result (exercising Freedom 3); you will then pay the programmer as you agreed at the outset. This possibility is especially useful for companies, but individuals can take advantage of it too. A free program develops democratically under the control of its users. By contrast, a non-free program develops under the autocracy of one developer—typically a corporation—and subjects the users to that developer’s power. The developer has sole control over what the program will do—and what it won’t do. The worshipers of the invisible hand dogmatically claim that developers will always do what the users want. Empirically, what we see is that developers tend to abuse their power, even to the point of installing malicious features. Windows Vista has features to spy on the user, restrict use of data in the machine, and even attack the user (Microsoft can forcibly install changes in the system at any time). Windows Media Player restricts copying, format conversion, and even viewing of files. The Macintosh operating system is similar. You may think you use these tools, but really they are using you. Free software rarely suffers from malicious features because no developer has the power to make them stick: any user might find them, remove them, and publish a modified version improved by their absence. Thus, even if you never take the trouble to change the free program or pay someone else to change it, you still receive the benefits of living in a democracy, the benefits of keeping development under the control of the users. Teaching children to use Windows is like teaching them to smoke tobacco—in a world where only one company sells tobacco. Like any addictive drug, it inculcates a harmful dependency. (Bill Gates made this comparison in a 1998 issue of Fortune Magazine.) No wonder Microsoft offers the first dose to children at a low price. Microsoft aims to teach poor children this dependency so they can smoke Windows for their whole lives. I don’t think governments or schools should support that aim. The OLPC was supposed to avoid that harmful result by using the free operating system GNU/Linux. Even more exciting for me, a lower-level piece of software, the startup program or “BIOS,” was going to be free as well. There were many laptops capable of running a free GNU/Linux system, and I used one of them; there was already a free BIOS, but no manufacturers had ever published the information a developer would need to make the free BIOS run on their laptops. When the OLPC appeared, it fell one step short of full freedom: the highly publicized wireless mesh network device, which allows OLPCs to connect to the Internet through nearby OLPCs, required a non-free program. This piece of non-free code prevented me from fully endorsing the OLPC. But that would not stop me from using one: I would just have to delete the non-free code and do without the internal wireless device. The OLPC had practical inconveniences, too: no internal hard disk, a small screen, and a tiny keyboard. In December 2007 I test-drove the OLPC with an external keyboard, and concluded I could use it with an external disk despite the small screen. I decided to switch. The OLPC developers advised me to wait for the next batch of machines, in which some technical glitches would be resolved. After the machine arrived and the Free Software Foundation obtained the necessary external disk, ethernet, Wi-Fi and modem devices, I had a week in April to move my files to the OLPC and prepare it to take on my next trip. That very week, Negroponte announced that future OLPC machines would be designed so they could run Windows. In Peru they will be delivered with Windows installed. (I plan to try to organize counterpressure while in Peru this November.) But even the OLPCs delivered with GNU/Linux will be easy to convert subsequently to Windows. It only requires a small card that is supposed to cost $7. (I expect Microsoft will hand these out to the kiddies like free samples of cigarettes.) This reversal of policy flew in the face of the project’s stated goals of promoting freedom. Several OLPC developers quit in disgust, and some members of the user community tried to oppose the change. But Negroponte ignored them and proceeded with his decision. As a result, I now expect that the main effect of the OLPC project—if it succeeds—will be to turn millions of children into Microsoft users. That is a negative effect, so the world would be better off if the OLPC project had never existed. People seeing me with an OLPC at my speeches took that as an endorsement of the project. This made me uncomfortable, so I decided to counteract the appearance by explicitly raising the issue of OLPC’s surrender to Windows. Fortunately I soon came across a better machine. In May, while in China, by pure chance I met people from Lemote, which produces a laptop based on a variant of the MIPS processor. They say it contains no non-free software, and that seems to be true. The Lemote machine I am using now is a prototype, and it has some inconveniences; for instance, it burns a great deal of electricity. I trust the production model will be better. Other companies in Europe and China are likewise planning to start selling cheap MIPS-based laptops soon. As a bonus, Windows does not run on the MIPS processor; it never has. * * * In 2007 the OLPC project asked the public for donations, basing its plea on its stated principles of freedom. Many people paid the price of two machines to receive one, with the other meant as a gift to a child in the developing world. Now the project proposes to make a similar appeal again, but is it worthy of support? It has not lived up to the commitments on the basis of which it received backing before. Some of their computers will be delivered with user-subjugating Windows software, and the rest are likely to be converted to Windows afterward. If you want to support a venture to distribute low-priced laptops to children, wait a few months, then choose one that donates MIPS-based machines that run entirely free software. That way you can be sure to give the gift of freedom. http://www.bostonreview.net/BR33.6/stallman.php  PATENT-B-GONE! Inventor Mitch Altman Explains Why He Open-Sourced His TV-B-Gone Kit As an inventor, I was taught that patents encouraged creativity and entrepreneurship. So, after finishing my first TV-B-Gone universal remote control prototype, I naturally called my brother the patent attorney, and together we filed a patent application. Was that the best move? TV-B-Gone remote controls are key chains with one button that make it fun to turn off almost any TV in public places. Oddly enough, within weeks of the first day of sales, the TV-B-Gone story appeared in major and minor newspaper, magazine, radio, and even TV outlets throughout the planet. It was a hit! With this vast popularity, what might have happened if my packaging had not displayed the words: “Patent Pending”? Maybe it stopped some large companies from copying TV-B-Gone remotes, since selling copies would open them up for being sued once my patent was granted. Would it be different if my product were open source? I knew about open source, of course, but never considered it viable for hardware until going to my first hacker convention. There I met people who are very critical of patents and other forms of intellectual property law. They see these laws as obsolete and obnoxious. Individuals who want to hack cool ideas to improve upon them and share their results are often preyed upon and silenced by corporate lawyers protecting their clients’ patents. Paradoxically, this stifles the creativity that patents were supposed to encourage. This point of view was an eye-opener for me. I decided to go for it. Together with Limor Fried (who makes lots of great kits), we’re making open source kits available so anyone can build and hack TV-B-Gone remote controls (look for an upcoming MAKE article about this). The firmware source code will be available online, as well as the board layout, lots of TV power codes, and all documentation. Even though my project was not open source, I benefited from the open source community. People hacked TV-B-Gone remote controls in wonderfully creative ways. (Search online for “TV-B-Gone hacks” and you’ll get the idea.) These hacks increased the product’s popularity, resulting in more sales and more people around the world experiencing the satisfaction of turning off TVs. Also, since there was an army of TV-B-Goners who emailed me with ideas on how to improve upon my initial design, the next versions of TV-B-Gone remotes were considerably better than the original. Everything added up for me to look seriously at Creative Commons, a form of open source licensing. The added buzz will likely also help sales of ready-made TV-B-Gone key chains, since not everyone wants to build their own. Everybody wins. In the words of my brother the patent lawyer, “The old way of patent law is to think: ‘This is mine and I’m going to keep it.’ This may have some advantages, but with open source you can share and bring more creative minds to the process. What’s really nice is that you don’t have to give up all your rights. With open source you can have the best of all worlds.” Mitch Altman’s next products, based on the “Brain Machine” article he wrote for MAKE, Volume 10, are also open source. http://blog.makezine.com/archive/200...ntor_mitc.html  How Much Ink Is Left in That Dead Cartridge? We ran printers until they said it was time to change the cartridge--and found that some left more than 40 percent of their ink unused. Jeff Bertolucci You've probably had this experience: Your printer tells you it's time to change the cartridge, but you dismiss the message and keep printing. Days or weeks later, you're still using the same cartridge and thinking to yourself that rumors of its death were greatly exaggerated. Or perhaps your printer simply shuts down when it decides you've gone deep enough into its ink well, refusing to operate until you replace the cartridge, though you suspect there's plenty of ink left. PC World decided to do some real lab testing on this issue; and the results confirm what you may have suspected: Many manufacturer-branded (OEM) and third-party (aftermarket) vendor cartridges leave a startling amount of ink unused when they read empty. In fact, some inkjet printers force users to replace black ink cartridges when the cartridge is nearly half full, PC World has found. Overview We tested using multifunction printers from four major manufacturers: Canon, Epson, Hewlett-Packard, and Kodak. (For the top-rated models, see our chart of top-rated multifunction printers.) PC World Test Center results show that models from Canon, Epson, and Kodak reported ink cartridges as being empty when in some cases the tanks had 40 percent of their black ink remaining. The quantity of unused ink ranged from about 8 percent in an Epson-brand cartridge to a whopping 45 percent in an aftermarket cartridge for a Canon printer. After posting low-ink warnings, those printers wouldn't let us resume printing until we inserted a new cartridge. Our test printers typically left more unused ink--in some cases significantly more--when using third-party or aftermarket print cartridges than when using the printer manufacturer's own cartridges. When using ink their own manufacturer's cartridges, the printers displayed several low-ink warning messages before finally shutting down due to low ink. Our HP printer, the Photosmart C5280, was the only one that continued to print even after displaying several low-ink messages, and those messages appeared only when we used an HP print cartridge. When we paired the C5280 with an aftermarket cartridge from LD Products, the printer provided no low-ink warning at all. It's important to note that our results show the performance of a clutch of single printers, each paired with just one cartridge. Since OEMs and their aftermarket competitors sell dozens of ink cartridges for a wide variety of printer models, you should consider our results as a kind of snapshot of the way each particular unit deals with "remaining ink." Why So Much Leftover Ink? There are valid reasons for not draining an ink cartridge completely, printing experts say. "Many inks, if they run dry, can cause significant damage to the printer," says Brian Hilton, a senior staff engineer at the Rochester Institute of Technology who holds 29 inkjet patents. "You always want to leave a buffer in the tank so that the printer never runs dry. There should always be a factor of safety included." Other observers point out that the quantity of leftover ink is often only a few milliliters. "Printers have generally become more efficient over the years," says Andy Lippman, a printing analyst with Lyra Research. "In the past, you might have seen 40 milliliters of ink in the black cartridge. Today you're going to get the same amount of pages out of 7 or 8 milliliters." Other people, however--both journalists and independent researchers--have reported very different experiences with ink cartridges. Judging from these findings, printer owners are probably throwing away a lot of usable ink. And that's a problem, when you consider how expensive the precious fluid is. An average black-ink cartridge contains 8 milliliters of ink and costs about $10 which translates into a cost of $1.25 per milliliter (or more horrifyingly, $1250 per liter). Liquid Gold? If you bought a gallon of the stuff over the life of your printer, you'd have paid about $4731 for a liquid that one aftermarket vendor told us was "cheap" to make. For some perspective, gasoline costs about $3 per gallon (at the moment), while a gallon of Beluga caviar (imagined as a liquid) costs about $18,000--surprisingly, only about four times as expensive as good old printer ink. "I personally think that consumers are getting ripped off," says Steve Pociask, president of the American Consumer Institute, a nonprofit educational and research institute in Washington, D.C. Pociask recently coauthored a 50-page study on the ink jet printer and cartridge market. "In some cases, we found that [the price of] the printer could be 1/8 of the total cost of printing," says Pociask. "Over the life of the printer--and by that I mean three years--you can easily spend $800 for the printer and ink." How We Tested We researched both online and brick-and-mortar tech outlets to find printers that are being used now by high numbers of consumers. We didn't test color inks because that would have introduced too many variables that might skew the results. For instance, some printers use separate cartridges for each ink, while others use single, tricolor cartridges. A standardized test might not drain the colors evenly, which might give one printer an unfair advantage. Tony Leung, Senior Data Analyst in the PC World Test Center, weighed each black ink cartridge (to an accuracy of 0.001 gram) to determine the cartridge's initial weight. We then printed pages until the printer, in response to the low level of ink in the cartridge, prevented us from continuing. When each printer stopped printing, we removed and weighed its black ink cartridge to determine the cartridge's out-of-ink weight. Then we removed all of the remaining ink from the cartridge (including the small sponges found in some cartridges), put the cartridge on the scale again, and measured it's true-empty weight. This method allowed us to identify the weight of the ink when the cartridge was full, when the printer announced that it was empty, and when it truly was empty. Using this method, here's what we found... Canon We tested Canon's Pixma MP610 multifunction printer with black ink cartridges from Canon and from G&G, an aftermarket brand owned by Ninestar Image. The differences in performance between the OEM ink and the aftermarket ink were striking. With the Canon cartridge installed, the printer stopped printing when 24 percent of the ink remained in the tank. Specifically, the full tank of ink weighed 27.333 grams, and the unused ink in the tank at nominal empty weighed 6.459 grams. Canon didn't dispute our results, but the company pointed out that its printers do allow users to print after the initial low-ink warning. "There are typically a series of warnings before the ink is out, alerting users to ink status," spokesperson Kevin McCarthy wrote in an e-mail message. (We calculated the remaining ink weight at the point when the printer actually shut down, which was after the preliminary warnings appeared.) When equipped with the aftermarket G&G cartridge, the Canon printer shut down with nearly 45 percent of the ink left. The full tank of ink weighed 27.320 grams, and its remaining ink weighed 12.277 grams. G&G responded by running its own tests with a different Canon printer, the Pixma iX4000. (The vendor says the model that the PC World Test Center used wasn't available in its workshop at the time of testing.) G&G told us that it tested three of its color cartridges--magenta, blue, and yellow--and found that the amount of residual ink ranged from 5.5 percent (for yellow) to 17 percent (for magenta). (Again, PC World limited its testing to black ink cartridges only.) Canon declined to comment on our test findings with the G&G print cartridge. Epson With an Epson black-ink cartridge installed, the Epson RX680 printer shut down with just over 8 percent of its ink remaining. The weight of the ink in the full cartridge was 11.700 grams; the weight of the residual ink at printer shutdown was 0.969 gram. In an e-mail response to PC World, an Epson spokesperson wrote: "Eight percent remaining ink measured in your testing is a normal amount. This reserve assures print quality and printer reliability." But the story was quite different when we printed pages on the RX680 using an aftermarket cartridge from LD Products. This time the printer shut down with a whopping 41 percent of the ink still in the tank. The full quantity of ink weighed 12.293 grams; the unused ink weighed 5.0005 grams. Why the huge gap between OEM and aftermarket? "Epson cartridges have an ink-level sensor to more accurately report ink levels, and to reduce the amount of ink in the safety reserve," the company spokesperson wrote. Third-party products don't have these sensors, according to Epson, and the printer manufacturer "cannot guarantee the performance, quality or longevity of these cartridges." LD Products has a different theory. "The ink itself is cheap, so we refill to more than the original level," says Ben Chafetz, vice president of marketing for LD Products. The Epson printer bases its low-ink message on the printing capacity of the OEM cartridge, but since the LD cartridge contains considerably more ink than the OEM version, it is bound to have more ink remaining when the printer shuts down, according to Chafetz. In other words, if Epson supplies enough ink in its cartridge for 120 pages plus a margin of error, say, while LD adds enough ink to print 200 pages, and if the Epson printer shuts off at 120 pages anyway, the percentage of leftover ink in the LD cartridge will be considerably higher than in the Epson cartridge. Chafetz points out that regardless of the percentage of unused (and unusable) ink in the nominally empty cartridges, the page yields of the LD Products cartridges and the high-capacity Epson cartridges should be the same. (Note: PC World didn't test page yields in this study.) Hewlett-Packard Testing the HP printer was difficult because HP takes an unusual approach toward diminishing ink supplies in its cartridges: The HP Photosmart C5280 multifunction printer we tested didn't shut down as ink levels approached exhaustion. With an OEM cartridge installed, the printer displayed warning messages as the ink level dropped, but it never forced us to replace the cartridge. As a result, we continued printing until the pages began showing telltale signs of low ink, such as banded text. The HP printer will continue to print until the cartridge is completely dry--but since the print heads are part of the cartridge in HP's design, running out of ink does not damage other parts of the printer. When using an aftermarket cartridge from LD Products, the C5280 failed to post any low-ink warnings--either on our test computer or on the printer console. Does that mean HP's warning system works only with house-brand cartridges? Not necessarily, but HP suggests that you are better off with its OEM cartridges. "Most aftermarket cartridges do not signal 'low-on-ink' alerts, giving customers no advance warning that ink is running low," wrote HP spokesperson Katie Neal in an e-mail message. LD Products' Chafetz disagrees. He says that LD's Photosmart C5280-compatible products are actually refurbished and refilled HP cartridges. One possible explanation for the lack of a low-ink warning is that the printer wasn't reading the refurbished cartridge's chip code correctly, he says. Chafetz says that the results from PC World's tests mark the first time that LD Products' technicians have heard of their cartridges' not posting a low-ink warning. Kodak The Kodak EasyShare 5300 was the only printer that lasted longer with an aftermarket cartridge than it did with the manufacturer's cartridge. Equipped with a Kodak cartridge, this printer shut down with 43 percent of the ink remaining. Its full quantity of ink weighed 16.857 grams, and its unused ink after shutdown weighed 7.272 grams. Kodak doesn't dispute our findings, but the company argues that our results don't tell the whole story. Roderick Eslinger, Kodak technical marketing manager, says that Kodak's in-house tests in 2007 indicated that 65 percent of its cartridge ink was used for consumer printing, while 35 percent was used to "protect/maintain optimal Kodak printer performance and document quality." Eslinger says that the remaining ink is "already factored into our industry advertising claims for consumers, and that Kodak cartridges offer "low costs and high quality yields as compared to competitors." With a G&G cartridge, the Kodak printer shut down with 36 percent of the ink remaining in the tank. The leftover ink weighed 5.360 grams. Kodak chose not to comment on the aftermarket results. Watch the Page Yield Some vendors and analysts advise consumers to make sure that they get the correct page yield (the total number of pages produced with a single cartridge), rather than focusing on the amount of ink left unused in a cartridge that must be discarded. "This is the most reliable way to understand the life of a cartridge, rather than the amount of ink, or what might be left over," says Lippman. But vendor page-yield estimates don't always match reality, as we discovered when testing printers for another PC World article, "Cheap Ink: Will It Cost You?" Using a different set of OEM cartridges and printers, we found that one HP black cartridge exceed its projected page yield (810 printed vs. 660 projected), while page yields from Epson and Kodak cartridges fell short of expectations. Specifically, Epson printed just 209 pages, far less than the 335 pages the company estimated it would produce; and Kodak generated 480 pages versus a projected page count of 540. Page yields aside, we have yet to hear a satisfactory and persuasive explanation from a vendor as to why so many printer cartridges leave so much ink behind. Even if the waste amount is only a few milliliters, that unused liquid could have printed a lot of pages. PC World's Tips for Saving Money on Printing For additional advice on reducing the cost of running your inkjet printer, see "The Cheapskate's Guide to Printing," "Save Money on Inkjet Printer Ink," and "How to Spend Less on Printing and Get Better Results." An earlier three-part PC World series on the subjects of counterfeit name-brand inks ("Bogus Ink Stink"), third-party ink quality ("Cheap Ink Probed"), and high ink-cartridge prices ("Why Do Ink Cartridges Cost So Much?") provides valuable historical background and additional test results for various ink cartridges. http://www.pcworld.com/article/15295...cartridge.html  Why I Copyfight Cory Doctorow Why does all this copyright reform stuff matter, anyway? What's at stake? Everything. Until a very short time ago, copyright was an industrial regulation. If you fell under copyright's domain, it meant that you were using a piece of extraordinary industrial apparatus — a printing press, a motion-picture camera, a record press. The cost of this apparatus was significant, so adding a couple hundred bucks for the services of a skilled copyright attorney to the deal wasn't much of a hardship. It merely tacked a couple percentage points of overhead onto the cost of doing business. When non-industrial entities (e.g., people, schools, church groups, etc.) interacted with copyrighted works, they did things that copyright law didn't have anything to say about: they read books, they listened to music, they sang around the piano or went to the movies. They discussed this stuff. They sang it in the shower. Retold it (with variations) to the kids at bedtime. Quoted it. Painted murals for the kids' room based on it. Then came the early days of the copyfight: the analog period, when VCRs, double-cassette-decks, photocopiers, and other proto-copying technology came along. Now it was possible to do things that rose to the realm of copyright's regulated activities (copying, performing, displaying, adapting) with stuff lying around the house. Dealer rooms at cons sometimes sported crudely bound fanfic "novels," teenagers courted each other with mix tapes, you could bring some HBO over to the neighbors' on VHS cassette and have a movie party. And yet, there was comparatively little danger in this process. Although these activities were of dubious legality (certainly, the big rightsholder groups considered them technological suitcase nukes, comparing the VCR to the Boston Strangler and promising that "home taping is killing music"), the cost of enforcement was very high. Publishers and record labels and studios couldn't watch what you did at home and work and parties and cons, not without an expensive network of paid snitches whose salaries would exceed any losses they were experiencing. Enter the Internet and the personal computer. These two technologies represent a perfect storm for bringing ordinary peoples' ordinary activity into the realm of copyright: every household has the apparatus to commit mass acts of infringement (the PC) and those infringements take place over a public conduit (the Internet) that can be cheaply monitored, allowing for low-cost enforcement against ordinary people by the thousand. What's more, Internet transactions are more apt to commit a copyright offense than their offline equivalents. That's because every transaction on the Internet involves copies. The Internet is a system for efficiently making copies between computers. Whereas a conversation in your kitchen involves mere perturbations of air by noise, the same conversation on the net involves making thousands of copies. Every time you press a key, the keypress is copied several times on your computer, then copied into your modem, then copied onto a series of routers, thence (often) to a server, which may make hundreds of copies both ephemeral and long-term, and then to the other party(ies) to the conversation, where dozens more copies might be made. Copyright law valorizes copying as a rare and noteworthy event. On the Internet, copying is automatic, massive, instantaneous, free, and constant. Clip a Dilbert cartoon and stick it on your office door and you're not violating copyright. Take a picture of your office door and put it on your homepage so that the same co-workers can see it, and you've violated copyright law, and since copyright law treats copying as such a rarified activity, it assesses penalties that run to the hundreds of thousands of dollars for each act of infringement. There's a word for all the stuff we do with creative works — all the conversing, retelling, singing, acting out, drawing, and thinking: we call it culture. Culture's old. It's older than copyright. The existence of culture is why copyright is valuable. The fact that we have a bottomless appetite for songs to sing together, for stories to share, for art to see and add to our visual vocabulary is the reason that people will pay money for these things. Let me say that again: the reason copyright exists is because culture creates a market for creative works. If there was no market for creative works, there'd be no reason to care about copyright. Content isn't king: culture is. The reason we go to the movies is to have something to talk about. If I sent you to a desert island and told you to choose between your records and your friends, you'd be a sociopath if you chose the music. Culture's imperative is to share information: culture is shared information. Science fiction readers know this: the guy across from you on the subway with a gaudy SF novel in his hands is part of your group. You two have almost certainly read some of the same books, you've got some shared cultural referents, some things to talk about. When you hear a song you love, you play it for the people in your tribe. When you read a book you love, you shove it into the hands of your friends to encourage them to read it too. When you see a great show, you get your friends to watch it too — or you seek out the people who've already watched it and strike up a conversation with them. So the natural inclination of anyone who is struck by a piece of creative work is to share it. And since "sharing" on the Internet is the same as "copying," this puts you square in copyright's crosshairs. Everyone copies. Dan Glickman, the ex-Congressman who now heads up the Motion Picture Association of America (as pure a copyright maximalist as you could hope to meet) admitted to copying Kirby Dick's documentary This Film is Not Yet Rated (a scorching critique of the MPAA's rating system) but excused it because the copy was "in [his] vault." To pretend that you do not copy is to adopt the twisted hypocrisy of the Victorians who swore that they never, ever masturbated. Everyone knows that they themselves are lying, and a large number of us know that everyone else is lying too. But copyright's problem is that most of the copyists cheerfully admit that they copy. The majority of American Internet users engage in infringing file-sharing. If file-sharing were stamped out tomorrow, they'd swap the same files — and more — by trading hard drives, or thumb drives, or memory cards (and more data would change hands, albeit more slowly). Copyists either know that they infringe but don't care, or they believe that the law can't possible criminalize what they're doing and assume that it punishes more egregious forms of copying, such as selling pirate DVDs in the street. In fact, copyright law penalizes selling DVDs at a much lower level than sharing the same movies over the Internet for free, and the risk of buying one of these DVDs is much lower (thanks to the high costs of enforcement against people making transactions in the real world) than the risk of downloading them online. Indeed, copyists are busily building an elaborate ethos of what can and can't be shared, and with whom, and under what circumstances. They join private sharing circles, argue norms among themselves, and in word and deed create a plethora of "para-copyrights" that reflect a cultural understanding of what they're meant to be doing. The tragedy is that these para-copyrights have almost nothing in common with actual copyright law. No matter how hard you adhere to them, you're probably breaking the law — so if you're in making anime music videos (videos for pop music made by cleverly splicing together clips of anime movies — google for "amv" to see examples), you can abide by all the rules of your group about not showing them to outsiders and only using certain sources for music and video, but you're still committing millions of dollars' worth of infringement every time you sit down to your keyboard. It's not surprising that para-copyright and copyright don't have much to say to one another. After all, copyright regulates what giant companies do with each other. Para-copyright regulates what individuals do with each other in a cultural settings. Why be surprised that these rulesets are so disjointed? It's entirely possible that there's a detente to be reached between the copyists and the copyright holders: a set of rules that only try to encompass "culture" and not "industry." But the only way to bring copyists to the table is to stop insisting that all unauthorized copying is theft and a crime and wrong. People who know that copying is simple, good, and beneficial hear that and assume that you're either talking nonsense or that you're talking about someone else. Because if copying on the Internet were ended tomorrow, it would be the end of culture on the Internet too. YouTube would vanish without its storehouse of infringing clips; LiveJournal would be dead without all those interesting little user-icons and those fascinating pastebombs from books, news-stories and blogs; Flickr would dry up and blow away without all those photos of copyrighted, trademarked and otherwise protected objects, works, and scenes. These conversations are why we want the things we're conversing about. Fanfic is written by people who love books. YouTube clips are made by people who want you to watch the shows they're taken from and discuss them. LJ icons demonstrate affinity for works. If culture loses the copyright wars, the reason for copyright dies with it. http://www.locusmag.com/Features/200...copyfight.html  Malaysian Court Frees Blogger A Malaysian court freed on Friday a blogger who was detained under the country's draconian security laws and whose arrest in September sparked condemnation from the opposition and rights groups. Opposition supporter Raja Petra Kamaruddin, 58, was held under Malaysia's Internal Security Act (ISA) that allows indefinite detention without trial. He was suspected of being a threat to security for insulting Islam in this mainly Muslim country of 27 million people. The blogger was brought to a court in Shah Alam, just outside Kuala Lumpur, where he was freed after a judge accepted his lawyer's plea saying the detention was illegal. "This showed that ISA cannot be used. I hope this is not a political decision," Raja Petra, who said he was surprised by the finding, told reporters outside the court. He later left the building in a friend's red Rolls-Royce. Raja Petra's blog (http://mt.m2day.org) has been a thorn in the side of Malaysia's government, especially for Deputy Prime Minister Najib Razak. The blogger is being tried in a separate court on sedition charges for linking Najib, who will become prime minister in March, to the gruesome murder of a Mongolian model. The model, Altantuya Shaariibuu, was shot in the head twice and her body blown up with explosives in a jungle near Shah Alam in October 2006. Najib has strongly denied the blogger's accusations, terming them "total lies." The issue has not halted his rise to the top of Malaysia's ruling party and he will be elected unopposed at party polls in March. Another court last week freed a former aide to Najib charged with abetting with two policemen in the murder of the Mongolian. The United Malays National Organization (UMNO) leads a coalition that has ruled this southeast Asian nation for 51 years but which stumbled to its worst ever election result in March when it lost its two-thirds majority. Malaysia holds about 61 people, mostly Muslim militants and Hindu activists, under the colonial-era ISA that some critics say is randomly used to silent government critics. The government, facing its biggest challenge to its grip on power since independence in 1957, has lately came under strong pressure to abolish the ISA. The Bar Council, which groups about 12,000 lawyers, told Prime Minister Abdullah Ahmad Badawi last week he should use his remaining months in power to start dismantling the law. "We question the wisdom of continuing to have such a repressive piece of legislation on our statute books," Bar Council president Ambiga Sreenevasan said. Abdullah's government faces a challenge from opposition leader Anwar Ibrahim, forced out of government in the late 1990s and then imprisoned on sodomy and corruption charges. Anwar, confronted by what he says are trumped-up charges of sodomy, won a legal reprieve on Friday after a judge disallowed a bid by the prosecution to transfer the case to a higher court. Anwar and his lawyers have argued against the transfer on fears he would not get a fair trial. (Reporting by David Chance and Jalil Hamid; Editing by Jerry Norton) http://www.reuters.com/article/techn...4A60XY20081107  Online Piracy Becomes a ‘National Sport’ in France enigmax Edging ever closer to becoming law, France’s “three-strikes” proposals have received support in the French Senate which voted overwhelmingly in favor for these draconian measures to deal with piracy. Now, a new report suggests that online piracy has become something of a ‘national sport’ in France. The online file-sharing debate is really heating up in France. Contrary to advice from the European Court of Justice, France is pressing ahead with its plan for a controversial “3 strikes” or “graduated response” framework to deal with alleged file-sharers. Now, supported by a Le Figaro headline, “Piracy Has Become a National Sport in France”, a new study from market research company TNS Sofres is set to add fuel to the fire. According to the poll of 2,011 people over 15 years old, the French use a diverse range of digital media to store or play pirated content. Of those questioned, 34% said their media players contained pirated files, with 20% admitting they go as far as using external hard drives to store illicit content. The USB storage key was used by 8% of respondents to shift illegal content, with 7% admitting to using mutimedia-capable cellphones. Although the piracy ‘problem’ seems to be massive in France, it is certainly not limited to that one country. Just over the English Channel from France lies the UK, where an estimated 6 million people engage in online piracy - roughly 10% of the population. Across the pond, in the United States, a 2007 study found that 18 percent of the total US online population downloaded at least 1 movie from the Internet, illegally. The French survey shows that the ‘problem’ is not limited to the younger generation, as is often assumed - it affects the entire population. The report further suggests that the actual numbers might be much greater than reported, but with news of draconian measures to deal with online piracy making headlines regularly, just how many people are prepared to be honest about their piracy habits? http://torrentfreak.com/online-pirac...france-081107/  Google's Growth Makes Privacy Advocates Wary Rachel Metz Perhaps the biggest threat to Google Inc.'s increasing dominance of Internet search and advertising is the rising fear, justified or not, that Google's broadening reach is giving it unchecked power. This scrutiny goes deeper than the skeptical eye that lawmakers and the Justice Department have given to Google's proposed ad partnership with Yahoo Inc. Many objections to that deal are financial, and surround whether Google and Yahoo could unfairly drive up online ad prices. A bigger long-term concern for Google could be criticisms over something less tangible _ privacy. Increasingly, as Google burrows deeper into everyday computing, its product announcements are prompting questions about its ability to gather more potentially sensitive personal information from users. Why does Google log the details of search queries for so long? What does it do with the information? Does it combine data from the search engine with information it collects through other avenues _ such as its recently released Web browser, Chrome? Data gathered through most of the company's services "disappears into a black hole once it hits the Googleplex," said Simon Davies, director of London-based Privacy International, referring to Google's headquarters. "It's impossible to track that information." Google _ whose corporate motto is "Don't Be Evil" _ generally sees such concerns as misinformed. For instance, the company says it stores the queries made through its popular search engine primarily so it can improve the service. But whether the criticisms are valid or not, they are likely indicative of the battles Google will face as it, like Microsoft Corp. in the 1990s, moves from world-wowing startup to the heart of the technology establishment. The September release of Chrome illuminated the budding conflicts. To Google, the new browser is a platform on which future Web-based software applications might run most efficiently. It also is a sign that Google understands its growing power, since launching a browser is a direct challenge to Microsoft. In other circles, Chrome provoked suspicion. One group, Santa Monica, Calif.-based Consumer Watchdog, argues that the browser crosses a new line. In a mid-October letter to Google directors, Consumer Watchdog said it had "serious privacy concerns" about the browser and the transfer of users' data through Google's services without giving people what it sees as "appropriate transparency and control." One of Consumer Watchdog's complaints surrounds Chrome's navigation bar, which can be used to enter a Web site address or a search query. The group points out that as users type in the navigation bar, Chrome relays their keystrokes to Google even before they click "Enter" to finalize the command. "The company is literally having this unnoticed conversation with itself about you and your information," Consumer Watchdog President Jamie Court said. This "conversation" stems from the "Google Suggest" feature, which is built into the browser and other Google products, including its basic Internet search engine. "Google Suggest" sends Google searches as you type, in hopes of anticipating your desires. So if you're keying in "Electoral College 2008 election," Google will offer multiple search queries along the way. First you'd be given results related to the term "electoral," then ones on the Electoral College in general, and finally you'd get links pertaining to Tuesday's presidential vote. This is what worries Consumer Watchdog: Say you key in something that could be embarrassing or deeply personal, but reconsider before you press "Enter." The autosuggest feature still sends this phrase to Google's servers, tied to your computer's numeric Internet Protocol (IP) address. Brian Rakowski, the product manager for Chrome, said Consumer Watchdog's fears stemmed from confusion about the role a Google Web browser plays. "There was some concern that, given a very naive way of how browsers work, you may think, `Now I'm using a Google browser _ Google must know everything on their servers about me,'" he said. Rakowski said queries sent to Google through the autosuggest feature do include data like a user's IP address and the time at which the queries were made. But Google logs just 2 percent of the information brought in through "Google Suggest," in order to improve the feature, Rakowski said, and anonymizes this data within 24 hours. The anonymization is accomplished by stripping off the last four digits of the IP address associated with the query. "You're flying blind without that information, so we have to collect a little bit," he said. "But we're really (collecting) the bare minimum we can to provide that service." The autosuggest function can be shut off in the browser or when using Google's search engine through its home page, but it is not immediately evident how to do so. One way is through Chrome's "incognito" tab, which turns off the autosuggest feature and lets users surf the Web without revealing their activities to people who have access to the same computer. However, Consumer Watchdog objects to the design of "incognito." The group claims the feature makes users feel that their Web surfing is totally private, while in fact Google is still sending some information back and forth between users' PCs and the company's servers. Google takes issue with that complaint, too. The "incognito" function lets users surf without leaving a trail of pages visited or "cookie" data-tracking files behind, but can't entirely cloak someone's Internet activity from the outside world. "We try to be very upfront with users when they enter this mode about what it provides and what it doesn't provide," Rakowski said. Although Chrome is new, Consumer Watchdog is not waiting to see whether it gets too little use to worry about. In October, Court's group wrote U.S. Attorney General Michael Mukasey to caution him about Google's plans to sell ads for Yahoo, saying that its fears about Google's market power have been exacerbated by Chrome's release. "It's about having a monopoly over our personal information, which, if it falls into the wrong hands, could be used in a very dangerous way against us," Court said. Google's senior product counsel, Michael Yang, said the company is not using any data from Chrome to make improvements to its ad services. But that doesn't mollify privacy critics, who fear Google might start doing that someday to best capitalize on its vast audience. Some 650 million people use Google's search engine and panoply of Web services. "The way Google has fashioned Chrome, it's a digital Trojan horse to collect even more masses of consumer data for Google's digital advertising business," said Jeff Chester, executive director for the Center for Digital Democracy, a consumer rights organization. For now, at least, Google is planning to adopt just one change suggested by Consumer Watchdog. When users spell a Web site's address incorrectly, Chrome sends a request to Google to help determine the actual site the user is trying to visit. This happens even when users are surfing "incognito," and Rakowski said it was an oversight. "It's something we're prioritizing now that we want to fix," he said. This is not to say that Google is avoiding other privacy-related changes. In July, the company began linking to its privacy policy on its home page. It also recently began its anonymization of the data it stores through the "Google Suggest" feature. But one other privacy-related move might say more about how Google is perceived than anything. In September, to placate European Union data protection officials, Google said it would maintain its search logs _ which track search queries and the IP addresses they came from _ for nine months instead of 18, as it had been doing. After that time, Google will alter IP addresses to mask their source. (That probably won't provide true anonymity, since an aggregated list of search queries over time will likely reveal clues about who made them.) Google hoped the move would win it favor. After all, Microsoft waits 18 months before it anonymizes its search engine logs, and Yahoo does so after 13. Even so, the EU's justice and home affairs commissioner said Google should shorten its logs further, to six months. Davies, of Privacy International, says the change from 18 to nine months was "not meaningful." Court says that with all its products, Google has more opportunities than its peers to capture personal information without users realizing it. "Google's founders may say, `We're going to protect that information,' but no other company," he said, "is positioned to exploit that information in the way Google is. http://www.washingtonpost.com/wp-dyn...110300956.html  Porn Mode for Firefox A Firefox developer has revealed that pre-release versions of Firefox 3.1 have been updated with a new feature. Officially called 'Private Browsing' it will be more familiar to many as the much talked about Porn Mode that caused such controversy when Microsoft announced it was being included within the forthcoming IE8 browser. I am not at all surprised to discover that Firefox 3.1, AKA Firefox Shiretoko, is adding this functionality as one of the things that I have always liked about the Mozilla browsing experience is the control over user privacy that it provides. Indeed, you might ask in the light of this how is the new Porn Mode any different to the existing Clear Private Data function which deletes your browsing history, cookies, cache etc after a session at the press of a button or even automatically when you close the browser itself if you have it so configured as I do? The answer would seem to be that it provides a best of both worlds scenario where you can ensure that no trace of your private browsing session is left on the computer but without impacting upon the non-private parts of your browsing activity. By which I mean that at present it's really an all or nothing, hit it with a lump hammer type affair. Get rid of everything to maintain privacy, but lose the benefit of that historical clicktrail for retracing steps when you need it later for example. In essence, porn mode provides a sandboxed environment (from a privacy perspective) in which to browse but only for the duration of that session. Toggle it off and you are back to normal, without having to restart the browser and flush the cache etc. Let's hope they sort all the bugs out before it is released though. http://www.daniweb.com/blogs/entry3462.html  Once Thought Safe, WPA Wi-Fi Encryption is Cracked Robert McMillan Security researchers say they've developed a way to partially crack the Wi-Fi Protected Access (WPA) encryption standard used to protect data on many wireless networks. The attack, described as the first practical attack on WPA, will be discussed at the PacSec conference in Tokyo next week. There, researcher Erik Tews will show how he was able to crack WPA encryption, in order to read data being sent from a router to a laptop computer. The attack could also be used to send bogus information to a client connected to the router. To do this, Tews and his co-researcher Martin Beck found a way to break the Temporal Key Integrity Protocol (TKIP) key, used by WPA, in a relatively short amount of time: 12 to 15 minutes, according to Dragos Ruiu, the PacSec conference's organizer. They have not, however, managed to crack the encryption keys used to secure data that goes from the PC to the router in this particular attack Security experts had known that TKIP could be cracked using what's known as a dictionary attack. Using massive computational resources, the attacker essentially cracks the encryption by making an extremely large number of educated guesses as to what key is being used to secure the wireless data. The work of Tews and Beck does not involve a dictionary attack, however. To pull off their trick, the researchers first discovered a way to trick a WPA router into sending them large amounts of data. This makes cracking the key easier, but this technique is also combined with a "mathematical breakthrough," that lets them crack WPA much more quickly than any previous attempt, Ruiu said. Tews is planning to publish the cryptographic work in an academic journal in the coming months, Ruiu said. Some of the code used in the attack was quietly added to Beck's Aircrack-ng Wi-Fi encryption hacking tool two weeks ago, he added. WPA is widely used on today's Wi-Fi networks and is considered a better alternative to the original WEP (Wired Equivalent Privacy) standard, which was developed in the late 1990s. Soon after the development of WEP, however, hackers found a way to break its encryption and it is now considered insecure by most security professionals. Store chain T.J. Maxx was in the process of upgrading from WEP to WPA encryption when it experienced one of the most widely publicized data breaches in U.S. history, in which hundreds of millions of credit card numbers were stolen over a two-year period. A new wireless standard known as WPA2 is considered safe from the attack developed by Tews and Beck, but many WPA2 routers also support WPA. "Everybody has been saying, 'Go to WPA because WEP is broken,'" Ruiu said. "This is a break in WPA." If WPA is significantly compromised, it would be a big blow for enterprise customers who have been increasingly adopting it, said Sri Sundaralingam, vice president of product management with wireless network security vendor AirTight Networks. Although customers can adopt Wi-Fi technology such as WPA2 or virtual private network software that will protect them from this attack, there are still may devices that connect to the network using WPA, or even the thoroughly cracked WEP standard, he said. Ruiu expects a lot more WPA research to follow this work. "Its just the starting point," he said. "Erik and Martin have just opened the box on a whole new hacker playground." http://www.itworld.com/security/5728...yption-cracked  WiFi Gains Strength in Cities Kim Hart Over the past three years, large cities and rural towns promised to bring WiFi to every street corner, park bench and doorstep. The wireless service was to be the key to extending cheap Internet access to underserved areas and low-income neighborhoods. But the efforts largely fell flat as Internet service providers abandoned the projects, which proved to be far more expensive than expected, leaving cities such as Philadelphia and Chicago -- as well as Alexandria and Arlington -- disconnected and discontent. Many municipalities decided to move forward by investing in the technology themselves. The souring economy has further encouraged some cities to experiment with building their own networks as a way to spur economic development. "The projects that are succeeding focus on government first," said Craig Settles, an independent wireless analyst and business consultant. "The cost to build the infrastructure is paid back with benefits for the government. If you want to expand beyond that, you don't need as many consumers to make the network profitable." Having a stake in the network means police officers, building inspectors and paramedics, for example, can access the network while working in the field, and the government can sell excess capacity to residents and businesses. Some communities are providing free WiFi to attract shops and offices to slumping areas. Such experiments come as federal officials try to shape broadband policies. The United States has fallen behind other countries in terms of broadband speed and reach, according to the Organization for Economic Cooperation and Development, an international organization. Federal Communications Commission Chairman Kevin J. Martin yesterday won approval to use empty TV airwaves for wireless broadband, a proposal backed by Google and Microsoft. Martin also wants to use another section of airwaves to provide free, filtered Internet access. Sprint Nextel and Clearwire recently launched WiMax service in Baltimore, with promises to provide wireless service for mobile devices. While these projects are getting off the ground, WiFi networks are the most feasible way to provide an alternative to typical DSL or cable Internet lines, said Esme Vos, editor of MuniWireless.com. "It is probably the easiest way to get competition as quickly as possible." WiFi networks, most often used in coffee shops and airports, beam Internet service through a building by connecting many transmitters, or hot spots. A citywide network would cobble together enough hot spots to cover every block. The push to drench cities with cheap wireless service began in 2005, when Philadelphia officials announced plans to bring Internet service to everyone within 130 square miles. Earthlink, an Internet service provider, pledged to build the sprawling network and reap revenue from subscriptions, and the city was to let the company erect WiFi transmitters, or hot spots, on buildings and lamp posts. A dozen other cities enthusiastically made similar plans. But the build-out process was slow and costly. A WiFi hot spot has a short signal range, so a few thousand, rather than initial estimates of a few dozen, were needed to blanket entire cities. And the service was often less reliable than the Internet service many residents already paid for at home, so they were reluctant to pay an additional subscription fee. A year ago, Earthlink pulled out of projects across the country. Other companies, such as MetroFi and Gobility, did the same. Cities from San Francisco and Houston to Portland, Ore., and Tempe, Ariz., stopped expanding or halted service. The profit-making model was the main cause of the failures, said Sascha Meinrath, technology analyst for the New America Foundation, a District-based research organization. "These communications systems should not just be solely about profit margins . . . It's more about providing a public service," he said. "Look at what cities pay for landscaping and street lights. It's a shame this hasn't been made a higher priority." Maryland's Allegany County built a network for the school system seven years ago, and it has since expanded to businesses, nonprofit groups, police departments, museums and government agencies. Cumberland, the county seat, now has service in its downtown area. Conxx, the Cumberland-based company that runs the county's network, is constructing a city-owned network intended to provide free Internet service to low-income students in Harrisburg, Pa. The company is building a network in Ohio to provide automatic utility meter-reading to cut costs. Mike Voll, vice president of sales for the firm, said interest in deploying city-run networks has spiked over the past few weeks as municipalities start cutting budgets. Minneapolis, for example, partnered with a local Internet service provider to cover the city's 60 square miles. US Internet owns the network, which is made up of more than 3,000 hot spots, and the city's government is the largest customer, allowing workers to eliminate paper records and work remotely. Residents can subscribe to the network for $20 a month. The city spends about $1.3 million a year for the service, said Joe Caldwell, US Internet's chief executive. He said he receives at least two calls every week from cities looking for help deploying new networks. In the faltering economy, consumers are looking for cheaper alternatives for high-speed Internet service. San Francisco, left in a lurch when a partnership with Google and Earthlink dissolved last year, has become a test site for another company. Meraki first installed an Internet connection in a volunteer's home and used rooftop repeaters to extend the signal across several blocks. More than a quarter of the city's neighborhoods now have strong coverage, with 160,000 people using the free service, said chief executive Sanjit Biswas. Biswas hopes that, as more apartment buildings and coffee shops in town install their own hot spots, they will merge into a giant network that covers entire towns and suburbs. "For a few thousand dollars, you can light up a business district and then scale to grow into other areas," he said. Meinrath of the New America Foundation is experimenting with technologies in his Greenbelt neighborhood, trying to find the best equipment to expand the service to more households. "While we're waiting for a single company to fund everything," he said, "the rest of the world is leaving us farther and farther behind." http://www.washingtonpost.com/wp-dyn...110403443.html  F.C.C. to Open Radio Spectrum Matt Richtel Over the objections of television broadcasters and other groups, federal regulators set aside a disputed slice of radio spectrum for public use on Tuesday, hoping it would lead to low-cost, high-speed Internet access and new wireless devices. The Federal Communications Commission voted 5 to 0 to approve the new use for the unlicensed frequencies, known as white spaces. A coalition of powerful groups, including broadcasters, Broadway theater producers and sports franchises, hoped to derail or delay the decision. They have argued that their own transmissions — whether from television signals or from wireless microphones used in live music performances — could face interference from new devices that use the white spaces. But F.C.C. commissioners said in a public meeting on Tuesday that they were confident that enough testing had been done to assure them that interference was not a major risk. “It’s fair to say few other engineering analyses at the F.C.C. have been as lengthy and open,” said Michael J. Copps, a commissioner. Echoing the views of other commissioners, he added that the measure could lead to development of a new generation of devices that use the spectrum to provide Internet access. Commissioners said such access could be more reliable than Wi-Fi, which also uses unlicensed frequencies but does not reach as far. That view has been heralded by technology companies, like Google, Hewlett-Packard and Microsoft, which will benefit from the spread of Internet access. “Some have called this Wi-Fi on steroids,” Mr. Copps said. “I hope they’re correct.” The measure was championed by Kevin J. Martin, the F.C.C.’s chairman. Some commissioners voted for the measure but said they agreed with its opponents that the issue was pushed too quickly and that more time could have been taken for discussion or testing. “When the commission puts expediency ahead of an open process, it creates unnecessary resentment from parties that believe they were not given a fair hearing,” said Jonathan S. Adelstein, a commissioner. He said he nevertheless voted for the measure because he felt further delay was unlikely to change the outcome. In addition to the broadcasters, the decision was opposed by the Broadway theater industry, which argued that new devices using the white spaces could interfere with transmissions from wireless microphones and among crew members. A coalition of Broadway producers and performers joined the broadcasters in arguing that the F.C.C. should conduct more tests. “We are deeply disappointed with the F.C.C. decision that could silence Broadway productions and those at other venues around the country,” said Charlotte St. Martin, executive director of the Broadway League, a trade group representing the New York theater industry. The discussion over how to handle white spaces emerged in light of an impending change in the way television signals were delivered. Starting in February, TV stations will be required to switch to digital from analog delivery. Since 2004, the F.C.C. has been studying whether the frequencies between television channels — the white spaces — could be used by other devices, particularly because digital signals are less prone to interference. The F.C.C. performed two sets of tests that showed some potential for disruption on frequencies used by broadcasters, live theater performances or others who rely on the same spectrum. But F.C.C. commissioners said they had confidence that interference could be mitigated through tight regulation of new devices. For devices to be automatically certified by the commission, they must include technology that determines whether they are in a location where the channels are protected for use by incumbent broadcasters; if they are, they must find some other channel to transmit on. Mr. Martin said he expected that devices using the spectrum could be on the market within a year to 18 months. These might include portable communications gadgets as well as in-home electronics that, for instance, could carry a video signal from a computer or recording device to a television. Technology companies applauded the F.C.C.’s decision. “The F.C.C. has taken a significant step to usher in a new era of technology allowing for major investments in innovative wireless broadband,” Greg Brown, president and co-chief executive of Motorola, said in a statement. In a blog post, Larry Page, Google’s co-founder and president of products, said he believed engineers and entrepreneurs would be quick to build devices to take advantage of the white spaces. “We think that this spectrum will help put better and faster Internet connections in the hands of the public,” he wrote. http://www.nytimes.com/2008/11/05/te...ectrum.html?hp  Airwaves Battle Pits Dolly Parton Against Google Matt Richtel Tuesday marks the end of a battle that has lasted for more than two years, with each side predicting apocalyptic consequences should it lose. Not the fight for the presidency. The one pitting Google against Dolly Parton. The titan of Silicon Valley and the queen of Country are two of the many combatants in a high-tech dispute over precious slices of the nation’s airwaves. The issue comes to a head on Election Day, when the Federal Communications Commission votes on a proposal to make a disputed chunk of radio spectrum available for public use. Google, Microsoft, Hewlett-Packard and other technology companies say the spectrum could be used by a whole new array of Internet-connected wireless gadgets. They say freeing it up would encourage innovation and investment in much the same way that the spread of Wi-Fi technology has. (This would, of course, generate more business for tech companies.) But a coalition of old-guard media — from television networks to Broadway producers — is objecting to the proposal, saying it needs a closer look. The opponents argue that signals sent over those frequencies could interfere with broadcasts and wireless microphones at live productions. The measure appears likely to pass, though its opponents have mounted a spirited late-stage lobbying effort supported by Senator Hillary Rodham Clinton, Democrat of New York, and others in Congress, the professional sports leagues, Las Vegas casinos, a coalition of rock musicians and, of late, Ms. Parton, who is soon to open a Broadway show called “9 to 5: The Musical.” If the spectrum is set free, Ms. Parton says, chaos could reign on Broadway — in the form of static and other interference. “The potential direct negative impact on countless people may be immeasurable,” Ms. Parton wrote in a letter last month to the F.C.C., urging it not to release the frequencies. Ms. Parton got involved after she was contacted by the Broadway League, a theater-industry trade group that has lobbied the F.C.C. on the issue and coordinated support from performers. The trade group said Ms. Parton had been more engaged than other performers because she also was a producer of live shows. In the digital era, airwaves carrying television, cellphone and wireless Internet signals are highly valuable. The F.C.C. regulates the spectrum and auctions off licenses for its use — in some cases for billions of dollars — to private companies. But in this case it is considering setting aside a free or “unlicensed” chunk for public use. Tech companies argue that if it does so, entrepreneurs and innovators will create a new generation of devices that transmit signals farther and more reliably than Wi-Fi, which also relies on unlicensed spectrum. The technology could also handle cheap Internet-based phone calls. “This could lead to Wi-Fi on steroids,” said Richard Whitt, a Washington lobbyist for Google on telecommunications issues. “It could become a ubiquitous nationwide broadband network.” The battle between the old- and new-media companies is a byproduct of an impending change in the way over-the-air TV signals are delivered. In February, TV stations will be required to switch over from analog broadcasting to digital, which is less susceptible to radio interference. Since 2004, the F.C.C. has been studying whether it might make better use of some “white spaces,” TV frequencies that are not being used by broadcast channels. These frequencies have traditionally been left largely empty, because broadcasters send out such powerful signals that a buffer is needed between channels. The theory behind the F.C.C. proposal is that handheld devices and other gadgets emit such low levels of power that their transmissions will not overlap or interfere with the digital TV signals. Plus, the proposal’s supporters say, devices can be made smart enough to sense when they might interfere with a broadcast signal and find another frequency. The F.C.C. has been studying the potential for interference and found that most problems can be avoided through tight regulation of the new devices, said Kevin J. Martin, chairman of the F.C.C., who proposed the white space measure, and Michael J. Copps, a commissioner who supports it. “Some want 100 percent certainty, and that’s kind of difficult to provide,” Mr. Copps said. But he added that he supported the measure because there was ample evidence that the new devices would not interfere, and that further study would amount to unnecessary delay. “This unlicensed spectrum is going to be a tremendous force for innovation,” he said. The five-member commission seems likely to approve the measure, according to several people involved in the agency’s internal discussions but who declined to be named because they were not authorized to speak to the media. Beneath the surface of the debate are shifts in politics and culture. Heavy Internet and computer adoption by consumers has given the technology industry lobby more power and prominence. At the same time, the broadcast industry has lost some of its lobbying sway as consumer tastes have changed and advertising dollars have flowed to the Internet. Still, the National Association of Broadcasters, which represents 8,300 local and national television stations, is helping lead the effort to get the F.C.C. to postpone a decision on the measure. Without more testing, “this could be a recipe for potentially massive interference into the television spectrum,” said Dennis Wharton, a spokesman for the broadcasting trade group, arguing that TV screens could go temporarily dark or that pictures could freeze. Broadcasters say the signal could even disrupt channels received over cable. The interest of TV providers is different from that of Broadway theaters, which rely on wireless microphones to broadcast sound to the audience and for communication among crew members. Gerald Schoenfeld, chairman of the Shubert Organization, a Broadway production company, said new gadgets that were designed to use the disputed frequencies could interfere with the 450 wireless microphones used in New York’s theater district. That could lead to static, he said, or worse — if, for instance, crew member communications were interfered with, causing an accident, like a falling set piece. “There’s a danger element attached to this,” he said. “They are fooling with many aspects of American society under the pretext of helping get Internet access for parties that already have the greatest amount of Internet usage.” Urging a delay on the vote, Mr. Schoenfeld added: “Why this is being rushed through at this time is mystifying.” The wireless microphone technology used for Broadway shows and other events uses some of the same frequencies that regulators would like to open up for wireless data. But under the F.C.C. proposal, these incumbent users would be given first rights to the space. In her letter to the F.C.C., Ms. Parton conceded that she did not understand all the technicalities of the debate. But based on the counsel of others, she concluded that the potential problems were serious. She called the proposal “a dangerous and shortsighted answer to a highly complicated question.” The Broadway League and Ms. Parton’s representatives said she was too busy to comment further. For his part, Eric E. Schmidt, the chief executive of Google, sent his own letter to the F.C.C. recently. “We are eight days away from a vote that could transform the way we connect to the Internet,” he wrote. “The time for study and talk is over. The time for action has arrived.” http://www.nytimes.com/2008/11/04/te...reless.html?hp  Cable Must Air Broadcast Signals Judge says over-the-air viewers are entitled to same channels after digital switch David B. Wilkerson Cable-television operators must continue to carry the same broadcast channels that over-the-air viewers receive once those stations make their federally mandated conversion to digital signals in February, the U.S. Court of Appeals for the D.C. Circuit ruled Friday. Under the Federal Communications Commission's requirement, cable operators must either switch to all-digital systems, or carry both the digital and analog signals of local stations in the first three years after the February 2009 conversion. Millions of cable customers have only the most basic service, sometimes with boxes that receive only traditional analog signals, which take up far more bandwidth than digital signals. "Today's action preserves the commission's decision to protect consumers and prevents cable companies from either choosing to cut off signals of must-carry broadcast stations after the digital conversion, or requiring customers to purchase higher-priced packages with set-top boxes to receive the same analog channels in digital," said Kevin Martin, chairman of the FCC, in a statement. Some cable programmers argued that the FCC's order would make it harder for them to gain access to cable systems if both analog and digital signals of local stations had to be offered. Cable operators could say there wasn't room for niche channels with the addition of bandwidth-clogging analog signals. The programmers also said their First Amendment rights of free speech would be violated. But in its decision Friday, the D.C. Court said the programmers hadn't met the burden of proving that they would be harmed by the mandate. In her majority opinion, Judge Judith Rogers said the programmers' case faltered because they couldn't cite an example of a cable operator who isn't either already using all-digital operations or moving in that direction. She said the FCC has found that "virtually all cable operators" ultimately will have all-digital systems, which would free up bandwidth. http://online.wsj.com/article/SB122567594743092087.html  Sirius Shareholders Sue Sirius XM Radio Management FMQB A group of Sirius shareholders, upset with CEO Mel Karmazin and the state of satcaster stock, have filed a lawsuit against Sirius XM Radio management. The group, calling themselves "Save Sirius," accuses the satellite radio company's management of violating the Federal Racketeer Influenced and Corrupt Organizations Act (RICO), Breach of the Fiduciary Duty and The Sherman Act. It also seeks to prevent Sirius XM from "further damaging its shareholders with massive amounts of additional dilution" of its stock, including the potential "reverse split" of its stock. "We are working to gain control of our company by seeking to remove current members of the board as well as top executive Mel Karmazin," said Save Sirius spokesperson Michael Hartleib. He also references a Wall Street Journal interview with Karmazin from September, where the CEO mentioned he would consider taking Sirius XM private. Hartleib continued in the statement, "It is clear that management under Mr. Karmazin's leadership has an agenda to steal this company from its shareholders." He added, "In light of the aforementioned, it is clear that they have lost sight of their obligations to shareholders and have breached and will continue to breach their fiduciary duties in the future. We, as a group, will not stand for this and will use any means possible to prevent and preclude them from stealing this company from its rightful owners -- we the shareholders." http://fmqb.com/Article.asp?id=965949  CNN's Holograms Not Really Holograms Peter Nowak CNN reporter Jessica Yellin said she was following in the tradition of Princess Leia. (CNN) CNN made waves on Tuesday night by incorporating three-dimensional holograms into its coverage of the U.S. election. The only problem was, they weren't really holograms. "They were quite sophisticated, no doubt," said Hans Jürgen Kreuzer, a professor of theoretical physics at Dalhousie University and an expert on holography who watched the 3-D interviews. "But I immediately said to my wife that I don't think it has anything to do with holograms." At about 7 p.m. EST, reporter Jessica Yellin, who was in Chicago, spoke with New York-based anchor Wolf Blitzer live "via hologram," CNN said. Yellin appeared somewhat fuzzy and her image, apparently projected a few feet in front of Blitzer, appeared to glow around the edges. "You're a terrific hologram," Blitzer said to her. "It's like I follow the tradition of Princess Leia," she said, referring to the Star Wars character. Yellin explained that her image was being filmed in Chicago by 35 high-definition cameras set in a ring inside a special tent, which were processed and synchronized by 20 computers to the cameras in the New York studio. The network, which made use of three-dimensional imaging technology produced by Norway-based Vizrt and Israel-based SportVu, billed the interview as a first for television. CNN also aired a second "hologram" interview between anchor Anderson Cooper and rapper Will.I.Am, who was also in Chicago. The CNN anchors were not really speaking to three-dimensional projected images, but rather empty space, Kreuzer said. The images were simply added to what viewers saw on their screens at home, in much the same way computer-generated special effects are added to movies. Kreuzer said the images were tomograms, which are images that are captured from all sides, reconstructed by computers, then displayed on screen. Holograms, on the other hand, are projected into space. CNN officials could not be reached for comment. Kreuzer said technology is not far from being able to produce what CNN had tried to do, although capturing and projecting holograms of big objects like people is still a ways off. Holographic images are generally captured and projected using coherent light such as lasers. A laser would need to be more than six feet in diameter to capture a person's image, which Kreuzer said is impossible because such a light would be blinding. It may soon be possible to capture and project large objects using other sources of coherent light, such as light-emitting diodes. LEDs are considerably cheaper and safer than lasers, Kreuzer said. "There will be some rapid development now because of the cheapness of these LEDs," he said. "You can use a thousand if you want." http://www.cbc.ca/technology/story/2...holograms.html  Shazam! A Projector Is Shrunk David Pogue Come on, admit it: is there anything more awesome than miniaturization? The Walkman put a stereo system in your pocket and changed the game forever. A modern digital watch has the computing power of a roomful of 1950s computer gear. And people are watching TV shows these days on iPods about the size of a business card. Enormous feats of shrinkage like that don’t come along very often, though. So when they do, you sit up and take notice — as you will the first time you see the Optoma Pico Projector ($430 list price). It’s a long-awaited, much-rumored projector about the size of a cellphone: 2 by 4.1 by 0.7 inches, weighing 4.2 ounces. A pocket projector? Are you kidding? This isn’t just a new product — it’s a whole new product category. Regular projectors, of course, are big, heavy, expensive, sometimes noisy machines. They’re standard equipment in corporate boardrooms where PowerPoint jockeys hold sway, in classrooms or auditoriums, or mounted to the ceiling in home theaters, where they provide extra-large movie-watching goodness. But there are lots of times when a 100-inch screen is overkill — and yet a 2-inch iPod screen doesn’t quite cut it. Those are the times when you need something in between. In those situations, a completely silent, ridiculously simple micro-projector like the Pico really shines. You’d have to be a jaded gizmophile indeed not to be impressed the first time you turn on this tiny, shiny black box. In the center of the short end, there’s a very bright light-emitting-diode lamp. Inside, there’s a miniaturized Texas Instruments digital-light-processing (D.L.P.) chip, similar in principle to the ones that drive some full-size HDTV sets. Together, they produce an astonishingly bright, clear, vivid video or still image. That’s right — from a projector you’ve pulled from your jeans pocket. There are no footnotes for that jeans-pocket statement, either (like, “not including enormous power brick”), because the Pico can run on battery power. Each charge lasts for about 90 minutes — longer if you use the lower brightness setting or when you’re playing video without sound. You can recharge the projector either from its power cord or from a computer’s USB jack. A spare battery comes with the projector, and so does a little drawstring carrying bag. A pocket-size, self-contained projector changes all the rules. An iPod and a Pico — that’s the entire setup. Now, for the first time, a tent wall can become a movie screen when you’re out camping. (So much for roughing it.) Now, let’s be clear: no pocket projector is going to produce as much brightness as tabletop projectors 10 times its size. The Pico manages 9 lumens (that’s how they measure the brightness of things like projectors), compared with, for example, 2,000 lumens for a $900 tabletop projector. That may not sound like much, but it’s plenty bright at the Pico’s shorter distances and smaller “screen” sizes. The minimum distance for this projector is eight inches from your “screen”; the maximum is 8.5 feet away, at which point you get a 65-inch image. And it really, really helps if you dim the lights or use a properly reflective movie screen. You can sit this little gizmo on your airplane tray table and project onto the seat back in front of you. (Yes, I tried it.) You get a dazzlingly bright, sharp, vivid video image about a foot across, so that you and your immediate seatmates can all watch. (Or shine the projector onto the plane’s ceiling. The three-foot movie image completely baffles everyone within several rows; nobody can figure out where it’s coming from. I tried that, too. It was fun.) Or you can park the projector on a little tripod — it comes with a tiny, screw-in tripod adapter — and project tonight’s dorm-room Wii marathon onto a bed sheet or someone’s T-shirt. Or you can lie in bed and point the thing straight up. In a dark room, you’ll have yourself a huge, bright movie playing on the ceiling. There’s no keystone adjustment to compensate for when the projector is facing the screen at an angle. The 20,000-hour bulb is not replaceable. And the picture resolution is only 480 by 320 pixels — on paper, much coarser than the 1024-by-768-pixel (or higher) resolution of a tabletop projector. But you know what? Pixels are overrated. Nobody will complain about the sharpness of the Pico’s image, especially after you find just the right spot on its little Focus dial. Over all, the Pico does surprisingly well. So what can you watch on this thing? It comes with a special composite cable. On one end, there’s a special, tiny audio-video pin that goes into the projector. On the other end, you’ll find the familiar three-headed, red-white-yellow RCA cables. These are female jacks, made to mate with the male composite cables that come with just about every DVD player, VCR, game console, digital camera and camcorder ever sold. So in a pinch, the Pico projector could replace a TV set when you’re using full-size gear like DVD players or game consoles. But the true mission of the Pico’s miraculous miniaturization is connecting to fellow micro-gadgets: digital cameras, cellphones, iPods or iPhones, for example. The necessary adapter for the iPod or iPhone comes with the projector. Old video iPods require only the short black cable, which goes into the iPod’s headphone jack but carries both audio and video. You also get a plastic nub that snaps onto the bottom of the iPhone or more recent iPods; the short black cable connects the nub to the projector. (The projector produces an image only when videos are playing. It doesn’t show, for example, the iPhone’s Web browser, e-mail program or other applications — a shame for instructors or anyone else who might like a way to demonstrate the iPhone’s workings to more than one audience member at a time.) To connect a digital camera, so you can show off your stills or your videos, or to connect your camcorder, you use the composite TV cable that came with it. Optoma plans to make adapter cables available for other smartphones in the coming months, starting with a Nokia cable for $10. The Pico projector does so much so well with so little, it might sound ungrateful to bring up its one really embarrassing shortfall. But somebody has to say it: What about the sound? The Pico has a built-in speaker, yes, but it’s about the size of a hydrogen atom. With the iPod volume cranked to full, the Pico puts out about as much volume as you ordinarily hear leaking from earbuds on somebody sitting next to you. In other words, the projector is as bad with audio as it is good with video. If you’re using an iPod, iPhone or cellphone, your last, best hope is the headphone jack. You can listen through earbuds, of course, although that’s not much of a communal experience. (A headphone splitter would at least let you invite a friend.) Or you can connect that headphone jack to a portable speaker — but now, of course, you’ve got a much more complex rack of gear, and you’re way beyond the realm of jeans pockets. Even so, the Pico projector is the first of its kind — other micro-projectors are on the way — and over all, it’s awesome. When it goes on sale in two weeks, it will give parents a completely portable backseat-of-the-minivan movie theater for the kids. It will let photographers display their portfolios with much greater size and impact than they’d get with a scrapbook — right from the digital camera, if need be. It will permit spur-of-the-moment demos or pitches for corporate presenters or independent filmmakers, wherever they happen to be, without having to set anything up or reserve a room. Miniaturization: it’s a blast, man. Gotta love those engineers. Just wait till they get their hands on air-conditioners, TiVos and jet engines. http://www.nytimes.com/2008/11/05/te...ogue.html?8dpc  Scripps Tries to Steer Local Ads to Papers’ Sites Stephanie Clifford KNOXVILLE, Tenn., is a place where residents root for the Vols, prefer their iced tea sweet and turn to the Knoxville News Sentinel for local coverage. The paper has been around since 1886, and it has entered the Internet age with a Web site featuring videos and blogs. But central as The News Sentinel may be to the local community, it is not attracting local advertisers to its Web site. This is a problem that newspapers across the country are having. Local advertisers, though, are spending more and more money online — but it is mostly going to portals and stand-alone Web sites, not newspapers. Local advertisers are expected to spend almost $12.9 billion online this year, almost five times what they spent in 2004, according to Borrell Associates, a firm that researches local media. But while newspaper sites received 44 percent of local Internet revenue in 2004, that figure dropped to 27 percent this year, according to Borrell. Now, publications like The News Sentinel, which is part of the E. W. Scripps Company, A. H. Belo and McClatchy are revamping their online sales to capture local ads. Since so many things are hurting newspaper companies — like rising printing and distribution costs, credit troubles, decreasing circulation and plummeting print advertising — online growth is essential. “That’s where we have most of our sights set for the foreseeable future,” said Rusty Coats, vice president for interactive at Scripps. “That’s the largest source of our growth across the company.” Mr. Coats is so confident about the strategy that he projects that Scripps Web sites will sell enough ads to support the staff and costs of the print and online newsrooms by 2012, without staff cuts. If Scripps could achieve that, it would mark a turnaround for it and for other newspaper publishers, who have been slashing costs to stay alive. Until recently, newspapers’ sales employees have focused on big local accounts, not small ones. And newspapers, especially local ones, did not emphasize Internet-only sales in recent years. Instead, the sales forces sold print ads and threw in Internet ad campaigns for those print advertisers. Print advertising at newspapers was down 16 percent in the second quarter, according to the Newspaper Association of America. When print sales decline and the ads are bundled, online sales decline. Scripps, where online revenue dropped 8 percent in the second quarter, has begun overhauling the way it sells local ads. At Scripps, about 10 percent of the advertising revenue comes from the Internet. Of that, 68 percent is tied to print ads, said Mark Contreras, the senior vice president for newspapers. The revenue from online advertising that is tethered to print is down about 17 percent this year compared with last, Mr. Contreras said. The online-only revenue is up almost 30 percent. So Mr. Contreras is reshuffling ad commission plans at Scripps. Currently, 95 percent of his sales employees’ bonuses is based on print sales, he said, and he will lower that to 70 percent by raising commissions for online ads. He is also adding sales staff who sell only online ads. He is even trying telemarketing, setting up a call center where representatives will call small businesses in Scripps markets. Scripps is also using the new Apt system from Yahoo, which was introduced in September. Apt stores and displays ads on newspaper sites, among other things, and lets newspaper sales teams sell ads that appear on local Yahoo sites. Apt also lets local newspapers use Yahoo’s behavioral targeting capabilities. Yahoo can deduce the likely age, gender, location and interests of someone looking at a page and show them a relevant ad. If someone types “Brazil” into Yahoo search and visits the Yahoo travel site, Yahoo might note that the person is interested in travel. Later, when the person (or, technically, the same Web browser) visits the News Sentinel site, Apt can display an ad for airfare to South America. Scripps sites tried behavioral targeting in the past but it was unsuccessful, Mr. Coats said, since Scripps couldn’t sell a big enough target audience to interest advertisers. With Apt, though, since newspapers can sell ads on certain Yahoo pages — like Yahoo Mail — they can gather a big enough group. The Knoxville paper switched to the Yahoo system two weeks ago. Mr. Coats said he expected that with targeted ads, Scripps sales staff could sell ads at two to three times the current price. That may be high: The News Sentinel’s director of digital media, Jay Horton, said the plan for his site was to raise the average charge to $12 to $15 per thousand impressions (the number of times an ad is seen) from $8 to $12. Karl Thomas, the director of marketing at Ripley’s Aquarium of the Smokies in Gatlinburg, Tenn., tried the system during its test phase. He ran an ad on aquarium admission, targeted to women with children, and received a “really good response,” he said. Scripps, the MediaNews Group, and Cox are among the first newspaper companies to use Apt. Other publishers are trying to ignite online sales, too. At McClatchy, about half of the online sales are tied to print, said Christian A. Hendricks, the vice president for interactive media. In the third quarter, online advertising sales rose 9 percent from a year earlier; online-only sales rose 27 percent, he said. McClatchy recently changed its commission plans to give sales representatives more incentive to sell online alone. At A. H. Belo, Internet revenue fell 19 percent in the third quarter from a year earlier. Executives are trying to remedy that. The company is starting to use telemarketers to woo local florists and barbers, and, because small businesses do not usually have their own graphics experts, Belo is building a make-your-own-ad tool. The company has also tested the Apt system at its Dallas Morning News Web site and is “having huge success” so far, said Donald F. Cass Jr., executive vice president of A. H. Belo. “There’s opportunity to do things we’re not doing today,” Mr. Cass said. “We just need to get about the business of doing it.” http://www.nytimes.com/2008/11/03/bu...a/03adcol.html  Critical Vulnerability in Adobe Reader Core Security Technologies issued an advisory disclosing a vulnerability that could affect millions of individuals and businesses using Adobe’s Reader PDF file viewing software. Engineers from CoreLabs determined that Adobe Reader could be exploited to gain access to vulnerable systems via the use of a specially crafted PDF file with malicious JavaScript content. Upon making the discovery, CoreLabs immediately alerted Adobe to the vulnerability and the two companies have since coordinated efforts to ensure that a patch could be created and made available to protect users of the program. Successful exploitation of the vulnerability requires that users open a maliciously crafted PDF file thereby allowing attackers to gain access to vulnerable systems and assume the privileges of a user running Acrobat Reader. Adobe Reader version 9, which was released in June 2008, is not vulnerable to the reported problem. Adobe has issued a security update that addresses the vulnerable version 8.1.2 of Reader. Alternatively, users of affected versions of the program can also work around the problem and reduce their exposure by disabling JavaScript functionality in the software’s Edit|Preferences menu. Vulnerability details While investigating the feasibility of exploiting a vulnerability previously disclosed in Foxit Reader (CVE-2008-1104), a CoreLabs researcher found that Adobe Reader was affected by the same bug. After an initial examination of the involved implementation bug, it was believed that although the problem was present, it was apparently not exploitable in Adobe Reader due to the use of two structured exception handlers in the program. The primary difference between the Adobe and Foxit applications is the manner in which they perform security checks, and at first glance, it seemed as if the bug was not exploitable in Reader, since there was no way to control the program’s first exception handler. However, upon further examination of the code, CoreLabs found that another overflow occurs before the call to the involved code is made in relation to the previously known vulnerability. This new problem was identified in the way vulnerable versions of Adobe Reader implement the JavaScript util.printf() function. The function first converts the argument it receives to a String, using only the first 16 digits of the argument and padding the rest with a fixed value of “0” (0x30). By passing an overly long and properly formatted command to the function, it is possible to overwrite the program’s memory and control its execution flow. A specifically crafted PDF file that embeds JavaScript code to manipulate the program’s memory allocation pattern and trigger the vulnerability can allow an attack to execute arbitrary code with the privileges of a user running the Adobe Reader application. The vulnerability was discovered by Damián Frizza, a CoreLabs researcher and software engineer with the CORE IMPACT Exploit Writers Team. The previously disclosed vulnerability (CVE-2008-1104) mentioned in this report was discovered in Foxit Reader by Dyon Balding from Secunia Research and disclosed on May 20th, 2008. http://www.net-security.org/secworld.php?id=6715  Hackers and Spending Sprees The computer systems of both the Obama and McCain campaigns were victims of a sophisticated cyberattack by an unknown "foreign entity," prompting a federal investigation, NEWSWEEK reports today. At the Obama headquarters in midsummer, technology experts detected what they initially thought was a computer virus—a case of "phishing," a form of hacking often employed to steal passwords or credit-card numbers. But by the next day, both the FBI and the Secret Service came to the campaign with an ominous warning: "You have a problem way bigger than what you understand," an agent told Obama's team. "You have been compromised, and a serious amount of files have been loaded off your system." The following day, Obama campaign chief David Plouffe heard from White House chief of staff Josh Bolten, to the same effect: "You have a real problem ... and you have to deal with it." The Feds told Obama's aides in late August that the McCain campaign's computer system had been similarly compromised. A top McCain official confirmed to NEWSWEEK that the campaign's computer system had been hacked and that the FBI had become involved. Officials at the FBI and the White House told the Obama campaign that they believed a foreign entity or organization sought to gather information on the evolution of both camps' policy positions—information that might be useful in negotiations with a future administration. The Feds assured the Obama team that it had not been hacked by its political opponents. (Obama technical experts later speculated that the hackers were Russian or Chinese.) A security firm retained by the Obama campaign took steps to secure its computer system and end the intrusion. White House and FBI officials had no comment earlier this week. NEWSWEEK has also learned that Palin's shopping spree at high-end department stores was more extensive than previously reported. While publicly supporting Palin, McCain's top advisers privately fumed at what they regarded as her outrageous profligacy. One senior aide said that Nicolle Wallace had told Palin to buy three suits for the convention and hire a stylist. But instead, the vice presidential nominee began buying for herself and her family—clothes and accessories from top stores such as Saks Fifth Avenue and Neiman Marcus. According to two knowledgeable sources, a vast majority of the clothes were bought by a wealthy donor, who was shocked when he got the bill. The Week in Review is edited and published by Jack Spratts. Palin also used low-level staffers to buy some of the clothes on their credit cards. The McCain campaign found out last week when the aides sought reimbursement. One aide estimated that she spent "tens of thousands" more than the reported $150,000, and that $20,000 to $40,000 went to buy clothes for her husband. Some articles of clothing have apparently been lost. An angry aide characterized the shopping spree as "Wasilla hillbillies looting Neiman Marcus from coast to coast," and said the truth will eventually come out when the Republican Party audits its books. A Palin aide said: "Governor Palin was not directing staffers to put anything on their personal credit cards, and anything that staffers put on their credit cards has been reimbursed, like an expense. Nasty and false accusations following a defeat say more about the person who made them than they do about Governor Palin." McCain himself rarely spoke to Palin during the campaign, and aides kept him in the dark about the details of her spending on clothes because they were sure he would be offended. Palin asked to speak along with McCain at his Arizona concession speech Tuesday night, but campaign strategist Steve Schmidt vetoed the request. The disclosures are among many revealed in "How He Did It, 2008," the latest installment in NEWSWEEK's Special Election Project, which was first published in 1984. As in the previous editions, "How He Did It, 2008" is an inside, behind-the-scenes account of the presidential election produced by a special team of reporters working for more than a year on an embargoed basis and detached from the weekly magazine and Newsweek.com. Everything the project team learns is kept confidential until the day after the polls close. Among the other revelations from the special project: • The Obama campaign was provided with reports from the Secret Service showing a sharp and disturbing increase in threats to Obama in September and early October, at the same time that many crowds at Palin rallies became more frenzied. Michelle Obama was shaken by the vituperative crowds and the hot rhetoric from the GOP candidates. "Why would they try to make people hate us?" Michelle asked a top campaign aide. • On the Sunday night before the last debate, McCain's core group of advisers—Steve Schmidt, Rick Davis, adman Fred Davis, strategist Greg Strimple, pollster Bill McInturff and strategy director Sarah Simmons—met to decide whether to tell McCain that the race was effectively over, that he no longer had a chance to win. The consensus in the room was no, not yet, not while he still had "a pulse." • The Obama campaign's New Media experts created a computer program that would allow a "flusher"—the term for a volunteer who rounds up nonvoters on Election Day—to know exactly who had, and had not, voted in real time. They dubbed it Project Houdini, because of the way names disappear off the list instantly once people are identified as they wait in line at their local polling station. • Palin launched her attack on Obama's association with William Ayers, the former Weather Underground bomber, before the campaign had finalized a plan to raise the issue. McCain's advisers were working on a strategy that they hoped to unveil the following week, but McCain had not signed off on it, and top adviser Mark Salter was resisting. • McCain also was reluctant to use Obama's incendiary pastor, the Rev. Jeremiah Wright, as a campaign issue. The Republican had set firm boundaries: no Jeremiah Wright; no attacking Michelle Obama; no attacking Obama for not serving in the military. McCain balked at an ad using images of children that suggested that Obama might not protect them from terrorism. Schmidt vetoed ads suggesting thatObama was soft on crime (no Willie Hortons). And before word even got to McCain, Schmidt and Salter scuttled a "celebrity" ad of Obama dancing with talk-show host Ellen DeGeneres (the sight of a black man dancing with a lesbian was deemed too provocative). • Obama was never inclined to choose Sen. Hillary Clinton as his running mate, not so much because she had been his sometime bitter rival on the campaign trail, but because of her husband. Still, as Hillary's name came up in veep discussions, and Obama's advisers gave all the reasons why she should be kept off the ticket, Obama would stop and ask, "Are we sure?" He needed to be convinced one more time that the Clintons would do more harm than good. McCain, on the other hand, was relieved to face Sen. Joe Biden as the veep choice, and not Hillary Clinton, whom the McCain camp had truly feared. • McCain was dumbfounded when Congressman John Lewis, a civil-rights hero, issued a press release comparing the GOP nominee with former Alabama governor George Wallace, a segregationist infamous for stirring racial fears. McCain had devoted a chapter to Lewis in one of his books, "Why Courage Matters," and had so admired Lewis that he had once taken his children to meet him. • On the night she officially lost the Democratic nomination, Hillary Clinton enjoyed a long and friendly phone conversation with McCain. Clinton was actually on better terms with McCain than she was with Obama. Clinton and McCain had downed shots together on Senate junkets; they regarded each other as grizzled veterans of the political wars and shared a certain disdain for Obama as flashy and callow. • At the GOP convention in St. Paul, Palin was completely unfazed by the boys' club fraternity she had just joined. One night, Steve Schmidt and Mark Salter went to her hotel room to brief her. After a minute, Palin sailed into the room wearing nothing but a towel, with another on her wet hair. She told them to chat with her laconic husband, Todd. "I'll be just a minute," she said. • The debates unnerved both candidates. When he was preparing for them during the Democratic primaries, Obama was recorded saying, "I don't consider this to be a good format for me, which makes me more cautious. I often find myself trapped by the questions and thinking to myself, 'You know, this is a stupid question, but let me … answer it.' So when Brian Williams is asking me about what's a personal thing that you've done [that's green], and I say, you know, 'Well, I planted a bunch of trees.' And he says, 'I'm talking about personal.' What I'm thinking in my head is, 'Well, the truth is, Brian, we can't solve global warming because I f---ing changed light bulbs in my house. It's because of something collective'." http://www.newsweek.com/id/167581  Obama-Themed Malware on the Rise Robert Vamosi Within hours of settling the U.S. presidential election on Tuesday, spam seen worldwide began incorporating the name and image of Barack Obama, according to various security vendors. The U.K.'s Sophos reported 60 percent of all spam seen by the lab on Wednesday was in some way Obama related. One piece of spam alleges to contain a link to video of Obama's acceptance speech. If you follow the video link within the e-mail message you will be taken to a Web page where you'll be asked to update your Adobe Flash Player with a file, adobe_flash9.exe, first. This is not an official Adobe update file and downloading this file may in turn infect your computer with a Trojan. Sophos named the Trojan Mal/Behav-027. F-Secure named it W32/Papras.CL. Sunbelt Software also has a blog about this particular piece of spam. Meanwhile, Websense is reporting a separate threat. An e-mail appears to be an interview with the new president elect. The e-mail features embedded links to a video site that attempts to install a file, BarackObama.exe. Downloading this file may infect your computer with a Trojan. http://news.cnet.com/8301-1009_3-100...html?tag=mncol  HBO Acquires Rights to Obama Documentary Gregg Goldstein HBO has closed a seven-figure deal for U.S. rights to an untitled Barack Obama documentary produced by actor Edward Norton. Norton's Class 5 Films approached the Obama campaign in early 2006 about a documentary chronicling the new president elect's history in politics. Directors Amy Rice and Alicia Sams were granted extensive access to film Obama before he launched his presidential run in 2007 and have continued their shoot through his historic victory this week. HBO, which has been pursuing rights for several months, plans to air the documentary next year. "Senator Obama's history-making race for the White House has given our film a perfect framework to explore the pulse of the country at this vital moment in our history," said Norton, who produced the project with Stuart Blumberg and Bill Migliore. http://www.reuters.com/article/enter...4A60X920081107  Dead-Tree Editions Sell Out Corey Kilgannon 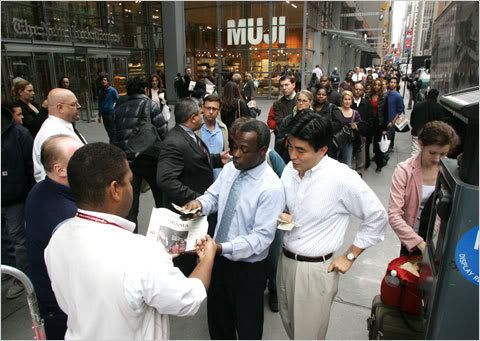 [Note to readers: Copies of Wednesday's paper were again available for the cover price Thursday morning at Times headquarters, at 620 Eighth Avenue in Manhattan, between 40th and 41st Streets. We are seeking more details about other ways to order a copy or commemorative edition.] Update | 2:50 p.m. If you were an early bird who likes news the old-fashioned way, you probably got your election results served up properly, with ink on newsprint — but if you slept late Wednesday morning, the news at many newsstands was that there was no News. No Daily News, that is. And no New York Times or New York Post, either. Newsstands across the city sold out of the daily city papers quickly, leaving latecomers searching for any remaining copies. “People want it as a souvenir,” said Rose Barmas, who runs a newsstand at Broadway and 116th Street. She said her daily papers were sold out by 9 a.m., including 180 copies of The Times. (Copies were up on eBay, with bidding as high as $100.) “I kept one copy for my son,” Ms. Barmas whispered. Across Broadway at 115th Street, M. D. Butto, at his newsstand, said he was tiring of telling people there were no more daily papers available. In Harlem, at the Eighth Avenue Deli Grocery, on Frederick Douglass Boulevard and 154th Street, the only papers left on the wire rack was a single copy of El Diario. (Headline: “Presidente.”) Gerald Addison, 54, a lifelong Harlem resident standing outside, said he had secured a Daily News, but his copies of other papers were snatched from a table in the front of the deli, when he put them down and turned his back to chat with friends. “People bought them all up early,” he said. “They were walking down the street waving them, because history was made.” Selim Malik, a Pakistani immigrant who works a newsstand at Broadway and 83rd Street, said customers were trying to buy up papers in quantity, so he had to establish a one-paper-per-customer rule. “By 8 a.m., I’m all sold out,” he said. “I called the company and asked for more papers, and they said, ‘Impossible.’ ” People walked up to the stand and asked for newspapers. Some registered their disappointment with shrugs, others with swear words. “I’ve turned away hundreds of people this morning,” he said. “They said there are no papers anywhere.” A man with a plastic bag filled with newspapers walked up and was told the same thing: No Times, no Post, no News. The man, a filmmaker and British native named Alex Wilson, was walking Broadway searching for newspapers to save for posterity. In a bag, he carried The Wall Street Journal, The New York Post, The New York Observer and The Financial Times. “It’s a momentous day for America, and I want the papers as mementos to show the grandkids someday, to show them this was a big turning point for this country.” Jennifer Mauer, a spokeswoman for The Daily News, said that by midday, the paper had printed more than 100,000 extra copies of the paper. A Times spokeswoman, Catherine J. Mathis, said on Wednesday morning that the paper had printed 35 percent more papers to be sold at newsstands. Still, by morning company officials found that papers were “selling out all across the metropolitan area” and decided to print 50,000 more copies for sale in the New York area. Ms. Mathis said that newly printed papers would be sold at select commuter hubs, including Pennsylvania Station, Grand Central Terminal and the Port Authority Bus Terminal. To address the additional demand, officials at The Times began selling copies of the paper directly outside the company’s headquarters at 40th Street and Eighth Avenue in Manhattan. On the sidewalk, security guards fashioned an ad-hoc newsstand by stacking several empty cardboard boxes. They rushed over bundles of newspapers and tried to maintain order as readers held out cash and clamored for papers, with many complaining about the one-per-customer policy. Sonia Pusey, 38, of a writer from Brooklyn, snagged the last paper, sending up a groan from the people lined up behind her. Ms. Pusey said she got to her newsstand in Brooklyn at 8 a.m. and asked the clerk to hold the last copy of The Times for her while she went to a cash machine. When she returned, he had sold it. “I said, ‘Do you know what you just sold?’ ” she recalled. ” ‘You just sold history.’ ” Ms. Pusey said she spent several hours searching Brooklyn and then Queens for daily newspapers and finally drove to The Times building. As she was leaving, the people in line roared as they spotted a man with a hand truck loaded with fresh newspapers. Ms. Mathis said The Times sold roughly 50,000 more copies than usual the day after Election Day in 2004, and “based on what we’ve seen today, we expect to significantly surpass those sales.” Print runs will also be increased for the Thursday paper, she said. The paper also reported a record-high 2.7 million “mobile page views” for Tuesday. http://cityroom.blogs.nytimes.com/20...s-sell-out/?hp Until next week, - js.  Current Week In Review  Recent WiRs - November 1st, October 25th, October 18th, October 11th Jack Spratts' Week In Review is published every Friday. Submit letters, articles, press releases, comments, questions etc. in plain text English to jackspratts (at) lycos (dot) com. Submission deadlines are Thursdays @ 1400 UTC. Please include contact info. The right to publish all remarks is reserved. "The First Amendment rests on the assumption that the widest possible dissemination of information from diverse and antagonistic sources is essential to the welfare of the public." - Hugo Black |
|||
|
|

|
|
|
#2 |
|
unibomber
Join Date: Dec 2003
Posts: 185
|
very nice read (very interesting read on the aussie censorship, i hadn't heard about that yet). keep it up!
|
|
|

|
 |
| Thread Tools | Search this Thread |
| Display Modes | |
|
|
 Similar Threads
Similar Threads
|
||||
| Thread | Thread Starter | Forum | Replies | Last Post |
| Peer-To-Peer News - The Week In Review - September 22nd, '07 | JackSpratts | Peer to Peer | 3 | 22-09-07 06:41 PM |
| Peer-To-Peer News - The Week In Review - May 19th, '07 | JackSpratts | Peer to Peer | 1 | 16-05-07 09:58 AM |
| Peer-To-Peer News - The Week In Review - December 9th, '06 | JackSpratts | Peer to Peer | 5 | 09-12-06 03:01 PM |
| Peer-To-Peer News - The Week In Review - September 16th, '06 | JackSpratts | Peer to Peer | 2 | 14-09-06 09:25 PM |
| Peer-To-Peer News - The Week In Review - July 22nd, '06 | JackSpratts | Peer to Peer | 1 | 20-07-06 03:03 PM |